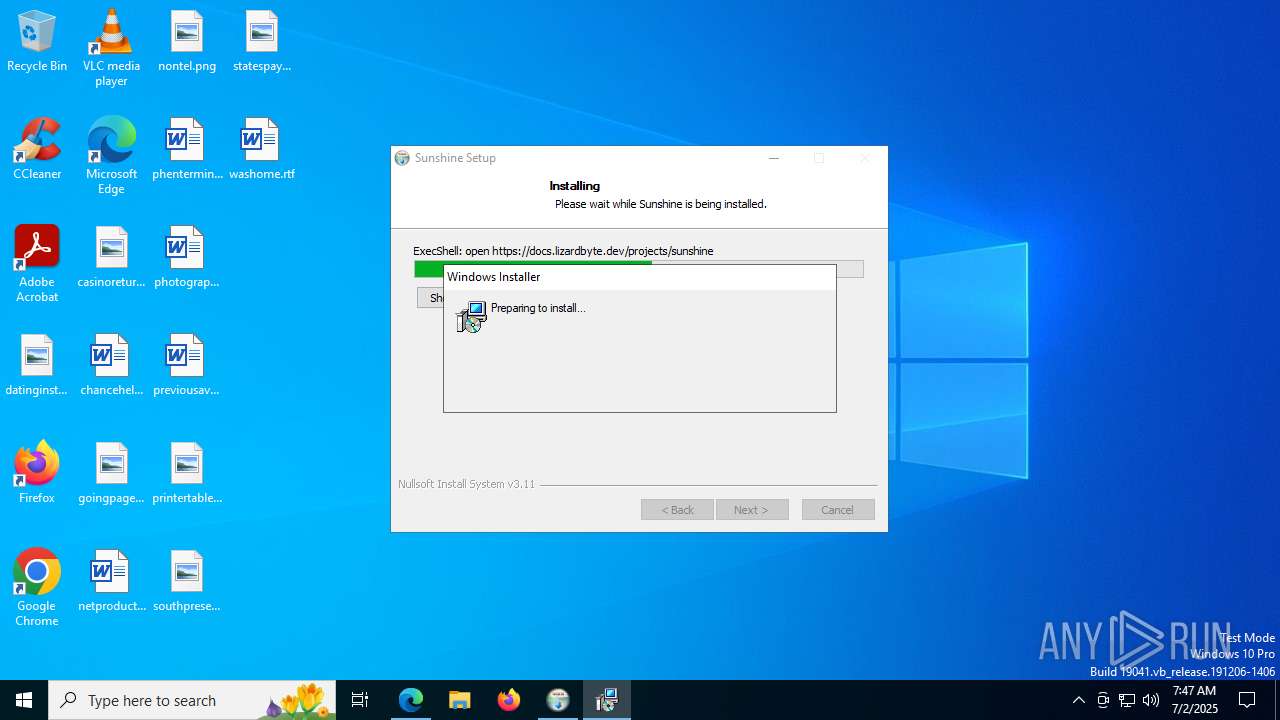
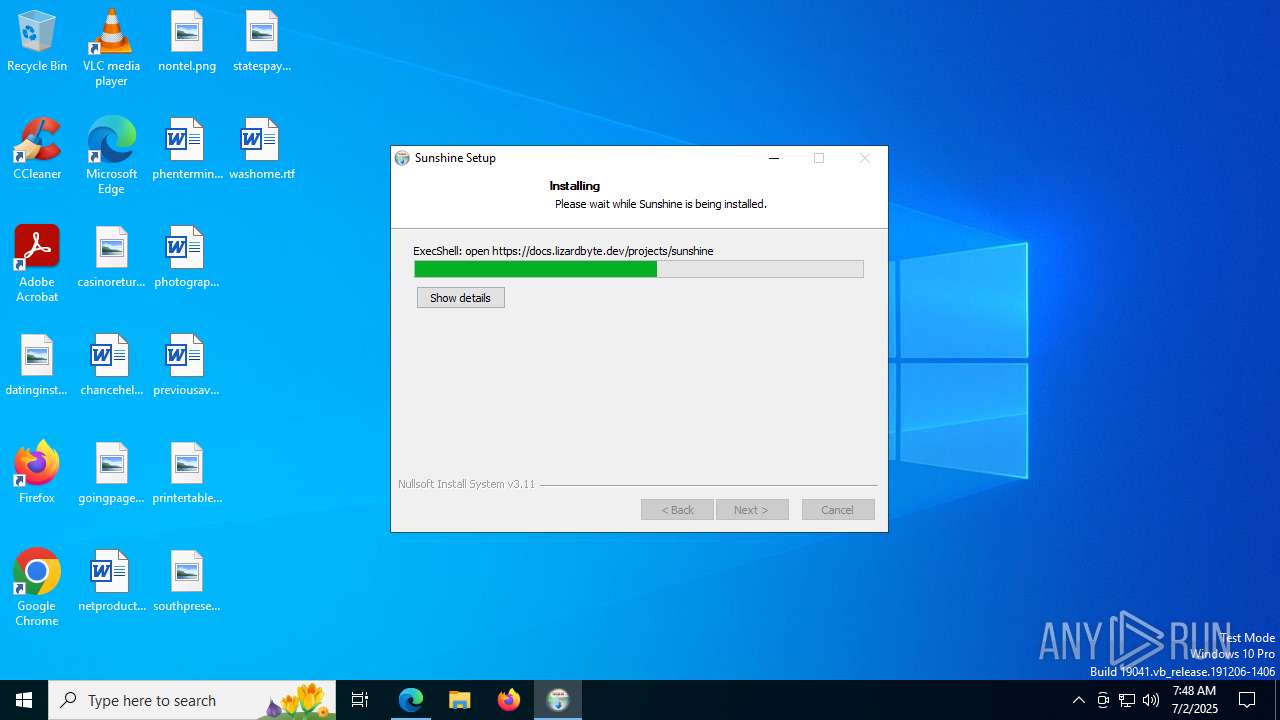
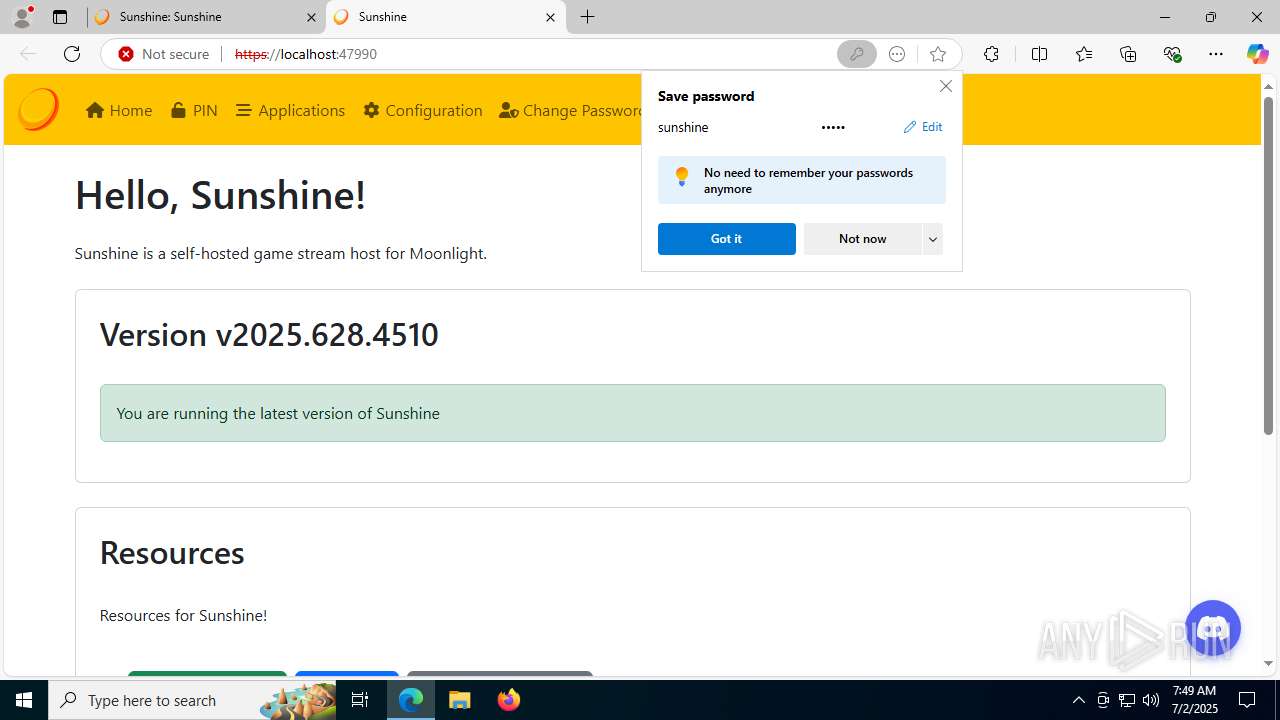
| download: | /LizardByte/Sunshine/releases/download/v2025.628.4510/sunshine-windows-installer.exe |
| Full analysis: | https://app.any.run/tasks/52535fed-fca1-4f1e-84dc-7a0c67ee40ef |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 07:47:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 9 sections |
| MD5: | F58A5DAC00A961028E4F971F48D5A53F |
| SHA1: | 2CF4294033A5601A88833D2A55D57C1494A971EF |
| SHA256: | C38E13FDC999CD1124E31CE66349891C4502425CD9154D362FF434722E27EBFC |
| SSDEEP: | 98304:LepknQWhxmMDxomWKQpZEicjBLYT4yiAOi01Bc1KDxQcC0T59Etv8jsqAWLyLB2I:5FBzs2owyog9Q+4ZKVz1ACz6i8sM4 |
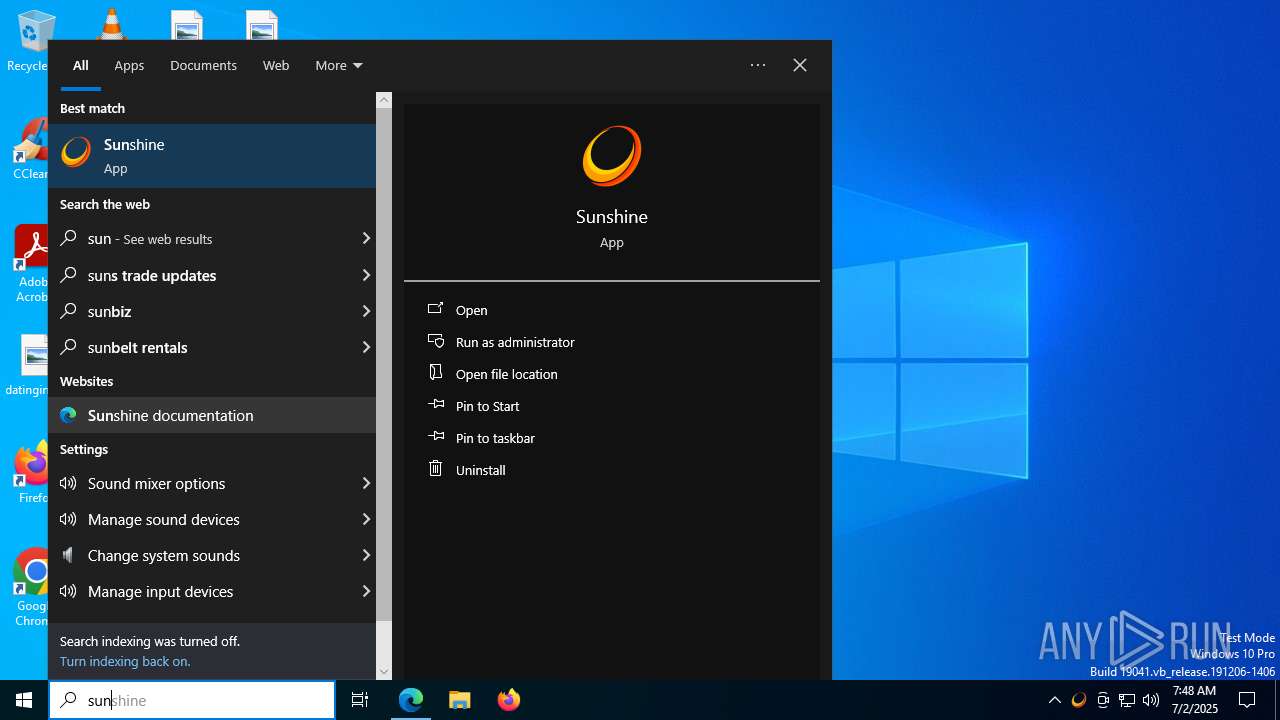
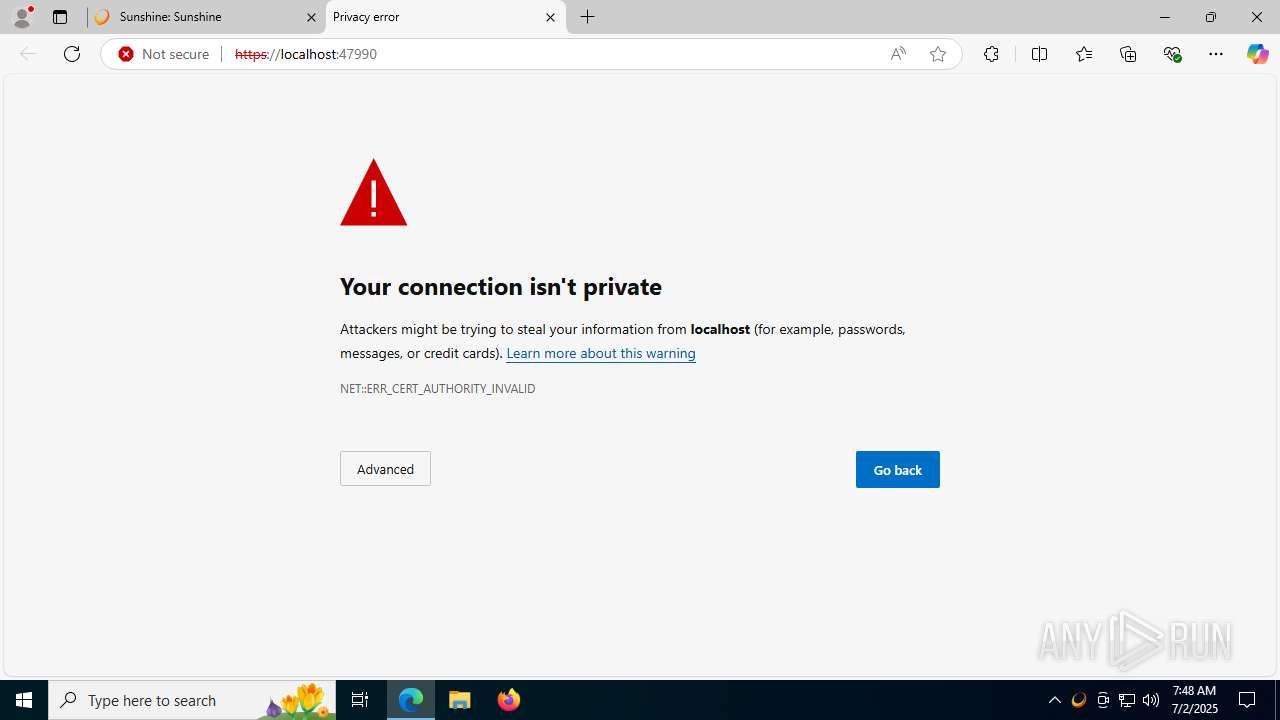
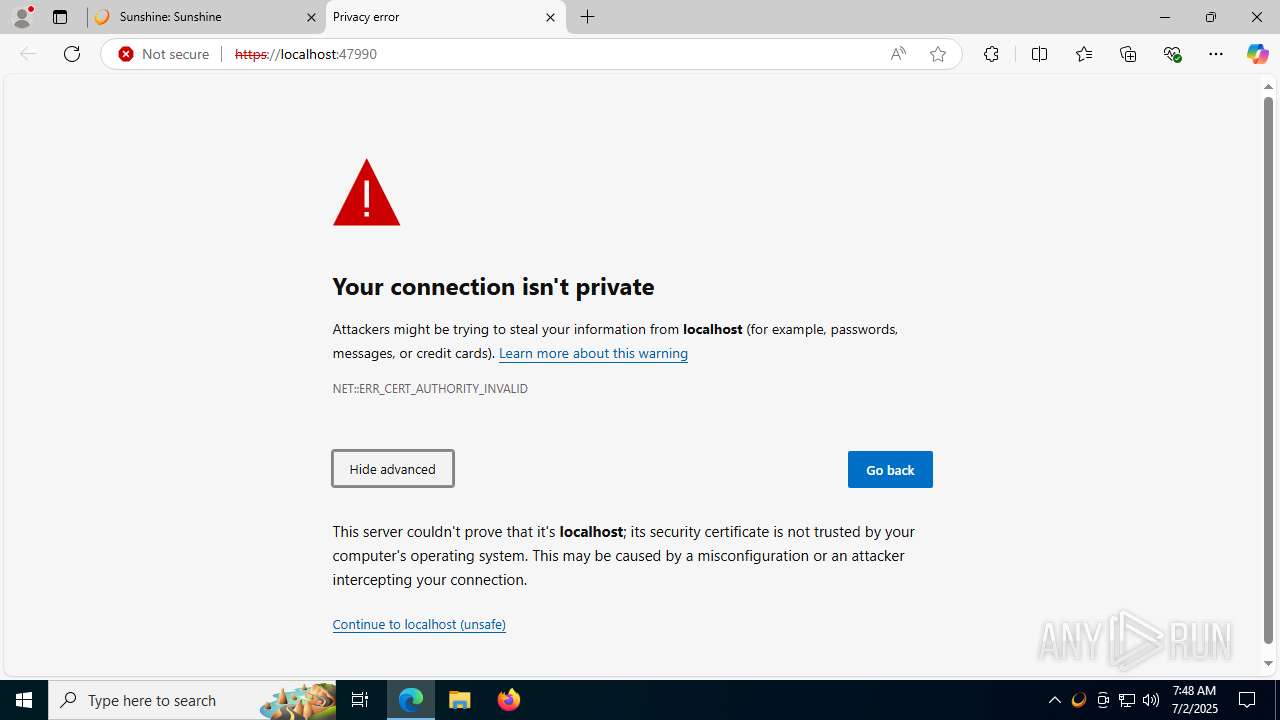
MALICIOUS
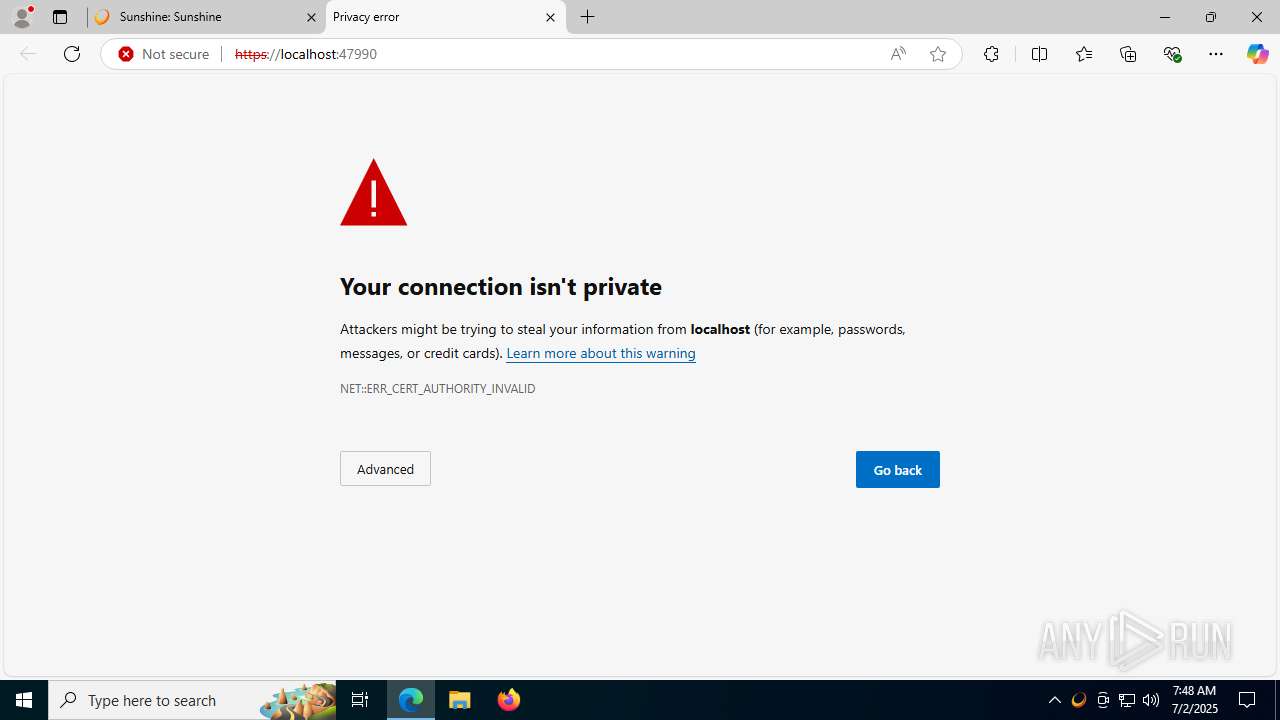
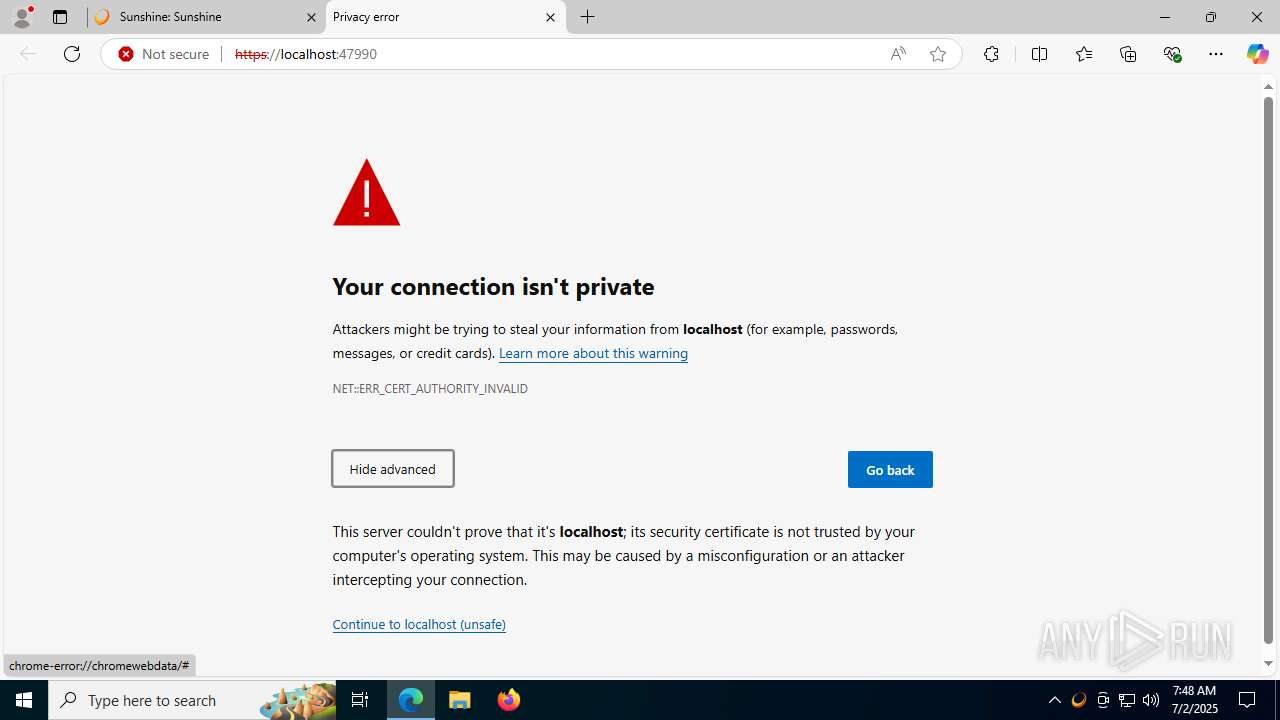
Executing a file with an untrusted certificate
- nefconw.exe (PID: 7396)
- nefconw.exe (PID: 7444)
Starts NET.EXE for service management
- net.exe (PID: 7500)
- cmd.exe (PID: 7344)
- net.exe (PID: 7232)
SUSPICIOUS
Executable content was dropped or overwritten
- sunshine-windows-installer.exe (PID: 1096)
- curl.exe (PID: 1936)
- virtual_gamepad.exe (PID: 7028)
- drvinst.exe (PID: 1100)
- nefconw.exe (PID: 7444)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6400)
- cmd.exe (PID: 2648)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6400)
- sunshine-windows-installer.exe (PID: 1096)
- cmd.exe (PID: 2148)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6400)
Executing commands from a ".bat" file
- sunshine-windows-installer.exe (PID: 1096)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 3584)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6260)
- sunshine-windows-installer.exe (PID: 1096)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2148)
Reads security settings of Internet Explorer
- sunshine-windows-installer.exe (PID: 1096)
- virtual_gamepad.exe (PID: 7028)
There is functionality for taking screenshot (YARA)
- sunshine-windows-installer.exe (PID: 1096)
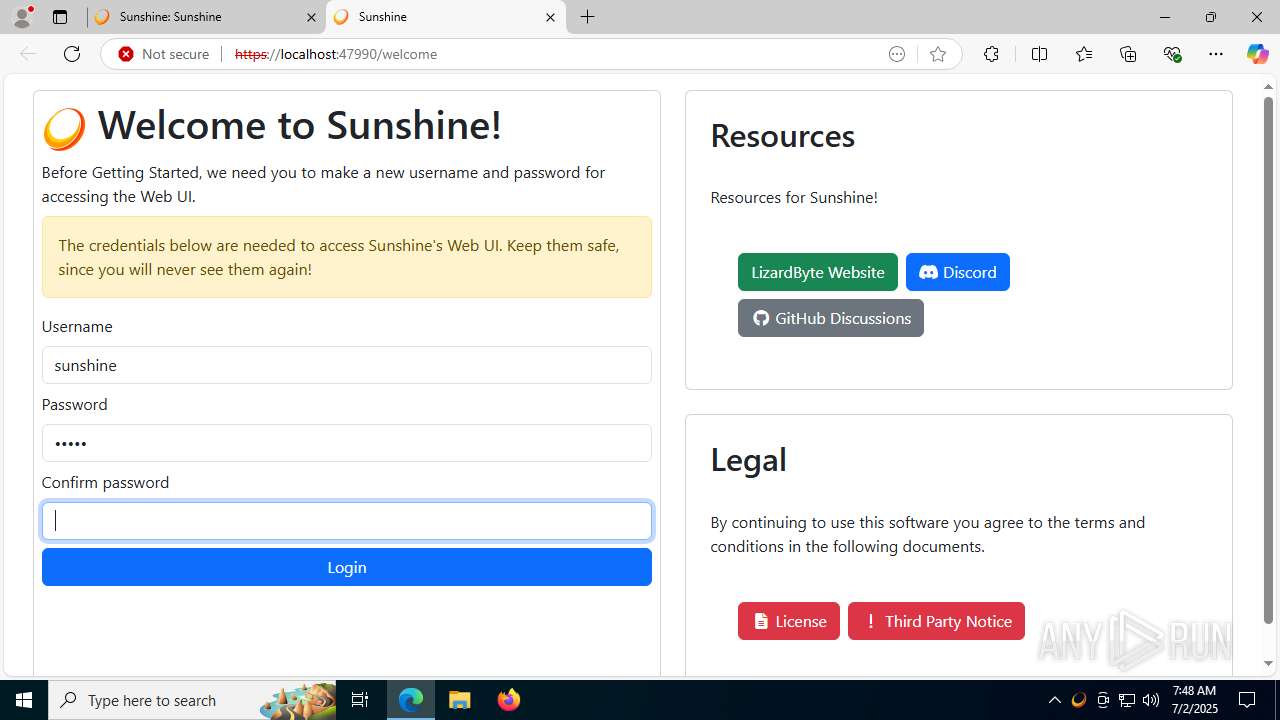
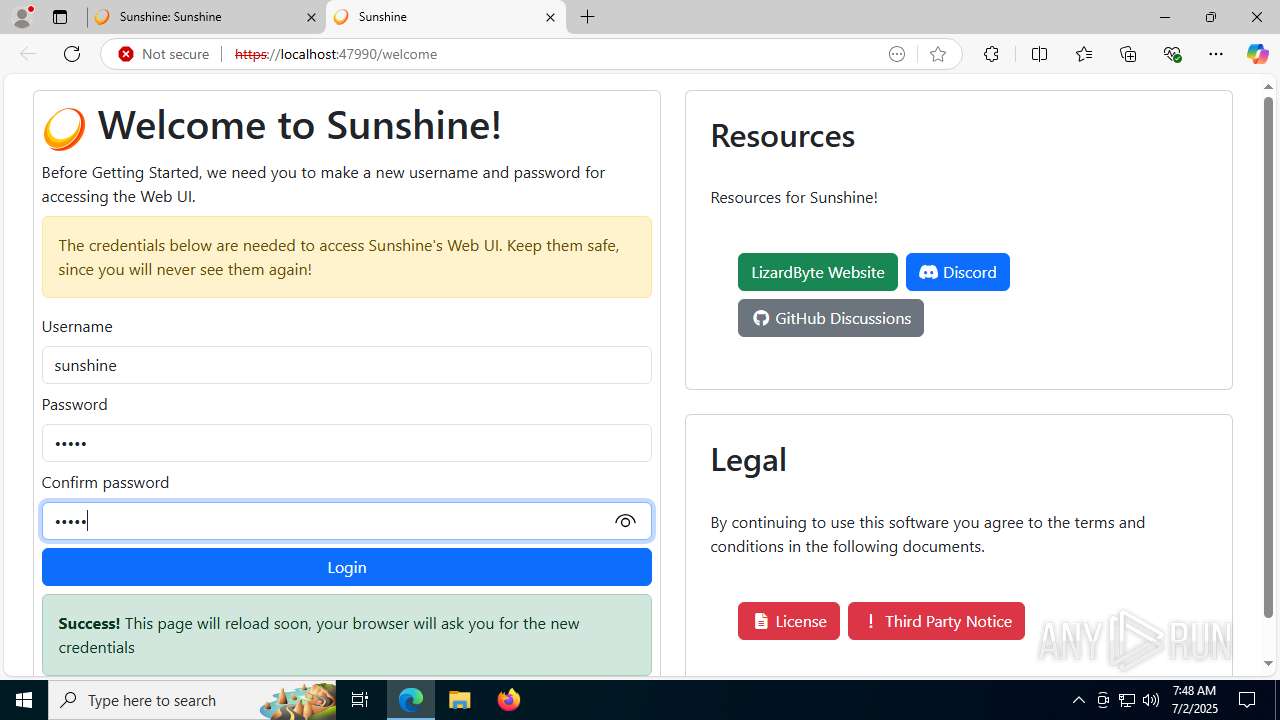
Creates a software uninstall entry
- sunshine-windows-installer.exe (PID: 1096)
Manipulates environment variables
- powershell.exe (PID: 4804)
Application launched itself
- cmd.exe (PID: 2148)
- cmd.exe (PID: 6400)
Execution of CURL command
- cmd.exe (PID: 2148)
The executable file from the user directory is run by the CMD process
- virtual_gamepad.exe (PID: 7028)
ADVANCEDINSTALLER mutex has been found
- virtual_gamepad.exe (PID: 7028)
Reads the Windows owner or organization settings
- virtual_gamepad.exe (PID: 7028)
- msiexec.exe (PID: 7384)
Process drops legitimate windows executable
- virtual_gamepad.exe (PID: 7028)
Executes as Windows Service
- VSSVC.exe (PID: 7672)
- sunshinesvc.exe (PID: 7292)
Drops a system driver (possible attempt to evade defenses)
- virtual_gamepad.exe (PID: 7028)
- nefconw.exe (PID: 7444)
- drvinst.exe (PID: 1100)
- msiexec.exe (PID: 7384)
Creates files in the driver directory
- drvinst.exe (PID: 1100)
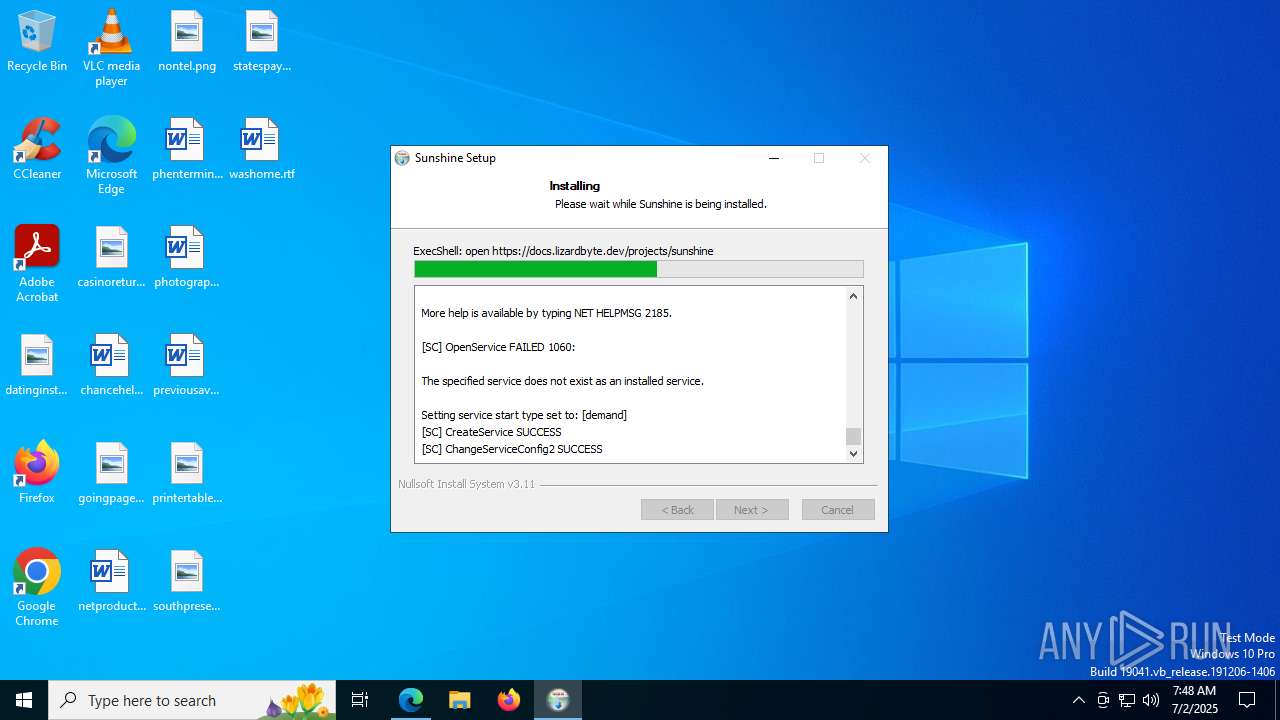
Creates or modifies Windows services
- drvinst.exe (PID: 7608)
Windows service management via SC.EXE
- sc.exe (PID: 8056)
- sc.exe (PID: 8156)
- sc.exe (PID: 7896)
Starts SC.EXE for service management
- cmd.exe (PID: 7344)
- cmd.exe (PID: 7376)
The process creates files with name similar to system file names
- sunshine-windows-installer.exe (PID: 1096)
Sets the service to start on system boot
- sc.exe (PID: 7772)
Creates a new Windows service
- sc.exe (PID: 4164)
Malware-specific behavior (creating "System.dll" in Temp)
- sunshine-windows-installer.exe (PID: 1096)
INFO
Creates files in the program directory
- cmd.exe (PID: 6260)
- sunshine-windows-installer.exe (PID: 1096)
- virtual_gamepad.exe (PID: 7028)
- sunshine.exe (PID: 7440)
Checks supported languages
- sunshine-windows-installer.exe (PID: 1096)
- curl.exe (PID: 3976)
- curl.exe (PID: 1936)
- virtual_gamepad.exe (PID: 7028)
- identity_helper.exe (PID: 7312)
- msiexec.exe (PID: 7464)
- msiexec.exe (PID: 7384)
- msiexec.exe (PID: 8168)
- nefconw.exe (PID: 7396)
- nefconw.exe (PID: 7444)
- drvinst.exe (PID: 1100)
- drvinst.exe (PID: 7608)
- sunshine.exe (PID: 7440)
- sunshinesvc.exe (PID: 7292)
- sunshine.exe (PID: 3640)
Reads the computer name
- sunshine-windows-installer.exe (PID: 1096)
- curl.exe (PID: 3976)
- curl.exe (PID: 1936)
- virtual_gamepad.exe (PID: 7028)
- identity_helper.exe (PID: 7312)
- msiexec.exe (PID: 7384)
- msiexec.exe (PID: 7464)
- msiexec.exe (PID: 8168)
- nefconw.exe (PID: 7396)
- nefconw.exe (PID: 7444)
- drvinst.exe (PID: 1100)
- drvinst.exe (PID: 7608)
- sunshinesvc.exe (PID: 7292)
- sunshine.exe (PID: 7440)
- sunshine.exe (PID: 3640)
Create files in a temporary directory
- sunshine-windows-installer.exe (PID: 1096)
- curl.exe (PID: 1936)
- virtual_gamepad.exe (PID: 7028)
- nefconw.exe (PID: 7444)
Application launched itself
- msedge.exe (PID: 5012)
- msedge.exe (PID: 7084)
- msedge.exe (PID: 3932)
- msedge.exe (PID: 4700)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4804)
Manual execution by a user
- msedge.exe (PID: 5012)
- sunshine.exe (PID: 3640)
Checks proxy server information
- reg.exe (PID: 6404)
- virtual_gamepad.exe (PID: 7028)
- slui.exe (PID: 2148)
Execution of CURL command
- cmd.exe (PID: 2648)
- cmd.exe (PID: 2148)
Reads Environment values
- virtual_gamepad.exe (PID: 7028)
- identity_helper.exe (PID: 7312)
- msiexec.exe (PID: 7464)
- msiexec.exe (PID: 8168)
Reads the machine GUID from the registry
- virtual_gamepad.exe (PID: 7028)
- msiexec.exe (PID: 7384)
- drvinst.exe (PID: 1100)
- sunshine.exe (PID: 7440)
Reads the software policy settings
- virtual_gamepad.exe (PID: 7028)
- msiexec.exe (PID: 7384)
- drvinst.exe (PID: 1100)
- slui.exe (PID: 2148)
Creates files or folders in the user directory
- virtual_gamepad.exe (PID: 7028)
The sample compiled with english language support
- curl.exe (PID: 1936)
- virtual_gamepad.exe (PID: 7028)
- msiexec.exe (PID: 7384)
- nefconw.exe (PID: 7444)
- drvinst.exe (PID: 1100)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7384)
Manages system restore points
- SrTasks.exe (PID: 8064)
Creates a software uninstall entry
- msiexec.exe (PID: 7384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:30 18:11:53+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.44 |
| CodeSize: | 35328 |
| InitializedDataSize: | 103936 |
| UninitializedDataSize: | 402432 |
| EntryPoint: | 0x42bd |
| OSVersion: | 5.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
250
Monitored processes
104
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x284,0x288,0x28c,0x27c,0x2dc,0x7ffc4526f208,0x7ffc4526f214,0x7ffc4526f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --always-read-main-dll --field-trial-handle=5292,i,675951759635211402,3101785525837639532,262144 --variations-seed-version --mojo-platform-channel-handle=5676 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 756 | icacls "C:\Program Files\Sunshine\config\credentials" /inheritance:r | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --always-read-main-dll --field-trial-handle=5340,i,675951759635211402,3101785525837639532,262144 --variations-seed-version --mojo-platform-channel-handle=6832 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --always-read-main-dll --field-trial-handle=6540,i,675951759635211402,3101785525837639532,262144 --variations-seed-version --mojo-platform-channel-handle=7008 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo "C:\Program Files (x86)\Common Files\Oracle\Java\javapath;%SystemRoot%\system32;%SystemRoot%;%SystemRoot%\System32\Wbem;%SYSTEMROOT%\System32\WindowsPowerShell\v1.0\;%SYSTEMROOT%\System32\OpenSSH\;C:\Program Files\PowerShell\7\" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | icacls "C:\Program Files\Sunshine" /reset | C:\Windows\System32\icacls.exe | — | sunshine-windows-installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\AppData\Local\Temp\sunshine-windows-installer.exe" | C:\Users\admin\AppData\Local\Temp\sunshine-windows-installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1100 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{434ac586-16af-0346-a466-bb330230118a}\ViGEmBus.inf" "9" "433776443" "00000000000001C8" "WinSta0\Default" "00000000000001D4" "208" "C:\Program Files\Nefarius Software Solutions\ViGEm Bus Driver" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 537
Read events
25 162
Write events
346
Delete events
29
Modification events
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Sunshine\Uninstall.exe" | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Sunshine\Sunshine.exe | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | HelpLink |
Value: https://docs.lizardbyte.dev/projects/sunshine/latest/md_docs_2getting__started.html | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | URLInfoAbout |
Value: https://app.lizardbyte.dev/Sunshine | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | Contact |
Value: https://app.lizardbyte.dev/Sunshine/support | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | DisplayName |
Value: Sunshine | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | DisplayVersion |
Value: 2025.628.4510 | |||
| (PID) Process: | (1096) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | Publisher |
Value: LizardByte | |||
Executable files
37
Suspicious files
440
Text files
159
Unknown types
105
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1096 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\sunshine.exe | — | |
MD5:— | SHA256:— | |||
| 1096 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_planar_y_ps_linear.hlsl | text | |
MD5:CCF41A6C14F7F15F15BE17B06B27AFE9 | SHA256:5778FC50BC74B44B752273A24B262ED0F960CCFA5F92C2DBF8A06589F614D43D | |||
| 1096 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_packed_uv_type0_vs.hlsl | text | |
MD5:88820E52A237F7B6E78BD99F4C081095 | SHA256:8B524DB00460581242BA8BFED502D04FD6DF2DC0B88E8BE1CB0042A4FEB9E1C1 | |||
| 1096 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_packed_uv_type0s_ps_perceptual_quantizer.hlsl | text | |
MD5:8C777B6A905DA66485687E28EAA369D9 | SHA256:9BB078E7E264C61C146CC82568FADF850A0B22D9F5879E492A058FFE4809EAE0 | |||
| 1096 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_packed_uv_type0s_ps.hlsl | text | |
MD5:75305AABC5B3D48C02CA2C6EA4503574 | SHA256:B3C44BF4515FAF5AEF652E3801FDD932EEF5977961E7C3CABAE6DAA96860F06E | |||
| 1096 | sunshine-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\nsk5B21.tmp\StartMenu.dll | executable | |
MD5:24ED78F875EBD2F412ABBD53820350EC | SHA256:643F52F1341EACE7D8FB2FD2BA54A41B8863F0AC435F2FA0918E2971A1B4BA1B | |||
| 1096 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_packed_uv_type0_ps_linear.hlsl | text | |
MD5:7BA99F704E3D336B7DA19EC698373F18 | SHA256:C0A67152C118E59C7B19BB55D180B3DBC7FC5841FC93688D799BD572F62997B8 | |||
| 1096 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_packed_uv_type0_ps_perceptual_quantizer.hlsl | text | |
MD5:770E5F40434C5B20DC0E4684A3869044 | SHA256:D5F937713422D2122BF57F482CF14C9B7CF70DBDB2E7A881742334E22FD951F2 | |||
| 1096 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\tools\sunshinesvc.exe | executable | |
MD5:B670EA49BB04D487D5895F23A6989CED | SHA256:A0B39D54C9A588C2530D76DB4A383073DA9D03CAF1119FF4E5176D2474E4CD25 | |||
| 1096 | sunshine-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\nsk5B21.tmp\UserInfo.dll | executable | |
MD5:7357838AC641996018FEF63B2F30E085 | SHA256:B12B4A4BA795356E4112F51986A329BE29929FD7CC533984F55BF6AFE5E3F2FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
128
DNS requests
119
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6320 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1740 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:wzjOjg1pkvyYo6aJ3nmddtc7JPVWj765M6ZTbIG2pLw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CECoW9cIBGAf3CpJj3Tw5qfI%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCrZoa1YnvoBZaCEzAShkn1 | unknown | — | — | whitelisted |
3396 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3396 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6368 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6320 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6320 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
docs.lizardbyte.dev |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
1740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
1740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
1740 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |