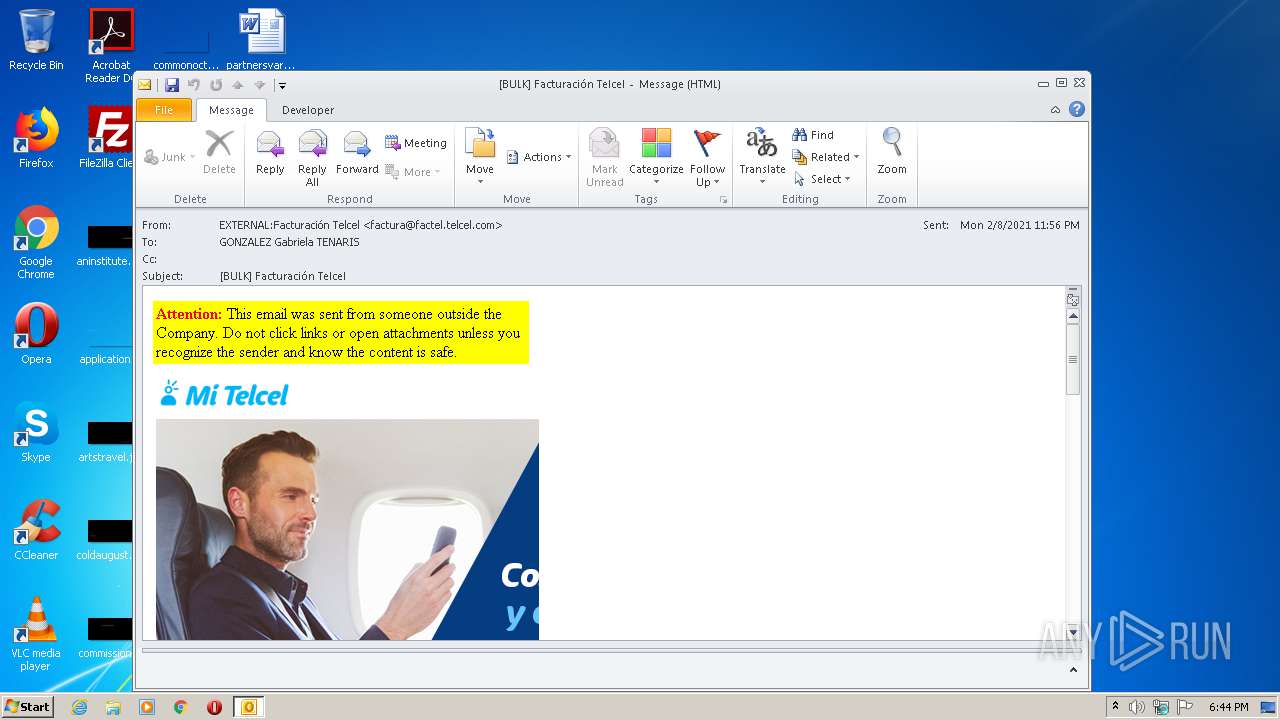
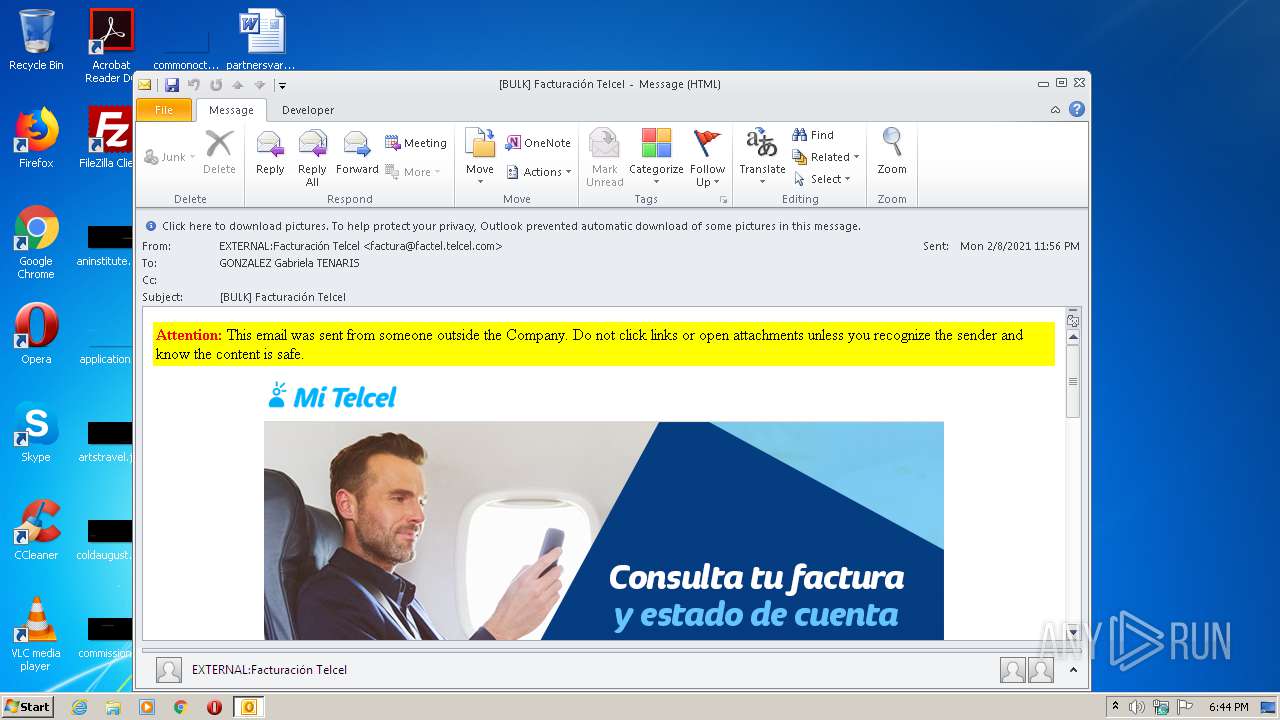
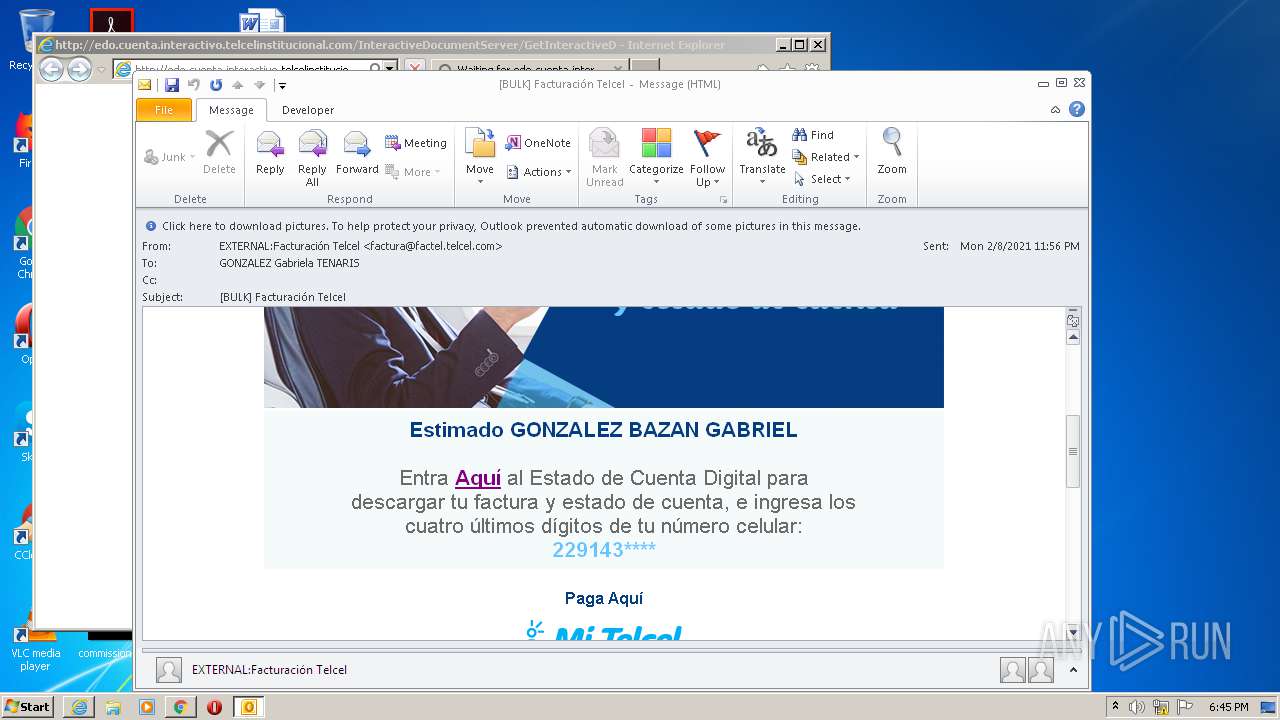
| File name: | BULK Facturación Telcel.msg |
| Full analysis: | https://app.any.run/tasks/0afba7f2-1942-42ba-bb85-565555e4a2af |
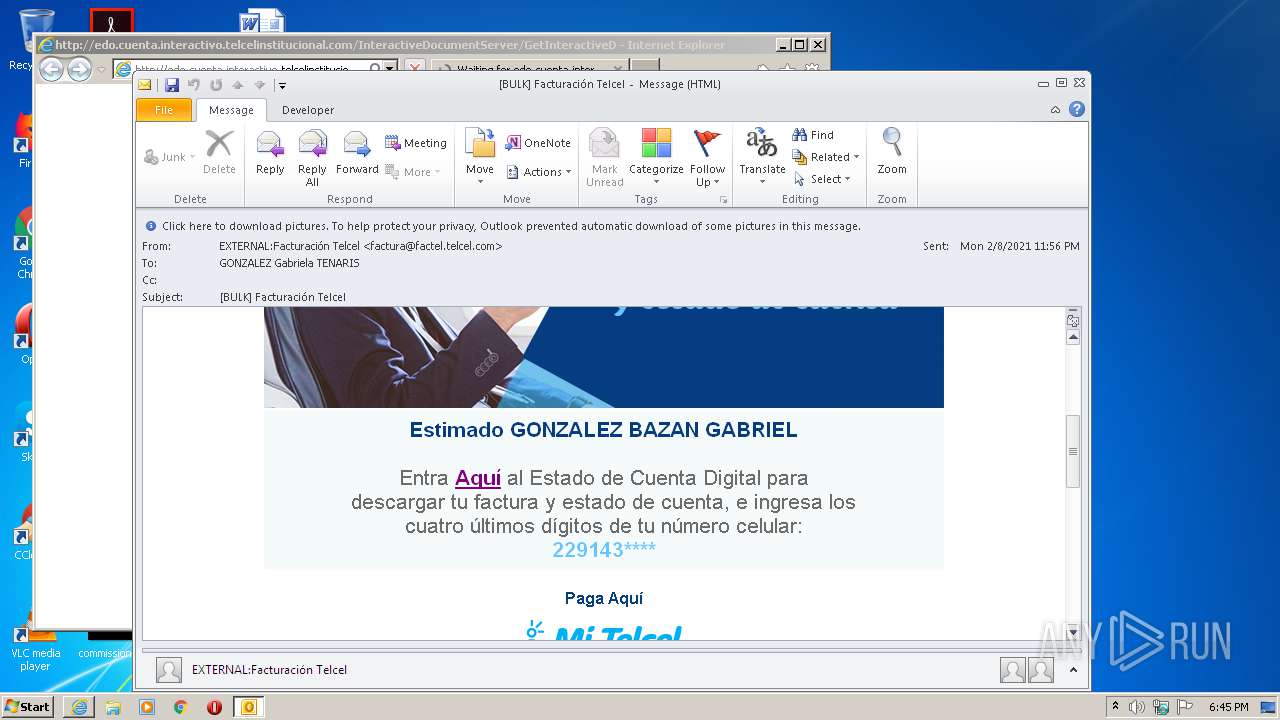
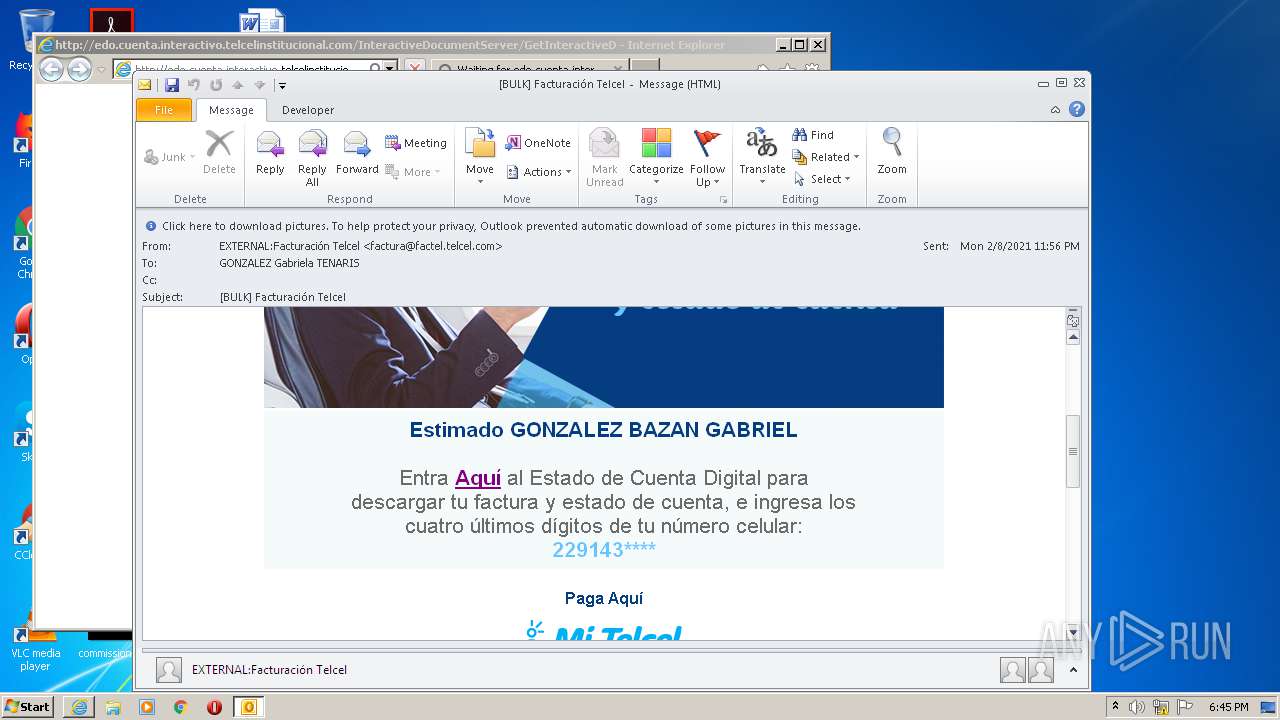
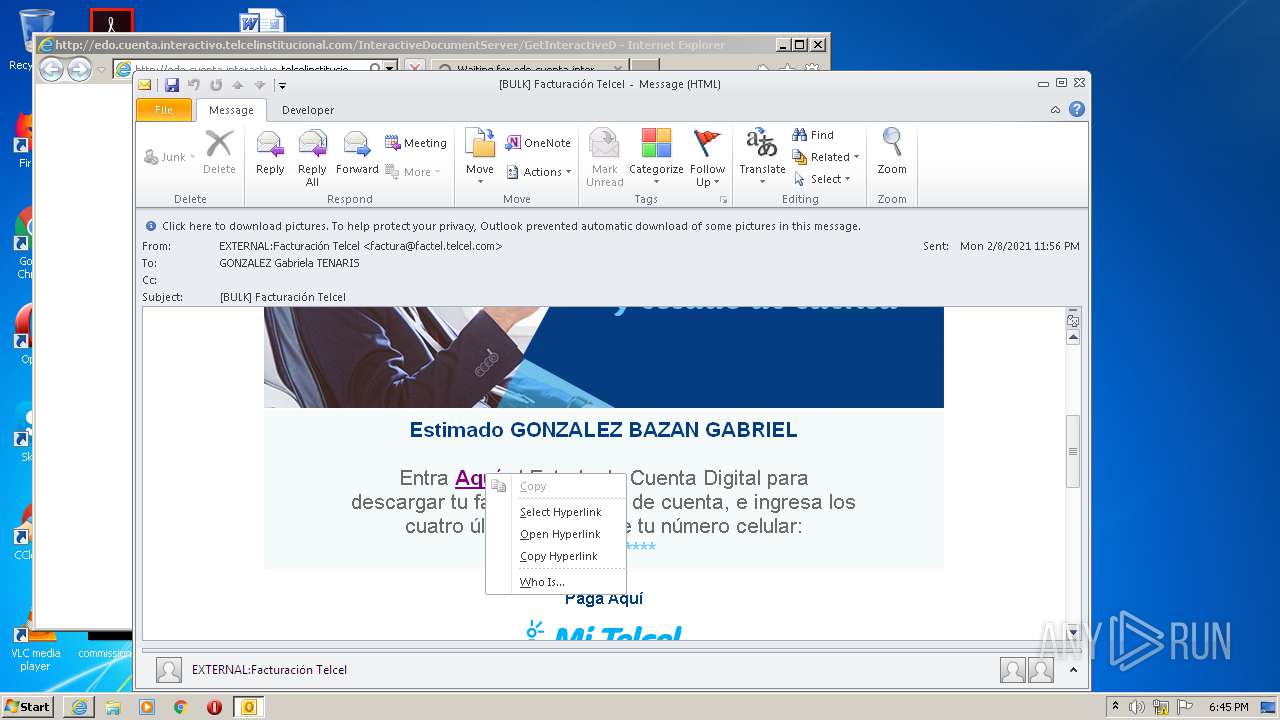
| Verdict: | Malicious activity |
| Analysis date: | February 09, 2021, 18:44:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 511D7E2CFE0C131DDF9BADB0F2F049BB |
| SHA1: | 285AC917840F3D68B41F63018448625FD55F173A |
| SHA256: | C3DC22FBA20A0380276A1C4421C02E9499F92A4B7CC4EA8396988D23755EFCA4 |
| SSDEEP: | 6144:/paueDGtVG5h08AETmanmSk/DRiKQdJIHyDU3WsPZFibWC2zi5:BteituFxtmSk/D+IHyDU7ZFioO |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 404)
SUSPICIOUS
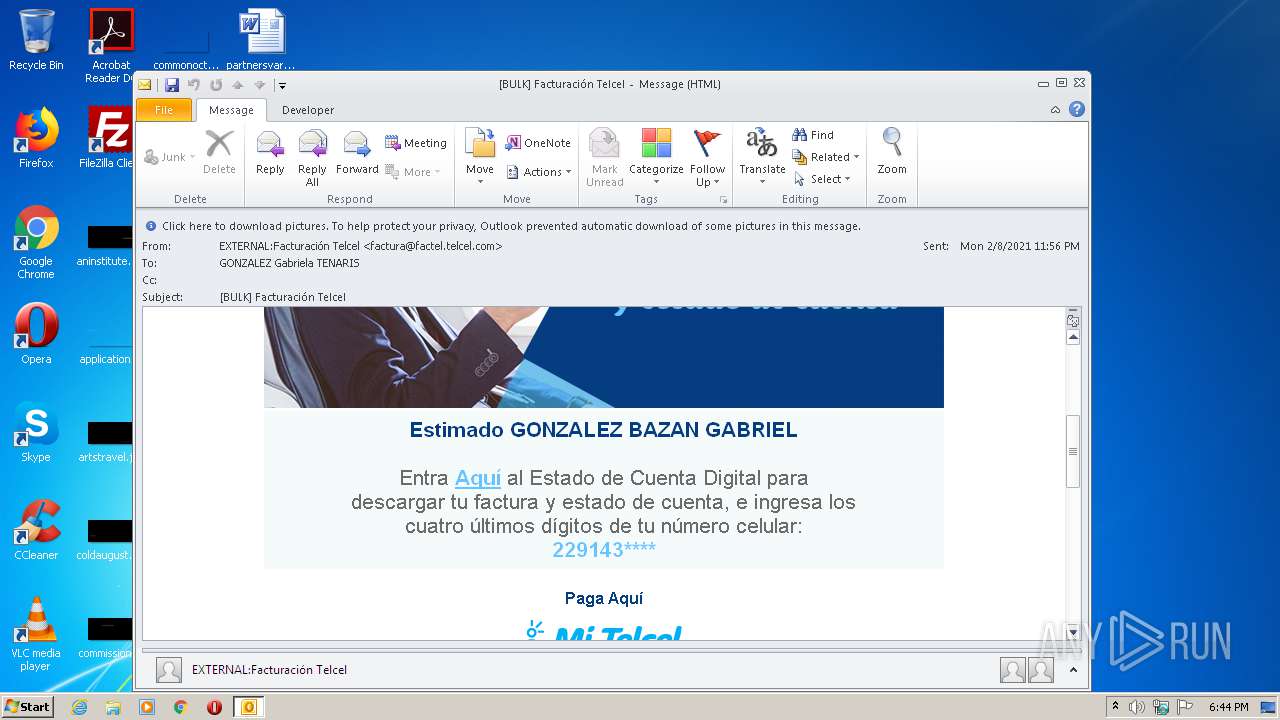
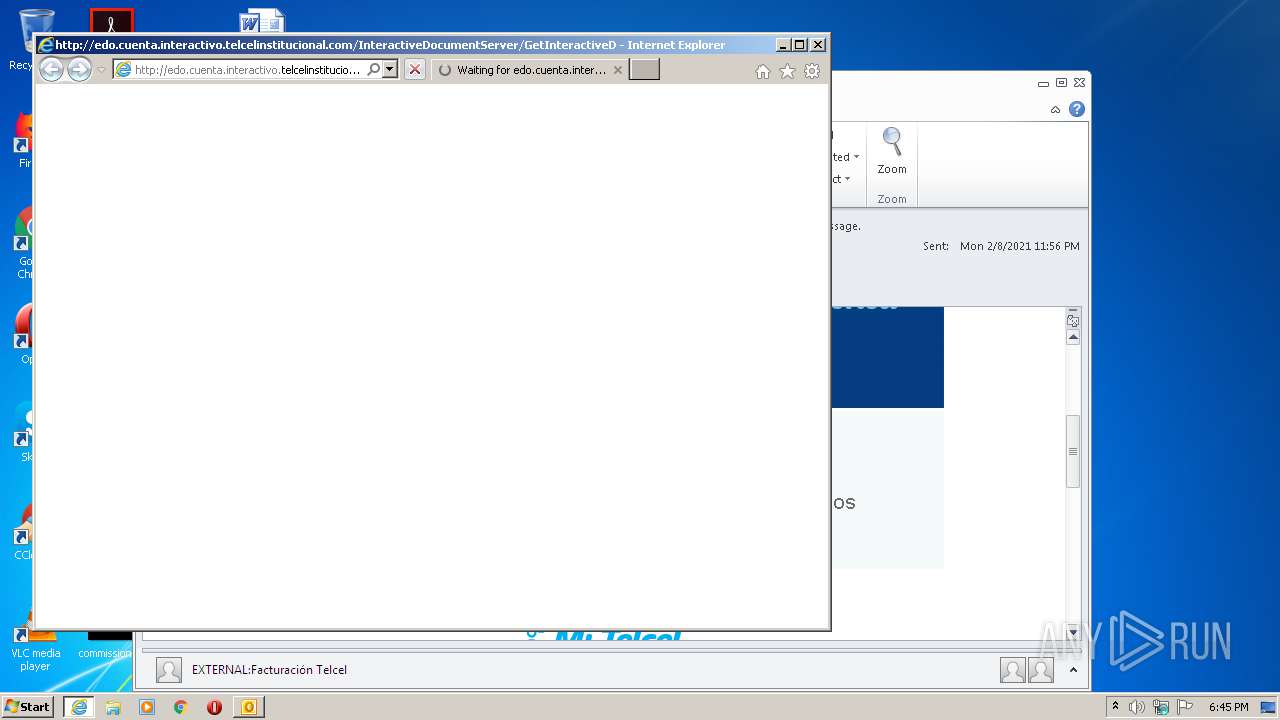
Starts Internet Explorer
- OUTLOOK.EXE (PID: 404)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2752)
INFO
Creates files in the user directory
- OUTLOOK.EXE (PID: 404)
- iexplore.exe (PID: 1748)
Manual execution by user
- chrome.exe (PID: 2752)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 404)
Changes internet zones settings
- iexplore.exe (PID: 1748)
Reads the hosts file
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2968)
Reads internet explorer settings
- iexplore.exe (PID: 3940)
Changes settings of System certificates
- iexplore.exe (PID: 1748)
Application launched itself
- iexplore.exe (PID: 1748)
- chrome.exe (PID: 2752)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1748)
Reads settings of System Certificates
- iexplore.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
74
Monitored processes
36
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\BULK Facturación Telcel.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6088a9d0,0x6088a9e0,0x6088a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10009693015732668407,18390030498971471436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=47813435989302246 --mojo-platform-channel-handle=3420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10009693015732668407,18390030498971471436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17418185841516370342 --mojo-platform-channel-handle=3740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10009693015732668407,18390030498971471436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17895809284635387143 --mojo-platform-channel-handle=3752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10009693015732668407,18390030498971471436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=506002124915955321 --mojo-platform-channel-handle=3764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Internet Explorer\iexplore.exe" http://edo.cuenta.interactivo.telcelinstitucional.com/InteractiveDocumentServer/GetInteractiveDocument/d?dWJrc3sjMy00Mj4wLyU5KiVzOj4uIz07cWZ3aWxmM1BMQVdUWiUoeWJ3Yit4YGFwPjE3NC4_Py8uMzEgenN6eC53aDssIjwsLjM1Ky4kKHBieypvbWF7eHA-MiBzc3YwZ2xkc3N3YGlwPjYgeHtrcWcyOkVLV0BJQiVrb3xgb296PldJTUJPWkwlc2dteTNeSkBLSU00enhvZnducXxrIDExPjcqITYtMjAhY3NzZ3E-ZGBpcGhvcWZ5R3J7fG9vanApZXF_KGt3PjYwLCI2KDY6NjYoJTs | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10009693015732668407,18390030498971471436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2366914756191657687 --mojo-platform-channel-handle=3384 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10009693015732668407,18390030498971471436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17088054222742592790 --mojo-platform-channel-handle=3784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,10009693015732668407,18390030498971471436,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8133402910860840630 --mojo-platform-channel-handle=4356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 647
Read events
1 921
Write events
700
Delete events
26
Modification events
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (404) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
29
Text files
331
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR7C61.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\27BAAEA6.dat | image | |
MD5:— | SHA256:— | |||
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7447026F.dat | image | |
MD5:— | SHA256:— | |||
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6F6A59A4.dat | image | |
MD5:— | SHA256:— | |||
| 1748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C921E555.dat | image | |
MD5:— | SHA256:— | |||
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1D658352.dat | image | |
MD5:— | SHA256:— | |||
| 404 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C37C572B.dat | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
36
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
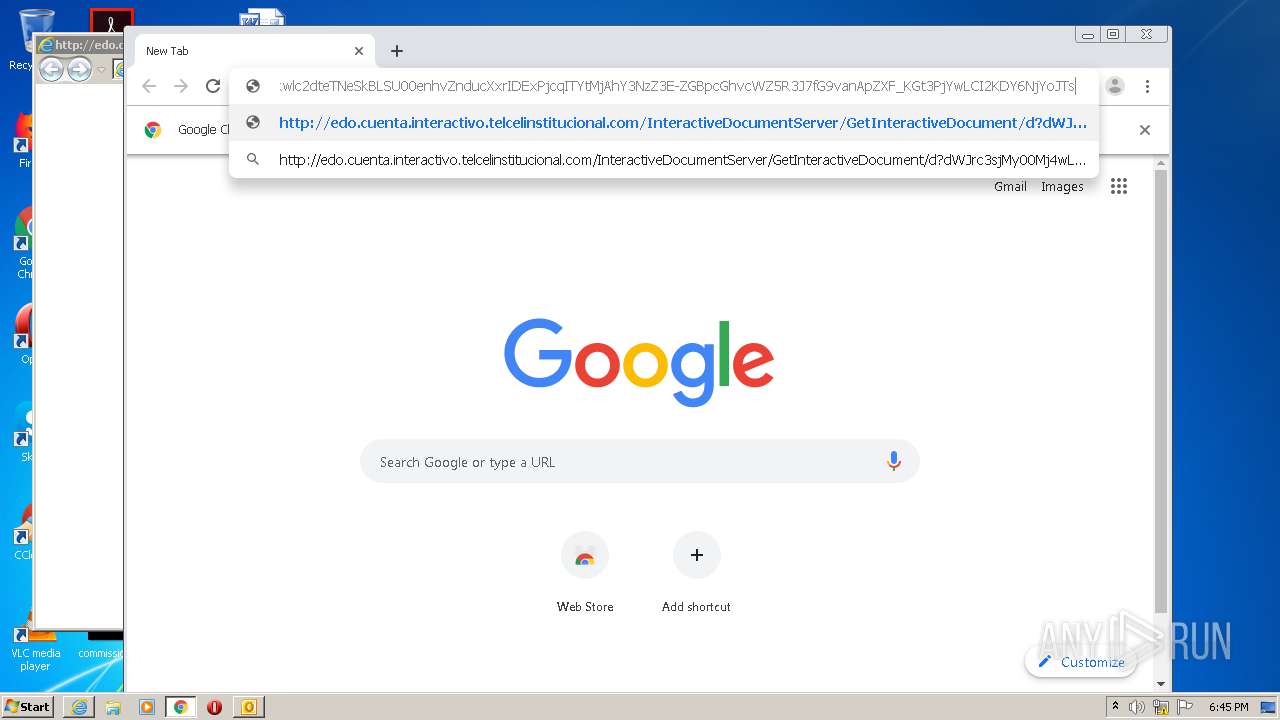
3940 | iexplore.exe | GET | — | 200.38.208.213:80 | http://edo.cuenta.interactivo.telcelinstitucional.com/InteractiveDocumentServer/GetInteractiveDocument/d?dWJrc3sjMy00Mj4wLyU5KiVzOj4uIz07cWZ3aWxmM1BMQVdUWiUoeWJ3Yit4YGFwPjE3NC4_Py8uMzEgenN6eC53aDssIjwsLjM1Ky4kKHBieypvbWF7eHA-MiBzc3YwZ2xkc3N3YGlwPjYgeHtrcWcyOkVLV0BJQiVrb3xgb296PldJTUJPWkwlc2dteTNeSkBLSU00enhvZnducXxrIDExPjcqITYtMjAhY3NzZ3E-ZGBpcGhvcWZ5R3J7fG9vanApZXF_KGt3PjYwLCI2KDY6NjYoJTs | MX | — | — | unknown |
2968 | chrome.exe | GET | — | 200.38.208.213:80 | http://edo.cuenta.interactivo.telcelinstitucional.com/InteractiveDocumentServer/GetInteractiveDocument/d?dWJrc3sjMy00Mj4wLyU5KiVzOj4uIz07cWZ3aWxmM1BMQVdUWiUoeWJ3Yit4YGFwPjE3NC4_Py8uMzEgenN6eC53aDssIjwsLjM1Ky4kKHBieypvbWF7eHA-MiBzc3YwZ2xkc3N3YGlwPjYgeHtrcWcyOkVLV0BJQiVrb3xgb296PldJTUJPWkwlc2dteTNeSkBLSU00enhvZnducXxrIDExPjcqITYtMjAhY3NzZ3E-ZGBpcGhvcWZ5R3J7fG9vanApZXF_KGt3PjYwLCI2KDY6NjYoJTs | MX | — | — | unknown |
2968 | chrome.exe | GET | — | 200.38.208.213:80 | http://edo.cuenta.interactivo.telcelinstitucional.com/InteractiveDocumentServer/GetInteractiveDocument/d?dWJrc3sjMy00Mj4wLyU5KiVzOj4uIz07cWZ3aWxmM1BMQVdUWiUoeWJ3Yit4YGFwPjE3NC4_Py8uMzEgenN6eC53aDssIjwsLjM1Ky4kKHBieypvbWF7eHA-MiBzc3YwZ2xkc3N3YGlwPjYgeHtrcWcyOkVLV0BJQiVrb3xgb296PldJTUJPWkwlc2dteTNeSkBLSU00enhvZnducXxrIDExPjcqITYtMjAhY3NzZ3E-ZGBpcGhvcWZ5R3J7fG9vanApZXF_KGt3PjYwLCI2KDY6NjYoJTs | MX | — | — | unknown |
2968 | chrome.exe | GET | 302 | 142.250.185.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
1748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1748 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2968 | chrome.exe | GET | 200 | 173.194.137.71:80 | http://r2---sn-aigzrn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=185.217.117.48&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1612896038&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | chrome.exe | 142.250.185.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 173.194.137.71:80 | r2---sn-aigzrn76.gvt1.com | Google Inc. | US | whitelisted |
1748 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2968 | chrome.exe | 200.38.208.213:80 | edo.cuenta.interactivo.telcelinstitucional.com | Uninet S.A. de C.V. | MX | unknown |
404 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
— | — | 200.38.208.213:80 | edo.cuenta.interactivo.telcelinstitucional.com | Uninet S.A. de C.V. | MX | unknown |
1748 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2968 | chrome.exe | 142.250.186.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.13.77:443 | accounts.google.com | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
edo.cuenta.interactivo.telcelinstitucional.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |