| File name: | KeePass.exe |
| Full analysis: | https://app.any.run/tasks/bec78b61-9d9c-4bc5-9c1c-c618c8c39960 |
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2023, 16:06:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E438C4379563D938E0BEF040E3FF16CD |
| SHA1: | 510E6639EDE57DE8EDFCC003EAE0BA95C2D9E743 |
| SHA256: | C3DA33EB4710273FA2EB87C35FB3E38DDCEDE5924641B672C2ACC1506B2A6ED2 |
| SSDEEP: | 49152:ifTdCmejIE61xttujlS6RsOuG1wrFH4w8sBNd/9fBHH:GdCmX/ujlS6uoRe |
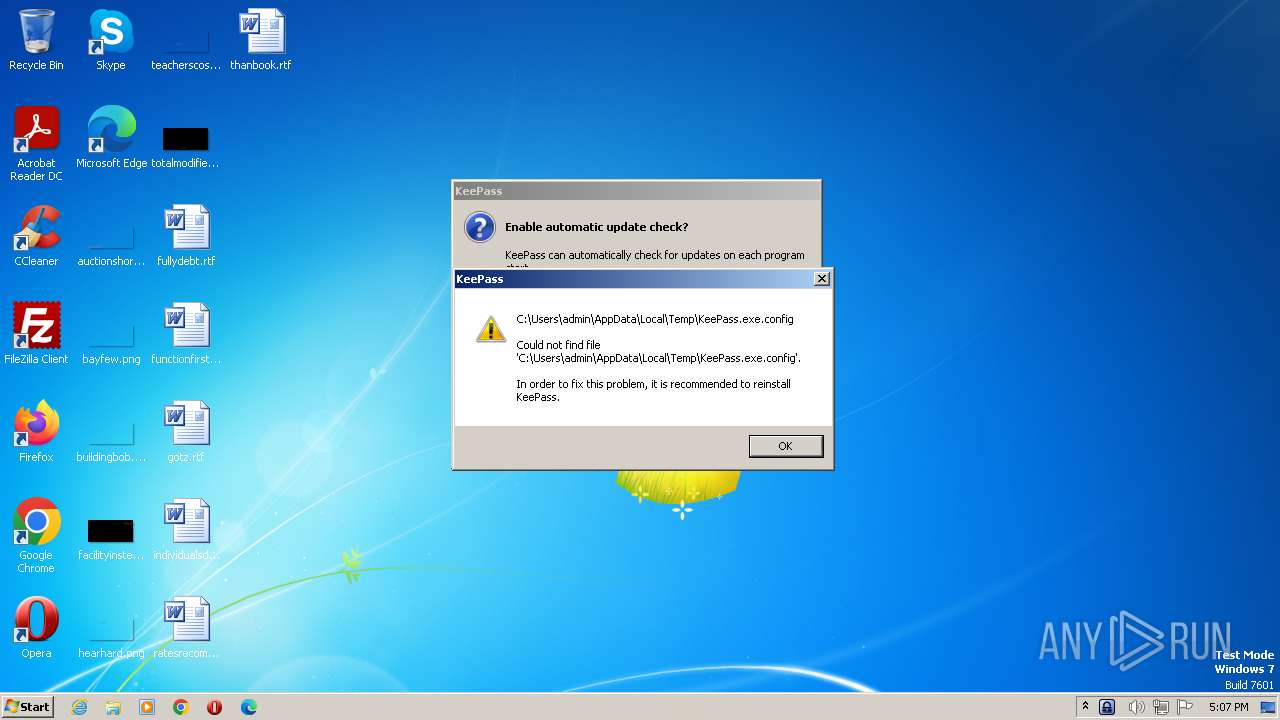
MALICIOUS
Starts Visual C# compiler
- KeePass.exe (PID: 3488)
SUSPICIOUS
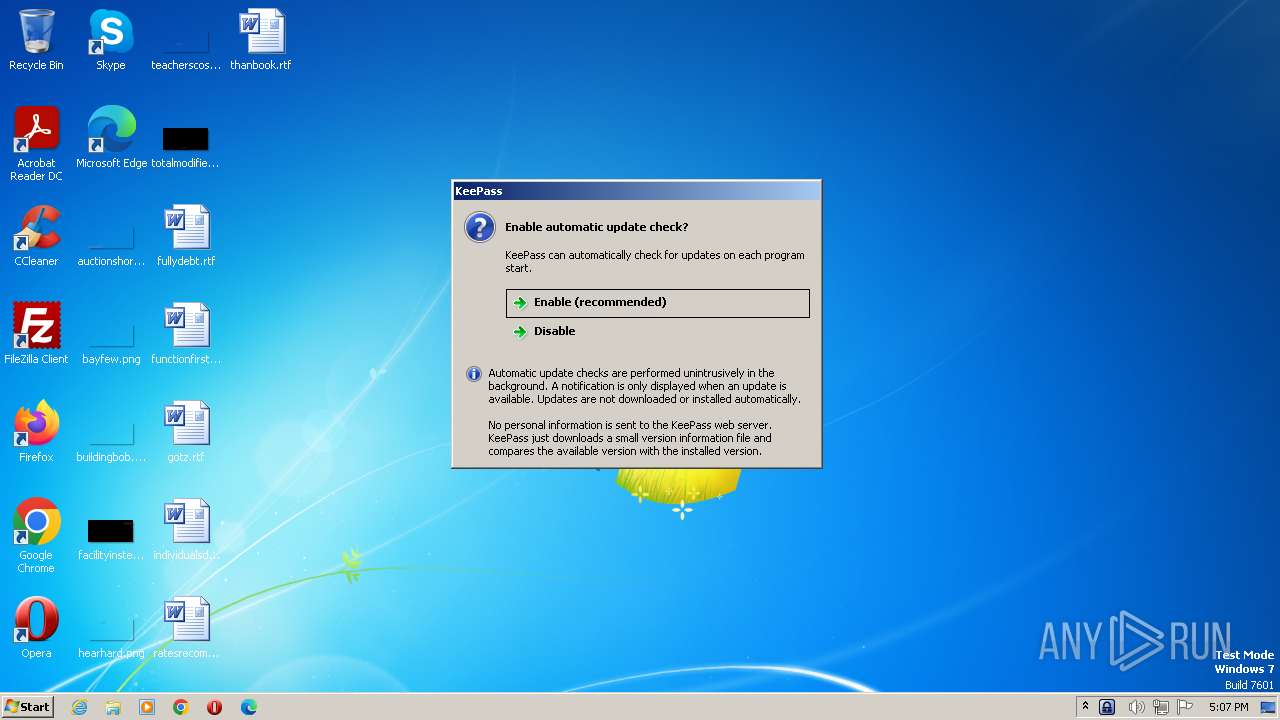
Checks Windows Trust Settings
- KeePass.exe (PID: 3488)
Reads security settings of Internet Explorer
- KeePass.exe (PID: 3488)
Executable content was dropped or overwritten
- csc.exe (PID: 3216)
Reads the Internet Settings
- KeePass.exe (PID: 3488)
Reads settings of System Certificates
- KeePass.exe (PID: 3488)
Uses .NET C# to load dll
- KeePass.exe (PID: 3488)
INFO
Checks supported languages
- KeePass.exe (PID: 3488)
- cvtres.exe (PID: 2888)
- csc.exe (PID: 3216)
Reads the computer name
- KeePass.exe (PID: 3488)
Create files in a temporary directory
- KeePass.exe (PID: 3488)
- cvtres.exe (PID: 2888)
- csc.exe (PID: 3216)
Reads the machine GUID from the registry
- csc.exe (PID: 3216)
- cvtres.exe (PID: 2888)
- KeePass.exe (PID: 3488)
The process checks LSA protection
- csc.exe (PID: 3216)
- cvtres.exe (PID: 2888)
- KeePass.exe (PID: 3488)
Reads Environment values
- KeePass.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| AssemblyVersion: | 2.53.1.20815 |
|---|---|
| ProductVersion: | 2.53.1.0 |
| ProductName: | KeePass |
| OriginalFileName: | KeePass.exe |
| LegalCopyright: | Copyright © 2003-2023 Dominik Reichl |
| InternalName: | KeePass.exe |
| FileVersion: | 2.53.1.0 |
| FileDescription: | KeePass |
| CompanyName: | Dominik Reichl |
| Comments: | KeePass Password Safe |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.53.1.0 |
| FileVersionNumber: | 2.53.1.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x304fde |
| UninitializedDataSize: | - |
| InitializedDataSize: | 67584 |
| CodeSize: | 3158016 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:02:08 10:33:50+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Feb-2023 10:33:50 |
| Debug artifacts: |
|
| Comments: | KeePass Password Safe |
| CompanyName: | Dominik Reichl |
| FileDescription: | KeePass |
| FileVersion: | 2.53.1.0 |
| InternalName: | KeePass.exe |
| LegalCopyright: | Copyright © 2003-2023 Dominik Reichl |
| OriginalFilename: | KeePass.exe |
| ProductName: | KeePass |
| ProductVersion: | 2.53.1.0 |
| Assembly Version: | 2.53.1.20815 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Feb-2023 10:33:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00302FE4 | 0x00303000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67559 |
.rsrc | 0x00306000 | 0x000104D8 | 0x00010600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.18568 |
.reloc | 0x00318000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.10839 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.75074 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.77375 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.25579 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.7266 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 7.95283 | 19883 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.65575 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.83026 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 5.21791 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2888 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES95EE.tmp" "c:\Users\admin\AppData\Local\Temp\CSC95ED.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 3216 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\j-0of351.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | KeePass.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
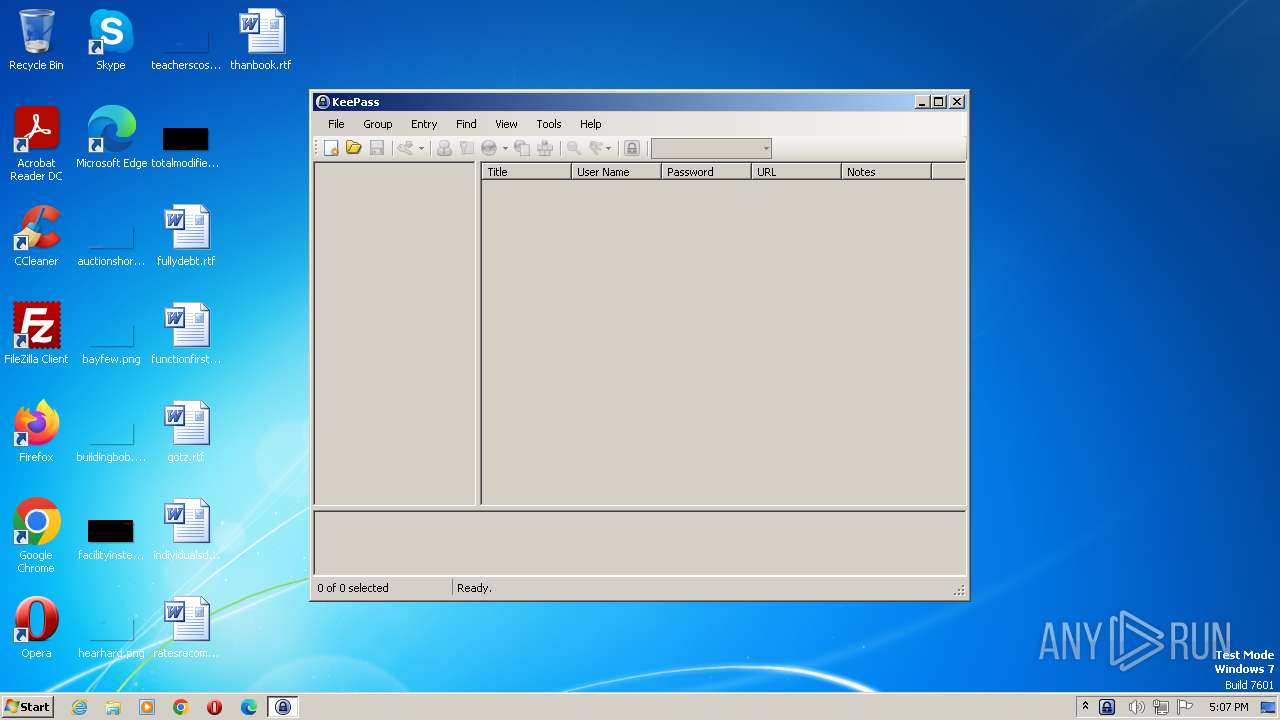
| 3488 | "C:\Users\admin\AppData\Local\Temp\KeePass.exe" | C:\Users\admin\AppData\Local\Temp\KeePass.exe | explorer.exe | ||||||||||||
User: admin Company: Dominik Reichl Integrity Level: MEDIUM Description: KeePass Exit code: 0 Version: 2.53.1.0 Modules
| |||||||||||||||
Total events
3 879
Read events
3 867
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3488) KeePass.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\178\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
0
Text files
3
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3488 | KeePass.exe | C:\Users\admin\AppData\Local\Temp\j-0of351.0.cs | text | |
MD5:44FFDD57199897350743823CA3461201 | SHA256:CAA8BD2C0FB4989DAFD02CBFC16649A3BB1A3CB42D6A9B337BD3232AC879E5A8 | |||
| 3216 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC95ED.tmp | res | |
MD5:ACB1130CBA75024D6F69B7BF42491EDD | SHA256:A55555E782D961E25538CAEC8D227E4AE1F6D549EBECDA117900F2B1B86DCF15 | |||
| 3216 | csc.exe | C:\Users\admin\AppData\Local\Temp\j-0of351.out | text | |
MD5:9660F4019598889FA8410FBB27A52E4A | SHA256:EB13C7BF9D8F13BB8BA69E6ED74C6CDF0C311E4E307B61D5A136C6D7A7D0FC45 | |||
| 2888 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES95EE.tmp | o | |
MD5:E4097625B36FC5A4DCE435C46A079E6A | SHA256:69E1A7ACD1BA18D27D267C814E071337896C08A2D9DCF2F296EF7DD94E641A99 | |||
| 3488 | KeePass.exe | C:\Users\admin\AppData\Local\Temp\j-0of351.cmdline | text | |
MD5:A209D5B005DC53AD63AD3E7B8398C5C4 | SHA256:D784975F7BC44442D22AAEBB59E2288E7A27B472671714320A57886B47405677 | |||
| 3216 | csc.exe | C:\Users\admin\AppData\Local\Temp\j-0of351.dll | executable | |
MD5:25C6F92D869F8FBEAAE9832D7C9D66FA | SHA256:FC64AC4A06A9073C4395645029D11F5A5DBA55386E1617648677AF4CC0DA8D5C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3488 | KeePass.exe | 92.205.64.102:443 | www.dominik-reichl.de | Host Europe GmbH | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dominik-reichl.de |
| suspicious |
dns.msftncsi.com |
| shared |