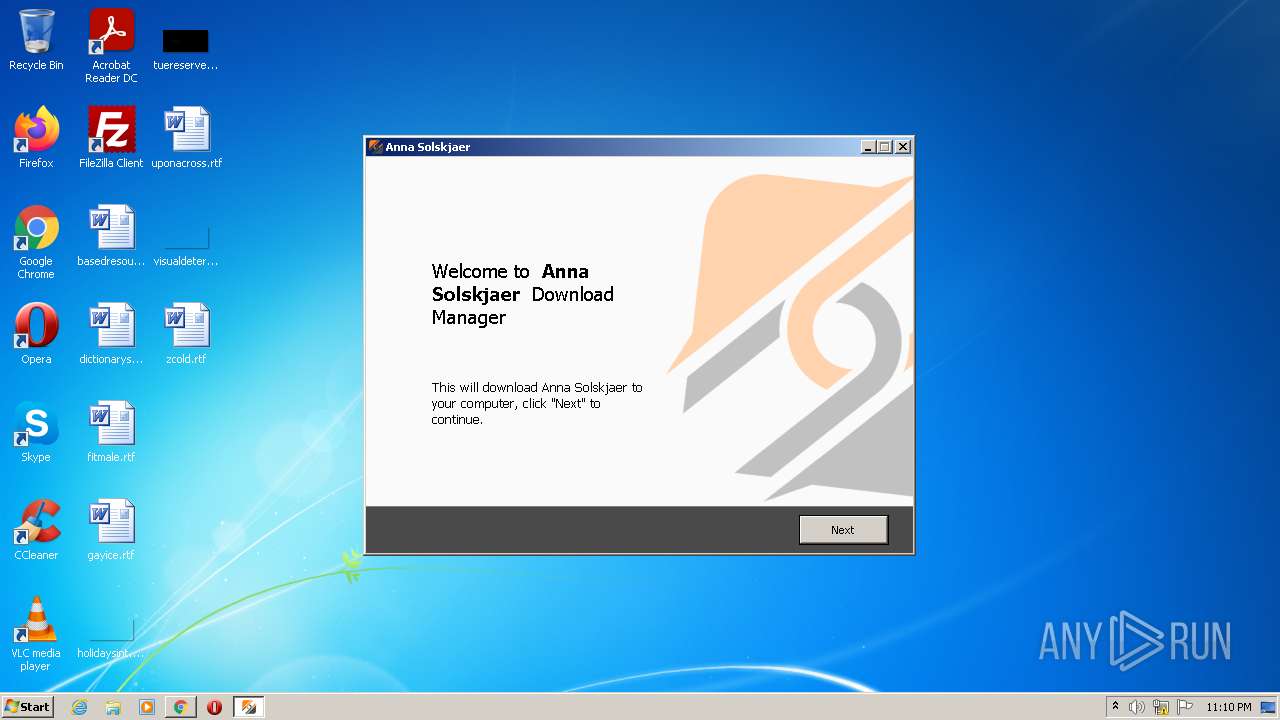
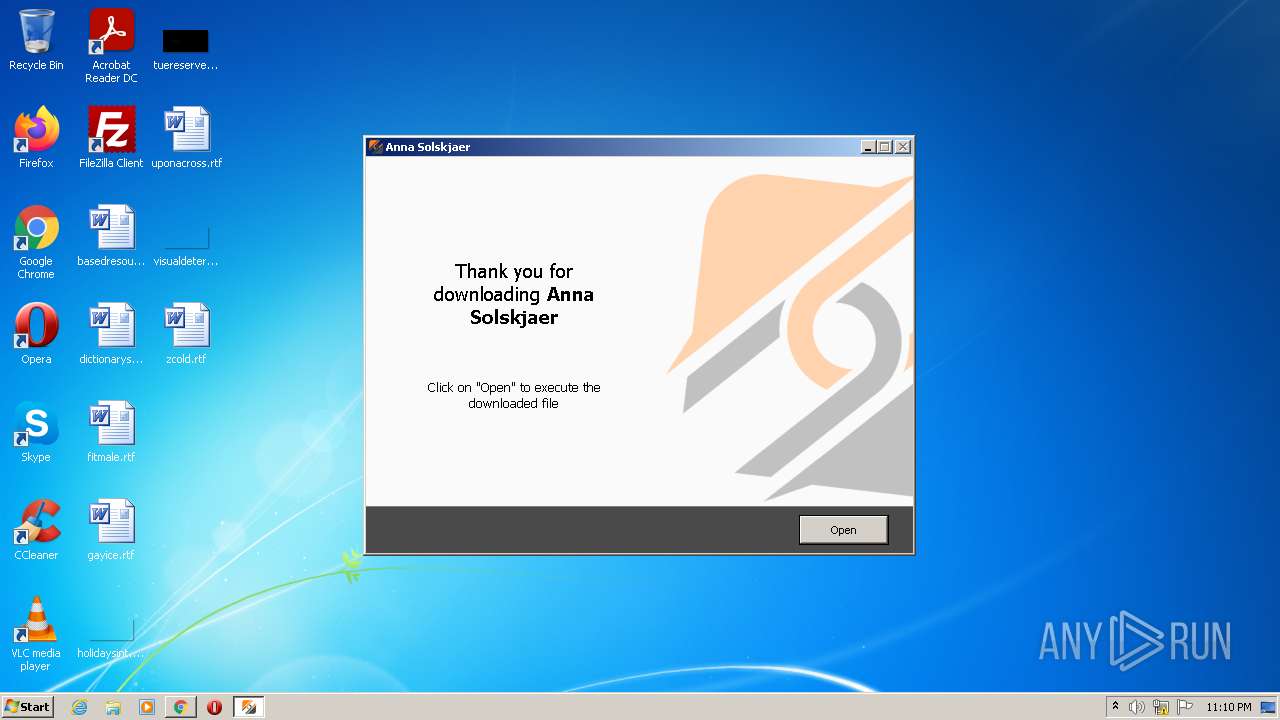
| File name: | Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe |
| Full analysis: | https://app.any.run/tasks/55e32b5d-1b70-43ec-a339-ec60471561c2 |
| Verdict: | Malicious activity |
| Analysis date: | December 28, 2021, 23:10:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1F2951435EE209E761A9DF276023C48F |
| SHA1: | 98D306E3248A3CF6FA61D0CD711FBC74F3B85702 |
| SHA256: | C3E83B560DB63700A60C5D4D8CD562FBC1A0F8BD4B6098A27B3F1CA8338C3D09 |
| SSDEEP: | 49152:qqe3f6a0zD7+H98AHaCfu6O/HCL+WuTmuKwEP:DSiBD7E9vBuT/HCK5NKXP |
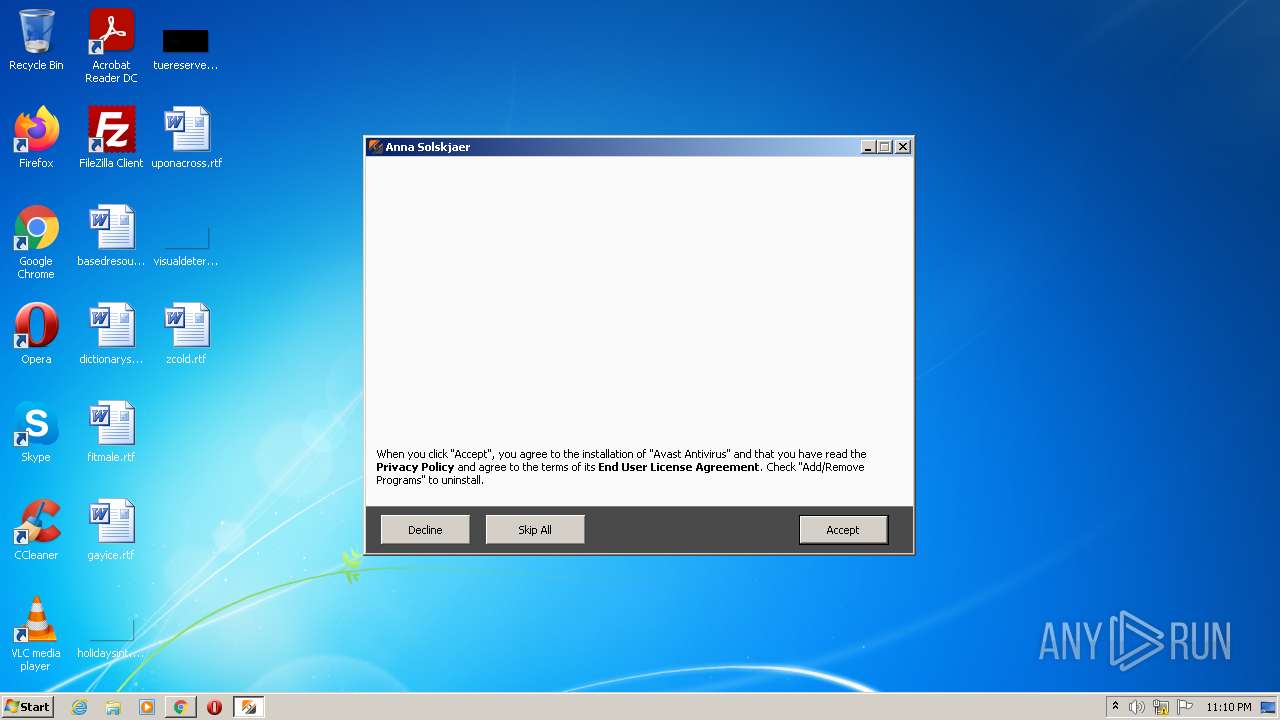
MALICIOUS
Drops executable file immediately after starts
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe (PID: 2868)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe (PID: 3640)
SUSPICIOUS
Reads the computer name
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 3852)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
Reads the Windows organization settings
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
Executable content was dropped or overwritten
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe (PID: 2868)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe (PID: 3640)
Checks supported languages
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe (PID: 3640)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe (PID: 2868)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 3852)
Reads Windows owner or organization settings
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
Drops a file with too old compile date
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
Drops a file that was compiled in debug mode
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
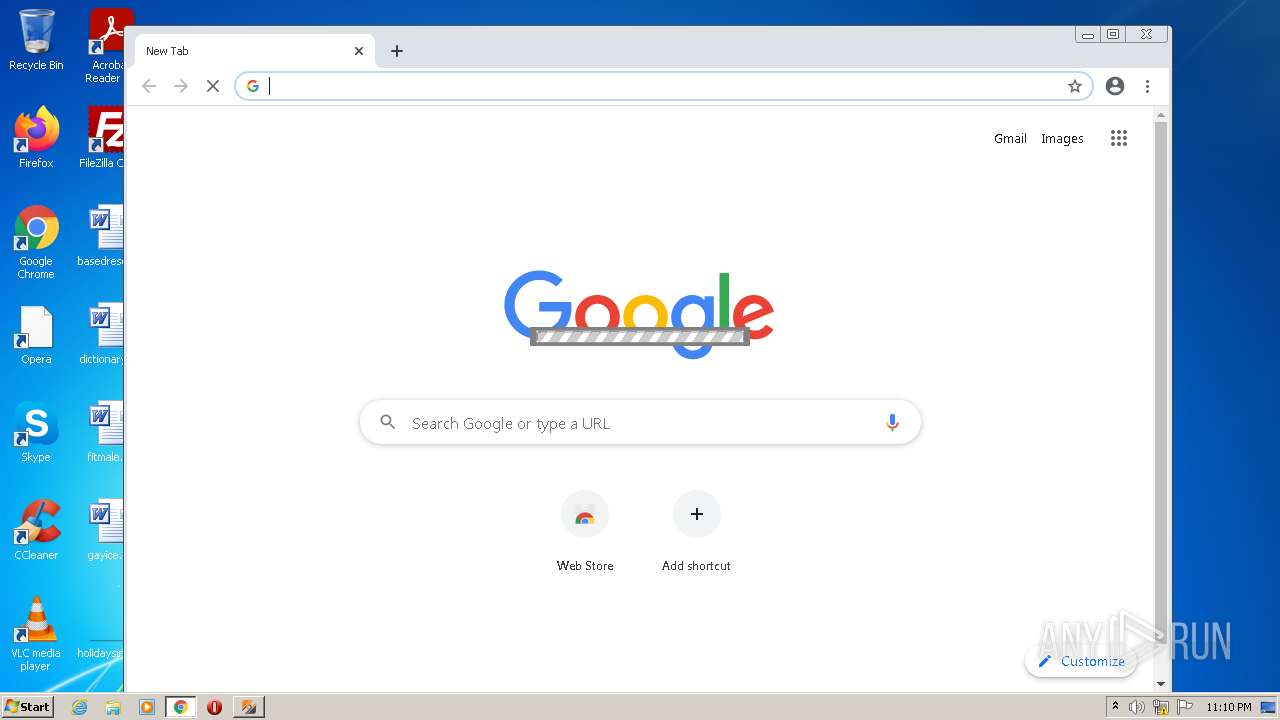
Modifies files in Chrome extension folder
- chrome.exe (PID: 3340)
INFO
Application was dropped or rewritten from another process
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 3852)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
Checks supported languages
- chrome.exe (PID: 3340)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 1768)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 2872)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 3416)
- chrome.exe (PID: 3040)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 1360)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 3808)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 2008)
- chrome.exe (PID: 3404)
- chrome.exe (PID: 2200)
Loads dropped or rewritten executable
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
Manual execution by user
- chrome.exe (PID: 3340)
Application launched itself
- chrome.exe (PID: 3340)
- chrome.exe (PID: 2332)
Reads the hosts file
- chrome.exe (PID: 3340)
- chrome.exe (PID: 2164)
Reads the computer name
- chrome.exe (PID: 3340)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 2164)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 2816)
Reads settings of System Certificates
- chrome.exe (PID: 2164)
- Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp (PID: 1952)
Changes default file association
- chrome.exe (PID: 3340)
Reads the date of Windows installation
- chrome.exe (PID: 3668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| ProductVersion: | 2.0.0.13 |
|---|---|
| ProductName: | Linkvertise GmbH & Co. KG |
| OriginalFileName: | |
| LegalCopyright: | |
| FileVersion: | 2.0.0.13 |
| FileDescription: | Linkvertise GmbH & Co. KG |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.0.0.13 |
| FileVersionNumber: | 2.0.0.13 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6 |
| OSVersion: | 6.1 |
| EntryPoint: | 0xb5eec |
| UninitializedDataSize: | - |
| InitializedDataSize: | 157184 |
| CodeSize: | 741376 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2020:11:15 10:48:30+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2020 09:48:30 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Linkvertise GmbH & Co. KG |
| FileVersion: | 2.0.0.13 |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | Linkvertise GmbH & Co. KG |
| ProductVersion: | 2.0.0.13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 15-Nov-2020 09:48:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000B361C | 0x000B3800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35606 |
.itext | 0x000B5000 | 0x00001688 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97275 |
.data | 0x000B7000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0444 |
.bss | 0x000BB000 | 0x00006DE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000C2000 | 0x00000F36 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.8987 |
.didata | 0x000C3000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75636 |
.edata | 0x000C4000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.87222 |
.tls | 0x000C5000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000C6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.38389 |
.rsrc | 0x000C7000 | 0x000216F0 | 0x00021800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.61597 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18295 | 1830 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.80552 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.40448 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.76613 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.12824 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.64443 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000BE63C |
__dbk_fcall_wrapper | 2 | 0x0000D0A0 |
TMethodImplementationIntercept | 3 | 0x00054060 |
Total processes
69
Monitored processes
32
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1116,10799209277393069778,18233364377730404918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1116,10799209277393069778,18233364377730404918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1116,10799209277393069778,18233364377730404918,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1952 | "C:\Users\admin\AppData\Local\Temp\is-03HM0.tmp\Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp" /SL5="$20140,1785071,899584,C:\Users\admin\AppData\Local\Temp\Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe" /SPAWNWND=$1013E /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-03HM0.tmp\Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp | Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1116,10799209277393069778,18233364377730404918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1116,10799209277393069778,18233364377730404918,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1116,10799209277393069778,18233364377730404918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1300 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1116,10799209277393069778,18233364377730404918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3572 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1116,10799209277393069778,18233364377730404918,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2988 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
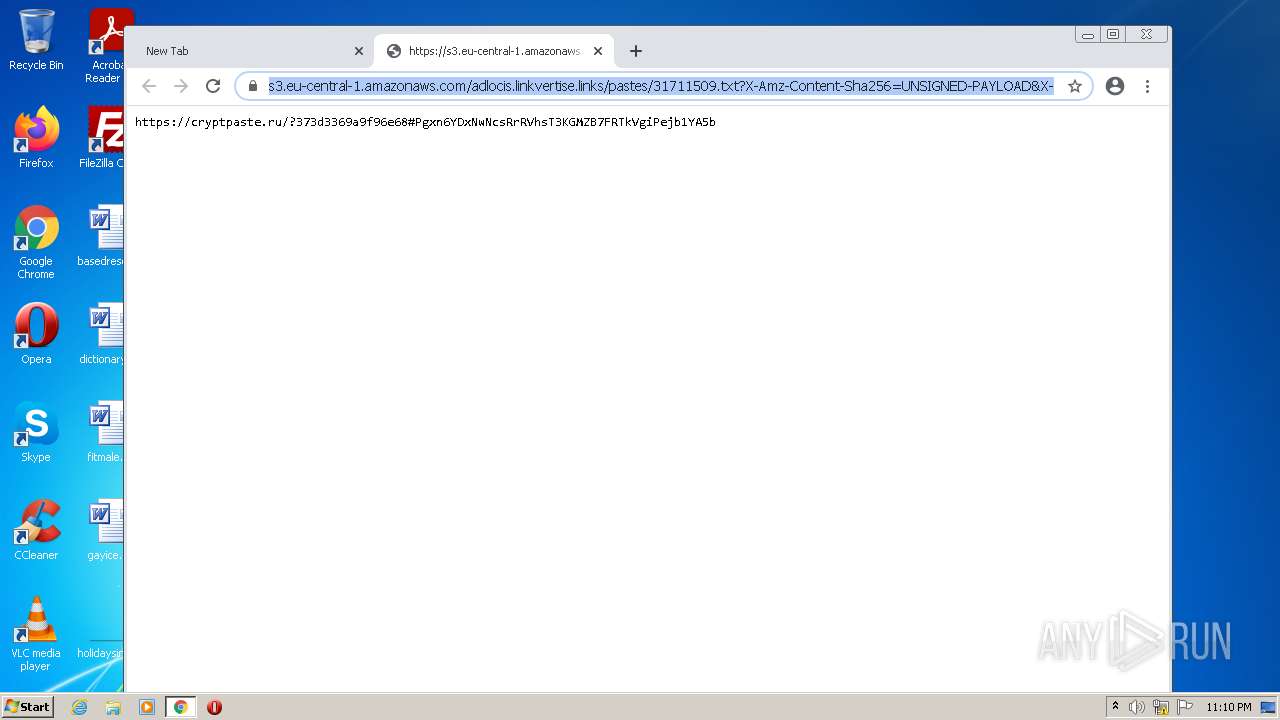
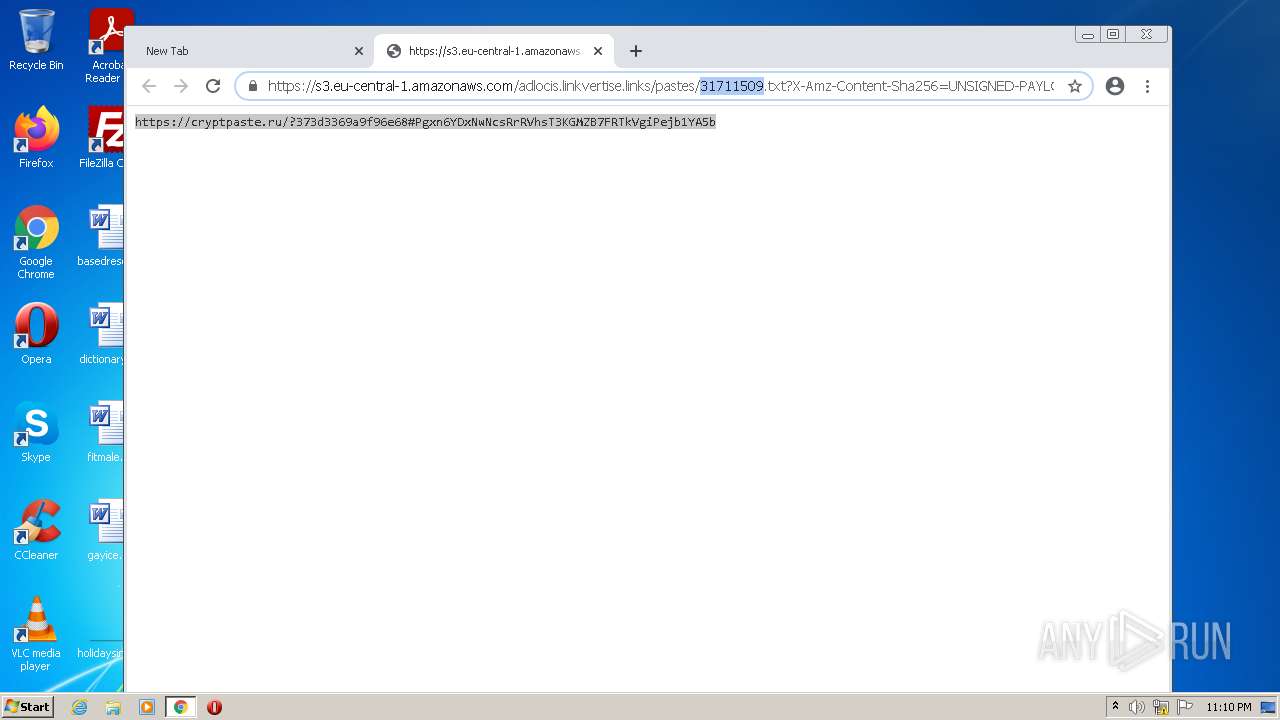
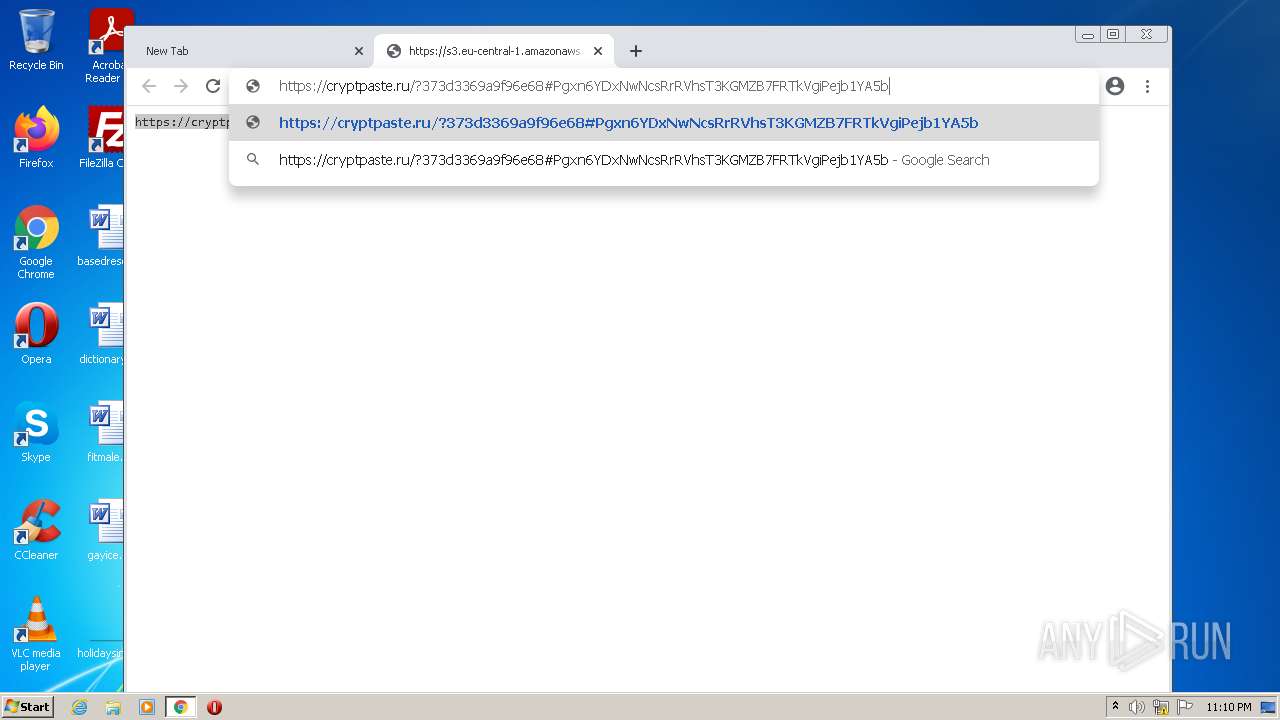
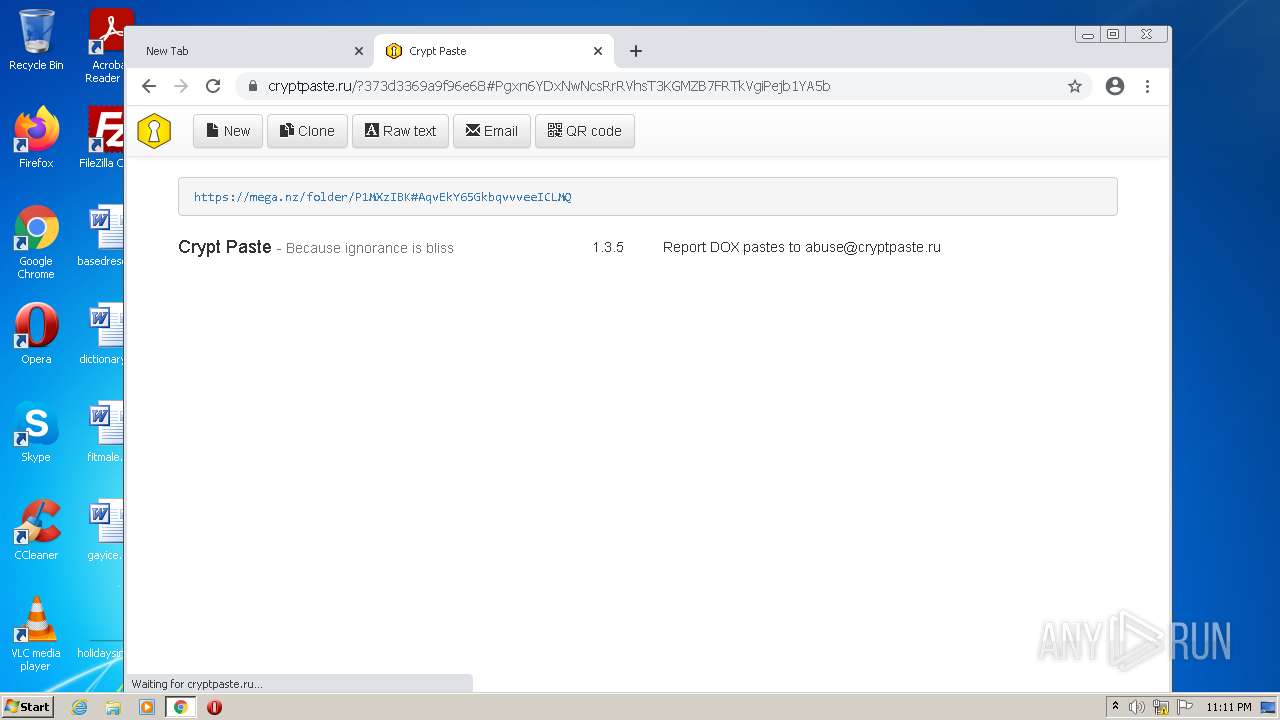
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --single-argument https://s3.eu-central-1.amazonaws.com/adlocis.linkvertise.links/pastes/31711509.txt?X-Amz-Content-Sha256=UNSIGNED-PAYLOAD&X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=AKIA6L5L3NKTBHJ3YVHU/20211228/eu-central-1/s3/aws4_request&X-Amz-Date=20211228T224908Z&X-Amz-SignedHeaders=host&X-Amz-Expires=432000&X-Amz-Signature=af249b92fe8055fa520396ebb353d22020ce032d51fc57092333bd54052b1ac9 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
14 181
Read events
13 988
Write events
176
Delete events
17
Modification events
| (PID) Process: | (1952) Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: A0070000FC2DB50F40FCD701 | |||
| (PID) Process: | (1952) Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 892848AFDCC09506F84991DABAEFC1C51297C36A8F05AF89BE093D17CCF83426 | |||
| (PID) Process: | (1952) Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3340) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
Executable files
4
Suspicious files
179
Text files
158
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61CB9956-D0C.pma | — | |
MD5:— | SHA256:— | |||
| 3340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a7d911f7-66a4-4e79-8c8a-9acaf6fa120e.tmp | text | |
MD5:— | SHA256:— | |||
| 1952 | Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp | C:\Users\admin\AppData\Local\Temp\is-TBRH3.tmp\zbShieldUtils.dll | executable | |
MD5:E1F18A22199C6F6AA5D87B24E5B39EF1 | SHA256:62C56C8CF2AC6521CE047B73AA99B6D3952CA53F11D34B00E98D17674A2FC10D | |||
| 1952 | Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp | C:\Users\admin\AppData\Local\Temp\is-TBRH3.tmp\botva2.dll | executable | |
MD5:67965A5957A61867D661F05AE1F4773E | SHA256:450B9B0BA25BF068AFBC2B23D252585A19E282939BF38326384EA9112DFD0105 | |||
| 3340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fc6d72fb-321d-4159-80bf-368d3aecd781.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF116f41.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3340 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
77
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
876 | svchost.exe | HEAD | 200 | 173.194.163.104:80 | http://r2---sn-5go7yne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx?cms_redirect=yes&mh=ls&mip=157.97.120.10&mm=28&mn=sn-5go7yne6&ms=nvh&mt=1640732657&mv=m&mvi=2&pl=24&rmhost=r3---sn-5go7yne6.gvt1.com&shardbypass=yes&smhost=r3---sn-5go7ynld.gvt1.com | US | — | — | whitelisted |
876 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
876 | svchost.exe | HEAD | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
876 | svchost.exe | GET | 206 | 173.194.163.103:80 | http://r1---sn-5go7yne6.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=157.97.120.10&mm=28&mn=sn-5go7yne6&ms=nvh&mt=1640732657&mv=m&mvi=1&pl=24&shardbypass=yes&smhost=r1---sn-5go7ynld.gvt1.com | US | binary | 5.64 Kb | whitelisted |
876 | svchost.exe | HEAD | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 593 b | whitelisted |
2164 | chrome.exe | GET | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 593 b | whitelisted |
876 | svchost.exe | GET | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | html | 504 b | whitelisted |
876 | svchost.exe | GET | 206 | 173.194.163.103:80 | http://r1---sn-5go7yne6.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw?cms_redirect=yes&mh=LV&mip=157.97.120.10&mm=28&mn=sn-5go7yne6&ms=nvh&mt=1640732657&mv=m&mvi=1&pl=24&shardbypass=yes&smhost=r1---sn-5go7ynld.gvt1.com | US | binary | 20.9 Kb | whitelisted |
876 | svchost.exe | GET | 302 | 216.58.212.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | html | 593 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2164 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
1952 | Anna Solskjaer - Linkvertise Downloader_WMnQ-G1.tmp | 18.66.242.140:443 | d17kz3i6hbr7d3.cloudfront.net | Massachusetts Institute of Technology | US | unknown |
2164 | chrome.exe | 142.250.185.68:443 | www.google.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.186.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2164 | chrome.exe | 142.250.186.74:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
— | — | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
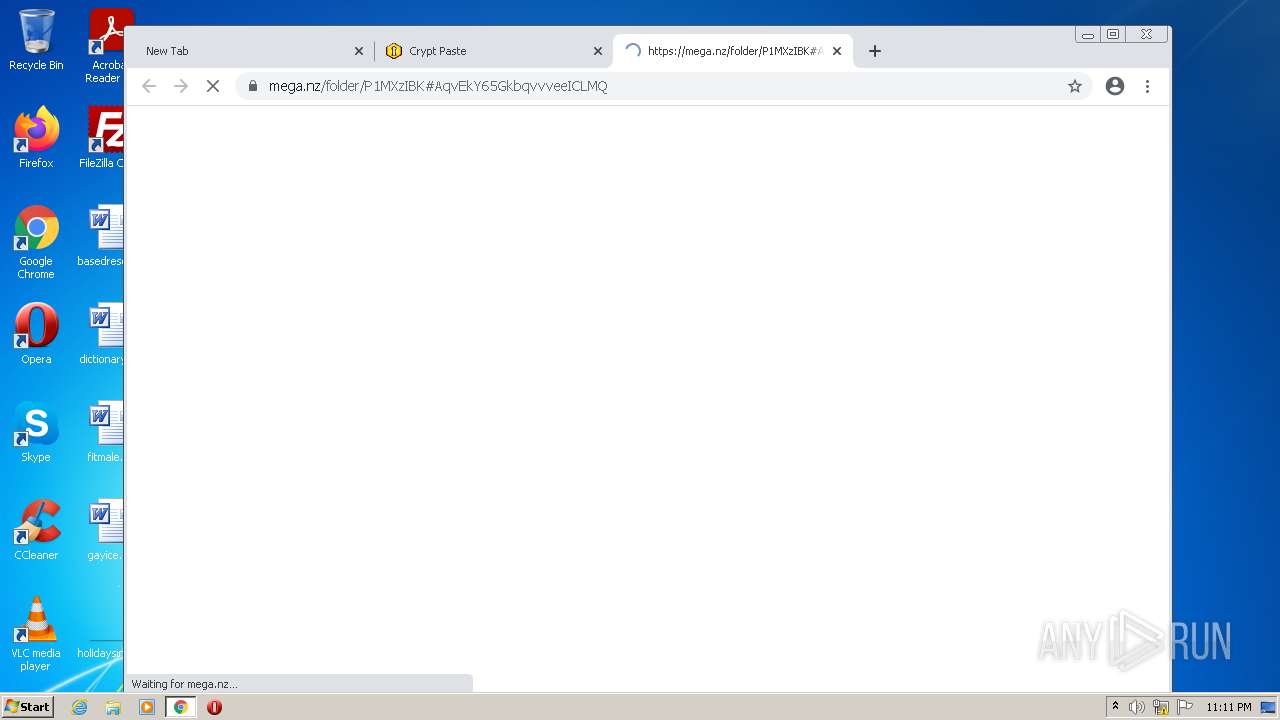
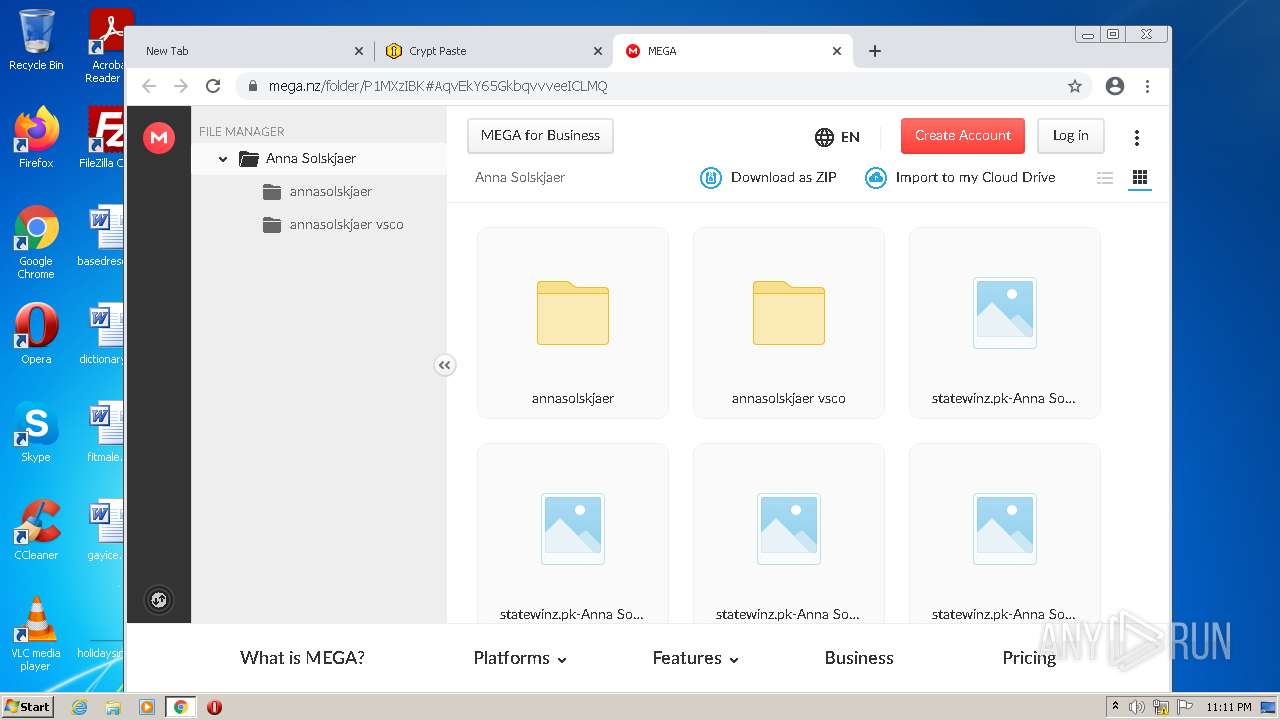
2164 | chrome.exe | 66.203.127.11:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
2164 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
2164 | chrome.exe | 52.219.168.163:443 | s3.eu-central-1.amazonaws.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d17kz3i6hbr7d3.cloudfront.net |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |