| File name: | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16 |
| Full analysis: | https://app.any.run/tasks/af8fd7c5-68f1-46eb-9841-ce84bc4e9aff |
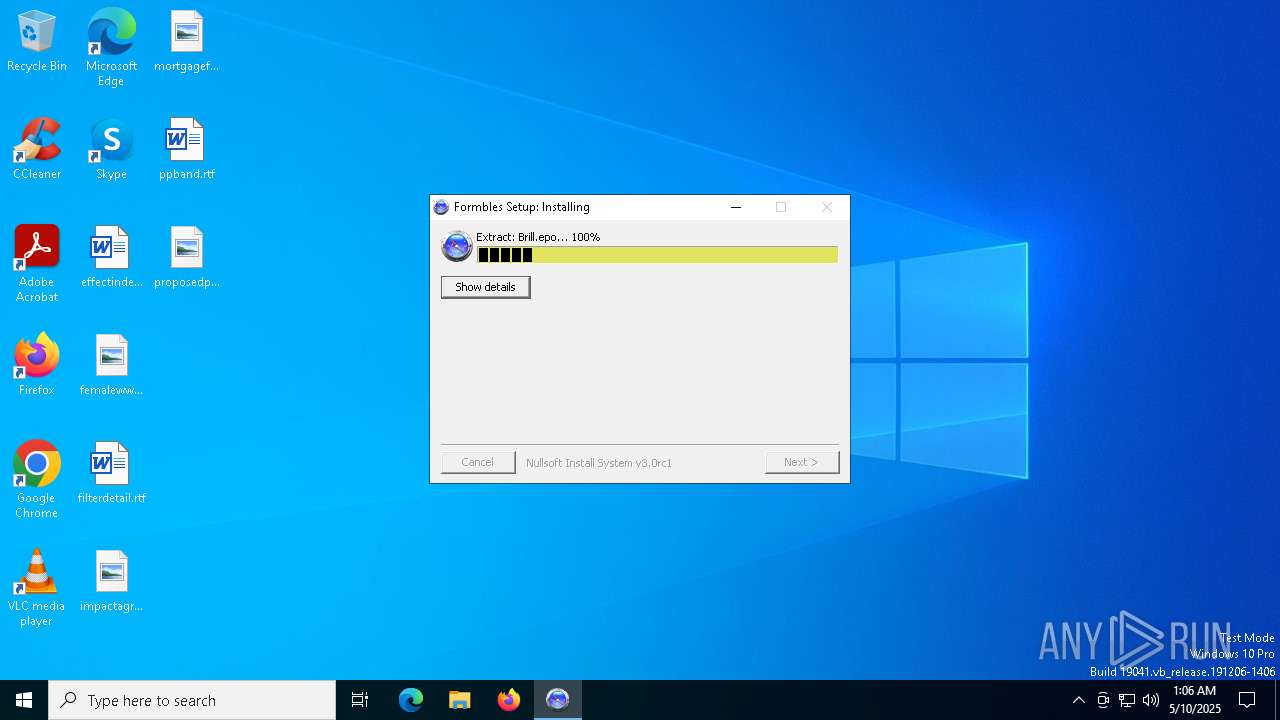
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 01:06:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 52A5DE628A72B697E3EFC2F88DBB250B |
| SHA1: | 9EA002AD3C226A5C87EE952F8E91EED6D8BE1C8E |
| SHA256: | C36C45A80DF11177270A9906B711737E3C9329195E0A9E8B1FD7F10879C28C16 |
| SSDEEP: | 49152:6L79YZKYWfJBq9MTYA0ZjNF8dYllSsl1E5pQd7bqPGRe4L+e/vaaJyoaJjmDx585:4YkYWfJBqOTYA0ZX8ylFyQd7bqPyTj/O |
MALICIOUS
Executing a file with an untrusted certificate
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
SUSPICIOUS
Executable content was dropped or overwritten
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
Malware-specific behavior (creating "System.dll" in Temp)
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
There is functionality for taking screenshot (YARA)
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
The process creates files with name similar to system file names
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
Application launched itself
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
Reads security settings of Internet Explorer
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
INFO
The sample compiled with english language support
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
Creates files or folders in the user directory
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
Create files in a temporary directory
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
Checks supported languages
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
Reads the computer name
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 7084)
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
Reads the machine GUID from the registry
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
Reads the software policy settings
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
- slui.exe (PID: 4776)
Checks proxy server information
- c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe (PID: 456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:03 20:18:50+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x326a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | isokeraunophonic |
| LegalTrademarks: | skrivekommandoens |
| OriginalFileName: | ublides varmeslangebekendtgrelsernes.exe |
Total processes
137
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Users\admin\AppData\Local\Temp\c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe" | C:\Users\admin\AppData\Local\Temp\c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | ||||||||||||
User: admin Company: isokeraunophonic Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4776 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6004 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7020 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7084 | "C:\Users\admin\AppData\Local\Temp\c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe" | C:\Users\admin\AppData\Local\Temp\c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | explorer.exe | ||||||||||||
User: admin Company: isokeraunophonic Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 652
Read events
1 377
Write events
275
Delete events
0
Modification events
| (PID) Process: | (7084) c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | Key: | HKEY_CURRENT_USER\damagement\Paraboloid |
| Operation: | write | Name: | droh |
Value: %Udtrringsarbejdet%\Klippevaeggen.exe | |||
| (PID) Process: | (456) c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (456) c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (456) c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
3
Suspicious files
18
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\Brill.epo | binary | |
MD5:D383E1E4395258F136AE2B4B0B319C4E | SHA256:6EDBFB685265C61C87EDA919ABAAADC66848BA9192D85116A42F4640EAF2F559 | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\woolpack\subglottal.ini | text | |
MD5:870B095435A57B144F04DE3110CCB48D | SHA256:41A94F25D3388EC2F55F65D516F4DAFCBDF61EB1C660F88EE8396CBB8ACB4D38 | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\Panuelos.Ban | binary | |
MD5:7F35CBA9623AFF92F75BAB7A7FE87E02 | SHA256:F1BACACD322FA51ABD070CEE348C46164C3EDFCE6295E753F9A77DADDABE60C2 | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\Telestyrelsens.Pal172 | binary | |
MD5:E10BF8BF584DD627FE70560C85508929 | SHA256:F1AF8E98ECBA34B69FC7FC14CE8989C497F3C87009E4C9A7857F64477E407C1B | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\Uegnethed.jpg | image | |
MD5:AE273AA8FFF9B76BF5928627AB9400CD | SHA256:20B1EFCFC8BCA93AAC3BB12C96604E4CC0FB3F1F23B2C97BA55AA45CBC06C083 | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\woolpack\phytohemagglutinin.tra | binary | |
MD5:322A8ABDC859FBF6339672708518C346 | SHA256:7480EF1339BCAD8B7D3CF3C4C6C709EE21FF0B4EAA8F07E87DC94DC8B94A168B | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\indtegningers.txt | text | |
MD5:97DE9CE2188B1DEE75CA68E809DBE1EF | SHA256:B444D0C5D4551DD20BB29F4185719920A85D5744439B55232B1E979060050158 | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\atomkernes.tor | binary | |
MD5:FCA5035E2376A1DB378967EF4E713145 | SHA256:4ACF7B1FAB9C5FAD255074681123E3C8BF0A1C57EB0DA30DD45B0A16623D0892 | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\AppData\Local\isoenzymic\aminobenzamide.jpg | image | |
MD5:CD4C58D7E720DEB25E24436453759A21 | SHA256:C01746DD8F5BCE4CA610BE8B410EA87280F7AE3AB52A338E592D9F6DF0772181 | |||
| 7084 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | C:\Users\admin\Documents\Anklers251.ini | text | |
MD5:BBE81BA8DBEF1FA1C8A2810049DA182C | SHA256:48E8797811ECFEEDDC1DDBA311CB7B4D430AEBC0AE0F9A3EF640899A5DAA7176 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
26
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
456 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | GET | 200 | 142.250.186.131:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
456 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | GET | 200 | 142.250.186.131:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
456 | c36c45a80df11177270a9906b711737e3c9329195e0a9e8b1fd7f10879c28c16.exe | GET | 200 | 216.58.206.35:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEA85wFTvuwmlCdtY0UxEIqg%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
drive.google.com |
| whitelisted |
c.pki.goog |
| whitelisted |