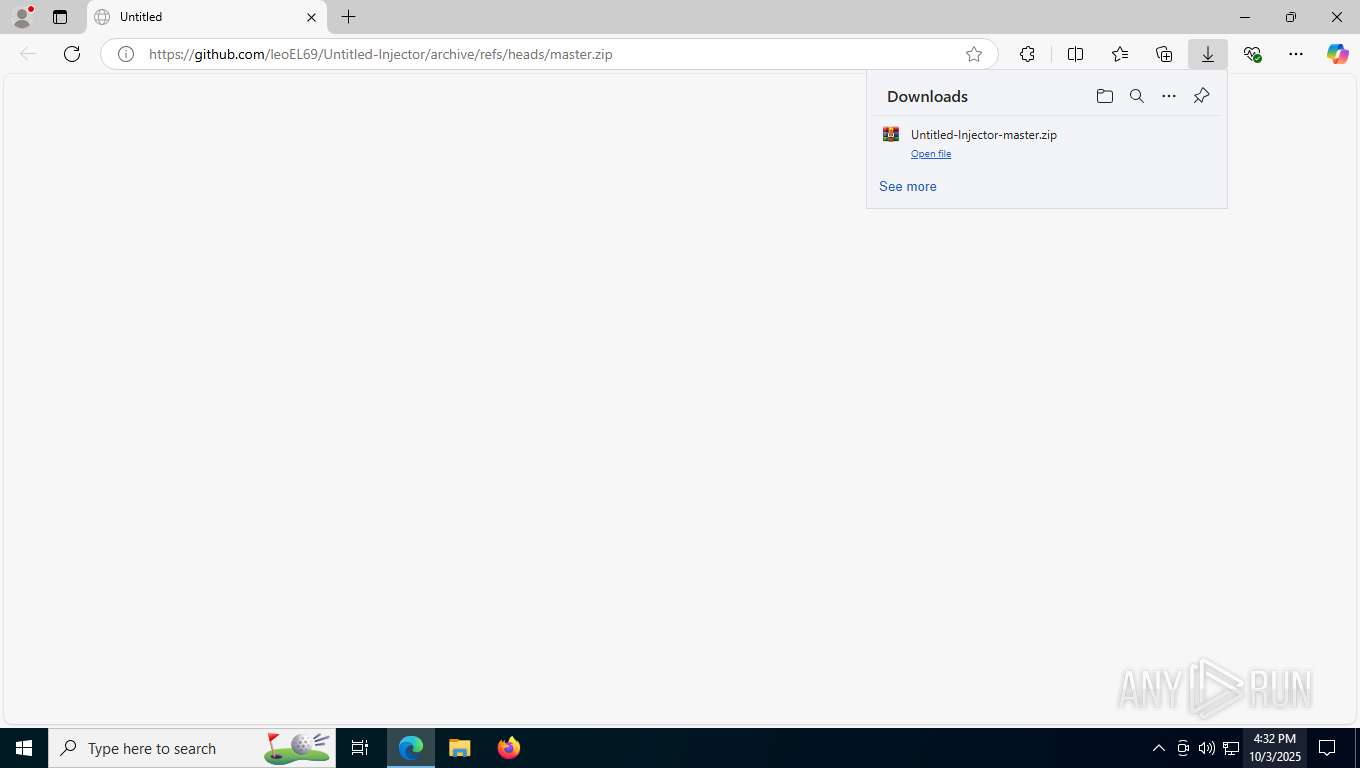
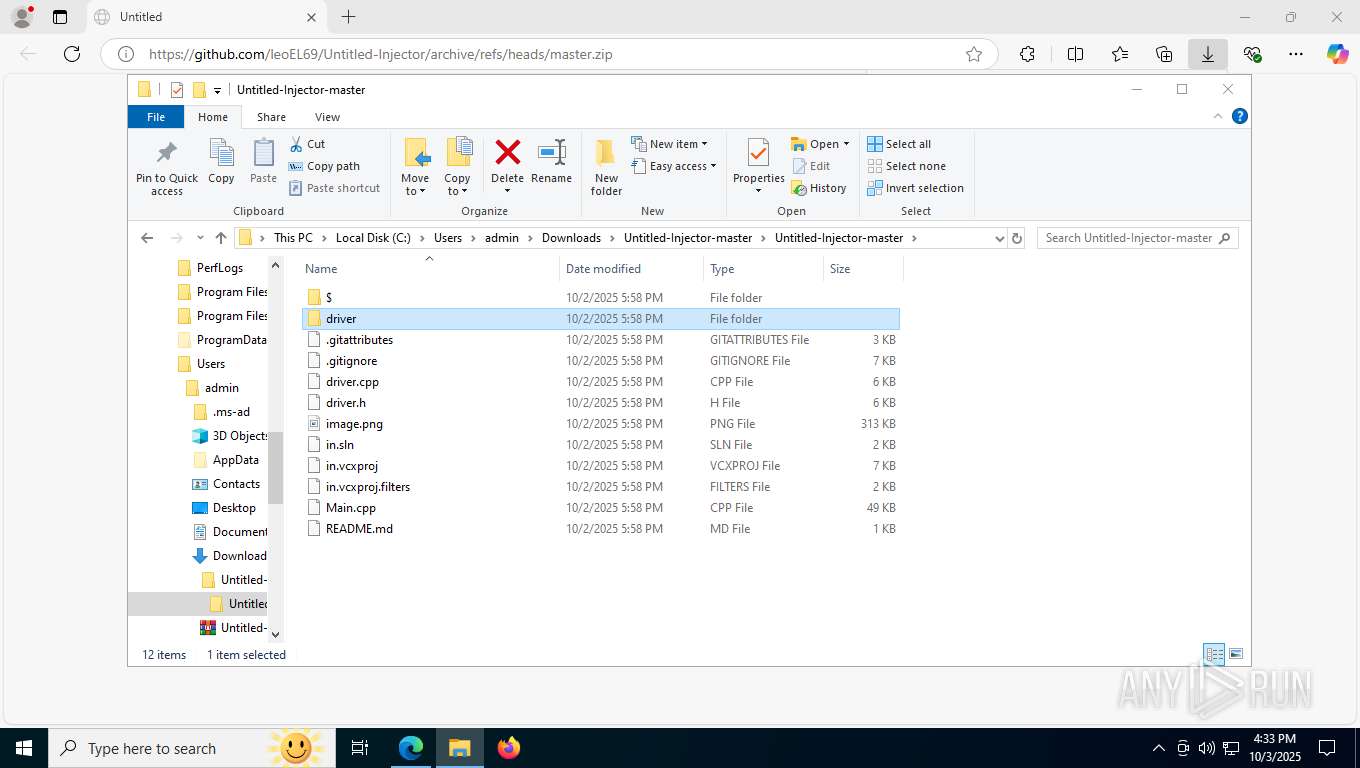
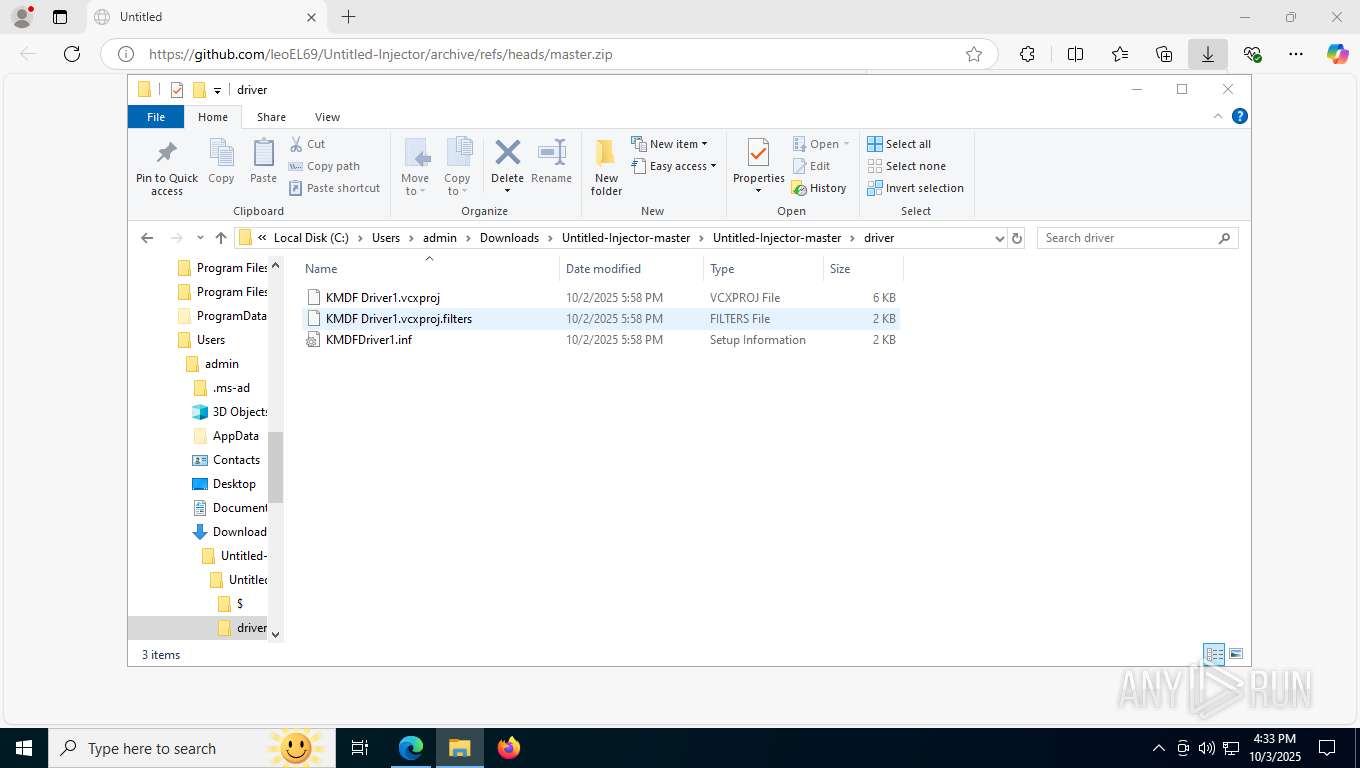
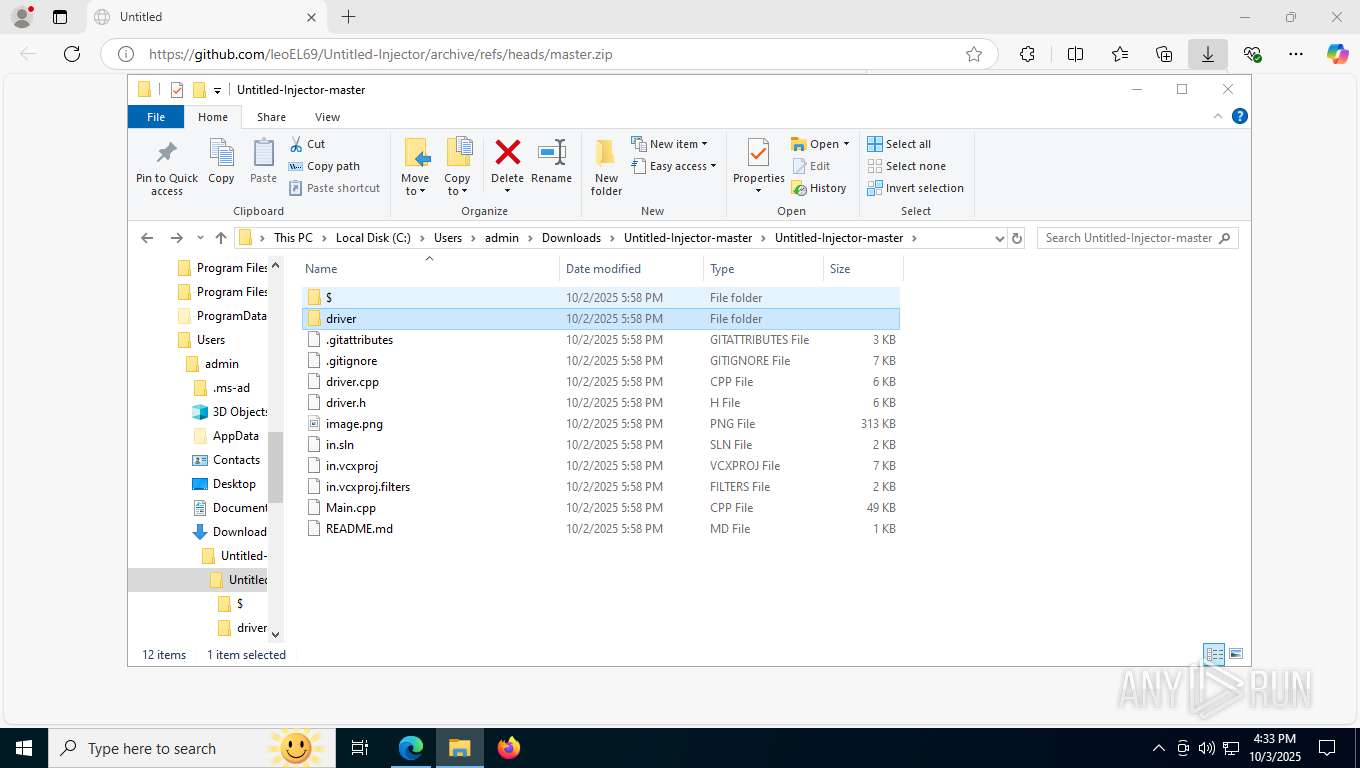
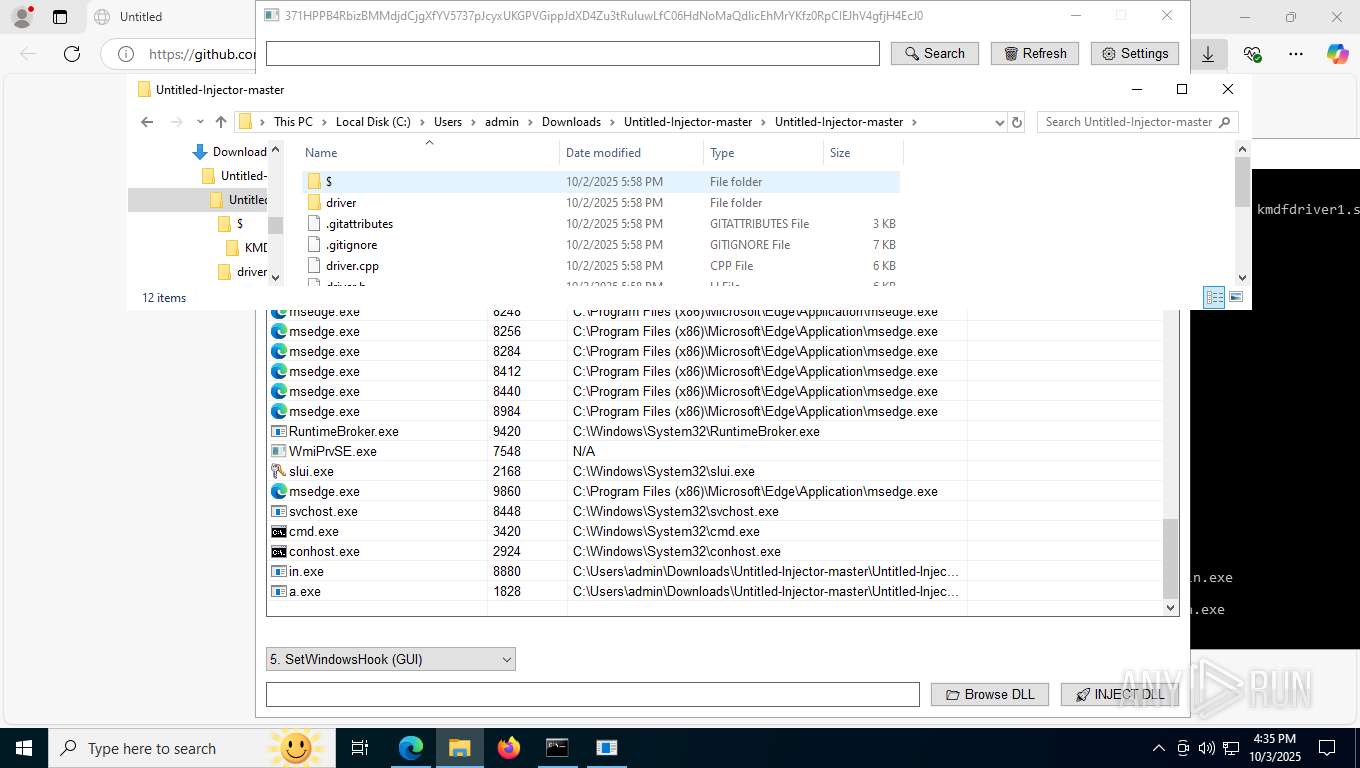
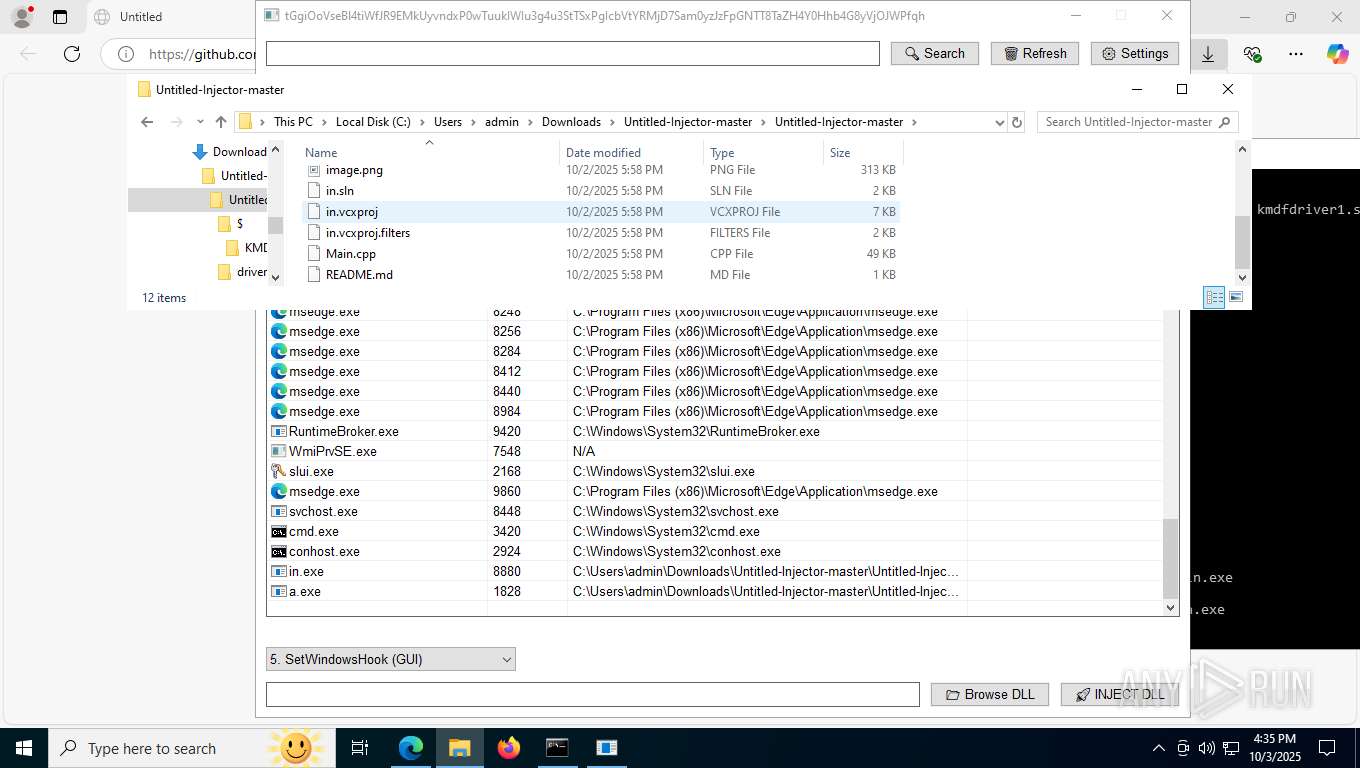
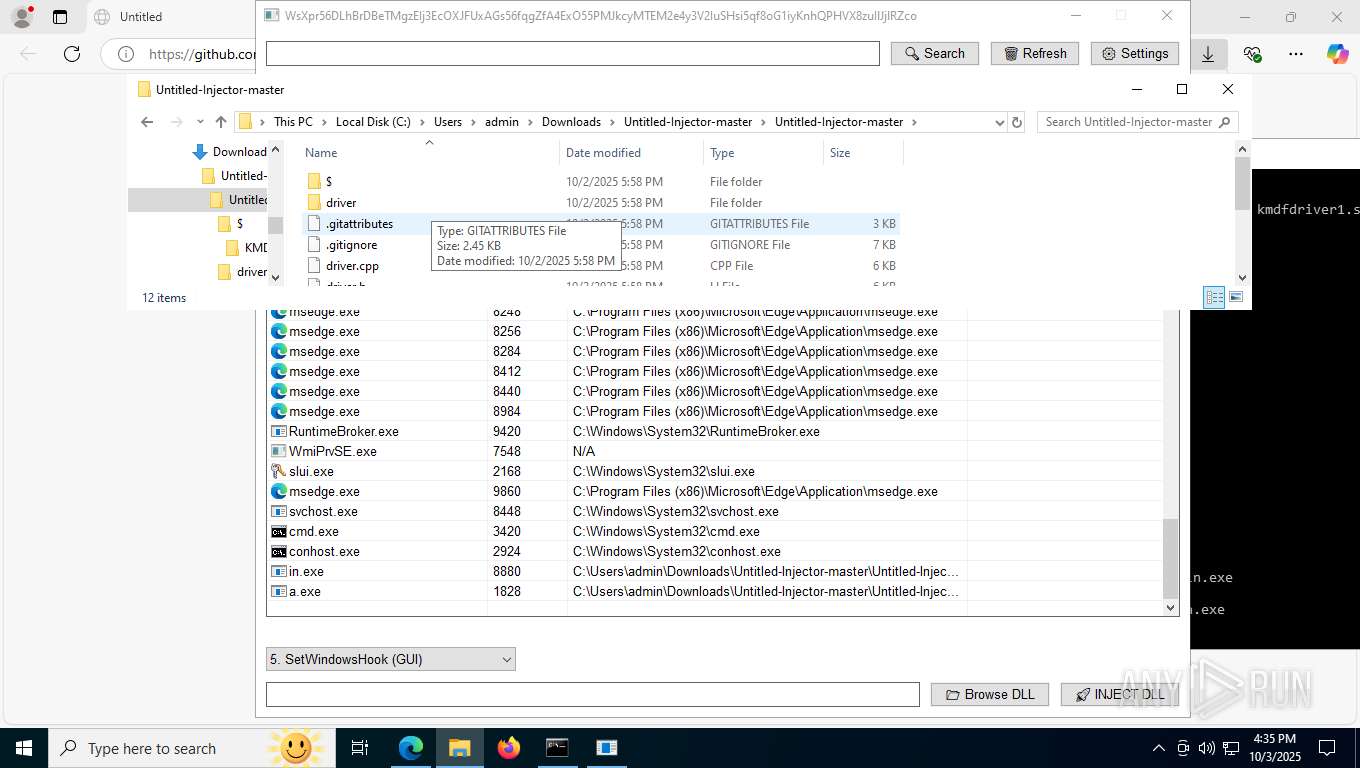
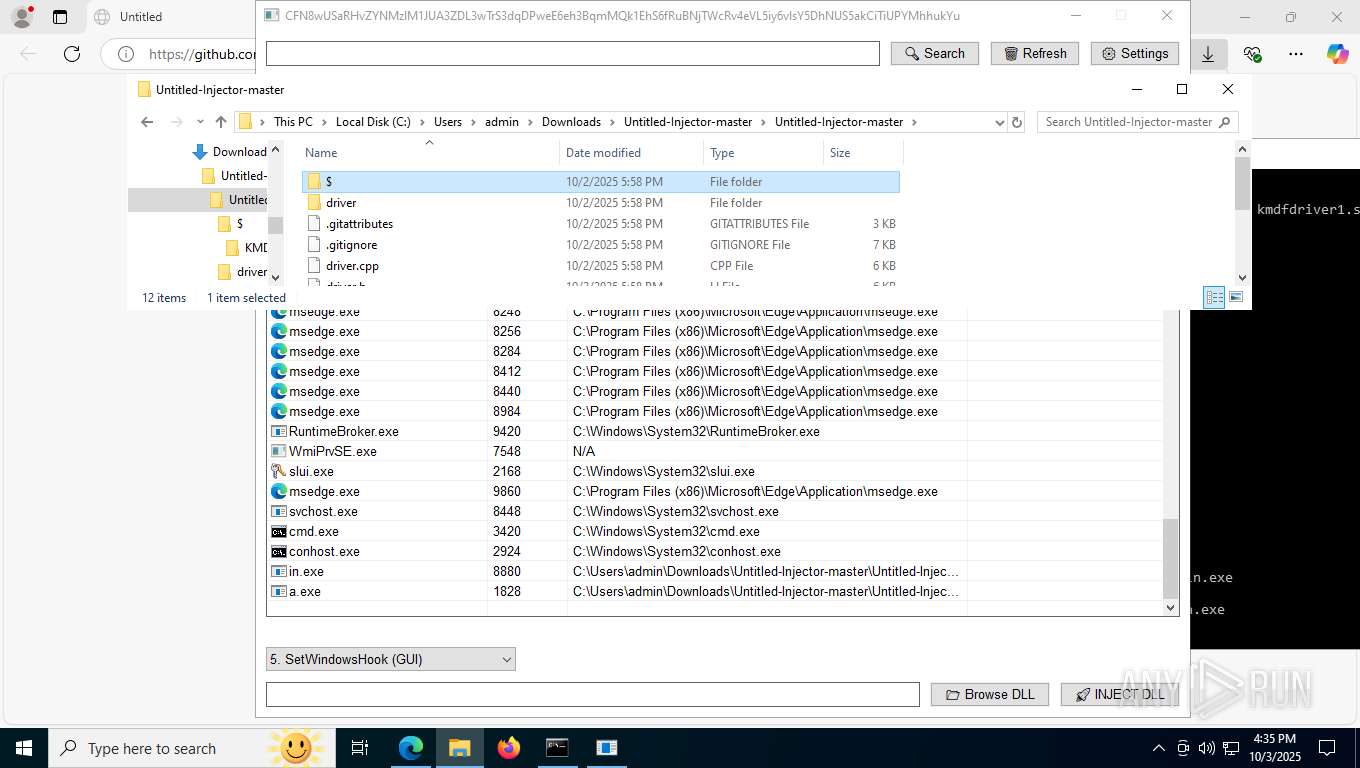
| URL: | https://github.com/leoEL69/Untitled-Injector/archive/refs/heads/master.zip |
| Full analysis: | https://app.any.run/tasks/d65de21f-0fb4-4b2b-b6c3-b5418eaf4c89 |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2025, 16:32:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6744ED0AFF07A1BFEC0C031A01A8F665 |
| SHA1: | CD896D729A89B1ABB41E4A9B7FBF46A841FF6A55 |
| SHA256: | C34F0C16A133495E8FD44575E5E1F47732EEBA107FC5A1547674B831161CC30C |
| SSDEEP: | 3:N8tEd5AtmqROBR74a+z4RSL6o:2uYt7sR4z4UL6o |
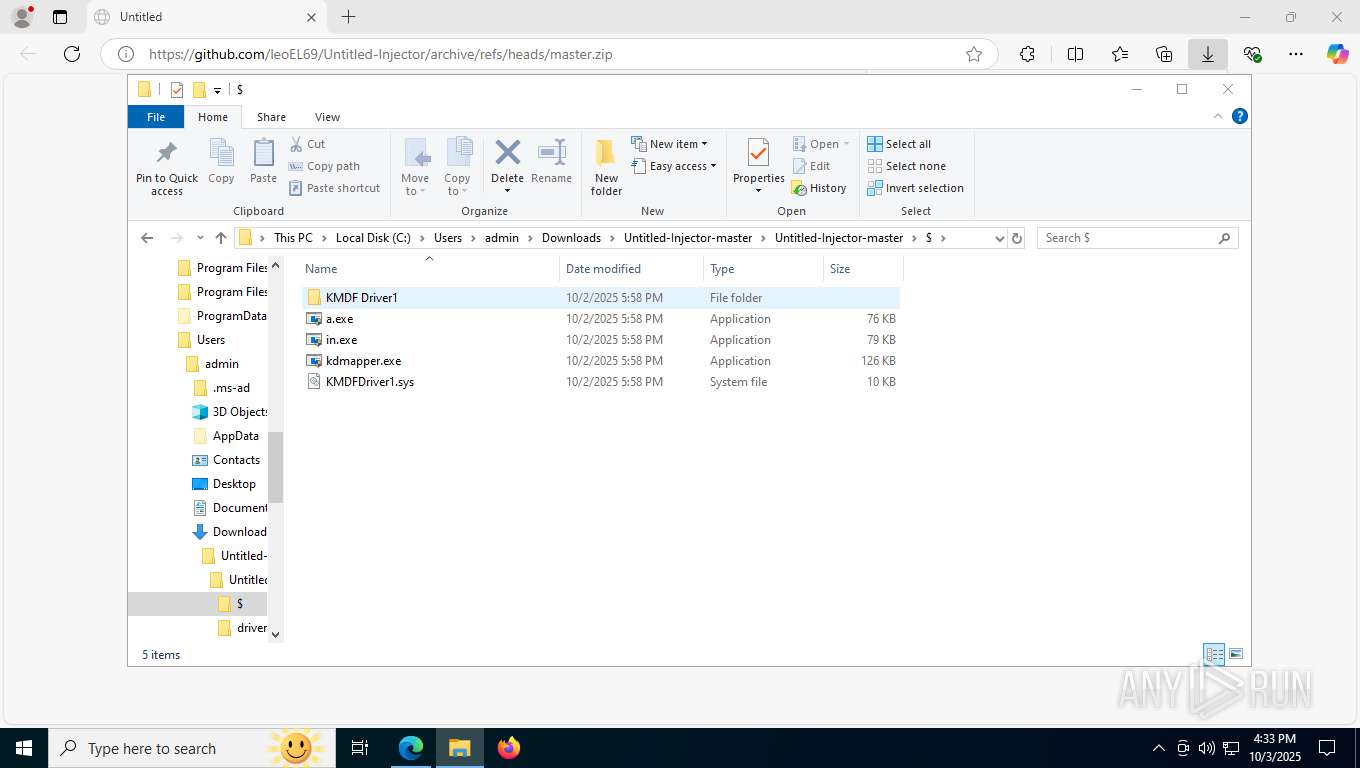
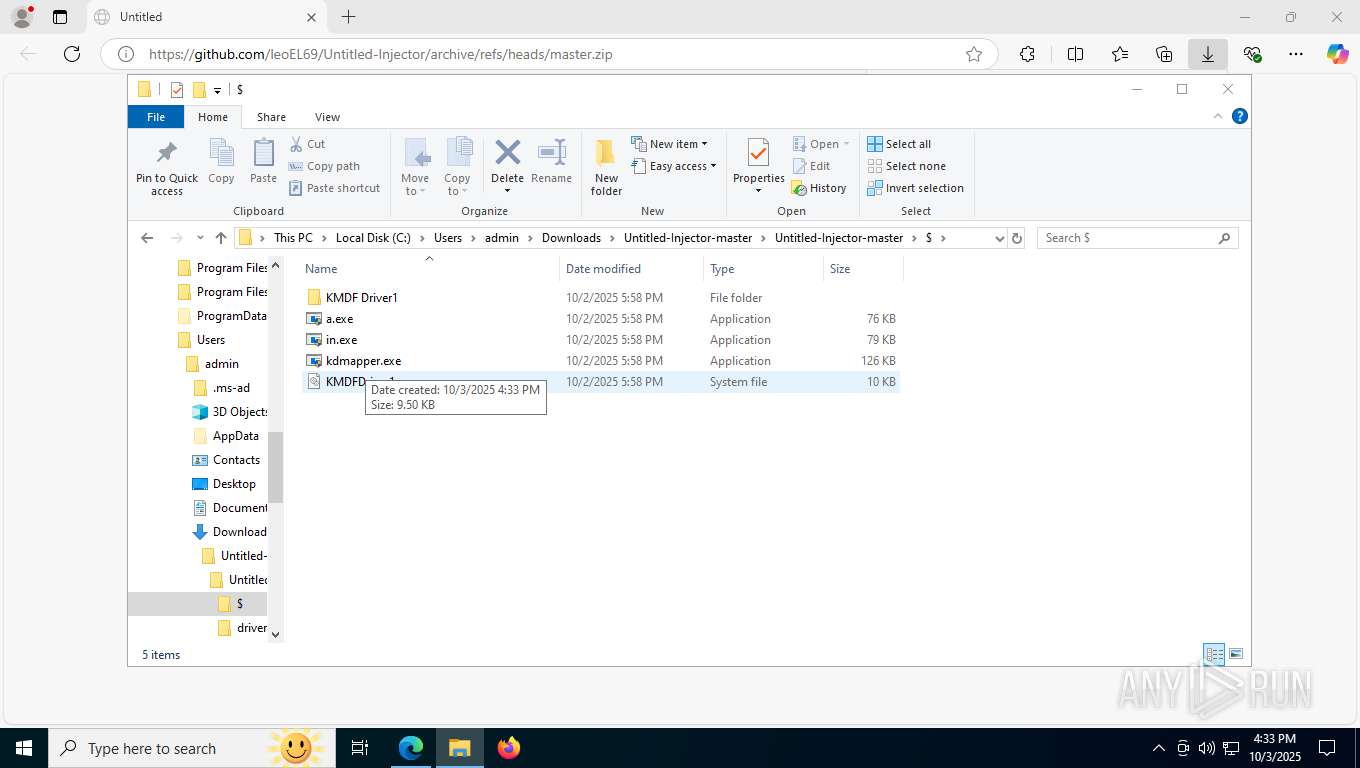
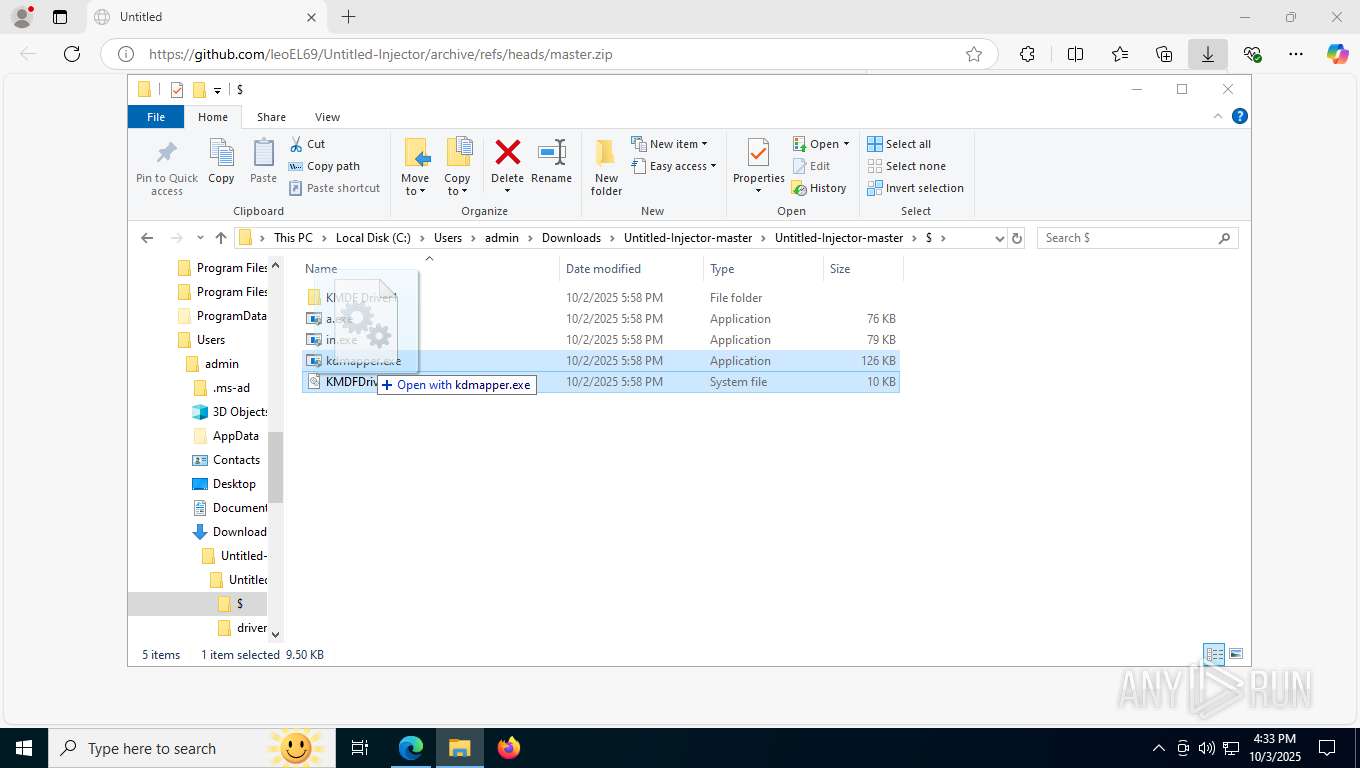
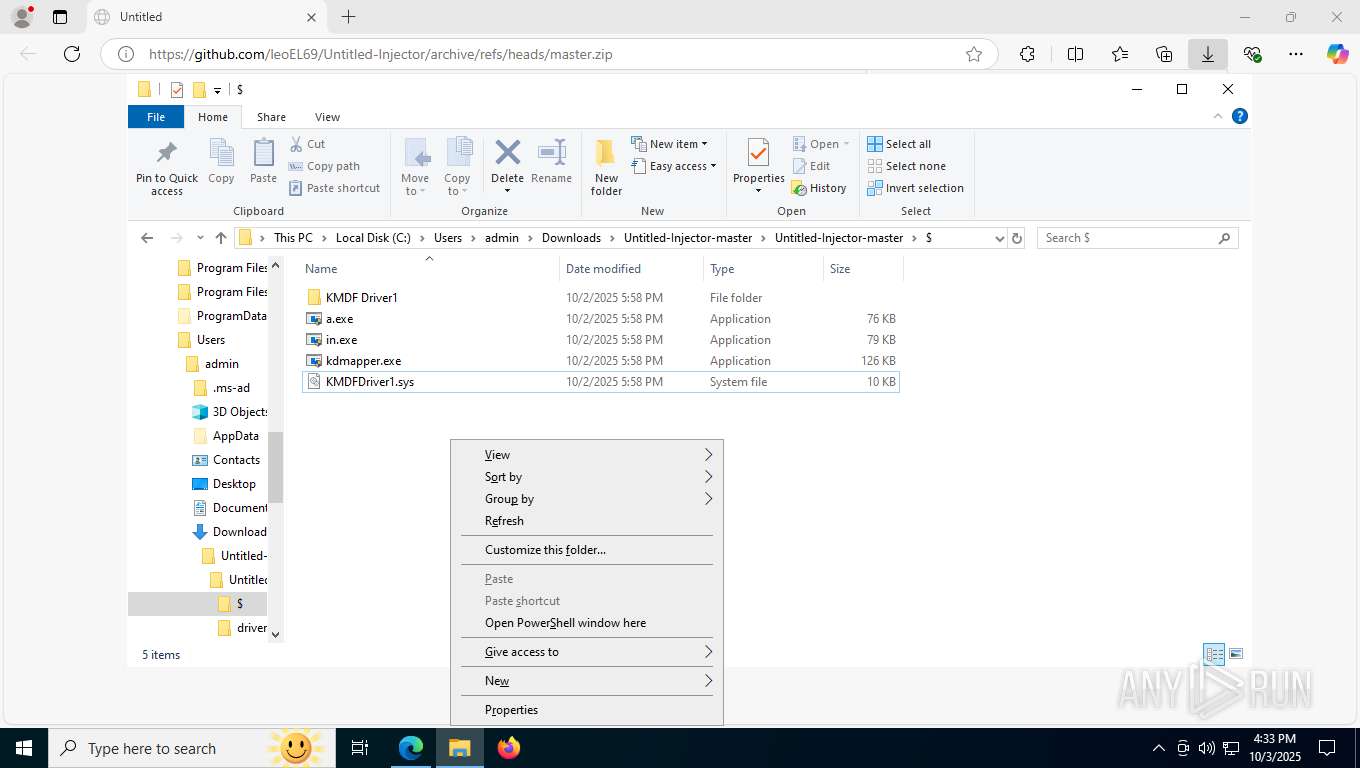
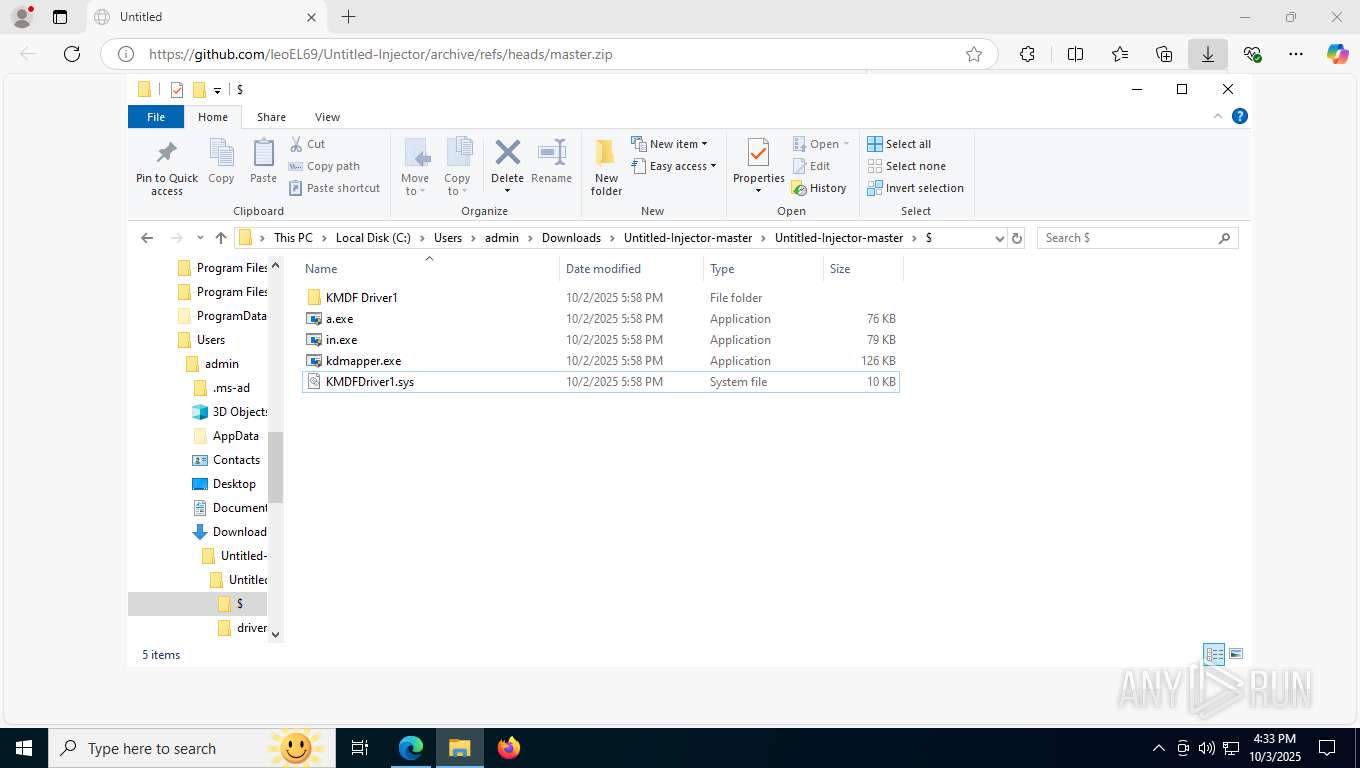
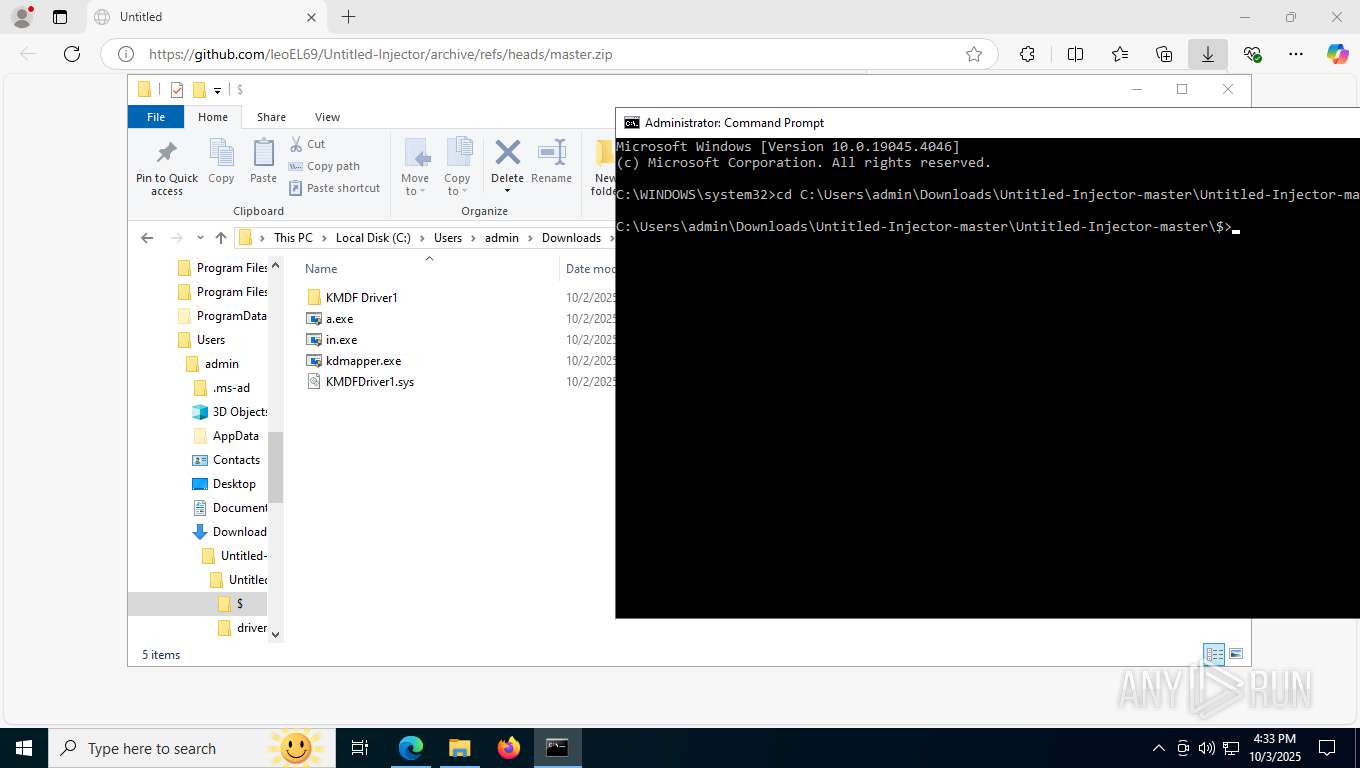
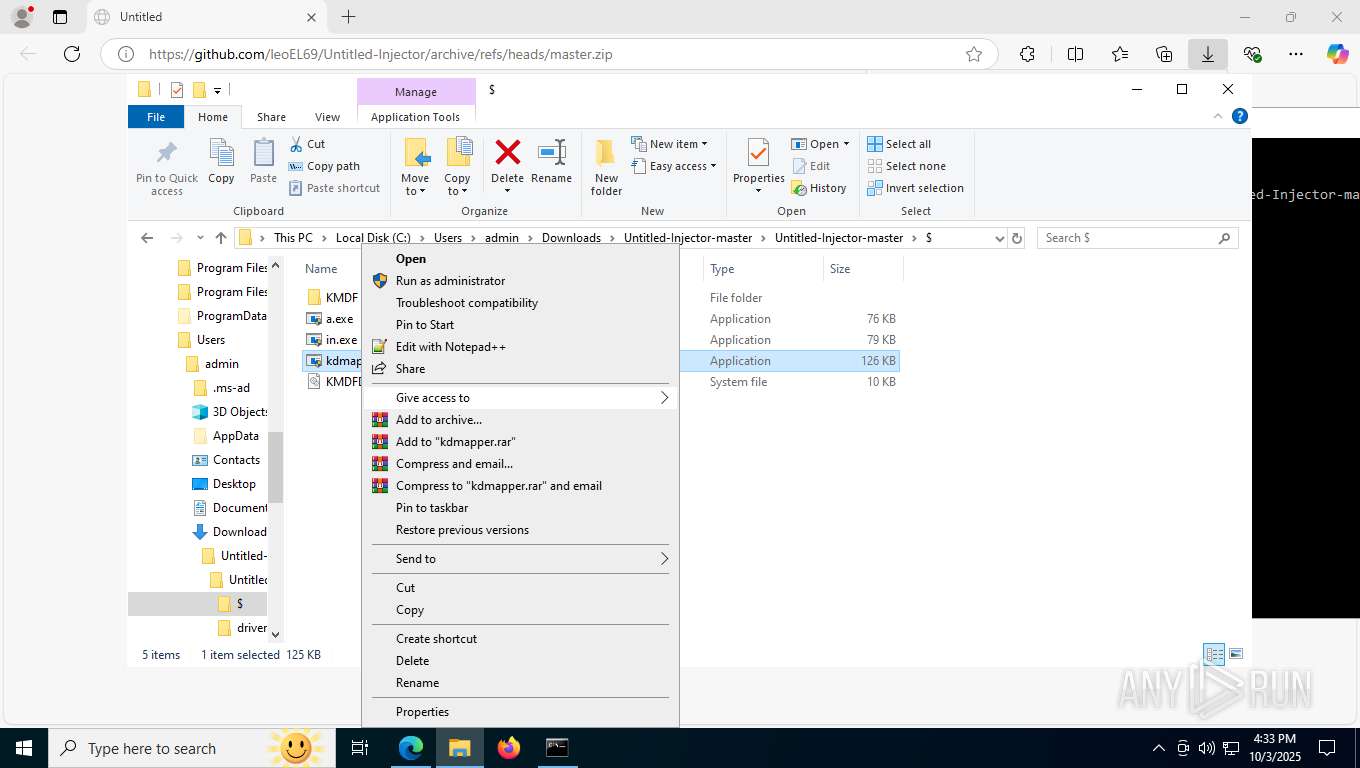
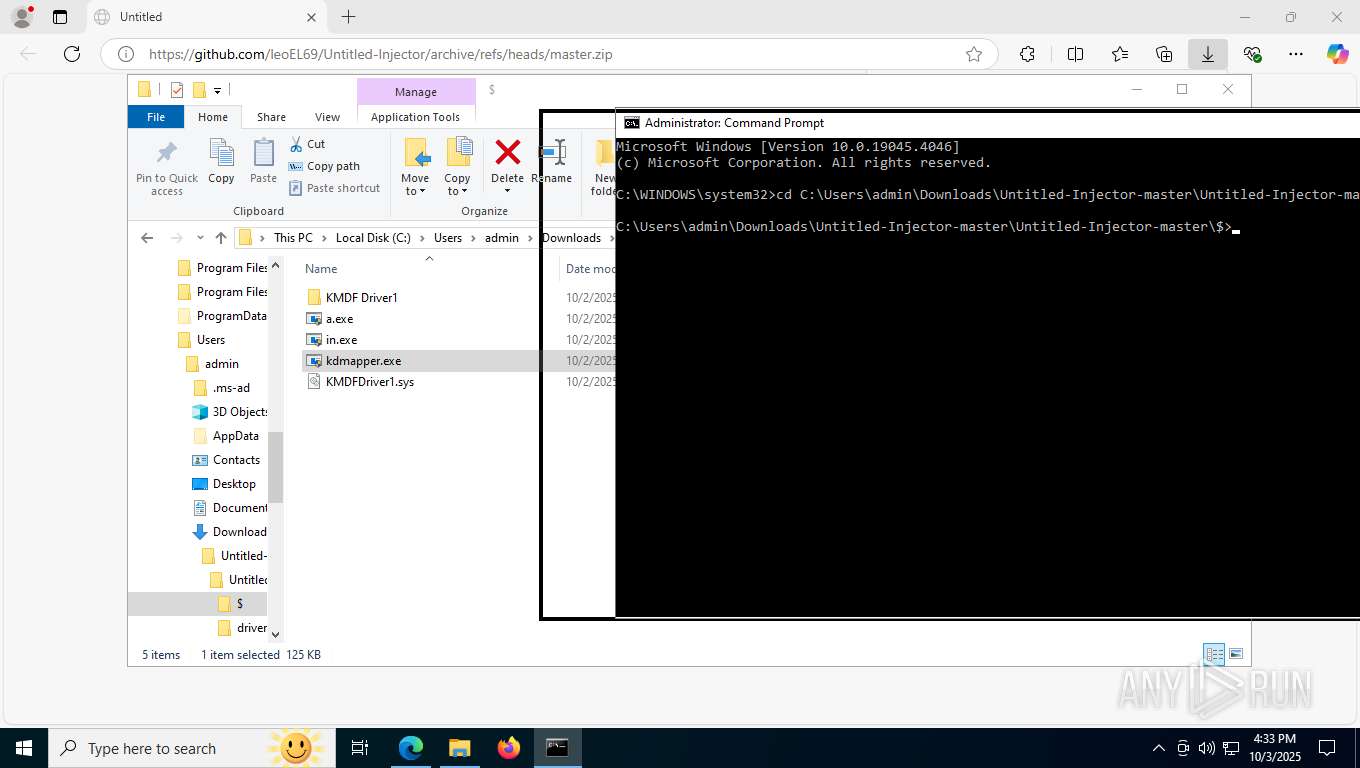
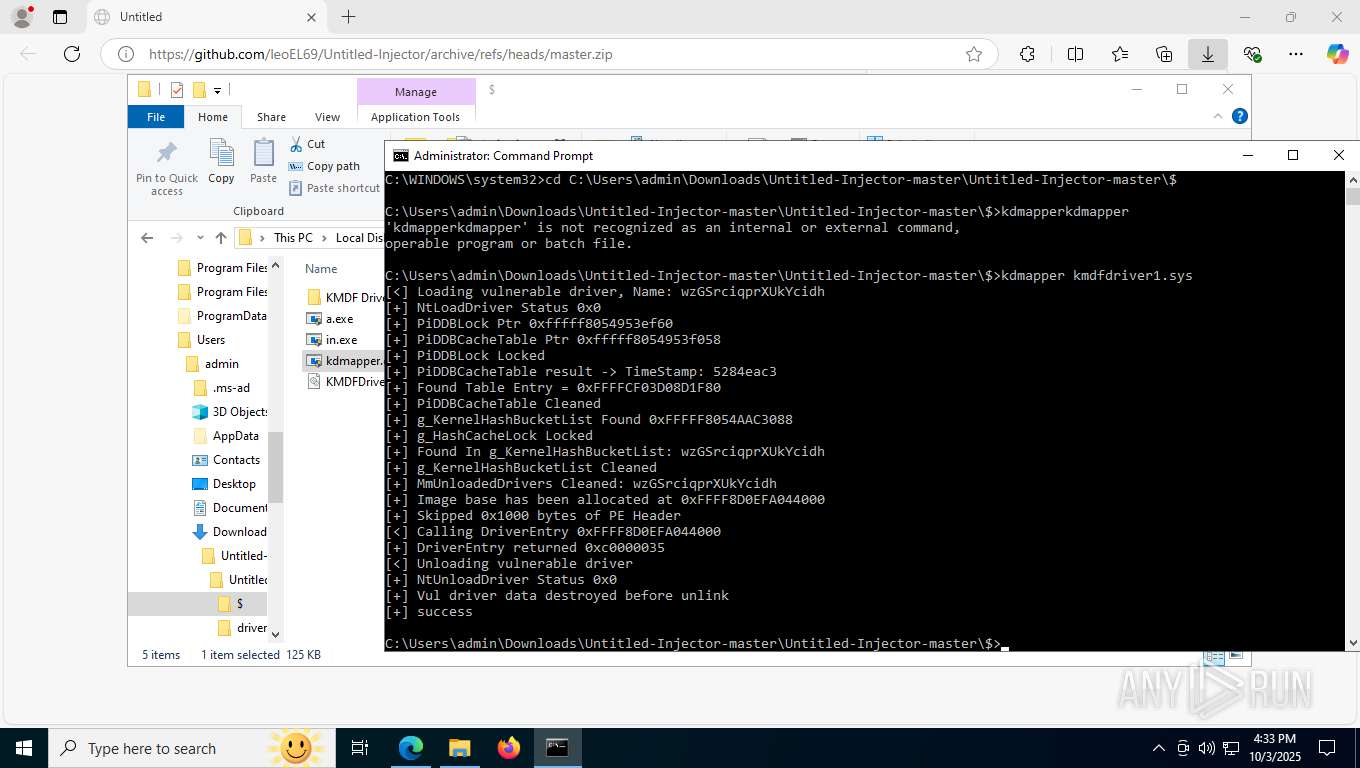
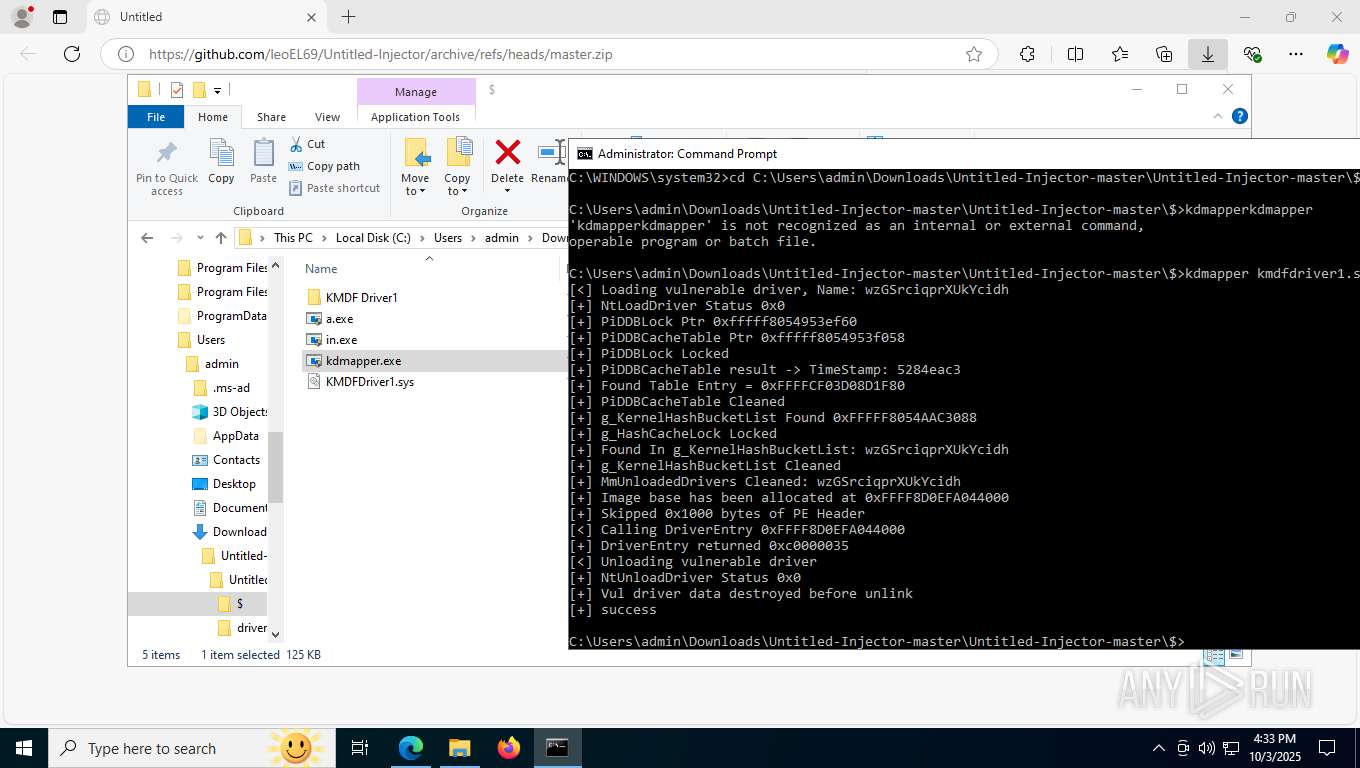
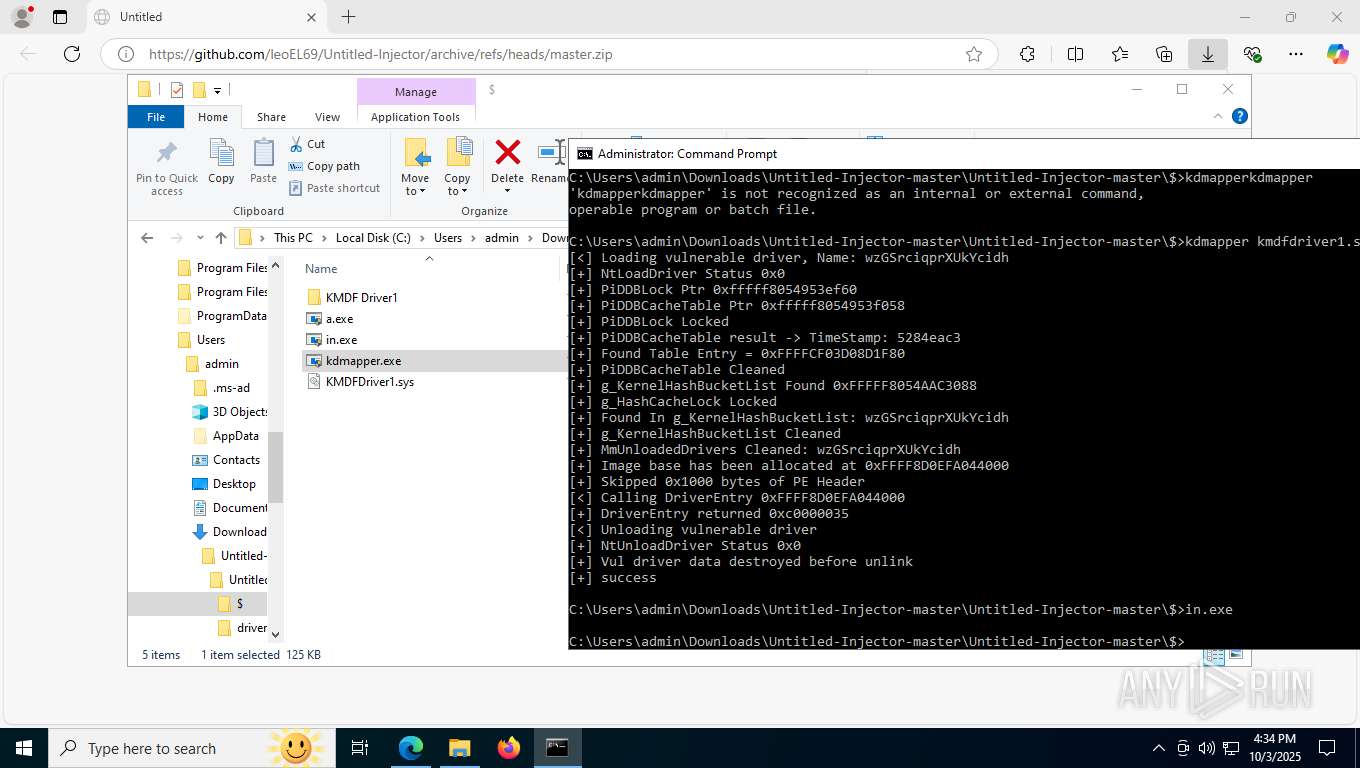
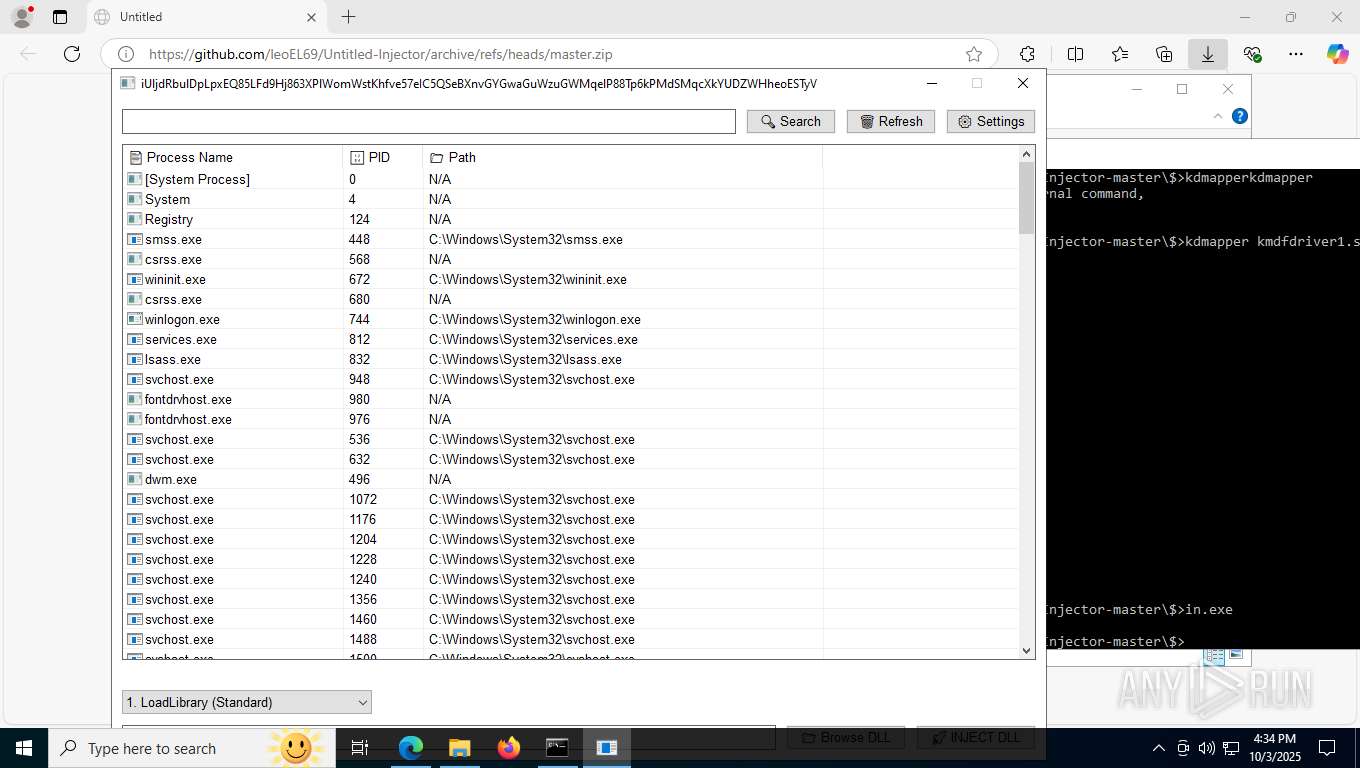
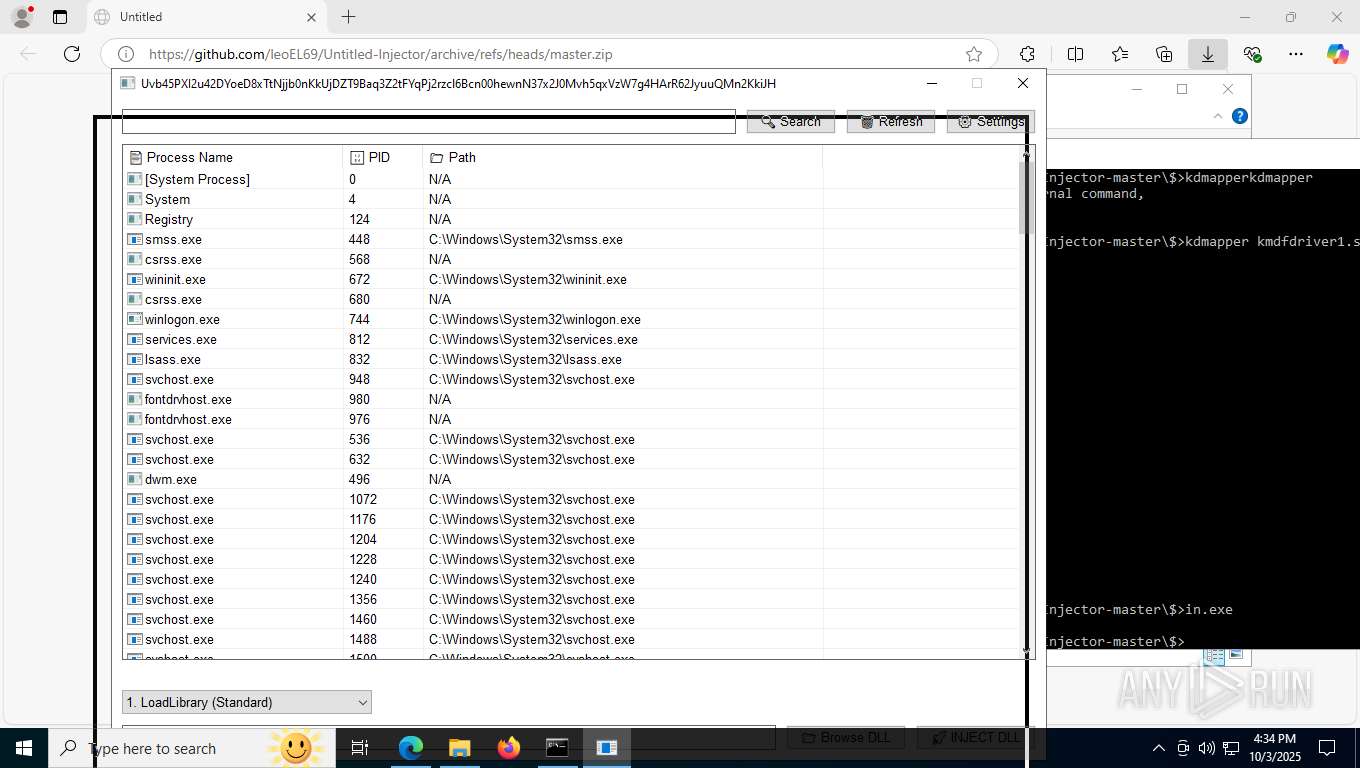
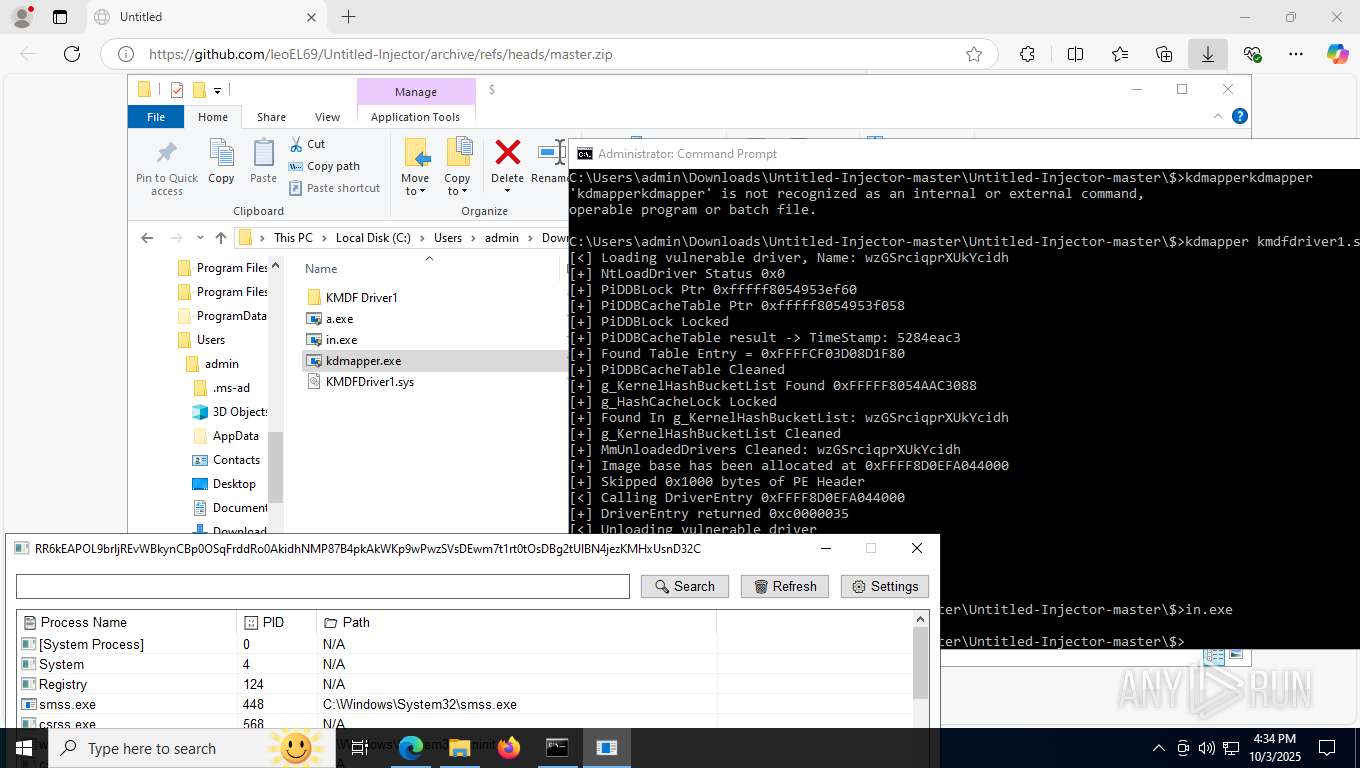
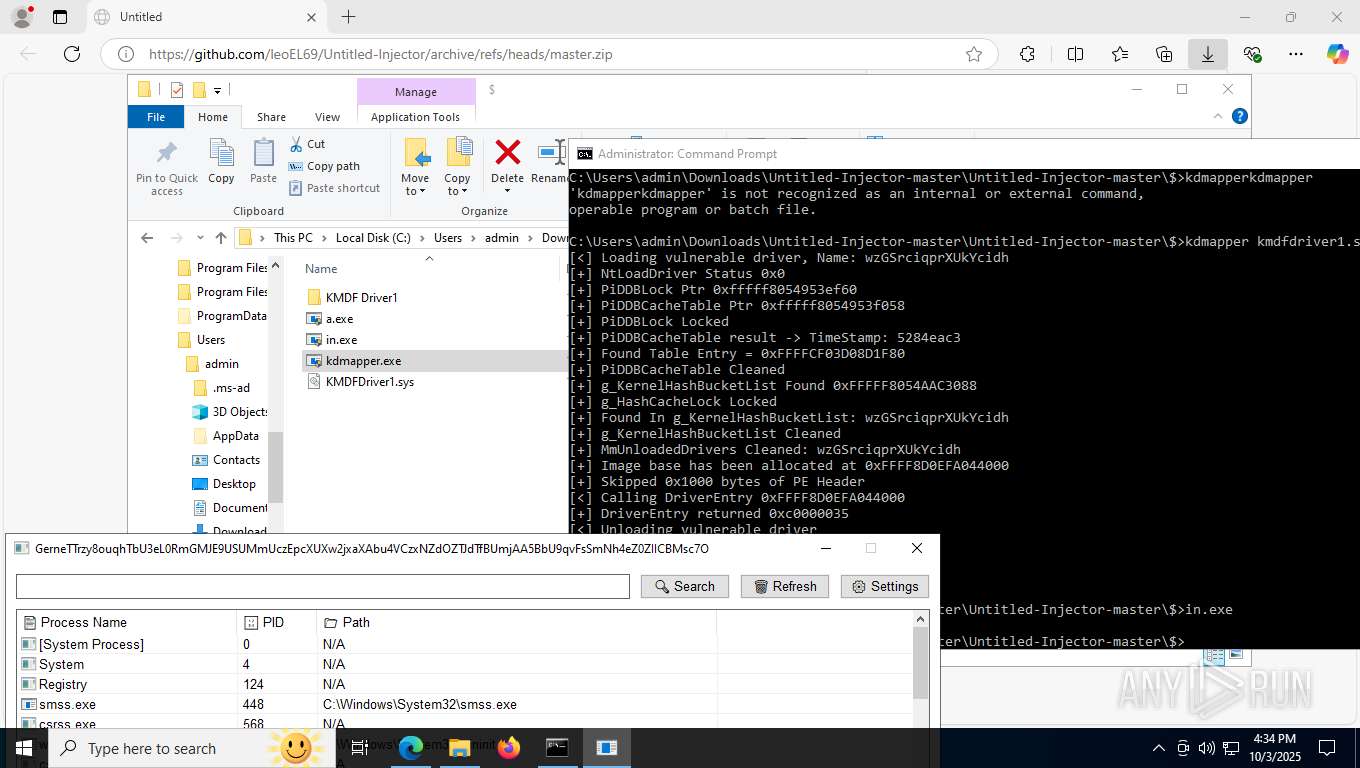
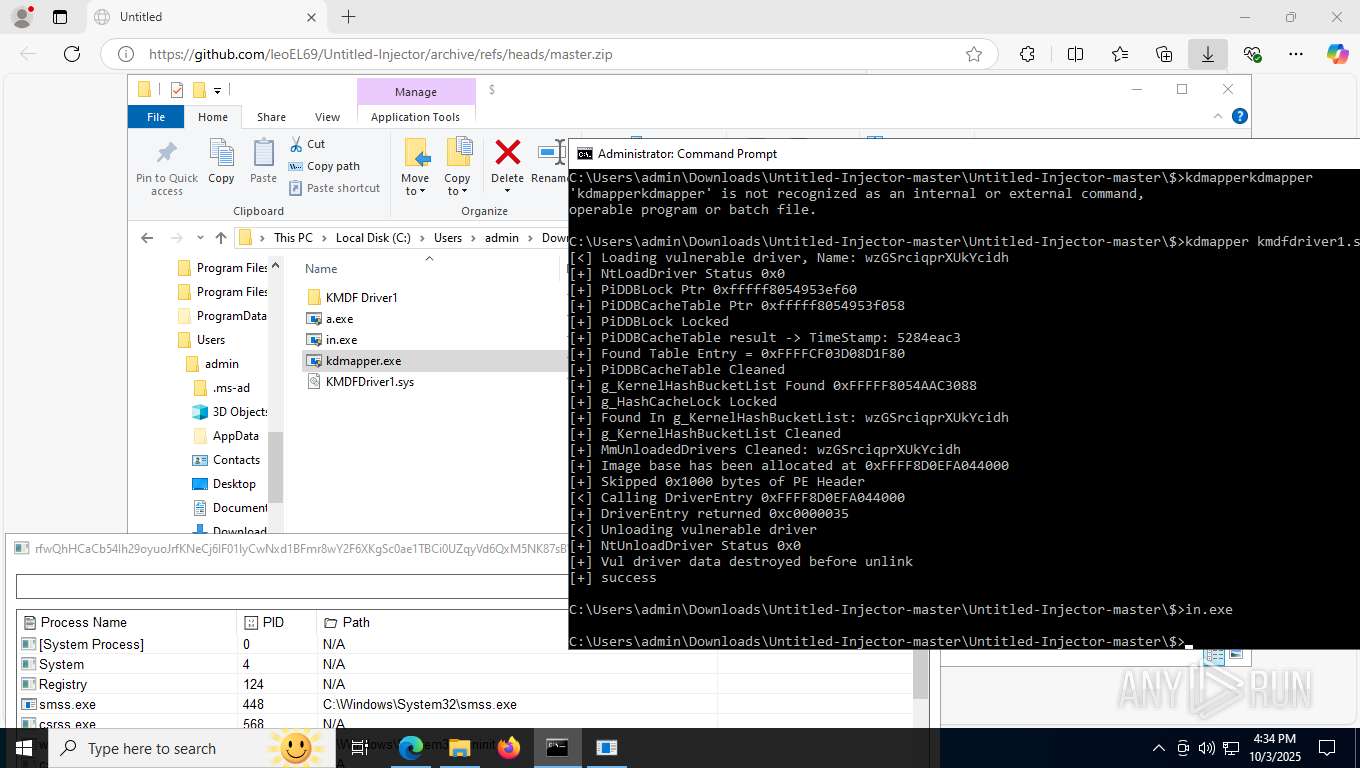
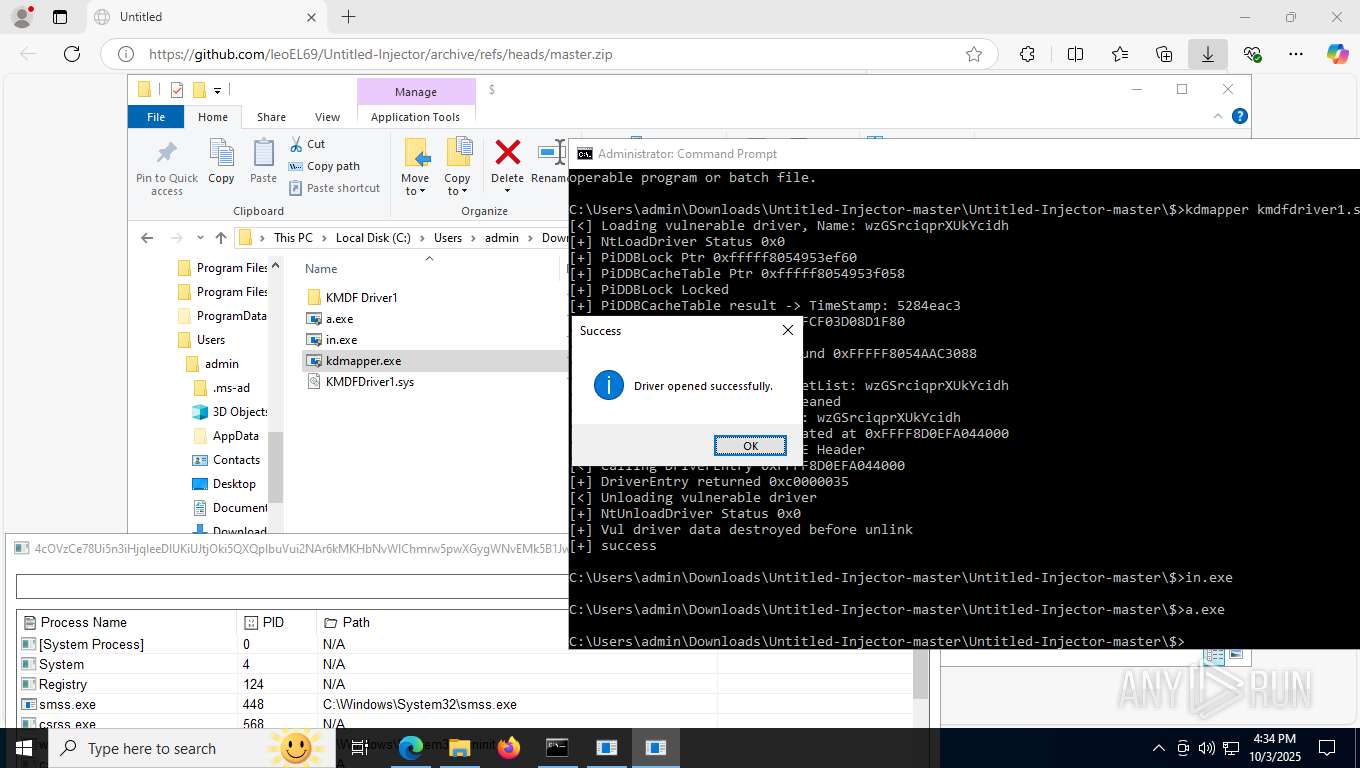
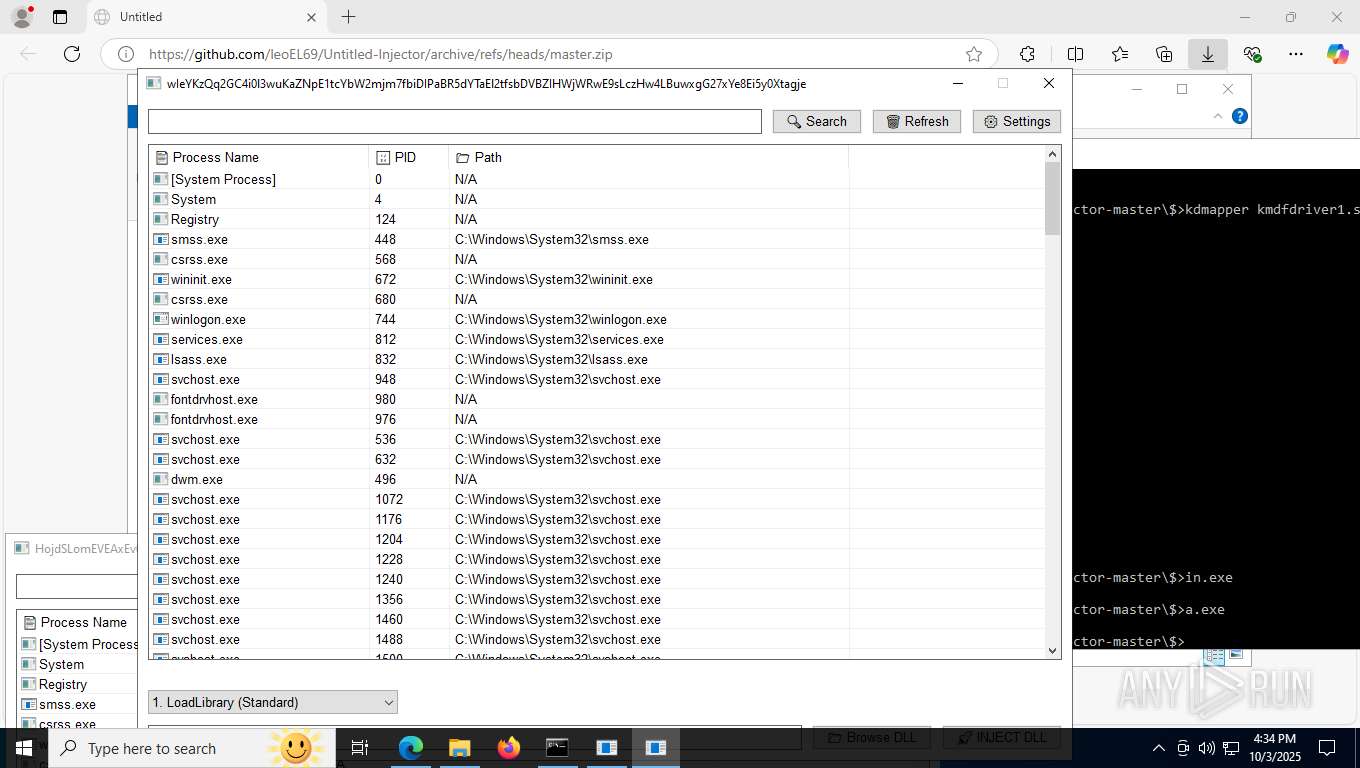
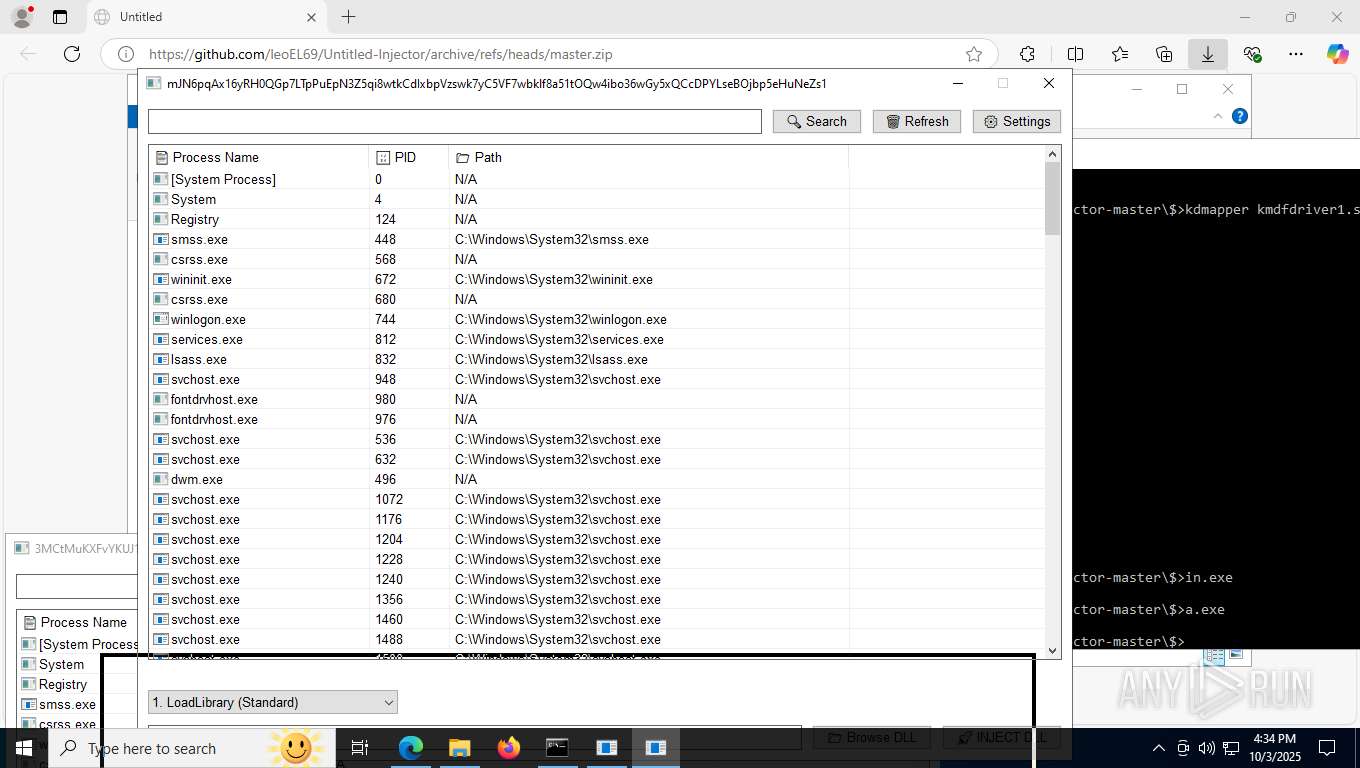
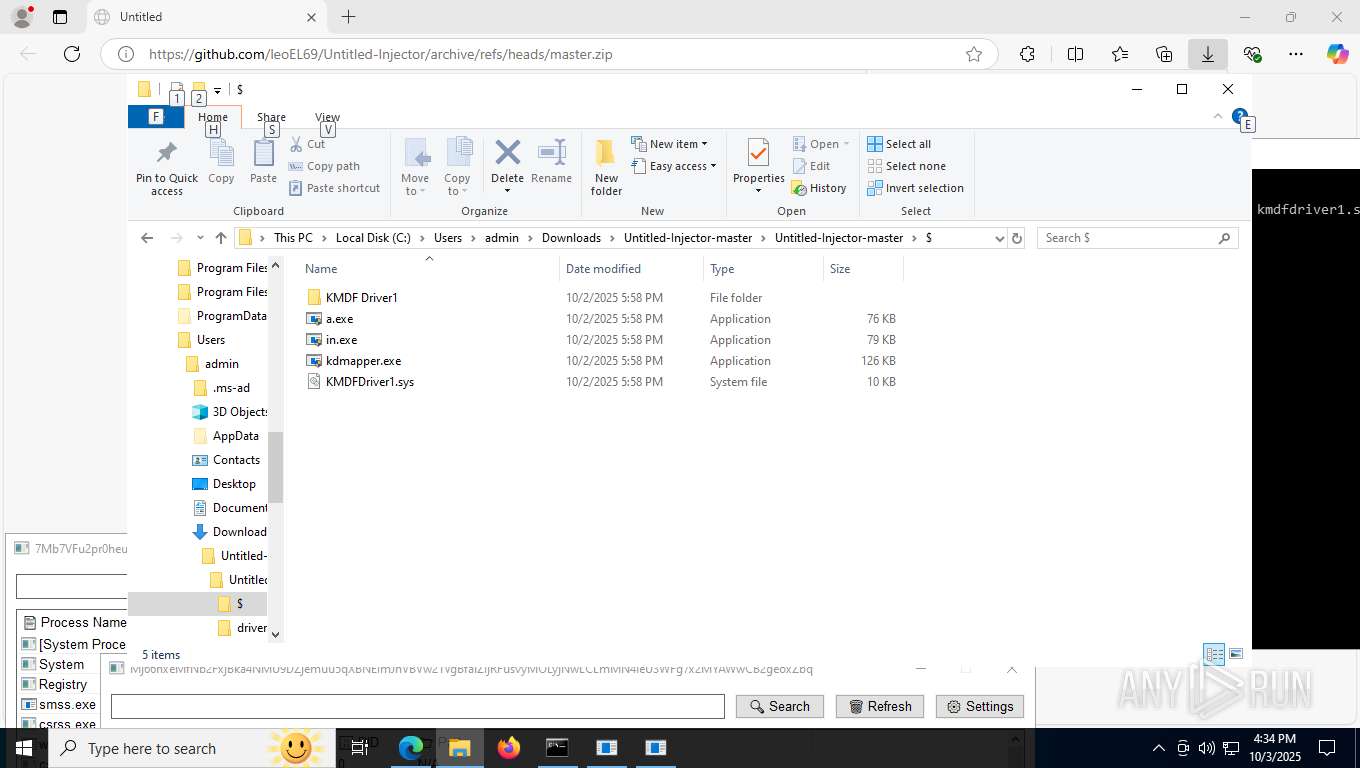
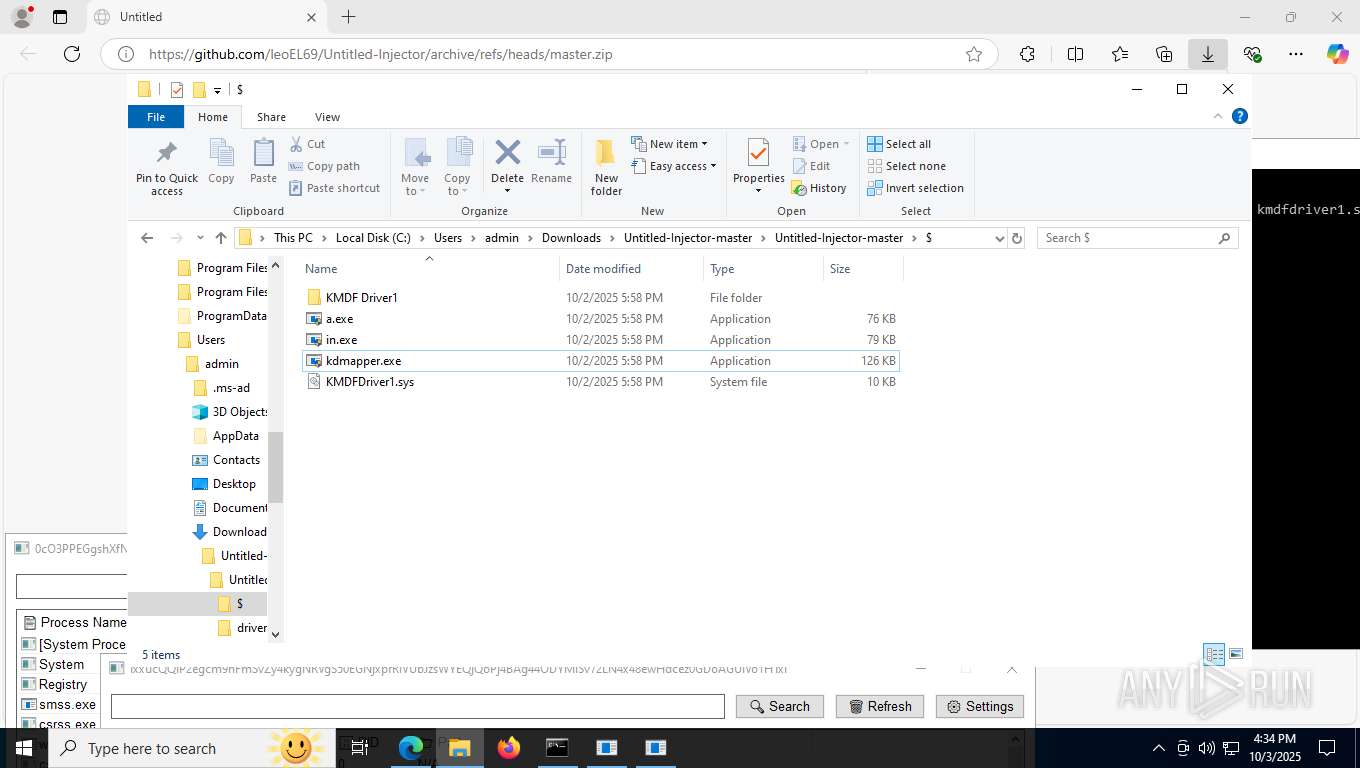
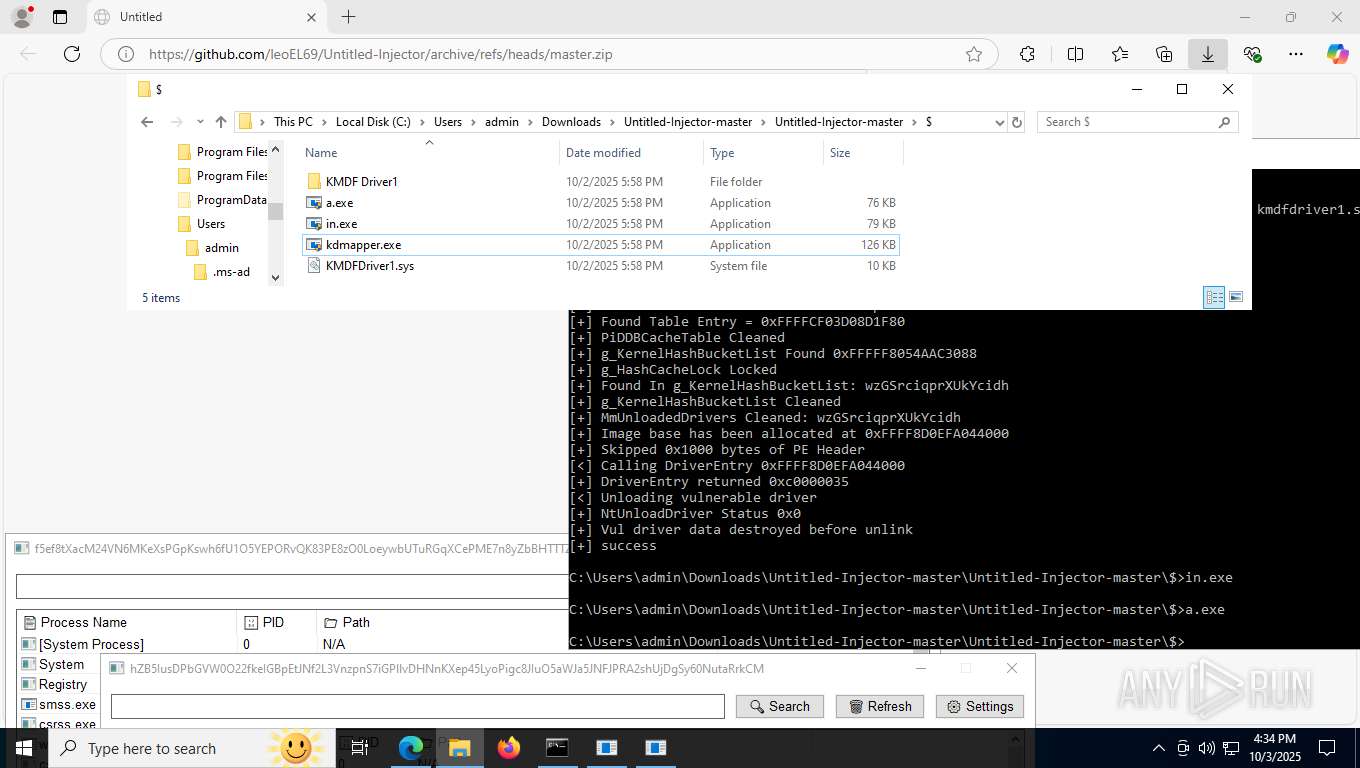
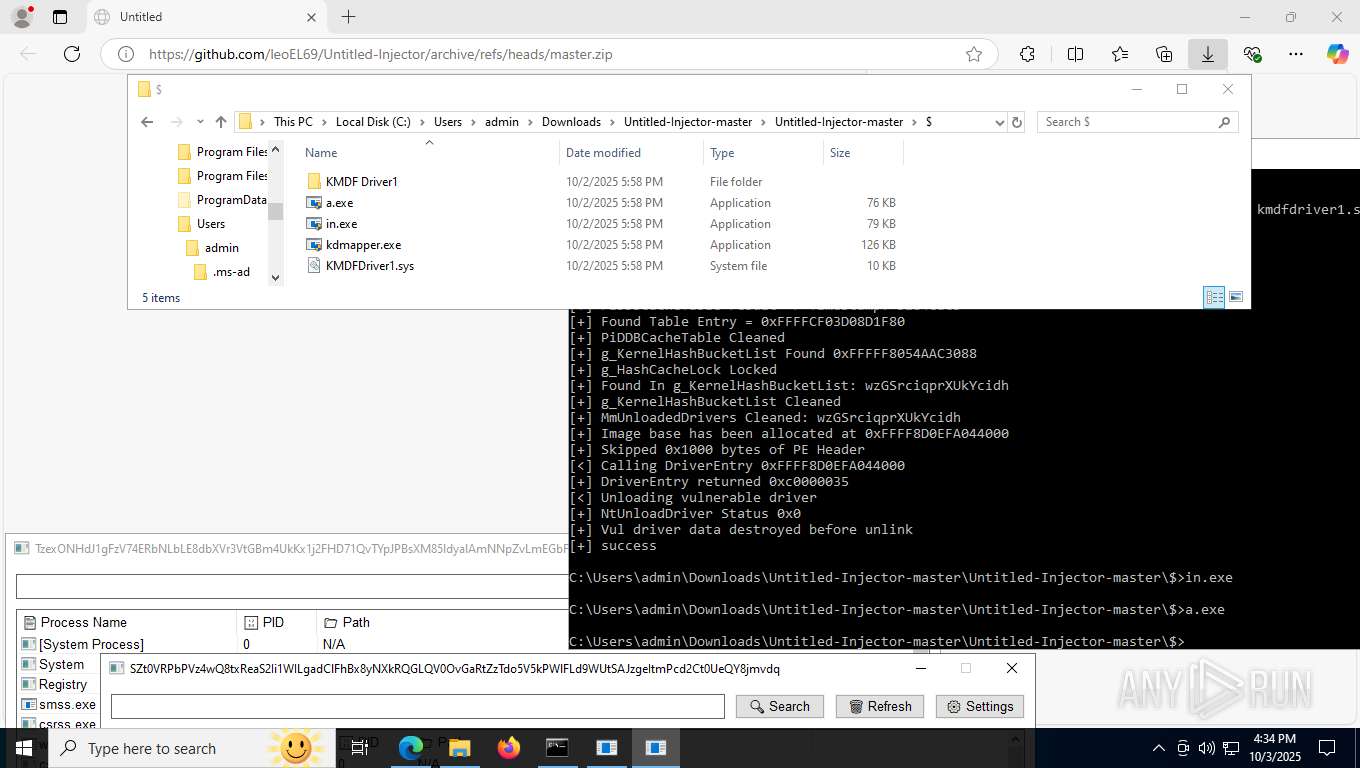
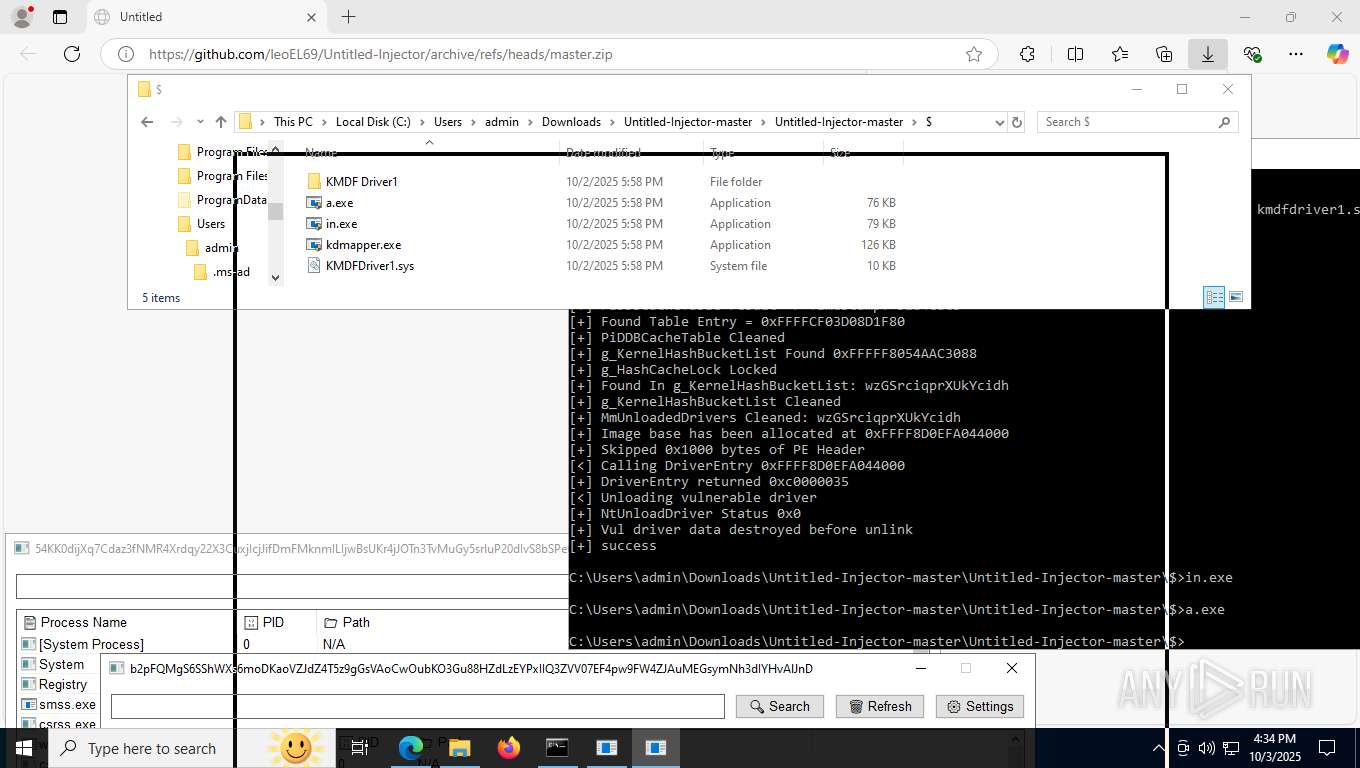
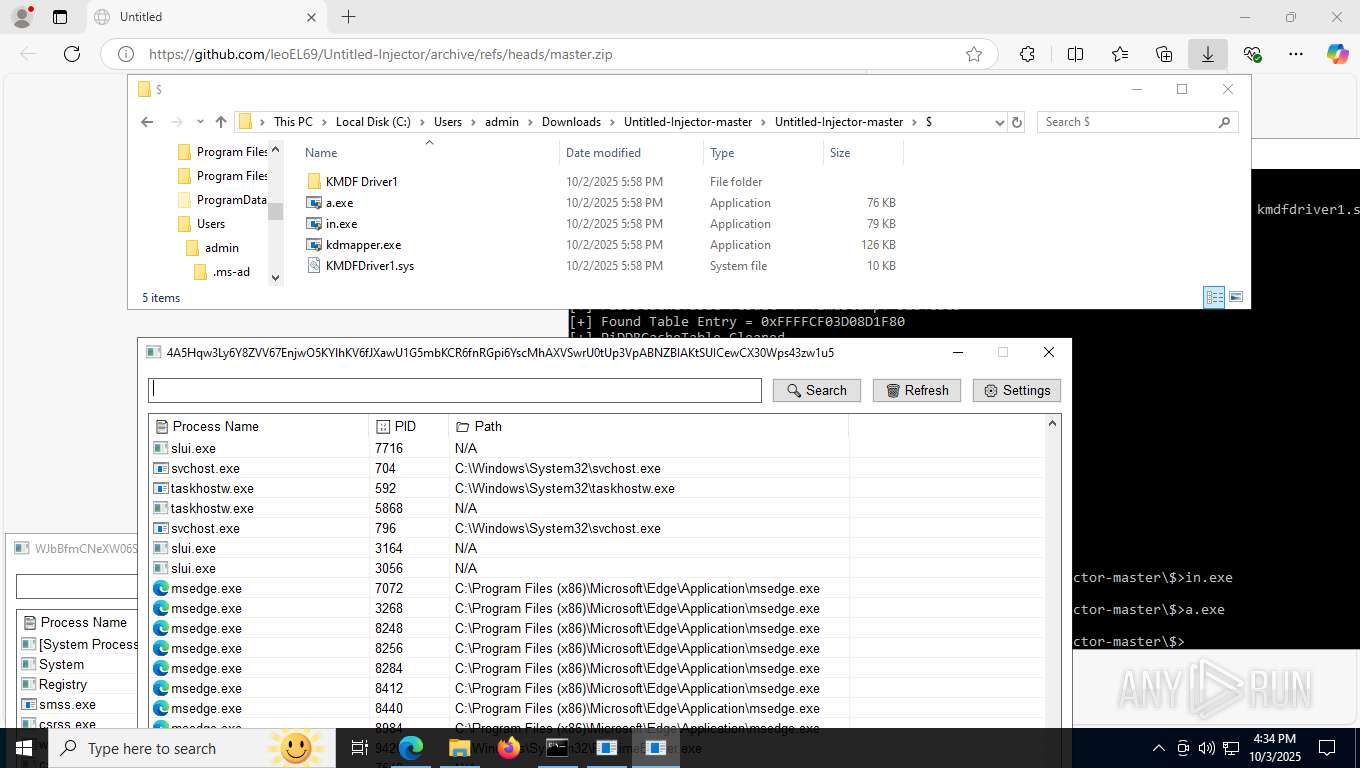
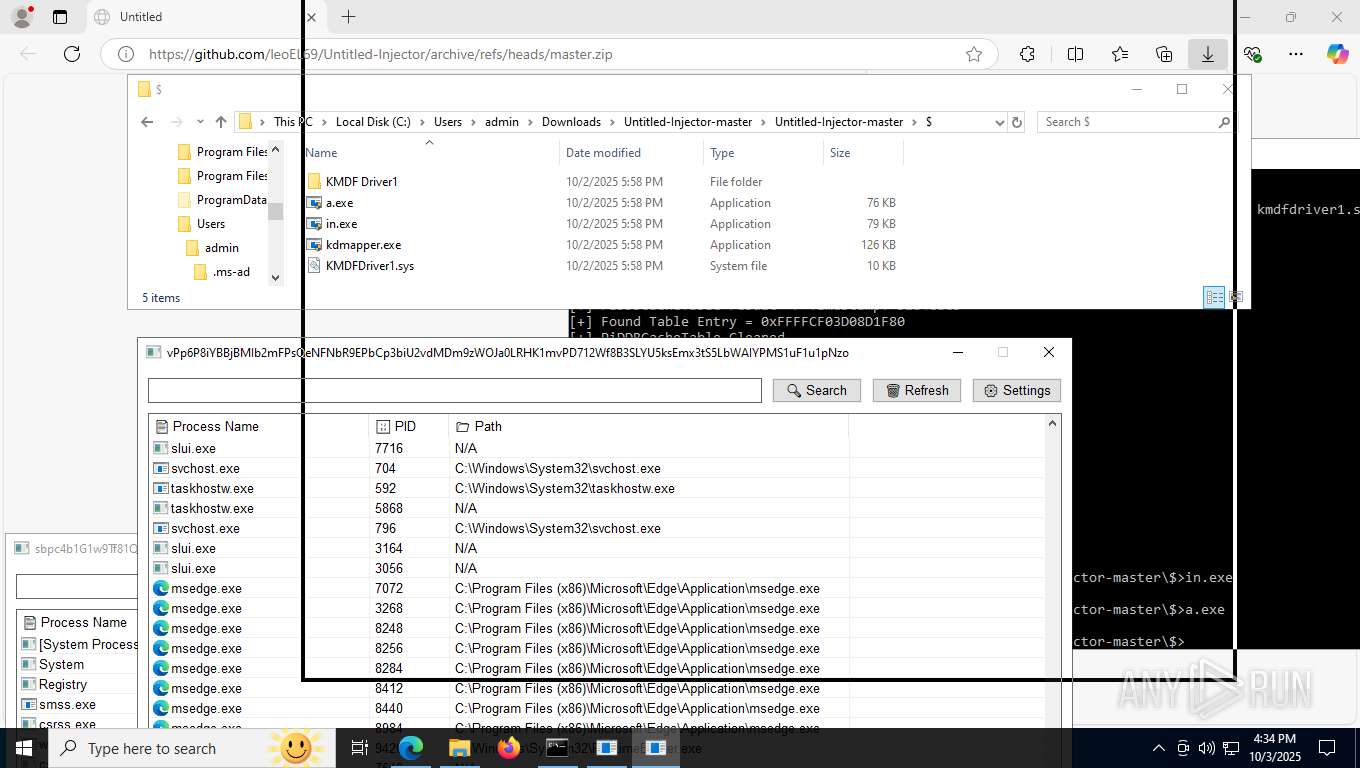
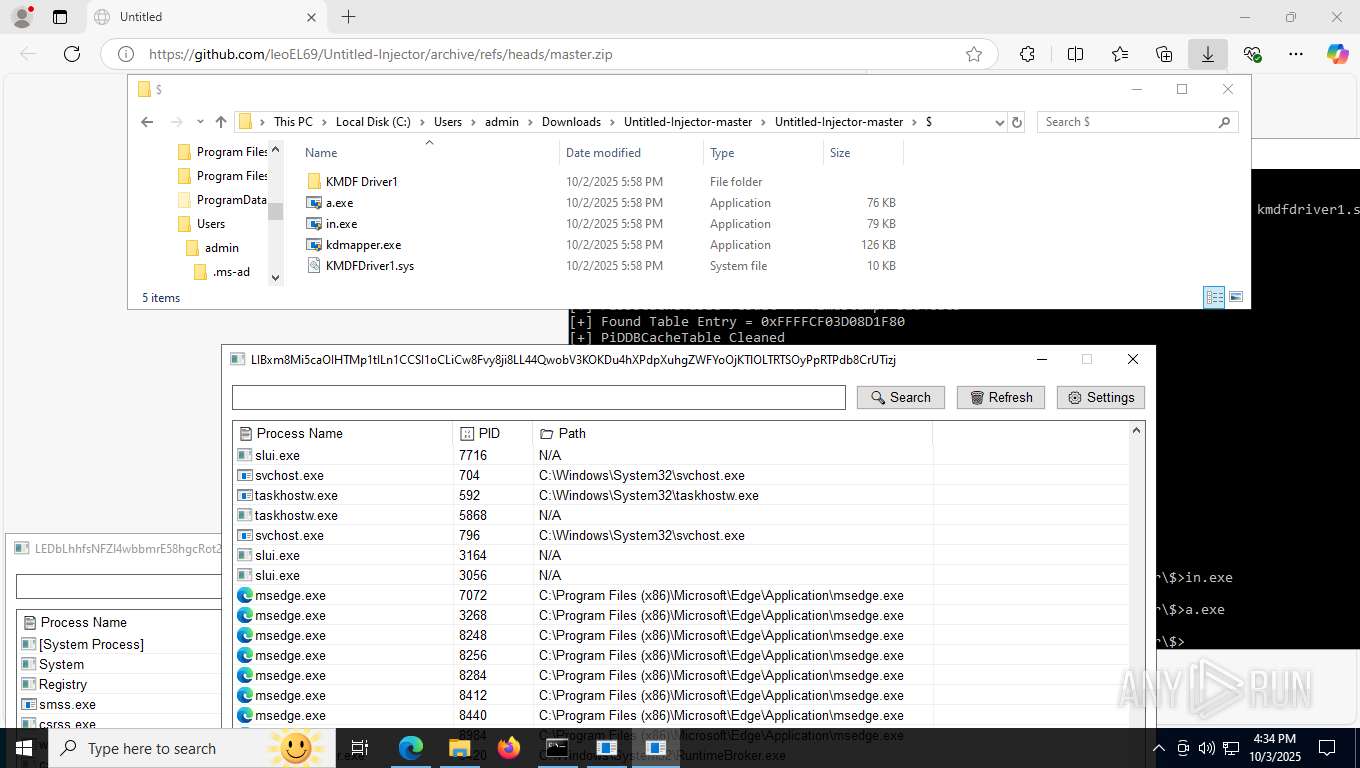
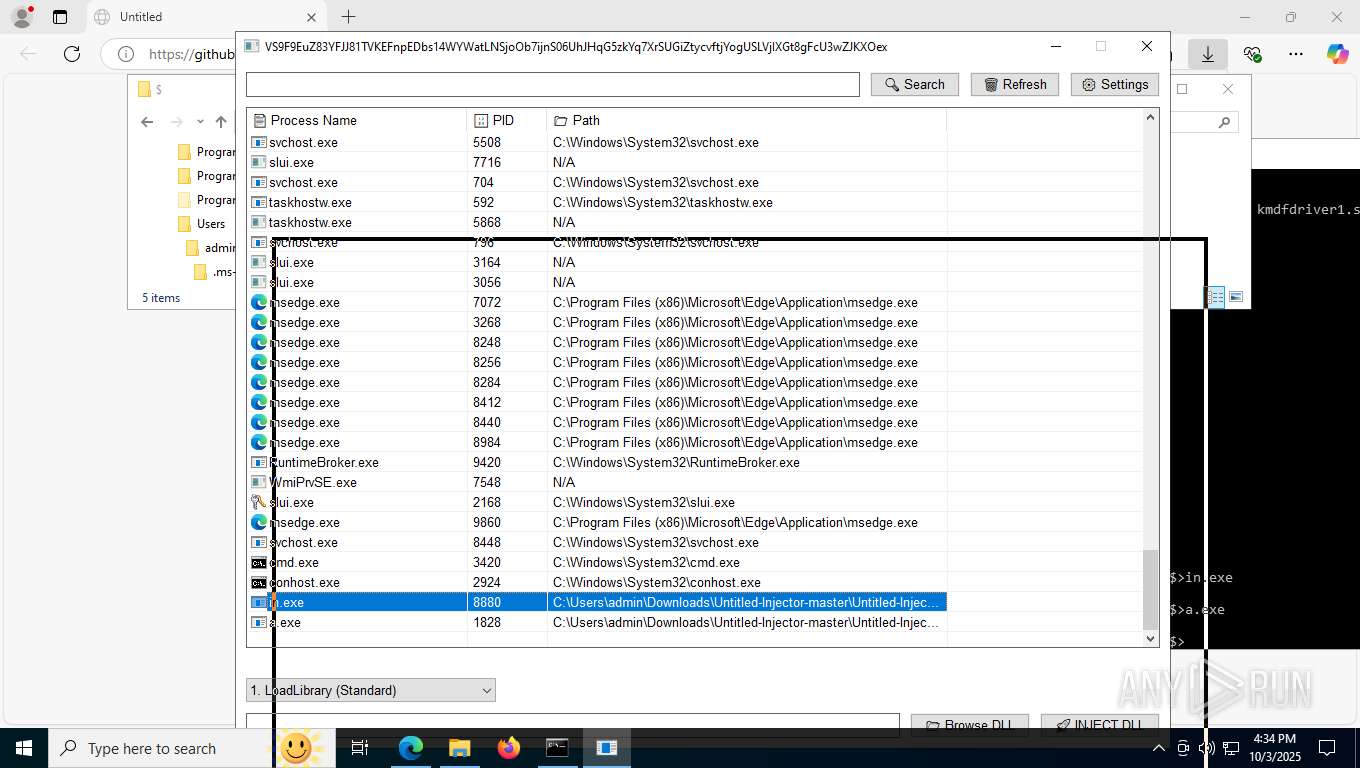
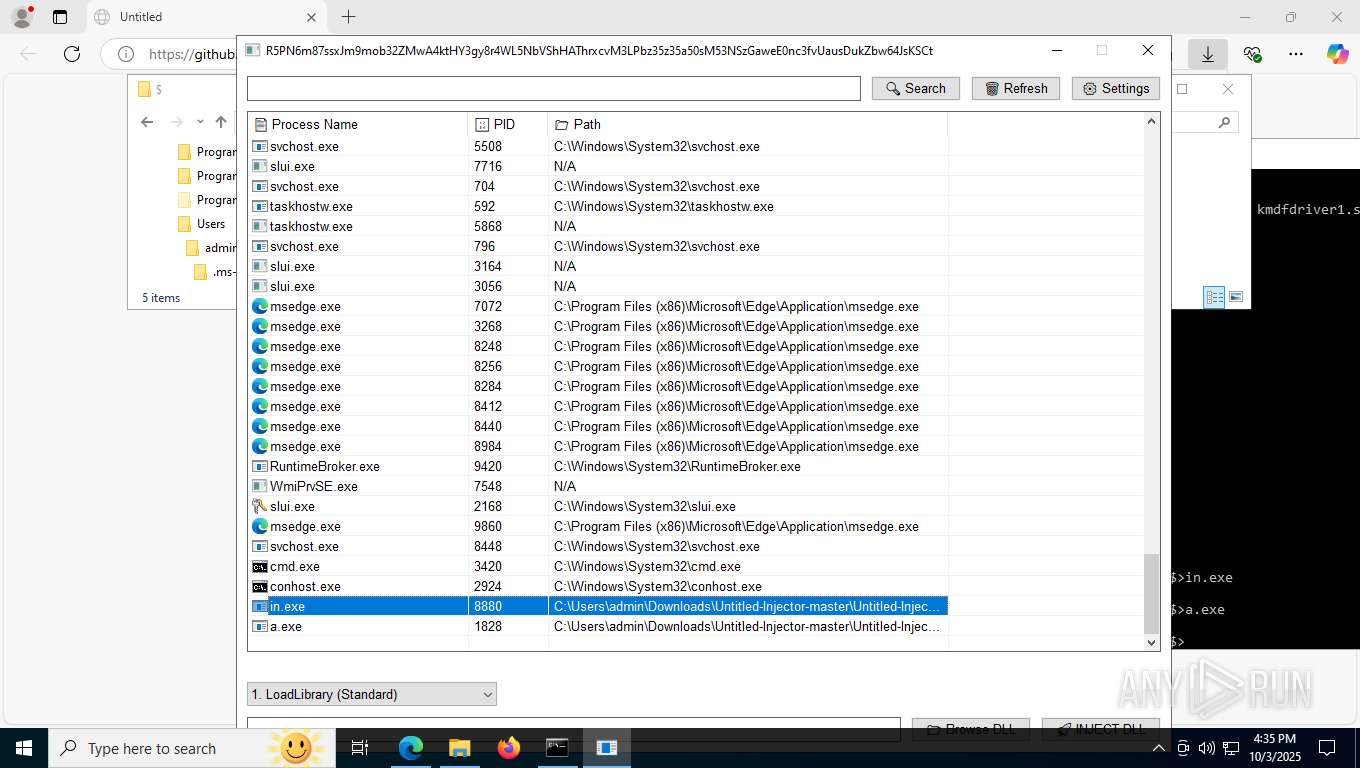
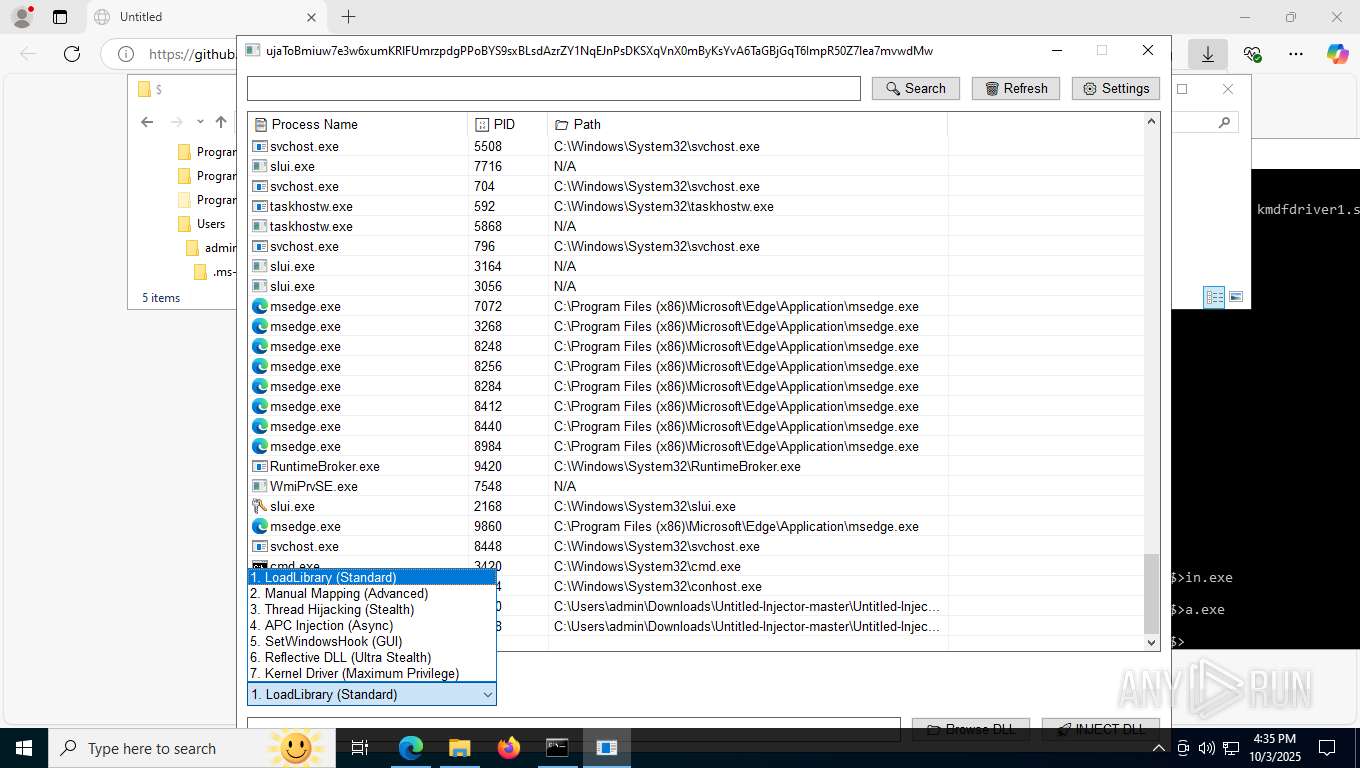
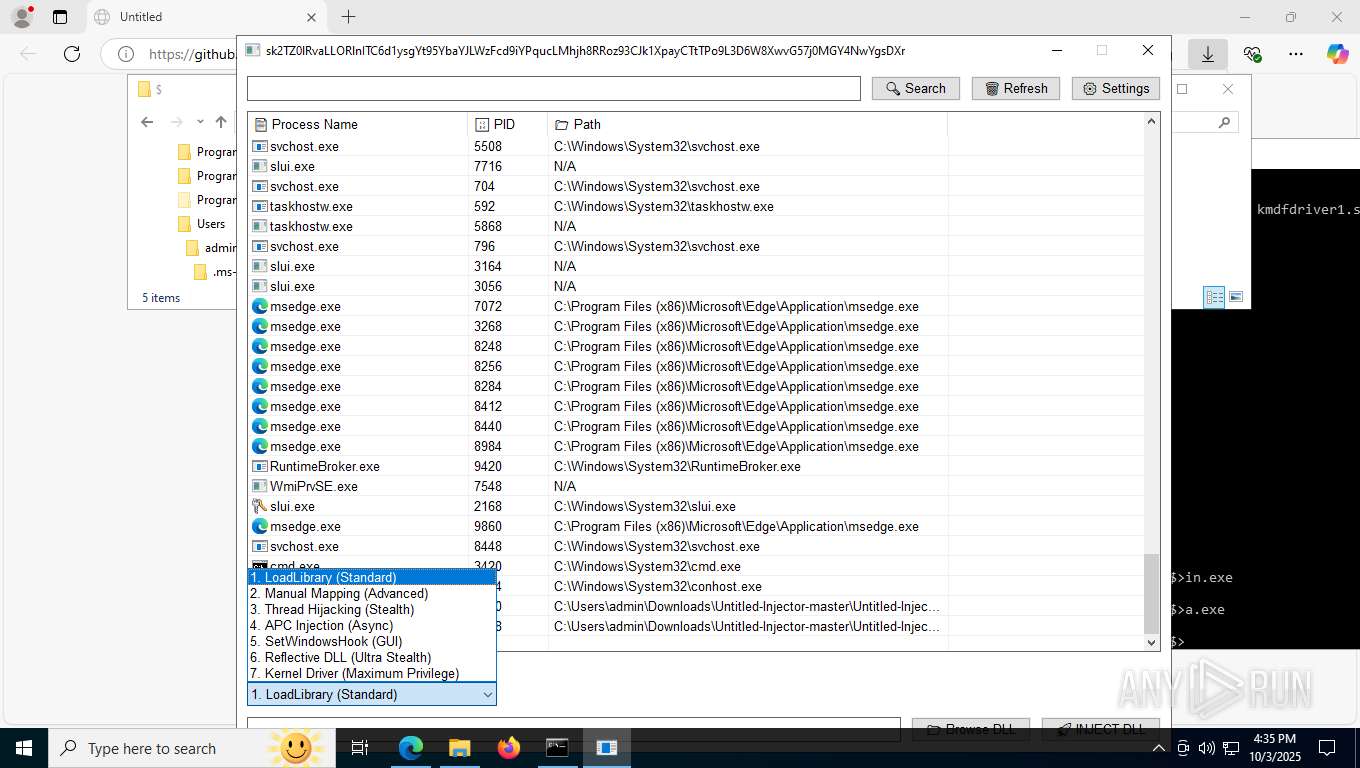
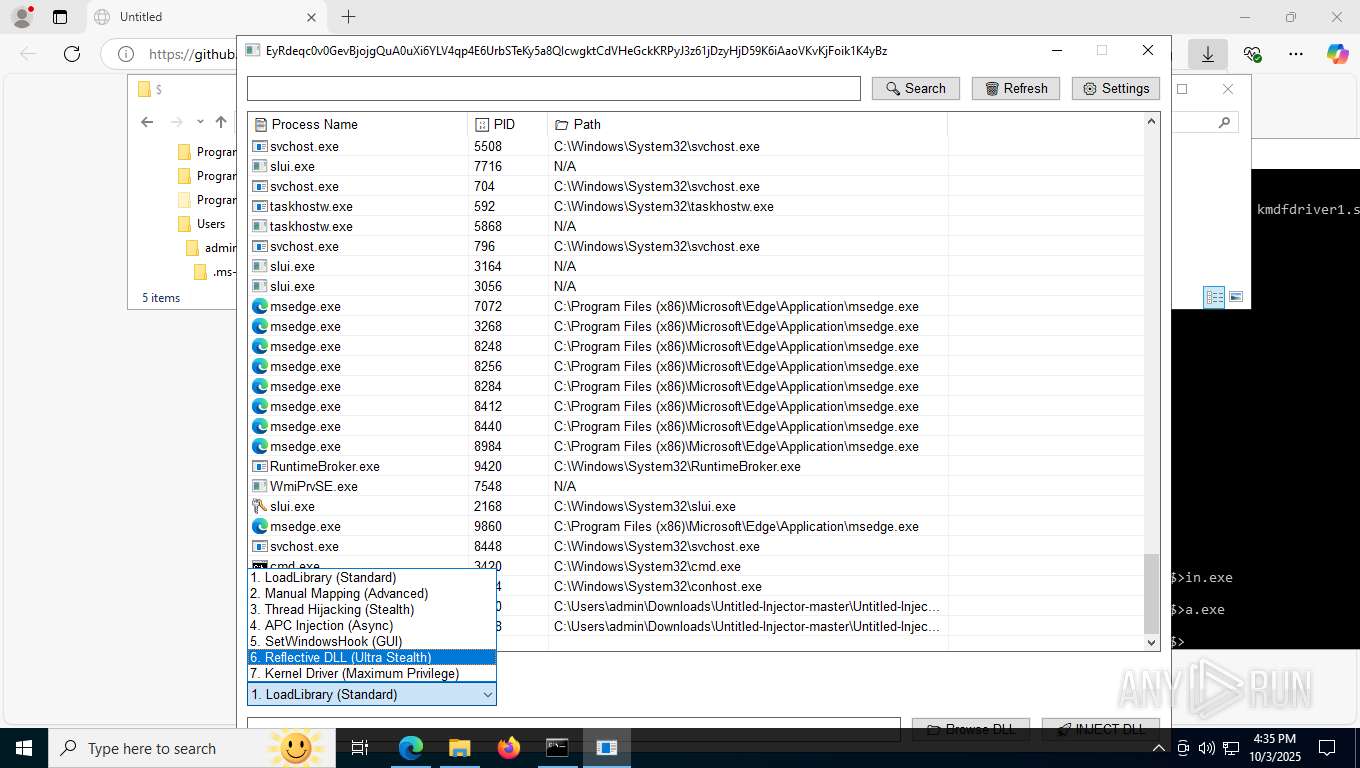
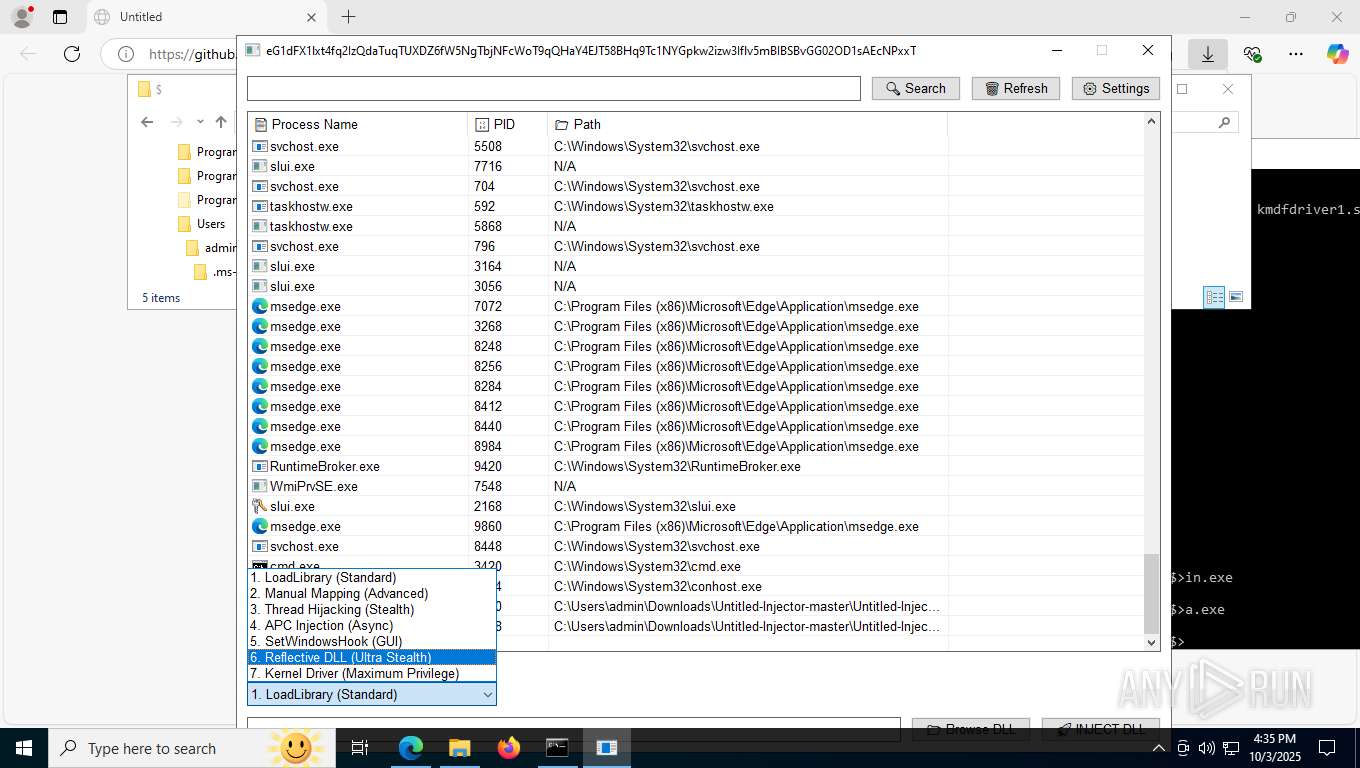
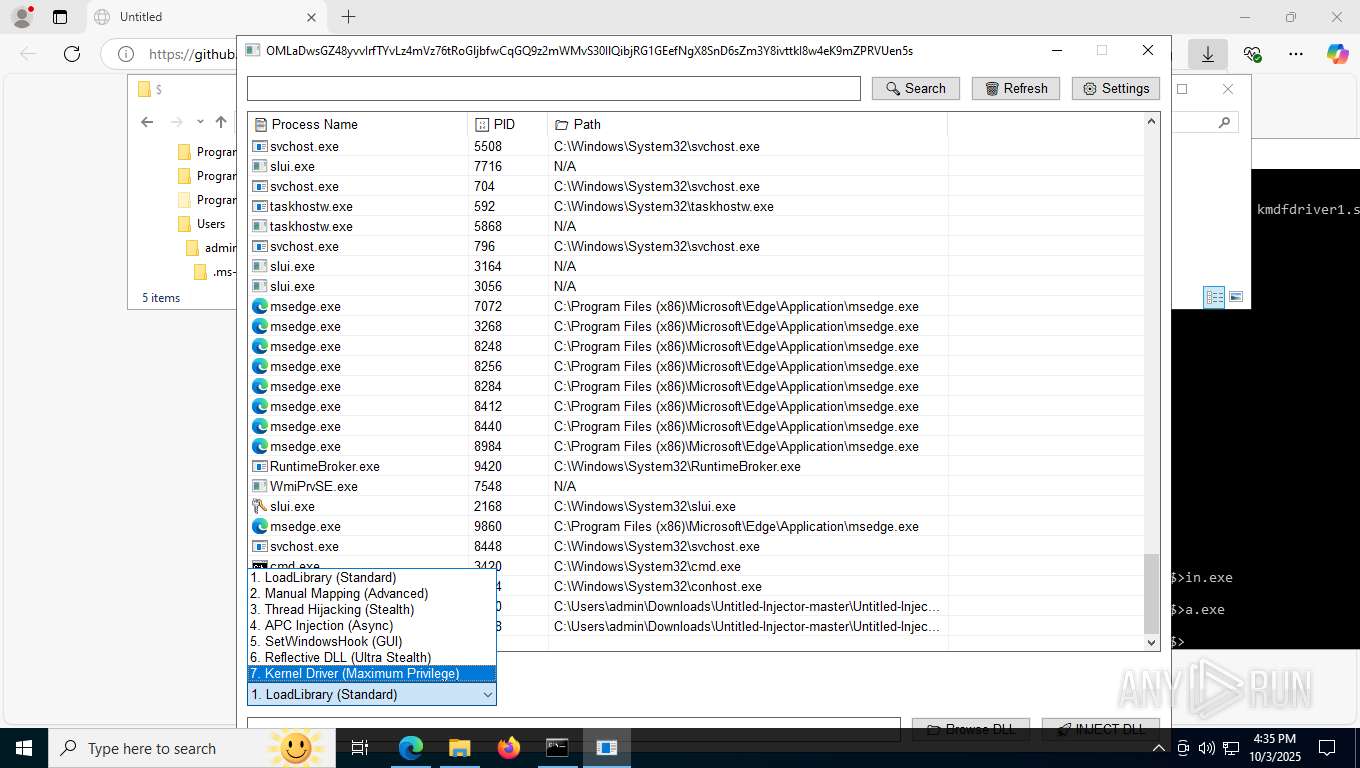
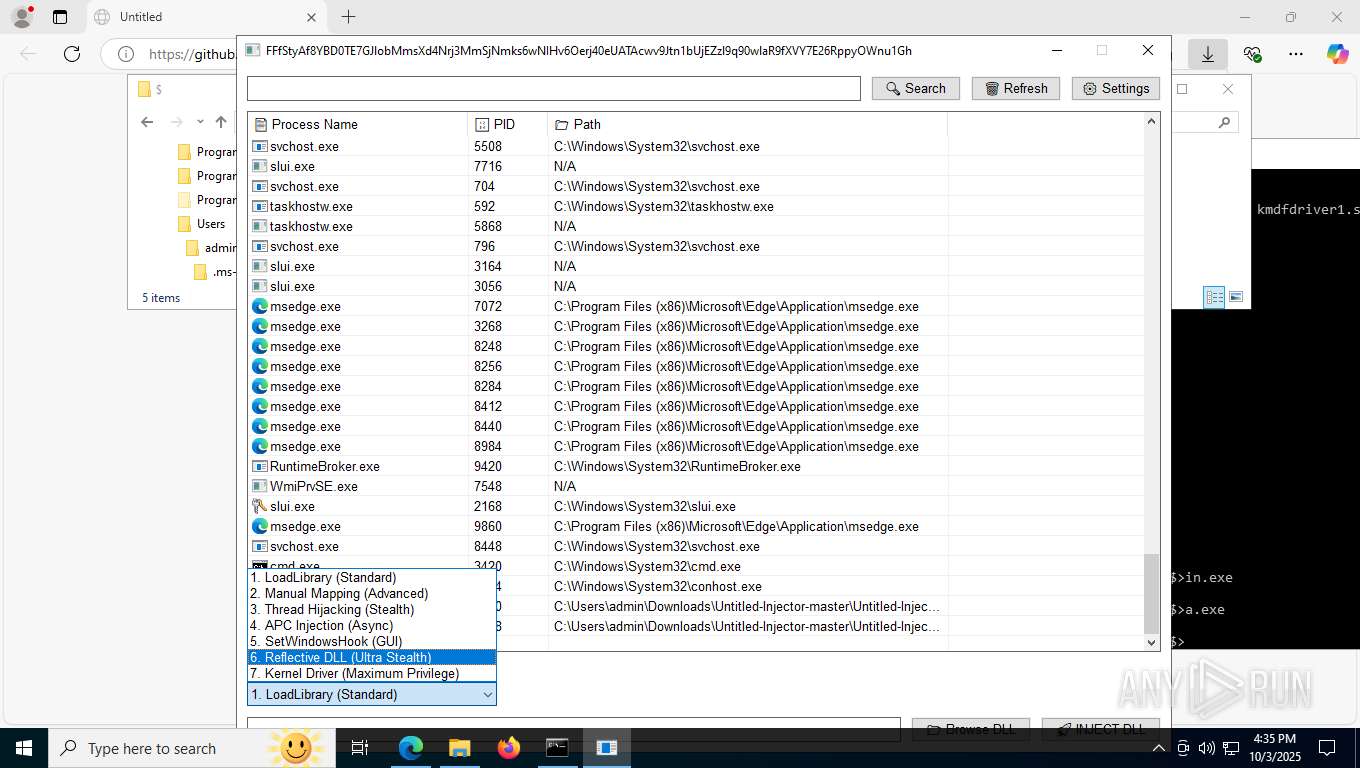
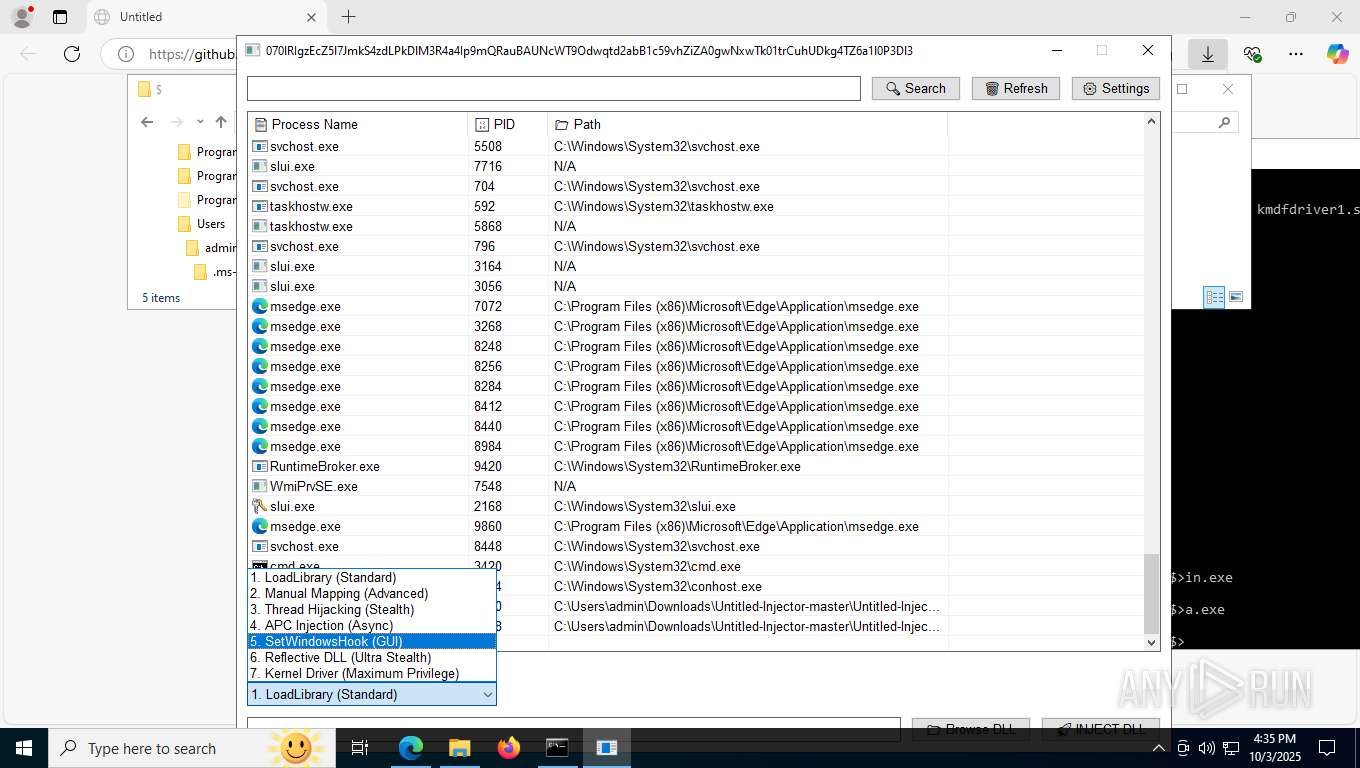
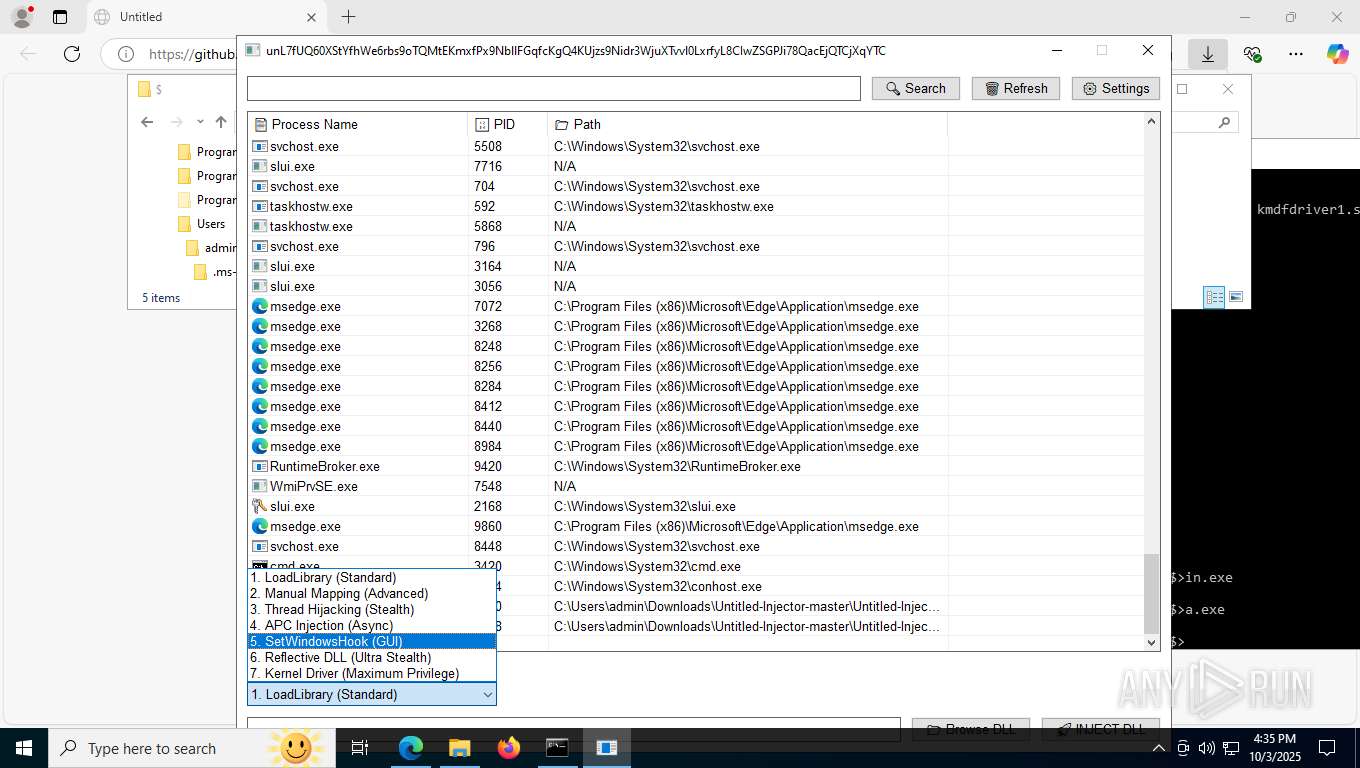
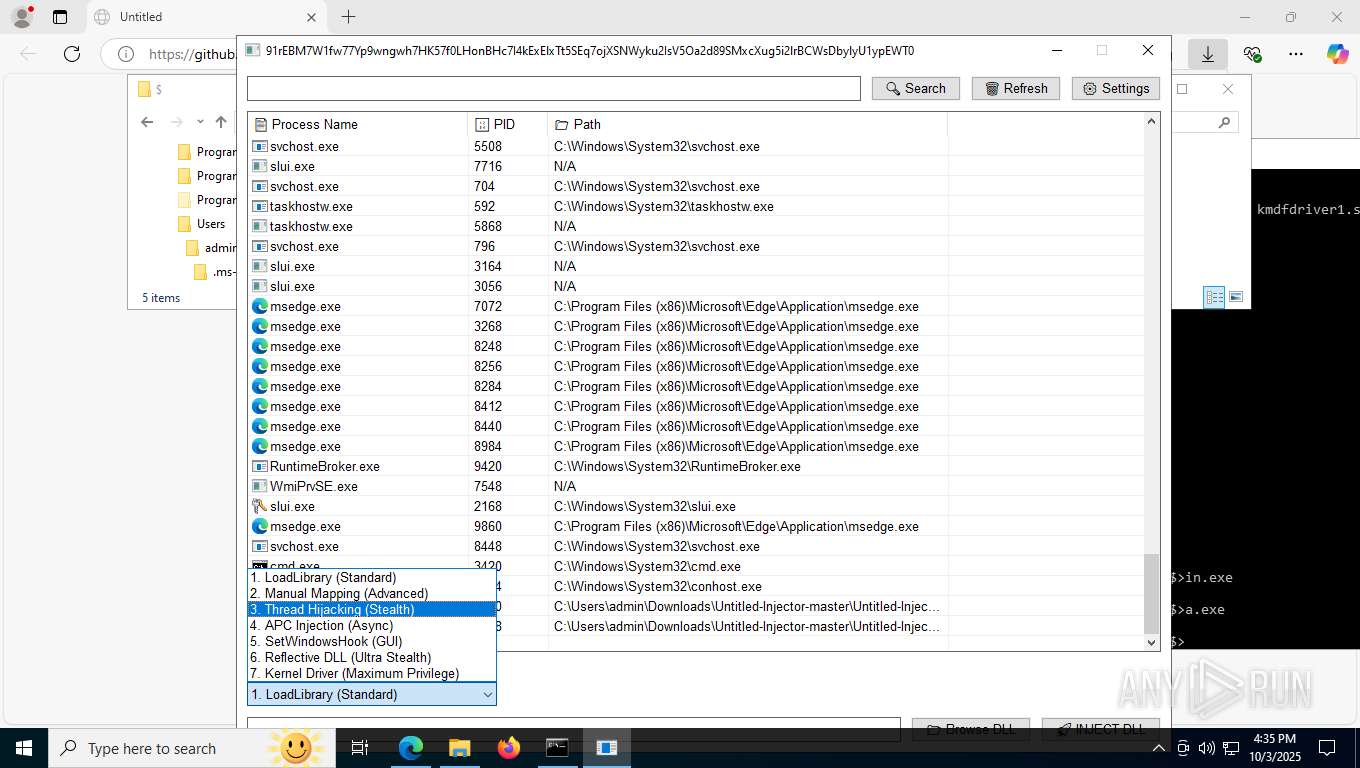
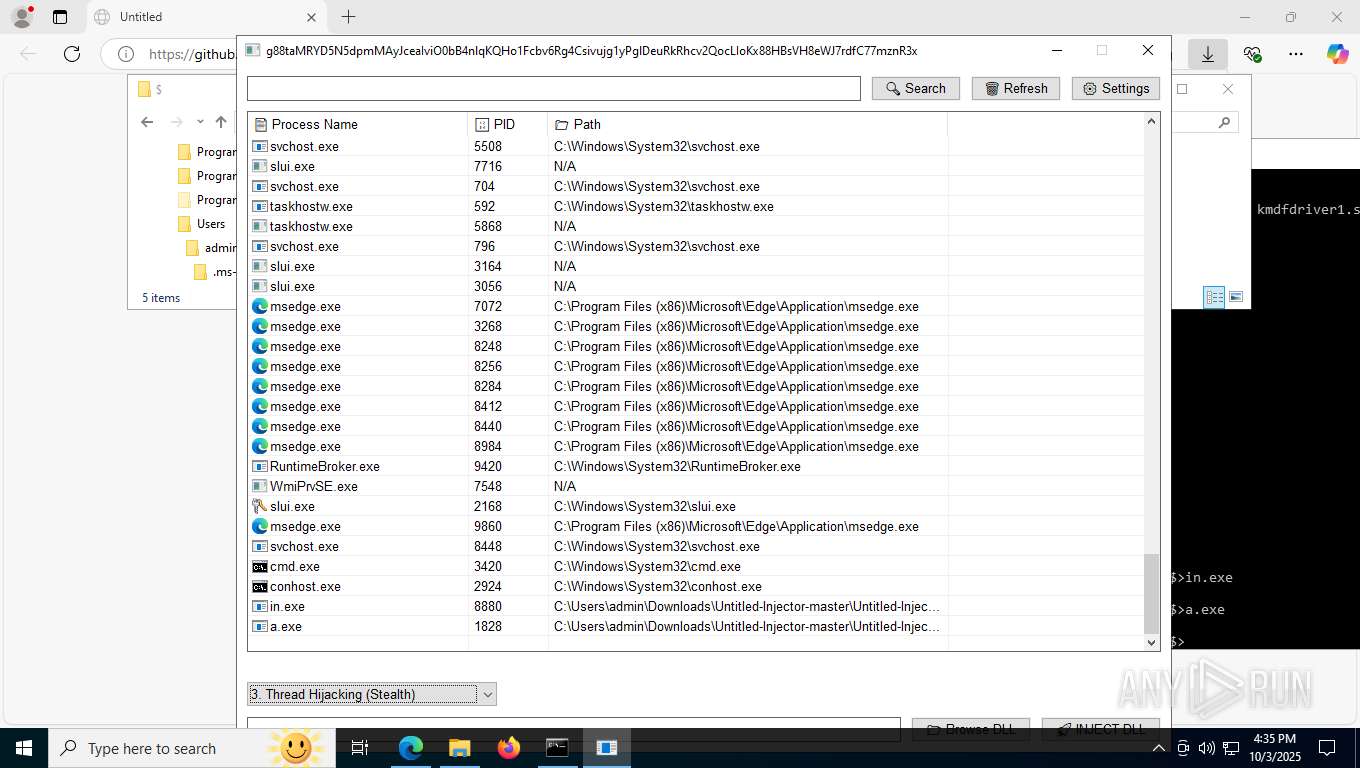
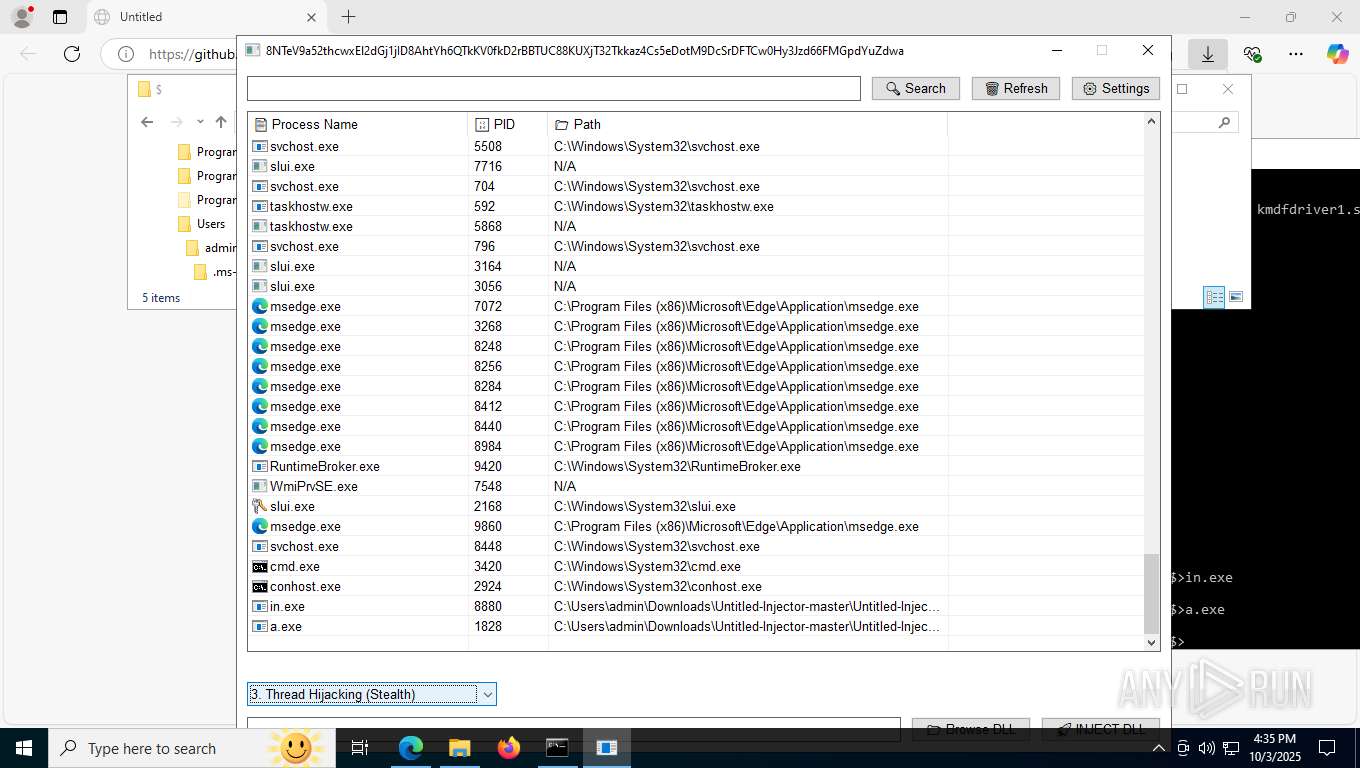
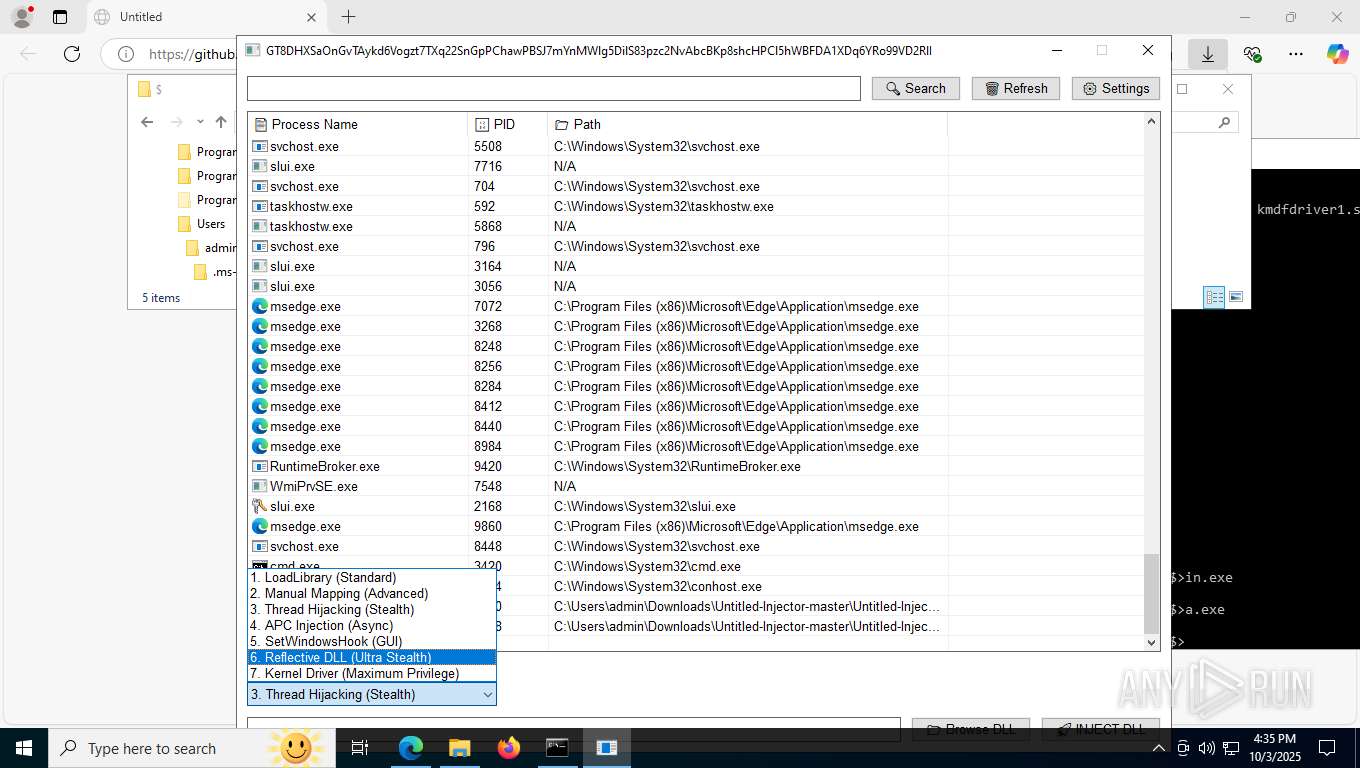
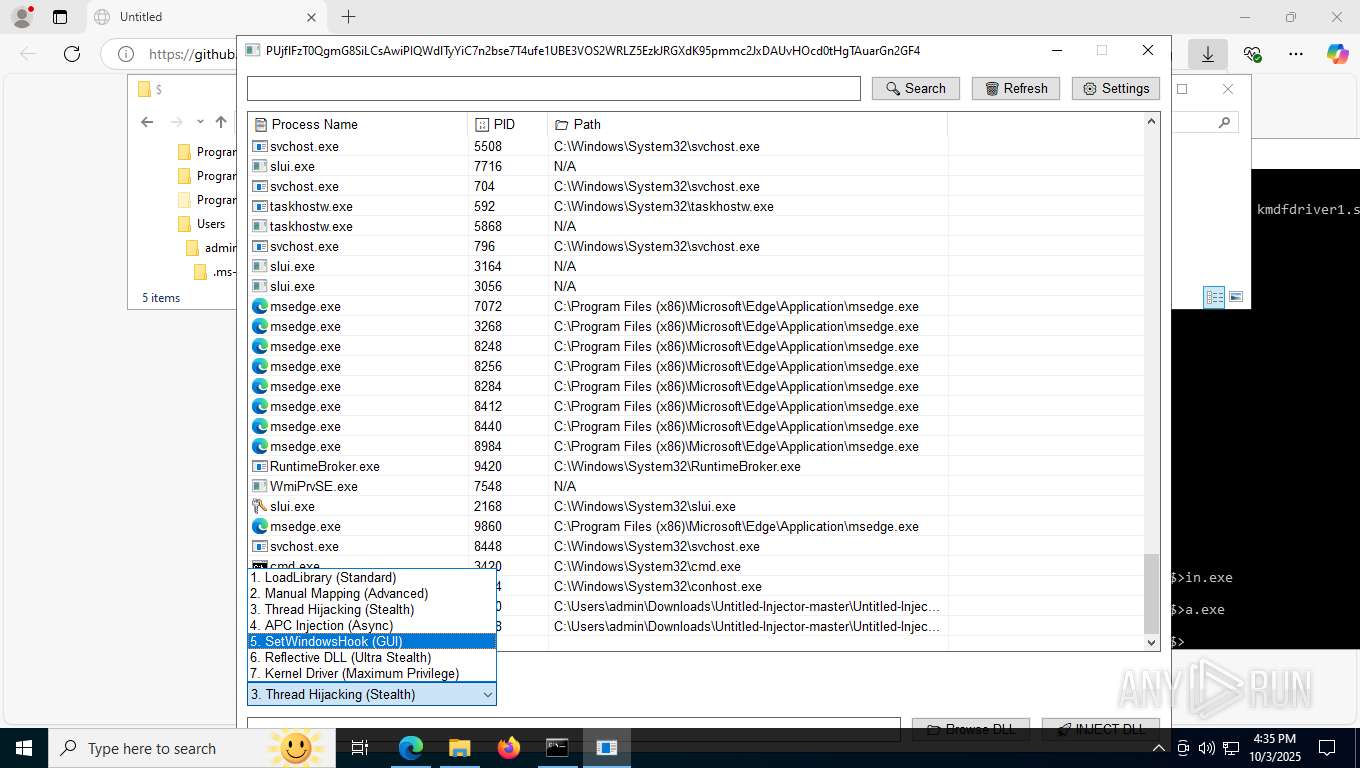
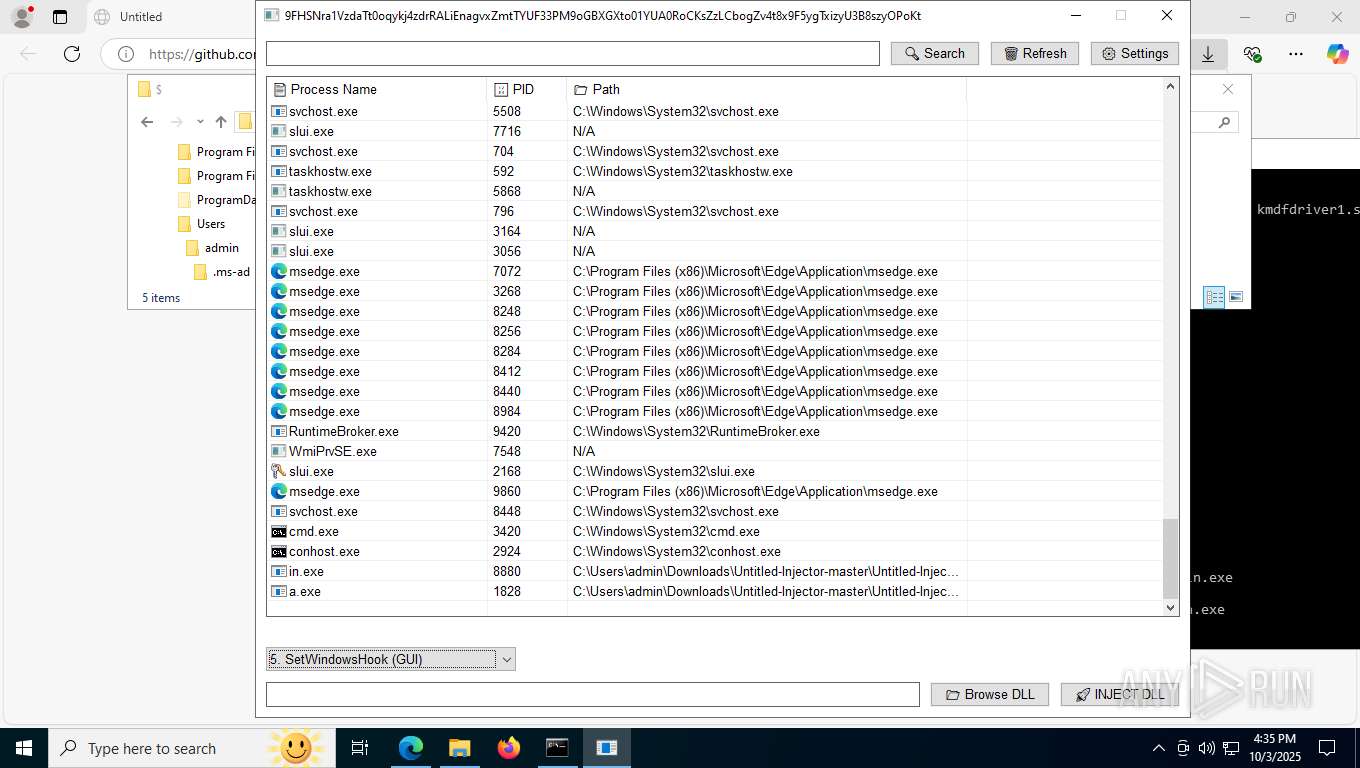
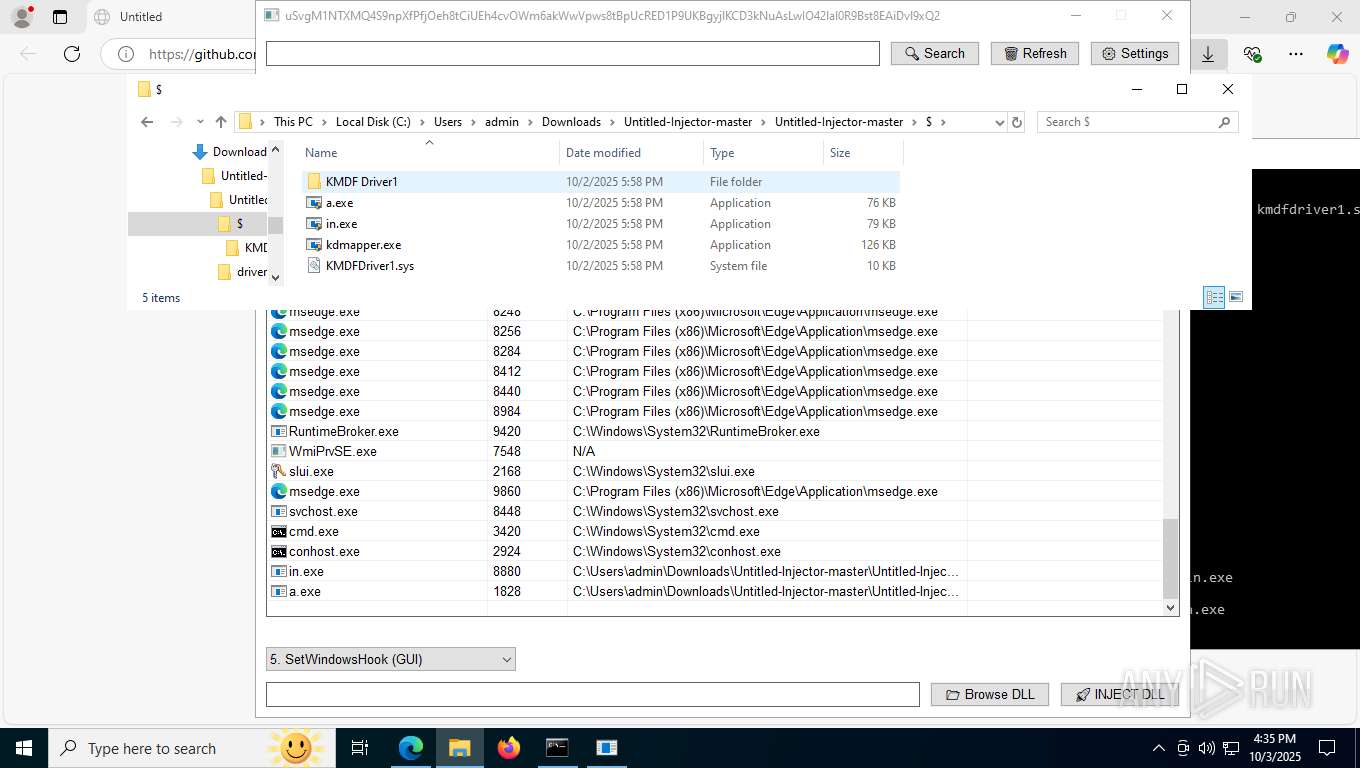
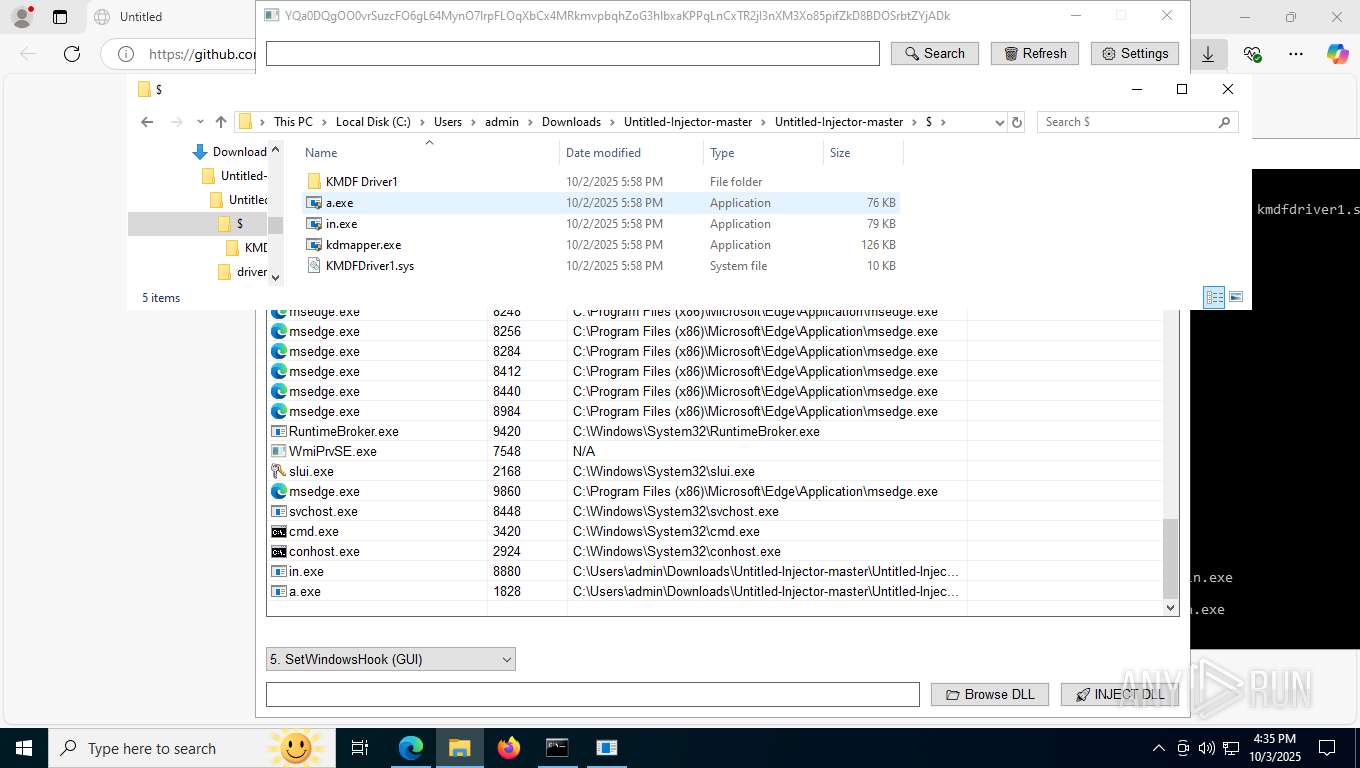
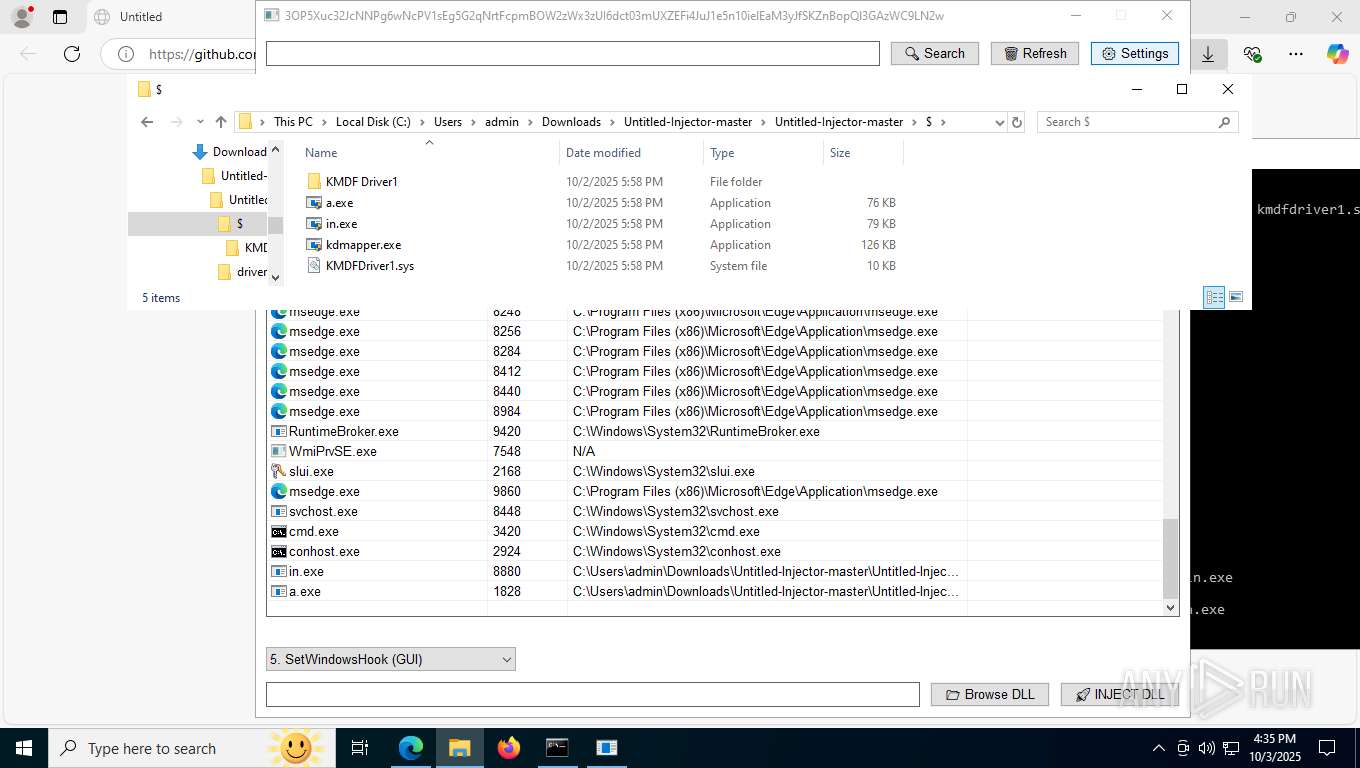
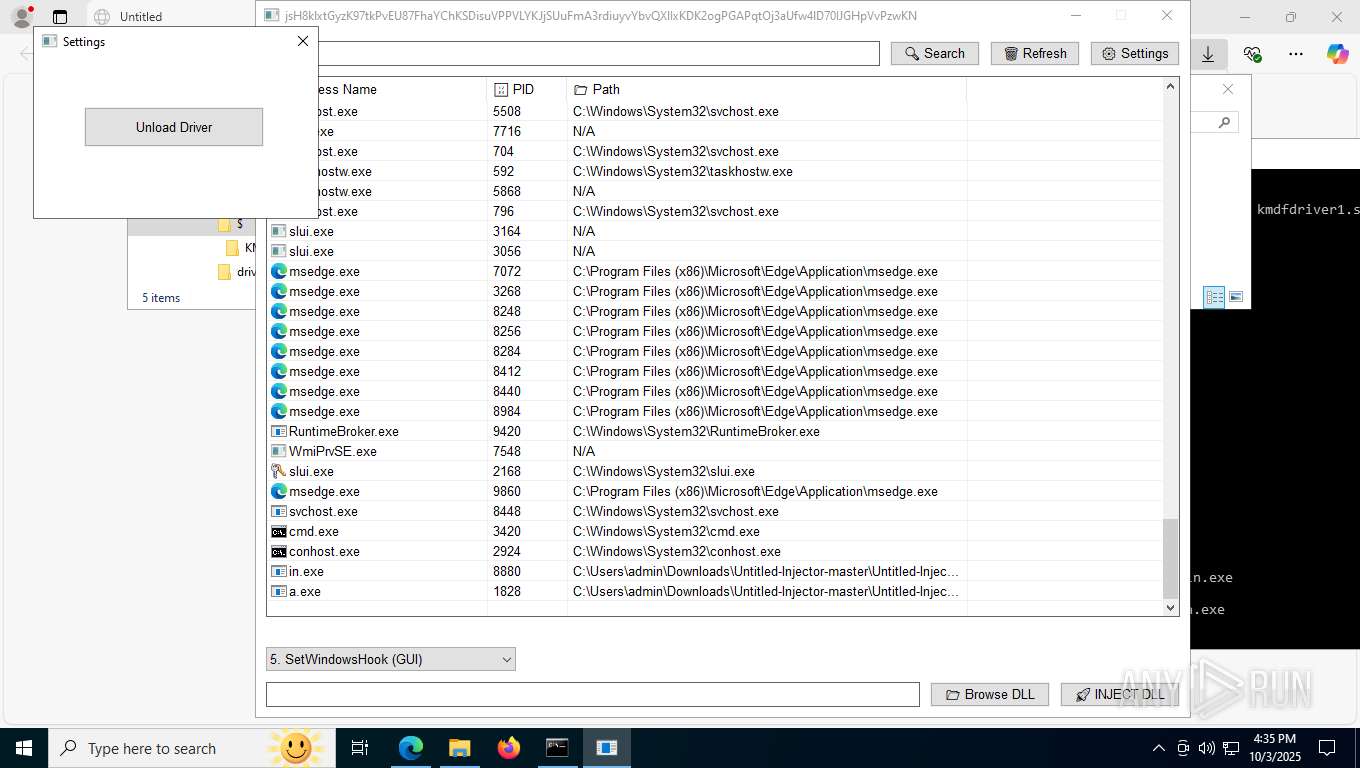
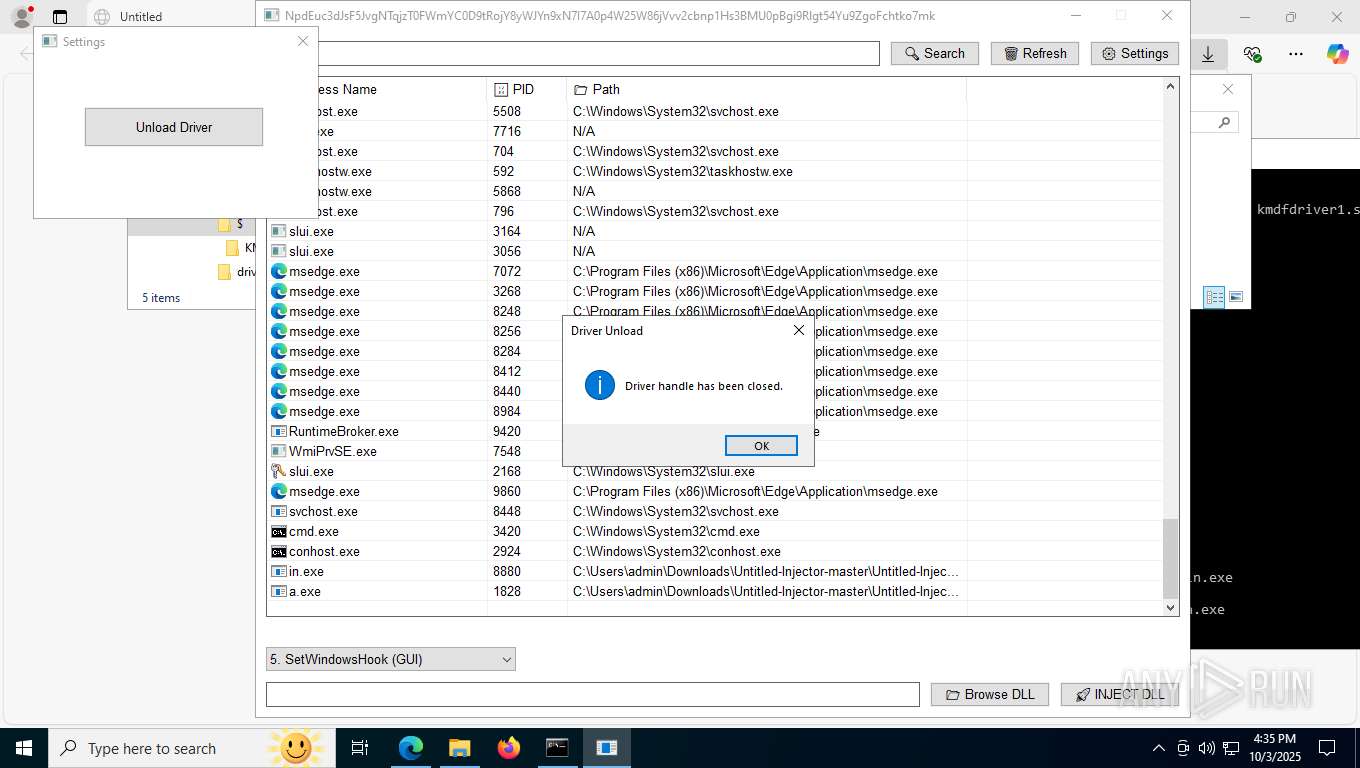
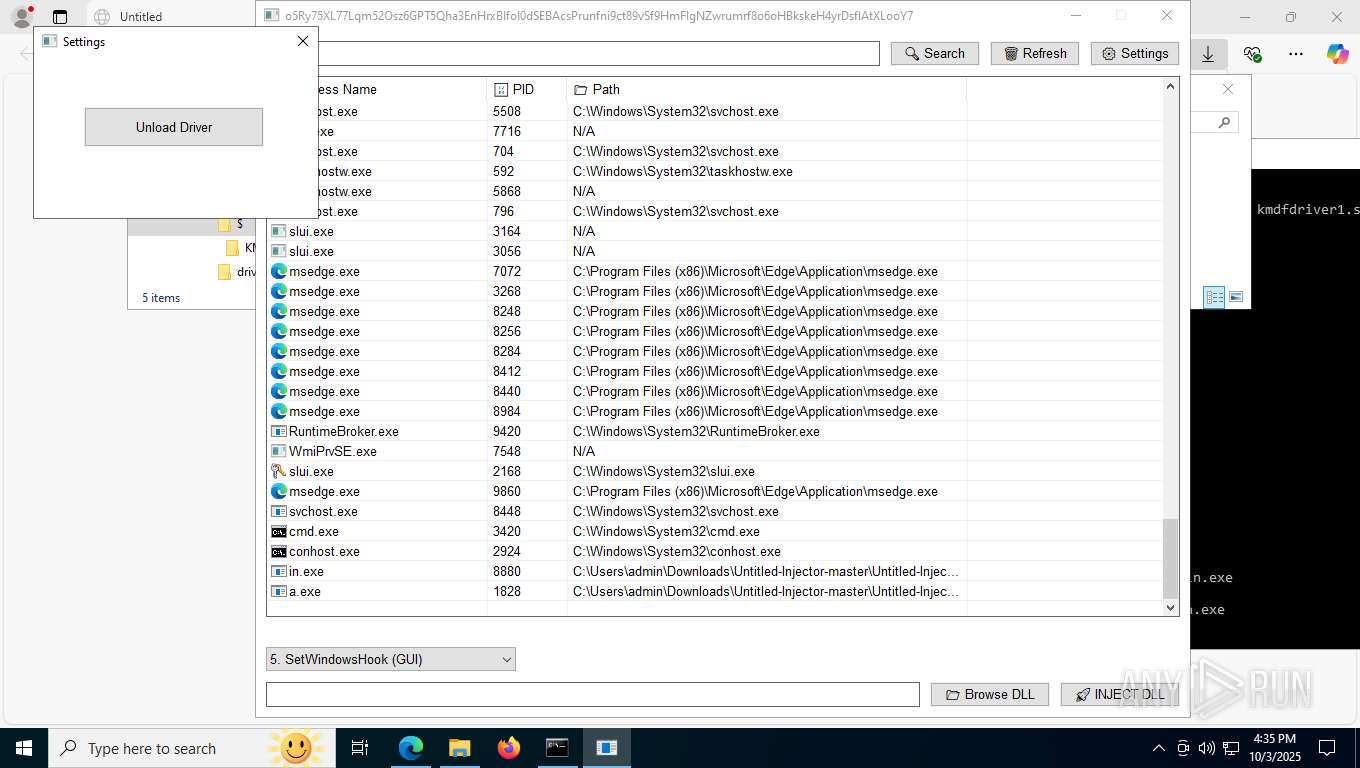
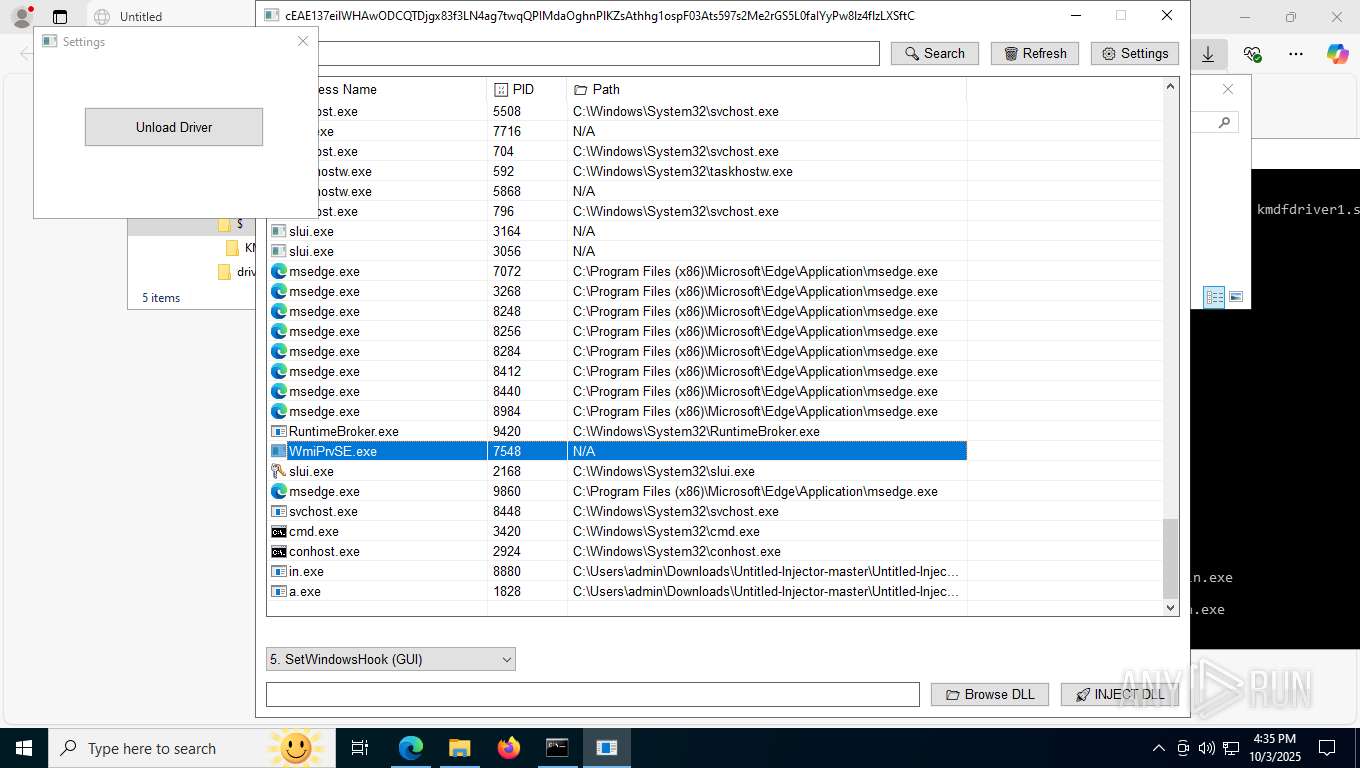
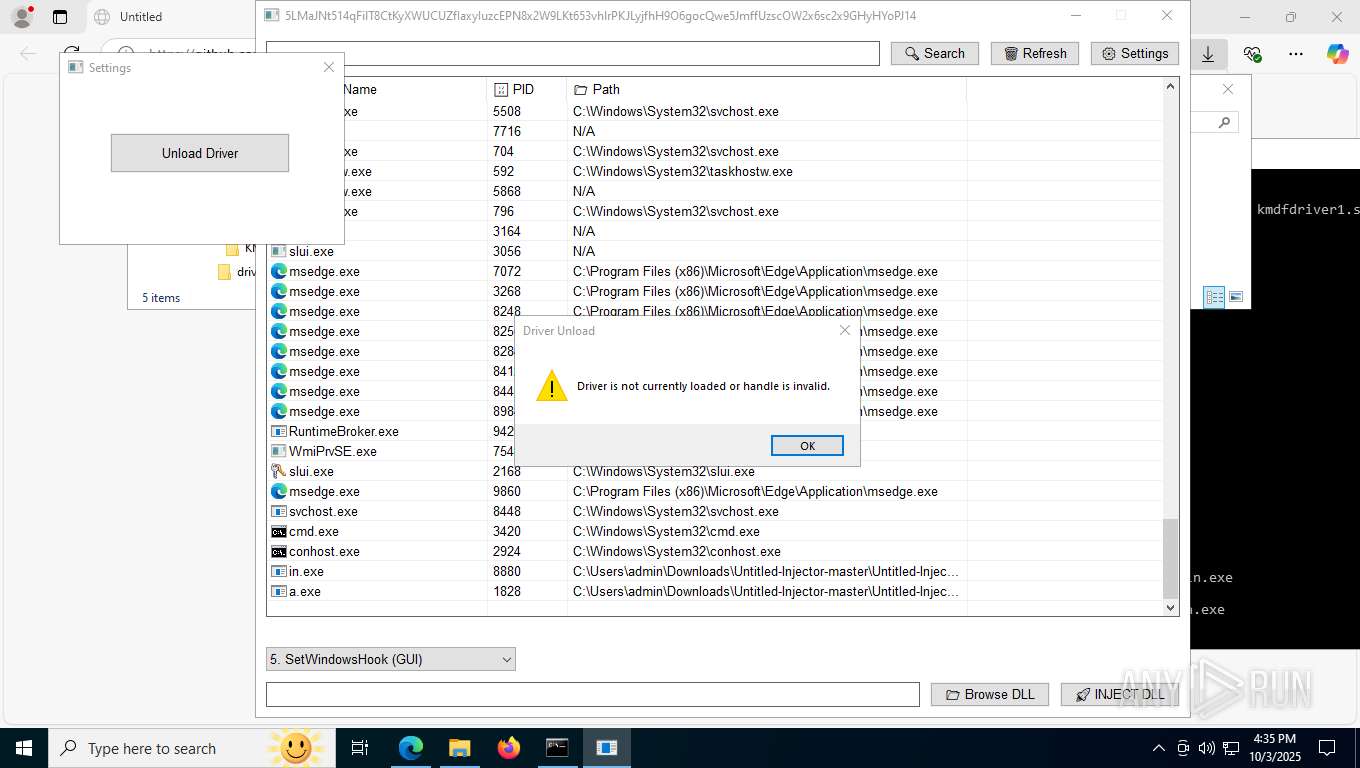
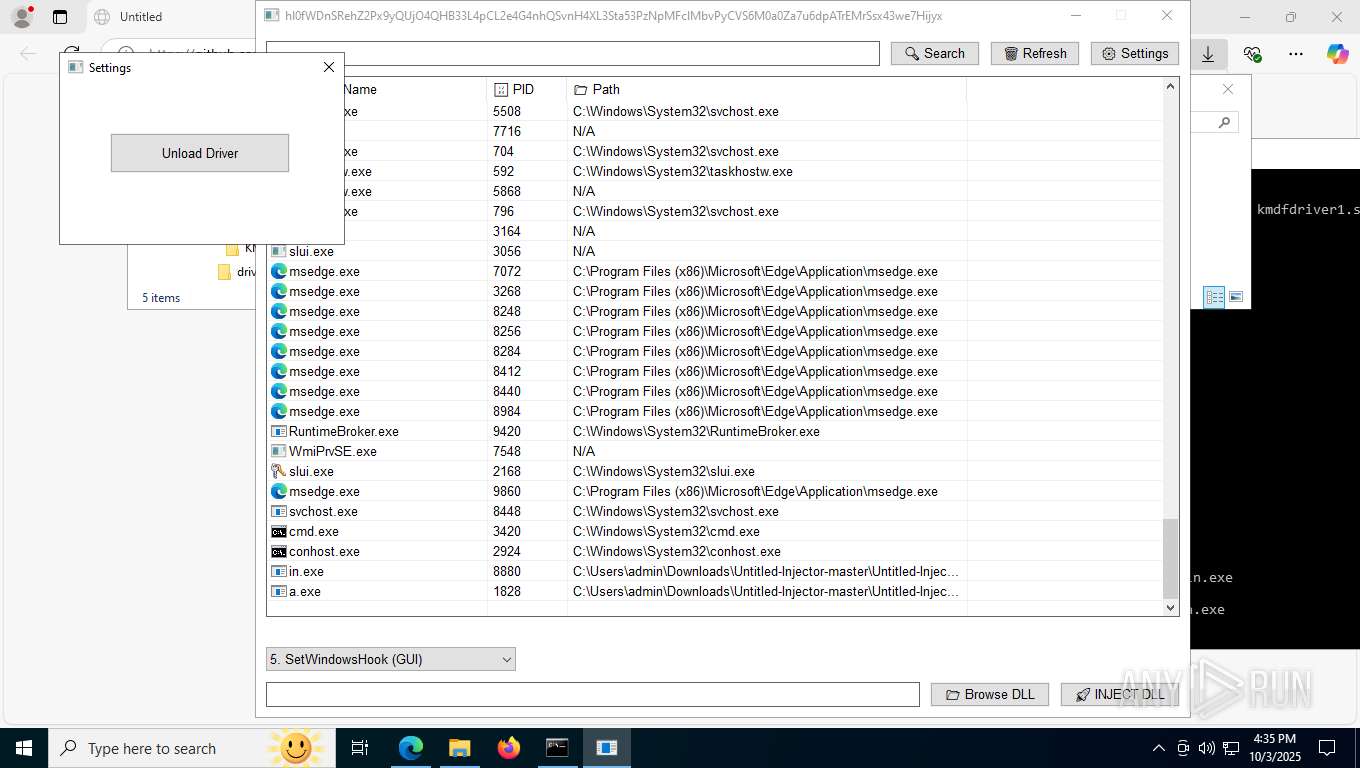
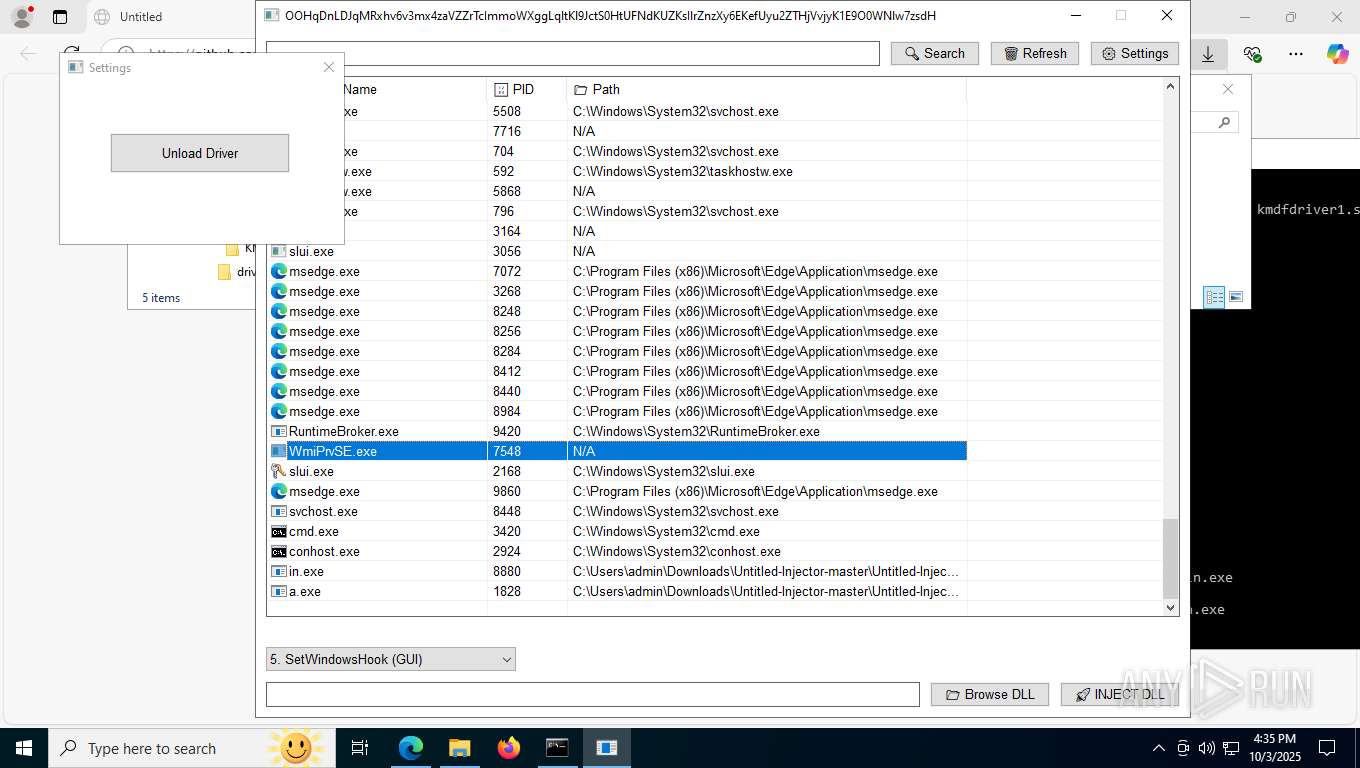
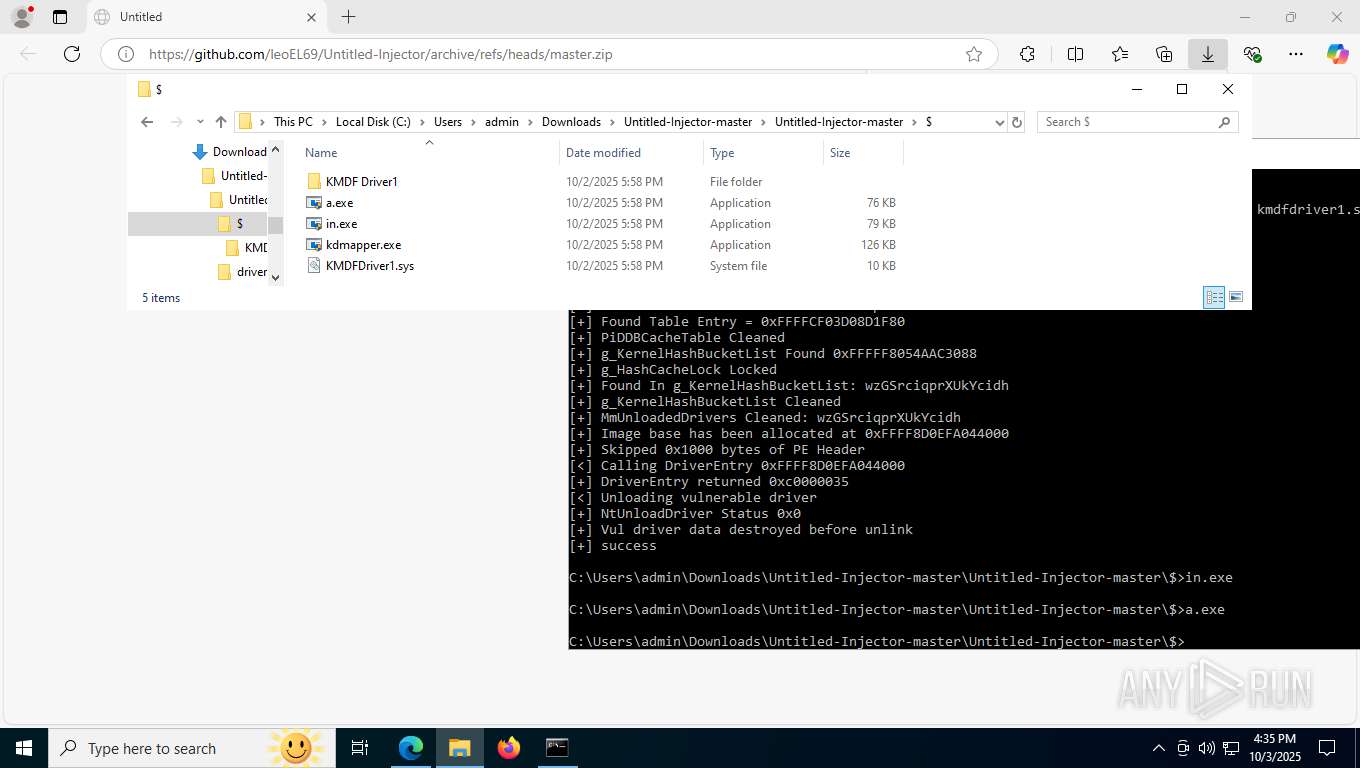
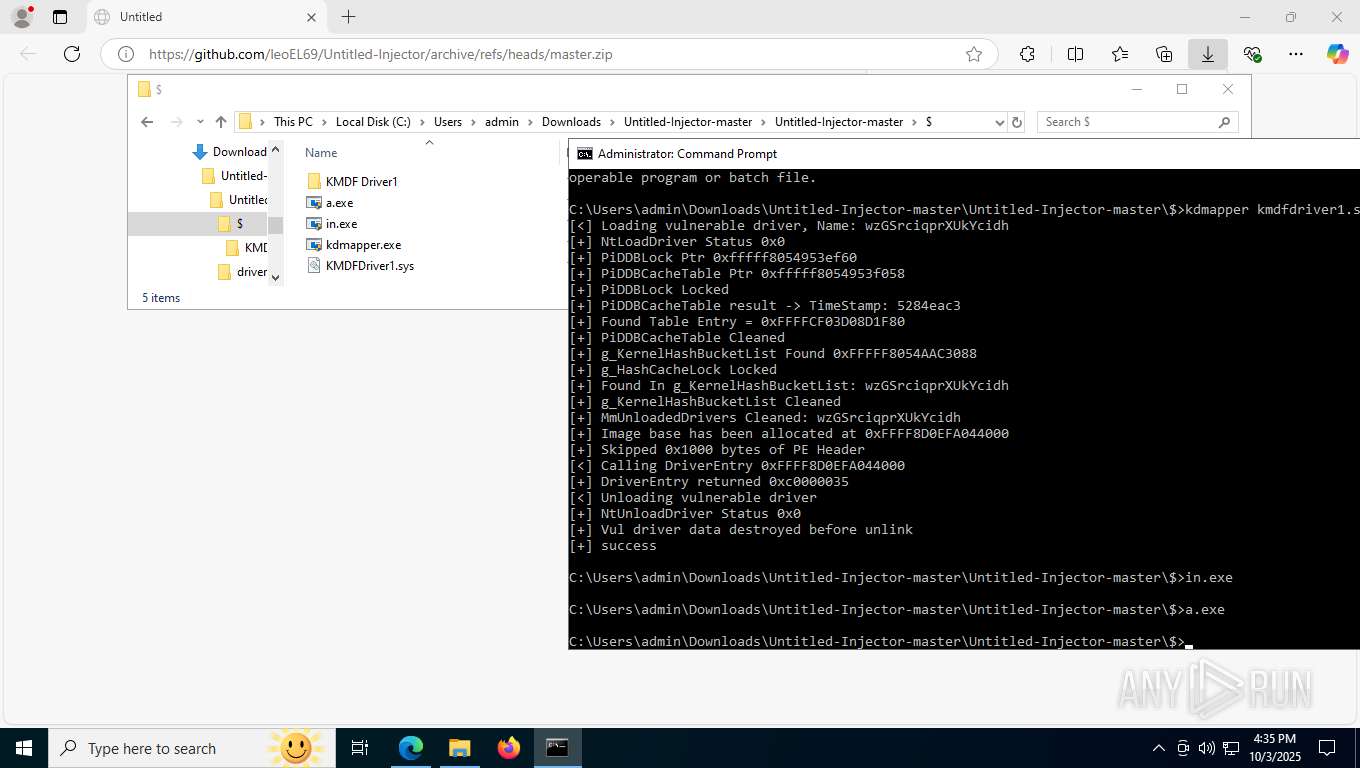
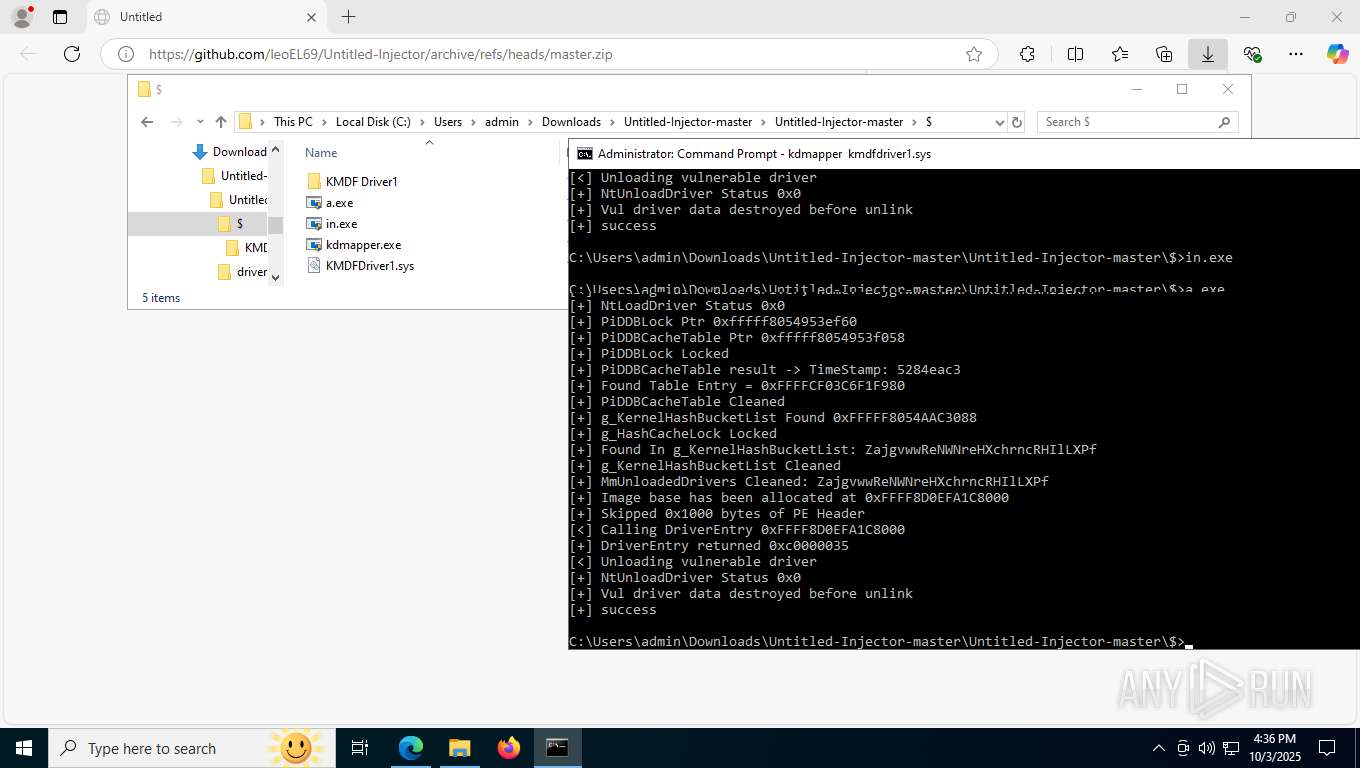
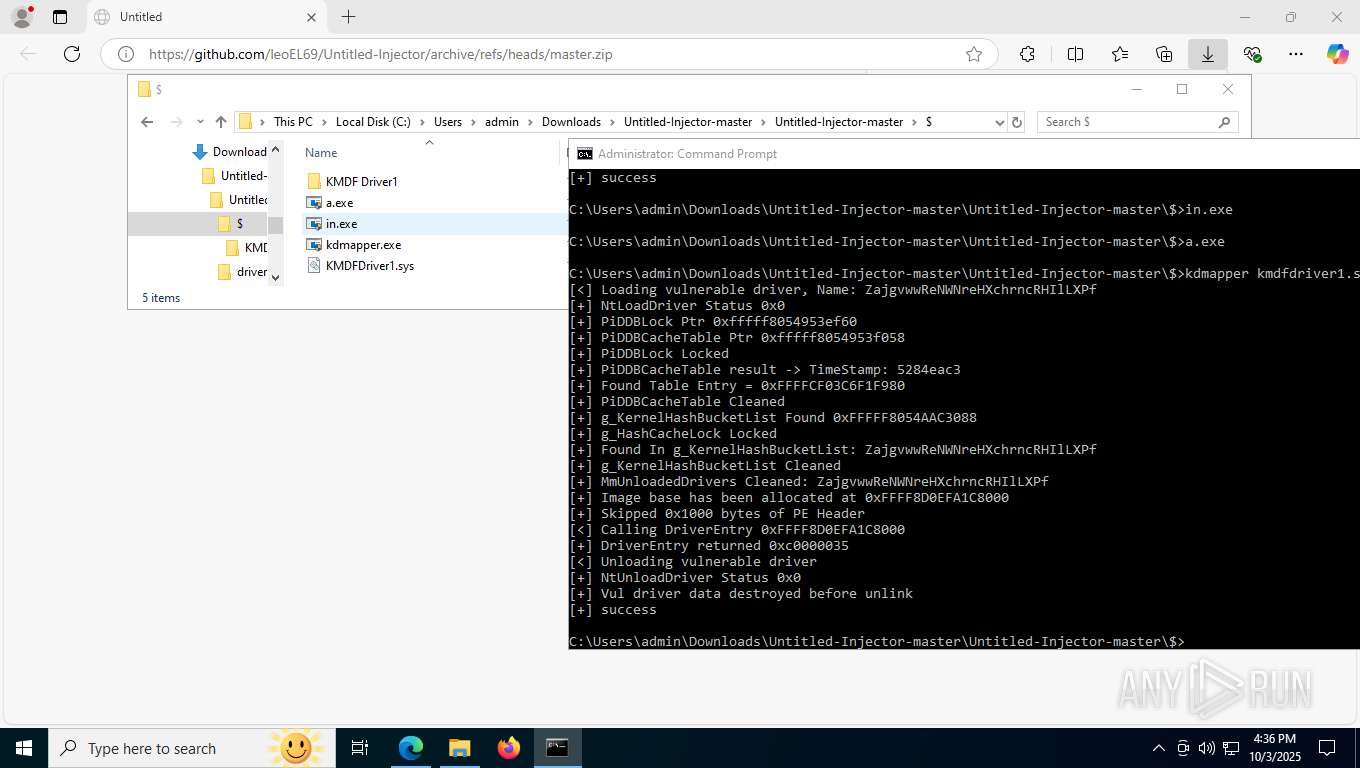
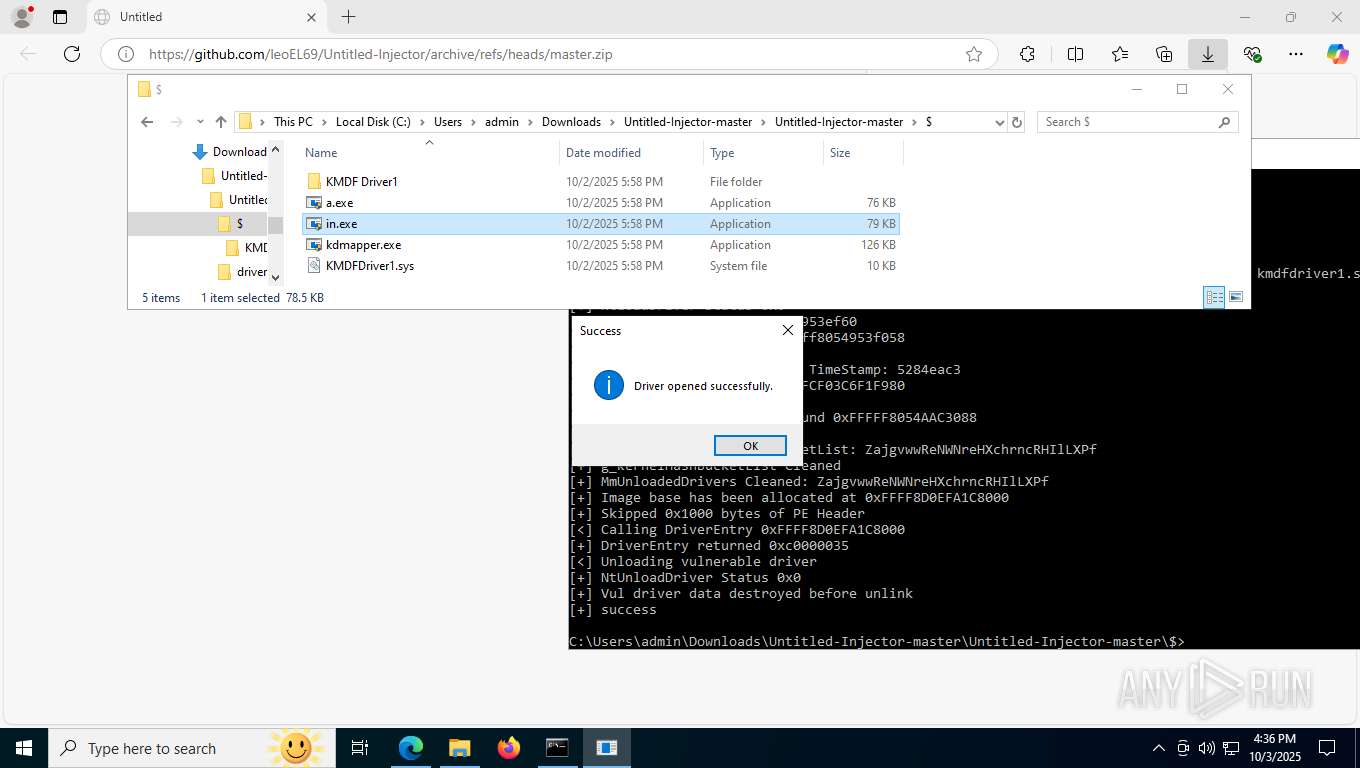
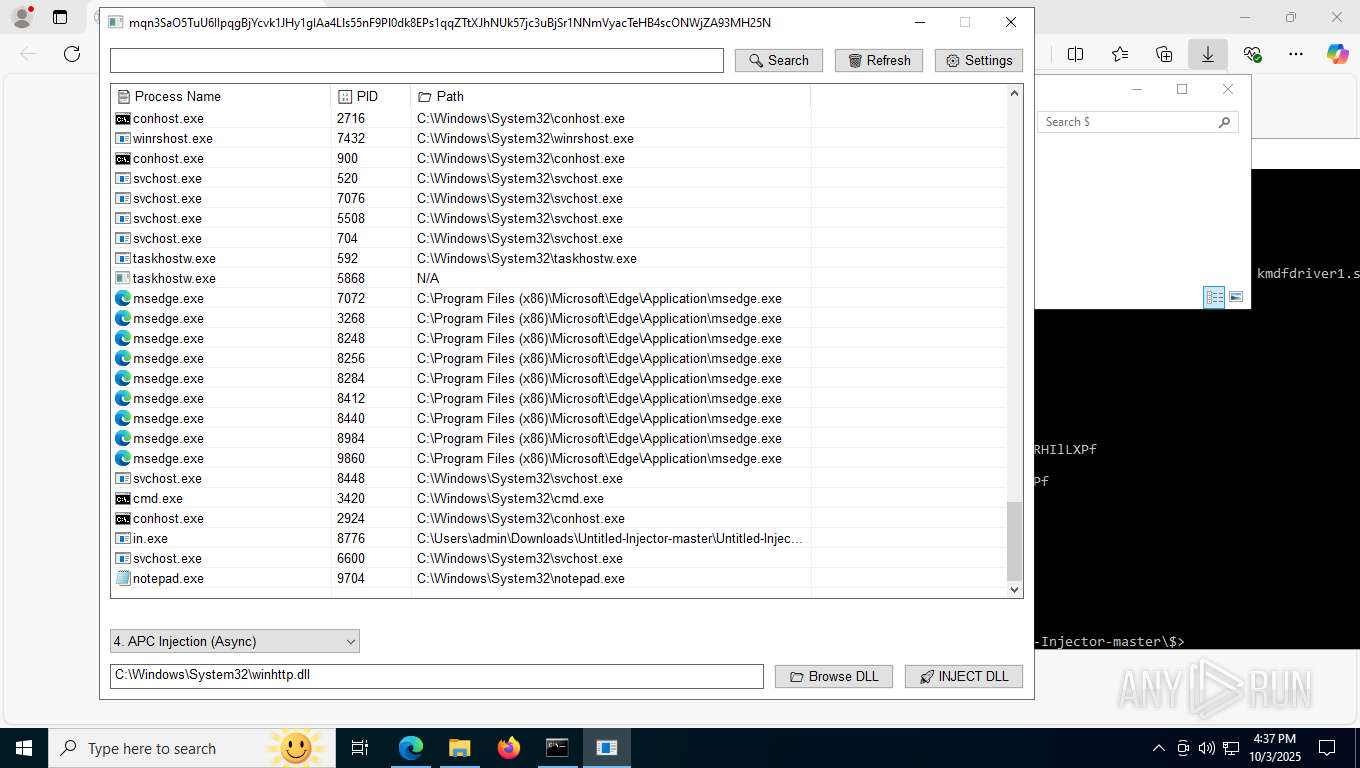
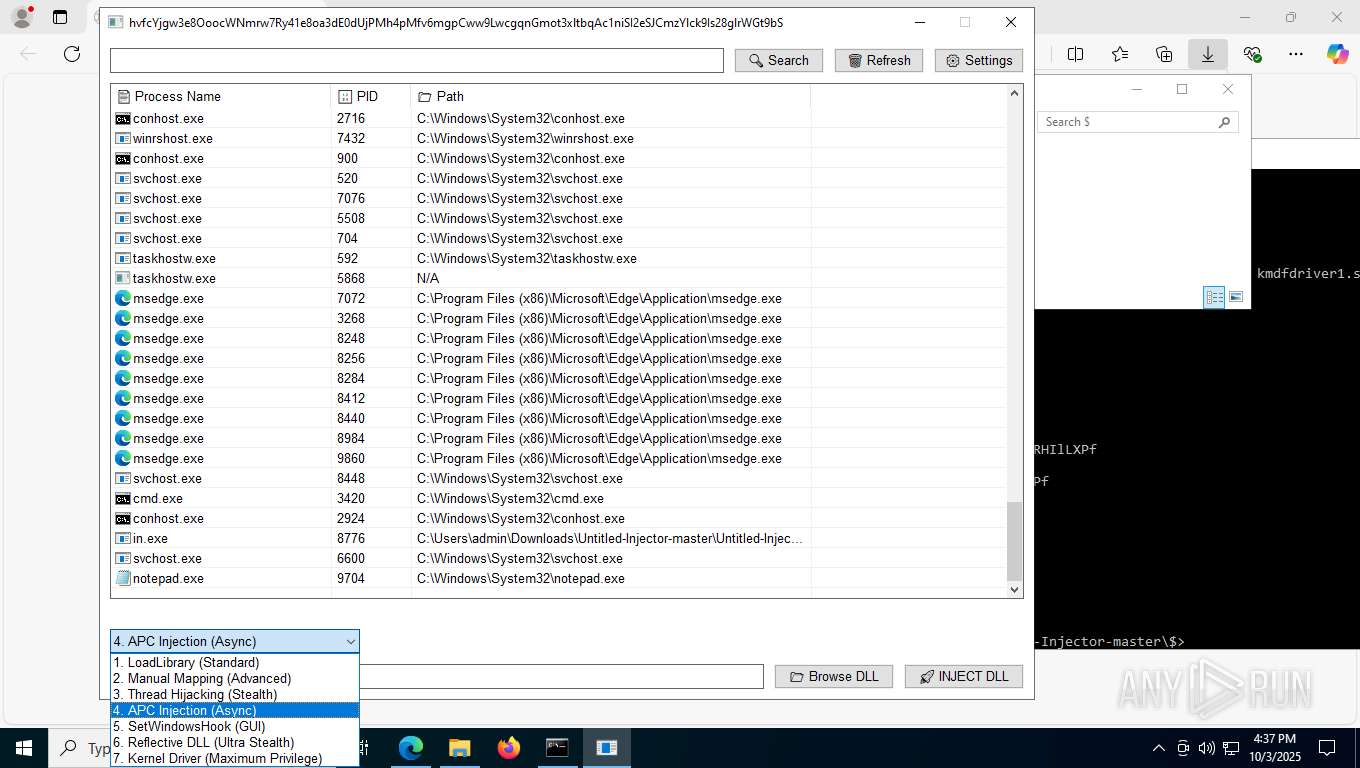
MALICIOUS
Vulnerable driver has been detected
- kdmapper.exe (PID: 9656)
- kdmapper.exe (PID: 9600)
- kdmapper.exe (PID: 1476)
SUSPICIOUS
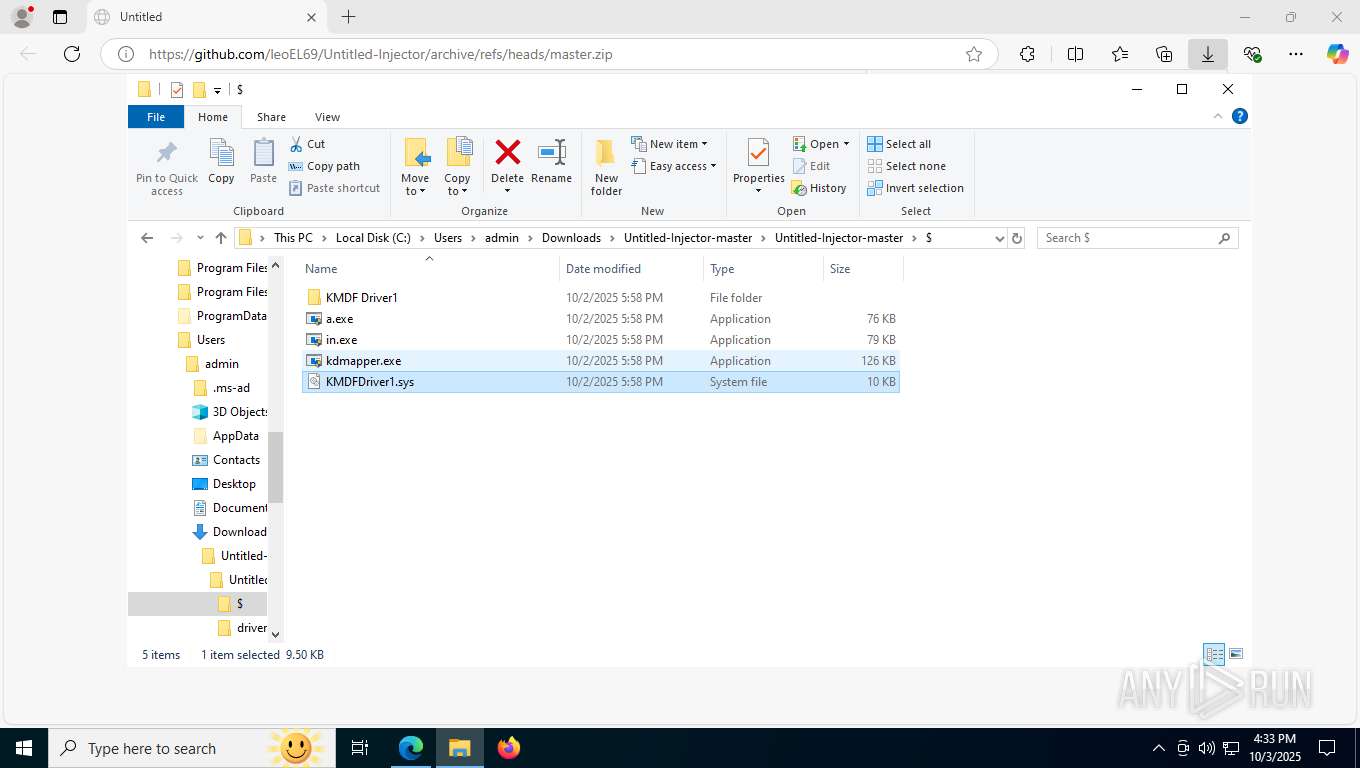
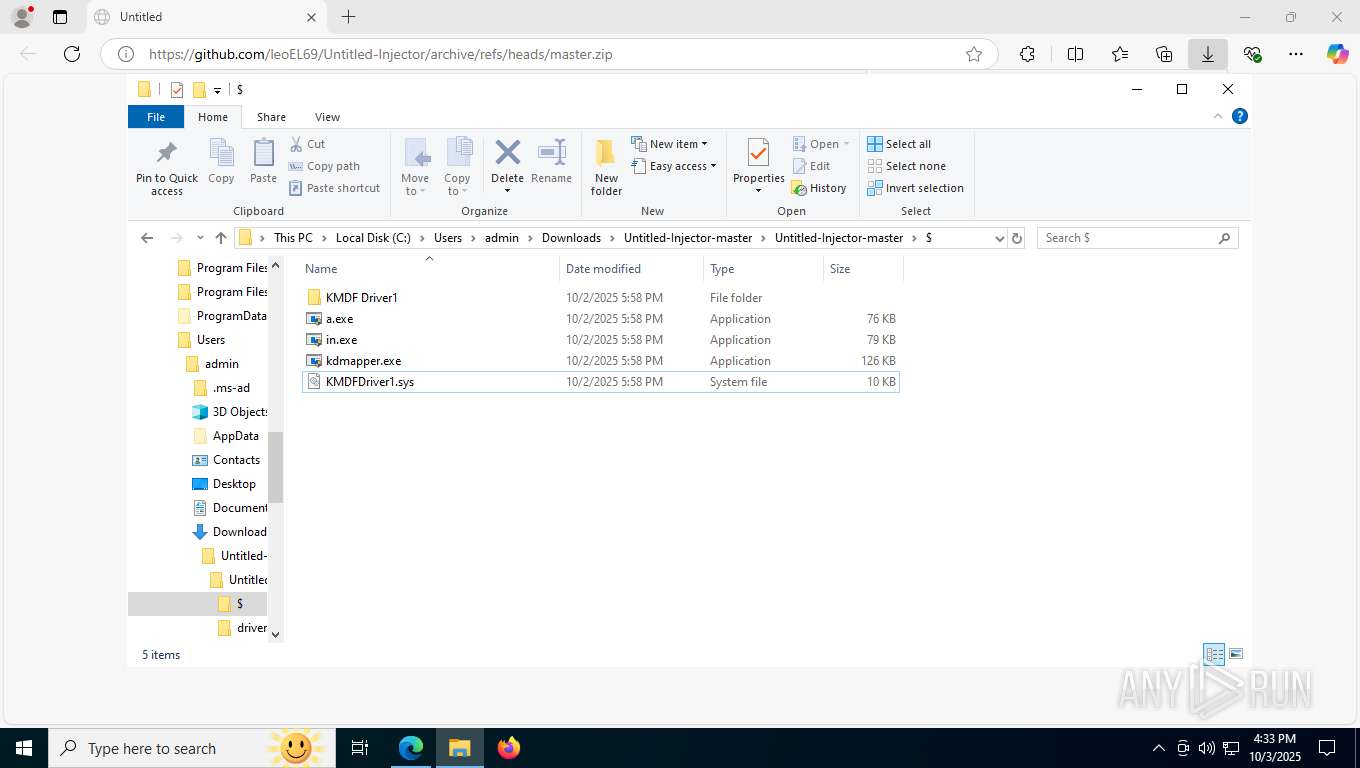
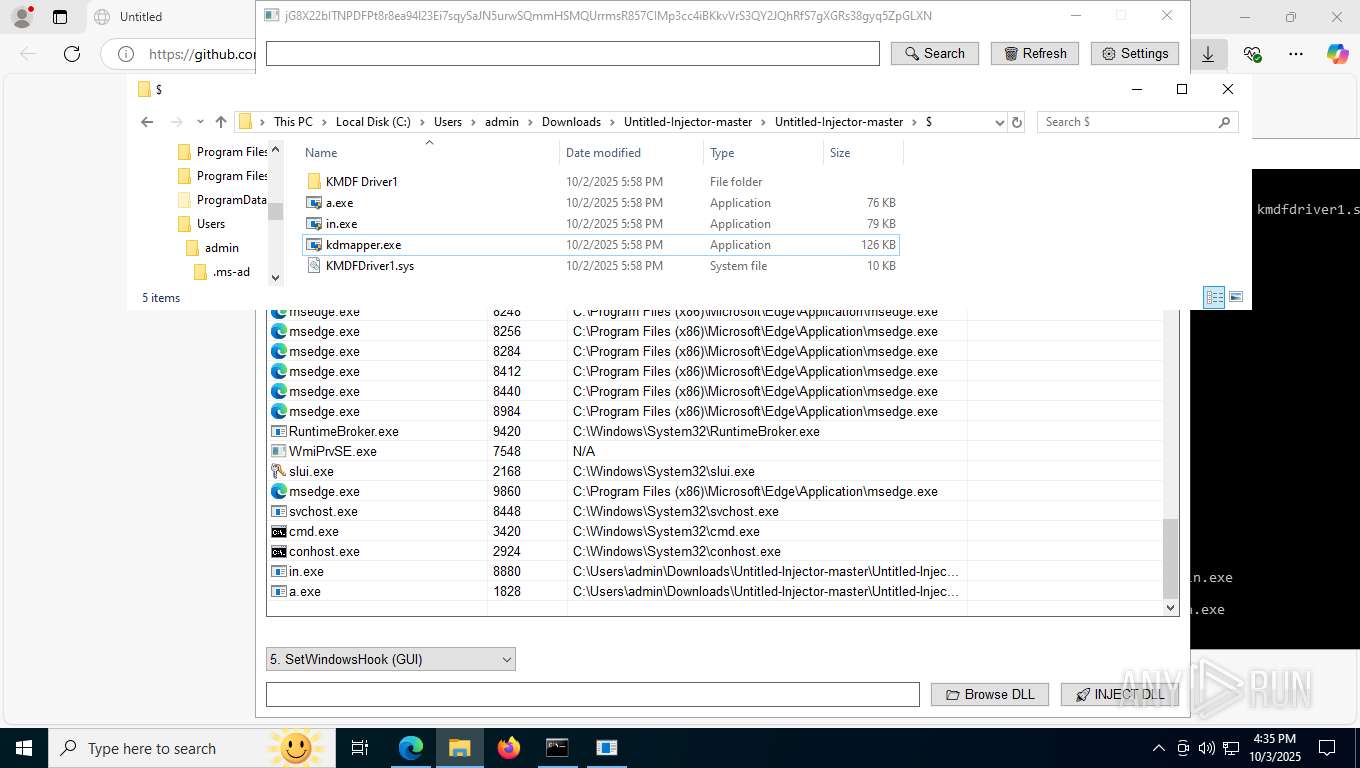
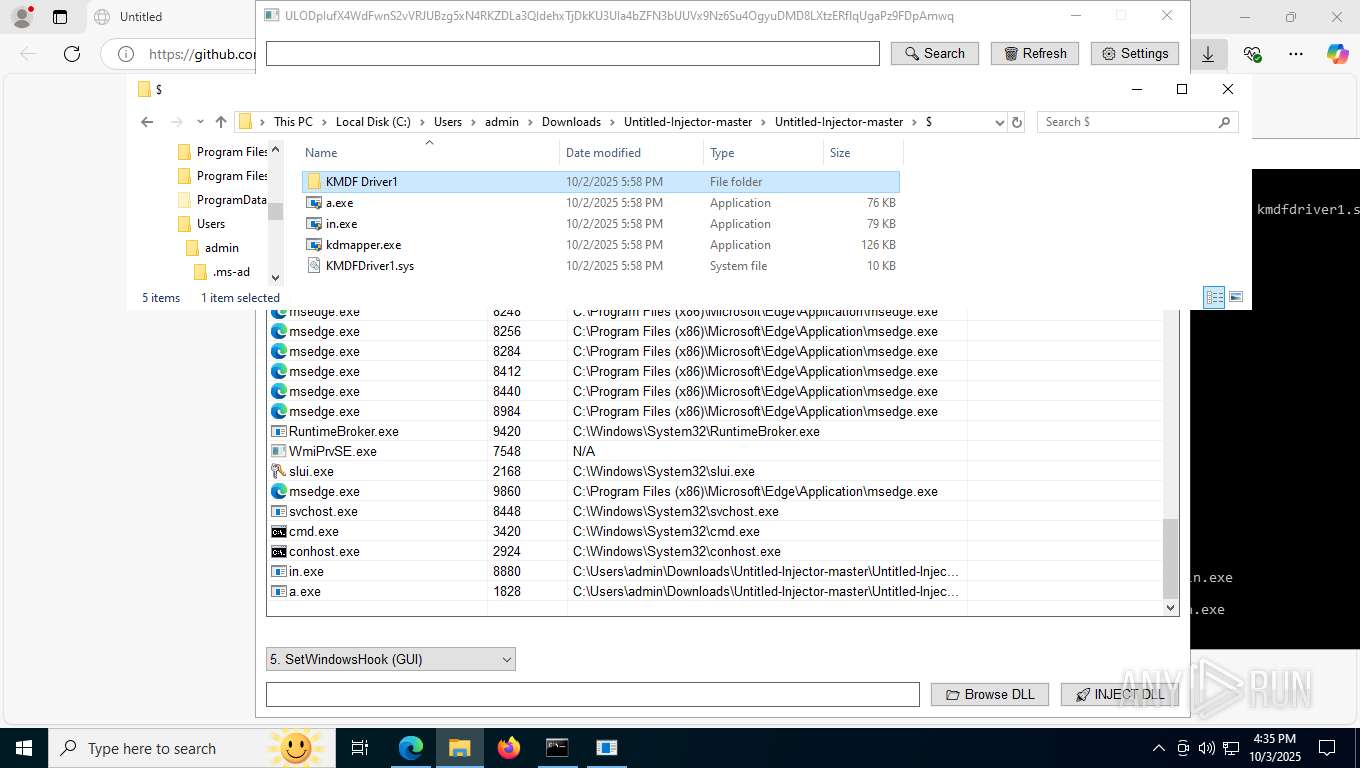
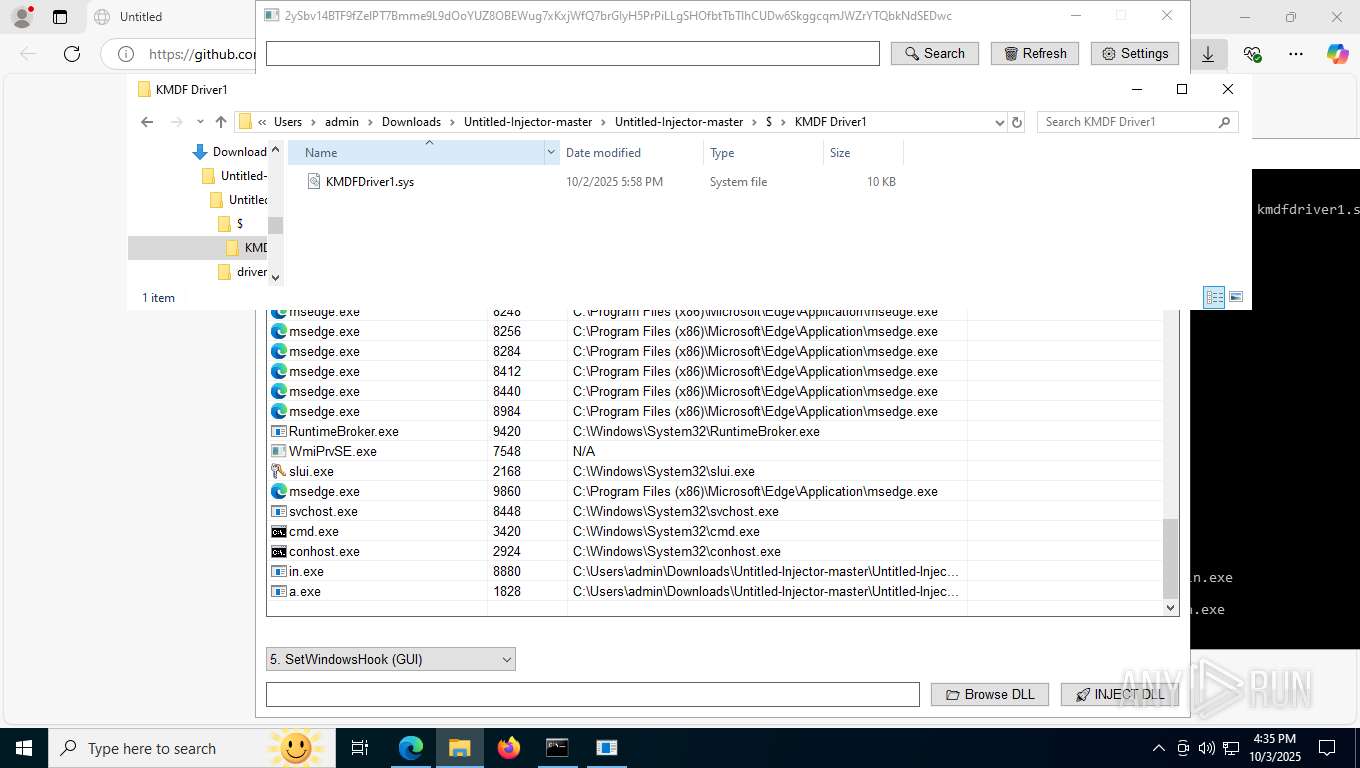
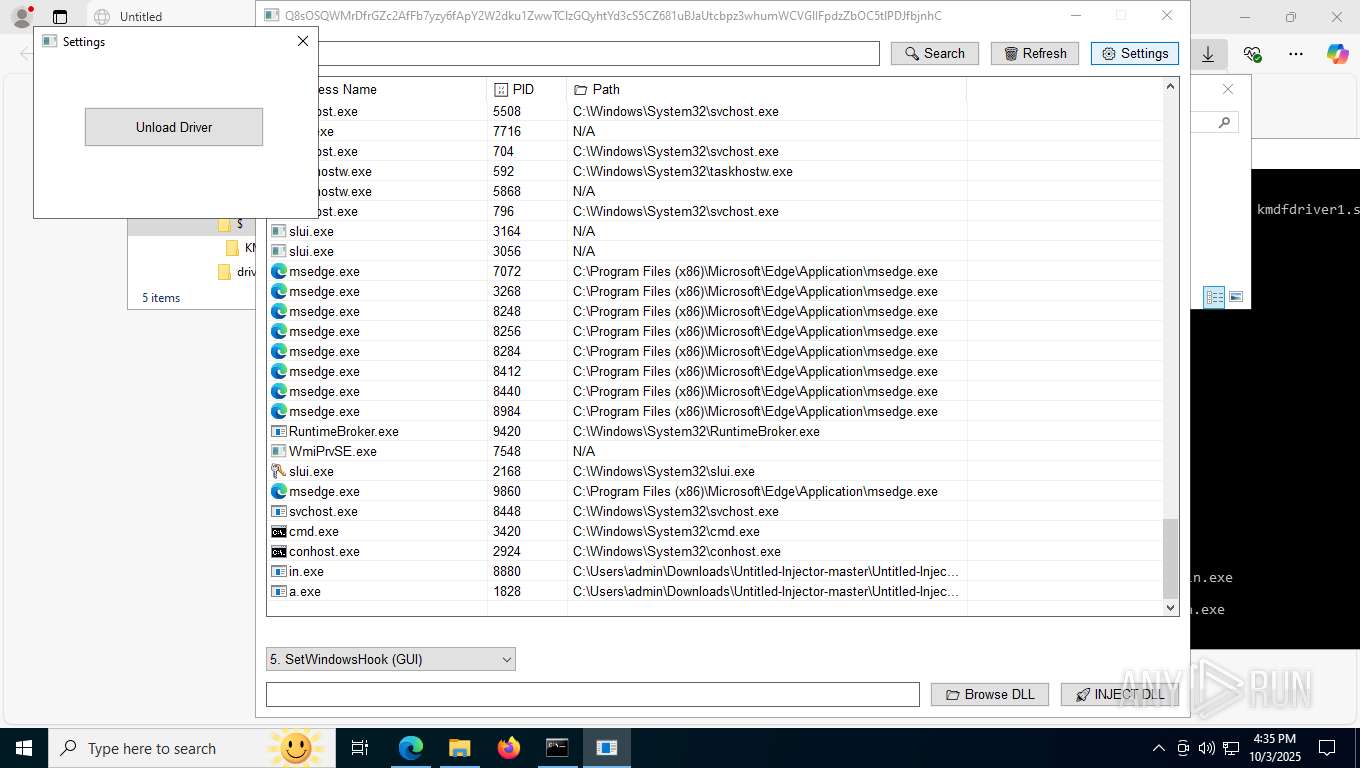
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 3420)
Creates or modifies Windows services
- kdmapper.exe (PID: 9600)
- kdmapper.exe (PID: 9656)
- kdmapper.exe (PID: 1476)
Executable content was dropped or overwritten
- kdmapper.exe (PID: 9656)
- kdmapper.exe (PID: 9600)
- kdmapper.exe (PID: 1476)
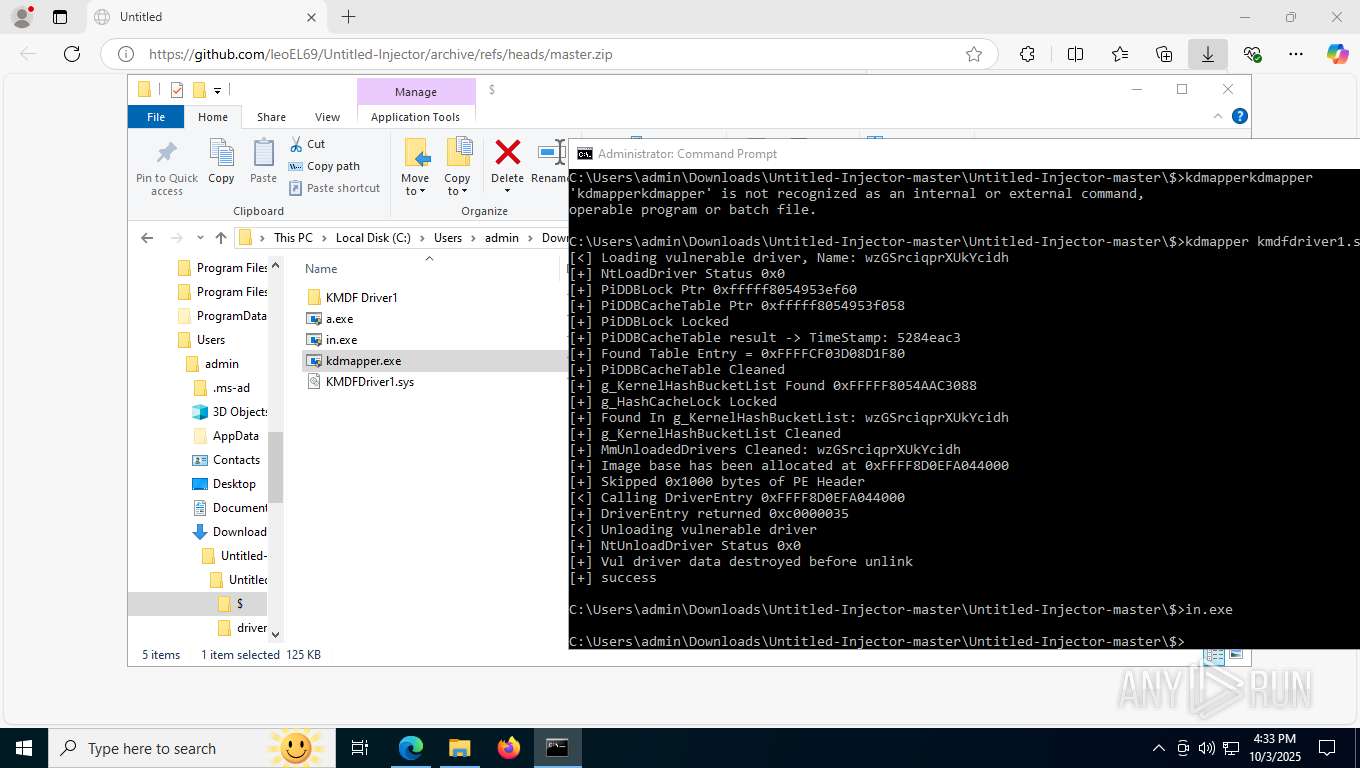
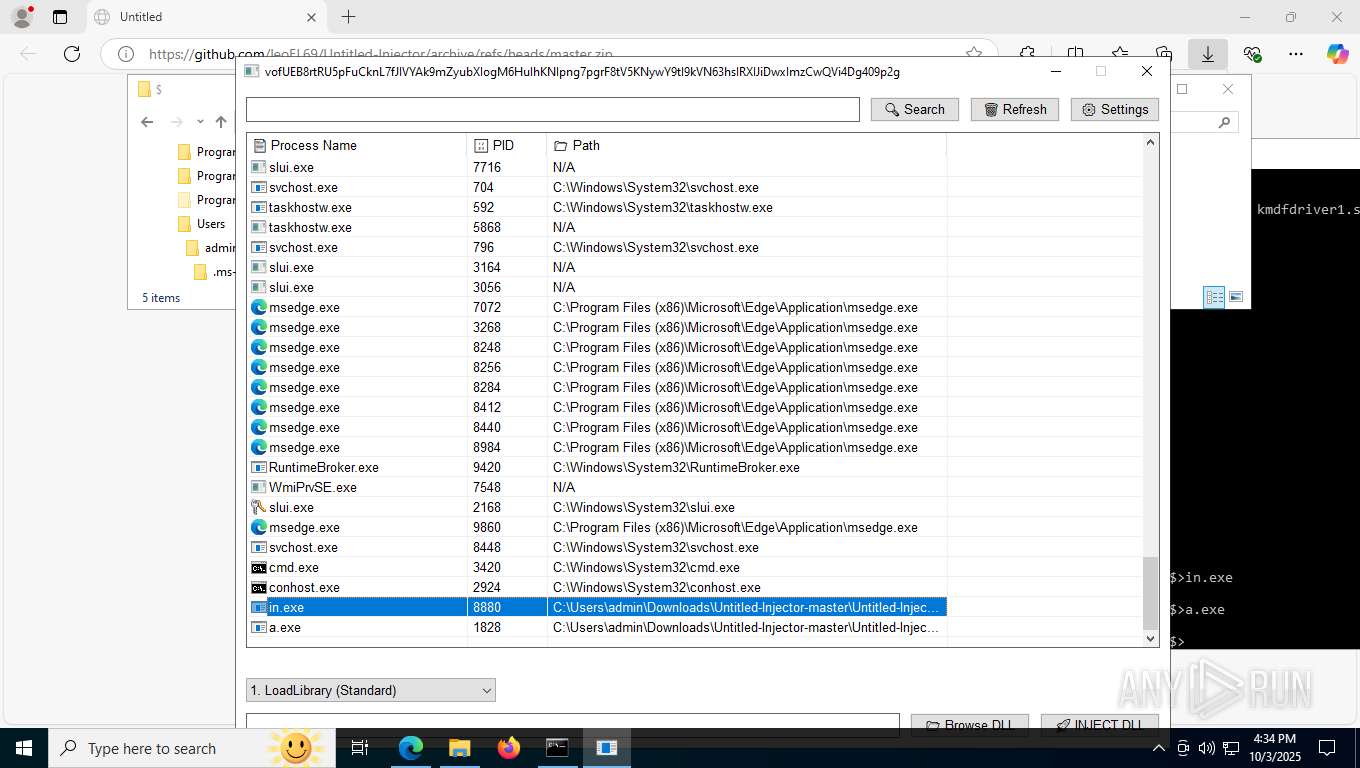
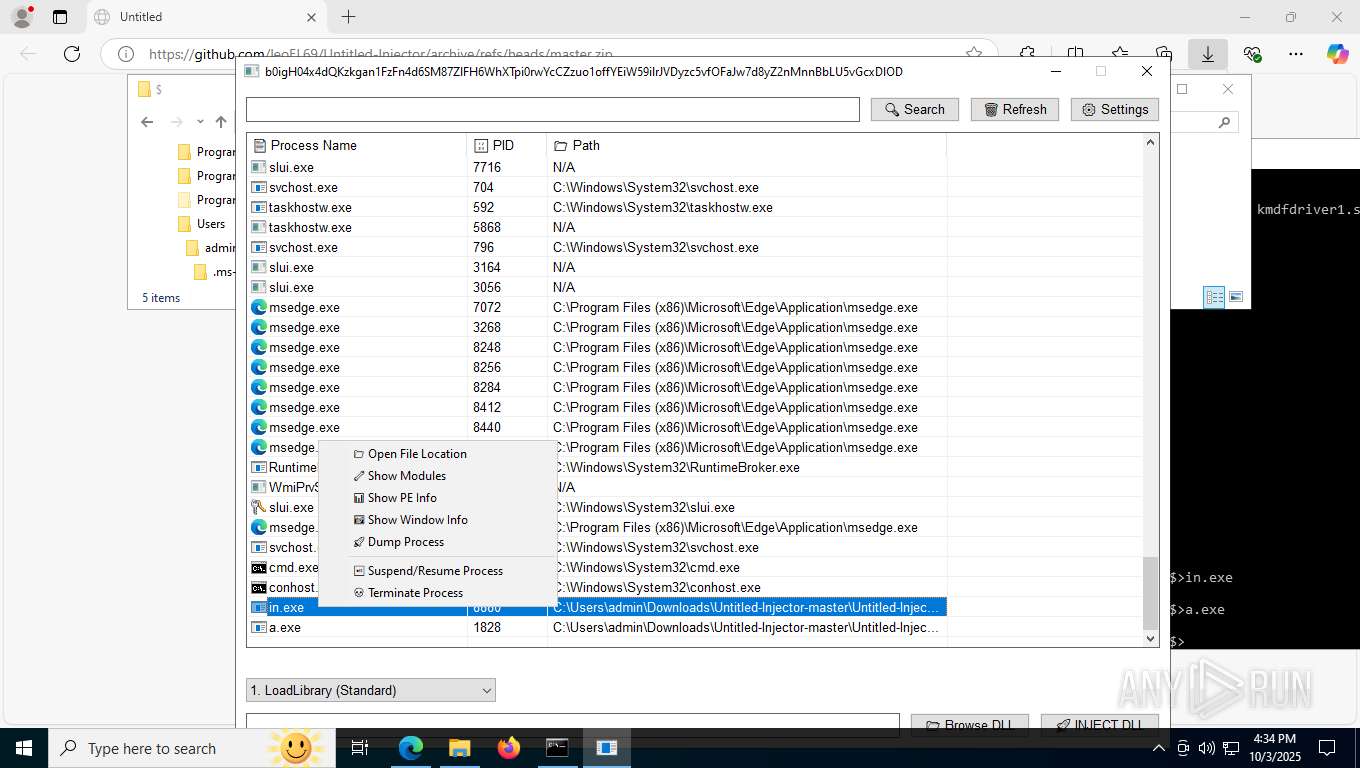
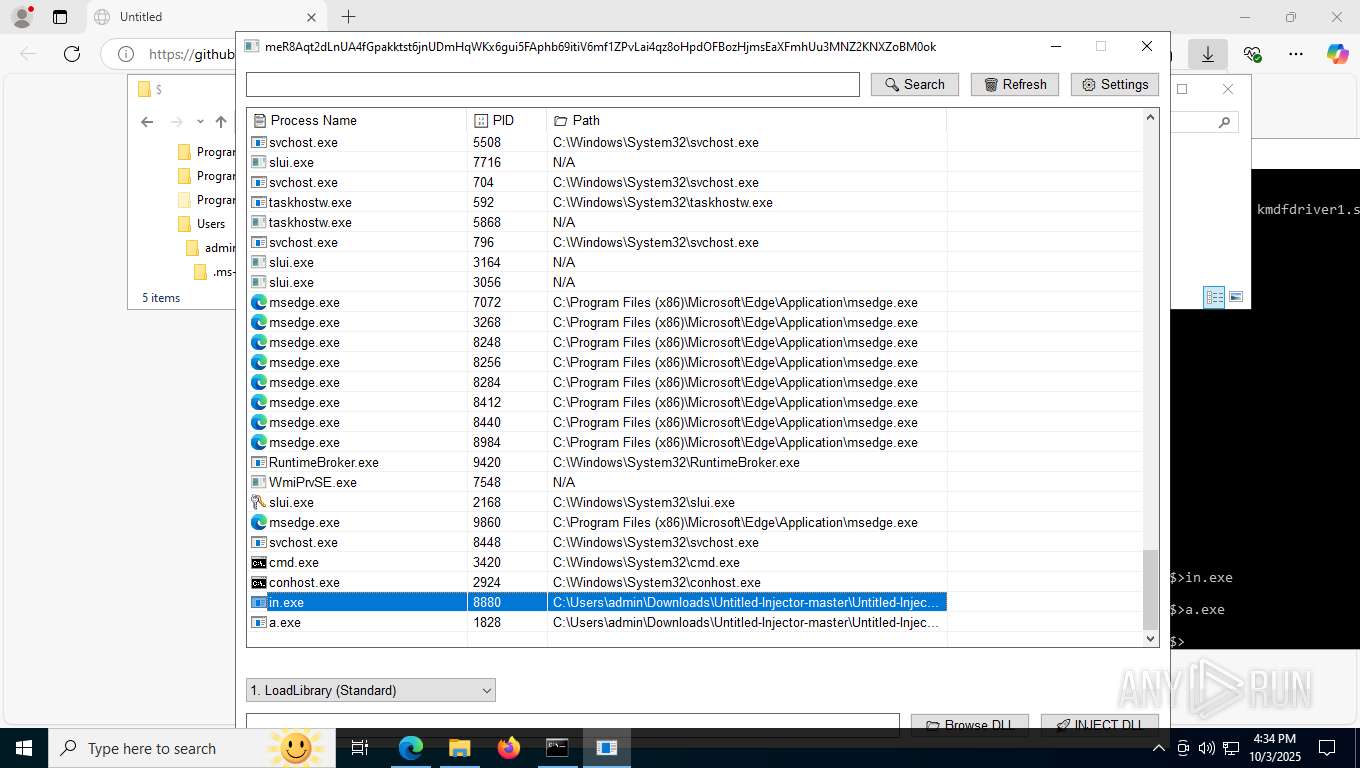
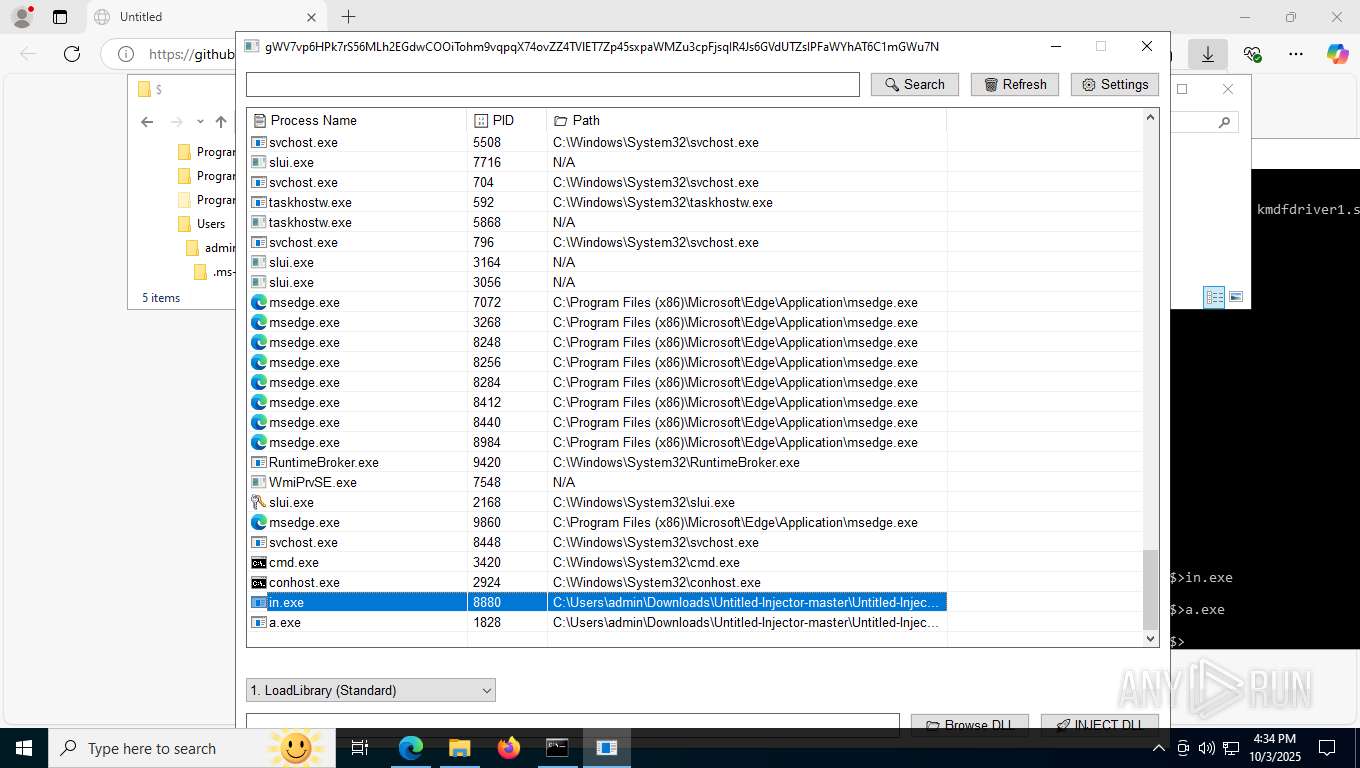
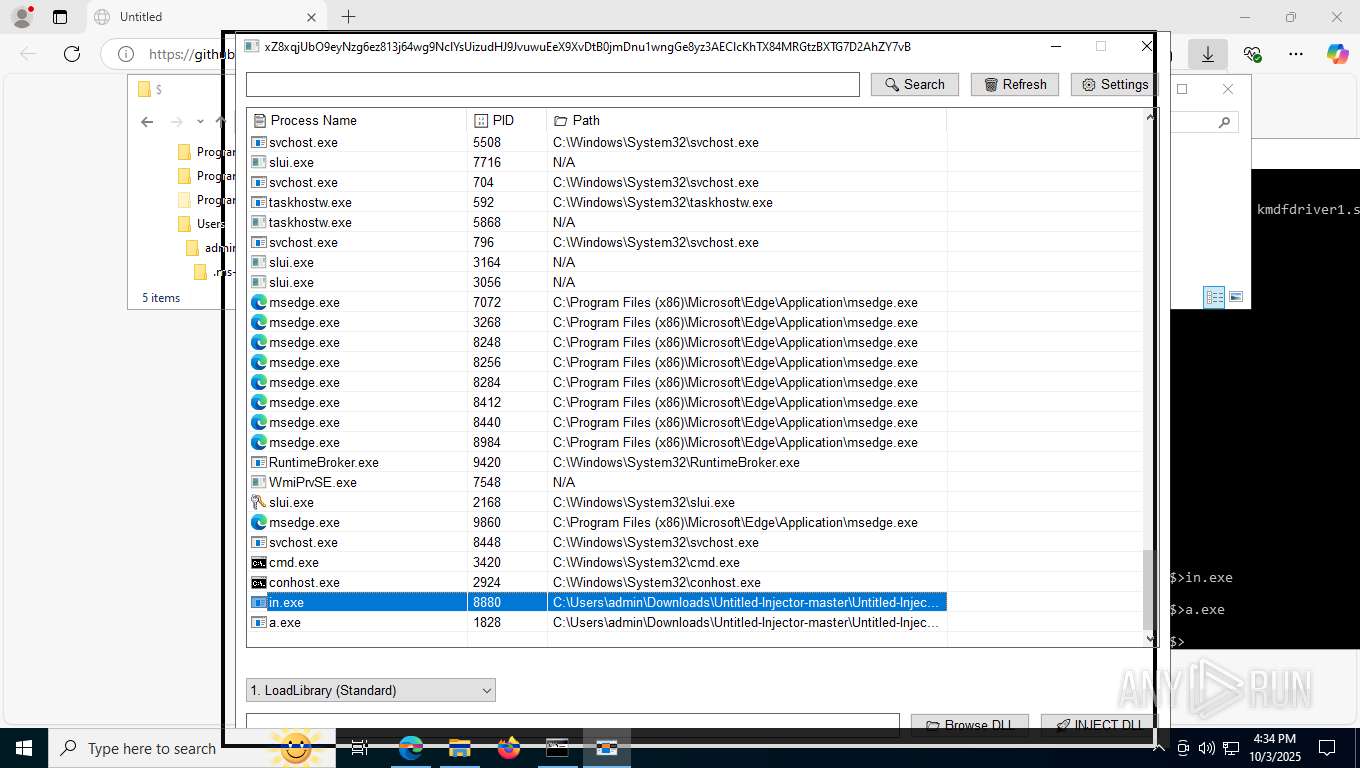
Reads security settings of Internet Explorer
- in.exe (PID: 8880)
- a.exe (PID: 1828)
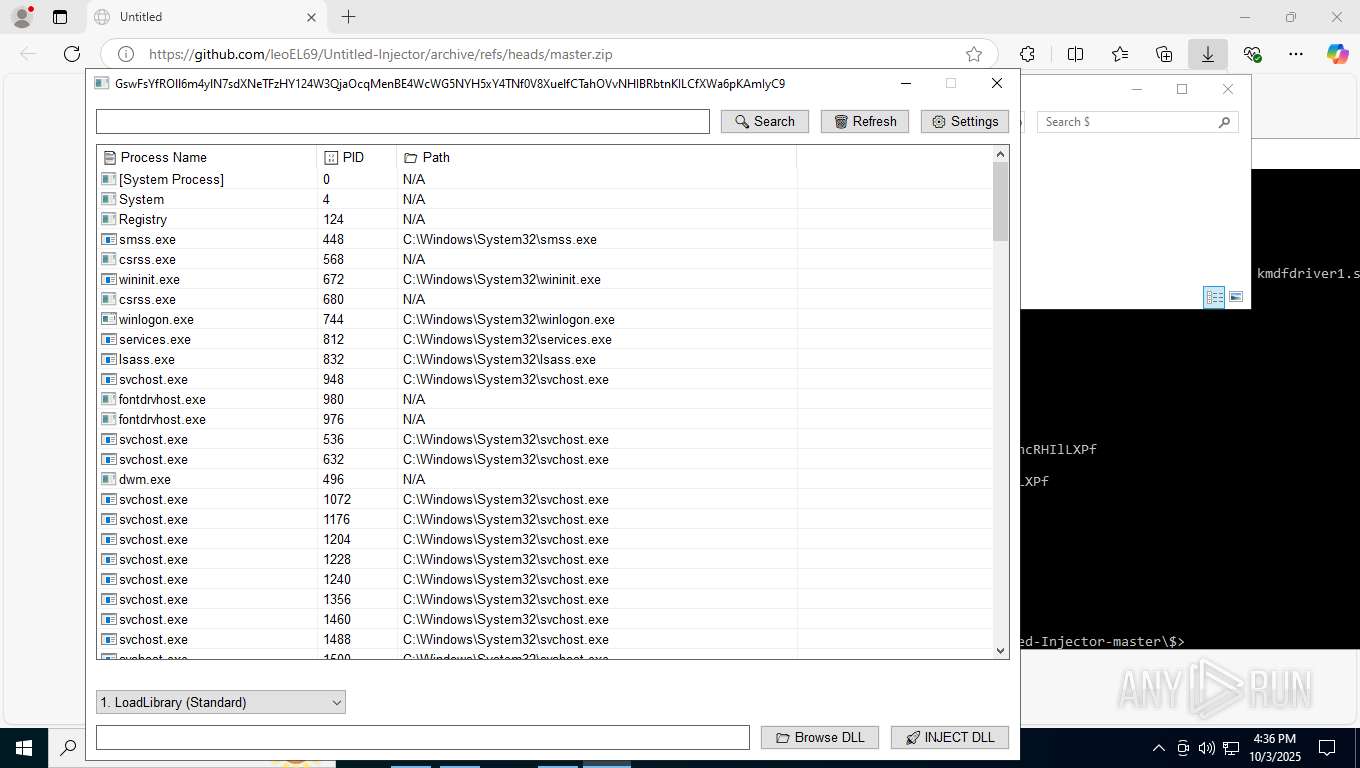
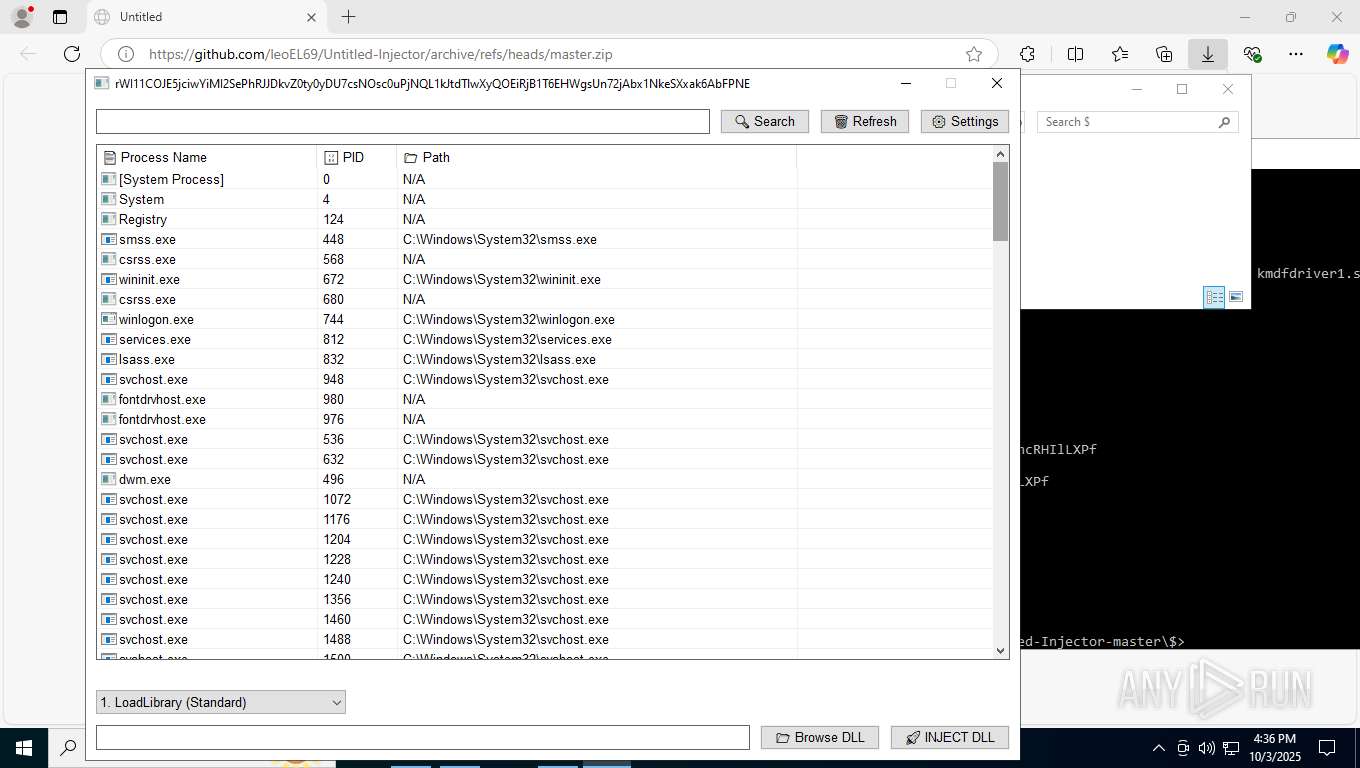
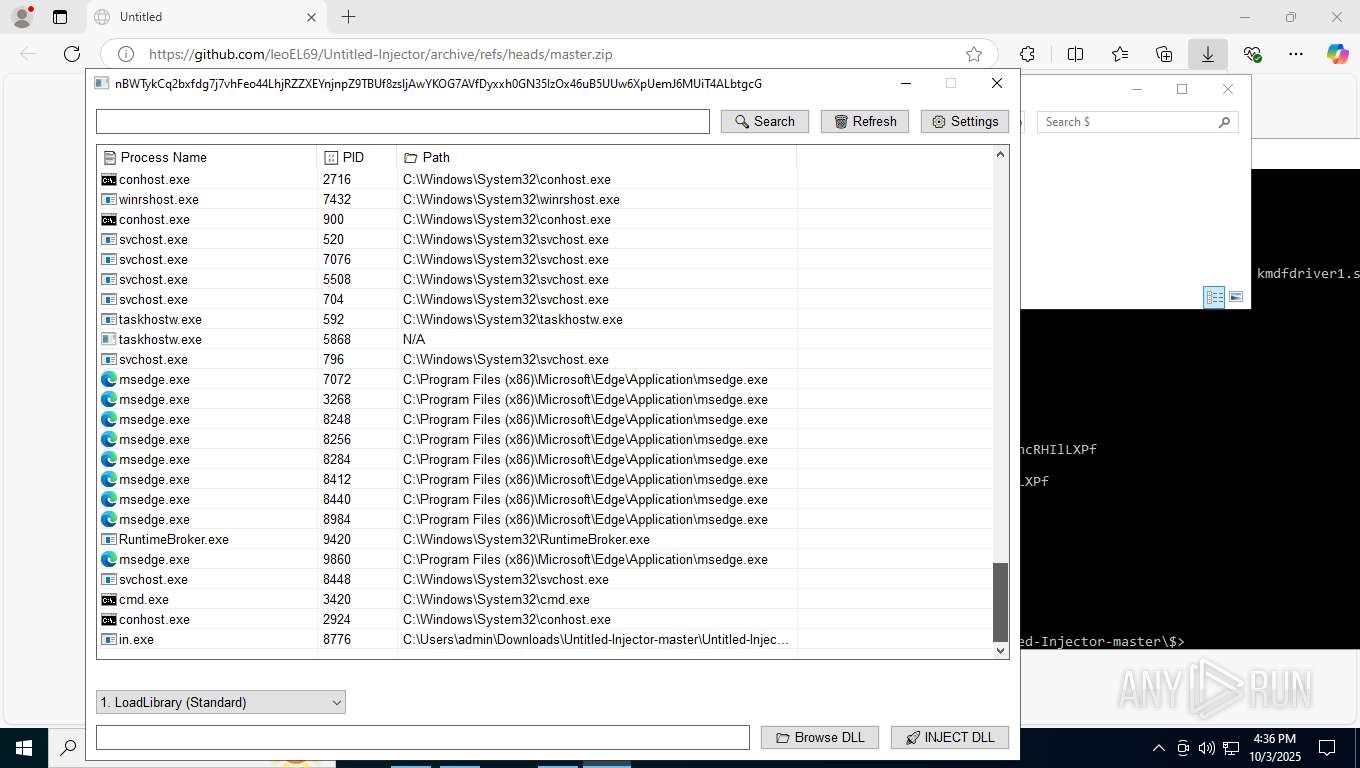
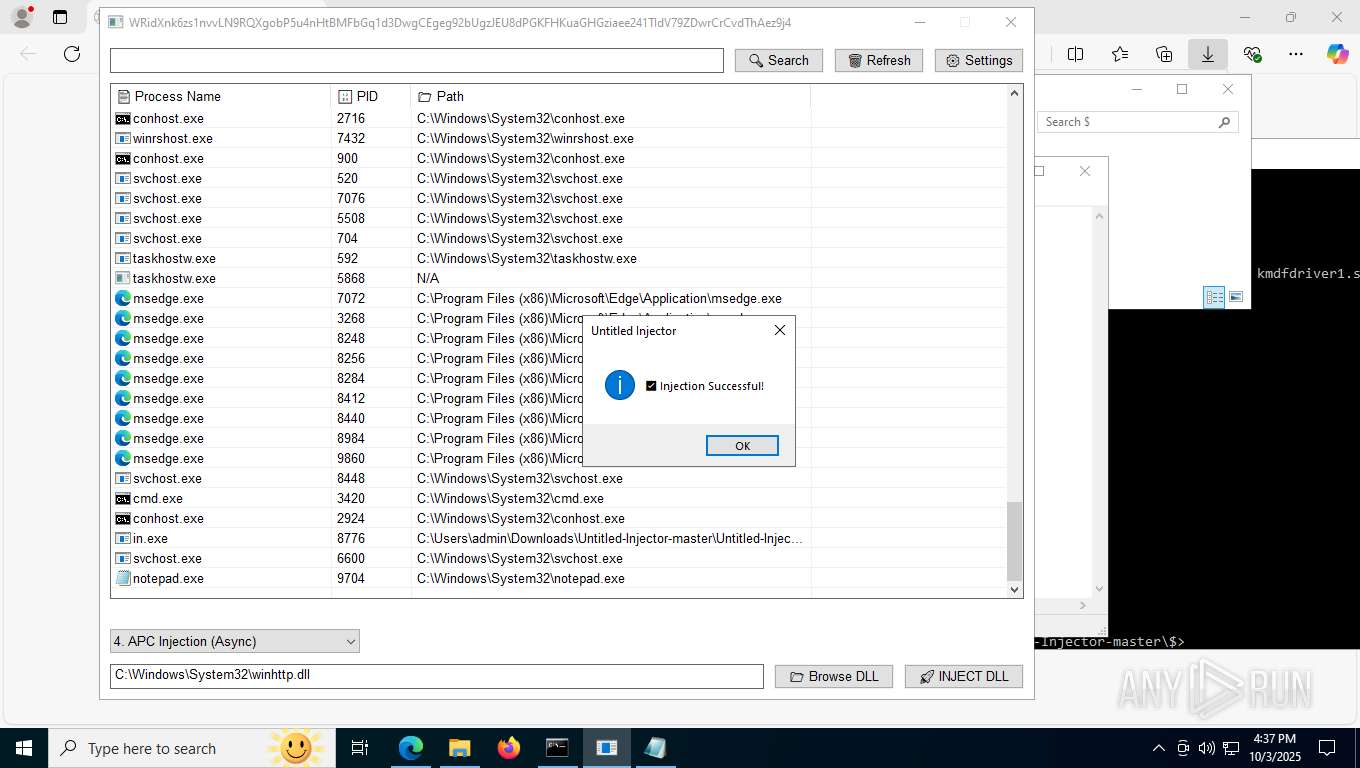
- in.exe (PID: 8776)
The process creates files with name similar to system file names
- WerFault.exe (PID: 9596)
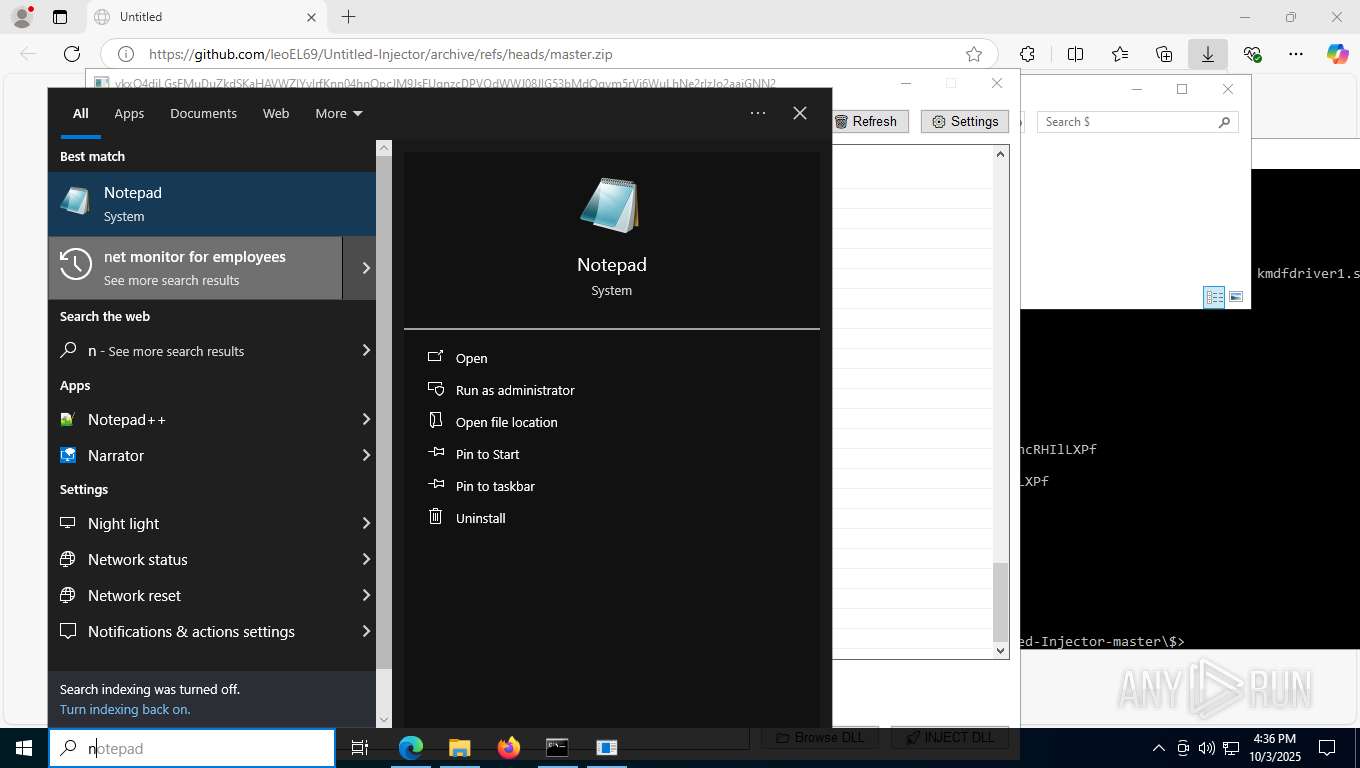
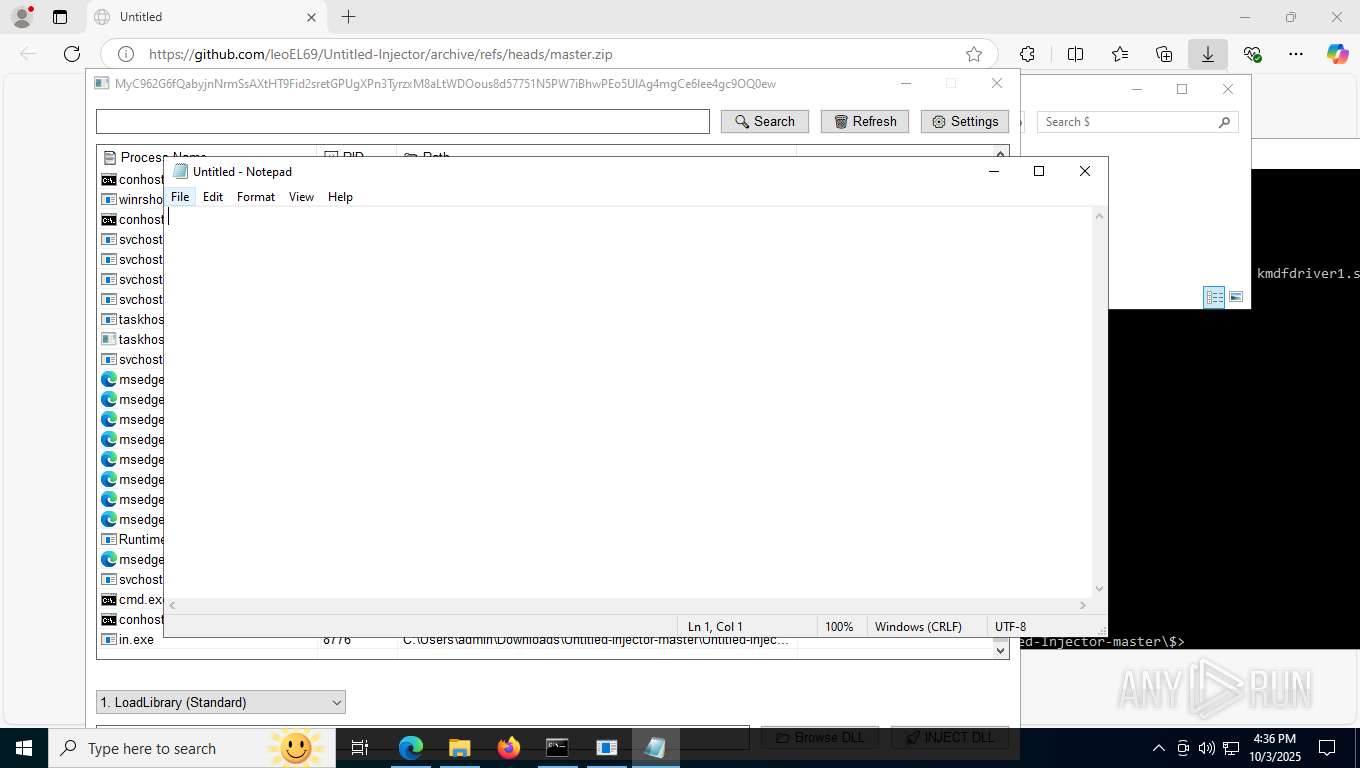
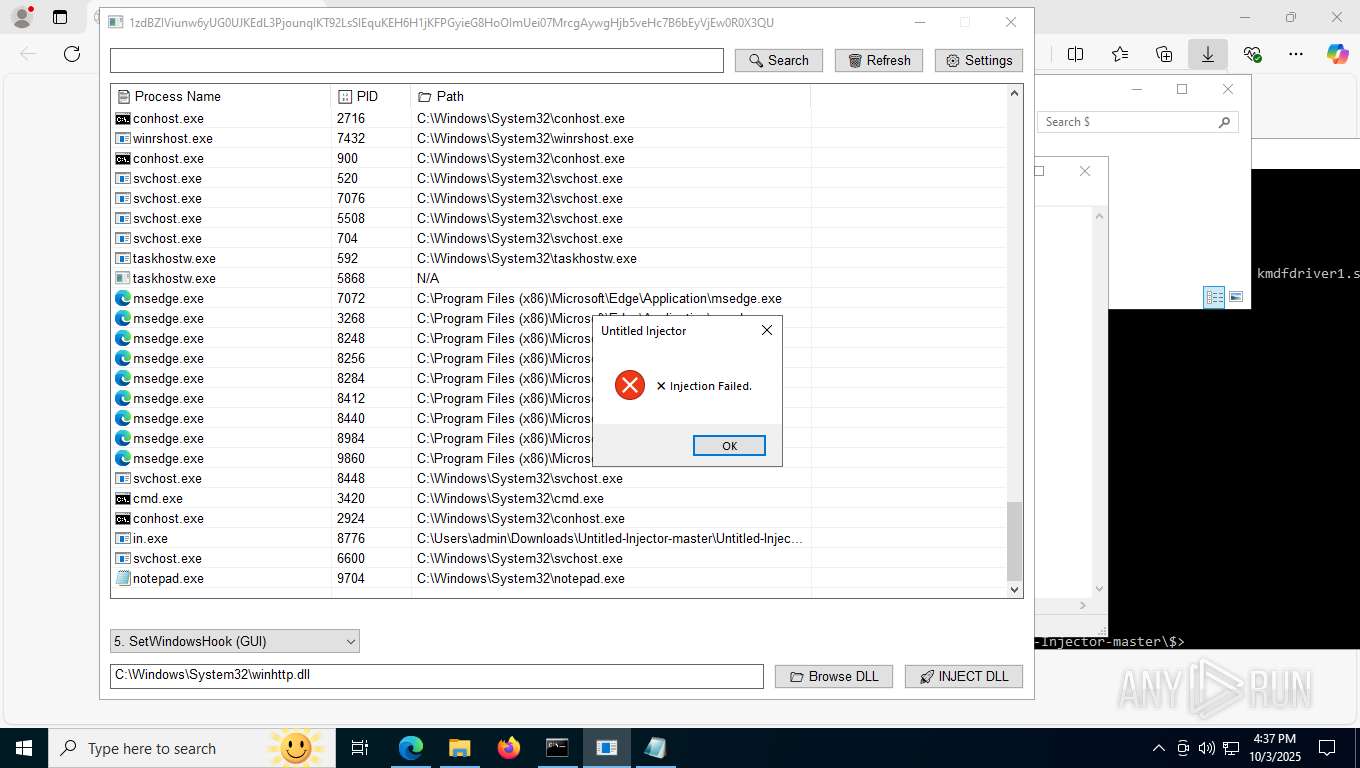
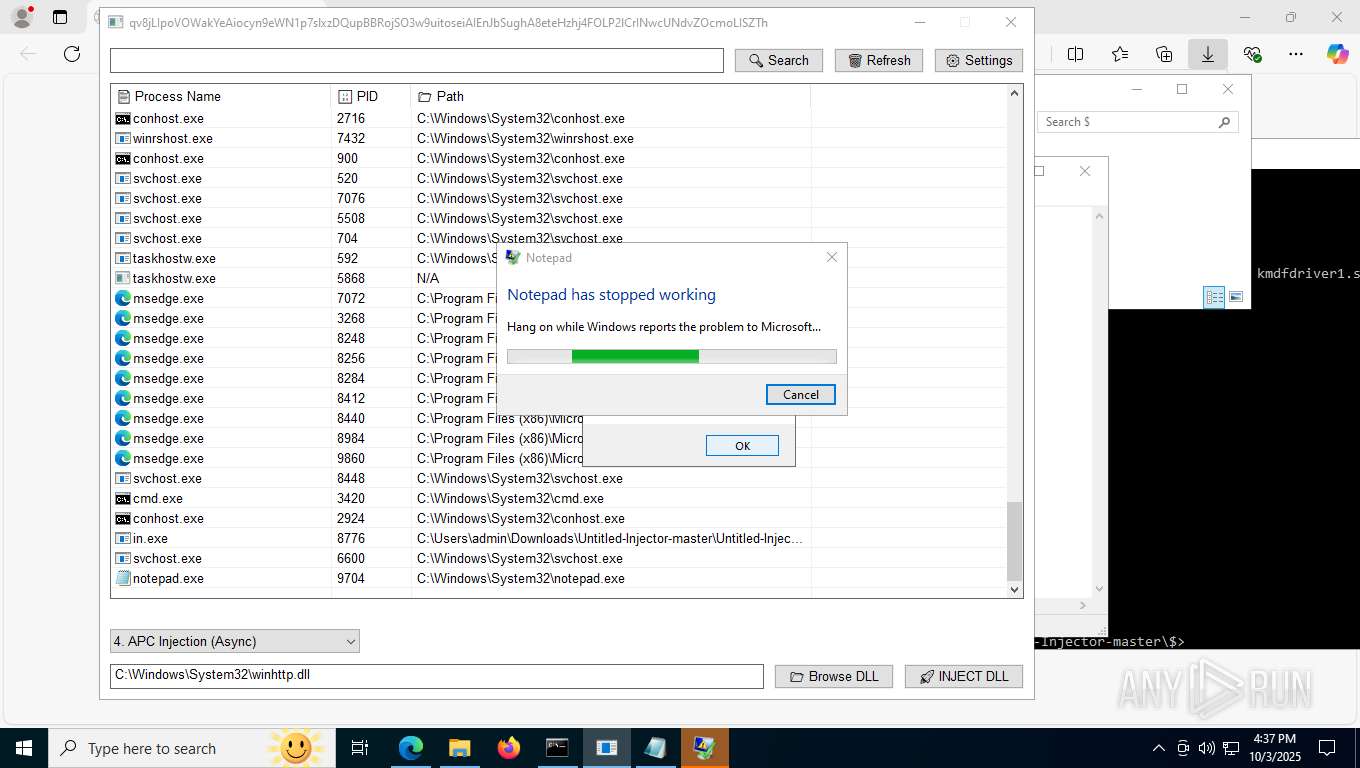
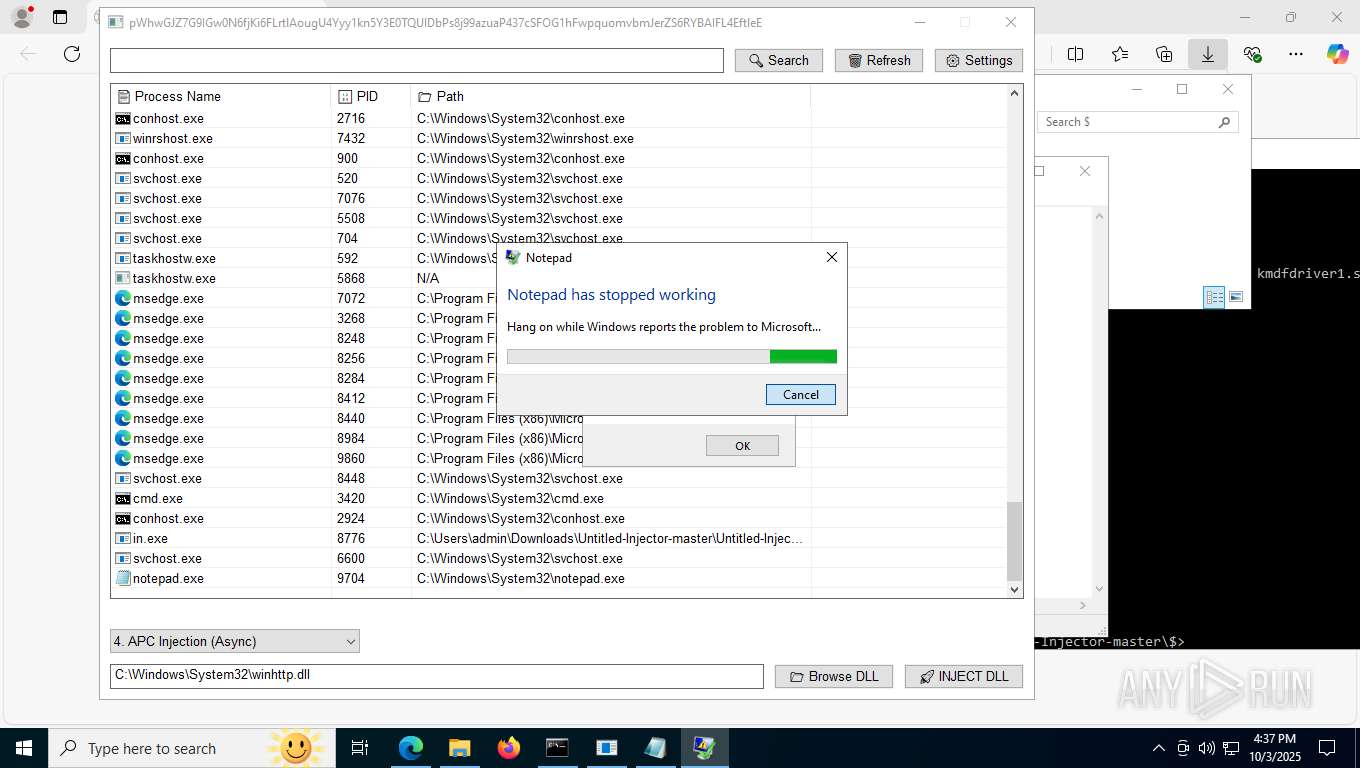
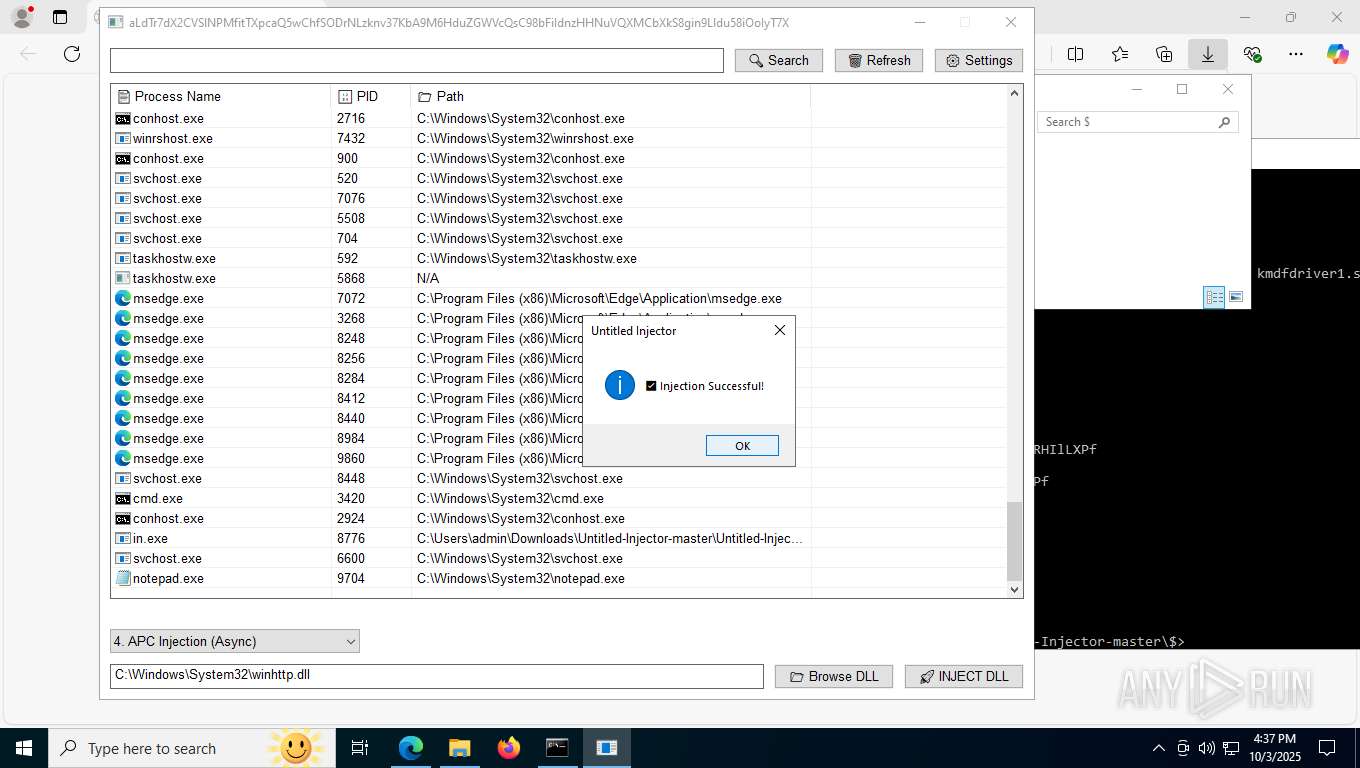
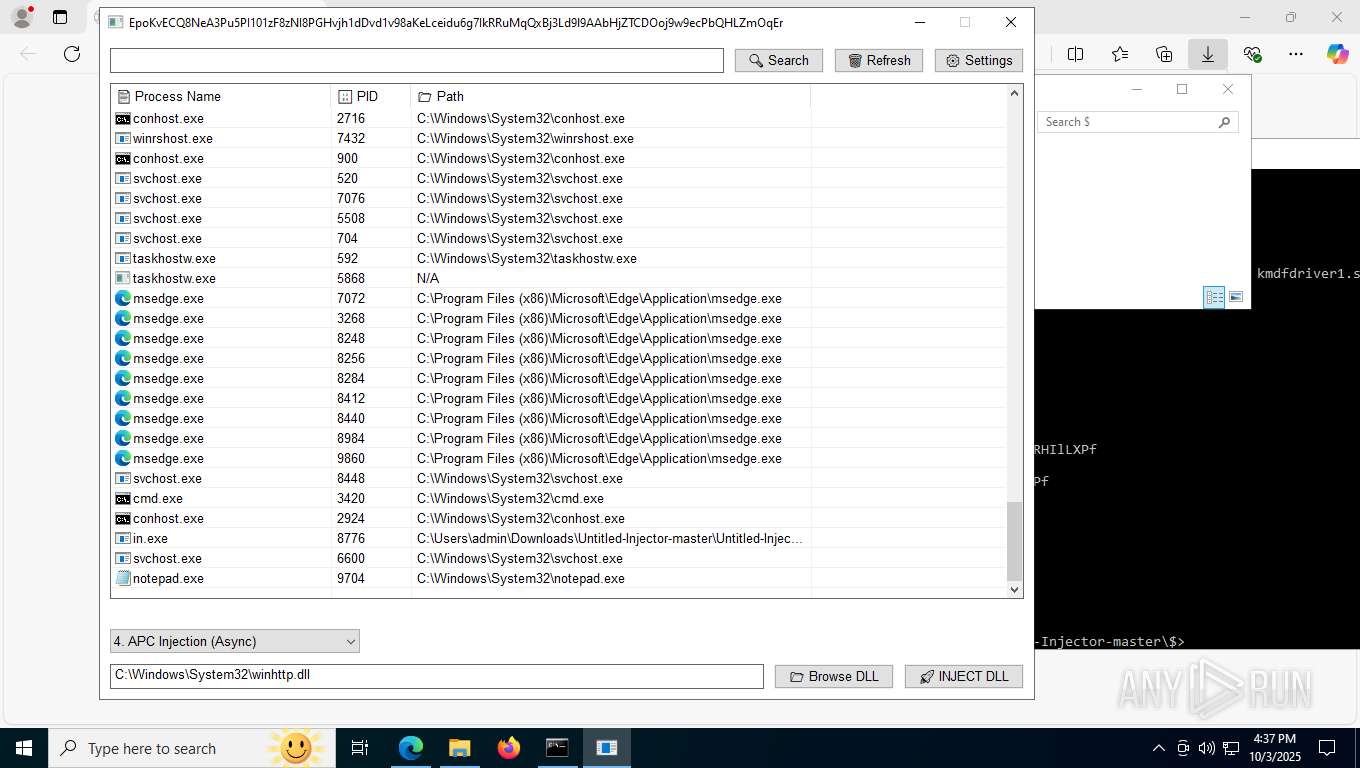
Executes application which crashes
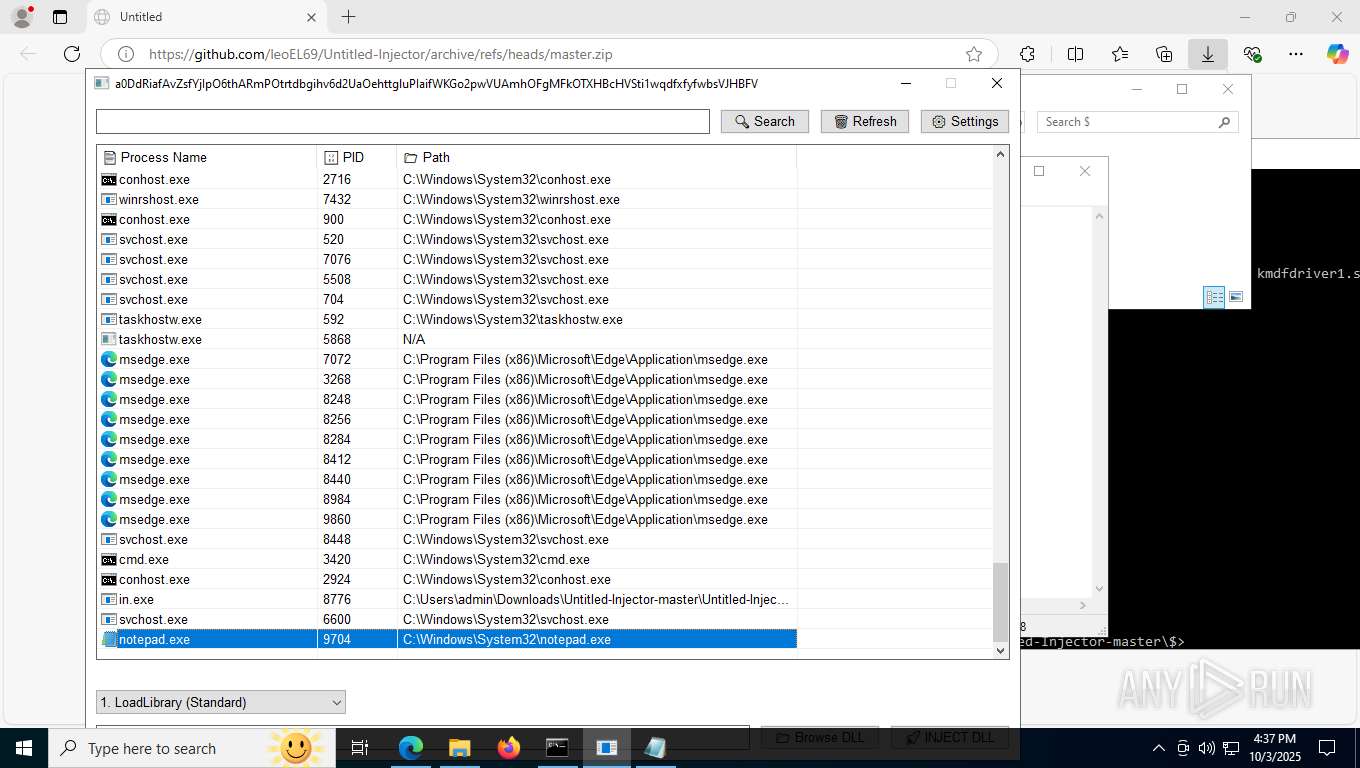
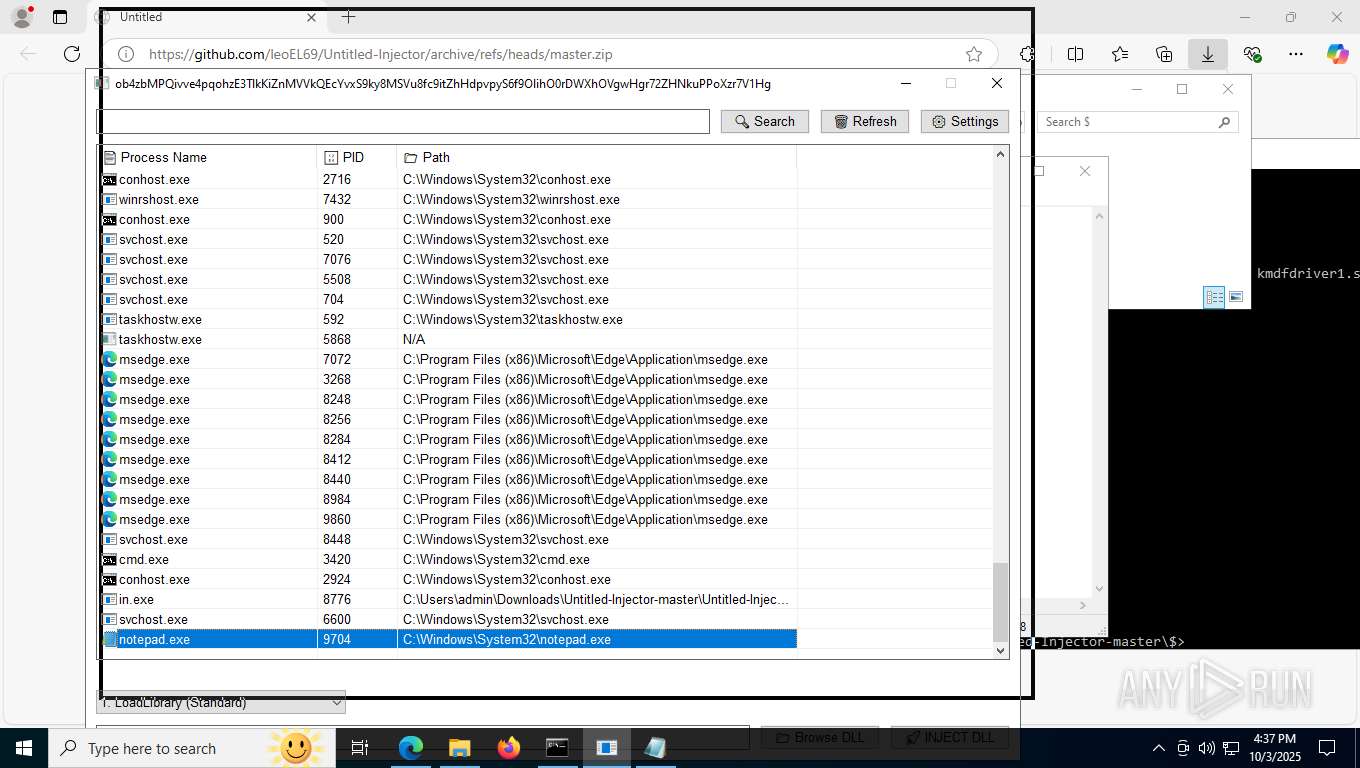
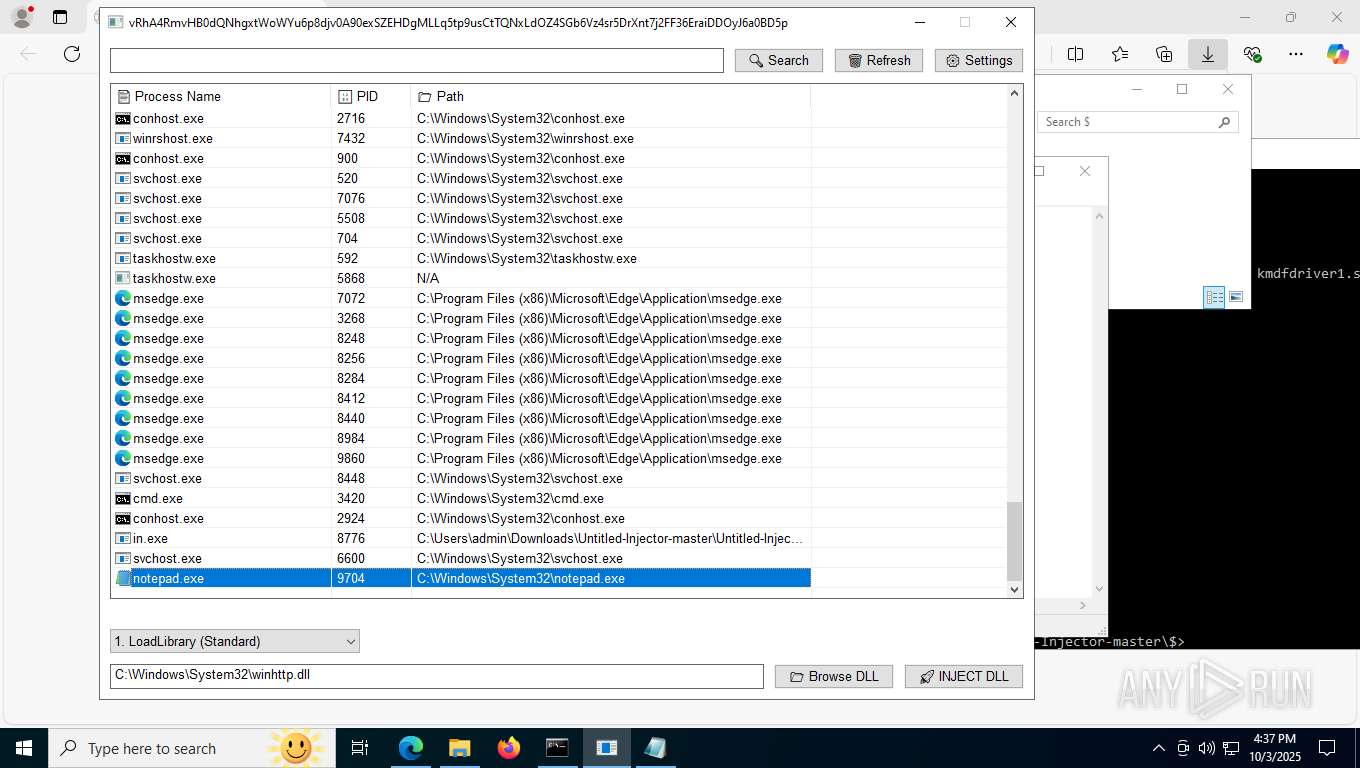
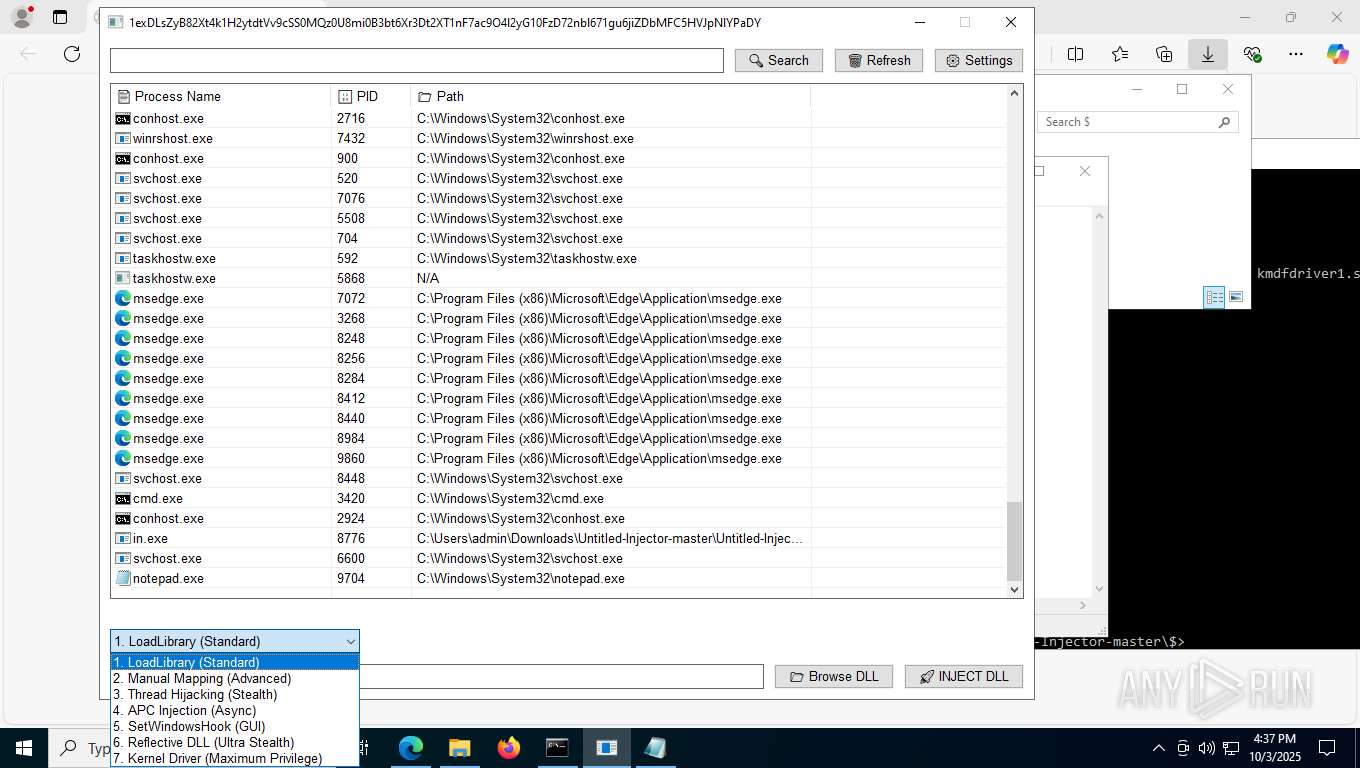
- notepad.exe (PID: 9704)
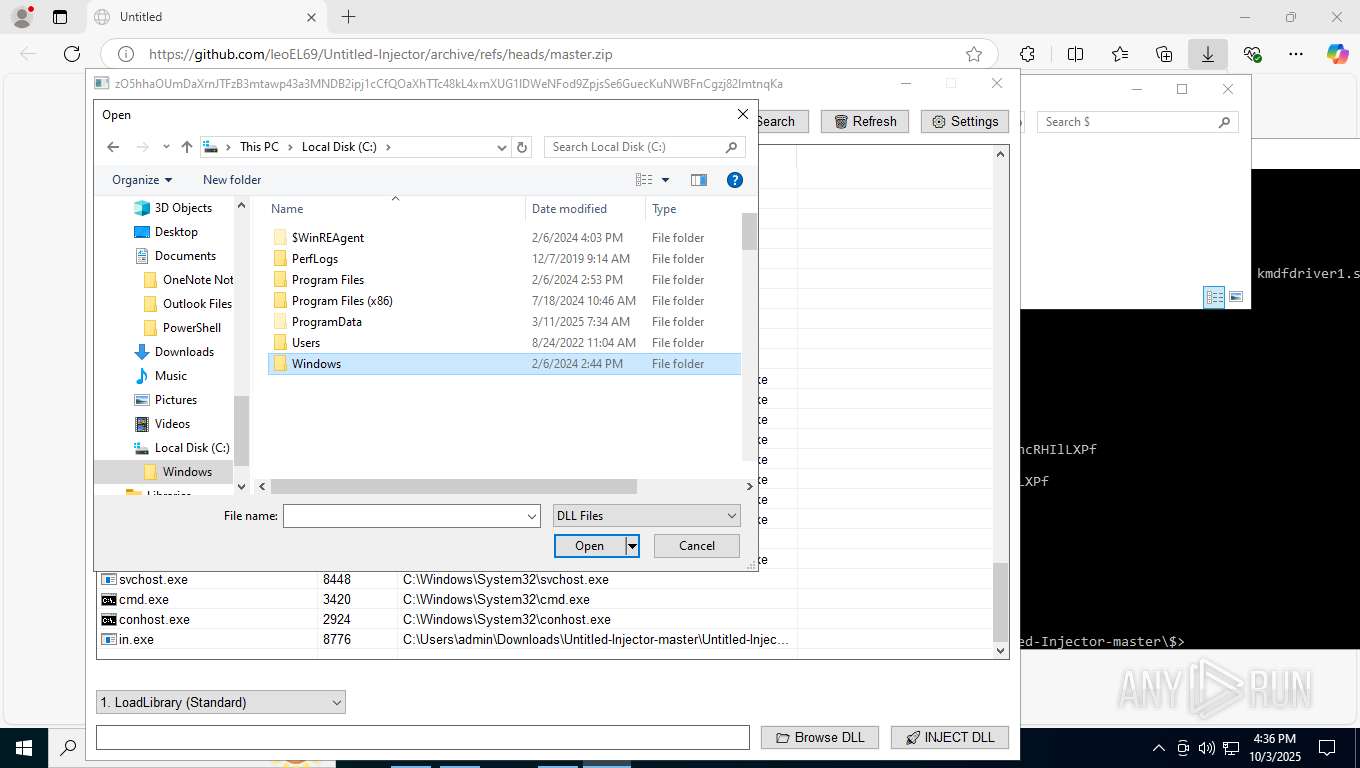
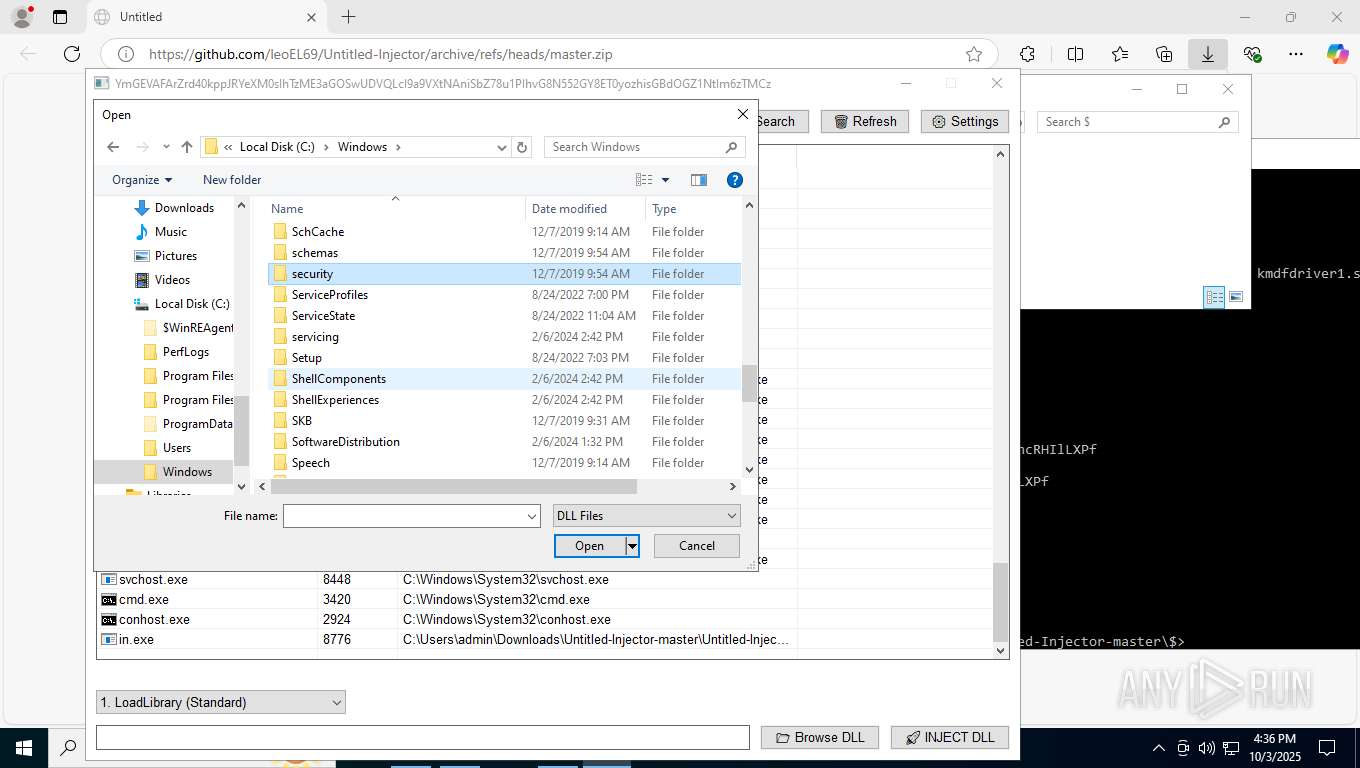
Creates file in the systems drive root
- in.exe (PID: 8776)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 7072)
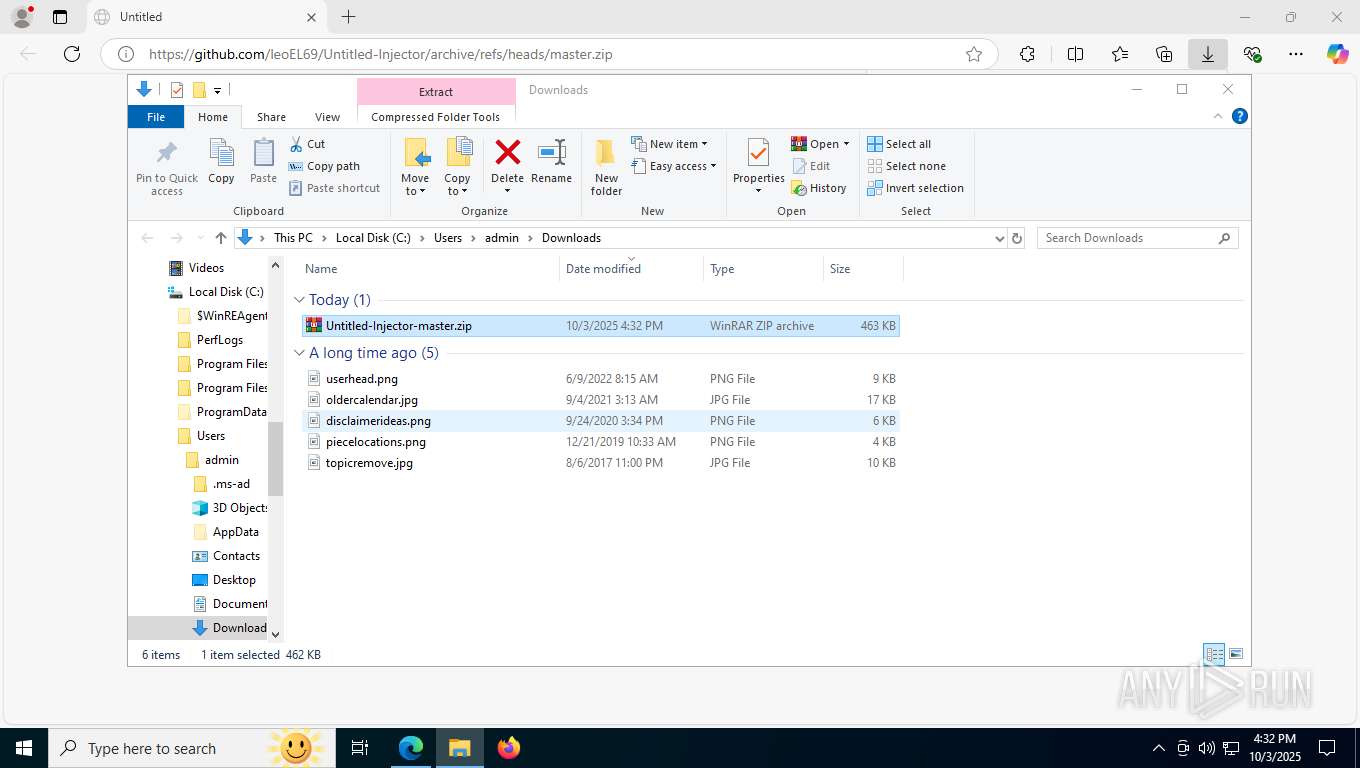
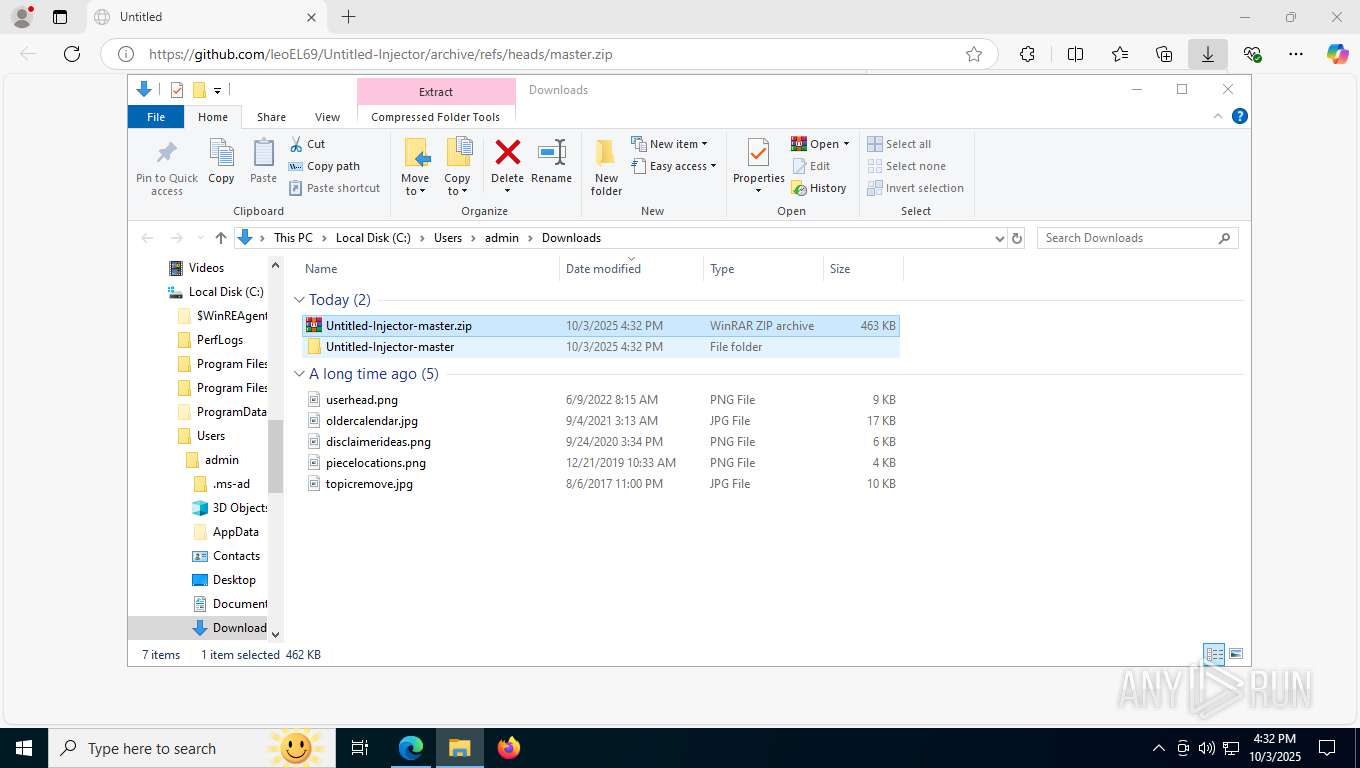
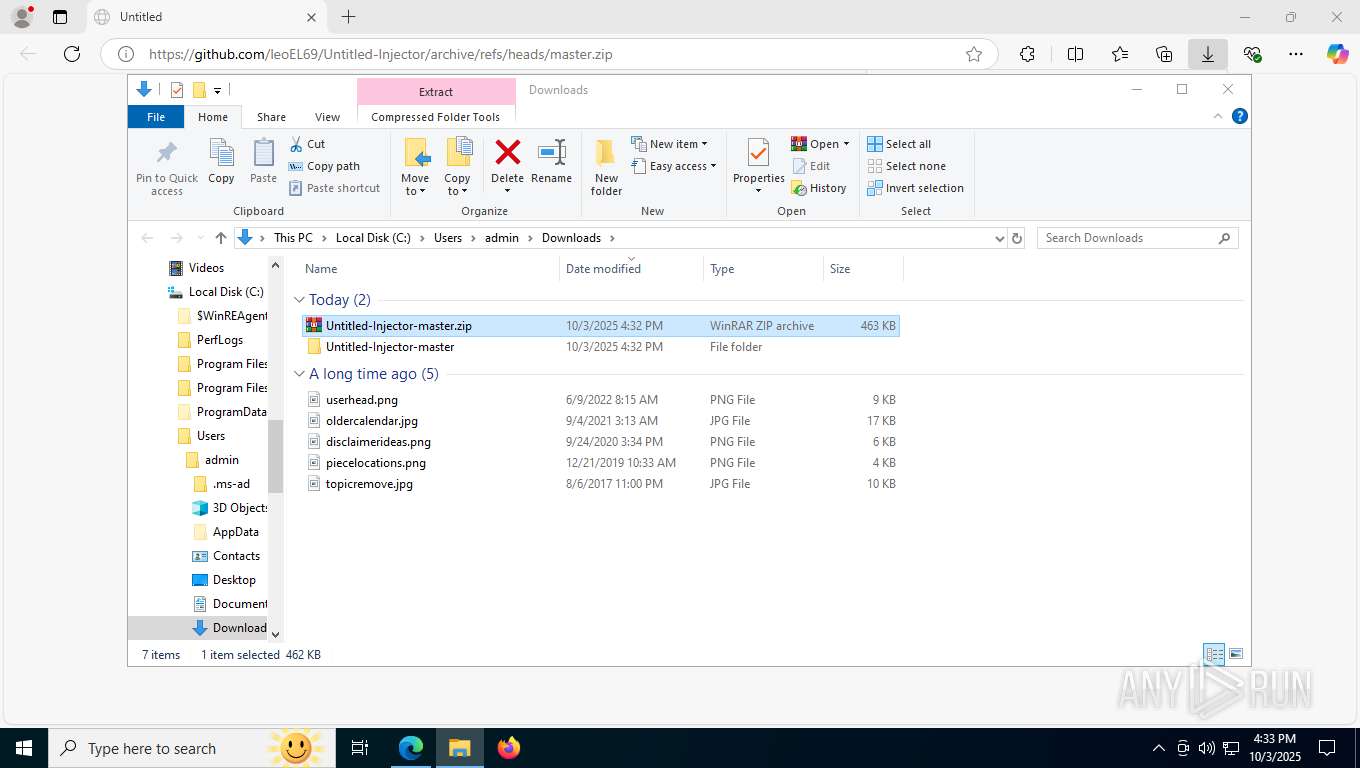
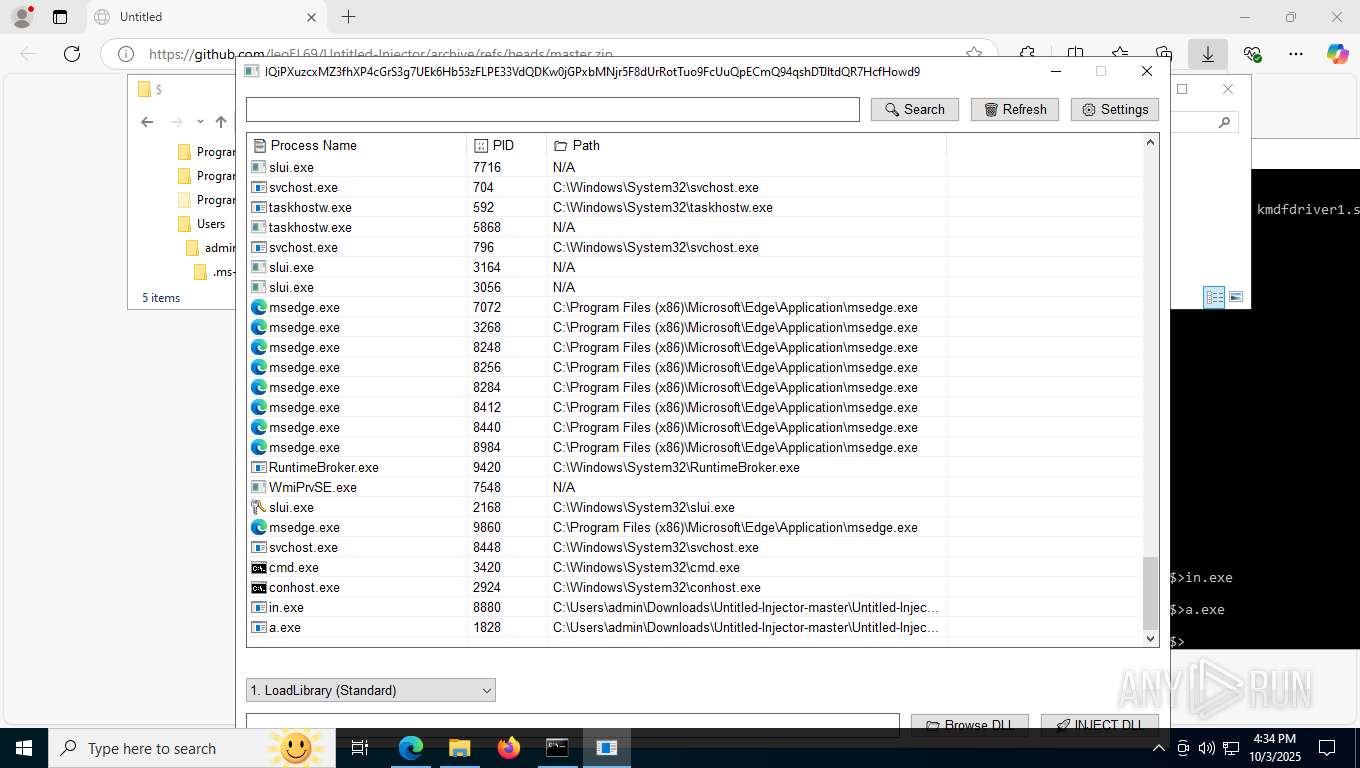
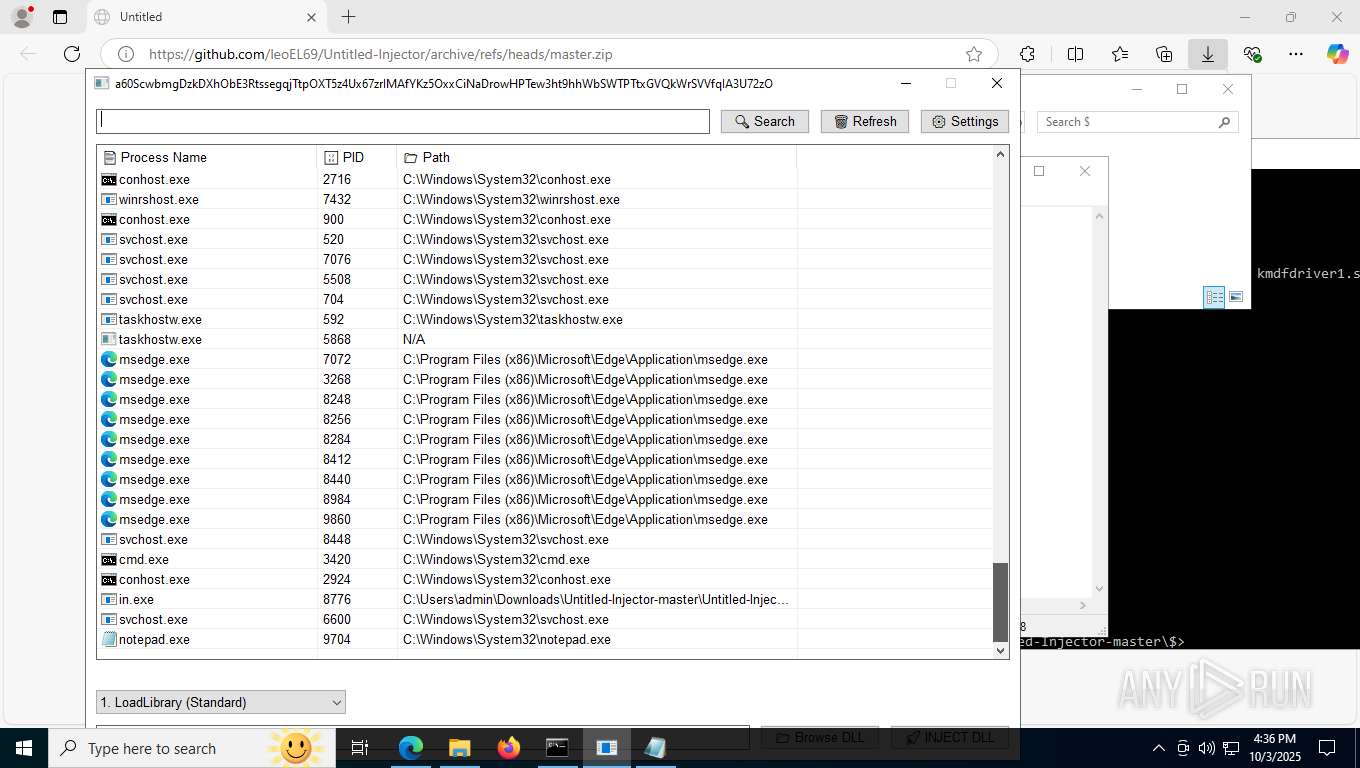
Launching a file from the Downloads directory
- msedge.exe (PID: 7072)
Application launched itself
- msedge.exe (PID: 7072)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 10056)
- WerFault.exe (PID: 9596)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 10056)
- slui.exe (PID: 2168)
- WerFault.exe (PID: 9596)
Executable content was dropped or overwritten
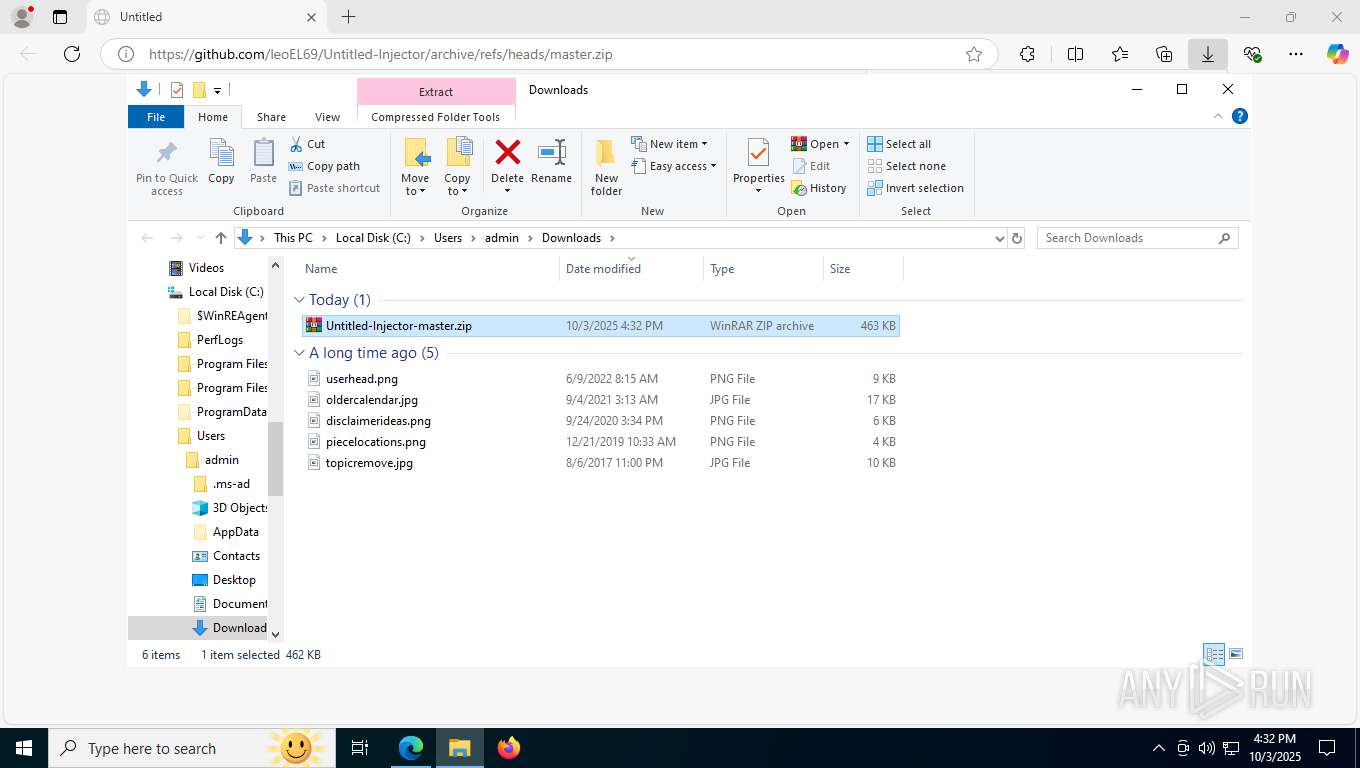
- WinRAR.exe (PID: 3420)
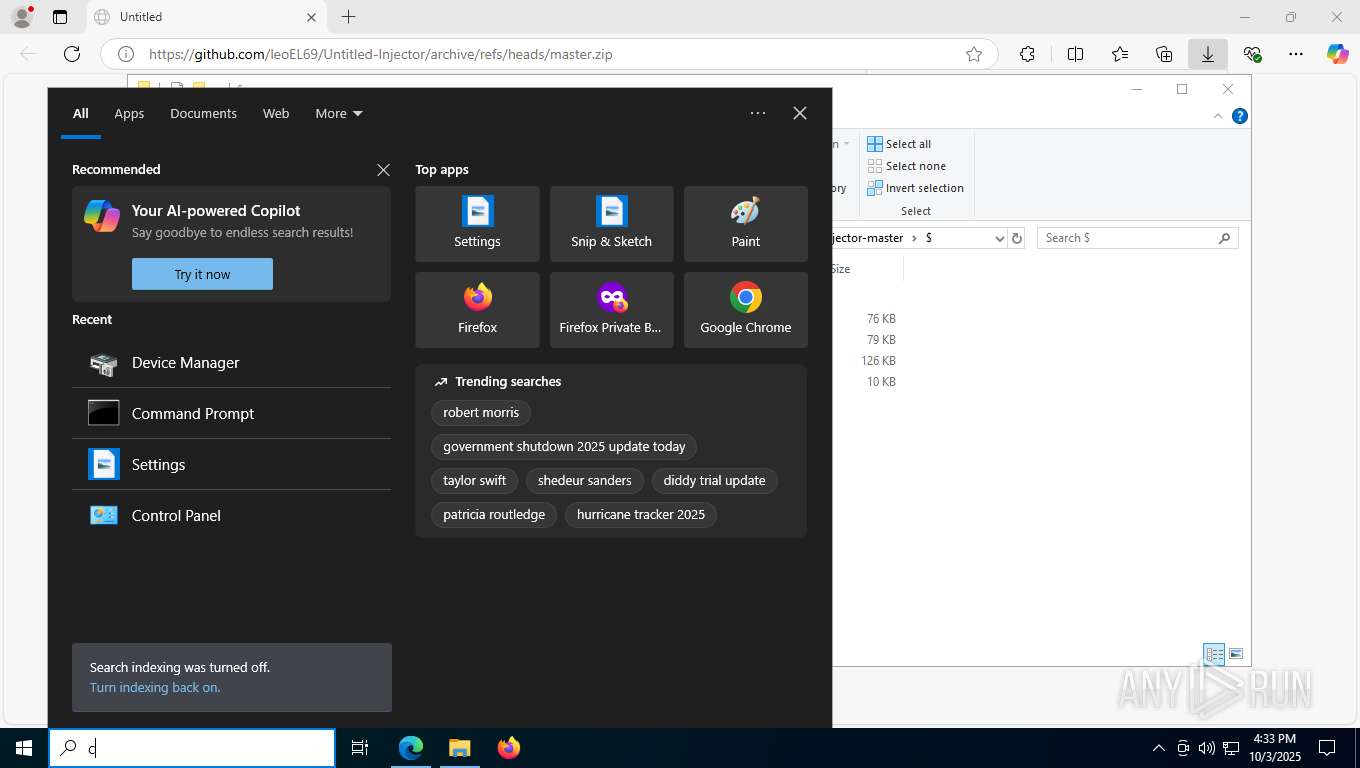
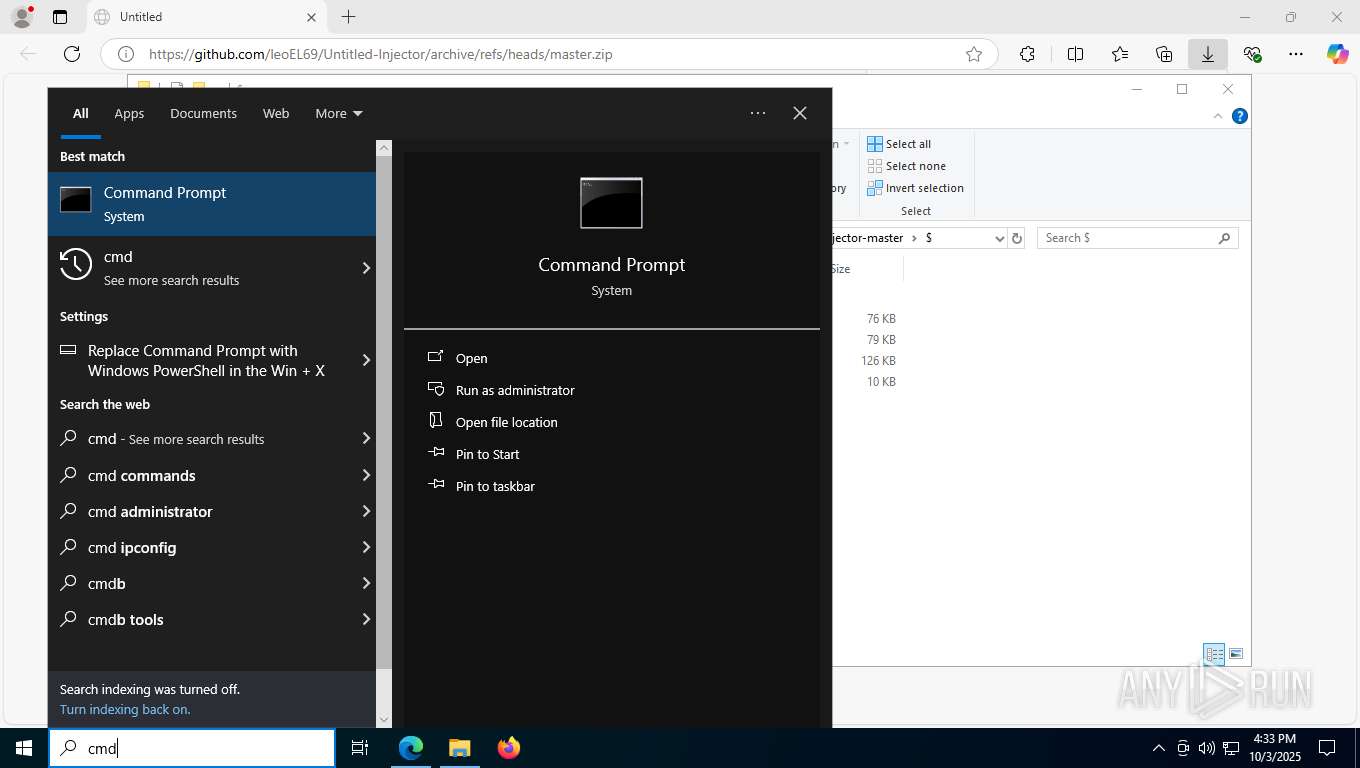
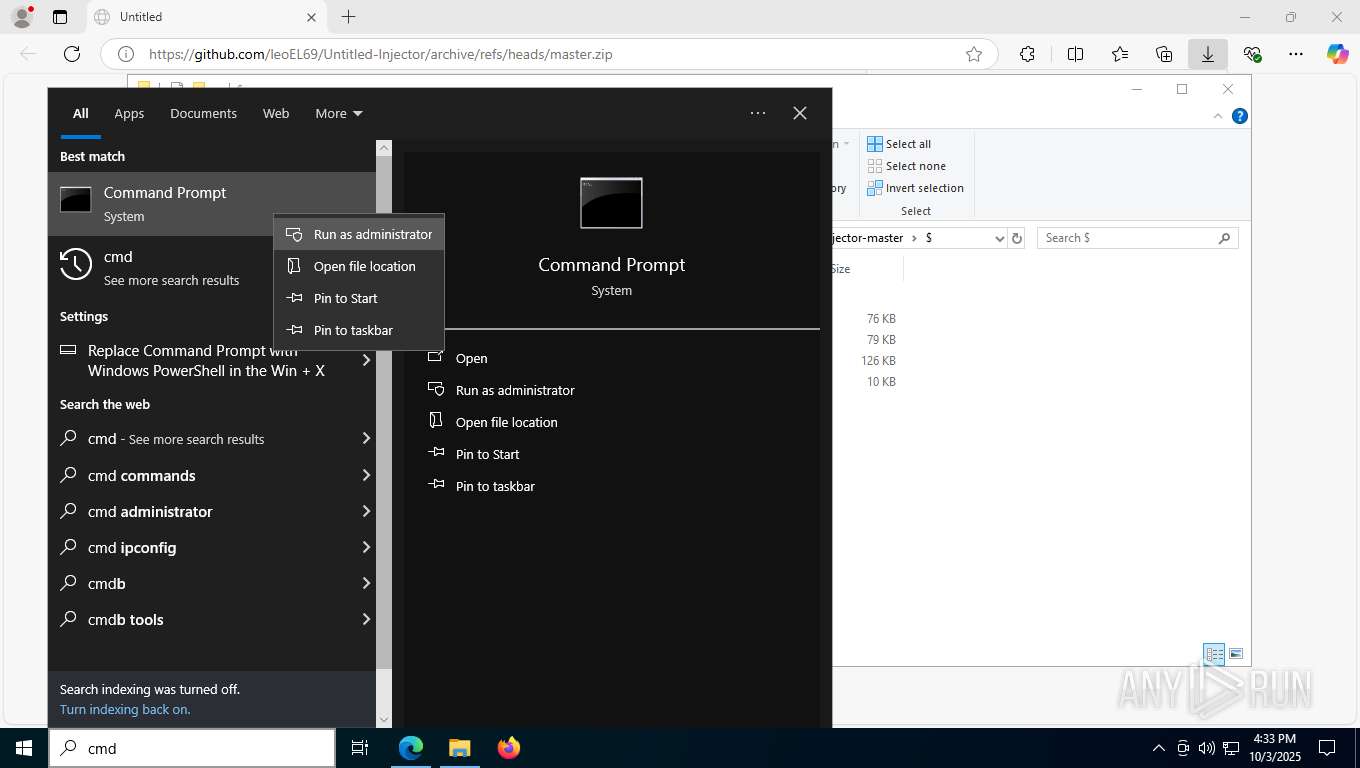
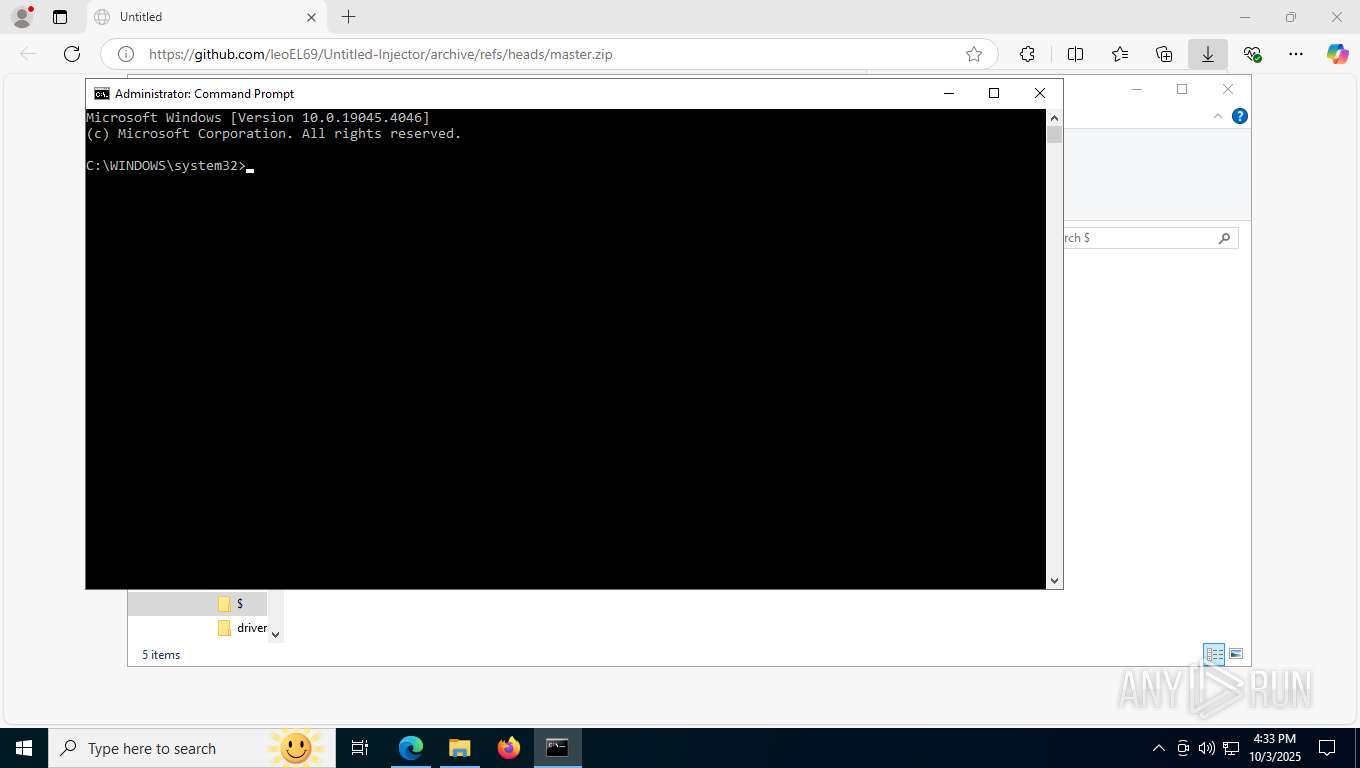
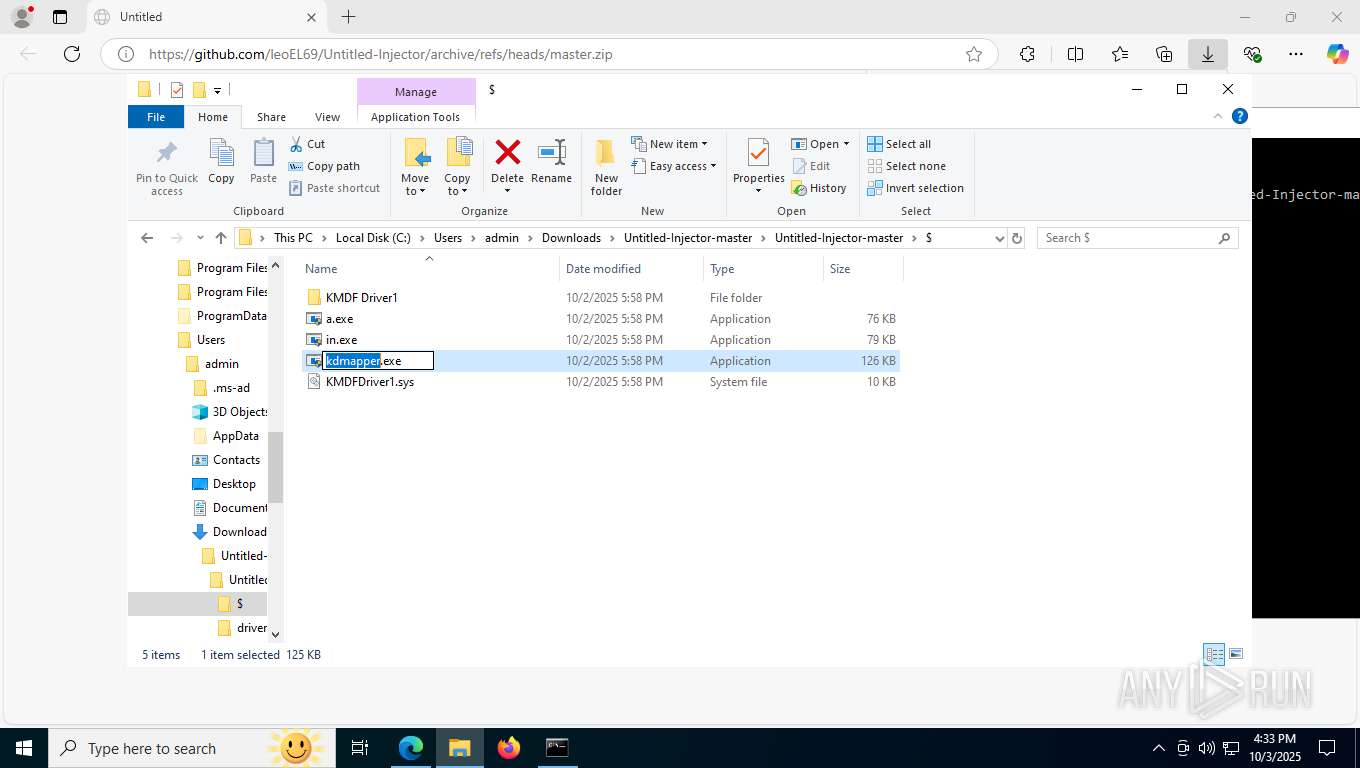
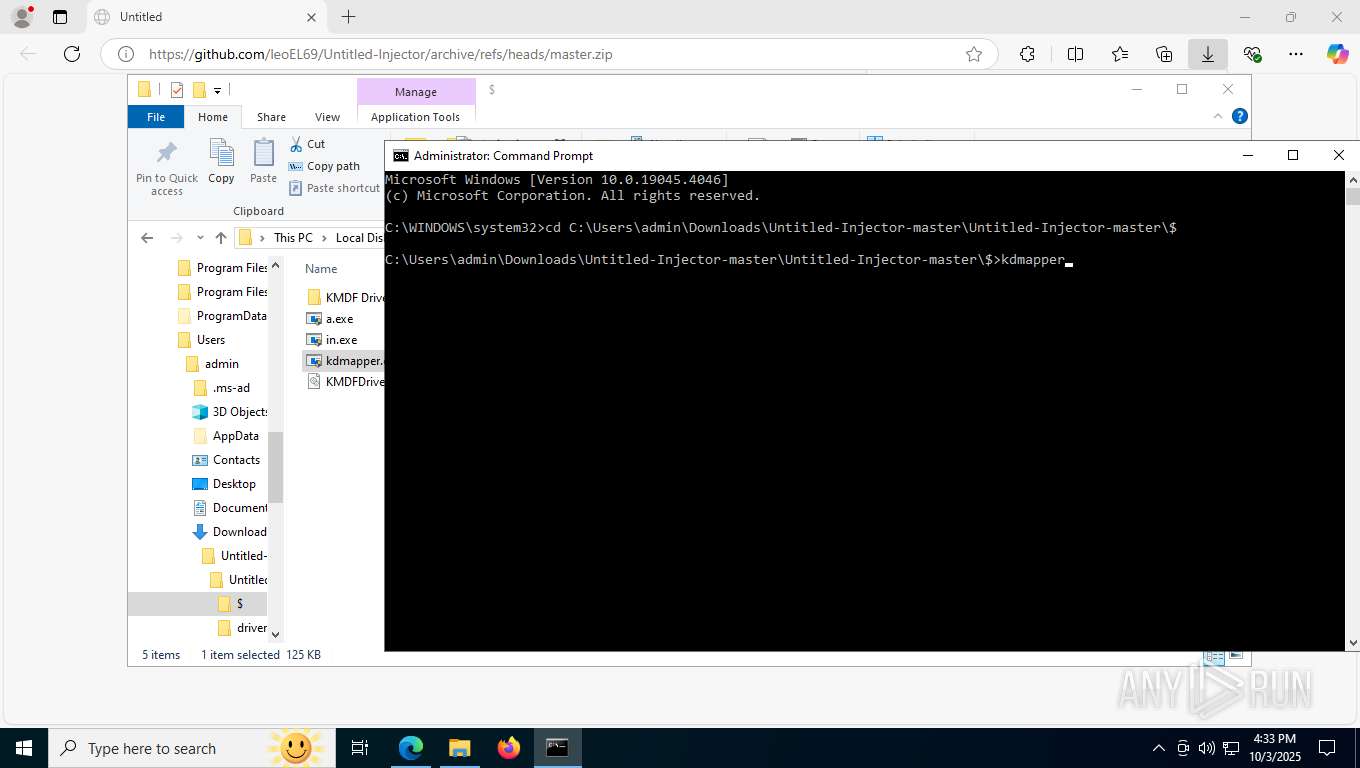
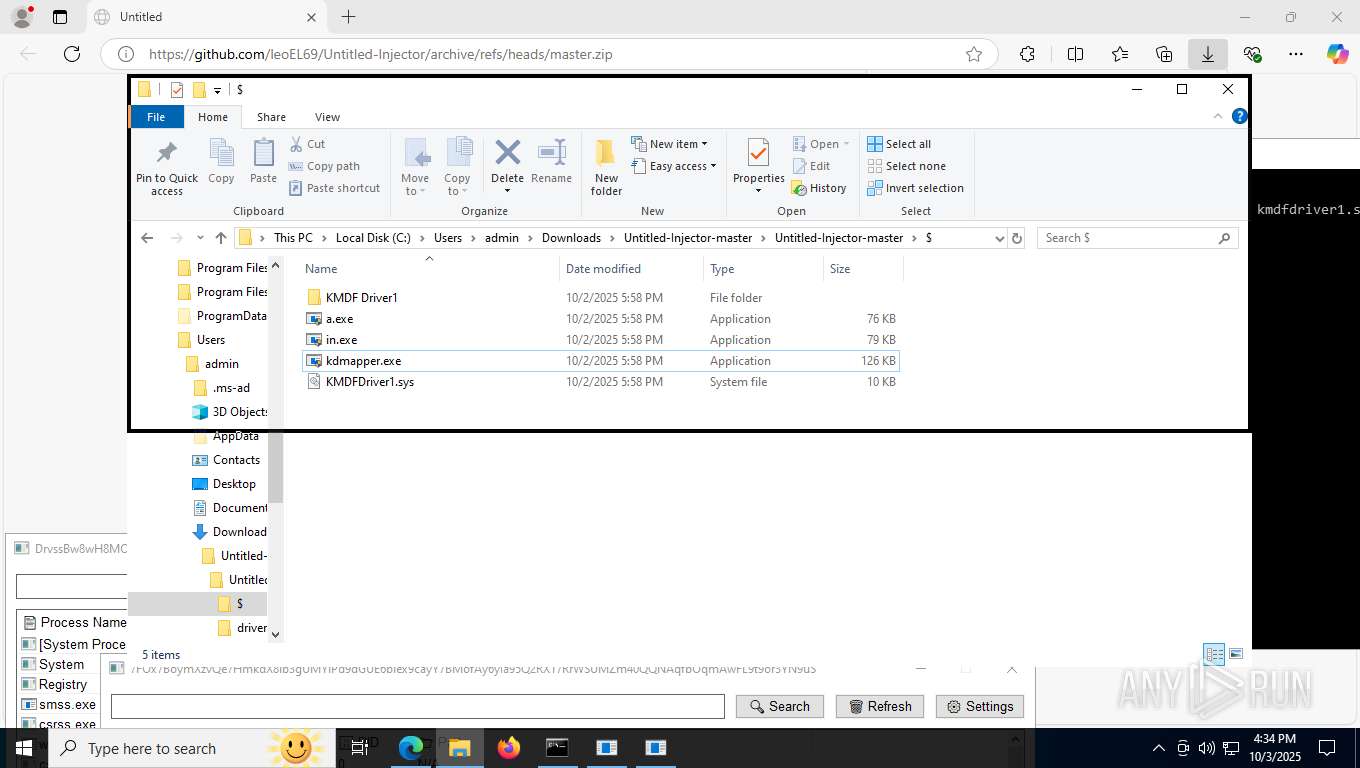
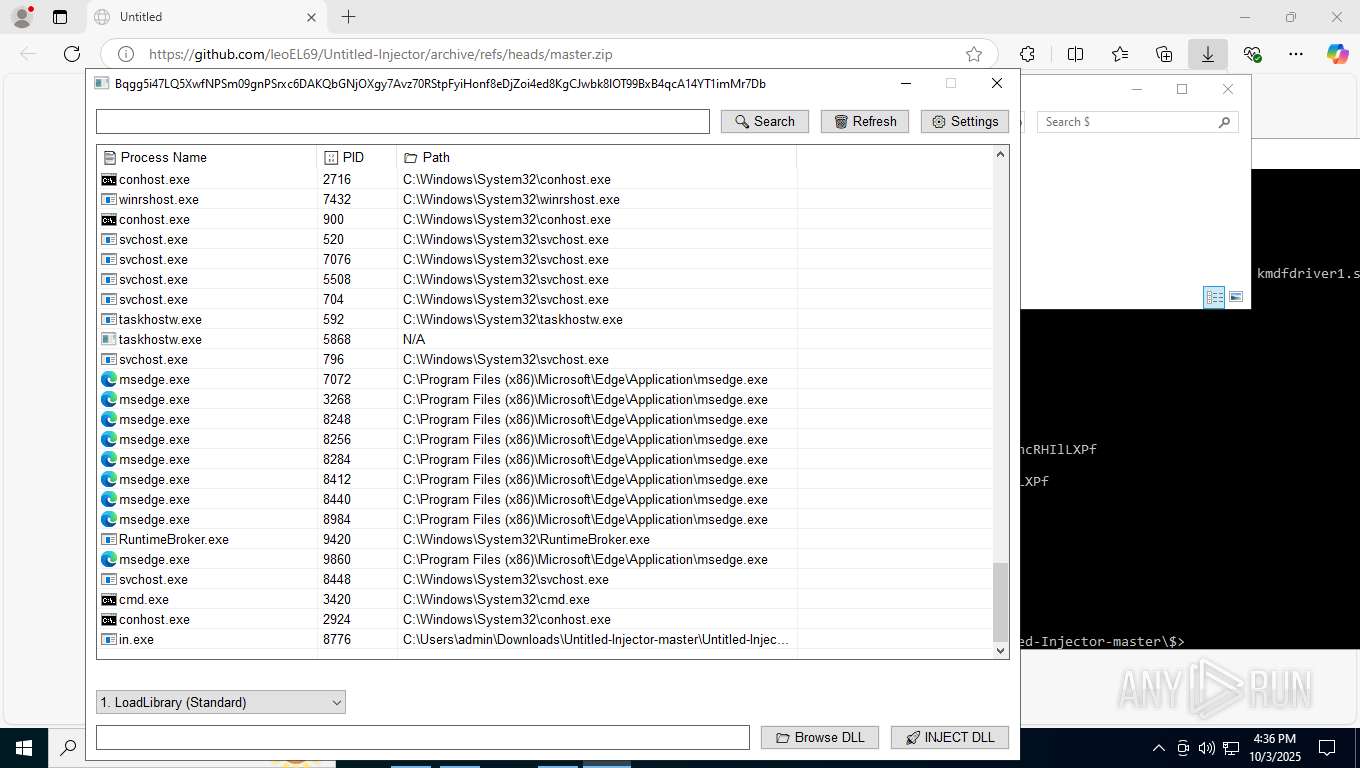
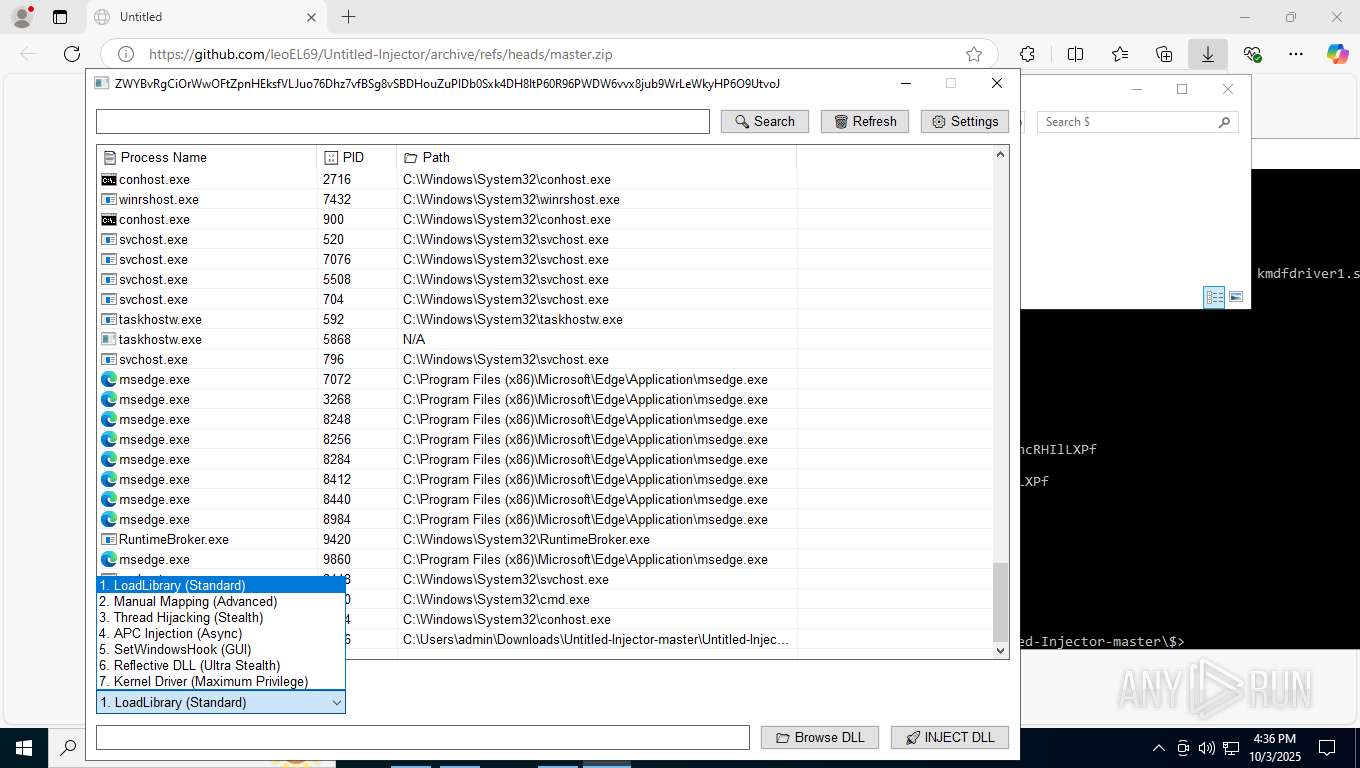
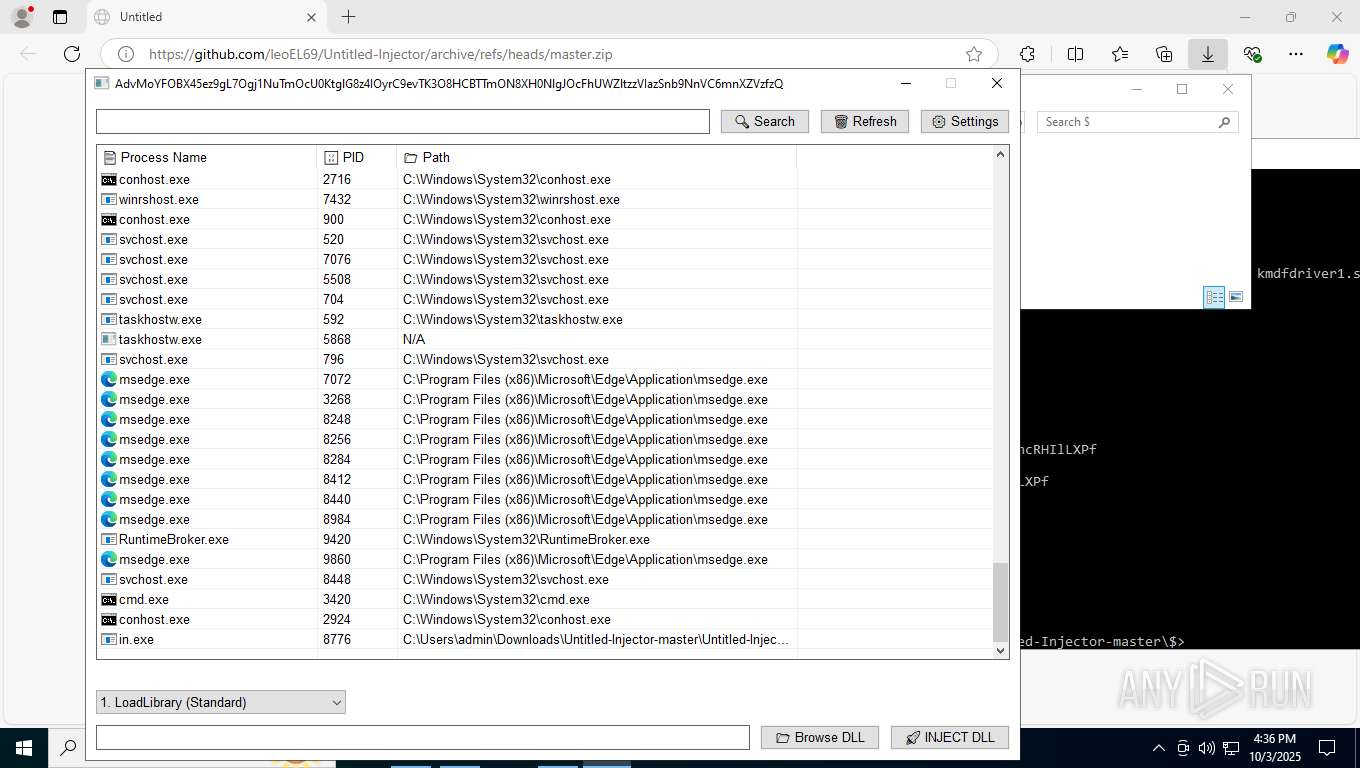
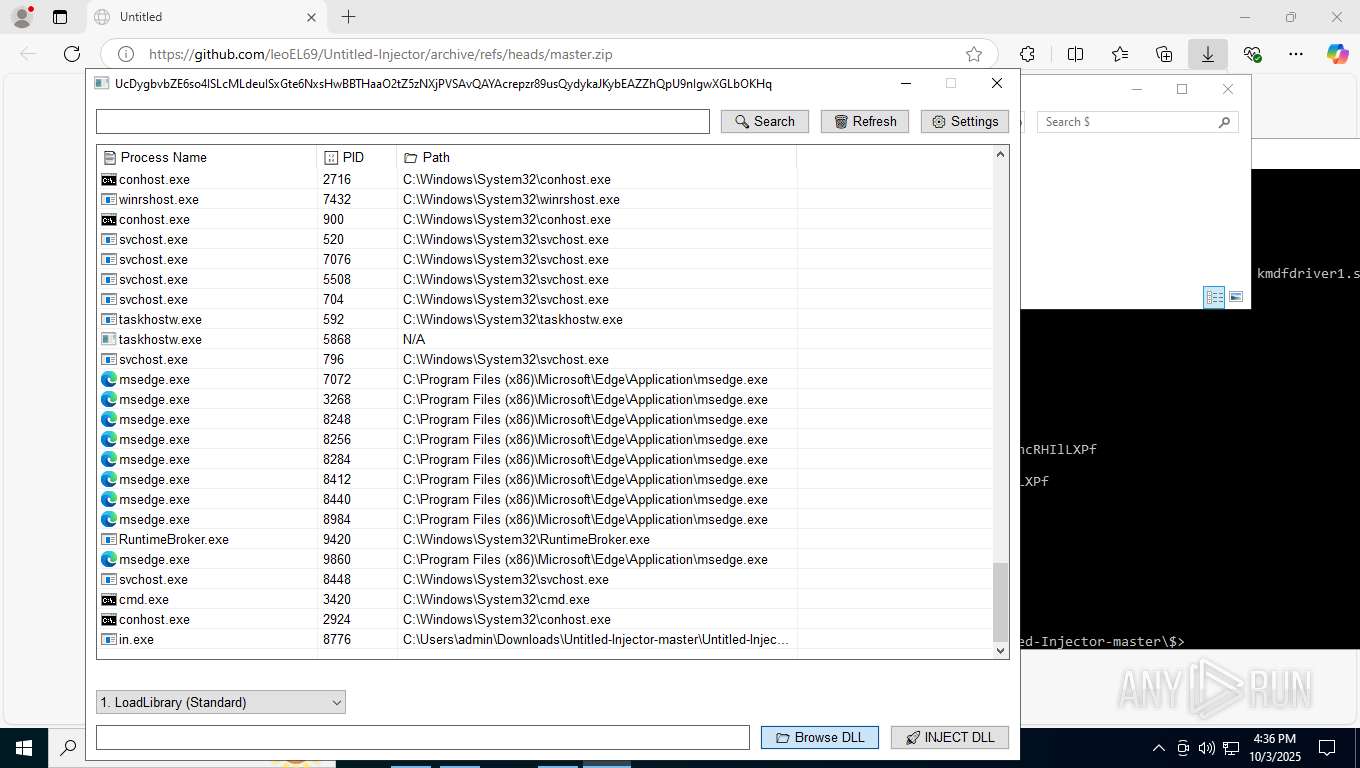
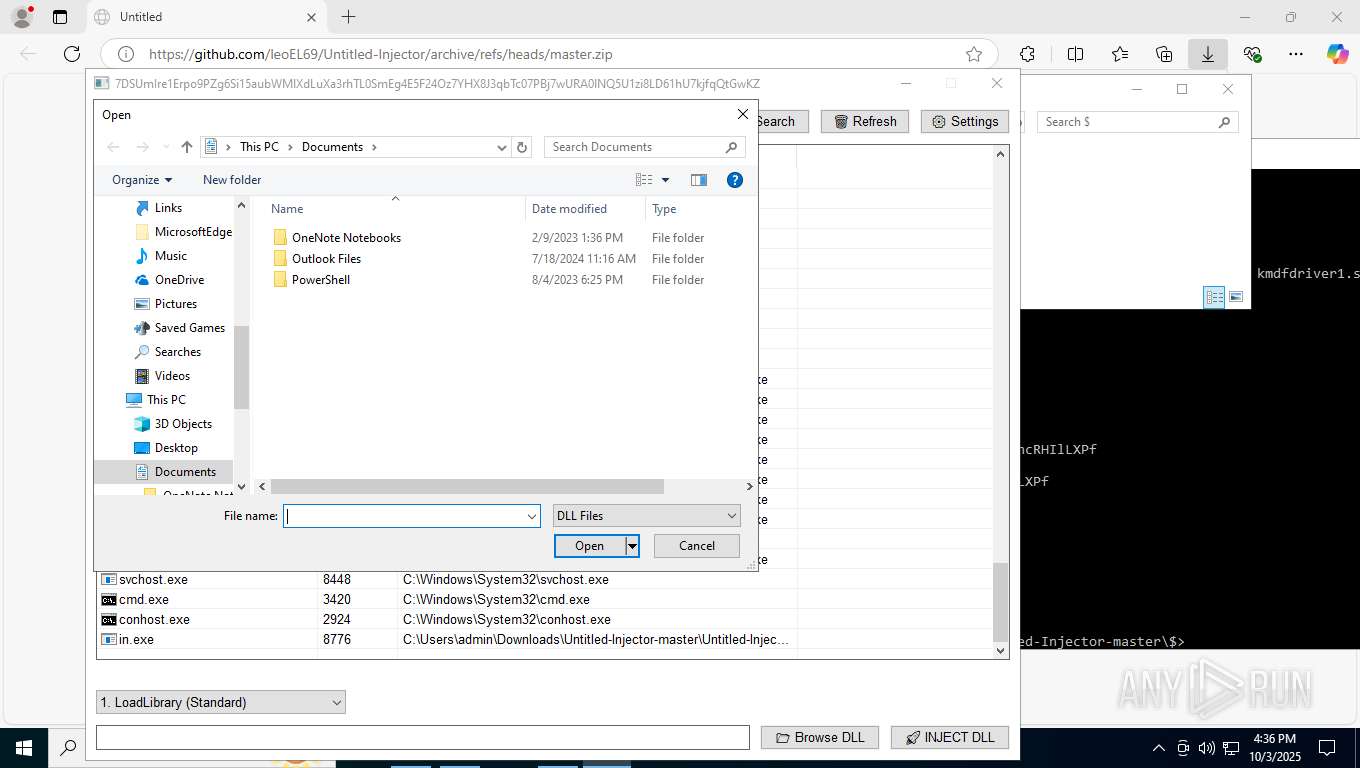
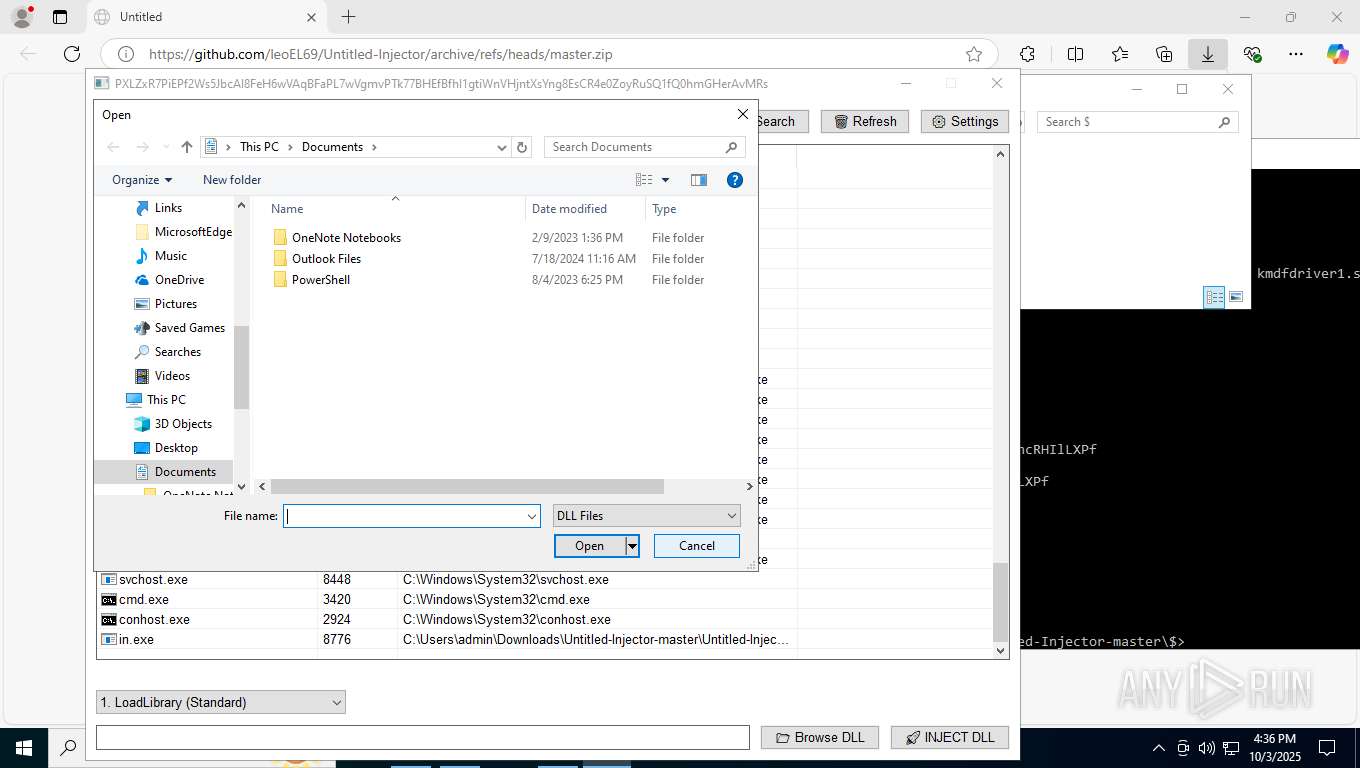
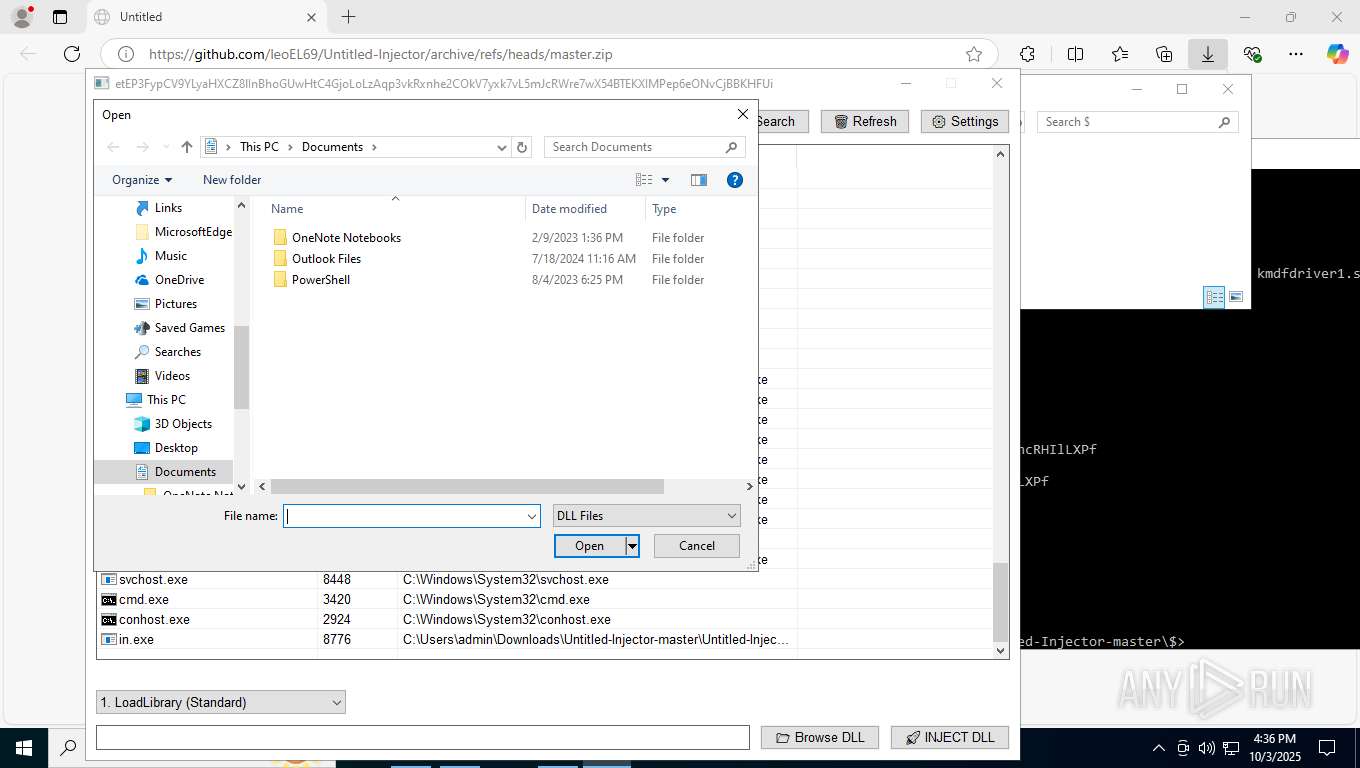
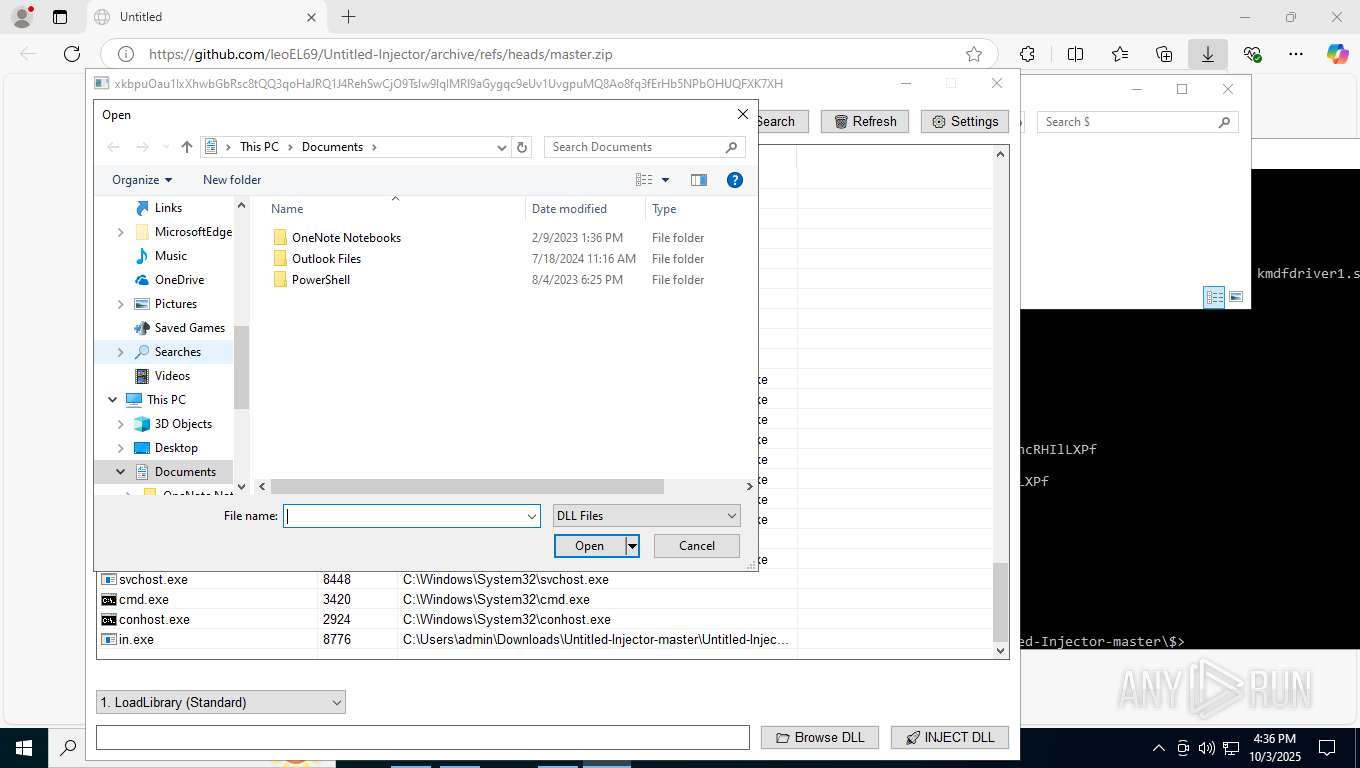
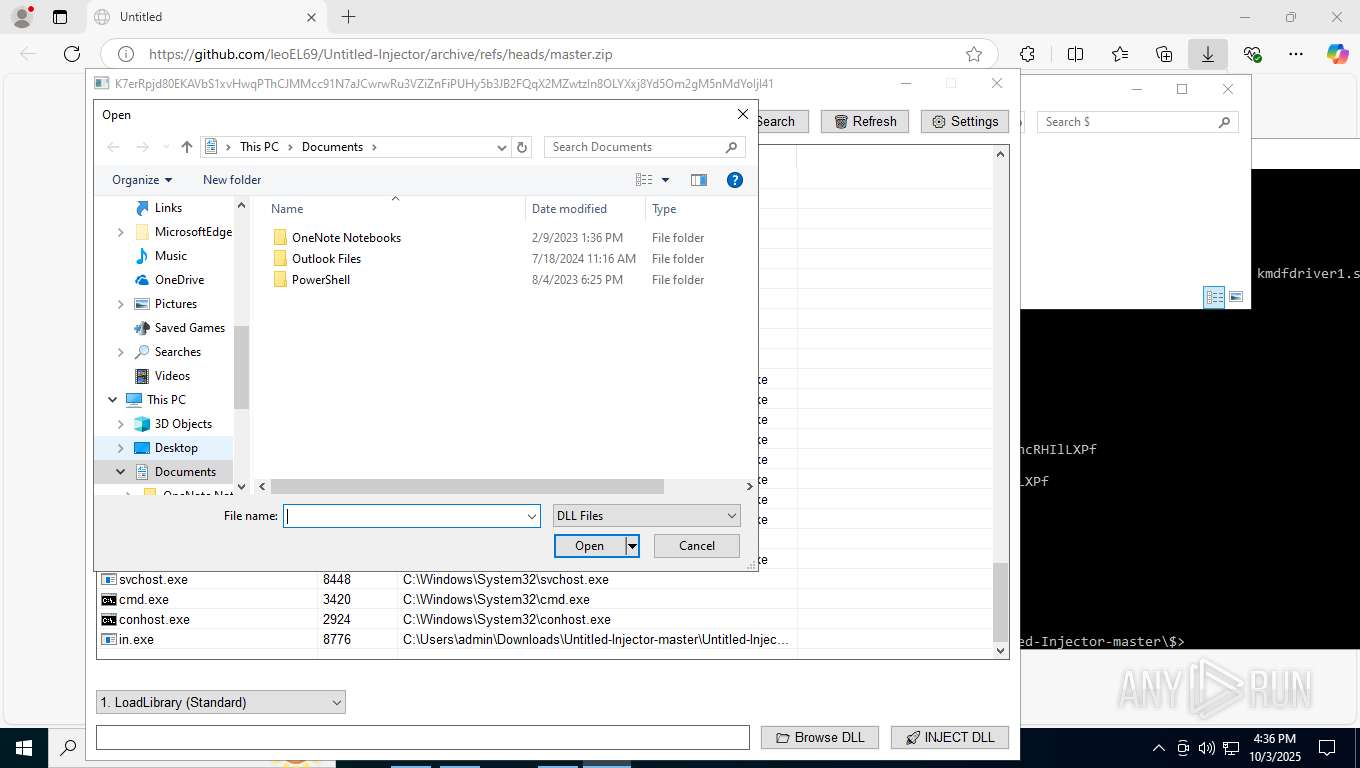
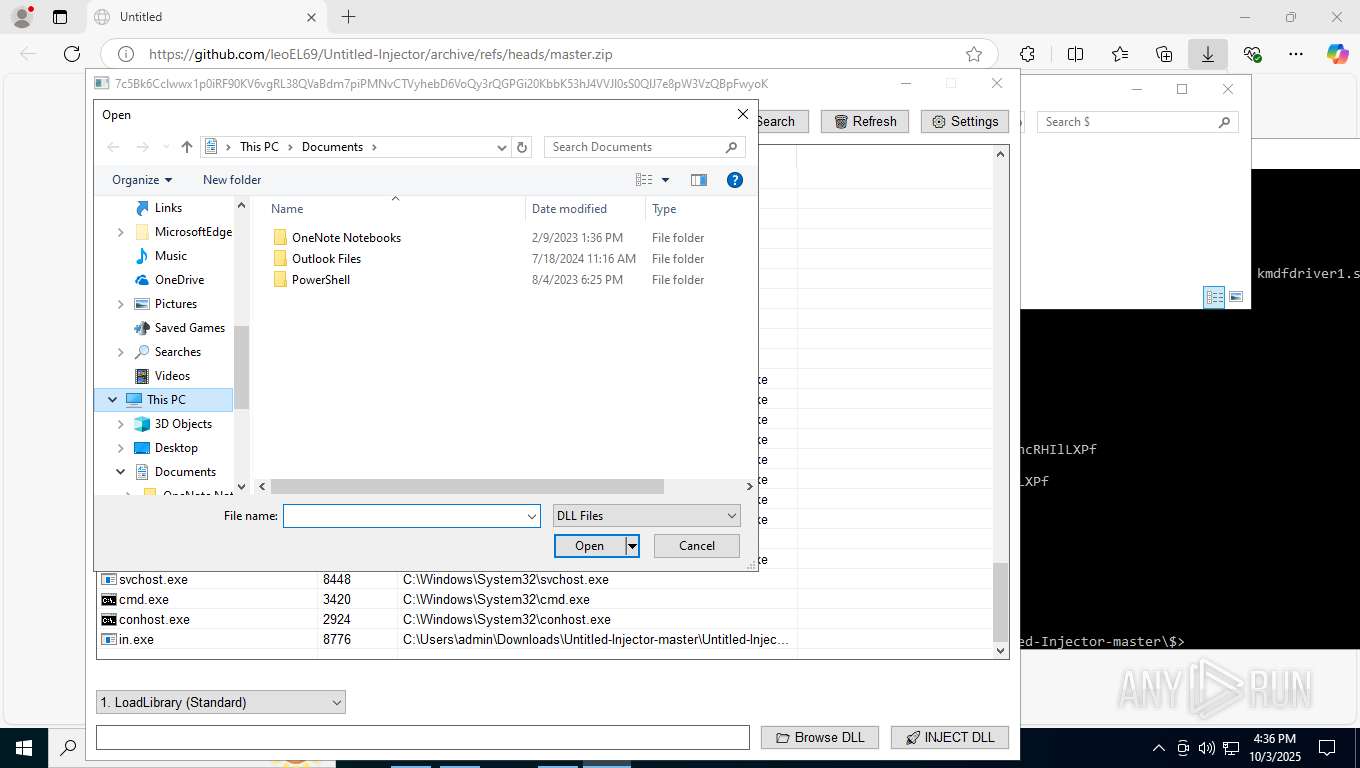
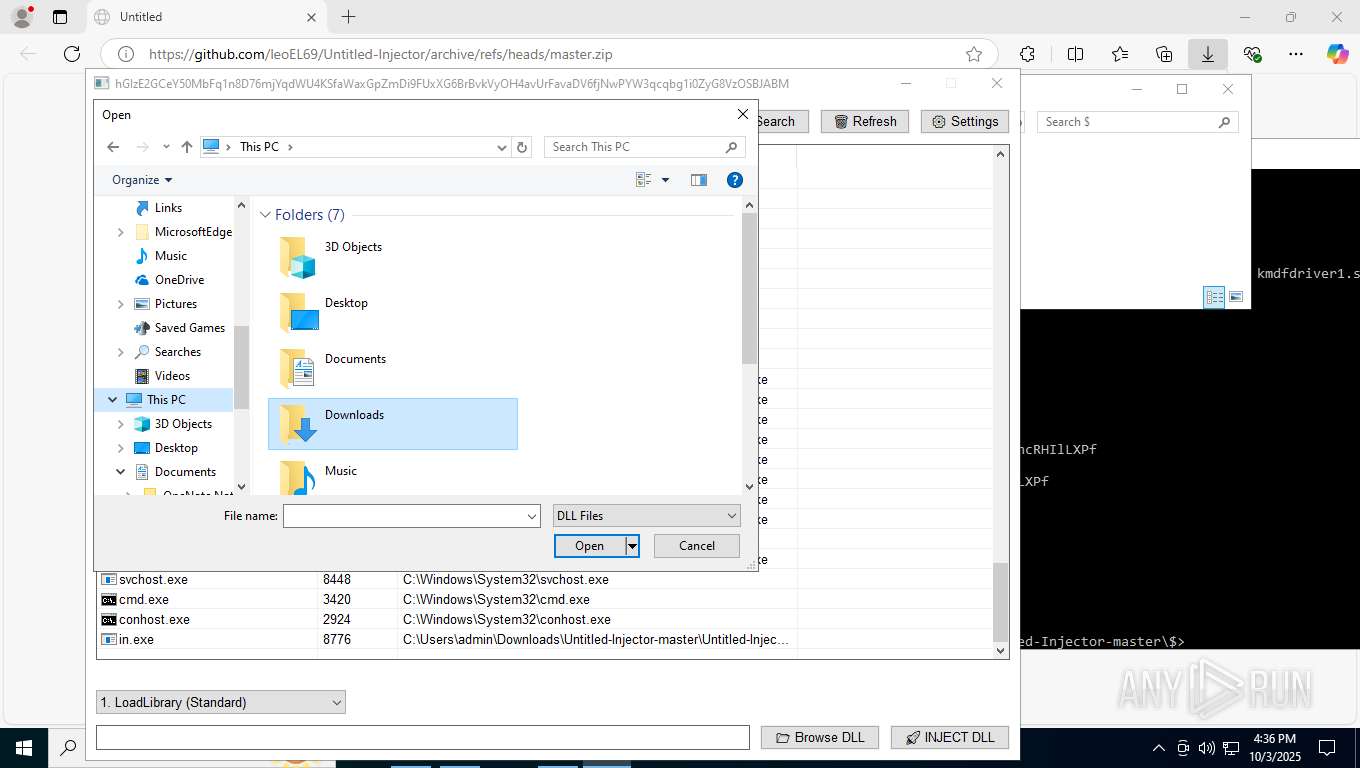
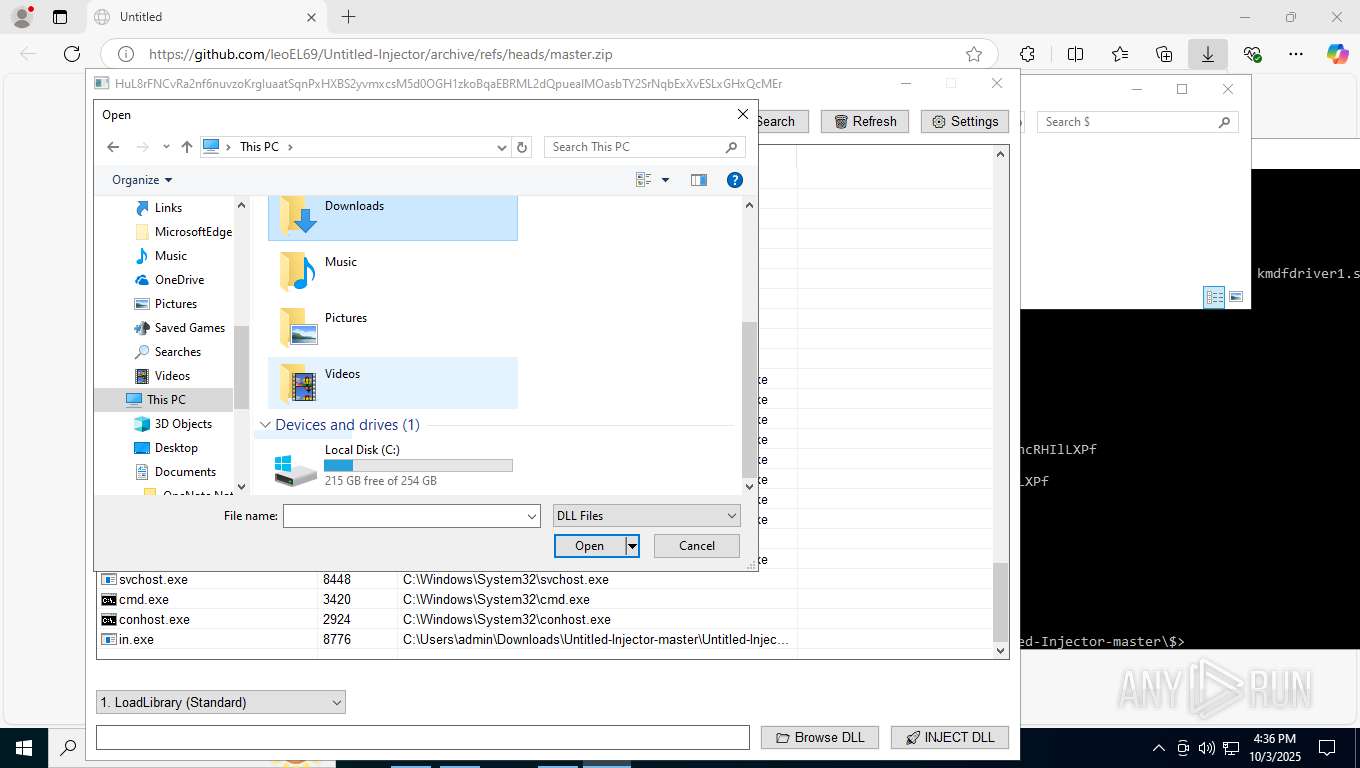
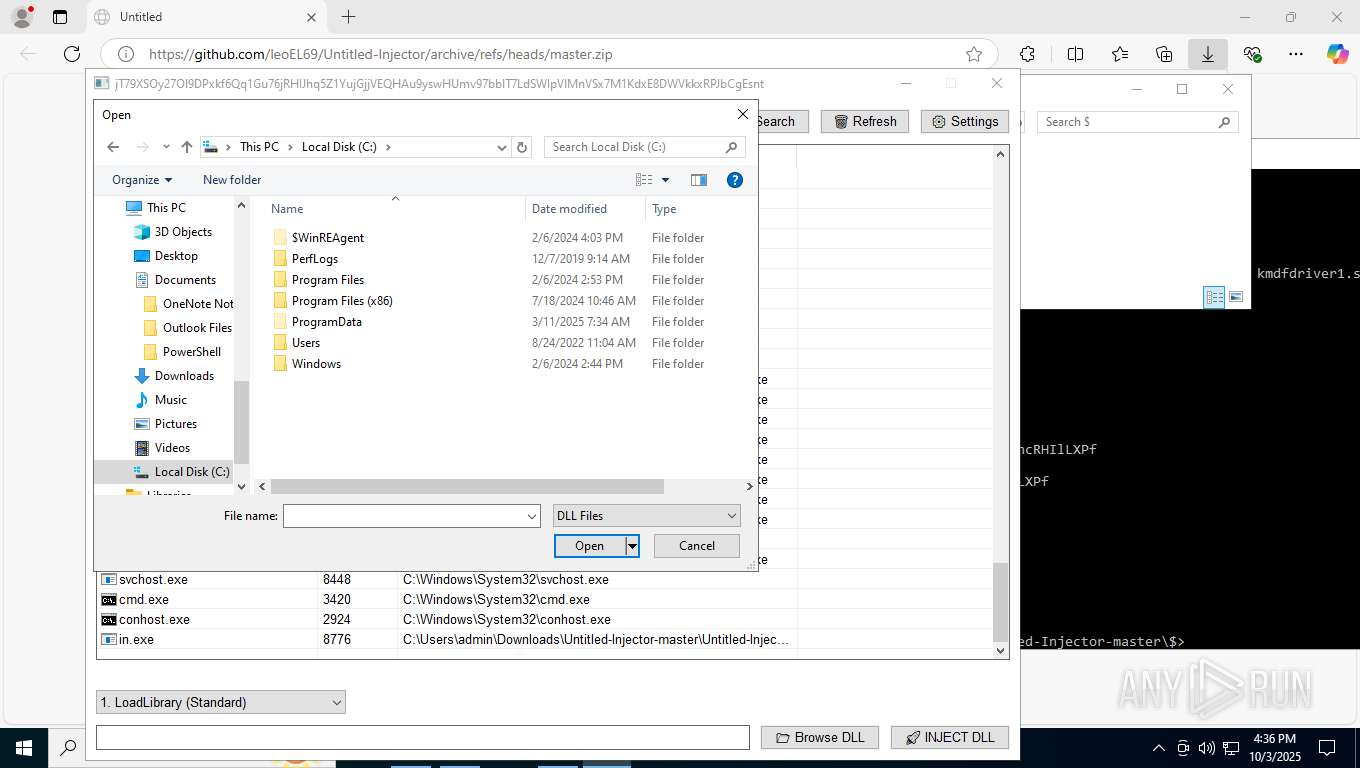
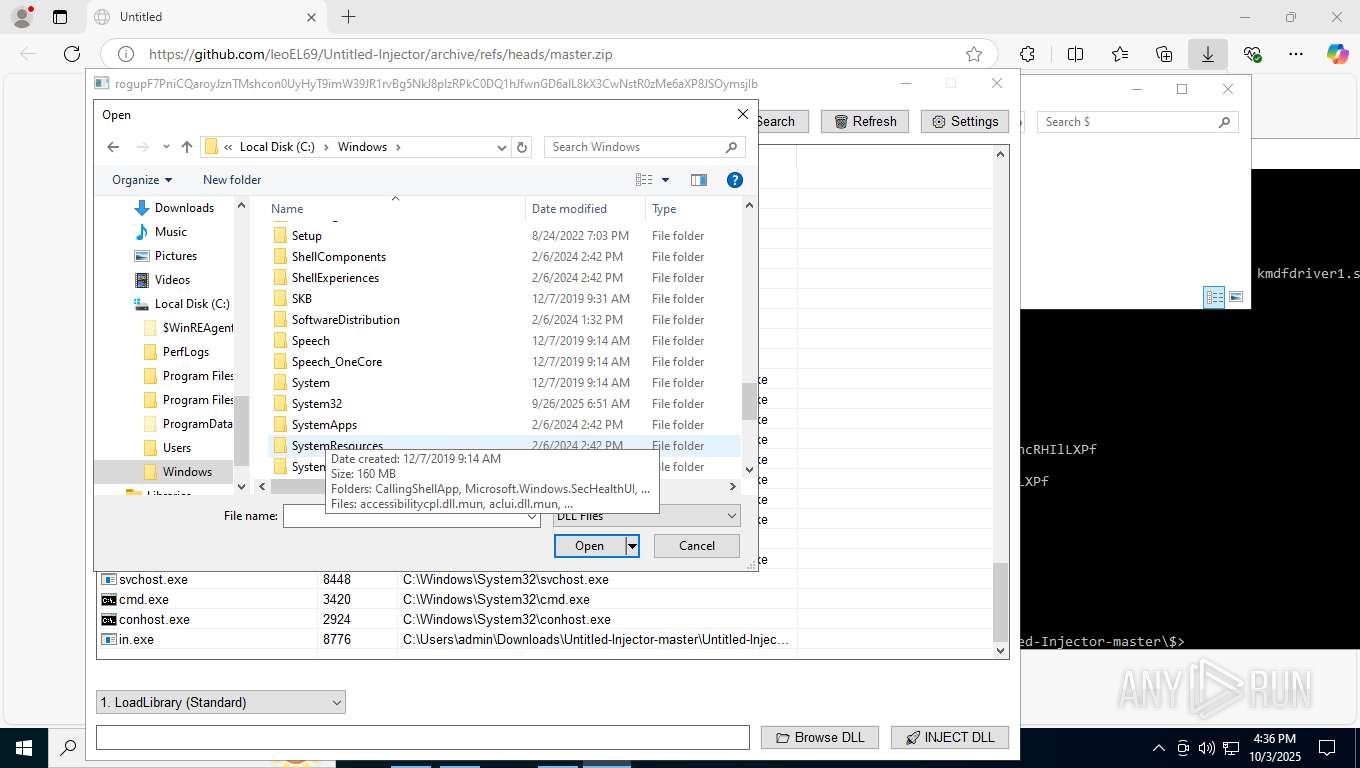
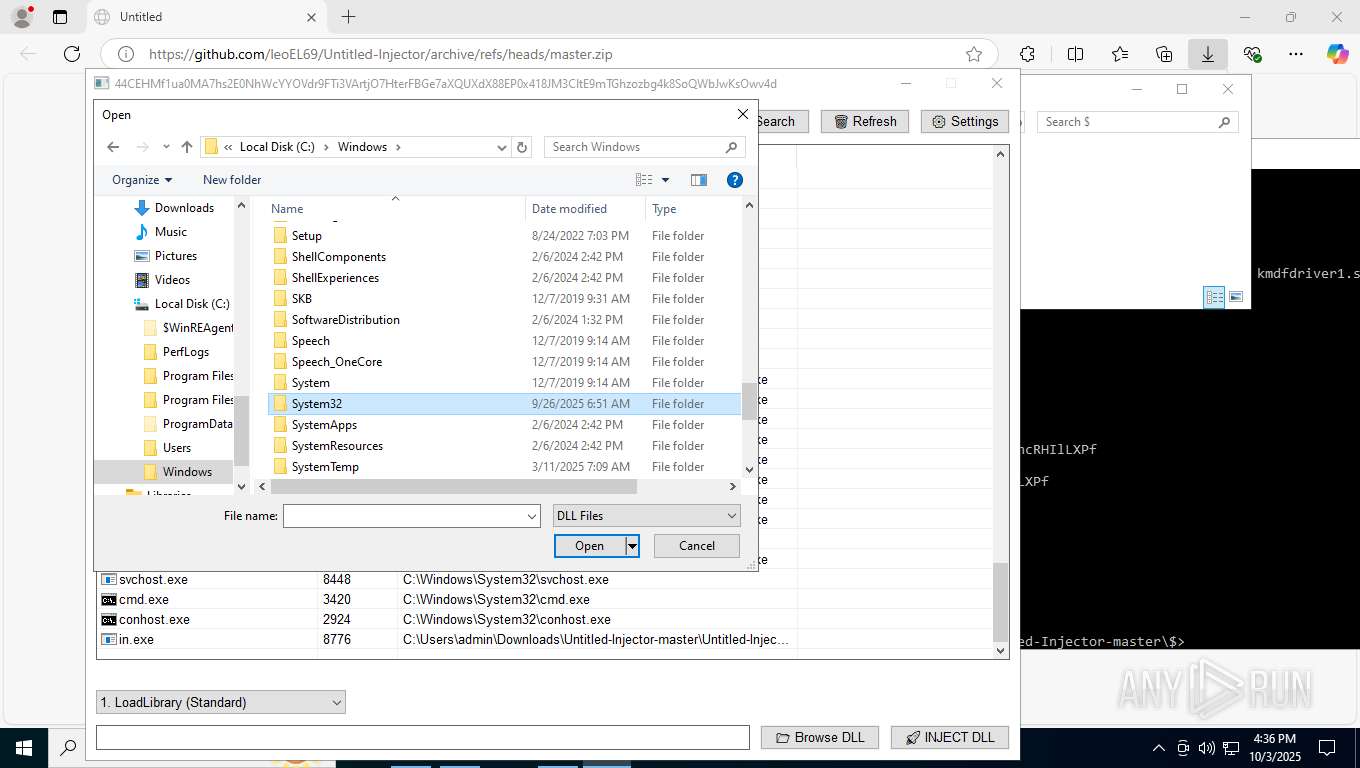
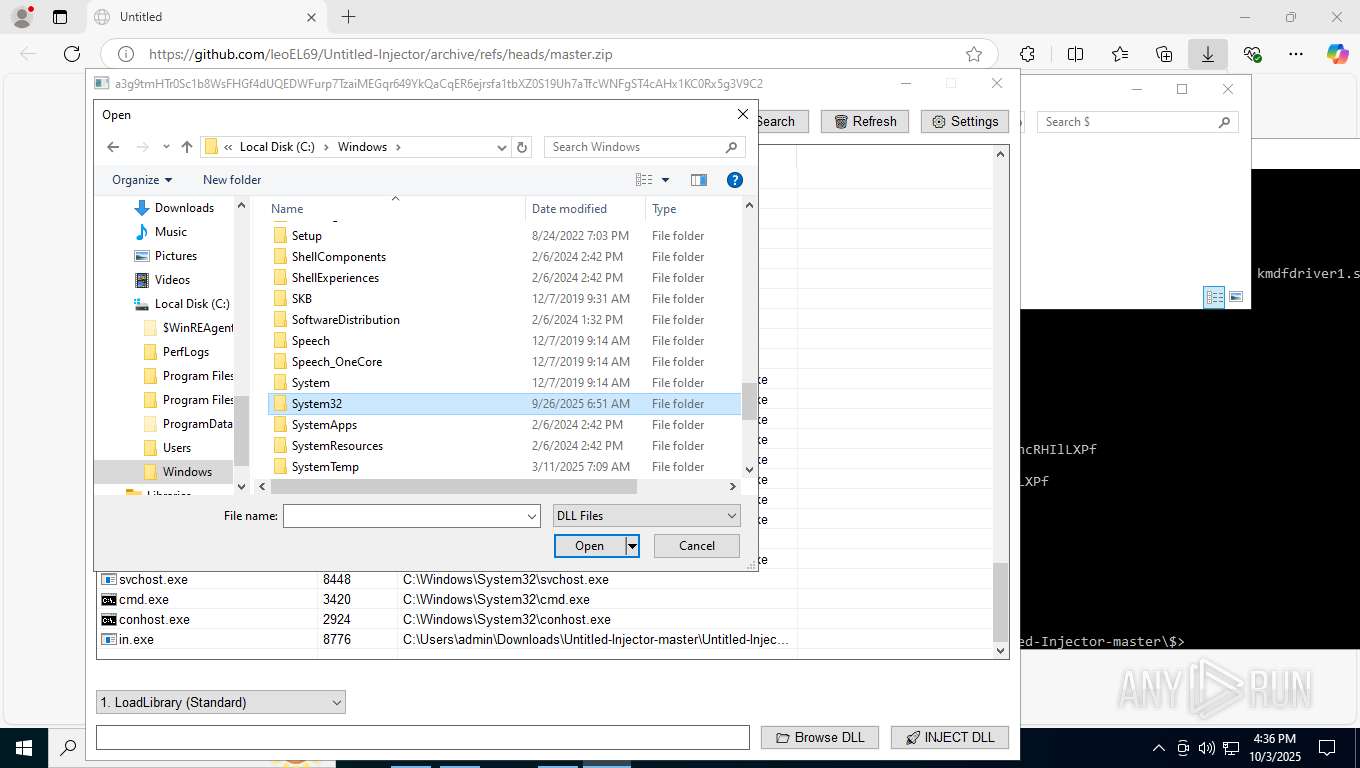
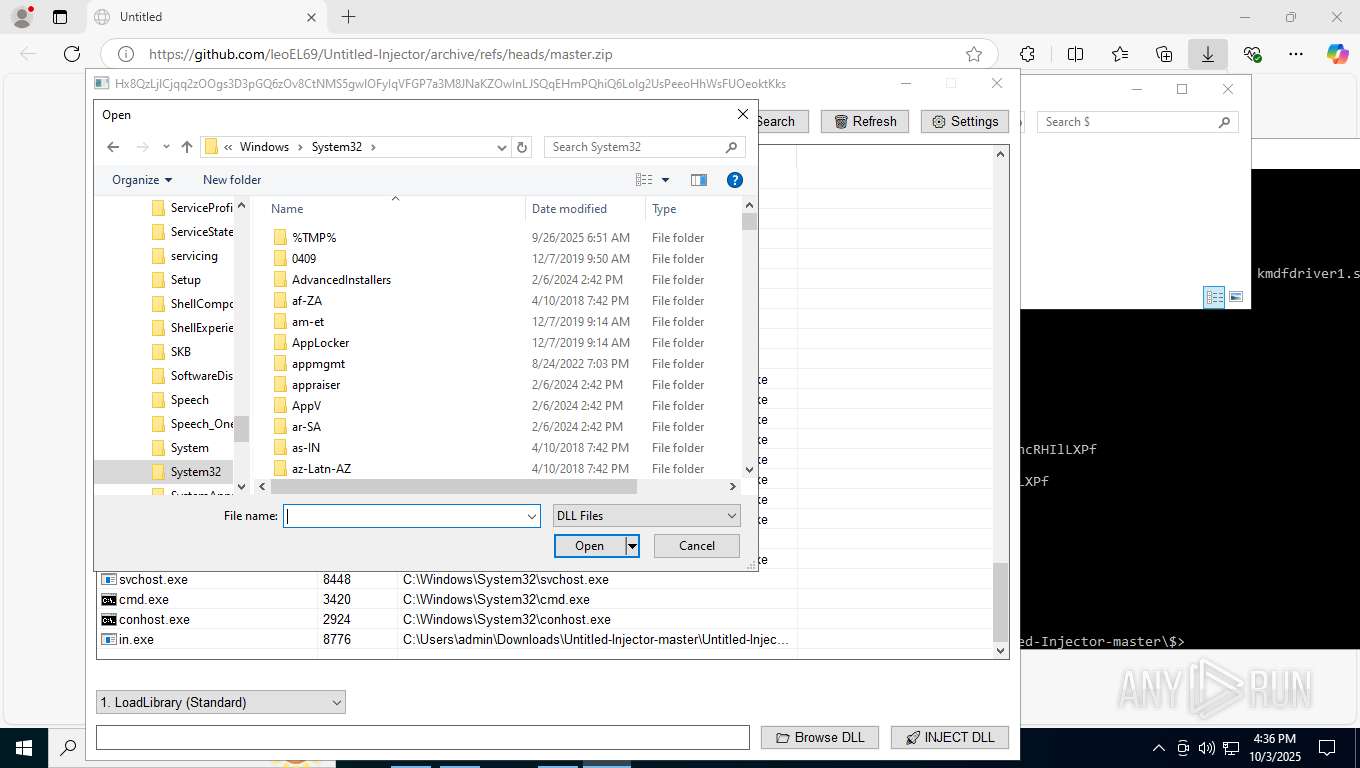
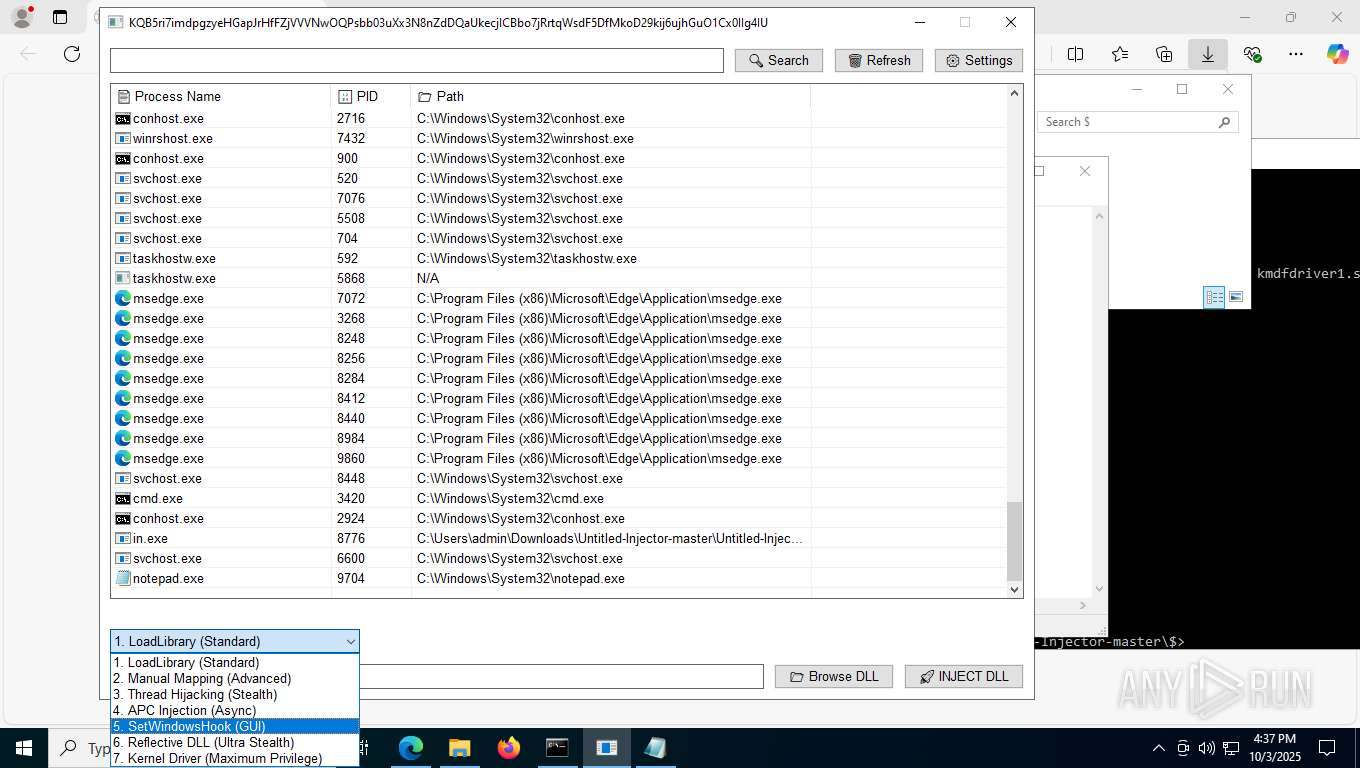
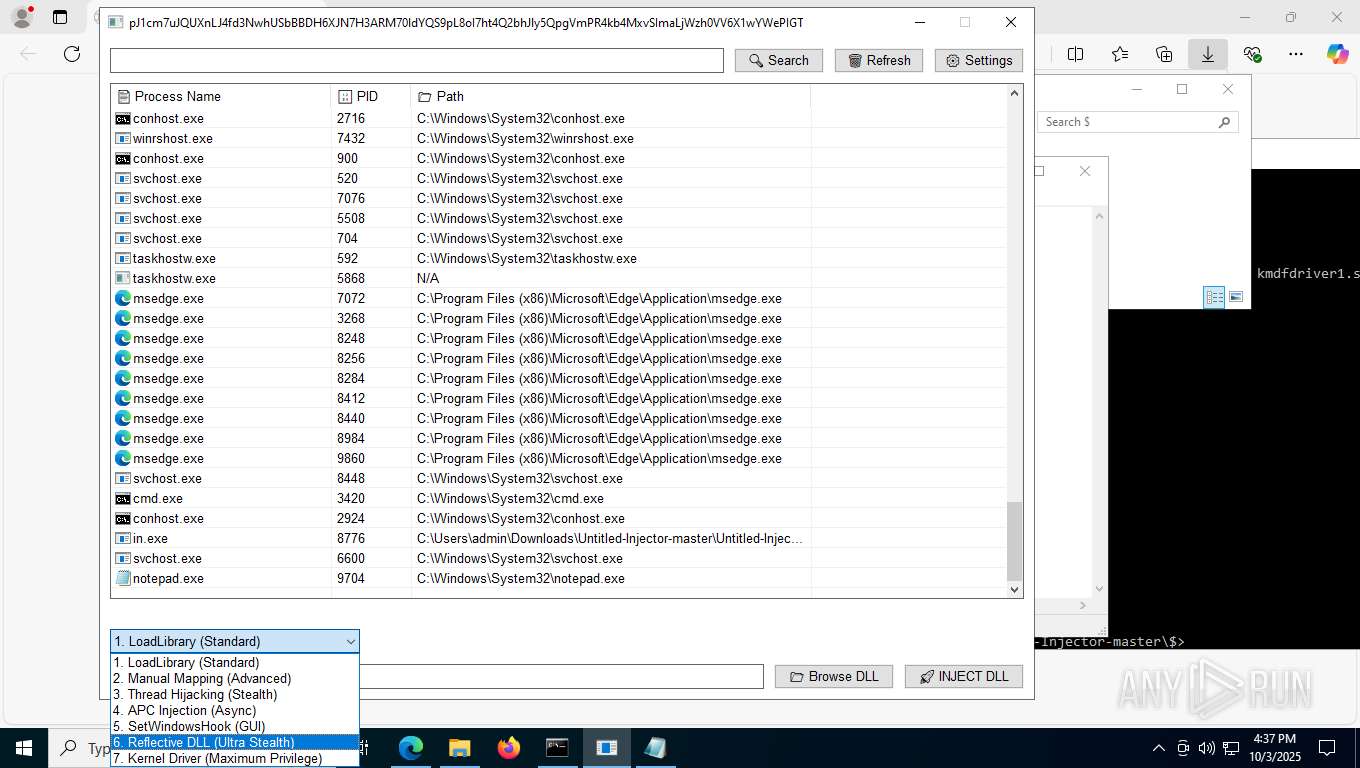
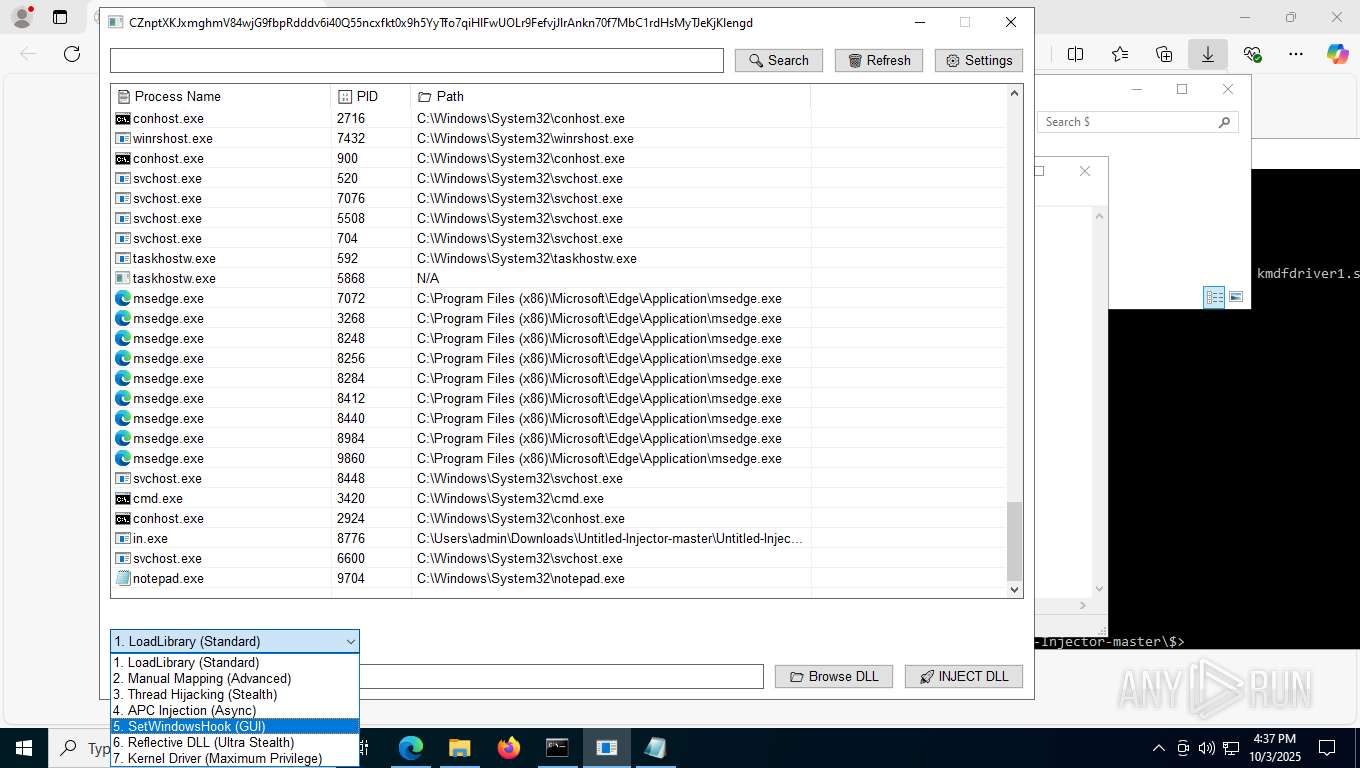
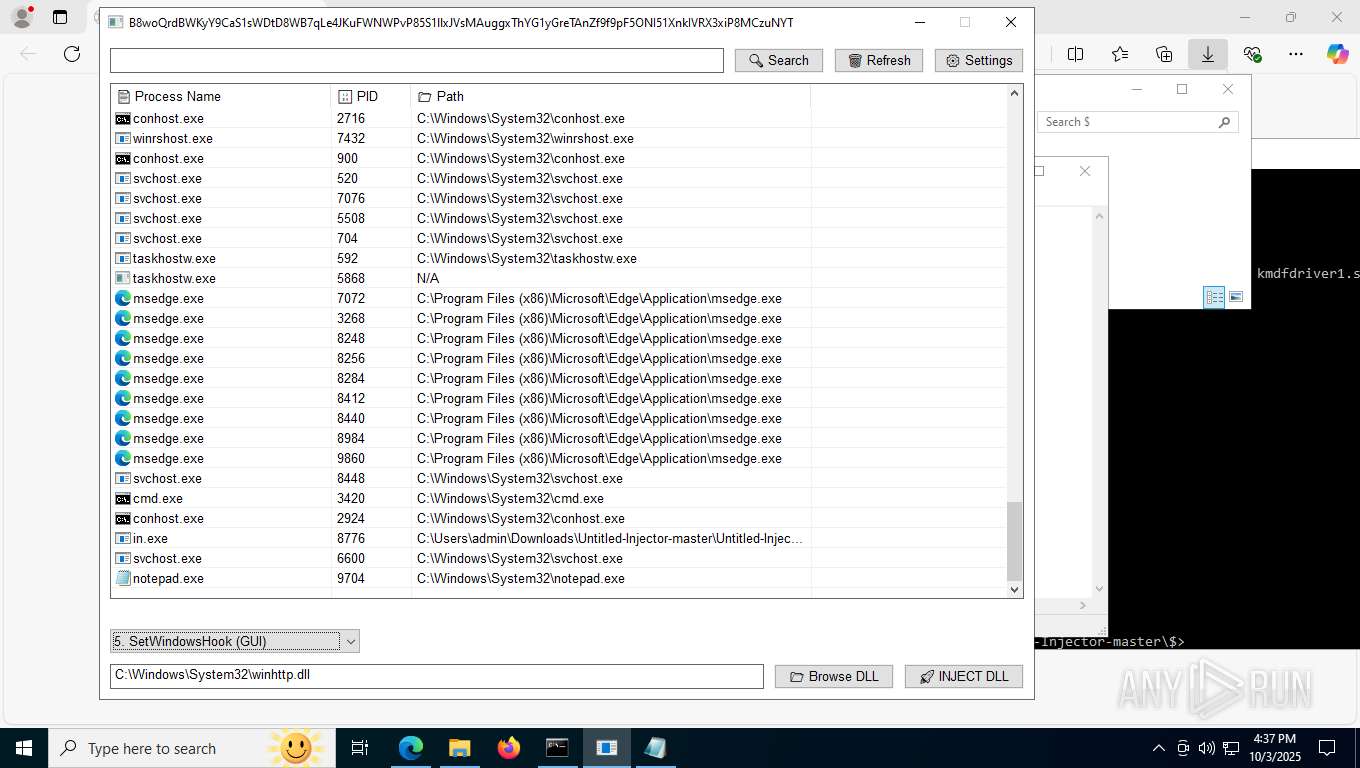
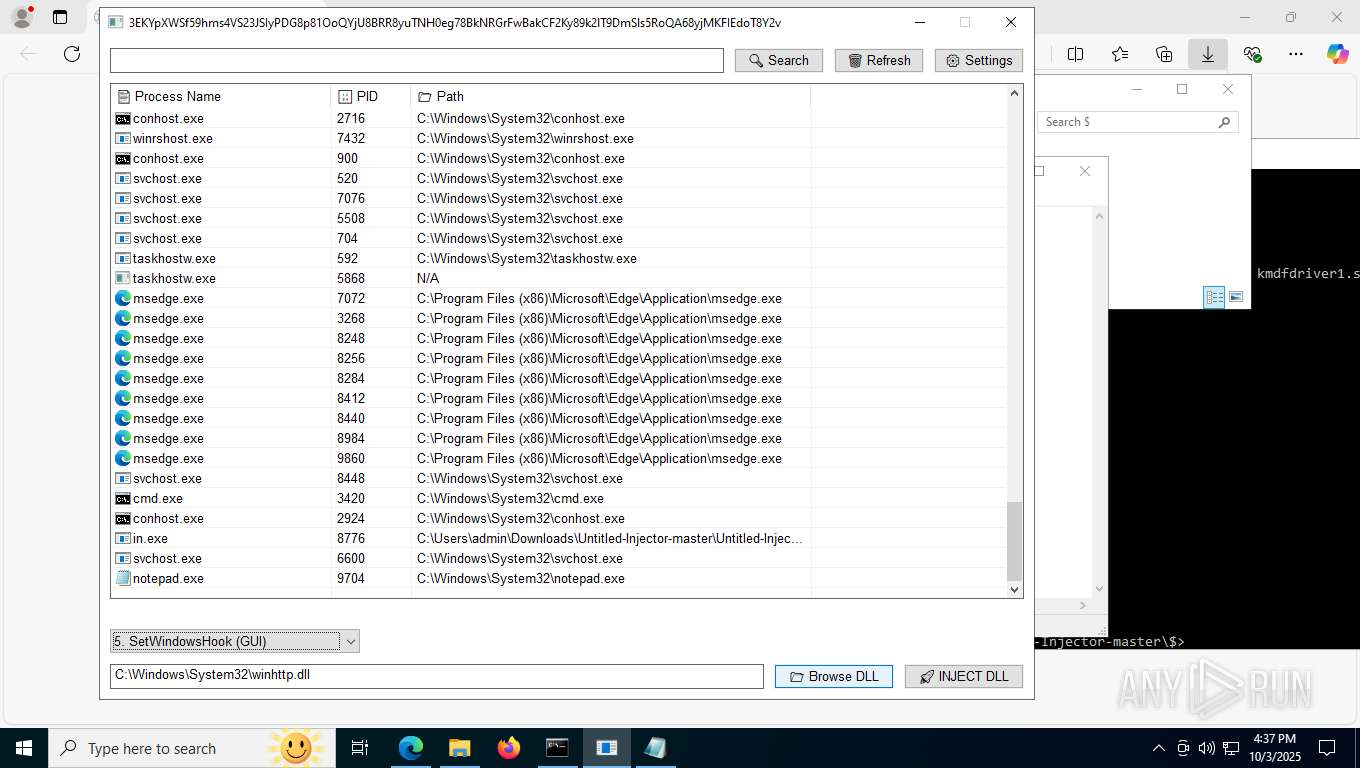
Manual execution by a user
- kdmapper.exe (PID: 4184)
- kdmapper.exe (PID: 9600)
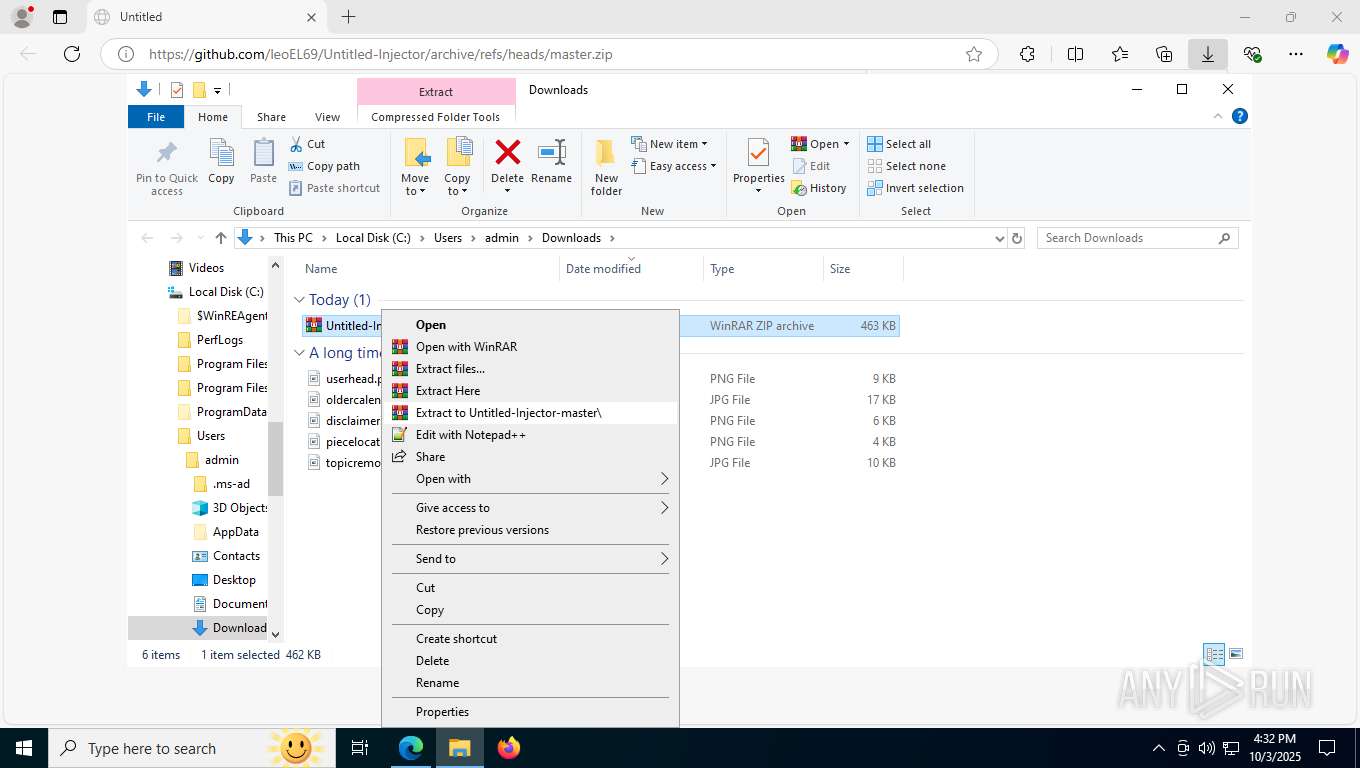
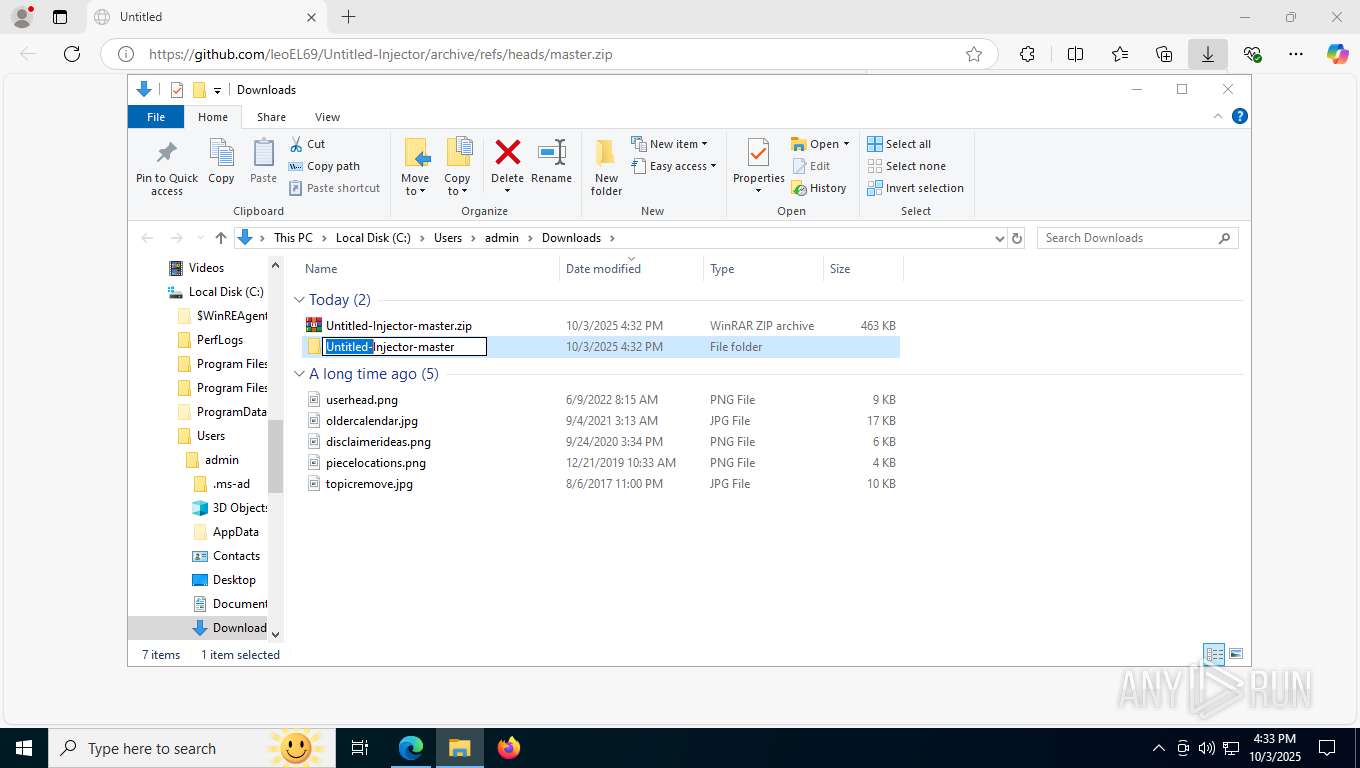
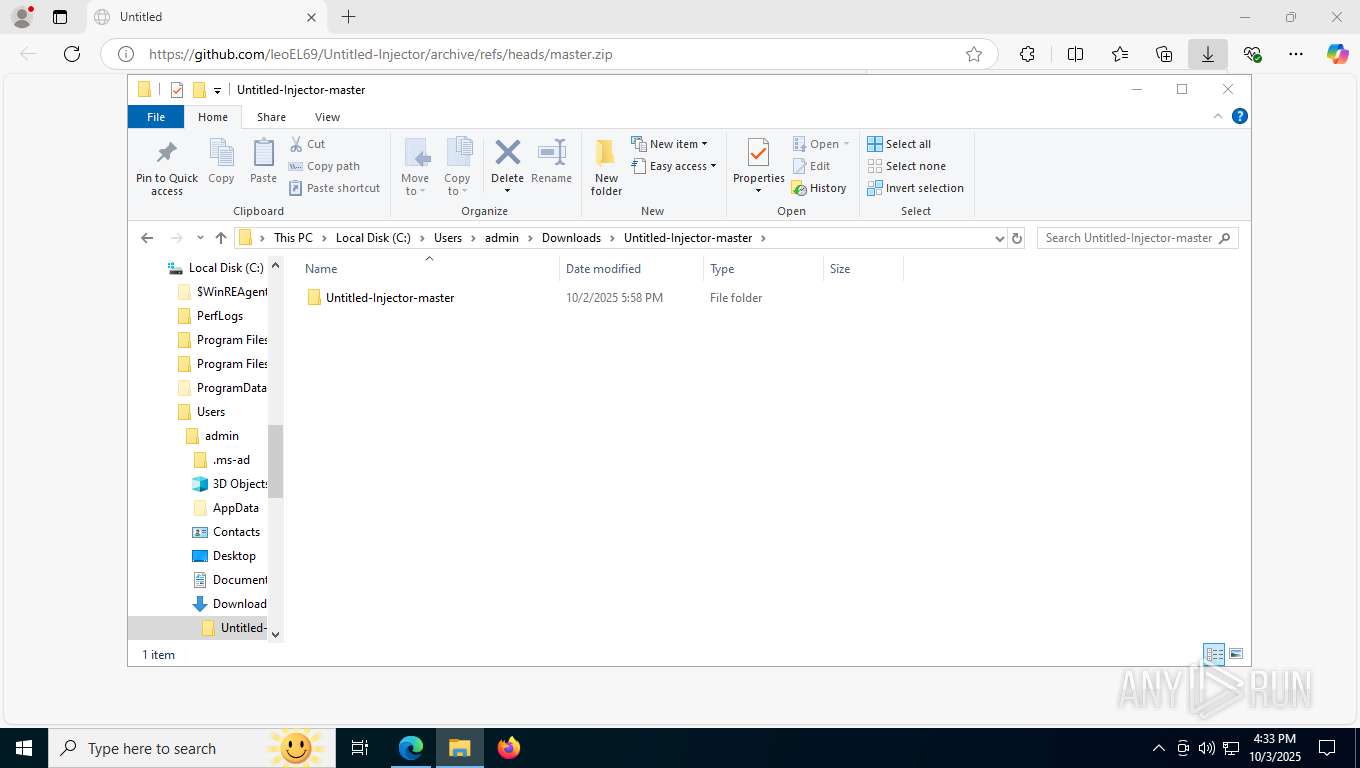
- WinRAR.exe (PID: 3420)
- cmd.exe (PID: 3420)
- in.exe (PID: 8776)
- in.exe (PID: 2368)
- notepad.exe (PID: 9704)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 2488)
- BackgroundTransferHost.exe (PID: 7656)
- BackgroundTransferHost.exe (PID: 9896)
- BackgroundTransferHost.exe (PID: 10056)
- BackgroundTransferHost.exe (PID: 9788)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 10056)
- slui.exe (PID: 2168)
- WerFault.exe (PID: 9596)
Checks supported languages
- kdmapper.exe (PID: 9600)
- identity_helper.exe (PID: 9132)
- kdmapper.exe (PID: 9656)
- in.exe (PID: 8880)
- a.exe (PID: 1828)
- kdmapper.exe (PID: 1476)
- in.exe (PID: 8776)
Create files in a temporary directory
- kdmapper.exe (PID: 9600)
- kdmapper.exe (PID: 9656)
- kdmapper.exe (PID: 1476)
The sample compiled with english language support
- kdmapper.exe (PID: 9600)
- kdmapper.exe (PID: 9656)
- kdmapper.exe (PID: 1476)
Reads the computer name
- in.exe (PID: 8880)
- a.exe (PID: 1828)
- in.exe (PID: 8776)
- identity_helper.exe (PID: 9132)
Reads Environment values
- identity_helper.exe (PID: 9132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
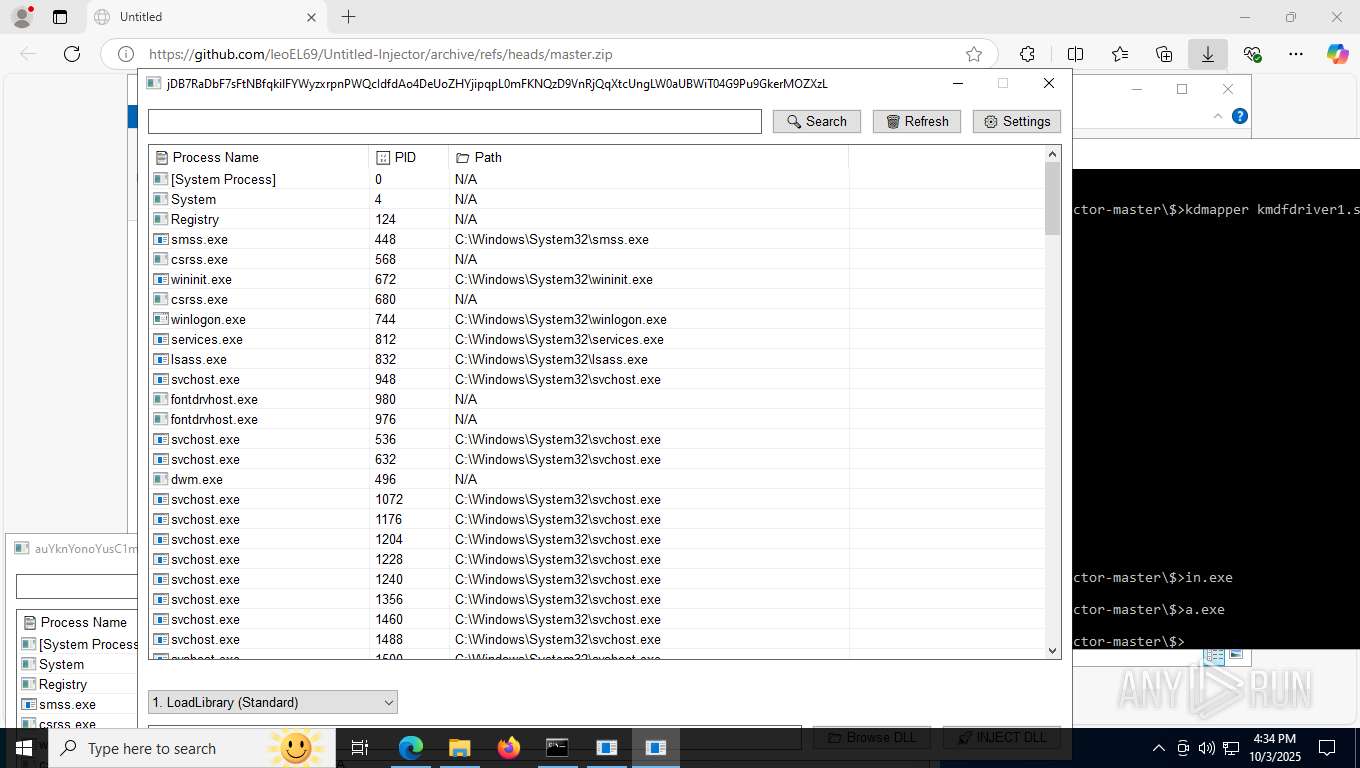
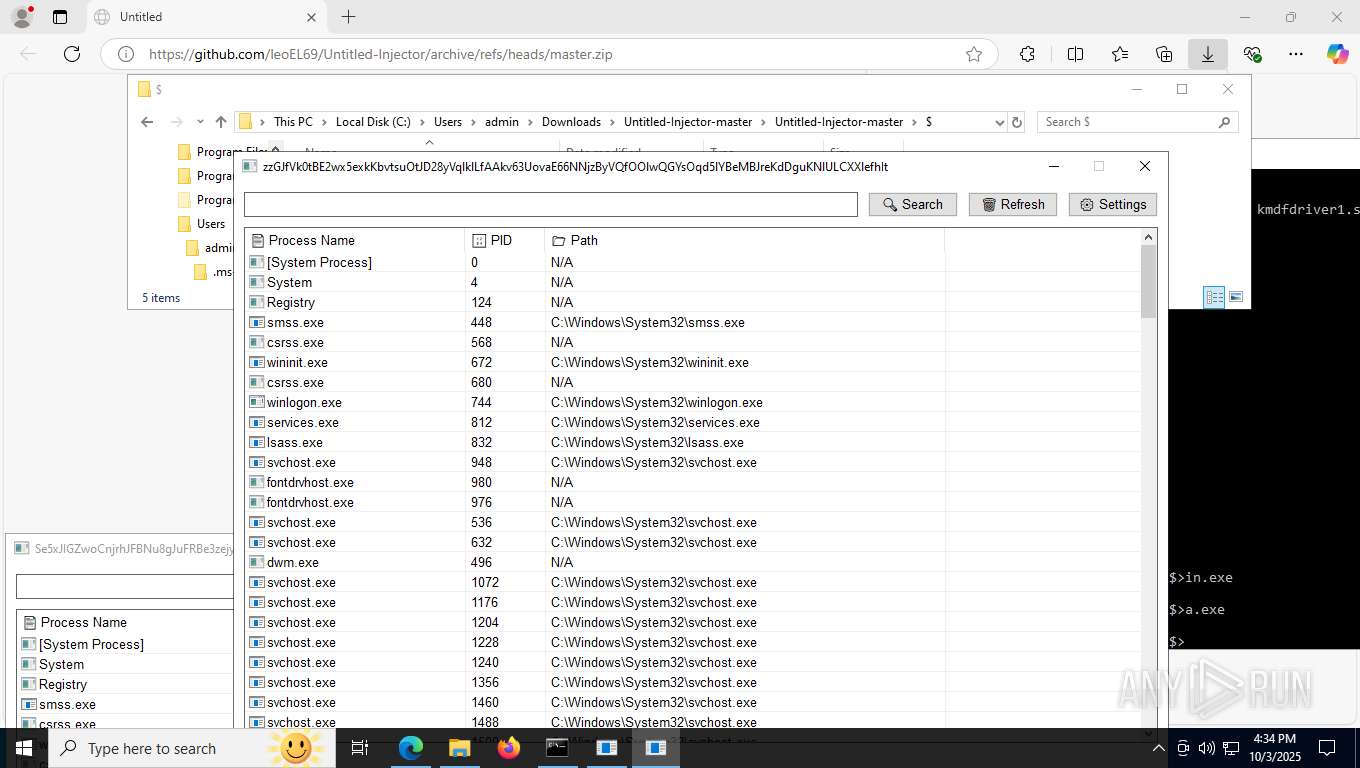
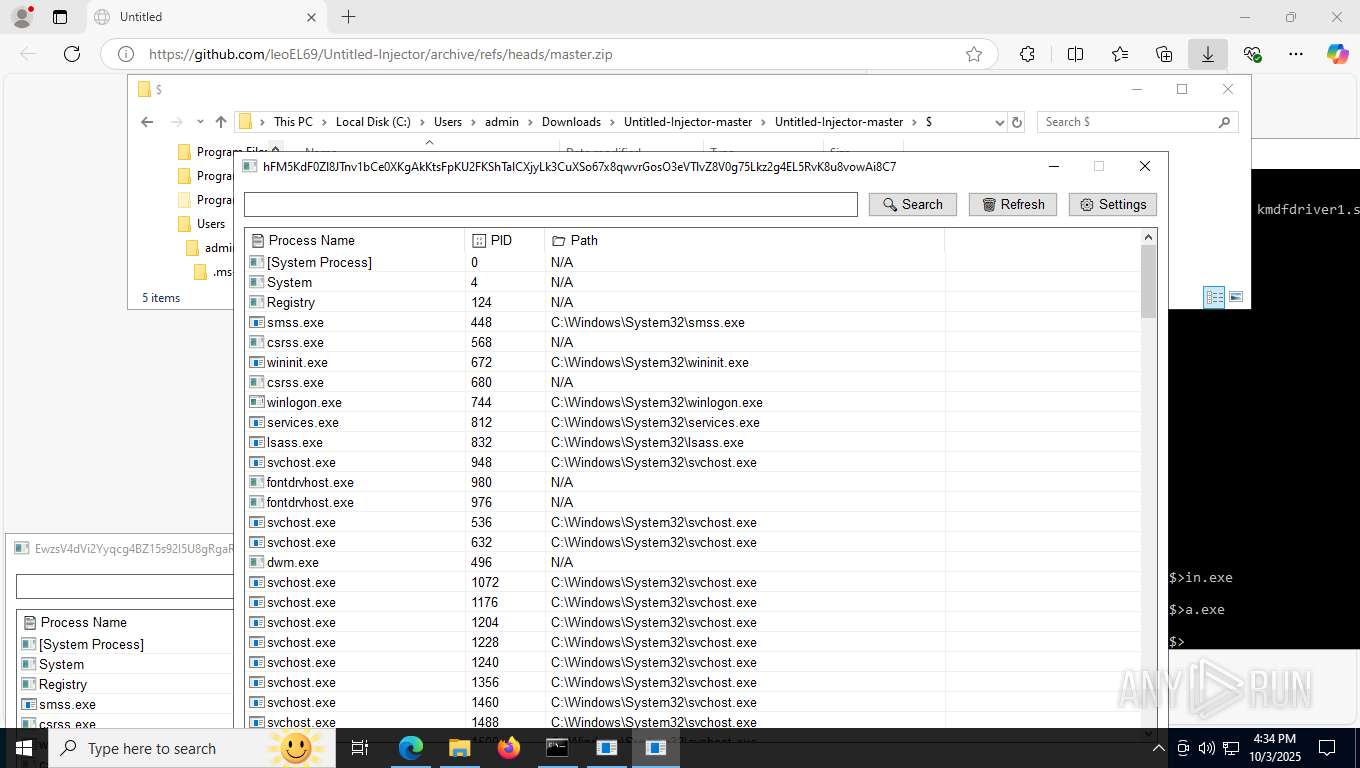
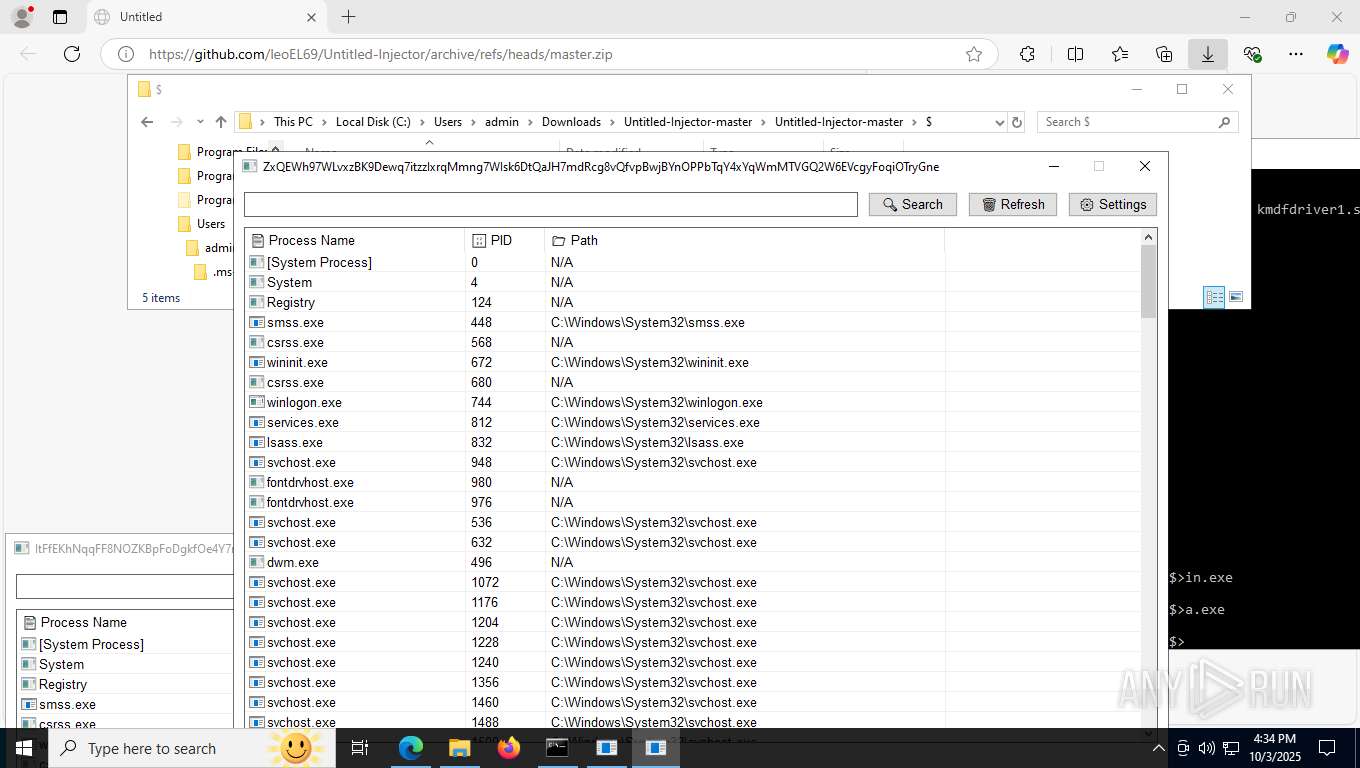
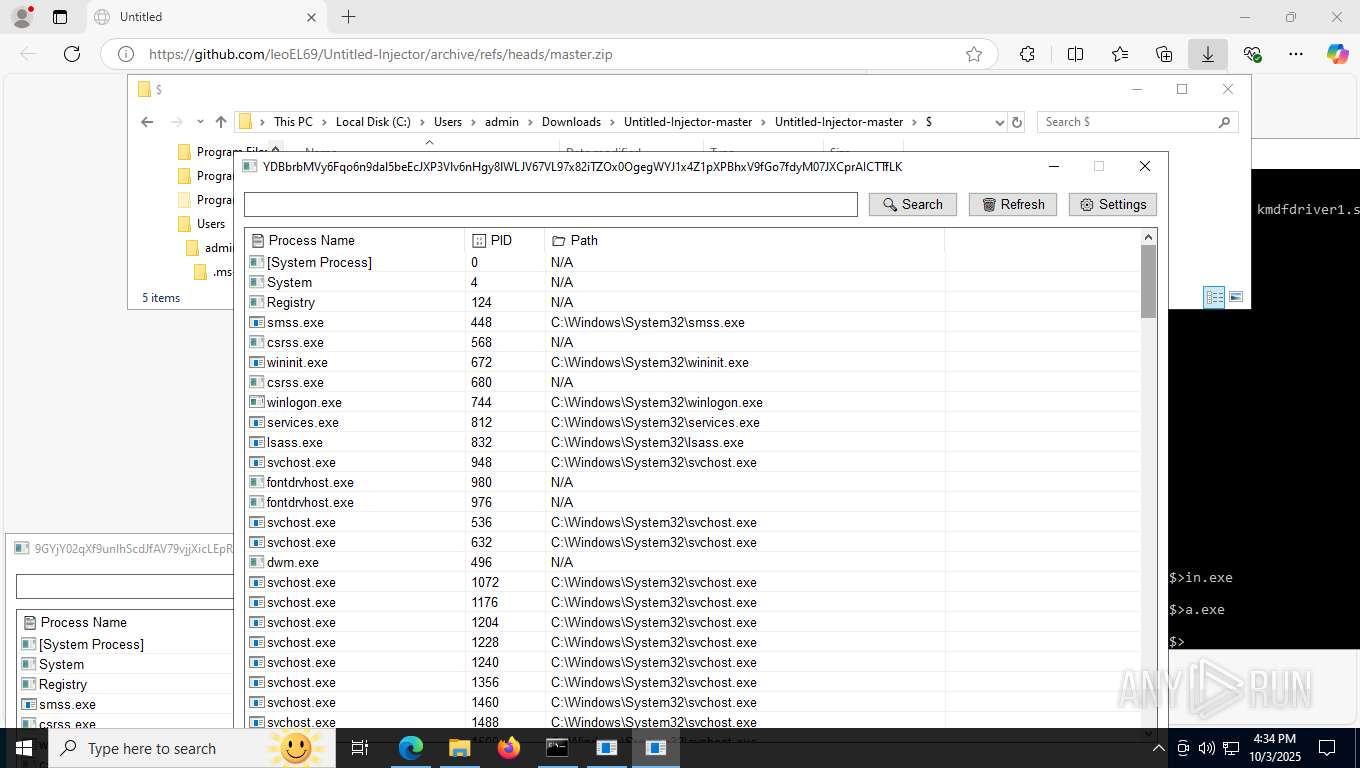
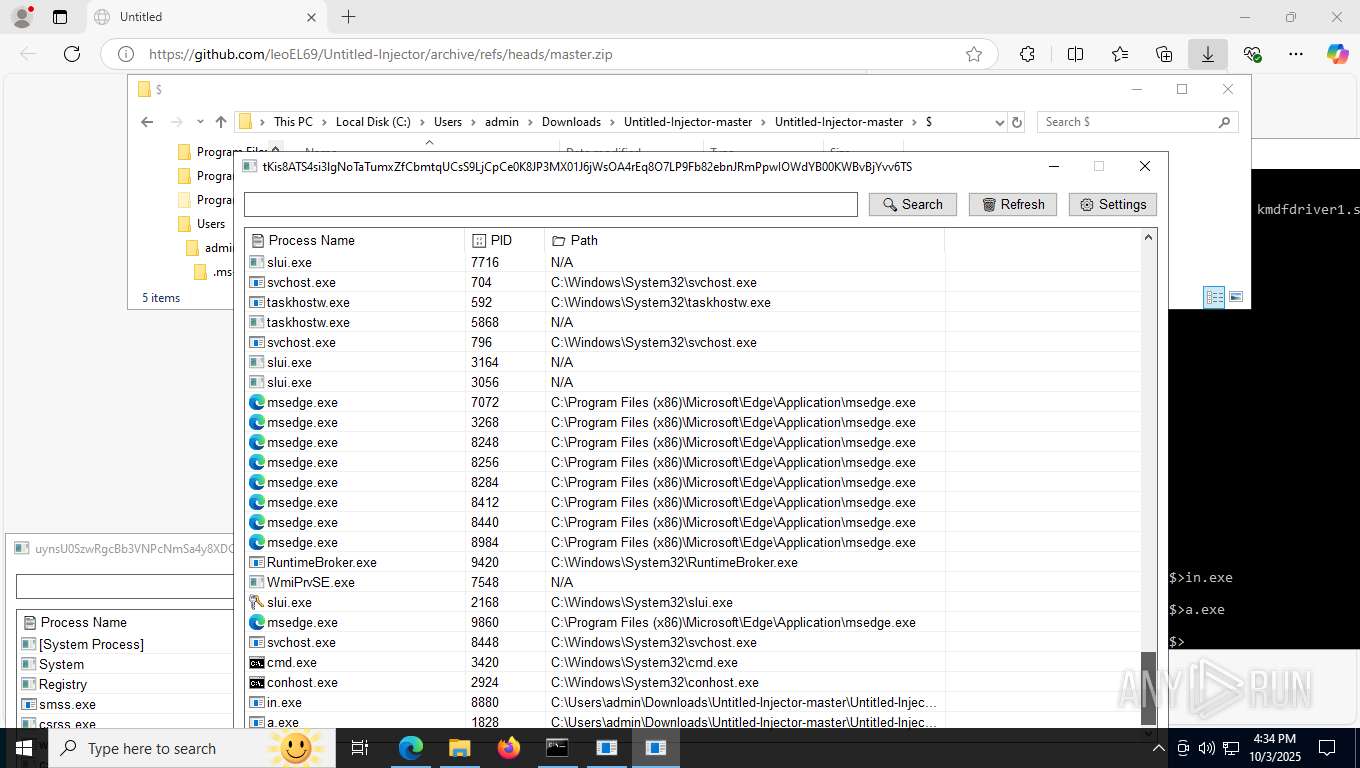
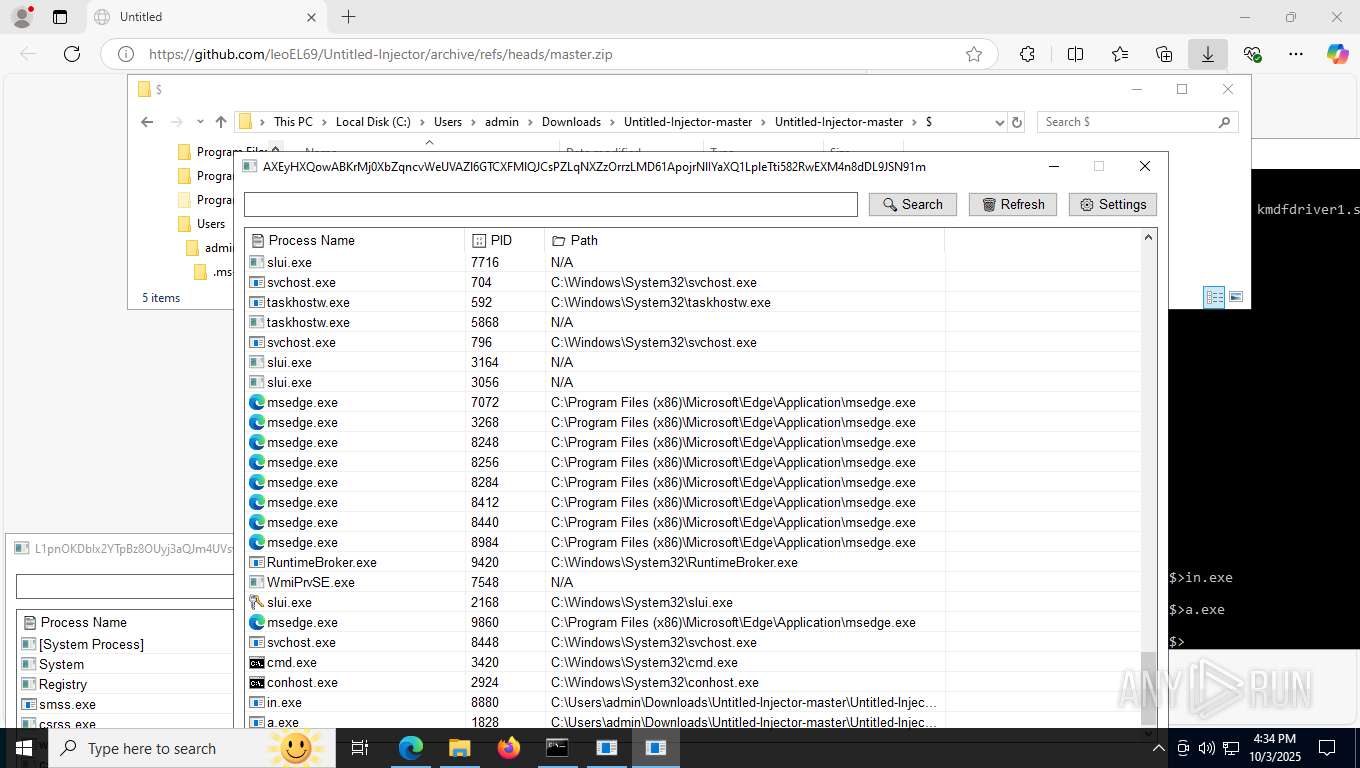
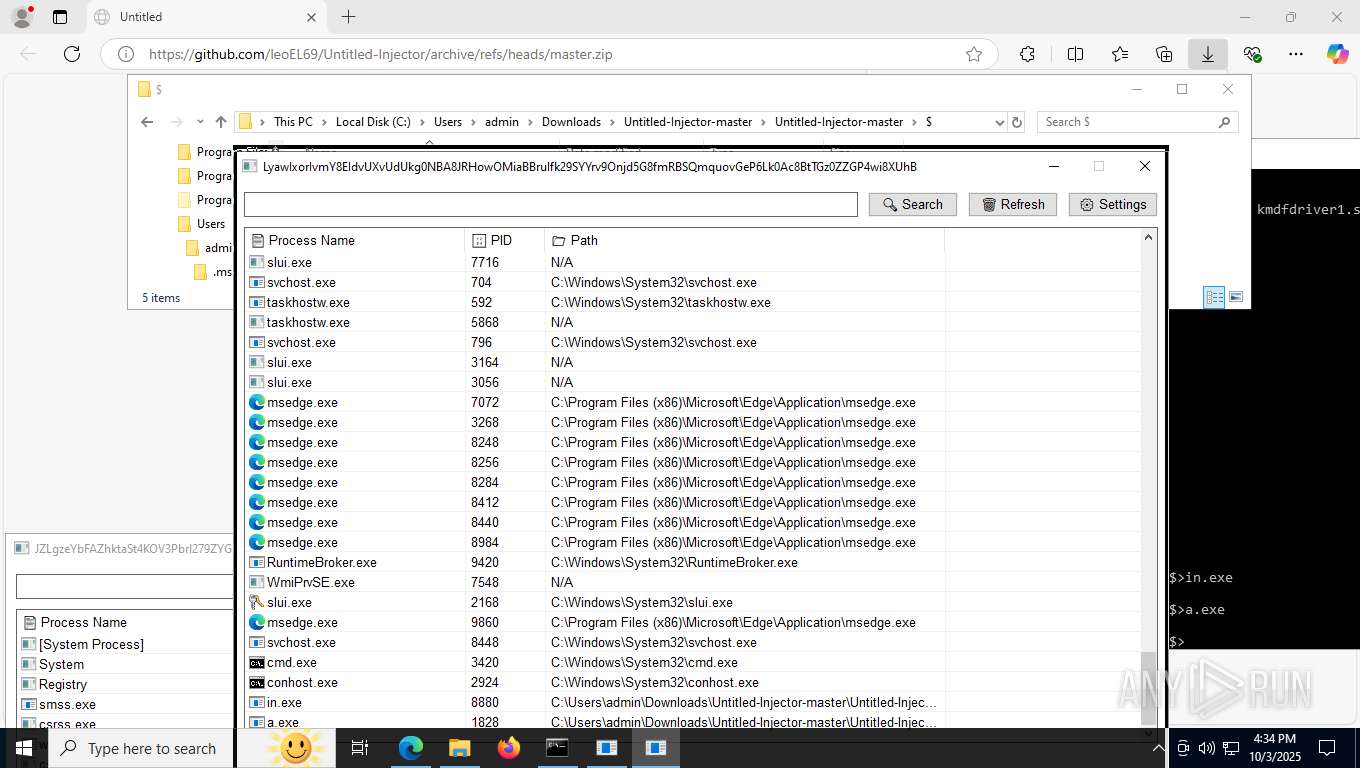
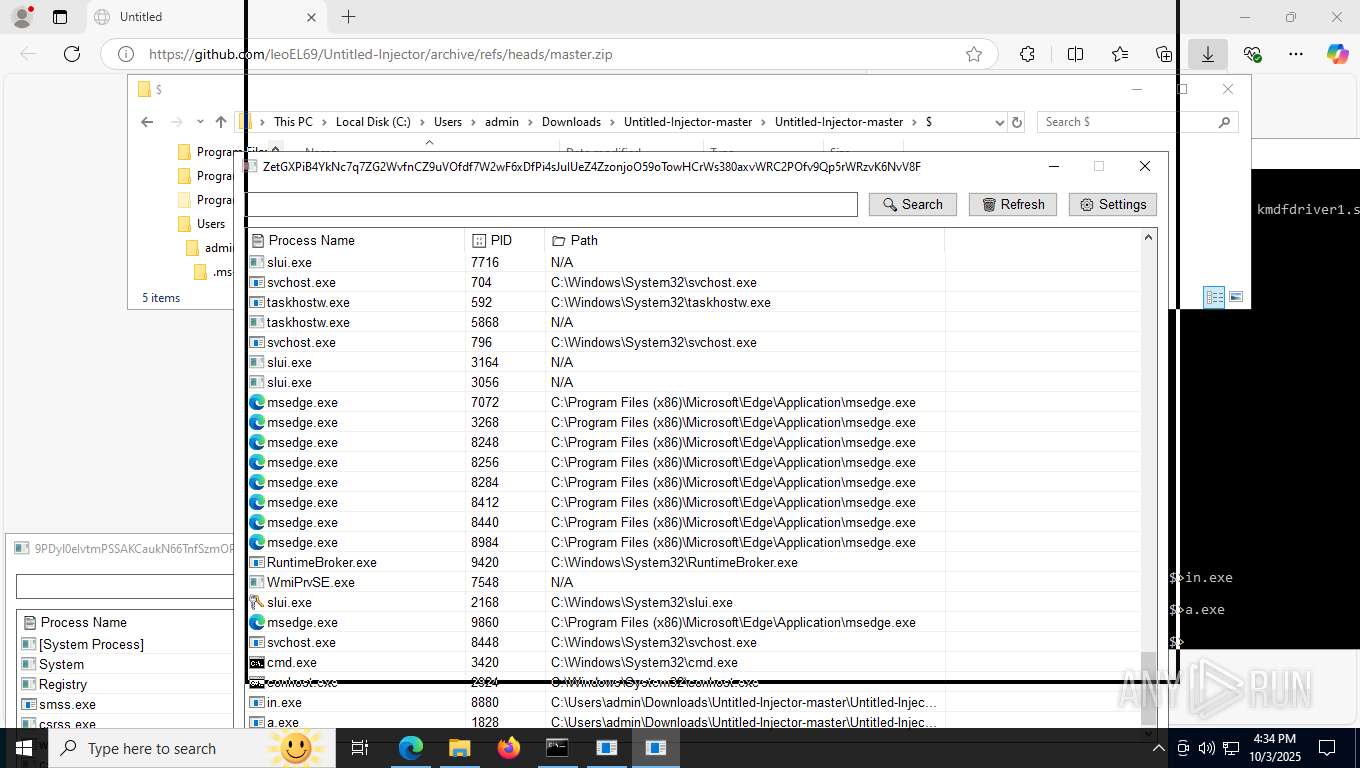
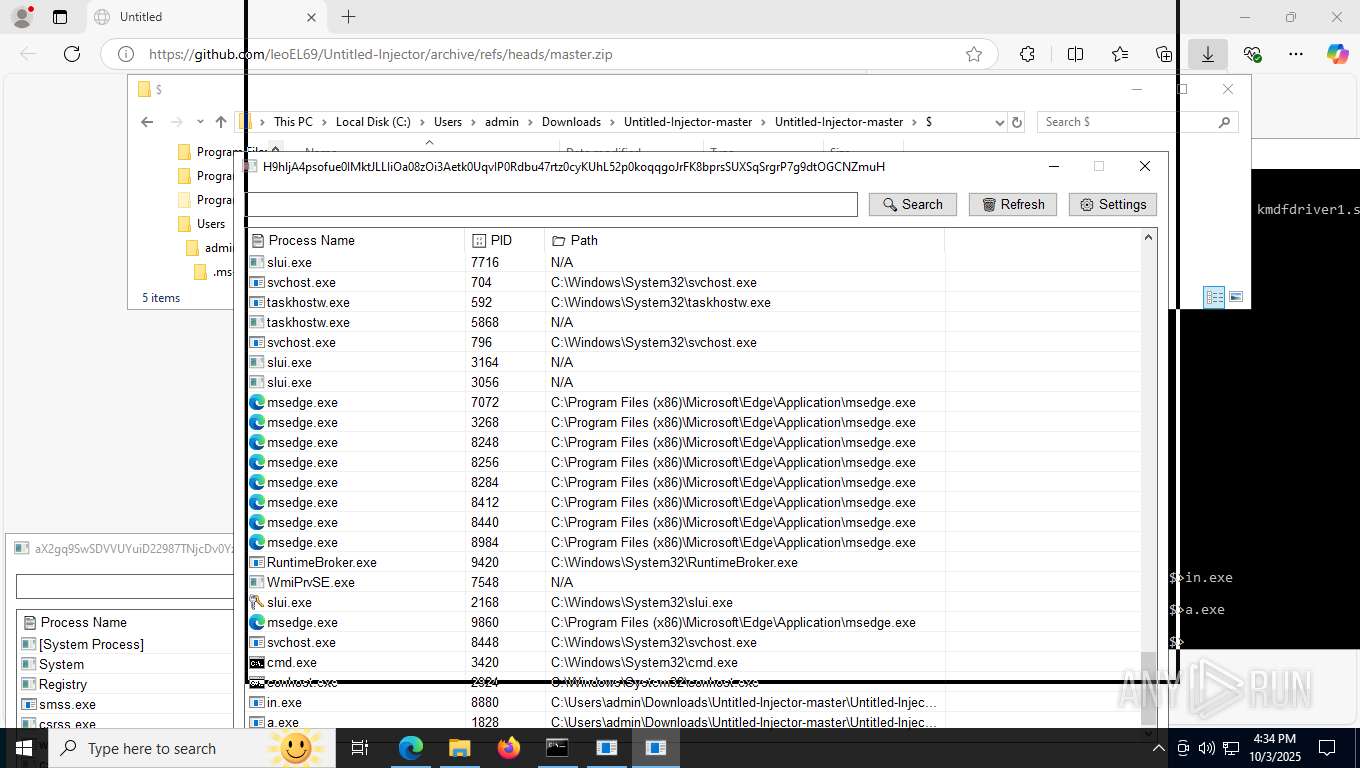
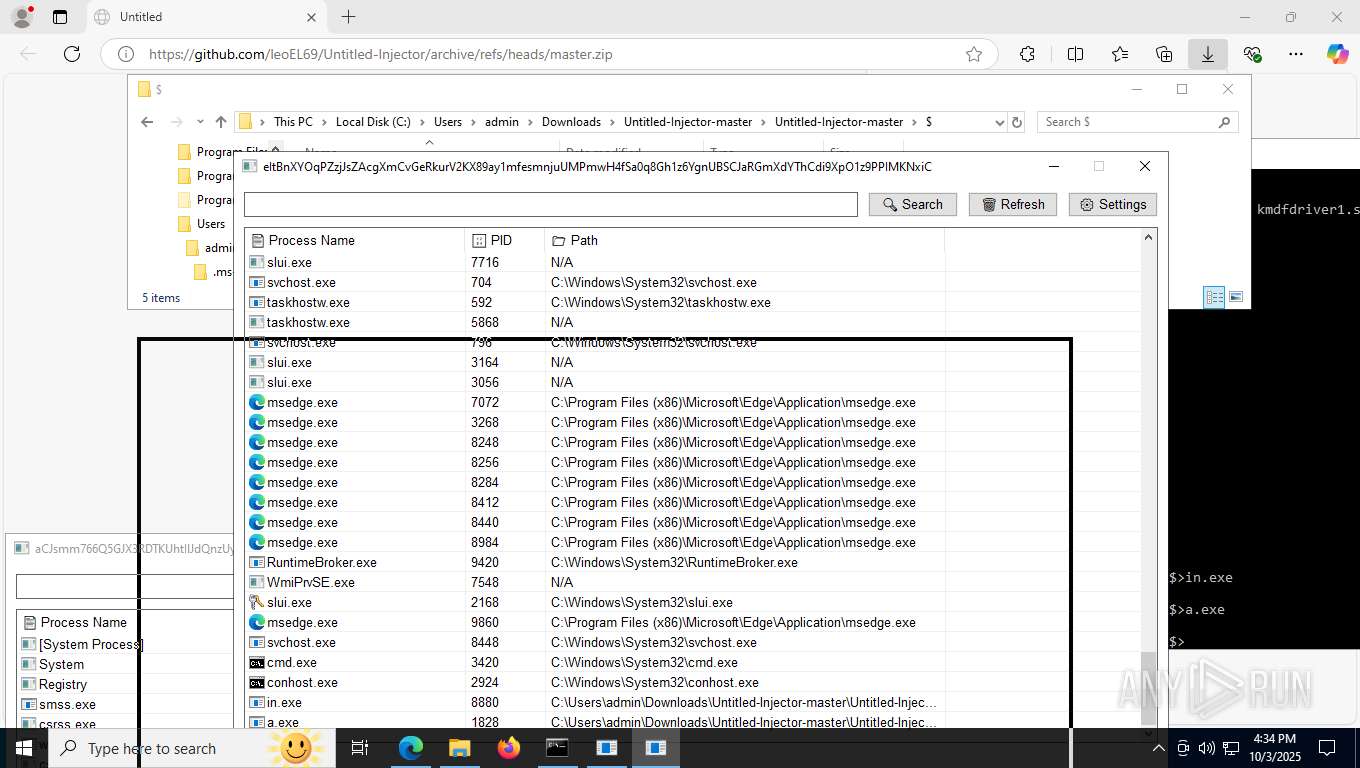
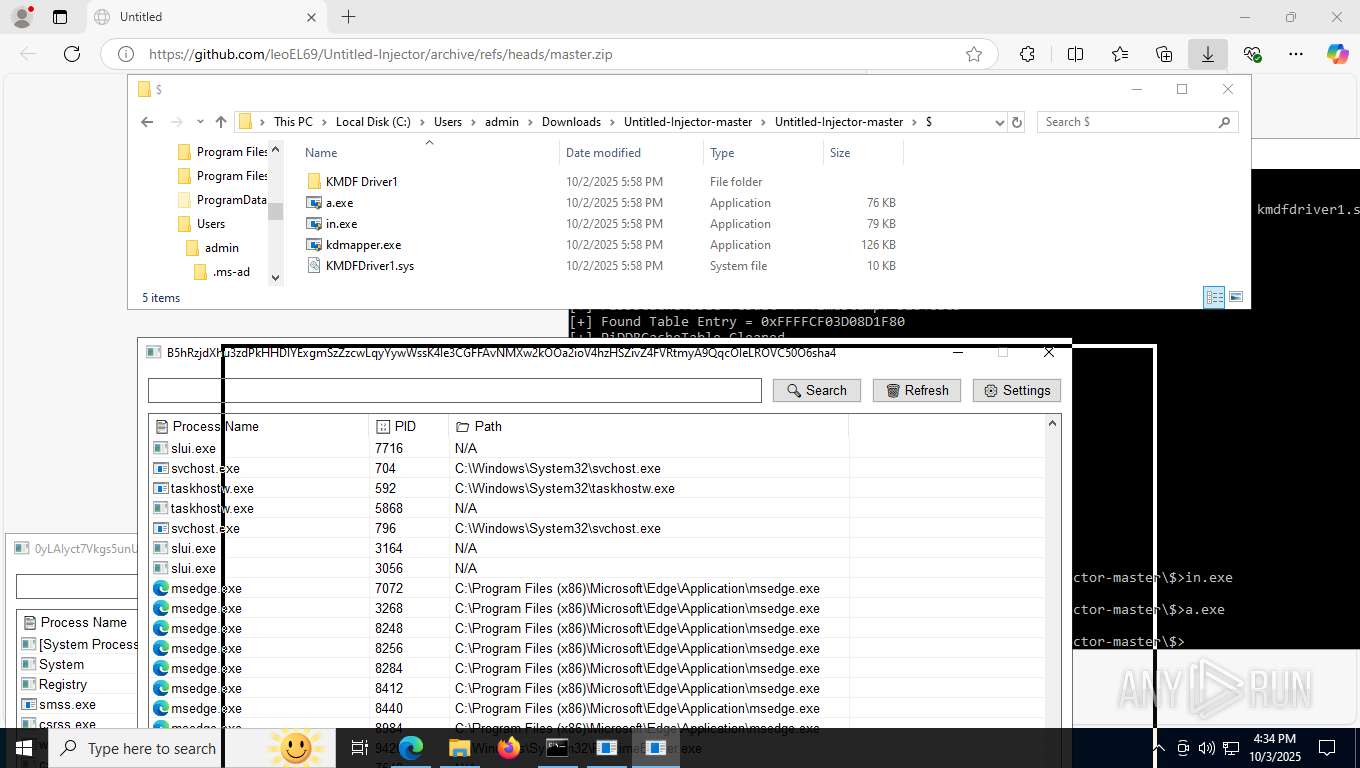
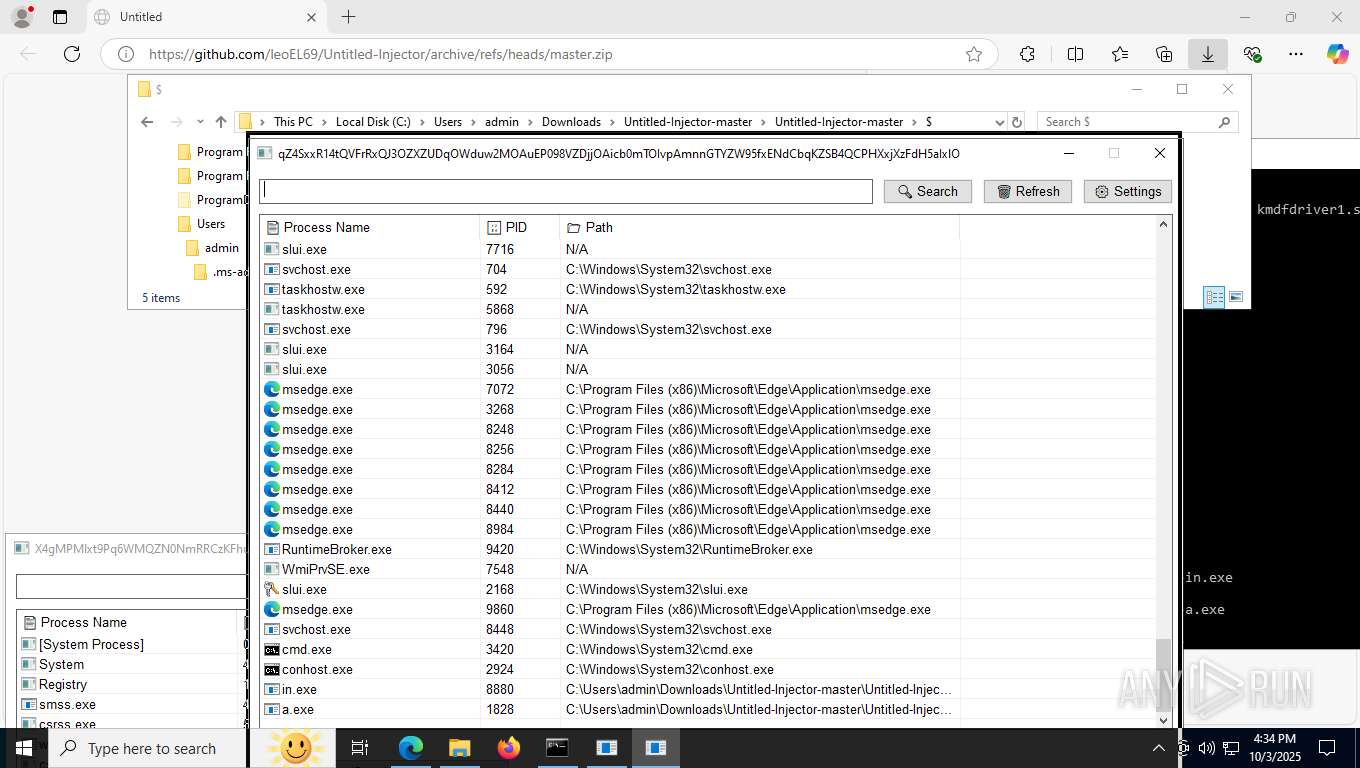
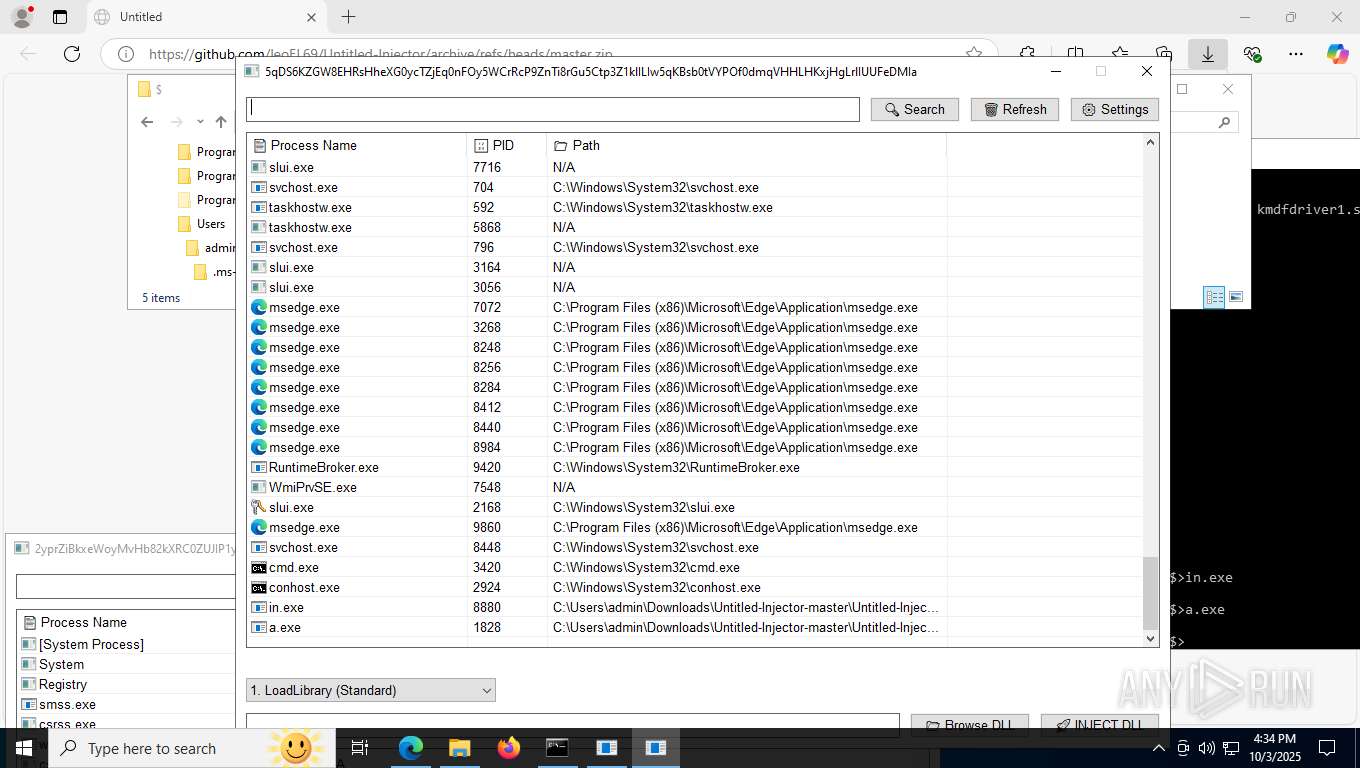
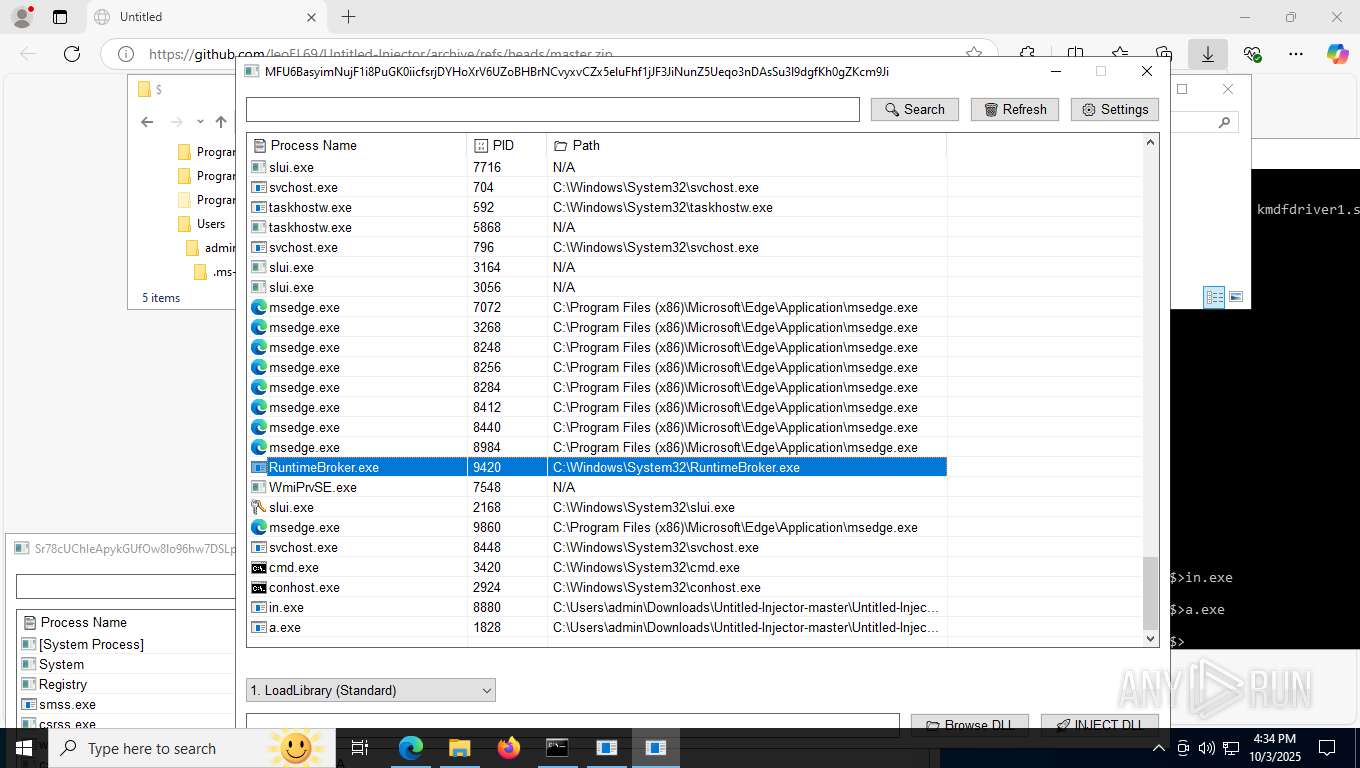
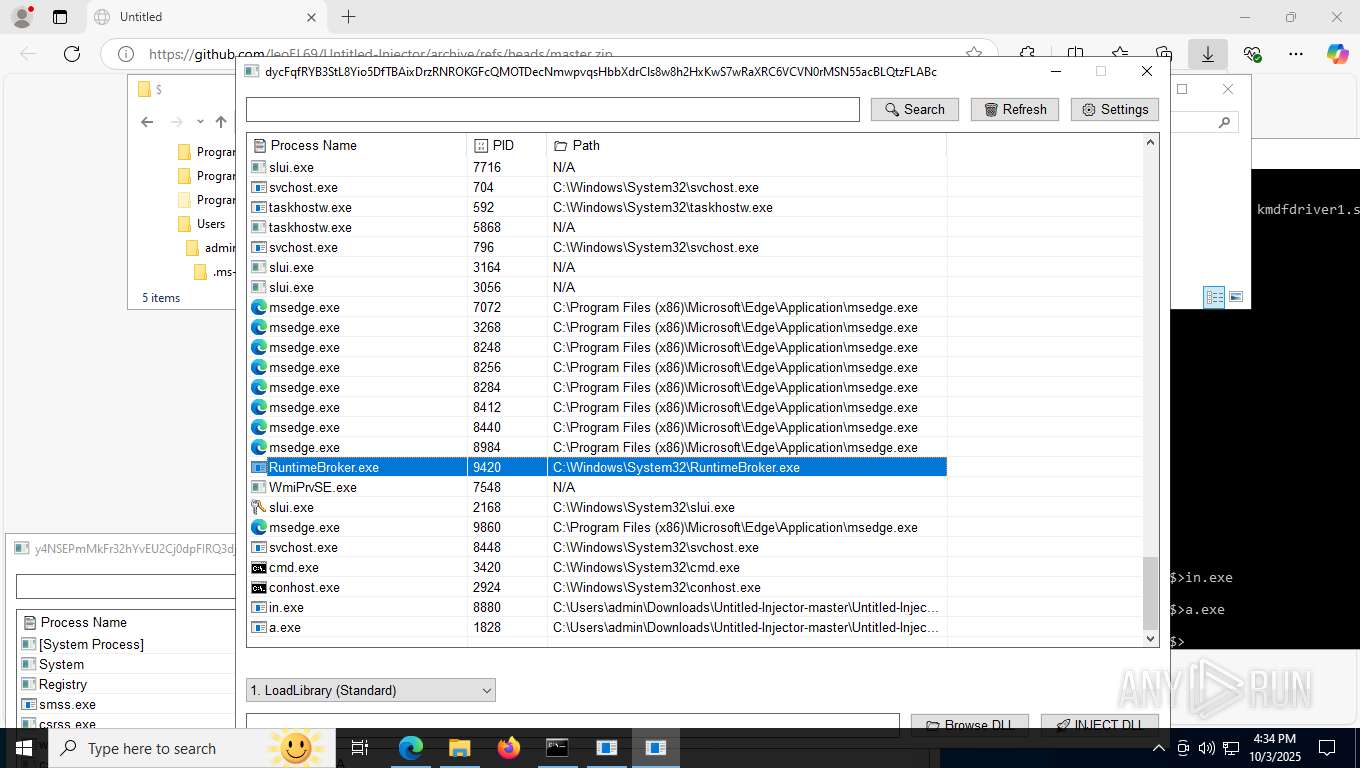
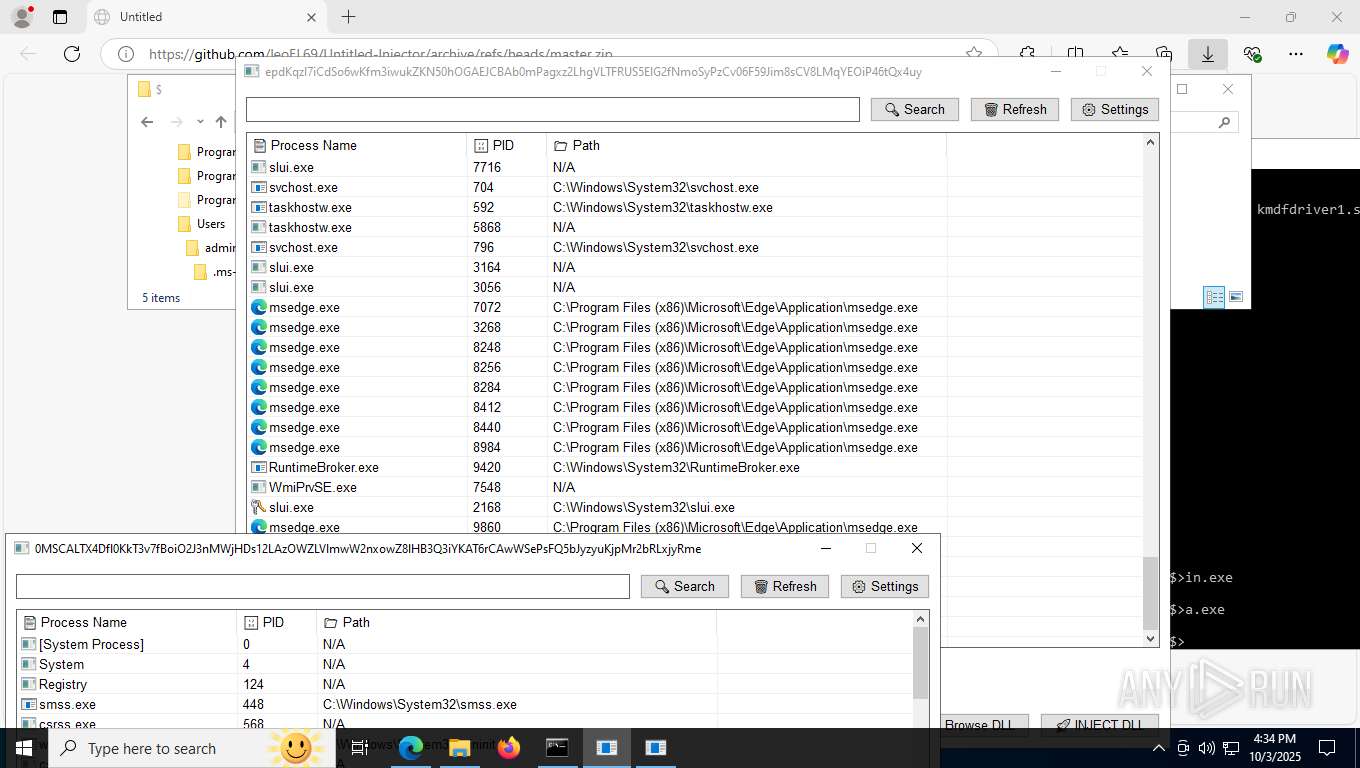
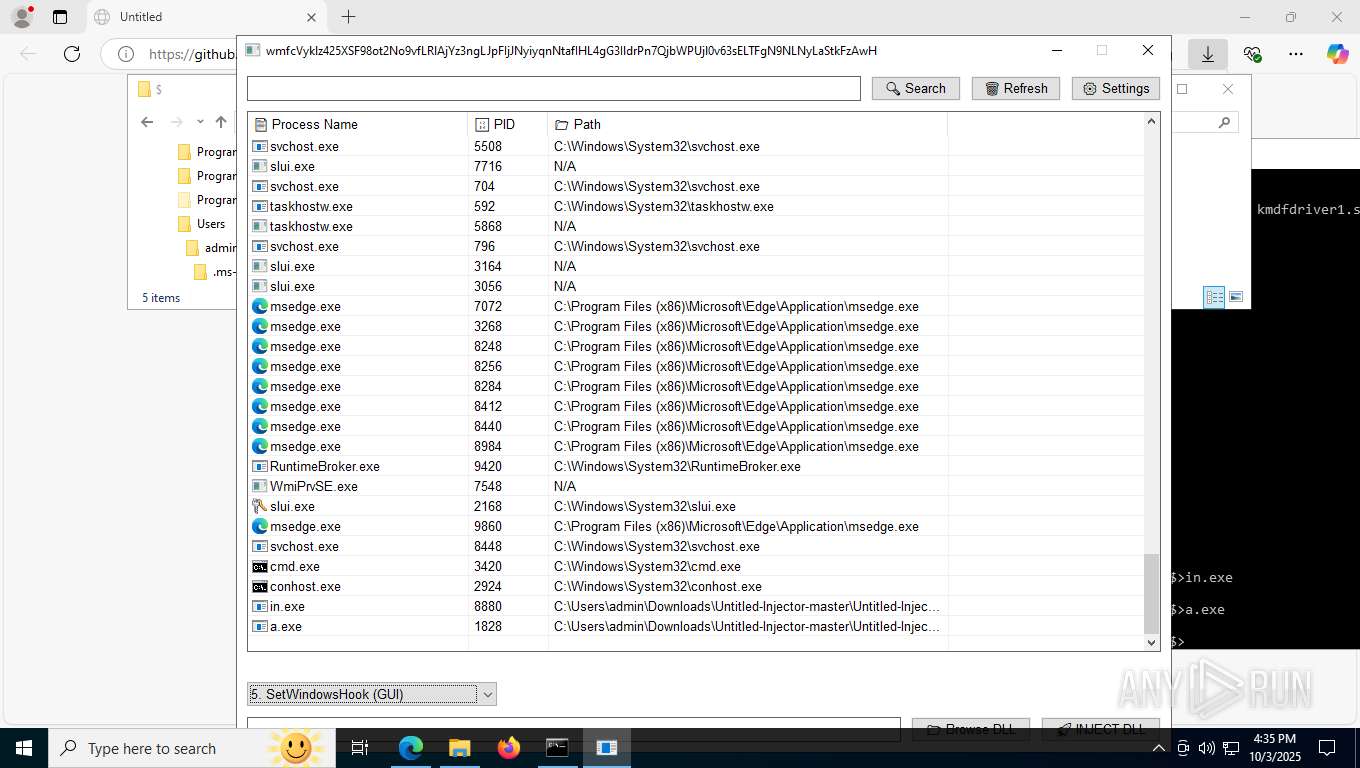
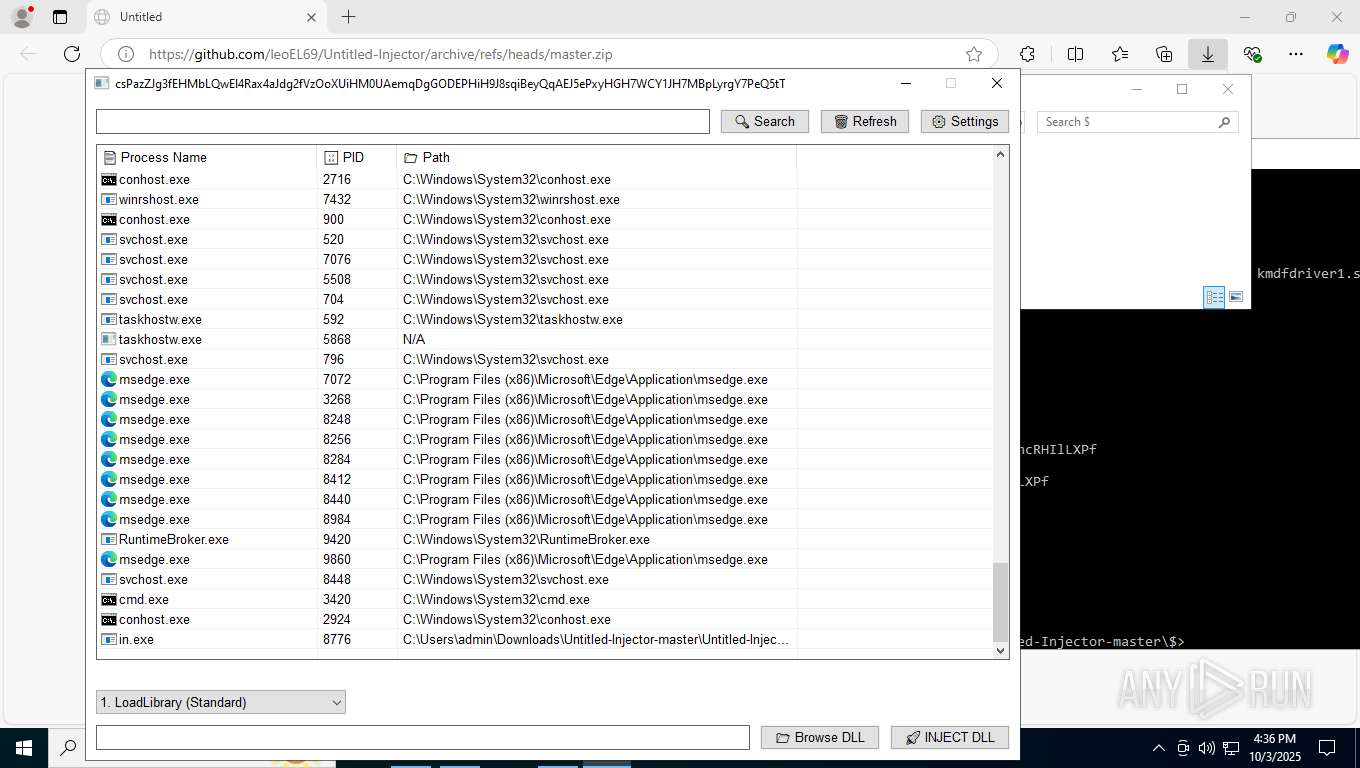
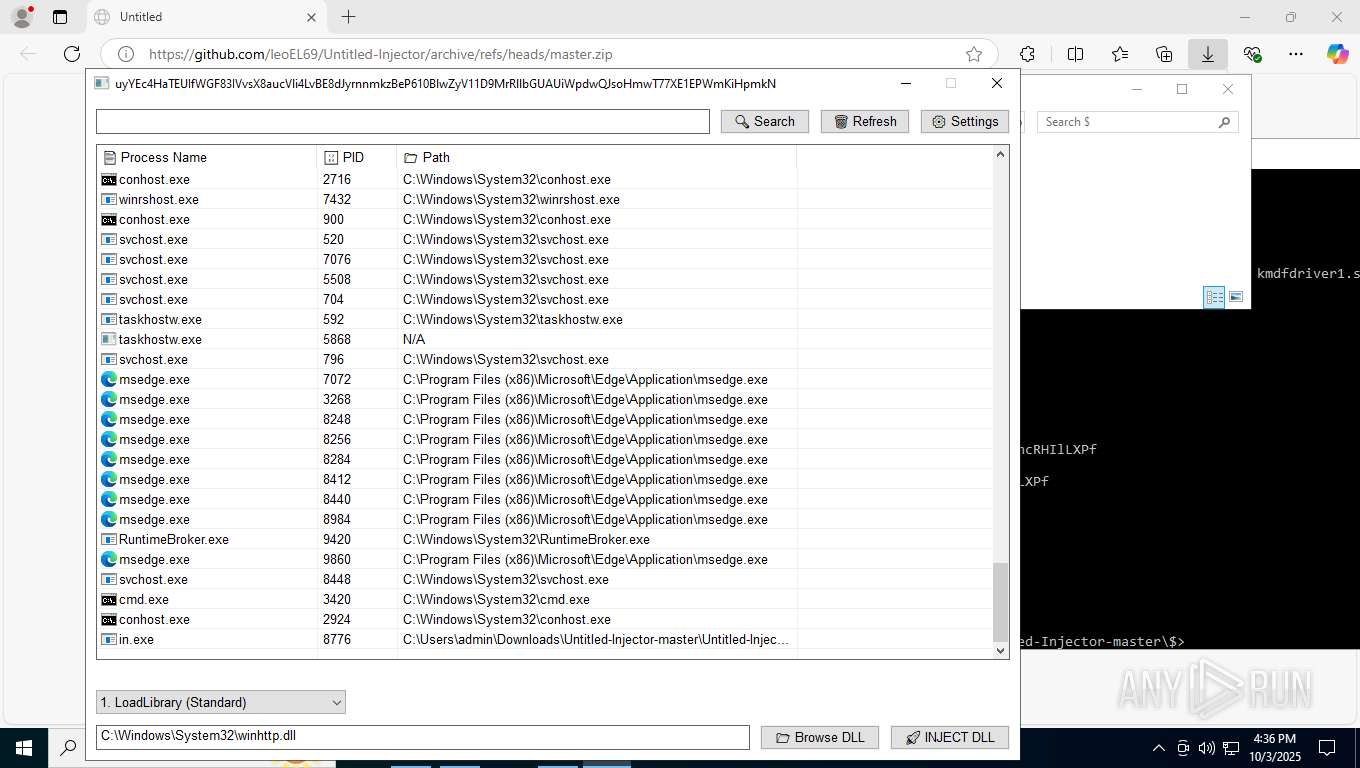
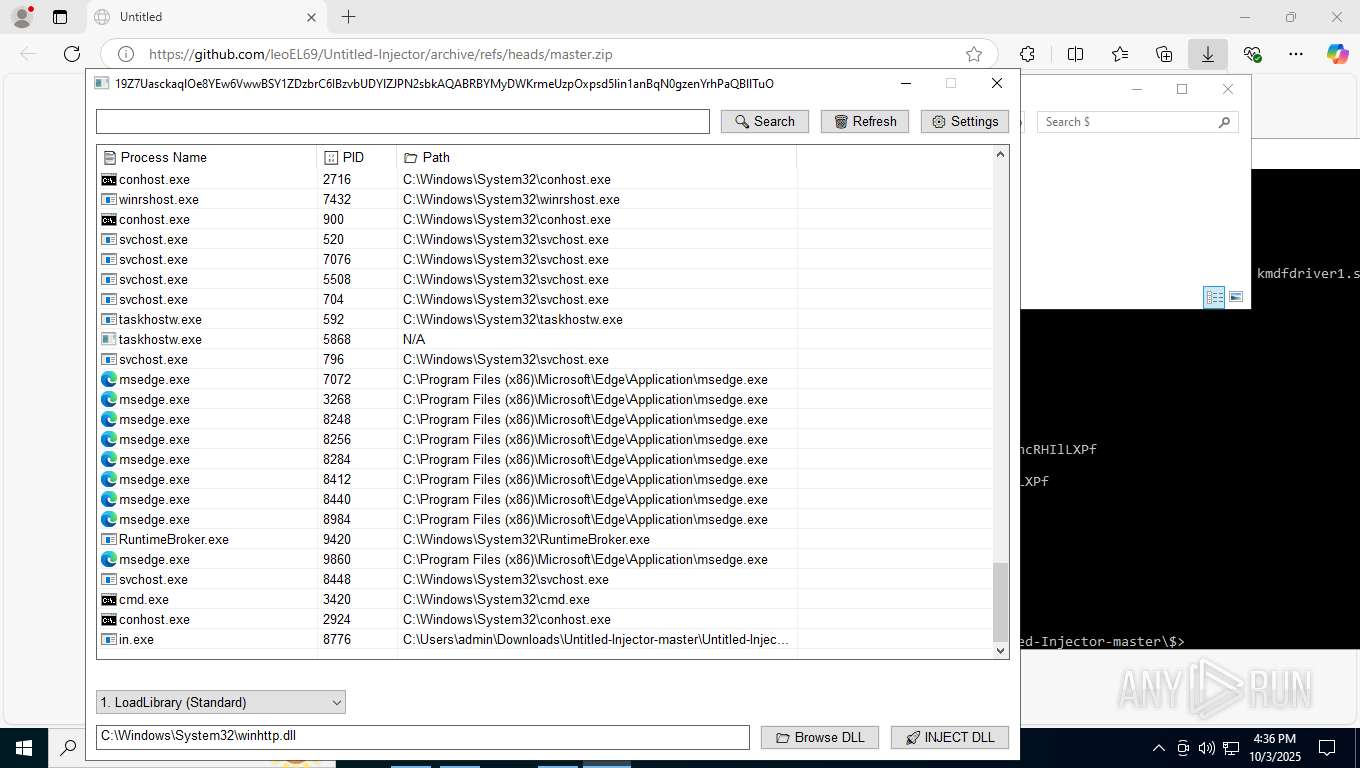
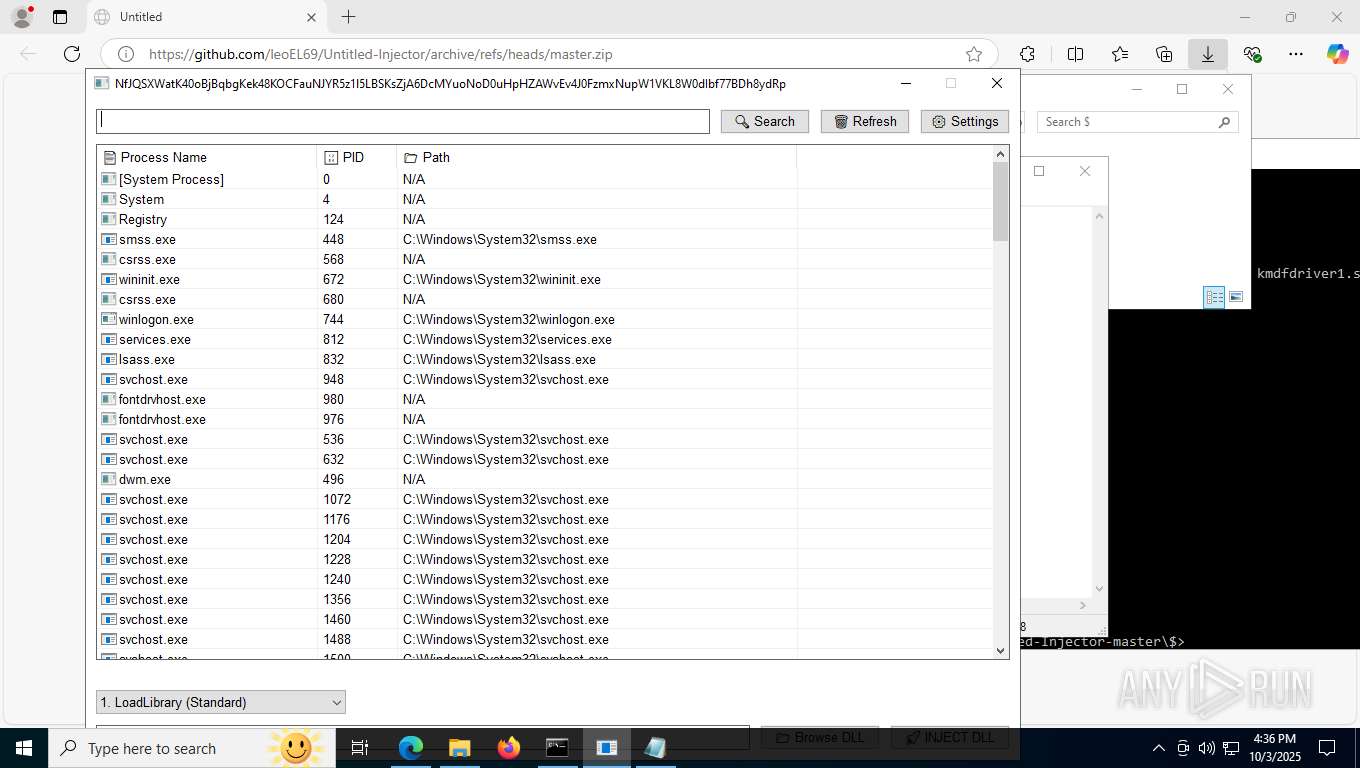
Total processes
242
Monitored processes
58
Malicious processes
4
Suspicious processes
0
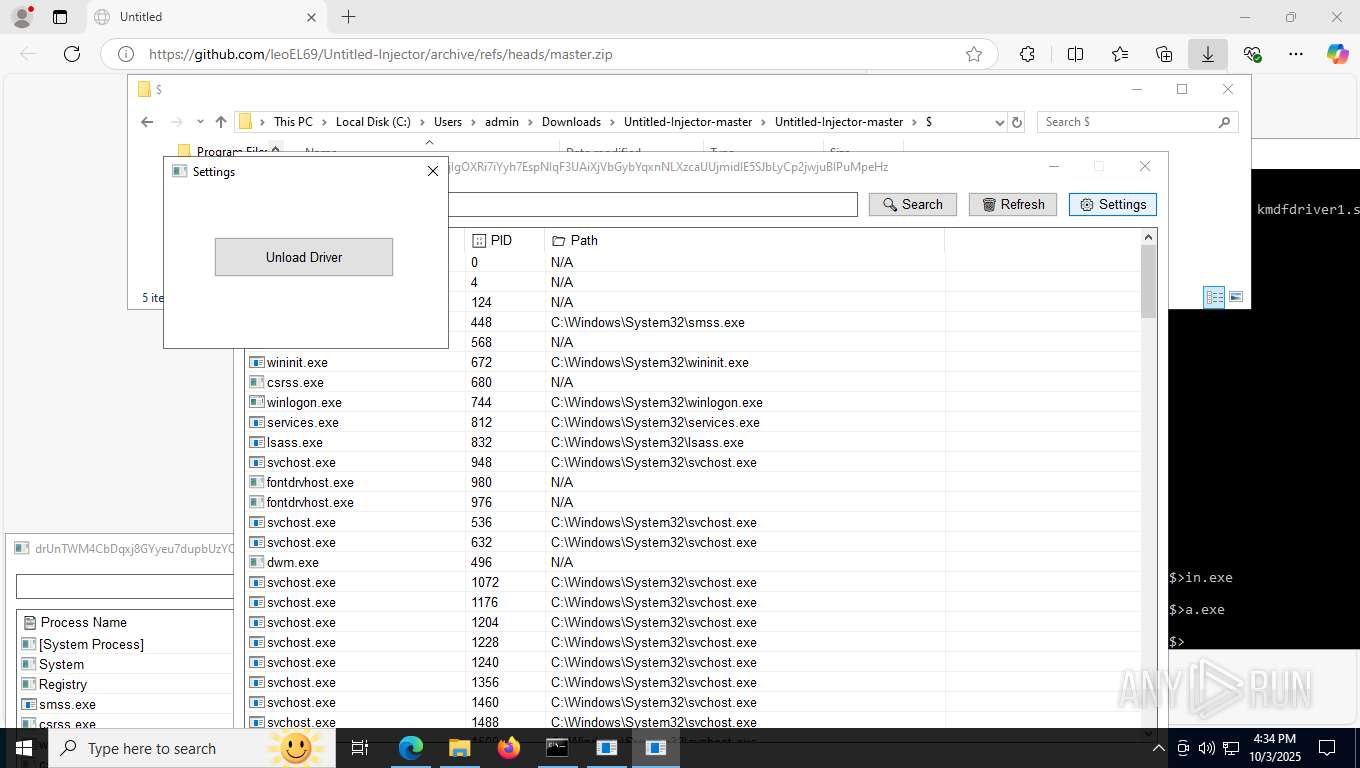
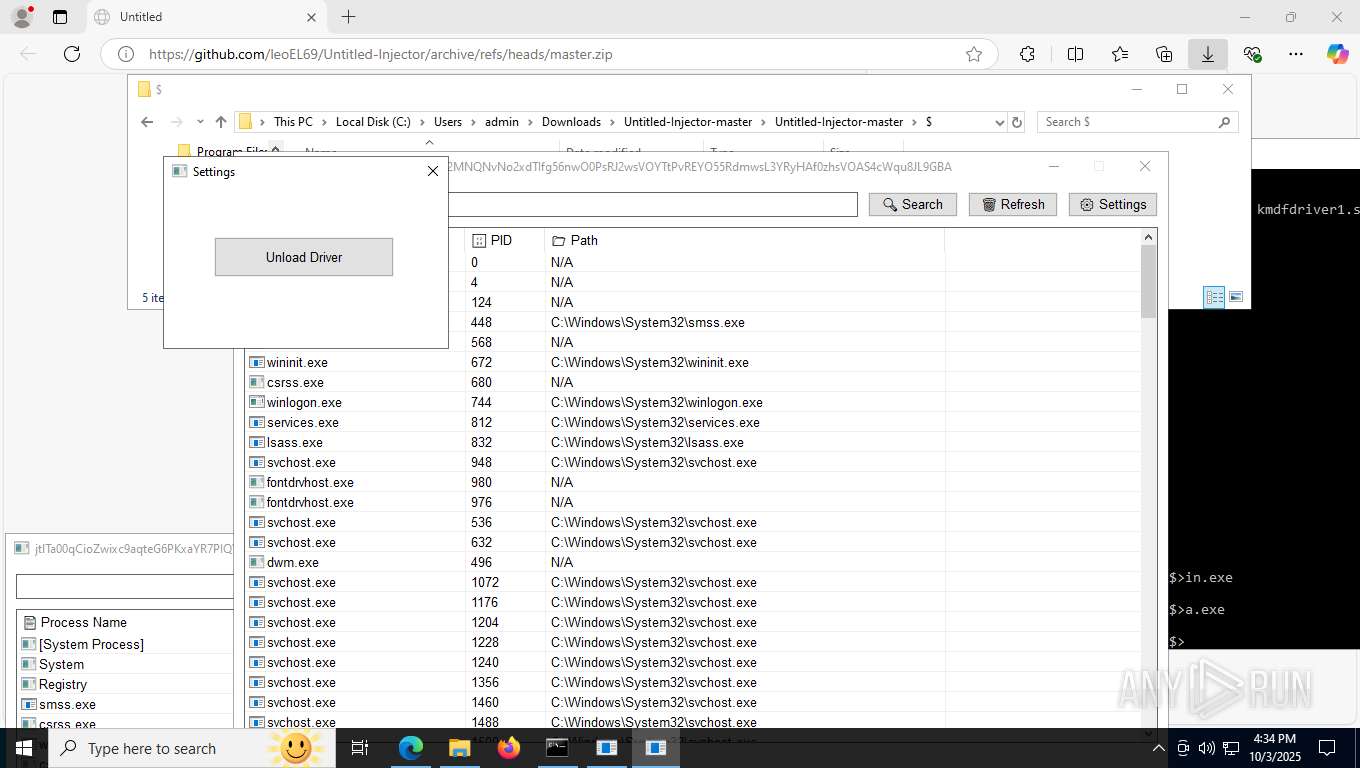
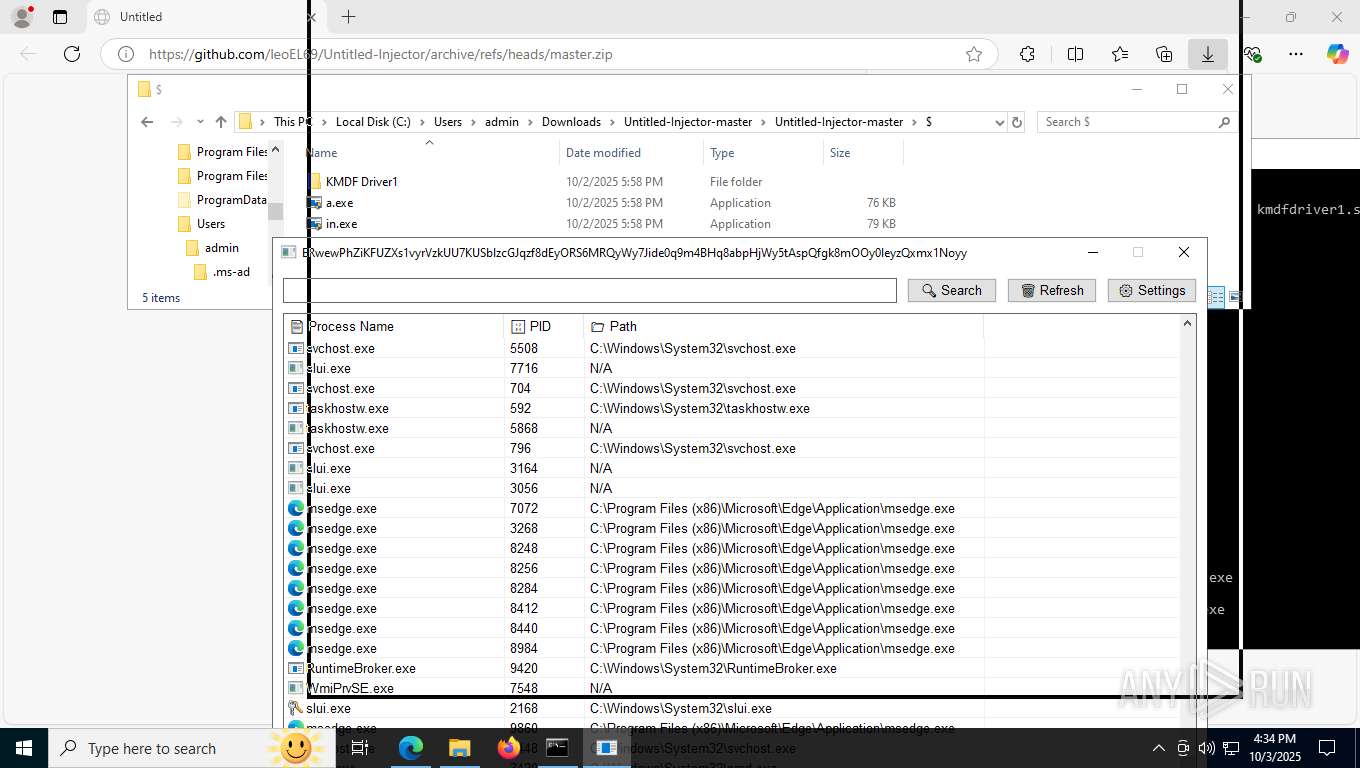
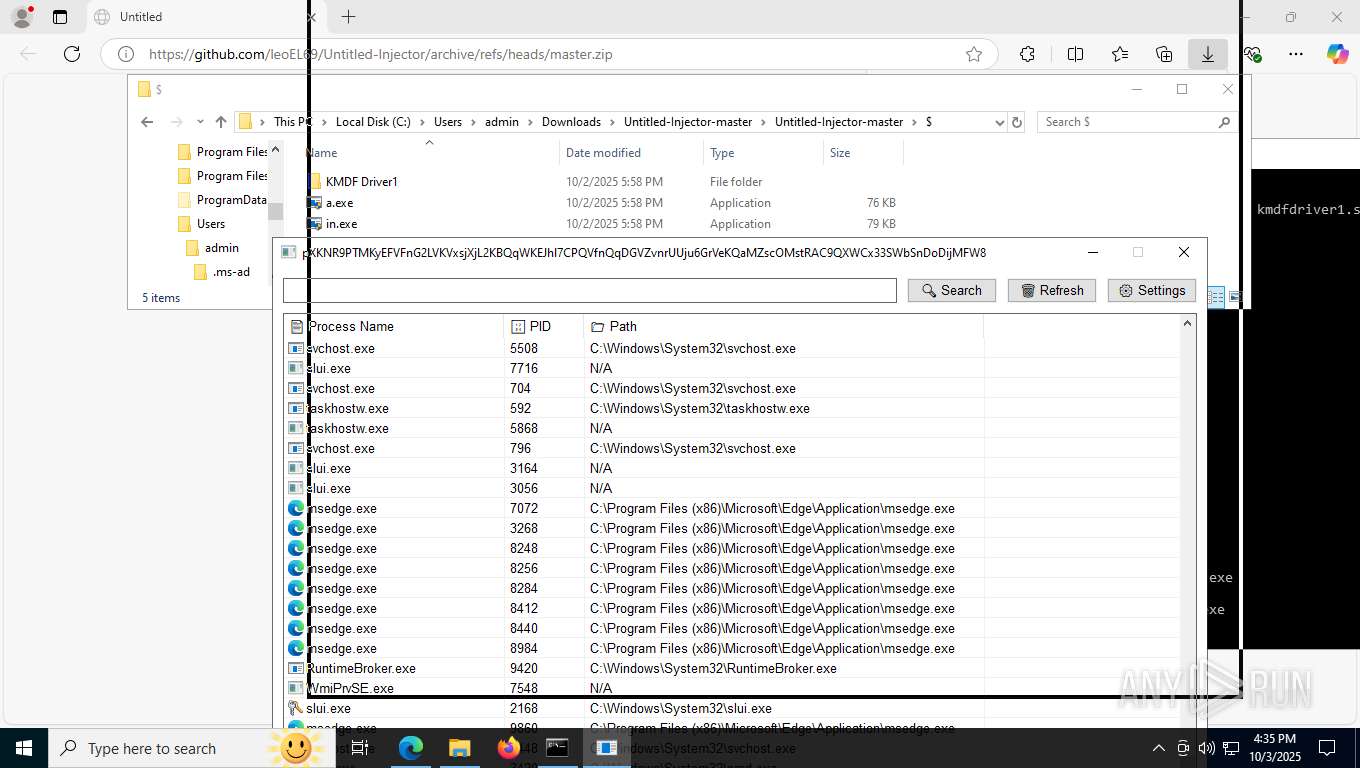
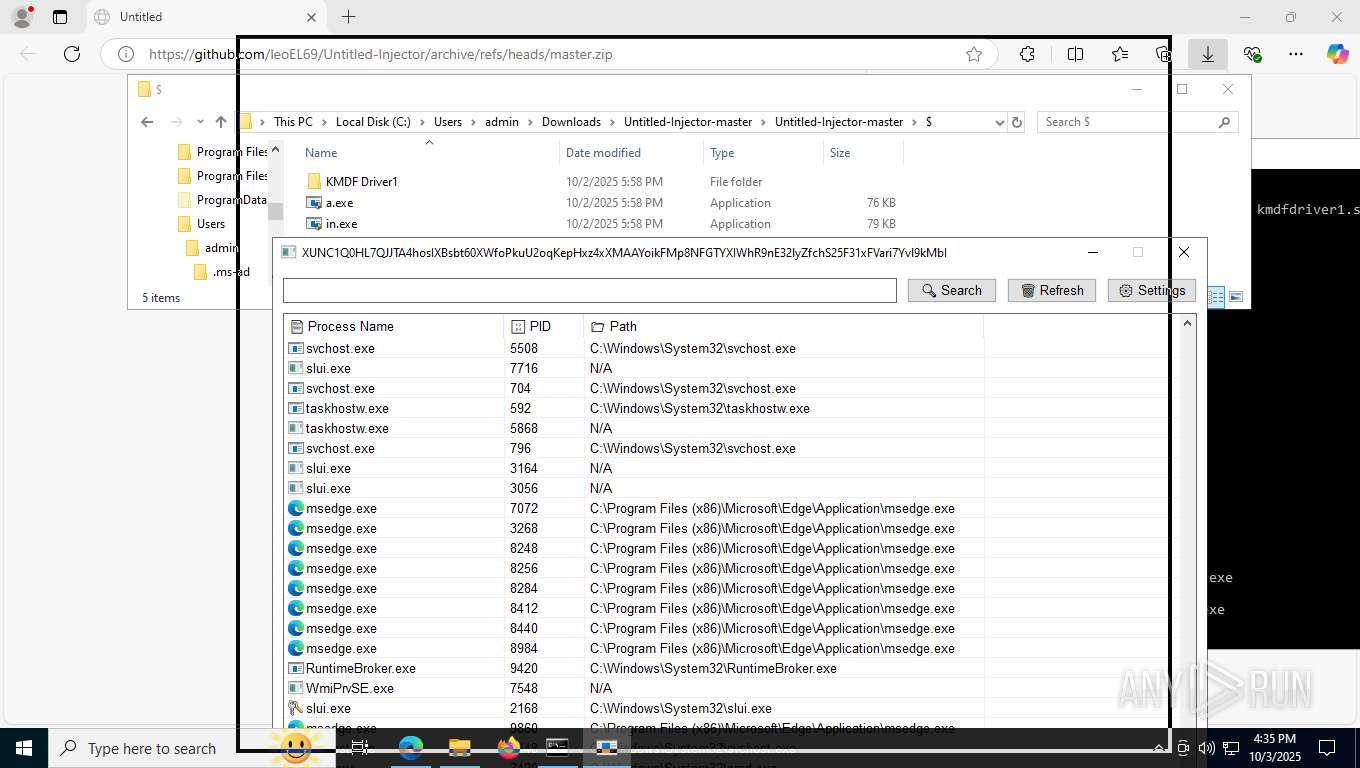
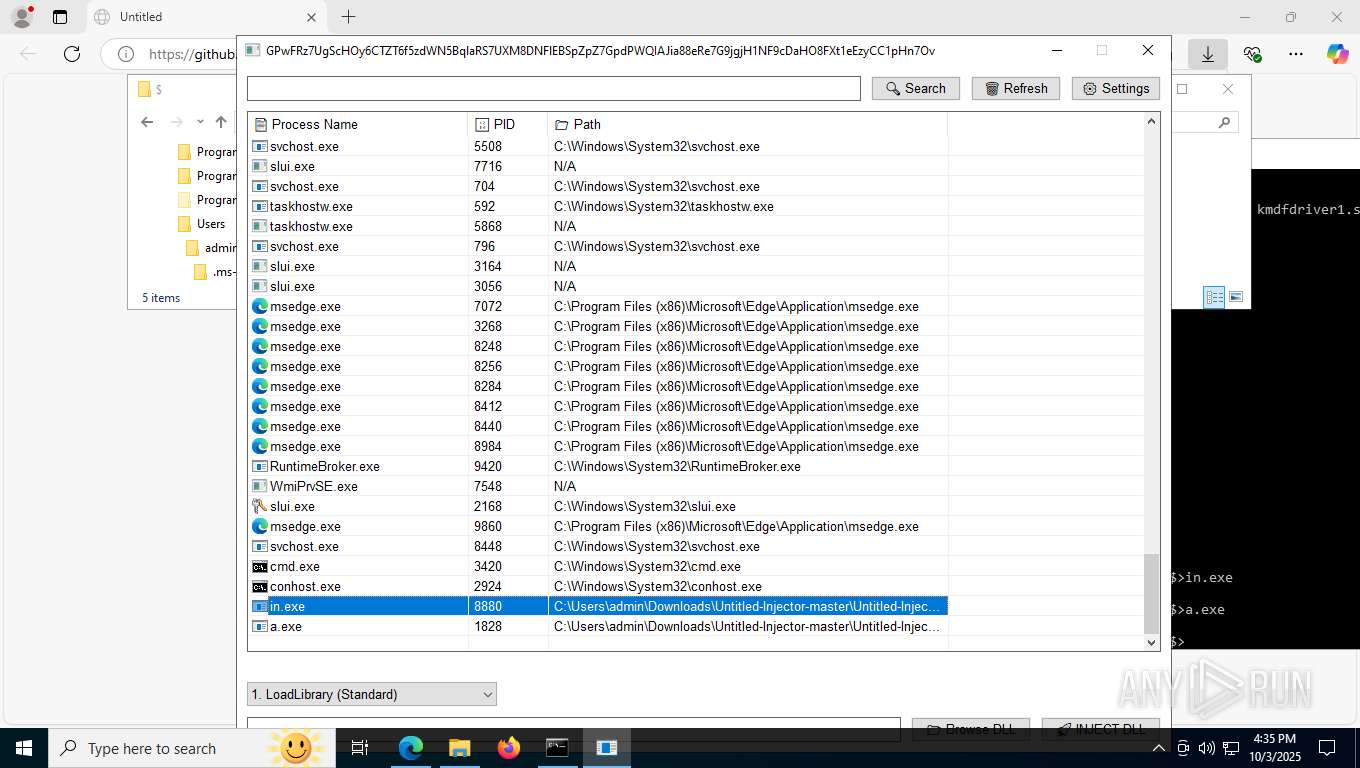
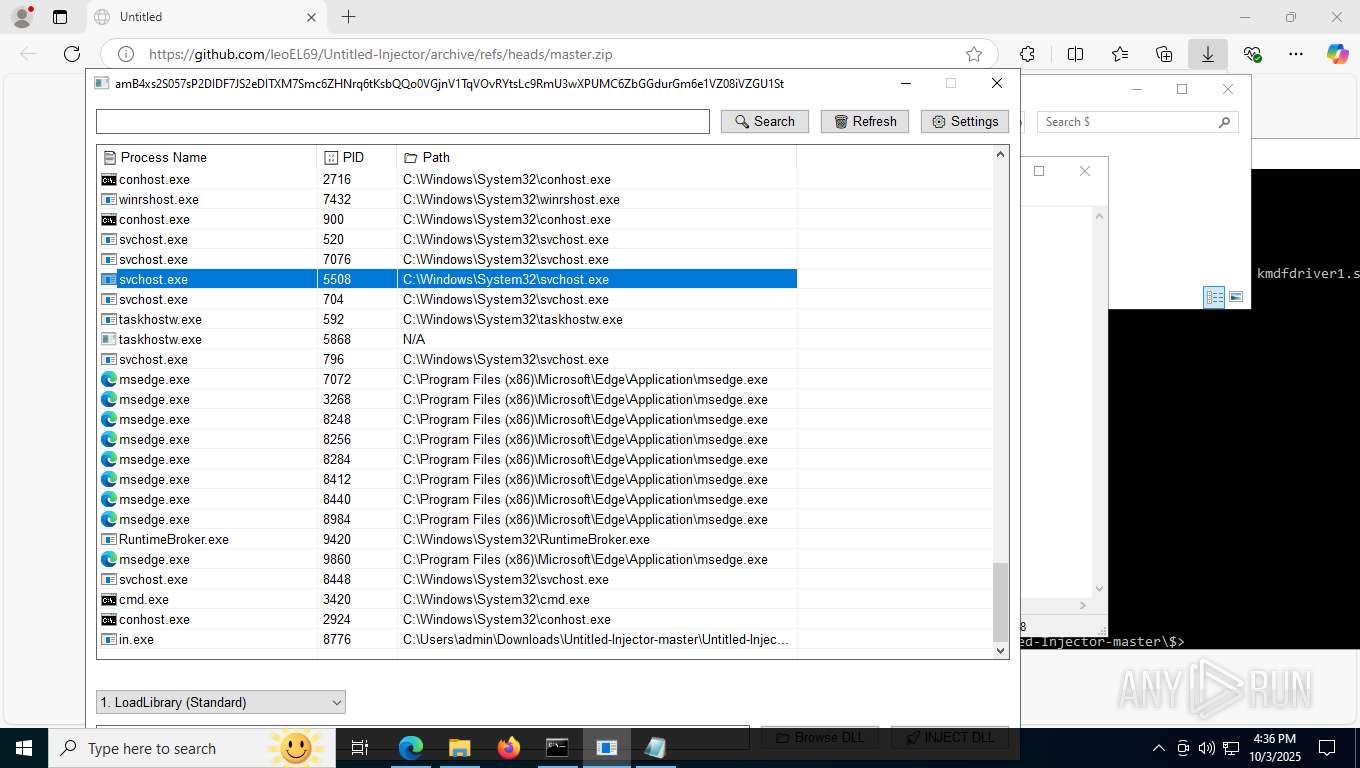
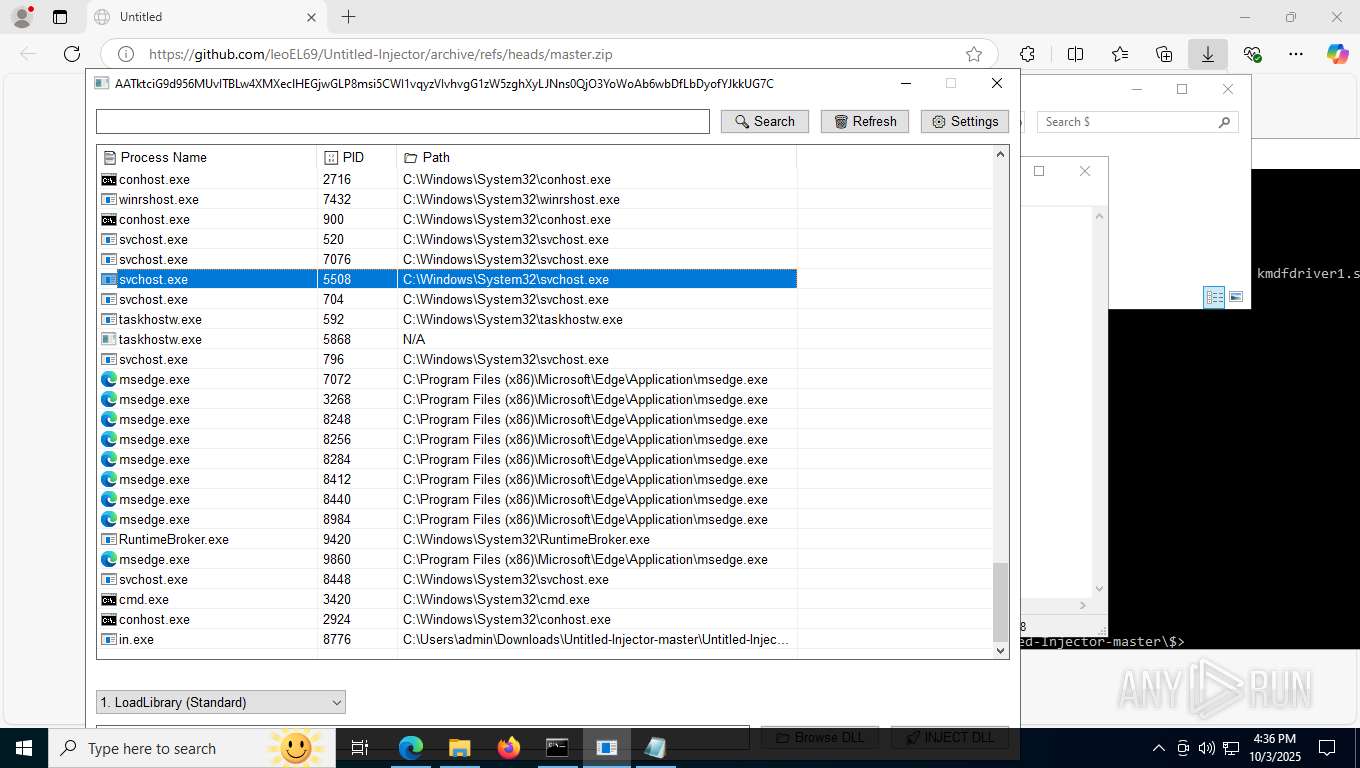
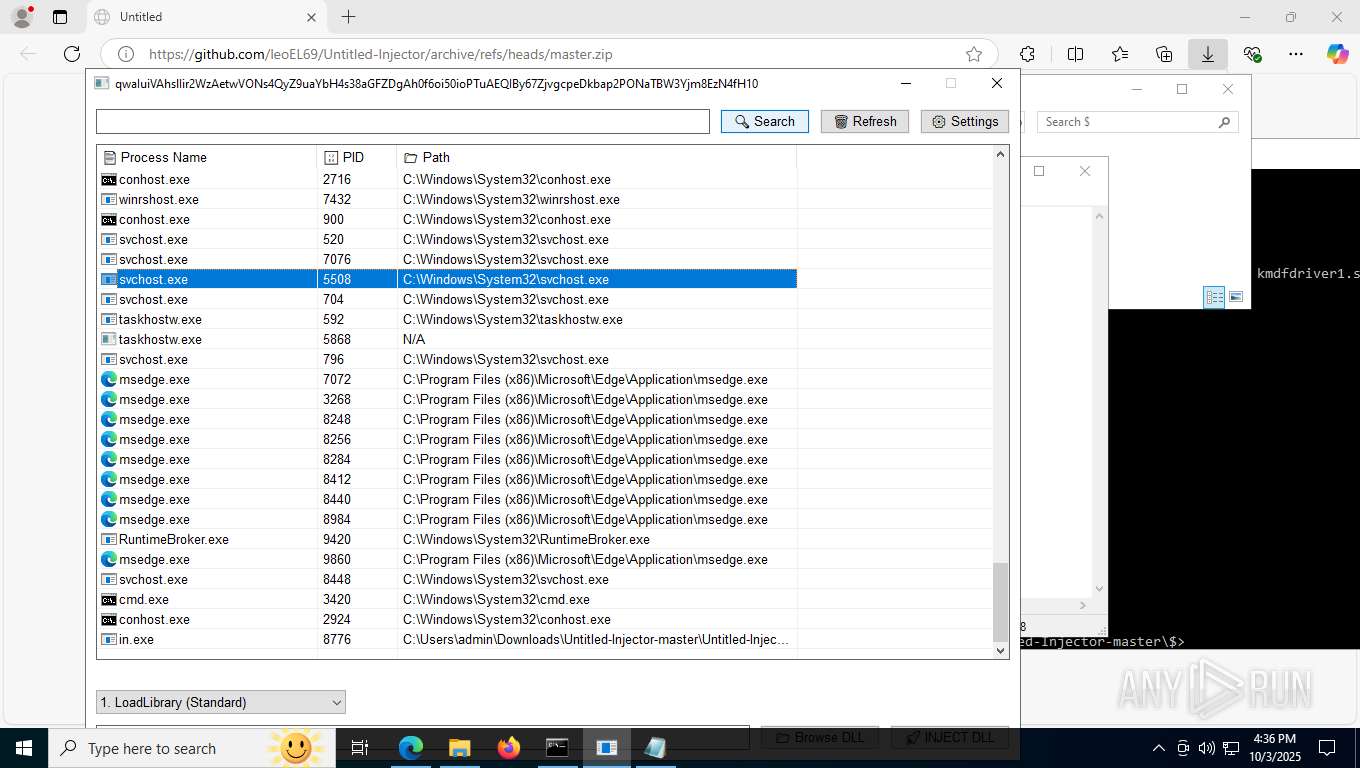
Behavior graph
Click at the process to see the details
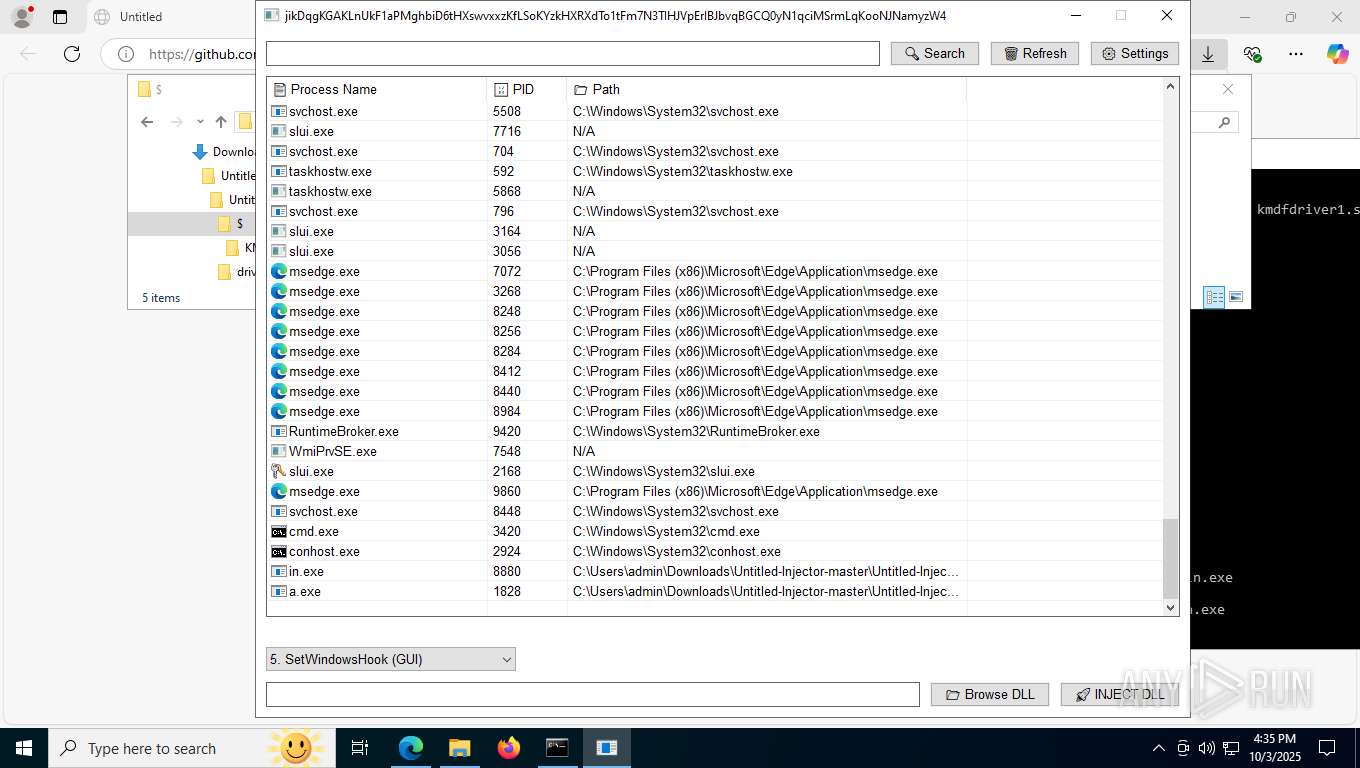
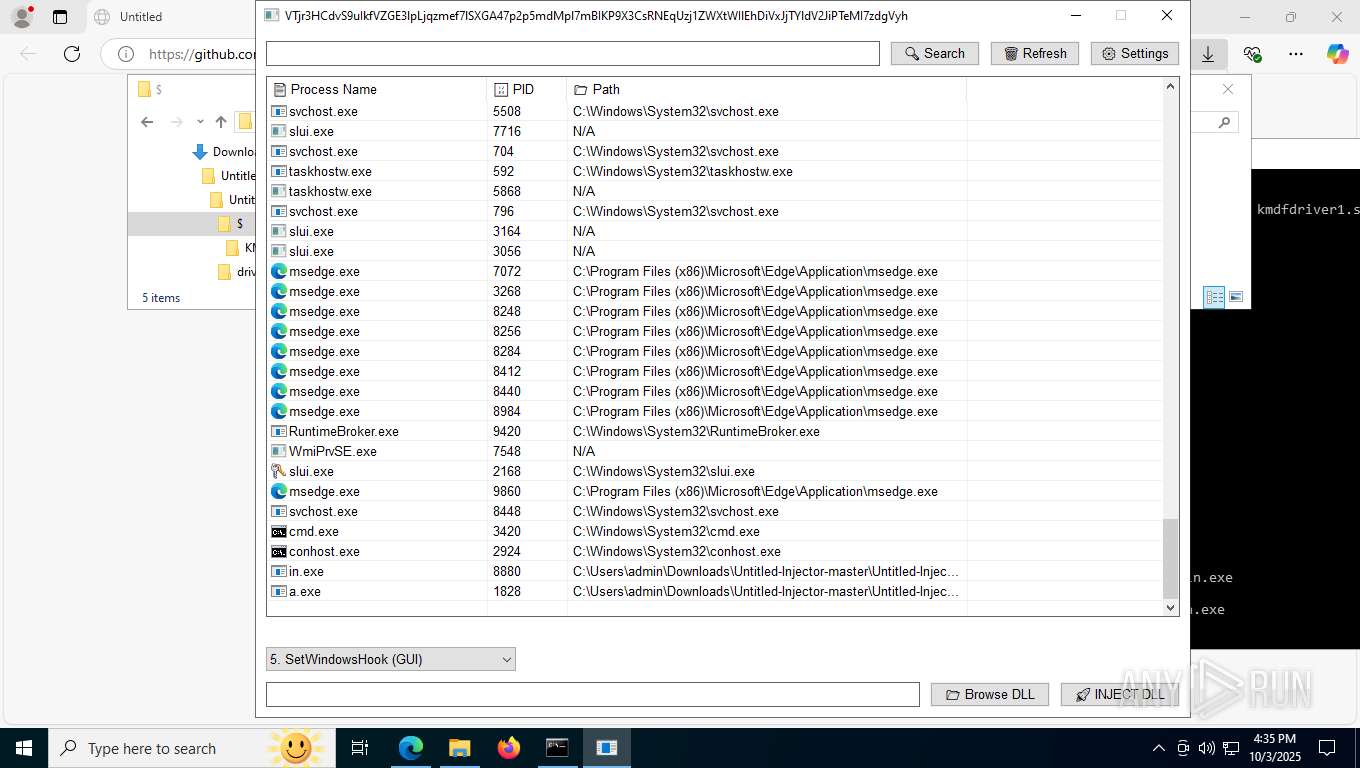
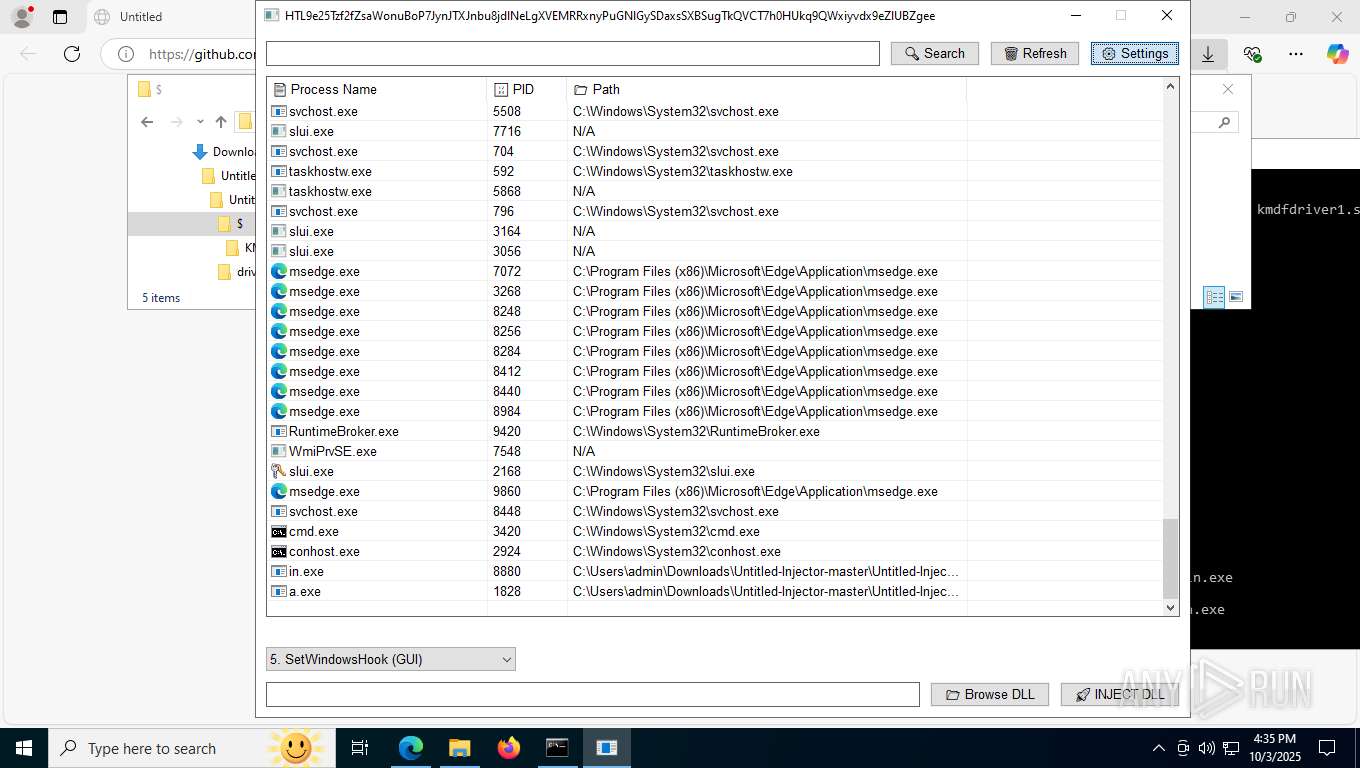
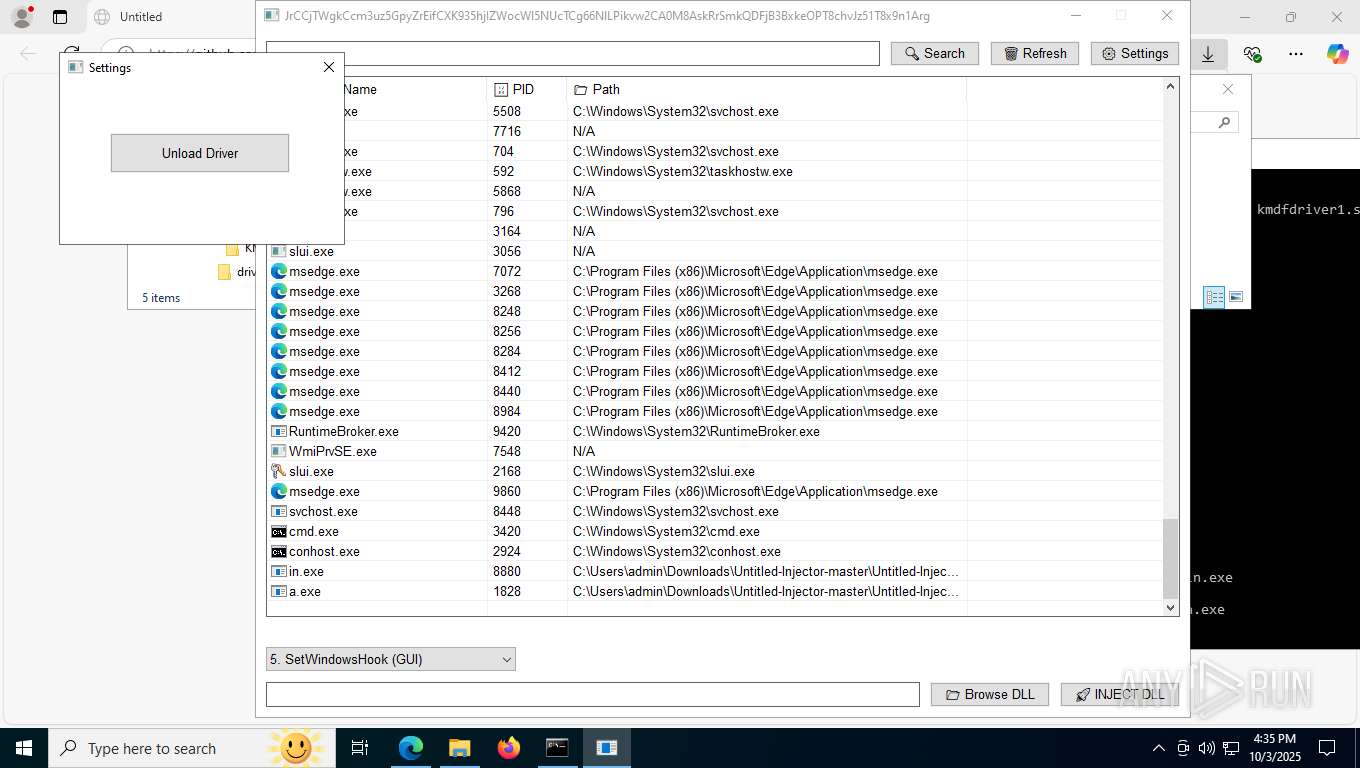
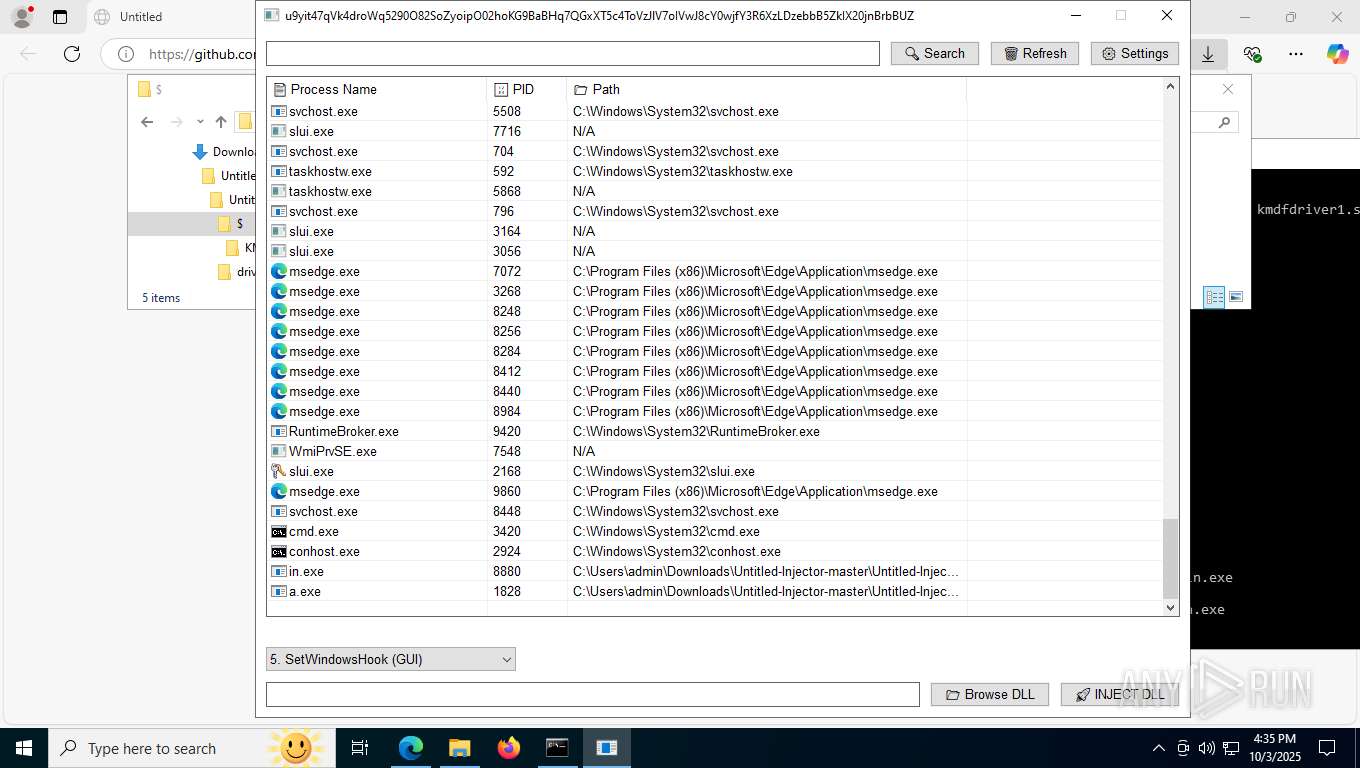
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1308 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
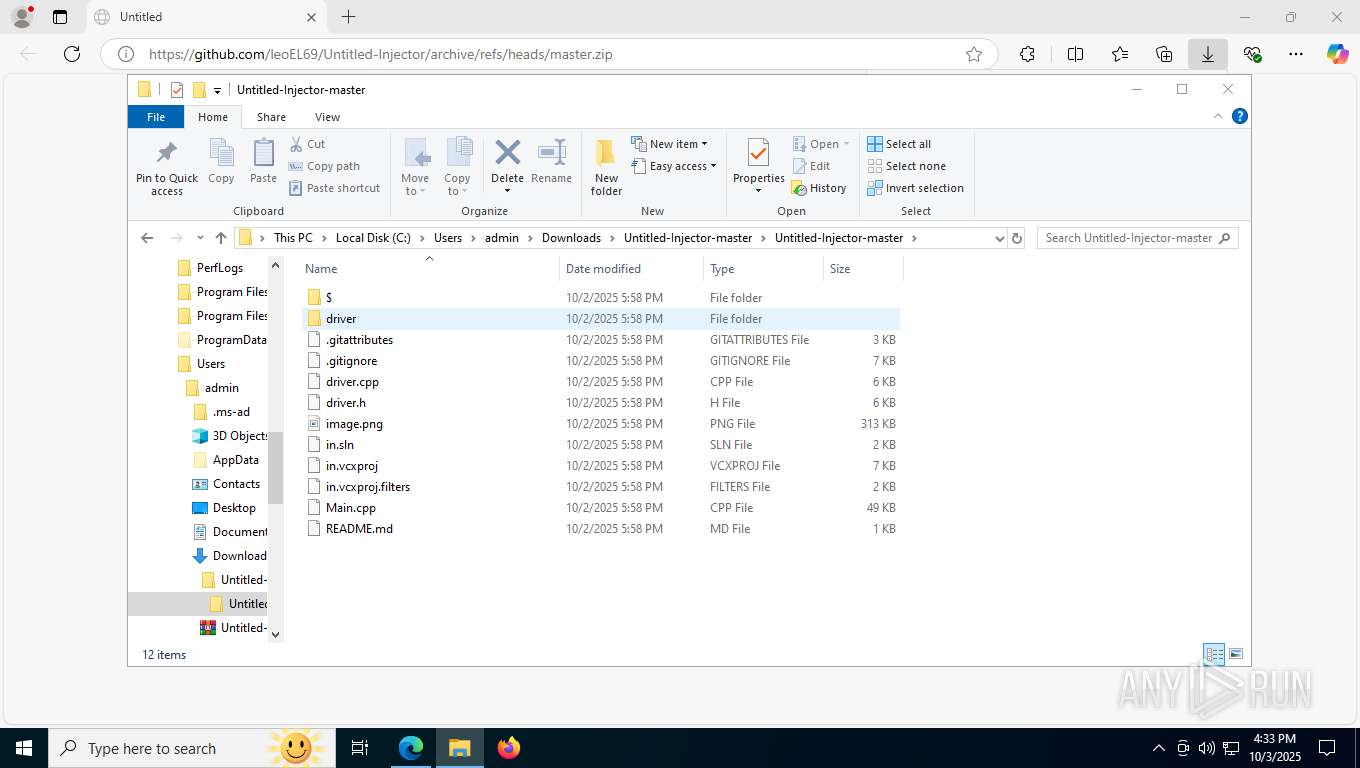
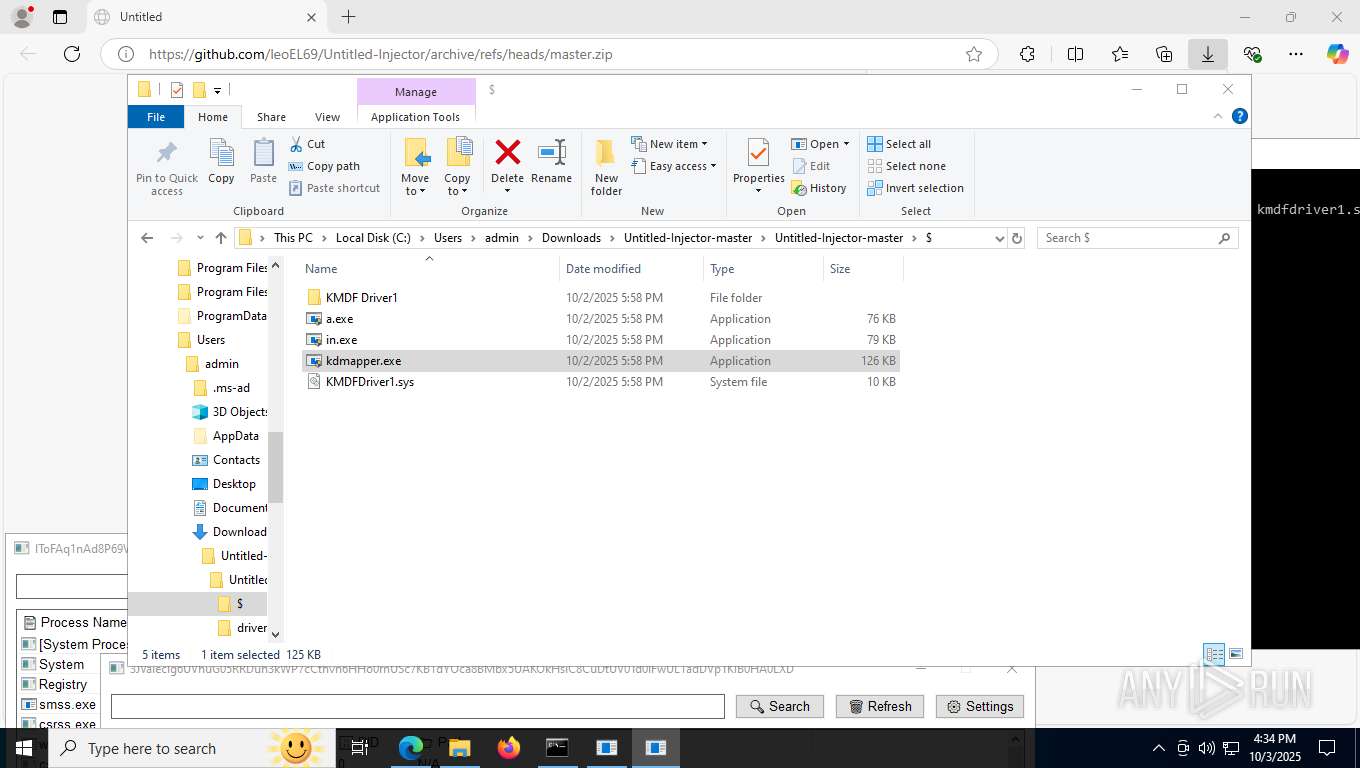
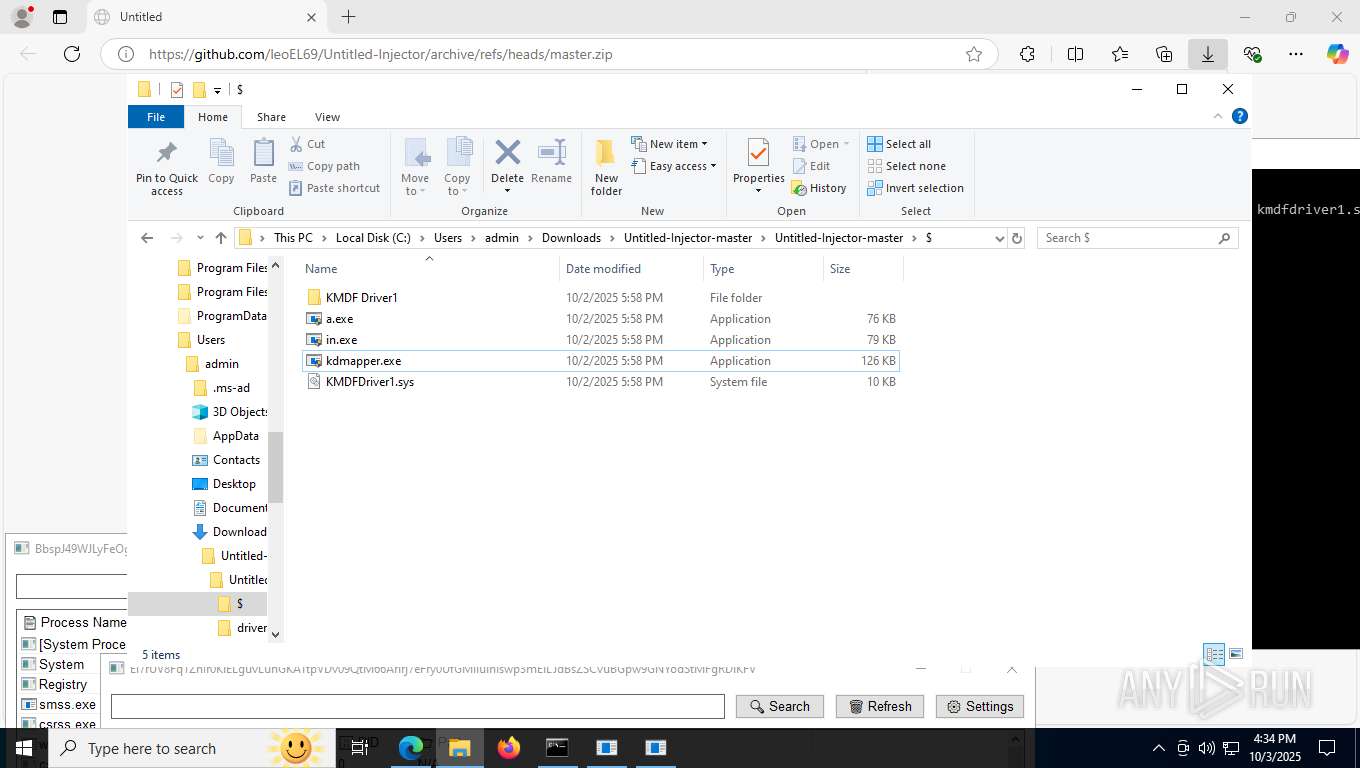
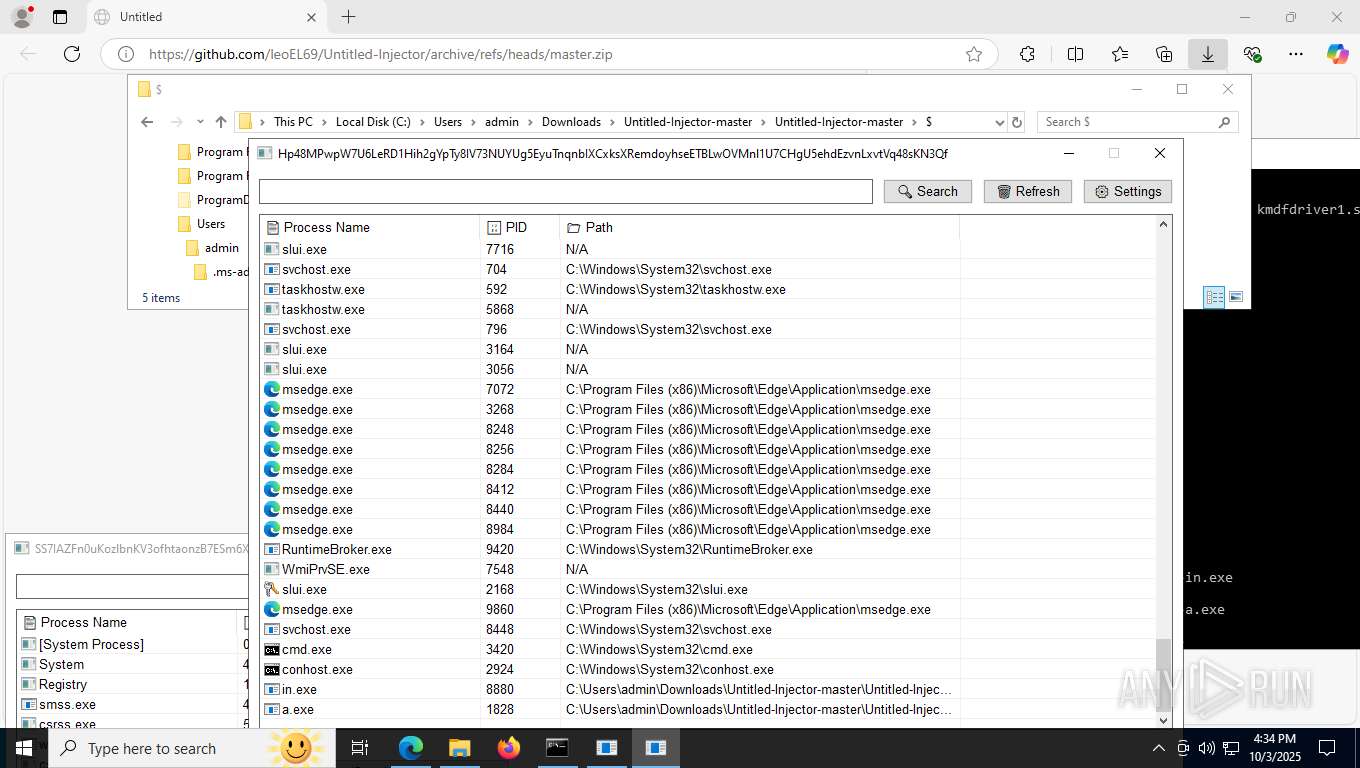
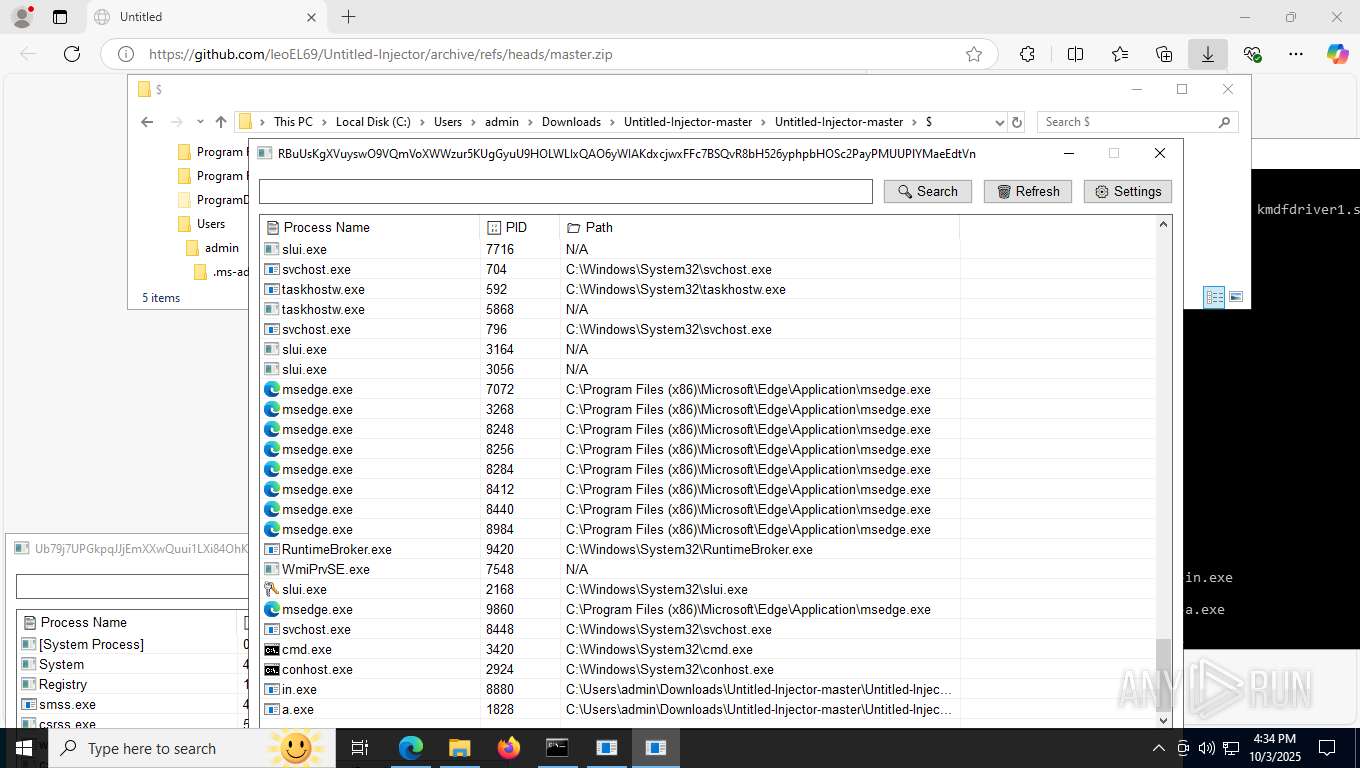
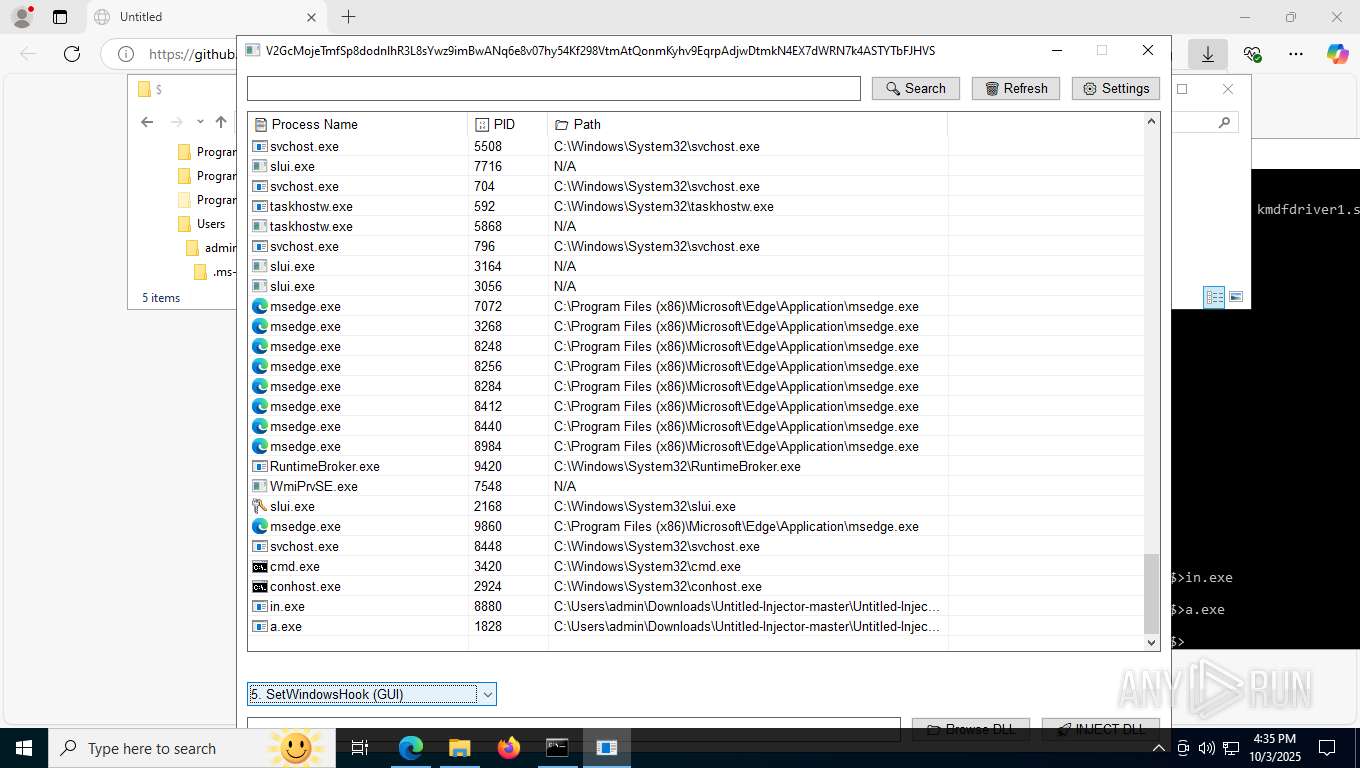
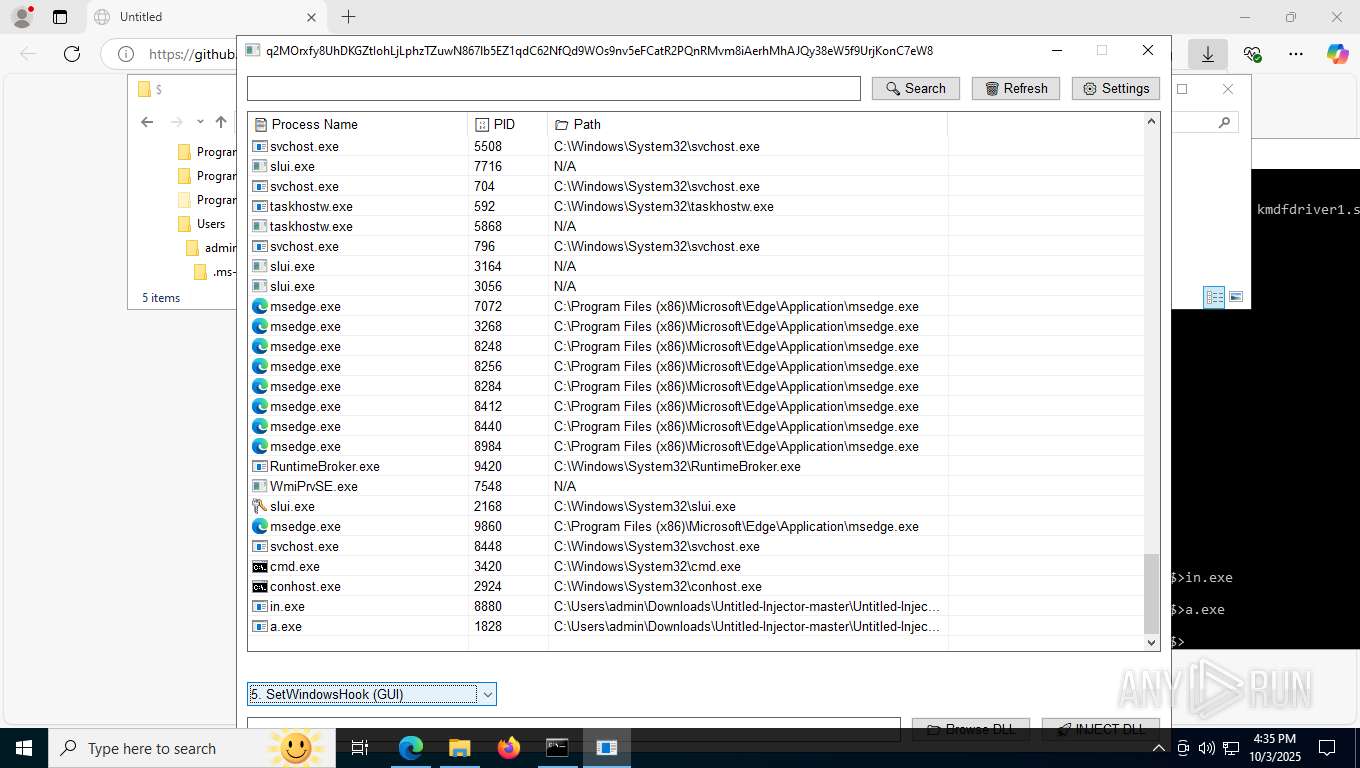
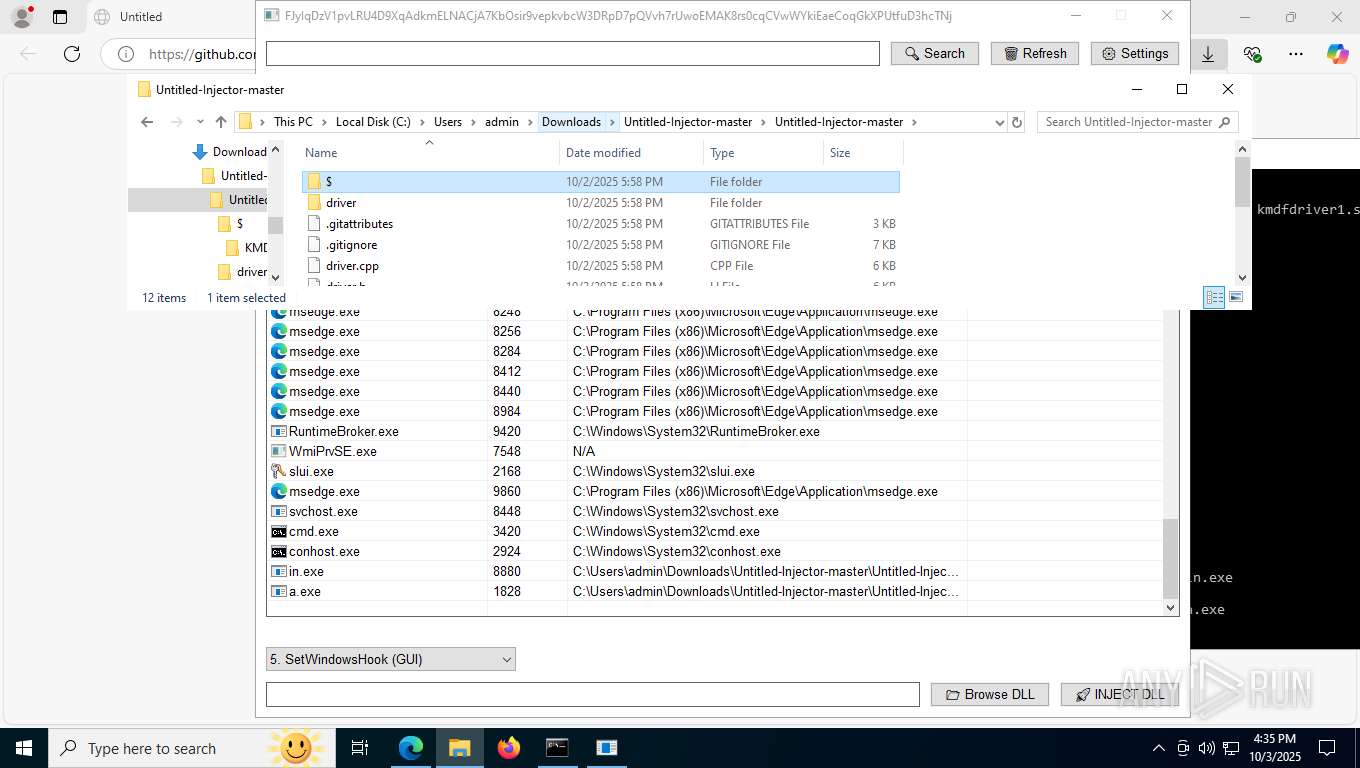
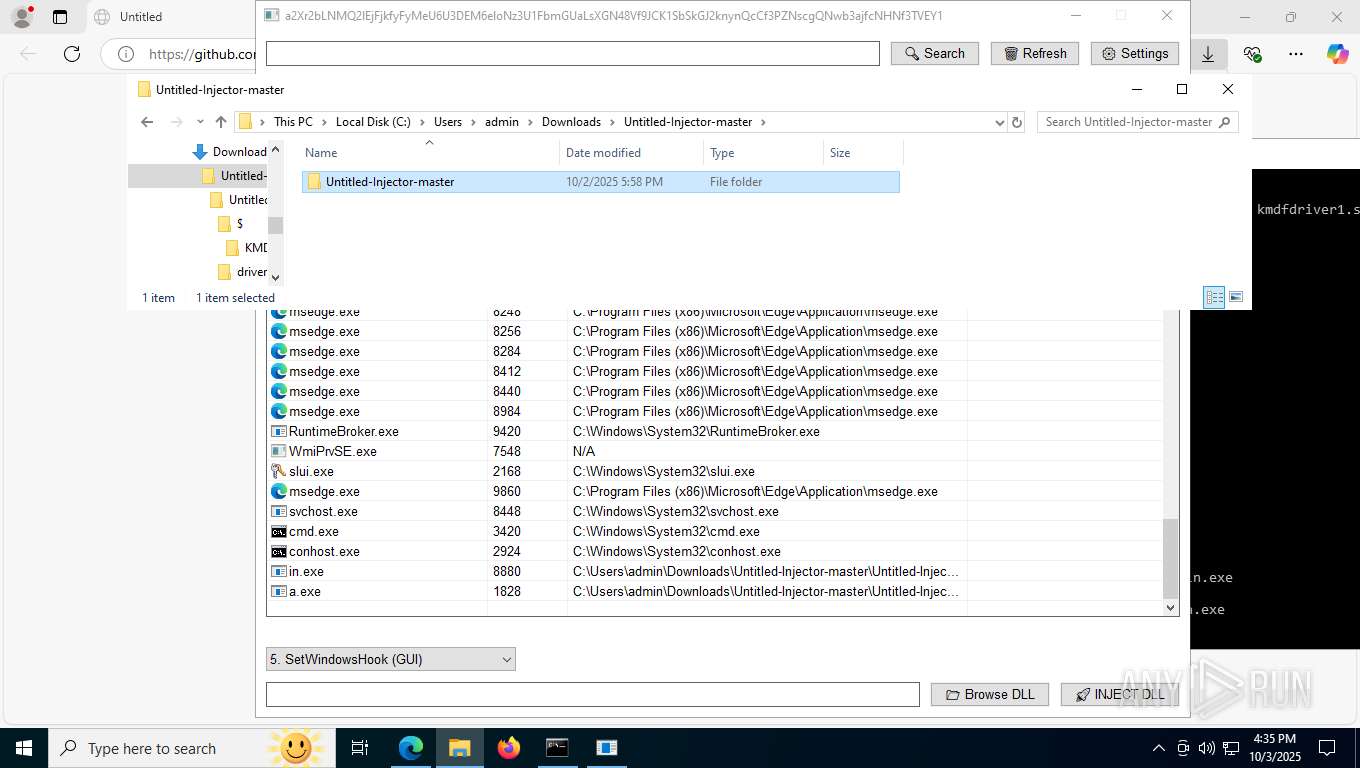
| 1476 | kdmapper kmdfdriver1.sys | C:\Users\admin\Downloads\Untitled-Injector-master\Untitled-Injector-master\$\kdmapper.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
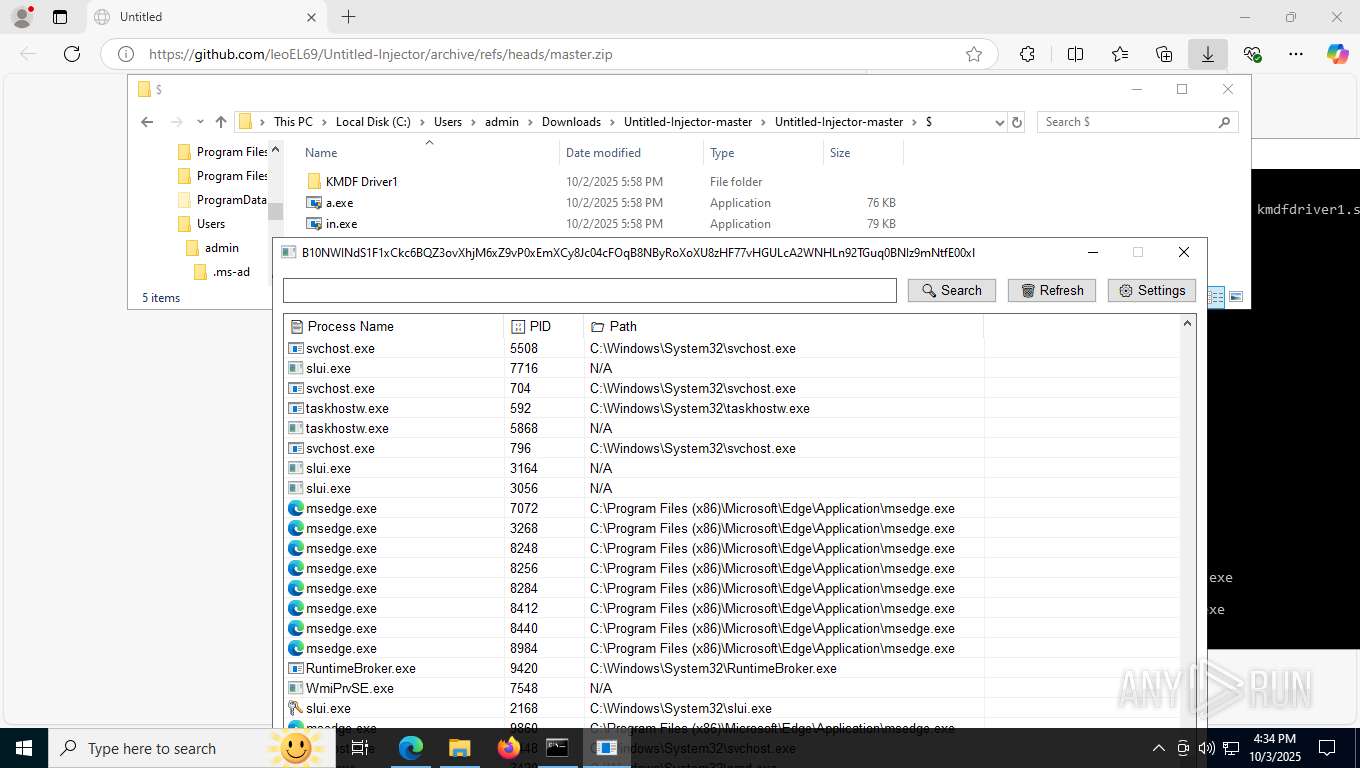
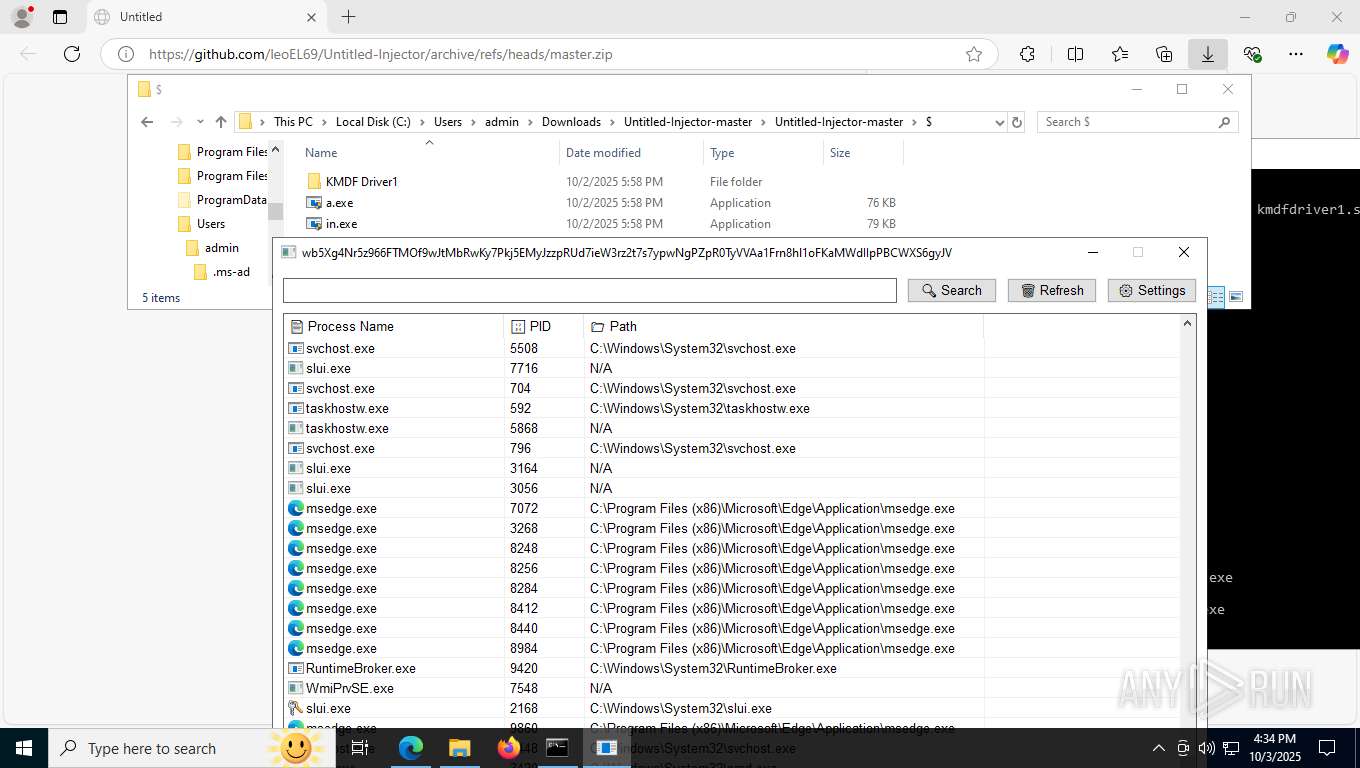
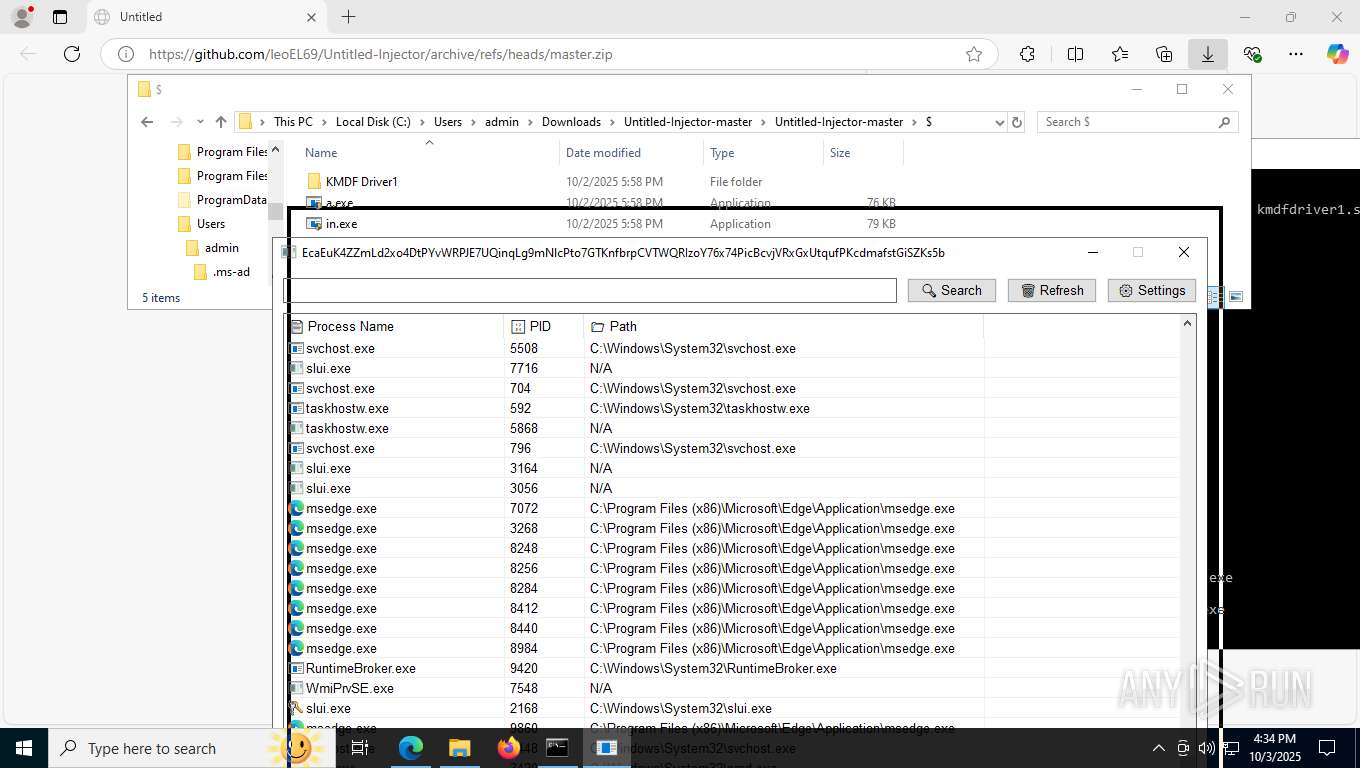
| 1828 | a.exe | C:\Users\admin\Downloads\Untitled-Injector-master\Untitled-Injector-master\$\a.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2168 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2368 | "C:\Users\admin\Downloads\Untitled-Injector-master\Untitled-Injector-master\$\in.exe" | C:\Users\admin\Downloads\Untitled-Injector-master\Untitled-Injector-master\$\in.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2488 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
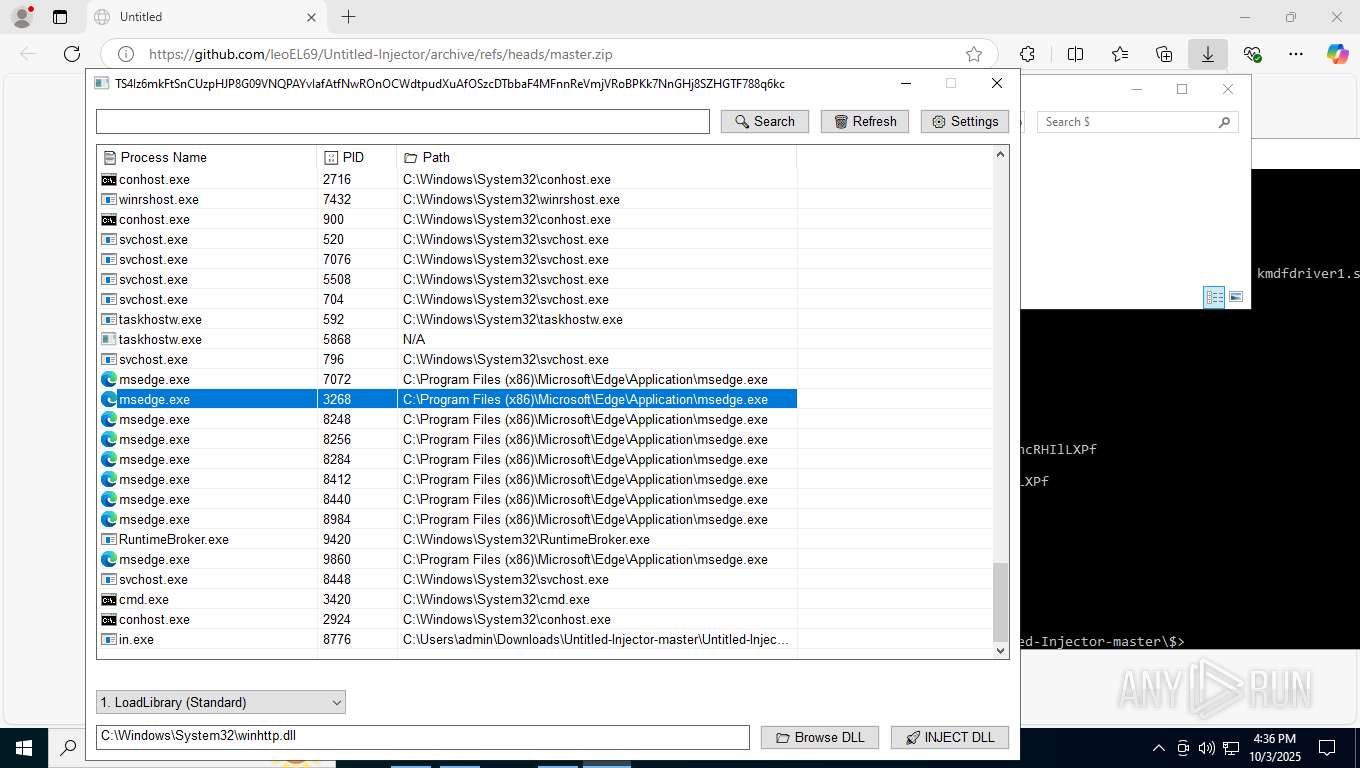
| 3268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x2ac,0x2b0,0x2b4,0x2a4,0x168,0x7ffba261f208,0x7ffba261f214,0x7ffba261f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
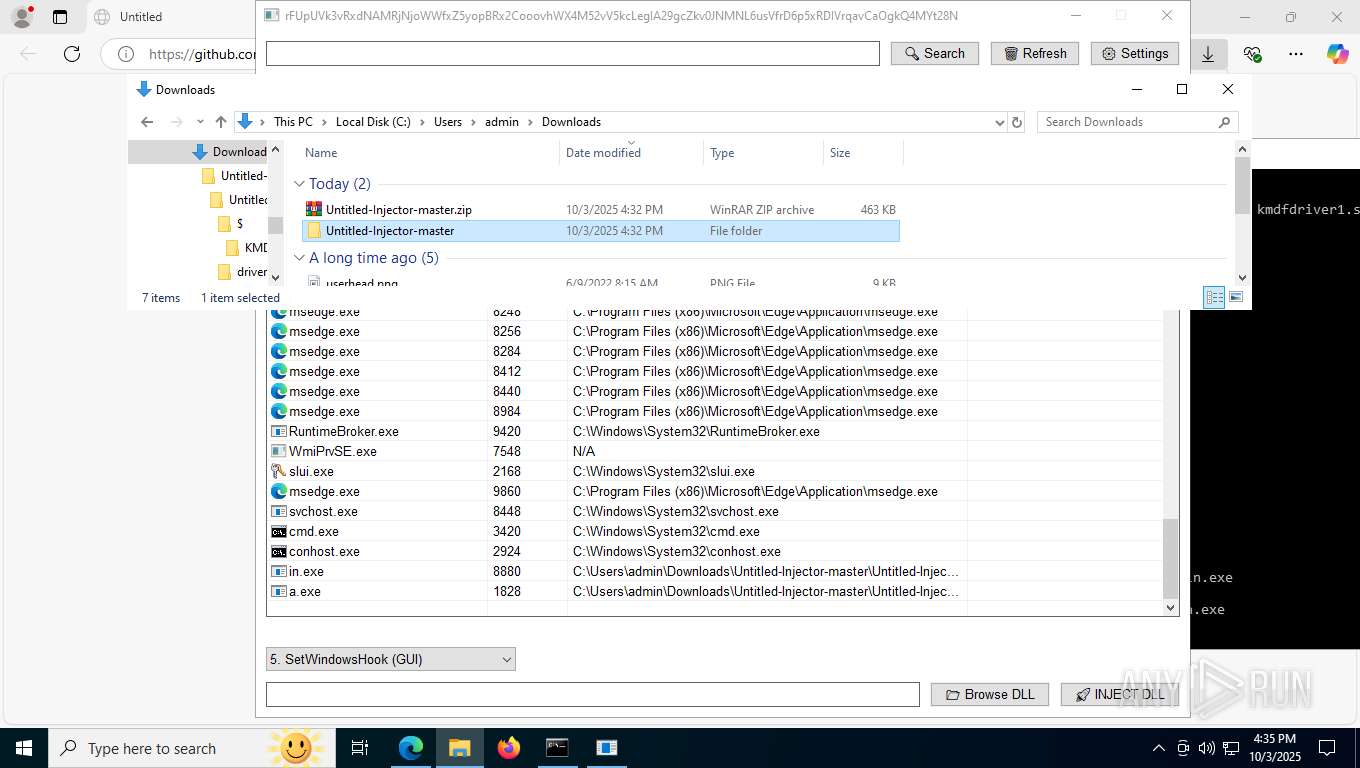
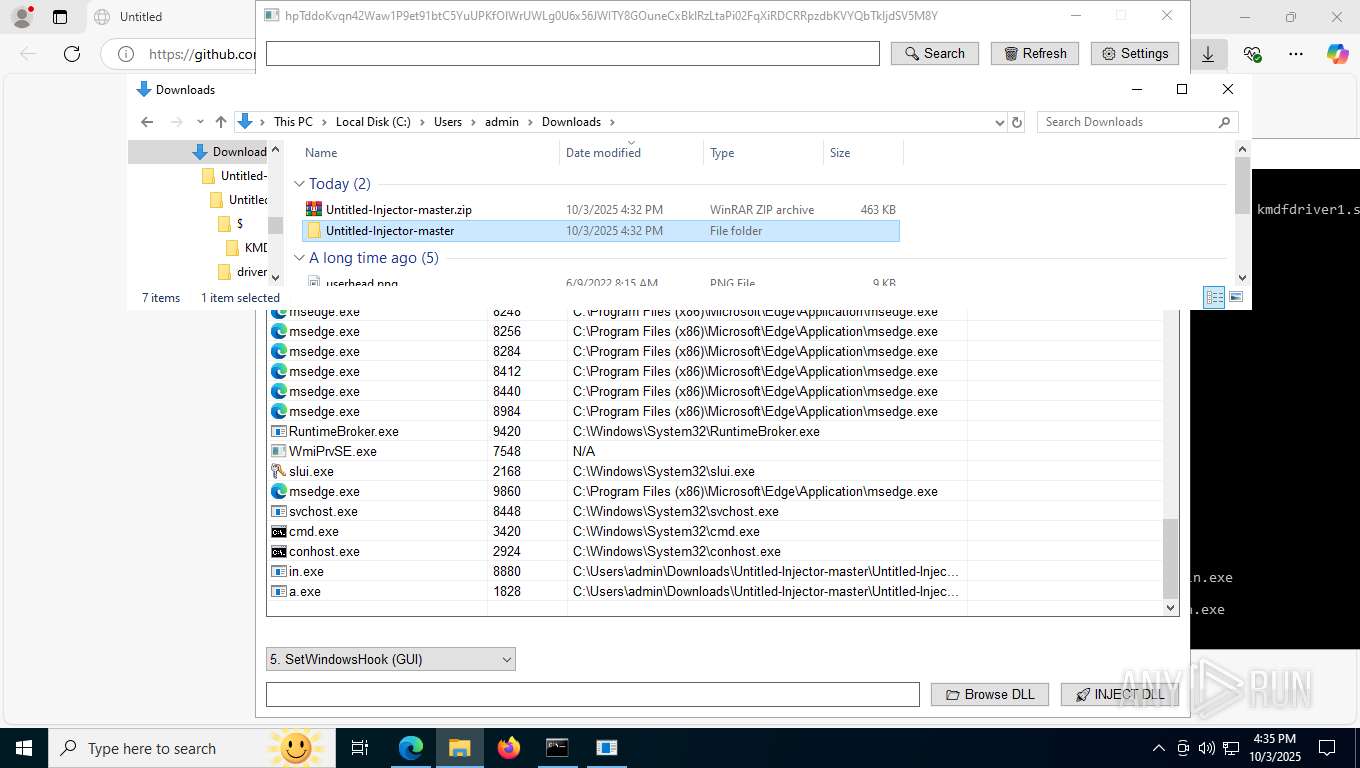
| 3420 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Untitled-Injector-master.zip" C:\Users\admin\Downloads\Untitled-Injector-master\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3420 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 635
Read events
27 383
Write events
235
Delete events
17
Modification events
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31208579 | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6292) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
20
Suspicious files
291
Text files
81
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1710f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1710f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1710f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1710f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF171107.TMP | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1710f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7072 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
93
DNS requests
79
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8256 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:uW2W6kcyyoPkMFmF8jicAFgP6voDh-HiLs5lia75-cg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 101 b | whitelisted |
8120 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
796 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
8860 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
796 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7024 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
10056 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
8448 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1759799333&P2=404&P3=2&P4=BkQFirz7JE14SFIKELrNWGJ7AaxzjkNtNUJzlXJRUL5D3vS2ucCAwCQfU8HrSdiwPC0IILf%2f9iQ%2bu29913W0JA%3d%3d | US | — | — | whitelisted |
8448 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1759799333&P2=404&P3=2&P4=BkQFirz7JE14SFIKELrNWGJ7AaxzjkNtNUJzlXJRUL5D3vS2ucCAwCQfU8HrSdiwPC0IILf%2f9iQ%2bu29913W0JA%3d%3d | US | binary | 1.09 Kb | whitelisted |
5224 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3432 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6016 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
8256 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8256 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8256 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
8256 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8256 | msedge.exe | 95.100.100.123:443 | copilot.microsoft.com | Akamai International B.V. | PT | whitelisted |
8256 | msedge.exe | 140.82.121.10:443 | codeload.github.com | GITHUB | US | whitelisted |
8256 | msedge.exe | 2.16.241.207:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
codeload.github.com |
| whitelisted |
www.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |