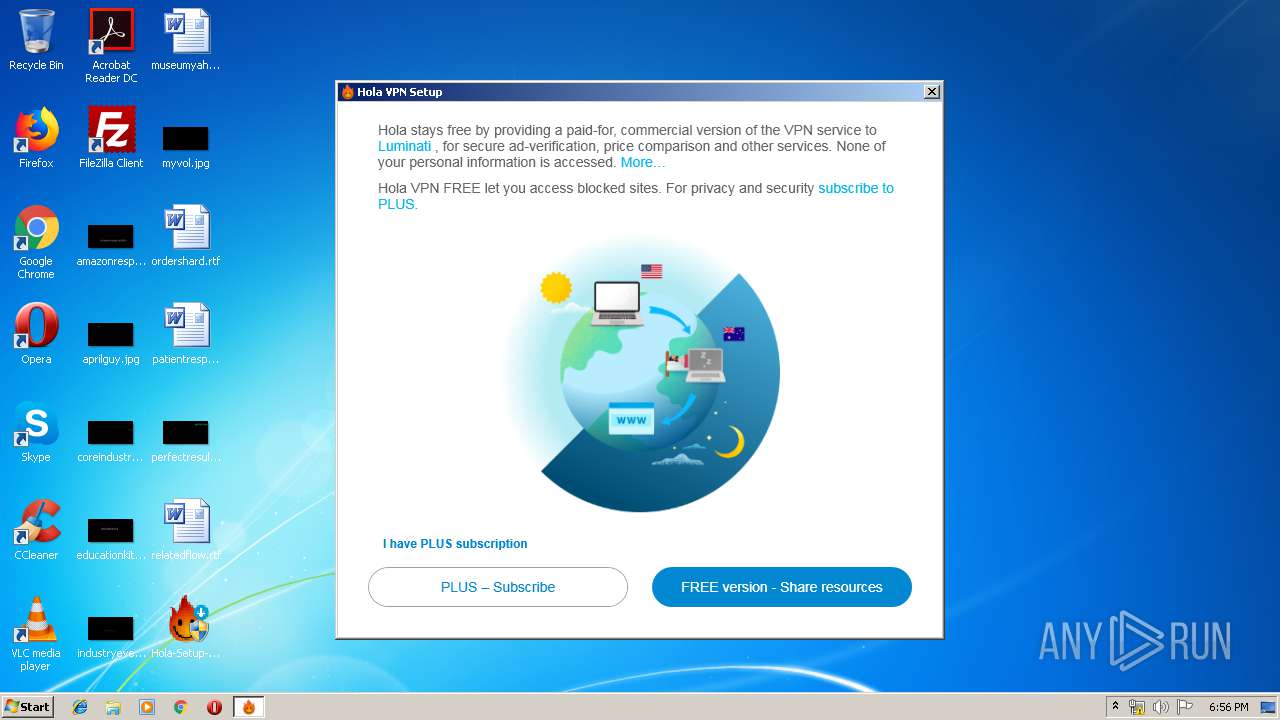
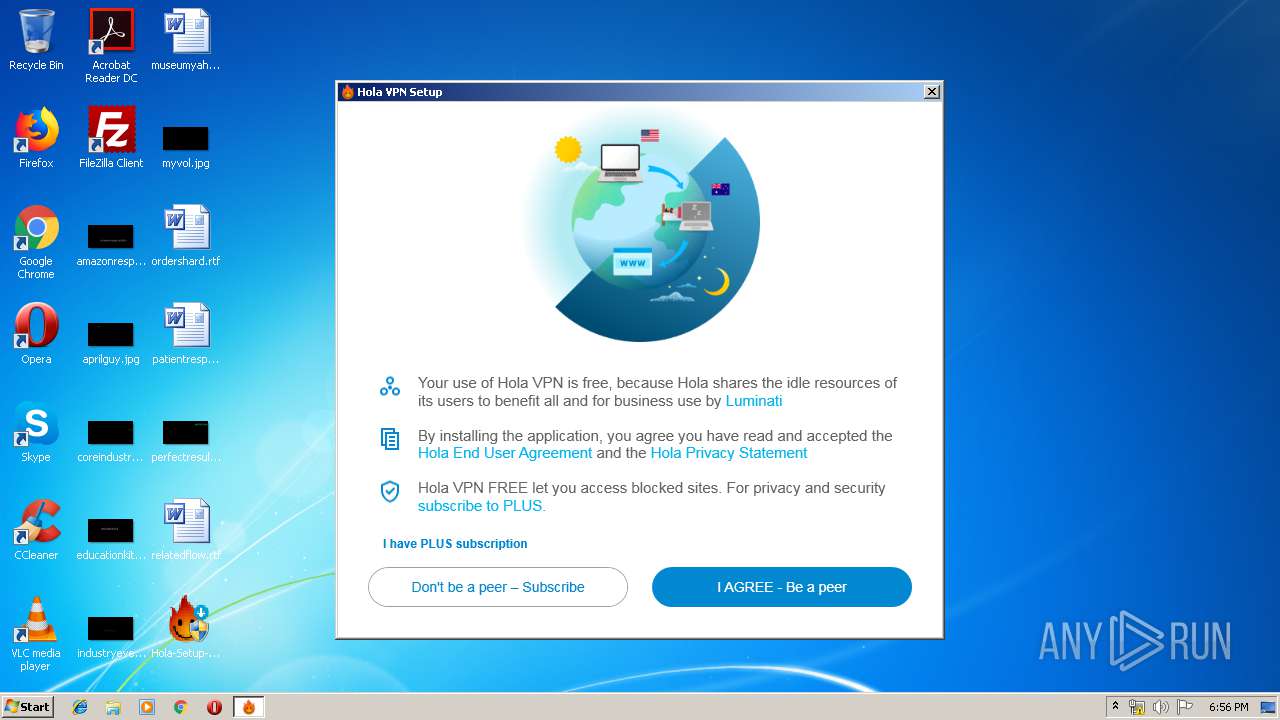
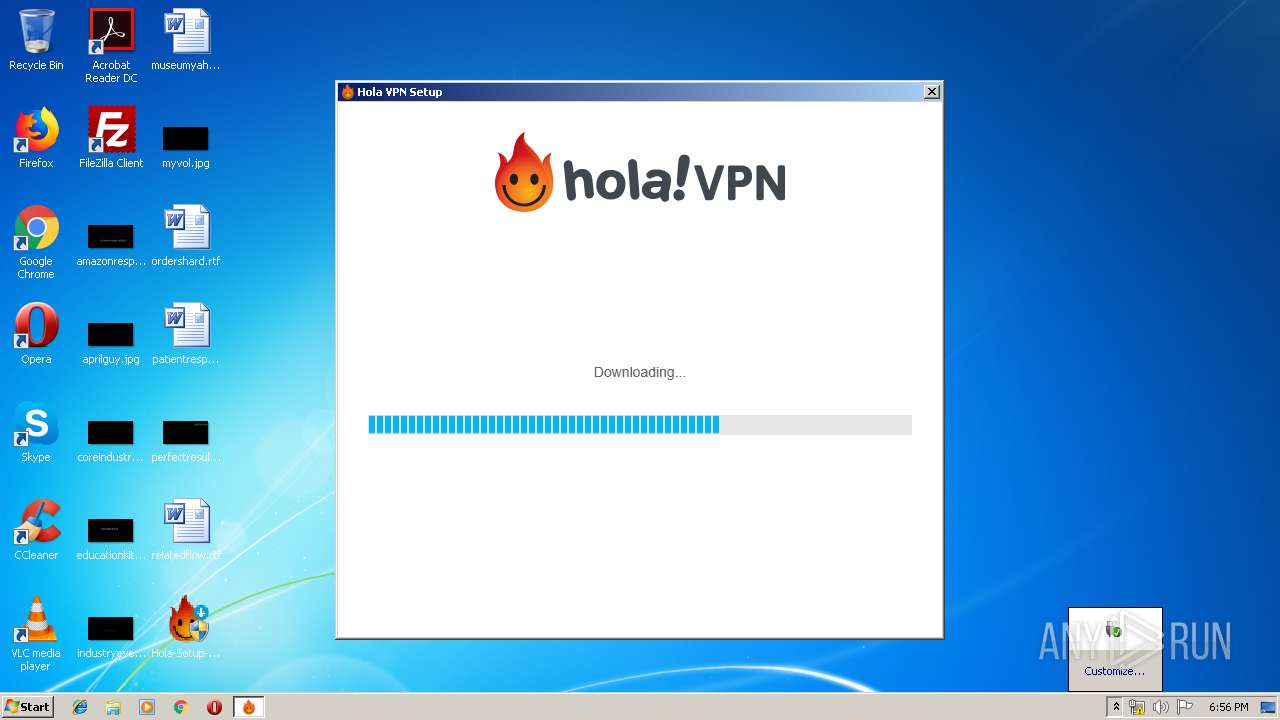
| download: | Hola-Setup-Agreed.exe |
| Full analysis: | https://app.any.run/tasks/b105f28f-c6ba-4795-a285-95fa86661118 |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2019, 17:54:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 3B286953EF91820665AEB4D7A44D7134 |
| SHA1: | DB0FE6115FEF13446C23D2879A90F11A87AAFCDB |
| SHA256: | C3E264504064EDD1CE7057C3D45D3959C605A2C7984285EA2BBDCEB1BF6A70AB |
| SSDEEP: | 12288:ns21lKazlmoSte0AvglAKVh0avxBCYjqhbSjWCpiBBybcQtW2e3zDS93OSO:nseKaQAYGKVOaLxjqVSjoWbZ3O2O |
MALICIOUS
Application was dropped or rewritten from another process
- Hola-Setup-Core.exe (PID: 2188)
- Hola-Setup-Core.exe (PID: 3460)
- Hola-Setup-1.151.979.exe (PID: 4032)
- Hola-Setup-1.151.979.exe (PID: 1816)
- Hola-Setup-1.151.979.exe (PID: 1856)
- 7za.exe (PID: 1260)
- hola.exe (PID: 2672)
- hola_updater.exe (PID: 3920)
- hola_svc.exe (PID: 1728)
- net_updater32.exe (PID: 1480)
- net_updater32.exe (PID: 3388)
- net_updater32.exe (PID: 3728)
- hola_cr.exe (PID: 2248)
- hola_cr.exe (PID: 4024)
- hola_cr.exe (PID: 2308)
- hola_cr.exe (PID: 3024)
- hola_cr.exe (PID: 2284)
- hola_cr.exe (PID: 3536)
- hola_cr.exe (PID: 2844)
- hola_cr.exe (PID: 2932)
- hola_cr.exe (PID: 296)
- hola_cr.exe (PID: 3228)
- hola_cr.exe (PID: 2364)
- hola_cr.exe (PID: 3416)
- hola_cr.exe (PID: 3524)
- hola_cr.exe (PID: 1736)
- hola_cr.exe (PID: 2744)
- hola_cr.exe (PID: 2324)
- hola_cr.exe (PID: 4000)
- hola_cr.exe (PID: 3212)
- hola_cr.exe (PID: 1132)
- hola_cr.exe (PID: 2616)
- hola_cr.exe (PID: 3004)
- hola_cr.exe (PID: 3772)
- hola_cr.exe (PID: 1524)
- hola_cr.exe (PID: 3844)
- hola_cr.exe (PID: 2952)
- hola_cr.exe (PID: 2764)
- hola_cr.exe (PID: 872)
- hola_cr.exe (PID: 4088)
- hola_cr.exe (PID: 3088)
- hola_cr.exe (PID: 3016)
- hola_cr.exe (PID: 3560)
- hola_cr.exe (PID: 2800)
- hola_cr.exe (PID: 3616)
- hola_cr.exe (PID: 2424)
- hola_cr.exe (PID: 2088)
- hola_cr.exe (PID: 3452)
- hola_cr.exe (PID: 3820)
- hola_cr.exe (PID: 3624)
- net_svc.exe (PID: 1628)
- hola_cr.exe (PID: 3720)
- test_wpf.exe (PID: 2556)
- hola_cr.exe (PID: 3376)
- net_svc.exe (PID: 2588)
- net_svc.exe (PID: 2568)
- hola_cr.exe (PID: 3628)
- hola_cr.exe (PID: 3784)
- hola_cr.exe (PID: 3780)
- hola_cr.exe (PID: 2964)
- hola_cr.exe (PID: 3912)
- net_svc.exe (PID: 3108)
Changes settings of System certificates
- Hola-Setup-Core.exe (PID: 2188)
- hola_cr.exe (PID: 2932)
Changes the autorun value in the registry
- Hola-Setup-1.151.979.exe (PID: 1816)
Loads dropped or rewritten executable
- net_updater32.exe (PID: 3728)
- net_updater32.exe (PID: 1480)
- net_updater32.exe (PID: 3388)
- hola_cr.exe (PID: 4024)
- hola_cr.exe (PID: 2308)
- hola_cr.exe (PID: 3024)
- hola_cr.exe (PID: 3536)
- hola_cr.exe (PID: 2932)
- hola_cr.exe (PID: 2248)
- hola_cr.exe (PID: 2284)
- hola_cr.exe (PID: 2844)
- hola_cr.exe (PID: 3228)
- hola_cr.exe (PID: 3628)
- hola_cr.exe (PID: 3524)
- hola_cr.exe (PID: 296)
- hola_cr.exe (PID: 3416)
- hola_cr.exe (PID: 3004)
- hola_cr.exe (PID: 2364)
- hola_cr.exe (PID: 1736)
- hola_cr.exe (PID: 2744)
- hola_cr.exe (PID: 3772)
- hola_cr.exe (PID: 2324)
- hola_cr.exe (PID: 4000)
- hola_cr.exe (PID: 3212)
- hola_cr.exe (PID: 1132)
- hola_cr.exe (PID: 1524)
