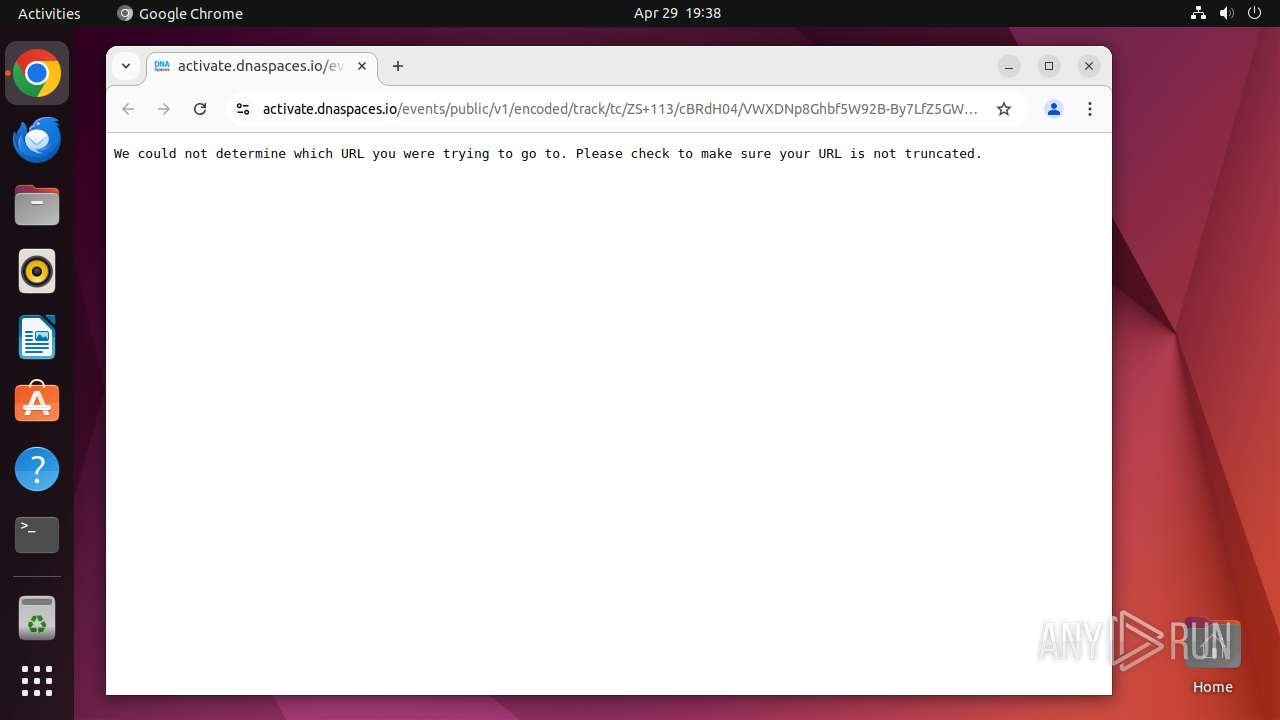
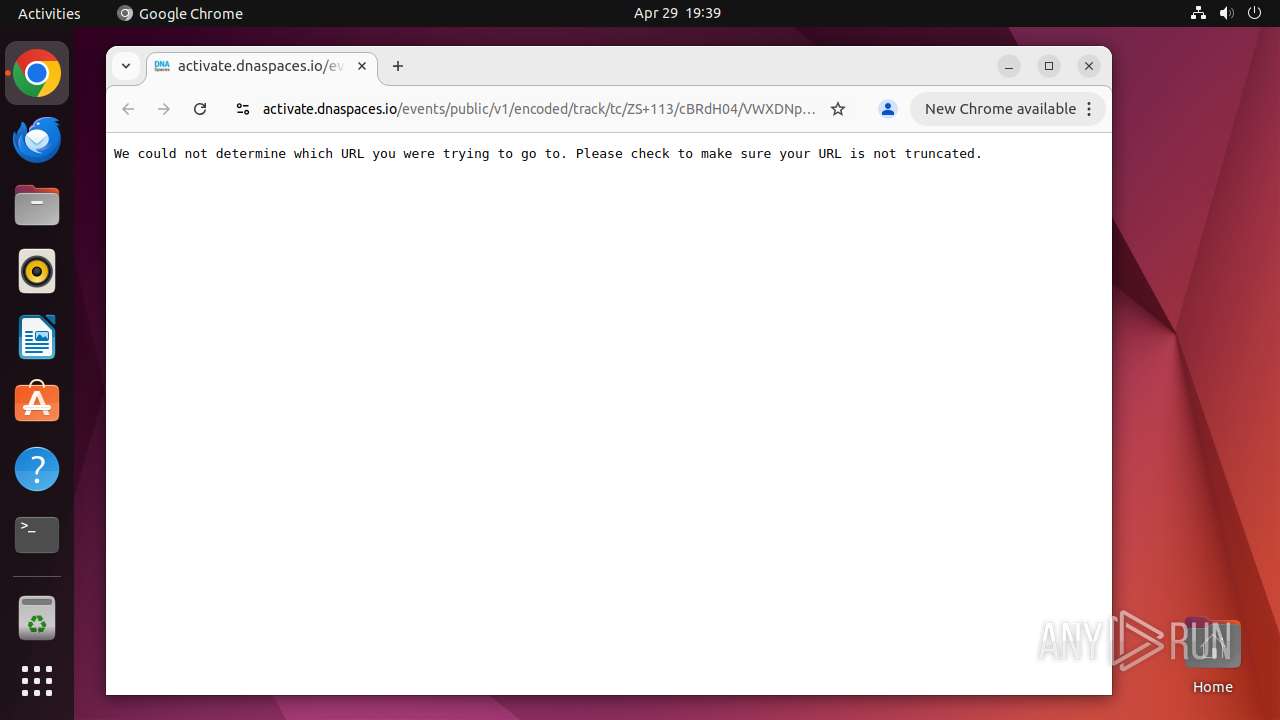
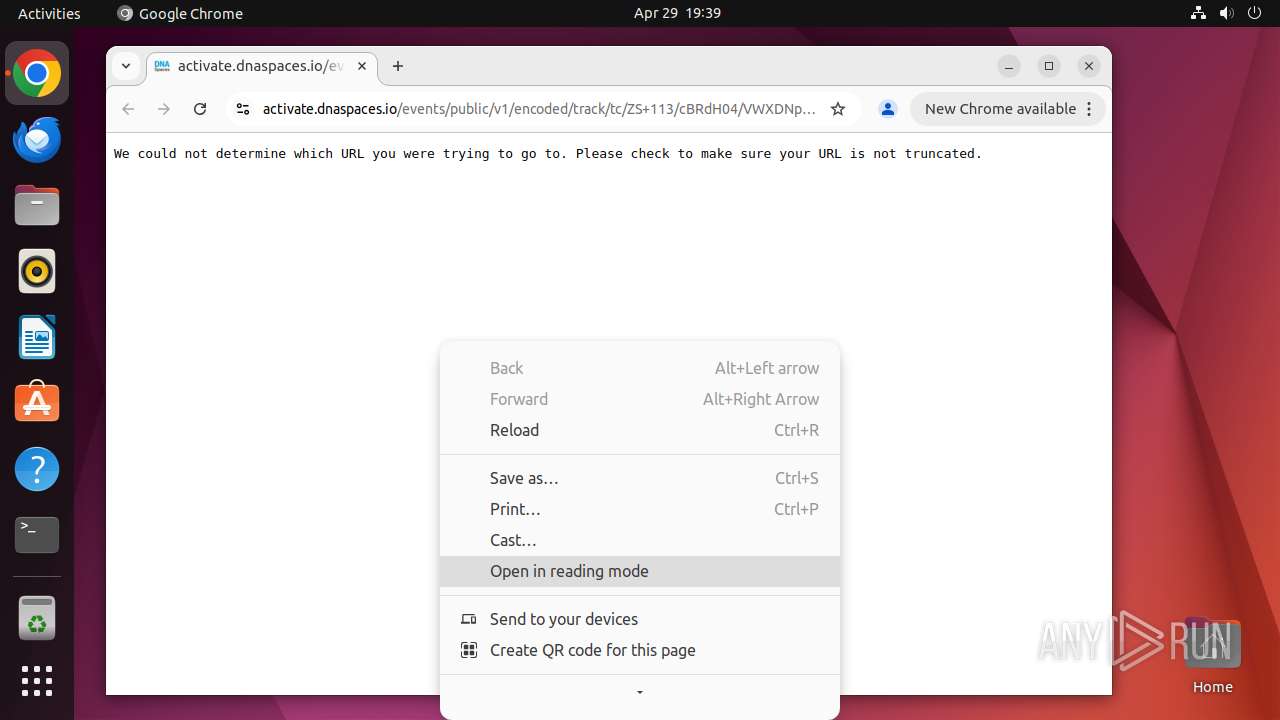
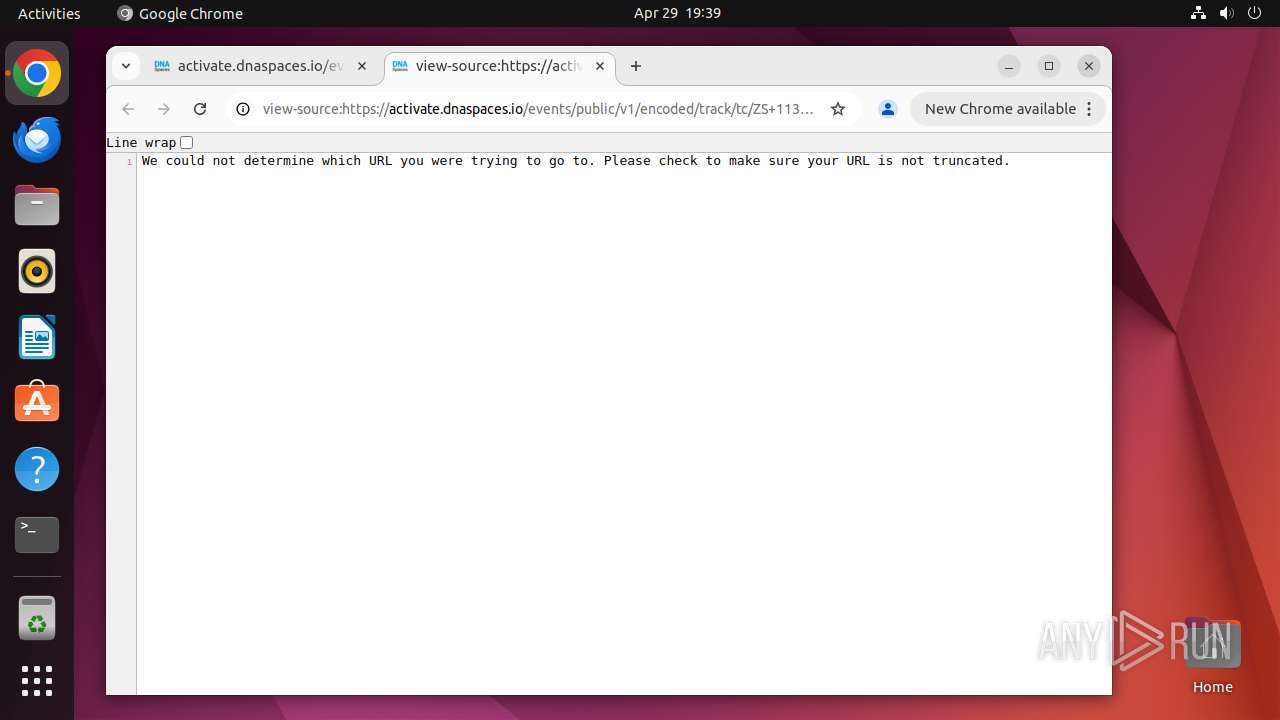
| URL: | https://activate.dnaspaces.io/e3t/Ctc/ZS+113/cBRdH04/VWXDNp8Ghbf5W92B-By7LfZ5GW5JQdxX5v-gTPN63y6pj3qgyTW95jsWP6lZ3p5W6BTHvd8yxTYMW8dzgCS5TbqM0W38yCMB5wlbRlW1y223R3LRyMSW4X80Qc62_FCzW72scPs8m5WgNW7x5NWr6xpq0zW53n76q57YQz1W8KKT9X2KySkNVXQLpt2wBBC2W4f7yP66pLx,%20category:%20Information%20Technology,%20id:%2052. |
| Full analysis: | https://app.any.run/tasks/0725d65a-c887-4f16-b1e4-ed2dd6e484f3 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 18:38:45 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MD5: | 1B014DE66C312C90E08DD62A59880B3E |
| SHA1: | 6700A4DCD00A65C7AC8BCF06E68C02C6690BCFFD |
| SHA256: | C36FC8C83F12D011DEF18ACD3B4D218450DCA918A40B92897F786448CCFE7FBF |
| SSDEEP: | 6:2gdm2An9qGaDO5ZspCHRf0fKQyTxJmm63imkKuhyPH7365RPMK0Fn88L:2f2AspyZspCxfvQAxJmm6XkKEkcN0FF |
MALICIOUS
No malicious indicators.SUSPICIOUS
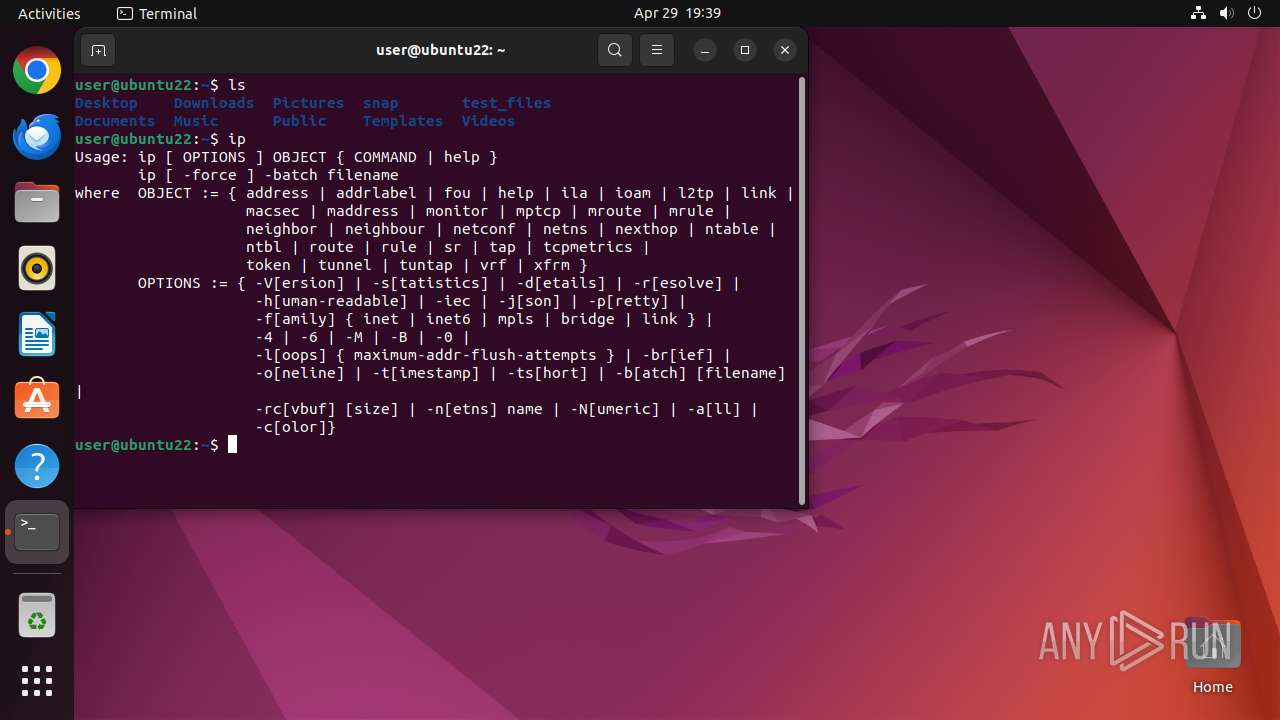
Executes commands using command-line interpreter
- chrome (PID: 39490)
- sudo (PID: 39489)
- gnome-terminal-server (PID: 39793)
Reads passwd file
- apt (PID: 39842)
- http (PID: 39882)
- perl (PID: 39884)
- tar (PID: 39932)
- tar (PID: 39941)
- mandb (PID: 39954)
- dpkg (PID: 39899)
- tar (PID: 39904)
- tar (PID: 39914)
- tar (PID: 39923)
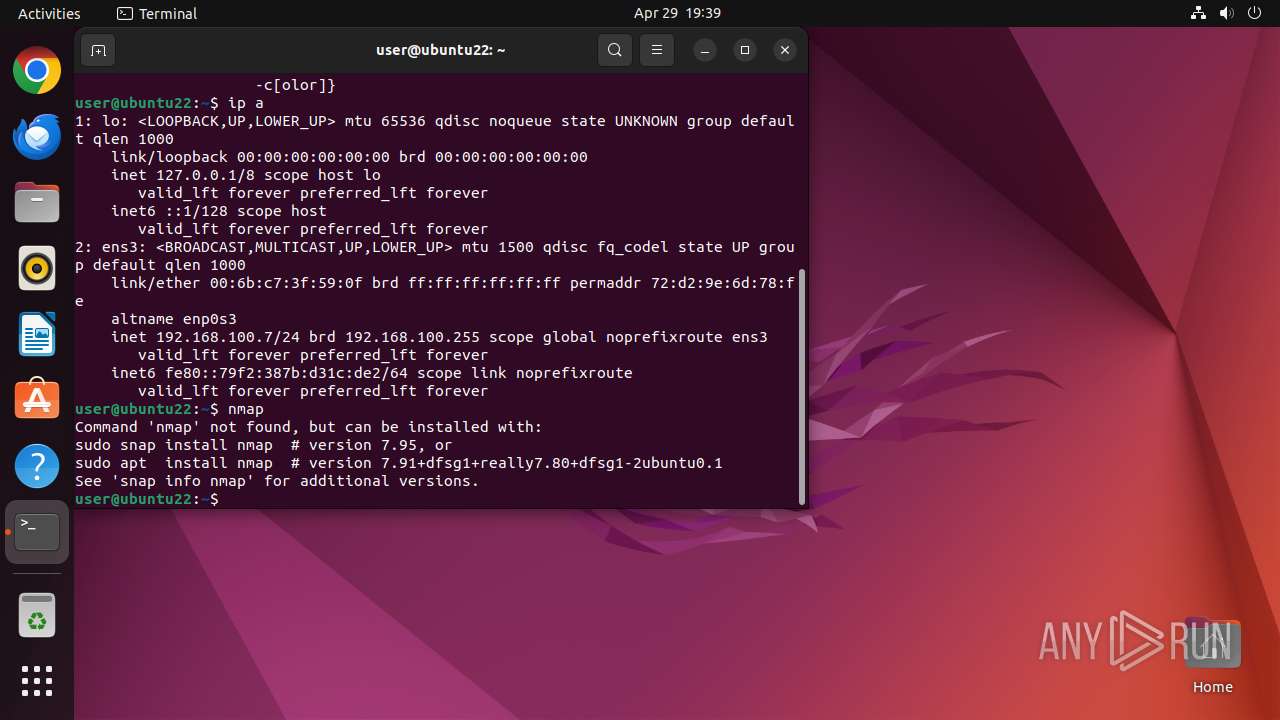
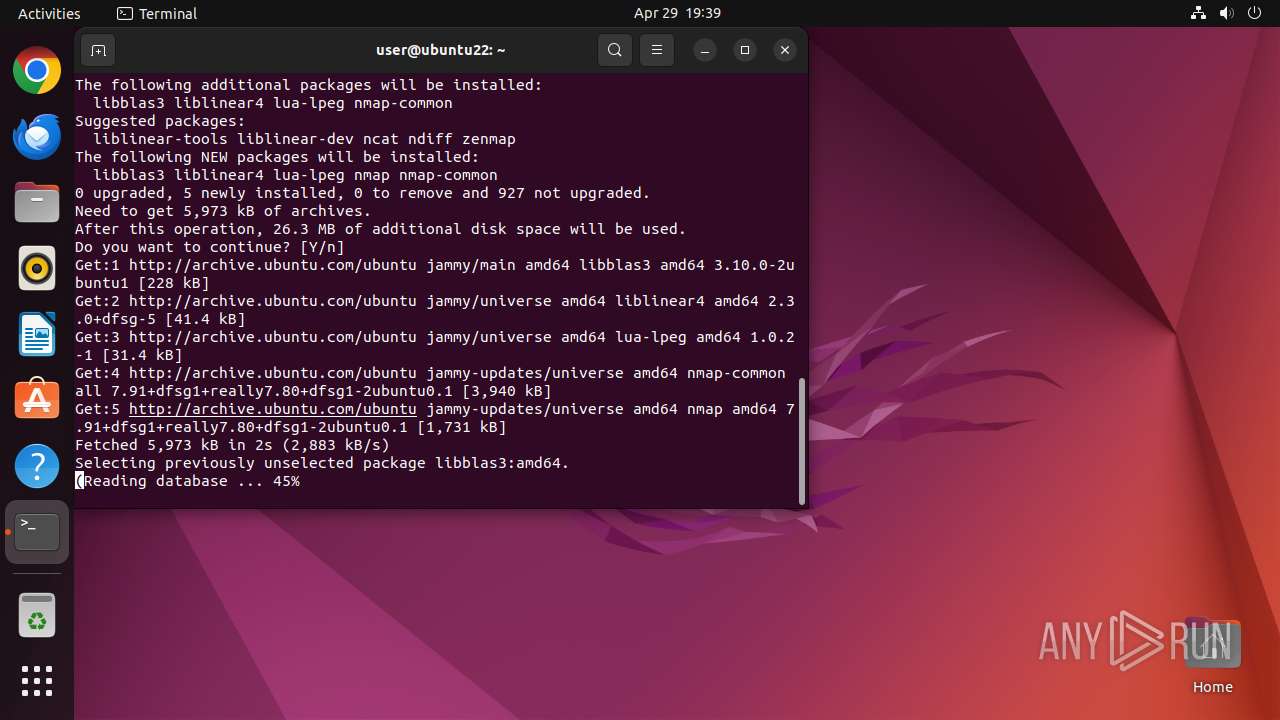
- nmap (PID: 40025)
- sshd (PID: 40026)
Creates or rewrites file in the "bin" folder
- dpkg (PID: 39899)
Uses base64 (probably to encode stolen data or decode malicious payload)
- dash (PID: 39949)
Changes time attribute to hide new files or make changes to the existing one
- dash (PID: 39964)
Check the Environment Variables Related to System Identification (os-release)
- python3.10 (PID: 39980)
- python3.10 (PID: 39990)
- python3.10 (PID: 39992)
- python3.10 (PID: 39994)
- python3.10 (PID: 39993)
- python3.10 (PID: 39995)
- python3.10 (PID: 39997)
- python3.10 (PID: 39996)
- python3.10 (PID: 39989)
- python3.10 (PID: 39991)
- python3.10 (PID: 39998)
- python3.10 (PID: 39999)
- python3.10 (PID: 40000)
- python3.10 (PID: 40001)
- python3.10 (PID: 40003)
- python3.10 (PID: 40005)
- python3.10 (PID: 40006)
- python3.10 (PID: 40002)
- python3.10 (PID: 40004)
- python3.10 (PID: 40007)
Executes the "rm" command to delete files or directories
