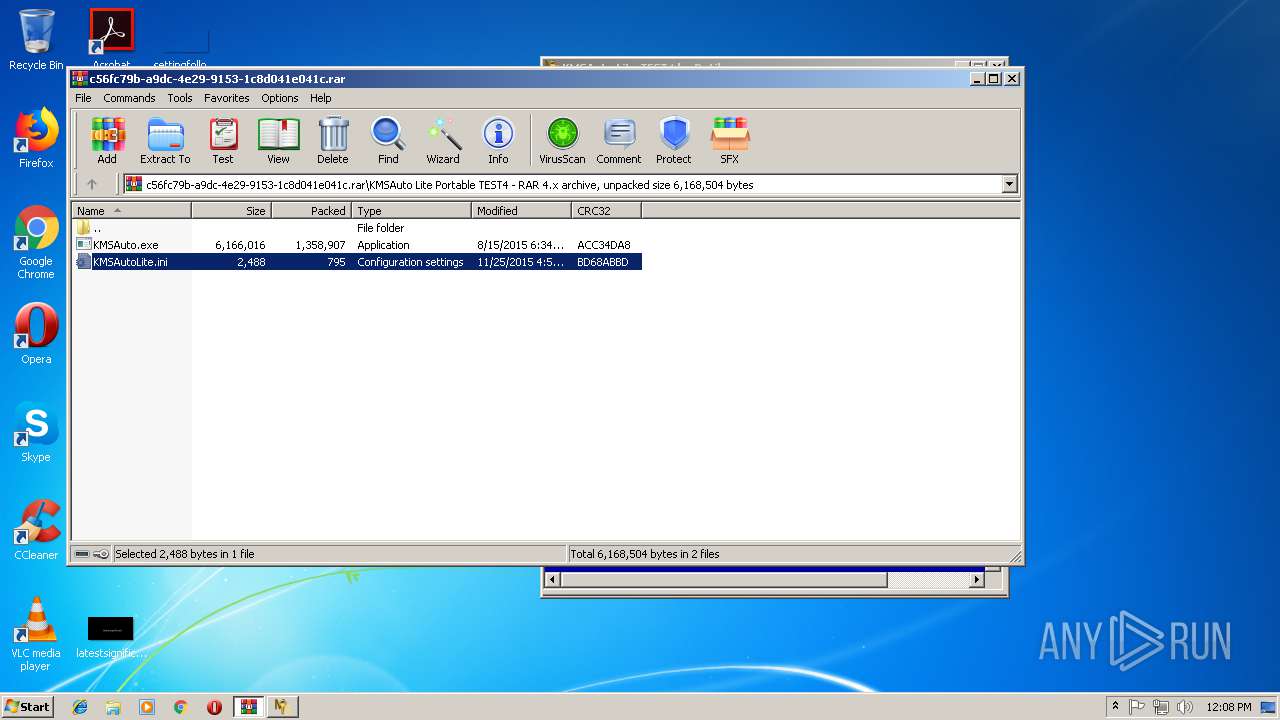
| download: | Ativador%20para%20Windows%2010.rar |
| Full analysis: | https://app.any.run/tasks/3413f579-3135-4f80-8fb0-63a107a2844b |
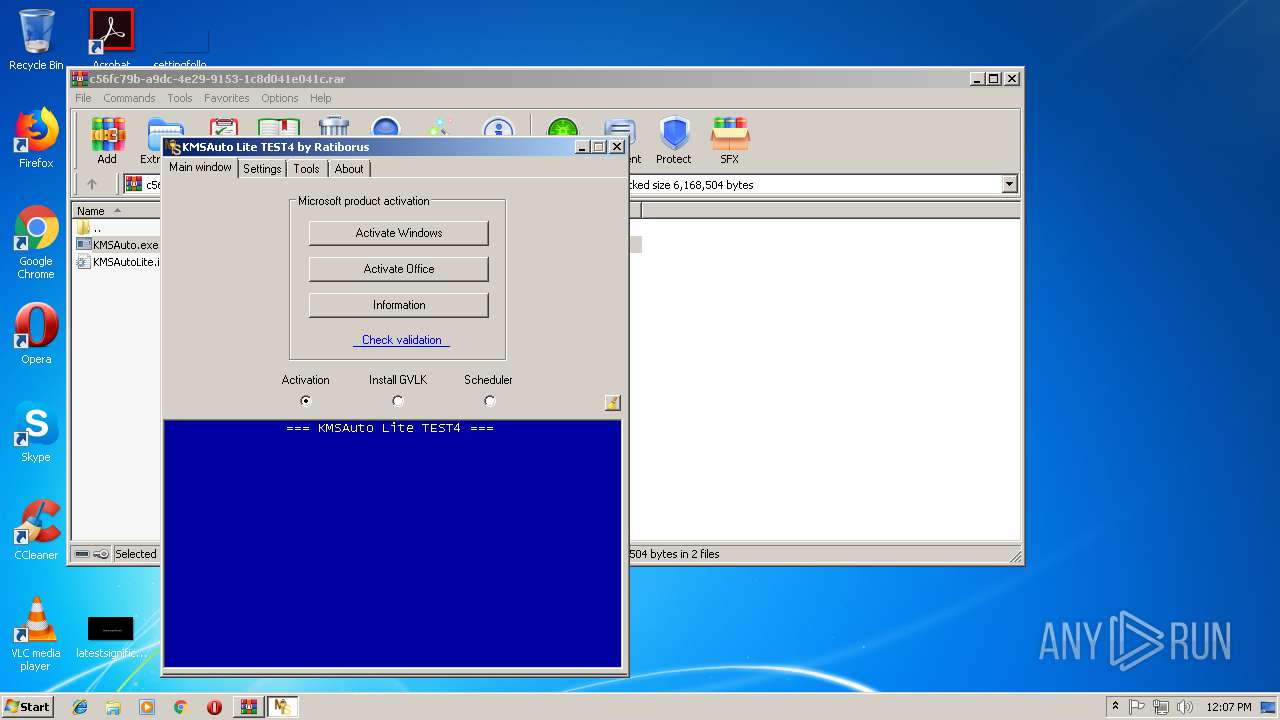
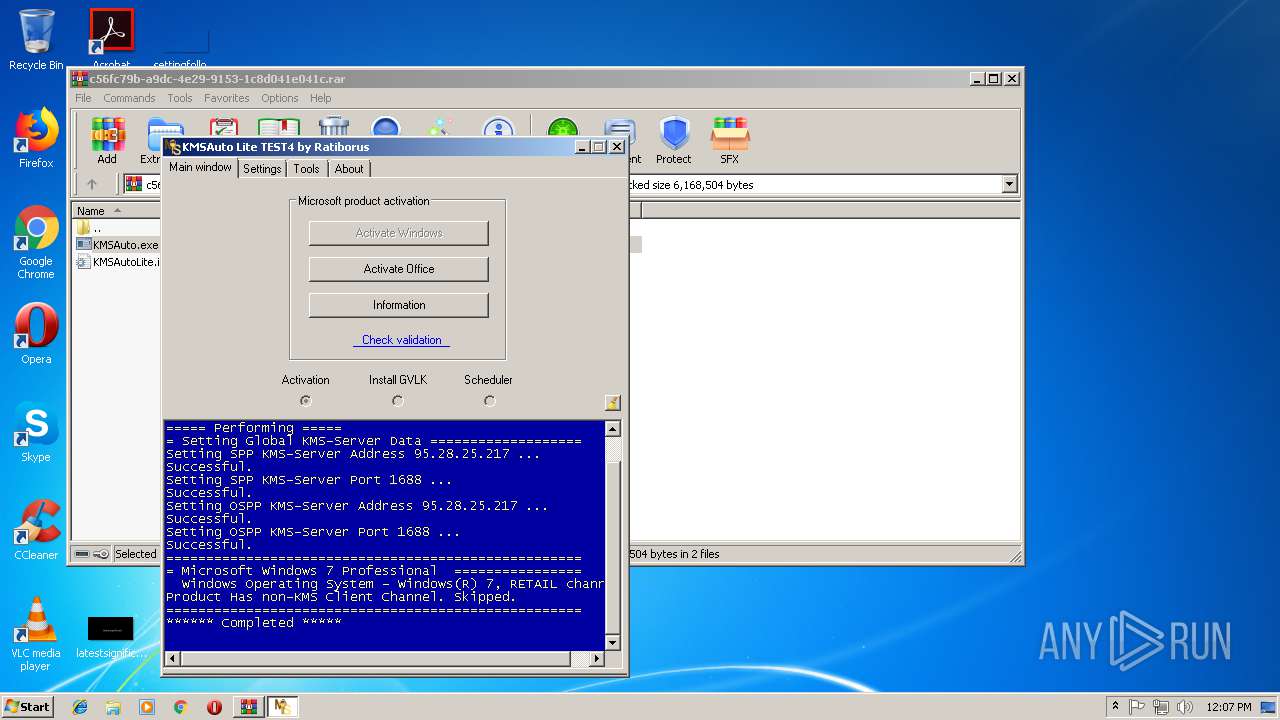
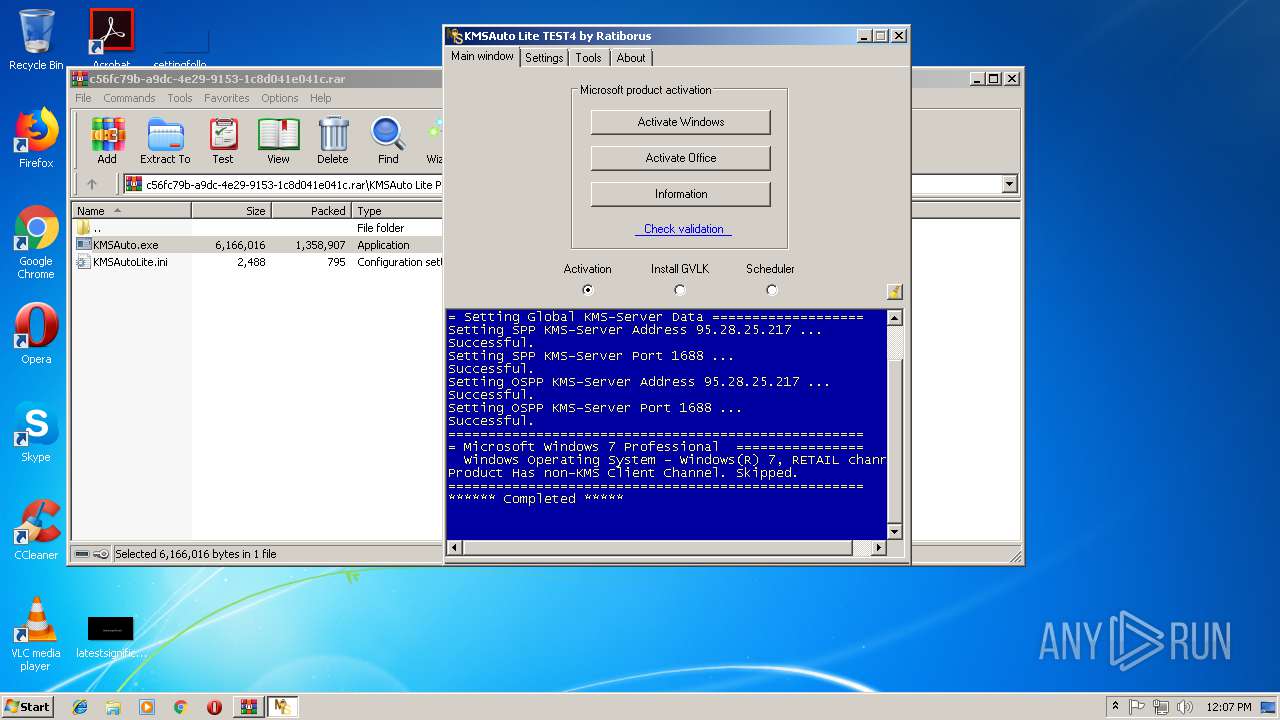
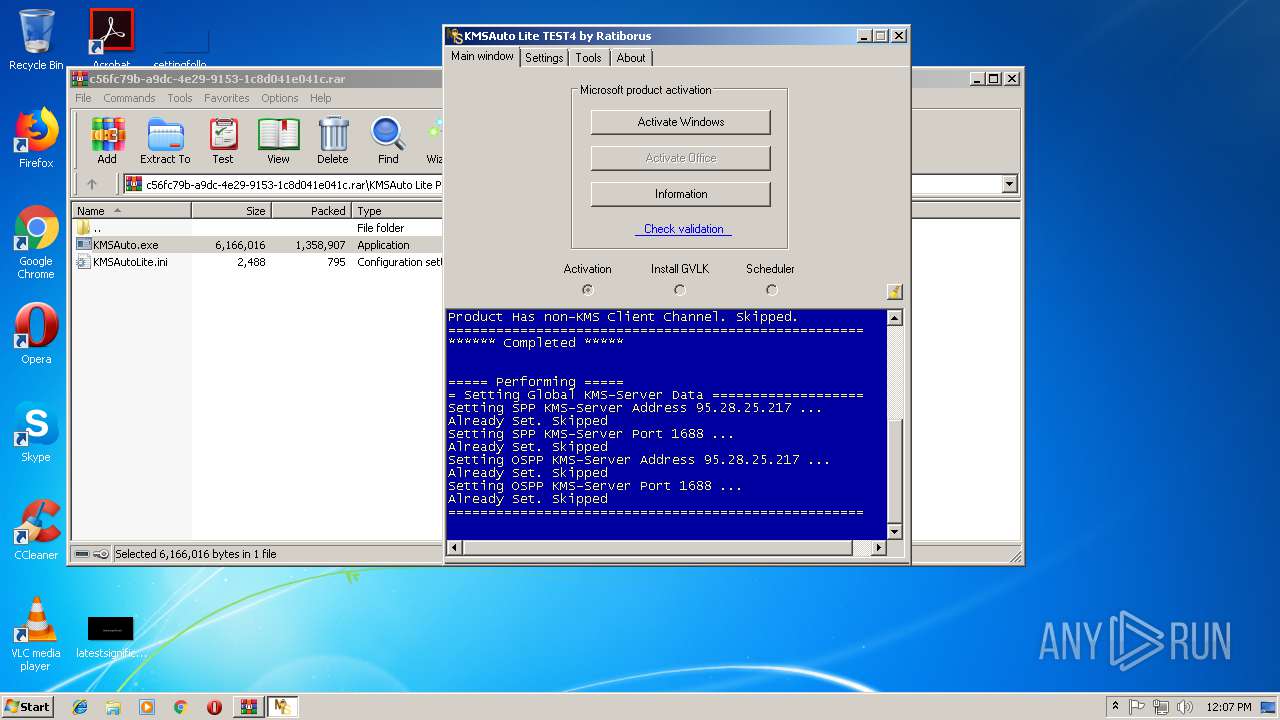
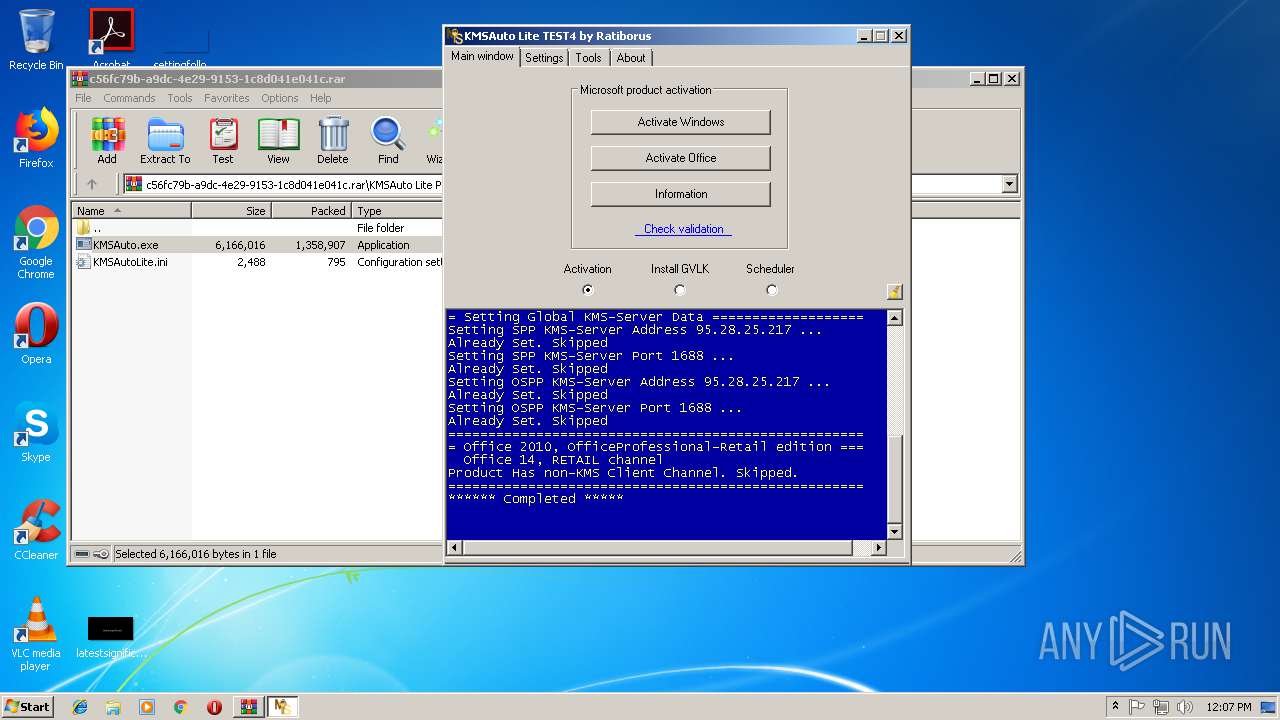
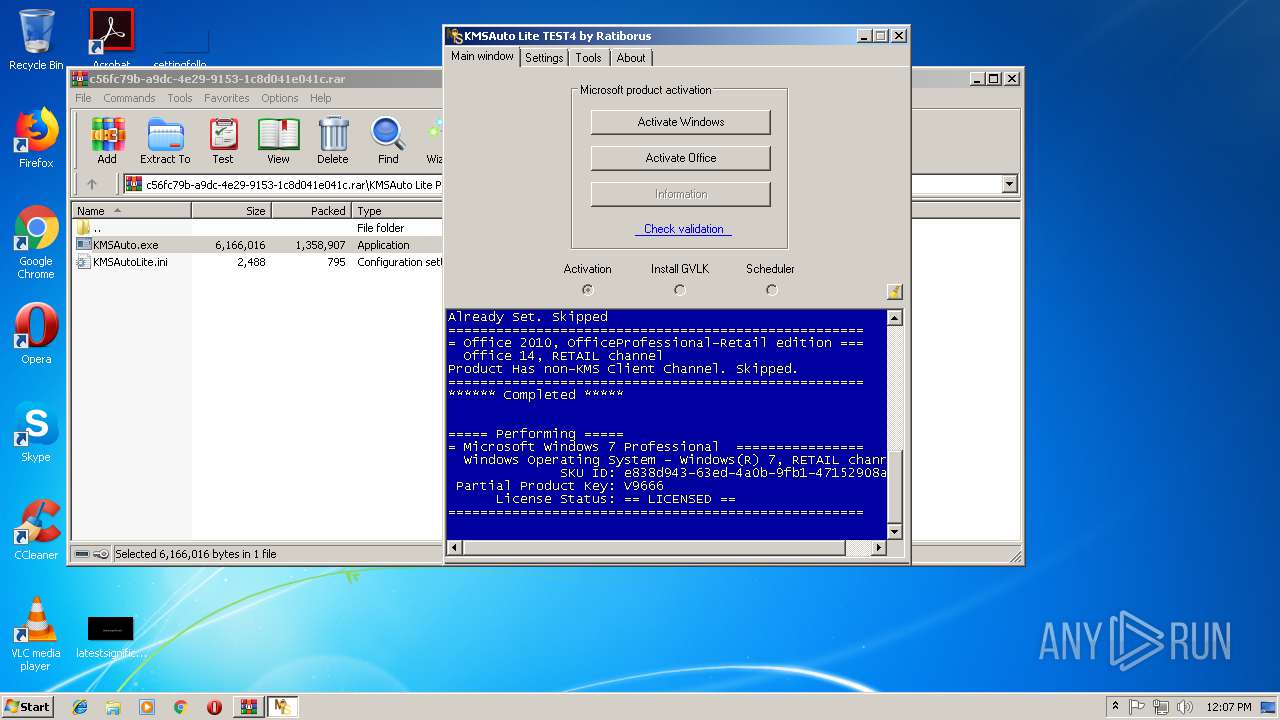
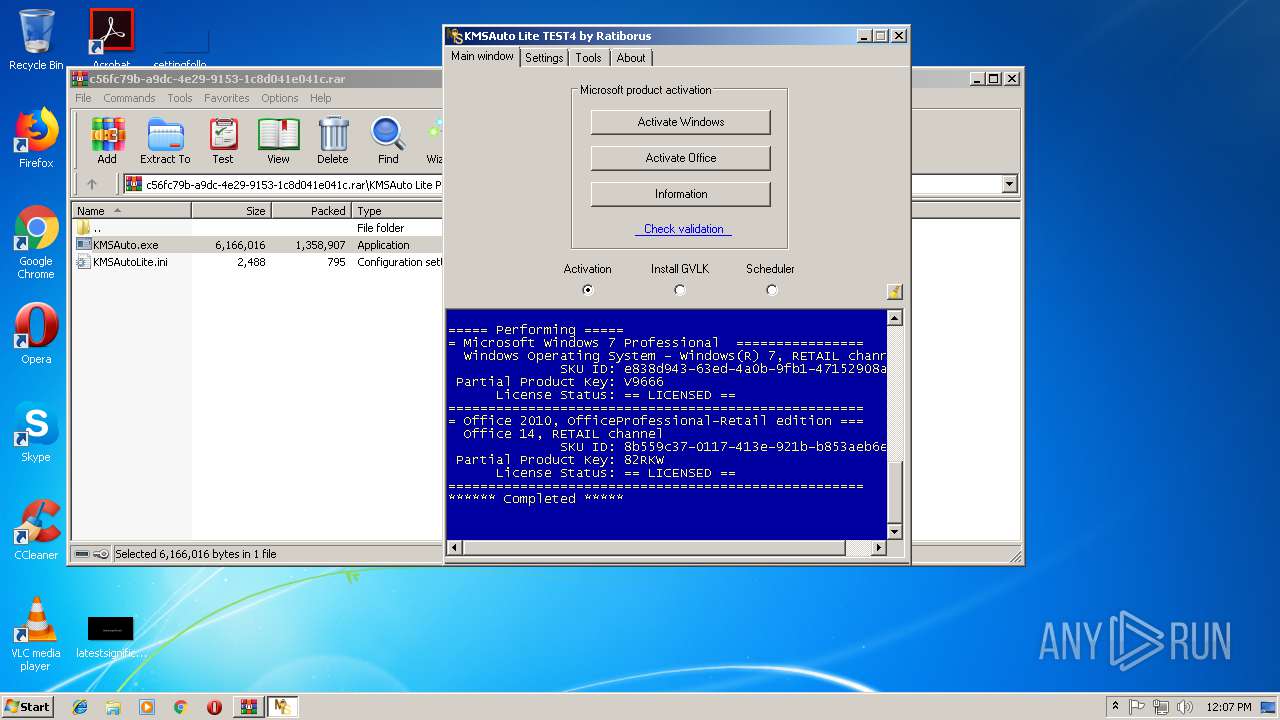
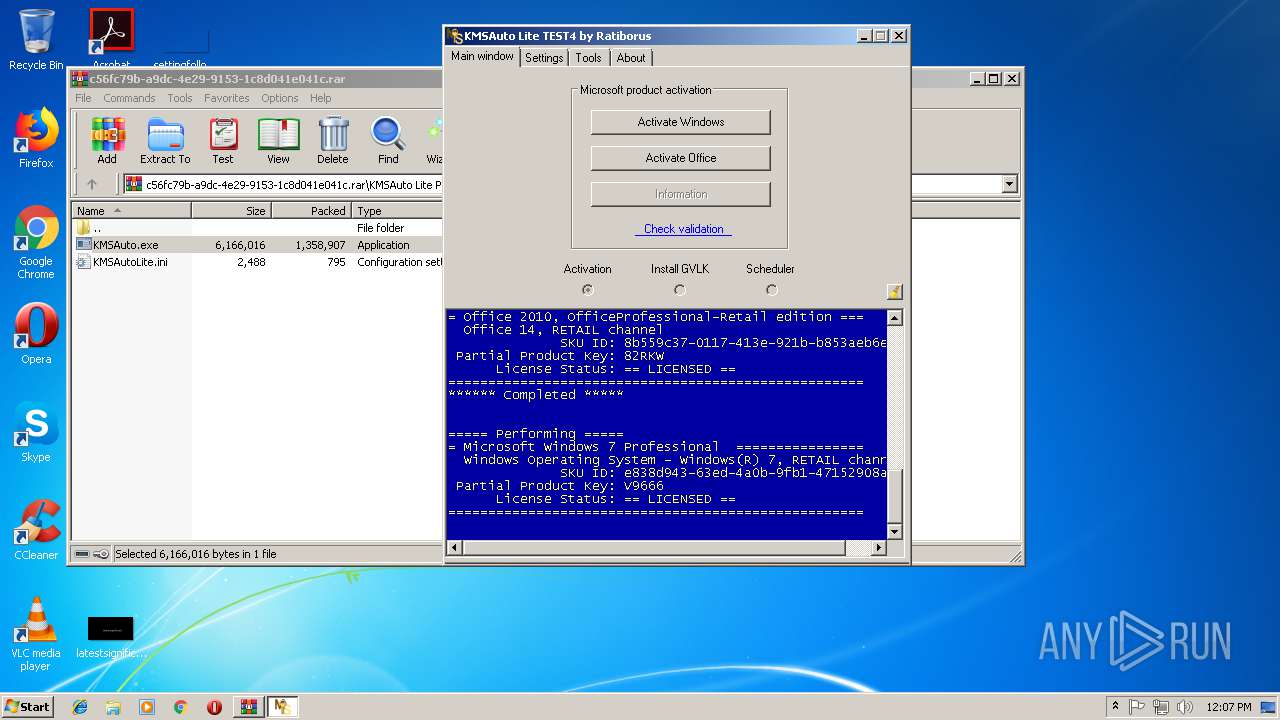
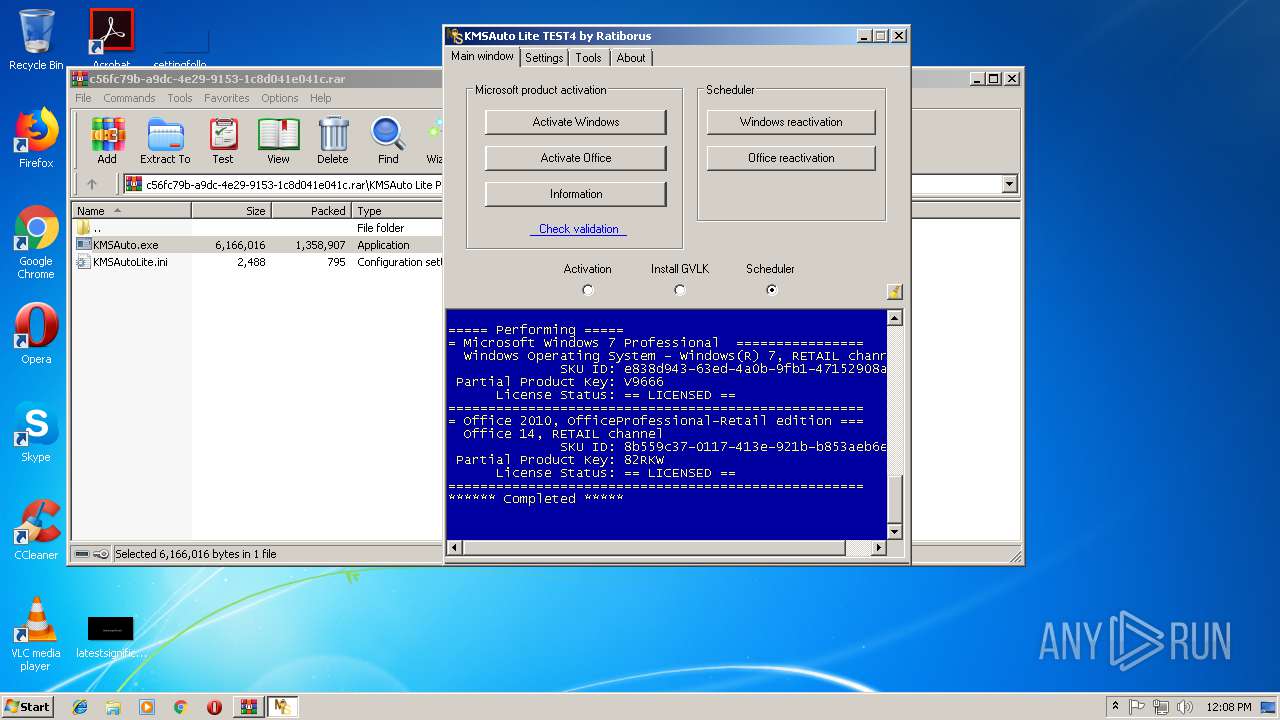
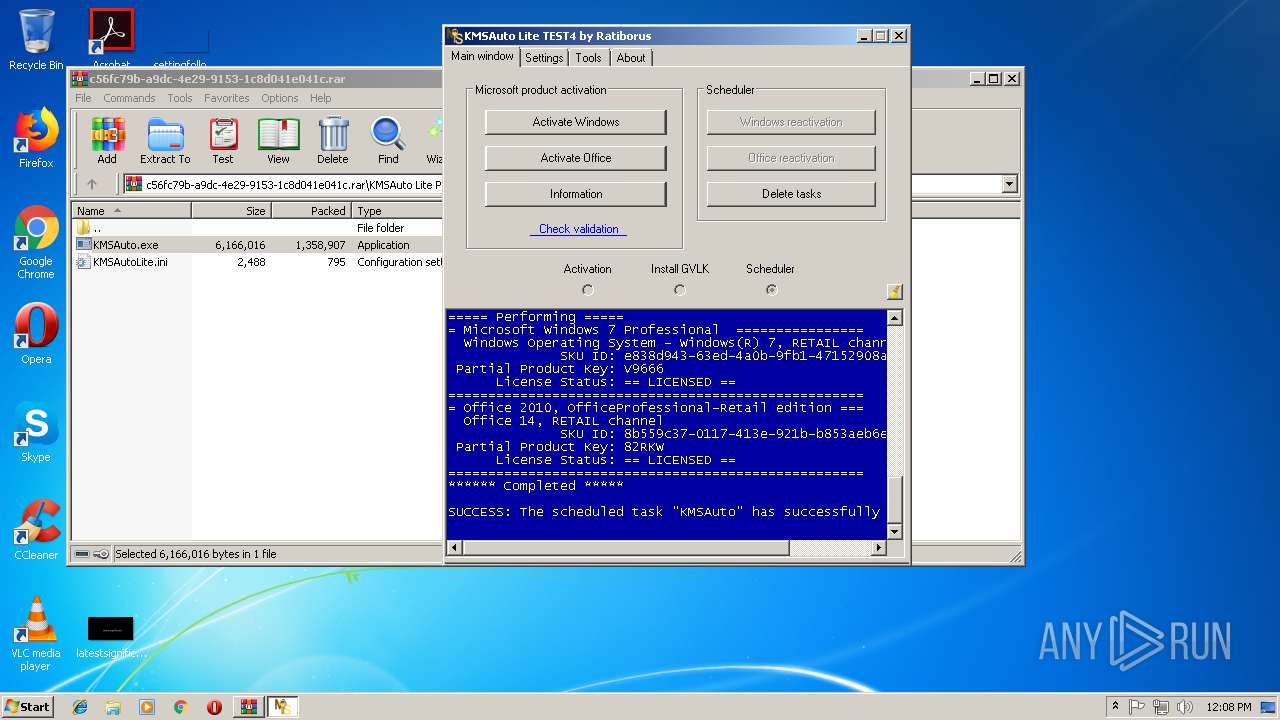
| Verdict: | Malicious activity |
| Analysis date: | November 11, 2018, 12:06:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
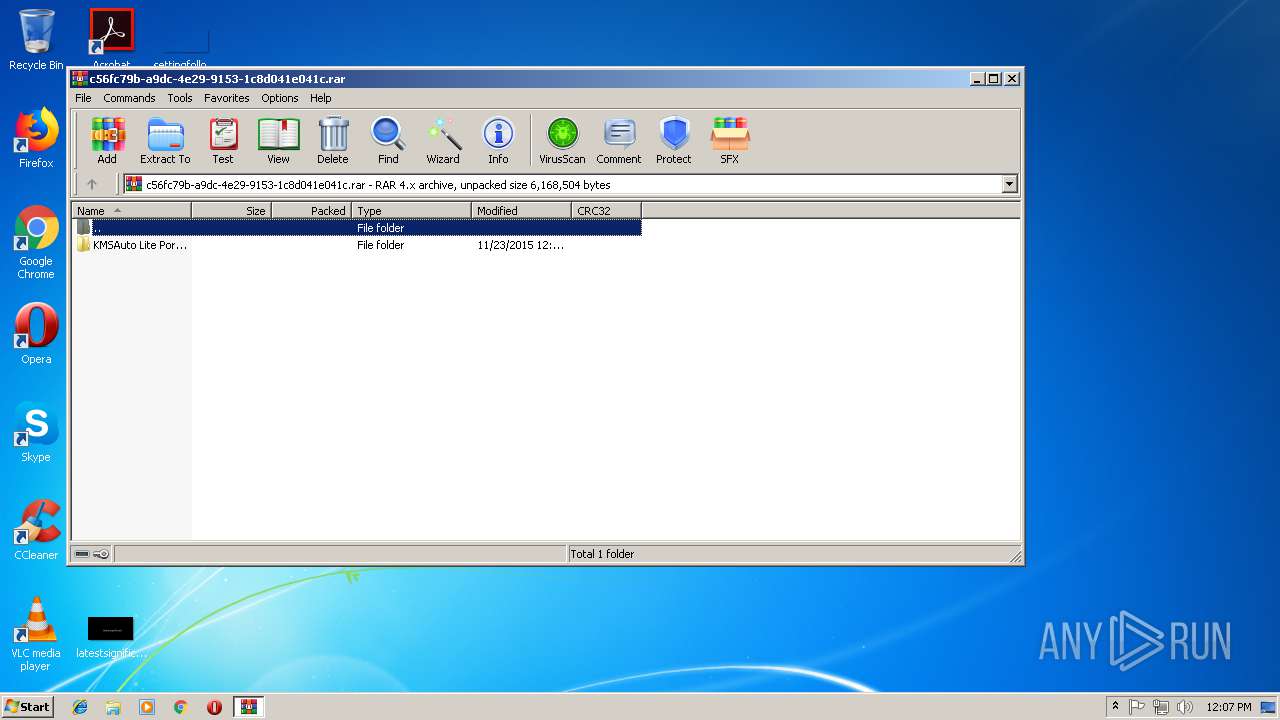
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 506F933637B16F11B4123686950887C1 |
| SHA1: | FF904B190757EA75C32234A196D343CAE6867C83 |
| SHA256: | C398E85ED47536EEABFBE17A6FEC1950435BC3F17BC2DFFE9EAFF8DF56AD1ADE |
| SSDEEP: | 24576:3lpJRWNWoD/9gVYubECzFA09PZsPhQToK4ZQX/7r3o3Jg4WMfJX7PH4Ux37sWVBO:3lpYb9g2ypzliQoOvmJN57r7RV5vO |
MALICIOUS
Application was dropped or rewritten from another process
- KMSAuto.exe (PID: 2124)
- bin.dat (PID: 3696)
- KMSAuto.exe (PID: 3768)
- KMSSS.exe (PID: 4008)
- FakeClient.exe (PID: 2216)
- bin_x86.dat (PID: 4060)
- bin.dat (PID: 3848)
- bin_x86.dat (PID: 3604)
- KMSSS.exe (PID: 844)
- FakeClient.exe (PID: 1388)
Loads dropped or rewritten executable
- FakeClient.exe (PID: 2216)
- FakeClient.exe (PID: 1388)
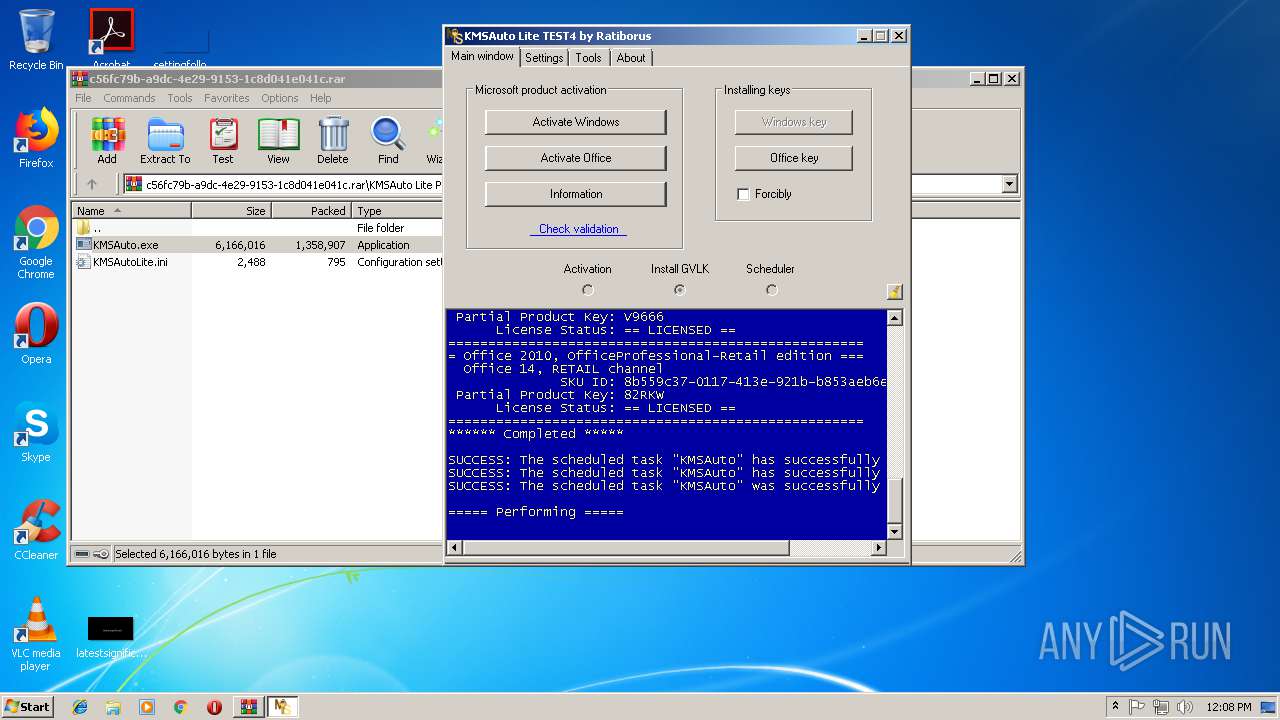
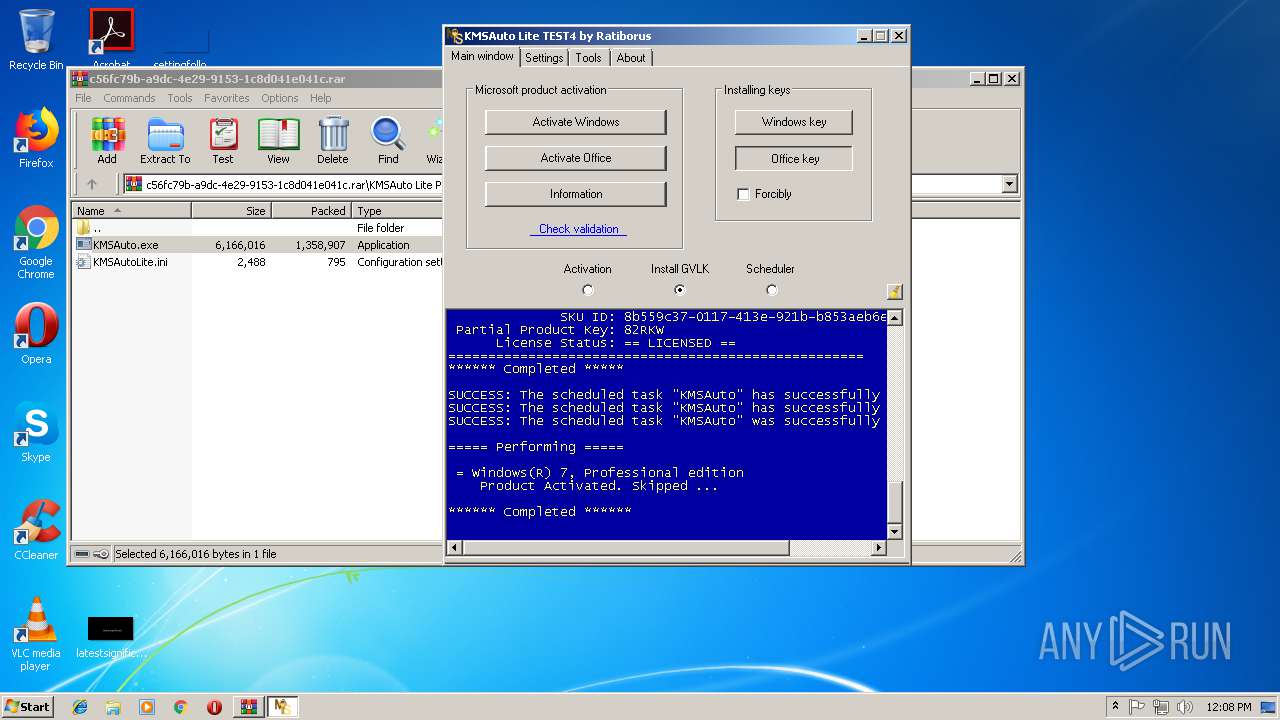
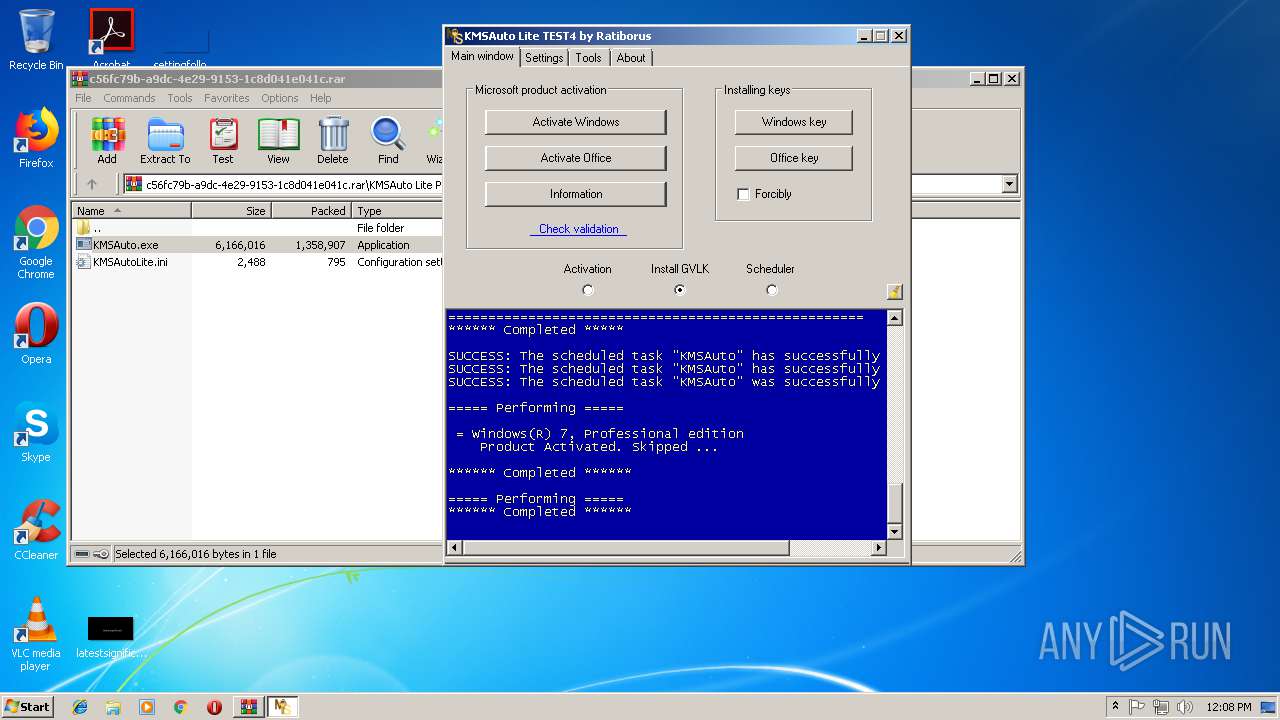
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4064)
- cmd.exe (PID: 3448)
- cmd.exe (PID: 3756)
- cmd.exe (PID: 2756)
- cmd.exe (PID: 648)
- cmd.exe (PID: 936)
- cmd.exe (PID: 1020)
- cmd.exe (PID: 3548)
- cmd.exe (PID: 2264)
- cmd.exe (PID: 1380)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2740)
- schtasks.exe (PID: 3300)
- schtasks.exe (PID: 2744)
- schtasks.exe (PID: 2116)
- schtasks.exe (PID: 3244)
- schtasks.exe (PID: 3348)
- schtasks.exe (PID: 3000)
- schtasks.exe (PID: 2604)
- schtasks.exe (PID: 1368)
- schtasks.exe (PID: 564)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2296)
- bin.dat (PID: 3696)
- bin_x86.dat (PID: 4060)
- KMSAuto.exe (PID: 3768)
- bin.dat (PID: 3848)
- bin_x86.dat (PID: 3604)
Creates files in the Windows directory
- bin.dat (PID: 3696)
- KMSAuto.exe (PID: 3768)
- KMSSS.exe (PID: 4008)
- bin_x86.dat (PID: 4060)
- bin.dat (PID: 3848)
- bin_x86.dat (PID: 3604)
- KMSSS.exe (PID: 844)
Starts application with an unusual extension
- cmd.exe (PID: 2108)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 2632)
Executes scripts
- cmd.exe (PID: 2016)
- cmd.exe (PID: 1000)
- cmd.exe (PID: 2456)
- cmd.exe (PID: 3308)
- cmd.exe (PID: 684)
- cmd.exe (PID: 2944)
Starts CMD.EXE for commands execution
- KMSAuto.exe (PID: 3768)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3424)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 1984)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 1744)
- cmd.exe (PID: 800)
Starts SC.EXE for service management
- cmd.exe (PID: 3688)
- cmd.exe (PID: 664)
- cmd.exe (PID: 2472)
- cmd.exe (PID: 1576)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 3476)
- cmd.exe (PID: 3416)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 3132)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 324)
- cmd.exe (PID: 4032)
Removes files from Windows directory
- KMSAuto.exe (PID: 3768)
Creates or modifies windows services
- KMSAuto.exe (PID: 3768)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1776)
- cmd.exe (PID: 3524)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
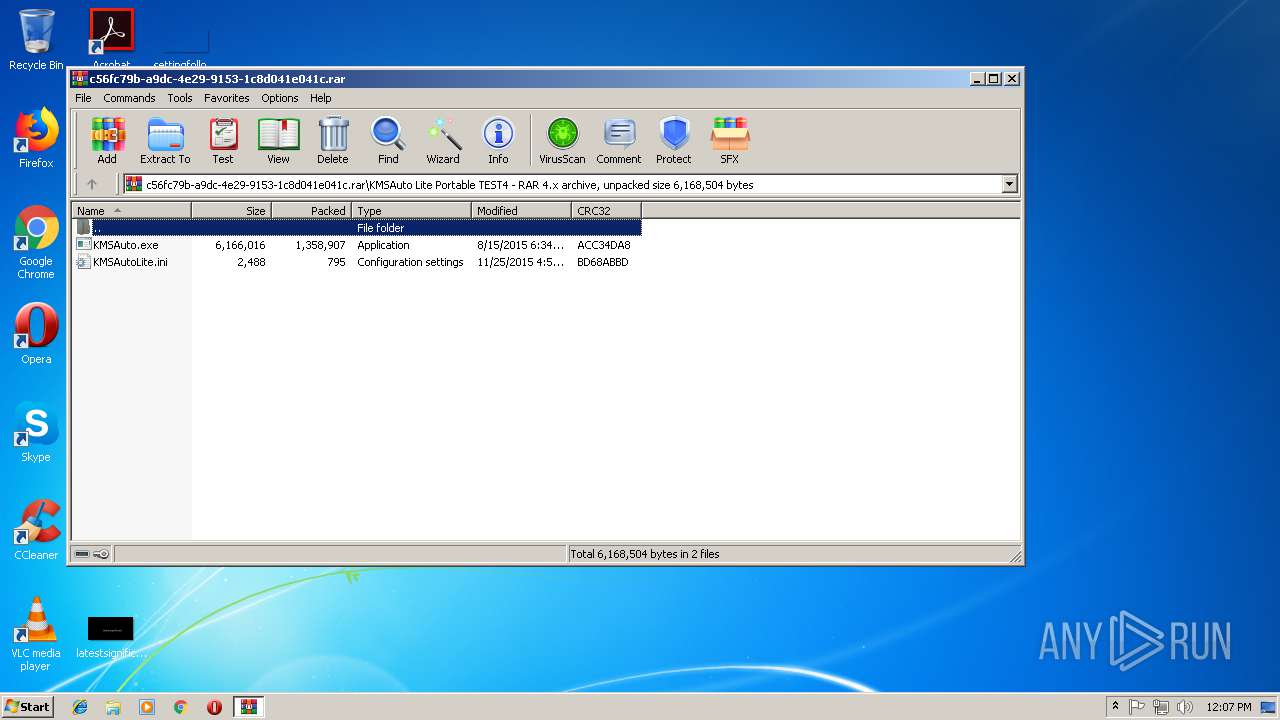
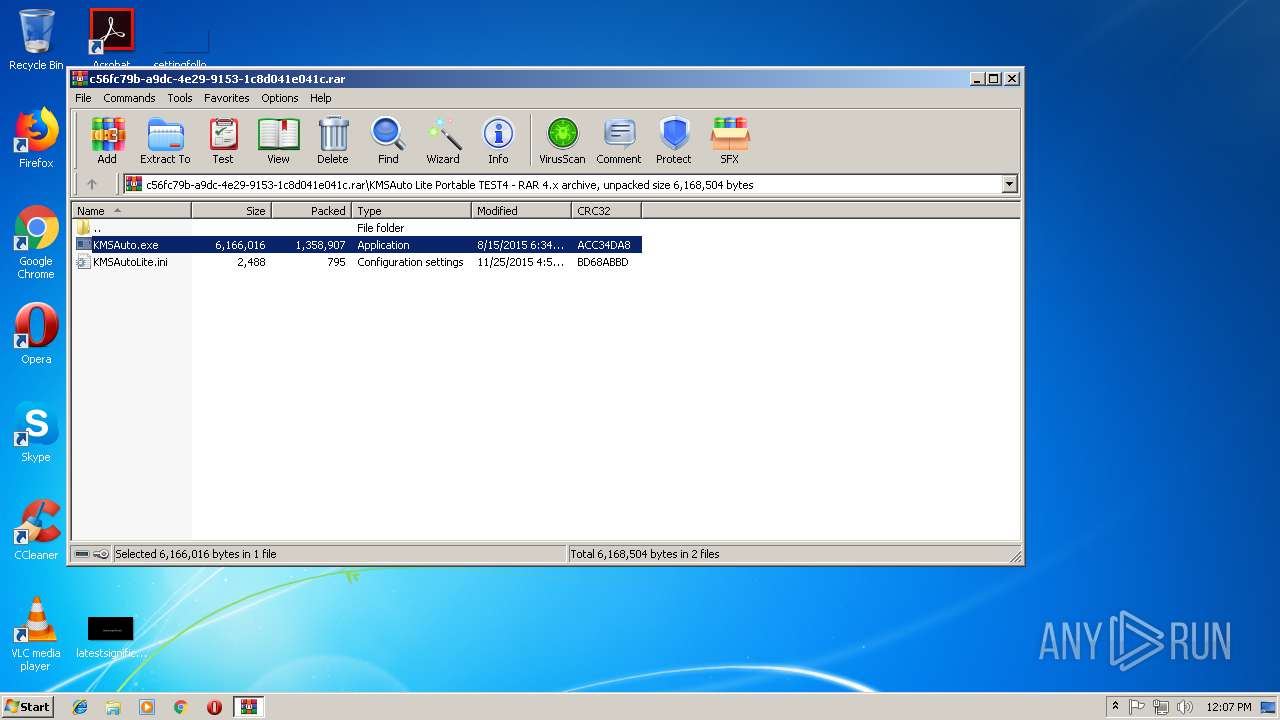
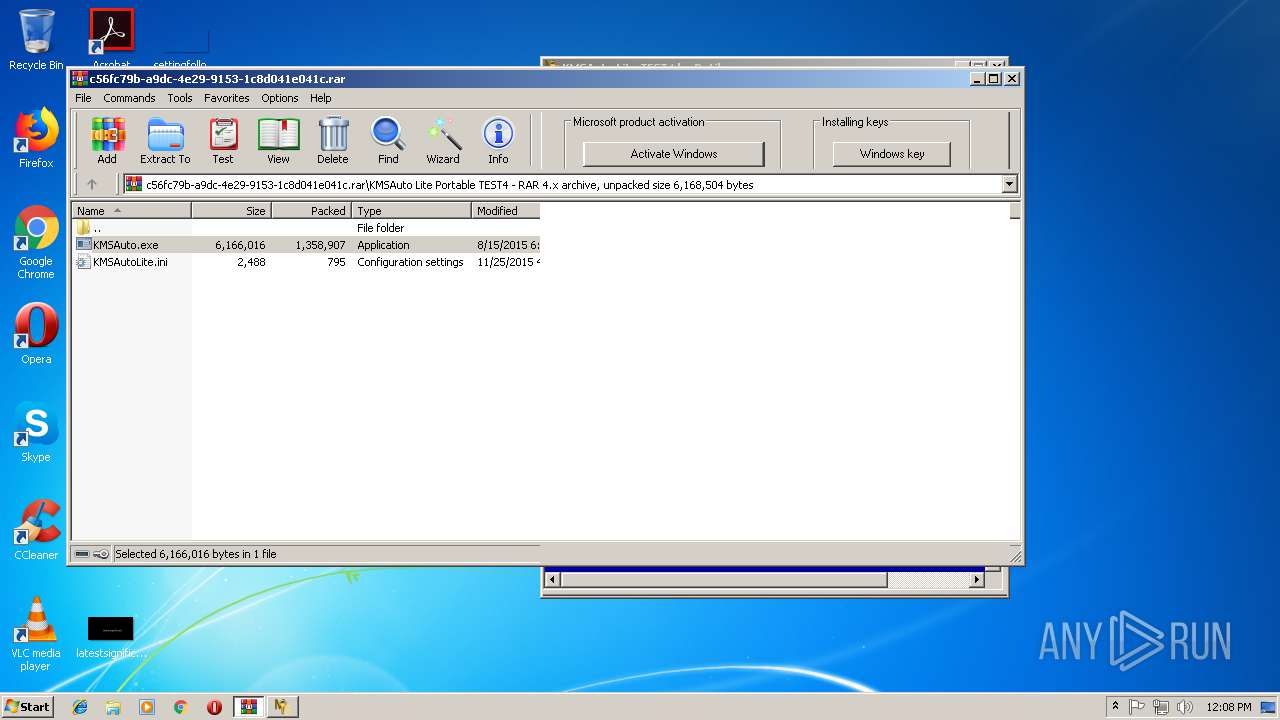
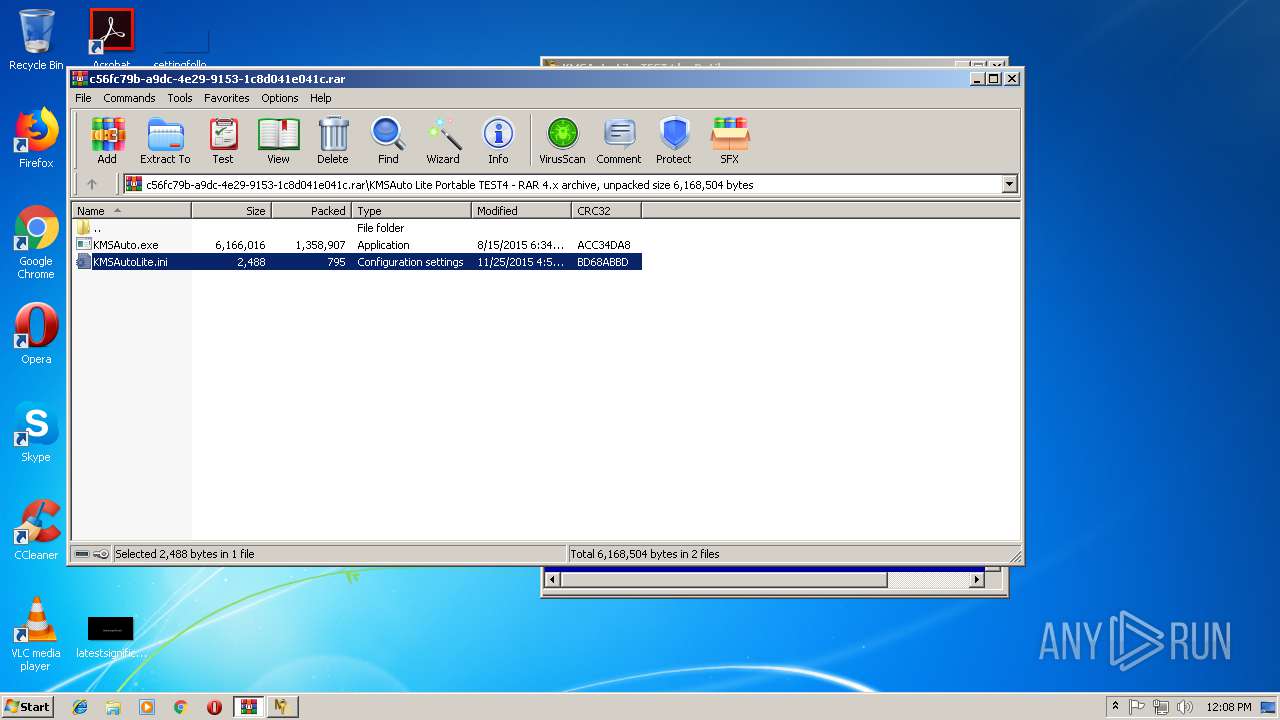
| CompressedSize: | 1358972 |
|---|---|
| UncompressedSize: | 6166016 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2015:08:15 06:34:17 |
| PackingMethod: | Normal |
| ArchivedFileName: | KMSAuto Lite Portable TEST4\KMSAuto.exe |
Total processes
189
Monitored processes
102
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
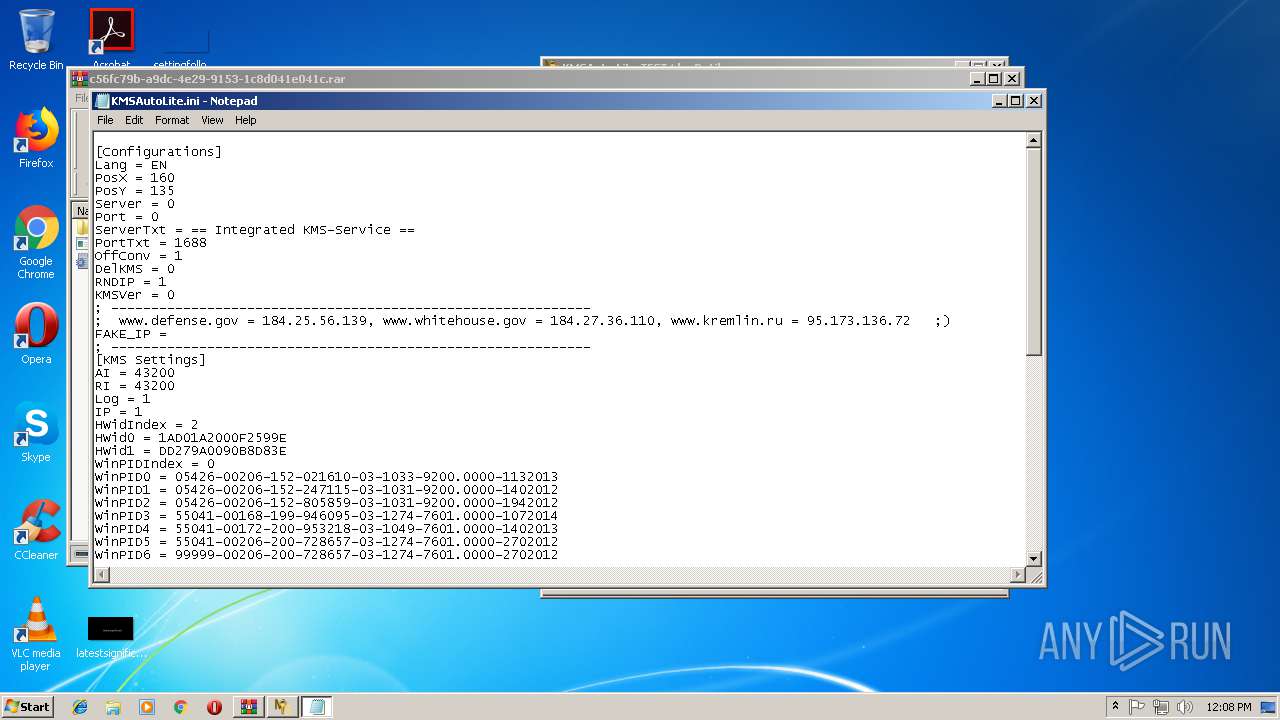
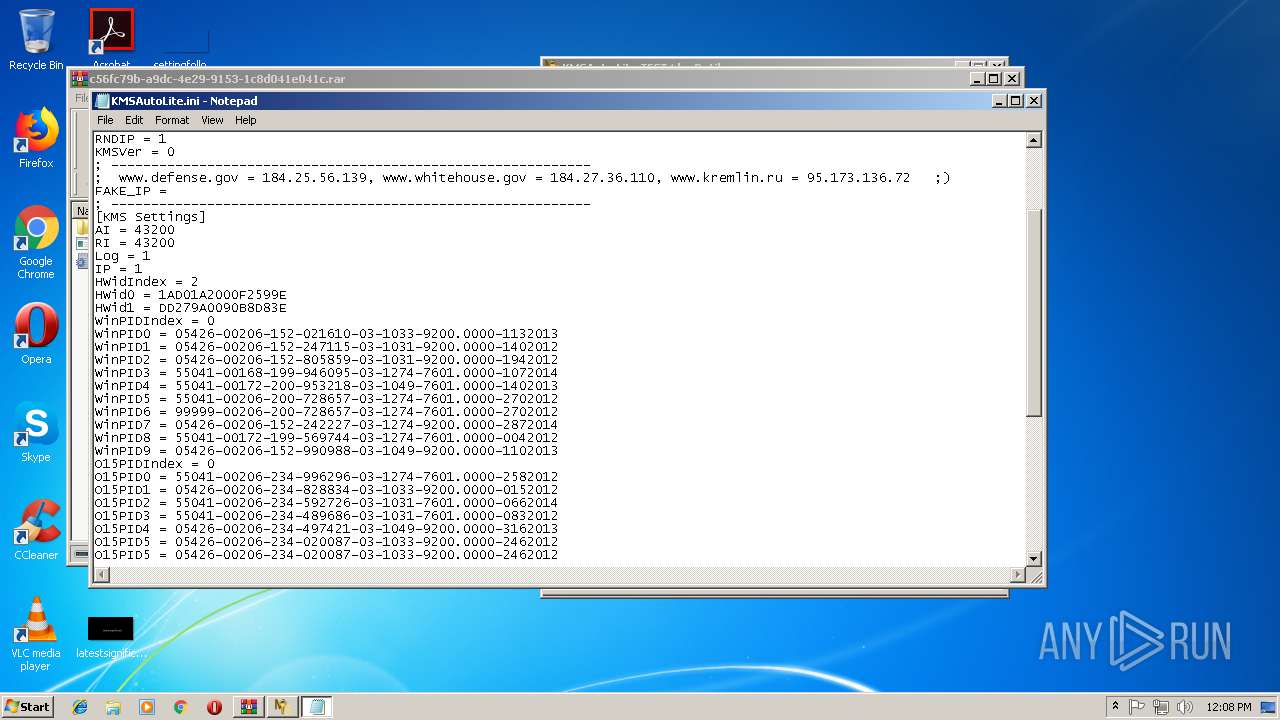
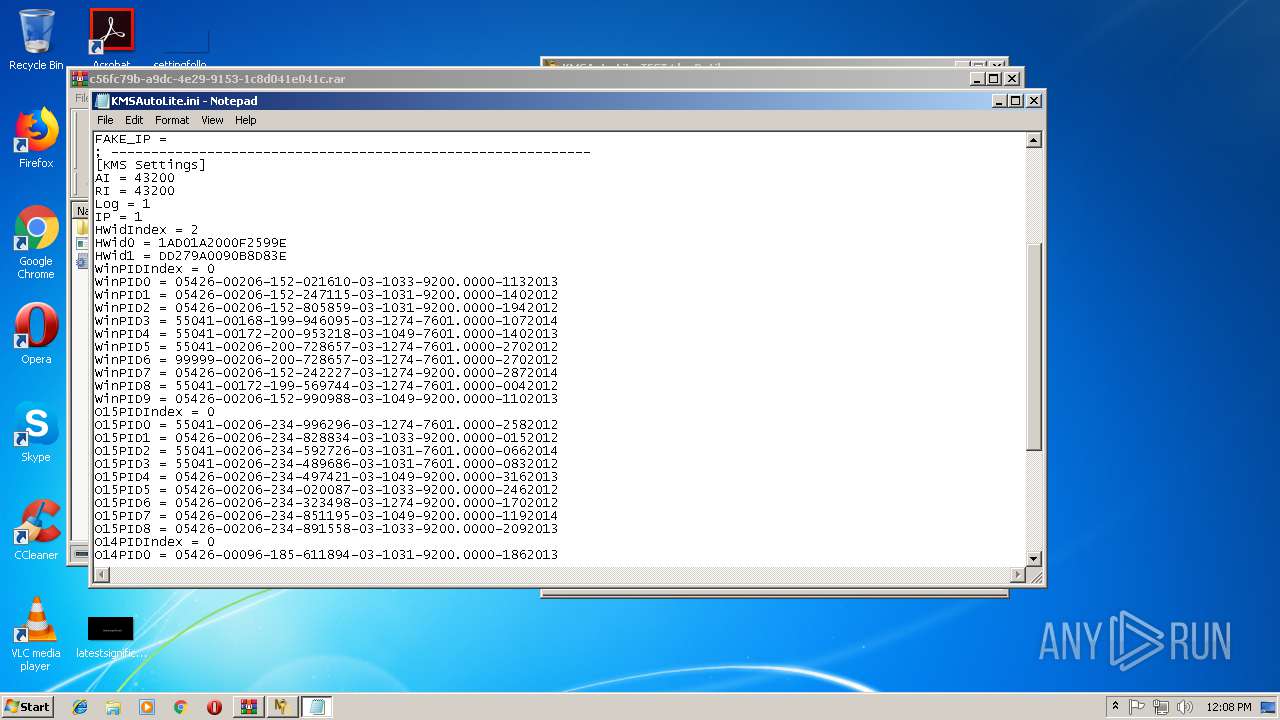
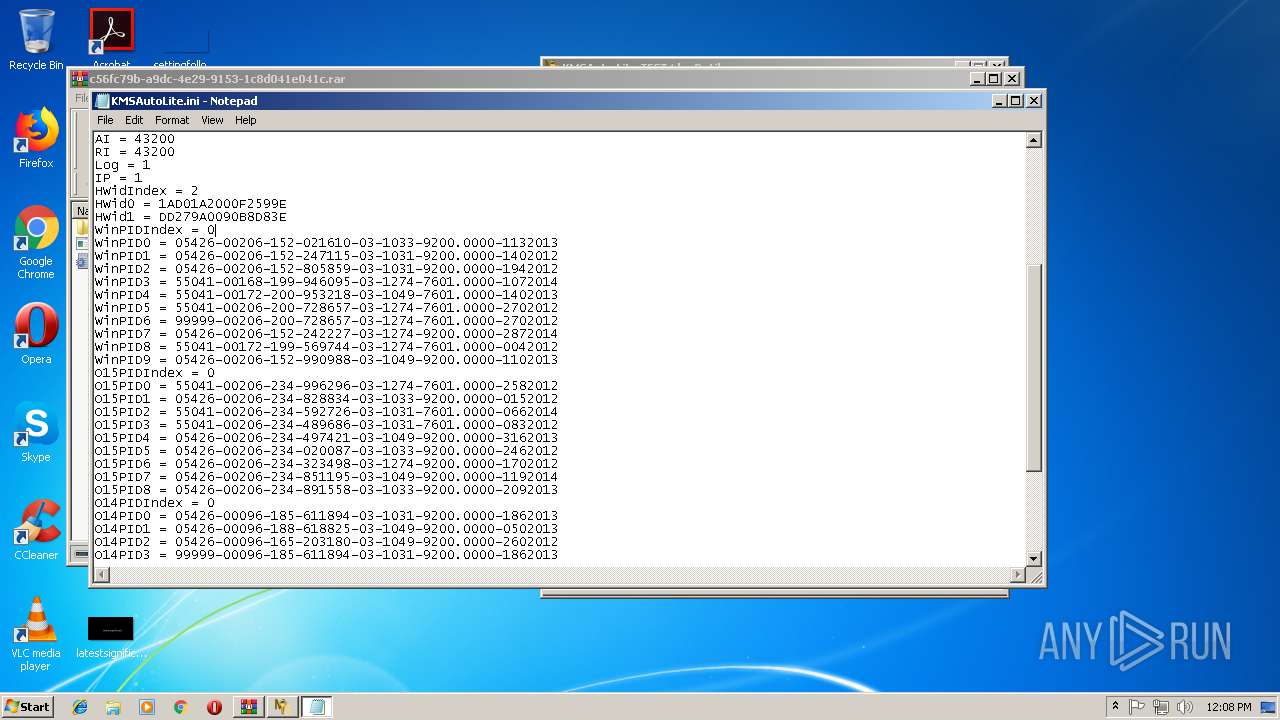
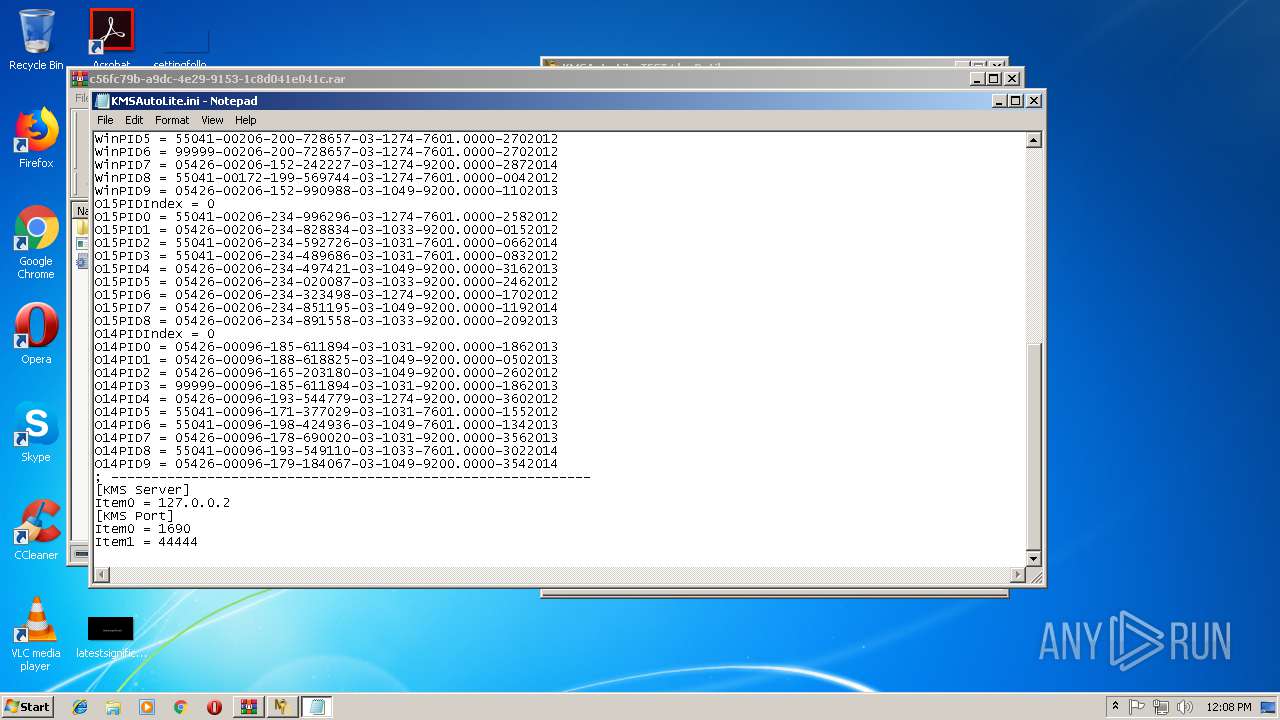
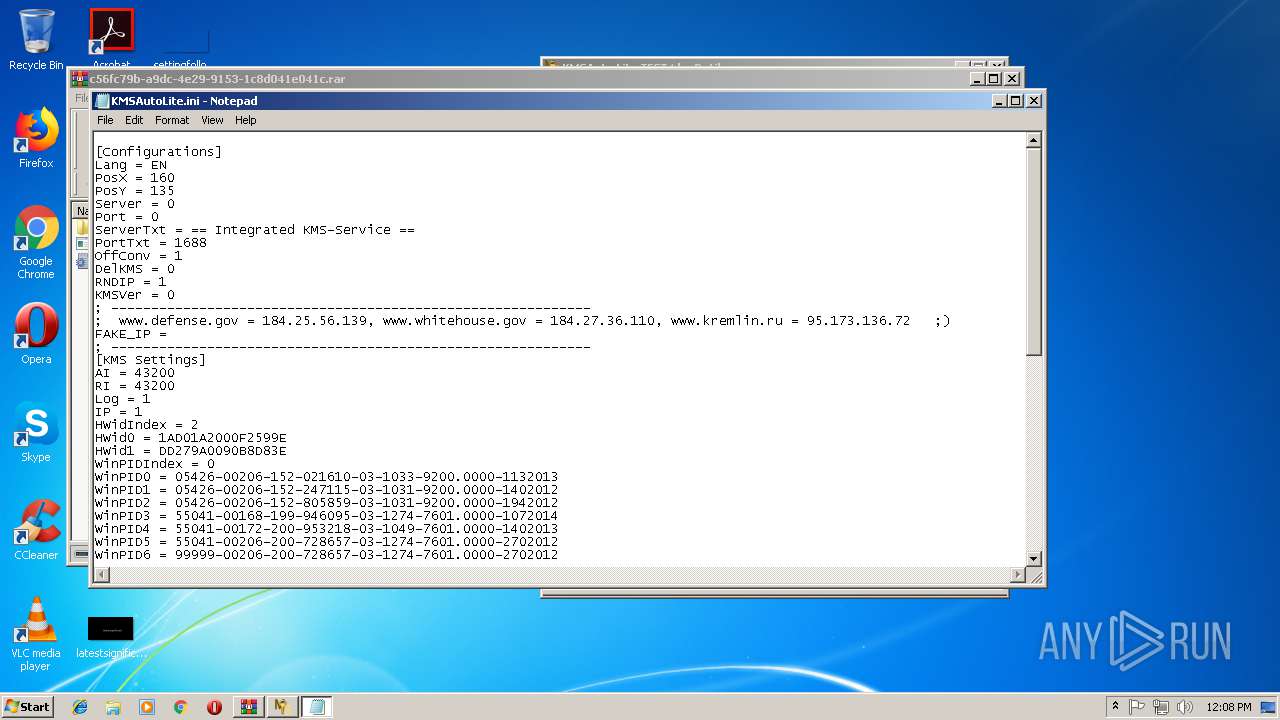
| 128 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa2296.11408\KMSAutoLite.ini | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 324 | "C:\Windows\System32\cmd.exe" /c sc.exe stop KMSEmulator | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 564 | schtasks.exe /delete /TN KMSAuto /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | Netsh.exe Advfirewall Firewall add rule name=0pen_Port_KMS dir=in action=allow protocol=TCP localport=1688 | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 648 | "C:\Windows\System32\cmd.exe" /c schtasks.exe /change /TN KMSAuto /RI 36000 | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 664 | "C:\Windows\System32\cmd.exe" /c sc.exe start KMSEmulator | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 684 | "C:\Windows\System32\cmd.exe" /c cscript.exe C:\Windows\Temp\KMSAuto\bin\KMSactivator.vbs //NoLogo /KEY:WIN | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 800 | "C:\Windows\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\cmd.exe | — | KMSAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 844 | "C:\Windows\Temp\KMSAuto\bin\KMSSS.exe" -Port 1688 -PWin RandomKMSPID -PO14 RandomKMSPID -PO15 RandomKMSPID -AI 43200 -RI 43200 KillProcessOnPort -Log -IP -Hwid DD279A0090B8D83E | C:\Windows\Temp\KMSAuto\bin\KMSSS.exe | — | services.exe | |||||||||||
User: SYSTEM Company: MDL Forum, mod by Ratiborus Integrity Level: SYSTEM Description: KMS Server Emulator Service (XP) Exit code: 0 Version: 1.1.9.0 Modules
| |||||||||||||||
| 884 | sc.exe stop WinDivert1.1 | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 177
Read events
889
Write events
288
Delete events
0
Modification events
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\c56fc79b-a9dc-4e29-9153-1c8d041e041c.rar | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
14
Suspicious files
0
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | KMSAuto.exe | C:\Windows\Temp\KMSAuto\bin\KMSactivator.vbs | text | |
MD5:— | SHA256:— | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2296.3417\KMSAuto Lite Portable TEST4\KMSAutoLite.ini | text | |
MD5:— | SHA256:— | |||
| 4008 | KMSSS.exe | C:\Windows\Temp\KMSAuto\bin\KMSSS.log | text | |
MD5:— | SHA256:— | |||
| 2216 | FakeClient.exe | C:\Windows\setupact.log | text | |
MD5:— | SHA256:— | |||
| 4060 | bin_x86.dat | C:\Windows\Temp\KMSAuto\bin\driver\x86WDV\WinDivert.sys | executable | |
MD5:AA03B0BF3D0A7DE8E19B00BD2043262F | SHA256:4BB7200BCB7D02B503EEB068492A1079F1273F3C0C2B0BCEB5B3F8425F5A32F8 | |||
| 3768 | KMSAuto.exe | C:\Windows\Temp\KMSAuto\bin.dat | executable | |
MD5:FE82465CFD6979F0EC065225676F395D | SHA256:091E75488987C1358216AD94EDC5EE39ED864FE1B4A809DC58EE6153615099DF | |||
| 3296 | cmd.exe | C:\Users\admin\AppData\Local\Temp\KMSAuto.tmp | — | |
MD5:— | SHA256:— | |||
| 4012 | cmd.exe | C:\Users\admin\AppData\Local\Temp\KMSAuto.tmp | — | |
MD5:— | SHA256:— | |||
| 2052 | cmd.exe | C:\Users\admin\AppData\Local\Temp\KMSAuto.tmp | — | |
MD5:— | SHA256:— | |||
| 3696 | bin.dat | C:\Windows\Temp\KMSAuto\bin\KMSSS.exe | executable | |
MD5:02EE3A012FD4B0205CDA2A75A04DB537 | SHA256:0C9E7AB2000F6FA70C7F6405D1896AC7B55ACE5372B49120B157996402634100 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
FakeClient.exe | WdfCoInstaller: [11/11/2018 12:07.19.623] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [11/11/2018 12:07.19.658] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [11/11/2018 12:07.19.661] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|
FakeClient.exe | WdfCoInstaller: [11/11/2018 12:07.30.192] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [11/11/2018 12:07.30.225] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [11/11/2018 12:07.30.229] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|