| File name: | WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe |
| Full analysis: | https://app.any.run/tasks/1920c4f2-c157-48c7-b4fe-3fa402bb4a26 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2023, 01:28:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BE1C770D590EBE8A22AE7B80C36969B3 |
| SHA1: | 607C0AAF8C6D3E7939FFC749AE8B1871A7BD6FFF |
| SHA256: | C421723BD434A8D7BA093888034B1597B745022082BB748441C2F0BC20CC96F8 |
| SSDEEP: | 98304:uPBndopmS4uqHSrGtk+S4XxWS0ipZOm+e3Bn/RlyaRycLsekS2kb5hxbo8fTnh0E:cgZ4uqy5+VXLumjxSaRycsNkbfNo+b |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
Reads the Internet Settings
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
Reads Internet Explorer settings
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
Executable content was dropped or overwritten
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
INFO
Checks supported languages
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
Reads the computer name
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
Checks proxy server information
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
The process checks LSA protection
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
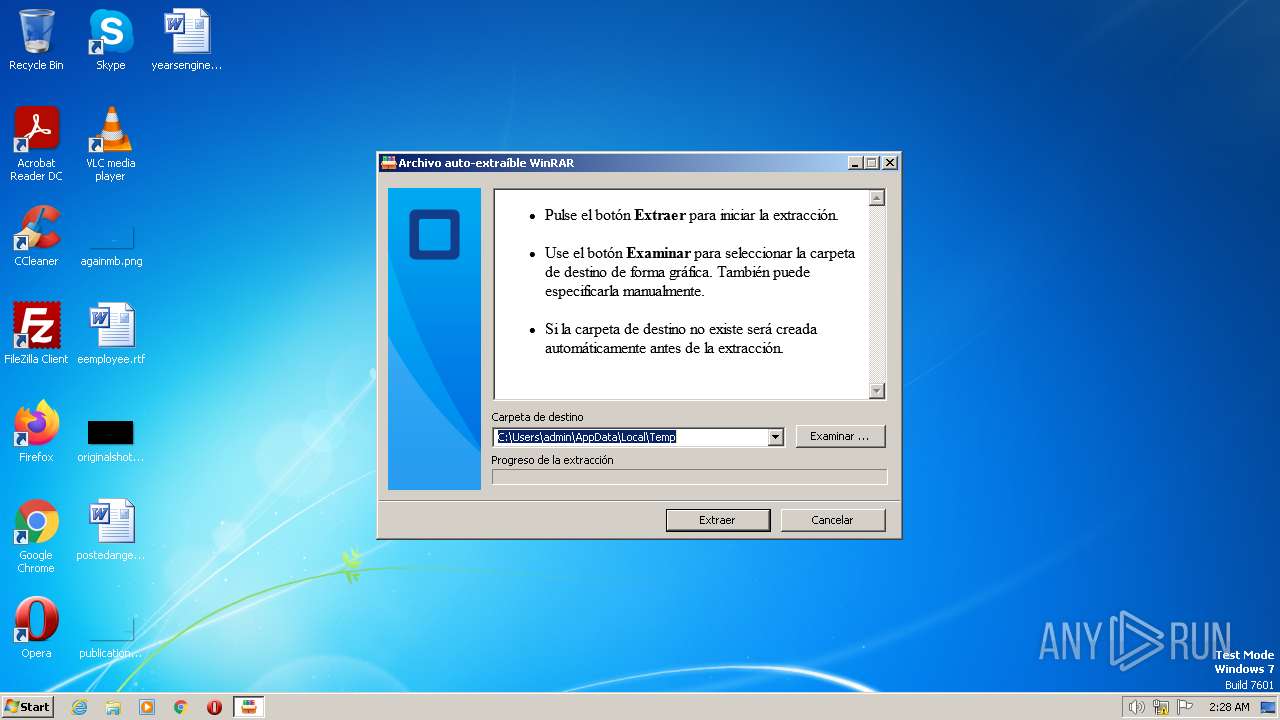
Create files in a temporary directory
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
Reads the machine GUID from the registry
- WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x205e0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 262144 |
| CodeSize: | 208384 |
| LinkerVersion: | 14.33 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:02:16 12:31:25+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Feb-2023 12:31:25 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 16-Feb-2023 12:31:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00032C1C | 0x00032E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69711 |
.rdata | 0x00034000 | 0x0000B130 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25783 |
.data | 0x00040000 | 0x00024750 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.08398 |
.didat | 0x00065000 | 0x00000190 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.37276 |
.rsrc | 0x00066000 | 0x0000DFF8 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63872 |
.reloc | 0x00074000 | 0x000023AC | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.64408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.11236 | 440 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
36
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2580 | "C:\Users\admin\AppData\Local\Temp\WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe" | C:\Users\admin\AppData\Local\Temp\WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
445
Read events
435
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2580) WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2580) WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2580) WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2580) WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2580) WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2580) WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | C:\Users\admin\AppData\Local\Temp\WinRAR.v6.22.Final.ES.x64.REGGED.exe | executable | |
MD5:E4A4CD5AC10F65171E5A0A933E00A69E | SHA256:23EB0516564E5E59866EAC1BAE33CC5C6EA7A67C625266E443A3852CC06C6A61 | |||
| 2580 | WinRAR.v6.22.Final.ES.x32.x64.REGGED.exe | C:\Users\admin\AppData\Local\Temp\WinRAR.v6.22.Final.ES.x32.REGGED.exe | executable | |
MD5:7D72650B66AB219B35B41D2E80FB2398 | SHA256:F39771358044C061B5C3E1E2A578506B717FAAA89DE638366E1F1748856410A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2424 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |