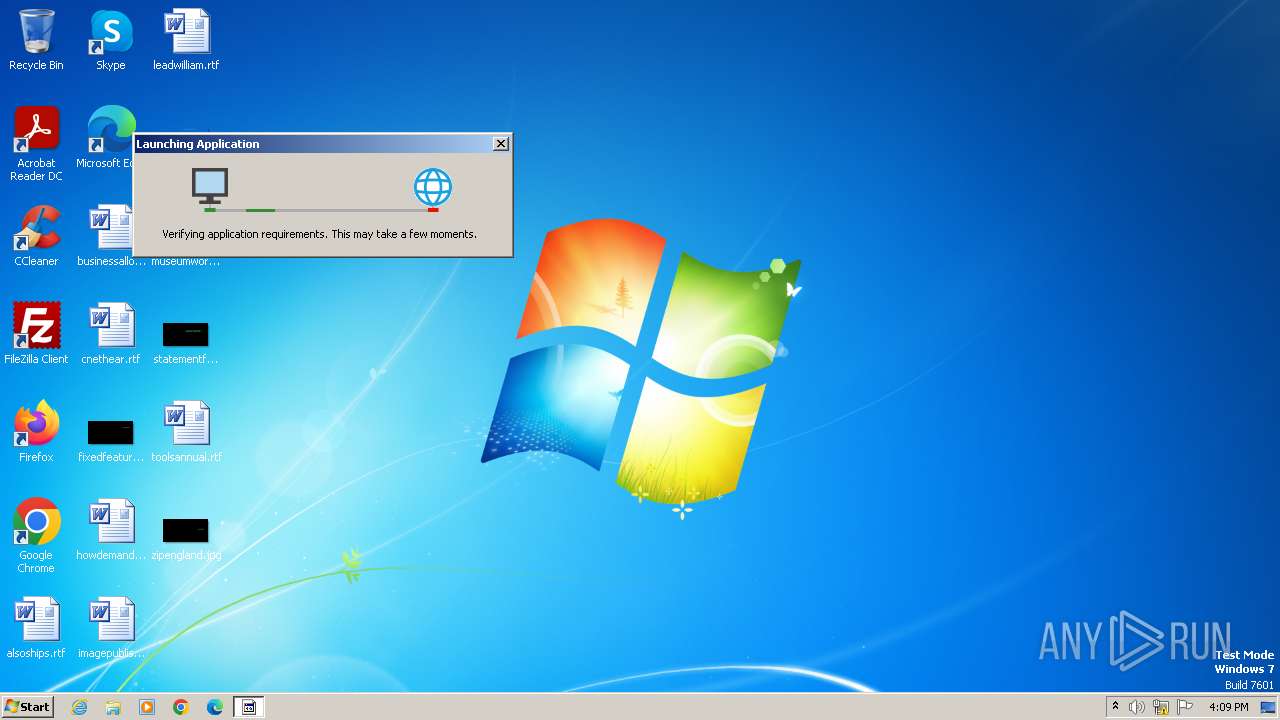
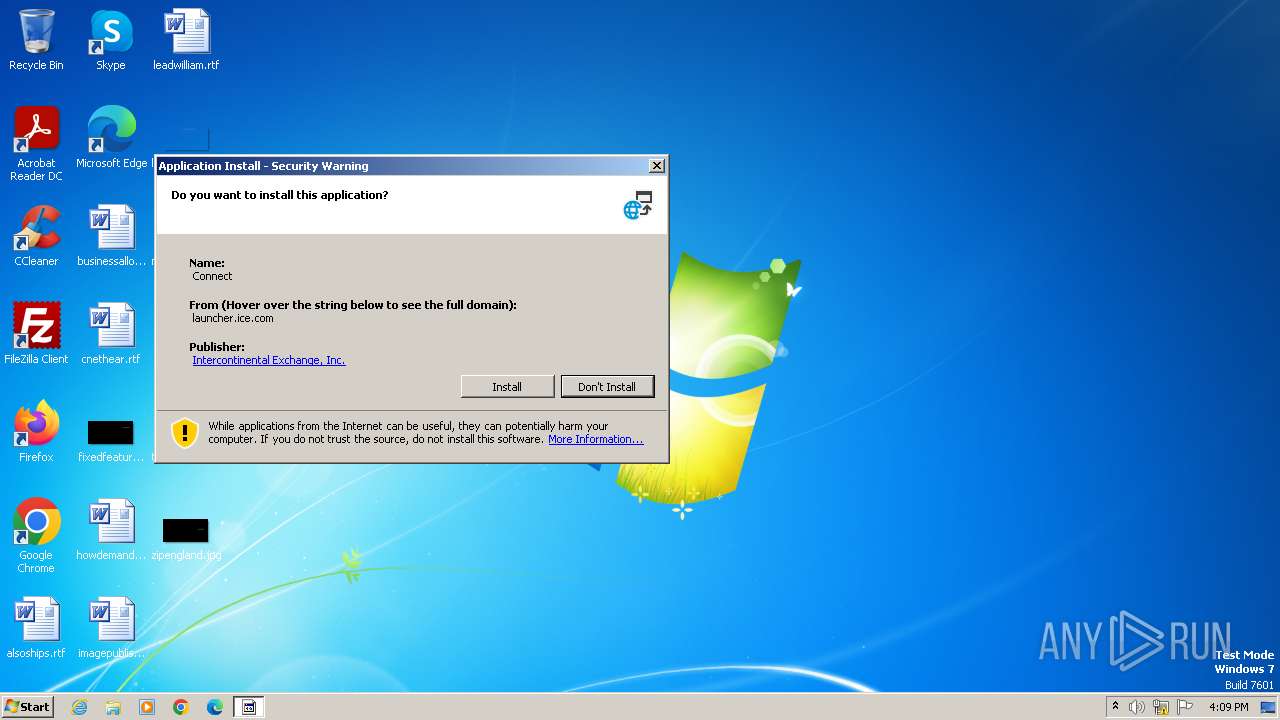
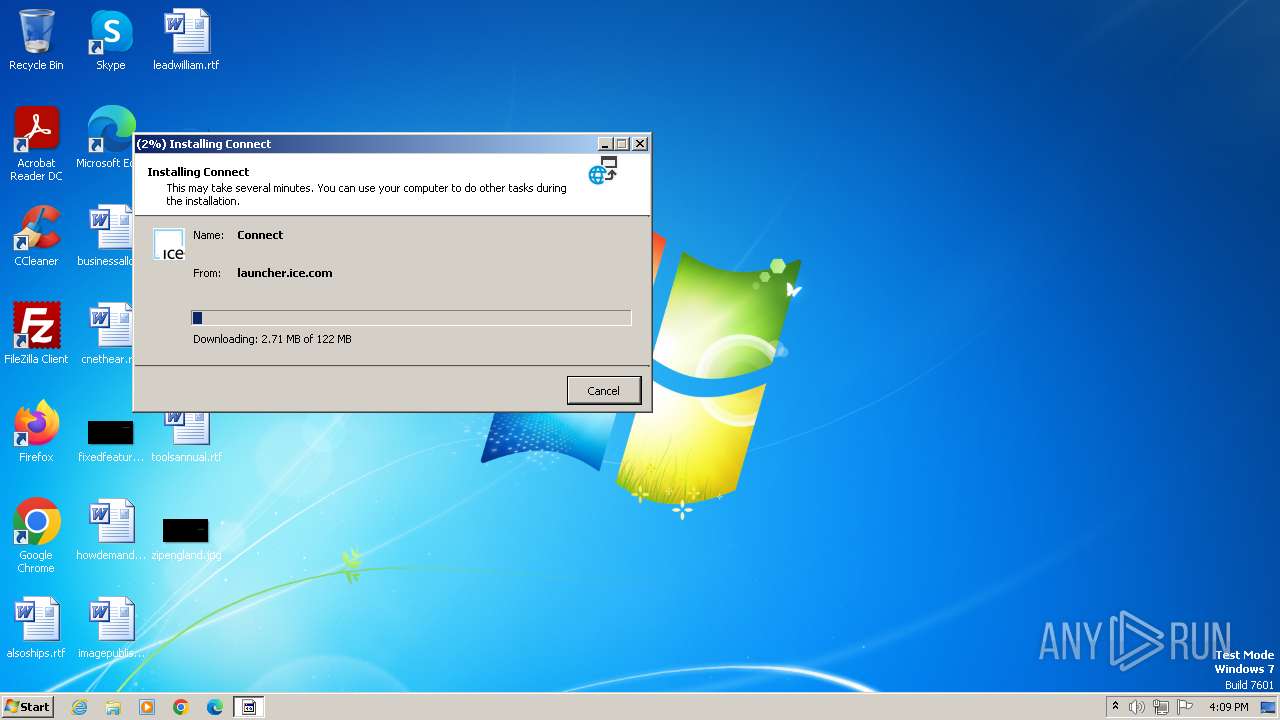
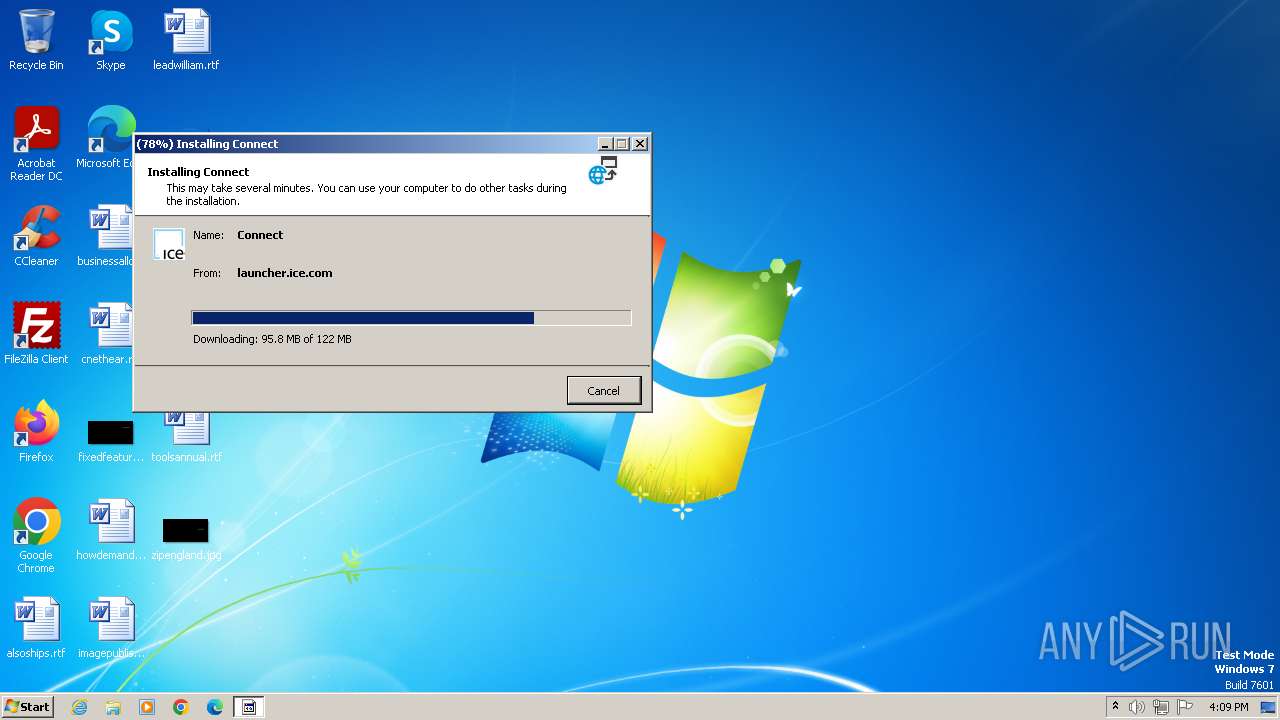
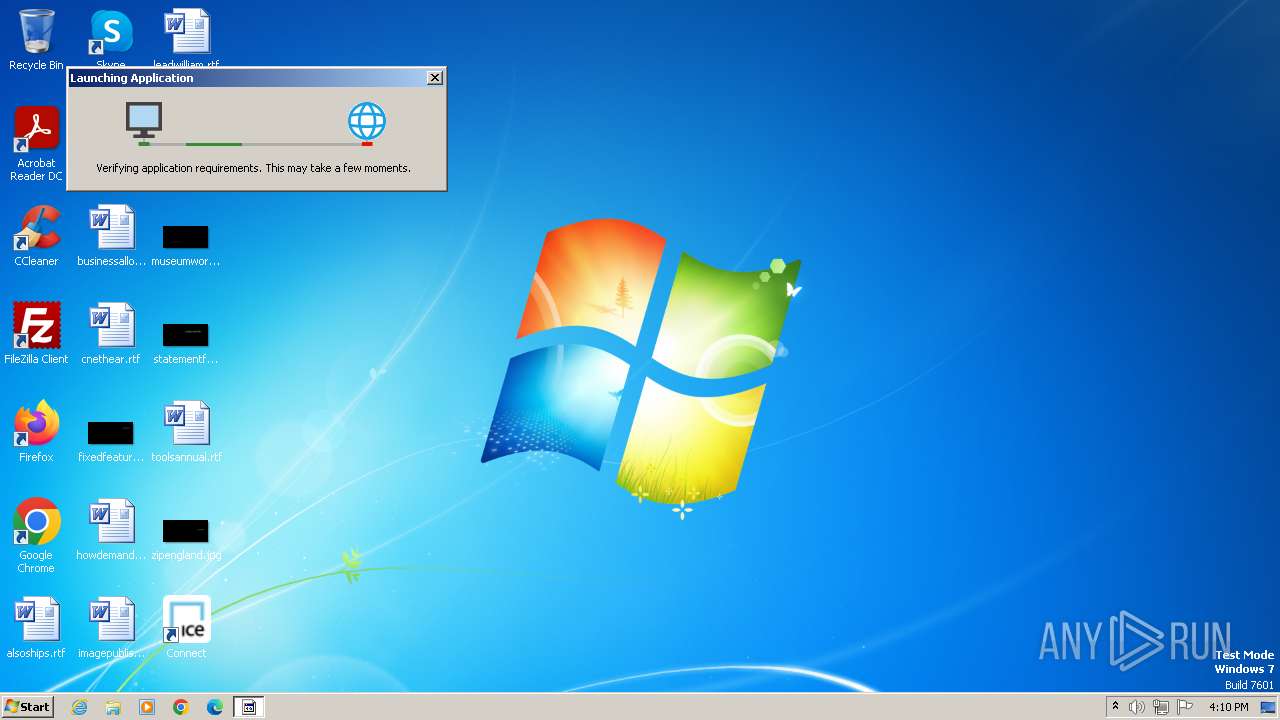
| URL: | https://launcher.ice.com/launcher/download/Connect.application |
| Full analysis: | https://app.any.run/tasks/5efa0c91-37bc-4ac0-8022-c3d071092555 |
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2024, 15:09:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0AD63BF3EB13EC24A640D37D61514357 |
| SHA1: | 0BE7E3F4FB9814623176AF6857D95BBA4F42715E |
| SHA256: | C3D91D682557EB083E216A166092F95FC129F7137087742F082B9E65E5C6A692 |
| SSDEEP: | 3:N8EQySoGuvEsR4Jk9/AGRQuMQn:2EQyPQm4s/AGGM |
MALICIOUS
Create files in the Startup directory
- ICE.Launcher.Client.exe (PID: 2068)
Drops the executable file immediately after the start
- dfsvc.exe (PID: 2028)
SUSPICIOUS
Reads settings of System Certificates
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.exe (PID: 1008)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
Checks Windows Trust Settings
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
Reads the Internet Settings
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.exe (PID: 1008)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
Reads Internet Explorer settings
- dfsvc.exe (PID: 2028)
The process drops C-runtime libraries
- dfsvc.exe (PID: 2028)
Searches for installed software
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 2028)
Process drops legitimate windows executable
- dfsvc.exe (PID: 2028)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 2028)
Creates a software uninstall entry
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
INFO
Checks supported languages
- dfsvc.exe (PID: 2028)
- wmpnscfg.exe (PID: 1588)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.exe (PID: 1008)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
- msiexec.exe (PID: 3260)
Disables trace logs
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.exe (PID: 1008)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
Checks proxy server information
- dfsvc.exe (PID: 2028)
Reads the computer name
- dfsvc.exe (PID: 2028)
- wmpnscfg.exe (PID: 1588)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.exe (PID: 1008)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
- msiexec.exe (PID: 3260)
Application launched itself
- iexplore.exe (PID: 3972)
Reads the machine GUID from the registry
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.exe (PID: 1008)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
- msiexec.exe (PID: 3260)
Reads Environment values
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.exe (PID: 1008)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 2028)
Reads the software policy settings
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.exe (PID: 1008)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1280)
Manual execution by a user
- wmpnscfg.exe (PID: 1588)
- rundll32.exe (PID: 2456)
Creates files or folders in the user directory
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.LogMoverAgent.exe (PID: 1596)
- ICE.Launcher.Client.exe (PID: 1008)
Create files in a temporary directory
- dfsvc.exe (PID: 2028)
- ICE.Launcher.Client.exe (PID: 2068)
Reads product name
- ICE.Launcher.Client.exe (PID: 2068)
- ICE.Launcher.Client.exe (PID: 1008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
12
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1008 | "C:\Users\admin\AppData\Local\Apps\2.0\OQVLXTZK.4P5\AK6KX289.K1P\conn...app_52f9374e80c65aae_0005.0004_0e57124701b7302e\ICE.Launcher.Client.exe" | C:\Users\admin\AppData\Local\Apps\2.0\OQVLXTZK.4P5\AK6KX289.K1P\conn...app_52f9374e80c65aae_0005.0004_0e57124701b7302e\ICE.Launcher.Client.exe | dfsvc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ICE.Launcher.Client Exit code: 4294967295 Version: 5.4.3.4 Modules
| |||||||||||||||
| 1280 | "ICE.Launcher.Client.LogMoverAgent.exe" C:\Users\admin\AppData\Local\ICE\Connect\Logs\logger_20240531.log 100 1008 https://launcher.ice.com/launcher plugin/Logger/LoggingEvent null 60 0 7676 768d3e85-47f3-49d1-a818-ca885cb5ccef | C:\Users\admin\AppData\Local\Apps\2.0\OQVLXTZK.4P5\AK6KX289.K1P\conn...app_52f9374e80c65aae_0005.0004_0e57124701b7302e\ICE.Launcher.Client.LogMoverAgent.exe | ICE.Launcher.Client.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ICE.Launcher-5.4.3 Exit code: 0 Version: 5.4.3.4 Modules
| |||||||||||||||
| 1412 | "msiexec" /i C:\Users\admin\AppData\Local\Temp\iws-install-win-32.msi /q | C:\Windows\System32\msiexec.exe | — | ICE.Launcher.Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1620 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | "ICE.Launcher.Client.LogMoverAgent.exe" C:\Users\admin\AppData\Local\ICE\Connect\Logs\logger_20240531.log 100 2068 https://launcher.ice.com/launcher plugin/Logger/LoggingEvent null 60 0 7575 21fcb1b5-8d43-4c26-8a35-8cb443360e17 | C:\Users\admin\AppData\Local\Apps\2.0\OQVLXTZK.4P5\AK6KX289.K1P\conn...app_52f9374e80c65aae_0005.0004_0e57124701b7302e\ICE.Launcher.Client.LogMoverAgent.exe | ICE.Launcher.Client.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ICE.Launcher-5.4.3 Version: 5.4.3.4 Modules
| |||||||||||||||
| 2028 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 2040 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: ClickOnce Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\AppData\Local\Apps\2.0\OQVLXTZK.4P5\AK6KX289.K1P\conn...app_52f9374e80c65aae_0005.0004_0e57124701b7302e\ICE.Launcher.Client.exe" | C:\Users\admin\AppData\Local\Apps\2.0\OQVLXTZK.4P5\AK6KX289.K1P\conn...app_52f9374e80c65aae_0005.0004_0e57124701b7302e\ICE.Launcher.Client.exe | dfsvc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ICE.Launcher.Client Version: 5.4.3.4 Modules
| |||||||||||||||
| 2456 | "C:\Windows\System32\rundll32.exe" dfshim.dll,ShOpenVerbApplication https://launcher.ice.com/launcher/download/Connect.application | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3260 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
37 265
Read events
35 850
Write events
1 259
Delete events
156
Modification events
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31109996 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31109996 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3972) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
117
Suspicious files
196
Text files
214
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2028 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\7XRYH3PN.PXM\RWDCYXJQ.RHT\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:0BD1ADFC157CE9A5039BE7E4294604D5 | SHA256:87201D9306B778A2A5BB80C58CE673C55B6E2E528671C09EE73BD8D0BC1E2930 | |||
| 2028 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\BOAQPO36.JNG\MTTQOEXE.30R.application | xml | |
MD5:221F94B0FBCEBDC9611EB8E702346BDD | SHA256:F7EE0C3C731A03DEDF85551608EAC5195E53B2DE1F5D8CD9DBB7B5FD728BBA2B | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{BDDCF689-1F5F-11EF-9E36-12A9866C77DE}.dat | binary | |
MD5:B5603E4F2CC3ACAFA48A1601FD71C824 | SHA256:13B93A8DE2E27F1864FFA906B6DB06617F3B01DD1869D438DE62DD60B8505615 | |||
| 2028 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\7XRYH3PN.PXM\RWDCYXJQ.RHT\ICE.Launcher.Client.exe.manifest | xml | |
MD5:C5257A51DD3E7046954E85DC7C0D4519 | SHA256:F63B3C45D9EB5F172DC175AA320FED9C4F7C2EC8C6FD8C03C10DA57F6E4521FB | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF4DC31751B18C6721.TMP | gmc | |
MD5:529EDCFBBE5FE482A0779975ADD9CCB4 | SHA256:71F0574A38CFB5F4C5ED1AFD9937AE81642ED258AD598155002F2F232380AE1B | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:A3D92EA56EBC6C5F829367951ECAE3B9 | SHA256:EF3740E63B3C090A606C6E000D6F9D6C80F3187BB439CEFB13525028749FD29B | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:186CC118CEE6571F854DEA775ACD4E3F | SHA256:691C1610FFAE828AF0CBB45B92B846EA34BA18C0F3B676A8CA5F37FDFE155F9D | |||
| 4036 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Connect[1].application | xml | |
MD5:221F94B0FBCEBDC9611EB8E702346BDD | SHA256:F7EE0C3C731A03DEDF85551608EAC5195E53B2DE1F5D8CD9DBB7B5FD728BBA2B | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFE5D80DF276A8F0F2.TMP | gmc | |
MD5:7B1207D25F83C9E43A8A52090FC97017 | SHA256:DC4B002A5A9289875965C11CA3A30FF3869FEA4D9EEAD2DFE6DF8927FCC3CDA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
15
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4036 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9b5f474efa3999f3 | unknown | — | — | unknown |
1088 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4765deda26f5bdfc | unknown | — | — | unknown |
4036 | iexplore.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ee8e7929c6b4ef0e | unknown | — | — | unknown |
4036 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4036 | iexplore.exe | 158.224.70.13:443 | launcher.ice.com | SIAC-SFTI | US | unknown |
4036 | iexplore.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
4036 | iexplore.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
4036 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2028 | dfsvc.exe | 158.224.70.13:443 | launcher.ice.com | SIAC-SFTI | US | unknown |
1088 | svchost.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
2068 | ICE.Launcher.Client.exe | 158.224.70.13:443 | launcher.ice.com | SIAC-SFTI | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
launcher.ice.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iws.ice.com |
| unknown |
Threats
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|