- hola_cr.exe (PID: 872)
- hola_cr.exe (PID: 3844)
- hola_cr.exe (PID: 2764)
- hola_cr.exe (PID: 2616)
- hola_cr.exe (PID: 2952)
- hola_cr.exe (PID: 4088)
- hola_cr.exe (PID: 3560)
- hola_cr.exe (PID: 2800)
- hola_cr.exe (PID: 3616)
- hola_cr.exe (PID: 2424)
- hola_cr.exe (PID: 3088)
- hola_cr.exe (PID: 3016)
- hola_cr.exe (PID: 3820)
- hola_cr.exe (PID: 3624)
- hola_cr.exe (PID: 3720)
- hola_cr.exe (PID: 3452)
- hola_cr.exe (PID: 3376)
- hola_cr.exe (PID: 2088)
- hola_cr.exe (PID: 2964)
- hola_cr.exe (PID: 3780)
- hola_cr.exe (PID: 3784)
- hola_cr.exe (PID: 3912)
SUSPICIOUS
Executable content was dropped or overwritten
- Hola-Setup-Agreed.exe (PID: 3440)
- Hola-Setup-Core.exe (PID: 2188)
- Hola-Setup-1.151.979.exe (PID: 4032)
- Hola-Setup-1.151.979.exe (PID: 1816)
- Hola-Setup-1.151.979.exe (PID: 1856)
- net_updater32.exe (PID: 3728)
- 7za.exe (PID: 1260)
Application launched itself
- Hola-Setup-Core.exe (PID: 2188)
- hola_cr.exe (PID: 2248)
- net_svc.exe (PID: 2568)
Adds / modifies Windows certificates
- Hola-Setup-Core.exe (PID: 2188)
- hola_cr.exe (PID: 2932)
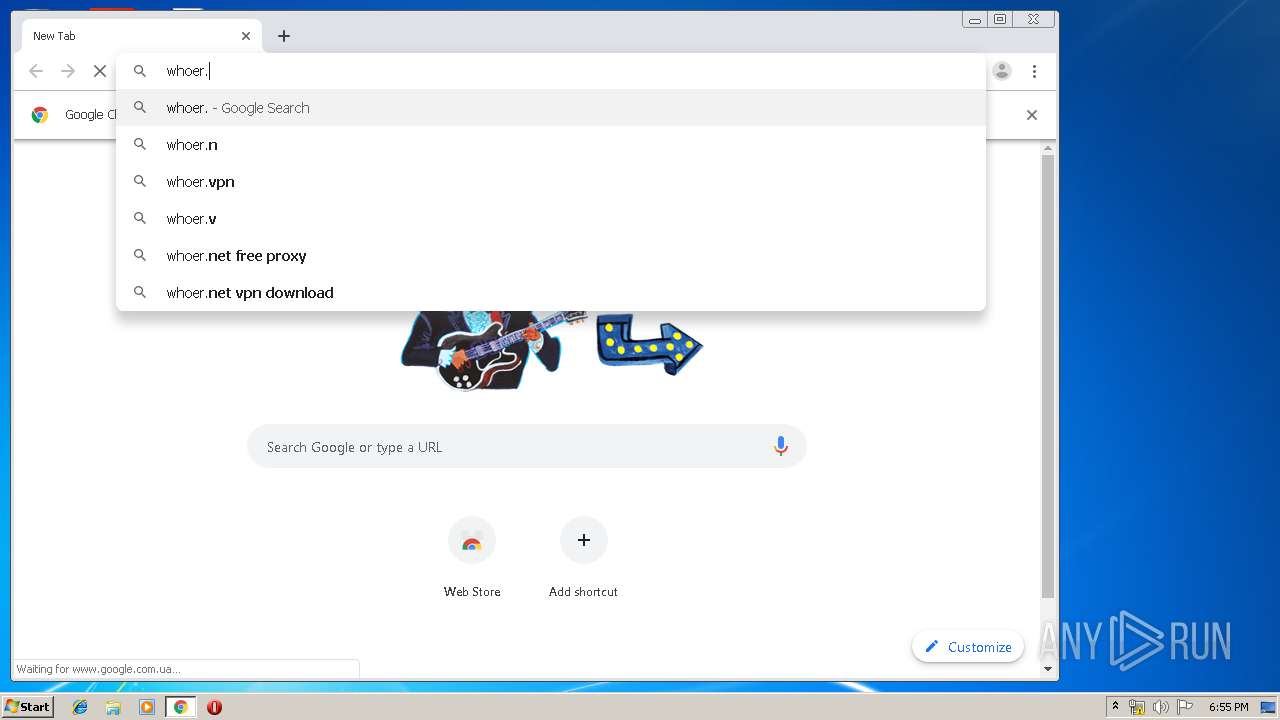
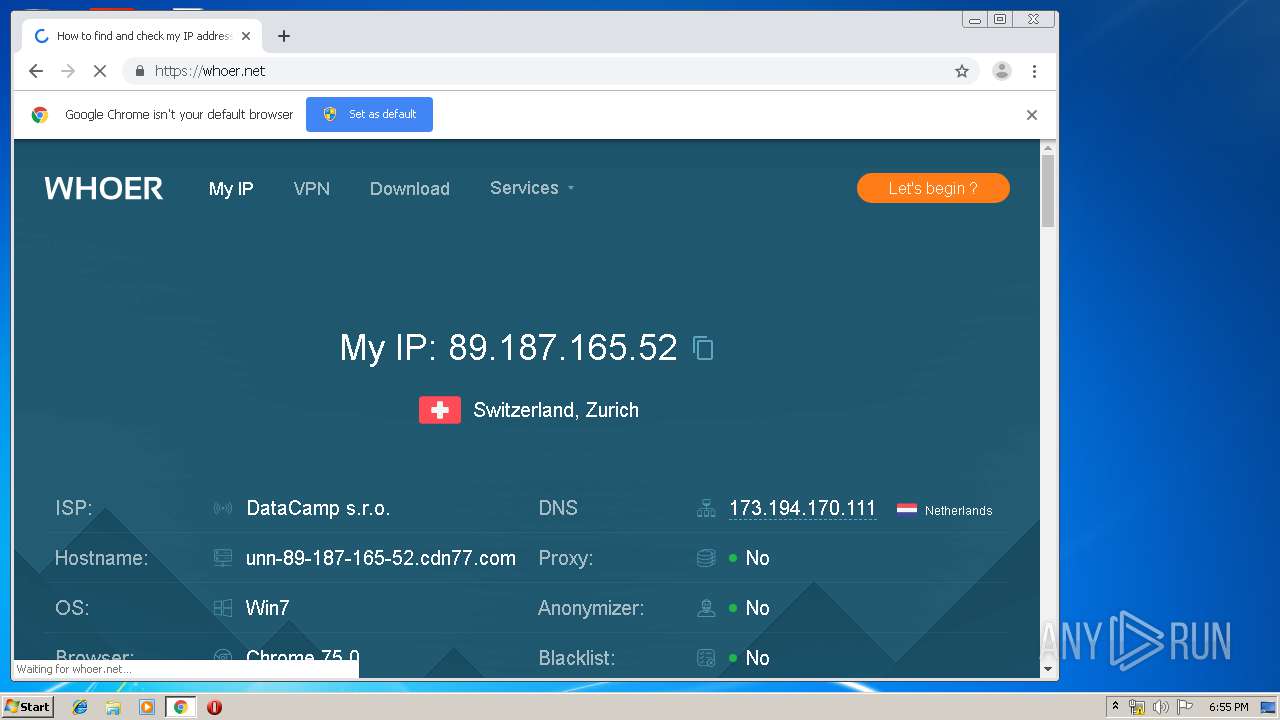
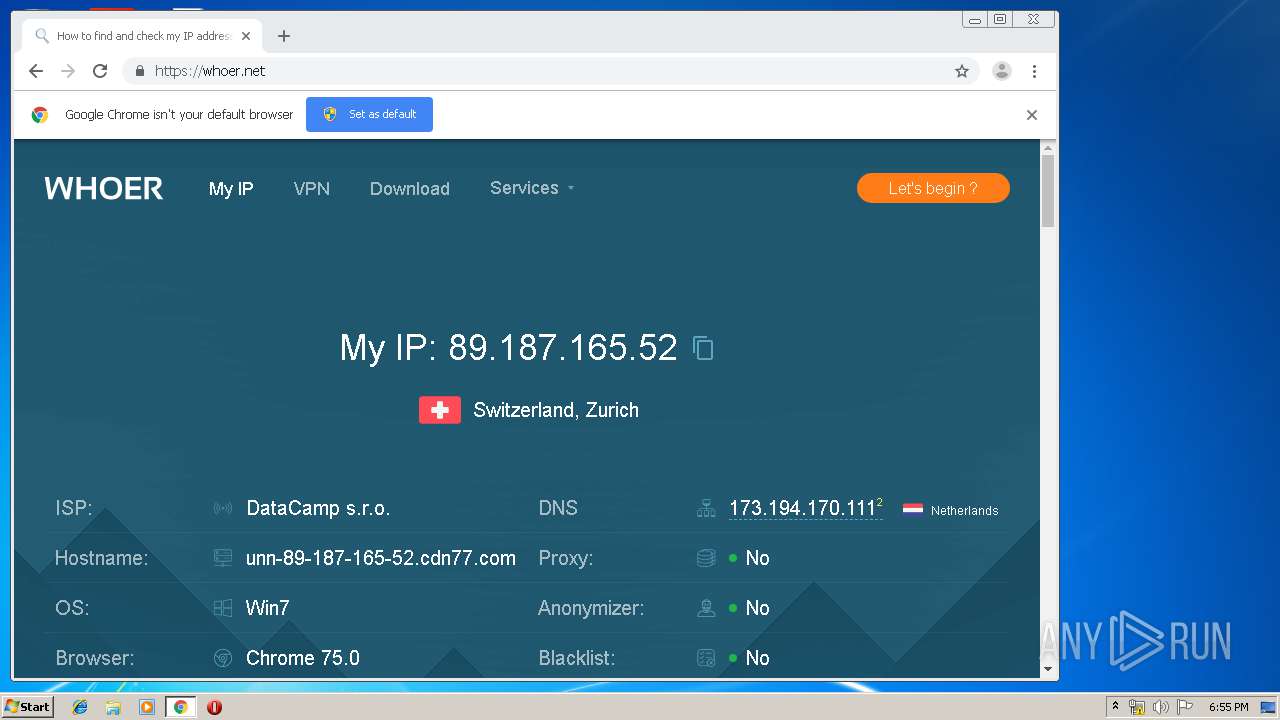
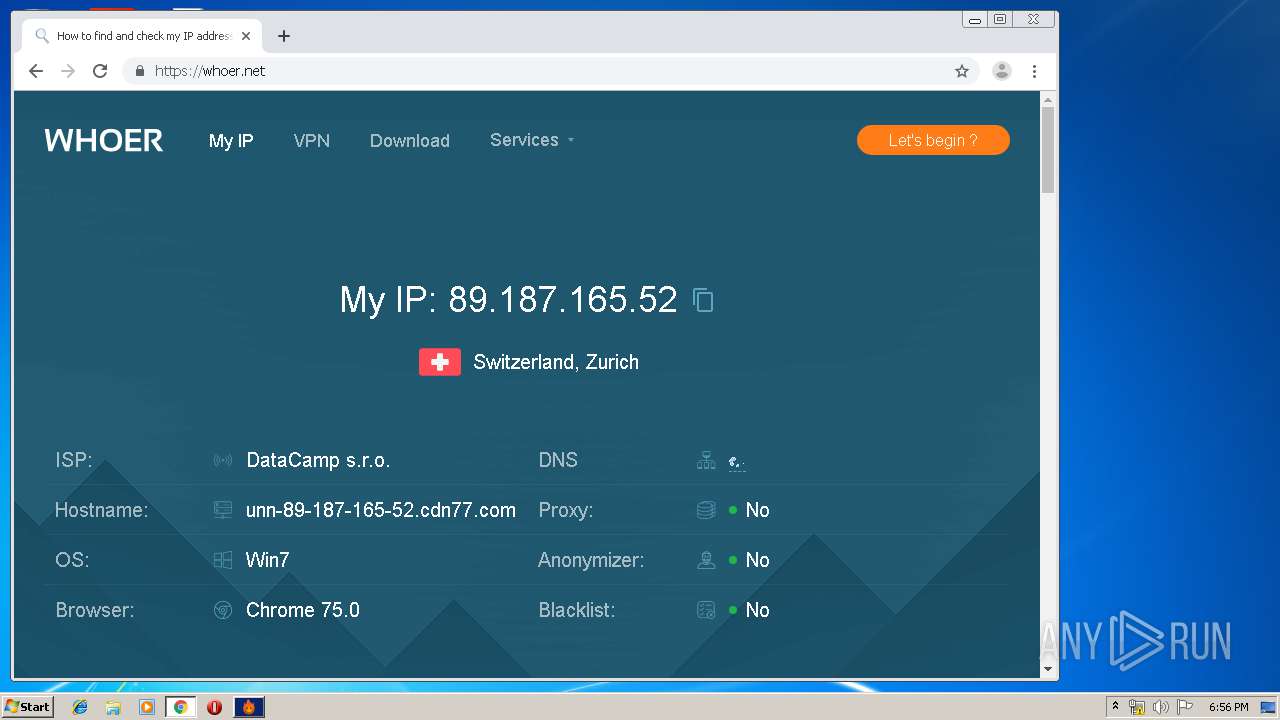
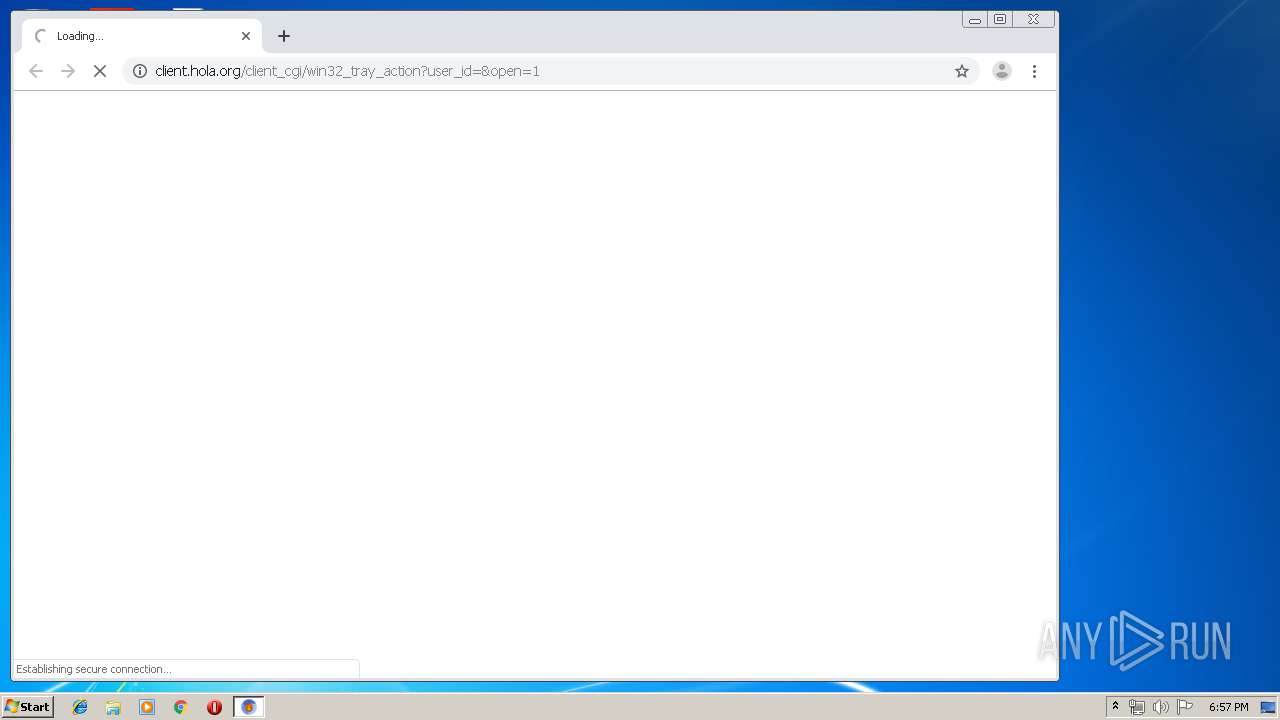
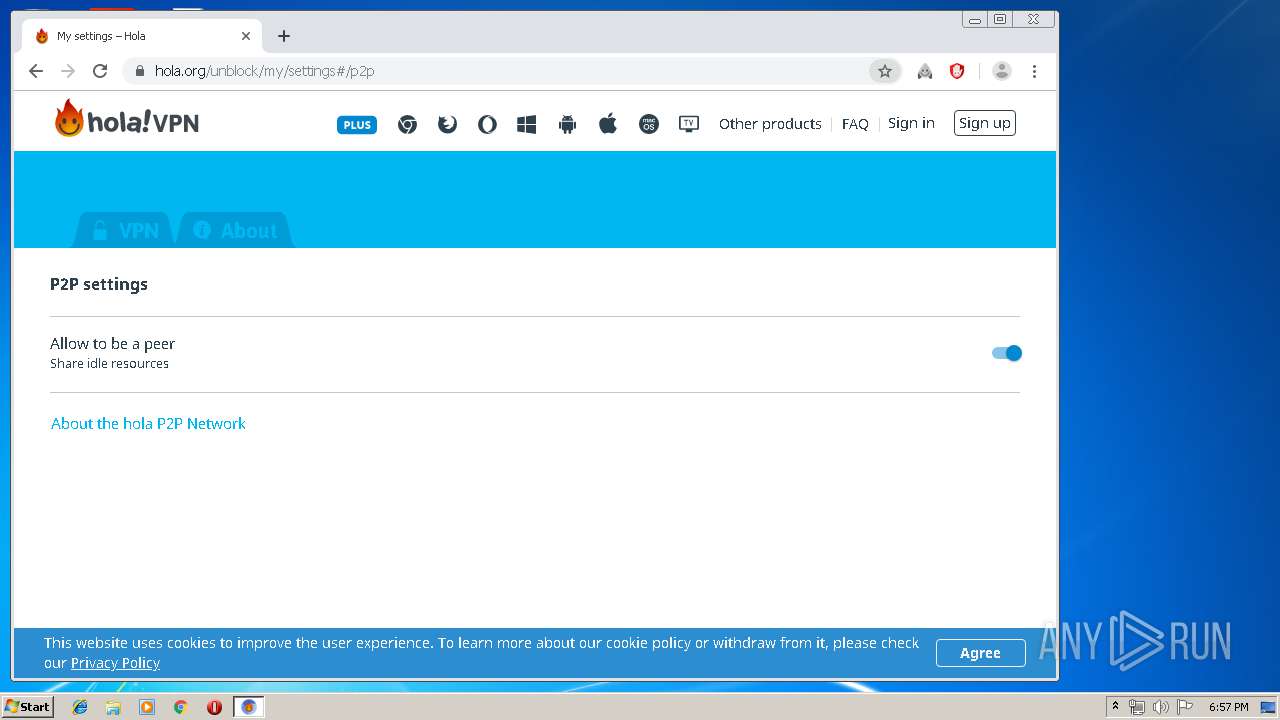
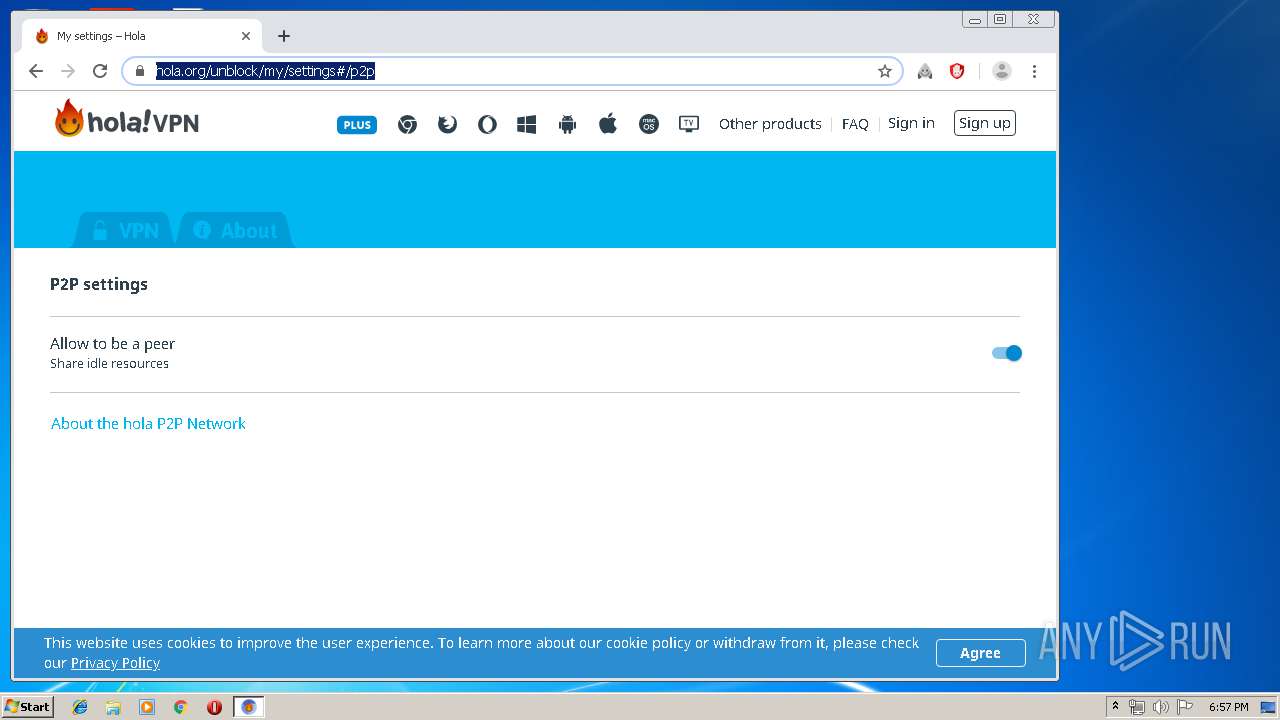
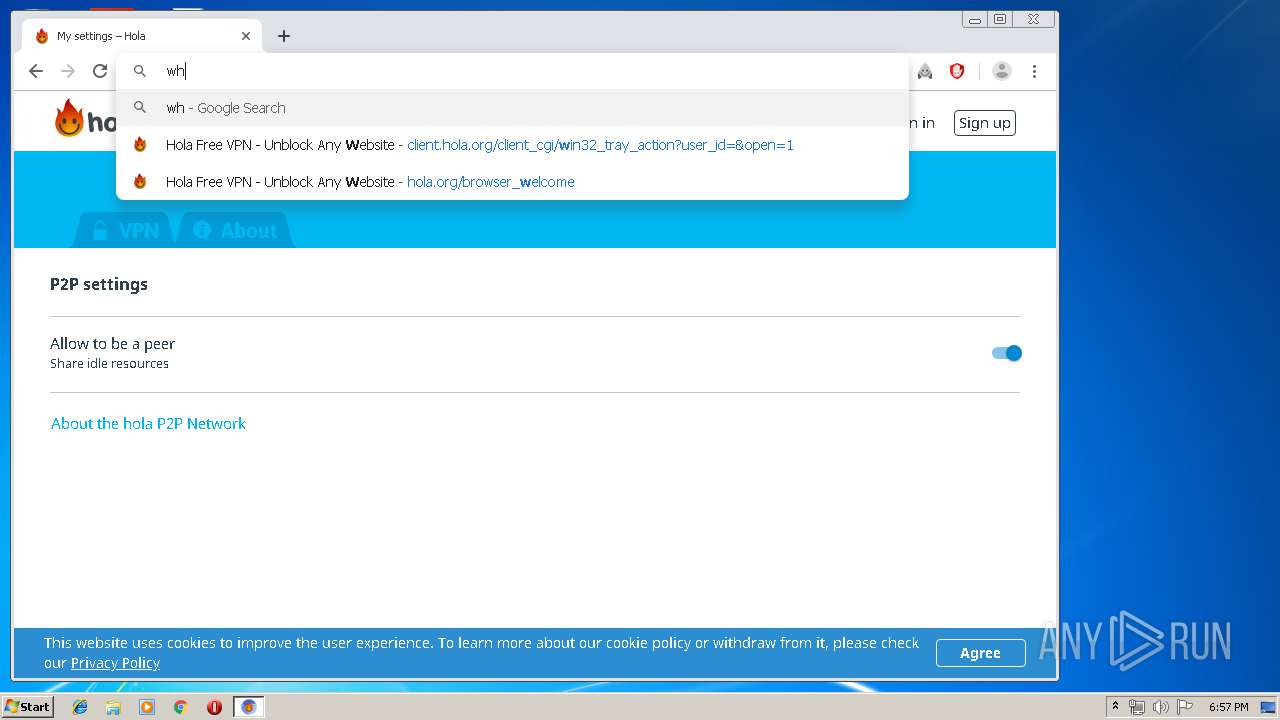
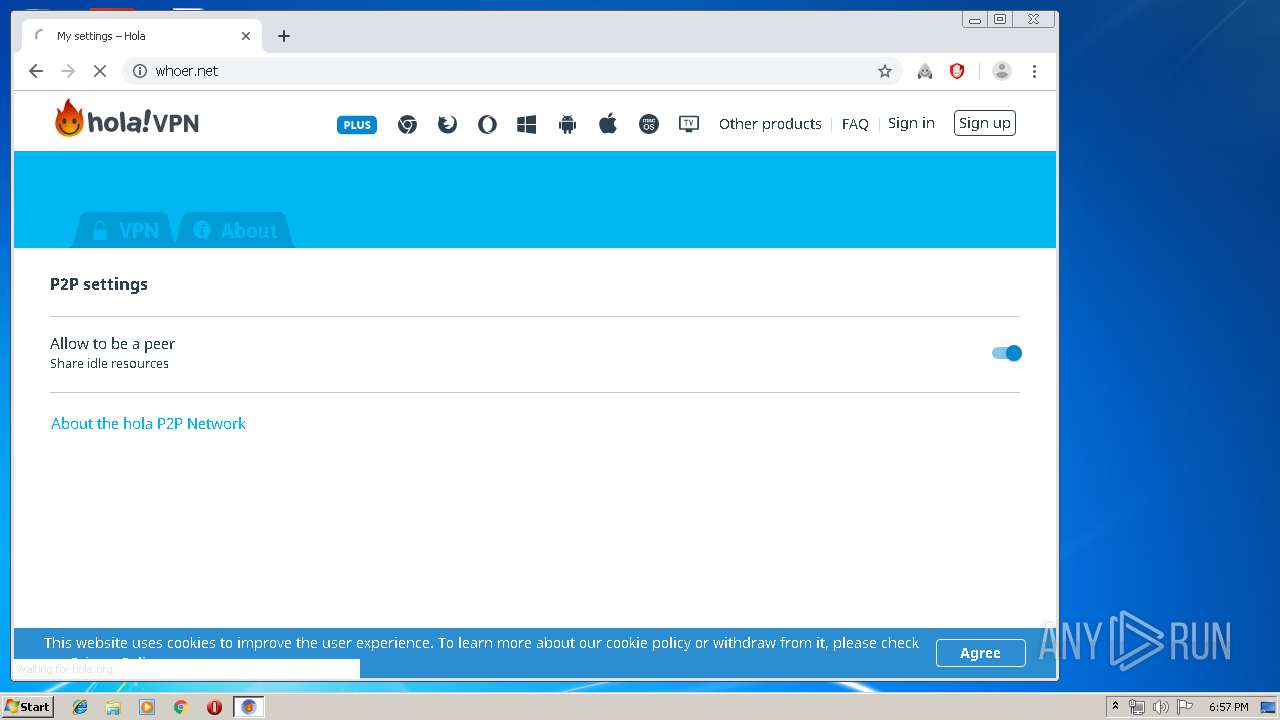
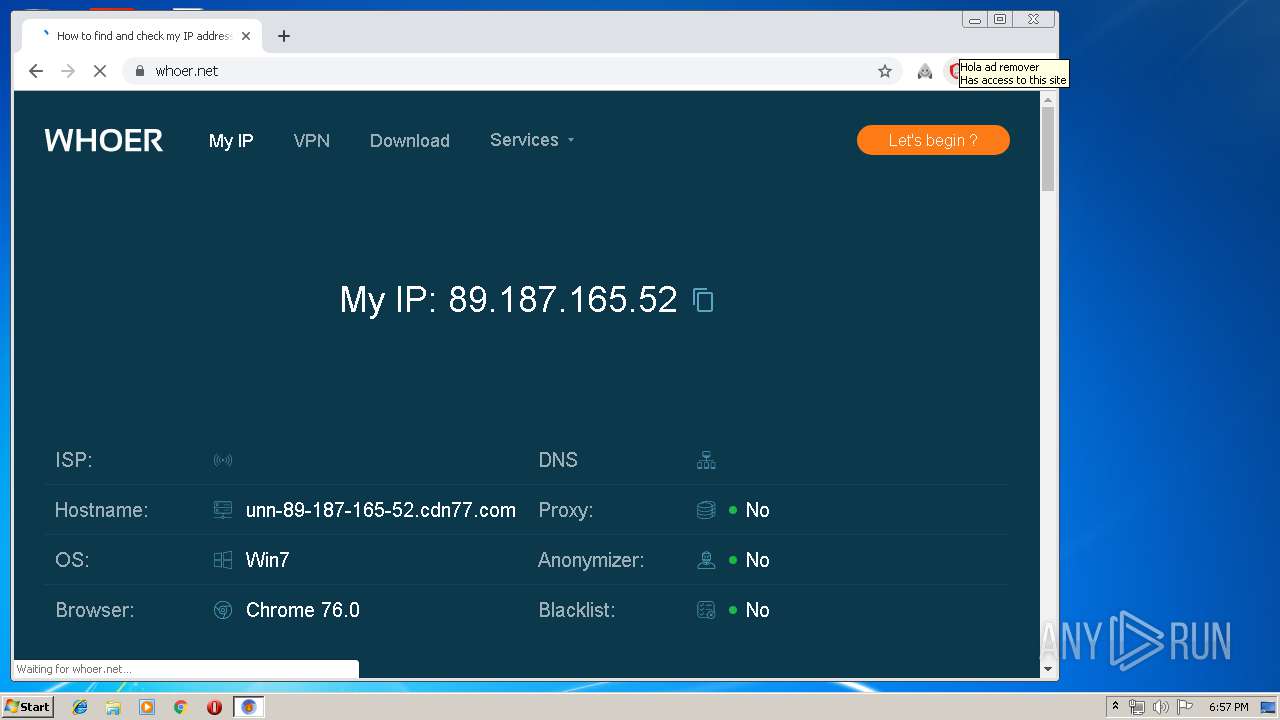
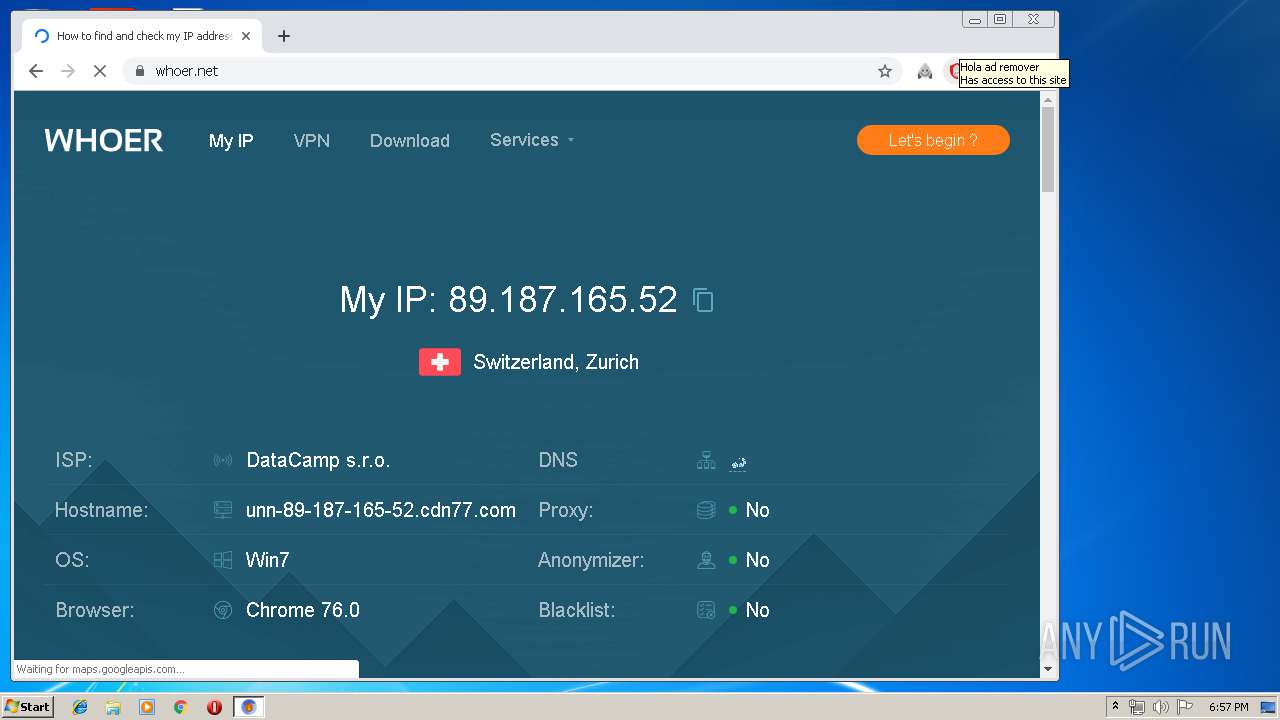
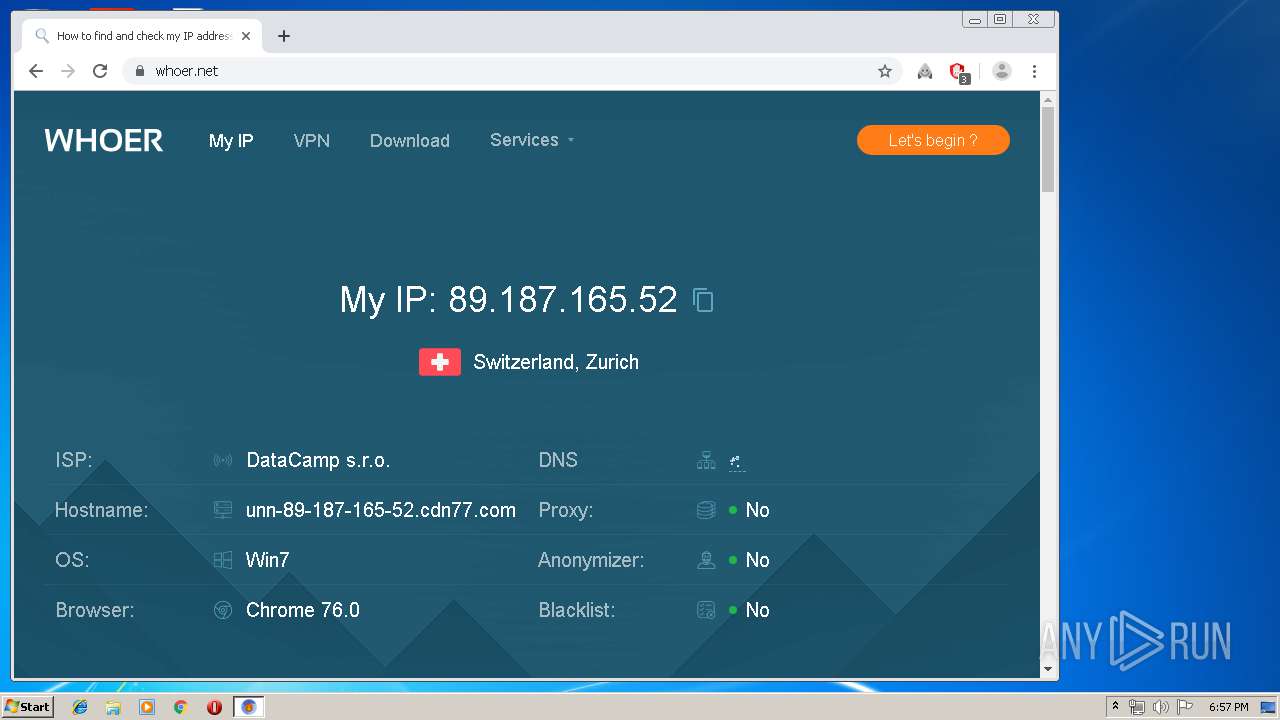
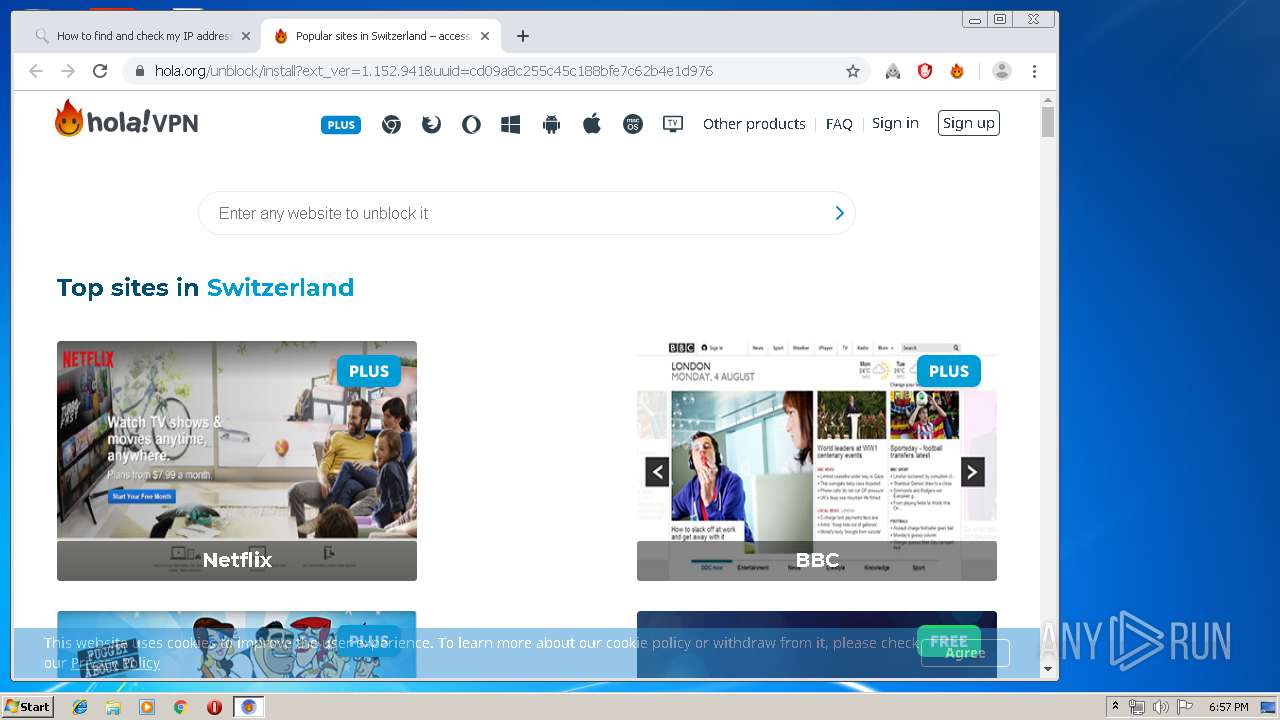
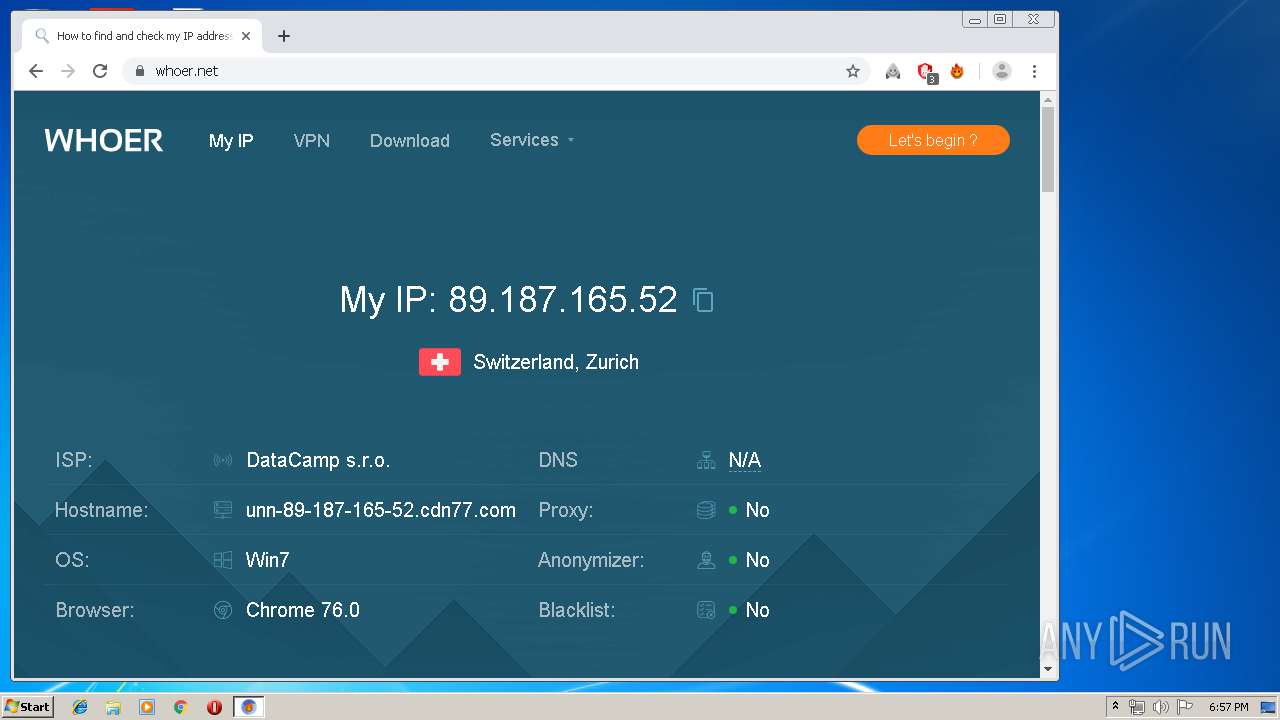
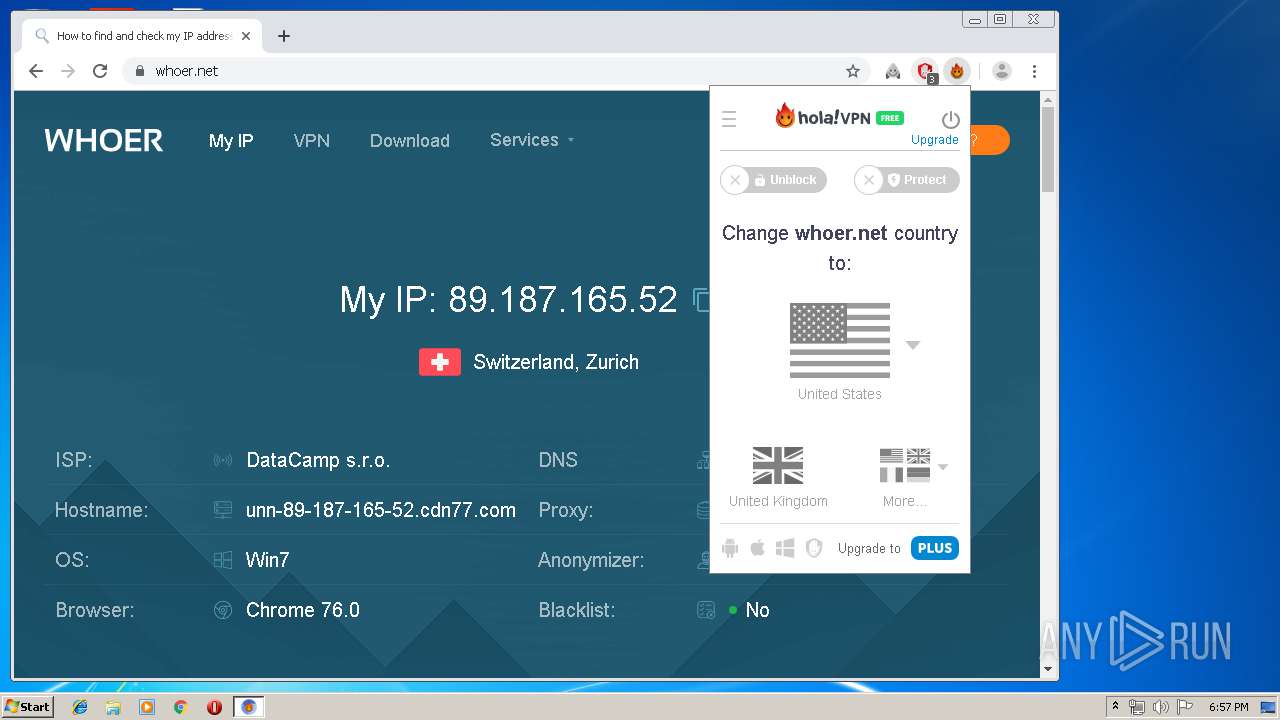
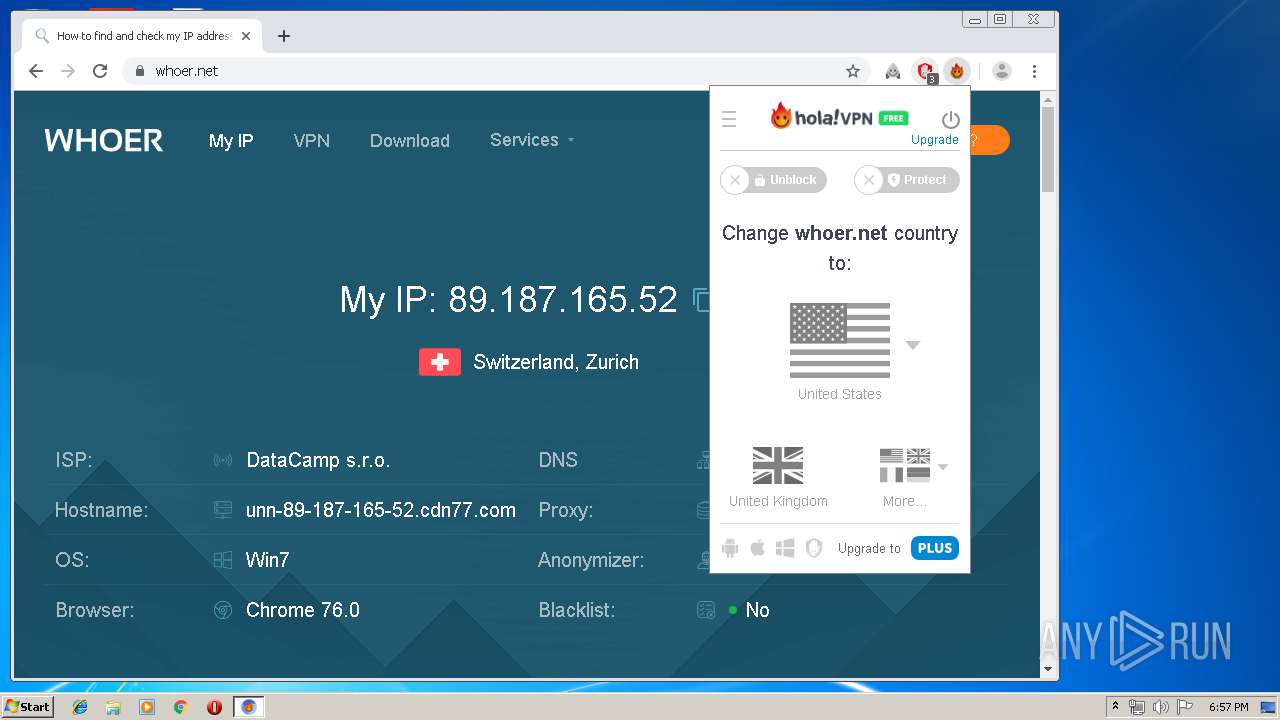
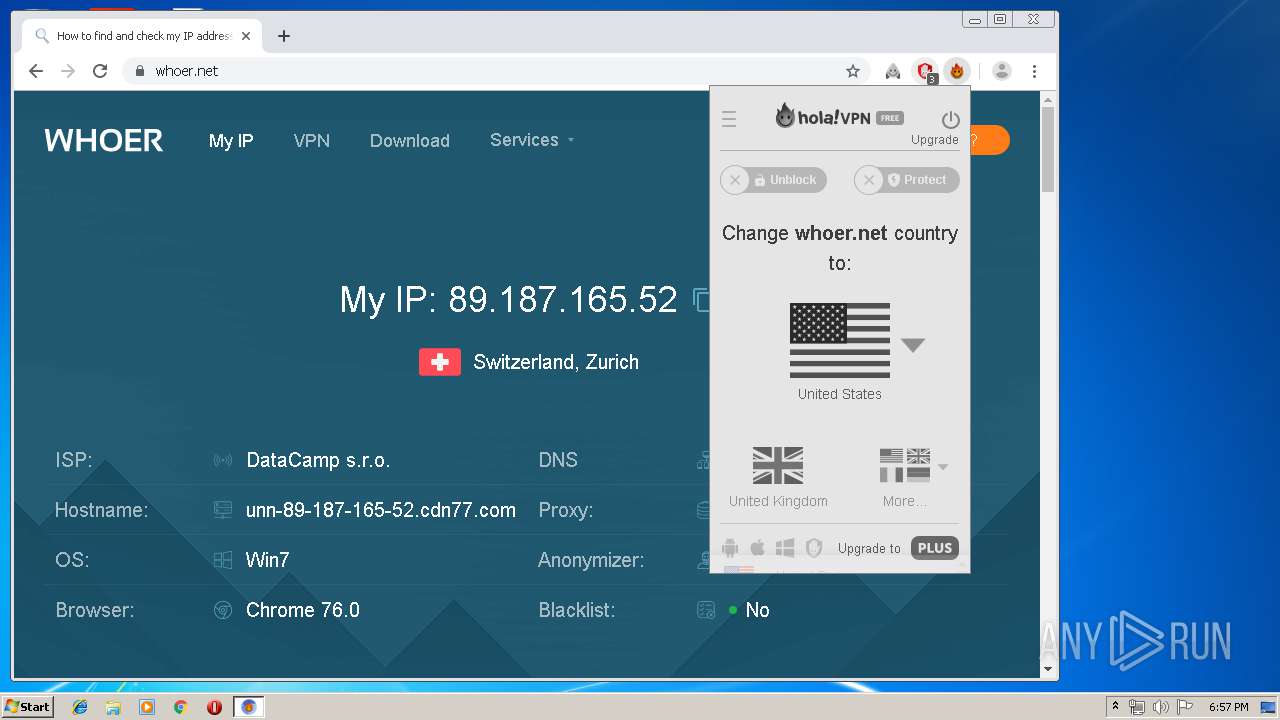
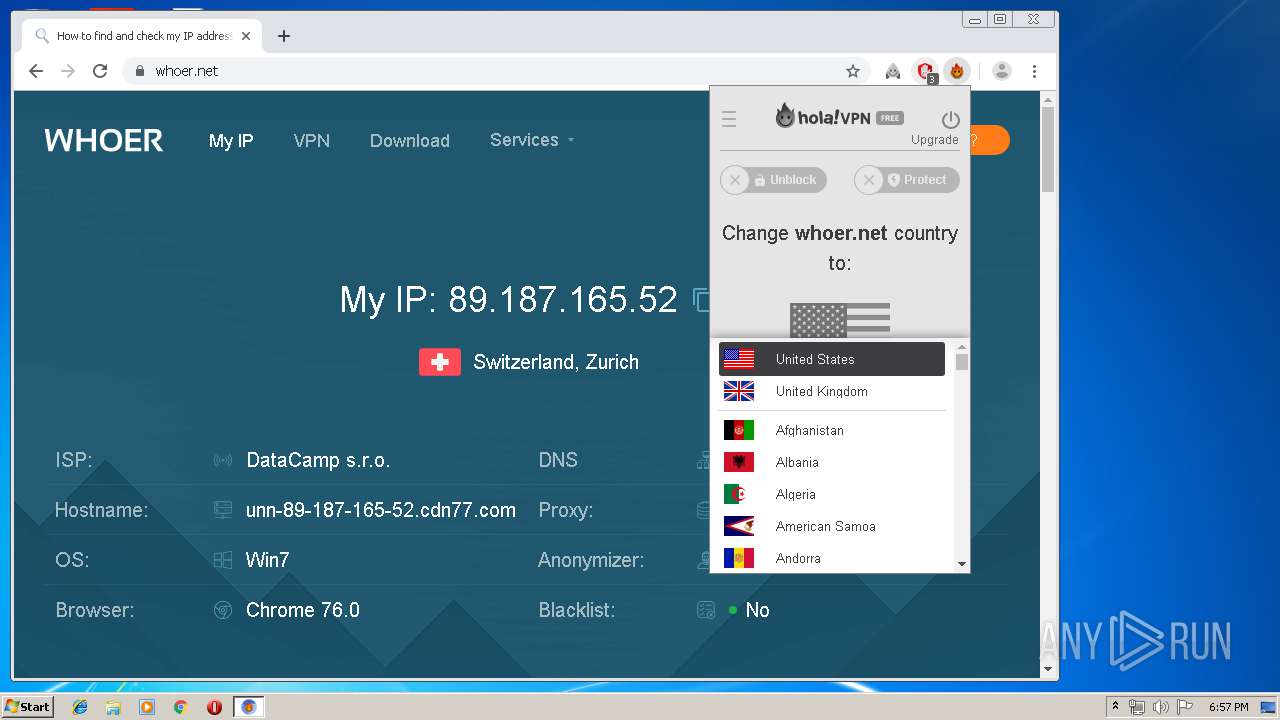
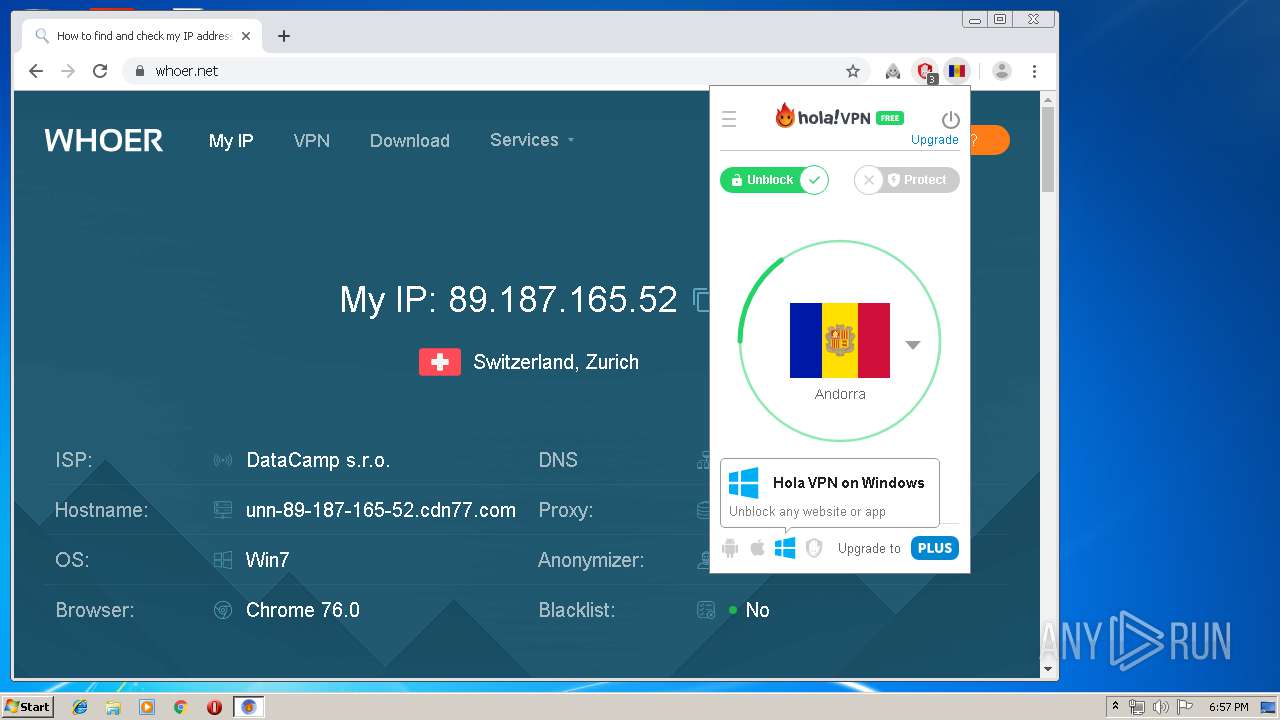
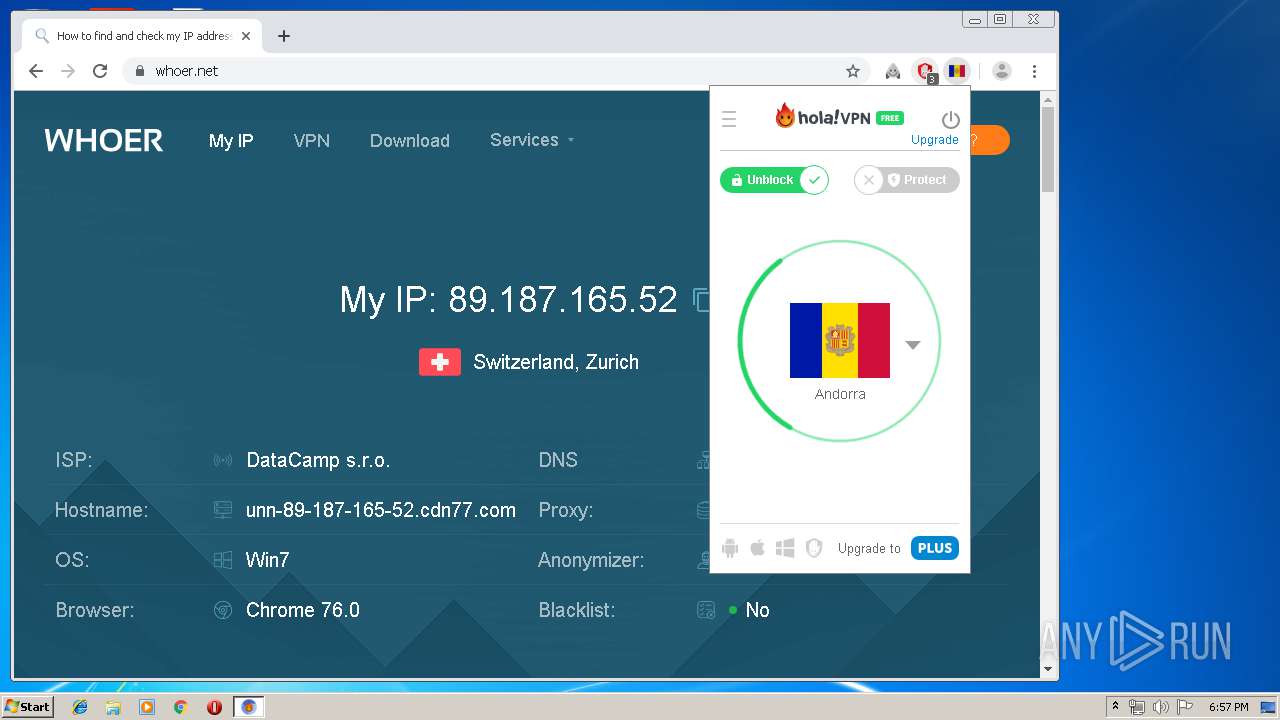
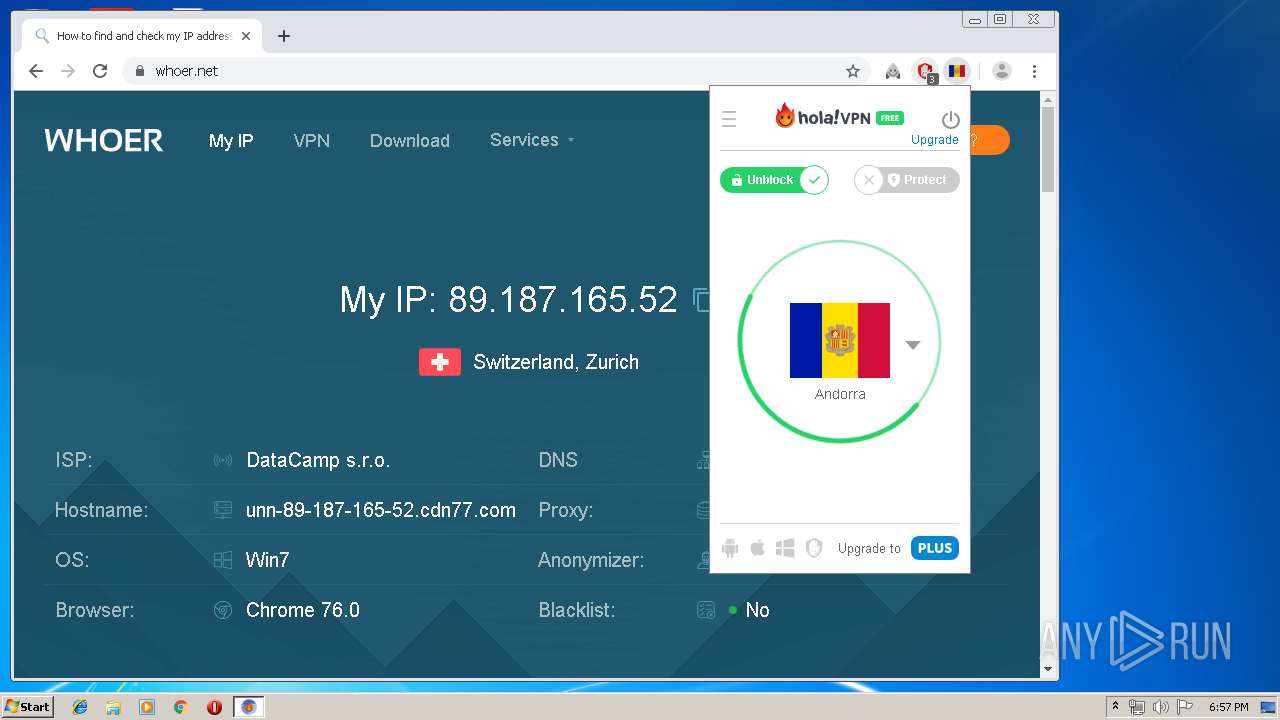
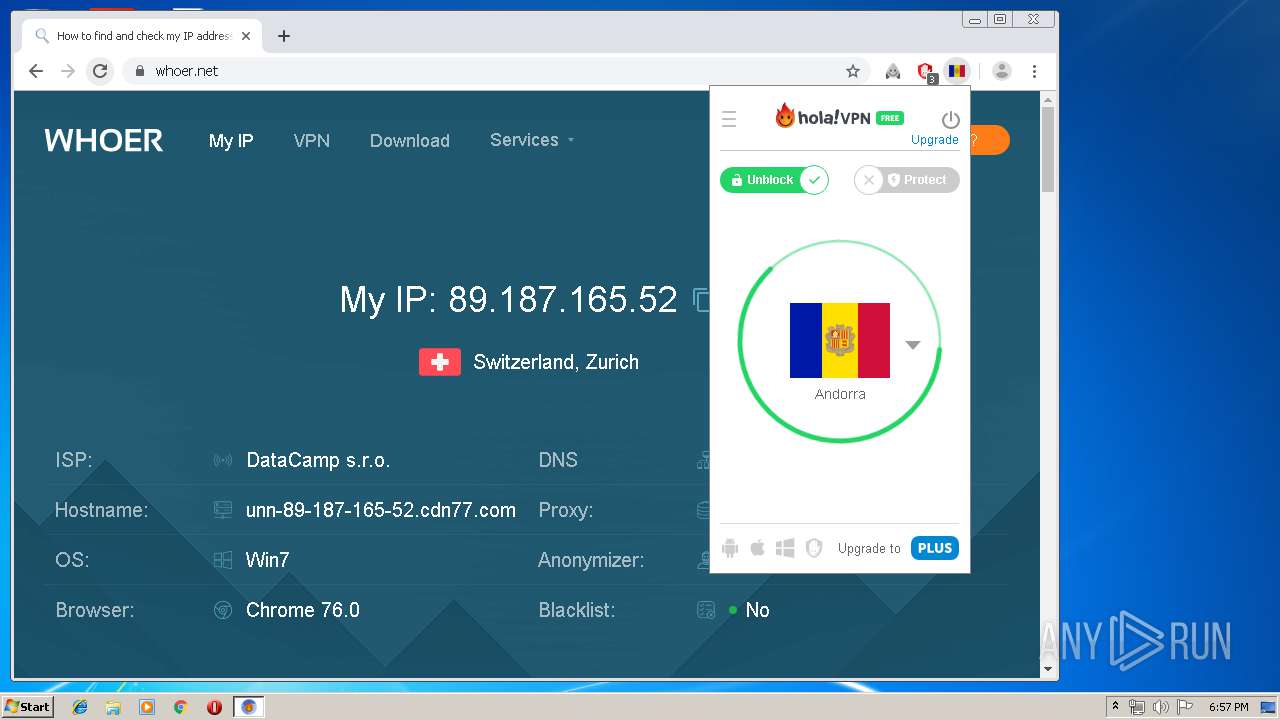
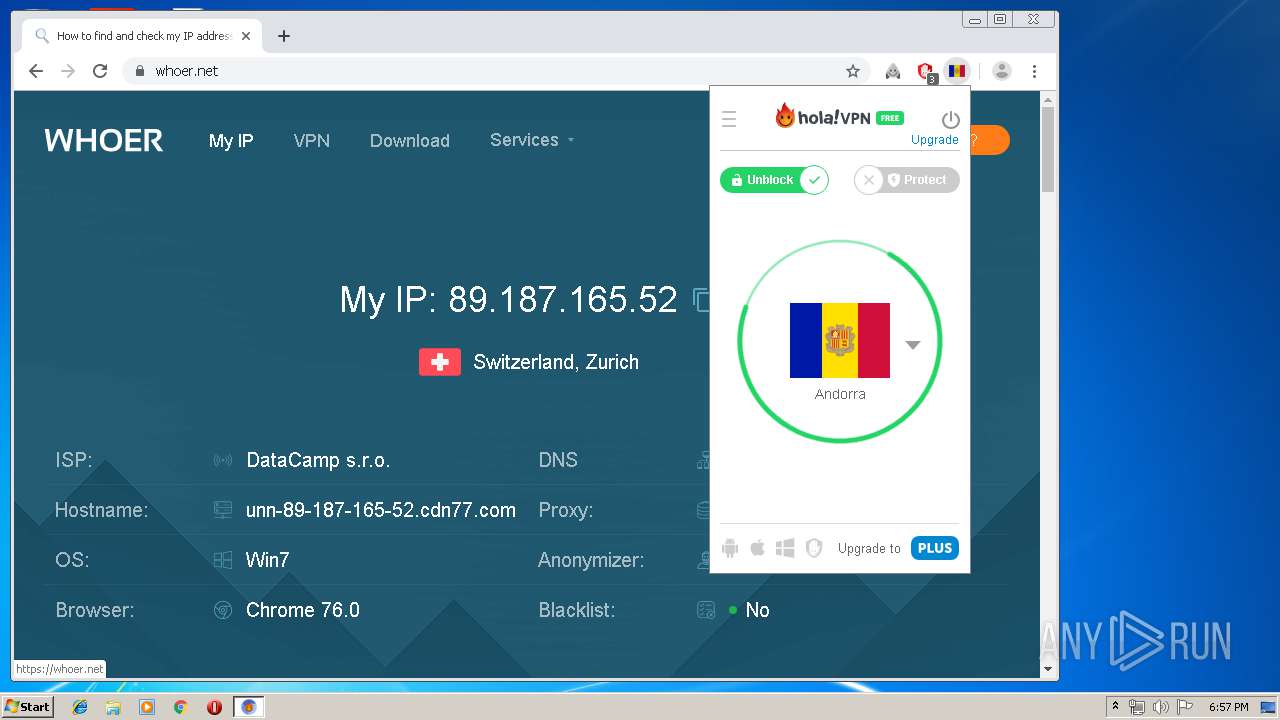
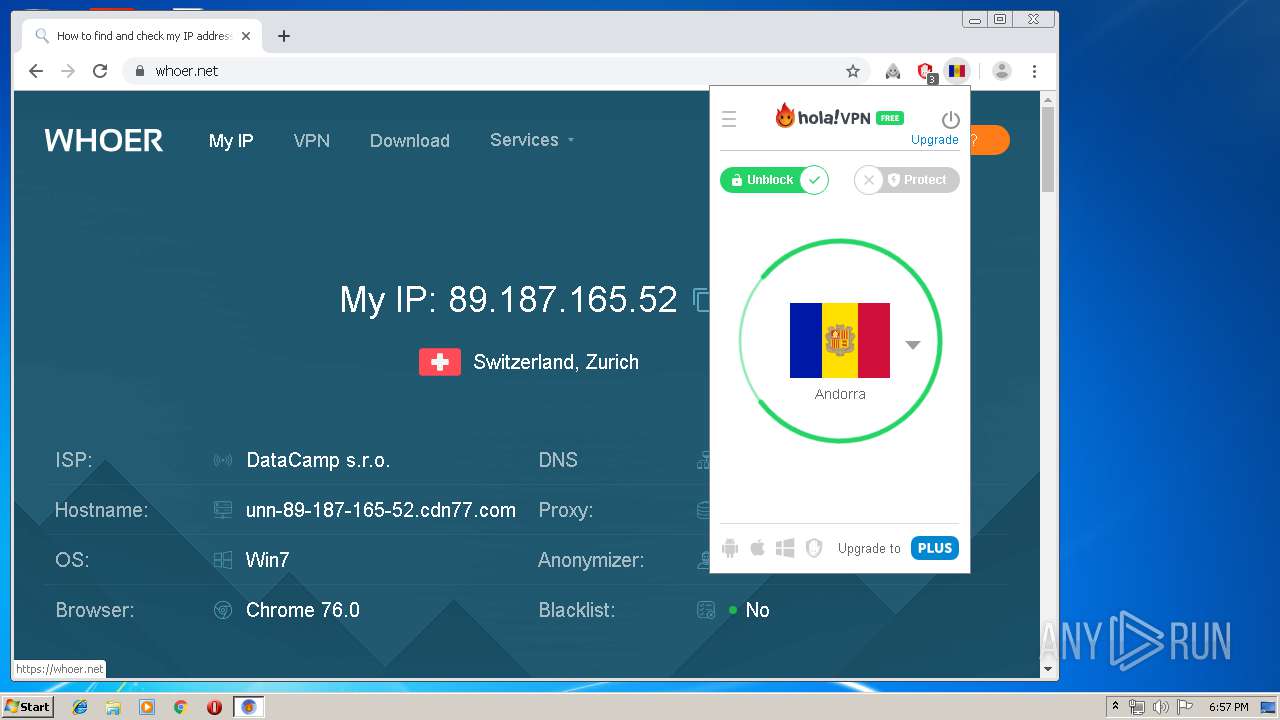
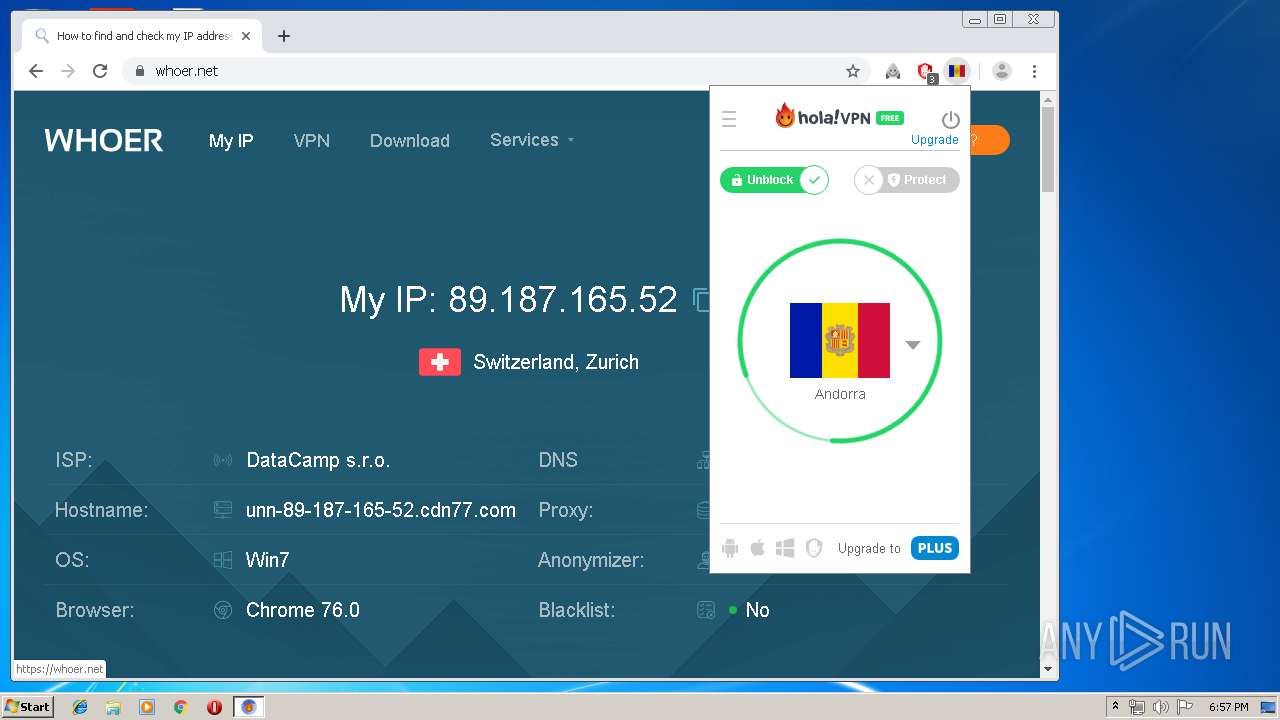
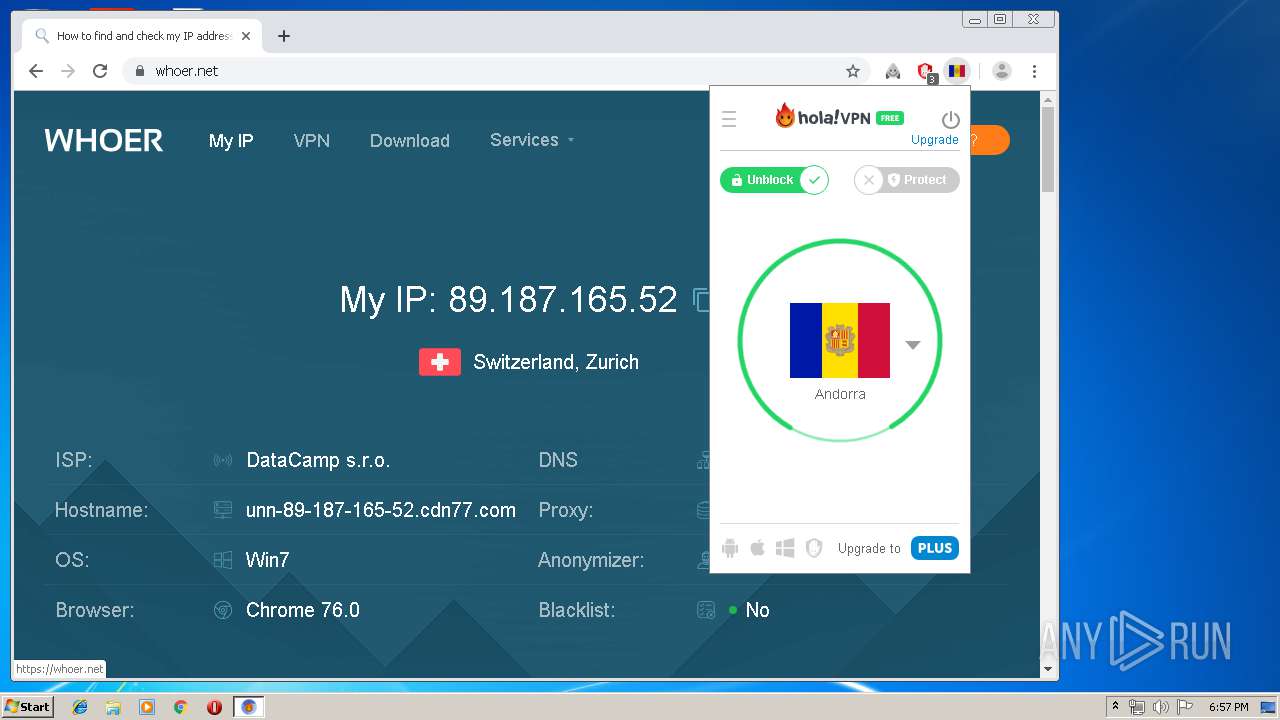
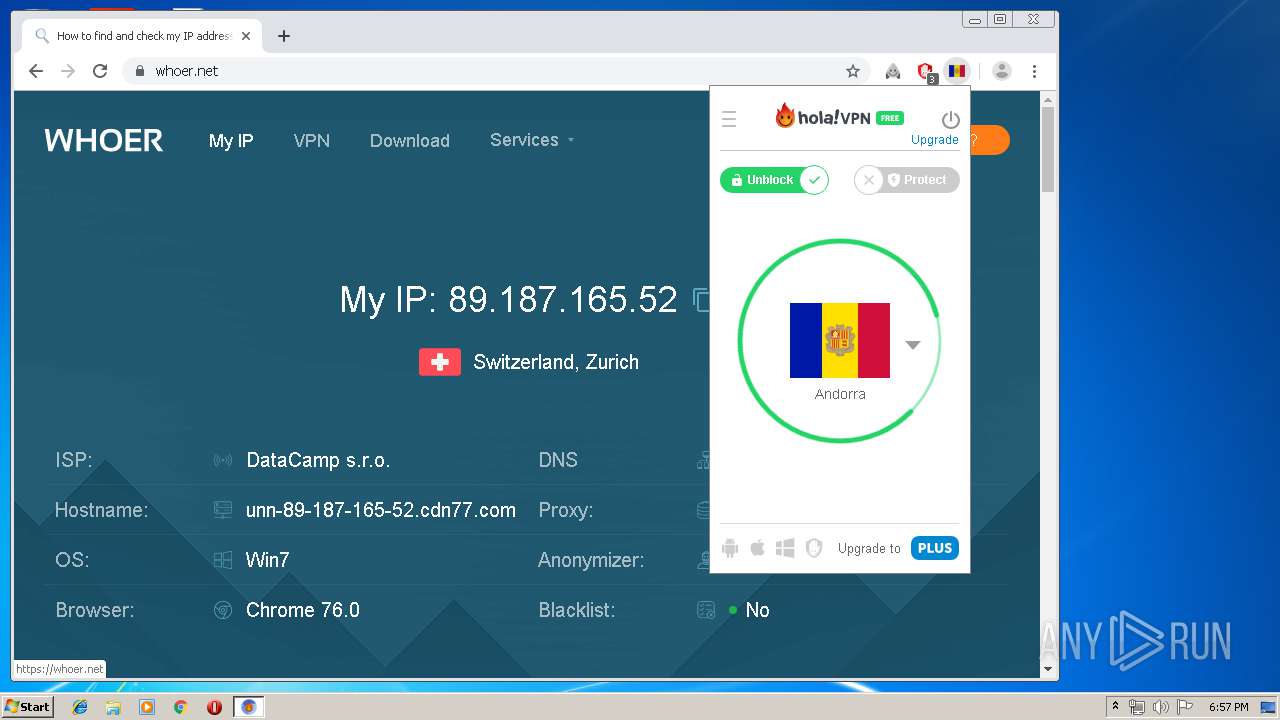
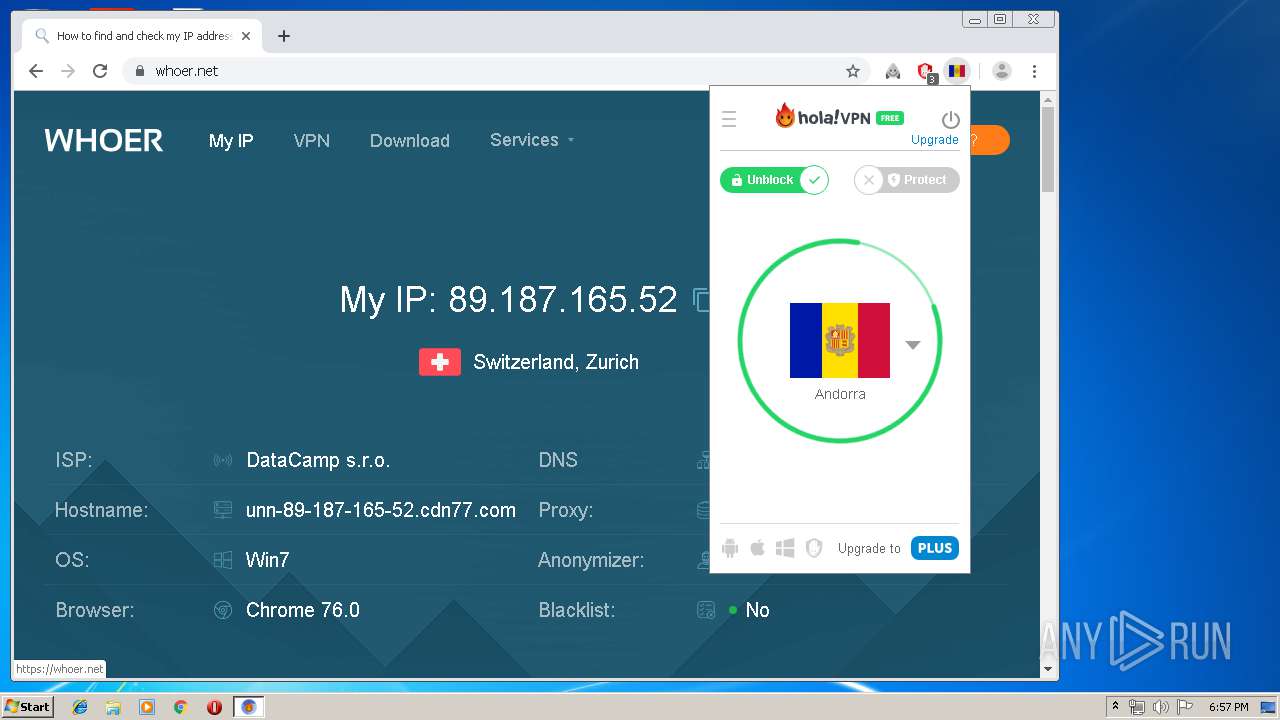
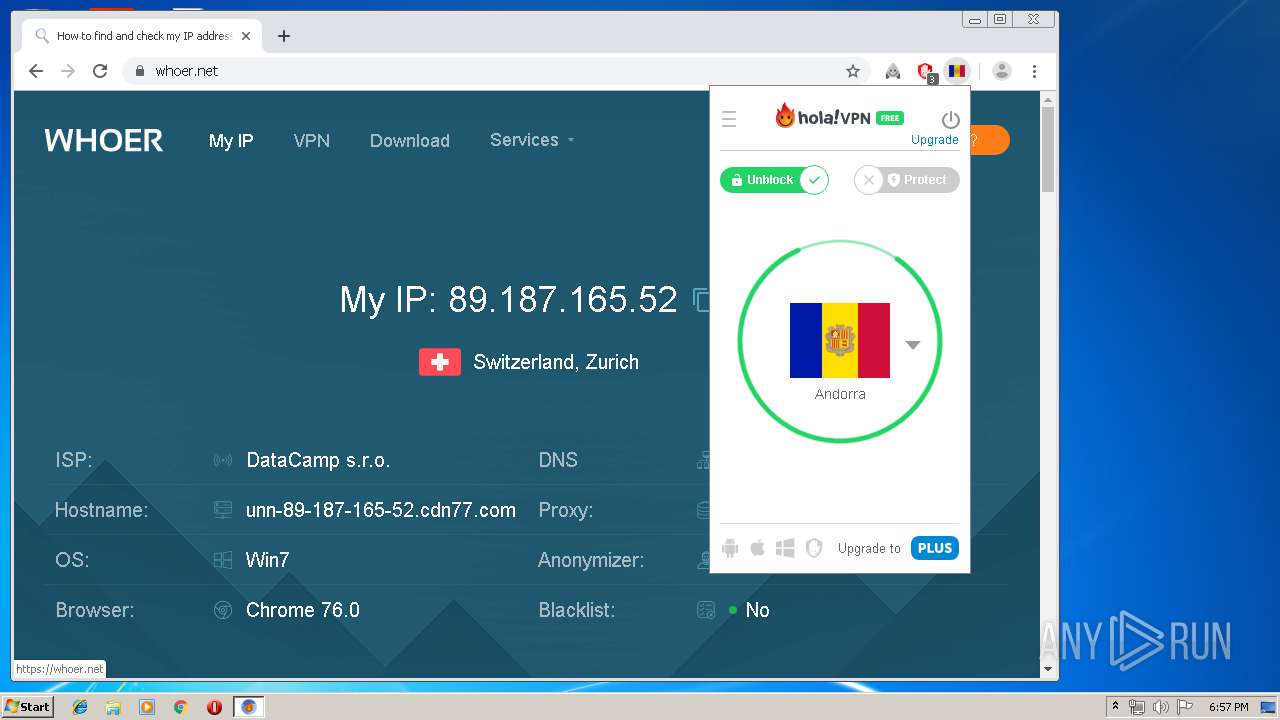
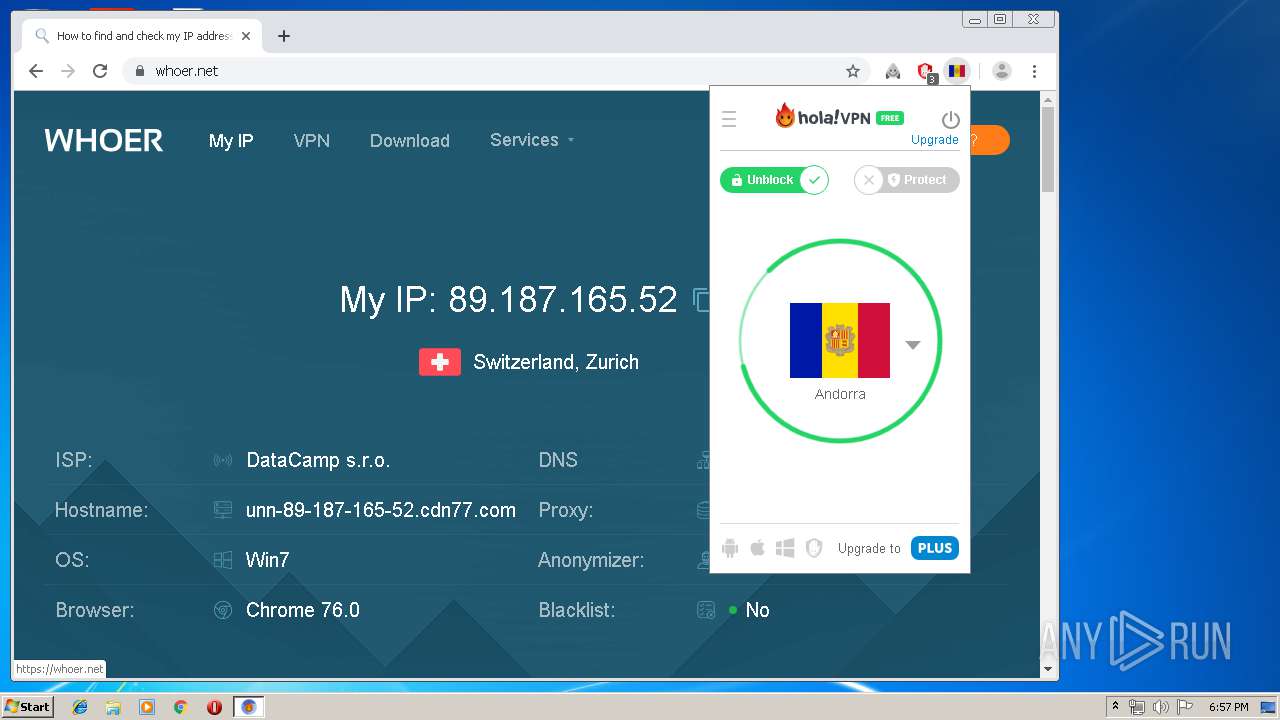
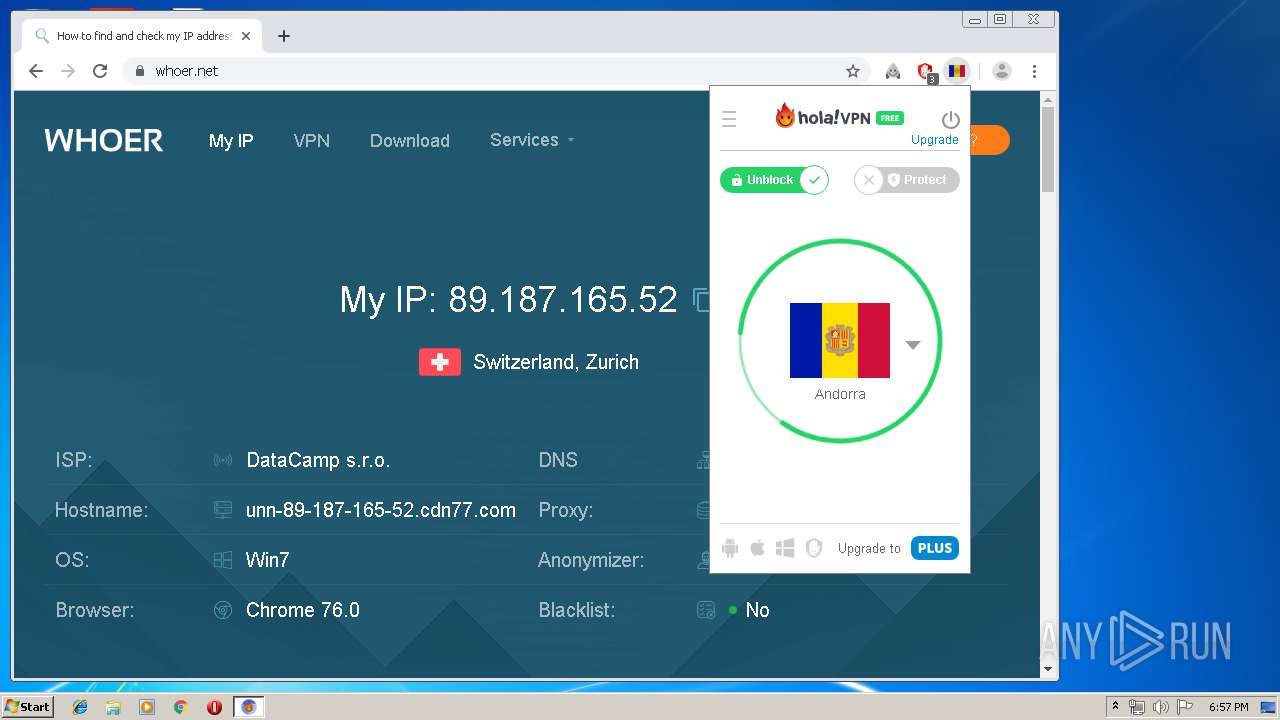
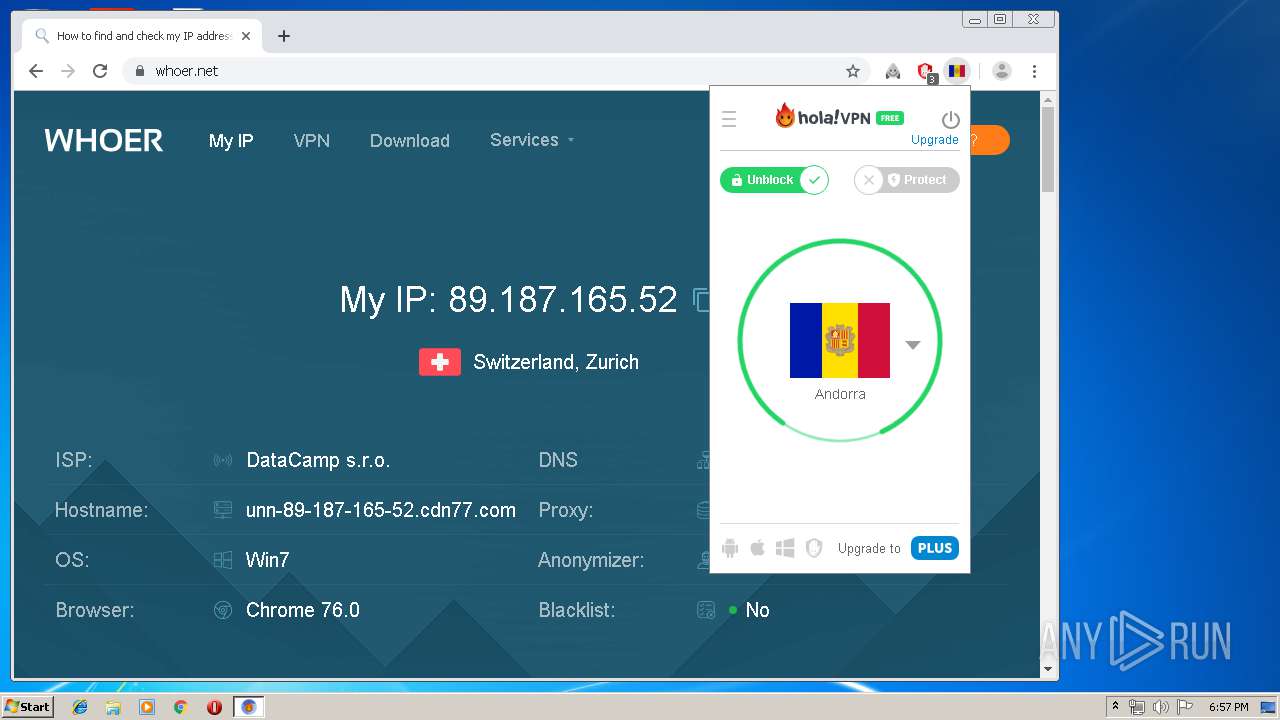
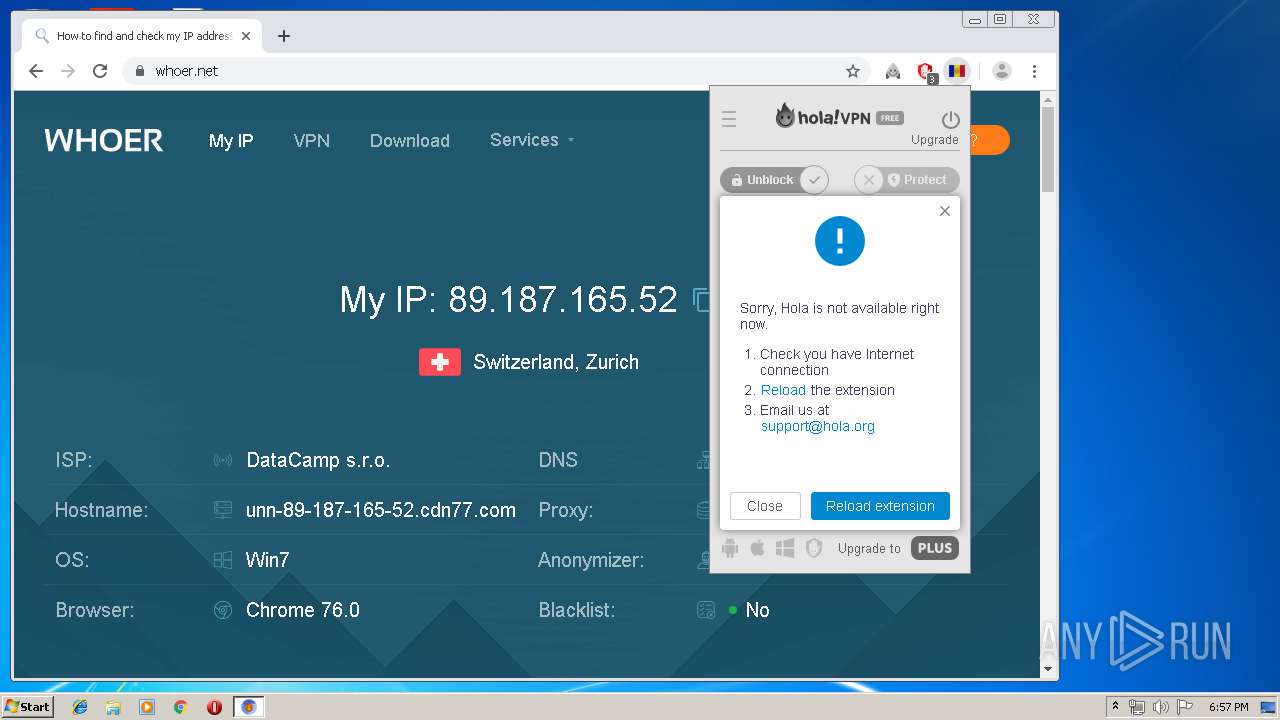
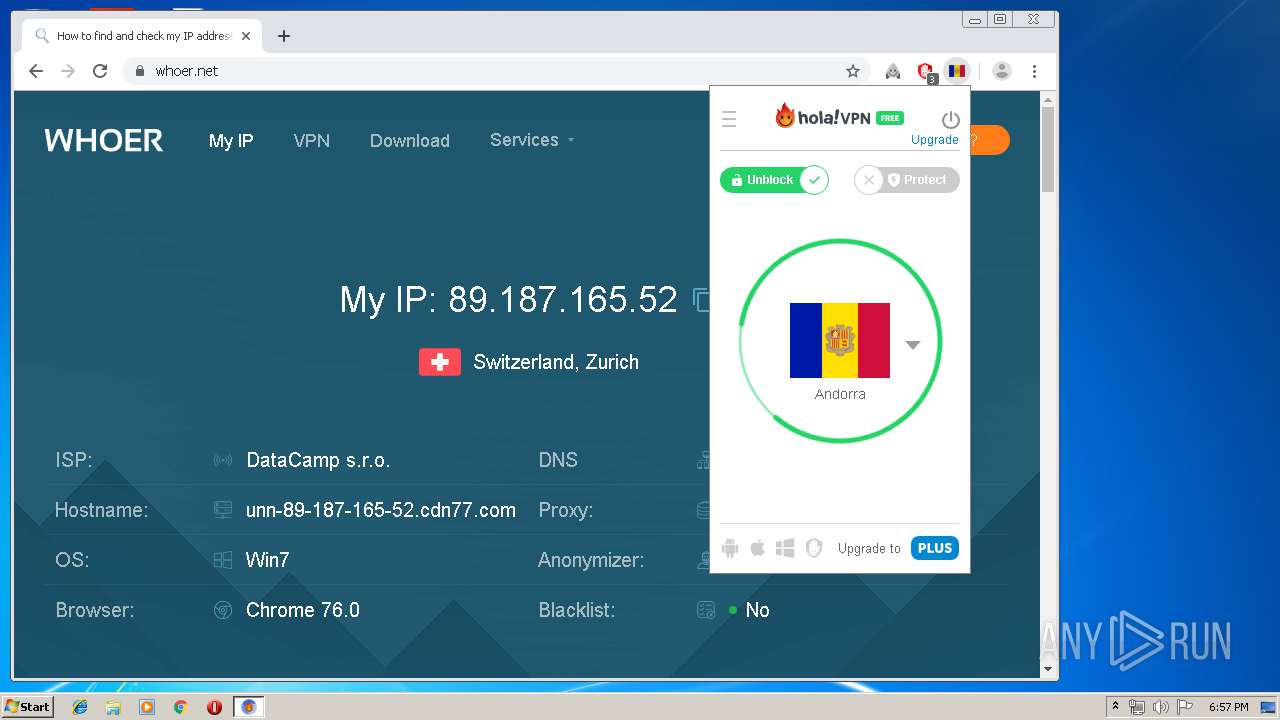
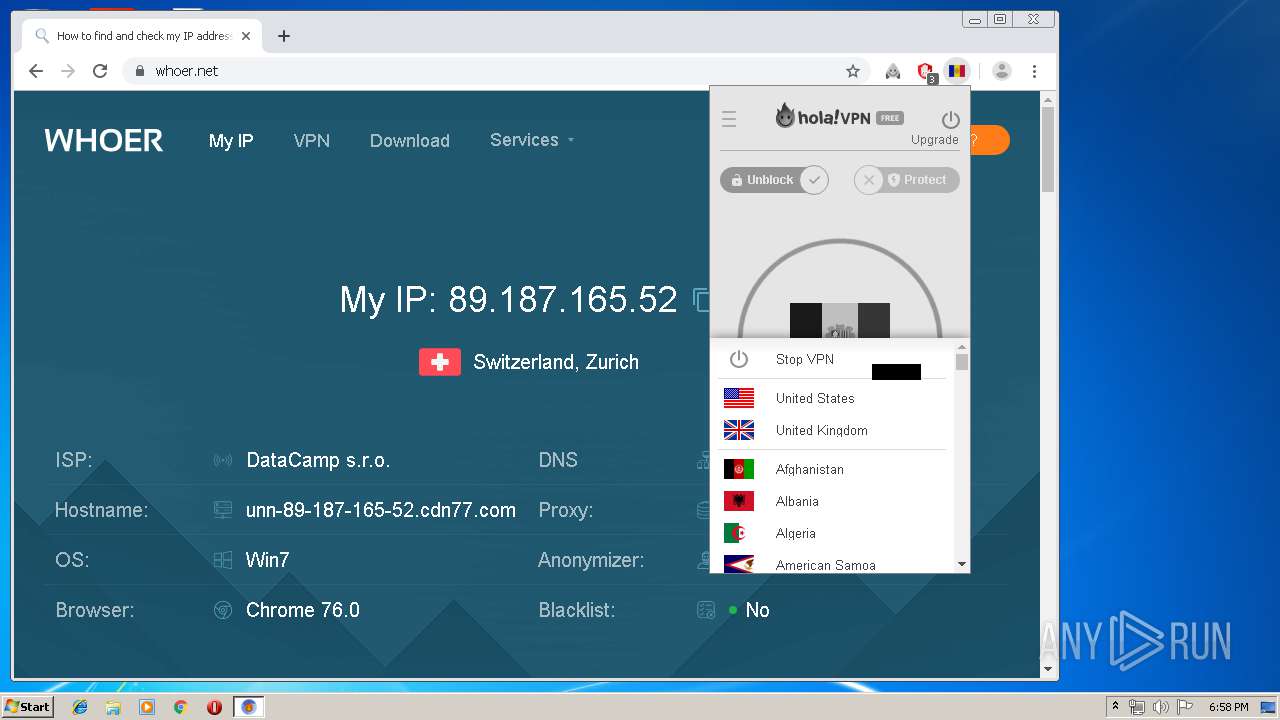
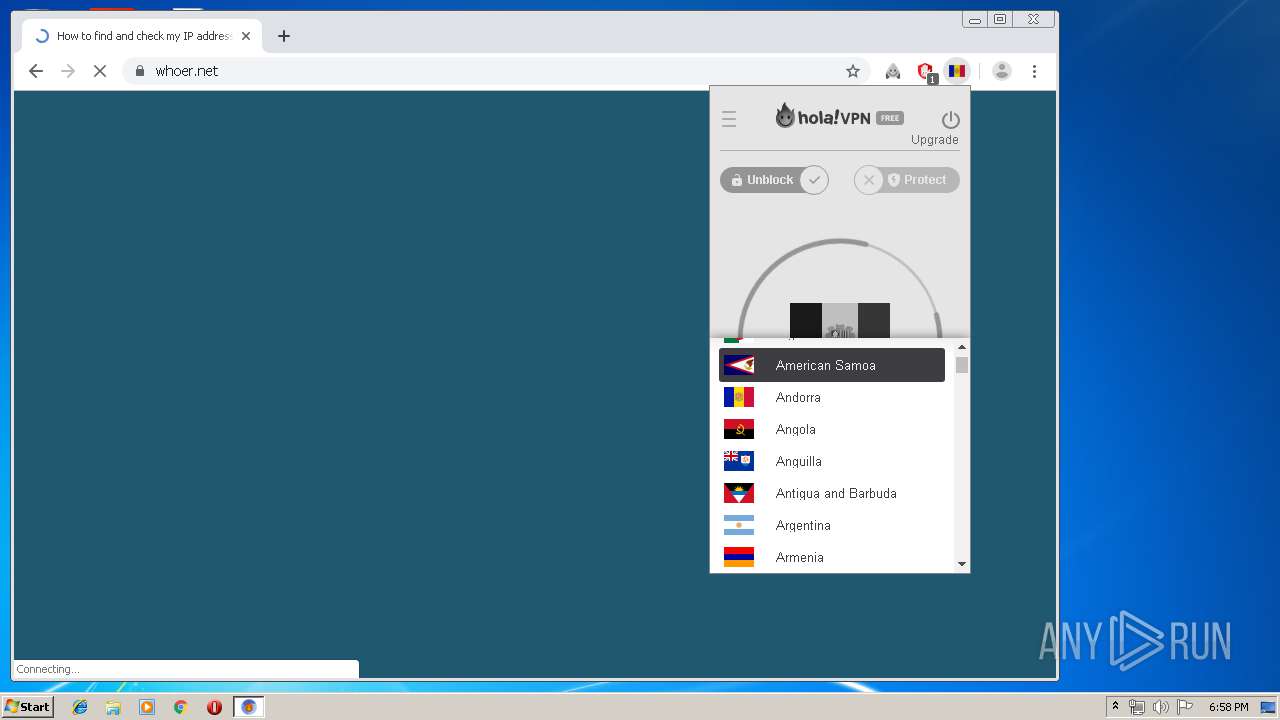
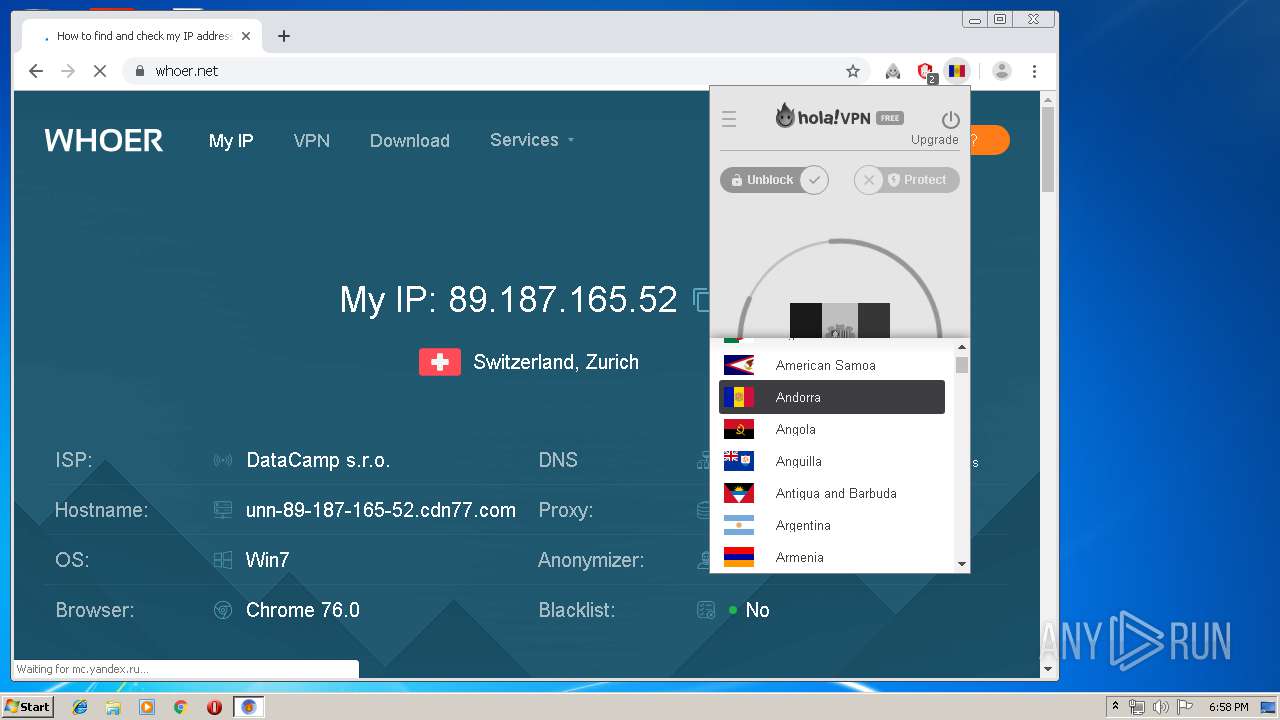
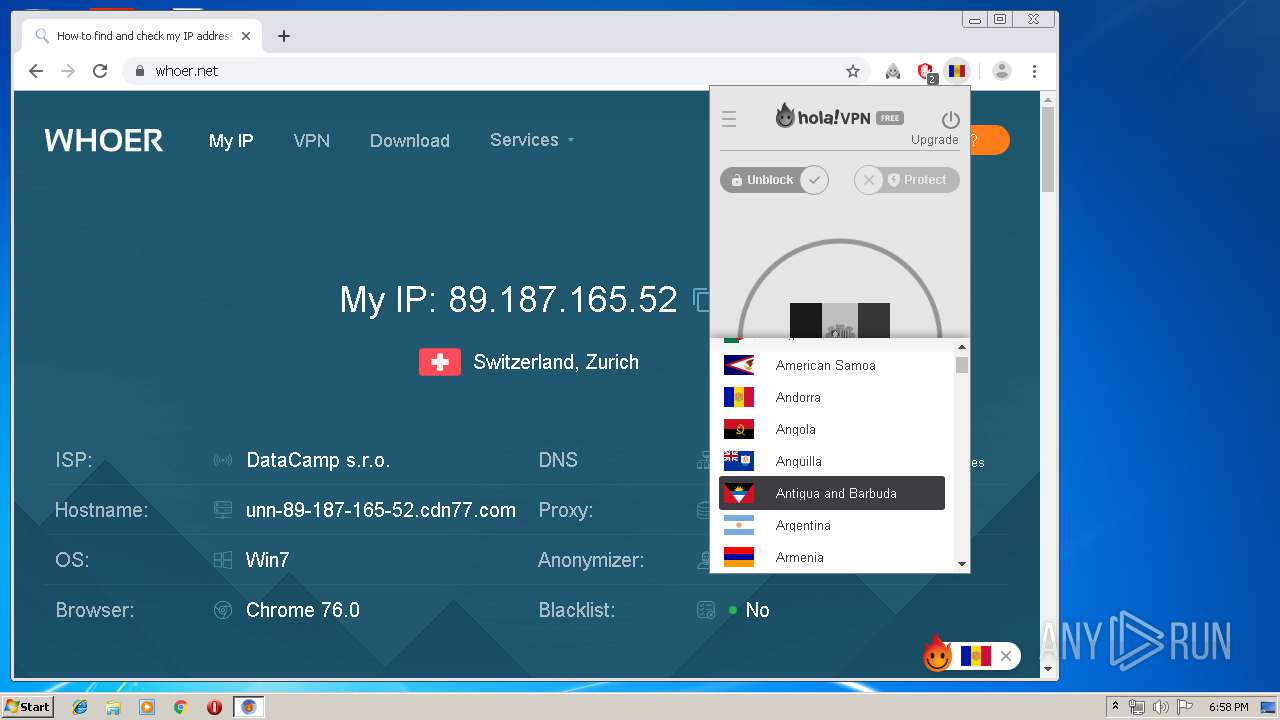
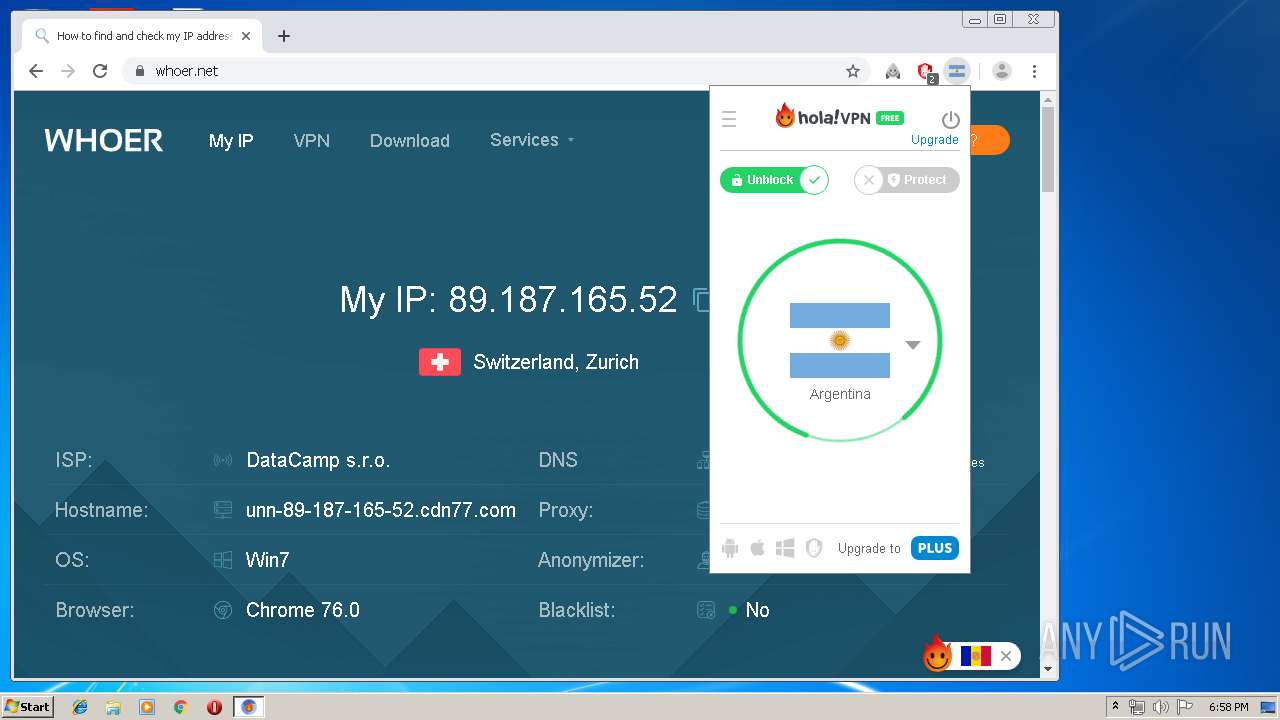
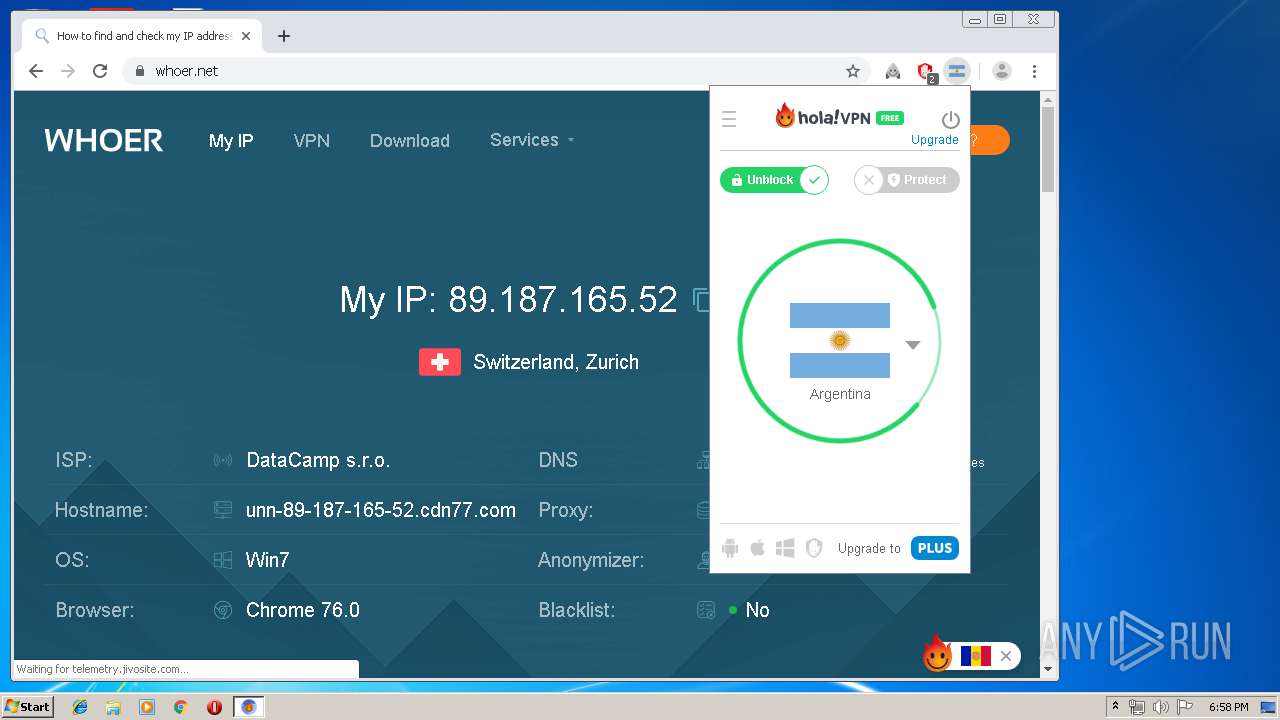
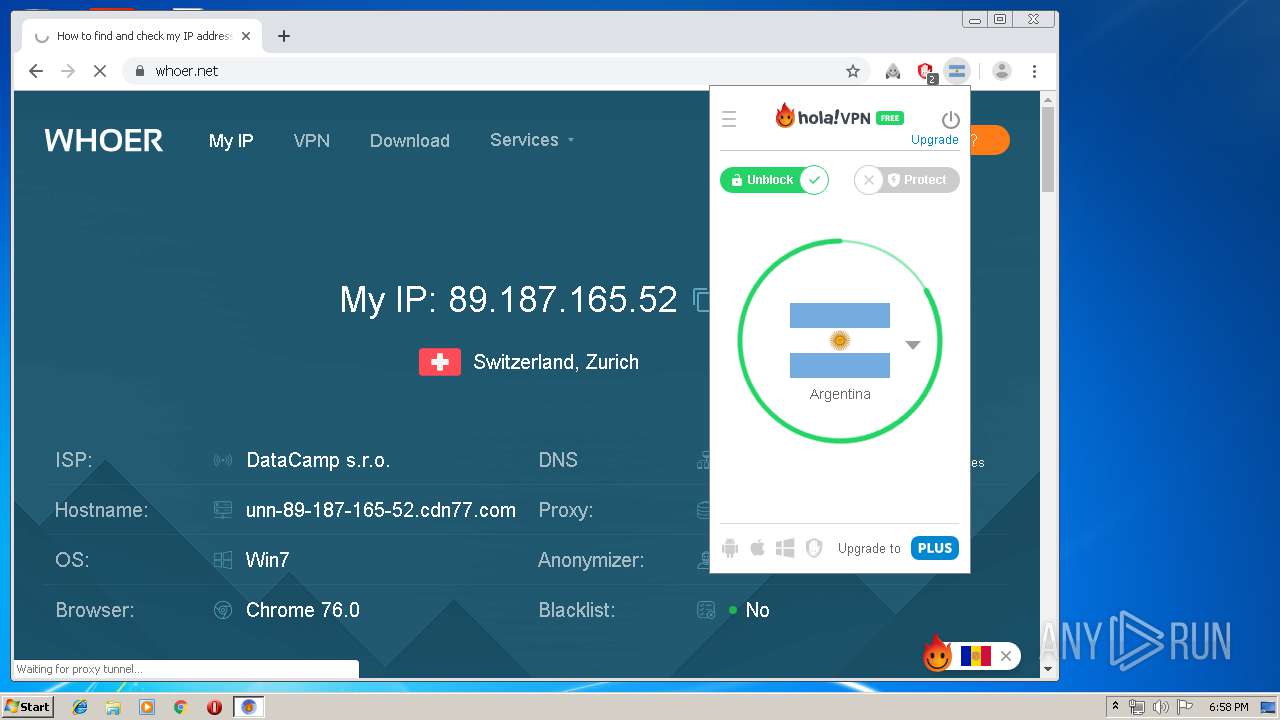
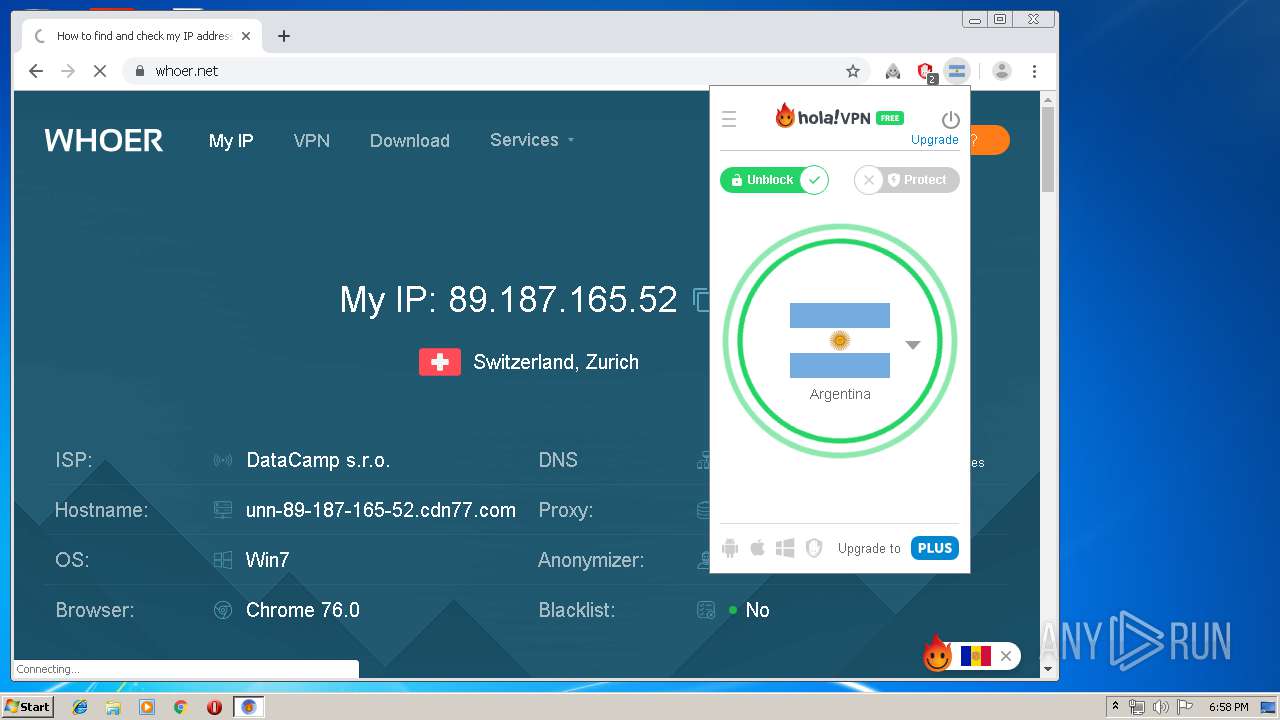
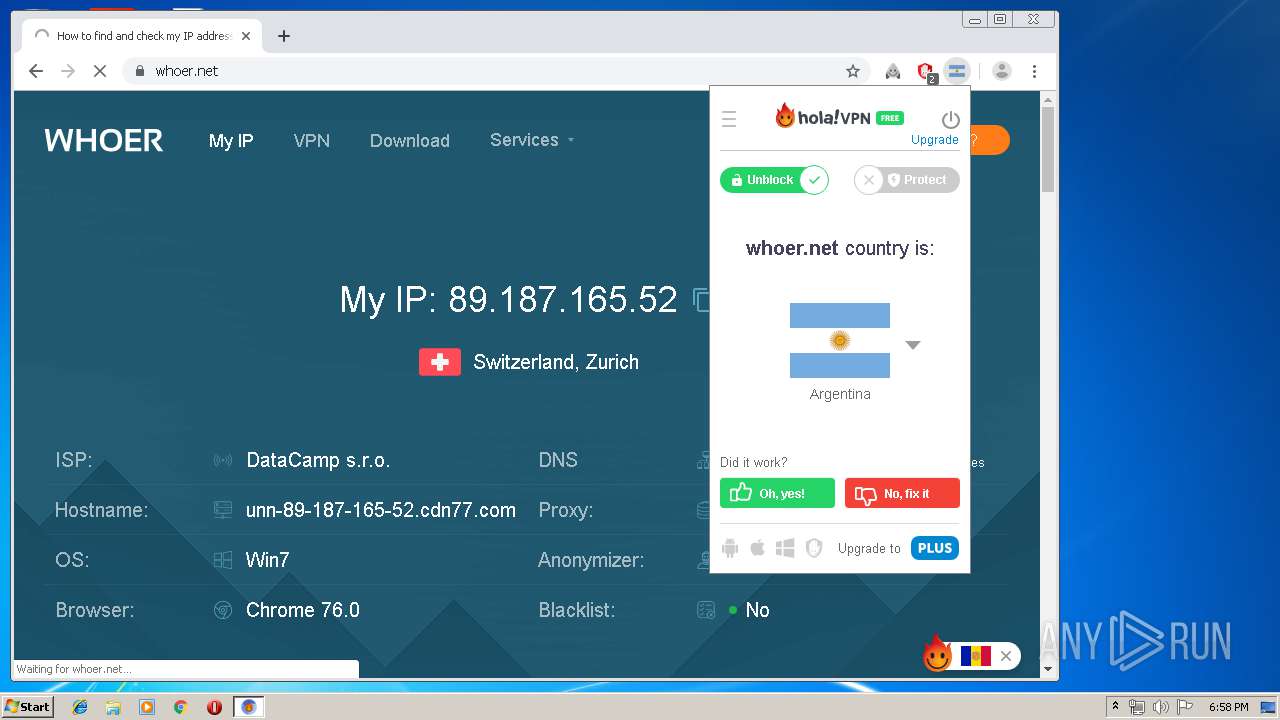
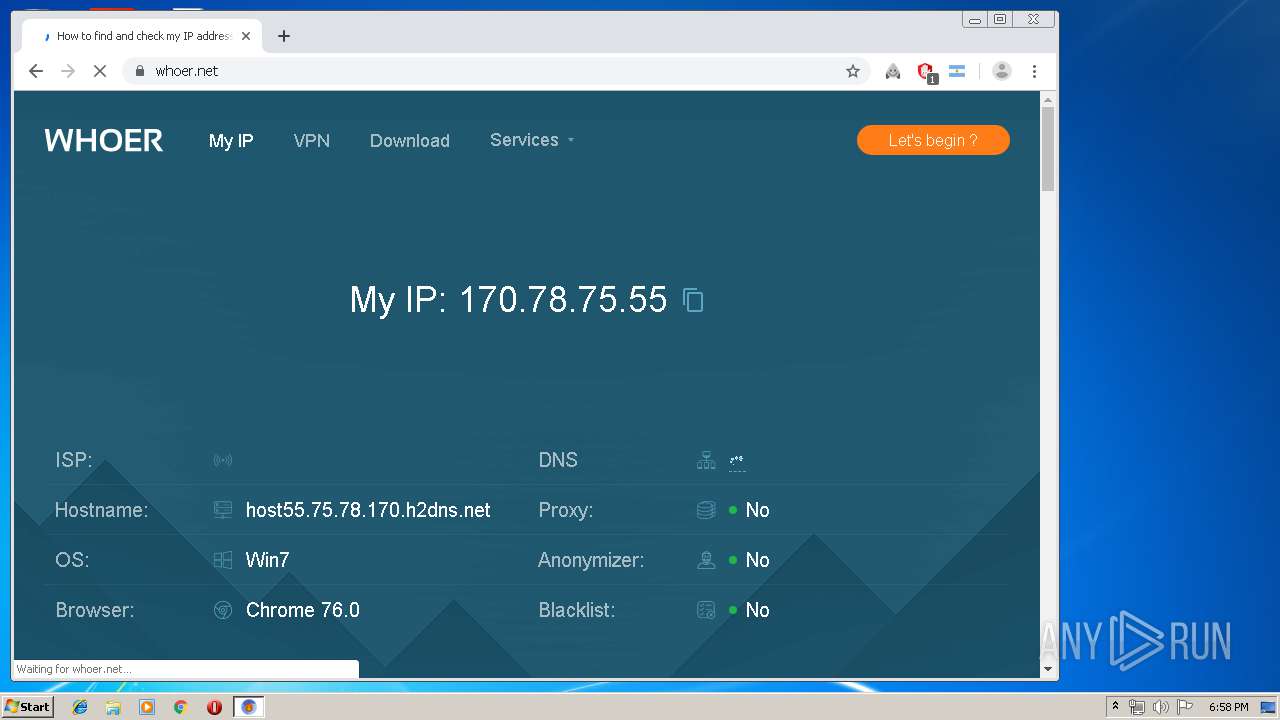
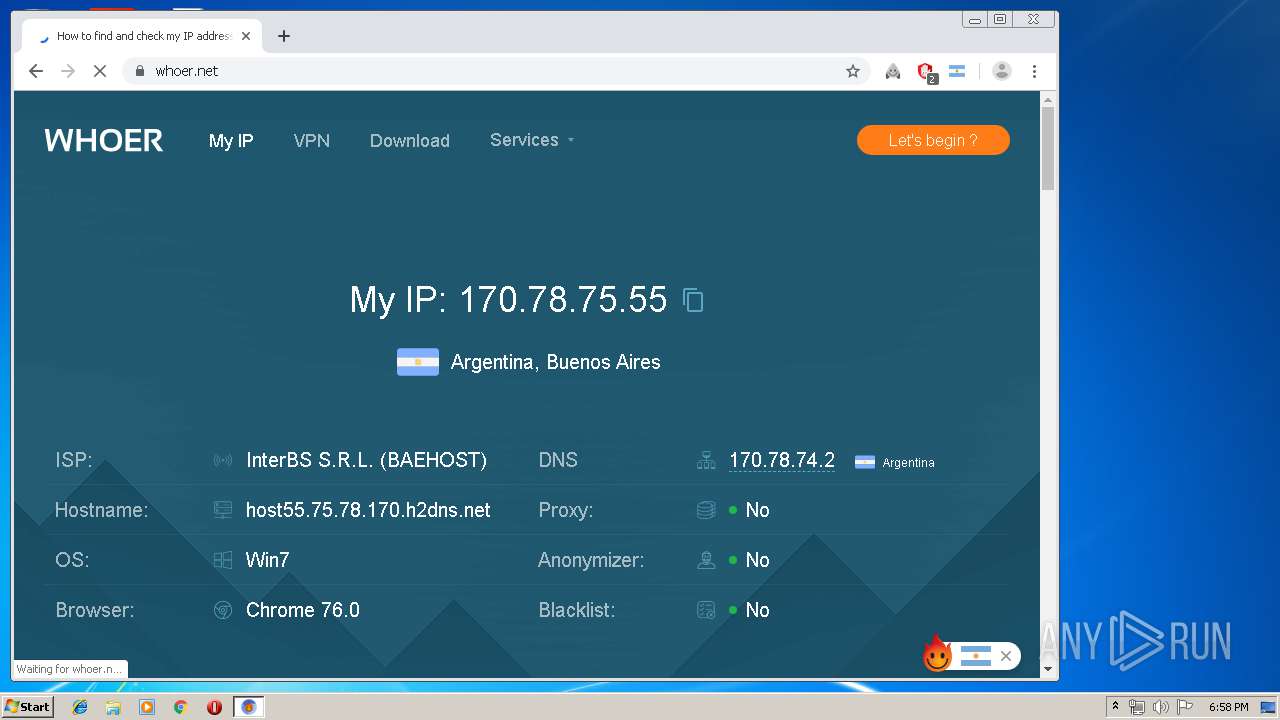
Checks for external IP
- chrome.exe (PID: 2808)
- hola_cr.exe (PID: 2932)
Creates files in the program directory
- Hola-Setup-1.151.979.exe (PID: 4032)
- hola_updater.exe (PID: 3920)
- Hola-Setup-1.151.979.exe (PID: 1816)
- net_updater32.exe (PID: 3388)
- Hola-Setup-1.151.979.exe (PID: 1856)
- hola_svc.exe (PID: 1728)
- net_updater32.exe (PID: 1480)
- 7za.exe (PID: 1260)
- net_updater32.exe (PID: 3728)
- hola.exe (PID: 2672)
- net_svc.exe (PID: 2568)
Executed as Windows Service
- hola_updater.exe (PID: 3920)
- hola_svc.exe (PID: 1728)
- PresentationFontCache.exe (PID: 2276)
- net_updater32.exe (PID: 3728)
Uses REG.EXE to modify Windows registry
- hola_updater.exe (PID: 3920)
- hola_svc.exe (PID: 1728)
Uses WMIC.EXE to obtain a list of AntiViruses
- hola_updater.exe (PID: 3920)
- hola_svc.exe (PID: 1728)
- net_svc.exe (PID: 2568)
Reads Internet Cache Settings
- Hola-Setup-1.151.979.exe (PID: 1816)
Uses WMIC.EXE to obtain a system information
- hola_updater.exe (PID: 3920)
- hola_svc.exe (PID: 1728)
- net_svc.exe (PID: 2568)
Creates a software uninstall entry
- Hola-Setup-1.151.979.exe (PID: 1816)
Executed via COM
- DeviceDisplayObjectProvider.exe (PID: 2448)
Creates files in the Windows directory
- net_updater32.exe (PID: 3728)
Reads Environment values
- net_updater32.exe (PID: 3728)
Creates files in the user directory
- hola_cr.exe (PID: 3024)
- hola_cr.exe (PID: 2248)
- hola_cr.exe (PID: 4024)
- hola_cr.exe (PID: 2932)
Removes files from Windows directory
- net_updater32.exe (PID: 3728)
INFO
Manual execution by user
- chrome.exe (PID: 3364)
Reads the hosts file
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3364)
- hola_cr.exe (PID: 2248)
- hola_cr.exe (PID: 2932)
Application launched itself
- chrome.exe (PID: 3364)
Dropped object may contain Bitcoin addresses
- 7za.exe (PID: 1260)
Reads settings of System Certificates
- hola_cr.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 17:27:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 65536 |
| InitializedDataSize: | 32768 |
| UninitializedDataSize: | 135168 |
| EntryPoint: | 0x30cd0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Hola Networks Ltd. |
| FileDescription: | Hola Setup |
| FileVersion: | 1 |
| InternalName: | Hola-Setup.exe |
| LegalCopyright: | Copyright (c) 2015 Hola Networks Ltd. |
| OriginalFileName: | Hola-Setup.exe |
| ProductName: | Hola-Setup |
| ProductVersion: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2010 16:27:35 |
| Detected languages: |
|
| CompanyName: | Hola Networks Ltd. |
| FileDescription: | Hola Setup |
| FileVersion: | 1.0 |
| InternalName: | Hola-Setup.exe |
| LegalCopyright: | Copyright (c) 2015 Hola Networks Ltd. |
| OriginalFilename: | Hola-Setup.exe |
| ProductName: | Hola-Setup |
| ProductVersion: | 1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 18-Nov-2010 16:27:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00021000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00022000 | 0x00010000 | 0x0000FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97588 |
.rsrc | 0x00032000 | 0x00008000 | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.4269 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17884 | 1873 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.96919 | 22872 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.10639 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.49361 | 52 | Latin 1 / Western European | English - United States | RT_STRING |
500 | 6.93639 | 184 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
KERNEL32.DLL |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
325
Monitored processes
186
Malicious processes
15
Suspicious processes
27
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Hola\app\chromium\hola_cr.exe" --type=renderer --field-trial-handle=948,17480311259675612919,4652874670385158730,131072 --lang=en-US --user-data-dir="C:\\Users\\admin\\AppData\\Roaming\\Hola\\chromium_profile" --enable-auto-reload --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2178229676976350489 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2052 /prefetch:1 | C:\Program Files\Hola\app\chromium\hola_cr.exe | — | hola_cr.exe | |||||||||||
User: admin Company: The Chromium Authors Integrity Level: LOW Description: Chromium Exit code: 0 Version: 76.0.3809.87 Modules
| |||||||||||||||
| 356 | rasdial | C:\Windows\system32\rasdial.exe | — | hola_svc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Remote Access Command Line Dial UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 360 | rasdial | C:\Windows\system32\rasdial.exe | — | hola_svc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Remote Access Command Line Dial UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 364 | rasdial | C:\Windows\system32\rasdial.exe | — | hola_svc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Remote Access Command Line Dial UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | rasdial | C:\Windows\system32\rasdial.exe | — | hola_svc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Remote Access Command Line Dial UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | wmic /namespace:\\root\SecurityCenter2 path AntiVirusProduct get displayName /value | C:\Windows\System32\Wbem\wmic.exe | — | hola_updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 776 | rasdial | C:\Windows\system32\rasdial.exe | — | hola_svc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Remote Access Command Line Dial UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6881a9d0,0x6881a9e0,0x6881a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Hola\app\chromium\hola_cr.exe" --type=gpu-process --field-trial-handle=948,17480311259675612919,4652874670385158730,131072 --disable-gpu-sandbox --use-gl=disabled --user-data-dir="C:\\Users\\admin\\AppData\\Roaming\\Hola\\chromium_profile" --gpu-preferences=IAAAAAAAAADgAAAwAAAAAAAAYAAAAAAACAAAAAAAAAAoAAAABAAAACAAAAAAAAAAKAAAAAAAAAAwAAAAAAAAADgAAAAAAAAAEAAAAAAAAAAAAAAABQAAABAAAAAAAAAAAAAAAAYAAAAQAAAAAAAAAAEAAAAFAAAAEAAAAAAAAAABAAAABgAAAA== --service-request-channel-token=5056326453289075500 --mojo-platform-channel-handle=4320 /prefetch:2 | C:\Program Files\Hola\app\chromium\hola_cr.exe | — | hola_cr.exe | |||||||||||
User: admin Company: The Chromium Authors Integrity Level: HIGH Description: Chromium Exit code: 0 Version: 76.0.3809.87 Modules
| |||||||||||||||
| 896 | rasdial | C:\Windows\system32\rasdial.exe | — | hola_svc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Remote Access Command Line Dial UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 716
Read events
1 342
Write events
363
Delete events
11
Modification events
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3460) Hola-Setup-Core.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\B51C067CEE2B0C3DF855AB2D92F4FE39D4E70F0E |
| Operation: | write | Name: | Blob |
Value: 0F000000010000002000000071B437F087F3700FFD4E2FA46F42B6B810D7BF19ADFEDF951C023EDD65B50B050B000000010000005400000053007400610072006600690065006C006400200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F007200690074007900200013202000470032000000090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B06010505070308060A2B0601040182370A030406082B0601050507030606082B0601050507030753000000010000002500000030233021060B6086480186FD6E0107170330123010060A2B0601040182373C0101030200C06200000001000000200000002CE1CB0BF9D2F9E102993FBE215152C3B2DD0CABDE1C68E5319B839154DBB7F51400000001000000140000007C0C321FA7D9307FC47D68A362A8A1CEAB075B271D000000010000001000000054E2CD85BA79CDA018FED9E6A863AA46030000000100000014000000B51C067CEE2B0C3DF855AB2D92F4FE39D4E70F0E2000000001000000E1030000308203DD308202C5A003020102020100300D06092A864886F70D01010B050030818F310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C6531253023060355040A131C537461726669656C6420546563686E6F6C6F676965732C20496E632E3132303006035504031329537461726669656C6420526F6F7420436572746966696361746520417574686F72697479202D204732301E170D3039303930313030303030305A170D3337313233313233353935395A30818F310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C6531253023060355040A131C537461726669656C6420546563686E6F6C6F676965732C20496E632E3132303006035504031329537461726669656C6420526F6F7420436572746966696361746520417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100BDEDC103FCF68FFC02B16F5B9F48D99D79E2A2B703615618C347B6D7CA3D352E8943F7A1699BDE8A1AFD13209CB44977322956FDB9EC8CDD22FA72DC276197EEF65A84EC6E19B9892CDC845BD574FB6B5FC589A51052894655F4B8751CE67FE454AE4BF85572570219F8177159EB1E280774C59D48BE6CB4F4A4B0F364377992C0EC465E7FE16D534C62AFCD1F0B63BB3A9DFBFC7900986174CF26824063F3B2726A190D99CAD40E75CC37FB8B89C159F1627F5FB35F6530F8A7B74D765A1E765E34C0E89656998AB3F07FA4CDBDDC32317C91CFE05F11F86BAA495CD19994D1A2E3635B0976B55662E14B741D96D426D4080459D0980E0EE6DEFCC3EC1F90F10203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147C0C321FA7D9307FC47D68A362A8A1CEAB075B27300D06092A864886F70D01010B050003820101001159FA254F036F94993B9A1F828539D47605945EE128936D625D09C2A0A8D4B07538F1346A9DE49F8A862651E62CD1C62D6E95204A9201ECB88A677B31E2672E8C9503262E439D4A31F60EB50CBBB7E2377F22BA00A30E7B52FB6BBB3BC4D379514ECD90F4670719C83C467A0D017DC558E76DE68530179A24C410E004F7E0F27FD4AA0AFF421D37ED94E5645912207738D3323E3881759673FA688FB1CBCE1FC5ECFA9C7ECF7EB1F1072DB6FCBFCAA4BFD097054ABCEA18280290BD5478092171D3D17D1DD916B0A9613DD00A0022FCC77BCB0964450B3B4081F77D7C32F598CA588E7D2AEE90597364F936745E25A1F566052E7F3915A92AFB508B8E8569F4 | |||
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\B51C067CEE2B0C3DF855AB2D92F4FE39D4E70F0E |
| Operation: | write | Name: | Blob |
Value: 19000000010000001000000060E2DC65295F1062E558F3FEF235ED3C030000000100000014000000B51C067CEE2B0C3DF855AB2D92F4FE39D4E70F0E1D000000010000001000000054E2CD85BA79CDA018FED9E6A863AA461400000001000000140000007C0C321FA7D9307FC47D68A362A8A1CEAB075B276200000001000000200000002CE1CB0BF9D2F9E102993FBE215152C3B2DD0CABDE1C68E5319B839154DBB7F553000000010000002500000030233021060B6086480186FD6E0107170330123010060A2B0601040182373C0101030200C0090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B06010505070308060A2B0601040182370A030406082B0601050507030606082B060105050703070B000000010000005400000053007400610072006600690065006C006400200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F0072006900740079002000132020004700320000000F000000010000002000000071B437F087F3700FFD4E2FA46F42B6B810D7BF19ADFEDF951C023EDD65B50B052000000001000000E1030000308203DD308202C5A003020102020100300D06092A864886F70D01010B050030818F310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C6531253023060355040A131C537461726669656C6420546563686E6F6C6F676965732C20496E632E3132303006035504031329537461726669656C6420526F6F7420436572746966696361746520417574686F72697479202D204732301E170D3039303930313030303030305A170D3337313233313233353935395A30818F310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C6531253023060355040A131C537461726669656C6420546563686E6F6C6F676965732C20496E632E3132303006035504031329537461726669656C6420526F6F7420436572746966696361746520417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100BDEDC103FCF68FFC02B16F5B9F48D99D79E2A2B703615618C347B6D7CA3D352E8943F7A1699BDE8A1AFD13209CB44977322956FDB9EC8CDD22FA72DC276197EEF65A84EC6E19B9892CDC845BD574FB6B5FC589A51052894655F4B8751CE67FE454AE4BF85572570219F8177159EB1E280774C59D48BE6CB4F4A4B0F364377992C0EC465E7FE16D534C62AFCD1F0B63BB3A9DFBFC7900986174CF26824063F3B2726A190D99CAD40E75CC37FB8B89C159F1627F5FB35F6530F8A7B74D765A1E765E34C0E89656998AB3F07FA4CDBDDC32317C91CFE05F11F86BAA495CD19994D1A2E3635B0976B55662E14B741D96D426D4080459D0980E0EE6DEFCC3EC1F90F10203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147C0C321FA7D9307FC47D68A362A8A1CEAB075B27300D06092A864886F70D01010B050003820101001159FA254F036F94993B9A1F828539D47605945EE128936D625D09C2A0A8D4B07538F1346A9DE49F8A862651E62CD1C62D6E95204A9201ECB88A677B31E2672E8C9503262E439D4A31F60EB50CBBB7E2377F22BA00A30E7B52FB6BBB3BC4D379514ECD90F4670719C83C467A0D017DC558E76DE68530179A24C410E004F7E0F27FD4AA0AFF421D37ED94E5645912207738D3323E3881759673FA688FB1CBCE1FC5ECFA9C7ECF7EB1F1072DB6FCBFCAA4BFD097054ABCEA18280290BD5478092171D3D17D1DD916B0A9613DD00A0022FCC77BCB0964450B3B4081F77D7C32F598CA588E7D2AEE90597364F936745E25A1F566052E7F3915A92AFB508B8E8569F4 | |||
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\B51C067CEE2B0C3DF855AB2D92F4FE39D4E70F0E |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000D63981C6527E9669FCFCCA66ED05F2960F000000010000002000000071B437F087F3700FFD4E2FA46F42B6B810D7BF19ADFEDF951C023EDD65B50B050B000000010000005400000053007400610072006600690065006C006400200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F007200690074007900200013202000470032000000090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B06010505070308060A2B0601040182370A030406082B0601050507030606082B0601050507030753000000010000002500000030233021060B6086480186FD6E0107170330123010060A2B0601040182373C0101030200C06200000001000000200000002CE1CB0BF9D2F9E102993FBE215152C3B2DD0CABDE1C68E5319B839154DBB7F51400000001000000140000007C0C321FA7D9307FC47D68A362A8A1CEAB075B271D000000010000001000000054E2CD85BA79CDA018FED9E6A863AA46030000000100000014000000B51C067CEE2B0C3DF855AB2D92F4FE39D4E70F0E19000000010000001000000060E2DC65295F1062E558F3FEF235ED3C2000000001000000E1030000308203DD308202C5A003020102020100300D06092A864886F70D01010B050030818F310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C6531253023060355040A131C537461726669656C6420546563686E6F6C6F676965732C20496E632E3132303006035504031329537461726669656C6420526F6F7420436572746966696361746520417574686F72697479202D204732301E170D3039303930313030303030305A170D3337313233313233353935395A30818F310B30090603550406130255533110300E060355040813074172697A6F6E61311330110603550407130A53636F74747364616C6531253023060355040A131C537461726669656C6420546563686E6F6C6F676965732C20496E632E3132303006035504031329537461726669656C6420526F6F7420436572746966696361746520417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100BDEDC103FCF68FFC02B16F5B9F48D99D79E2A2B703615618C347B6D7CA3D352E8943F7A1699BDE8A1AFD13209CB44977322956FDB9EC8CDD22FA72DC276197EEF65A84EC6E19B9892CDC845BD574FB6B5FC589A51052894655F4B8751CE67FE454AE4BF85572570219F8177159EB1E280774C59D48BE6CB4F4A4B0F364377992C0EC465E7FE16D534C62AFCD1F0B63BB3A9DFBFC7900986174CF26824063F3B2726A190D99CAD40E75CC37FB8B89C159F1627F5FB35F6530F8A7B74D765A1E765E34C0E89656998AB3F07FA4CDBDDC32317C91CFE05F11F86BAA495CD19994D1A2E3635B0976B55662E14B741D96D426D4080459D0980E0EE6DEFCC3EC1F90F10203010001A3423040300F0603551D130101FF040530030101FF300E0603551D0F0101FF040403020106301D0603551D0E041604147C0C321FA7D9307FC47D68A362A8A1CEAB075B27300D06092A864886F70D01010B050003820101001159FA254F036F94993B9A1F828539D47605945EE128936D625D09C2A0A8D4B07538F1346A9DE49F8A862651E62CD1C62D6E95204A9201ECB88A677B31E2672E8C9503262E439D4A31F60EB50CBBB7E2377F22BA00A30E7B52FB6BBB3BC4D379514ECD90F4670719C83C467A0D017DC558E76DE68530179A24C410E004F7E0F27FD4AA0AFF421D37ED94E5645912207738D3323E3881759673FA688FB1CBCE1FC5ECFA9C7ECF7EB1F1072DB6FCBFCAA4BFD097054ABCEA18280290BD5478092171D3D17D1DD916B0A9613DD00A0022FCC77BCB0964450B3B4081F77D7C32F598CA588E7D2AEE90597364F936745E25A1F566052E7F3915A92AFB508B8E8569F4 | |||
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Hola-Setup-Core.exe | |||
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hola-Setup-Core_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hola-Setup-Core_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hola-Setup-Core_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2188) Hola-Setup-Core.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hola-Setup-Core_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
36
Suspicious files
357
Text files
2 378
Unknown types
101
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | Hola-Setup-Core.exe | C:\Users\admin\AppData\Local\Temp\CabA0B9.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | Hola-Setup-Core.exe | C:\Users\admin\AppData\Local\Temp\TarA0BA.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | Hola-Setup-Core.exe | C:\Users\admin\AppData\Local\Temp\CabA0DA.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | Hola-Setup-Core.exe | C:\Users\admin\AppData\Local\Temp\TarA0DB.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | Hola-Setup-Core.exe | C:\Users\admin\AppData\Local\Temp\CabAD6F.tmp | — | |
MD5:— | SHA256:— | |||
| 2188 | Hola-Setup-Core.exe | C:\Users\admin\AppData\Local\Temp\TarAD70.tmp | — | |
MD5:— | SHA256:— | |||
| 3460 | Hola-Setup-Core.exe | C:\Users\admin\AppData\Local\Temp\CabAFEC.tmp | — | |
MD5:— | SHA256:— | |||
| 3460 | Hola-Setup-Core.exe | C:\Users\admin\AppData\Local\Temp\TarAFED.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF17a160.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
129
TCP/UDP connections
379
DNS requests
116
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4032 | Hola-Setup-1.151.979.exe | GET | — | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3einit%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | — | — | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3efree_space%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3eupdater-%3econf_delete%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3eregistry_init%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3eprerequisites%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=vpn.svc.install_full_start&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3eupdater-%3estop%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3eupdater-%3eextract%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3eupdater%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
4032 | Hola-Setup-1.151.979.exe | GET | 200 | 23.22.252.240:80 | http://perr.hola.org/client_cgi/perr?id=install_dl_step_start&info=%7b%22step%22%3a%22INSTALL-%3earchive_init%22%7d&ver=1.151.979&build=Version%3a+1.151.979+win+x86%0aTag%3a+Ntag-1_151_979%0aBuild+date%3a+09-Sep-19+10%3a56%3a53%0aMakeflags%3a+DIST%3dAPP+RELEASE%3dy+CC64_32%3dy+CONFIG_LUM_LOCAL%3dy+CONFIG_BATREQ%3dy+CONFIG_BAT_CYCLE%3dy+CONFIG_BAT_PLATFORM%3dapp_win32r%0aOs+version%3a+Win32+6.1.7601.2+sp1%0a | US | text | 10 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2188 | Hola-Setup-Core.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2188 | Hola-Setup-Core.exe | 34.237.179.253:443 | perr.hola.org | Amazon.com, Inc. | US | suspicious |
2808 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 104.25.38.26:80 | whoer.net | Cloudflare Inc | US | shared |
2808 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
2808 | chrome.exe | 205.185.208.52:443 | code.jquery.com | Highwinds Network Group, Inc. | US | unknown |
2188 | Hola-Setup-Core.exe | 23.22.252.240:443 | perr.hola.org | Amazon.com, Inc. | US | suspicious |
2808 | chrome.exe | 104.25.38.26:443 | whoer.net | Cloudflare Inc | US | shared |
2808 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
perr.hola.org |
| whitelisted |
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
whoer.net |
| shared |
stackpath.bootstrapcdn.com |
| whitelisted |
code.jquery.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2808 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup whoer.net |
3728 | net_updater32.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
2932 | hola_cr.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup whoer.net |
Process | Message |
|---|---|
Hola-Setup-Core.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Hola-Setup-Core.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
Hola-Setup-Core.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Hola-Setup-Core.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
Hola-Setup-Core.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Hola-Setup-Core.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
Hola-Setup-Core.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Hola-Setup-Core.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
Hola-Setup-Core.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
Hola-Setup-Core.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|