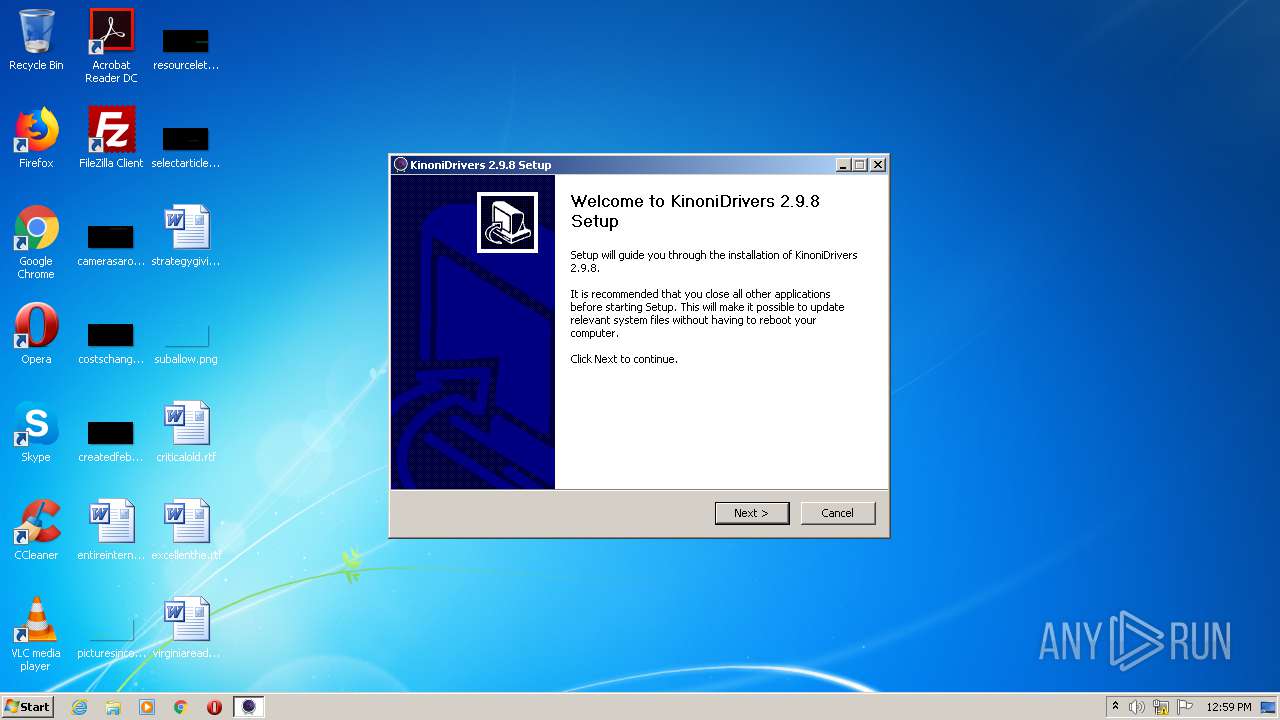
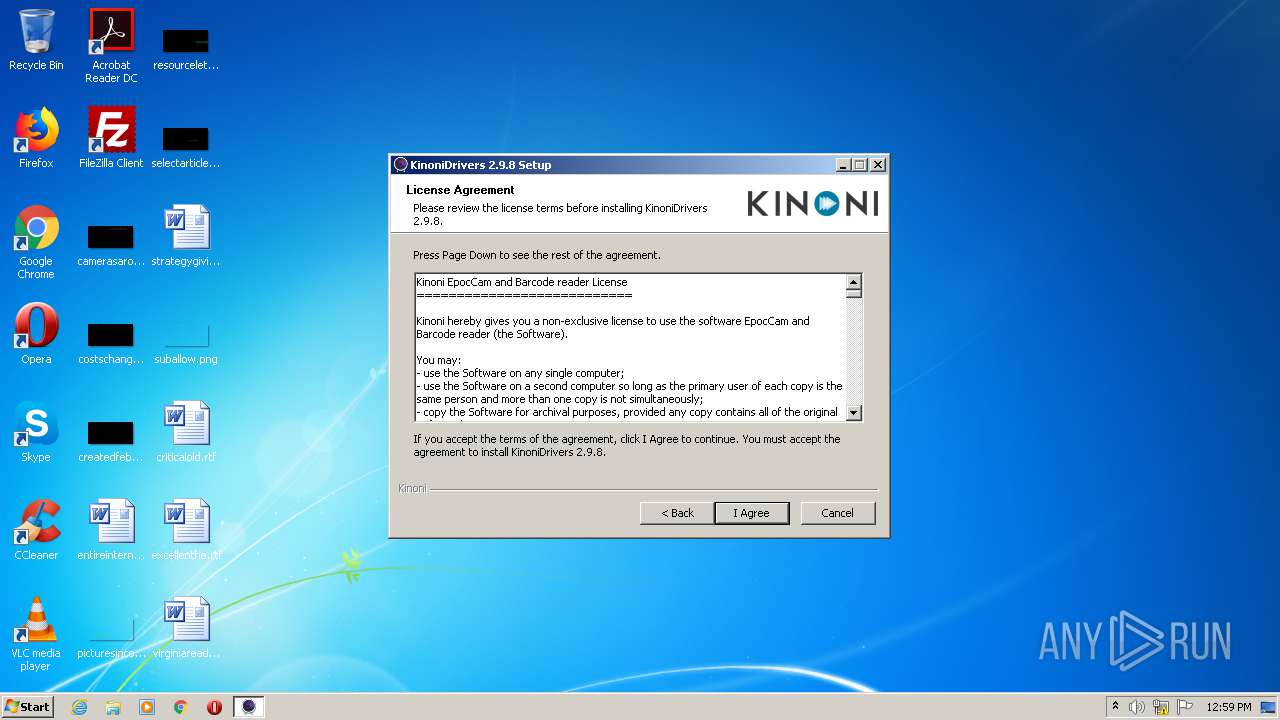
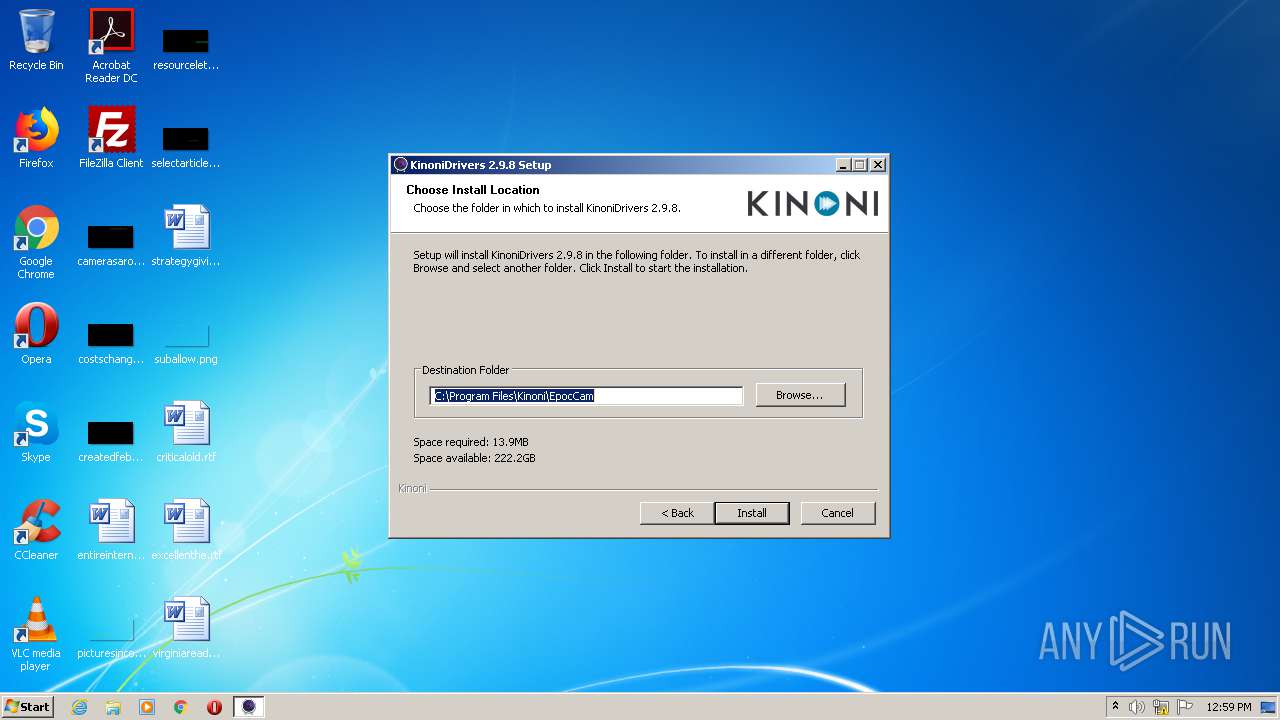
| File name: | EpocCamInstaller298.exe |
| Full analysis: | https://app.any.run/tasks/8639857b-de1d-40f5-99e4-da891fbdd0c7 |
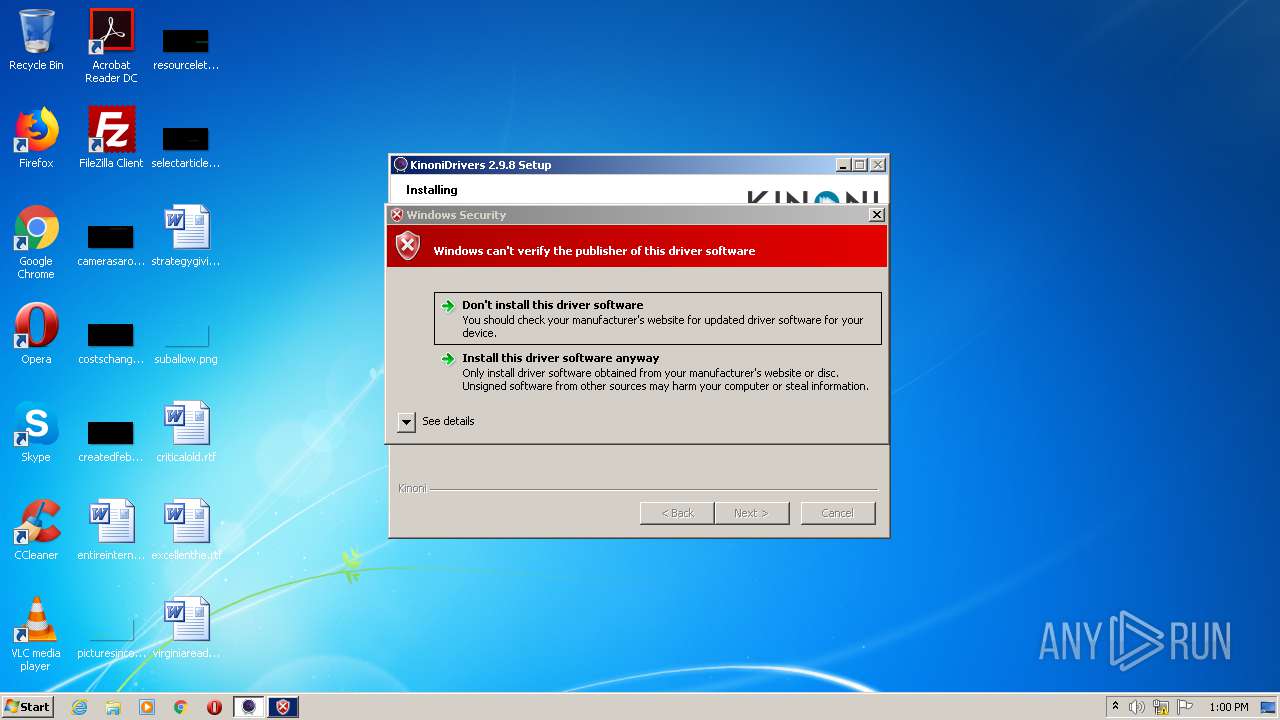
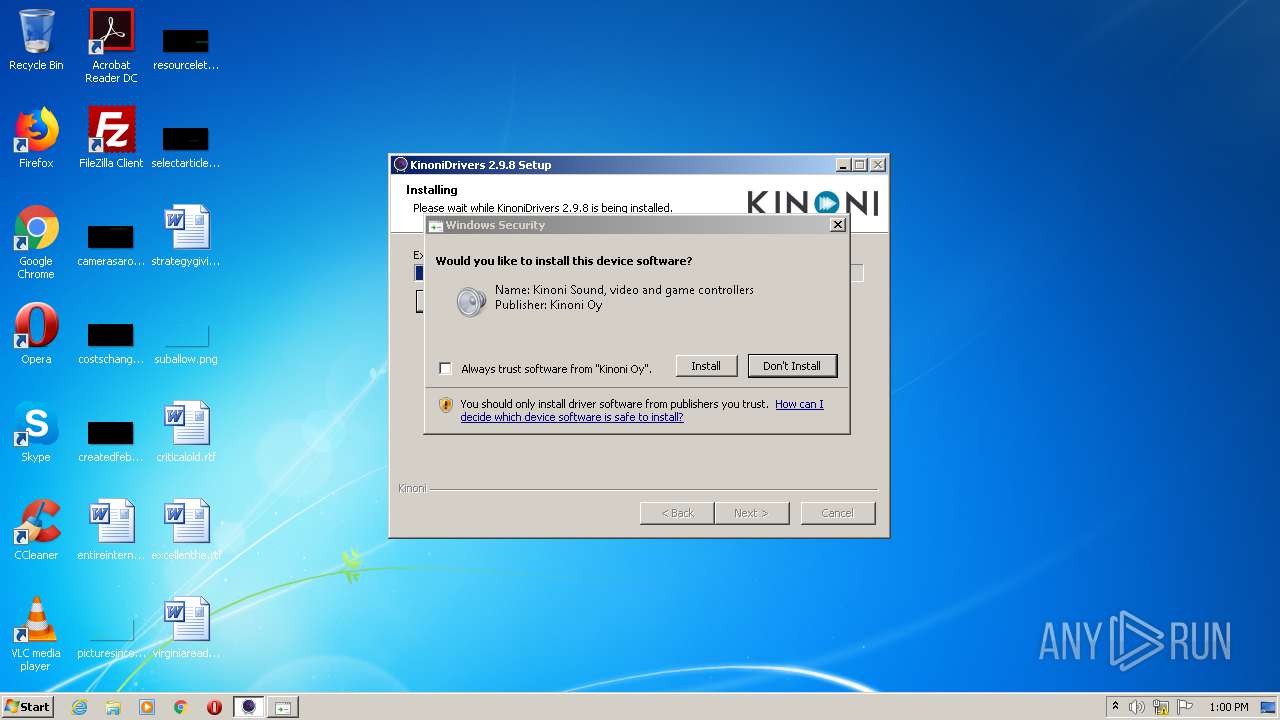
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2020, 11:58:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B28C80E2B10DD930628019370082F275 |
| SHA1: | 770041F9BC48F19B23437211725981C9CF81E004 |
| SHA256: | C417ED684B355C685504D170A5CACB916D529D339D64288FC311E2A90C59AEAA |
| SSDEEP: | 49152:ks9z7VWAAR7k0NYgGmnVGkTktypbVC61fdmtlGhv7EOMQEirAomFFeFv4GUO:ks905IUV061fdilqDTMEEJFYFv4a |
MALICIOUS
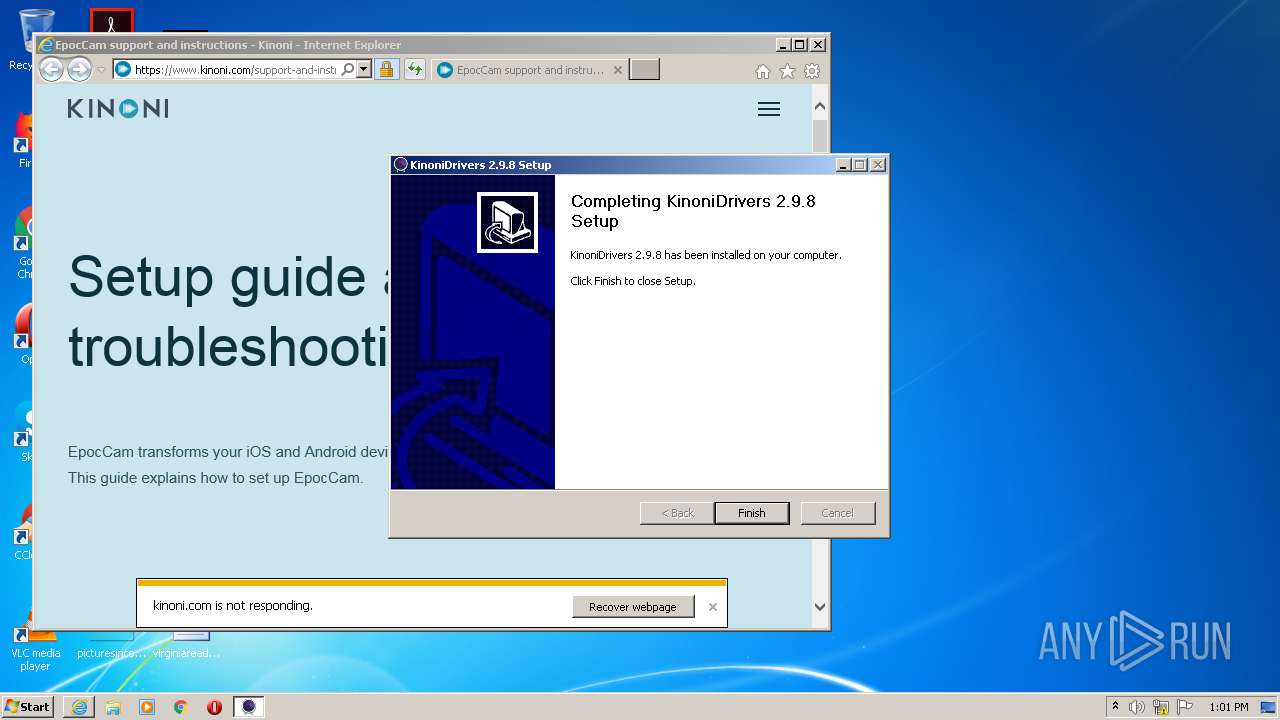
Loads dropped or rewritten executable
- EpocCamInstaller298.exe (PID: 2580)
- MsiExec.exe (PID: 2984)
- KinoniSvc.exe (PID: 2980)
- iexplore.exe (PID: 2348)
- svchost.exe (PID: 844)
- iexplore.exe (PID: 3072)
Application was dropped or rewritten from another process
- ns7987.tmp (PID: 2864)
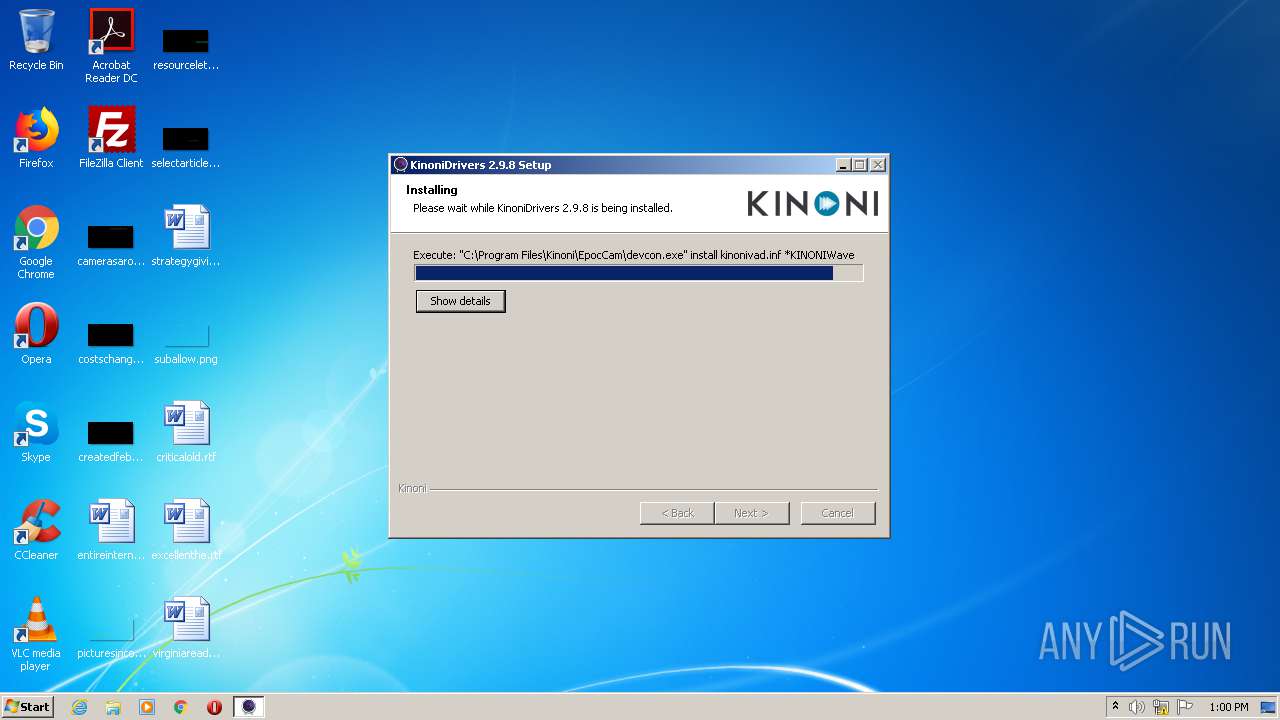
- devcon.exe (PID: 3016)
- ns7A72.tmp (PID: 2536)
- mDNSResponder.exe (PID: 2872)
- devcon.exe (PID: 1232)
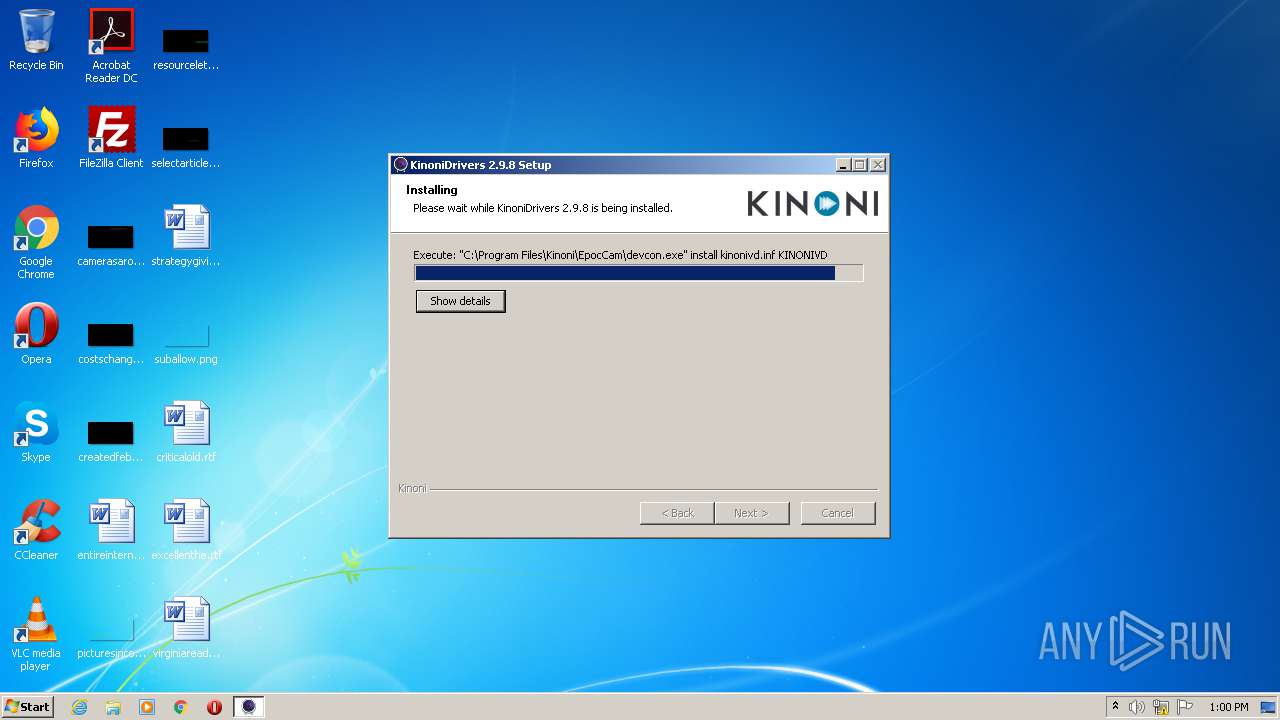
- devcon.exe (PID: 2052)
- devcon.exe (PID: 1944)
- nsD763.tmp (PID: 2452)
- KinoniSvc.exe (PID: 2612)
- nsD929.tmp (PID: 2792)
- KinoniSvc.exe (PID: 2980)
Changes settings of System certificates
- msiexec.exe (PID: 1980)
- devcon.exe (PID: 1944)
SUSPICIOUS
Creates files in the program directory
- EpocCamInstaller298.exe (PID: 2580)
Starts SC.EXE for service management
- cmd.exe (PID: 1840)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 2588)
Starts application with an unusual extension
- EpocCamInstaller298.exe (PID: 2580)
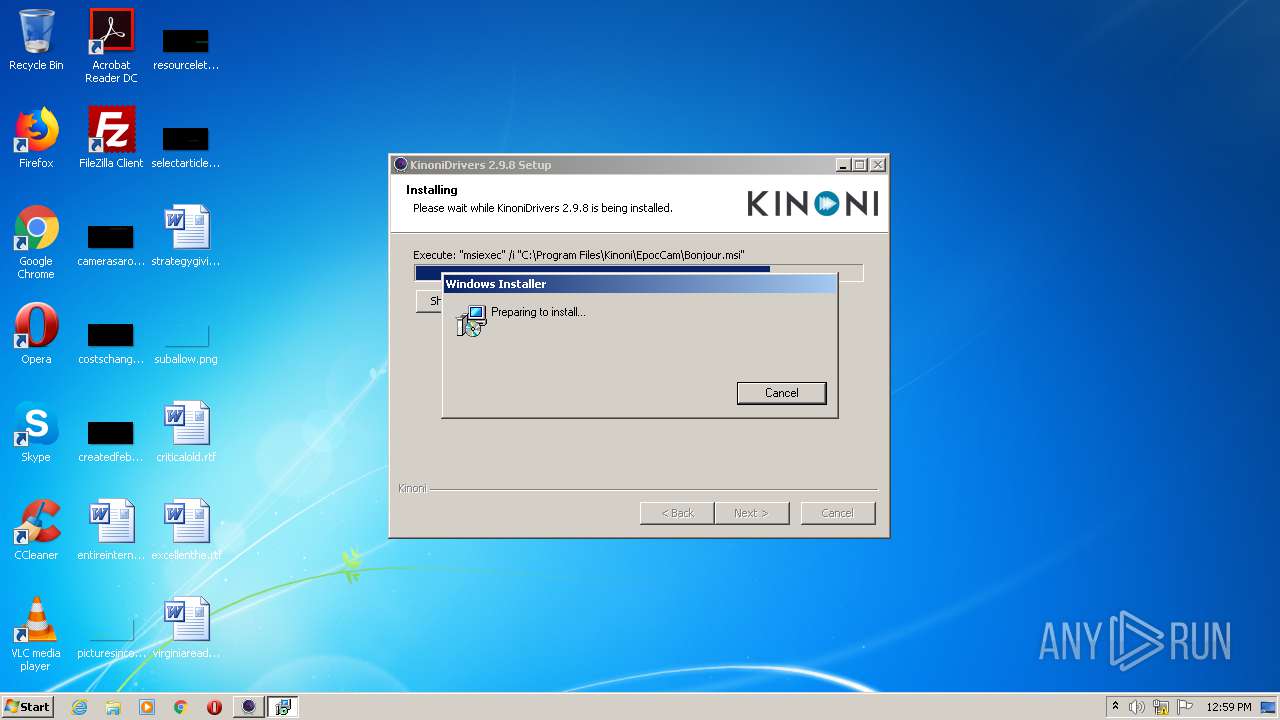
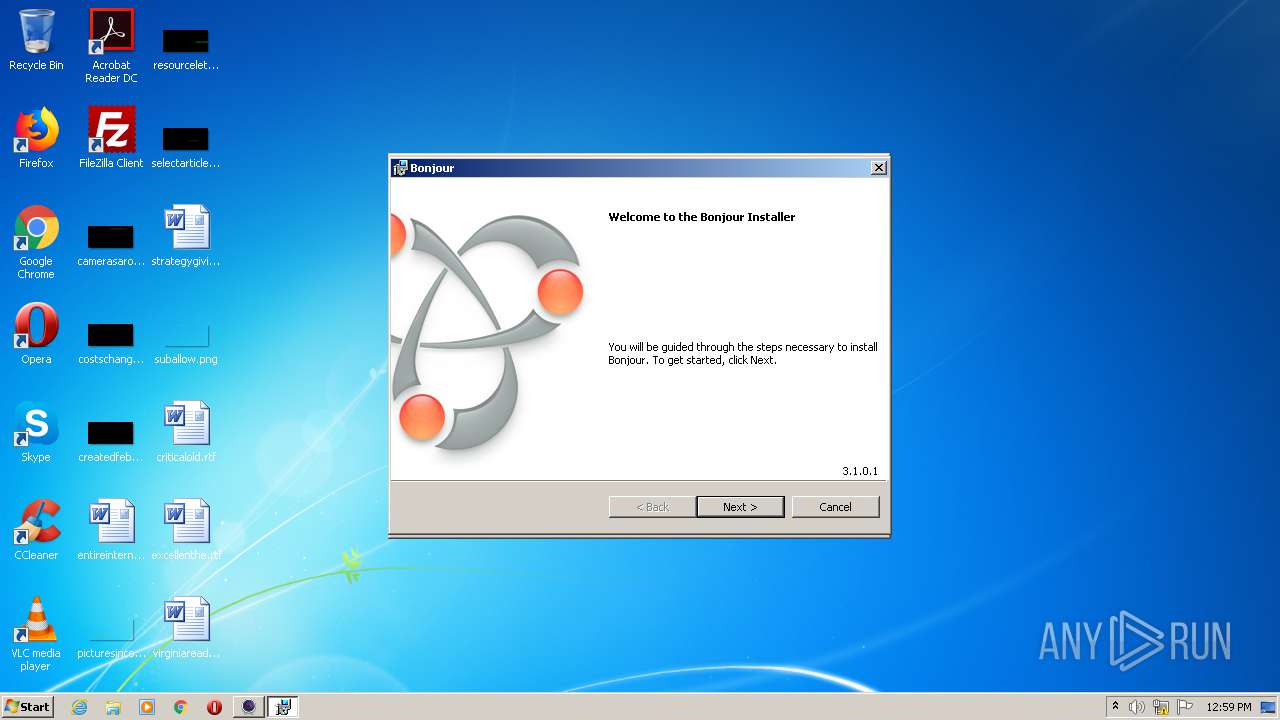
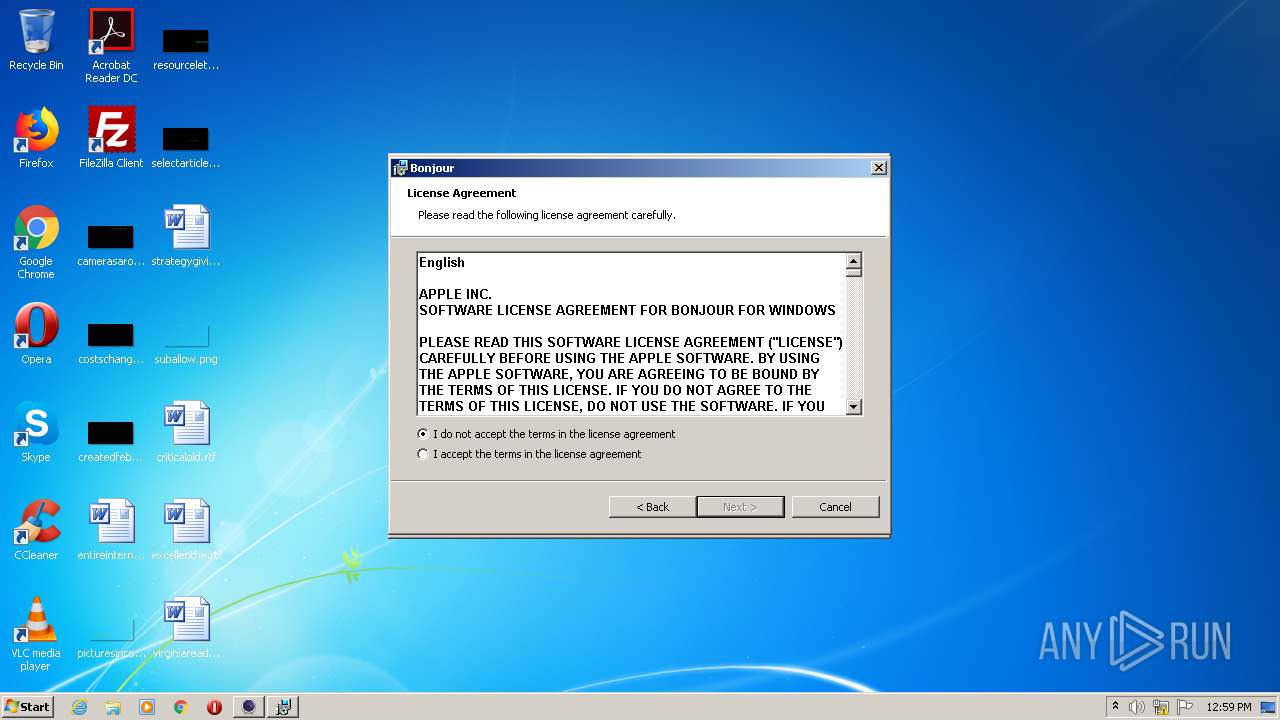
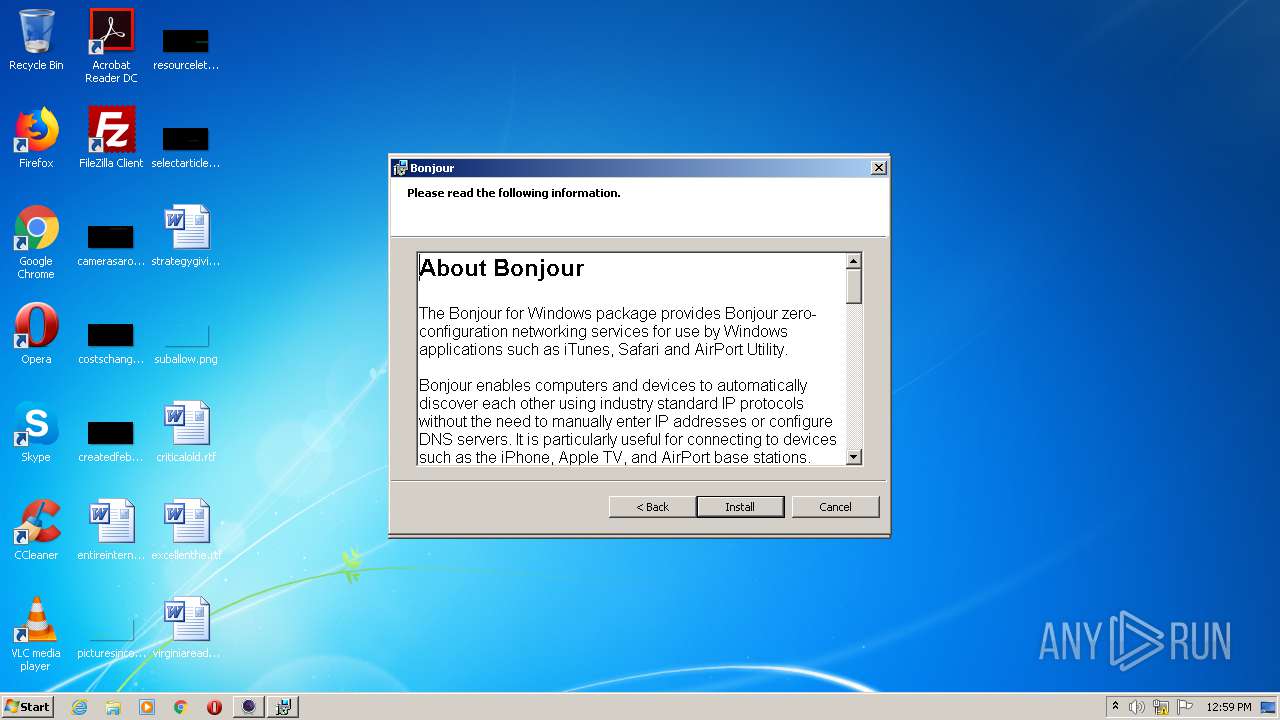
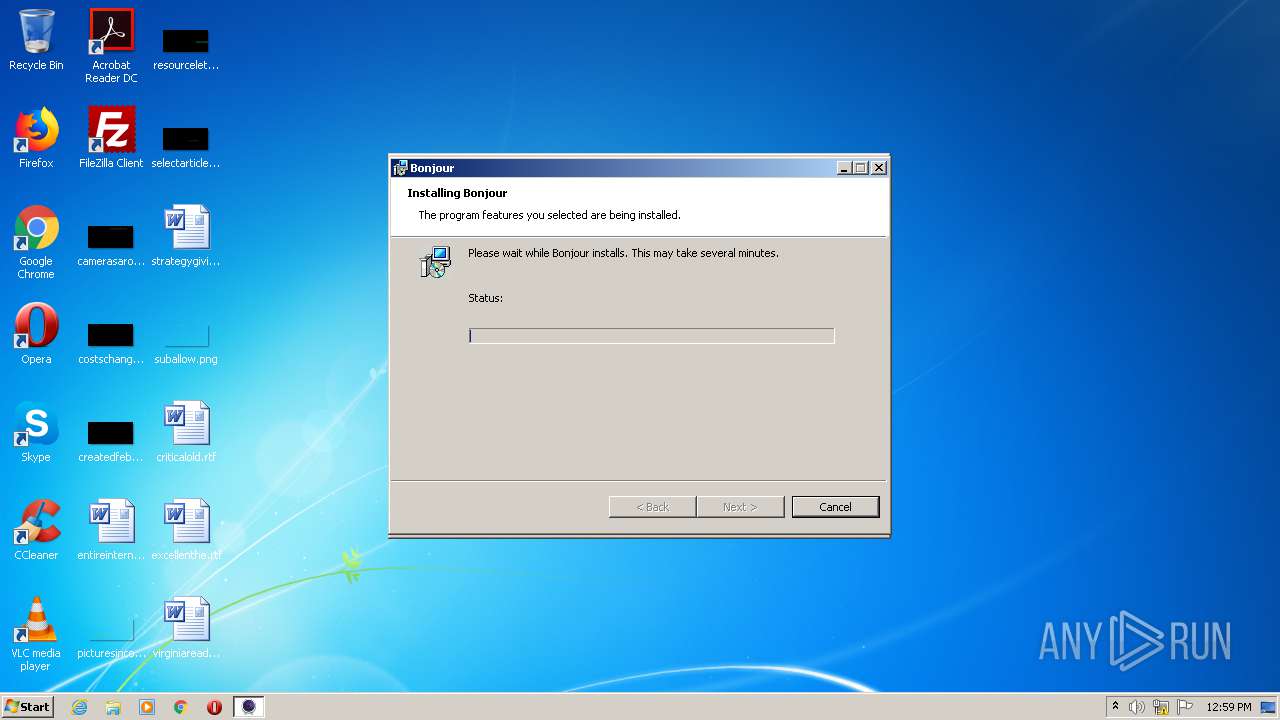
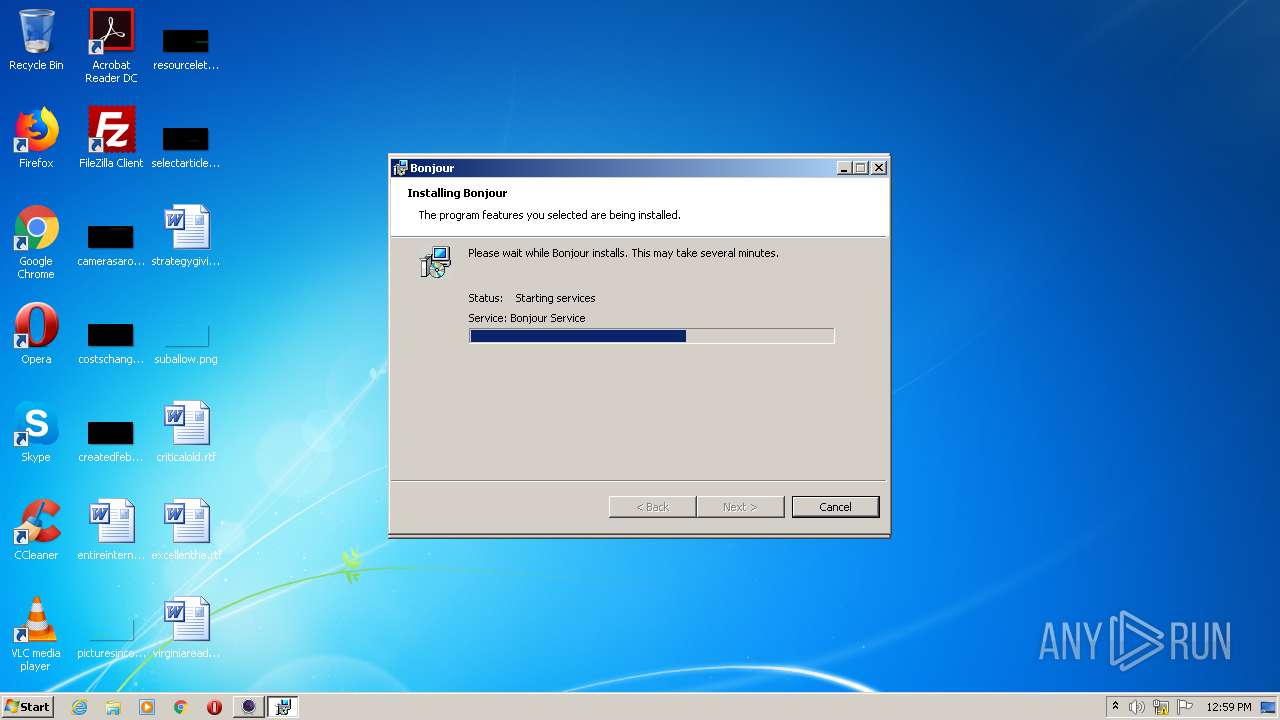
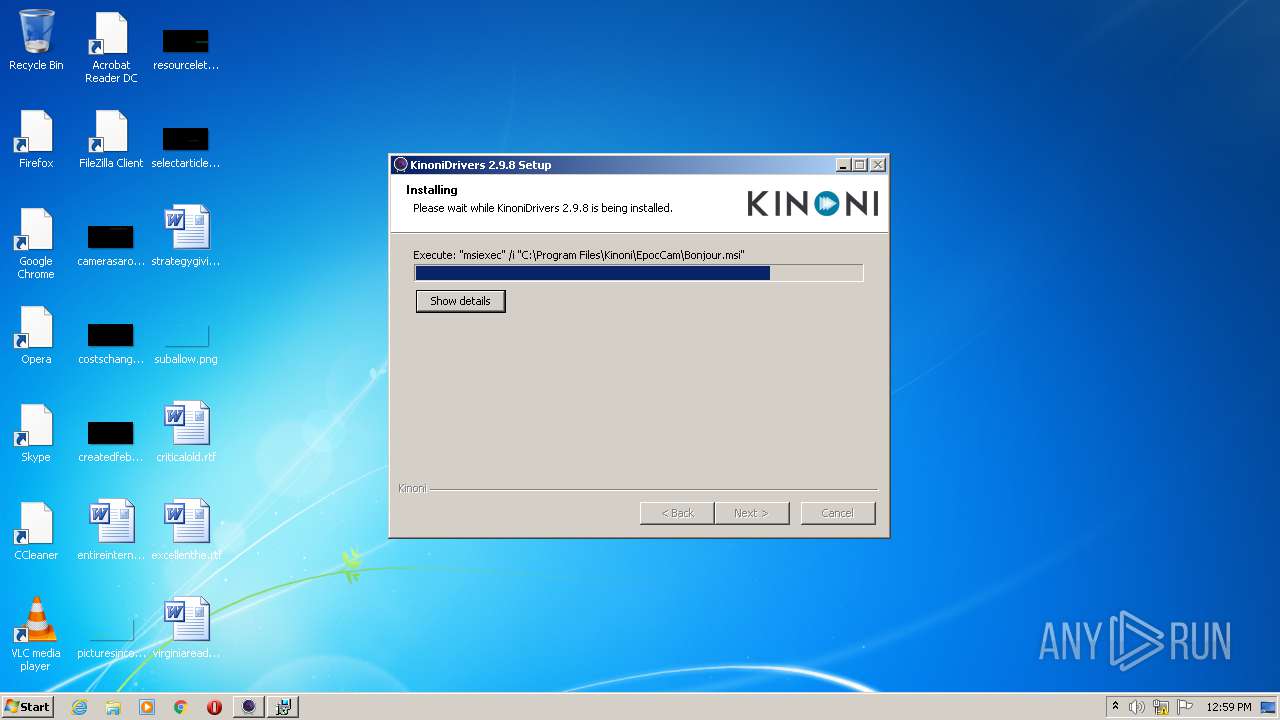
Starts Microsoft Installer
- EpocCamInstaller298.exe (PID: 2580)
Starts CMD.EXE for commands execution
- ns7A72.tmp (PID: 2536)
- ns7987.tmp (PID: 2864)
- nsD763.tmp (PID: 2452)
- nsD929.tmp (PID: 2792)
Executable content was dropped or overwritten
- EpocCamInstaller298.exe (PID: 2580)
- DrvInst.exe (PID: 3420)
- devcon.exe (PID: 1232)
- DrvInst.exe (PID: 3964)
- devcon.exe (PID: 1944)
- DrvInst.exe (PID: 3732)
- DrvInst.exe (PID: 3580)
Executed as Windows Service
- mDNSResponder.exe (PID: 2872)
- KinoniSvc.exe (PID: 2980)
Adds / modifies Windows certificates
- msiexec.exe (PID: 1980)
- devcon.exe (PID: 1944)
Executed via COM
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3964)
- DrvInst.exe (PID: 3732)
- DrvInst.exe (PID: 3580)
- DllHost.exe (PID: 1464)
Removes files from Windows directory
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3964)
- DrvInst.exe (PID: 3732)
- DrvInst.exe (PID: 3580)
Creates files in the Windows directory
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3964)
- DrvInst.exe (PID: 3732)
- DrvInst.exe (PID: 3580)
- svchost.exe (PID: 844)
Creates files in the driver directory
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3964)
- DrvInst.exe (PID: 3732)
- DrvInst.exe (PID: 3580)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3732)
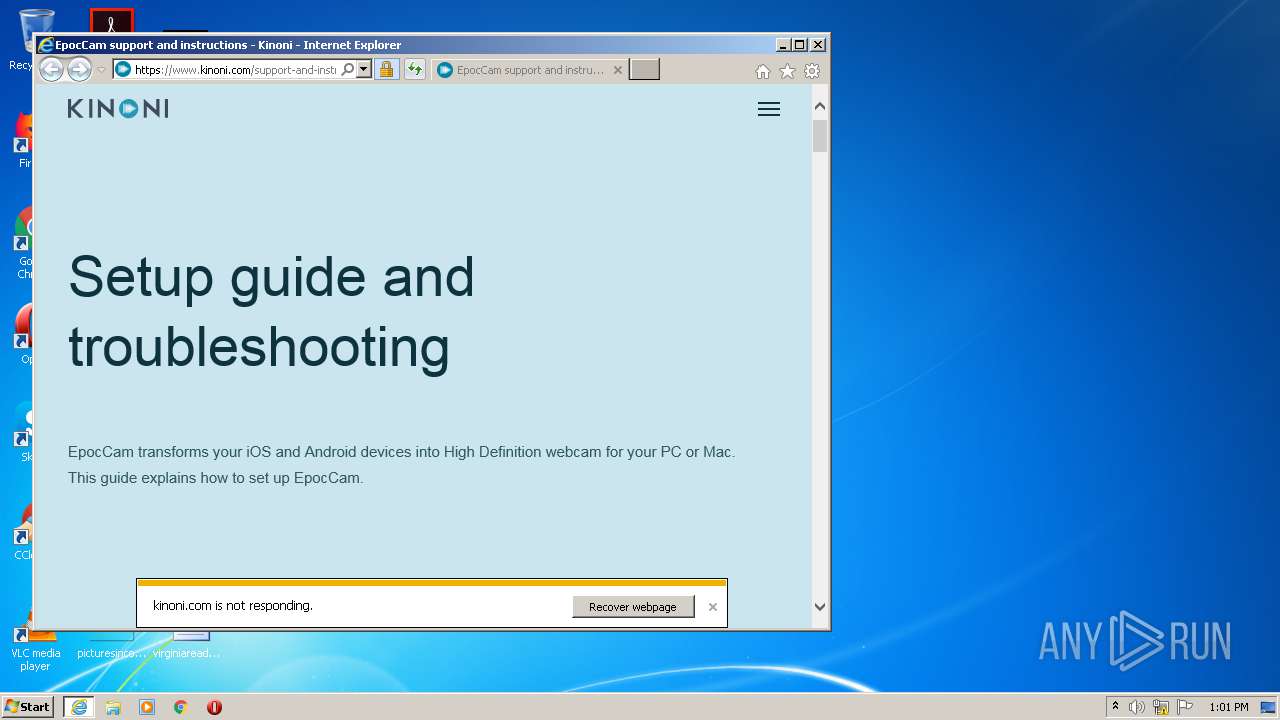
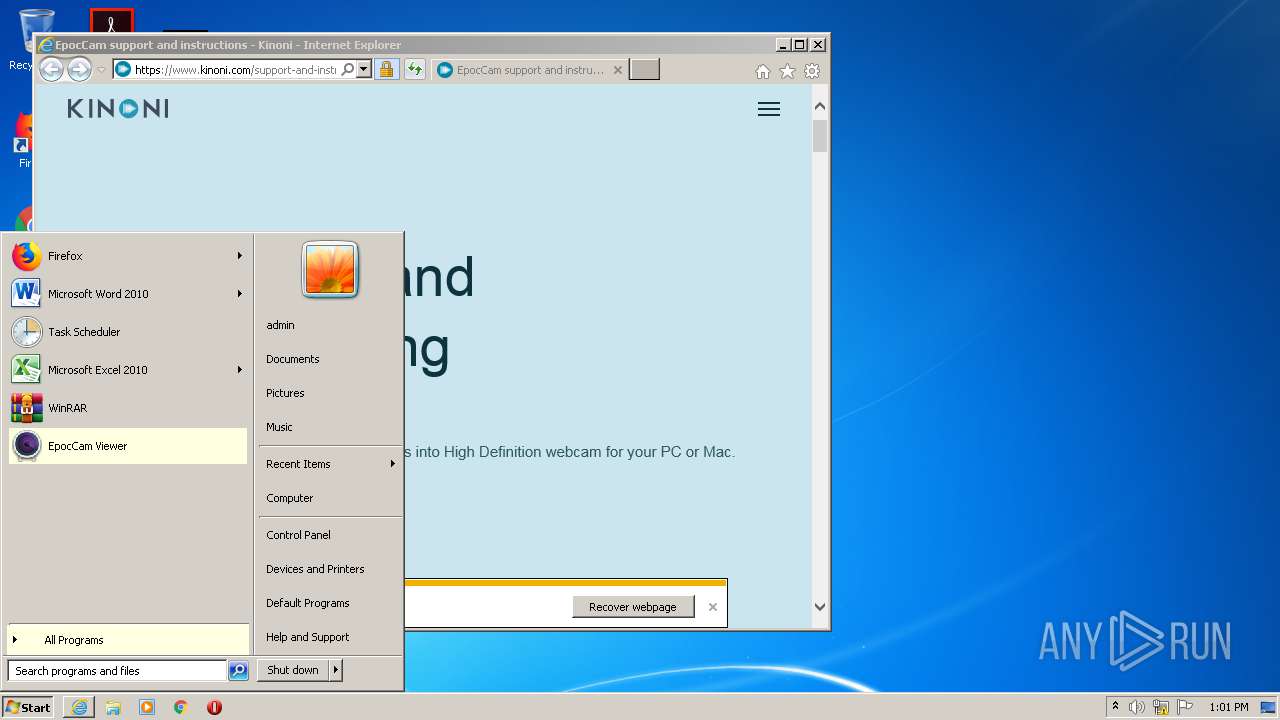
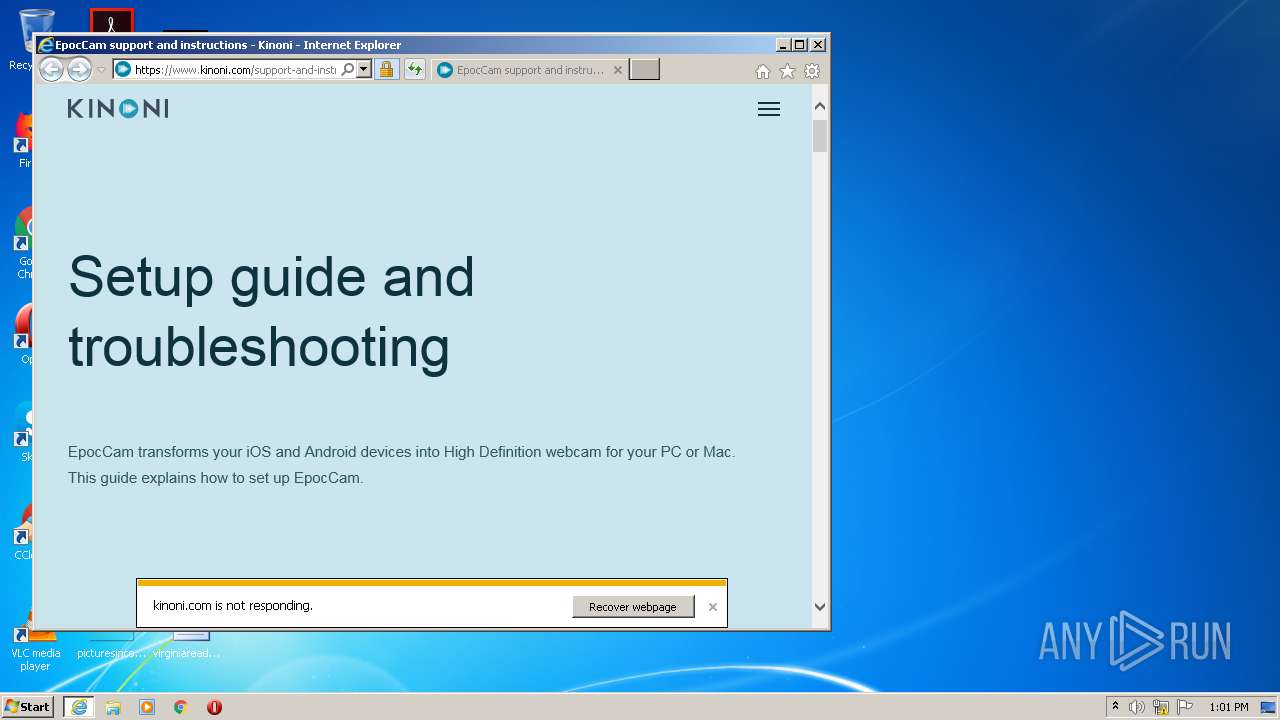
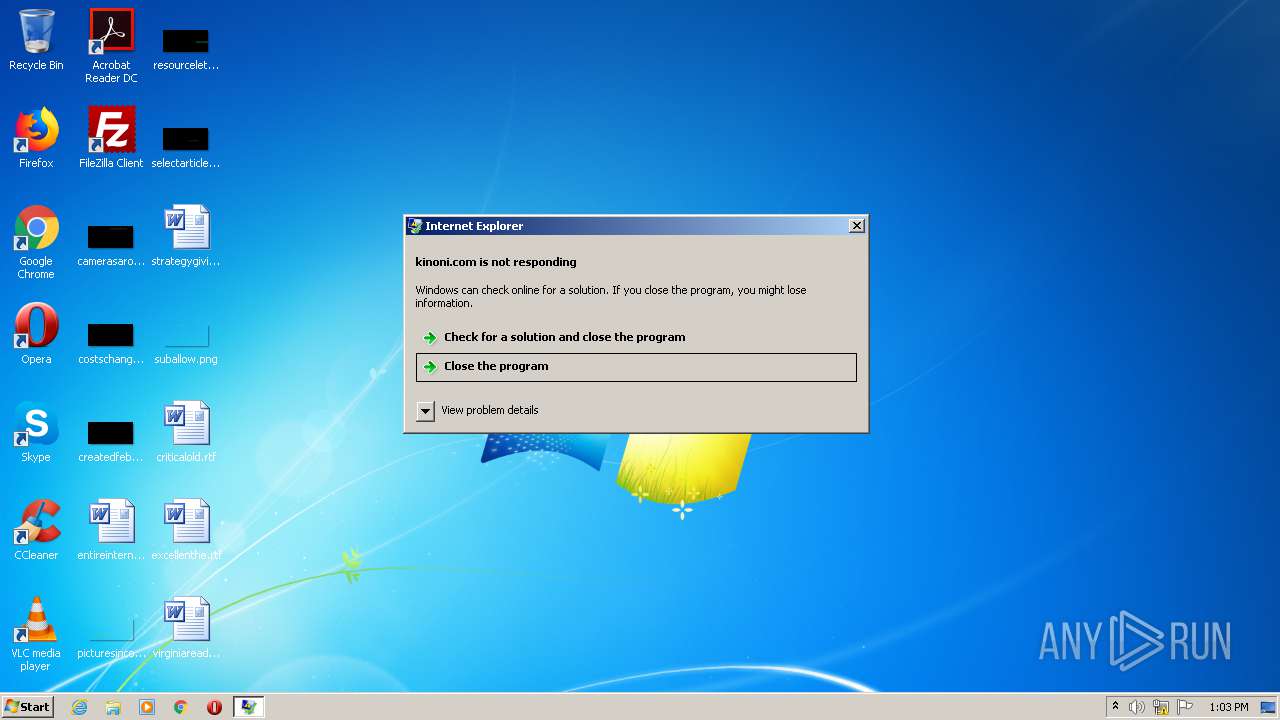
Starts Internet Explorer
- EpocCamInstaller298.exe (PID: 2580)
Creates a software uninstall entry
- EpocCamInstaller298.exe (PID: 2580)
Reads Internet Cache Settings
- DllHost.exe (PID: 1464)
INFO
Reads settings of System Certificates
- devcon.exe (PID: 1232)
- DrvInst.exe (PID: 3964)
- iexplore.exe (PID: 2348)
Searches for installed software
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3732)
Reads Internet Cache Settings
- iexplore.exe (PID: 2348)
- iexplore.exe (PID: 3072)
Changes internet zones settings
- iexplore.exe (PID: 2348)
Application launched itself
- iexplore.exe (PID: 2348)
Creates files in the user directory
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2348)
Changes settings of System certificates
- iexplore.exe (PID: 3072)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3072)
Reads internet explorer settings
- iexplore.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:50:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x32bf |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.9.8.0 |
| ProductVersionNumber: | 2.9.8.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | Kinoni Driver Installer |
| CompanyName: | Kinoni |
| FileDescription: | Kinoni Driver Installer |
| FileVersion: | 2.9.8 |
| LegalCopyright: | Copyright Kinoni |
| ProductName: | Kinoni Driver Installer |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:50:45 |
| Detected languages: |
|
| Comments: | Kinoni Driver Installer |
| CompanyName: | Kinoni |
| FileDescription: | Kinoni Driver Installer |
| FileVersion: | 2.9.8 |
| LegalCopyright: | Copyright Kinoni |
| ProductName: | Kinoni Driver Installer |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:50:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005E59 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42419 |
.rdata | 0x00007000 | 0x00001246 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0004 |
.data | 0x00009000 | 0x0001A818 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21193 |
.ndata | 0x00024000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x00004D00 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.47447 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28813 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 1.7815 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
202 | 2.63447 | 160 | UNKNOWN | English - United States | RT_DIALOG |
203 | 2.47654 | 268 | UNKNOWN | English - United States | RT_DIALOG |
205 | 2.62576 | 492 | UNKNOWN | English - United States | RT_DIALOG |
206 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
80
Monitored processes
32
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 10 Global\{0a85c2f8-de59-44f7-e6d3-2516e43d9710} Global\{50e38127-26f9-0504-524a-984255f6847e} C:\Windows\System32\DriverStore\Temp\{3e07d269-4bbc-2b46-4da6-725601c96c60}\kinonivad.inf C:\Windows\System32\DriverStore\Temp\{3e07d269-4bbc-2b46-4da6-725601c96c60}\kinonivad.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 844 | C:\Windows\system32\svchost.exe -k LocalService | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\AppData\Local\Temp\EpocCamInstaller298.exe" | C:\Users\admin\AppData\Local\Temp\EpocCamInstaller298.exe | — | explorer.exe | |||||||||||
User: admin Company: Kinoni Integrity Level: MEDIUM Description: Kinoni Driver Installer Exit code: 3221226540 Version: 2.9.8 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Kinoni\EpocCam\devcon.exe" install kinonivad.inf *KINONIWave | C:\Program Files\Kinoni\EpocCam\devcon.exe | EpocCamInstaller298.exe | ||||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
| 1464 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1840 | C:\Windows\system32\cmd.exe /C sc.exe stop KinoniSvc | C:\Windows\system32\cmd.exe | — | ns7987.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1840 | C:\Windows\system32\cmd.exe /C "C:\Program Files\Kinoni\EpocCam\KinoniSvc.exe" install | C:\Windows\system32\cmd.exe | — | nsD763.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Kinoni\EpocCam\devcon.exe" install kinonivd.inf KINONIVD | C:\Program Files\Kinoni\EpocCam\devcon.exe | EpocCamInstaller298.exe | ||||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
| 1980 | "msiexec" /i "C:\Program Files\Kinoni\EpocCam\Bonjour.msi" | C:\Windows\system32\msiexec.exe | — | EpocCamInstaller298.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Kinoni\EpocCam\devcon.exe" remove KINONIVD | C:\Program Files\Kinoni\EpocCam\devcon.exe | — | EpocCamInstaller298.exe | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
Total events
2 298
Read events
1 652
Write events
638
Delete events
8
Modification events
| (PID) Process: | (1980) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1980) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\4EB6D578499B1CCF5F581EAD56BE3D9B6744A5E5 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000CB17E431673EE209FE455793F30AFA1C0F0000000100000014000000E91E1E972B8F467AB4E0598FA92285387DEE94C90300000001000000140000004EB6D578499B1CCF5F581EAD56BE3D9B6744A5E57E00000001000000080000000040D0D1B0FFD4017F000000010000000C000000300A06082B060105050703011D0000000100000010000000C6CBCAFA17955C4CFD41ECA0C654C3610B000000010000001200000056006500720069005300690067006E0000001400000001000000140000007FD365A7C2DDECBBF03009F34339FA02AF3331336200000001000000200000009ACFAB7E43C8D880D06B262A94DEEEE4B4659989C3D0CAF19BAF6405E41AB7DF09000000010000002A000000302806082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030353000000010000004600000030443021060B6086480186F8450107170630123010060A2B0601040182373C0101030200C0301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0190000000100000010000000D8B5FB368468620275D142FFD2AADE372000000001000000D7040000308204D3308203BBA003020102021018DAD19E267DE8BB4A2158CDCC6B3B4A300D06092A864886F70D01010505003081CA310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E311F301D060355040B1316566572695369676E205472757374204E6574776F726B313A3038060355040B1331286329203230303620566572695369676E2C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79314530430603550403133C566572695369676E20436C6173732033205075626C6963205072696D6172792043657274696669636174696F6E20417574686F72697479202D204735301E170D3036313130383030303030305A170D3336303731363233353935395A3081CA310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E311F301D060355040B1316566572695369676E205472757374204E6574776F726B313A3038060355040B1331286329203230303620566572695369676E2C20496E632E202D20466F7220617574686F72697A656420757365206F6E6C79314530430603550403133C566572695369676E20436C6173732033205075626C6963205072696D6172792043657274696669636174696F6E20417574686F72697479202D20473530820122300D06092A864886F70D01010105000382010F003082010A0282010100AF240808297A359E600CAAE74B3B4EDC7CBC3C451CBB2BE0FE2902F95708A364851527F5F1ADC831895D22E82AAAA642B38FF8B955B7B1B74BB3FE8F7E0757ECEF43DB66621561CF600DA4D8DEF8E0C362083D5413EB49CA59548526E52B8F1B9FEBF5A191C23349D843636A524BD28FE870514DD189697BC770F6B3DC1274DB7B5D4B56D396BF1577A1B0F4A225F2AF1C926718E5F40604EF90B9E400E4DD3AB519FF02BAF43CEEE08BEB378BECF4D7ACF2F6F03DAFDD759133191D1C40CB7424192193D914FEAC2A52C78FD50449E48D6347883C6983CBFE47BD2B7E4FC595AE0E9DD4D143C06773E314087EE53F9F73B8330ACF5D3F3487968AEE53E825150203010001A381B23081AF300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106306D06082B0601050507010C0461305FA15DA05B3059305730551609696D6167652F6769663021301F300706052B0E03021A04148FE5D31A86AC8D8E6BC3CF806AD448182C7B192E30251623687474703A2F2F6C6F676F2E766572697369676E2E636F6D2F76736C6F676F2E676966301D0603551D0E041604147FD365A7C2DDECBBF03009F34339FA02AF333133300D06092A864886F70D0101050500038201010093244A305F62CFD81A982F3DEADC992DBD77F6A5792238ECC4A7A07812AD620E457064C5E797662D98097E5FAFD6CC2865F201AA081A47DEF9F97C925A0869200DD93E6D6E3C0D6ED8E606914018B9F8C1EDDFDB41AAE09620C9CD64153881C994EEA284290B136F8EDB0CDD2502DBA48B1944D2417A05694A584F60CA7E826A0B02AA251739B5DB7FE784652A958ABD86DE5E8116832D10CCDEFDA8822A6D281F0D0BC4E5E71A2619E1F4116F10B595FCE7420532DBCE9D515E28B69E85D35BEFA57D4540728EB70E6B0E06FB33354871B89D278BC4655F0D86769C447AF6955CF65D320833A454B6183F685CF2424A853854835FD1E82CF2AC11D6A8ED636A | |||
| (PID) Process: | (1980) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\BE36A4562FB2EE05DBB3D32323ADF445084ED656 |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000007F667A71D3EB6978209A51149D83DA200F0000000100000010000000E8A598BE84828EFEAE701115013576B2030000000100000014000000BE36A4562FB2EE05DBB3D32323ADF445084ED65609000000010000000C000000300A06082B060105050703080B000000010000000E00000074006800610077007400650000001D00000001000000100000006454A4AA36F9B5CC8338E5A67FABFF17140000000100000014000000DDBCBD869C3F07ED40E31B08EFCEC4D188CD3B156200000001000000200000006B6C1E01F590F5AFC5FCF85CD0B9396884048659FC2C6D1170D68B045216C3FD190000000100000010000000181C2BE05851F96993E196F279954B232000000001000000A5020000308202A13082020AA003020102020100300D06092A864886F70D010104050030818B310B3009060355040613025A41311530130603550408130C5765737465726E2043617065311430120603550407130B44757262616E76696C6C65310F300D060355040A1306546861777465311D301B060355040B13145468617774652043657274696669636174696F6E311F301D060355040313165468617774652054696D657374616D70696E67204341301E170D3937303130313030303030305A170D3230313233313233353935395A30818B310B3009060355040613025A41311530130603550408130C5765737465726E2043617065311430120603550407130B44757262616E76696C6C65310F300D060355040A1306546861777465311D301B060355040B13145468617774652043657274696669636174696F6E311F301D060355040313165468617774652054696D657374616D70696E6720434130819F300D06092A864886F70D010101050003818D0030818902818100D62B587861458653EA347B519CEDB0E62E180EFEE05FA827D3B4C9E07C594E160E735460C17FF69F2EE93A8524153CDB470463C39EC4941A5ADF4C7AF3D9431D3C107A7925DB90FEF051E730D64100FD9F28DF79BE94BB9DB614E32385D7A941E04CA479B02B1A8BF2F83B8A3E45AC719200B4904198FB5FEDFAB72E8AF888370203010001A3133011300F0603551D130101FF040530030101FF300D06092A864886F70D01010405000381810067DBE2C2E6873D40838637357D1FCE9AC30C6620A8BAAA048986C2F510080DBFCBA2058AD04D363EF4D7EF69C65EE4B0946F4AB9E7DE5B88B67BDBE327E576C3F035C1CBB5279B3379DC90A6009E77FAFCCD279442169CD31C68ECBF5CDDE5A97B100A32745413318B85038491B75801301438AF28CAFCB150191909AC8949D3 | |||
| (PID) Process: | (2984) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries\000000000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2984) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries\000000000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2984) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries\000000000003 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2984) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries\000000000004 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2984) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries\000000000005 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2984) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries\000000000006 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2984) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinSock2\Parameters\NameSpace_Catalog5\Catalog_Entries\000000000001 |
| Operation: | write | Name: | LibraryPath |
Value: %SystemRoot%\system32\NLAapi.dll | |||
Executable files
31
Suspicious files
48
Text files
332
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | EpocCamInstaller298.exe | C:\Users\admin\AppData\Local\Temp\nsk60CE.tmp\ns7987.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | EpocCamInstaller298.exe | C:\Users\admin\AppData\Local\Temp\nsk60CE.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2580 | EpocCamInstaller298.exe | C:\Program Files\Kinoni\EpocCam\COPYING.LESSER | text | |
MD5:— | SHA256:— | |||
| 1980 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI7CFE.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | EpocCamInstaller298.exe | C:\Program Files\Kinoni\EpocCam\EpocCamTest.exe | executable | |
MD5:— | SHA256:— | |||
| 2580 | EpocCamInstaller298.exe | C:\Users\admin\AppData\Local\Temp\nsk60CE.tmp\ns7A72.tmp | executable | |
MD5:— | SHA256:— | |||
| 2580 | EpocCamInstaller298.exe | C:\Program Files\Kinoni\EpocCam\avcodec-58.dll | executable | |
MD5:— | SHA256:— | |||
| 2580 | EpocCamInstaller298.exe | C:\Program Files\Kinoni\EpocCam\swscale-5.dll | executable | |
MD5:— | SHA256:— | |||
| 2580 | EpocCamInstaller298.exe | C:\Users\admin\AppData\Local\Temp\nsk60CE.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 2580 | EpocCamInstaller298.exe | C:\Program Files\Kinoni\EpocCam\KinoniSvc.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
26
DNS requests
14
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3072 | iexplore.exe | GET | 301 | 31.217.192.169:80 | http://www.kinoni.com/thankyou.html | FI | — | — | unknown |
2184 | werfault.exe | GET | — | 51.143.111.81:80 | http://watson.microsoft.com/StageOne/Generic/AppHangB1/iexplore_exe/11_0_9600_17840/555fe1bb/af81/131072.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
3072 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3072 | iexplore.exe | GET | 200 | 2.16.177.195:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
3072 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3072 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDt878iBbv1RCAAAAABTHN4%3D | US | der | 471 b | whitelisted |
3072 | iexplore.exe | GET | 200 | 216.58.205.227:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEDt878iBbv1RCAAAAABTHN4%3D | US | der | 471 b | whitelisted |
2348 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3072 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3072 | iexplore.exe | 31.217.192.169:80 | www.kinoni.com | Equinix (Finland) Oy | FI | unknown |
3072 | iexplore.exe | 31.217.192.169:443 | www.kinoni.com | Equinix (Finland) Oy | FI | unknown |
3072 | iexplore.exe | 216.58.205.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3072 | iexplore.exe | 172.217.18.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3072 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2184 | werfault.exe | 51.143.111.81:80 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
3072 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2348 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2348 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3072 | iexplore.exe | 172.217.22.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kinoni.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
kinonicom.r.worldssl.net |
| unknown |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2184 | werfault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
2184 | werfault.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |