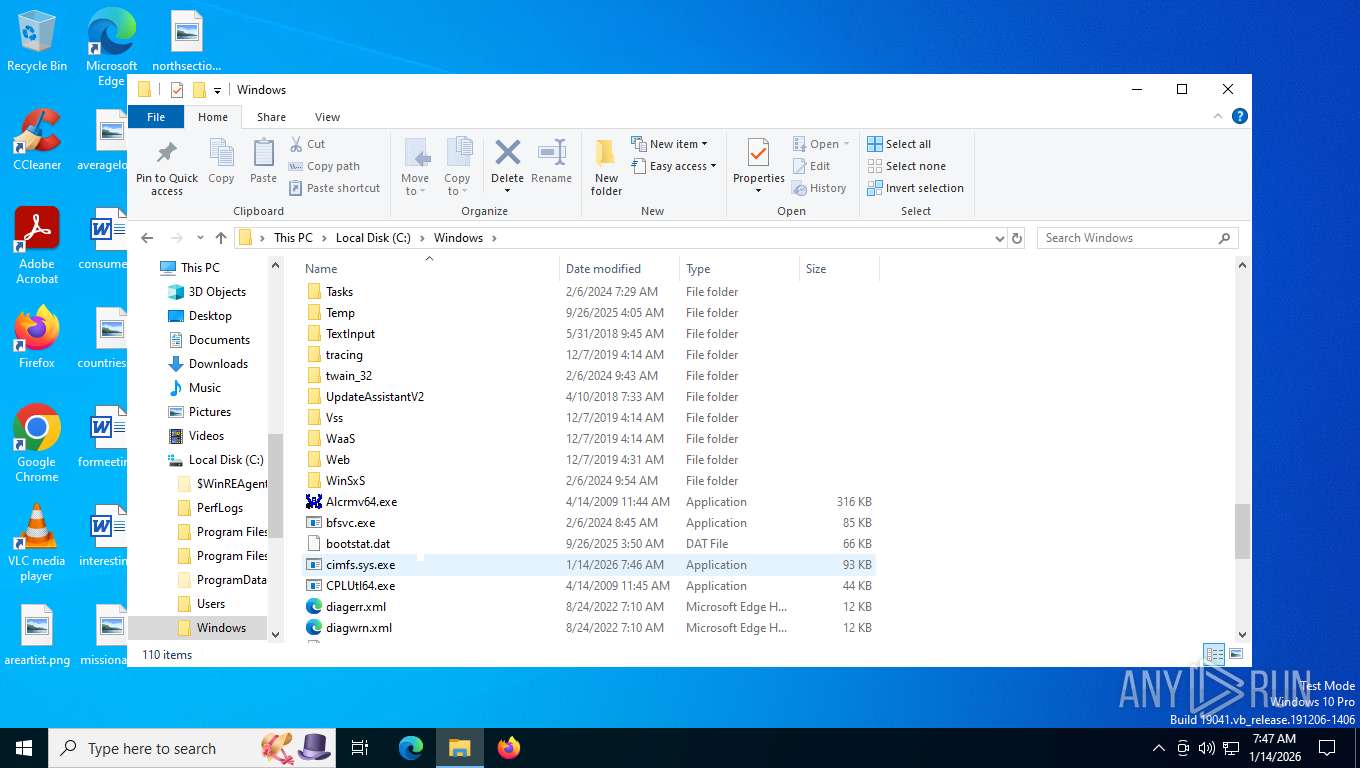
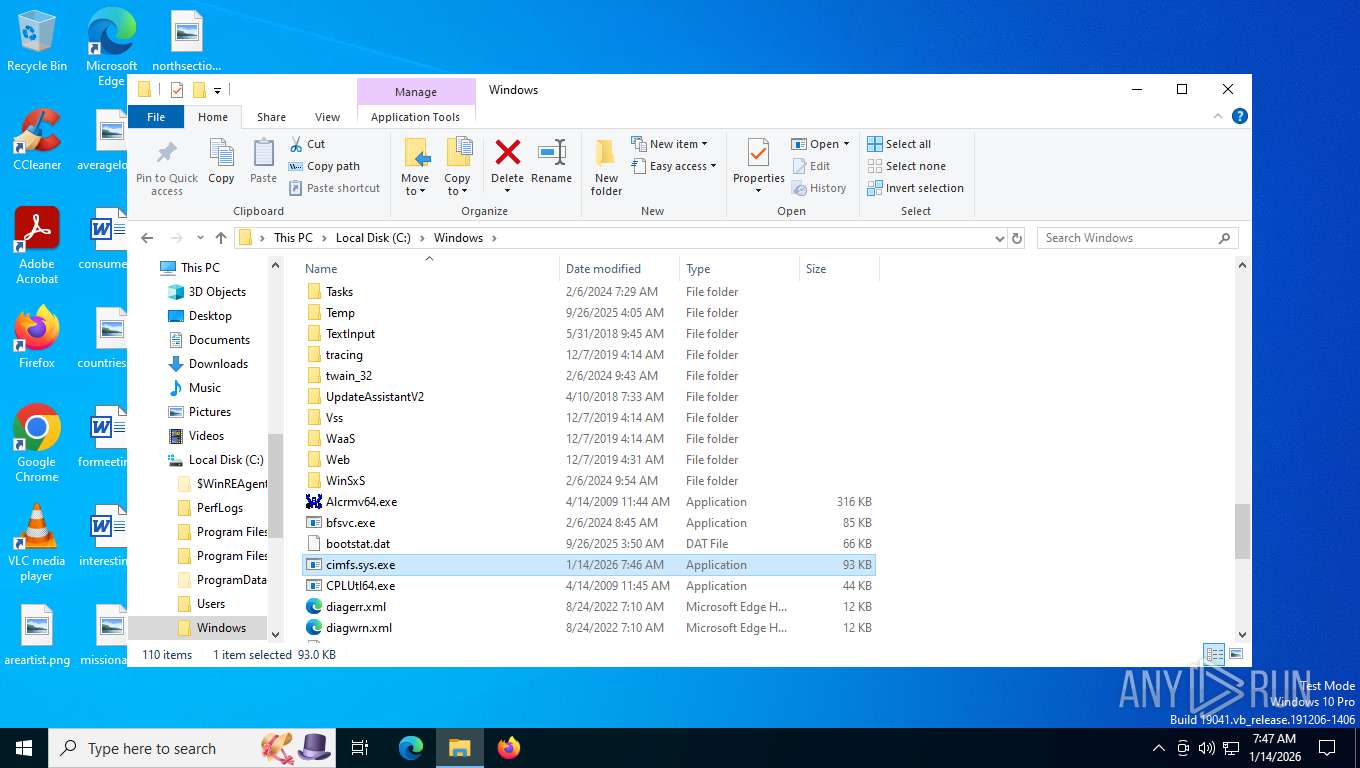
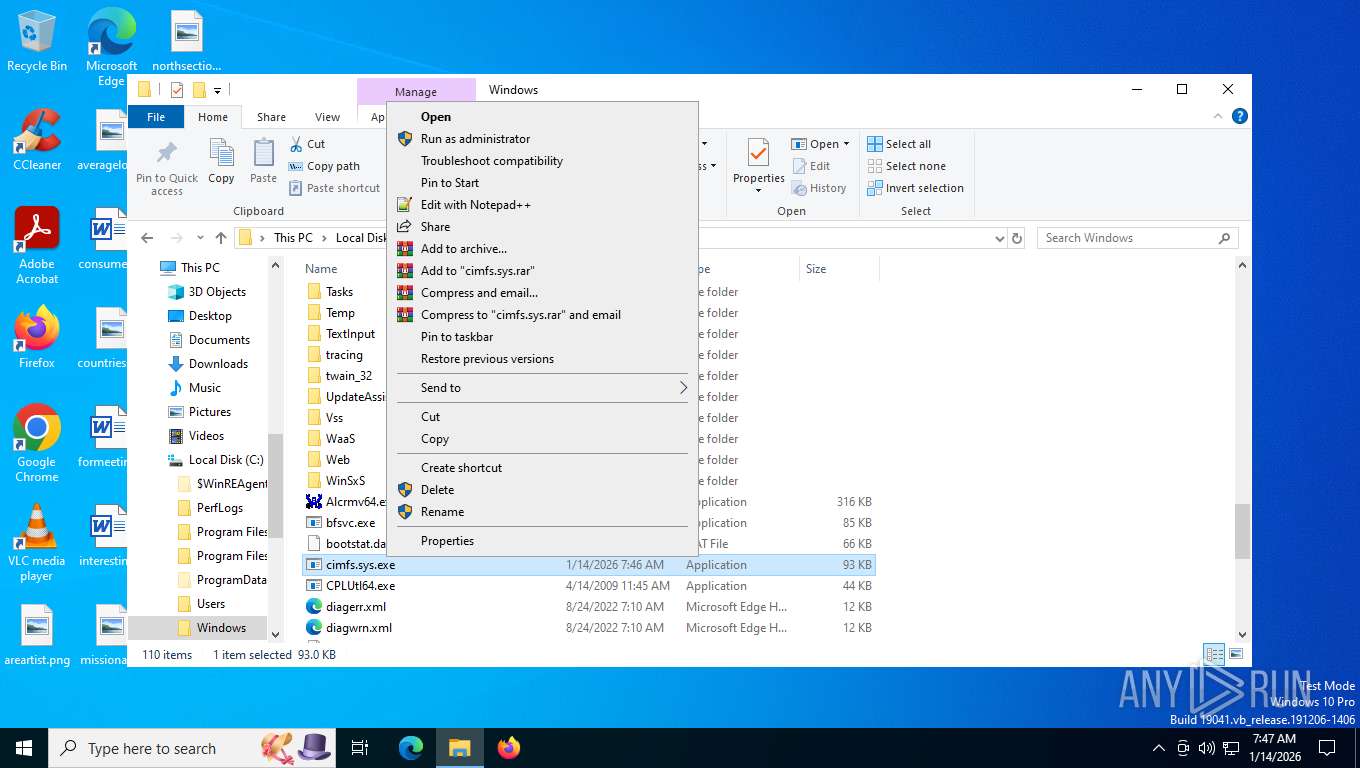
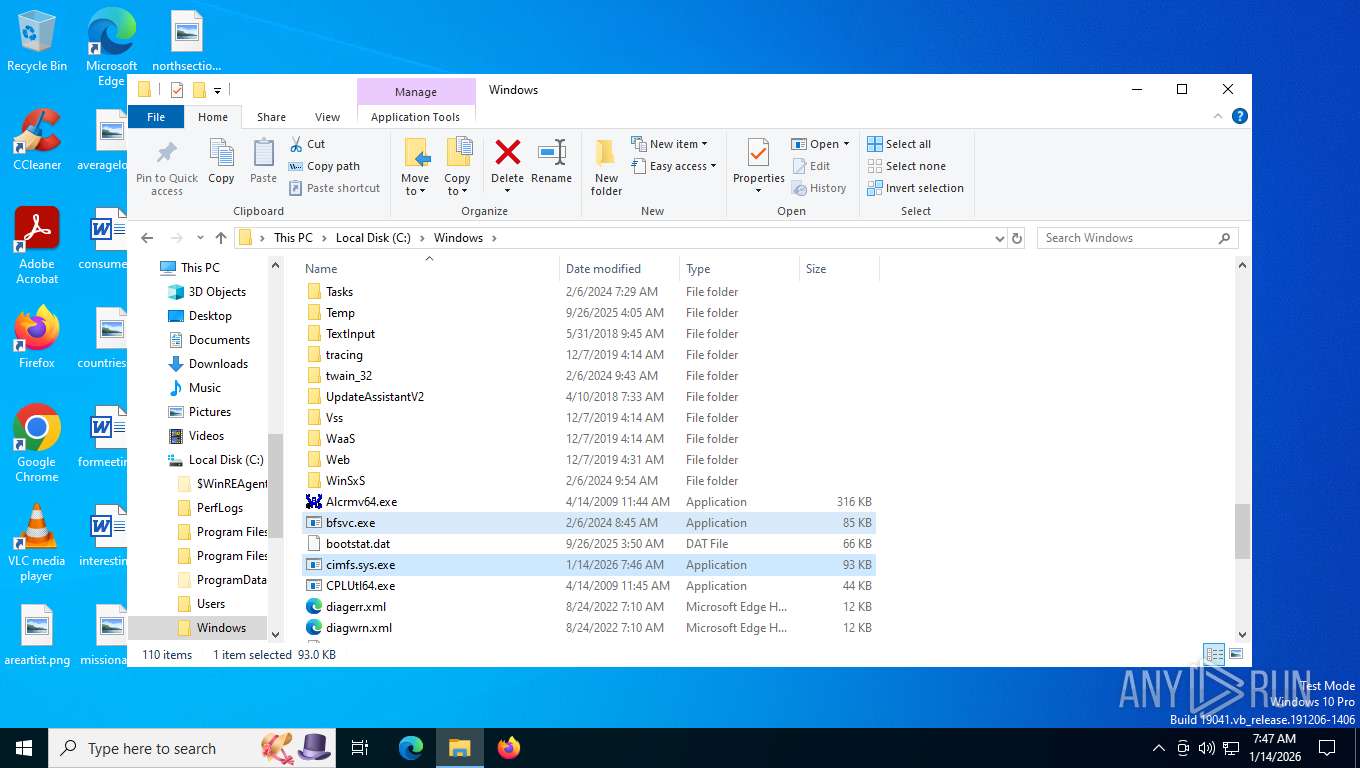
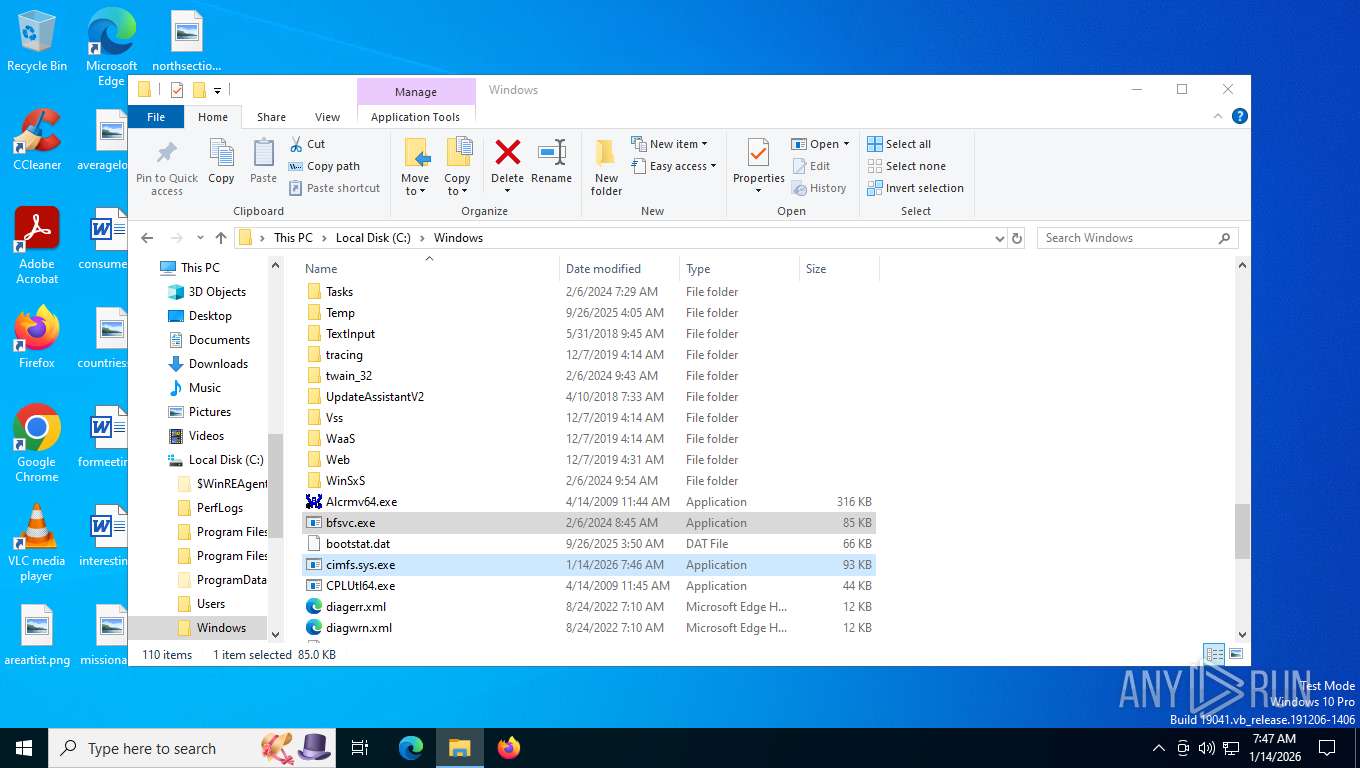
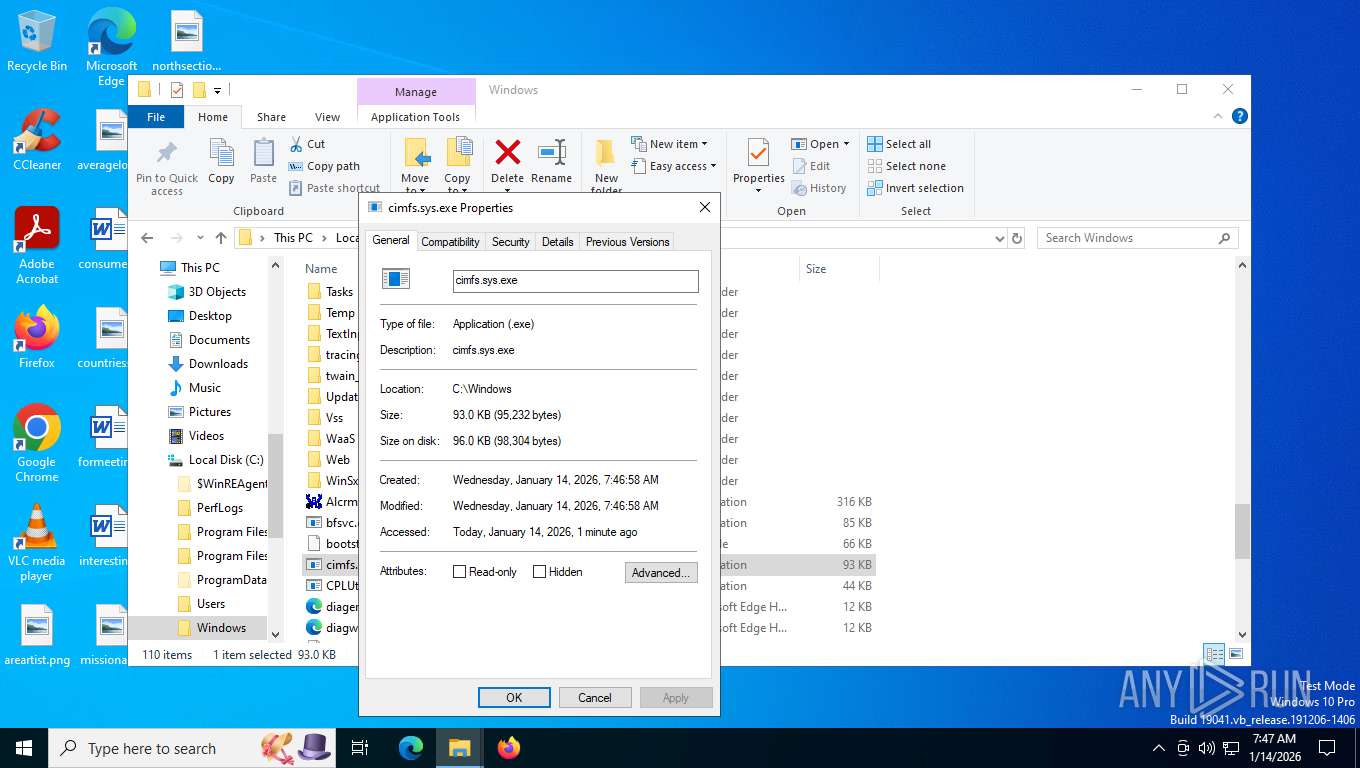
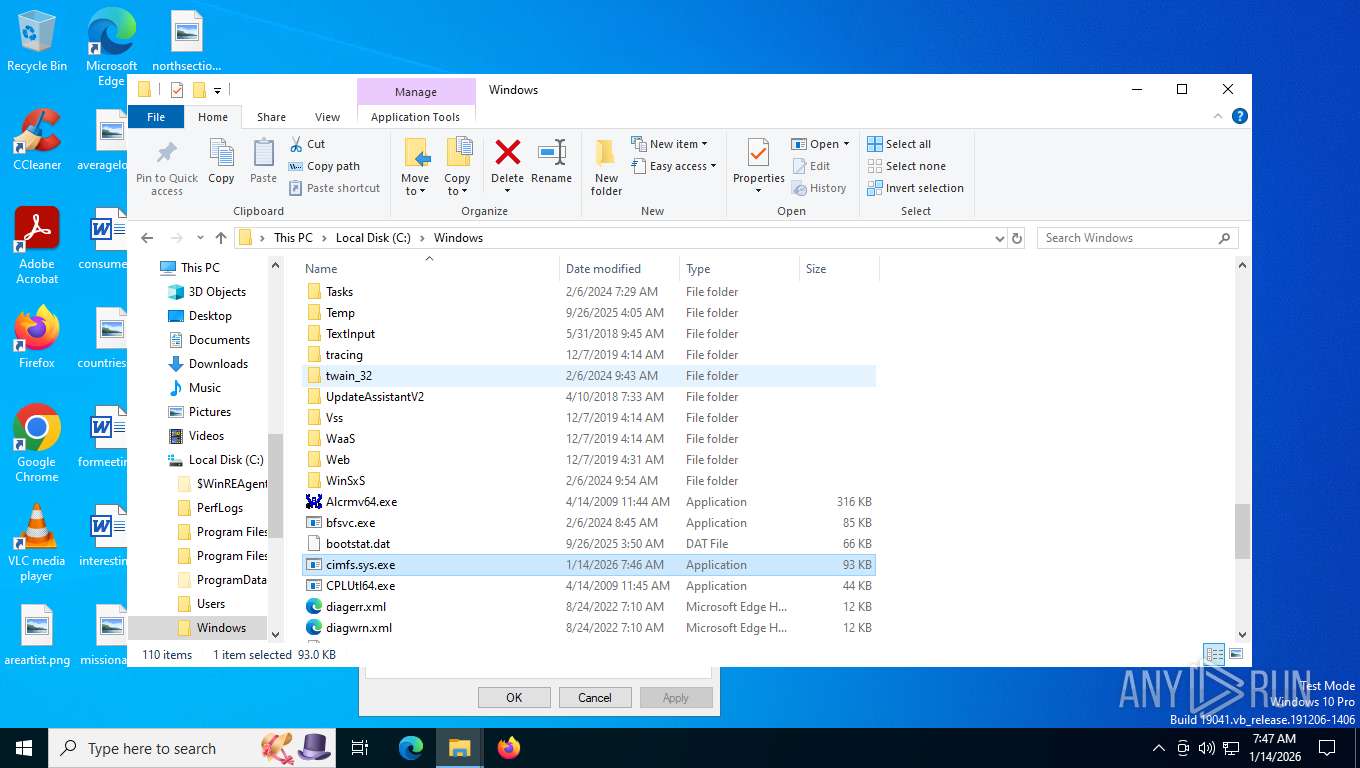
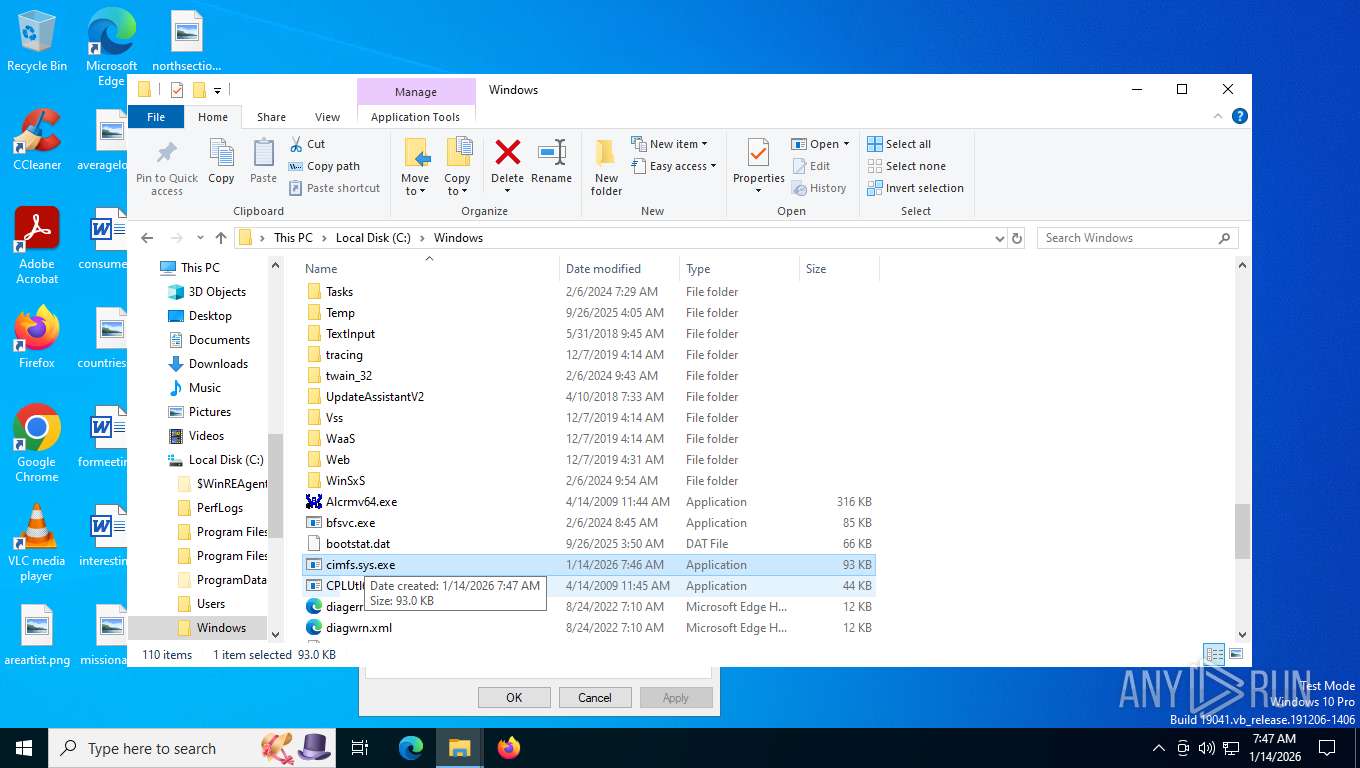
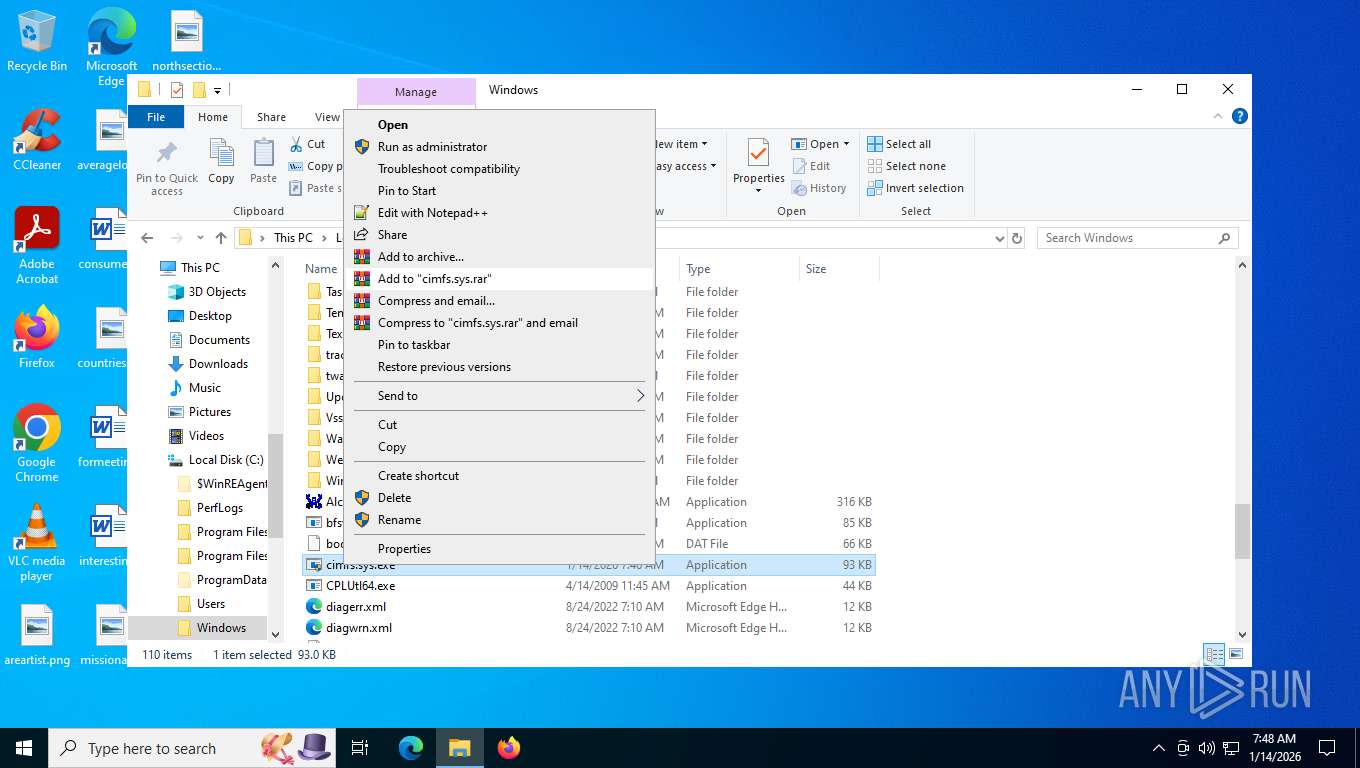
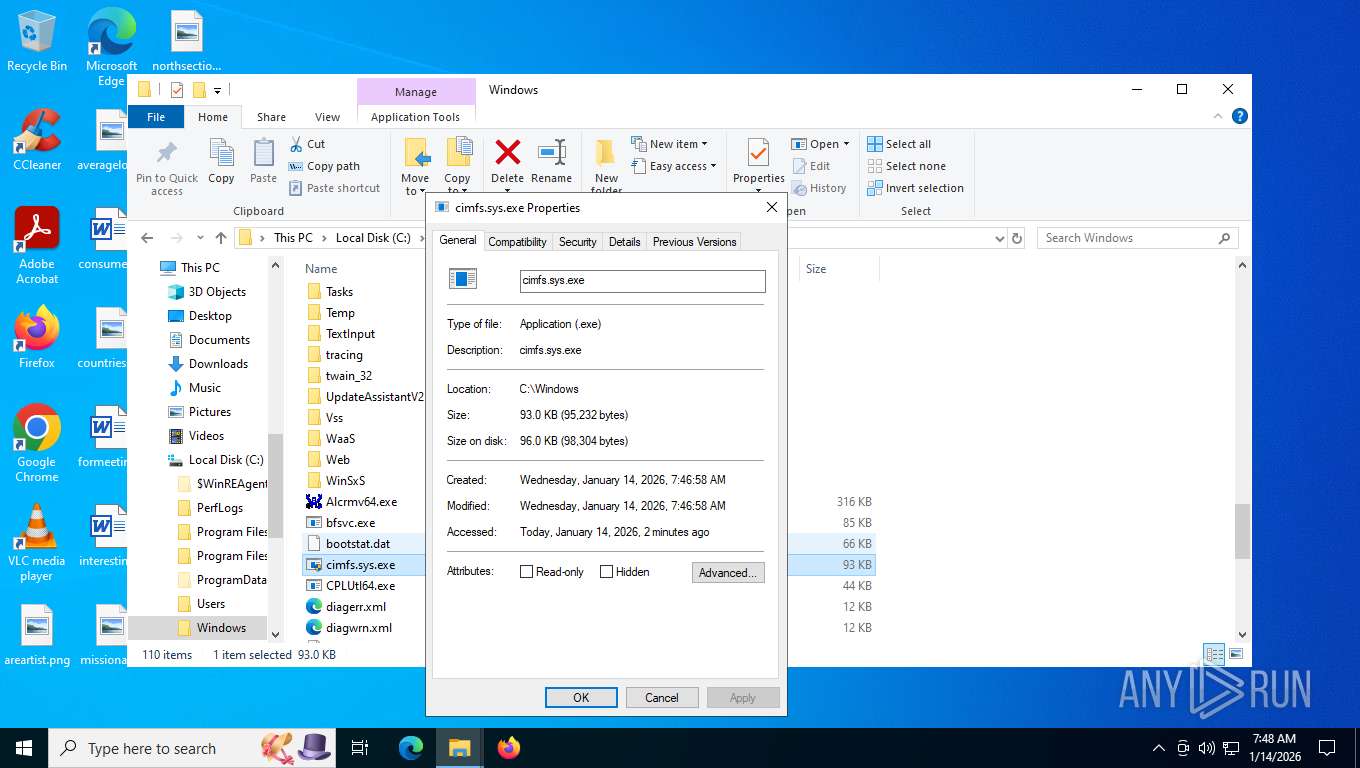
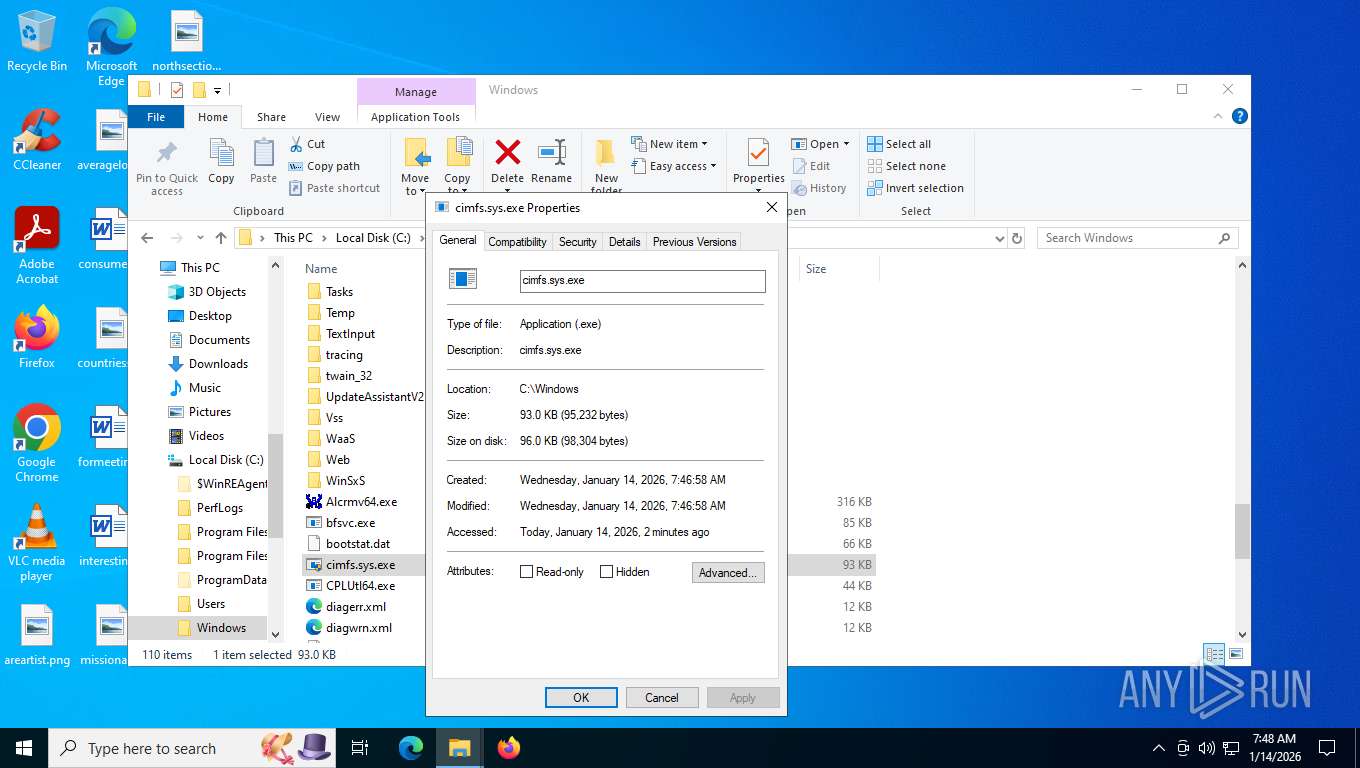
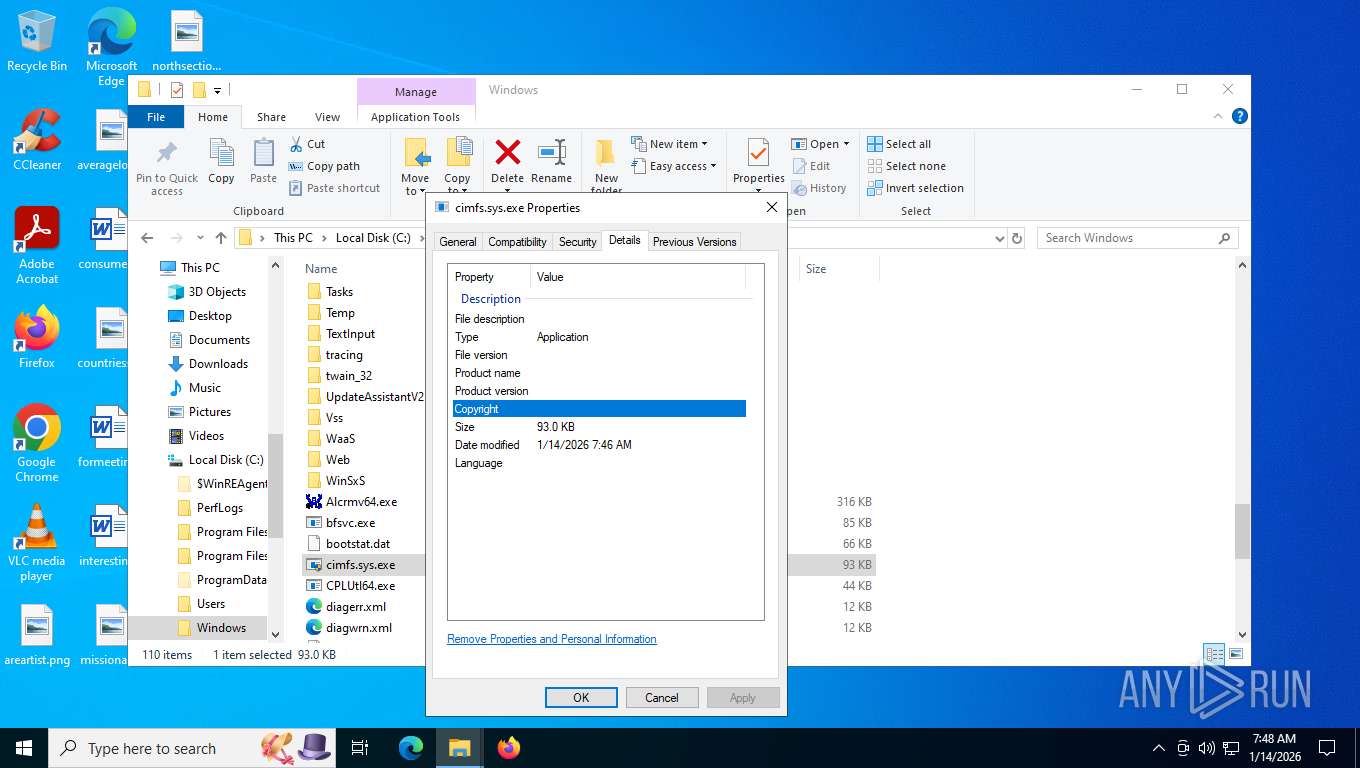
| File name: | cimfs.sys |
| Full analysis: | https://app.any.run/tasks/19195ccc-7712-4b10-be79-2ac3cf983acb |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2026, 12:46:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (native) x86-64, for MS Windows, 9 sections |
| MD5: | 4BC63233CB763FC44DEB32D462A41911 |
| SHA1: | F118E28BDEE9BAD3E606354C6D6FAF6C6EA87FF6 |
| SHA256: | C3A00CC5774051580015113483BFD516E1F11C720530842DBAFE8B6900746BDE |
| SSDEEP: | 3072:Gu9Cfg3B3fr65lm5Sy5Gc7kbLaXWrlau6M0bzBBNY6Hwe:Gu8mlr65lkSy5GcgbLabzBBNVwe |
MALICIOUS
No malicious indicators.SUSPICIOUS
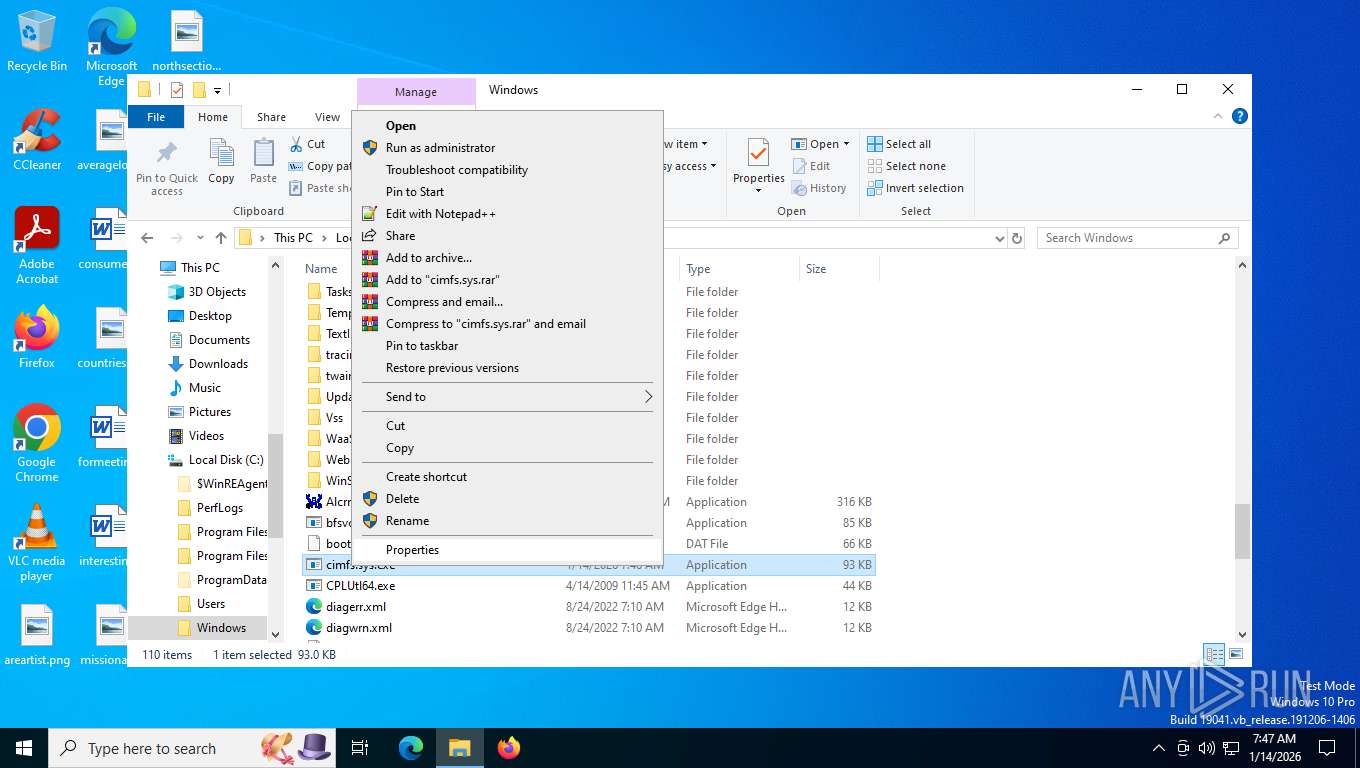
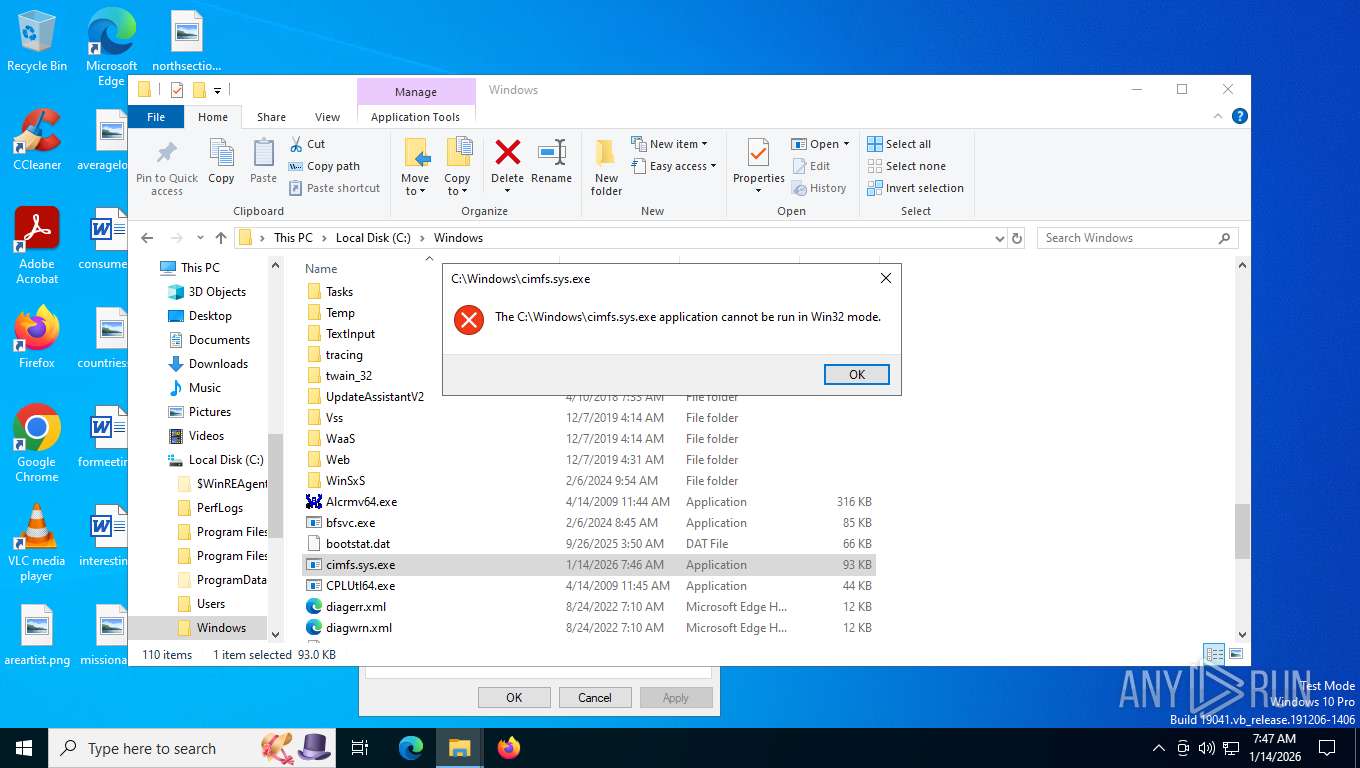
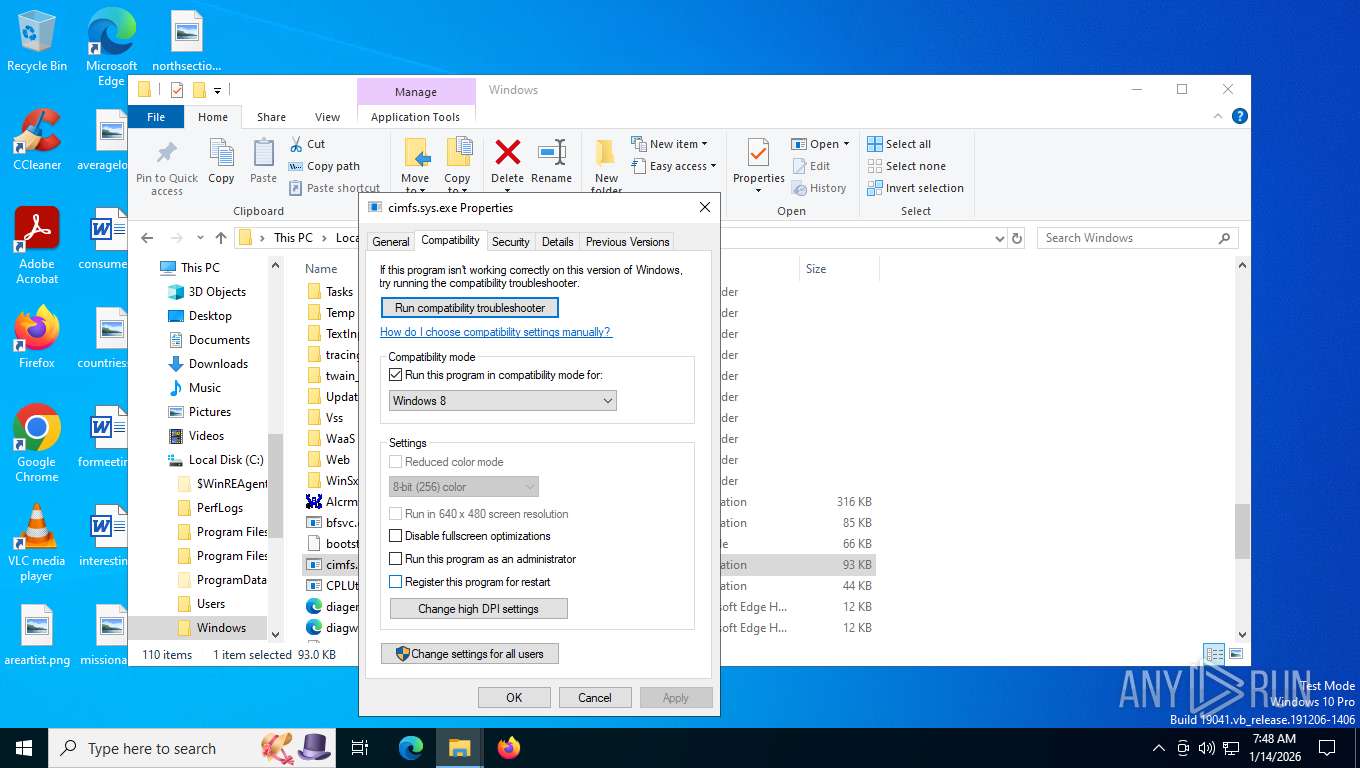
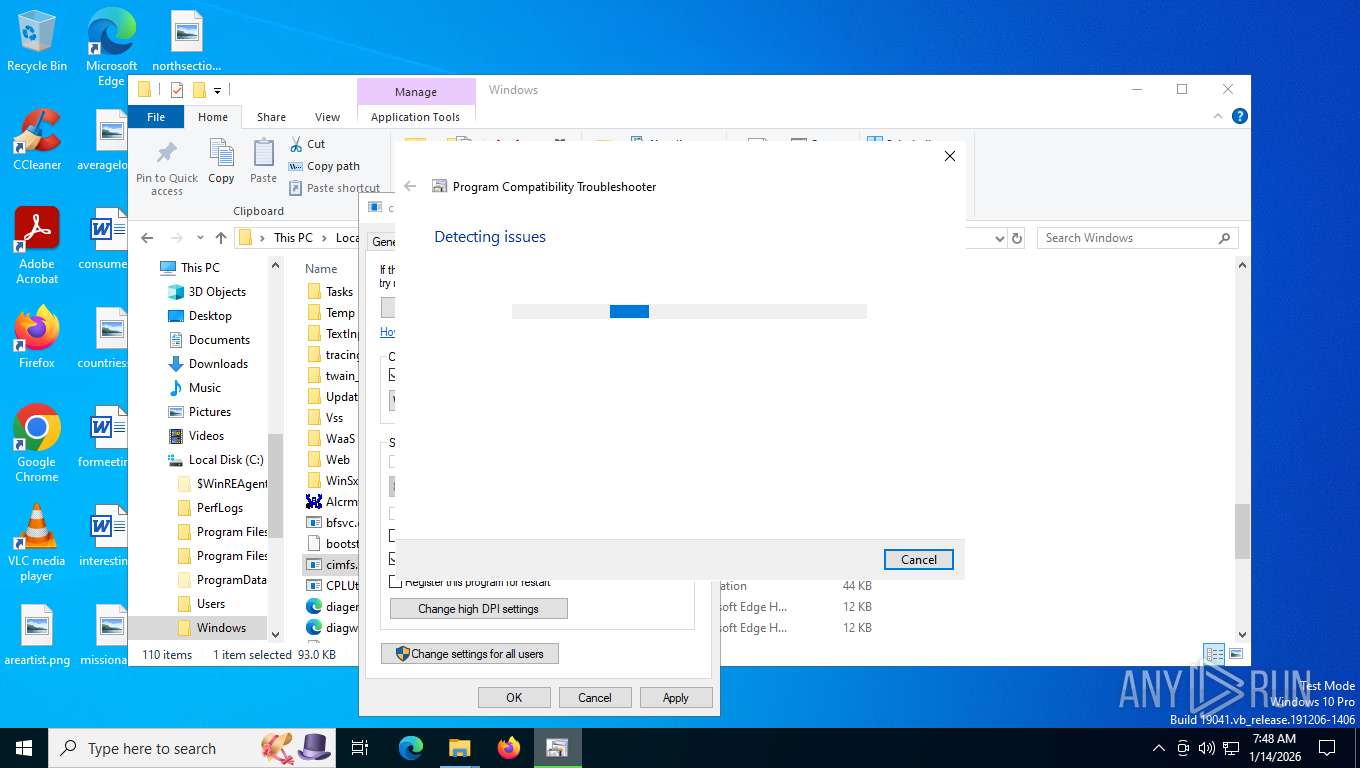
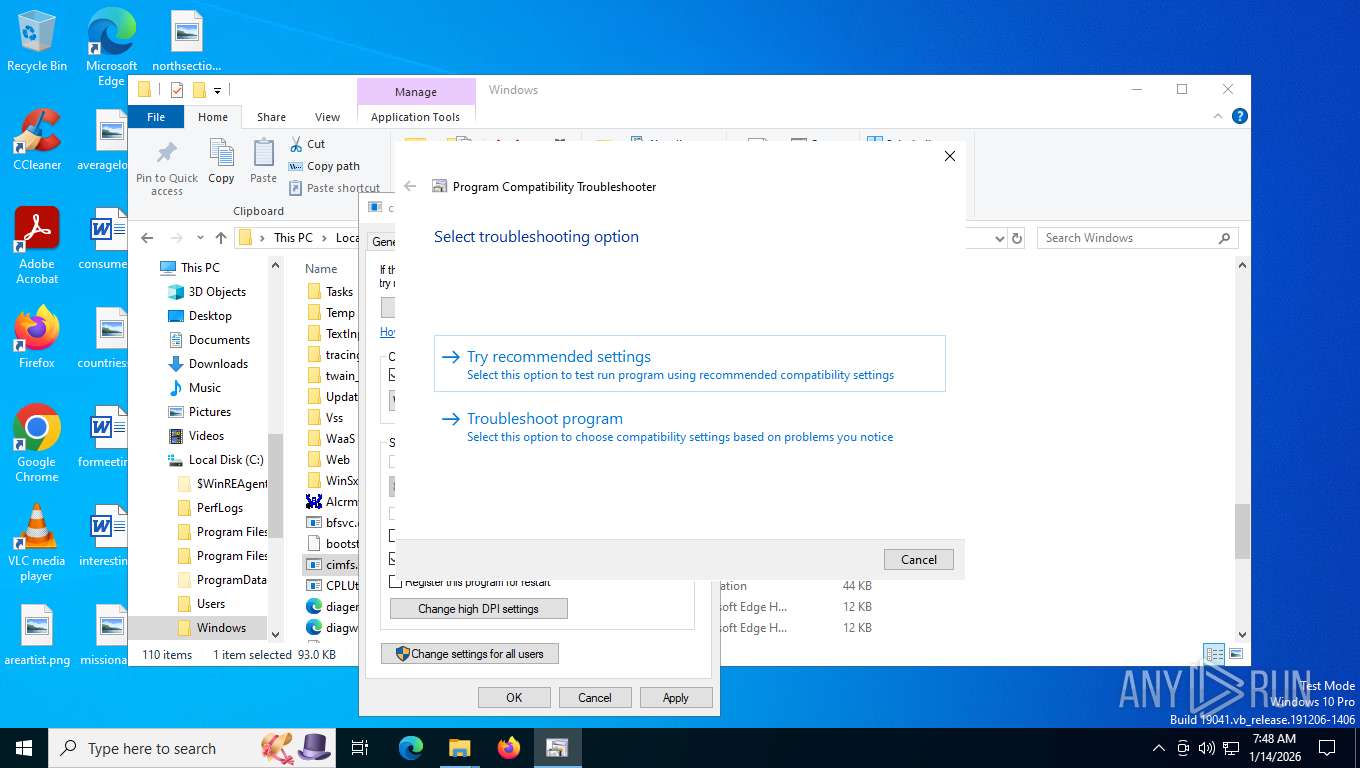
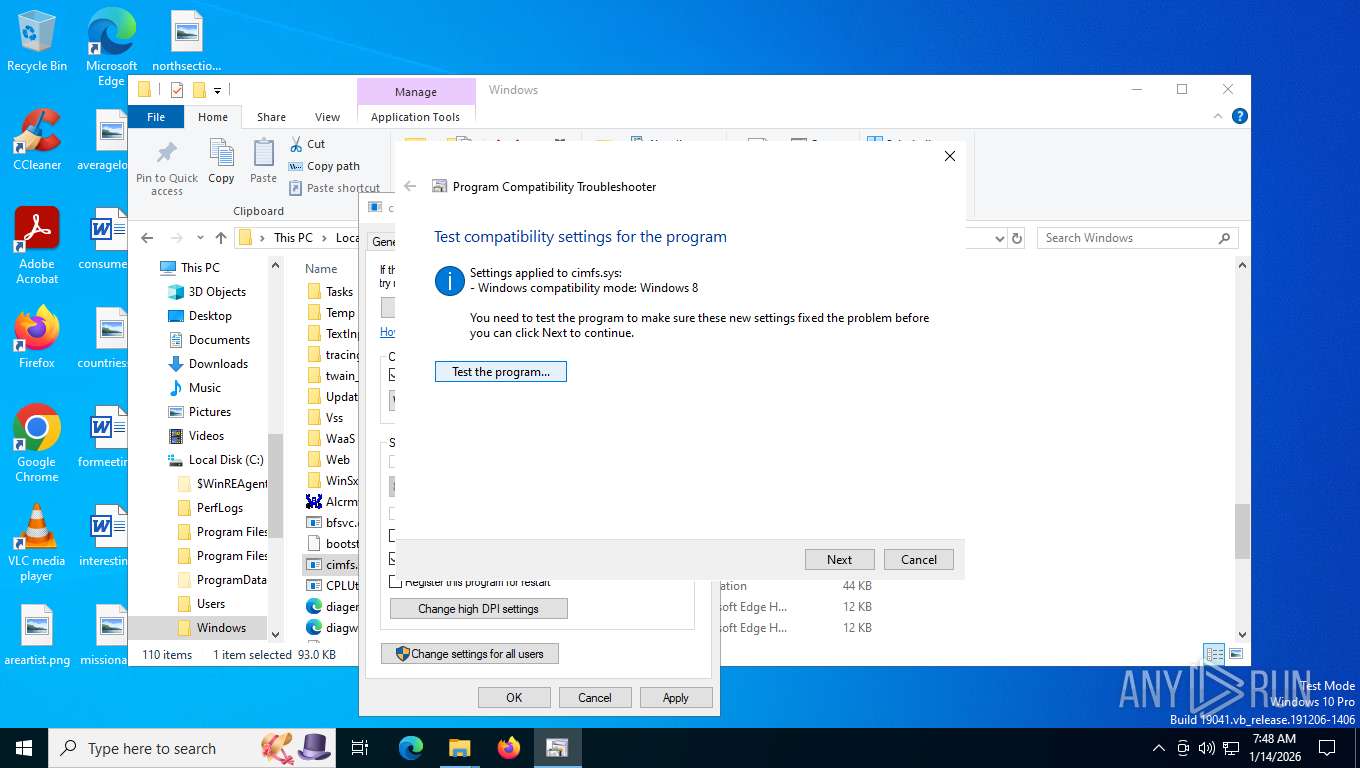
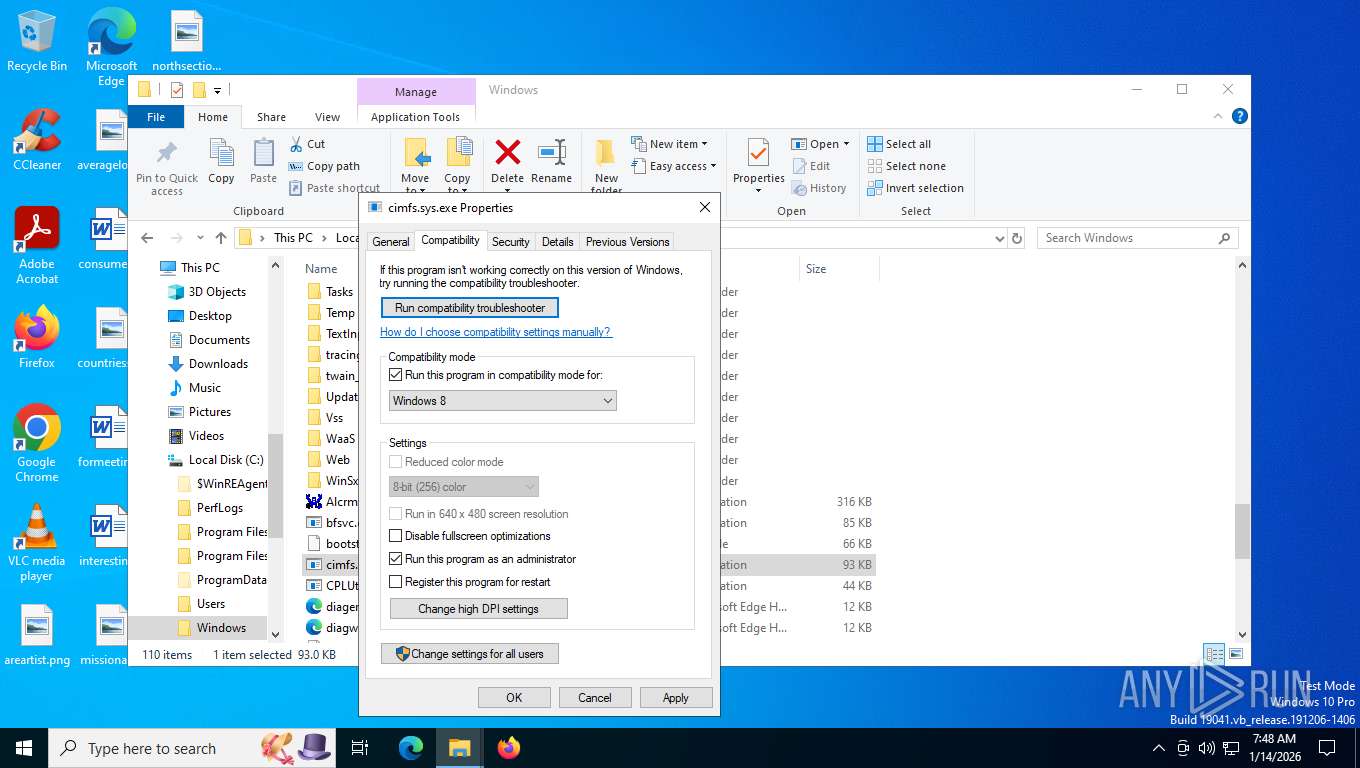
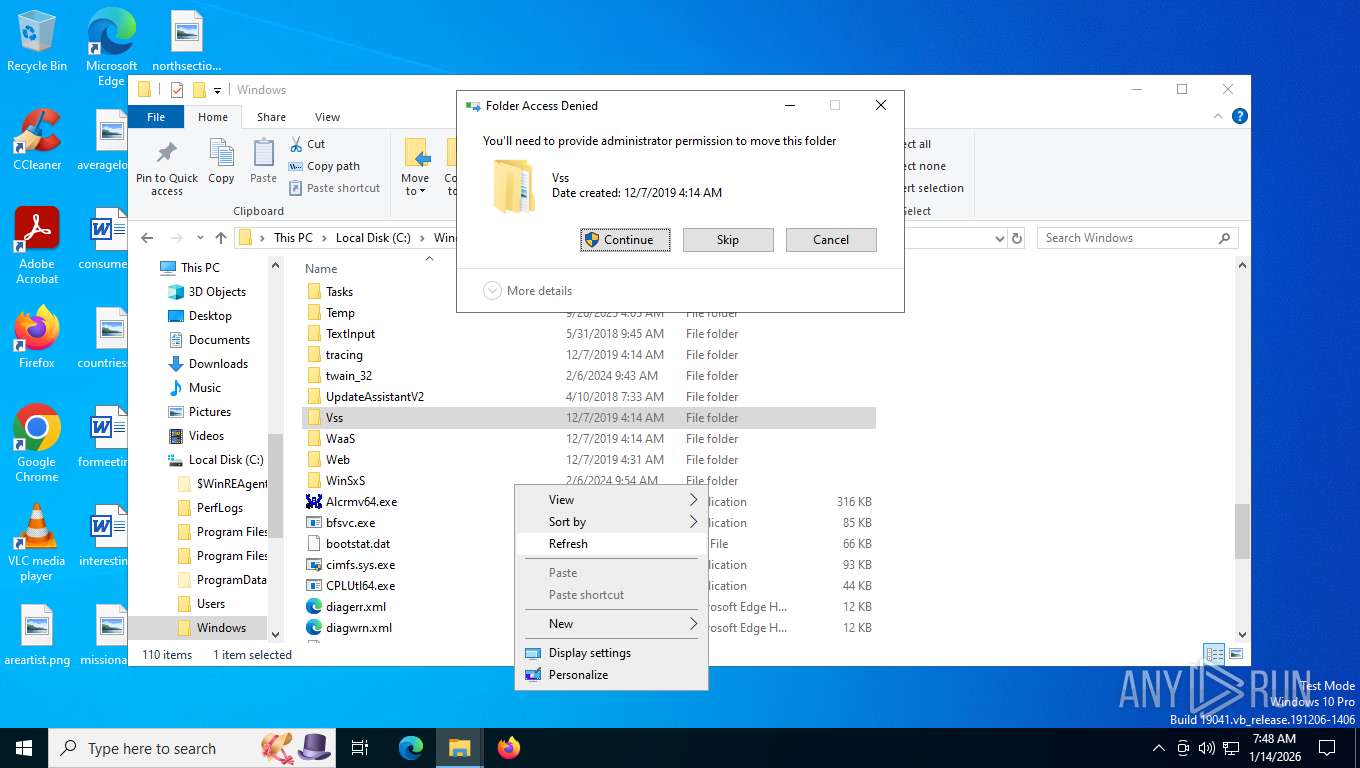
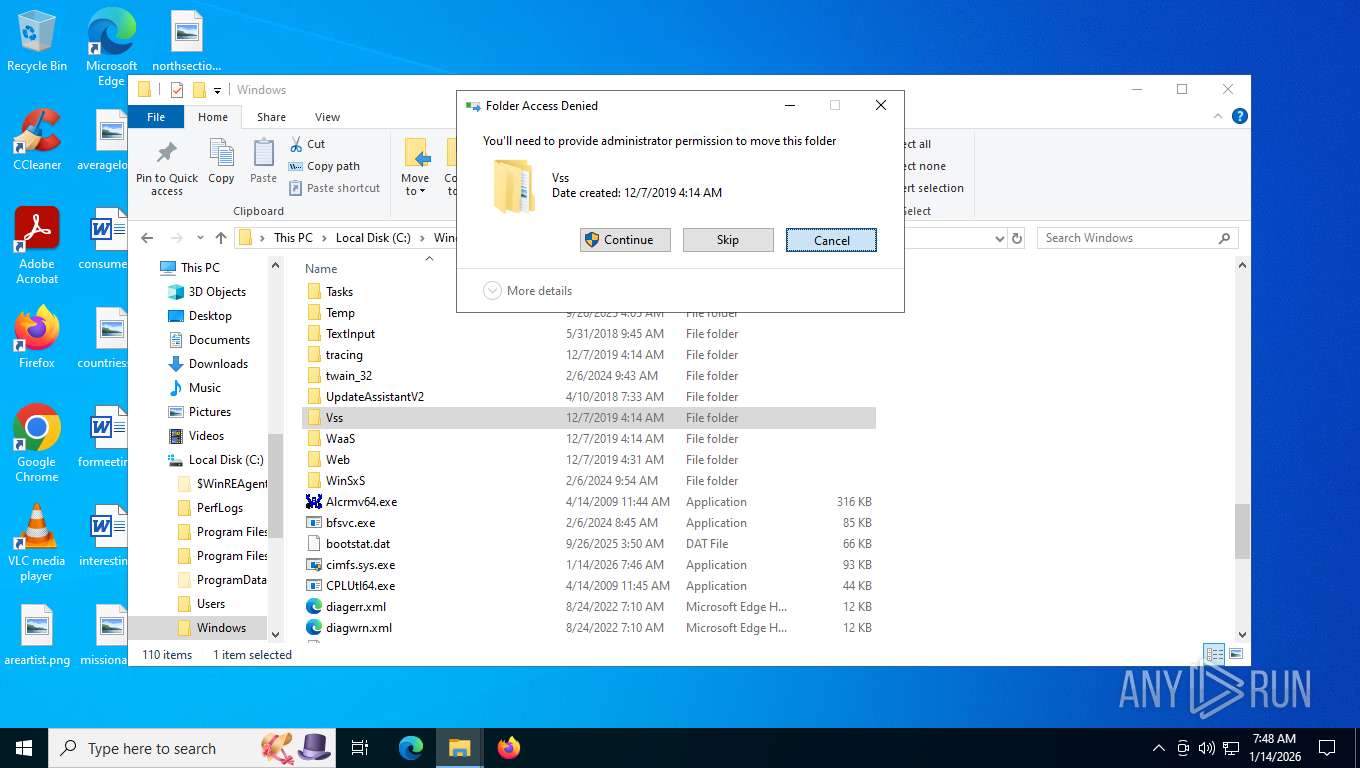
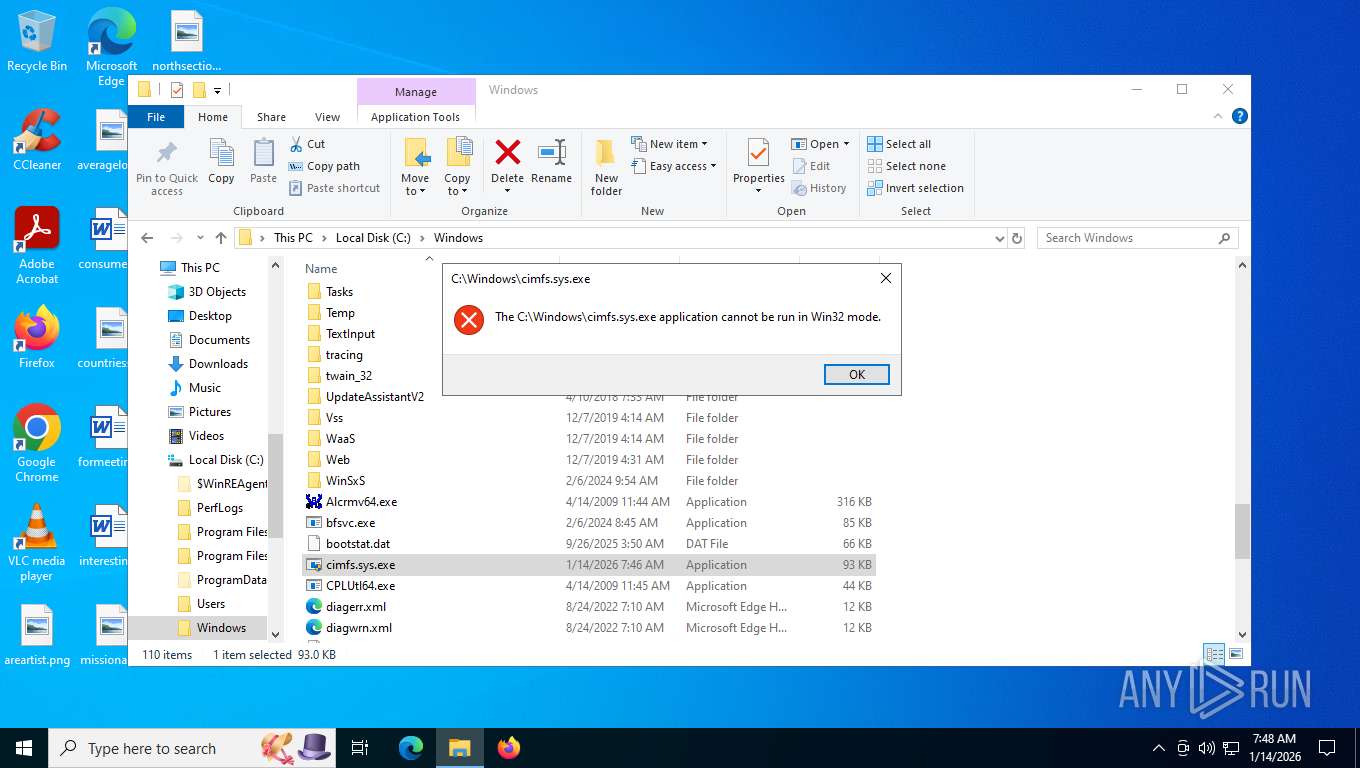
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 7220)
CSC.EXE is used to compile C# code
- csc.exe (PID: 2460)
- csc.exe (PID: 2752)
- csc.exe (PID: 4912)
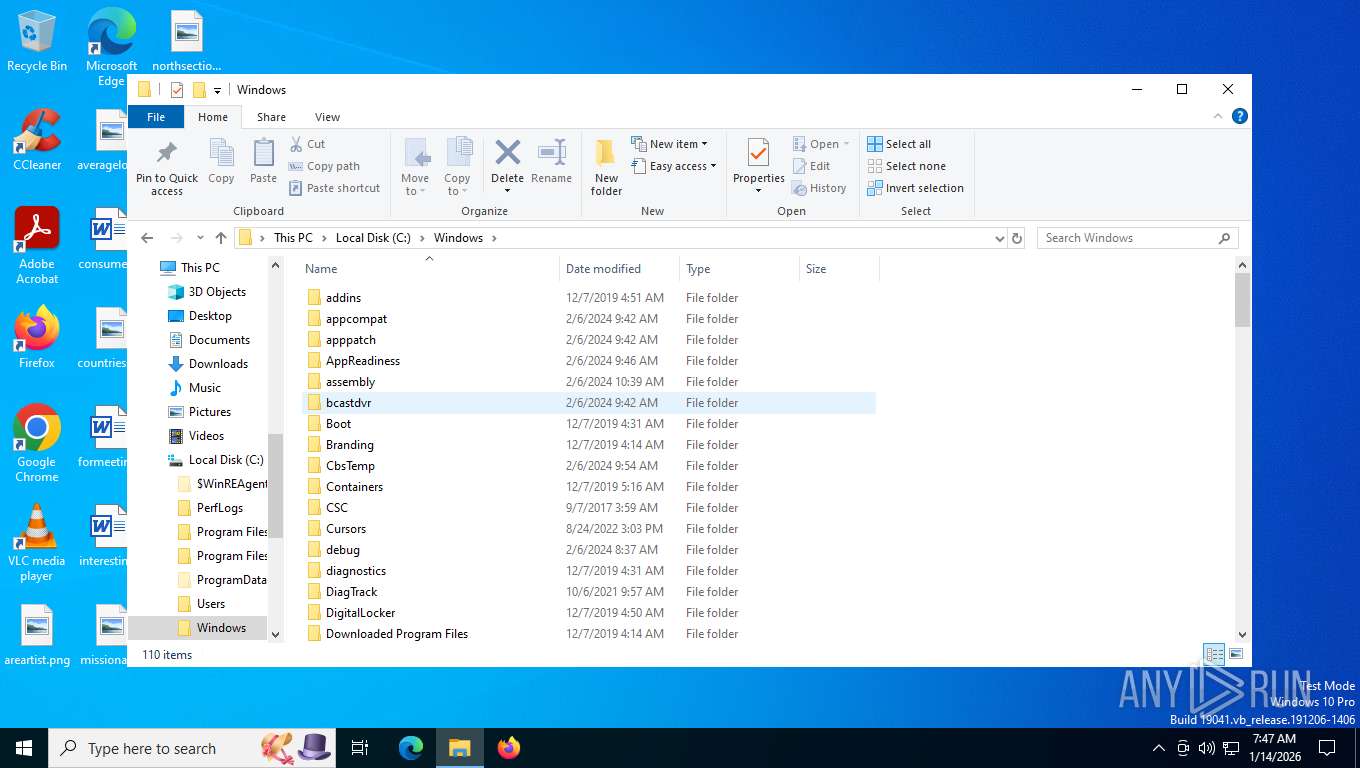
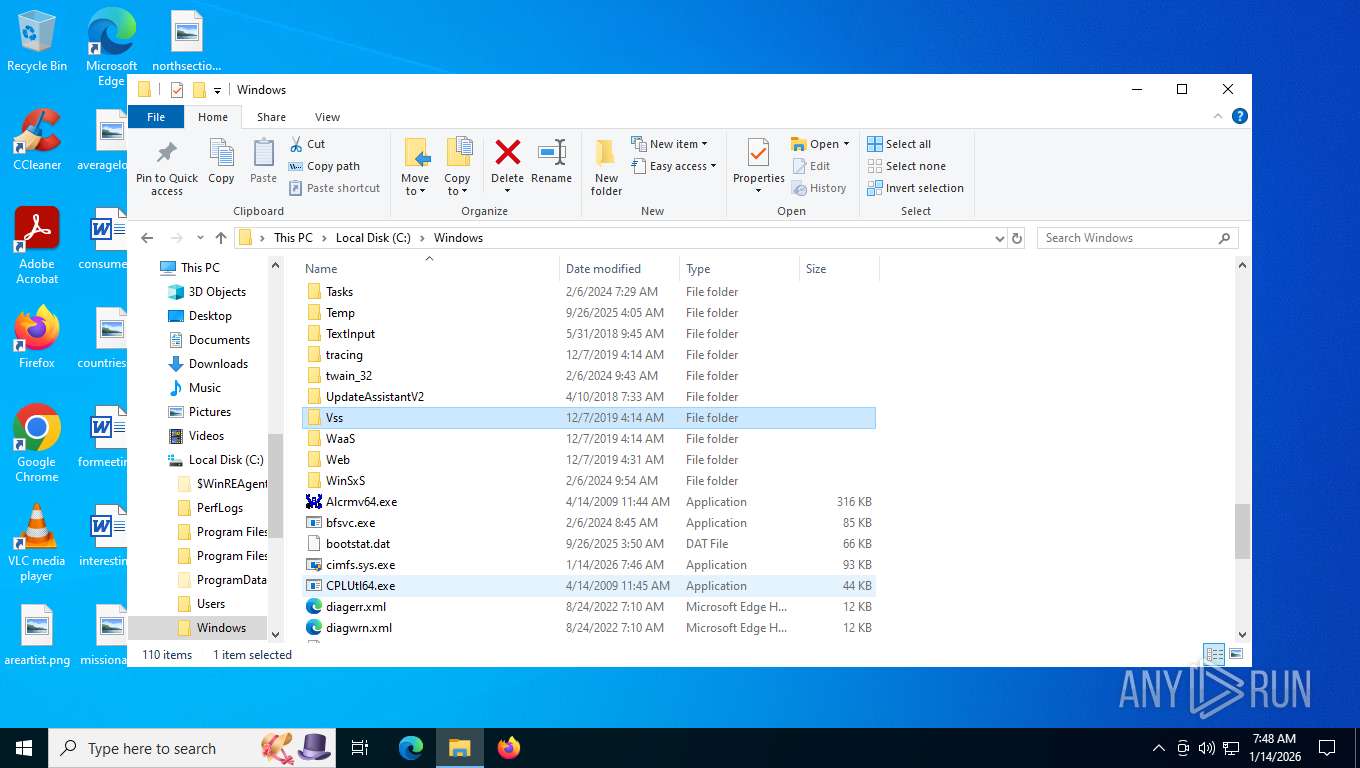
Executable content was dropped or overwritten
- csc.exe (PID: 2460)
- csc.exe (PID: 2752)
- csc.exe (PID: 4912)
Converts a string into array of characters (POWERSHELL)
- sdiagnhost.exe (PID: 7300)
Gets file extension (POWERSHELL)
- sdiagnhost.exe (PID: 7300)
INFO
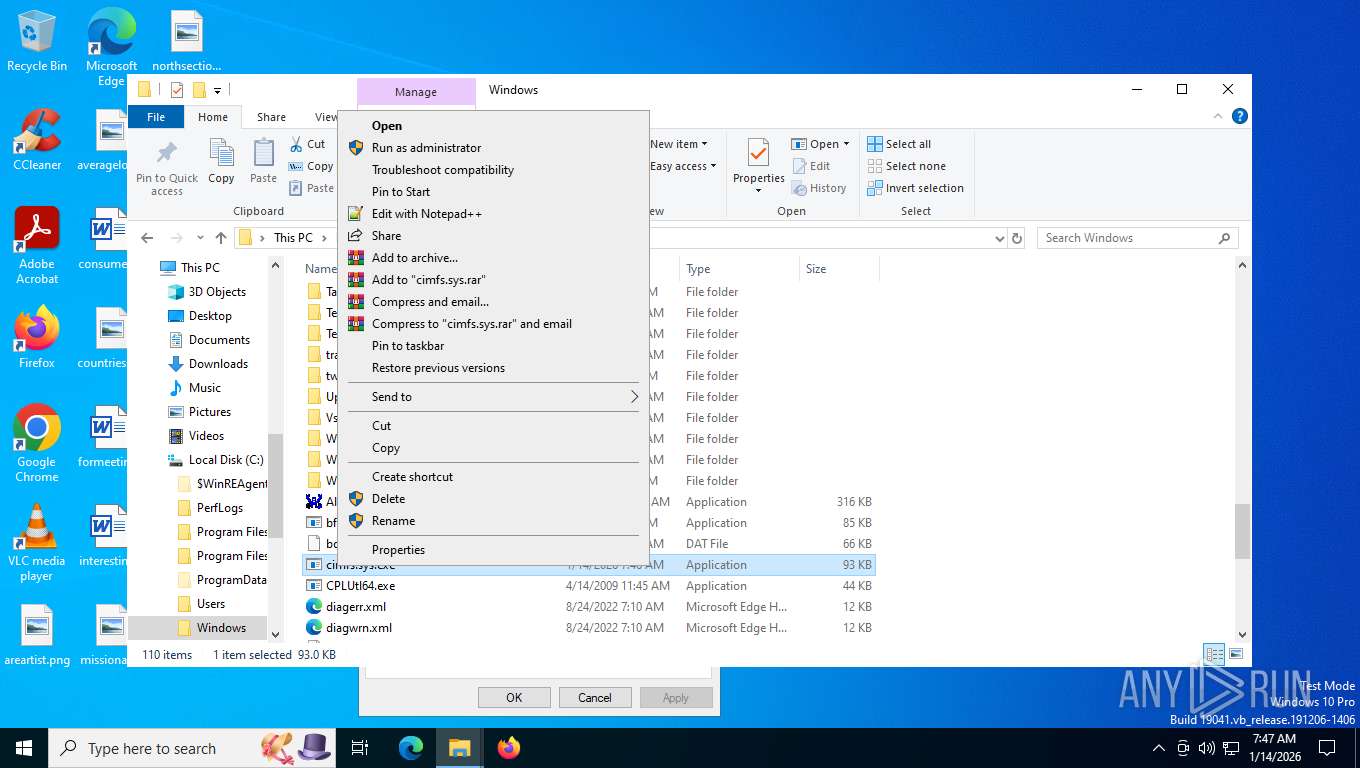
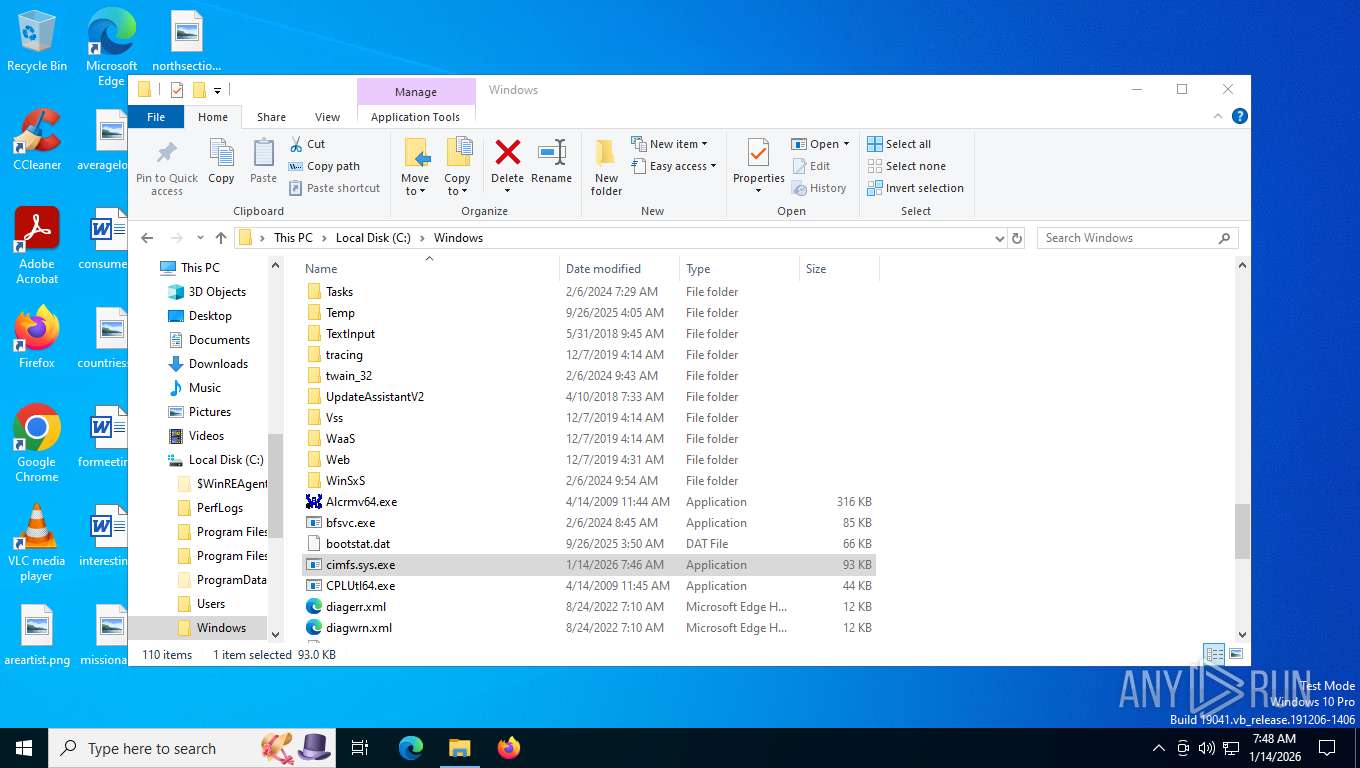
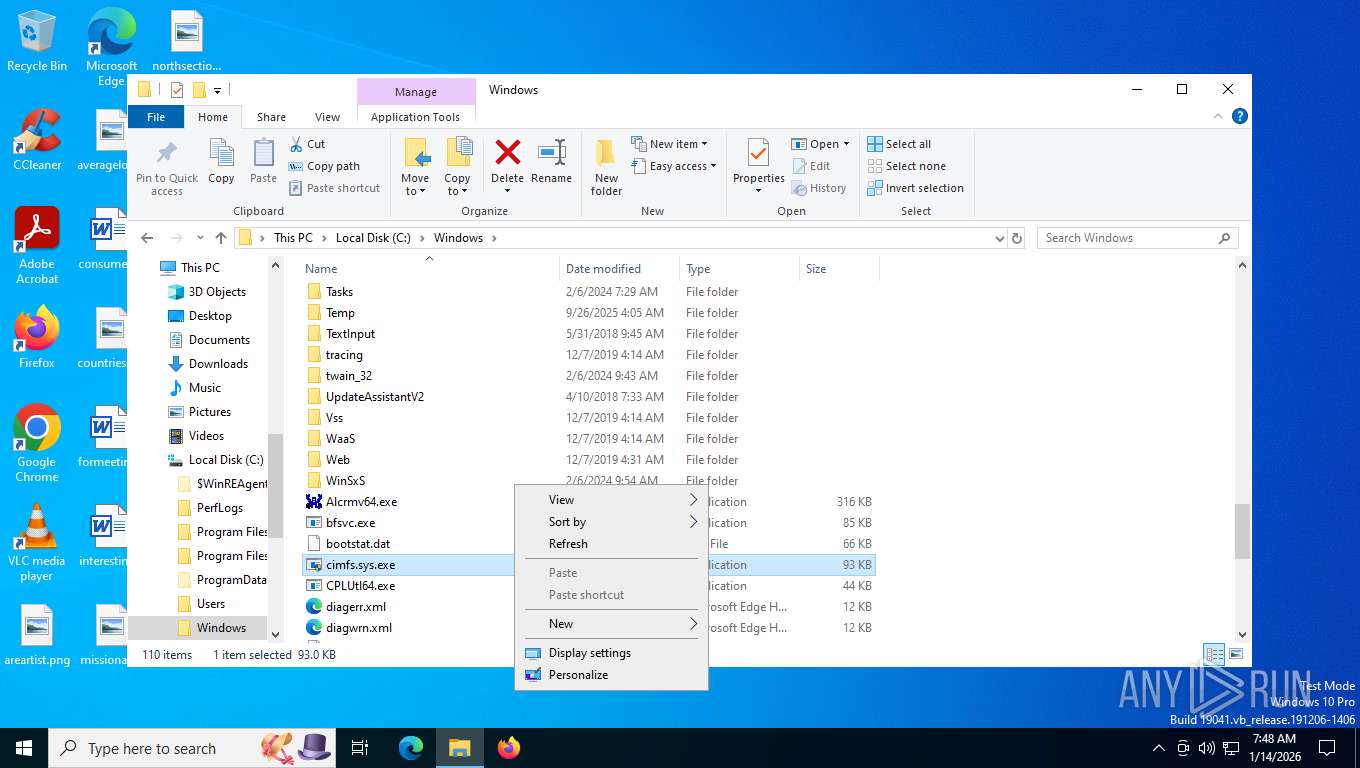
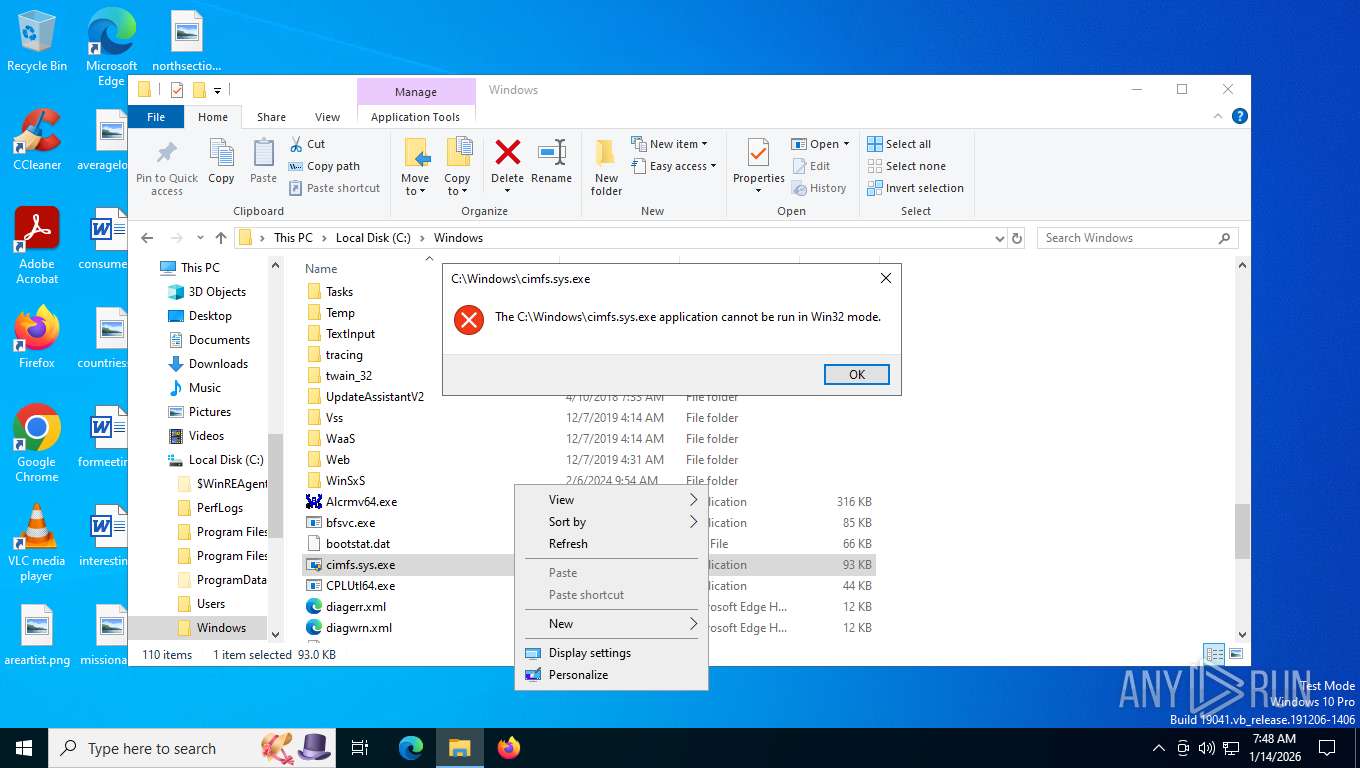
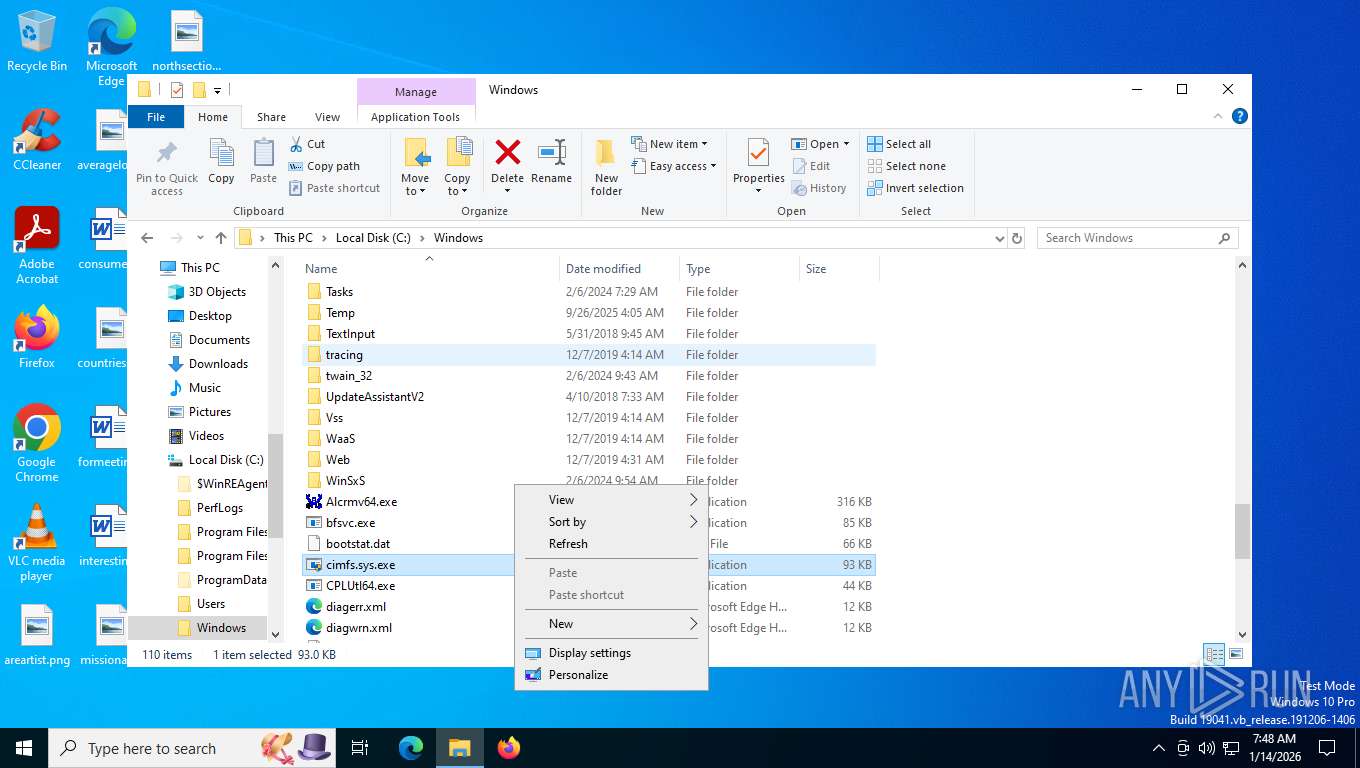
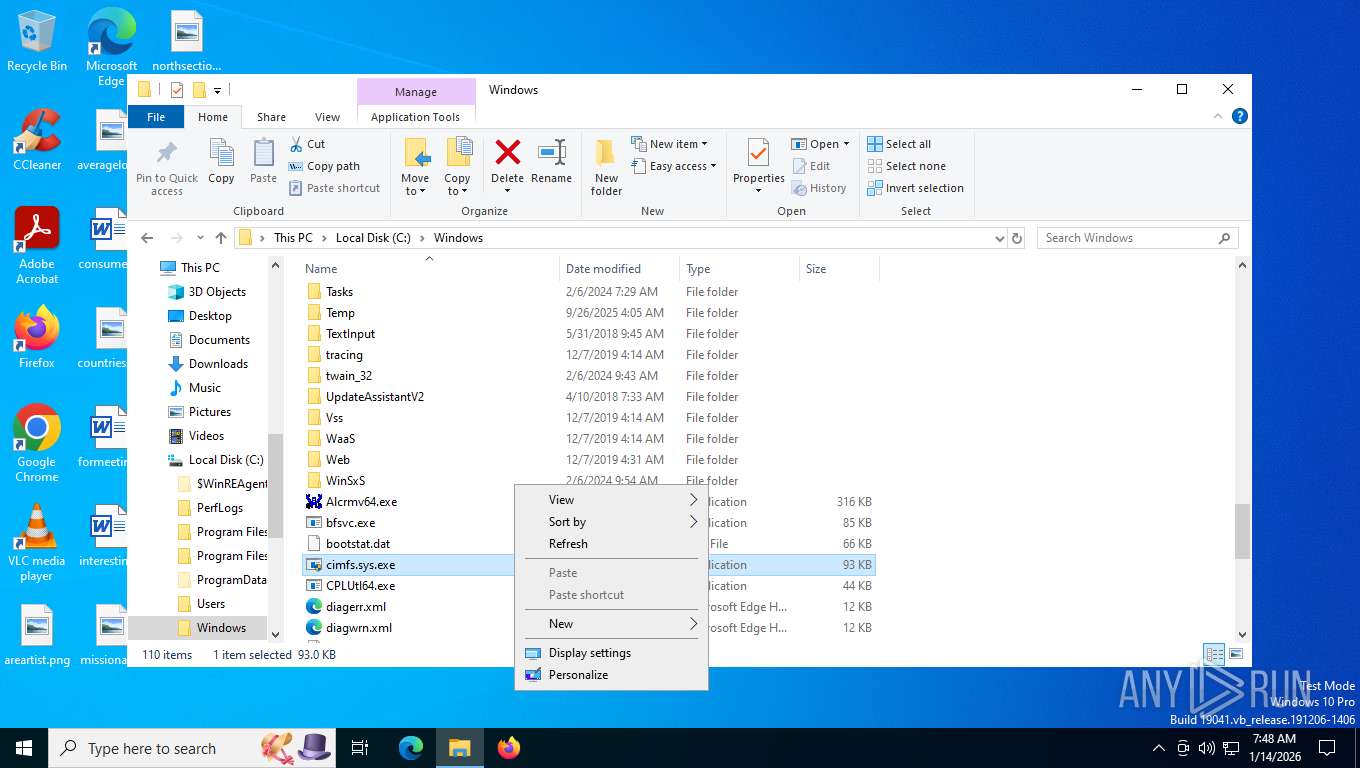
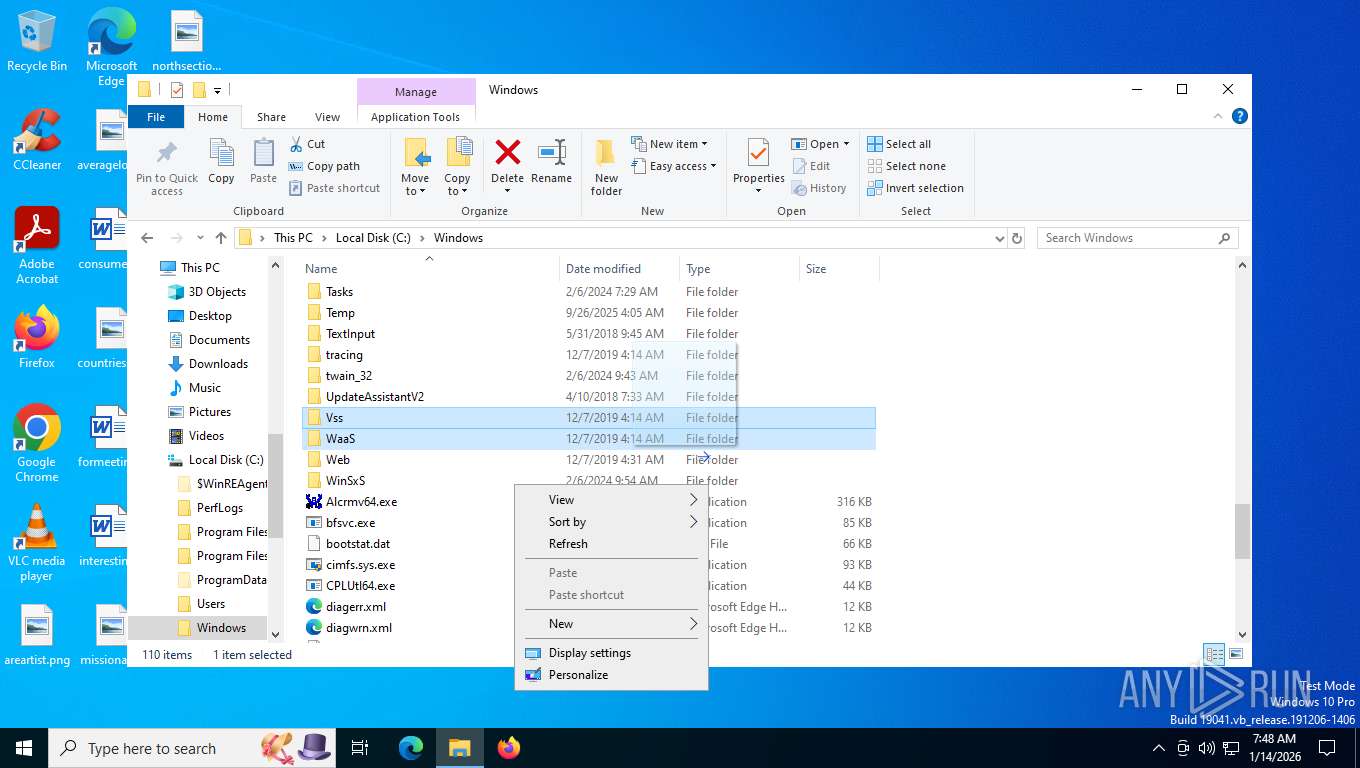
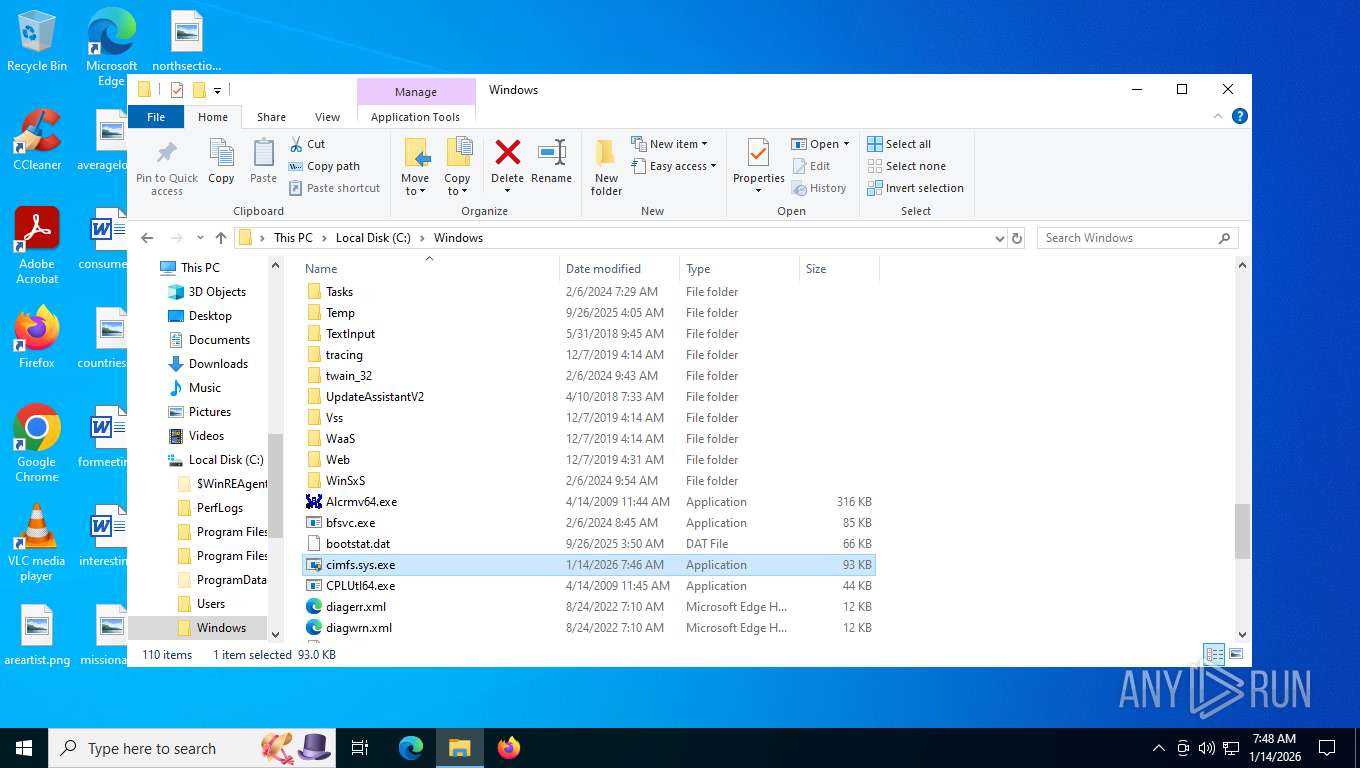
Manual execution by a user
- cimfs.sys.exe (PID: 4636)
- pcwrun.exe (PID: 7220)
- cimfs.sys.exe (PID: 7844)
- cimfs.sys.exe (PID: 4968)
Create files in a temporary directory
- pcwrun.exe (PID: 7220)
- msdt.exe (PID: 7232)
- csc.exe (PID: 2460)
- cvtres.exe (PID: 5040)
- sdiagnhost.exe (PID: 7300)
- csc.exe (PID: 2752)
- cvtres.exe (PID: 2428)
- cvtres.exe (PID: 3136)
- csc.exe (PID: 4912)
Reads security settings of Internet Explorer
- msdt.exe (PID: 7232)
- sdiagnhost.exe (PID: 7300)
Checks supported languages
- csc.exe (PID: 2460)
- cvtres.exe (PID: 5040)
- csc.exe (PID: 2752)
- cvtres.exe (PID: 2428)
- csc.exe (PID: 4912)
- cvtres.exe (PID: 3136)
The sample compiled with english language support
- msdt.exe (PID: 7232)
Reads the machine GUID from the registry
- csc.exe (PID: 2460)
- csc.exe (PID: 2752)
- csc.exe (PID: 4912)
Creates files or folders in the user directory
- sdiagnhost.exe (PID: 7300)
- msdt.exe (PID: 7232)
Checks proxy server information
- sdiagnhost.exe (PID: 7300)
- slui.exe (PID: 5752)
Uses string split method (POWERSHELL)
- sdiagnhost.exe (PID: 7300)
Uses string replace method (POWERSHELL)
- sdiagnhost.exe (PID: 7300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2033:12:07 04:25:36+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.2 |
| CodeSize: | 70656 |
| InitializedDataSize: | 23552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b230 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 10 |
| Subsystem: | Native |
Total processes
160
Monitored processes
15
Malicious processes
0
Suspicious processes
1
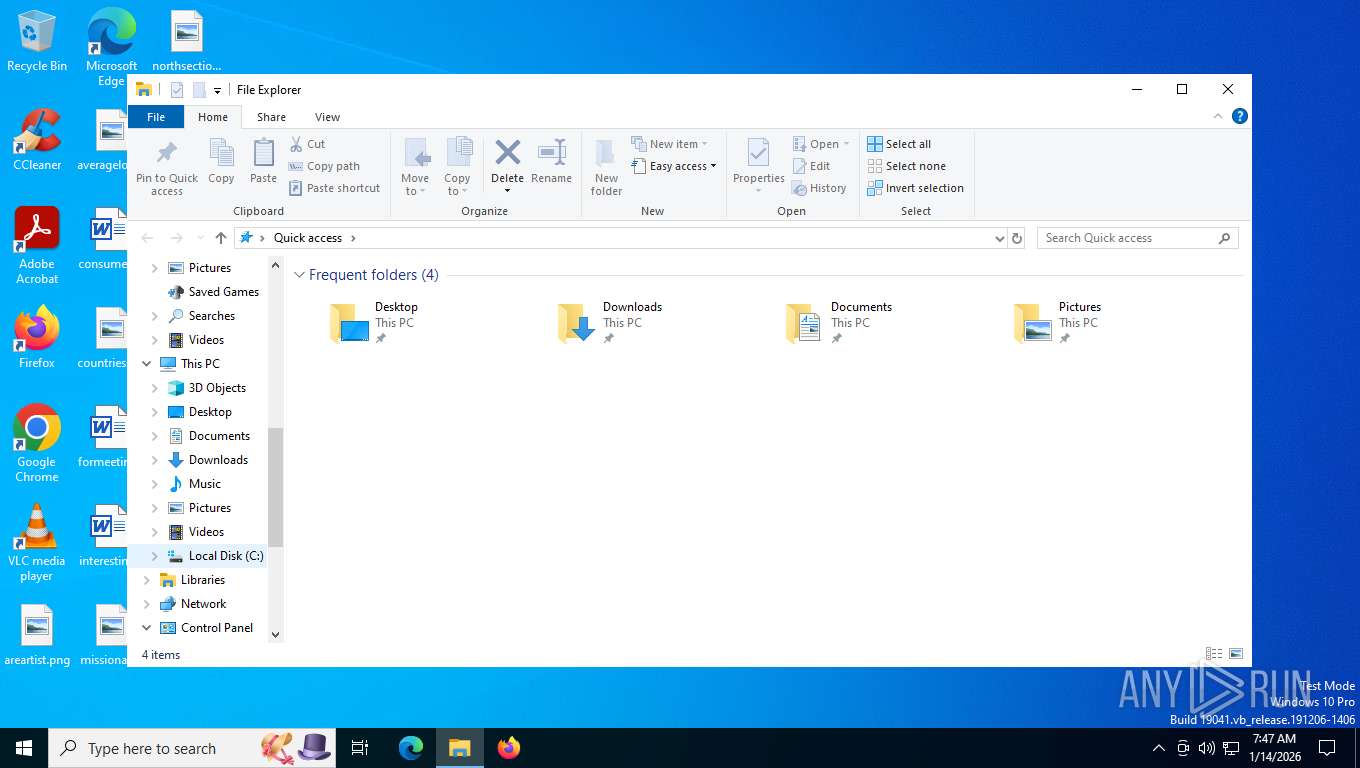
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2428 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESF08C.tmp" "c:\Users\admin\AppData\Local\Temp\CSCB4754CF3AE30407EA3B170C0BC1E7431.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2460 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\wcgyp3ad.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2752 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\0gzw3gcq.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3136 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESF510.tmp" "c:\Users\admin\AppData\Local\Temp\CSCF7F979A79BD34333B01678A3F0BA1527.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
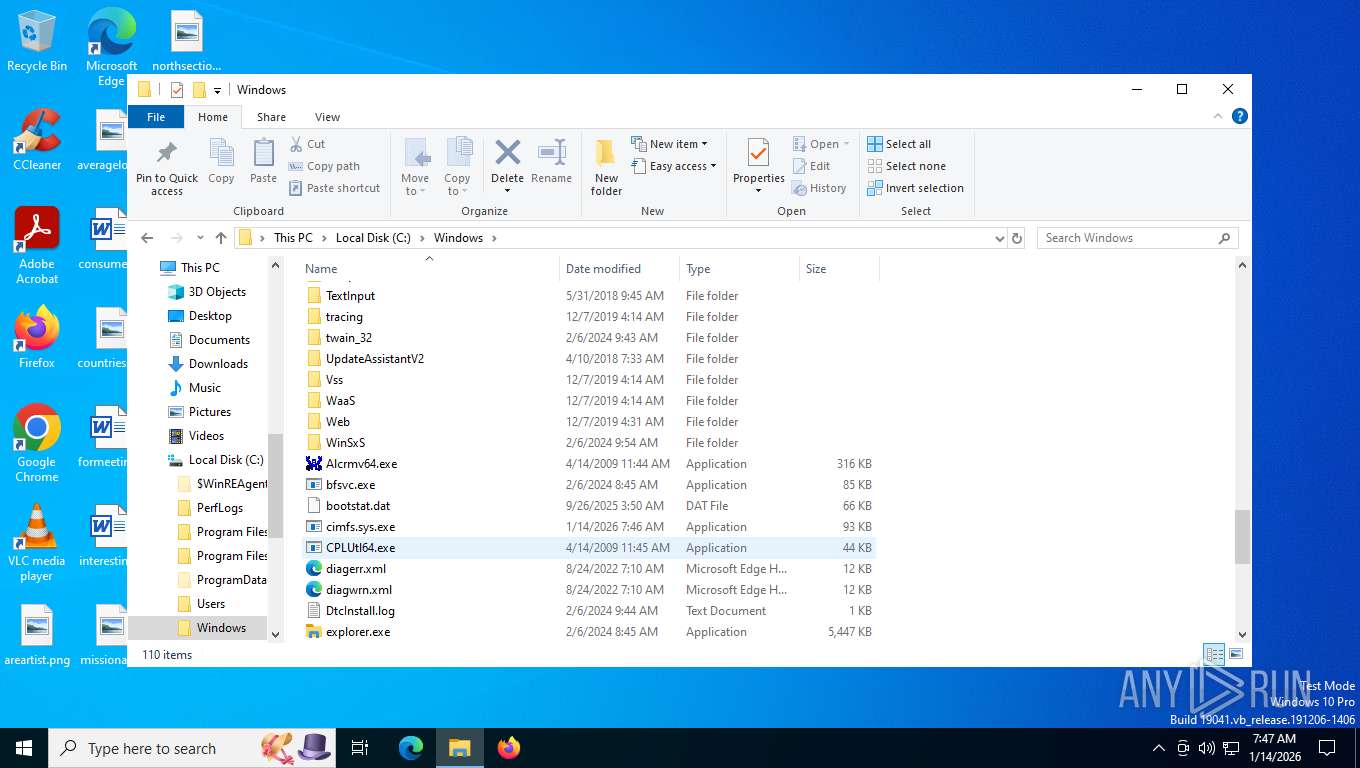
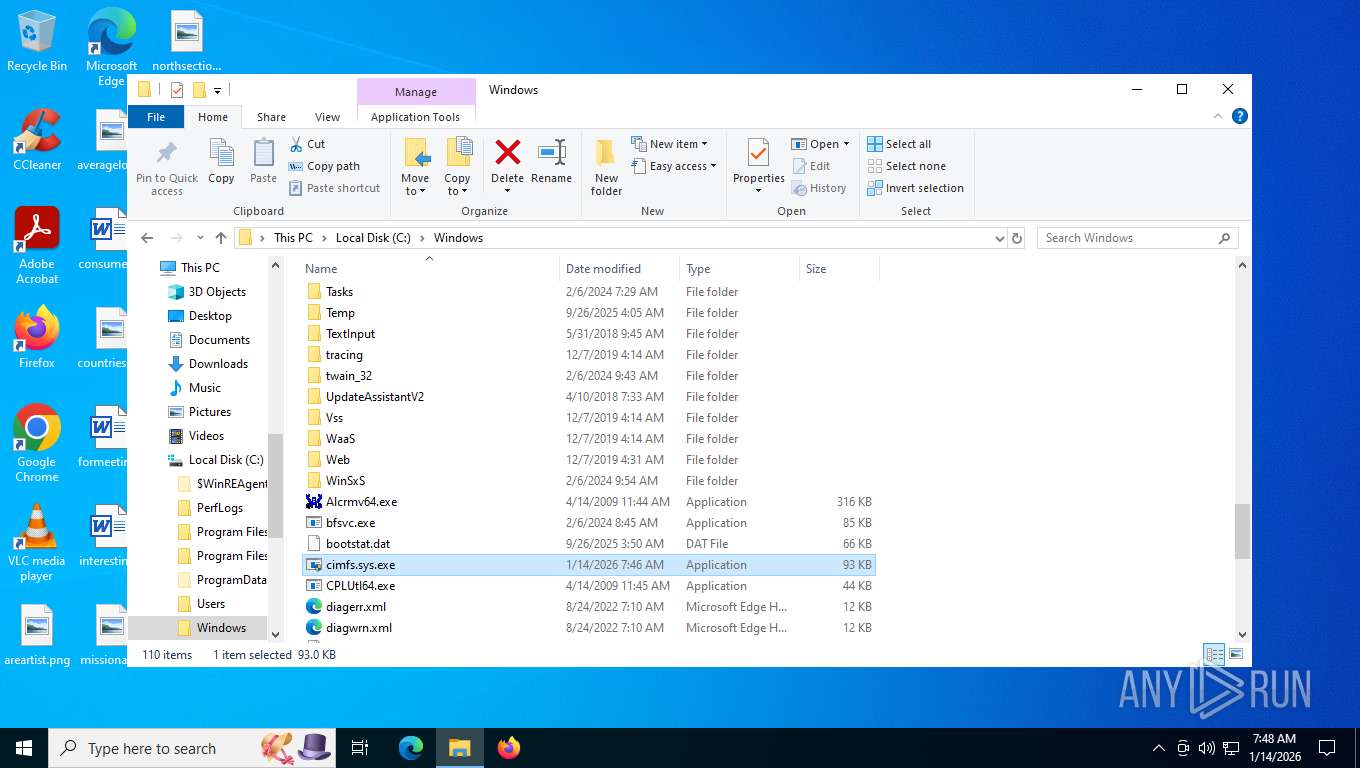
| 4636 | "C:\Windows\cimfs.sys.exe" | C:\Windows\cimfs.sys.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4912 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\x5emcjgl.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4968 | "C:\Windows\cimfs.sys.exe" | C:\Windows\cimfs.sys.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5040 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESE800.tmp" "c:\Users\admin\AppData\Local\Temp\CSC11667FFC7AC742B487ECD7E29FB51363.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 5752 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7220 | C:\WINDOWS\system32\pcwrun.exe "C:\Windows\cimfs.sys.exe" CompatTab | C:\Windows\System32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 848
Read events
11 836
Write events
12
Delete events
0
Modification events
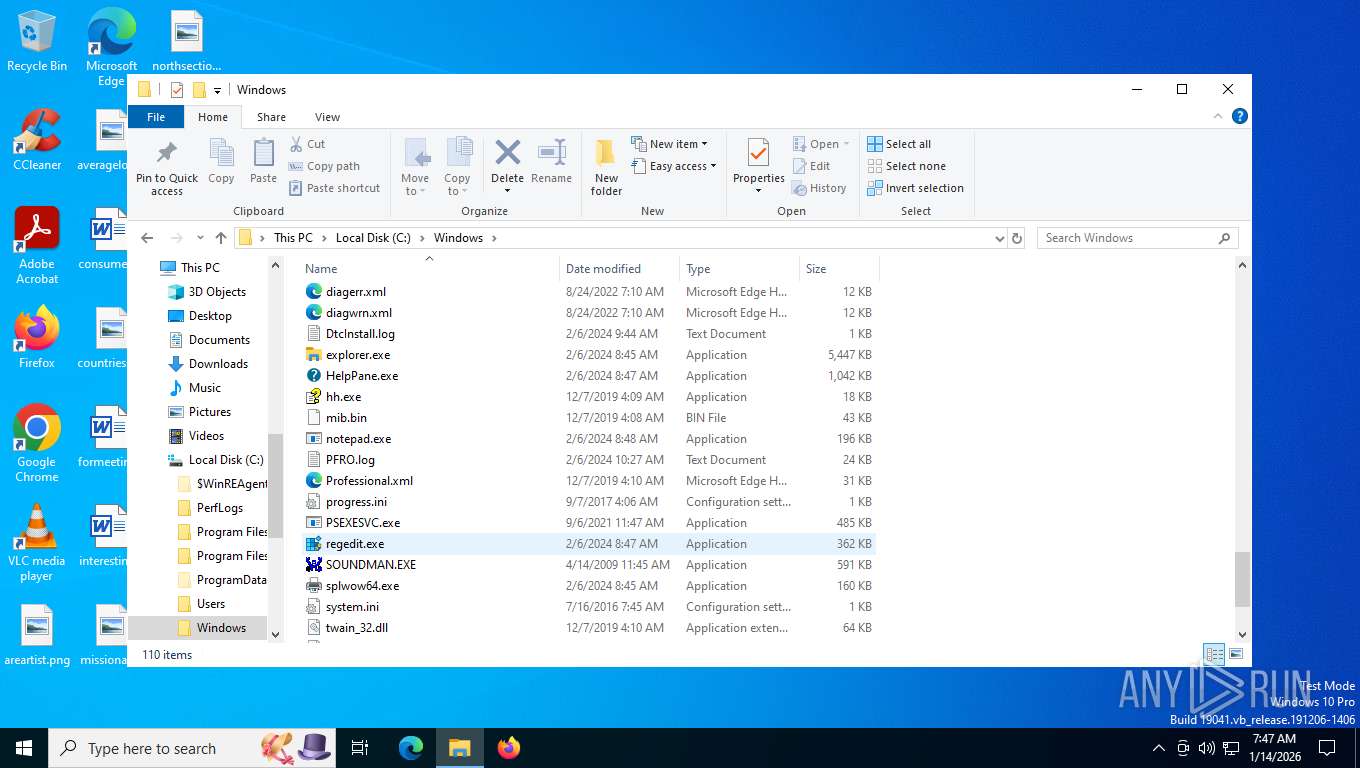
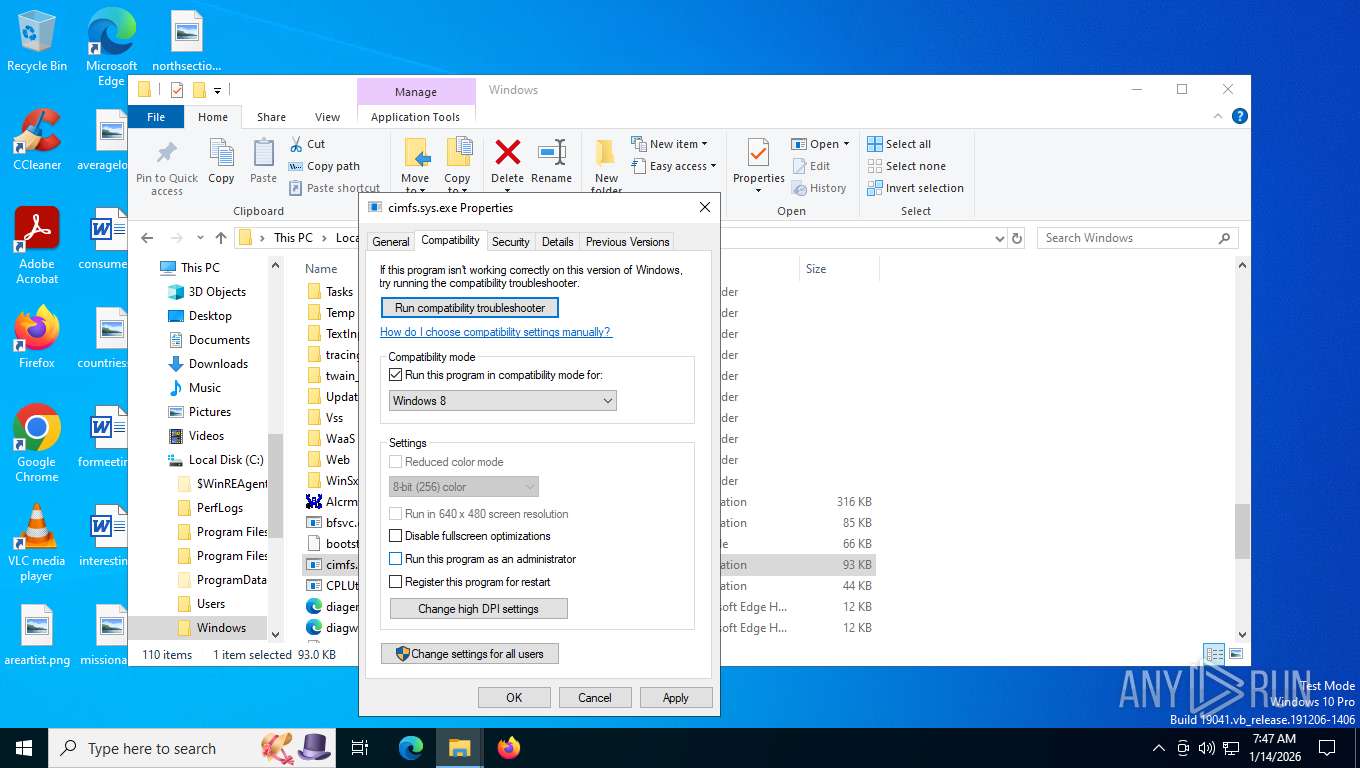
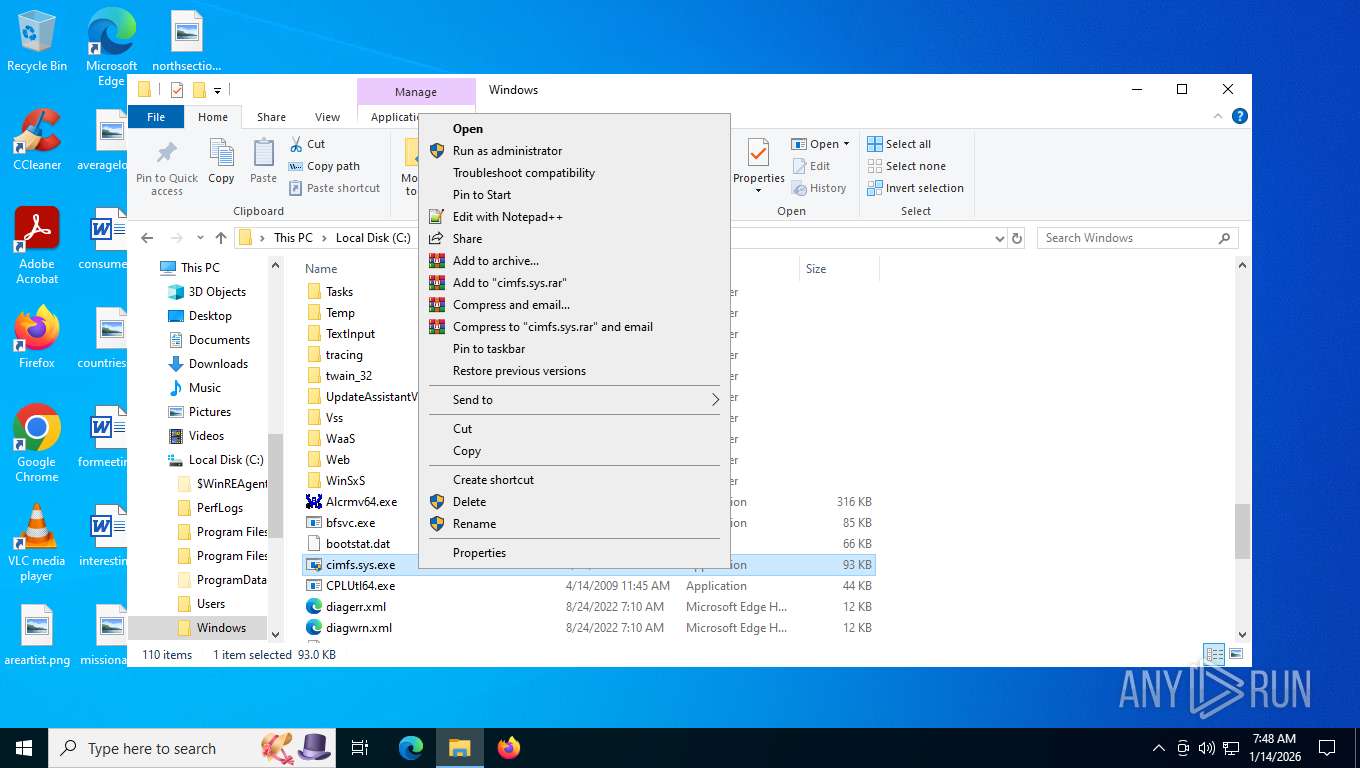
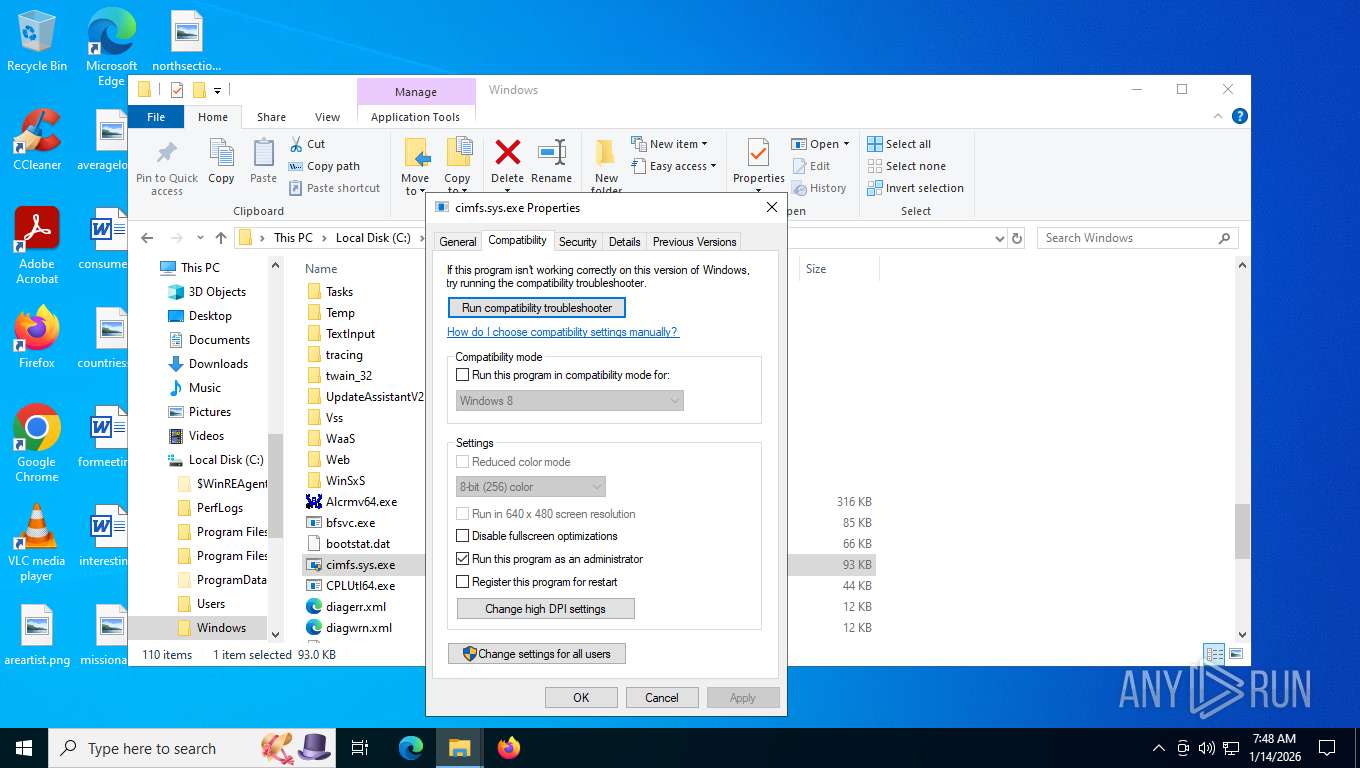
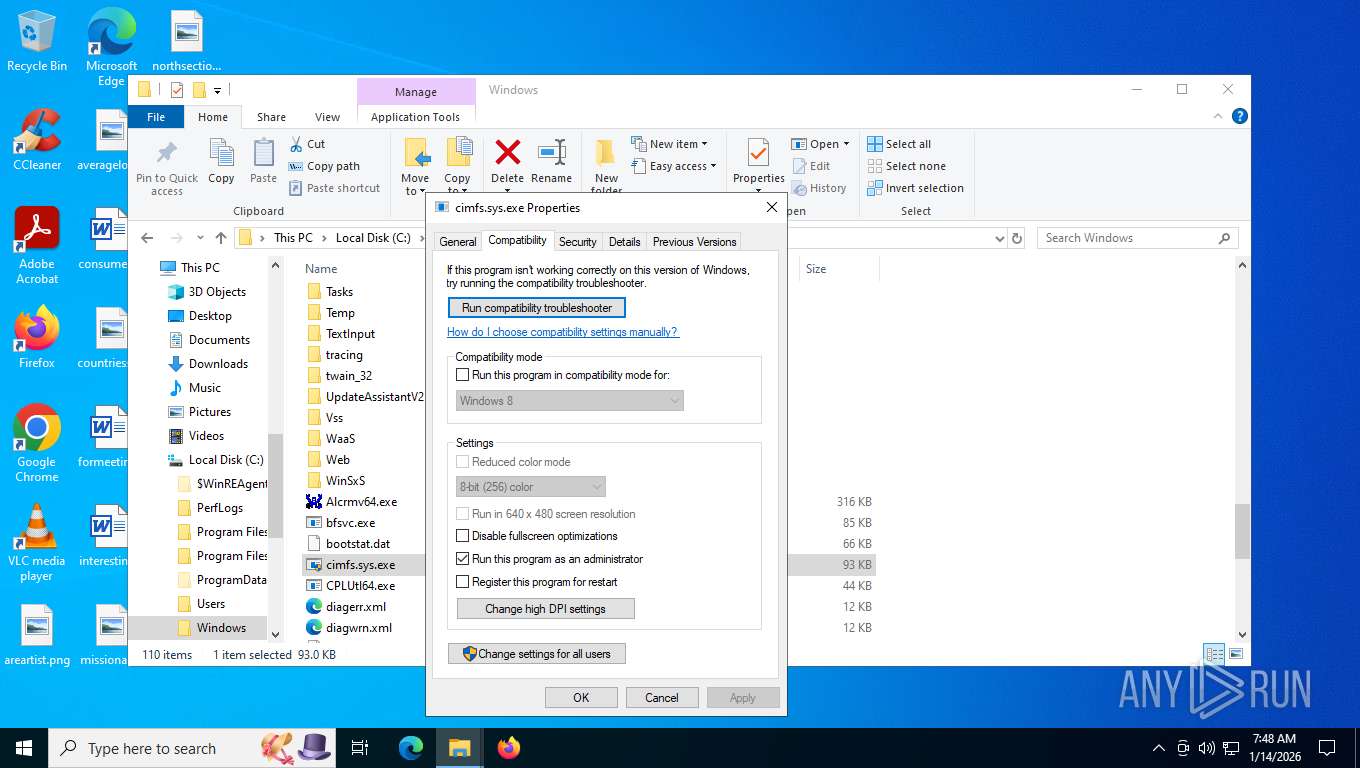
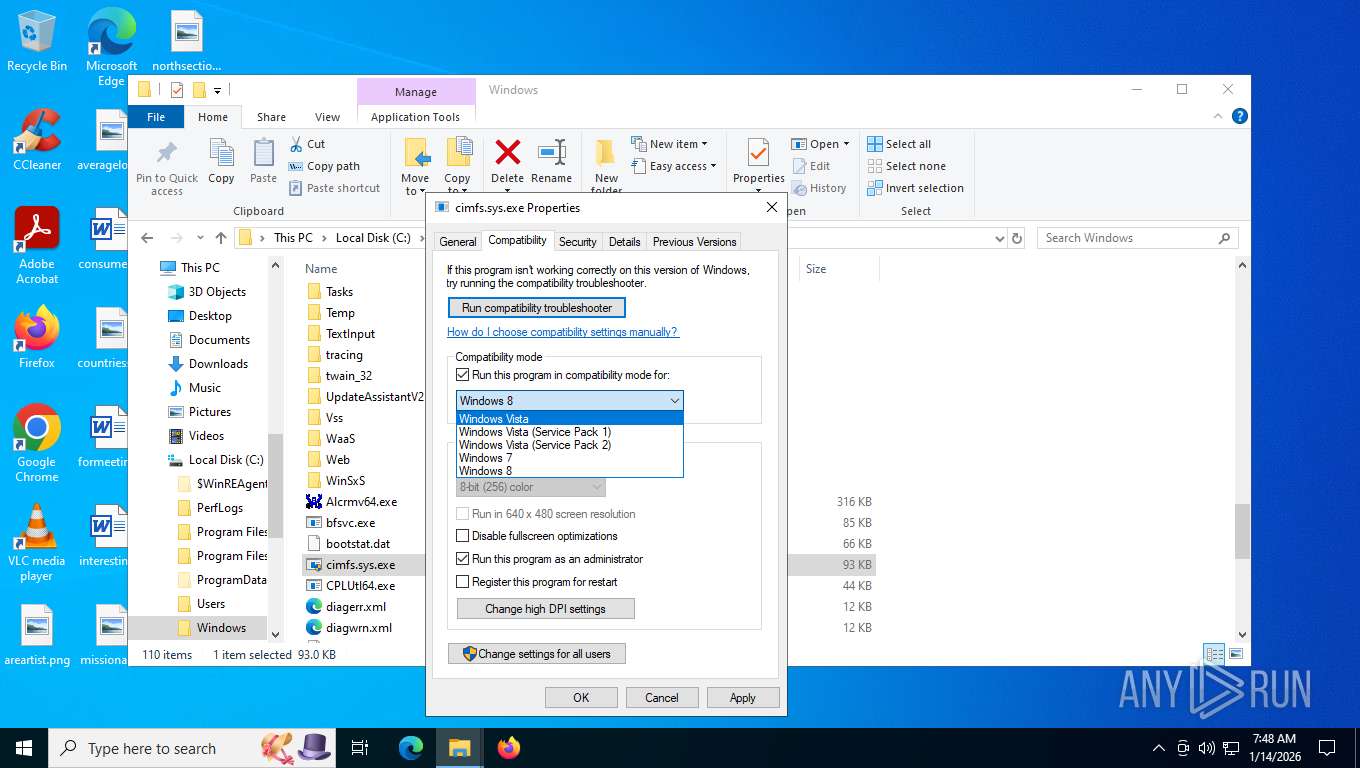
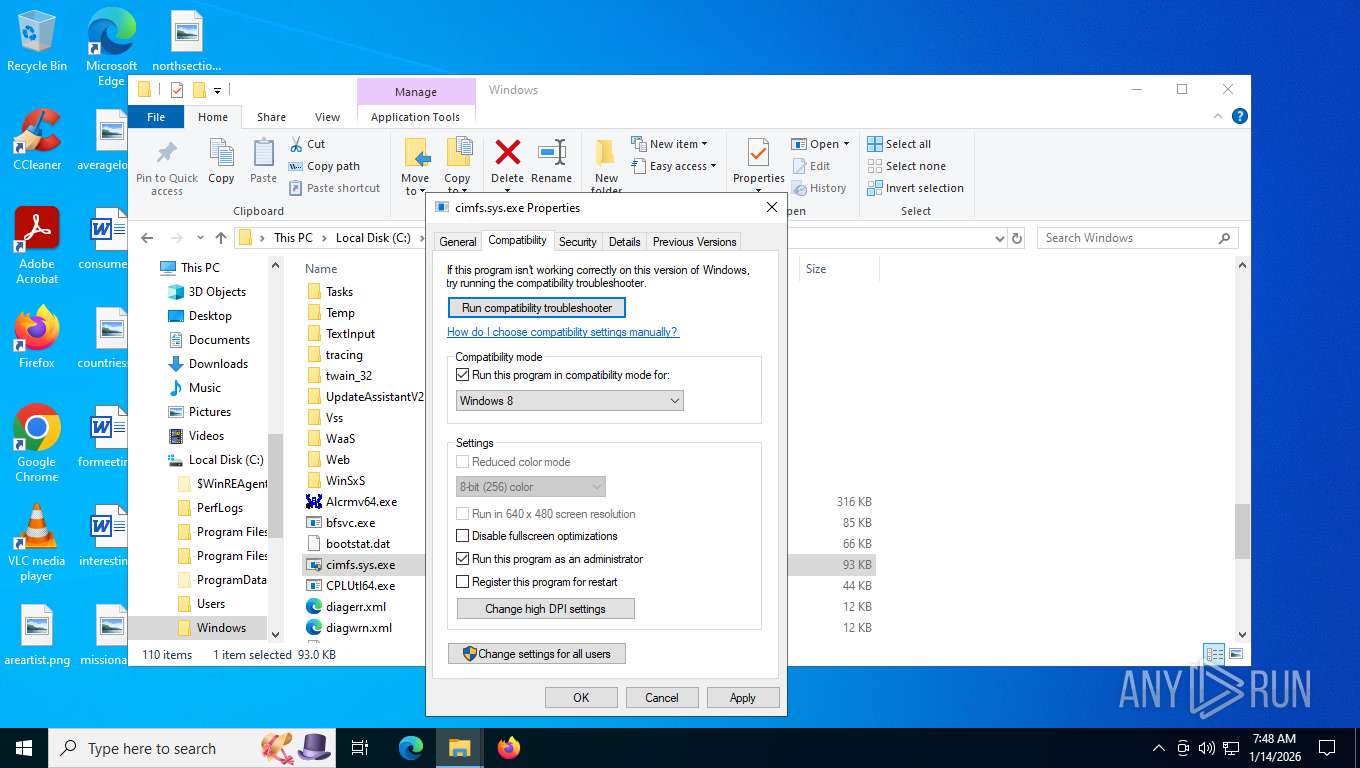
| (PID) Process: | (7300) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Windows\cimfs.sys.exe |
Value: ~^ WIN8RTM | |||
| (PID) Process: | (7300) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Layers |
| Operation: | write | Name: | C:\Windows\cimfs.sys.exe |
Value: ~ WIN8RTM | |||
Executable files
5
Suspicious files
12
Text files
25
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7232 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_00943ac8-4d26-4203-a90a-139fdc383bba\DiagPackage.dll | executable | |
MD5:C98E07483BC615D93BEF0BD16A4448AD | SHA256:CF435666DDCA273010E92606542A4A20E20846369ACB2DCDDB71DBE5584784AD | |||
| 7232 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_00943ac8-4d26-4203-a90a-139fdc383bba\en-US\CL_LocalizationData.psd1 | text | |
MD5:2C81A148F8E851CE008686F96E5BF911 | SHA256:1A2381382671147F56CF137E749CB8A18F176A16793B2266A70154EE27971437 | |||
| 7232 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_00943ac8-4d26-4203-a90a-139fdc383bba\result\results.xsl | xml | |
MD5:310E1DA2344BA6CA96666FB639840EA9 | SHA256:67401342192BABC27E62D4C1E0940409CC3F2BD28F77399E71D245EAE8D3F63C | |||
| 7300 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\wcgyp3ad.cmdline | text | |
MD5:22E690A05694A6F4429D66A67564937D | SHA256:802FAF7724092056AACE5D573D03021252137EF4616ABD76B1587C8AA427B8A7 | |||
| 2460 | csc.exe | C:\Users\admin\AppData\Local\Temp\wcgyp3ad.dll | executable | |
MD5:93FB70E766FA894C9D020F59BCE04425 | SHA256:C248E521E89904565BF9518A7BA98ED8F99D427B293FC1CEB5157F8D6ED617E1 | |||
| 5040 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESE800.tmp | binary | |
MD5:A4031282046360D45DCE7BDA8E58B4E6 | SHA256:16E106AE60774EC9D87DDF5AFB7C352B73BFE8FF77A51D26E2AF7586F4080EEC | |||
| 7300 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_armly1k4.dyg.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7232 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_00943ac8-4d26-4203-a90a-139fdc383bba\RS_ProgramCompatibilityWizard.ps1 | text | |
MD5:E6B5B69A9F0C44BDDA6A5662054CD8BF | SHA256:F7FD69FAA5D66BEDD294BFCBF5962F7A70D60F69D04251F8CF3ACA927D878E3A | |||
| 7232 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_00943ac8-4d26-4203-a90a-139fdc383bba\en-US\DiagPackage.dll.mui | executable | |
MD5:D7309F9B759CCB83B676420B4BDE0182 | SHA256:51D06AFFD4DB0E4B37D35D0E85B8209D5FAB741904E8D03DF1A27A0BE102324F | |||
| 2460 | csc.exe | C:\Users\admin\AppData\Local\Temp\wcgyp3ad.out | text | |
MD5:5AC37560E1B7B54C08E7704BED786B37 | SHA256:BB806DD247BEC1A8C3C8F51259F612B141D2C1C9F9326A587D582FAE431A07A0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
32
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
3352 | svchost.exe | POST | 200 | 20.190.160.66:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
3352 | svchost.exe | POST | 200 | 20.190.160.66:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
2672 | SIHClient.exe | GET | 200 | 13.85.23.206:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
2672 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
2672 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
404 | svchost.exe | GET | 200 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | text | 5.58 Kb | whitelisted |
404 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3352 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
404 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1976 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3352 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3352 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
404 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
404 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |