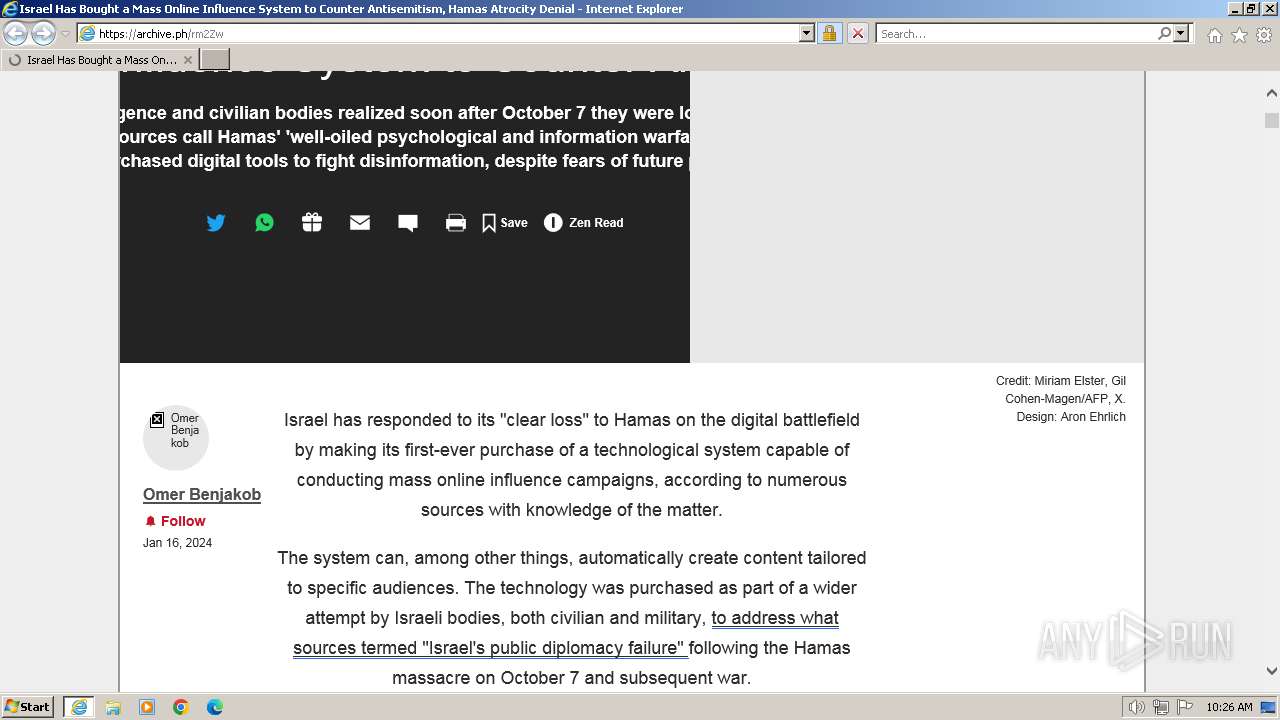
| URL: | https://archive.ph/rm2Zw |
| Full analysis: | https://app.any.run/tasks/010d69bf-6d53-4cd4-9468-7b73dc9b1825 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2024, 10:26:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 12F3077F917583ED79178784CD455294 |
| SHA1: | E17FF6E1C55360E47A8FF57615BDF6A4F8F61FCE |
| SHA256: | C3E32E28402E1456AA50FF5DF22A091171682DD9B02A272771D36485B2C45191 |
| SSDEEP: | 3:N8MaNBS:2MF |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2040 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://archive.ph/rm2Zw" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 459
Read events
16 383
Write events
74
Delete events
2
Modification events
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
48
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:95C671CB7163FFC3A96696E131A650CE | SHA256:0DA4C06EF678E51FD4FFCEFB1F64F3C17AB171CEC3C4DA0D6B0D5822F3383385 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF955.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF954.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\69B469D13C028EECB8BDFB6458F4A8D1 | binary | |
MD5:F92A3DF0FEB54D3A0E776C099EEB648A | SHA256:3A542555B56FF227C4189A897CA84798851FB58EC5A37FAF676F95C4B7ABDFC5 | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\10a6f7f8519cb8b3860a53a9e7900fef5361e174[1].webp | image | |
MD5:69F0ED034ED4AC100E504CD91021D3E4 | SHA256:7854F6F597EA79815D75FDEEAC8106DCB5B001510CBFD4C2416B467253387CCB | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\69B469D13C028EECB8BDFB6458F4A8D1 | binary | |
MD5:B9B4B79F987D8FF654FFE9A89D1F7863 | SHA256:8BEBD0EBBC51ED75FFEA352DE62821D3798D638A23E8F7882F1C28F09131246C | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\1100[1].js | text | |
MD5:85F21B6C2DC964C1D275523329BD7E89 | SHA256:DE576F58A754F39143662056411ABFB9C5AB8937D21D6DC004E69210D233E0DA | |||
| 1056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:A8E2CD0C5A6DF624B5AADE24468DA3E7 | SHA256:C17307168019F6E303612DBA90917724AA7D880BDCAB294E6AEC30AD2236065E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
47
DNS requests
23
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1056 | iexplore.exe | GET | 200 | 2.19.11.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b21170b0e7a1648 | unknown | compressed | 4.66 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 2.19.11.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | unknown | compressed | 4.66 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 2.19.11.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?947fb26d7412b1b7 | unknown | compressed | 65.2 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 2.19.11.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b67c9d757472bd69 | unknown | compressed | 65.2 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 2.19.105.18:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
1056 | iexplore.exe | GET | 200 | 95.101.54.114:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgN2lMscK%2BESHslnVduO%2FOJpTg%3D%3D | unknown | binary | 503 b | unknown |
1056 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | unknown | binary | 1.37 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | unknown | binary | 1.49 Kb | unknown |
1056 | iexplore.exe | GET | 200 | 108.138.2.173:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | unknown | binary | 2.02 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1056 | iexplore.exe | 195.123.246.100:443 | archive.ph | Green Floid LLC | CZ | unknown |
1056 | iexplore.exe | 2.19.11.178:80 | ctldl.windowsupdate.com | Elisa Oyj | NL | unknown |
1056 | iexplore.exe | 2.19.105.18:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
1056 | iexplore.exe | 95.101.54.114:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1056 | iexplore.exe | 52.217.139.216:443 | s3.amazonaws.com | AMAZON-02 | US | unknown |
1056 | iexplore.exe | 104.26.0.163:443 | a.publir.com | CLOUDFLARENET | US | unknown |
1056 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
archive.ph |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
a.publir.com |
| unknown |
s3.amazonaws.com |
| shared |
ocsp.digicert.com |
| whitelisted |
216.24.216.21.de.itl1.367445112.pixel.archive.ph |
| unknown |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain in DNS Lookup (archive .ph) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |
1056 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Abused Website Archival Domain (archive .ph in TLS SNI) |