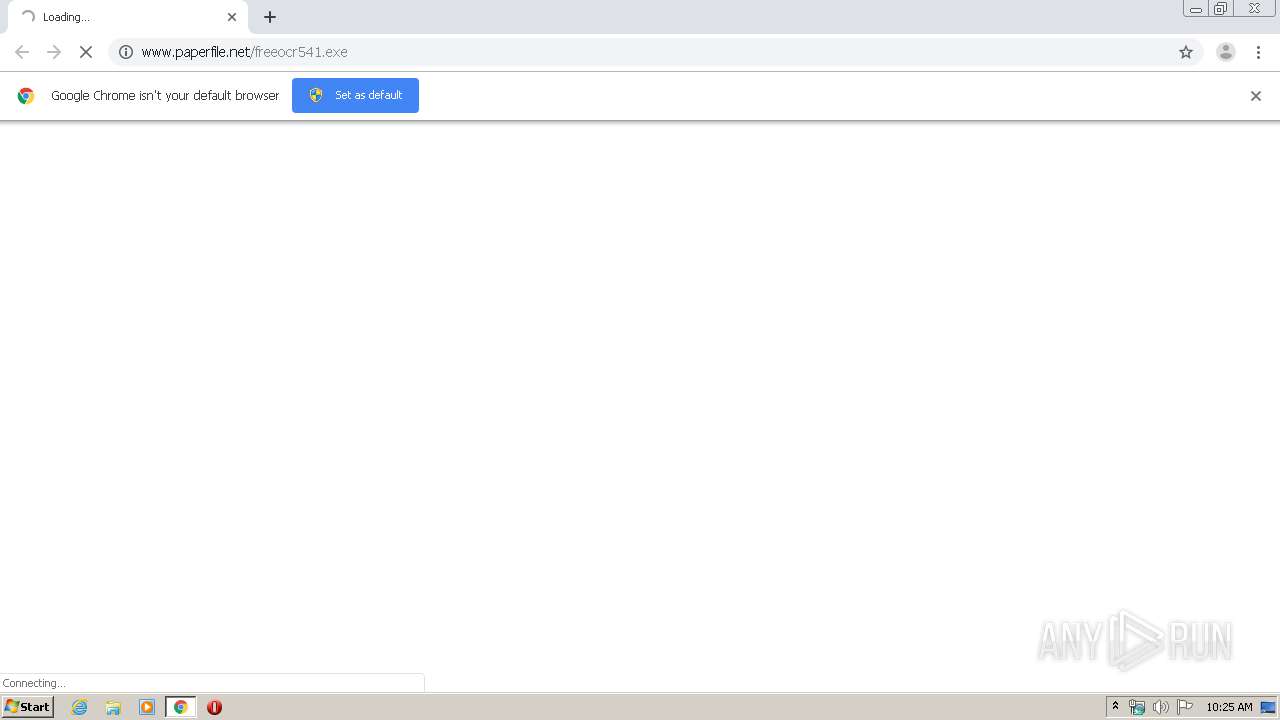
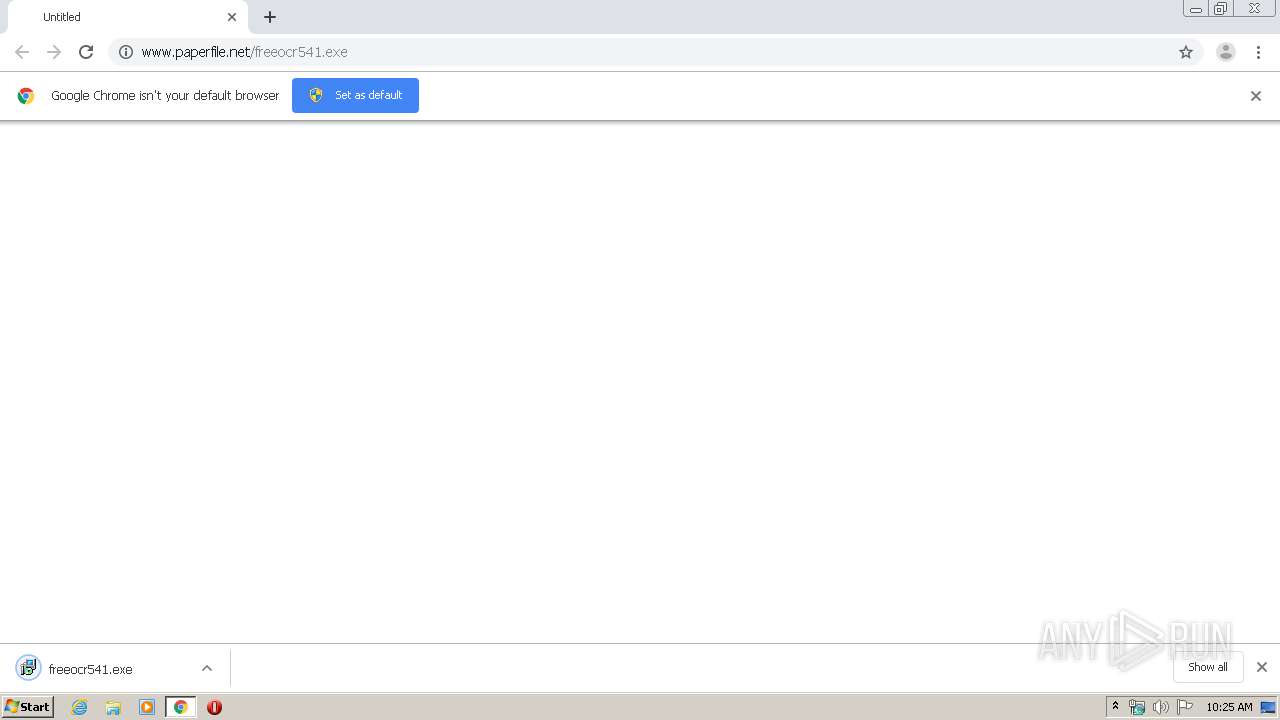
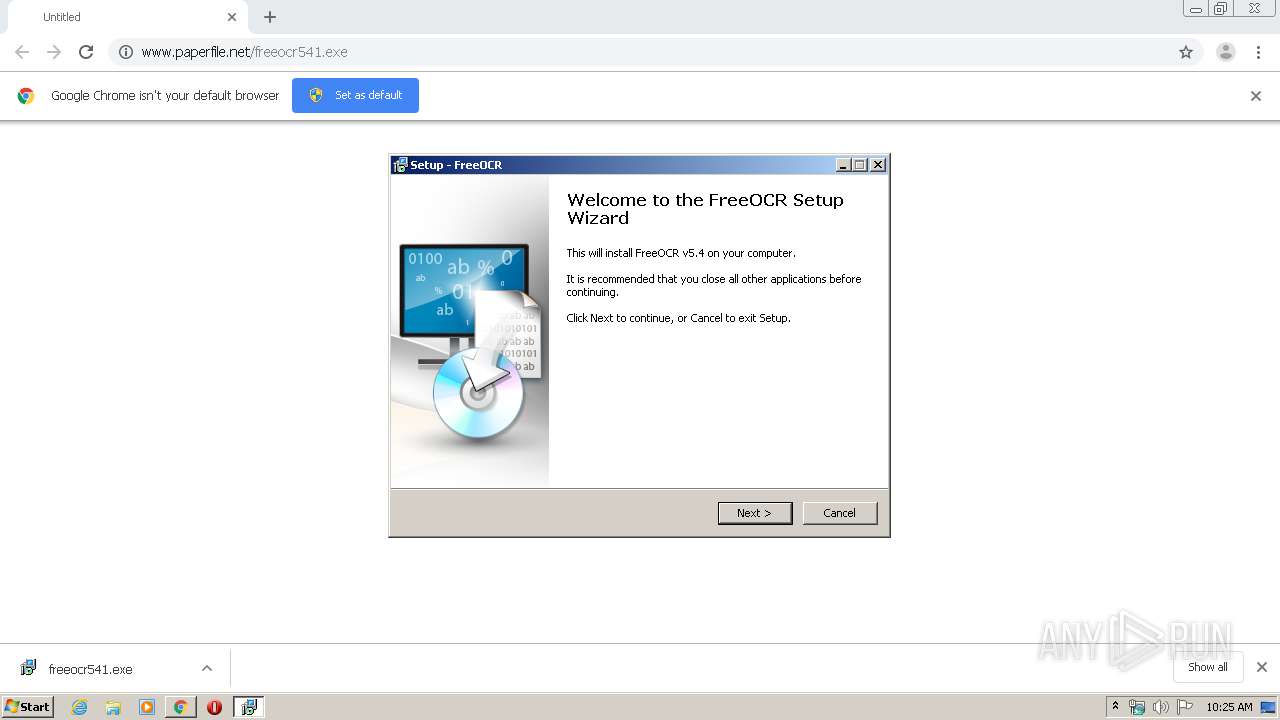
| URL: | http://www.paperfile.net/freeocr541.exe |
| Full analysis: | https://app.any.run/tasks/05b7adc8-6182-498c-9daf-bf62a9af1f33 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2020, 10:25:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 88BBB135B7F0E24EE48C396BFE22CACC |
| SHA1: | 27F9A57B3CC60D750F6BF616CBF669D8A7182344 |
| SHA256: | C4275200A5CFB5A627DFCBC0CE96D57EA78655DFD40C86DFA2971CA7F17C5E8E |
| SSDEEP: | 3:N1KJS4LO5eXEG:Cc4S5e0G |
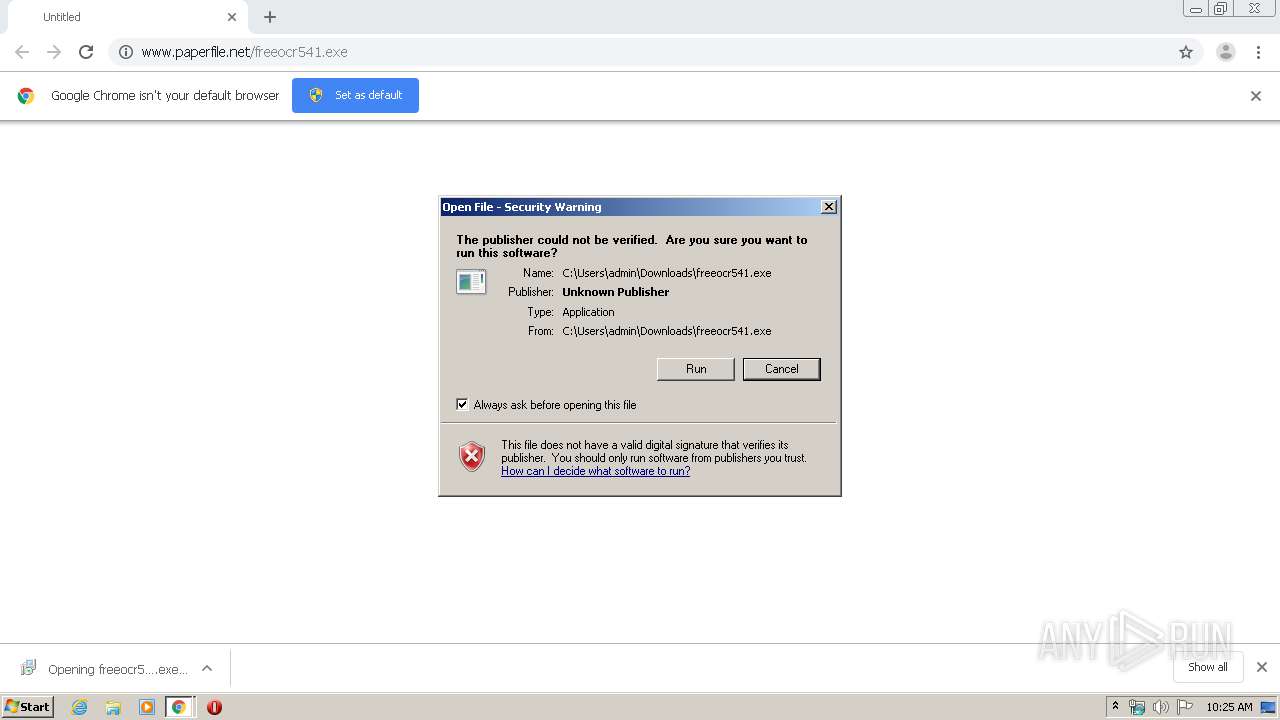
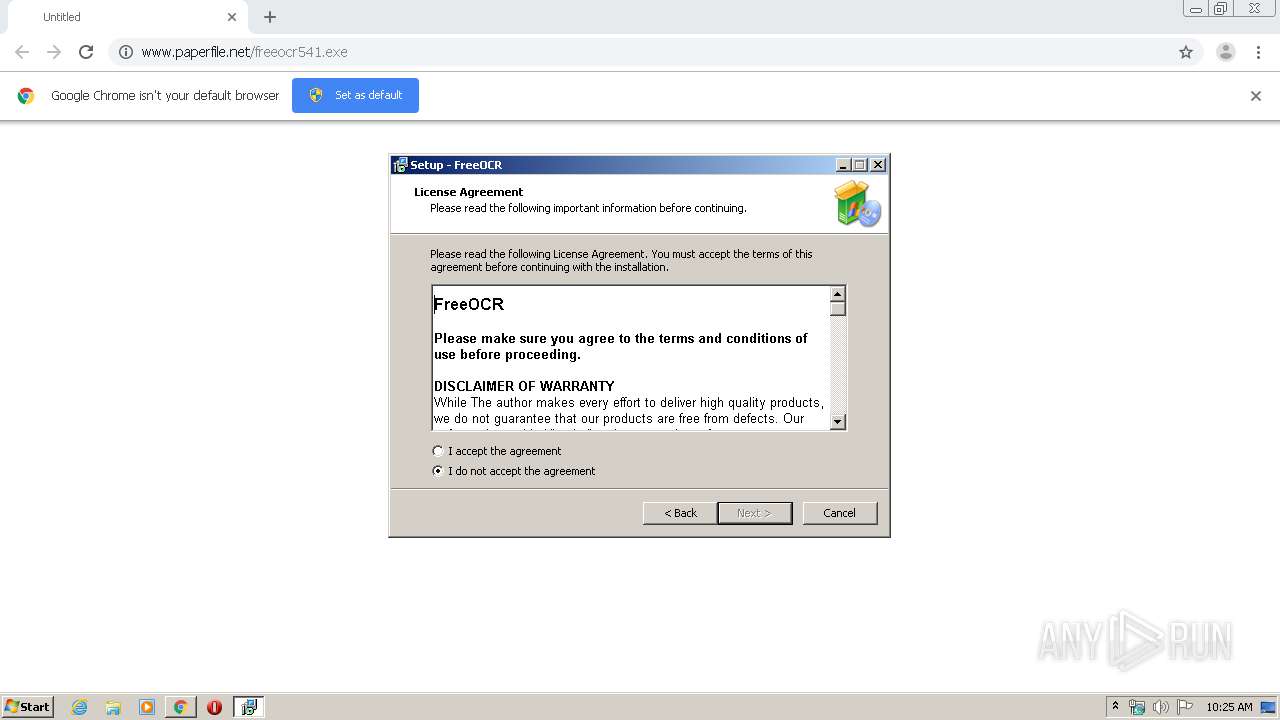
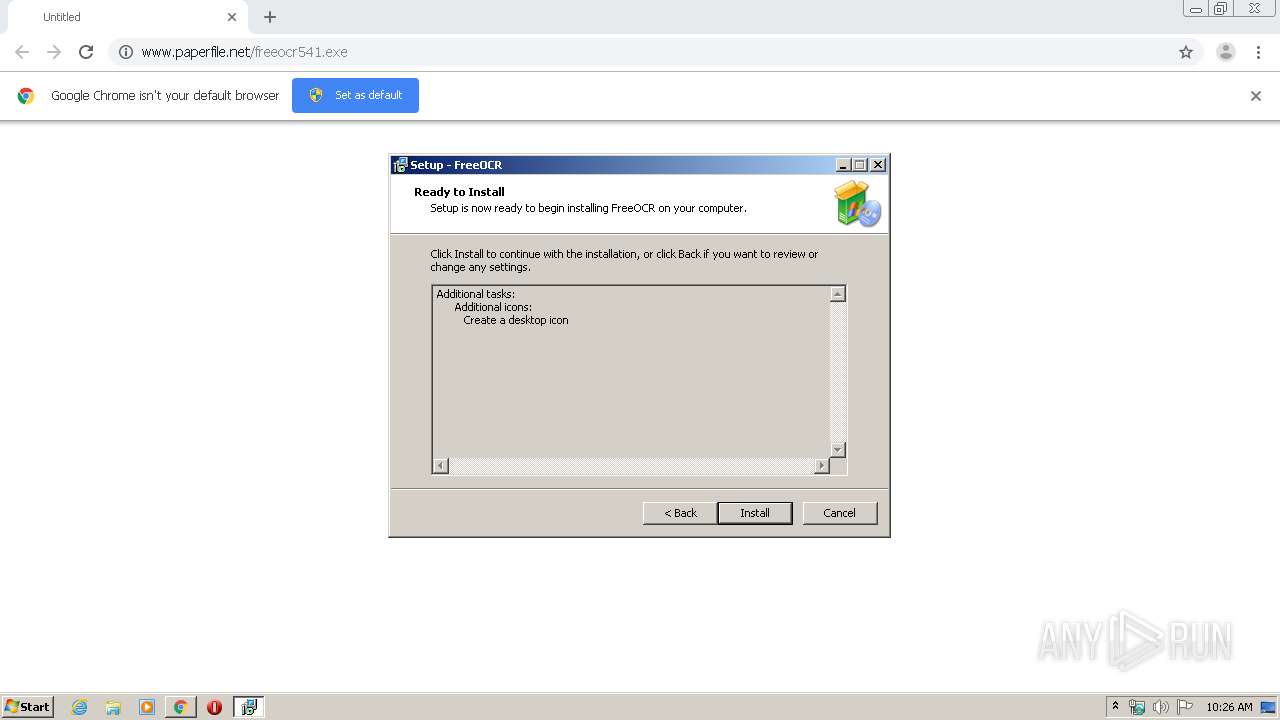
MALICIOUS
Application was dropped or rewritten from another process
- FreeOCR.exe (PID: 308)
- freeocr541.exe (PID: 3000)
- freeocr541.exe (PID: 4016)
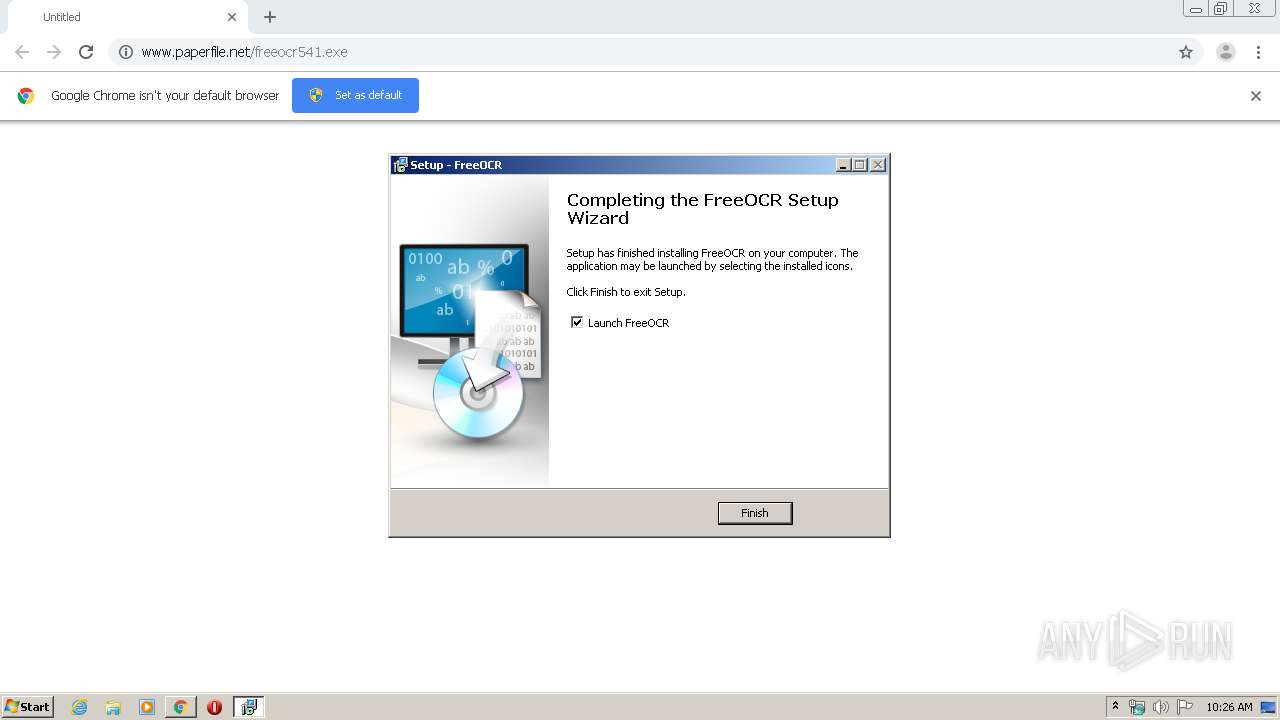
Loads dropped or rewritten executable
- FreeOCR.exe (PID: 308)
Registers / Runs the DLL via REGSVR32.EXE
- freeocr541.tmp (PID: 1876)
SUSPICIOUS
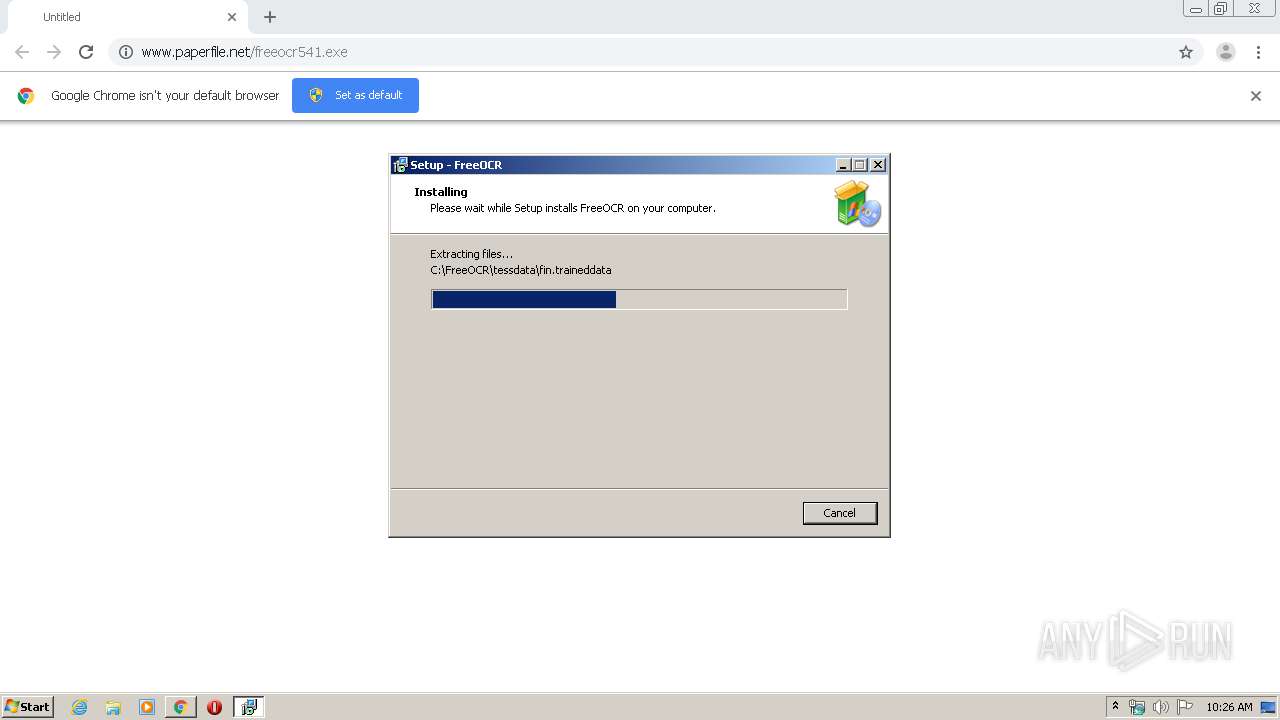
Executable content was dropped or overwritten
- freeocr541.exe (PID: 3000)
- freeocr541.exe (PID: 4016)
- freeocr541.tmp (PID: 1876)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 944)
Creates files in the Windows directory
- freeocr541.tmp (PID: 1876)
INFO
Application launched itself
- chrome.exe (PID: 3540)
Reads Internet Cache Settings
- chrome.exe (PID: 3540)
Dropped object may contain Bitcoin addresses
- freeocr541.tmp (PID: 1876)
Application was dropped or rewritten from another process
- freeocr541.tmp (PID: 768)
- freeocr541.tmp (PID: 1876)
Reads the hosts file
- chrome.exe (PID: 3540)
- chrome.exe (PID: 944)
Loads dropped or rewritten executable
- freeocr541.tmp (PID: 1876)
Creates a software uninstall entry
- freeocr541.tmp (PID: 1876)
Creates files in the program directory
- freeocr541.tmp (PID: 1876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
17
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\FreeOCR\FreeOCR.exe" | C:\FreeOCR\FreeOCR.exe | freeocr541.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: FreeOCR Exit code: 0 Version: 1.1.0.8 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,14146493481855519011,14793605077411293254,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17759651423797324027 --mojo-platform-channel-handle=1020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,14146493481855519011,14793605077411293254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4446292366595300624 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 768 | "C:\Users\admin\AppData\Local\Temp\is-3HFPT.tmp\freeocr541.tmp" /SL5="$6012C,11027424,54272,C:\Users\admin\Downloads\freeocr541.exe" | C:\Users\admin\AppData\Local\Temp\is-3HFPT.tmp\freeocr541.tmp | — | freeocr541.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,14146493481855519011,14793605077411293254,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4953704856527796504 --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1284 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\ImageEnXLibrary.ocx" | C:\Windows\system32\regsvr32.exe | — | freeocr541.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\is-GM95F.tmp\freeocr541.tmp" /SL5="$40182,11027424,54272,C:\Users\admin\Downloads\freeocr541.exe" /SPAWNWND=$30184 /NOTIFYWND=$6012C | C:\Users\admin\AppData\Local\Temp\is-GM95F.tmp\freeocr541.tmp | freeocr541.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,14146493481855519011,14793605077411293254,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7596467188752431966 --mojo-platform-channel-handle=3688 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x7305a9d0,0x7305a9e0,0x7305a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,14146493481855519011,14793605077411293254,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14636097521179168316 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 555
Read events
1 413
Write events
133
Delete events
9
Modification events
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3696) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3540-13224162314951125 |
Value: 259 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3540) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
19
Suspicious files
34
Text files
80
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E28230B-DD4.pma | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d5612c19-63d5-4edd-982a-6056353e7d78.tmp | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF2c0ab8.TMP | text | |
MD5:FC9FFE77348619CC285333DFF5E1D5D1 | SHA256:7CB9B3575330B3D776A21EB7A7407E34F013A0975B7418DA11B5C85DEC91D1F3 | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:A9C81BA506E2A0D898698EAF075EBE5C | SHA256:92FB2125FB5A0B877B76C4E3409B250EFF394804C7F24E236FBE162E1054AF90 | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:6F174C3088498A2CD266BCA5EE2F6624 | SHA256:2EEEC1240EB66978ED12E9034F8D4284B0CA1DC82495954636D68140E2187FA4 | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:702AEC53DCDCFEA33C4BE3D2F888473E | SHA256:D16286D6EE0EB33E7907EE4FCB8FDB6B5A54E5A56BFAF99A9C2451D239BC9765 | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF2c0bd1.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
15
DNS requests
10
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
308 | FreeOCR.exe | GET | 200 | 52.216.92.186:80 | http://www.paperfile.net/version.html | US | text | 4 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
944 | chrome.exe | 172.217.23.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 52.216.134.50:80 | www.paperfile.net | Amazon.com, Inc. | US | suspicious |
308 | FreeOCR.exe | 52.216.92.186:80 | www.paperfile.net | Amazon.com, Inc. | US | unknown |
944 | chrome.exe | 172.217.16.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 172.217.23.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
944 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.paperfile.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
944 | chrome.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
944 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |