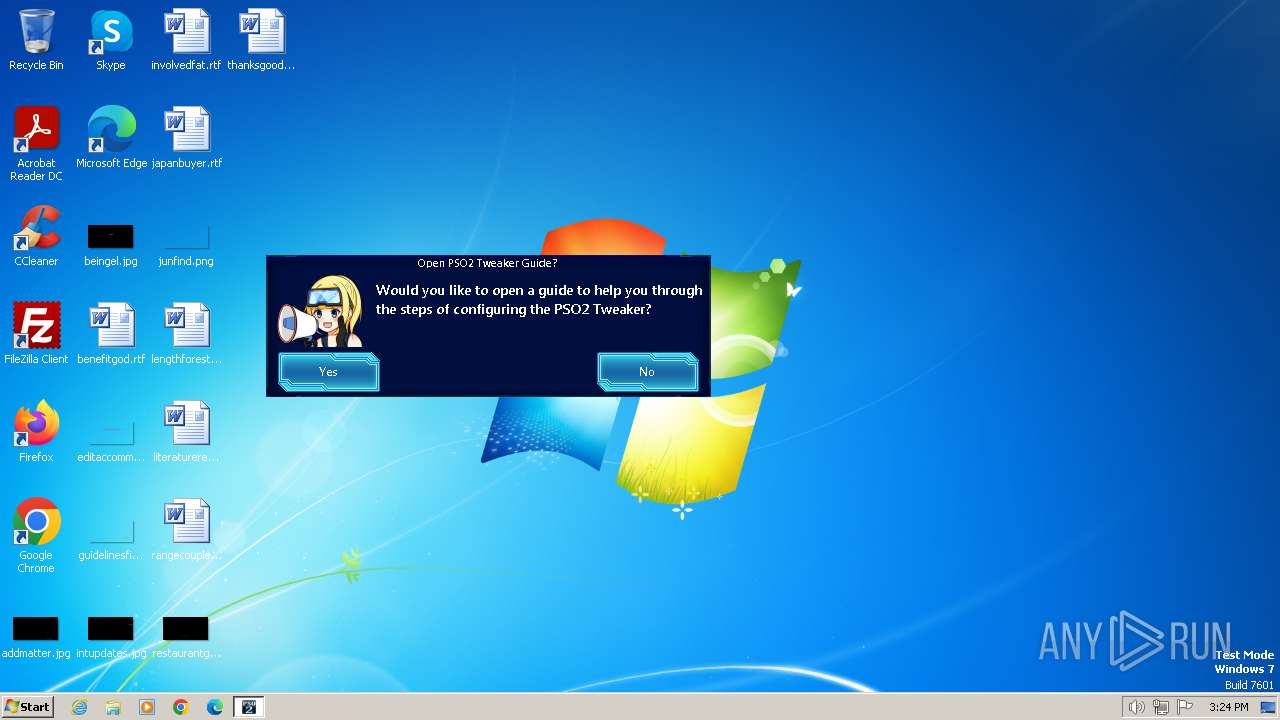
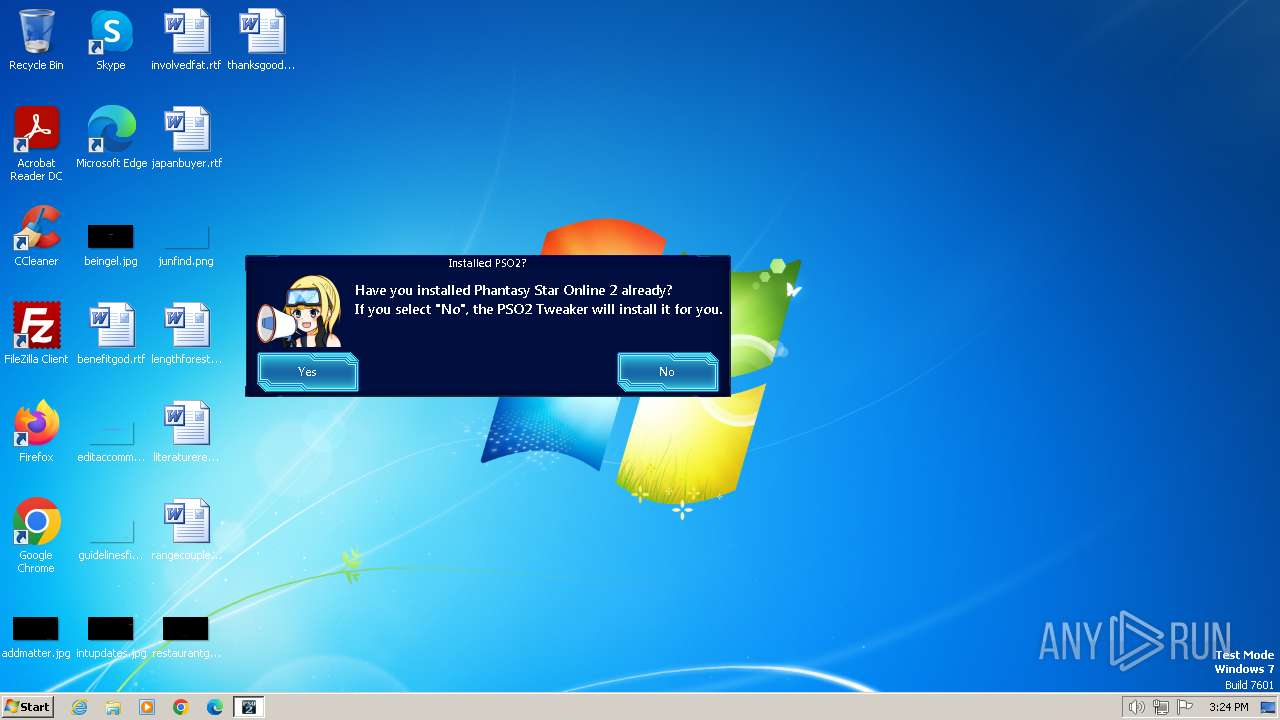
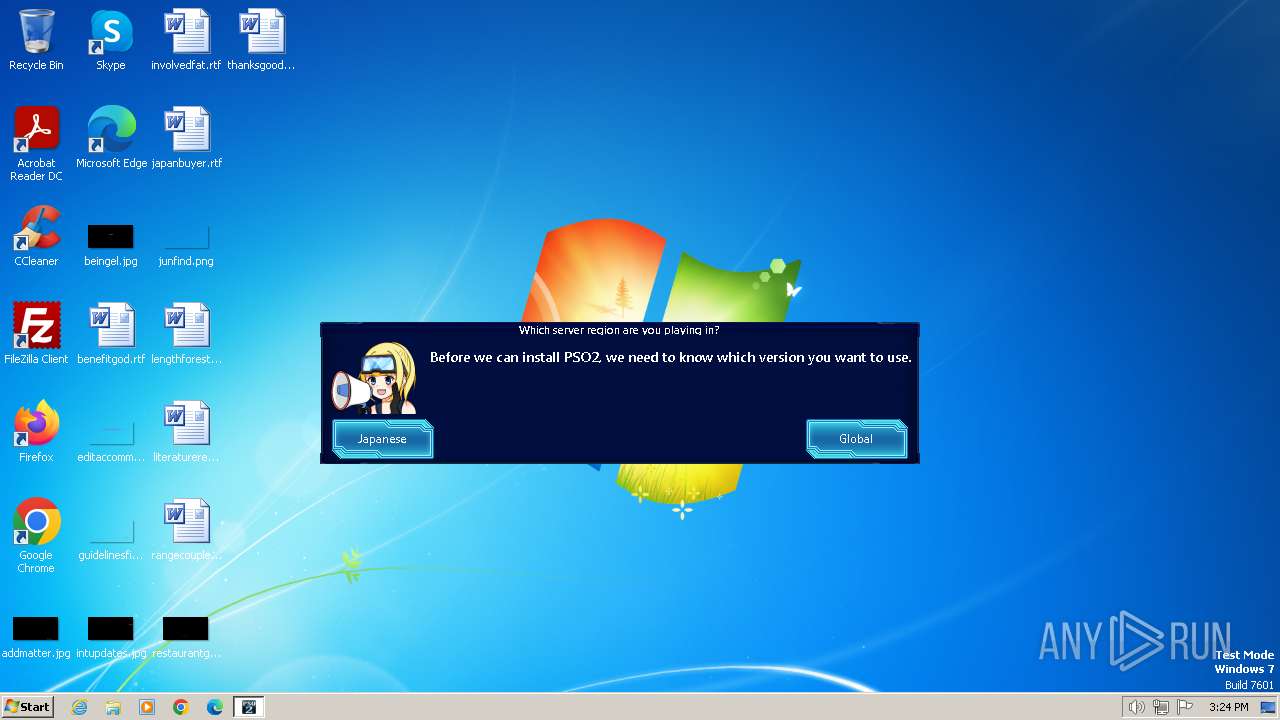
| File name: | PSO2 Tweaker.exe |
| Full analysis: | https://app.any.run/tasks/e5d539a8-8c39-4a42-be9d-5cc1ee9bca38 |
| Verdict: | Malicious activity |
| Analysis date: | January 31, 2024, 15:24:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 49AB87C568C66B50A9C85EAB683CA693 |
| SHA1: | A1BDBF0BFF64296ED09FCFFBF274CFE1C2F3758B |
| SHA256: | C3E2A857D85A09A580427E11A851775413E8309335FDCE4691CD6BD075636A01 |
| SSDEEP: | 98304:UROsy0xYCSmkGxhE3SmkGxhE3mYKRGYT7TKoFV7tDCcpO/KxQeLJJahp+U7i9THL:amNmBJrL8T |
MALICIOUS
Drops the executable file immediately after the start
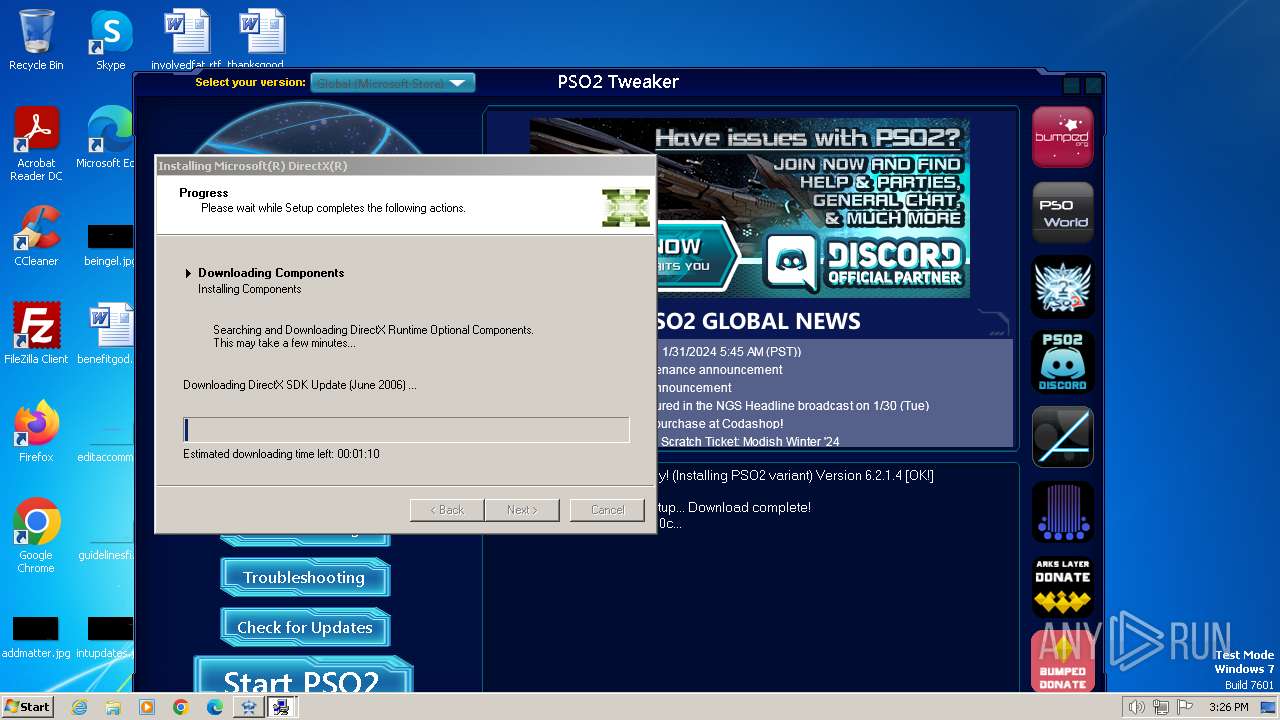
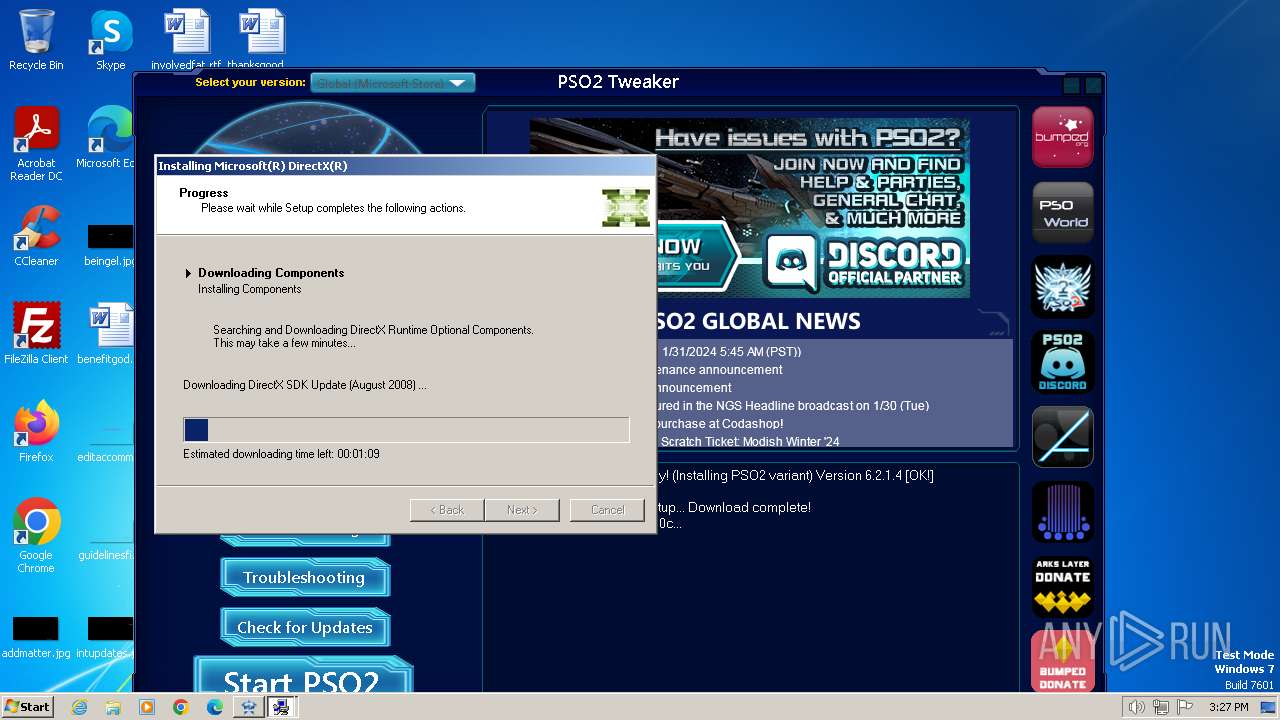
- PSO2 Tweaker.exe (PID: 1072)
- dxwsetup.exe (PID: 3364)
- dxwebsetup.exe (PID: 2524)
- PSO2 Tweaker.exe (PID: 3332)
Creates a writable file in the system directory
- dxwsetup.exe (PID: 3364)
SUSPICIOUS
Reads the Internet Settings
- PSO2 Tweaker.exe (PID: 1072)
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
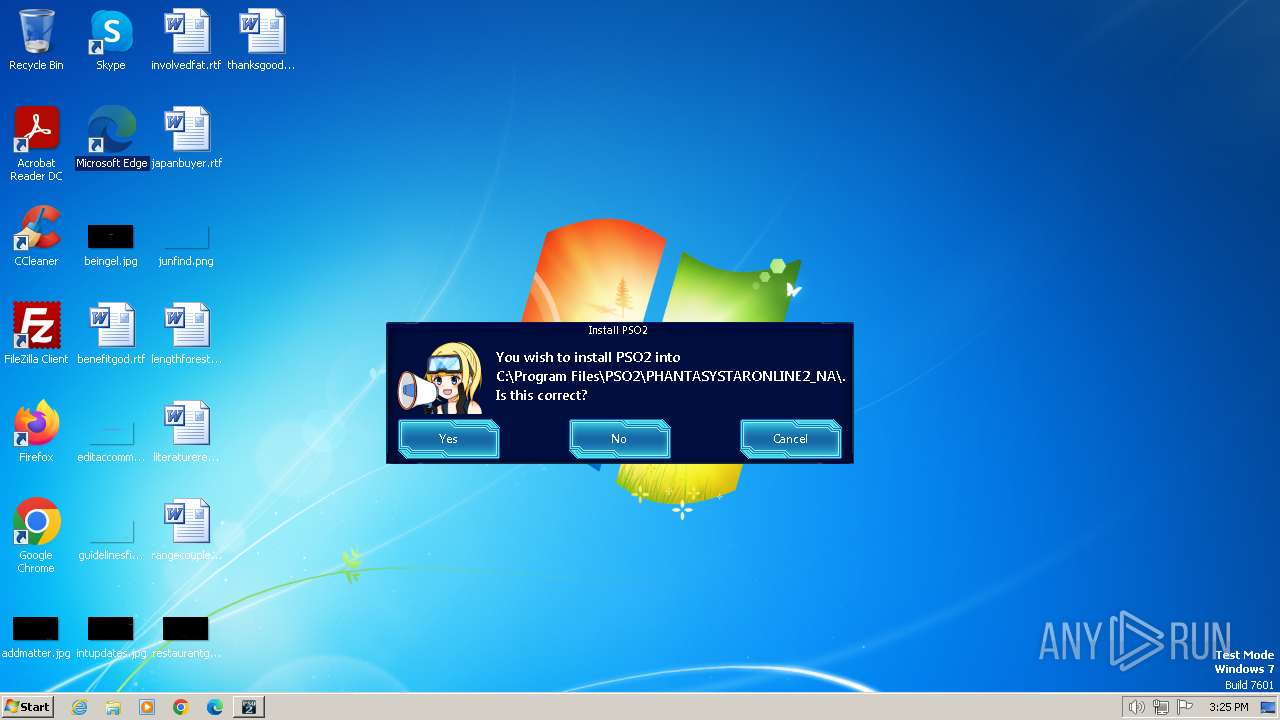
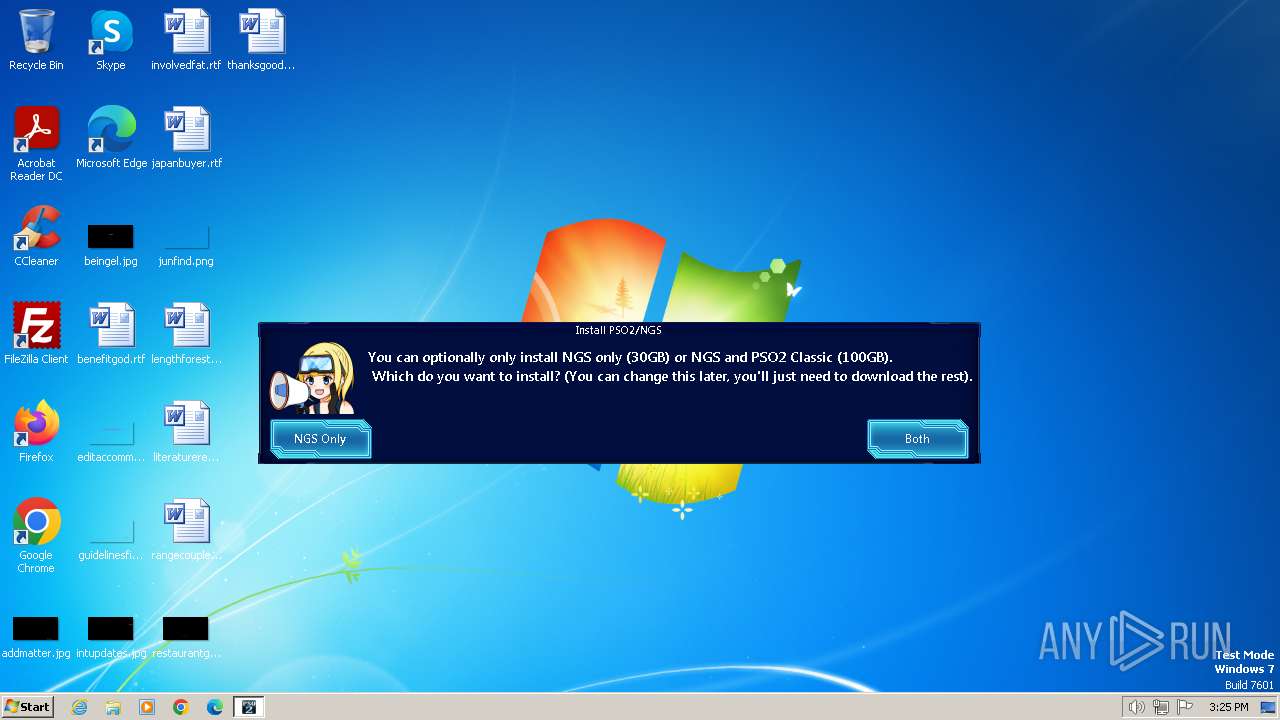
Application launched itself
- PSO2 Tweaker.exe (PID: 1072)
Reads settings of System Certificates
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
Reads Microsoft Outlook installation path
- PSO2 Tweaker.exe (PID: 3332)
Adds/modifies Windows certificates
- PSO2 Tweaker.exe (PID: 3332)
Checks Windows Trust Settings
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
Reads security settings of Internet Explorer
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
Executable content was dropped or overwritten
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
- dxwebsetup.exe (PID: 2524)
Reads Internet Explorer settings
- PSO2 Tweaker.exe (PID: 3332)
Process drops legitimate windows executable
- PSO2 Tweaker.exe (PID: 3332)
- dxwebsetup.exe (PID: 2524)
- dxwsetup.exe (PID: 3364)
Starts a Microsoft application from unusual location
- dxwsetup.exe (PID: 3364)
INFO
Checks supported languages
- PSO2 Tweaker.exe (PID: 1072)
- PSO2 Tweaker.exe (PID: 3332)
- dxwebsetup.exe (PID: 2524)
- dxwsetup.exe (PID: 3364)
Reads the machine GUID from the registry
- PSO2 Tweaker.exe (PID: 1072)
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
Reads the computer name
- PSO2 Tweaker.exe (PID: 1072)
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
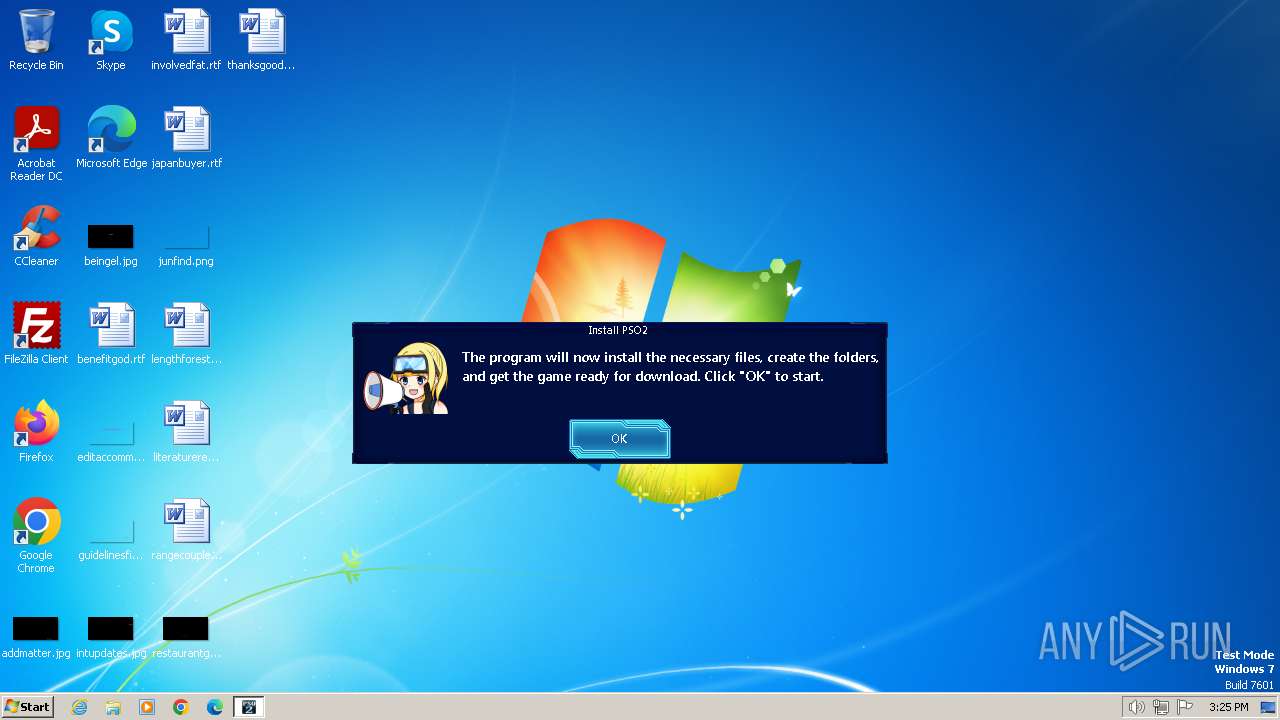
Creates files or folders in the user directory
- PSO2 Tweaker.exe (PID: 1072)
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
Reads Environment values
- PSO2 Tweaker.exe (PID: 3332)
Creates files in the program directory
- PSO2 Tweaker.exe (PID: 3332)
Checks proxy server information
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
Create files in a temporary directory
- dxwebsetup.exe (PID: 2524)
- PSO2 Tweaker.exe (PID: 3332)
- dxwsetup.exe (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:11:23 15:23:16+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 7394816 |
| InitializedDataSize: | 346112 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x70f508 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.1.4 |
| ProductVersionNumber: | 6.2.1.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | A replacement launcher to help you play (and fix!) PSO2: New Genesis (Global and JP)! |
| CompanyName: | Arks-Layer |
| FileDescription: | PSO2 Tweaker |
| FileVersion: | 6.2.1.4 |
| InternalName: | PSO2 Tweaker.exe |
| LegalCopyright: | Copyright ©2023 |
| LegalTrademarks: | - |
| OriginalFileName: | PSO2 Tweaker.exe |
| ProductName: | PSO2 Tweaker |
| ProductVersion: | 6.2.1.4 |
| AssemblyVersion: | 6.2.1.4 |
Total processes
44
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | "C:\Users\admin\AppData\Roaming\PSO2 Tweaker.exe" | C:\Users\admin\AppData\Roaming\PSO2 Tweaker.exe | explorer.exe | ||||||||||||
User: admin Company: Arks-Layer Integrity Level: HIGH Description: PSO2 Tweaker Exit code: 0 Version: 6.2.1.4 Modules
| |||||||||||||||
| 1632 | "C:\Users\admin\AppData\Roaming\PSO2 Tweaker.exe" | C:\Users\admin\AppData\Roaming\PSO2 Tweaker.exe | — | explorer.exe | |||||||||||
User: admin Company: Arks-Layer Integrity Level: MEDIUM Description: PSO2 Tweaker Exit code: 3221226540 Version: 6.2.1.4 Modules
| |||||||||||||||
| 2524 | "C:\Users\admin\AppData\Roaming\dxwebsetup.exe" /Q | C:\Users\admin\AppData\Roaming\dxwebsetup.exe | PSO2 Tweaker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX 9.0 Web setup Exit code: 0 Version: 9.29.1974.0 Modules
| |||||||||||||||
| 3332 | "C:\Users\admin\AppData\Roaming\PSO2 Tweaker.exe" | C:\Users\admin\AppData\Roaming\PSO2 Tweaker.exe | PSO2 Tweaker.exe | ||||||||||||
User: admin Company: Arks-Layer Integrity Level: HIGH Description: PSO2 Tweaker Exit code: 0 Version: 6.2.1.4 Modules
| |||||||||||||||
| 3364 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe /windowsupdate | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | dxwebsetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX Setup Exit code: 0 Version: 4.9.0.0904 Modules
| |||||||||||||||
Total events
12 392
Read events
12 301
Write events
91
Delete events
0
Modification events
| (PID) Process: | (1072) PSO2 Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1072) PSO2 Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1072) PSO2 Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1072) PSO2 Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
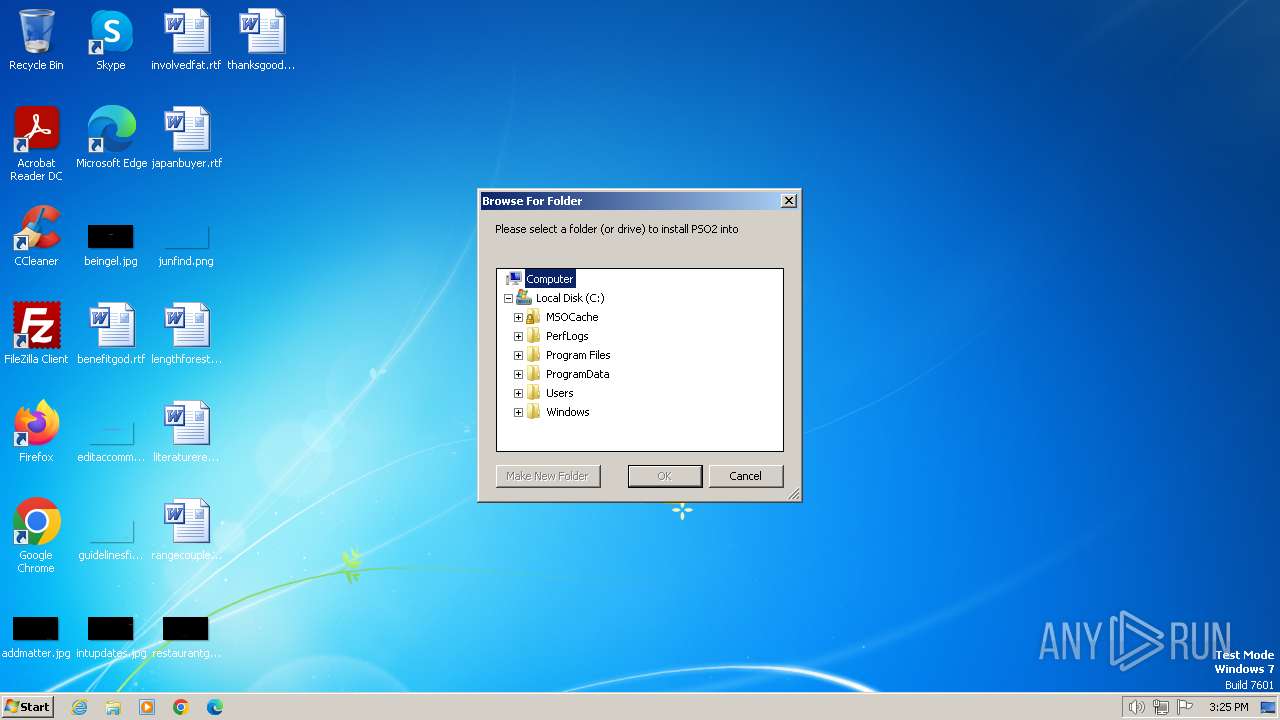
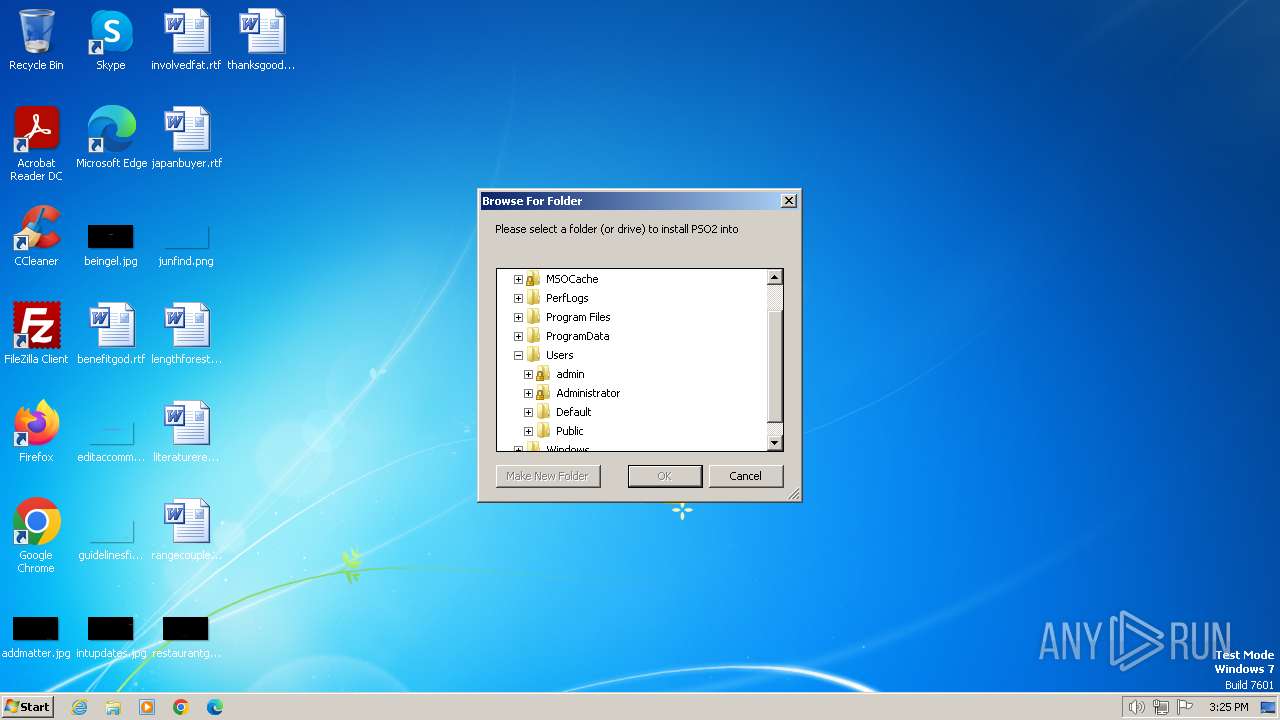
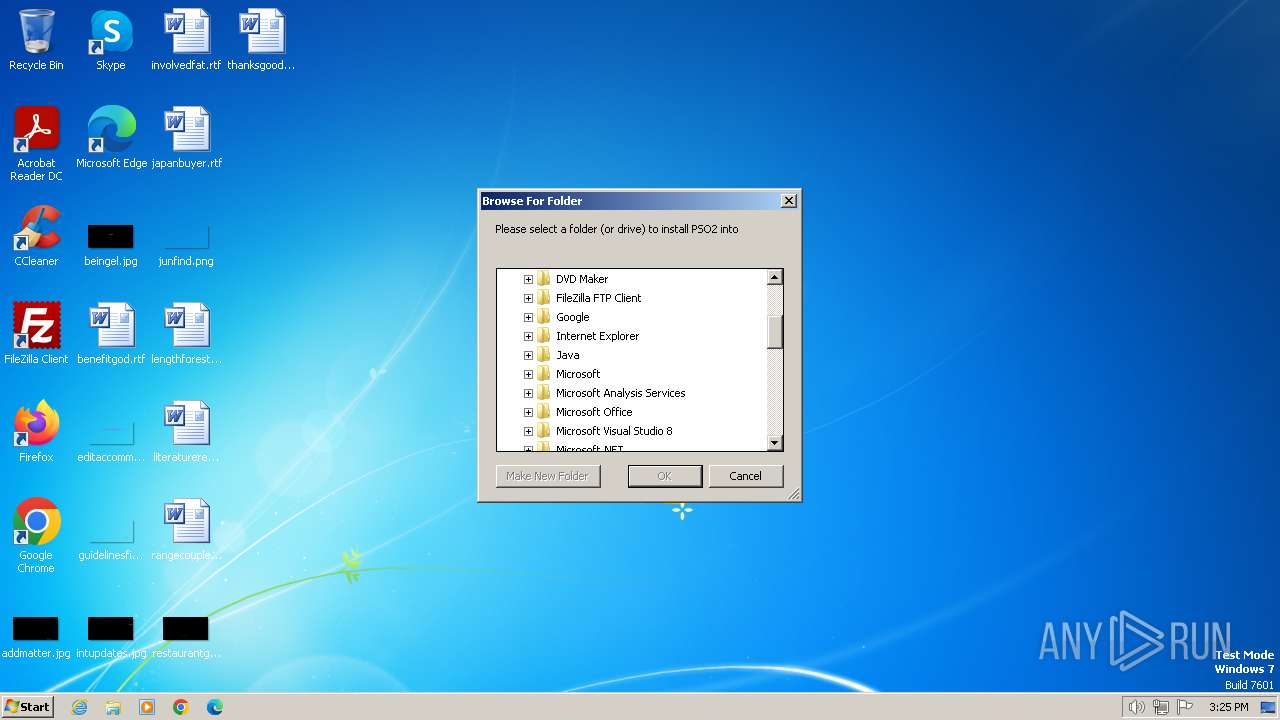
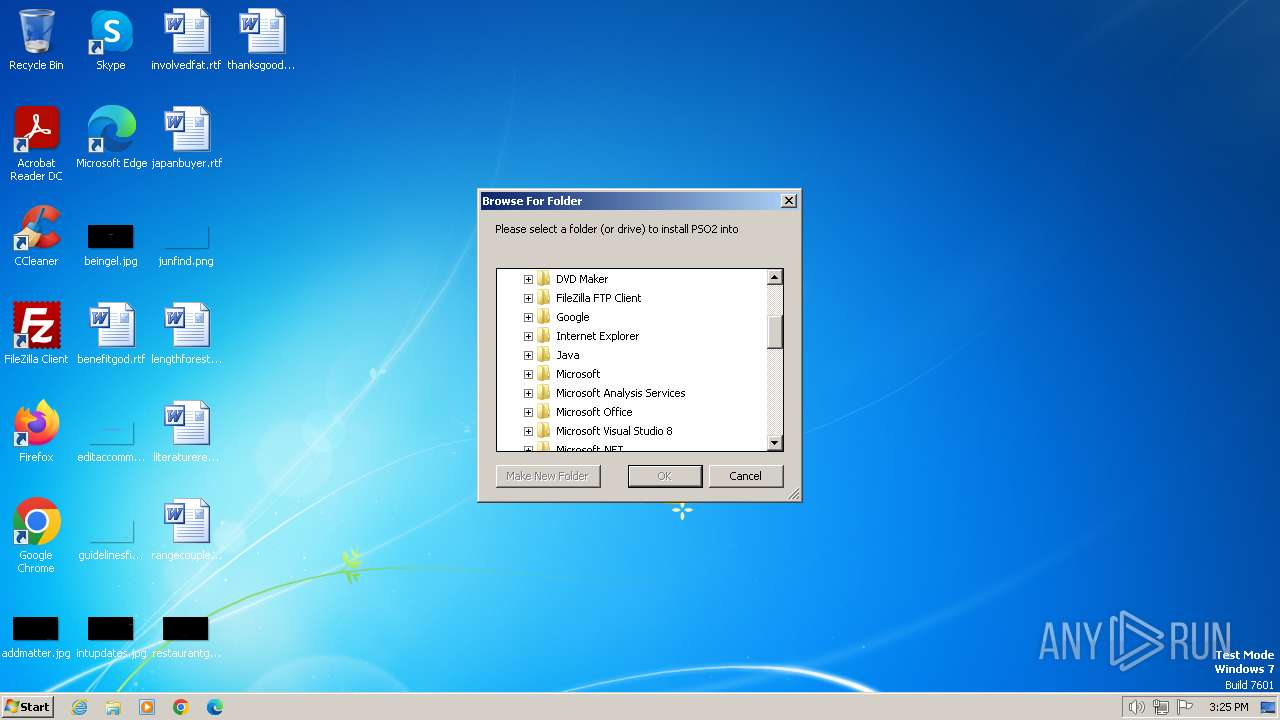
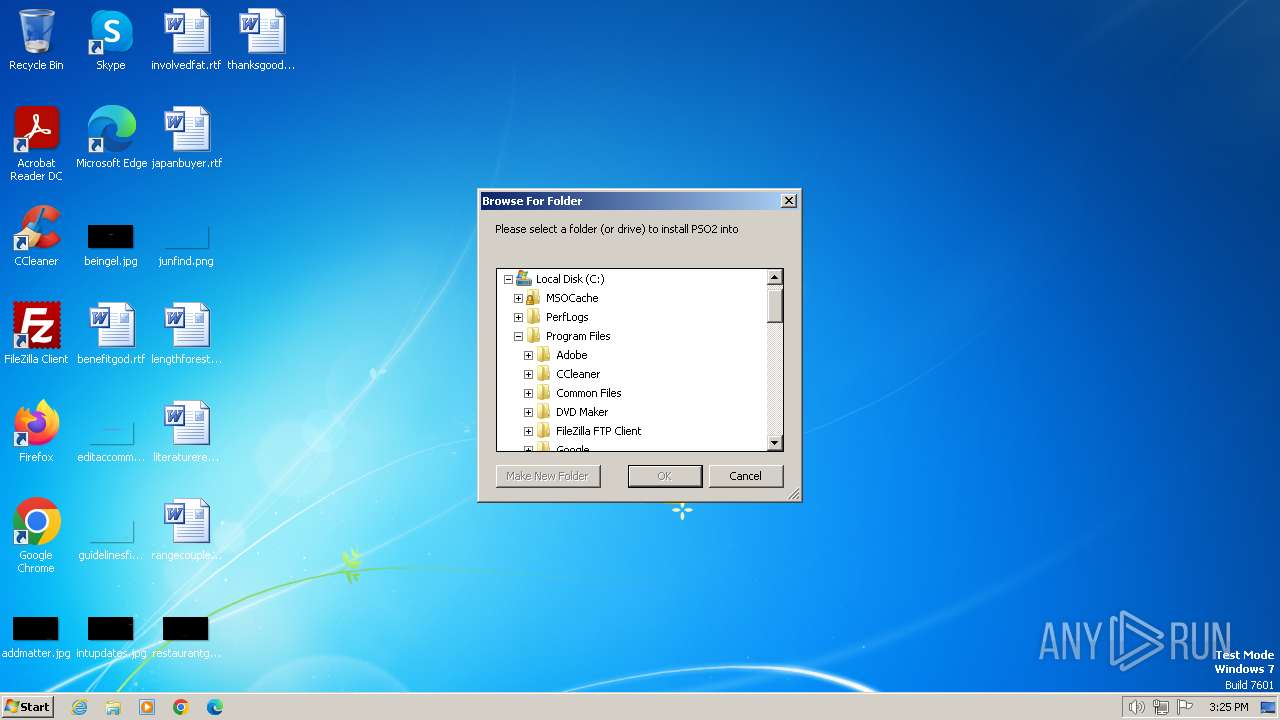
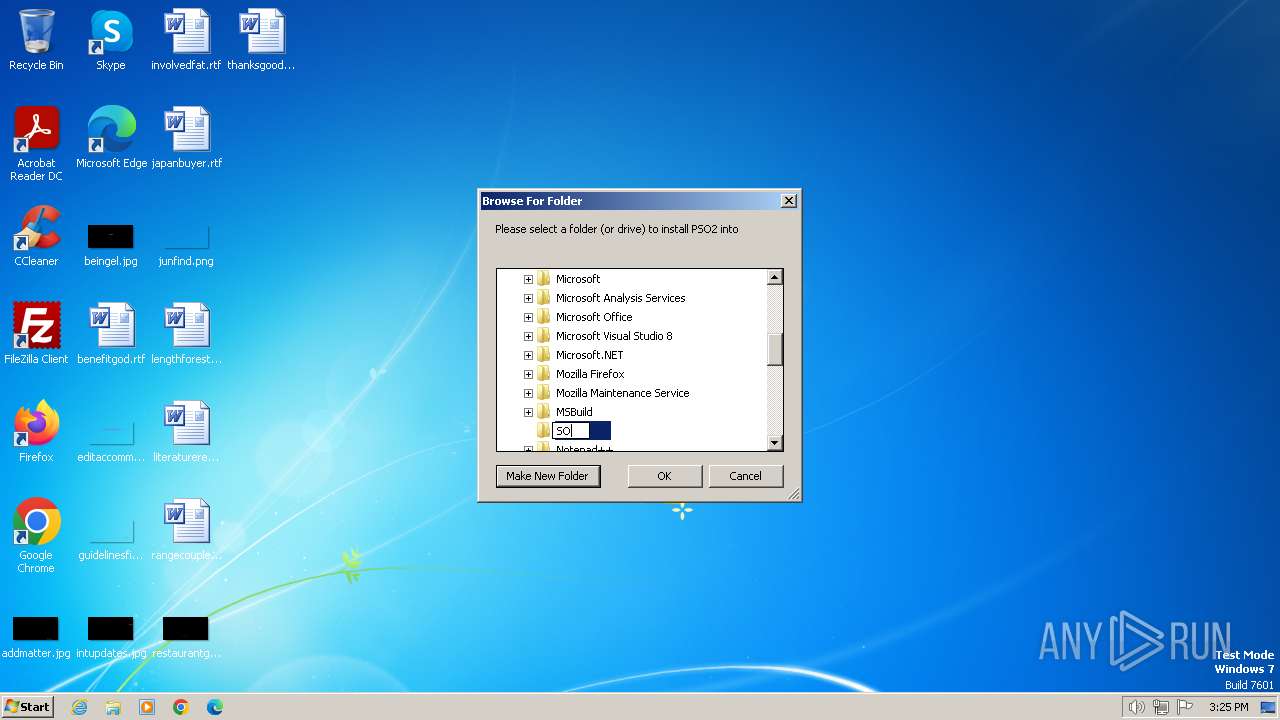
| (PID) Process: | (3332) PSO2 Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (3332) PSO2 Tweaker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (3332) PSO2 Tweaker.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3332) PSO2 Tweaker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB6200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
| (PID) Process: | (3332) PSO2 Tweaker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates\9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000200000009065F32AFC2CFEA7F452D2D6BE94D20C877EFC1C05433D9935696193FDCC05D80300000001000000140000009F6134C5FA75E4FDDE631B232BE961D6D4B97DB6200000000100000047030000308203433082022BA00302010202147327B7C17D5AE708EF73F1F45A79D78B4E99A29F300D06092A864886F70D01010B05003031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C084469676943657274301E170D3233303932393130353030335A170D3339303530383130353030335A3031310B3009060355040613025553310F300D06035504080C06426F73746F6E3111300F060355040A0C08446967694365727430820122300D06092A864886F70D01010105000382010F003082010A0282010100D91B7A55548F44F3E97C493153B75B055695736B184640D7335A2E6218083B5A1BEE2695209350E57A3EB76FBC604CB3B250DF3D9D0C560D1FBDFE30108D233A3C555100BE1A3F8E543C0B253E06E91B6D5F9CB3A093009BC8B4D3A0EB19DB59E56DA7E3D637847970D6C2AEB4A1FCF3896A7C080FE68759BAA62E6AAA8B7C7CBDA176DDC72F8D259A16D3469E31F19D2959904611D730D7D26FCFED789A0C49698FDFABF3F6727D08C61A073BB11E85C96486D49B0E0D38364C008A5EB964F8813C5DF004F9E76D2F8DB90702D800032674959BF0DF823785419101CEA928A10ACBAE7E48FE19202F3CB7BCF416476D17CB64C5570FCED443BD75D9F2C632FF0203010001A3533051301D0603551D0E041604145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7301F0603551D230418301680145D6CA352CEFC713CBBC5E21F663C3639FD19D4D7300F0603551D130101FF040530030101FF300D06092A864886F70D01010B05000382010100AF2218E4CA18144728FCC76EA14958061522FD4A018BED1A4BFCC5CCE70BC6AE9DF7D3795C9A010D53628E2B6E7C10D6B07E53546235A5EE480E5A434E312154BF1E39AAC27D2C18D4F41CBBECFE4538CEF93EF62C17D187A7F720F4A9478410D09620C9F8B293B5786A5440BC0743B7B7753CF66FBA498B7E083BC267597238DC031B9BB131F997D9B8164AAED0D6E328420E53E1969DA6CD035078179677A7177BB2BF9C87CF592910CD380E8501B92040A39469C782BA383BEAE498C060FCC7C429BC10B7B6B7A0659C9BE03DC13DB46C638CF5E3B22A303726906DC8DD91C64501EBFC282A3A497EC430CACC066EE4BF9C5C8F2F2A05D0C1921A9E3E85E3 | |||
| (PID) Process: | (3332) PSO2 Tweaker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\CABD2A79A1076A31F21D253635CB039D4329A5E8 |
| Operation: | write | Name: | Blob |
Value: 1900000001000000100000002FE1F70BB05D7C92335BC5E05B984DA662000000010000002000000096BCEC06264976F37460779ACF28C5A7CFE8A3C0AAE11A8FFCEE05C0BDDF08C60B000000010000001A0000004900530052004700200052006F006F007400200058003100000014000000010000001400000079B459E67BB6E5E40173800888C81A58F6E99B6E1D000000010000001000000073B6876195F5D18E048510422AEF04E309000000010000000C000000300A06082B06010505070301030000000100000014000000CABD2A79A1076A31F21D253635CB039D4329A5E80F00000001000000200000003F0411EDE9C4477057D57E57883B1F205B20CDC0F3263129B1EE0269A2678F6320000000010000006F0500003082056B30820353A0030201020211008210CFB0D240E3594463E0BB63828B00300D06092A864886F70D01010B0500304F310B300906035504061302555331293027060355040A1320496E7465726E65742053656375726974792052657365617263682047726F7570311530130603550403130C4953524720526F6F74205831301E170D3135303630343131303433385A170D3335303630343131303433385A304F310B300906035504061302555331293027060355040A1320496E7465726E65742053656375726974792052657365617263682047726F7570311530130603550403130C4953524720526F6F7420583130820222300D06092A864886F70D01010105000382020F003082020A0282020100ADE82473F41437F39B9E2B57281C87BEDCB7DF38908C6E3CE657A078F775C2A2FEF56A6EF6004F28DBDE68866C4493B6B163FD14126BBF1FD2EA319B217ED1333CBA48F5DD79DFB3B8FF12F1219A4BC18A8671694A66666C8F7E3C70BFAD292206F3E4C0E680AEE24B8FB7997E94039FD347977C99482353E838AE4F0A6F832ED149578C8074B6DA2FD0388D7B0370211B75F2303CFA8FAEDDDA63ABEB164FC28E114B7ECF0BE8FFB5772EF4B27B4AE04C12250C708D0329A0E15324EC13D9EE19BF10B34A8C3F89A36151DEAC870794F46371EC2EE26F5B9881E1895C34796C76EF3B906279E6DBA49A2F26C5D010E10EDED9108E16FBB7F7A8F7C7E50207988F360895E7E237960D36759EFB0E72B11D9BBC03F94905D881DD05B42AD641E9AC0176950A0FD8DFD5BD121F352F28176CD298C1A80964776E4737BACEAC595E689D7F72D689C50641293E593EDD26F524C911A75AA34C401F46A199B5A73A516E863B9E7D72A712057859ED3E5178150B038F8DD02F05B23E7B4A1C4B730512FCC6EAE050137C439374B3CA74E78E1F0108D030D45B7136B407BAC130305C48B7823B98A67D608AA2A32982CCBABD83041BA2830341A1D605F11BC2B6F0A87C863B46A8482A88DC769A76BF1F6AA53D198FEB38F364DEC82B0D0A28FFF7DBE21542D422D0275DE179FE18E77088AD4EE6D98B3AC6DD27516EFFBC64F533434F0203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E0416041479B459E67BB6E5E40173800888C81A58F6E99B6E300D06092A864886F70D01010B05000382020100551F58A9BCB2A850D00CB1D81A6920272908AC61755C8A6EF882E5692FD5F6564BB9B8731059D321977EE74C71FBB2D260AD39A80BEA17215685F1500E59EBCEE059E9BAC915EF869D8F8480F6E4E99190DC179B621B45F06695D27C6FC2EA3BEF1FCFCBD6AE27F1A9B0C8AEFD7D7E9AFA2204EBFFD97FEA912B22B1170E8FF28A345B58D8FC01C954B9B826CC8A8833894C2D843C82DFEE965705BA2CBBF7C4B7C74E3B82BE31C822737392D1C280A43939103323824C3C9F86B255981DBE29868C229B9EE26B3B573A82704DDC09C789CB0A074D6CE85D8EC9EFCEABC7BBB52B4E45D64AD026CCE572CA086AA595E315A1F7A4EDC92C5FA5FBFFAC28022EBED77BBBE3717B9016D3075E46537C3707428CD3C4969CD599B52AE0951A8048AE4C3907CECC47A452952BBAB8FBADD233537DE51D4D6DD5A1B1C7426FE64027355CA328B7078DE78D3390E7239FFB509C796C46D5B415B3966E7E9B0C963AB8522D3FD65BE1FB08C284FE24A8A389DAAC6AE1182AB1A843615BD31FDC3B8D76F22DE88D75DF17336C3D53FB7BCB415FFFDCA2D06138E196B8AC5D8B37D775D533C09911AE9D41C1727584BE0241425F67244894D19B27BE073FB9B84F817451E17AB7ED9D23E2BEE0D52804133C31039EDD7A6C8FC60718C67FDE478E3F289E0406CFA5543477BDEC899BE91743DF5BDB5FFE8E1E57A2CD409D7E6222DADE1827 | |||
Executable files
13
Suspicious files
97
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\Local\Temp\Cab8368.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\Roaming\PSO2 Tweaker\settings.json | binary | |
MD5:EE152AD98B3D6944AE4BBD850DB48217 | SHA256:9D7E762E388357B3D623B7823DEF4846BF26939F23B195291C36EE165C288FD9 | |||
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:E80F90FCD124218590DC08197C50199B | SHA256:ADBF2A154EBD9AA8F0CC5B676ACF542101E8BDA923036D4A1AAFD88A13D42C9C | |||
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\Local\Temp\Tar8369.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:B0379907005B62D445A198AC009B6F2D | SHA256:CB29AA8A09EB49770EC94B8D01C6860BEE92EFEC49E22E4821CF2F0536171987 | |||
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:A36145503CA0F37B0823206F00401E88 | SHA256:E74B29D2FF549A5789F2253DA22F7310608A840DE3142AD0CBE25C29A173C05E | |||
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1B1495DD322A24490E2BF2FAABAE1C61 | binary | |
MD5:DEC6BBE308EB44937F77160A25EE32DB | SHA256:68A71DE28F488586C2B169F4652347E0A1FD632D48A6D6725393607BFA18BC7E | |||
| 3332 | PSO2 Tweaker.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\html5shiv.min[1].js | html | |
MD5:7B7A4E3A218061D489D18EDC20018200 | SHA256:DD09D170ACA1C1EB67A16F0E23FDA993989A3333A0C495080B4E83E8E270C3DD | |||
| 1072 | PSO2 Tweaker.exe | C:\Users\admin\AppData\Roaming\logfile.txt | text | |
MD5:CB492B7DF9B5C170D7C87527940EFF3B | SHA256:DBA5166AD9DB9BA648C1032EBBD34DCD0D085B50023B839EF5C68CA1DB93A563 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
20
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3332 | PSO2 Tweaker.exe | GET | 200 | 184.24.77.186:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f34bf006e77033a5 | unknown | compressed | 65.2 Kb | unknown |
3364 | dxwsetup.exe | GET | 302 | 2.18.160.223:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Jun2006_xact_x86.cab | unknown | — | — | unknown |
3364 | dxwsetup.exe | GET | 302 | 2.18.160.223:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Dec2006_d3dx10_00_x86.cab | unknown | — | — | unknown |
3364 | dxwsetup.exe | GET | 302 | 2.18.160.223:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Aug2006_xact_x86.cab | unknown | — | — | unknown |
3364 | dxwsetup.exe | GET | 302 | 2.18.160.223:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Oct2006_xact_x86.cab | unknown | — | — | unknown |
3364 | dxwsetup.exe | GET | 302 | 2.18.160.223:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Dec2006_xact_x86.cab | unknown | — | — | unknown |
3332 | PSO2 Tweaker.exe | GET | 200 | 23.192.153.142:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3332 | PSO2 Tweaker.exe | GET | 304 | 184.24.77.186:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d4c03b16ab765dba | unknown | compressed | 65.2 Kb | unknown |
3332 | PSO2 Tweaker.exe | GET | 200 | 23.192.153.142:80 | http://x2.c.lencr.org/ | unknown | binary | 300 b | unknown |
3332 | PSO2 Tweaker.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3332 | PSO2 Tweaker.exe | 104.21.16.63:443 | arks-layer.com | CLOUDFLARENET | — | unknown |
3332 | PSO2 Tweaker.exe | 184.24.77.186:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3332 | PSO2 Tweaker.exe | 149.56.22.24:443 | aida.moe | OVH SAS | CA | unknown |
3332 | PSO2 Tweaker.exe | 23.192.153.142:80 | x1.c.lencr.org | AKAMAI-AS | GB | unknown |
3332 | PSO2 Tweaker.exe | 172.217.16.202:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
3332 | PSO2 Tweaker.exe | 142.250.74.202:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3332 | PSO2 Tweaker.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
arks-layer.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
aida.moe |
| unknown |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
1 ETPRO signatures available at the full report