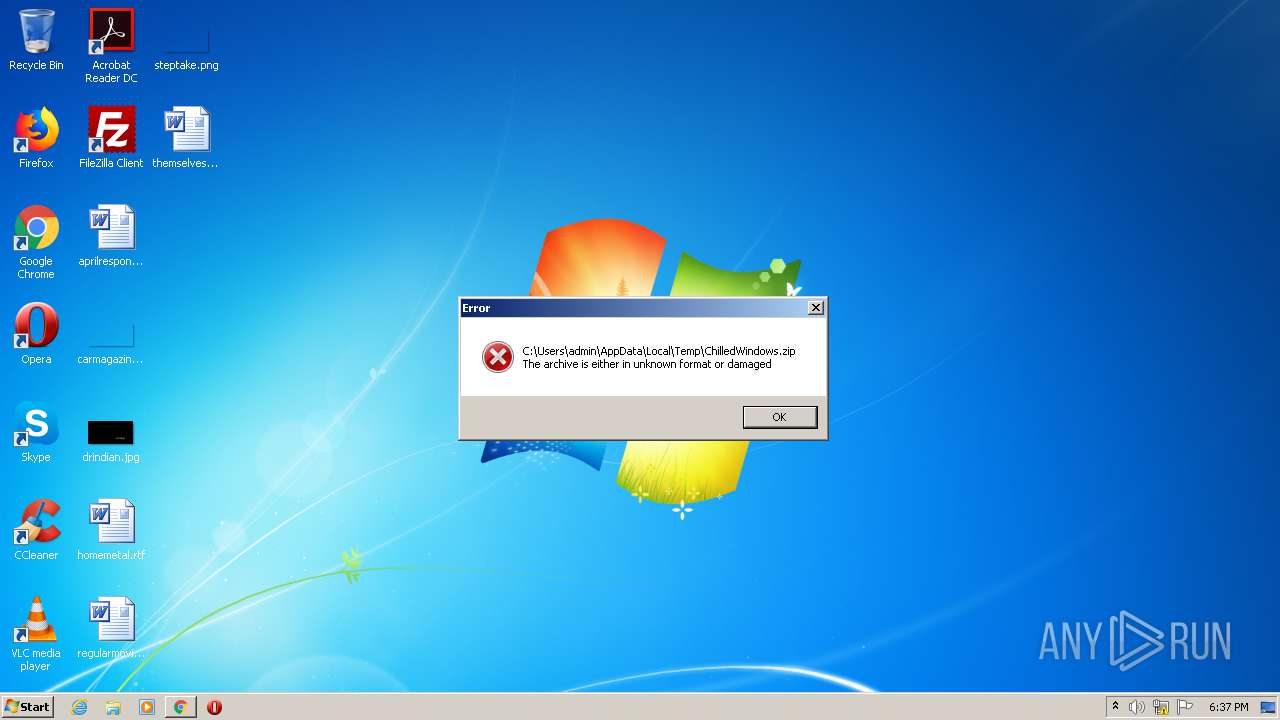
| download: | ChilledWindows.zip |
| Full analysis: | https://app.any.run/tasks/bc6cf919-f4b9-4b39-b344-bcd01bfd33c1 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 18:37:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | B473419A9991E8155E6891624874A838 |
| SHA1: | 1885362A1F97C7952A55F81464A822EEA5CAB60F |
| SHA256: | C363CD924ABD73D4427F142207FD2A8396791AA3D0B73FC11E6CC96C8FC789CB |
| SSDEEP: | 1536:p8yte6uqw2wIbmT0cYadYVadYmadYV7smX9ADvSAtLZ0WrfdEQDwZ4L+K8vQVib8:KytDuqw2wIbFadYVadYmadYV7rODSAtF |
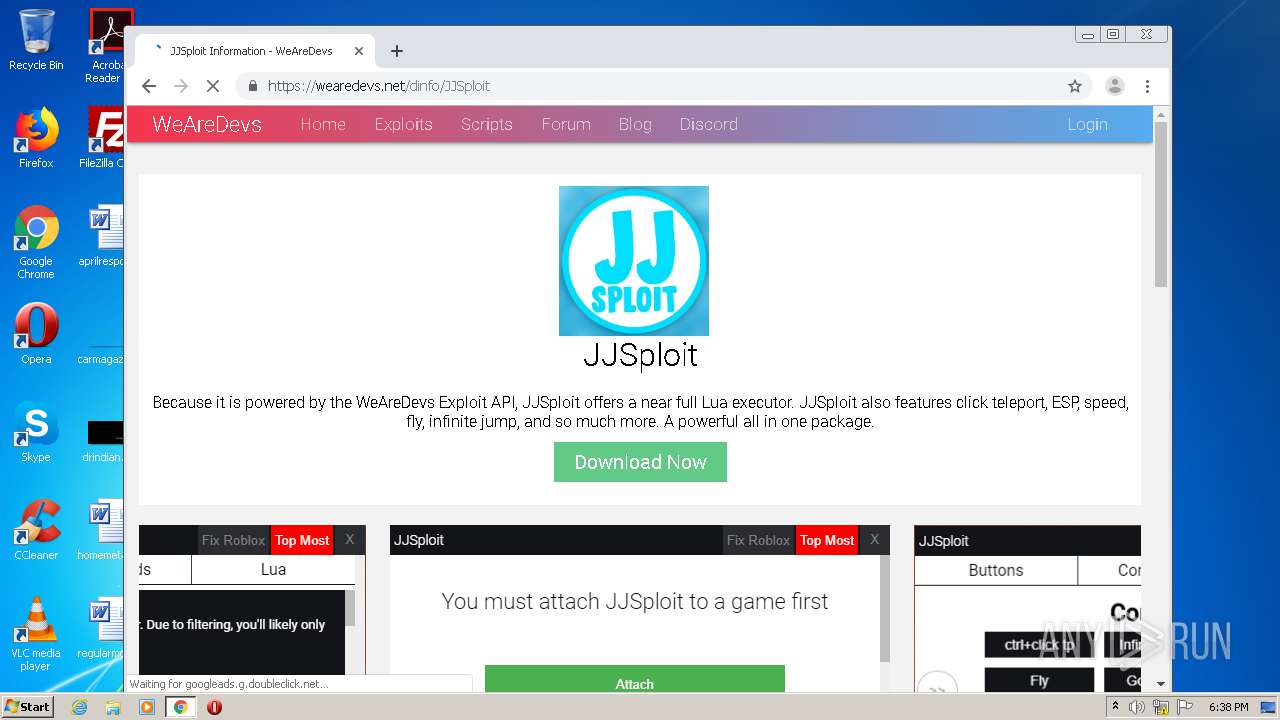
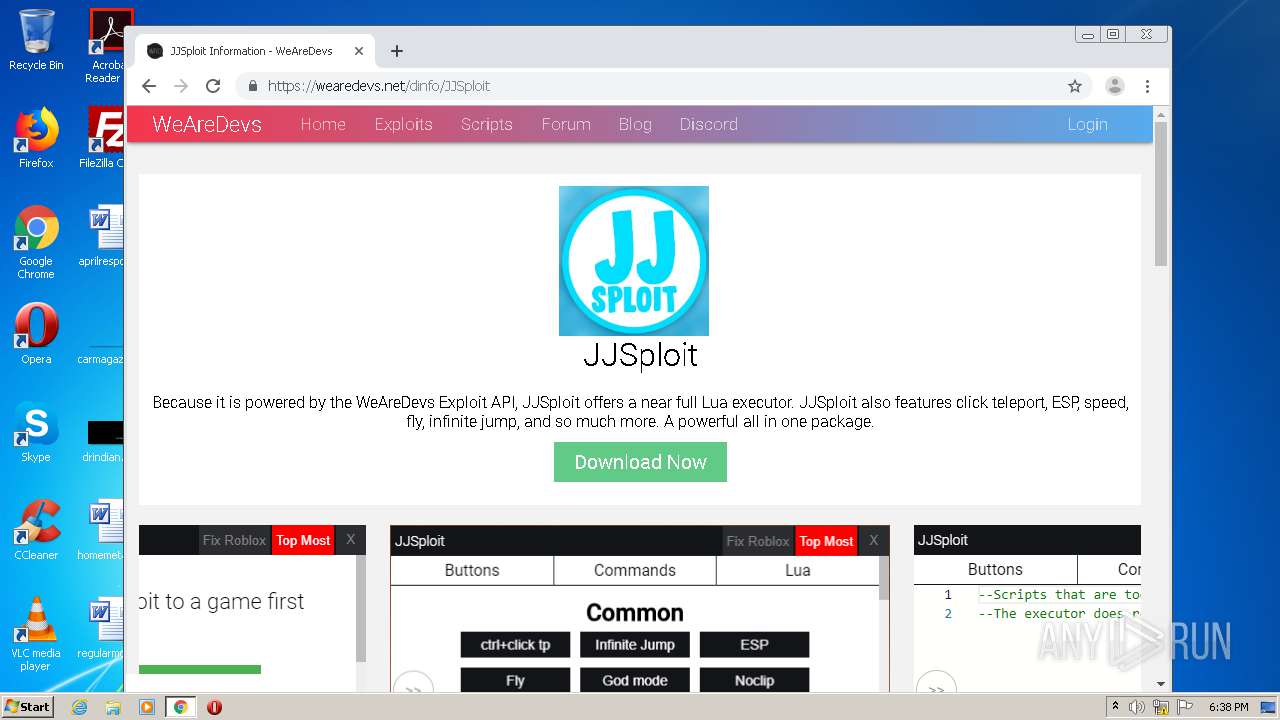
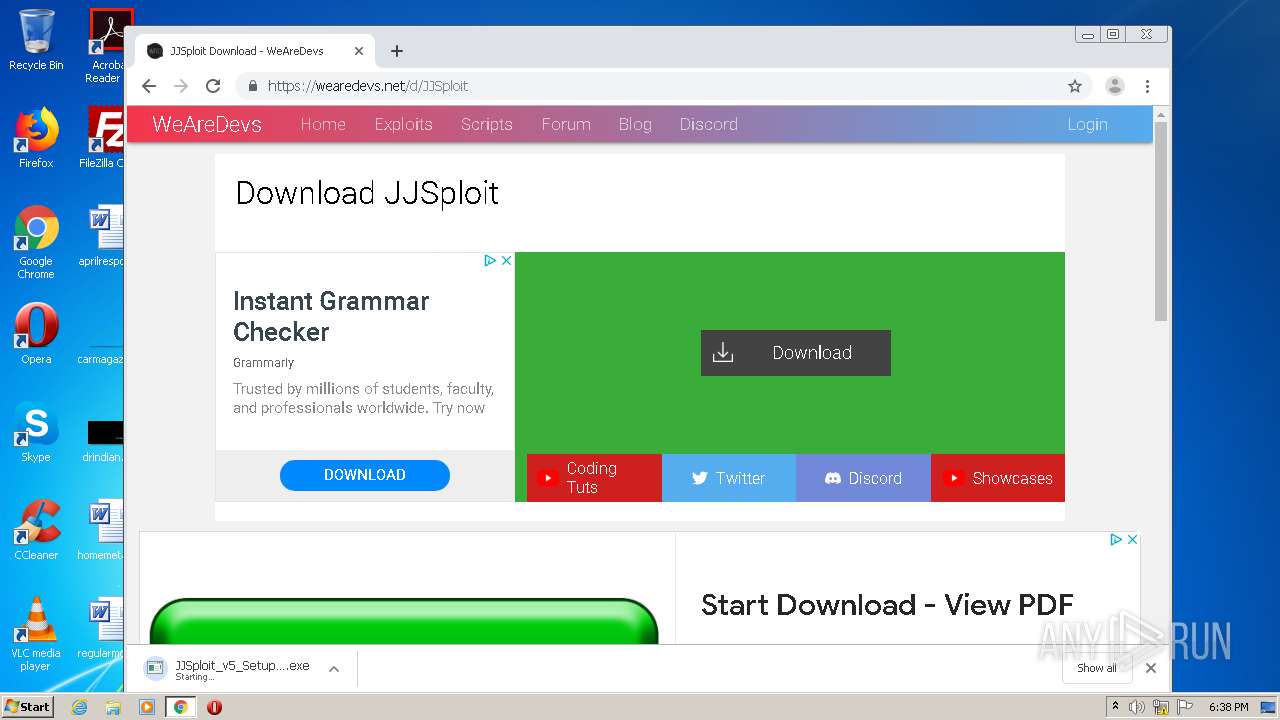
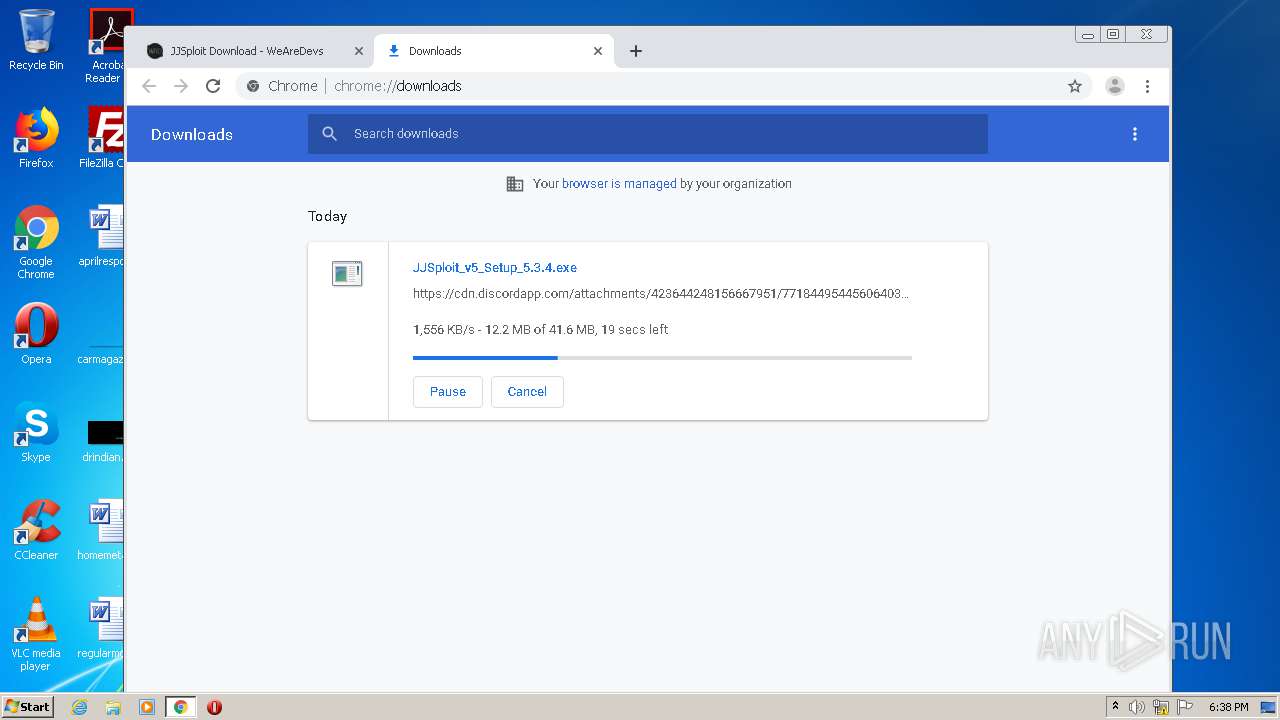
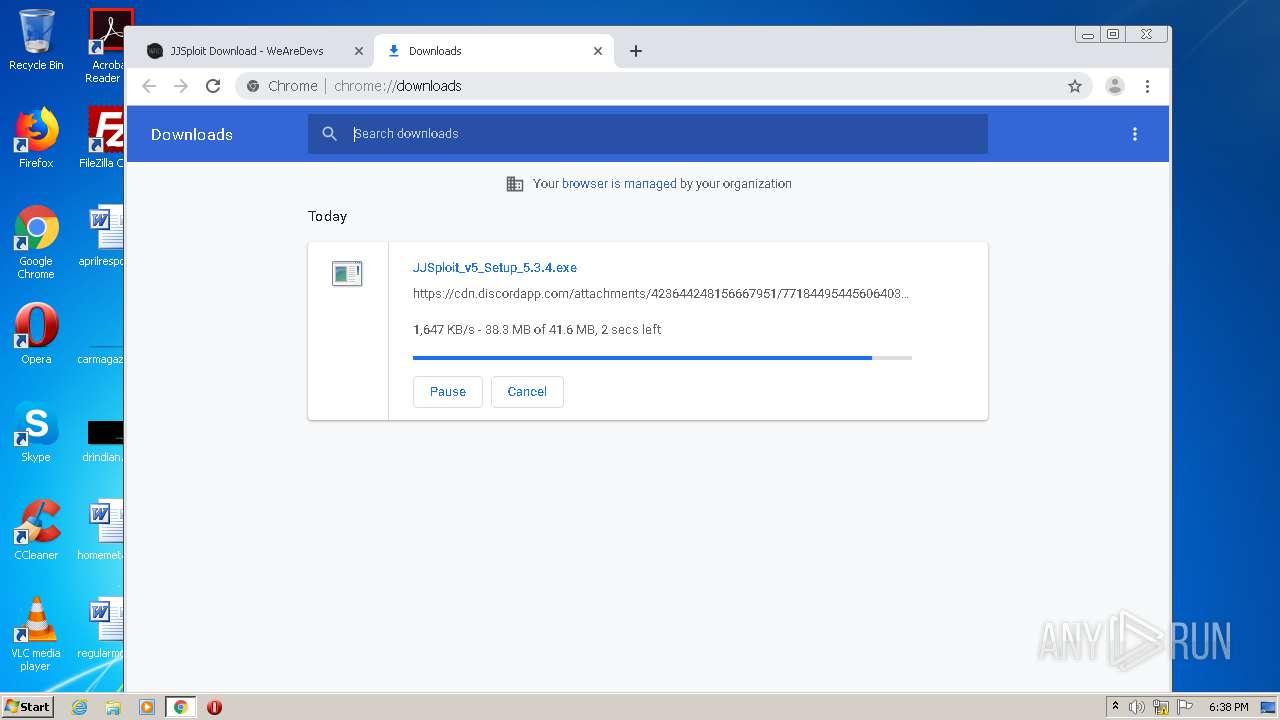
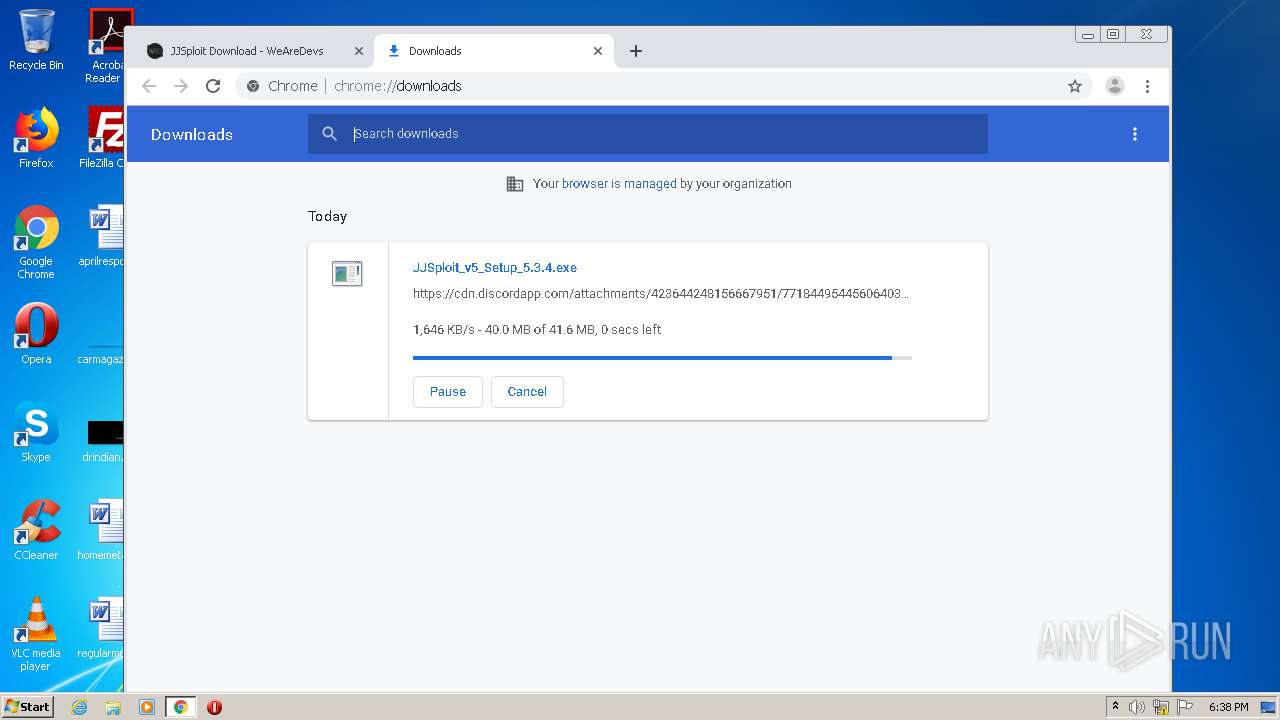
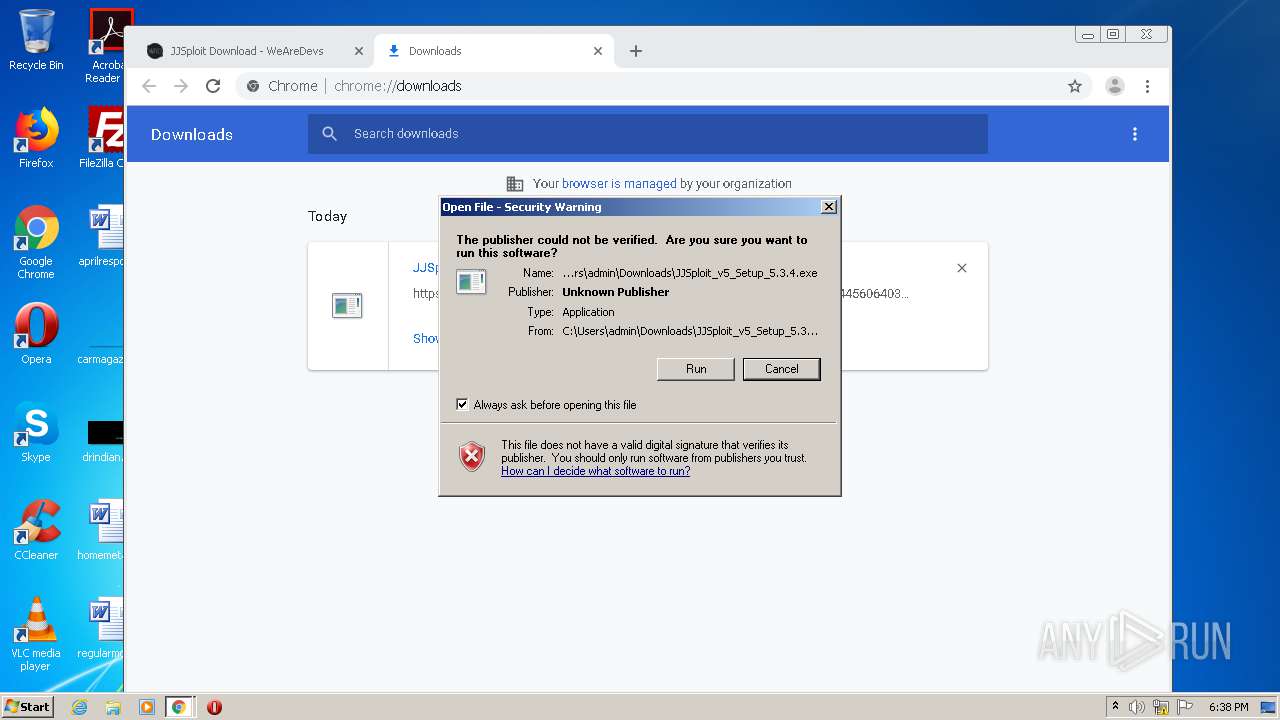
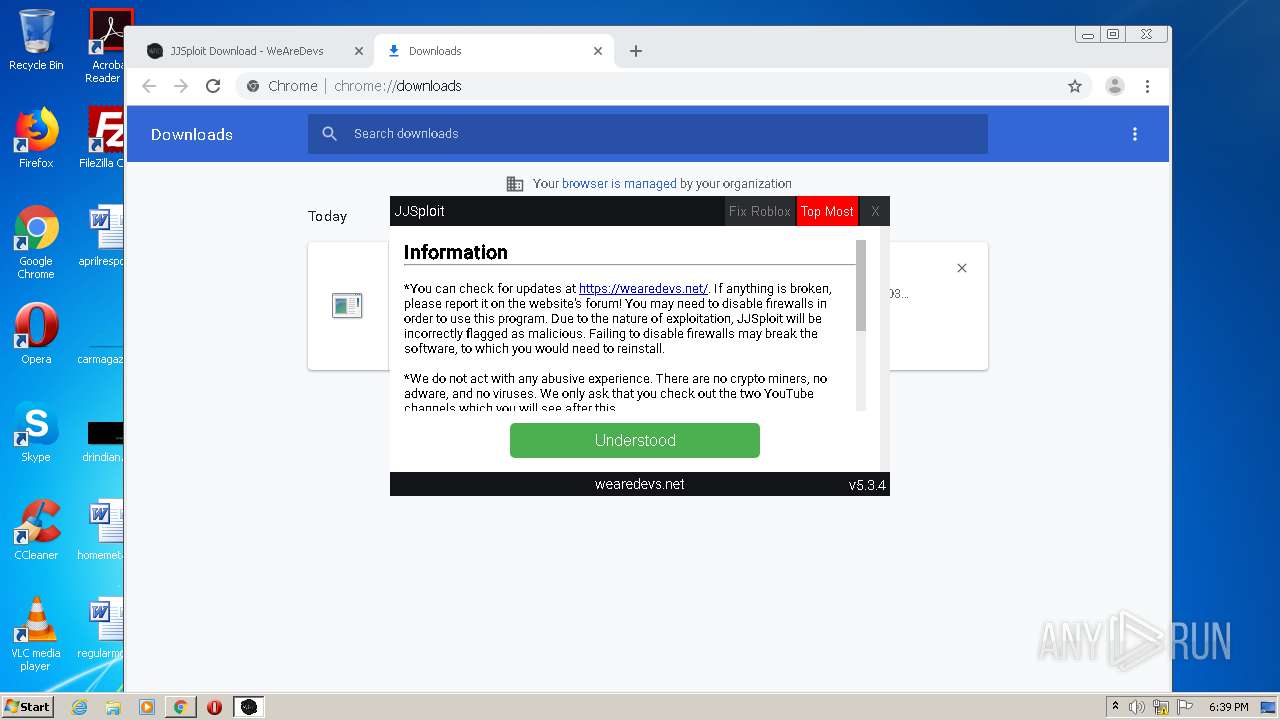
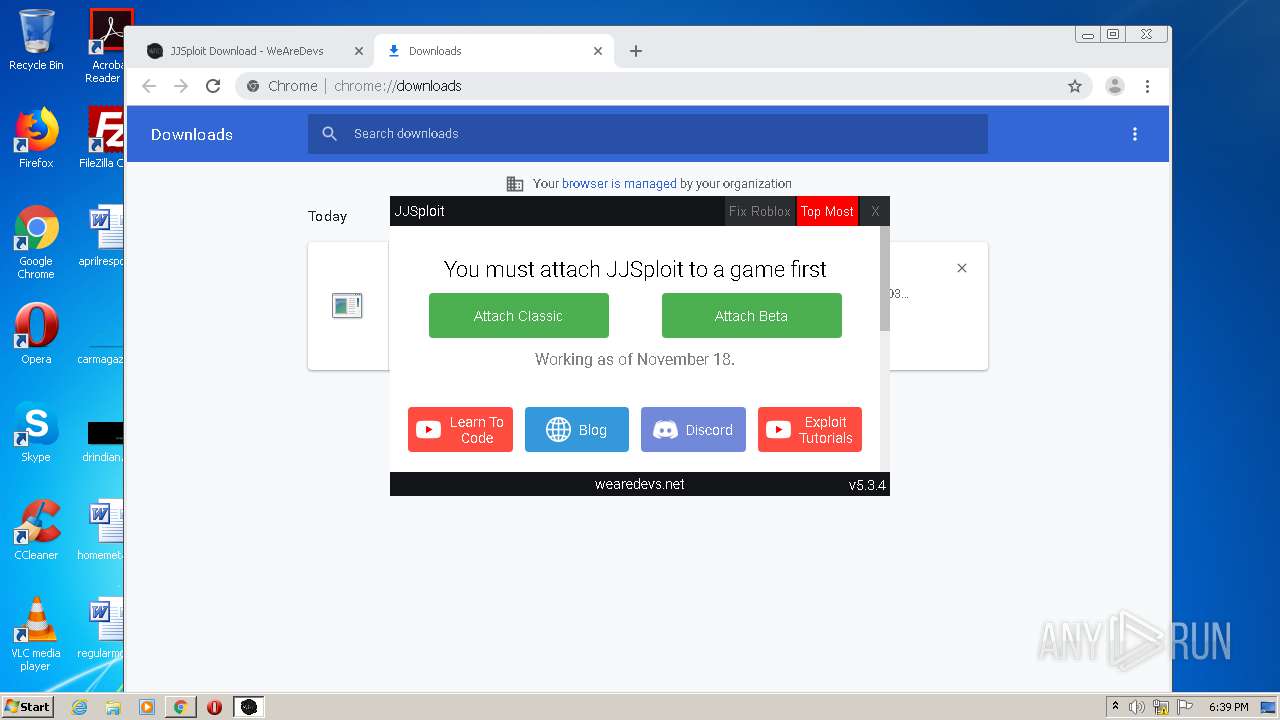
MALICIOUS
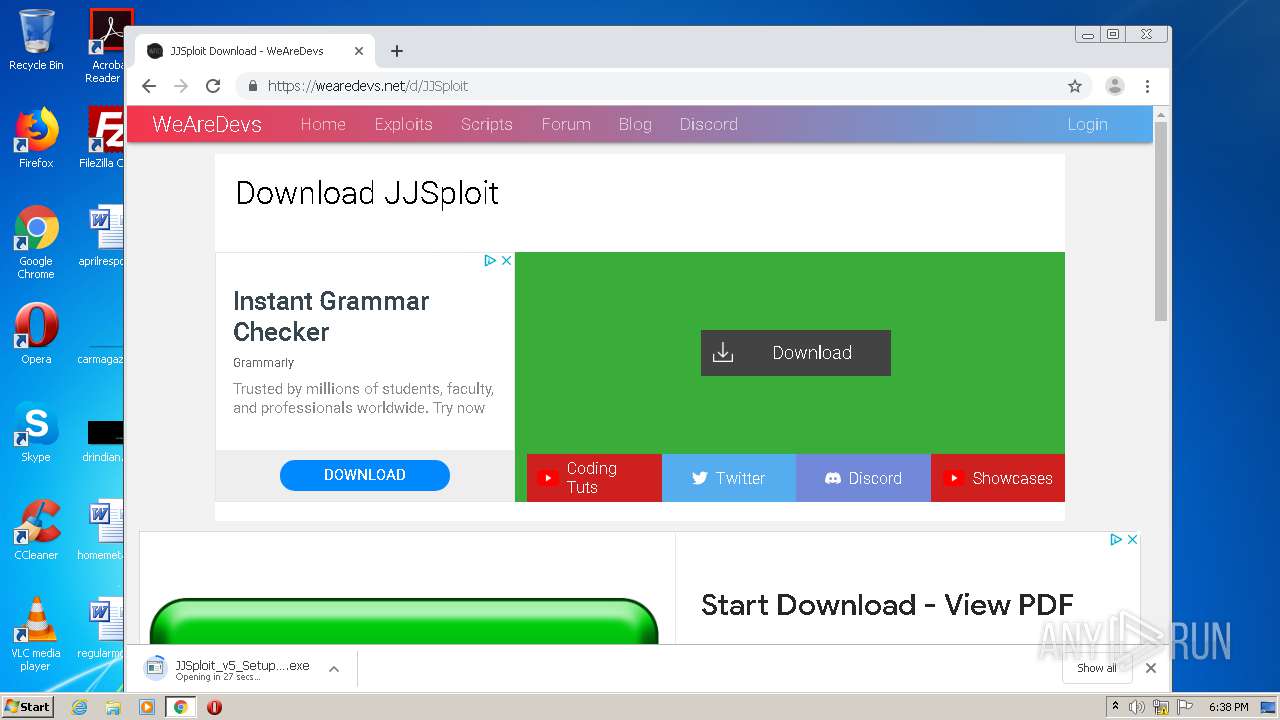
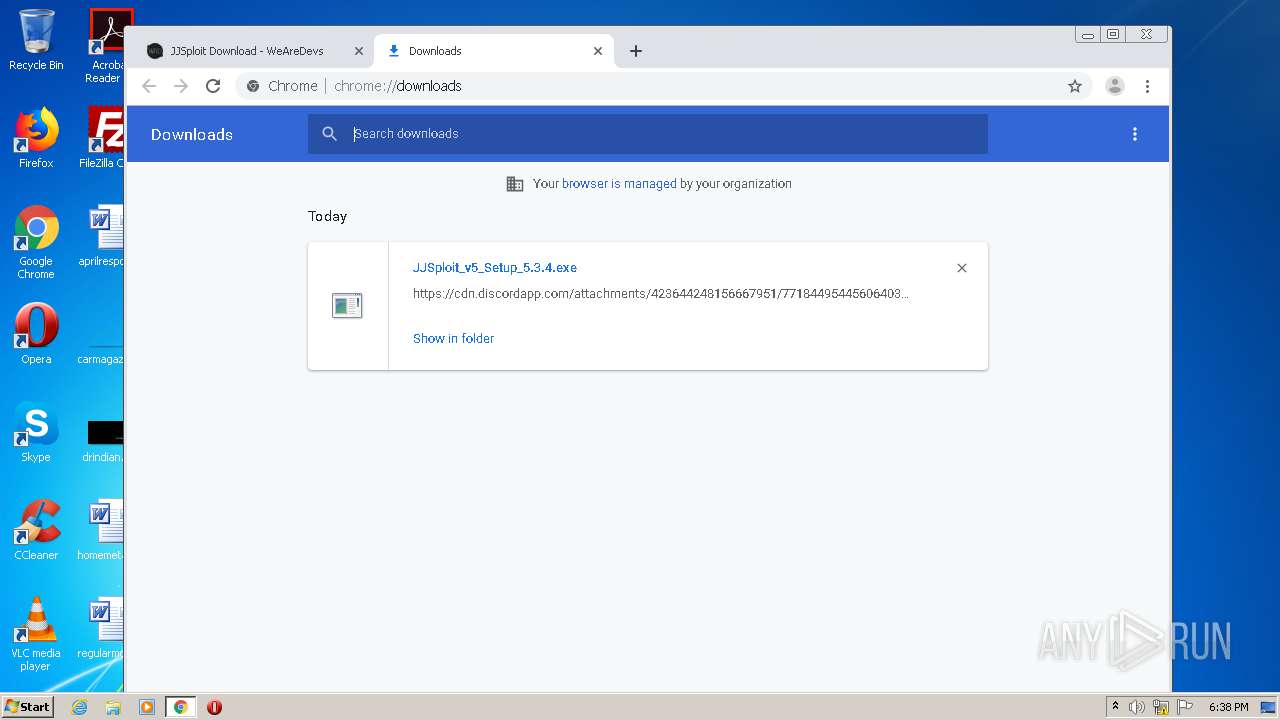
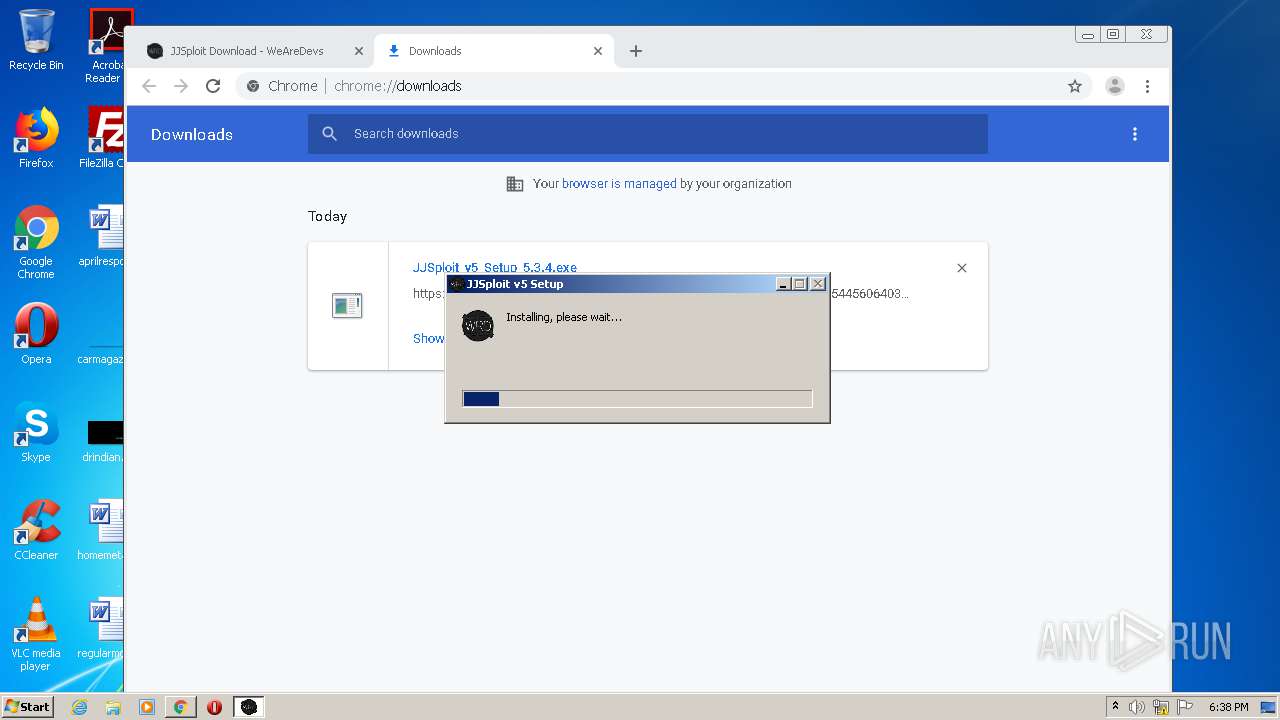
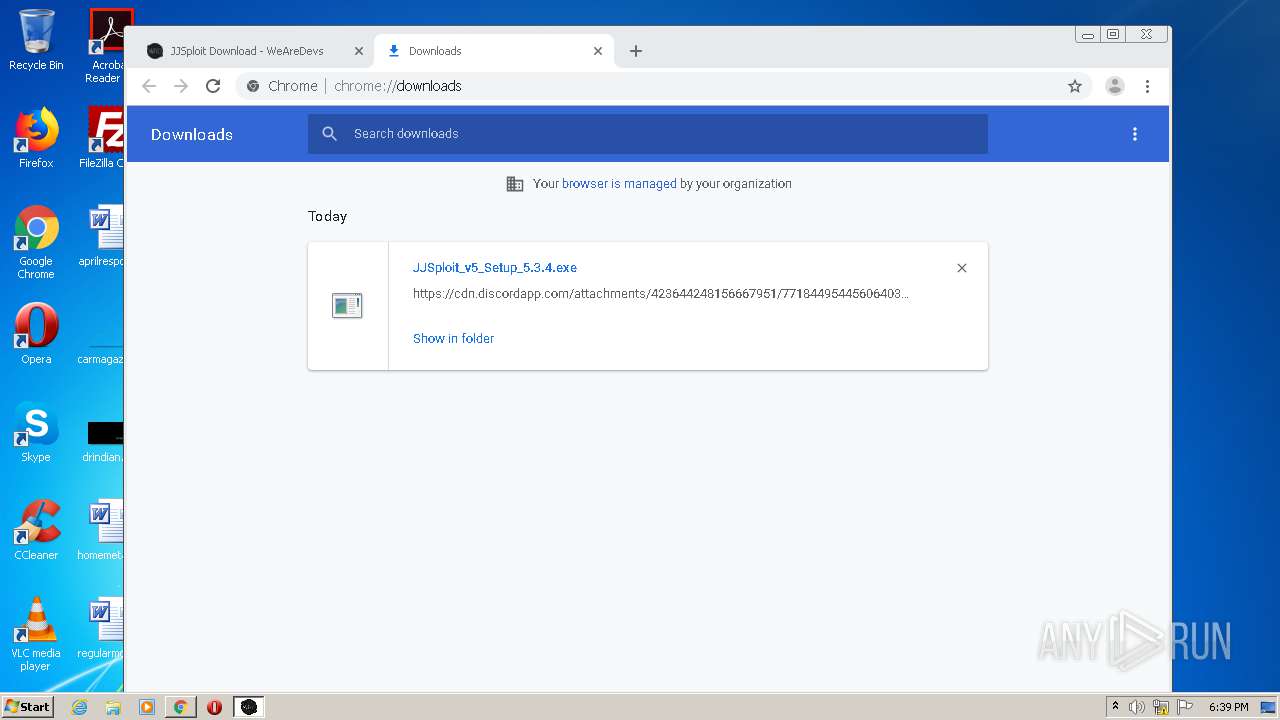
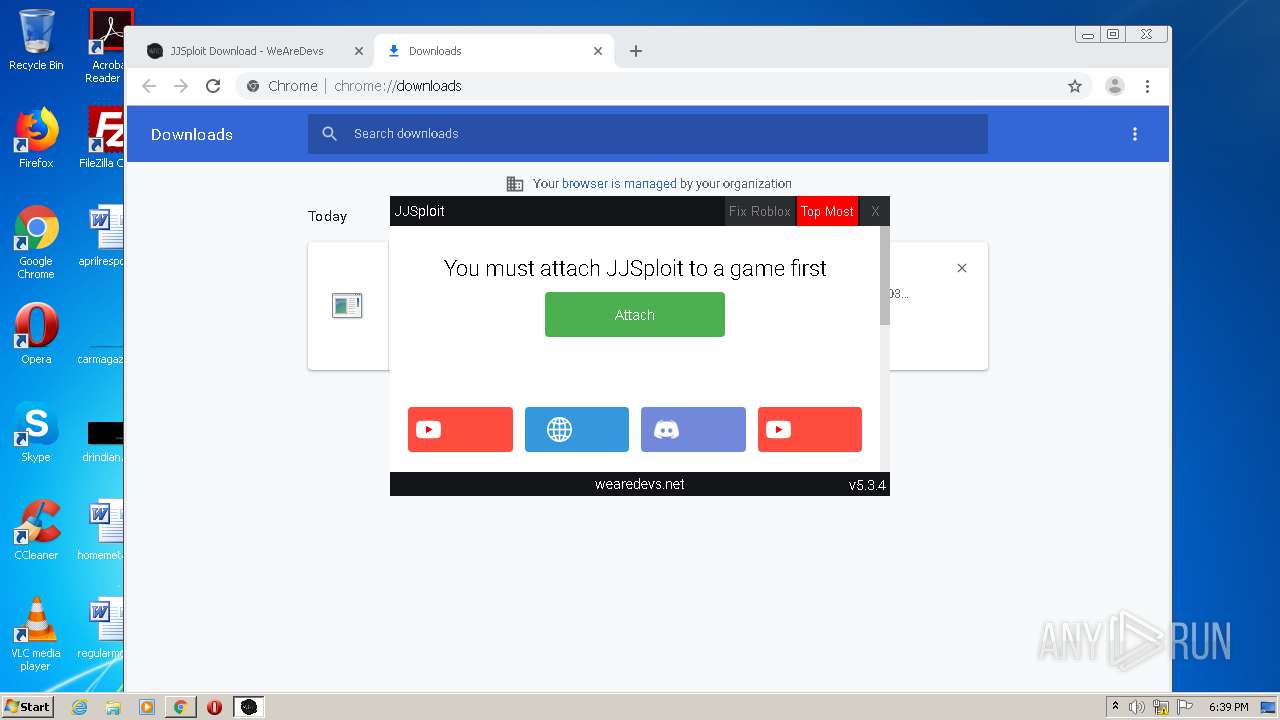
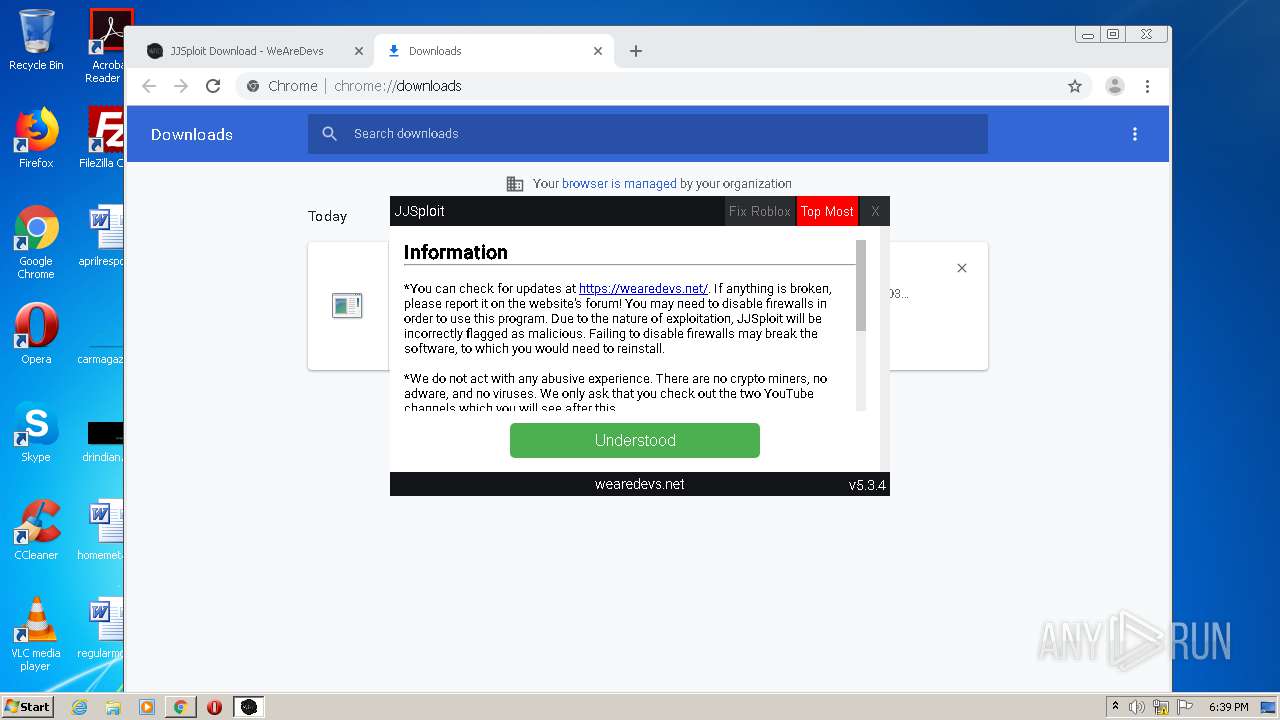
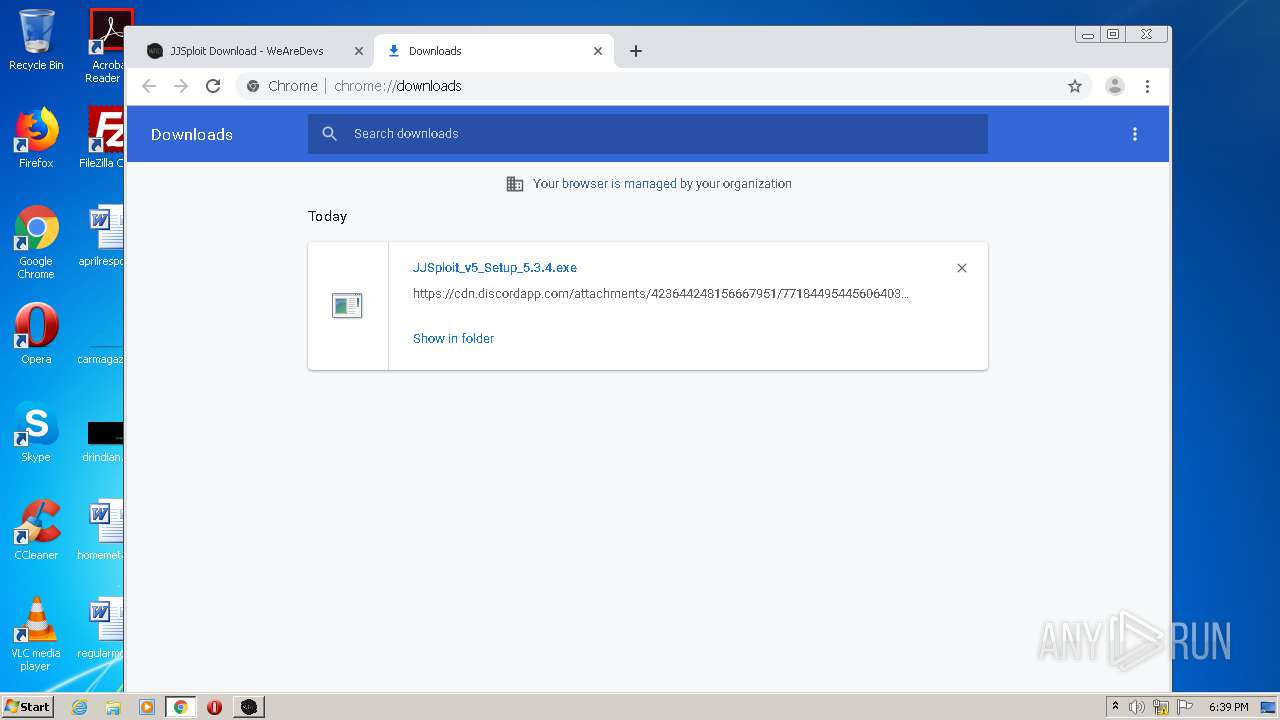
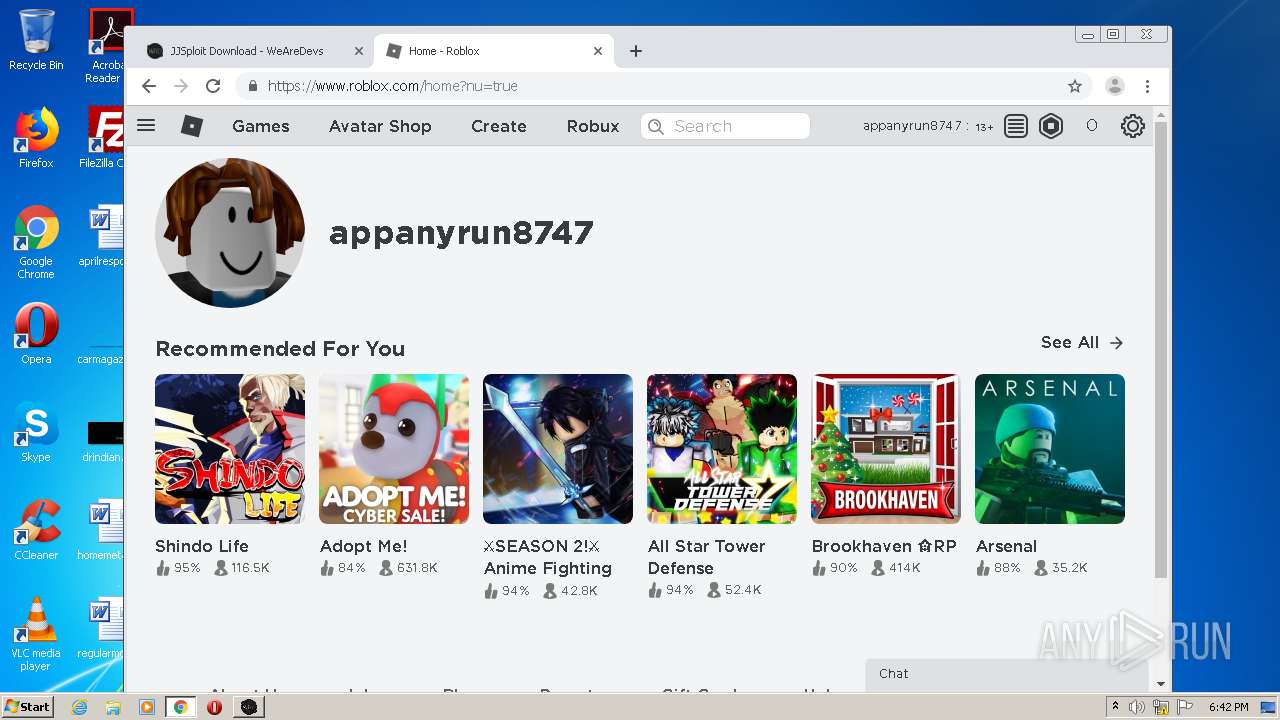
Application was dropped or rewritten from another process
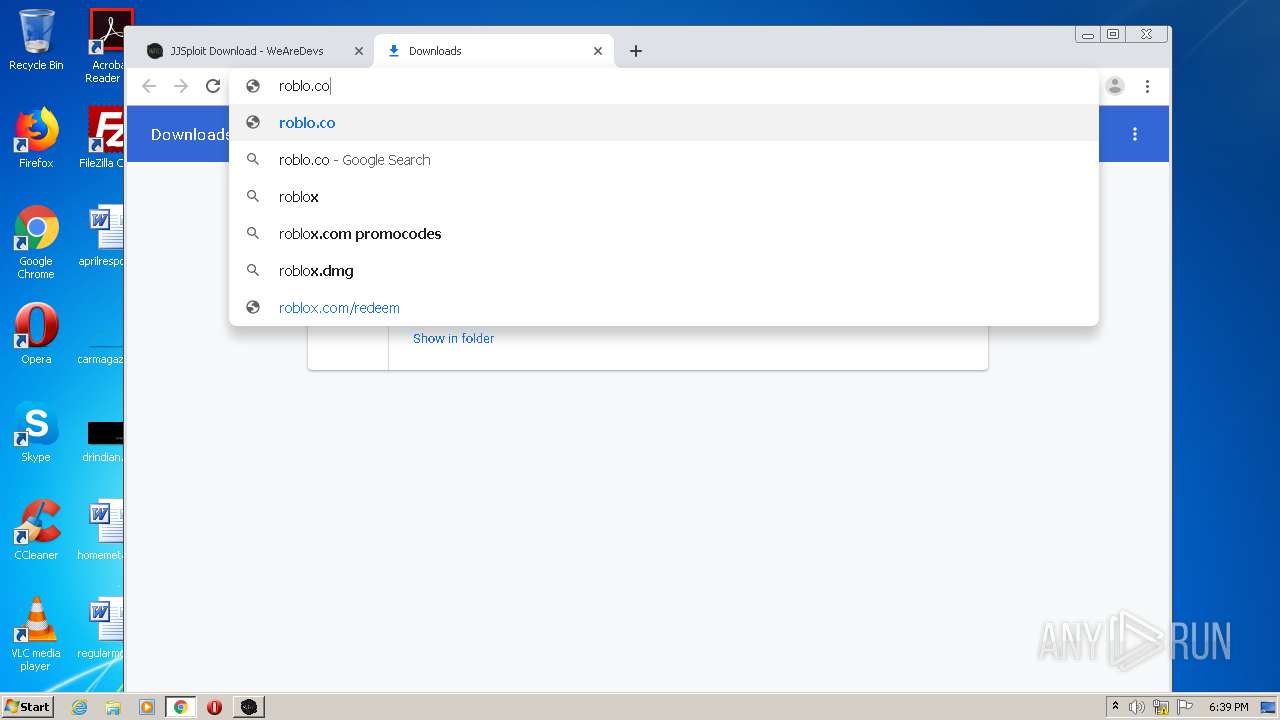
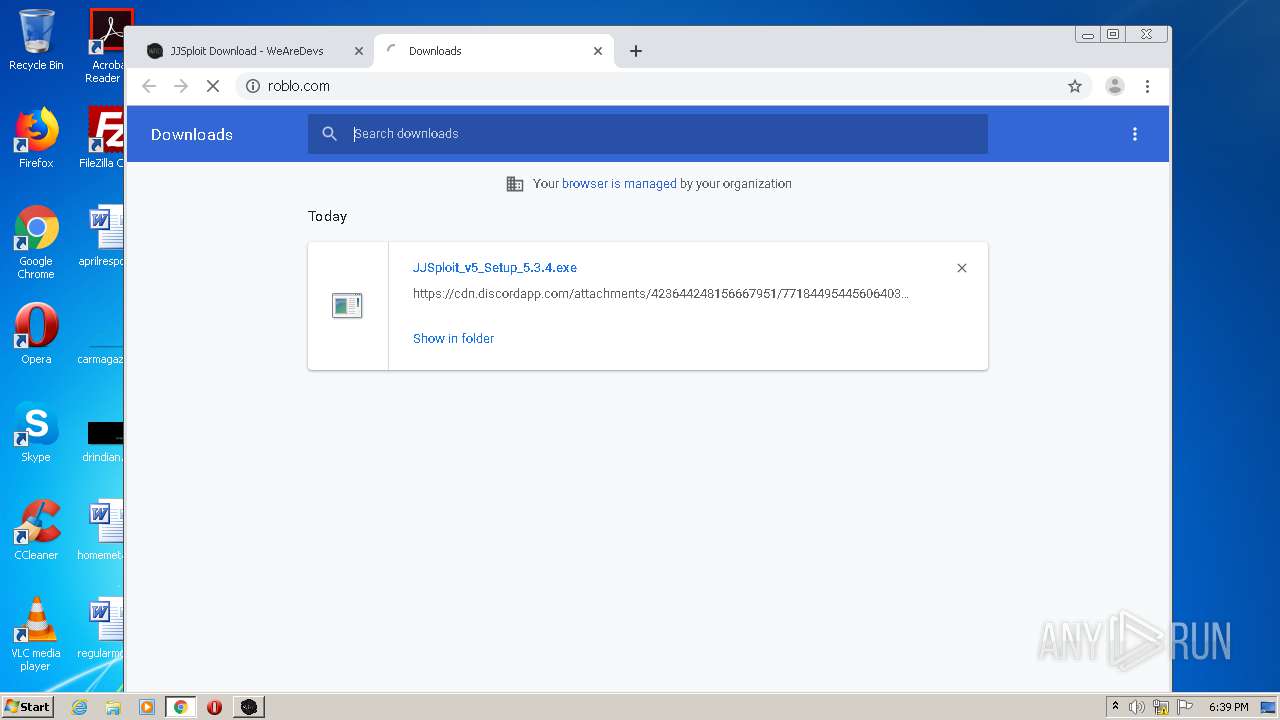
- JJSploit_v5_Setup_5.3.4.exe (PID: 3812)
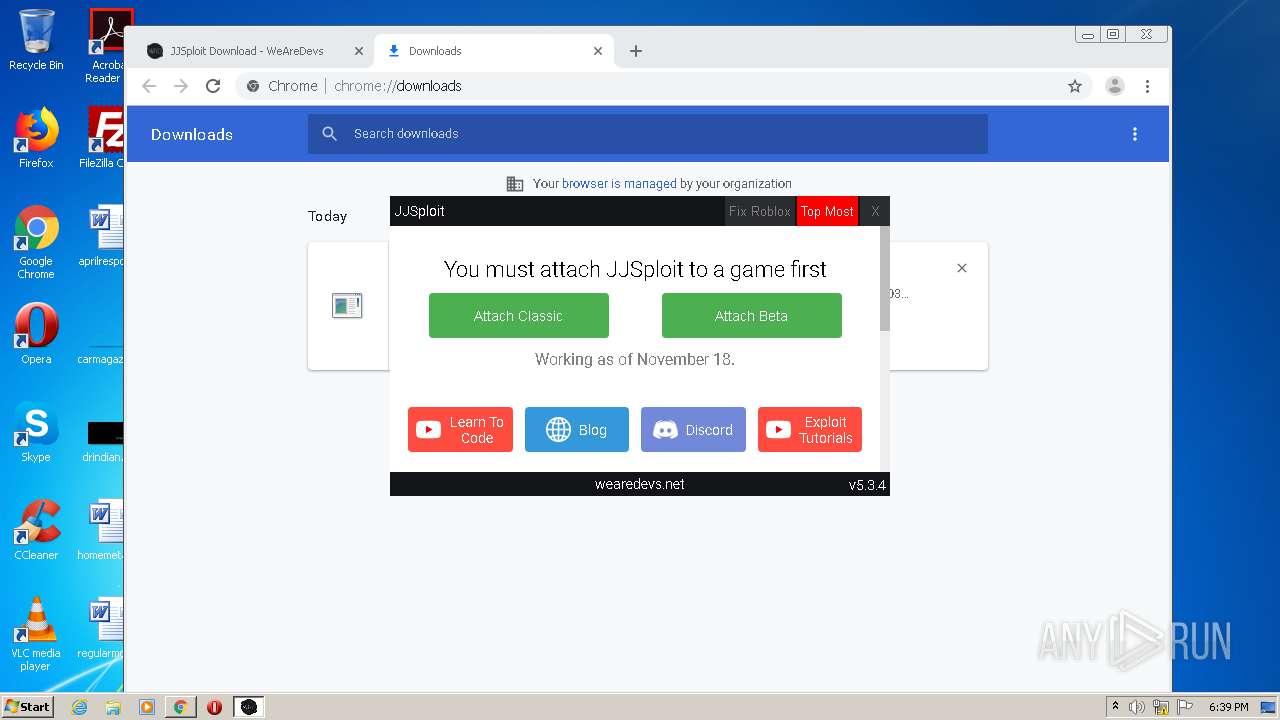
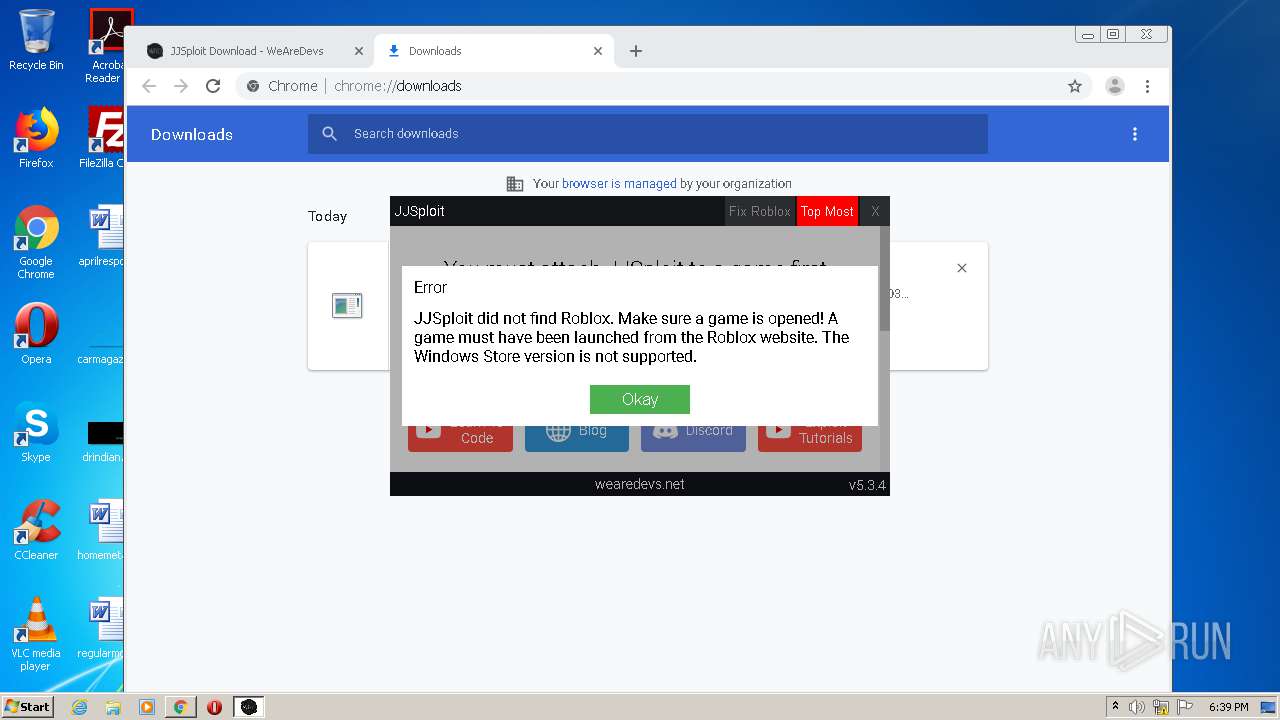
Loads dropped or rewritten executable
- JJSploit v5.exe (PID: 2360)
- JJSploit_v5_Setup_5.3.4.exe (PID: 3812)
- JJSploit v5.exe (PID: 3528)
- JJSploit v5.exe (PID: 3428)
SUSPICIOUS
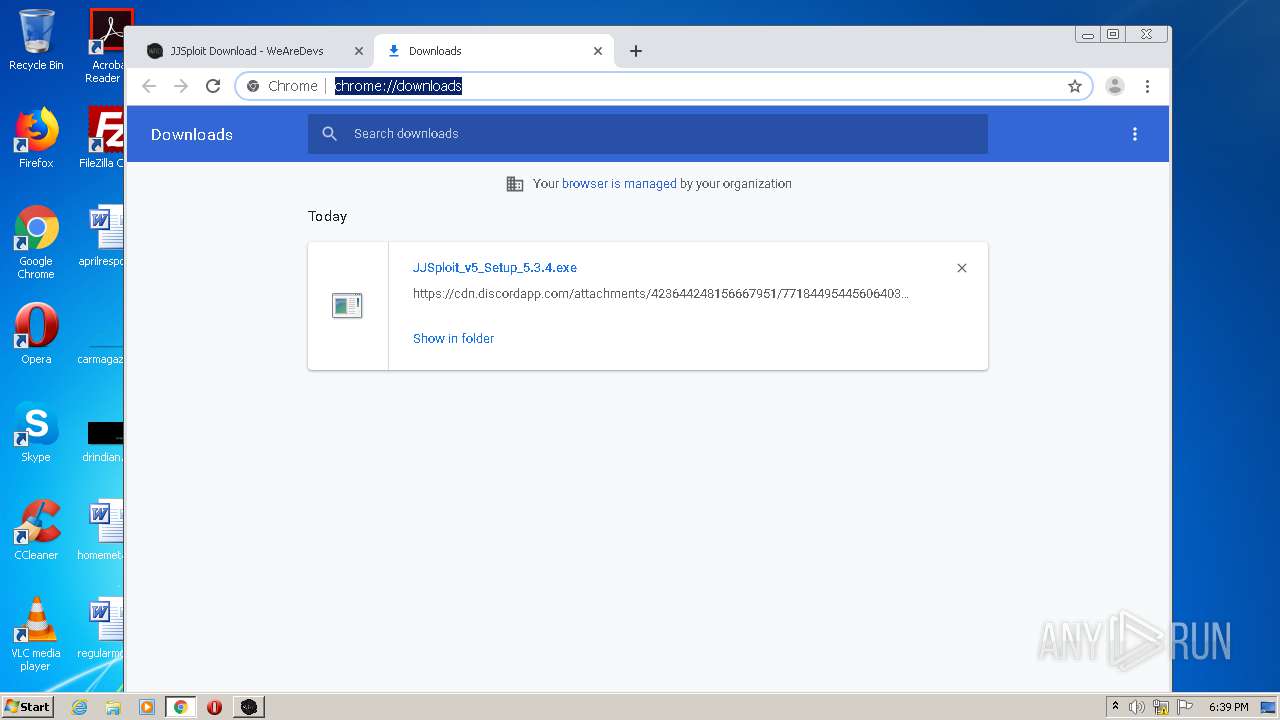
Executable content was dropped or overwritten
- JJSploit_v5_Setup_5.3.4.exe (PID: 3812)
- chrome.exe (PID: 2160)
- JJSploit v5.exe (PID: 2360)
Creates files in the user directory
- JJSploit_v5_Setup_5.3.4.exe (PID: 3812)
- JJSploit v5.exe (PID: 2360)
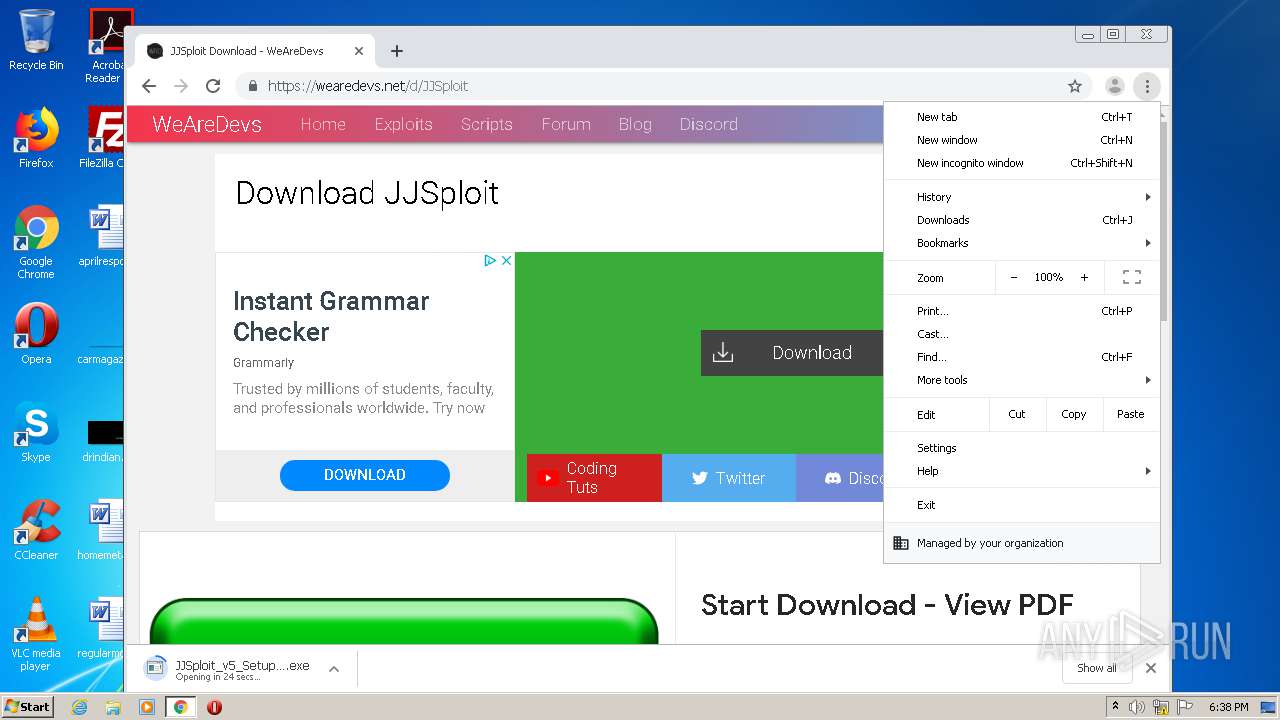
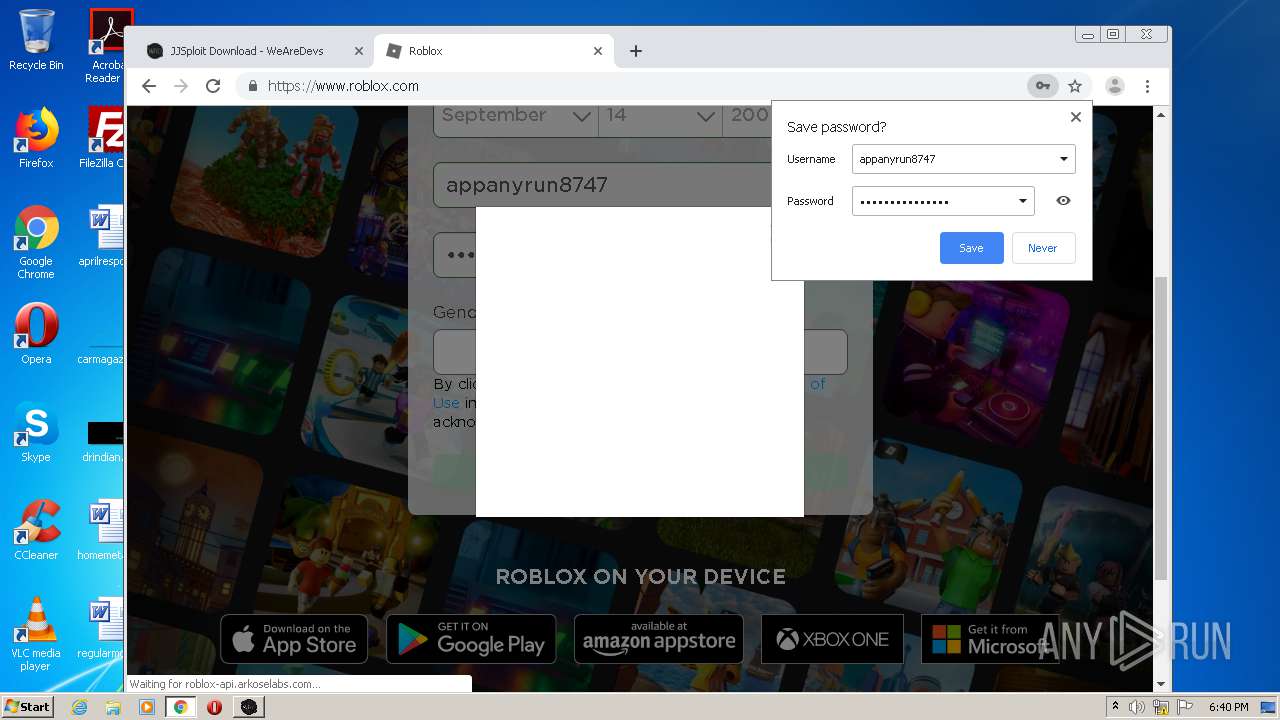
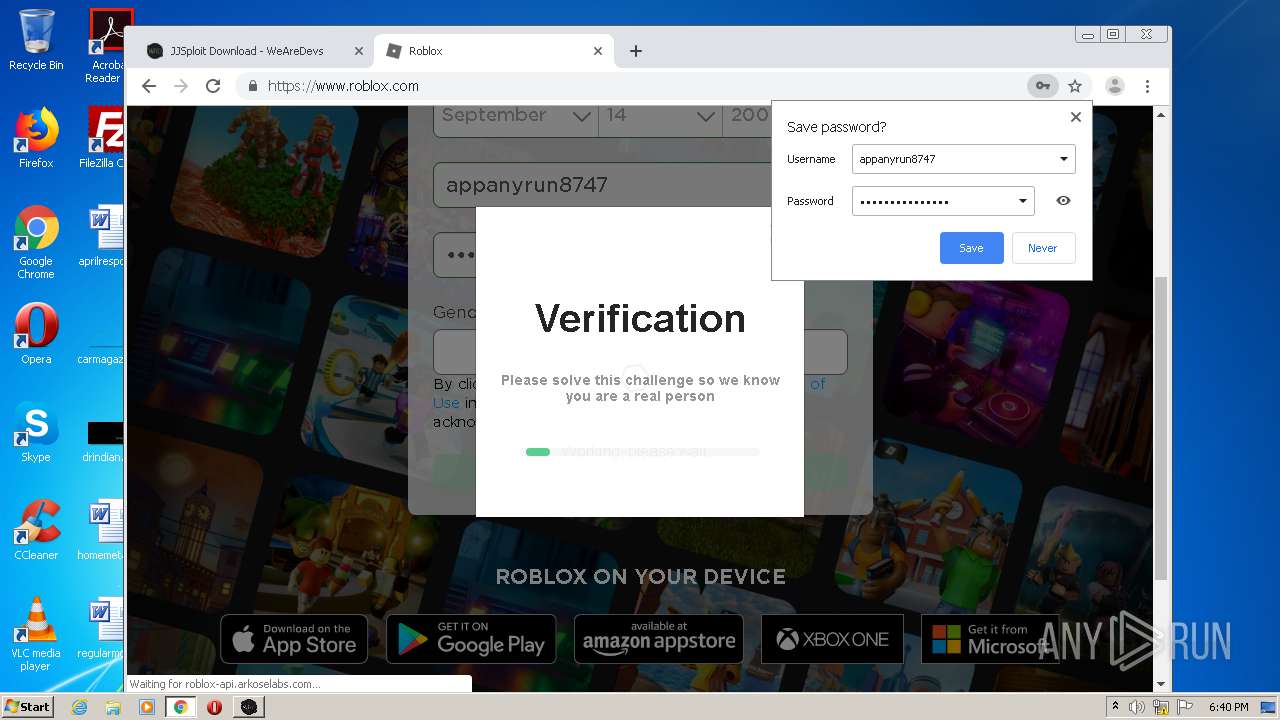
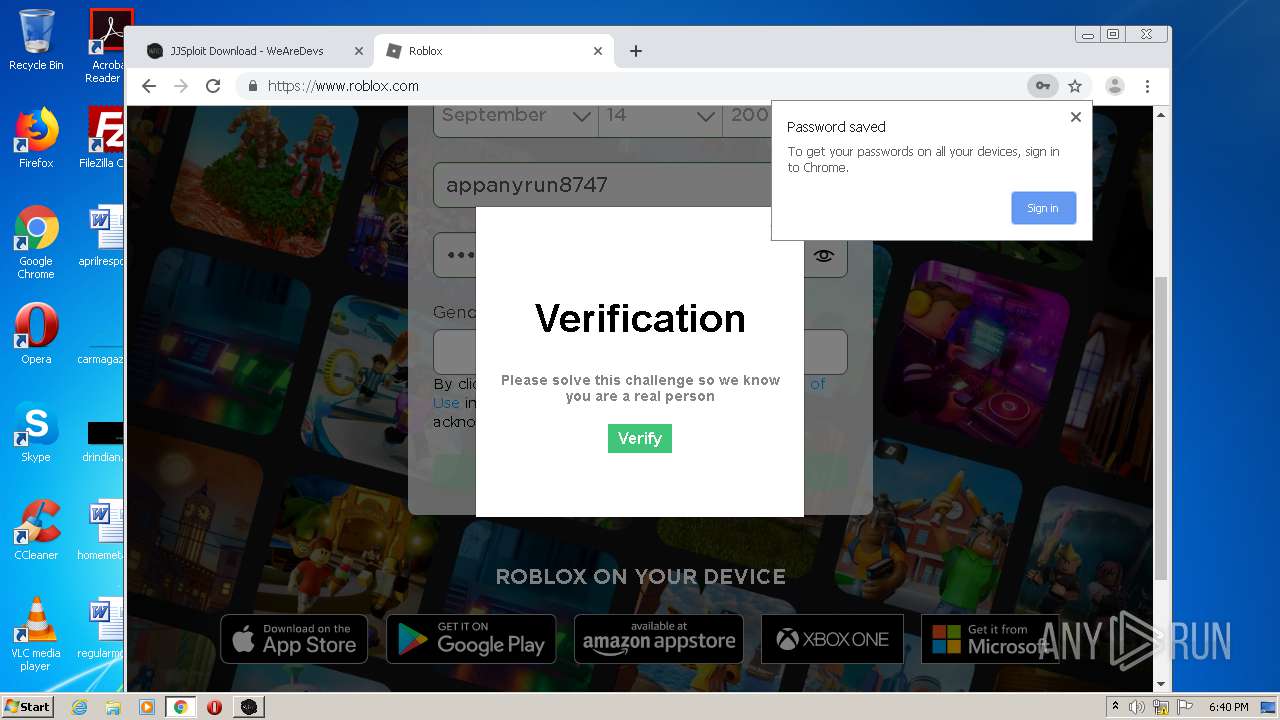
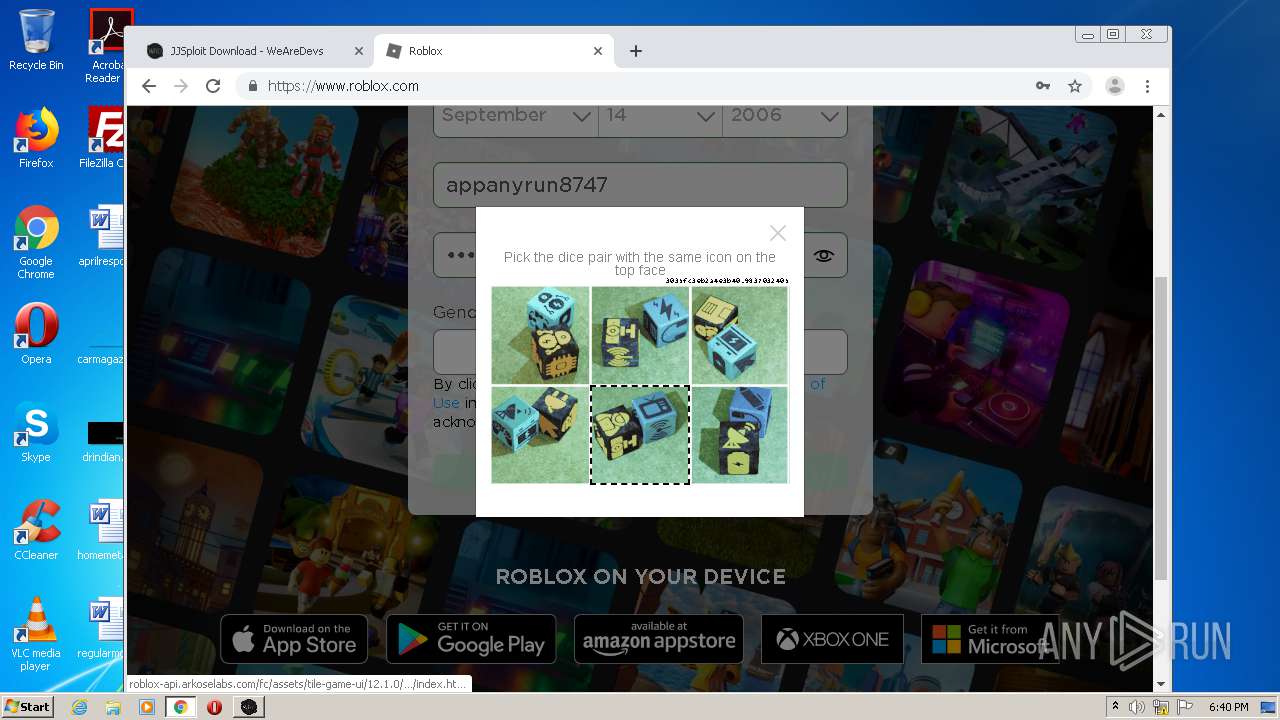
Modifies files in Chrome extension folder
- chrome.exe (PID: 2160)
Drops a file that was compiled in debug mode
- JJSploit_v5_Setup_5.3.4.exe (PID: 3812)
- JJSploit v5.exe (PID: 2360)
Drops a file with too old compile date
- JJSploit_v5_Setup_5.3.4.exe (PID: 3812)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.3.4.exe (PID: 3812)
Application launched itself
- JJSploit v5.exe (PID: 2360)
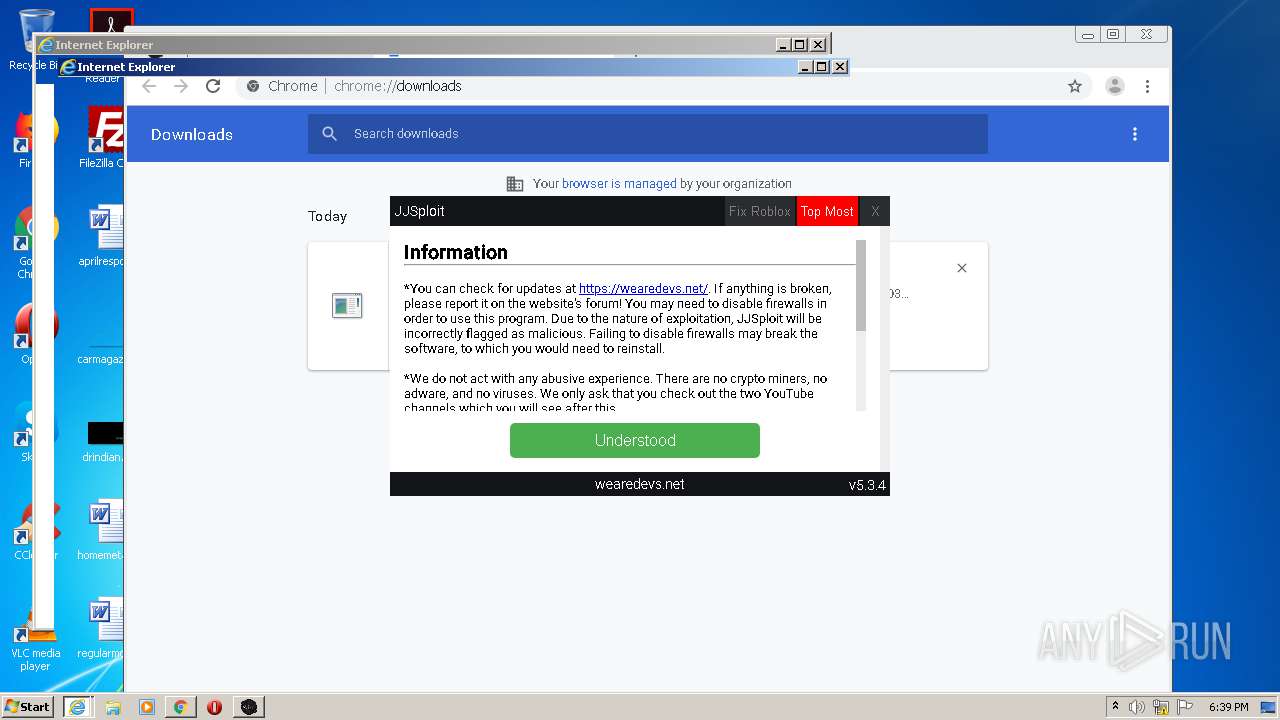
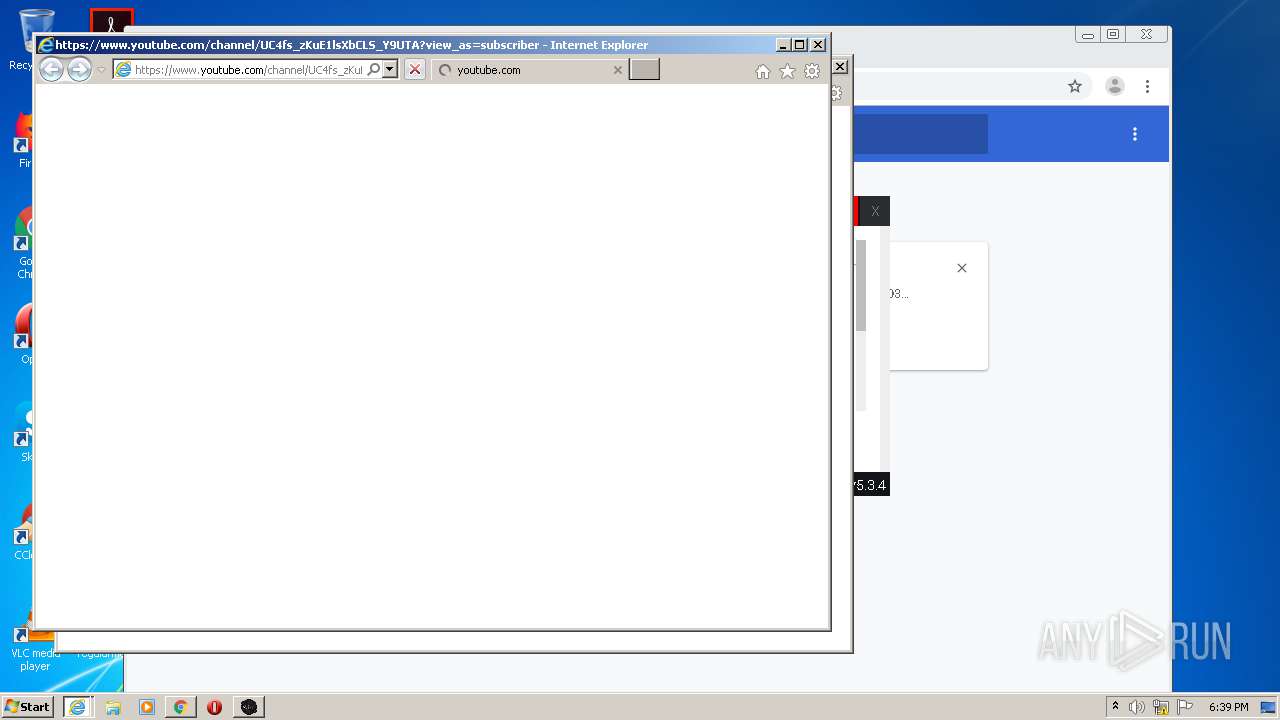
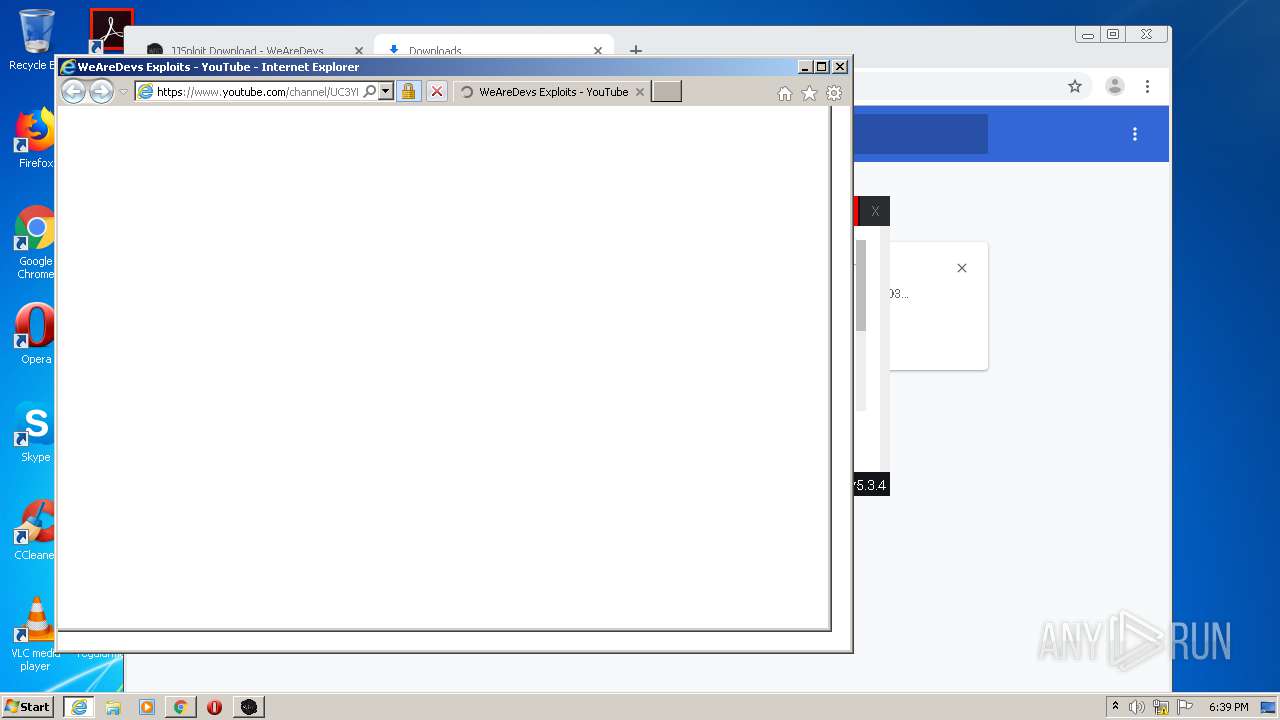
Starts Internet Explorer
- JJSploit v5.exe (PID: 2360)
Drops a file with a compile date too recent
- JJSploit v5.exe (PID: 2360)
INFO
Application launched itself
- chrome.exe (PID: 2160)
- iexplore.exe (PID: 2908)
- iexplore.exe (PID: 3524)
Reads the hosts file
- chrome.exe (PID: 2160)
- chrome.exe (PID: 2324)
- JJSploit v5.exe (PID: 2360)
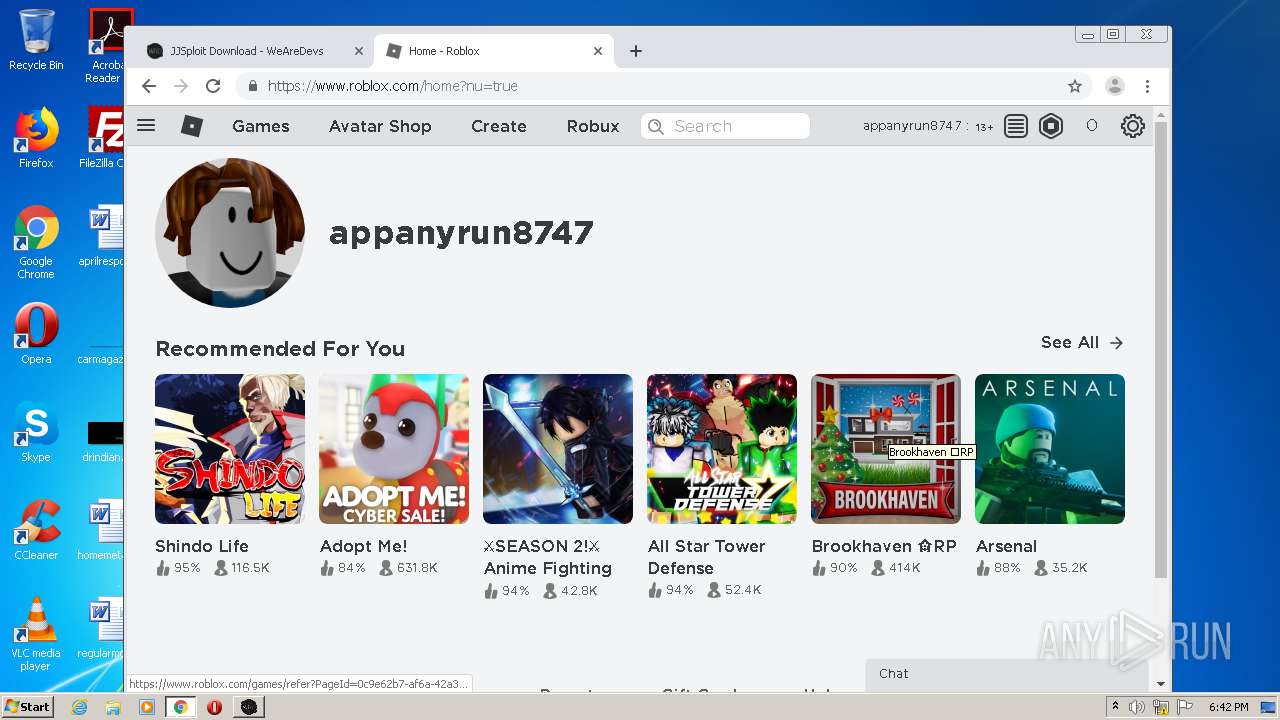
Manual execution by user
- chrome.exe (PID: 2160)
- JJSploit v5.exe (PID: 2360)
Reads settings of System Certificates
- chrome.exe (PID: 2324)
- iexplore.exe (PID: 976)
- iexplore.exe (PID: 3076)
Changes internet zones settings
- iexplore.exe (PID: 2908)
- iexplore.exe (PID: 3524)
Reads internet explorer settings
- iexplore.exe (PID: 3076)
- iexplore.exe (PID: 976)
Creates files in the user directory
- iexplore.exe (PID: 976)
- iexplore.exe (PID: 3076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| viewport: | width=device-width |
|---|---|
| Title: | MalwareDatabase/ChilledWindows.zip at master · Endermanch/MalwareDatabase · GitHub |
| Description: | This repository is one of a few malware collections on the GitHub. - Endermanch/MalwareDatabase |
| appleItunesApp: | app-id=1477376905 |
| twitterImageSrc: | https://avatars1.githubusercontent.com/u/44542704?s=400&v=4 |
| twitterSite: | @github |
| twitterCard: | summary |
| twitterTitle: | Endermanch/MalwareDatabase |
| twitterDescription: | This repository is one of a few malware collections on the GitHub. - Endermanch/MalwareDatabase |
| requestId: | 5A89:8DD2:8BEE0A2:B677E21:5FC3EA69 |
| htmlSafeNonce: | 89fd6e6a0cfefd33601dcb9baf8a93dbe1369ce53220faccb25d2551d0218d41 |
| visitorPayload: | eyJyZWZlcnJlciI6IiIsInJlcXVlc3RfaWQiOiI1QTg5OjhERDI6OEJFRTBBMjpCNjc3RTIxOjVGQzNFQTY5IiwidmlzaXRvcl9pZCI6IjE3MDAzMjgyNzc5MzI3NTgyNTciLCJyZWdpb25fZWRnZSI6ImZyYSIsInJlZ2lvbl9yZW5kZXIiOiJmcmEifQ== |
| visitorHmac: | 11864a12cdd173b9166c3fe301bc93f13b6751a22def7ec6408cdf6a0a834b18 |
| cookieConsentRequired: | |
| hovercardSubjectTag: | repository:155052331 |
| githubKeyboardShortcuts: | repository,source-code |
| googleSiteVerification: | GXs5KoUUkNCoaAZn7wPN-t01Pywp9M3sEjnt_3_ZWPc |
| octolyticsHost: | collector.githubapp.com |
| octolyticsAppId: | github |
| octolyticsEventUrl: | https://collector.githubapp.com/github-external/browser_event |
| analyticsLocation: | /<user-name>/<repo-name>/blob/show |
| optimizelyDatafile: | {"version": "4", "rollouts": [], "typedAudiences": [], "anonymizeIP": true, "projectId": "16737760170", "variables": [], "featureFlags": [], "experiments": [{"status": "Running", "audienceIds": [], "variations": [{"variables": [], "id": "18630402174", "key": "launchpad"}, {"variables": [], "id": "18866331456", "key": "control"}], "id": "18651193356", "key": "_features_redesign_rollout", "layerId": "18645992876", "trafficAllocation": [{"entityId": "18630402174", "endOfRange": 500}, {"entityId": "18866331456", "endOfRange": 1000}, {"entityId": "18630402174", "endOfRange": 5000}, {"entityId": "18630402174", "endOfRange": 5500}, {"entityId": "18866331456", "endOfRange": 10000}], "forcedVariations": {"143327983.1601483920": "launchpad", "1955030087.1562868941": "launchpad", "1983887325.1550021416": "launchpad", "1947530619.1600461583": "launchpad"}}, {"status": "Running", "audienceIds": [], "variations": [{"variables": [], "id": "19136700362", "key": "show_plans"}, {"variables": [], "id": "19157700511", "key": "control"}], "id": "19062314978", "key": "account_billing_plans", "layerId": "19068014945", "trafficAllocation": [{"entityId": "19136700362", "endOfRange": 5000}, {"entityId": "19157700511", "endOfRange": 10000}], "forcedVariations": {"1238720267648ea2c88a74b410aa3c5c": "show_plans", "c4abf59d1620c671458b2a74df2a2410": "control"}}], "audiences": [{"conditions": "[\"or\", {\"match\": \"exact\", \"name\": \"$opt_dummy_attribute\", \"type\": \"custom_attribute\", \"value\": \"$opt_dummy_value\"}]", "id": "$opt_dummy_audience", "name": "Optimizely-Generated Audience for Backwards Compatibility"}], "groups": [], "attributes": [{"id": "16822470375", "key": "user_id"}, {"id": "17143601254", "key": "spammy"}, {"id": "18175660309", "key": "organization_plan"}, {"id": "18813001570", "key": "is_logged_in"}, {"id": "19073851829", "key": "geo"}], "botFiltering": false, "accountId": "16737760170", "events": [{"experimentIds": [], "id": "17911811441", "key": "hydro_click.dashboard.teacher_toolbox_cta"}, {"experimentIds": [], "id": "18124116703", "key": "submit.organizations.complete_sign_up"}, {"experimentIds": [], "id": "18145892387", "key": "no_metric.tracked_outside_of_optimizely"}, {"experimentIds": [], "id": "18178755568", "key": "click.org_onboarding_checklist.add_repo"}, {"experimentIds": [], "id": "18180553241", "key": "submit.repository_imports.create"}, {"experimentIds": [], "id": "18186103728", "key": "click.help.learn_more_about_repository_creation"}, {"experimentIds": [], "id": "18188530140", "key": "test_event.do_not_use_in_production"}, {"experimentIds": [], "id": "18191963644", "key": "click.empty_org_repo_cta.transfer_repository"}, {"experimentIds": [], "id": "18195612788", "key": "click.empty_org_repo_cta.import_repository"}, {"experimentIds": [], "id": "18210945499", "key": "click.org_onboarding_checklist.invite_members"}, {"experimentIds": [], "id": "18211063248", "key": "click.empty_org_repo_cta.create_repository"}, {"experimentIds": [], "id": "18215721889", "key": "click.org_onboarding_checklist.update_profile"}, {"experimentIds": [], "id": "18224360785", "key": "click.org_onboarding_checklist.dismiss"}, {"experimentIds": [], "id": "18234832286", "key": "submit.organization_activation.complete"}, {"experimentIds": [], "id": "18252392383", "key": "submit.org_repository.create"}, {"experimentIds": [], "id": "18257551537", "key": "submit.org_member_invitation.create"}, {"experimentIds": [], "id": "18259522260", "key": "submit.organization_profile.update"}, {"experimentIds": [], "id": "18564603625", "key": "view.classroom_select_organization"}, {"experimentIds": [], "id": "18568612016", "key": "click.classroom_sign_in_click"}, {"experimentIds": [], "id": "18572592540", "key": "view.classroom_name"}, {"experimentIds": [], "id": "18574203855", "key": "click.classroom_create_organization"}, {"experimentIds": [], "id": "18582053415", "key": "click.classroom_select_organization"}, {"experimentIds": [], "id": "18589463420", "key": "click.classroom_create_classroom"}, {"experimentIds": [], "id": "18591323364", "key": "click.classroom_create_first_classroom"}, {"experimentIds": [], "id": "18591652321", "key": "click.classroom_grant_access"}, {"experimentIds": [], "id": "18607131425", "key": "view.classroom_creation"}, {"experimentIds": [], "id": "18831680583", "key": "upgrade_account_plan"}, {"experimentIds": [], "id": "19064064515", "key": "click.signup"}, {"experimentIds": [], "id": "19075373687", "key": "click.view_account_billing_page"}, {"experimentIds": [], "id": "19077355841", "key": "click.dismiss_signup_prompt"}, {"experimentIds": ["19062314978"], "id": "19079713938", "key": "click.contact_sales"}, {"experimentIds": ["19062314978"], "id": "19120963070", "key": "click.compare_account_plans"}, {"experimentIds": ["19062314978"], "id": "19151690317", "key": "click.upgrade_account_cta"}], "revision": "338"} |
Total processes
94
Monitored processes
57
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7691634404015474861 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1609985010492564849 --mojo-platform-channel-handle=2600 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3599319526938822840 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2908 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15410779601903186730 --mojo-platform-channel-handle=3732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5858381714555834262 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2476 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18007325464600430582 --mojo-platform-channel-handle=4272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12713620424431606522 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10931760914215664899 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,234909439871535566,8453634264629953469,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14587948281221493930 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 557
Read events
2 297
Write events
253
Delete events
7
Modification events
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_0 |
Value: 38000000730100000402000000000000D4D0C800000000000000000000000000380105000000000039000000B40200000000000001000000 | |||
| (PID) Process: | (2380) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_1 |
Value: 38000000730100000500000000000000D4D0C8000000000000000000000000004E01040000000000160000002A0000000000000002000000 | |||
Executable files
21
Suspicious files
291
Text files
276
Unknown types
116
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3EA84-870.pma | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5626f150-41e4-4b6b-9c8e-97a66404de74.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFff68c.TMP | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFff7a5.TMP | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFff861.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
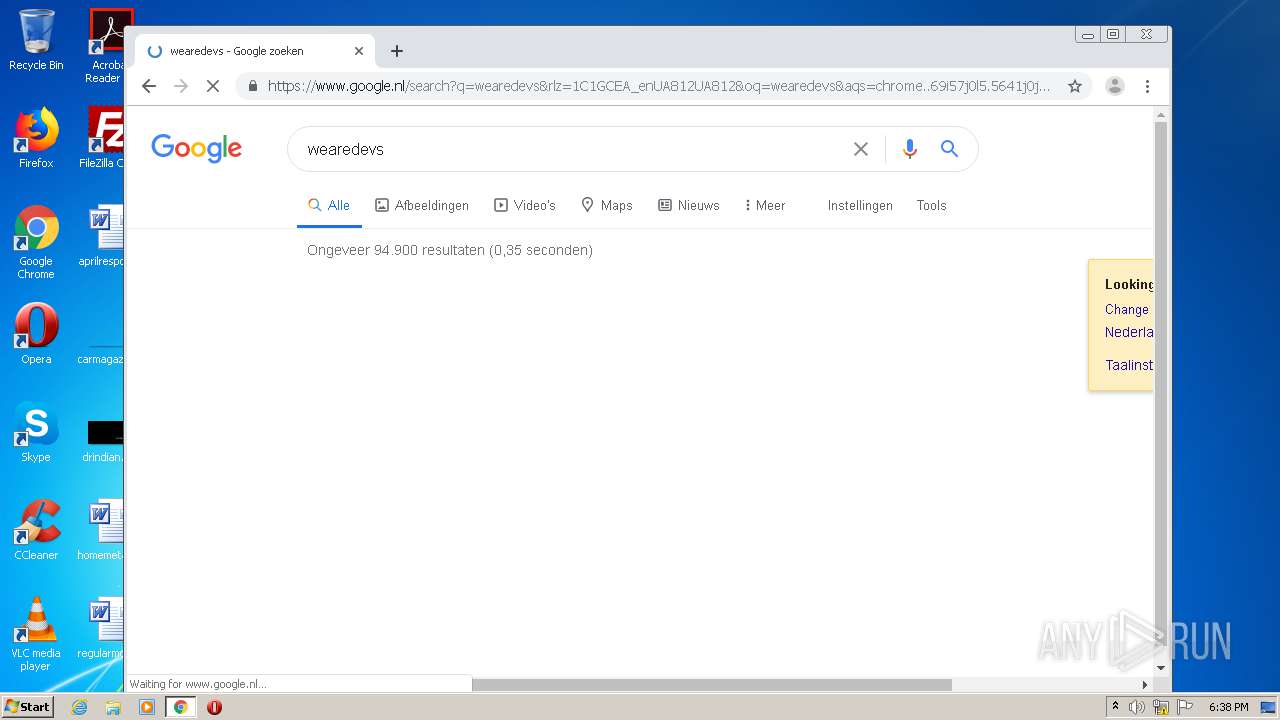
HTTP(S) requests
36
TCP/UDP connections
199
DNS requests
129
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3076 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | — | — | whitelisted |
976 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | — | whitelisted |
3076 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | — | — | whitelisted |
976 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDgM%2F2Oalb9SggAAAAAYth0 | US | — | — | whitelisted |
976 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | — | — | whitelisted |
3076 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | — | — | whitelisted |
976 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD76E8xQFZstgIAAAAAgFWS | US | — | — | whitelisted |
976 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDa2MTpyZrzlQgAAAAAYth4 | US | — | — | whitelisted |
976 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDDCp%2BiAKlAlQIAAAAAgFRY | US | — | — | whitelisted |
3076 | iexplore.exe | GET | — | 172.217.16.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDgM%2F2Oalb9SggAAAAAYth0 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2324 | chrome.exe | 172.217.12.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 142.250.64.77:443 | accounts.google.com | Google Inc. | US | unknown |
2324 | chrome.exe | 142.250.74.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2324 | chrome.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 172.217.23.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2324 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 172.217.6.206:443 | apis.google.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
2324 | chrome.exe | 172.217.18.163:443 | www.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |