| File name: | vcredist_x86 (1).exe |
| Full analysis: | https://app.any.run/tasks/ef32f33a-ef10-43ba-8c1e-ae439c9f420f |
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2024, 15:44:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8AC2452C46DD0F50FE156C0753CF1256 |
| SHA1: | E9B06A7AE593A616C5D66853F7889747FDC7345E |
| SHA256: | C42BFE261D606D2C37FBC57408CC10DE3884A278B73950987C6D646AC5AAC5C6 |
| SSDEEP: | 98304:o28pq+suCgGdZNvExjz1H9DH6wIRFm5WUlXFnqKHQuAxiu8fWWIZ9NypOsCPtWCz:e8IJOi00lcjicDE |
MALICIOUS
Drops the executable file immediately after the start
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Changes the autorun value in the registry
- vcredist_x86.exe (PID: 2332)
SUSPICIOUS
Process drops legitimate windows executable
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Starts a Microsoft application from unusual location
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Executable content was dropped or overwritten
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Searches for installed software
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Reads the Internet Settings
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Reads security settings of Internet Explorer
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Executes as Windows Service
- VSSVC.exe (PID: 3500)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 2332)
Checks Windows Trust Settings
- vcredist_x86.exe (PID: 2332)
Reads settings of System Certificates
- vcredist_x86.exe (PID: 2332)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 3240)
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Reads the computer name
- wmpnscfg.exe (PID: 3240)
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Create files in a temporary directory
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Reads the machine GUID from the registry
- vcredist_x86 (1).exe (PID: 2160)
- vcredist_x86.exe (PID: 2332)
Creates files in the program directory
- vcredist_x86.exe (PID: 2332)
Reads the software policy settings
- vcredist_x86.exe (PID: 2332)
Creates files or folders in the user directory
- vcredist_x86.exe (PID: 2332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:08:20 23:25:02+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 320000 |
| InitializedDataSize: | 34816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x474b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.61030.0 |
| ProductVersionNumber: | 11.0.61030.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
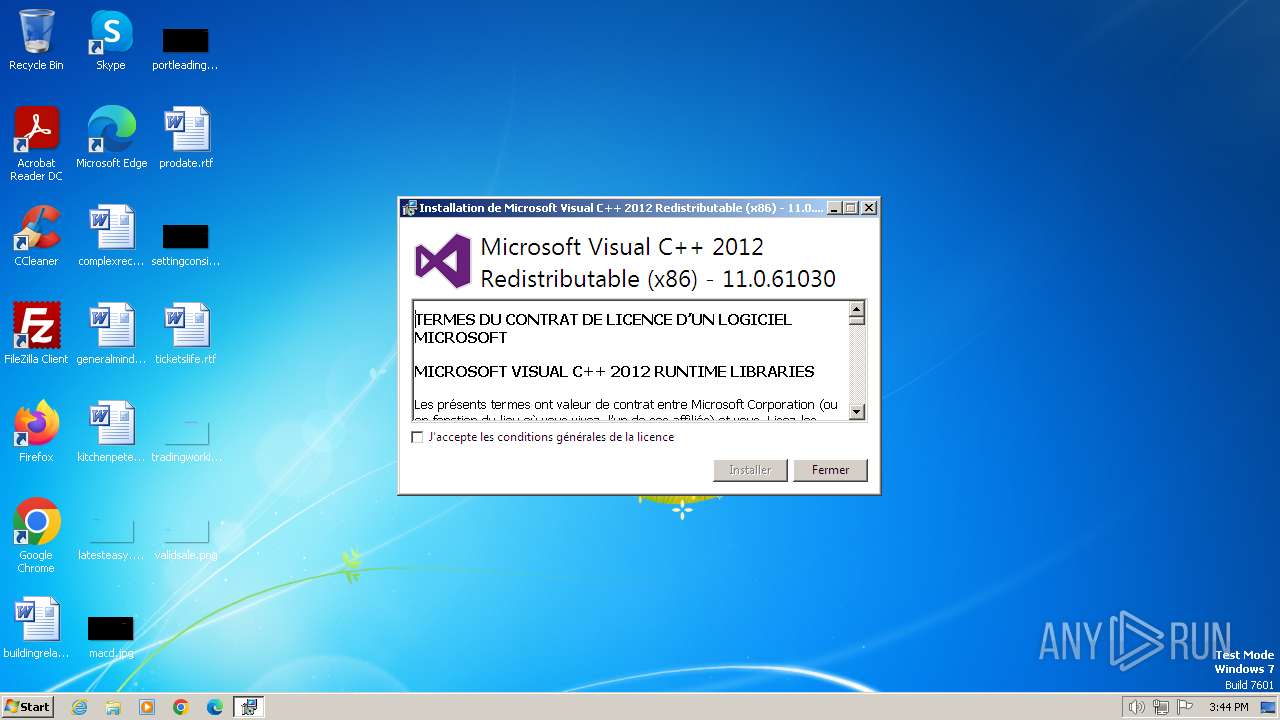
| FileDescription: | Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 |
| FileVersion: | 11.0.61030.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | vcredist_x86.exe |
| ProductName: | Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 |
| ProductVersion: | 11.0.61030.0 |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2160 | "C:\Users\admin\AppData\Local\Temp\vcredist_x86 (1).exe" | C:\Users\admin\AppData\Local\Temp\vcredist_x86 (1).exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\AppData\Local\Temp\{3bcf8c72-b231-4d28-9f39-3405c22d8b5a}\.be\vcredist_x86.exe" -q -burn.elevated BurnPipe.{319BFD16-FF6C-466A-A212-8ECA2B936A84} {B8882B0A-0DE4-416B-A40B-0AD648C9CFDB} 2160 | C:\Users\admin\AppData\Local\Temp\{3bcf8c72-b231-4d28-9f39-3405c22d8b5a}\.be\vcredist_x86.exe | vcredist_x86 (1).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 3240 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3500 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 277
Read events
11 075
Write events
190
Delete events
12
Modification events
| (PID) Process: | (2160) vcredist_x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2160) vcredist_x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2160) vcredist_x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2160) vcredist_x86 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2332) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000929BACF02560DA011C09000000090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2332) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000929BACF02560DA011C09000000090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2332) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 75 | |||
| (PID) Process: | (2332) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000005487B8F02560DA011C09000000090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2332) vcredist_x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000062AEBFF02560DA011C090000580A0000E8030000010000000000000000000000BB935D0199FC2A48BB39B92AE318C1EB0000000000000000 | |||
| (PID) Process: | (3500) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000070D5C6F02560DA01AC0D0000A00F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
10
Suspicious files
6
Text files
7
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2332 | vcredist_x86.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2160 | vcredist_x86 (1).exe | C:\Users\admin\AppData\Local\Temp\{3bcf8c72-b231-4d28-9f39-3405c22d8b5a}\cabB3E1576D1FEFBB979E13B1A5379E0B16 | — | |
MD5:— | SHA256:— | |||
| 2160 | vcredist_x86 (1).exe | C:\Users\admin\AppData\Local\Temp\{3bcf8c72-b231-4d28-9f39-3405c22d8b5a}\.ba1\logo.png | image | |
MD5:D6BD210F227442B3362493D046CEA233 | SHA256:335A256D4779EC5DCF283D007FB56FD8211BBCAF47DCD70FE60DED6A112744EF | |||
| 2160 | vcredist_x86 (1).exe | C:\Users\admin\AppData\Local\Temp\{3bcf8c72-b231-4d28-9f39-3405c22d8b5a}\.ba1\wixstdba.dll | executable | |
MD5:D7BF29763354EDA154AAD637017B5483 | SHA256:7F5F8FCFD84132579F07E395E65B44E1B031FE01A299BCE0E3DD590131C5CB93 | |||
| 2332 | vcredist_x86.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{015d93bb-fc99-482a-bb39-b92ae318c1eb}_OnDiskSnapshotProp | binary | |
MD5:A2BDBF46815F35B489AD539461EDCABB | SHA256:AC98398AA8E86CC7E566696FD3942EC3E33FF72CB702F0AD4BA5A4BC58514391 | |||
| 2160 | vcredist_x86 (1).exe | C:\Users\admin\AppData\Local\Temp\{3bcf8c72-b231-4d28-9f39-3405c22d8b5a}\.ba1\thm.wxl | xml | |
MD5:7B46AE8698459830A0F9116BC27DE7DF | SHA256:704DDF2E60C1F292BE95C7C79EE48FE8BA8534CEB7CCF9A9EA68B1AD788AE9D4 | |||
| 2332 | vcredist_x86.exe | C:\ProgramData\Package Cache\{3bcf8c72-b231-4d28-9f39-3405c22d8b5a}\vcredist_x86.exe | executable | |
MD5:6F85FA5CFAD1A3FB32ACBB813407A430 | SHA256:3F40737608E6185956F395043D61762FD9616D6AEFF96E94059E934558F4DF43 | |||
| 2160 | vcredist_x86 (1).exe | C:\Users\admin\AppData\Local\Temp\{3bcf8c72-b231-4d28-9f39-3405c22d8b5a}\.ba1\BootstrapperApplicationData.xml | xml | |
MD5:6182F3BB2D861DC04D0EA55F3BA4FFED | SHA256:EF0085C0476FBE4D6D170C6909F4AD35762FB05E125E9ED707B3C413AE6BBC74 | |||
| 2332 | vcredist_x86.exe | C:\ProgramData\Package Cache\.unverified\cabB3E1576D1FEFBB979E13B1A5379E0B16 | — | |
MD5:— | SHA256:— | |||
| 2332 | vcredist_x86.exe | C:\ProgramData\Package Cache\{B175520C-86A2-35A7-8619-86DC379688B9}v11.0.61030\packages\vcRuntimeAdditional_x86\cab1.cab | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2332 | vcredist_x86.exe | GET | 304 | 184.24.77.186:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3794d472e97dabfc | unknown | — | — | unknown |
2332 | vcredist_x86.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | binary | 767 b | unknown |
2332 | vcredist_x86.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | binary | 519 b | unknown |
1080 | svchost.exe | GET | 200 | 173.222.108.210:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c503292d7802e201 | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2332 | vcredist_x86.exe | 184.24.77.186:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2332 | vcredist_x86.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 173.222.108.210:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |