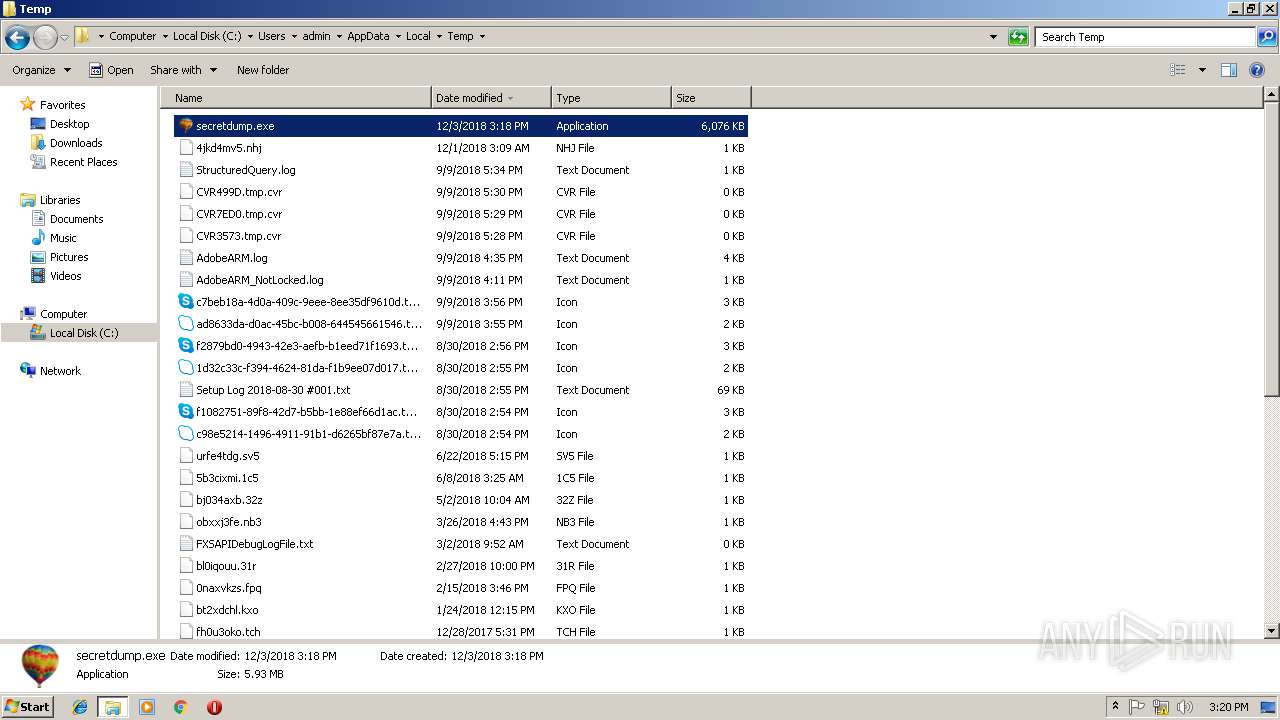
| File name: | secretdump |
| Full analysis: | https://app.any.run/tasks/22381f80-1542-44a1-9e41-5818231e785e |
| Verdict: | No threats detected |
| Analysis date: | December 03, 2018, 15:18:24 |
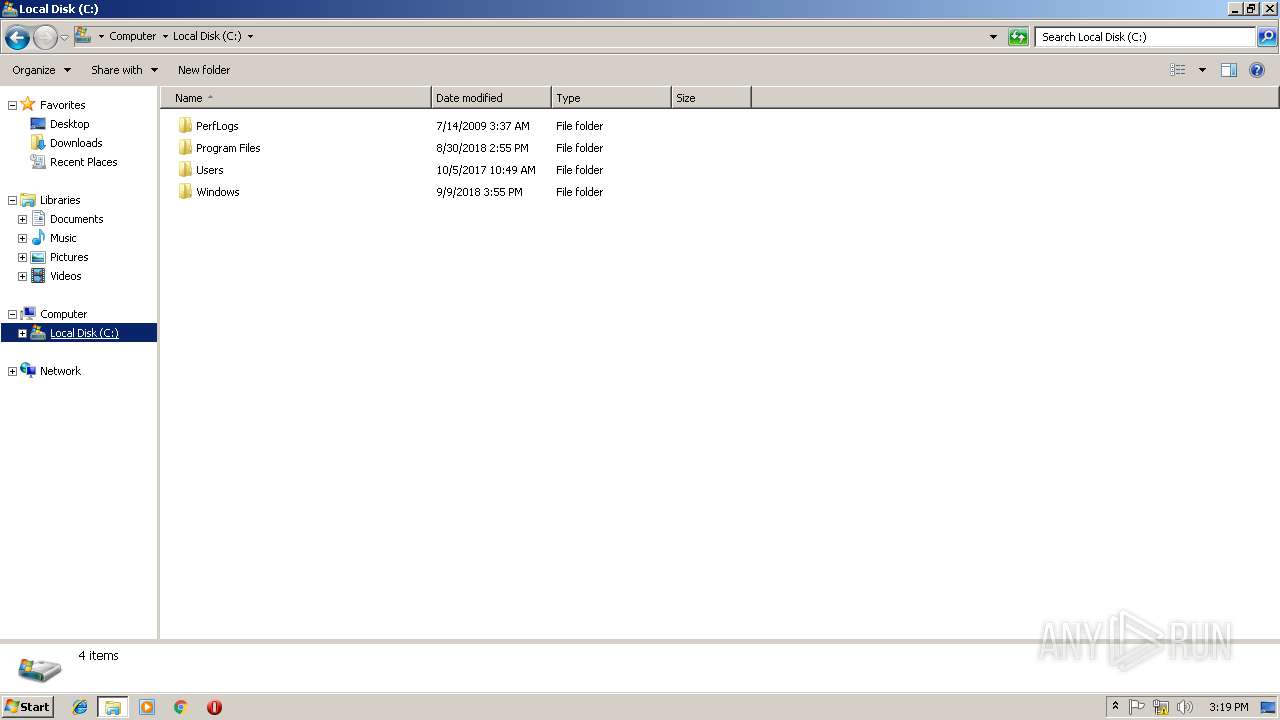
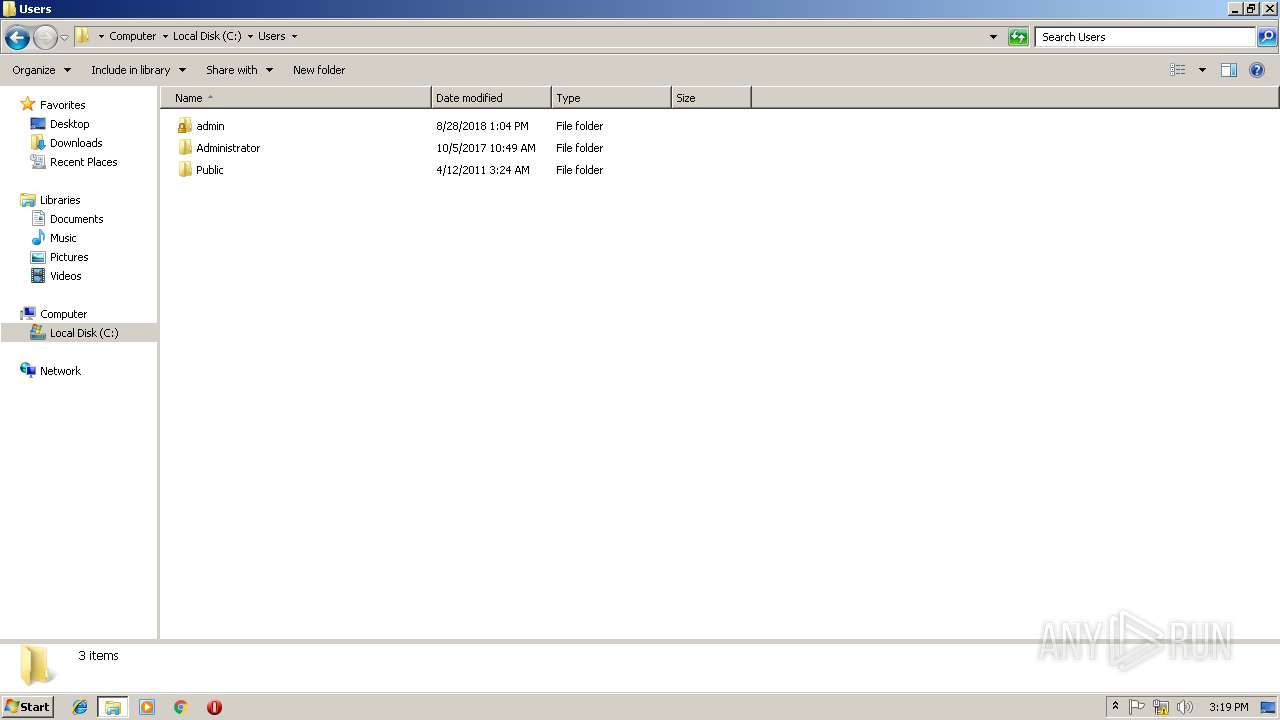
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 96EC8798BBA011D5BE952E0E6398795D |
| SHA1: | AF7C73C47C62D70C546B62C8E1CC707841EC10E3 |
| SHA256: | C3405D9C9D593D75D773C0615254E69D0362954384058EE970A3EC0944519C37 |
| SSDEEP: | 98304:gP9cgRyyVyGHAeBSut+aFNnLlPLeqNZ8hY/1KbxabdDk1duupRWQgWseI9eIfbkr:C9hlX+aFFLlPKQ8hY/DkWWst9e4ge+ |
MALICIOUS
Loads dropped or rewritten executable
- secretdump.exe (PID: 2660)
- explorer.exe (PID: 236)
SUSPICIOUS
Executable content was dropped or overwritten
- secretdump.exe (PID: 3736)
Loads Python modules
- secretdump.exe (PID: 2660)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (54.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (34.8) |
| .exe | | | Win32 Executable (generic) (5.6) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:12:11 16:09:08+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 127488 |
| InitializedDataSize: | 427008 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x769a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
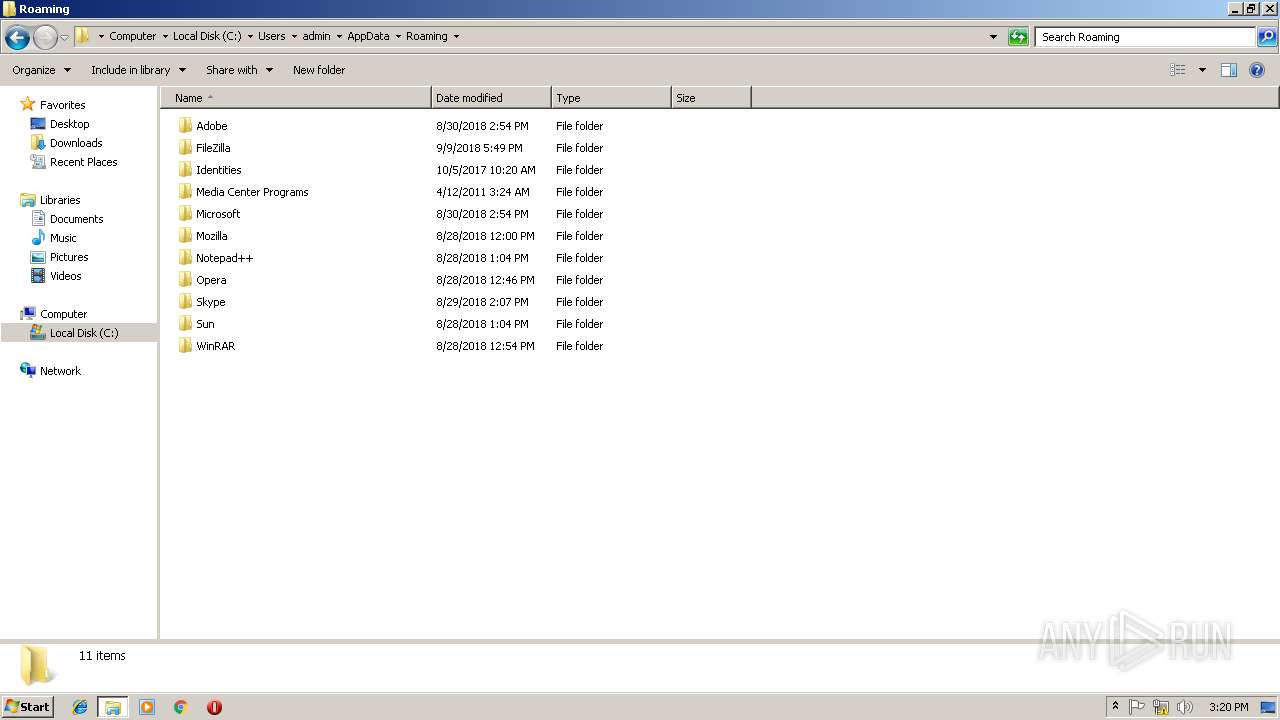
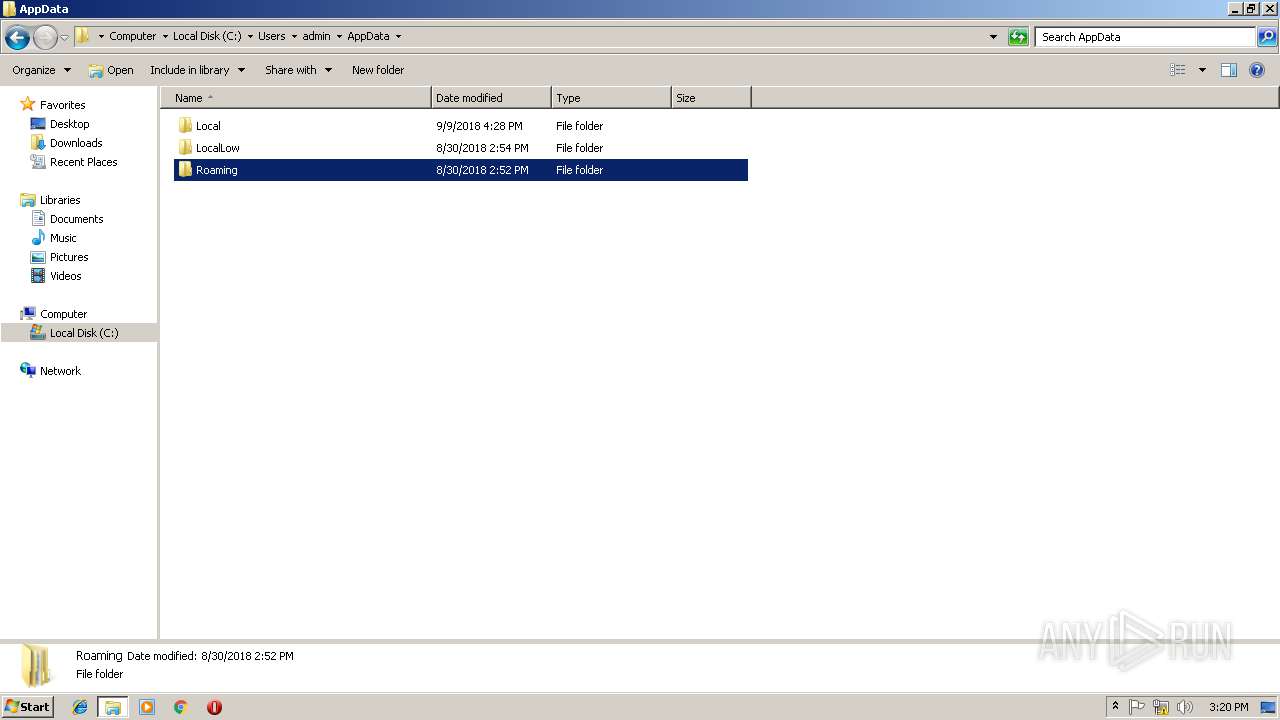
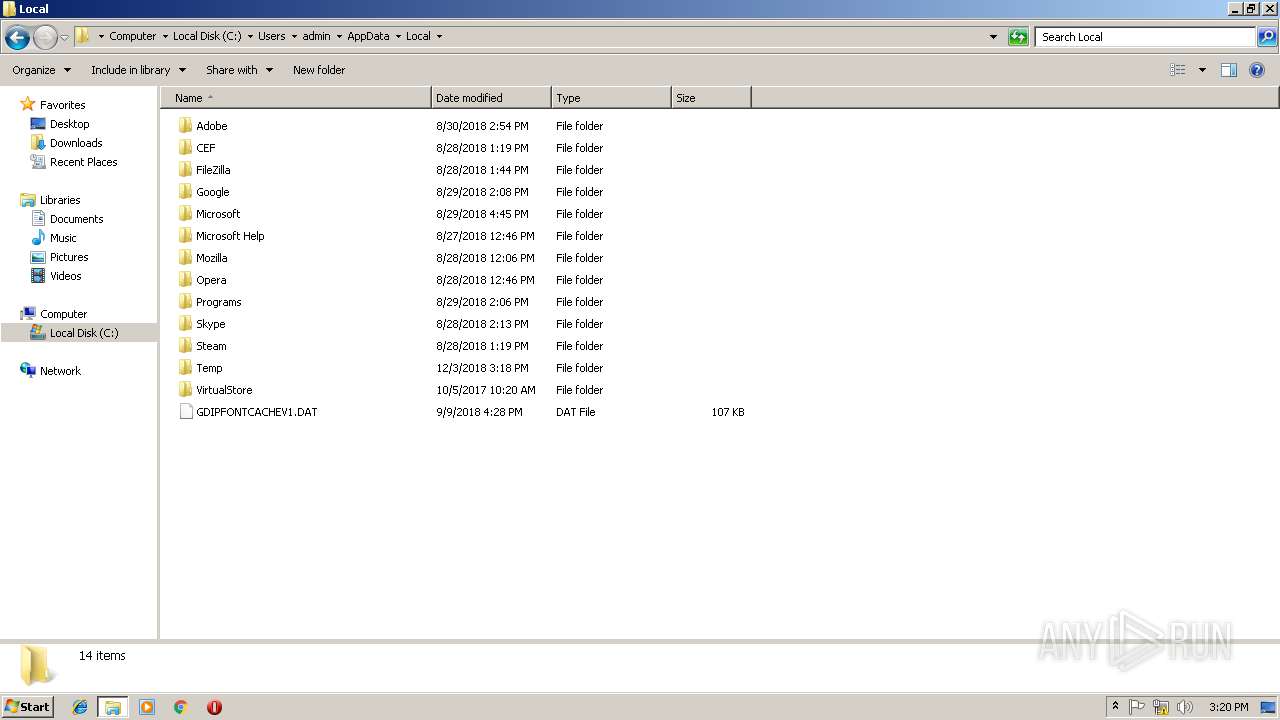
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 11-Dec-2017 15:09:08 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-Dec-2017 15:09:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F144 | 0x0001F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66103 |
.rdata | 0x00021000 | 0x0000B06C | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.0856 |
.data | 0x0002D000 | 0x0000E678 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.93451 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.85613 |
.rsrc | 0x0003D000 | 0x0005AC4C | 0x0005AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.54885 |
.reloc | 0x00098000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6361 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.76511 | 90 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.28517 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
2 | 4.93416 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.75846 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.71137 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.57044 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.49661 | 270376 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
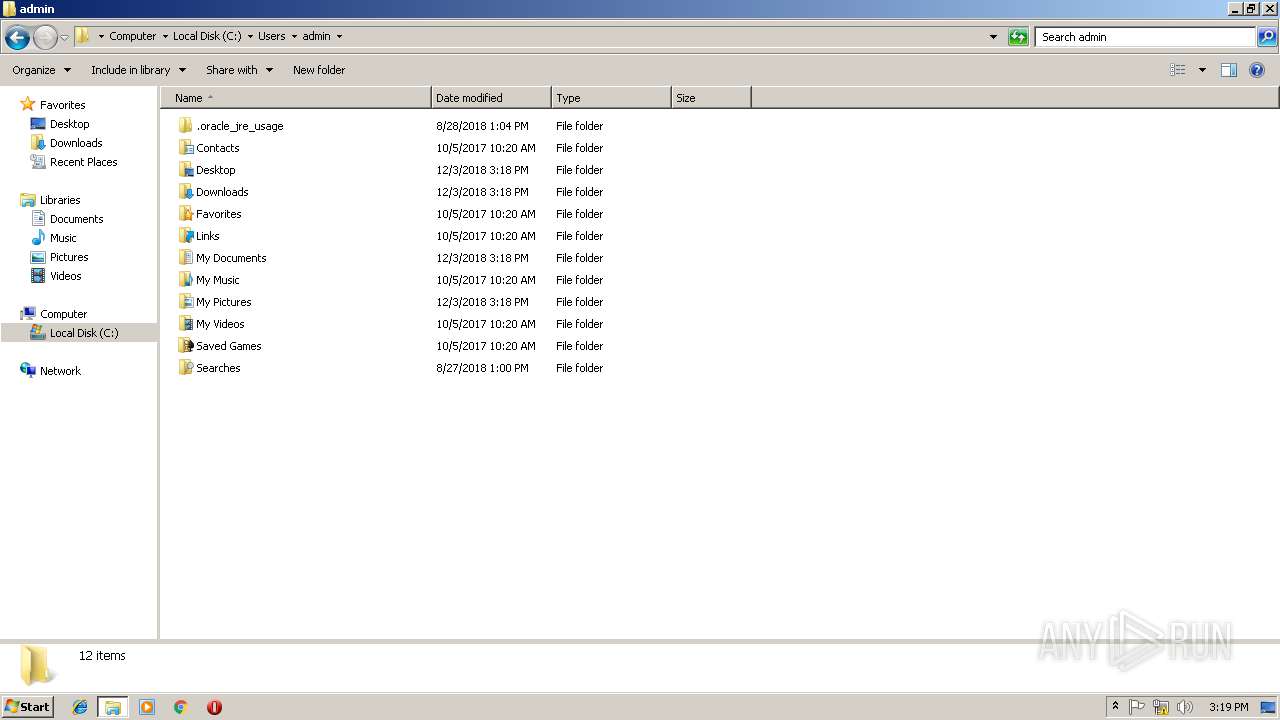
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
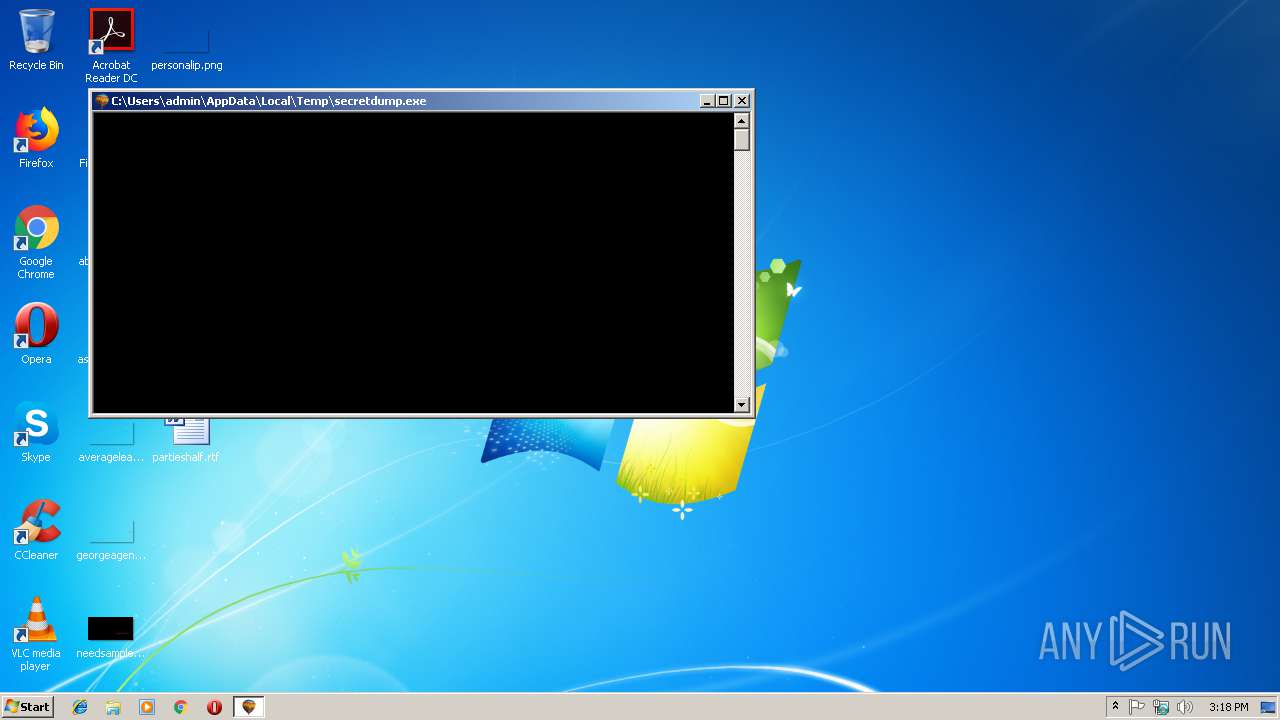
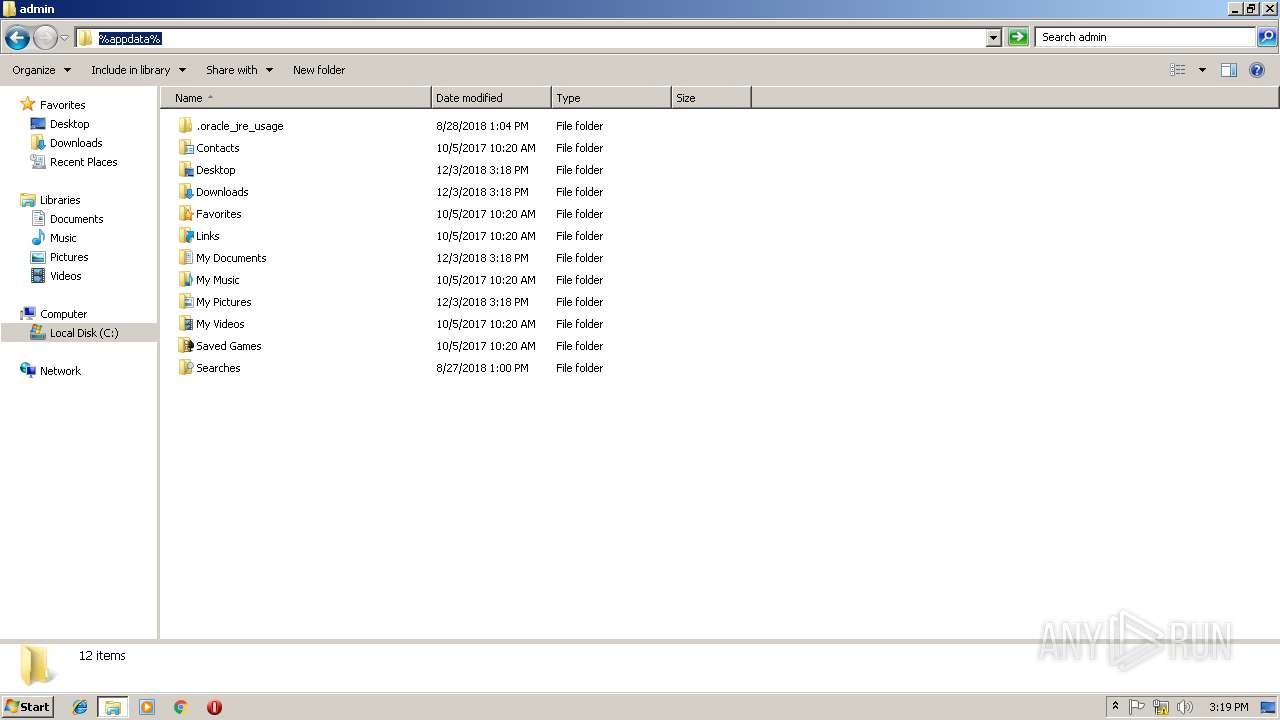
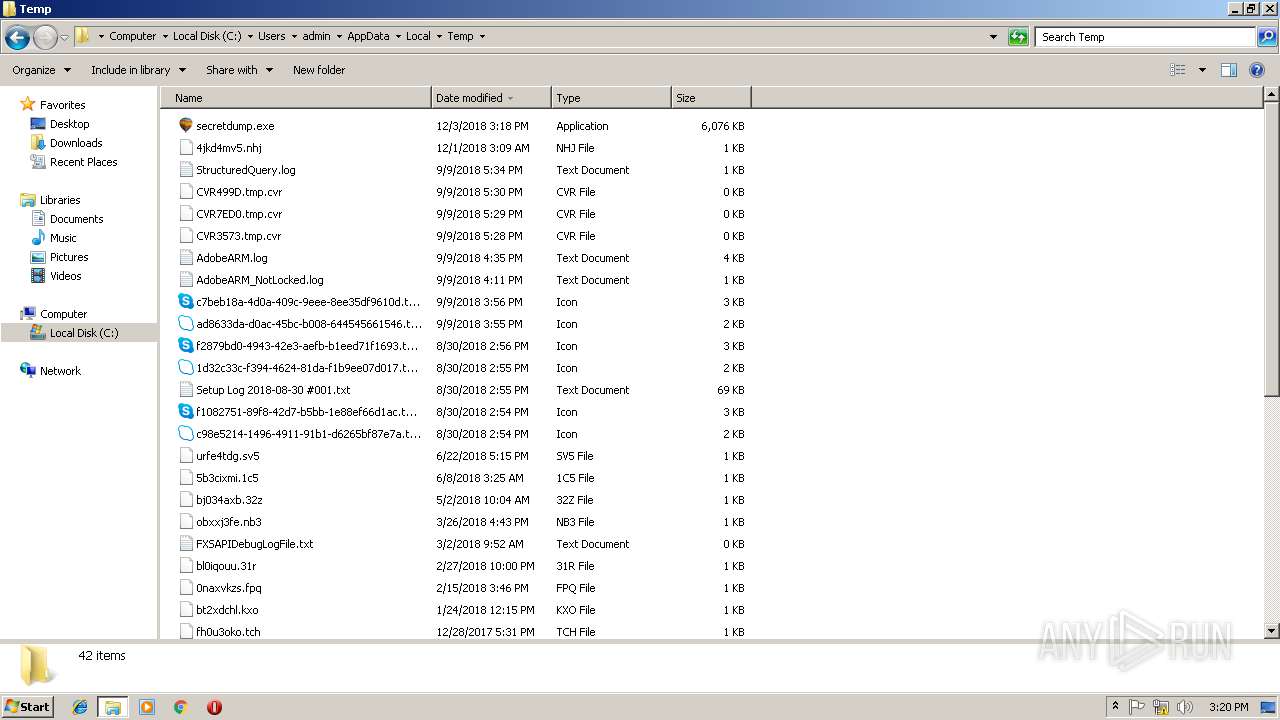
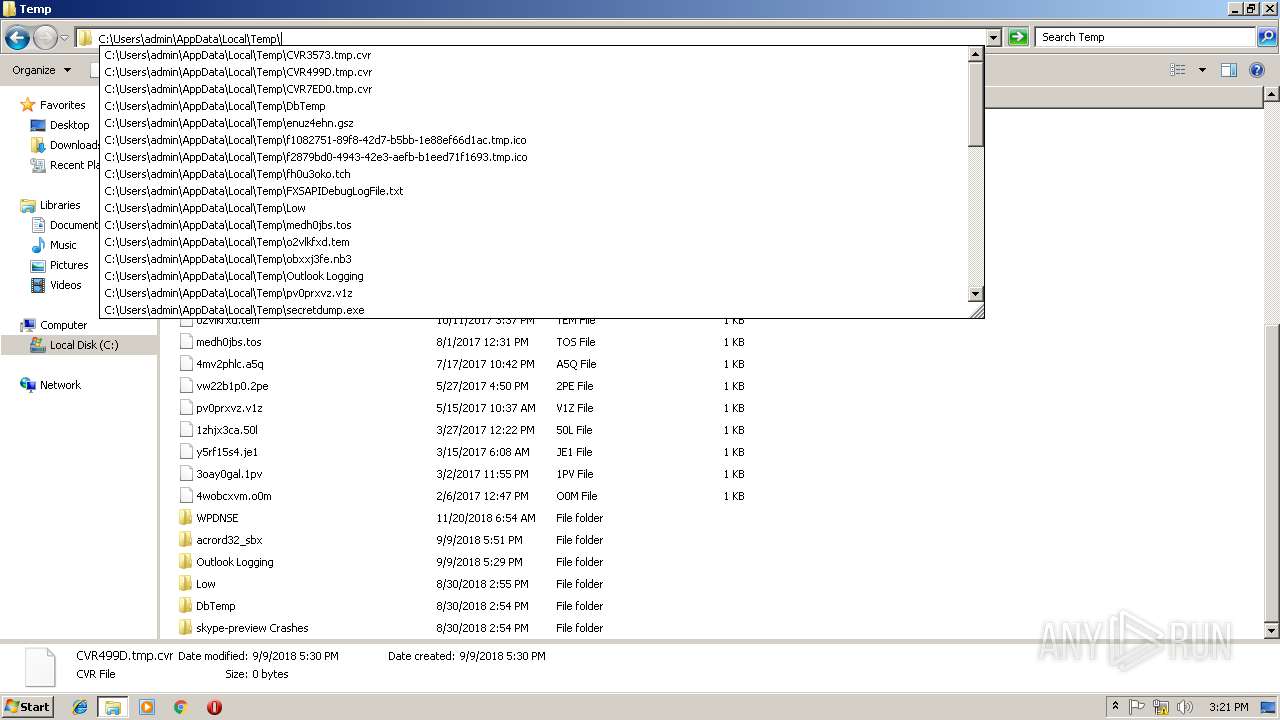
| 2660 | "C:\Users\admin\AppData\Local\Temp\secretdump.exe" | C:\Users\admin\AppData\Local\Temp\secretdump.exe | — | secretdump.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2780 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3736 | "C:\Users\admin\AppData\Local\Temp\secretdump.exe" | C:\Users\admin\AppData\Local\Temp\secretdump.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
1 890
Read events
1 392
Write events
498
Delete events
0
Modification events
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\frpergqhzc.rkr |
Value: 0000000000000000000000000D030000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002E0000003D00000006601500090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000E0000005DEC04007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000003702000008023CE23702350100C082BAD075B048D4750200000001000000A048D4750100000068E23702C5B8D075A848D47501000000C81008000000000090E237026BB9D07500000000350100C001000000B0E23702973CB8779C3CB877F58CF77501000000350100C00000000088E23702FFFFFFFFF8E23702EDE0B47745727800FEFFFFFFC0E237020D6BD075A0E737028CE8370200000000F8E23702973CB8779C3CB877BD8CF775000000008CE83702A0E73702D0E237020100000070E73702EDE0B47745727800FEFFFFFF08E337020D6BD0757E0000008CE8370280E73702F36BD075E186D0752794C6128CE8370210000000570104003E0040008CE83702A0E73702000000000000000000000000000008025CE537020000080254E33702350100C000000000D8E637023200000018000000000000000000000088E3370211000000B8450B00B0450B0032000000D8E63702F0E300009B1EC112A0E3370282919576F0E33702A4E3370227959576000000006C155002CCE33702CD9495766C15500278E43702E0105002E194957600000000E010500278E43702D4E33702090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {S38OS404-1Q43-42S2-9305-67QR0O28SP23}\rkcybere.rkr |
Value: 000000000700000009000000A8D90300000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFB035C09B1B8BD40100000000 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000002F0000003D00000006601500090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000E0000005DEC04007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000003702000008023CE23702350100C082BAD075B048D4750200000001000000A048D4750100000068E23702C5B8D075A848D47501000000C81008000000000090E237026BB9D07500000000350100C001000000B0E23702973CB8779C3CB877F58CF77501000000350100C00000000088E23702FFFFFFFFF8E23702EDE0B47745727800FEFFFFFFC0E237020D6BD075A0E737028CE8370200000000F8E23702973CB8779C3CB877BD8CF775000000008CE83702A0E73702D0E237020100000070E73702EDE0B47745727800FEFFFFFF08E337020D6BD0757E0000008CE8370280E73702F36BD075E186D0752794C6128CE8370210000000570104003E0040008CE83702A0E73702000000000000000000000000000008025CE537020000080254E33702350100C000000000D8E637023200000018000000000000000000000088E3370211000000B8450B00B0450B0032000000D8E63702F0E300009B1EC112A0E3370282919576F0E33702A4E3370227959576000000006C155002CCE33702CD9495766C15500278E43702E0105002E194957600000000E010500278E43702D4E33702090000000B000000DCC402007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C00410064006F00620065005C004100630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000000000D09866060000000034E82802C05D5A740200000002000000000C00940F000000E8E82802010000000400000001000000010000006B001001D098660605000000D098660602020000E20101AE2B51EA0088E7280239B58D76E20101AE24E82802130000000400000030000000120000001D000000130000001D0000000E00000012000000020000003200000014000000E387EE7A38E82802F3AE5B7400574100E20101AE010000000000000011000000F0443500E8443500A14A52740000000020E800001F51EA7AD0E728028291917520E828028CD800006B51EA7AE4E72802B69C917590D8D4035C0000000401000084F2280244F228026B4E317411000000F0443500E8443500A8EAD403FA4F31740000000074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000070000000000000006000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFB035C09B1B8BD40100000000 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000026000000000000002500000009000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D02 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | {9R3995NO-1S9P-4S13-O827-48O24O6P7174}\GnfxOne\Jvaqbjf Rkcybere.yax |
Value: 00000000070000000000000007000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFB035C09B1B8BD40100000000 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{F4E57C4B-2036-45F0-A9AB-443BCFE33D9F}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 0000000026000000000000002600000009000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D0209000000000000000900000043003A005C00550073006500720073005C005000750062006C00690063005C004400650073006B0074006F0070005C004100630072006F0062006100740020005200650061006400650072002000440043002E006C006E006B0000006C006E006B000000630072006F0062006100740020005200650061006400650072002000440043005C005200650061006400650072005C004100630072006F0052006400330032002E0065007800650000001D020000000085F990758C52F402BCD51D0294D51D028852F402C8D51D02546F9D76BC66AC760000000068DA1D026C31917568DA1D02553E9175337AD50628DD1D0200000000813E917590DA1D0294DA1D028852F402CD78D50656DD1D0200000000337AD506740A91750000000000000000000000000000000000000000000000000000000000000000FFFFFFFF00000000000000000000000091768106A77681069176810600000000000000000000000000000000000000000000000000000000000000009D240000C0ED9D0388D61D0233AB4777C019F5EFFC0B00001027000008000000ED530200BCD61D02F8AA4777ED530200C0ED9D03DCD61D02E8DED4035CD71D0200000000A20100001CD700001360DF7ACCD61D02829191751CD71D02D0D61D02279591750000000074E3D403F8D61D02CD94917574E3D403A4D71D02E8DED403E194917500000000E8DED403A4D71D0200D71D02 | |||
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
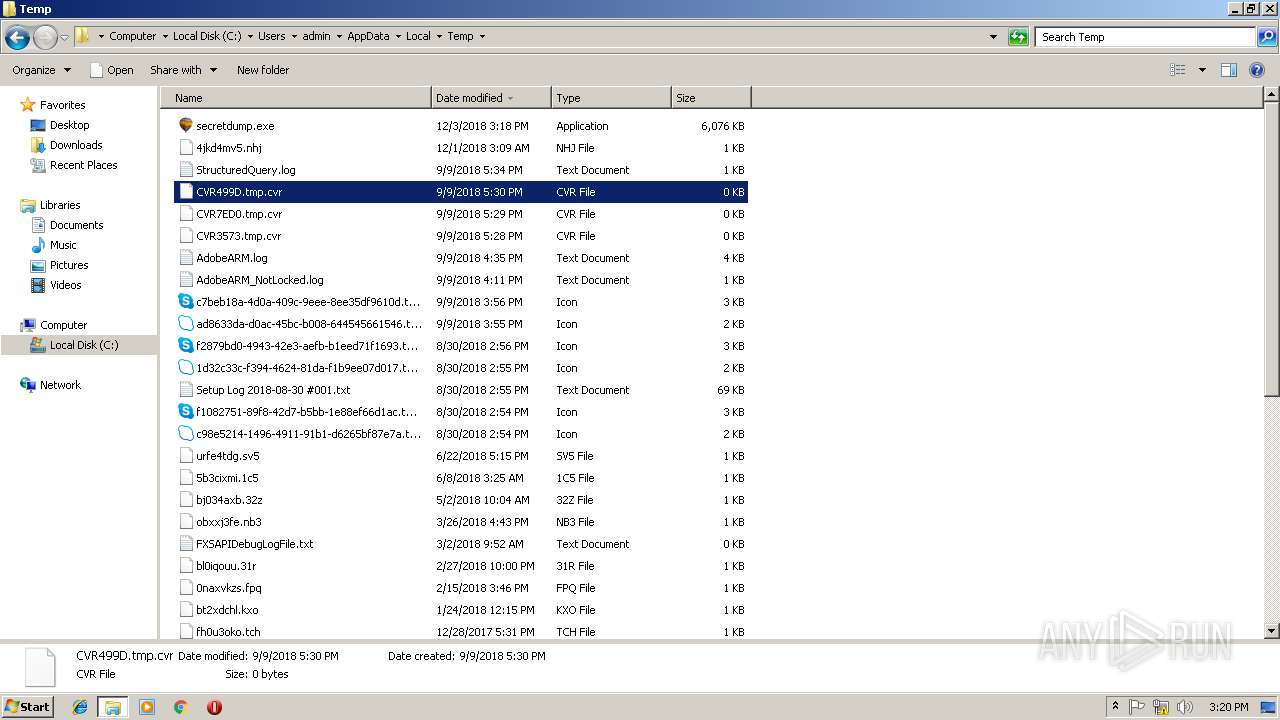
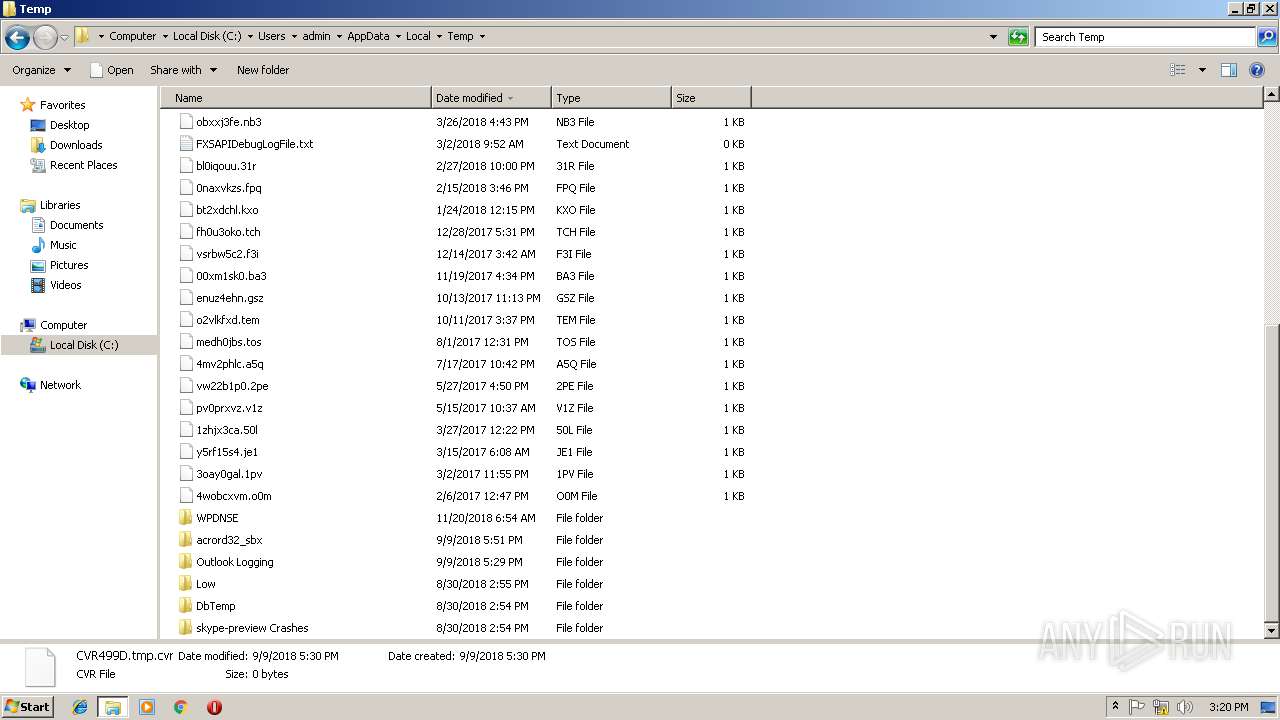
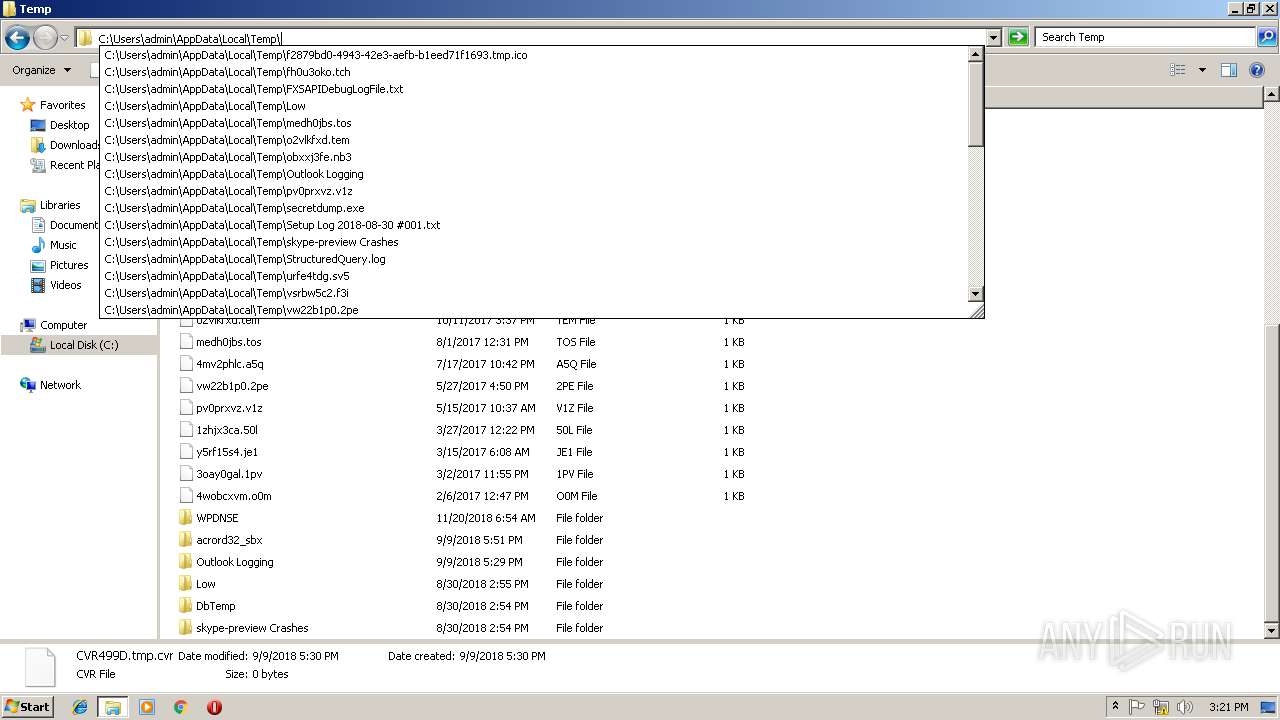
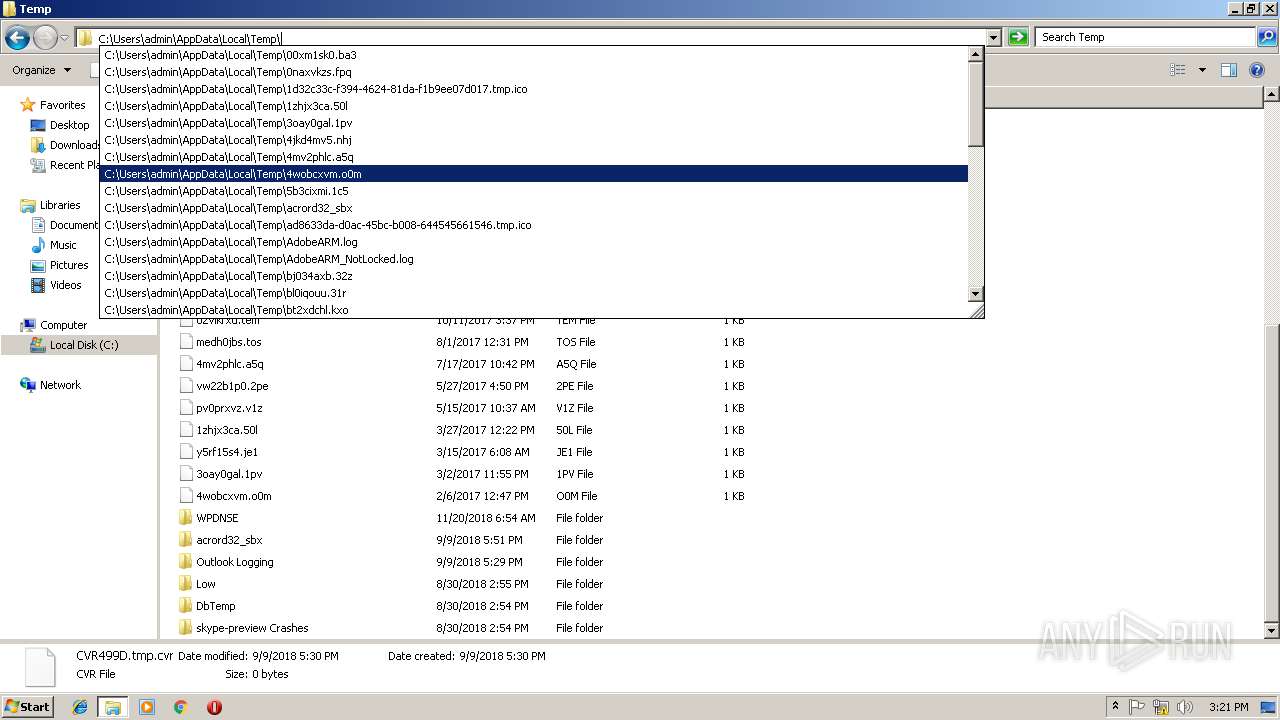
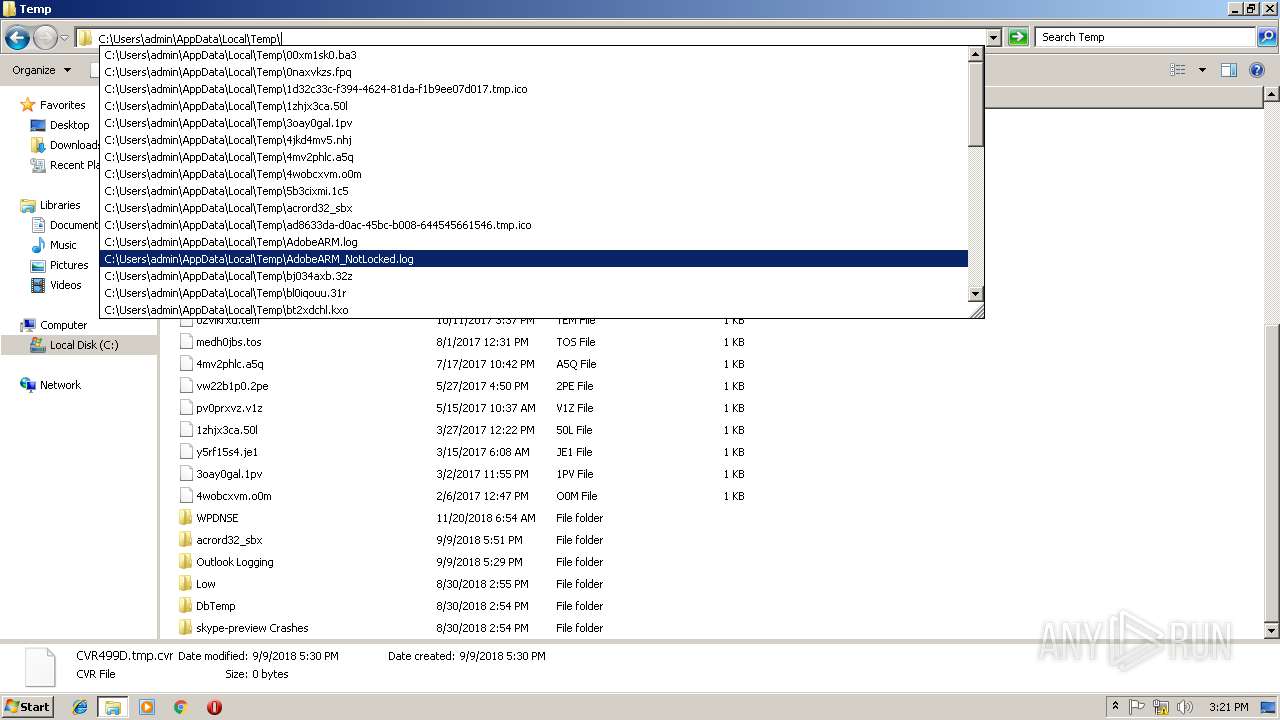
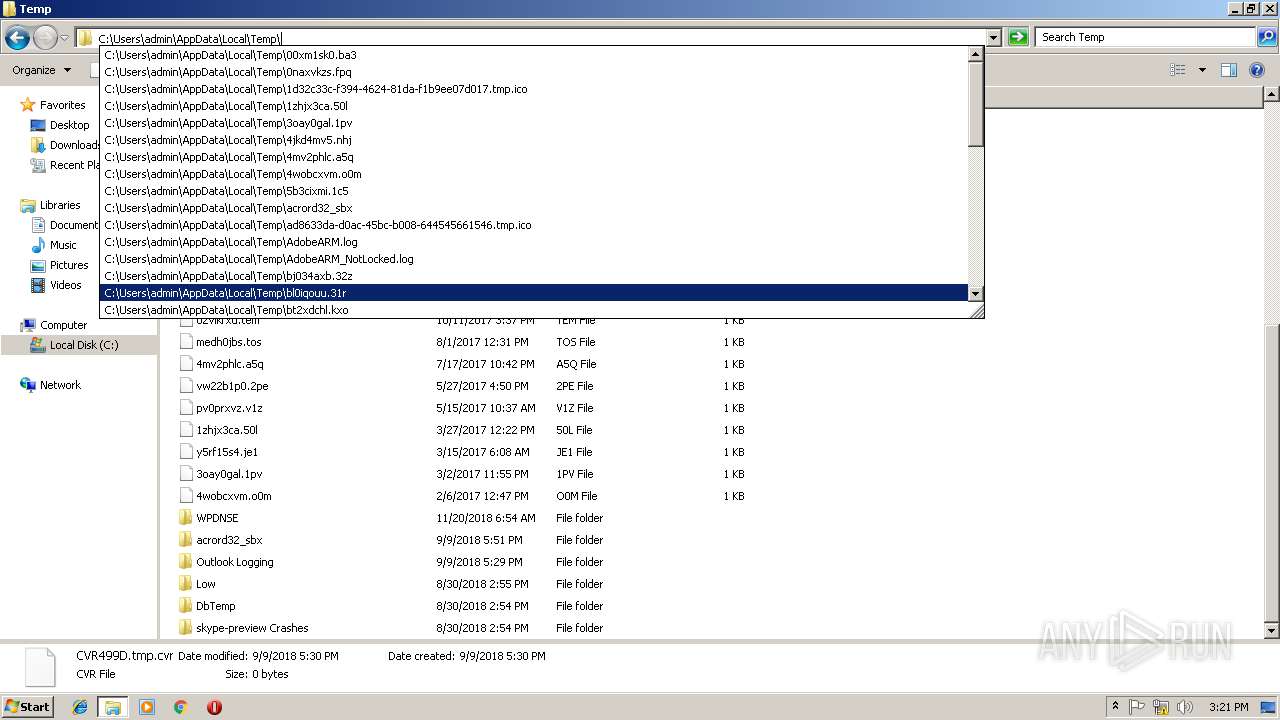
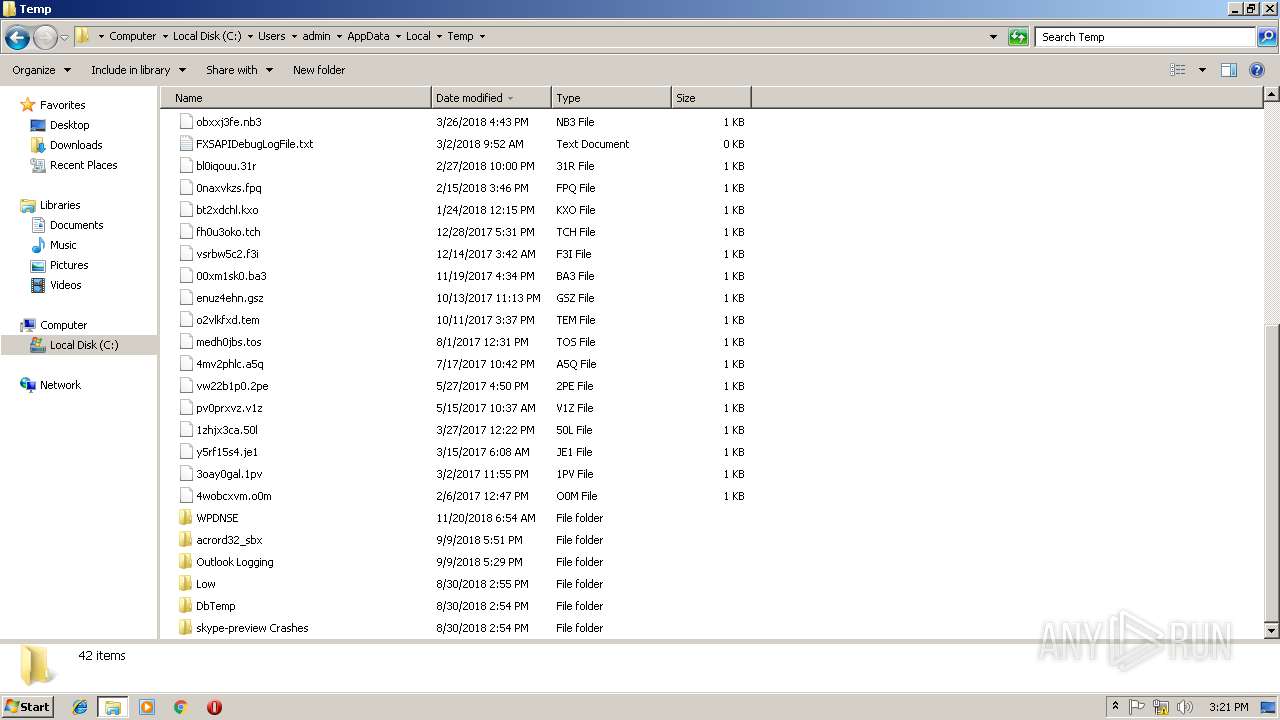
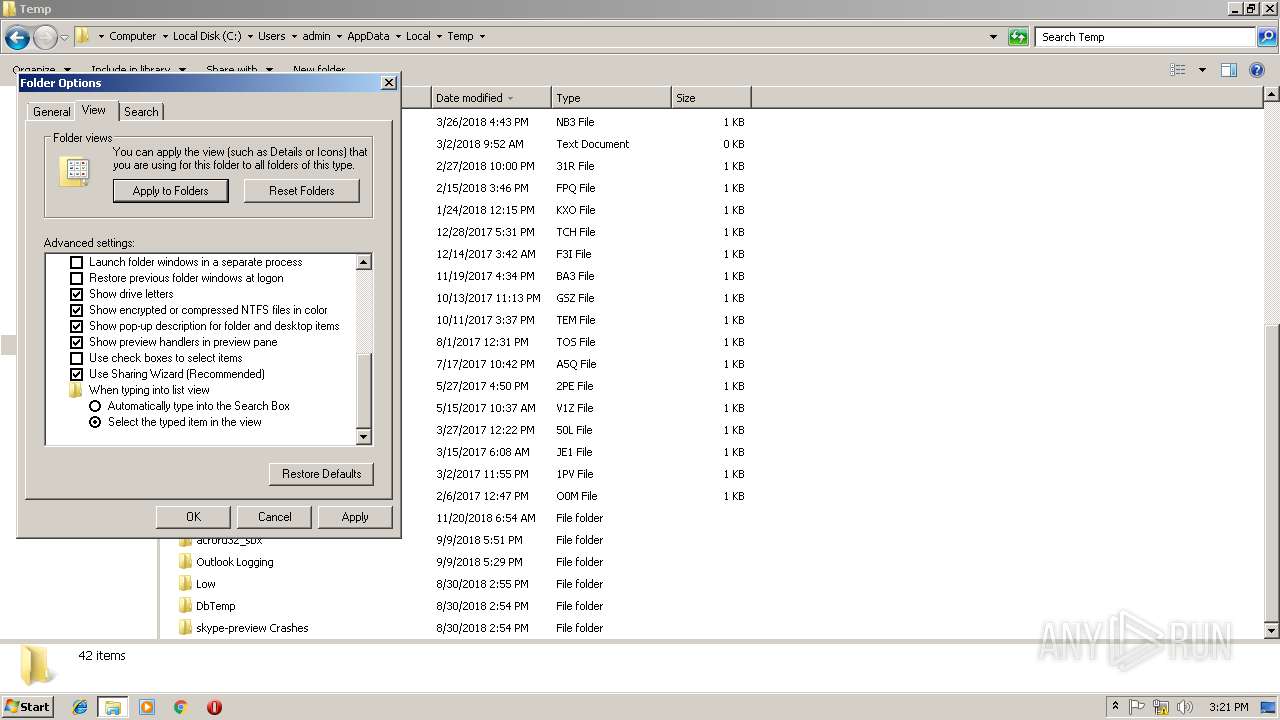
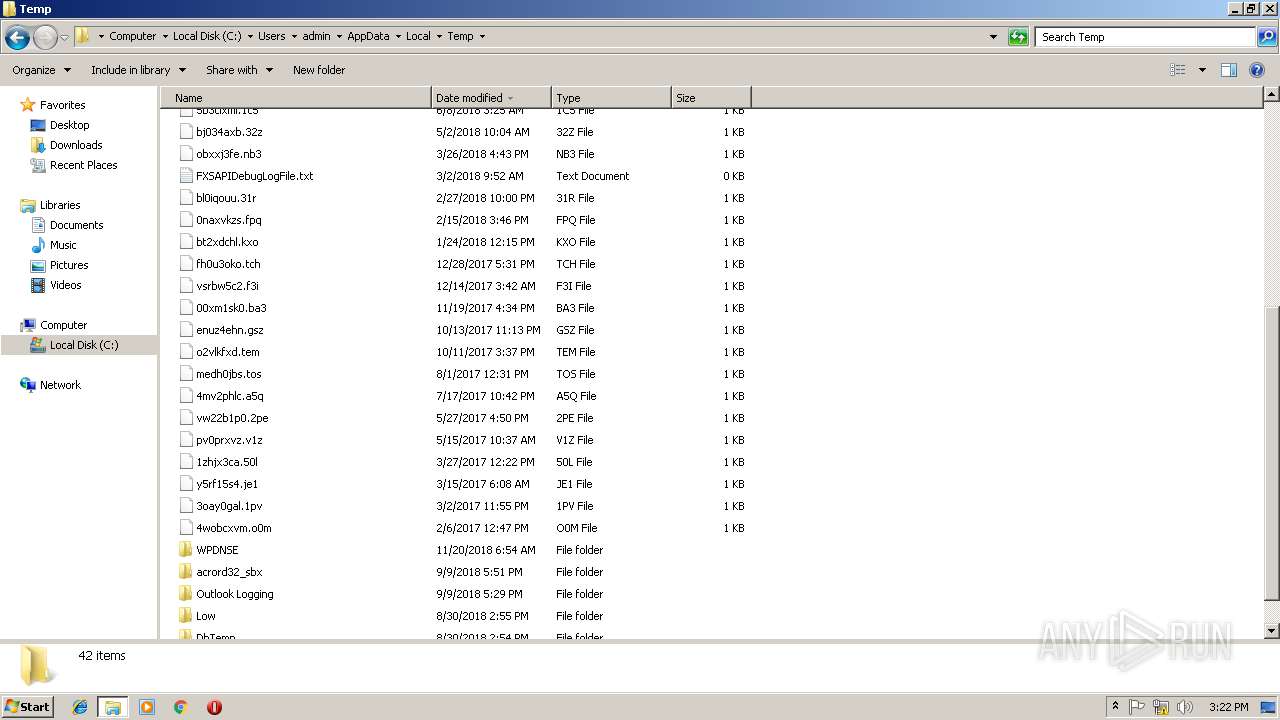
Executable files
25
Suspicious files
0
Text files
2
Unknown types
0
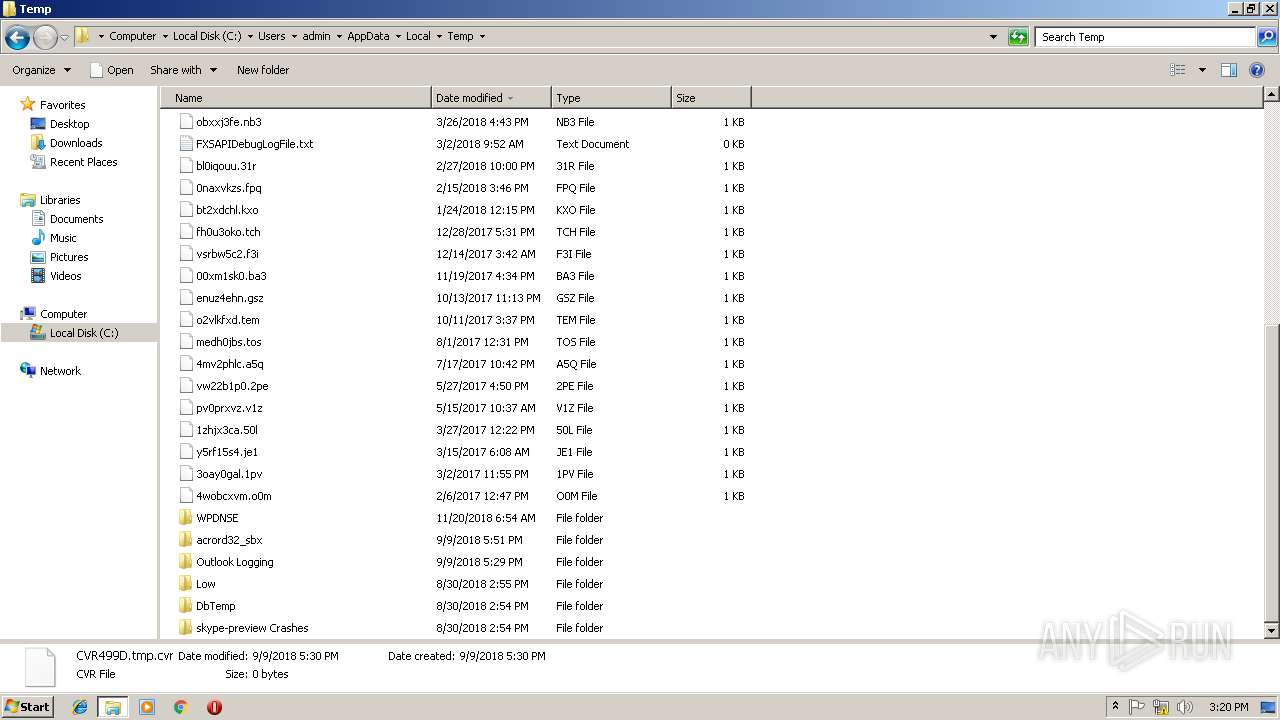
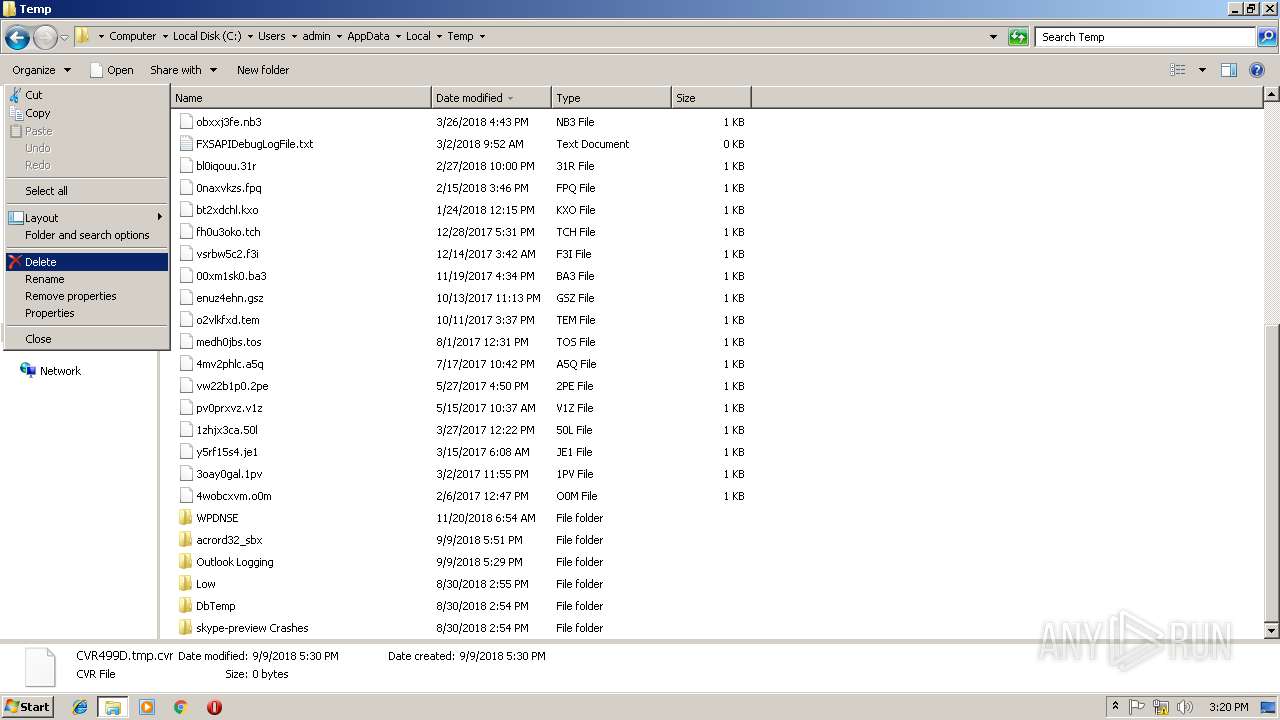
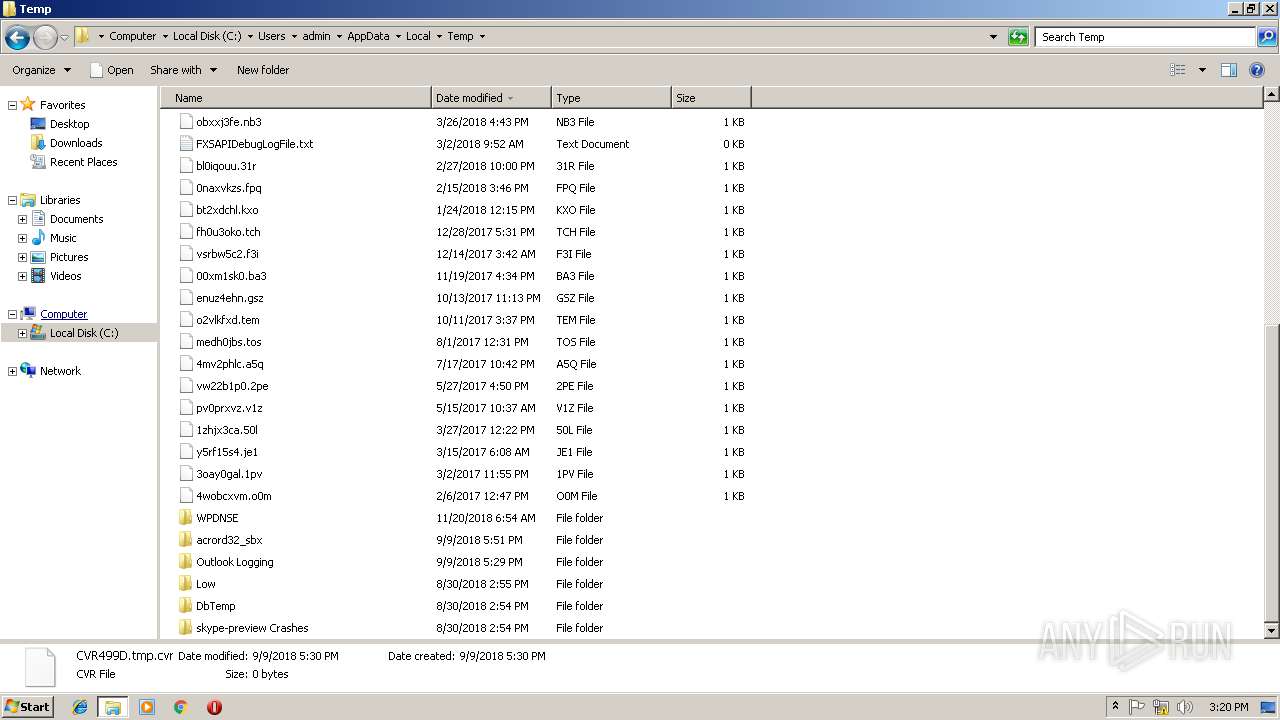
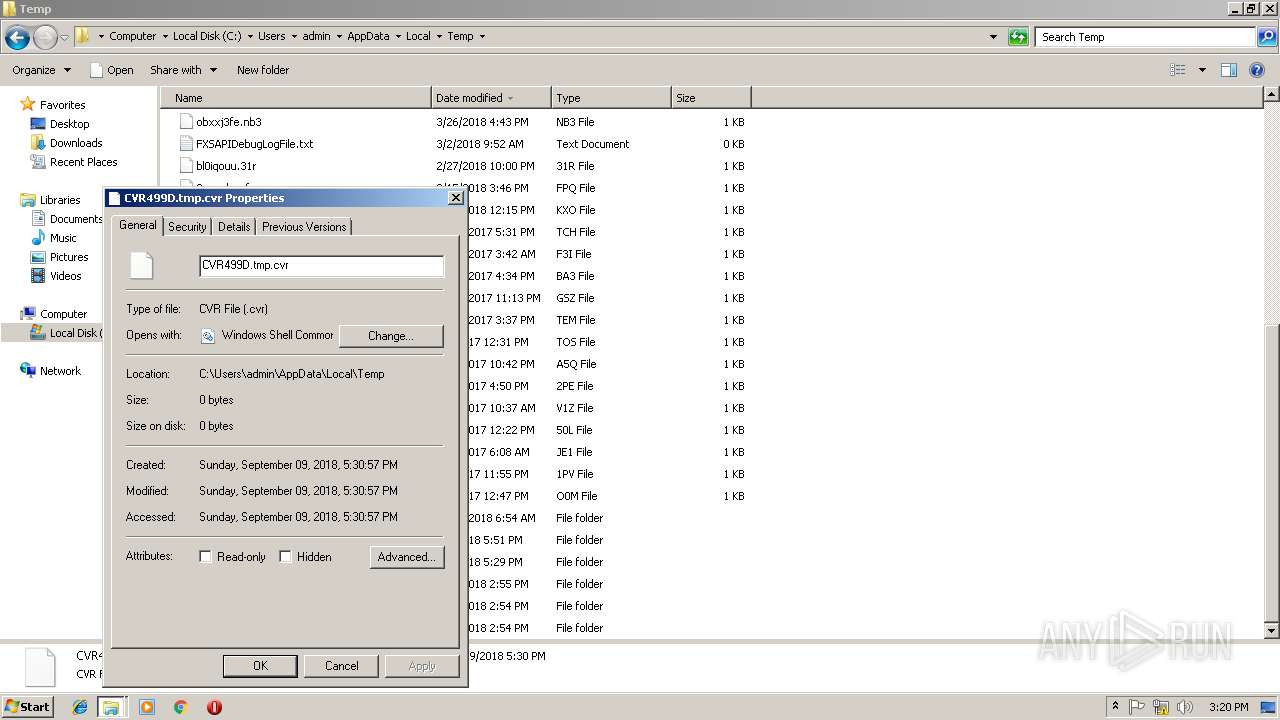
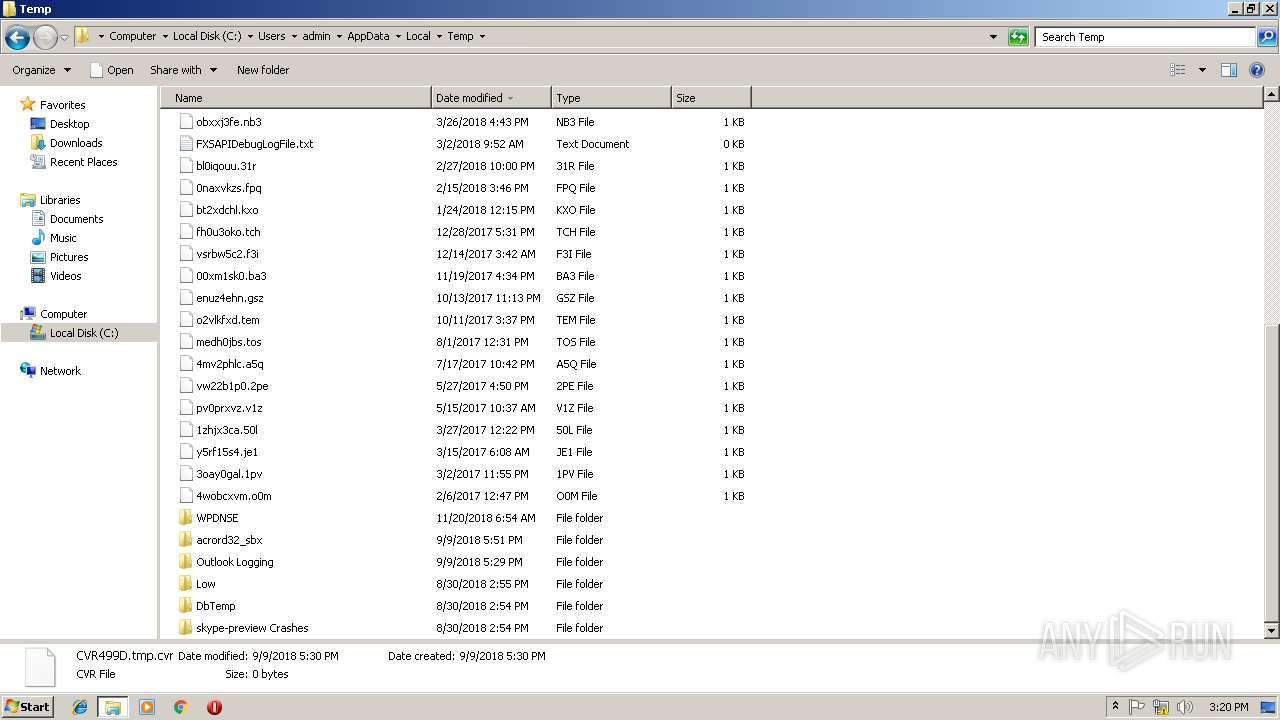
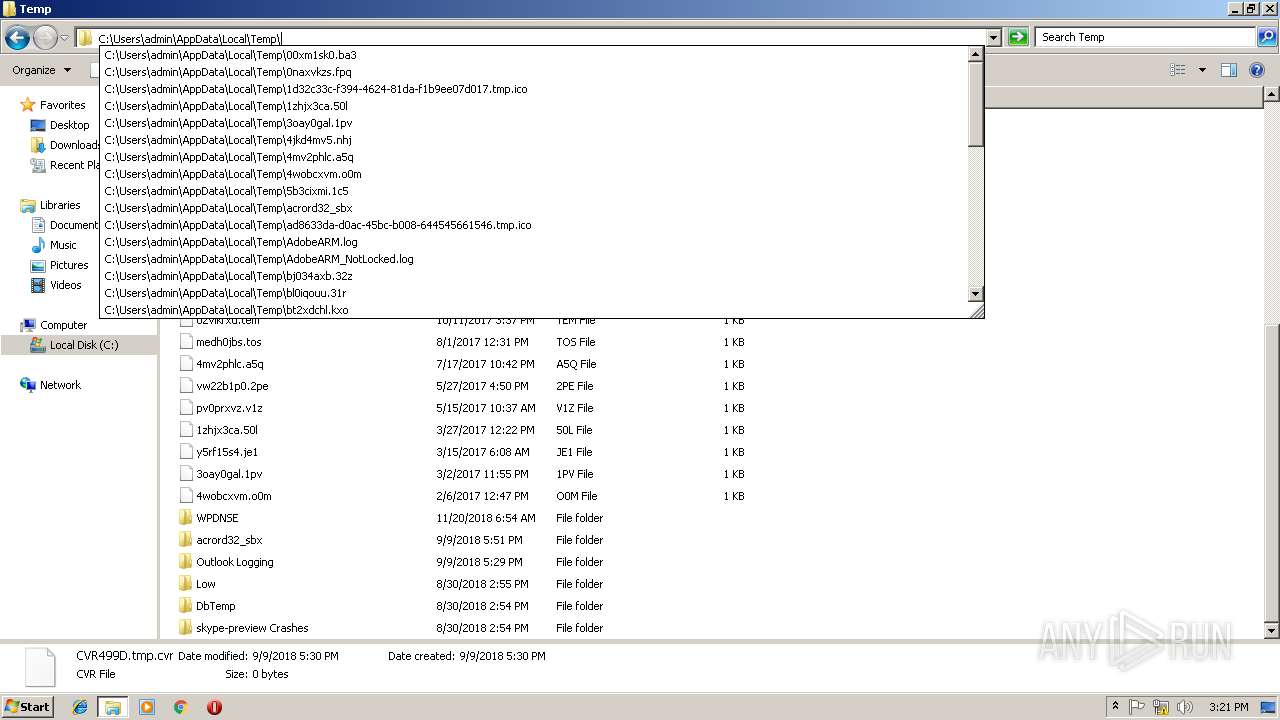
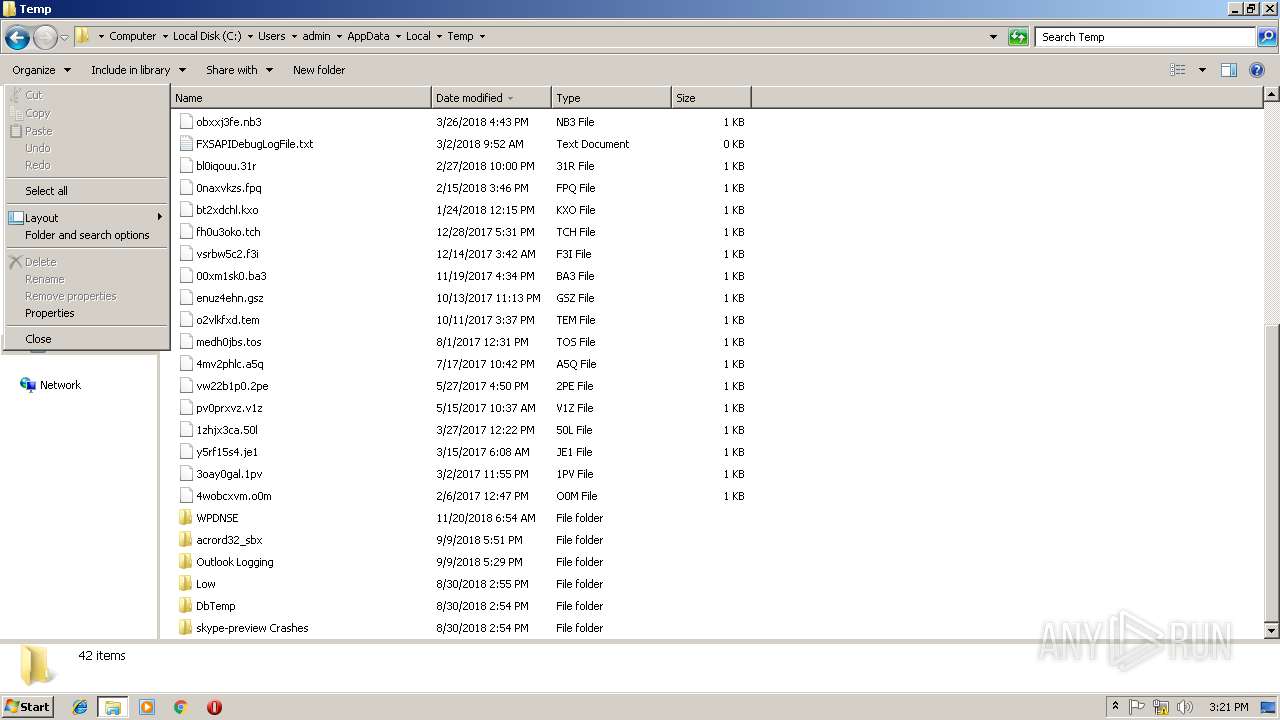
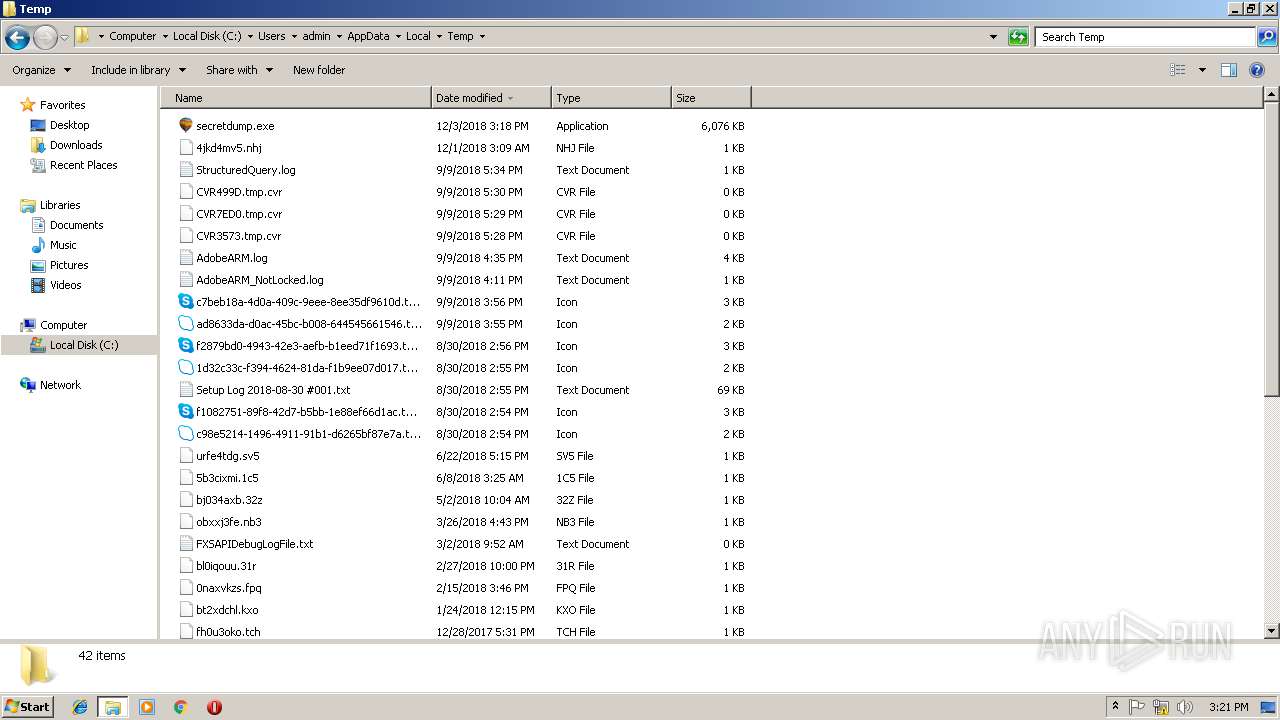
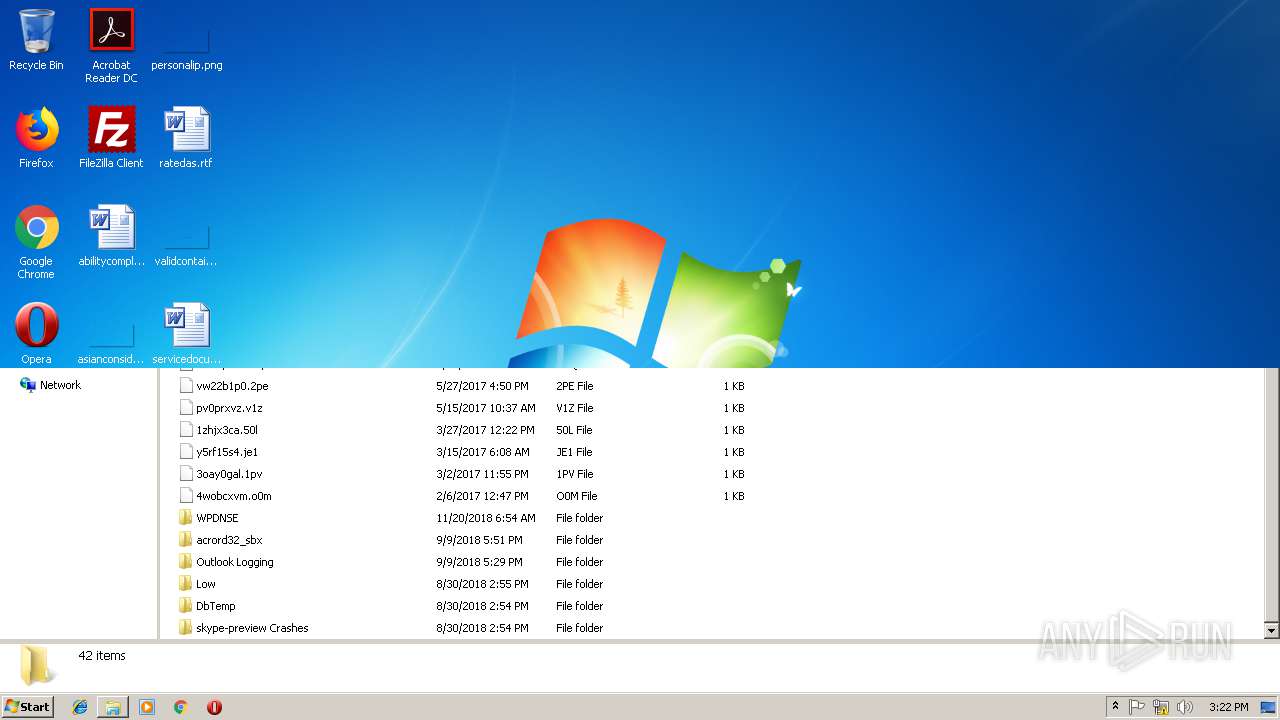
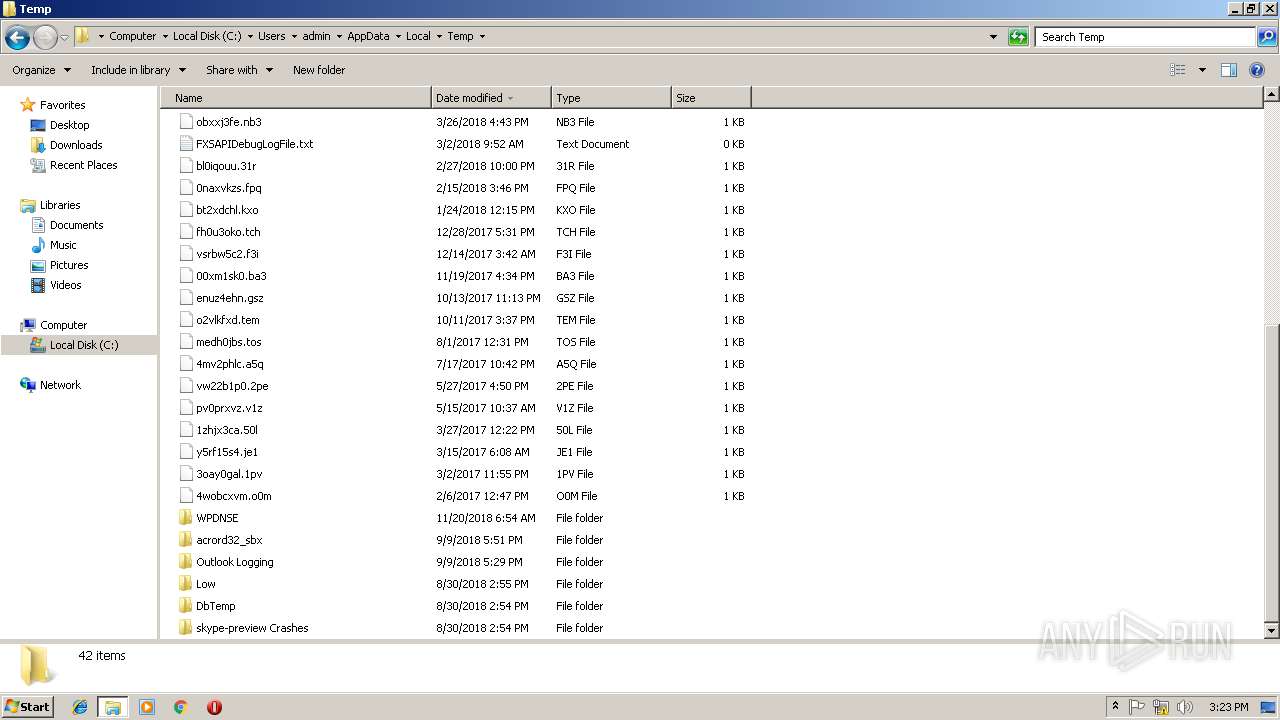
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\Microsoft.VC90.CRT.manifest | xml | |
MD5:BFB93876892CCA8E2AD0021585C34C8B | SHA256:0D060ED7C25159B7B75F16D449963BFD639C15B3C5280BC7897403268C2B9F35 | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\_hashlib.pyd | executable | |
MD5:B1DBD52E5DA083E5B5613A2B4C17A4EF | SHA256:FA57BF3173F2D636984305401C06F1618B8119FEA2C311D1173566EA236FA0C6 | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\Crypto.Util.strxor.pyd | executable | |
MD5:62DCC6B73822F5F0106AAF264BAA8174 | SHA256:D4E63D4A0C9243C076054861274BE232ADEBEF41533EC4CBB8A6FA833903ACE3 | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\_ctypes.pyd | executable | |
MD5:9E6C48EC9508423D0CE6B6E4D4A10D90 | SHA256:B700441351B3A24A1EC392376984D3D95A541EA548C77F0DF55D7AF579EA9C1A | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\_socket.pyd | executable | |
MD5:600DE8A82E2204E88DF27714687F88B9 | SHA256:A24422D519E5A9283A0887D4BE09BE2AC89797886D8F45151CAB5E9FEF8DB1E1 | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\msvcm90.dll | executable | |
MD5:D34A527493F39AF4491B3E909DC697CA | SHA256:7A74DA389FBD10A710C294C2E914DC6F18E05F028F07958A2FA53AC44F0E4B90 | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\bz2.pyd | executable | |
MD5:58C57A662CDE57FEA311444CC8DADC24 | SHA256:69B4EC17DE1368A9EA62313954629E1ACE3F414A7EAEDCEDBFC79B110CADBAAC | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\_ssl.pyd | executable | |
MD5:9B59BE1FA8427368C4E0E763F578D74C | SHA256:4BA198E7F53A37B3A825FF2CE4D3E6CA00AD96E62852F0127A46C57A9A4A3026 | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\pyexpat.pyd | executable | |
MD5:C79A904C852347565950E437335BE107 | SHA256:5FB1D9F49A61BF1641EB097298B635E42A9AEF9755C9F22CA09B812B94614AEF | |||
| 3736 | secretdump.exe | C:\Users\admin\AppData\Local\Temp\_MEI37362\msvcr90.dll | executable | |
MD5:CDBE9690CF2B8409FACAD94FAC9479C9 | SHA256:8E7FE1A1F3550C479FFD86A77BC9D10686D47F8727025BB891D8F4F0259354C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report