| File name: | sunshine-windows-installer.exe |
| Full analysis: | https://app.any.run/tasks/380404c5-deef-4dc0-b269-c54a412a521e |
| Verdict: | Malicious activity |
| Analysis date: | July 10, 2025, 22:54:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 9 sections |
| MD5: | F58A5DAC00A961028E4F971F48D5A53F |
| SHA1: | 2CF4294033A5601A88833D2A55D57C1494A971EF |
| SHA256: | C38E13FDC999CD1124E31CE66349891C4502425CD9154D362FF434722E27EBFC |
| SSDEEP: | 98304:LepknQWhxmMDxomWKQpZEicjBLYT4yiAOi01Bc1KDxQcC0T59Etv8jsqAWLyLB2I:5FBzs2owyog9Q+4ZKVz1ACz6i8sM4 |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 4860)
- net.exe (PID: 6788)
- net.exe (PID: 4084)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- sunshine-windows-installer.exe (PID: 5616)
Reads security settings of Internet Explorer
- sunshine-windows-installer.exe (PID: 5616)
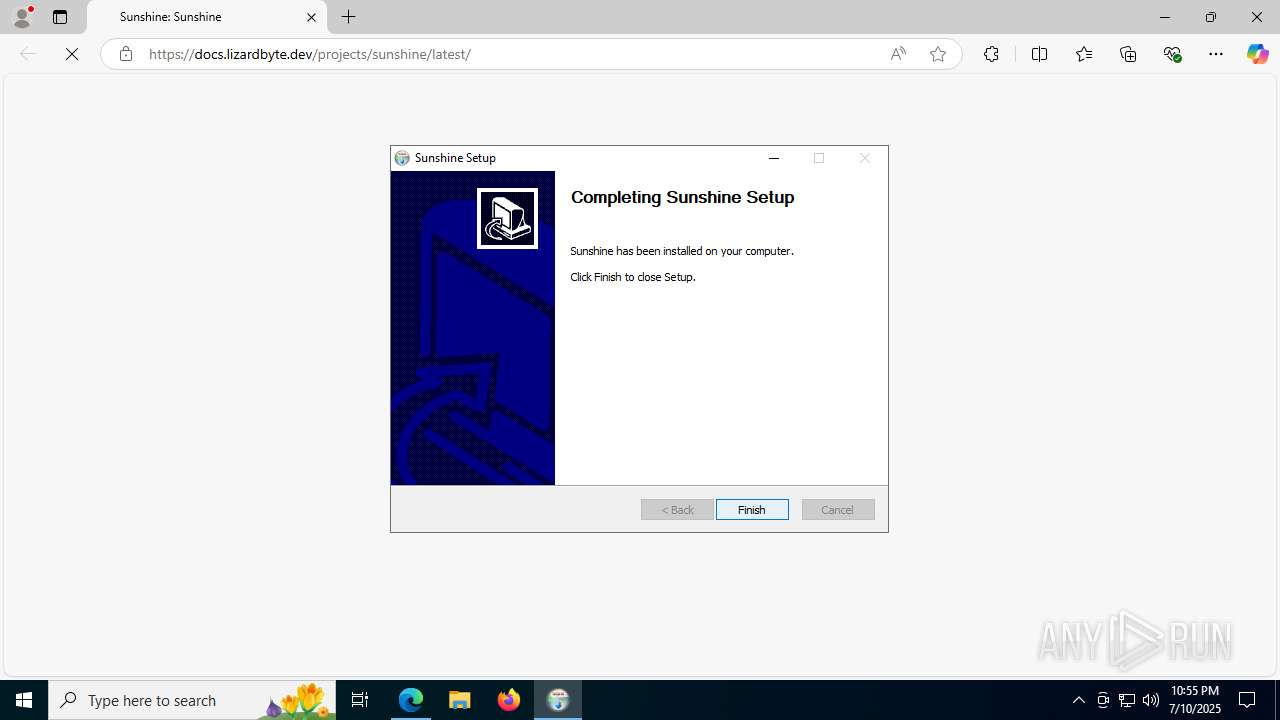
Creates a software uninstall entry
- sunshine-windows-installer.exe (PID: 5616)
Uses ICACLS.EXE to modify access control lists
- sunshine-windows-installer.exe (PID: 5616)
- cmd.exe (PID: 3620)
Executing commands from a ".bat" file
- sunshine-windows-installer.exe (PID: 5616)
Starts CMD.EXE for commands execution
- sunshine-windows-installer.exe (PID: 5616)
- cmd.exe (PID: 3668)
- cmd.exe (PID: 2140)
Application launched itself
- cmd.exe (PID: 3668)
- cmd.exe (PID: 2140)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3668)
- cmd.exe (PID: 6336)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3668)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 6652)
Manipulates environment variables
- powershell.exe (PID: 1352)
Executable content was dropped or overwritten
- sunshine-windows-installer.exe (PID: 5616)
Execution of CURL command
- cmd.exe (PID: 2140)
Starts SC.EXE for service management
- cmd.exe (PID: 4860)
- cmd.exe (PID: 1964)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2140)
Malware-specific behavior (creating "System.dll" in Temp)
- sunshine-windows-installer.exe (PID: 5616)
Sets the service to start on system boot
- sc.exe (PID: 3876)
Creates a new Windows service
- sc.exe (PID: 756)
Windows service management via SC.EXE
- sc.exe (PID: 5620)
- sc.exe (PID: 3584)
- sc.exe (PID: 6284)
Executes as Windows Service
- sunshinesvc.exe (PID: 432)
The process creates files with name similar to system file names
- sunshine-windows-installer.exe (PID: 5616)
INFO
Checks supported languages
- sunshine-windows-installer.exe (PID: 5616)
- curl.exe (PID: 4920)
- curl.exe (PID: 2032)
- sunshinesvc.exe (PID: 432)
- sunshine.exe (PID: 1944)
- identity_helper.exe (PID: 1832)
Creates files in the program directory
- sunshine-windows-installer.exe (PID: 5616)
- cmd.exe (PID: 3620)
- sunshine.exe (PID: 1944)
Reads the computer name
- sunshine-windows-installer.exe (PID: 5616)
- curl.exe (PID: 4920)
- sunshinesvc.exe (PID: 432)
- sunshine.exe (PID: 1944)
- identity_helper.exe (PID: 1832)
Create files in a temporary directory
- sunshine-windows-installer.exe (PID: 5616)
Application launched itself
- msedge.exe (PID: 2160)
- msedge.exe (PID: 5284)
- msedge.exe (PID: 3964)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1352)
Manual execution by a user
- msedge.exe (PID: 5284)
Checks proxy server information
- reg.exe (PID: 6400)
- slui.exe (PID: 2680)
Execution of CURL command
- cmd.exe (PID: 6336)
- cmd.exe (PID: 2140)
Reads the machine GUID from the registry
- sunshine.exe (PID: 1944)
Reads Environment values
- identity_helper.exe (PID: 1832)
Reads the software policy settings
- slui.exe (PID: 2680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:30 18:11:53+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.44 |
| CodeSize: | 35328 |
| InitializedDataSize: | 103936 |
| UninitializedDataSize: | 402432 |
| EntryPoint: | 0x42bd |
| OSVersion: | 5.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
226
Monitored processes
88
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | "C:\Program Files\Sunshine\tools\sunshinesvc.exe" | C:\Program Files\Sunshine\tools\sunshinesvc.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Modules
| |||||||||||||||
| 756 | sc create SunshineService binPath= "C:\Program Files\Sunshine\tools\sunshinesvc.exe" start= demand DisplayName= "Sunshine Service" | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | powershell -c Exit $(if ((Get-Item "$env:SystemRoot\System32\drivers\ViGEmBus.sys").VersionInfo.FileVersion -ge [System.Version]"1.17") { 2 } Else { 1 }) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1484 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1484 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4100,i,16829845553617556458,18275683768662394984,262144 --variations-seed-version --mojo-platform-channel-handle=4188 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1564 | C:\WINDOWS\system32\cmd.exe /c reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings" | find /i "ProxyEnable" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=5092,i,16829845553617556458,18275683768662394984,262144 --variations-seed-version --mojo-platform-channel-handle=4672 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1732 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=2896,i,16829845553617556458,18275683768662394984,262144 --variations-seed-version --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1832 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6276,i,16829845553617556458,18275683768662394984,262144 --variations-seed-version --mojo-platform-channel-handle=6308 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
15 137
Read events
15 072
Write events
65
Delete events
0
Modification events
| (PID) Process: | (5616) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (5616) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (5616) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Sunshine\Sunshine.exe | |||
| (PID) Process: | (5616) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | HelpLink |
Value: https://docs.lizardbyte.dev/projects/sunshine/latest/md_docs_2getting__started.html | |||
| (PID) Process: | (5616) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | URLInfoAbout |
Value: https://app.lizardbyte.dev/Sunshine | |||
| (PID) Process: | (5616) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | Contact |
Value: https://app.lizardbyte.dev/Sunshine/support | |||
| (PID) Process: | (5616) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | StartMenu |
Value: Sunshine | |||
| (PID) Process: | (2160) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2160) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5616) sunshine-windows-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Sunshine |
| Operation: | write | Name: | DisplayName |
Value: Sunshine | |||
Executable files
10
Suspicious files
199
Text files
145
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5616 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\sunshine.exe | — | |
MD5:— | SHA256:— | |||
| 5616 | sunshine-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\nss6293.tmp\InstallOptions.dll | executable | |
MD5:79C985EA58A63ADF00D79D5D9BEDE11C | SHA256:FE1D0728BCFB370048F1738259CAC8835B5E41DAFEADD5D80486C8ECC3C1577B | |||
| 5616 | sunshine-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\nss6293.tmp\StartMenu.dll | executable | |
MD5:24ED78F875EBD2F412ABBD53820350EC | SHA256:643F52F1341EACE7D8FB2FD2BA54A41B8863F0AC435F2FA0918E2971A1B4BA1B | |||
| 5616 | sunshine-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\nss6293.tmp\ioSpecial.ini | ini | |
MD5:E2D5070BC28DB1AC745613689FF86067 | SHA256:D95AED234F932A1C48A2B1B0D98C60CA31F962310C03158E2884AB4DDD3EA1E0 | |||
| 5616 | sunshine-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\nss6293.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 5616 | sunshine-windows-installer.exe | C:\Users\admin\AppData\Local\Temp\nss6293.tmp\modern-header.bmp | image | |
MD5:92FCFB4F2E95D8BA0EC7DE564E62F68A | SHA256:1967D92ABD7EE2151CA9A50CEEF9210FDBF0023ECCEF294B2042F5FBBEE08067 | |||
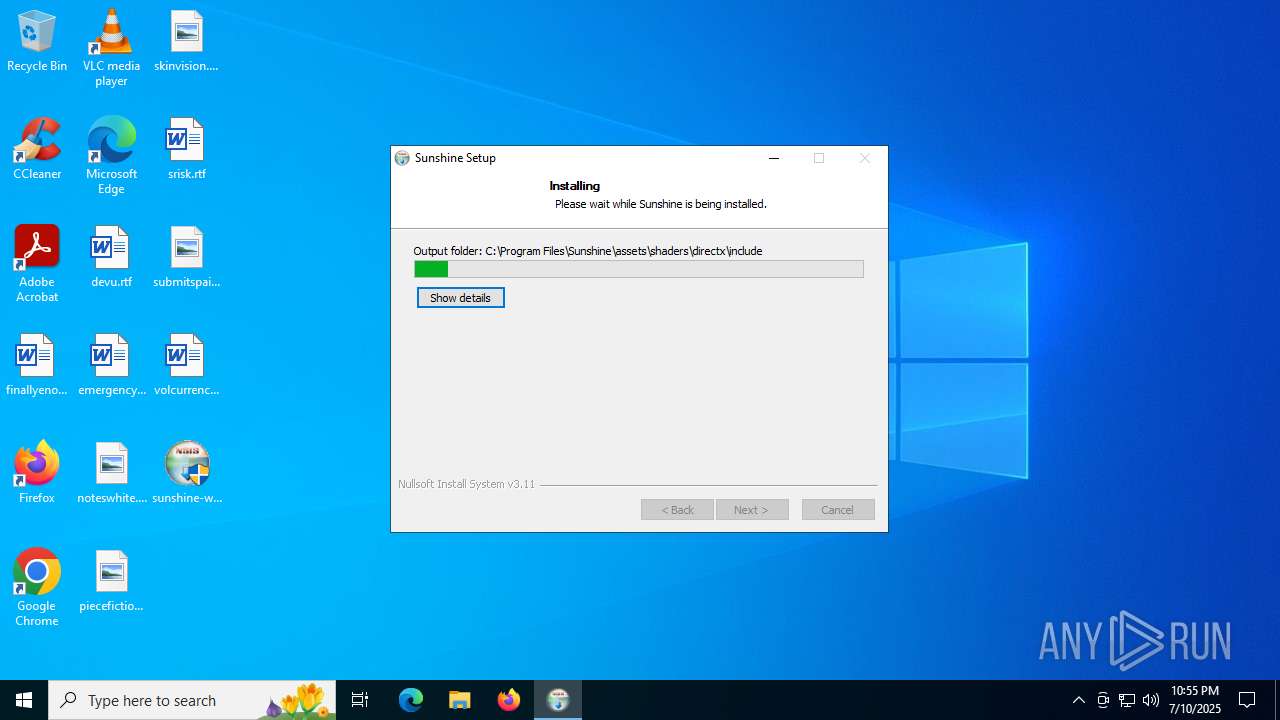
| 5616 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_packed_uv_type0_ps_perceptual_quantizer.hlsl | text | |
MD5:770E5F40434C5B20DC0E4684A3869044 | SHA256:D5F937713422D2122BF57F482CF14C9B7CF70DBDB2E7A881742334E22FD951F2 | |||
| 5616 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_packed_uv_type0_ps_linear.hlsl | text | |
MD5:7BA99F704E3D336B7DA19EC698373F18 | SHA256:C0A67152C118E59C7B19BB55D180B3DBC7FC5841FC93688D799BD572F62997B8 | |||
| 5616 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\apps.json | binary | |
MD5:EB13A568BF69204CF61786B9AF0088C7 | SHA256:3B6C2715114F8C71189AB1BE359EAB01C391A7B0996F18A89F686B9518B7069C | |||
| 5616 | sunshine-windows-installer.exe | C:\Program Files\Sunshine\assets\shaders\directx\convert_yuv420_packed_uv_type0s_ps.hlsl | text | |
MD5:75305AABC5B3D48C02CA2C6EA4503574 | SHA256:B3C44BF4515FAF5AEF652E3801FDD932EEF5977961E7C3CABAE6DAA96860F06E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
373
TCP/UDP connections
236
DNS requests
216
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5876 | RUXIMICS.exe | GET | 200 | 184.24.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5876 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
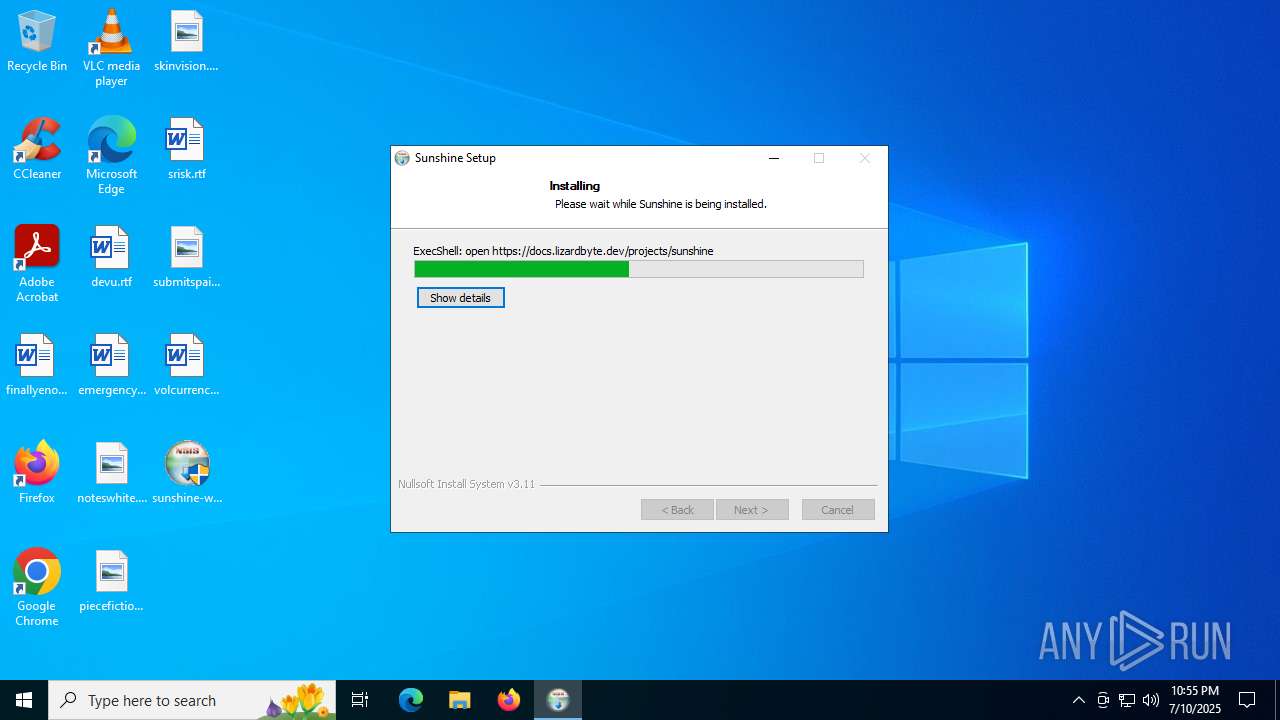
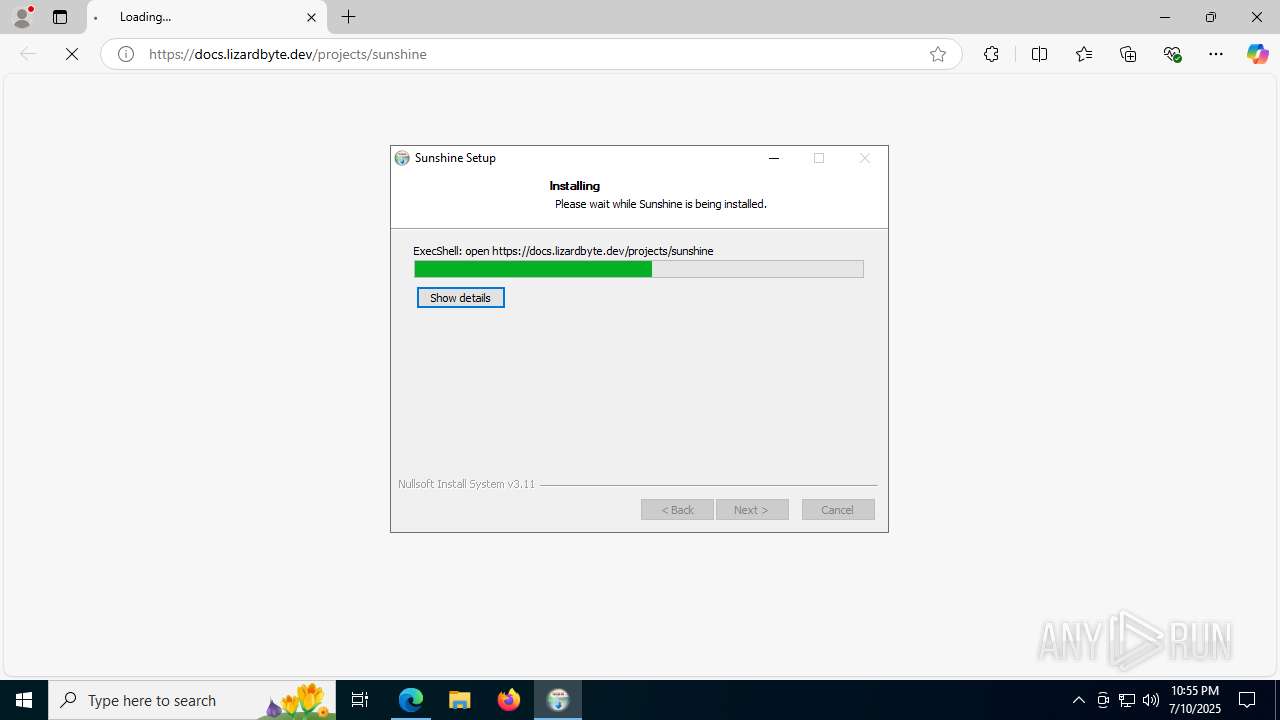
— | — | GET | 302 | 104.16.253.120:443 | https://docs.lizardbyte.dev/projects/sunshine | unknown | — | — | unknown |
6724 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:tdKzl-ILZURecUfUH5vZL1r5VCNx7zNe3PjomWDngko&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=51&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | unknown | binary | 1.47 Kb | whitelisted |
— | — | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | binary | 715 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5876 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.24.77.27:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.24.77.27:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5876 | RUXIMICS.exe | 184.24.77.27:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
docs.lizardbyte.dev |
| unknown |
copilot.microsoft.com |
| whitelisted |
api.github.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |