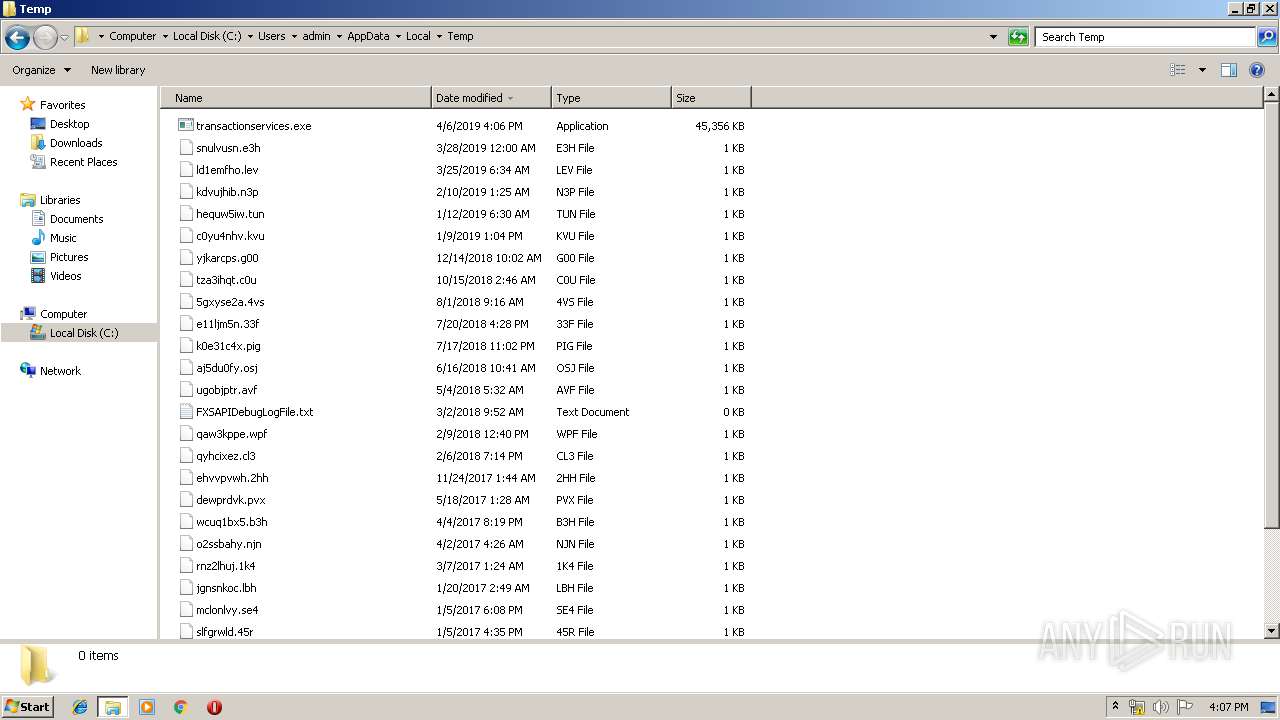
| File name: | http://194.63.143.226/transactionservices.exe |
| Full analysis: | https://app.any.run/tasks/740c2021-2f9a-4369-a42b-db2f9ccea1ce |
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2019, 15:05:32 |
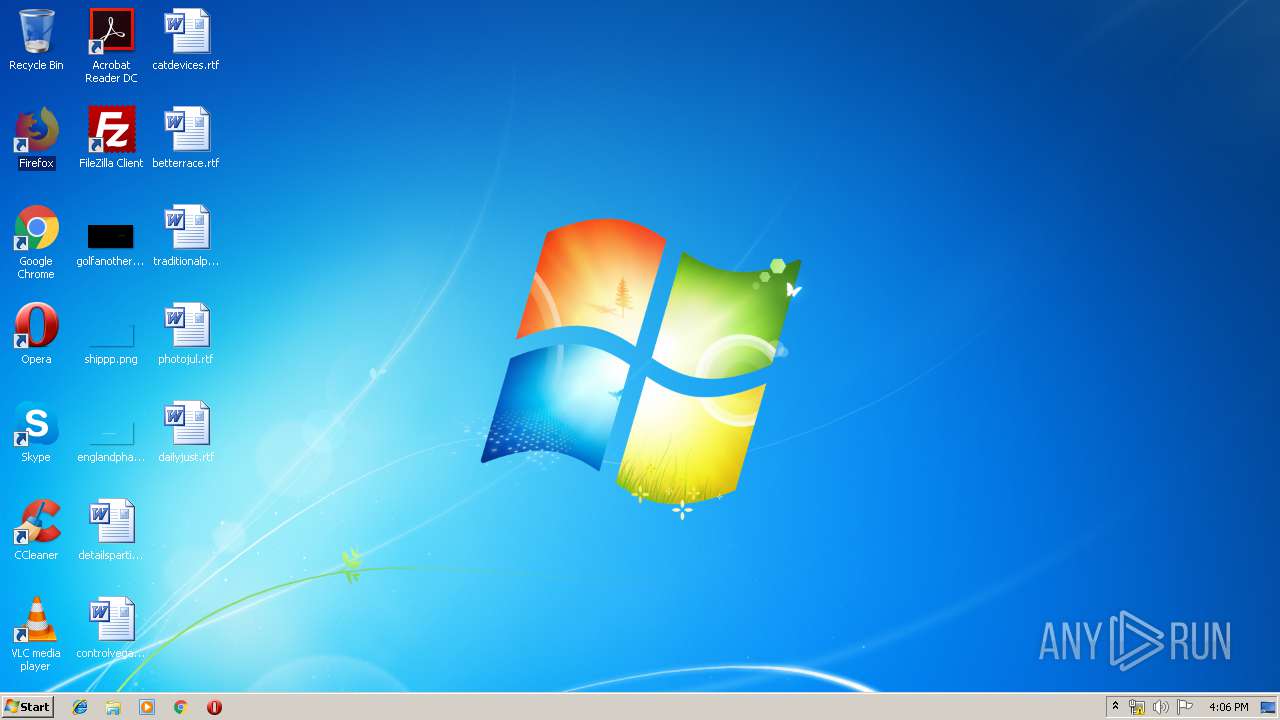
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 93676F464D4265B52A89DE8C886DDDAD |
| SHA1: | F4DC8DEA1AFBB8AC2554026C88A11B08F9152252 |
| SHA256: | C3A7CF30428689A44328090B994CE593BBF2A68141FCBEFB899DEE4FEC336198 |
| SSDEEP: | 786432:YsFKEWWGlso5EYWSsXtHnrCs6xOIb9Fb5nltVyX6xTFOX/7RGRp6hPbzLk2Lum4R:YsMbZd5EwsdCJxOIJFllL9xT0DRxh7a |
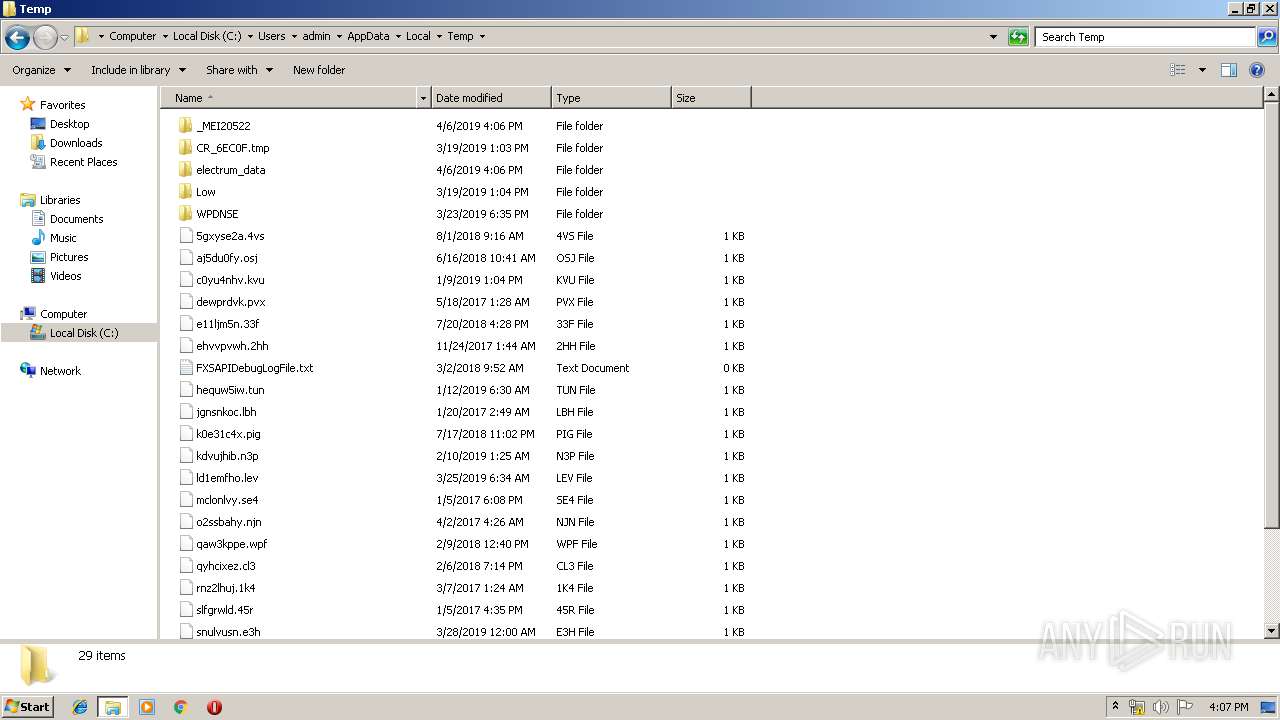
MALICIOUS
Loads dropped or rewritten executable
- transactionservices.exe (PID: 3168)
SUSPICIOUS
Application launched itself
- transactionservices.exe (PID: 2052)
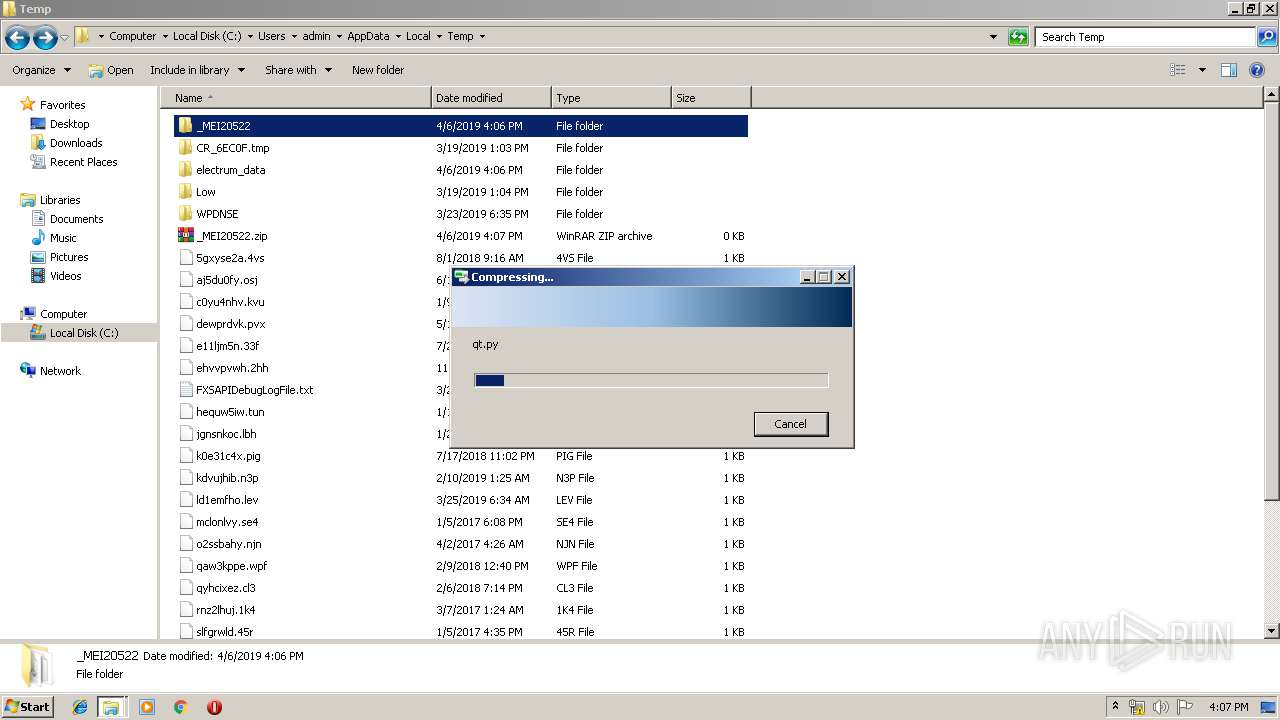
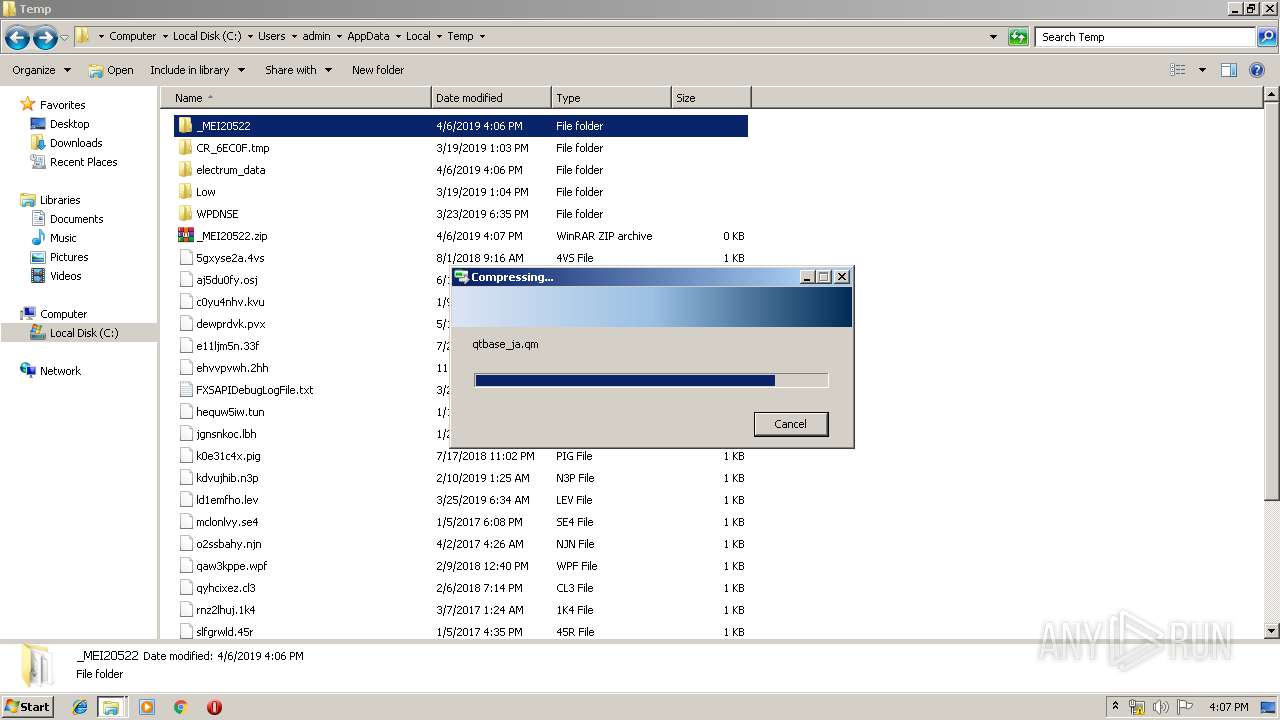
Loads Python modules
- transactionservices.exe (PID: 3168)
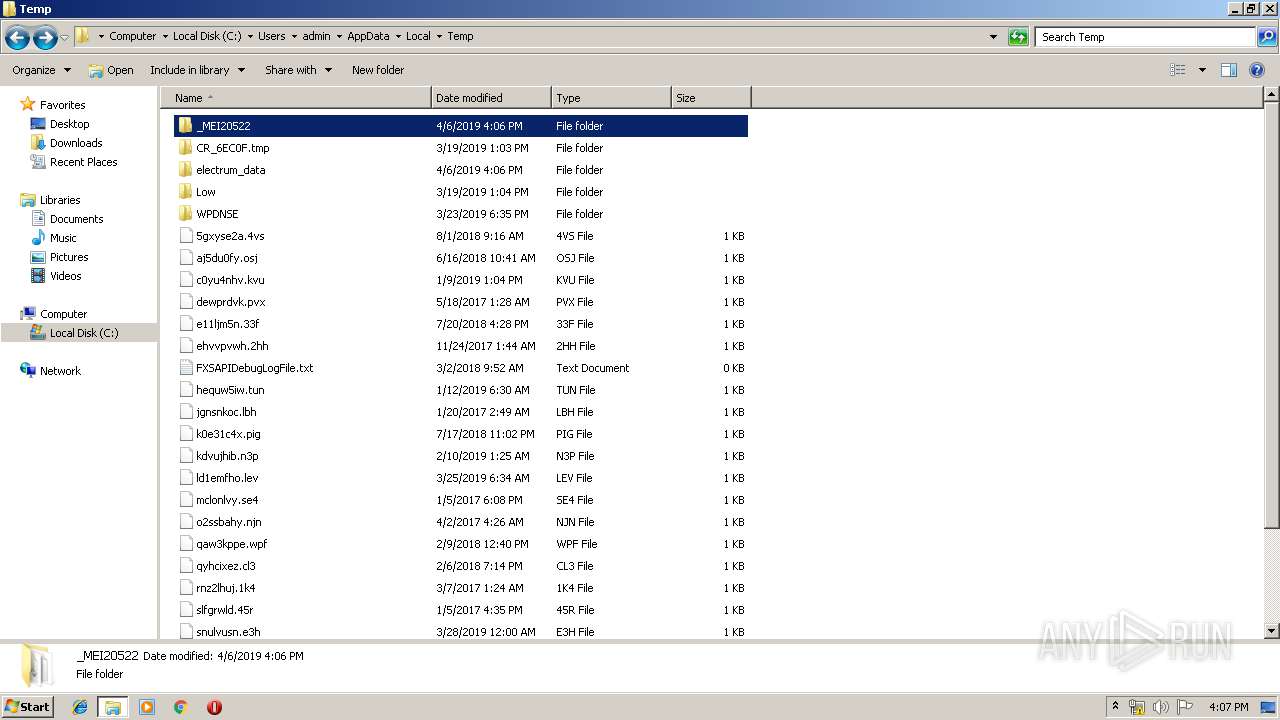
Executable content was dropped or overwritten
- transactionservices.exe (PID: 2052)
INFO
Dropped object may contain TOR URL's
- transactionservices.exe (PID: 2052)
Dropped object may contain Bitcoin addresses
- transactionservices.exe (PID: 2052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:43:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 125952 |
| InitializedDataSize: | 107520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79d3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Sep-2018 14:43:33 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:43:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001EB34 | 0x0001EC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64811 |
.rdata | 0x00020000 | 0x0000B164 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.09995 |
.data | 0x0002C000 | 0x0000E688 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.92387 |
.gfids | 0x0003B000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.83952 |
.rsrc | 0x0003C000 | 0x0000D000 | 0x0000CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.159 |
.reloc | 0x00049000 | 0x000017B4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65332 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.90294 | 146 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 | 1.734 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 1.15935 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.17452 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.65167 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.47831 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.52336 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.66811 | 1640 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 2.80722 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 3.20642 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1304 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | "C:\Users\admin\AppData\Local\Temp\transactionservices.exe" | C:\Users\admin\AppData\Local\Temp\transactionservices.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3168 | "C:\Users\admin\AppData\Local\Temp\transactionservices.exe" | C:\Users\admin\AppData\Local\Temp\transactionservices.exe | transactionservices.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
253
Read events
253
Write events
0
Delete events
0
Modification events
Executable files
200
Suspicious files
412
Text files
939
Unknown types
85
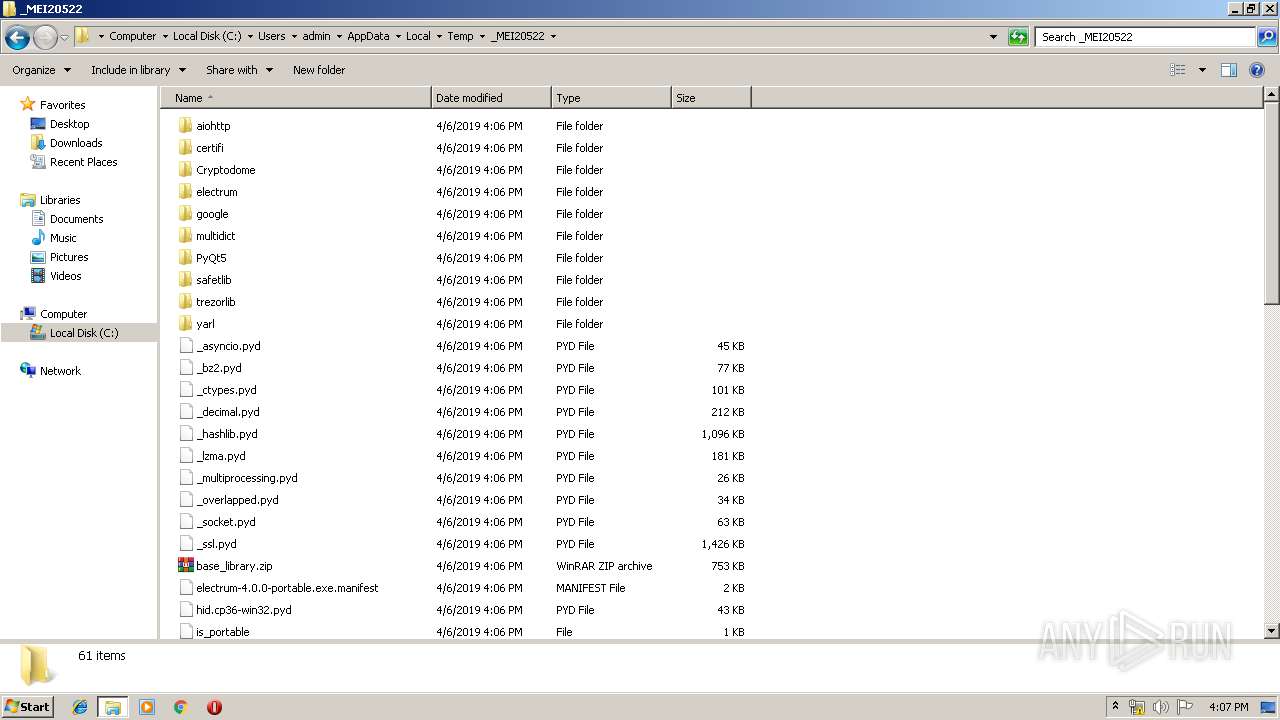
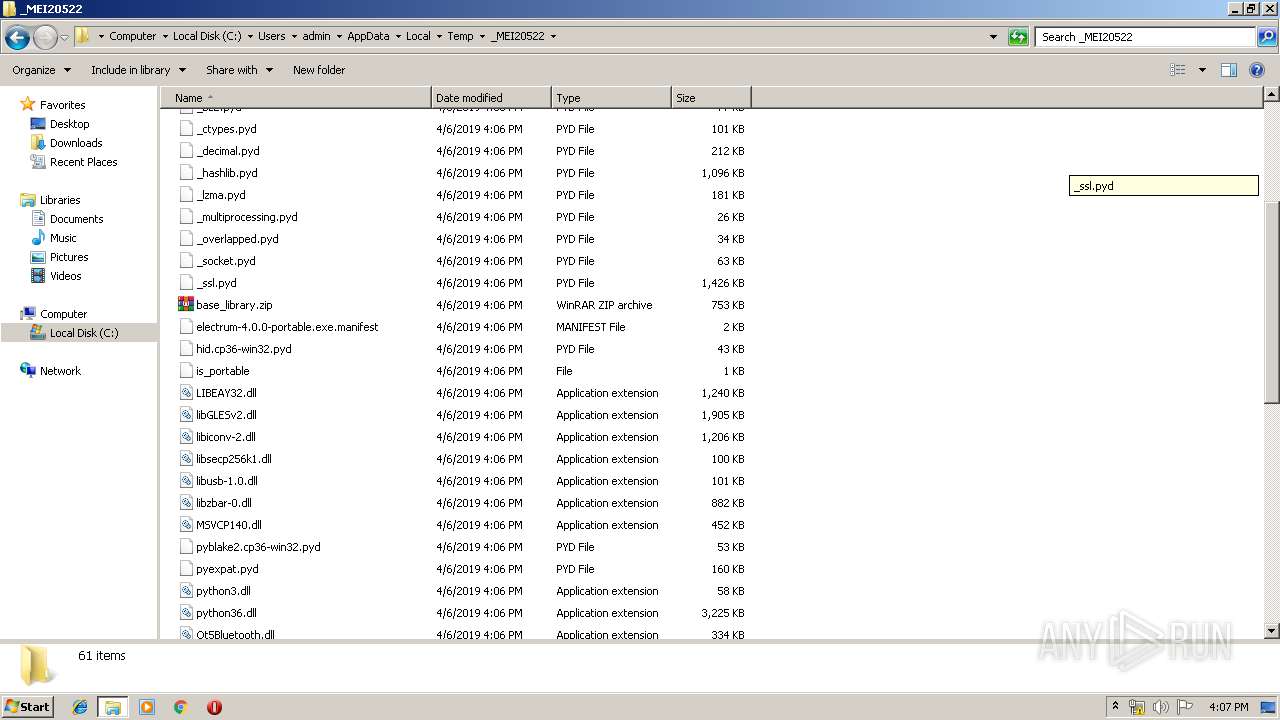
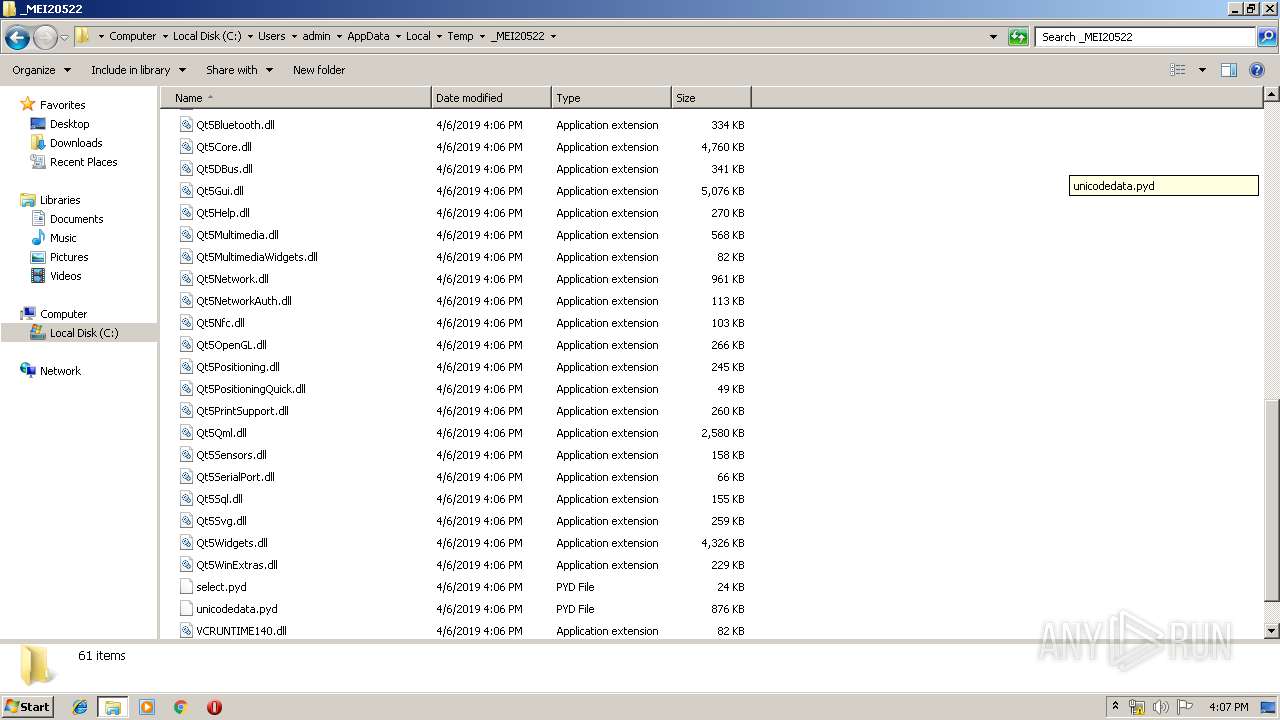
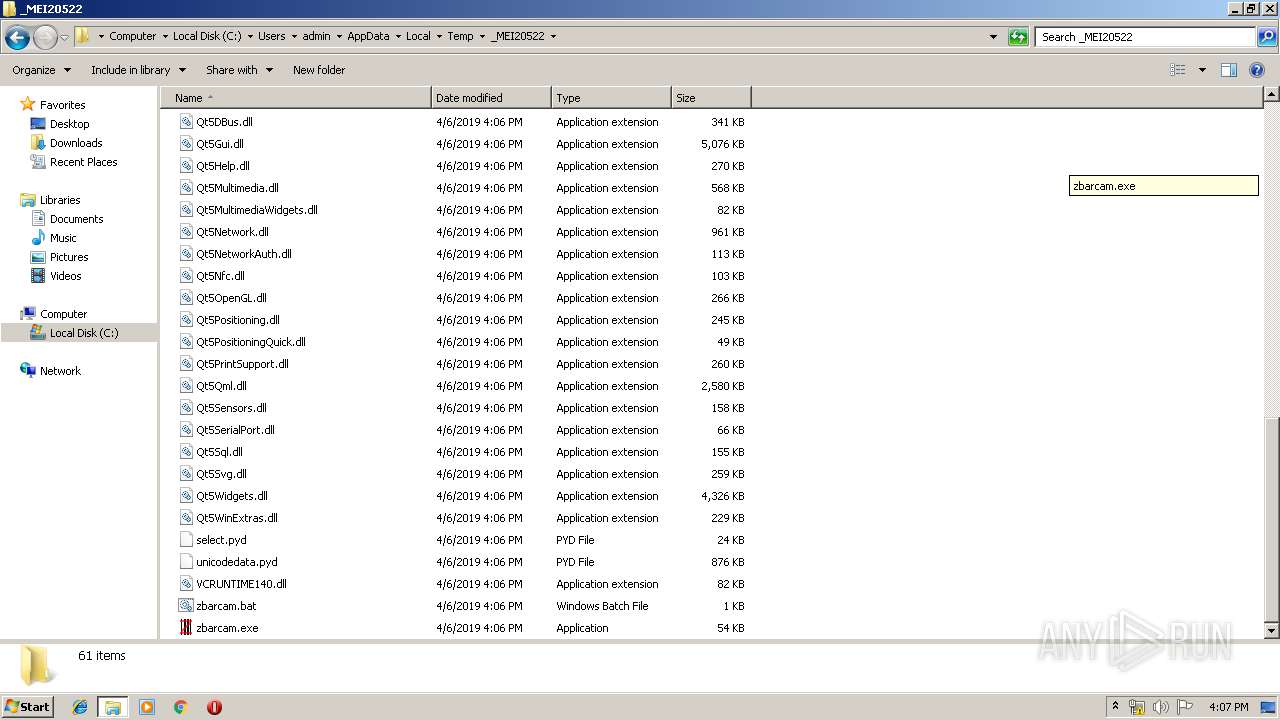
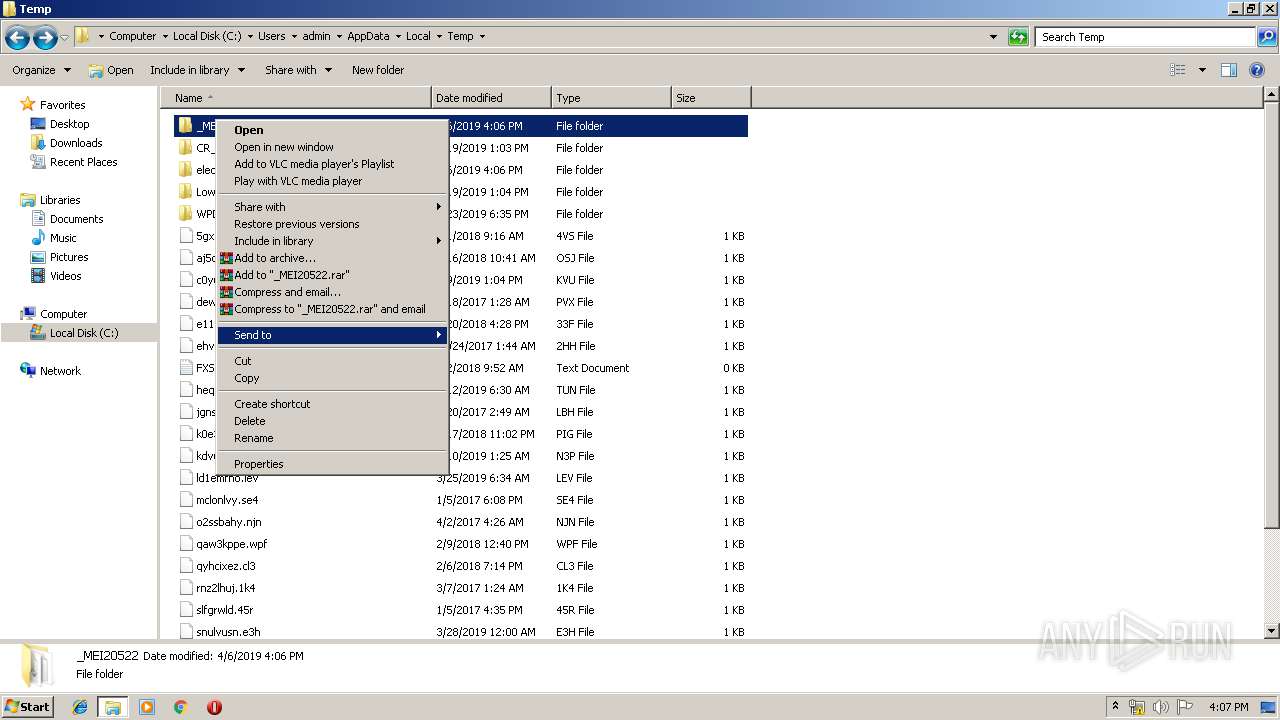
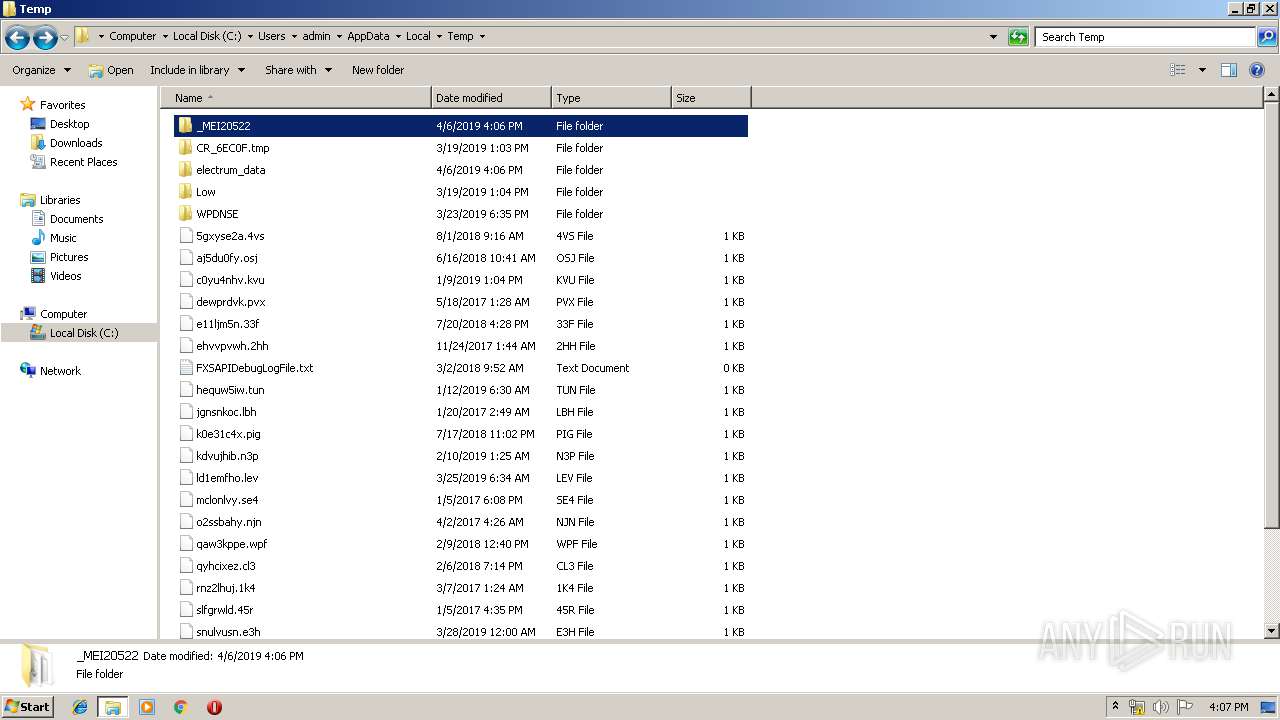
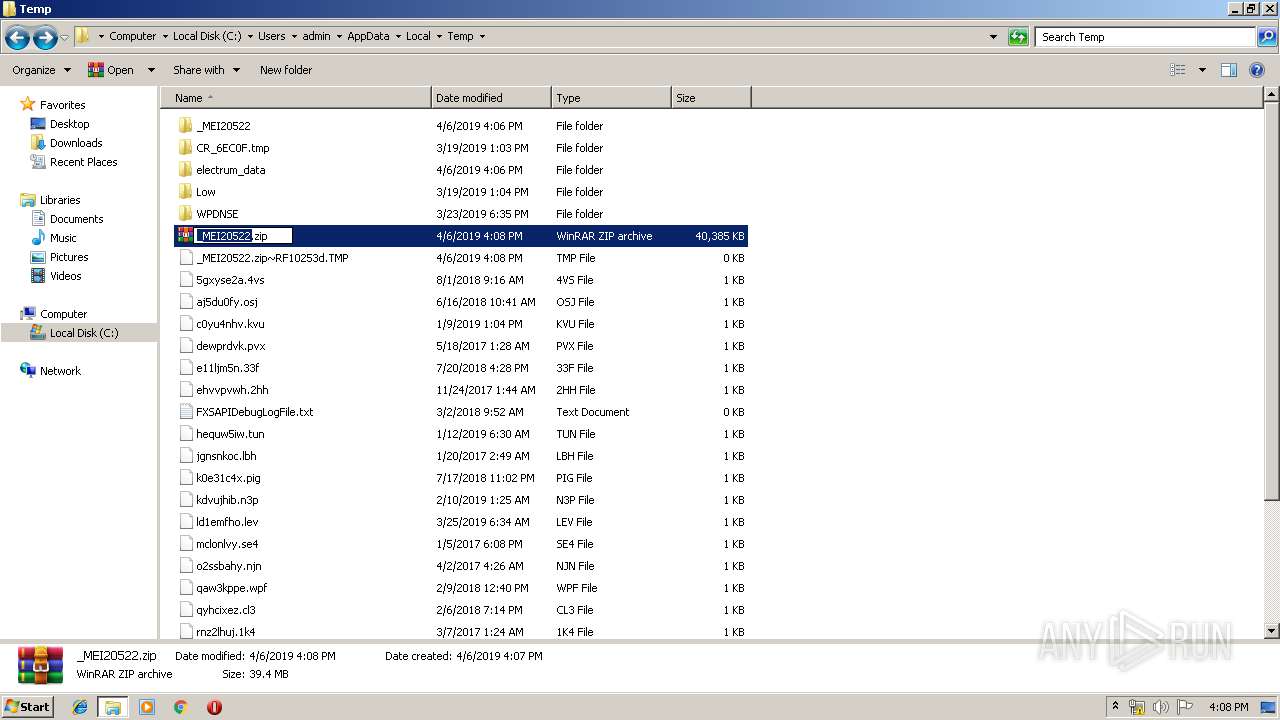
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_raw_blowfish.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_ARC4.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_raw_aes.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_raw_cfb.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_raw_ctr.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_raw_cbc.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_raw_des3.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_raw_cast.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_Salsa20.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 2052 | transactionservices.exe | C:\Users\admin\AppData\Local\Temp\_MEI20522\Cryptodome\Cipher\_raw_aesni.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report