- dpkg (PID: 39899)
- dash (PID: 39966)
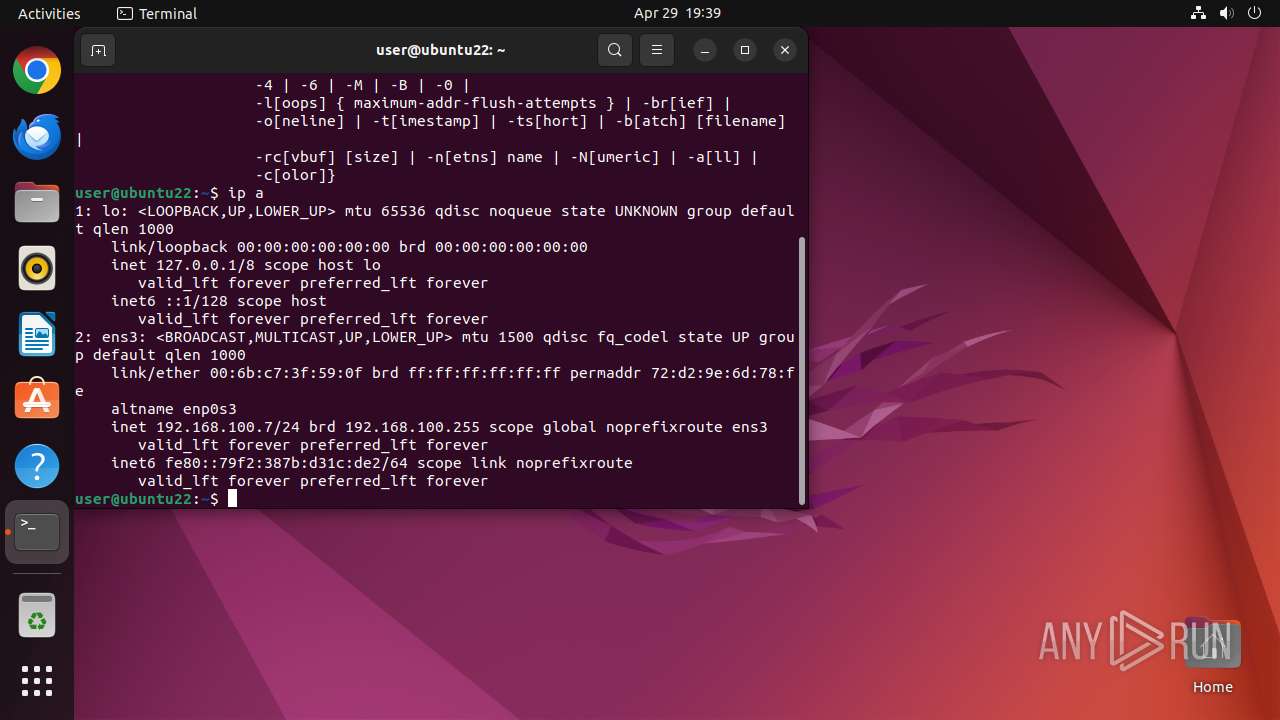
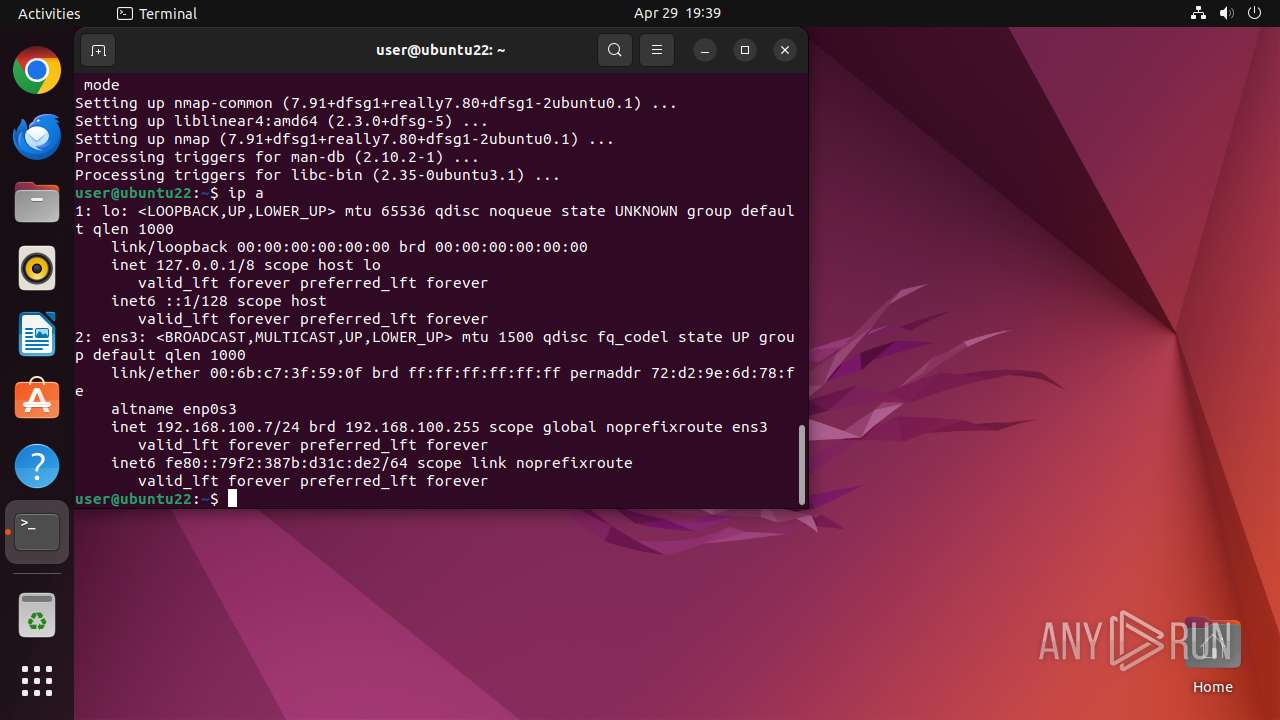
Reads network configuration
- sudo (PID: 40024)
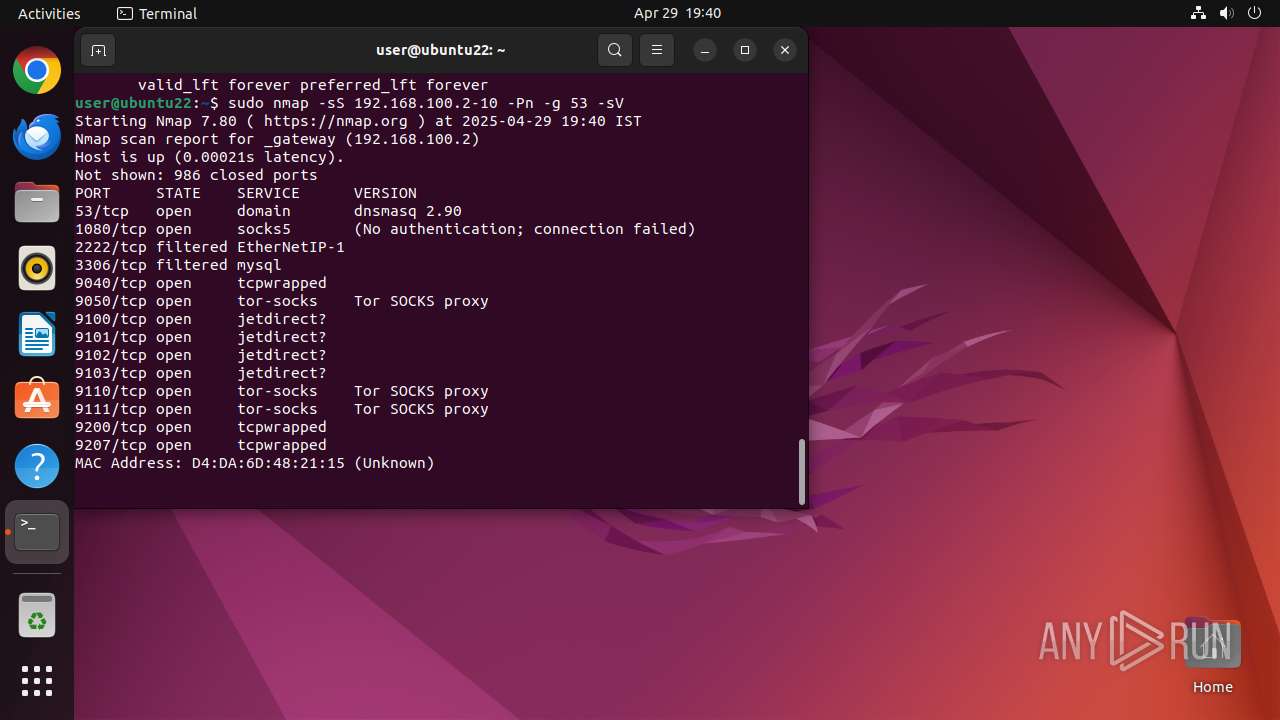
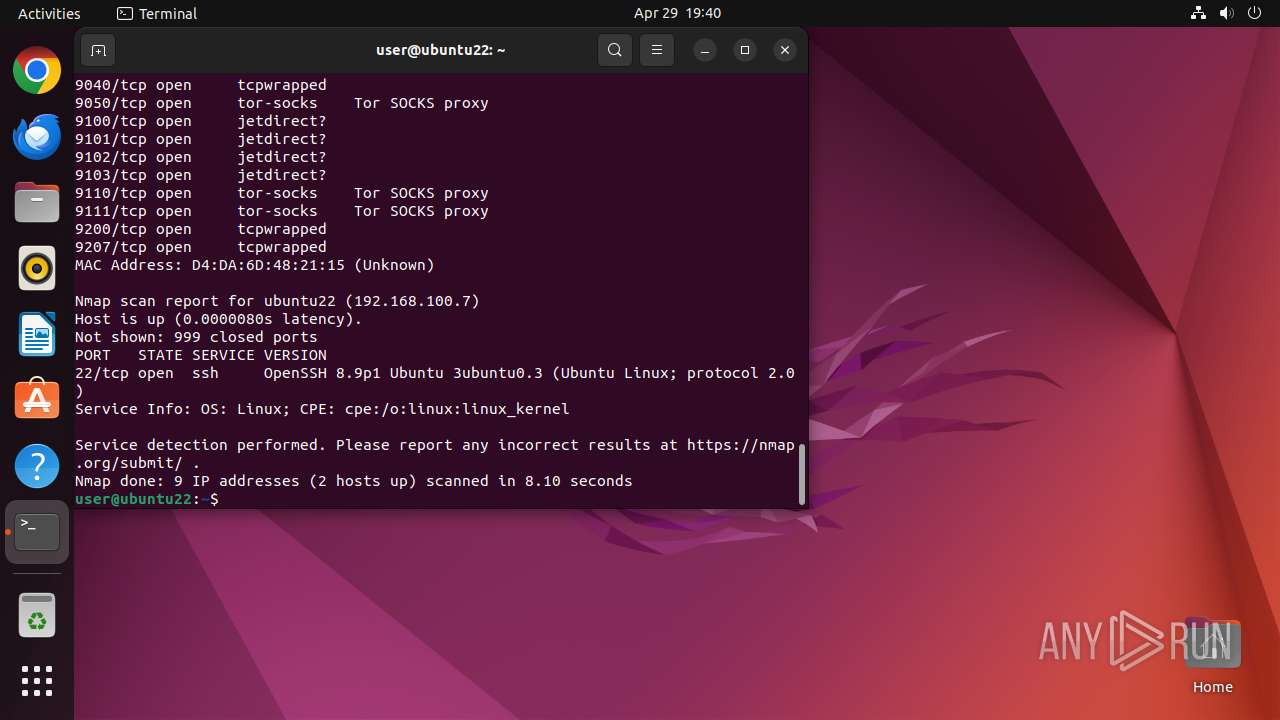
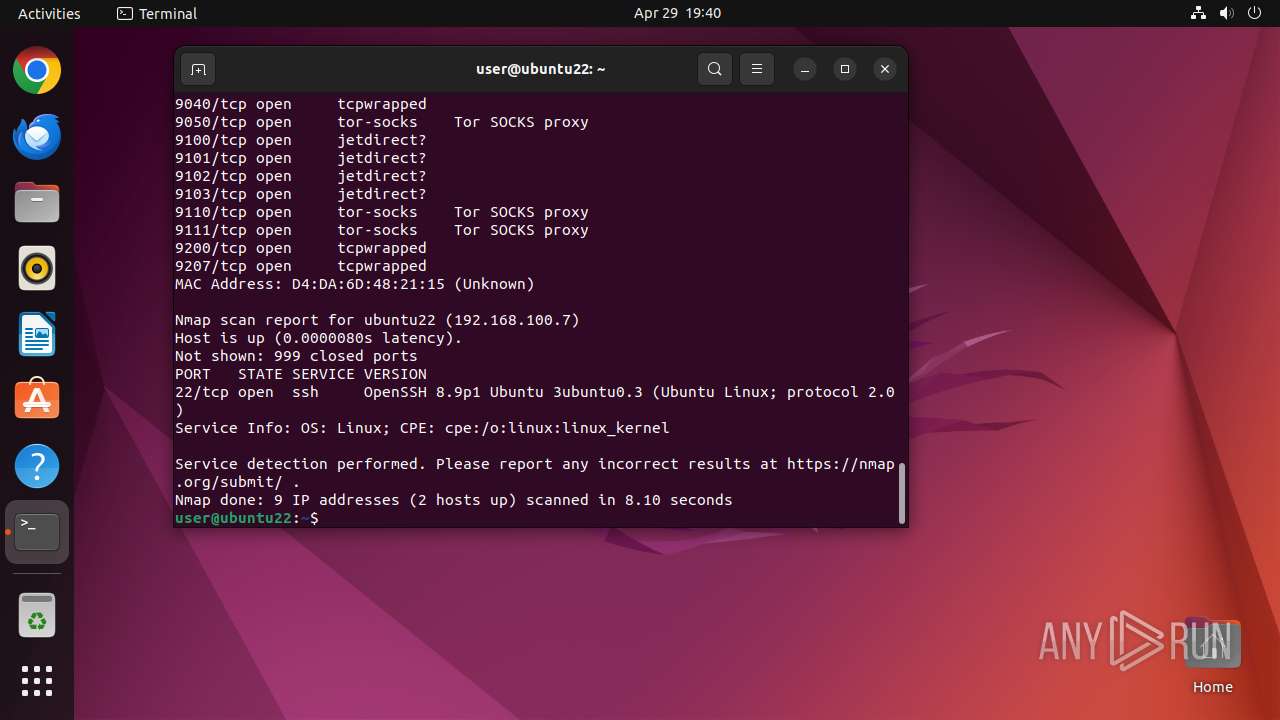
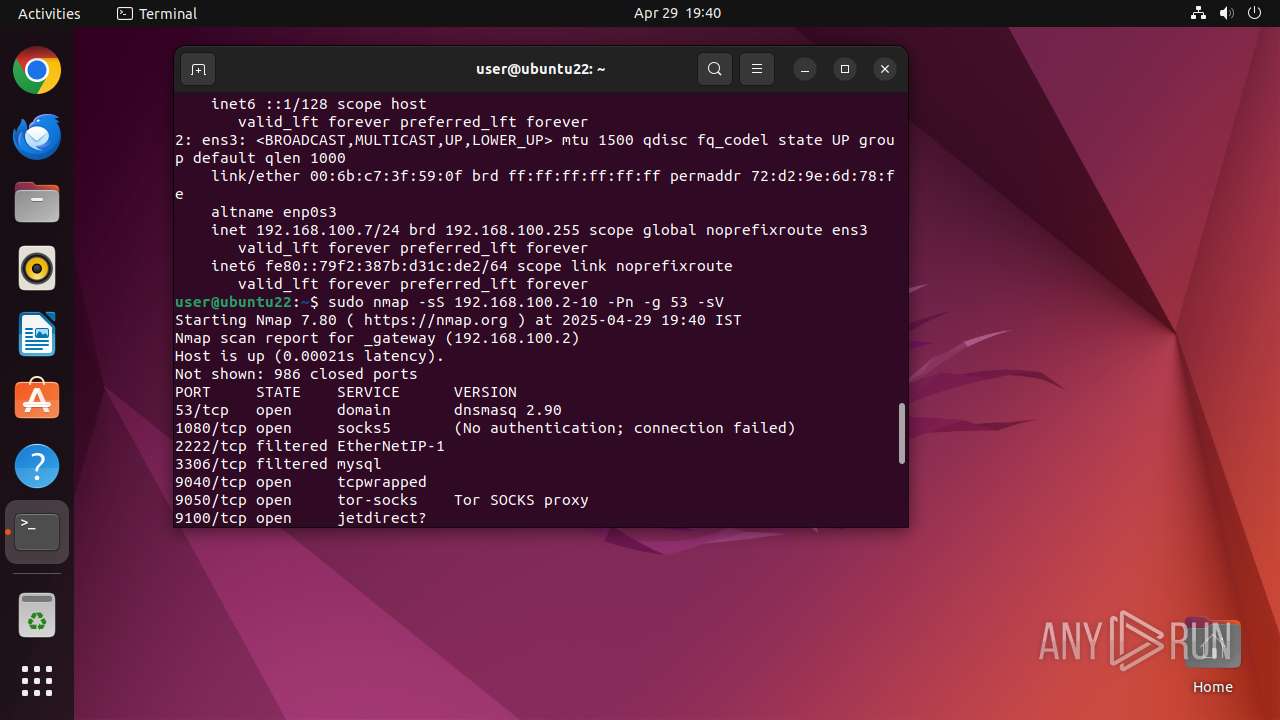
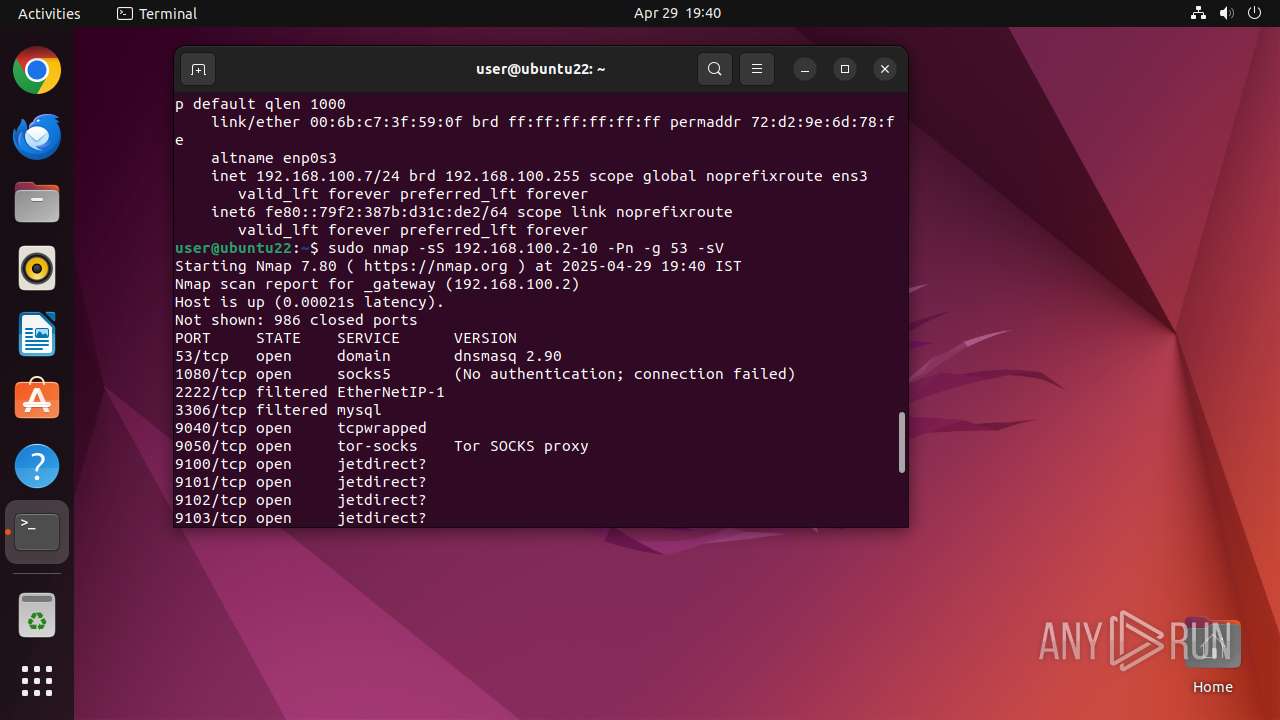
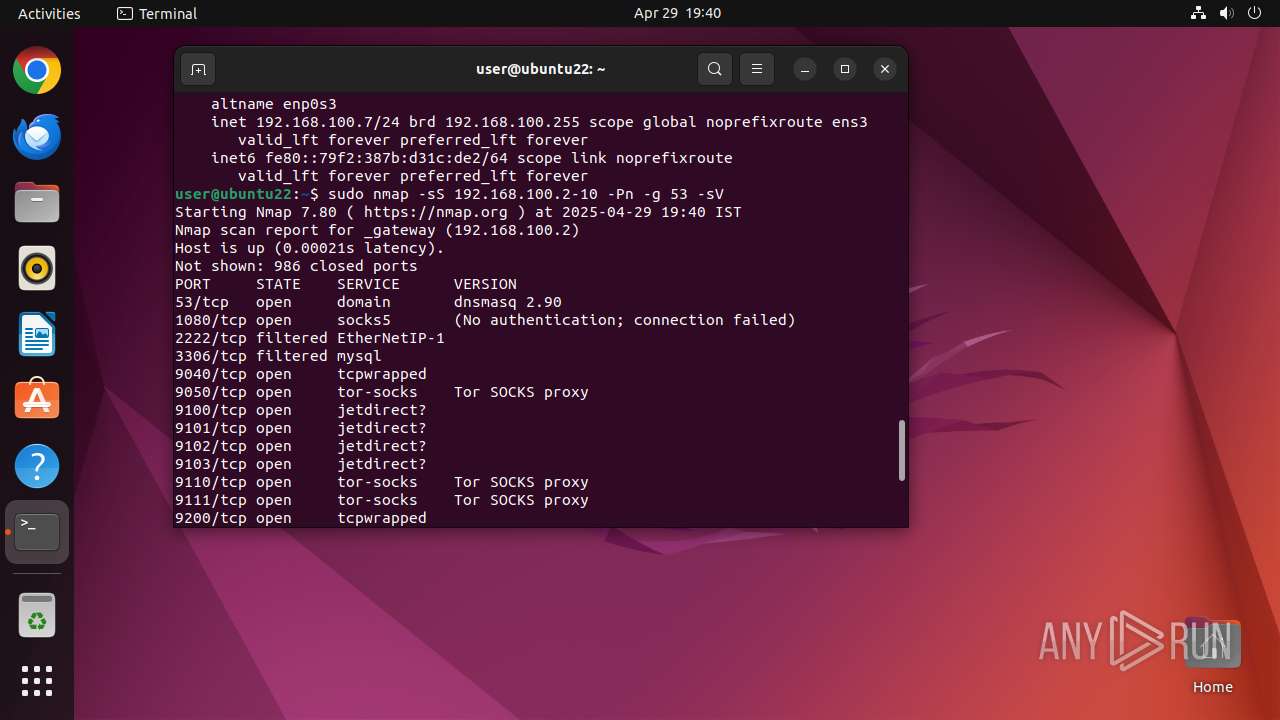
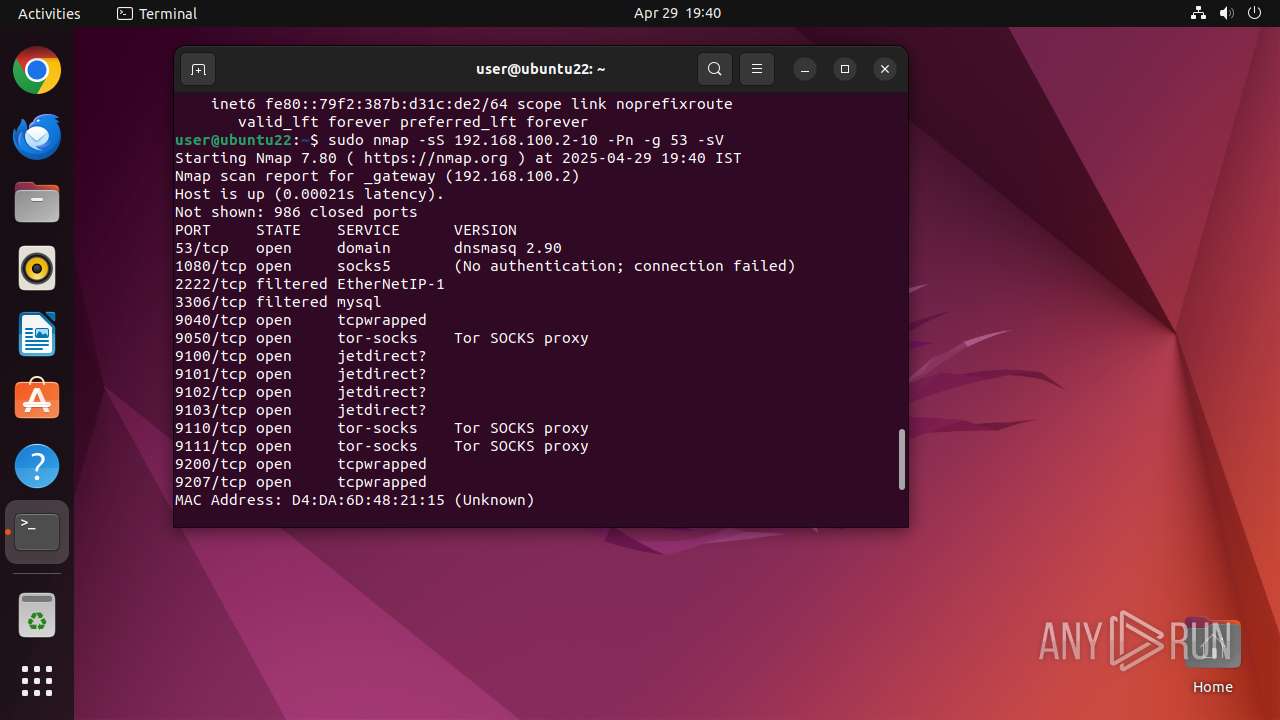
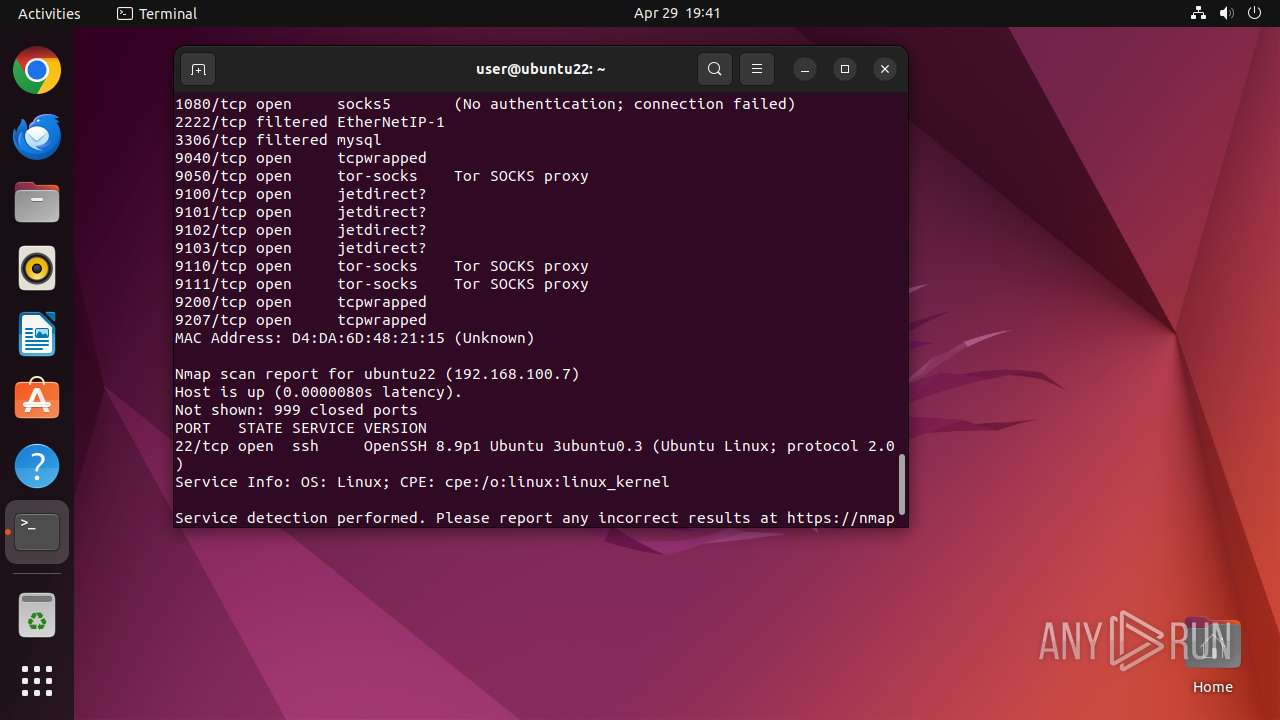
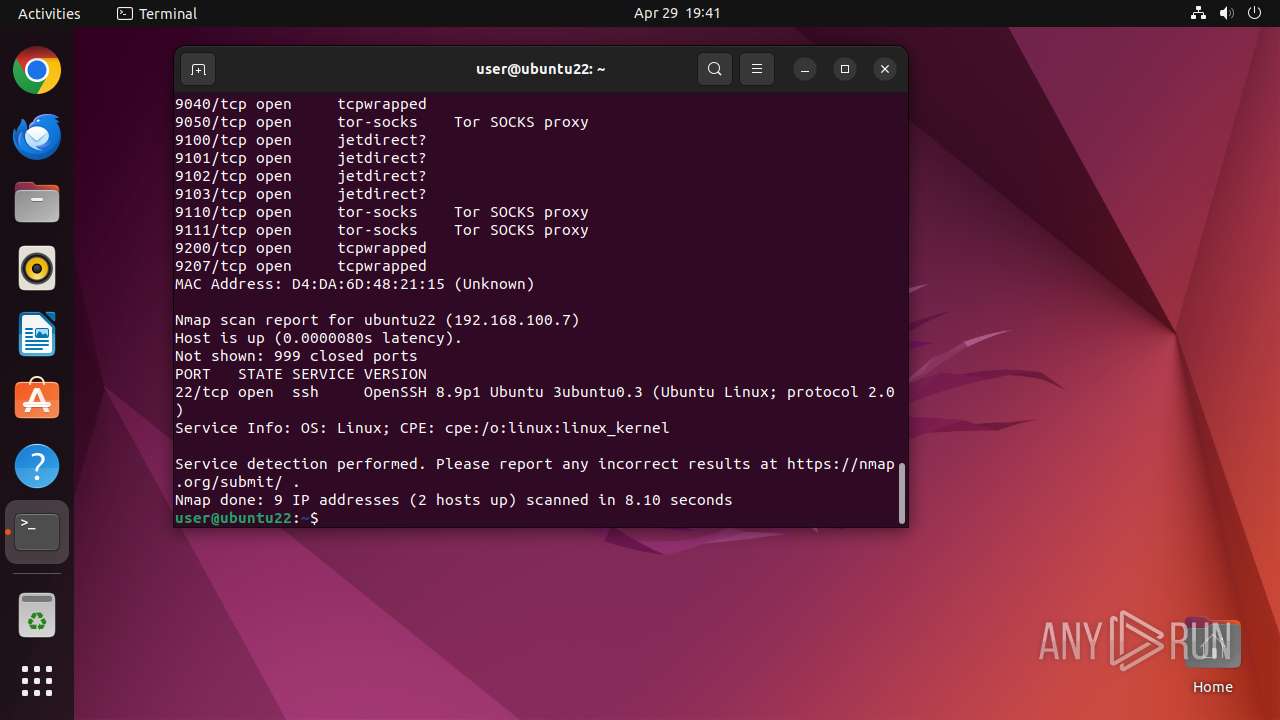
Connects to unusual port
- nmap (PID: 40025)
INFO
Checks timezone
- chrome (PID: 39490)
- python3.10 (PID: 39786)
- python3.10 (PID: 39826)
- apt (PID: 39842)
- http (PID: 39882)
- apt-extracttemplates (PID: 39893)
- dpkg (PID: 39946)
- update-alternatives (PID: 39948)
- python3.10 (PID: 39980)
- dpkg (PID: 39899)
- python3.10 (PID: 39992)
- python3.10 (PID: 39991)
- python3.10 (PID: 39993)
- python3.10 (PID: 39997)
- python3.10 (PID: 39996)
- python3.10 (PID: 39999)
- python3.10 (PID: 39989)
- python3.10 (PID: 39990)
- python3.10 (PID: 39994)
- python3.10 (PID: 39995)
- python3.10 (PID: 39998)
- python3.10 (PID: 40000)
- python3.10 (PID: 40001)
- python3.10 (PID: 40002)
- python3.10 (PID: 40004)
- python3.10 (PID: 40003)
- python3.10 (PID: 40005)
- sshd (PID: 40026)
- python3.10 (PID: 40006)
- python3.10 (PID: 40007)
- nmap (PID: 40025)
Creates file in the temporary folder
- apt (PID: 39842)
- apt-extracttemplates (PID: 39893)
- python3.10 (PID: 39980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
466
Monitored processes
243
Malicious processes
1
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 39488 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://activate\.dnaspaces\.io/e3t/Ctc/ZS+113/cBRdH04/VWXDNp8Ghbf5W92B-By7LfZ5GW5JQdxX5v-gTPN63y6pj3qgyTW95jsWP6lZ3p5W6BTHvd8yxTYMW8dzgCS5TbqM0W38yCMB5wlbRlW1y223R3LRyMSW4X80Qc62_FCzW72scPs8m5WgNW7x5NWr6xpq0zW53n76q57YQz1W8KKT9X2KySkNVXQLpt2wBBC2W4f7yP66pLx,%20category:%20Information%20Technology,%20id:%2052\. " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39489 | sudo -iu user google-chrome https://activate.dnaspaces.io/e3t/Ctc/ZS+113/cBRdH04/VWXDNp8Ghbf5W92B-By7LfZ5GW5JQdxX5v-gTPN63y6pj3qgyTW95jsWP6lZ3p5W6BTHvd8yxTYMW8dzgCS5TbqM0W38yCMB5wlbRlW1y223R3LRyMSW4X80Qc62_FCzW72scPs8m5WgNW7x5NWr6xpq0zW53n76q57YQz1W8KKT9X2KySkNVXQLpt2wBBC2W4f7yP66pLx,%20category:%20Information%20Technology,%20id:%2052. | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39490 | /usr/bin/google-chrome https://activate.dnaspaces.io/e3t/Ctc/ZS+113/cBRdH04/VWXDNp8Ghbf5W92B-By7LfZ5GW5JQdxX5v-gTPN63y6pj3qgyTW95jsWP6lZ3p5W6BTHvd8yxTYMW8dzgCS5TbqM0W38yCMB5wlbRlW1y223R3LRyMSW4X80Qc62_FCzW72scPs8m5WgNW7x5NWr6xpq0zW53n76q57YQz1W8KKT9X2KySkNVXQLpt2wBBC2W4f7yP66pLx,%20category:%20Information%20Technology,%20id:%2052. | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39491 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39492 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39493 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39494 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39495 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39496 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 39497 | "/opt/google/chrome/chrome https://activate\.dnaspaces\.io/e3t/Ctc/ZS+113/cBRdH04/VWXDNp8Ghbf5W92B-By7LfZ5GW5JQdxX5v-gTPN63y6pj3qgyTW95jsWP6lZ3p5W6BTHvd8yxTYMW8dzgCS5TbqM0W38yCMB5wlbRlW1y223R3LRyMSW4X80Qc62_FCzW72scPs8m5WgNW7x5NWr6xpq0zW53n76q57YQz1W8KKT9X2KySkNVXQLpt2wBBC2W4f7yP66pLx,%20category:%20Information%20Technology,%20id:%205" | /opt/google/chrome/chrome | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
168
Text files
423
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 39764 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | binary | |
MD5:— | SHA256:— | |||
| 39884 | perl | /var/cache/debconf/config.dat | text | |
MD5:— | SHA256:— | |||
| 39884 | perl | /var/cache/debconf/templates.dat | text | |
MD5:— | SHA256:— | |||
| 39490 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 39490 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 39490 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 39490 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 39490 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/metadata/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 39490 | chrome | /home/user/.config/google-chrome/Default/Extension State/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 39490 | chrome | /home/user/.config/google-chrome/Default/shared_proto_db/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
1 037
DNS requests
38
Threats
36
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.18:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
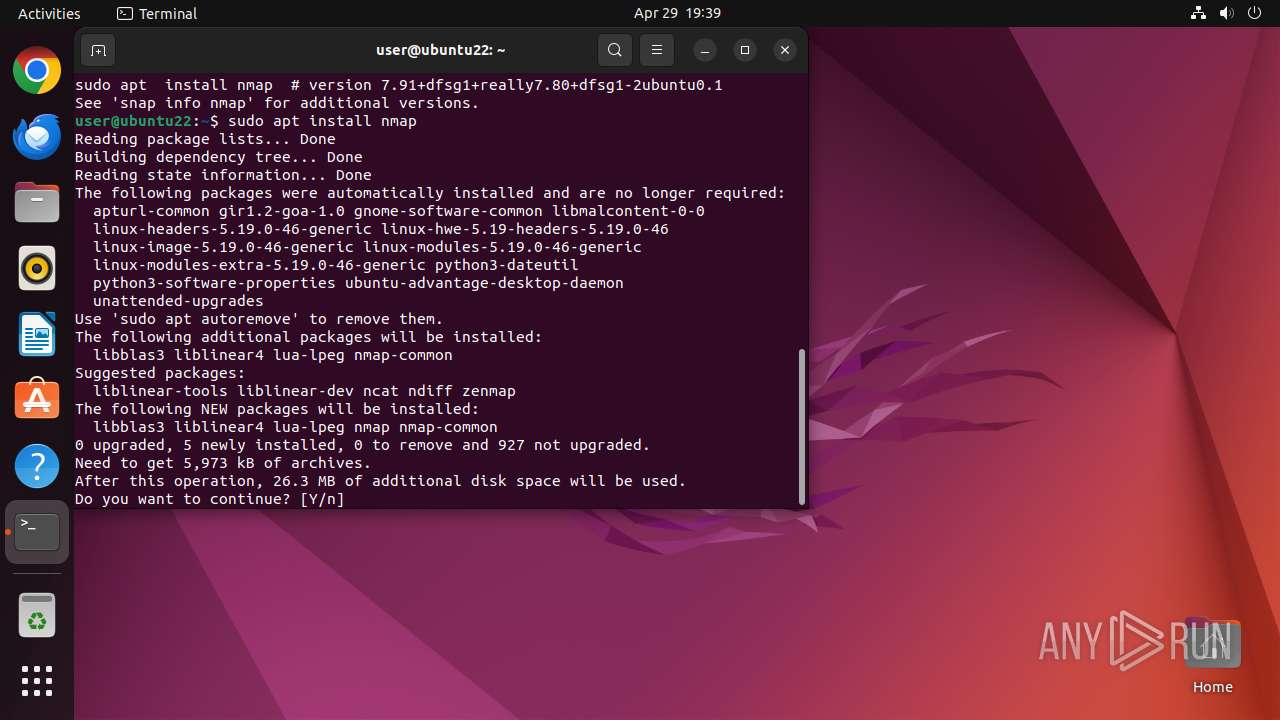
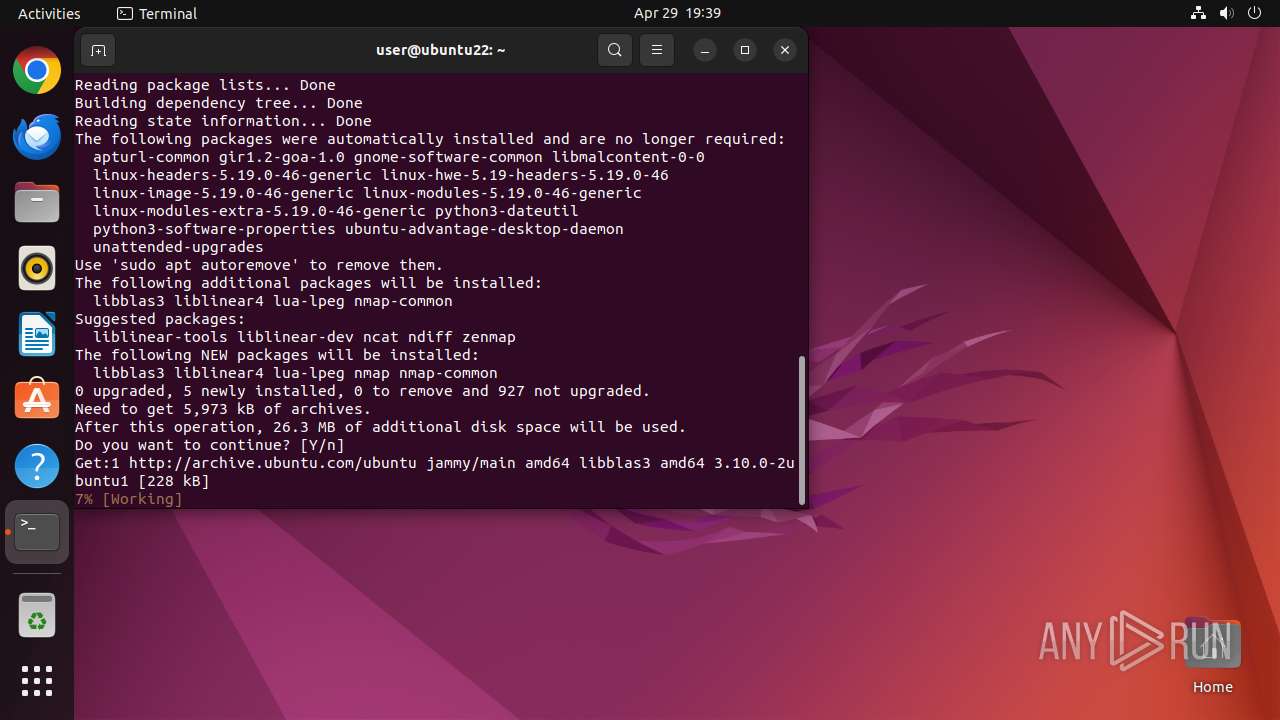
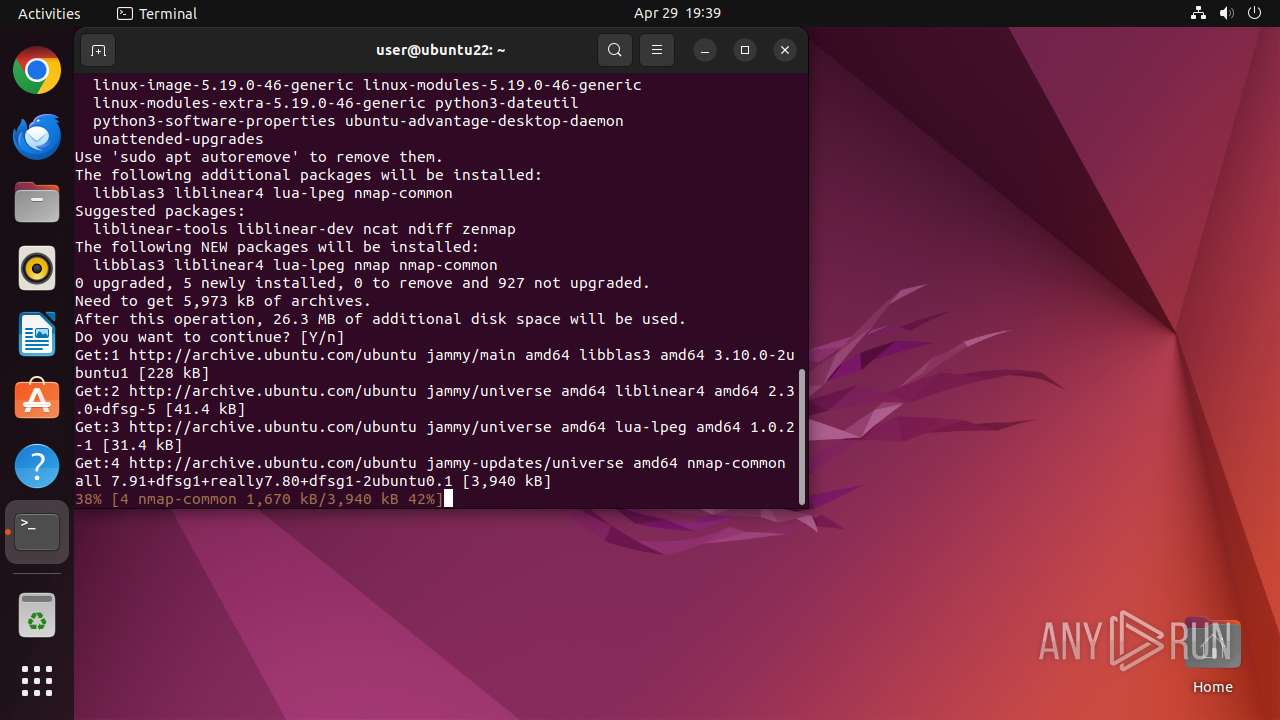
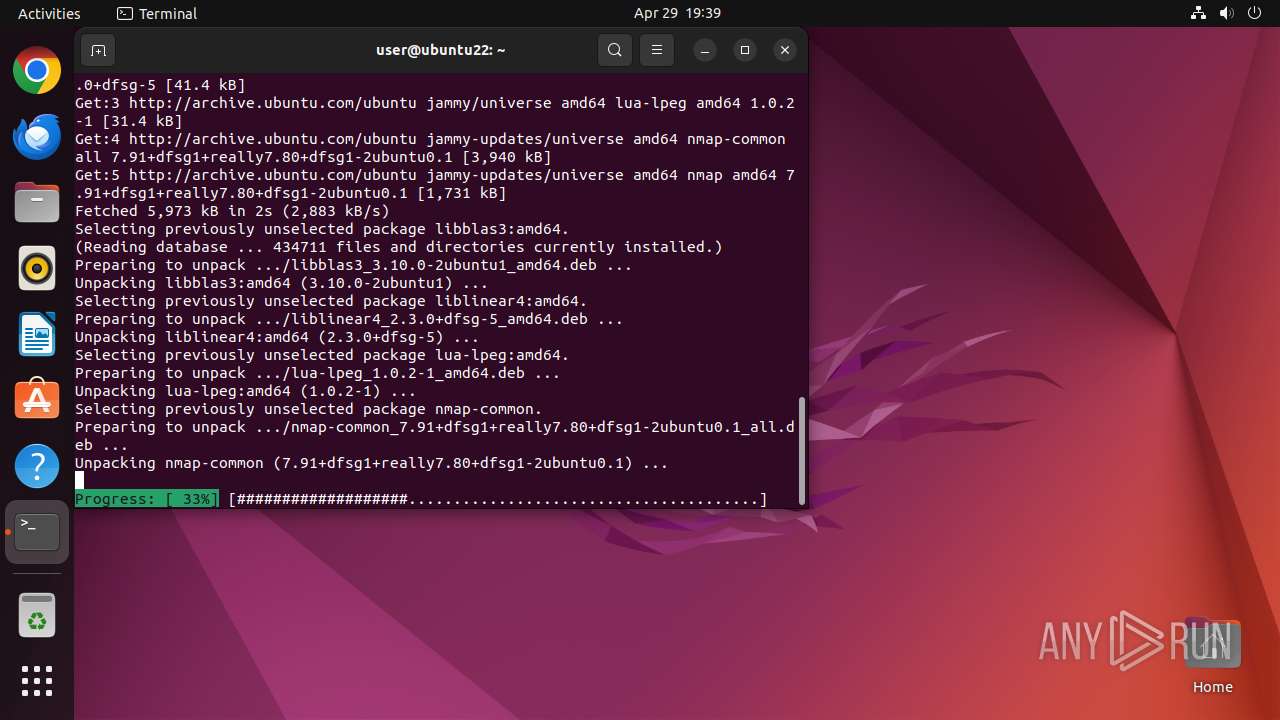
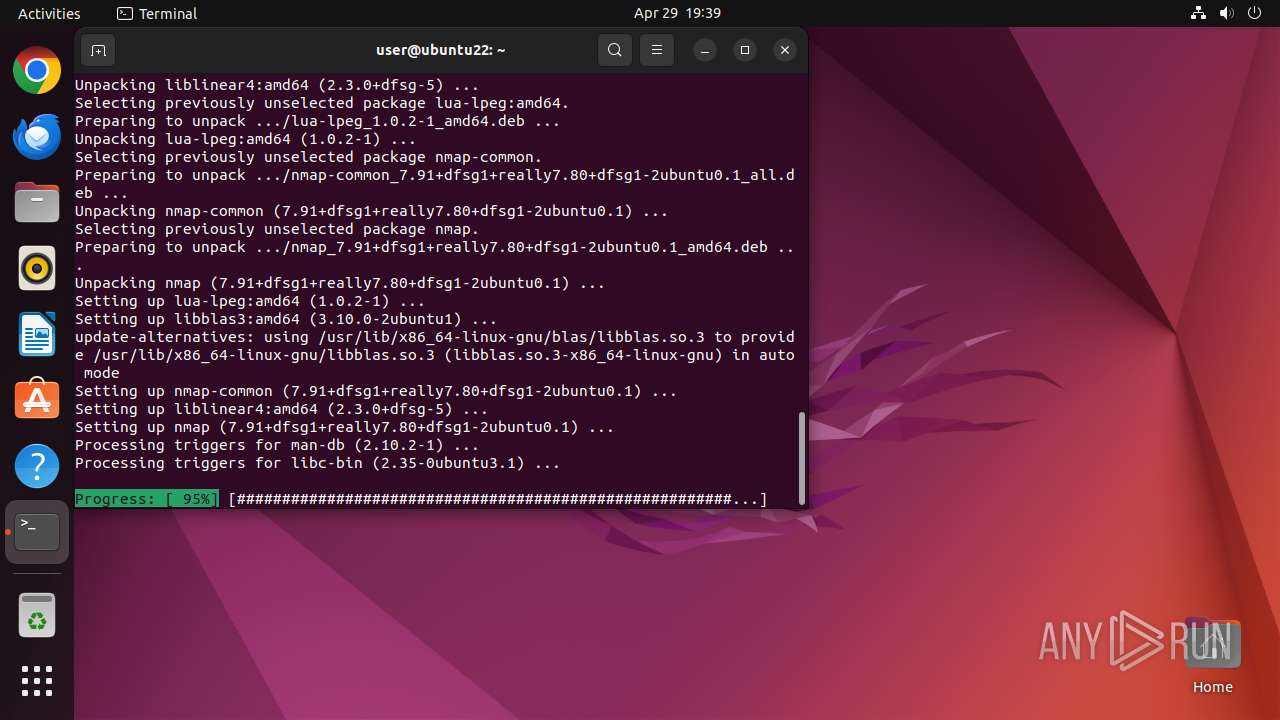
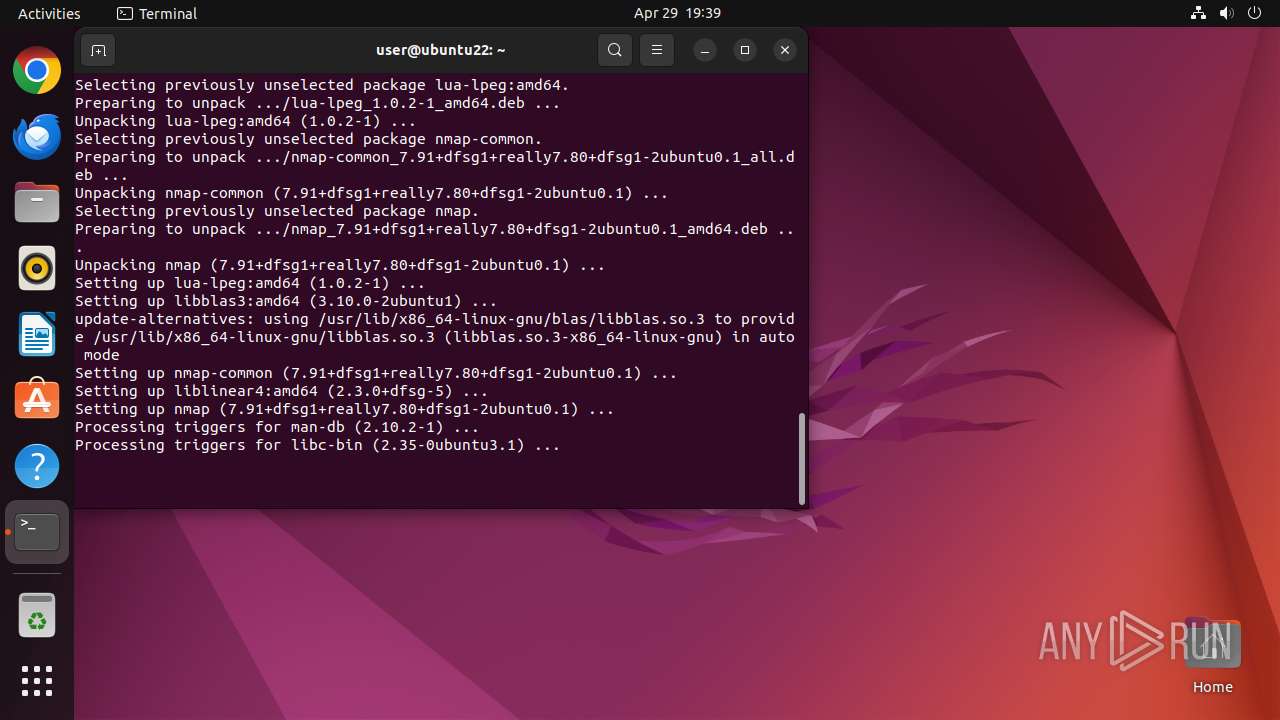
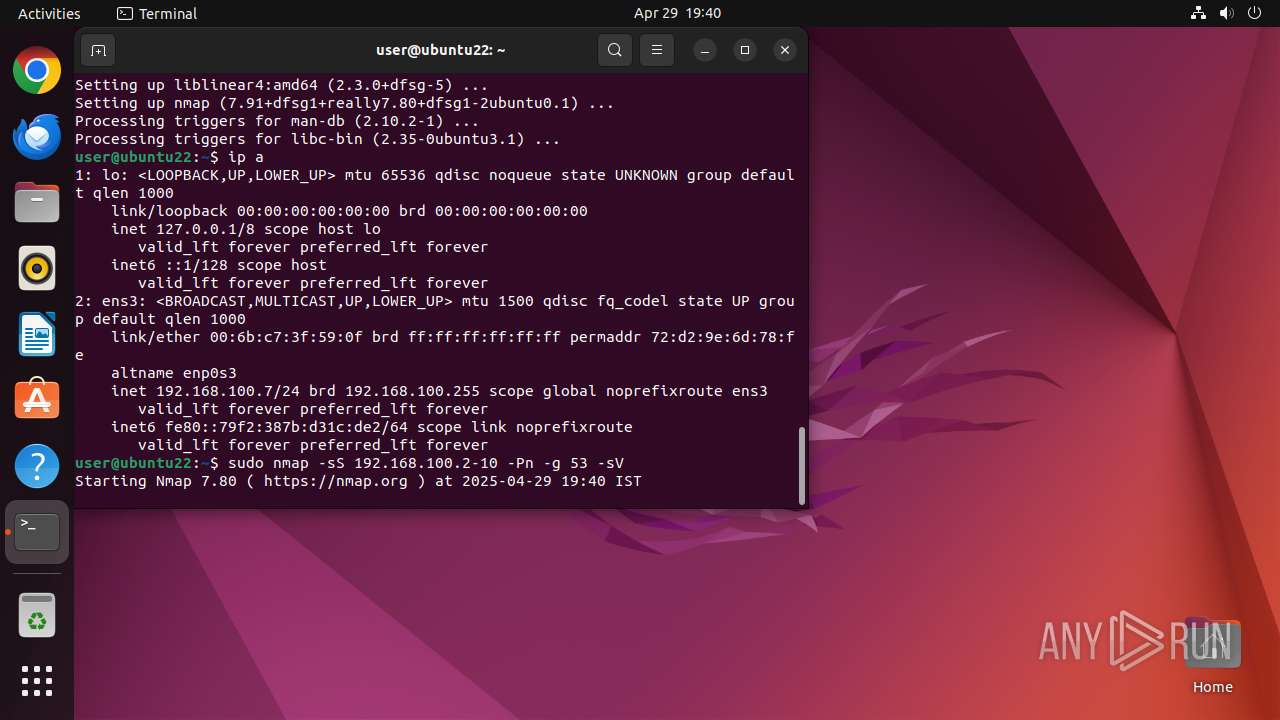
39882 | http | GET | 200 | 91.189.91.81:80 | http://archive.ubuntu.com/ubuntu/pool/main/l/lapack/libblas3_3.10.0-2ubuntu1_amd64.deb | unknown | — | — | whitelisted |
39882 | http | GET | — | 91.189.91.81:80 | http://archive.ubuntu.com/ubuntu/pool/universe/libl/liblinear/liblinear4_2.3.0%2bdfsg-5_amd64.deb | unknown | — | — | whitelisted |
39882 | http | GET | — | 91.189.91.81:80 | http://archive.ubuntu.com/ubuntu/pool/universe/l/lua-lpeg/lua-lpeg_1.0.2-1_amd64.deb | unknown | — | — | whitelisted |
39882 | http | GET | — | 91.189.91.81:80 | http://archive.ubuntu.com/ubuntu/pool/universe/n/nmap/nmap-common_7.91%2bdfsg1%2breally7.80%2bdfsg1-2ubuntu0.1_all.deb | unknown | — | — | whitelisted |
39882 | http | GET | 200 | 91.189.91.81:80 | http://archive.ubuntu.com/ubuntu/pool/universe/n/nmap/nmap_7.91%2bdfsg1%2breally7.80%2bdfsg1-2ubuntu0.1_amd64.deb | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.18:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
1178 | snap-store | 195.181.170.19:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
39535 | chrome | 199.60.103.2:443 | activate.dnaspaces.io | — | — | suspicious |
39535 | chrome | 216.58.206.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
39535 | chrome | 142.250.185.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
39535 | chrome | 108.177.119.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
39535 | chrome | 151.101.193.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | FASTLY | US | unknown |
39535 | chrome | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
activate.dnaspaces.io |
| unknown |
accounts.google.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
a.nel.cloudflare.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
39535 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39535 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39535 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39535 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39535 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39535 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
39535 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
39535 | chrome | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |