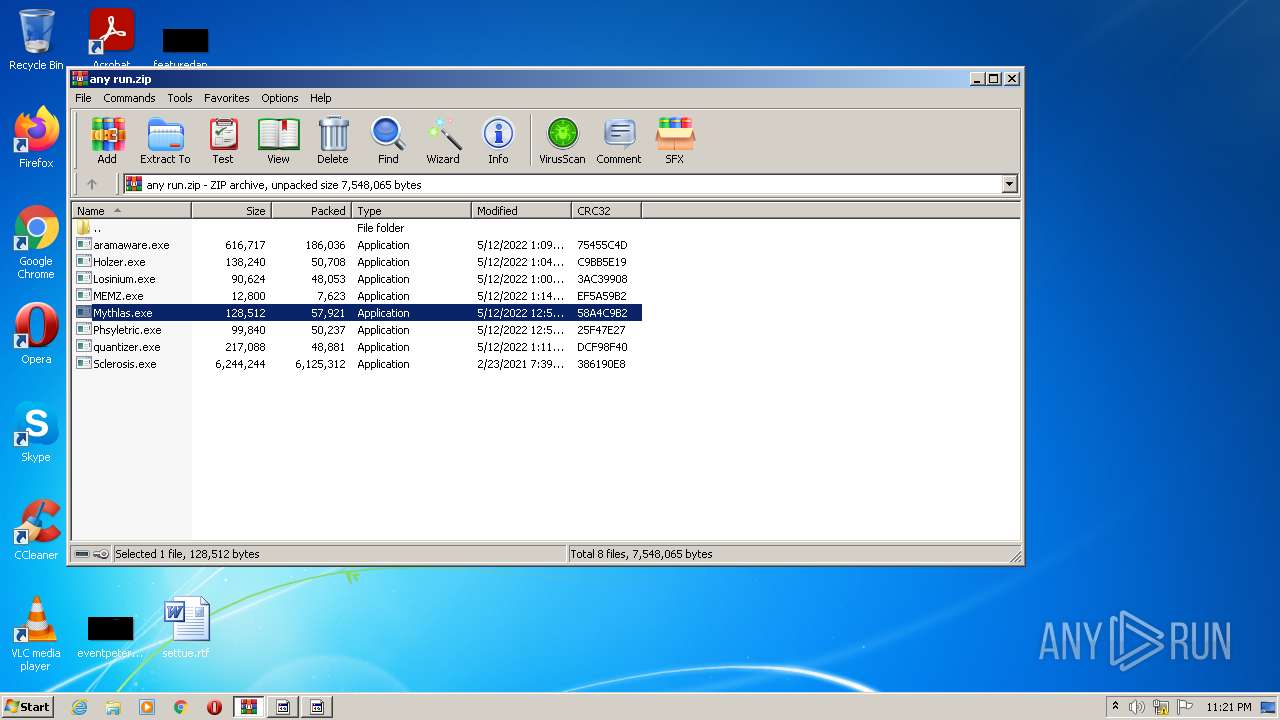
| File name: | any run.zip |
| Full analysis: | https://app.any.run/tasks/74d036fb-32c3-4448-9587-016eaa377ea4 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 22:21:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D5580C9560F5FF87A09FC6100654D4E4 |
| SHA1: | 5F42337E5F30A7D73546BFBB399453D2328E5A8D |
| SHA256: | C33C4CC5639886BFF516F52872C773EC9D7D15B6CAAE3530753A0458B334C60B |
| SSDEEP: | 196608:XH/djrRJhxwSAGm7eGfp4mFWjsa0e1y8ky+q:XVvfH2lpbafT+q |
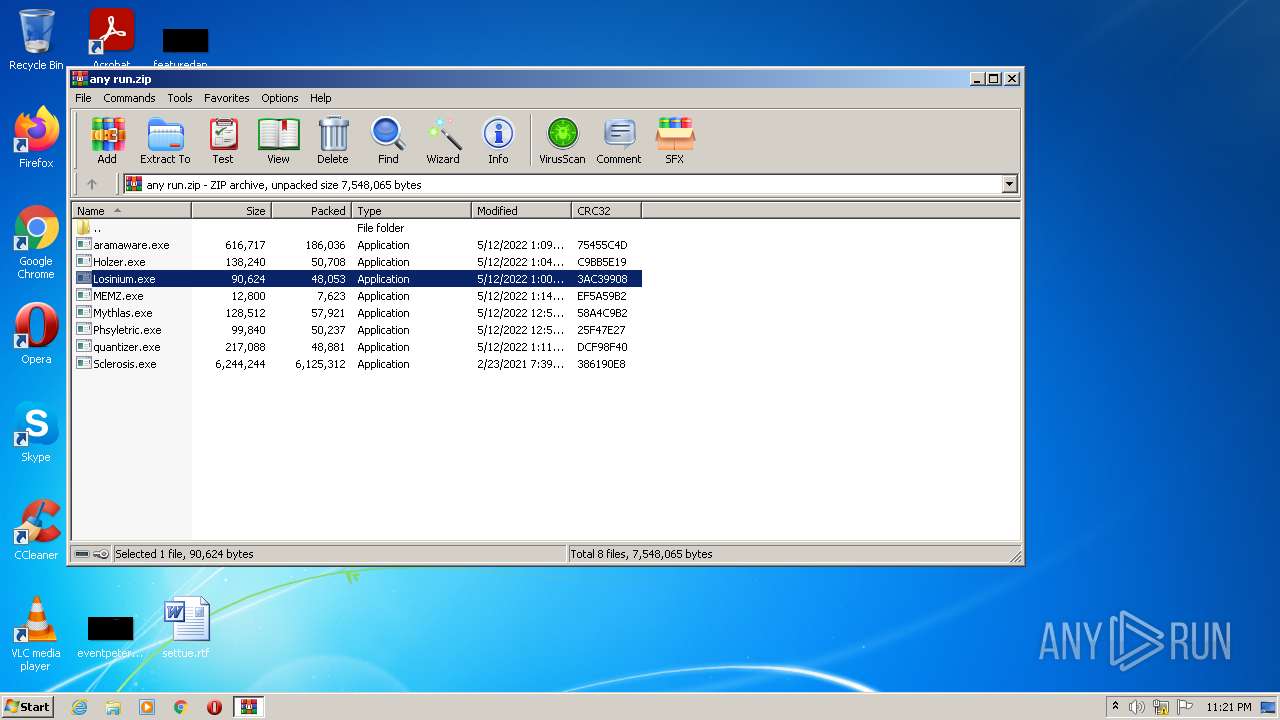
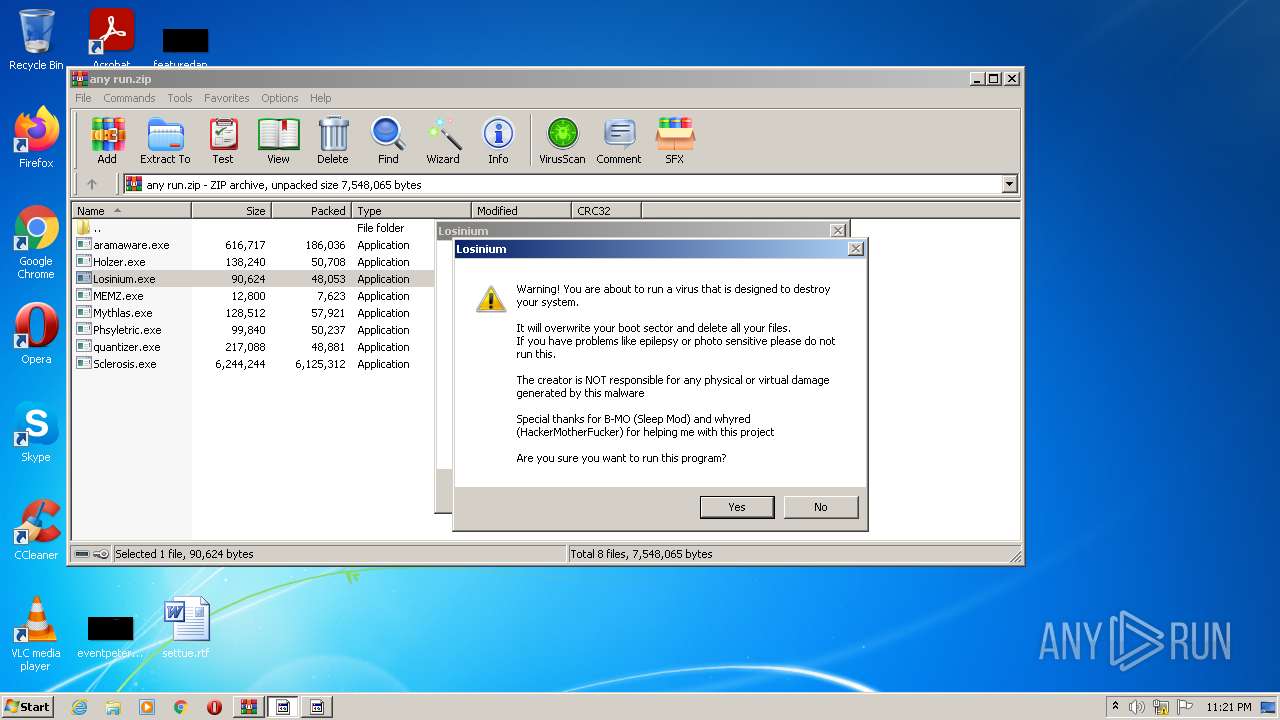
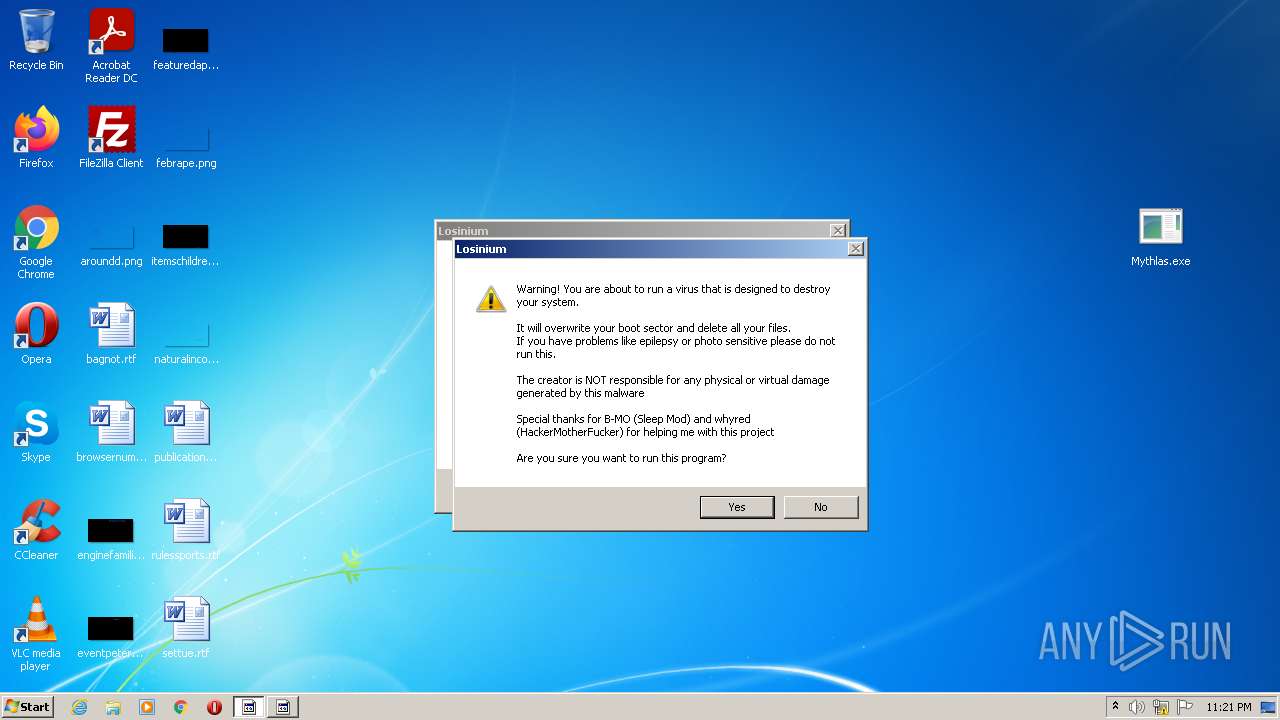
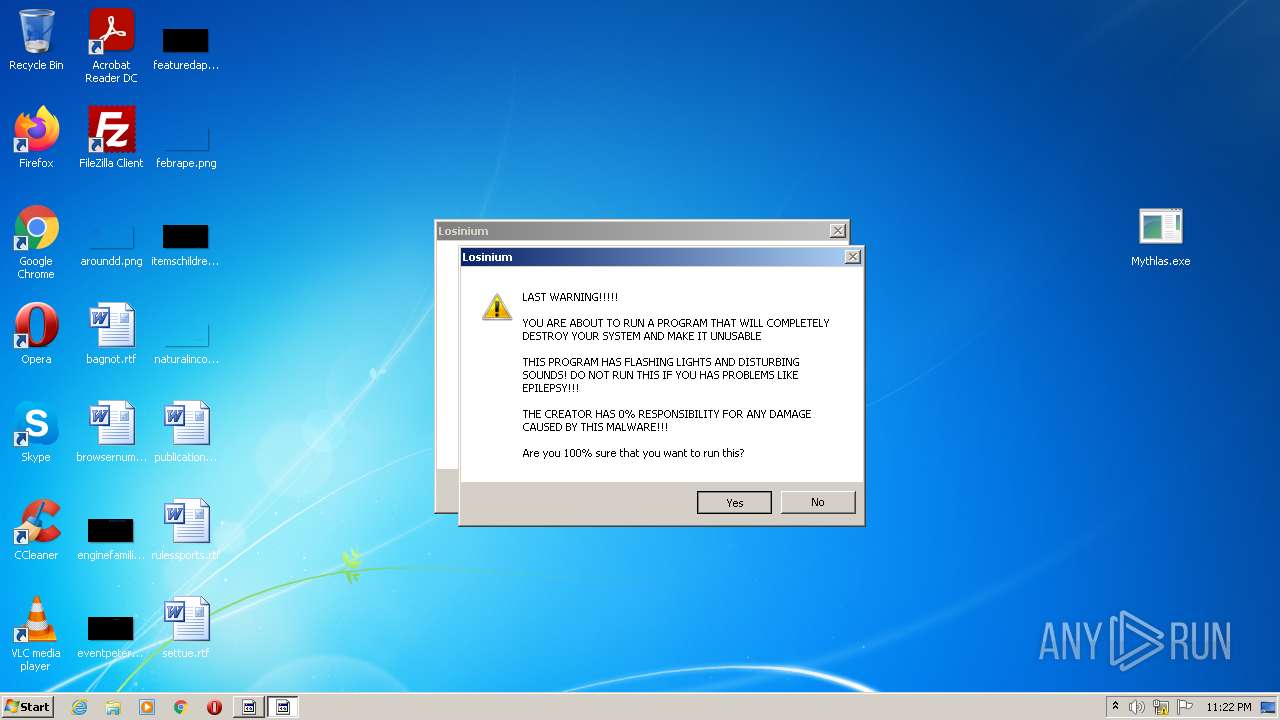
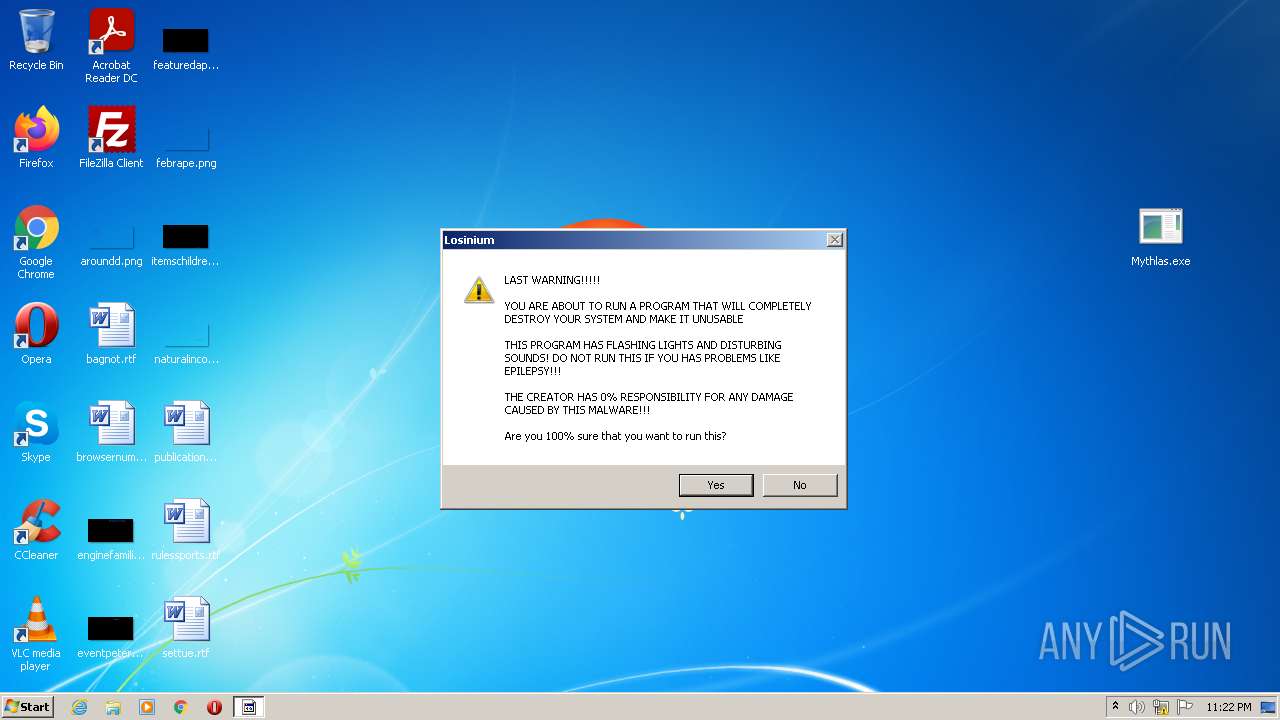
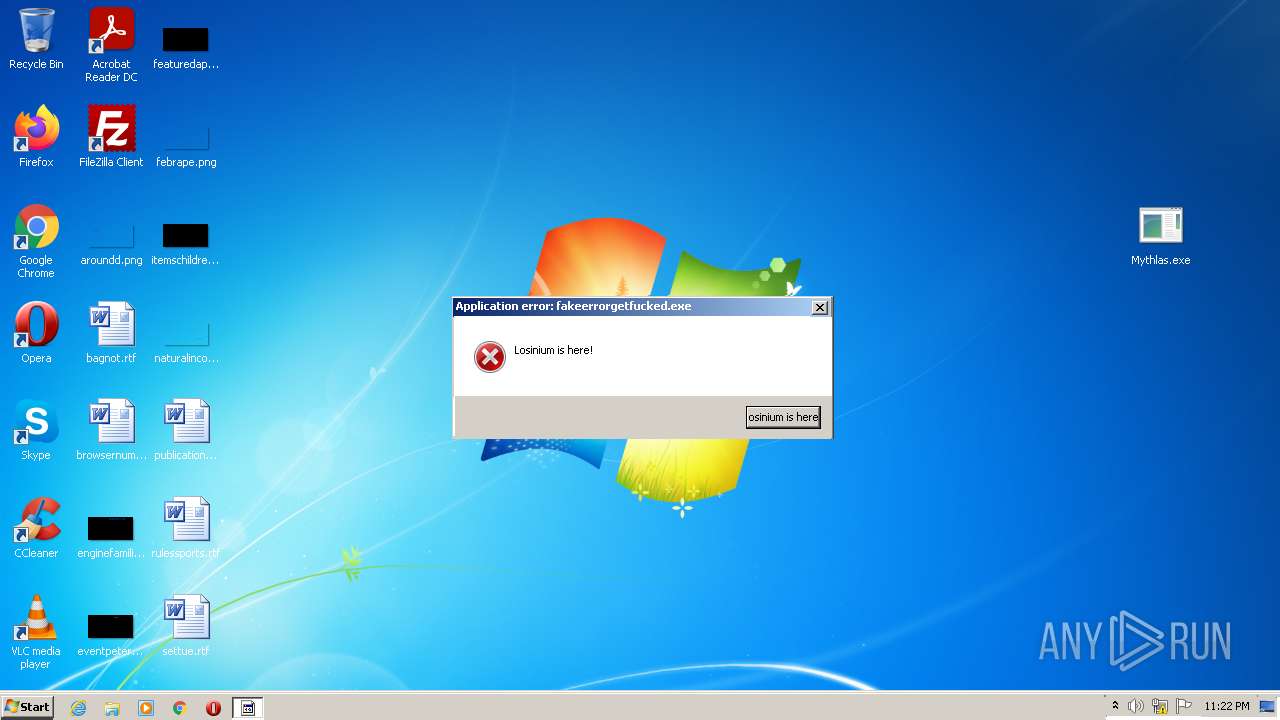
MALICIOUS
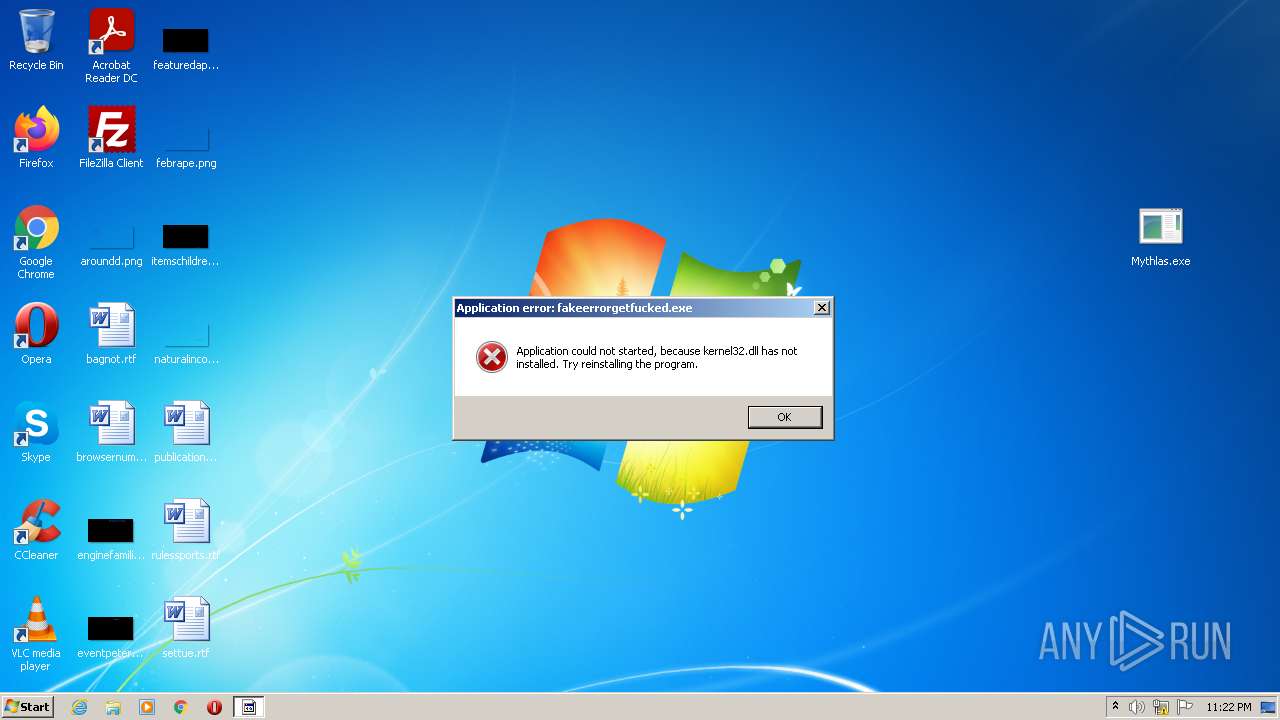
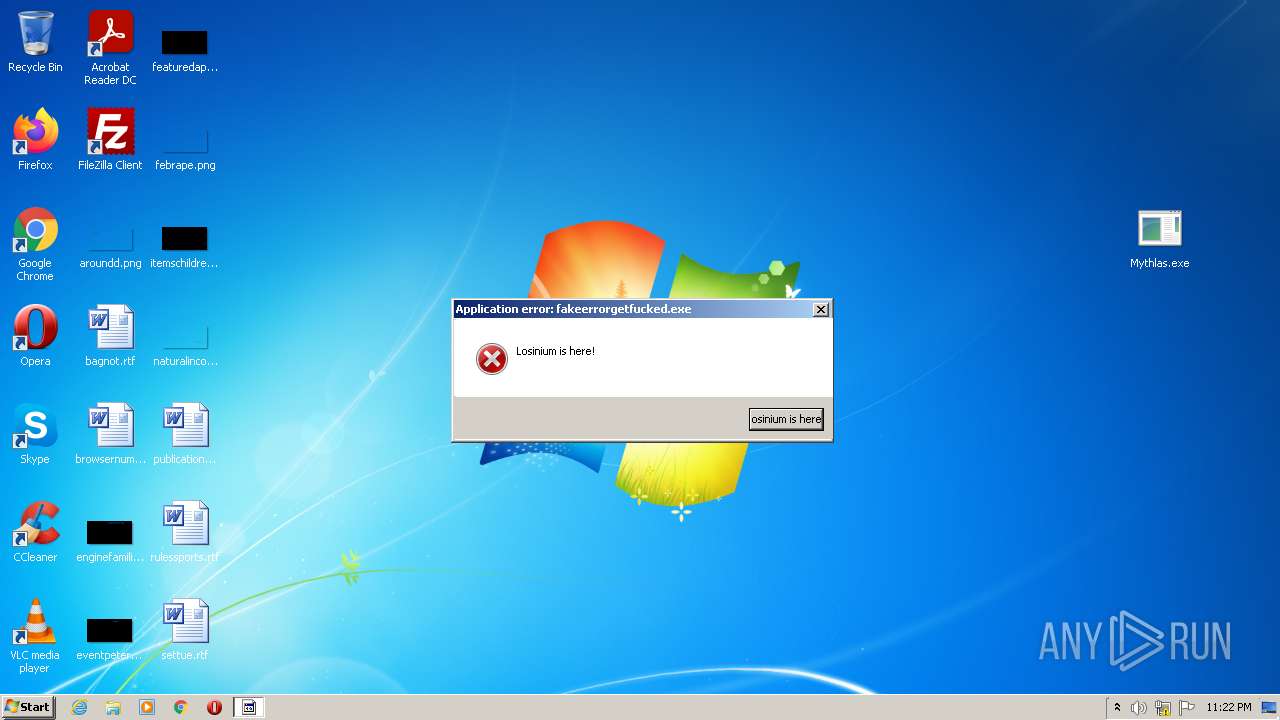
Application was dropped or rewritten from another process
- Losinium.exe (PID: 2332)
- Losinium.exe (PID: 4052)
- Losinium.exe (PID: 2848)
- Losinium.exe (PID: 2860)
- Mythlas.exe (PID: 2340)
Drops executable file immediately after starts
- WinRAR.exe (PID: 3068)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3068)
- Losinium.exe (PID: 2848)
- Losinium.exe (PID: 2860)
- Mythlas.exe (PID: 2340)
Reads the computer name
- WinRAR.exe (PID: 3068)
- Losinium.exe (PID: 2860)
- Mythlas.exe (PID: 2340)
- Losinium.exe (PID: 2848)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3068)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3068)
INFO
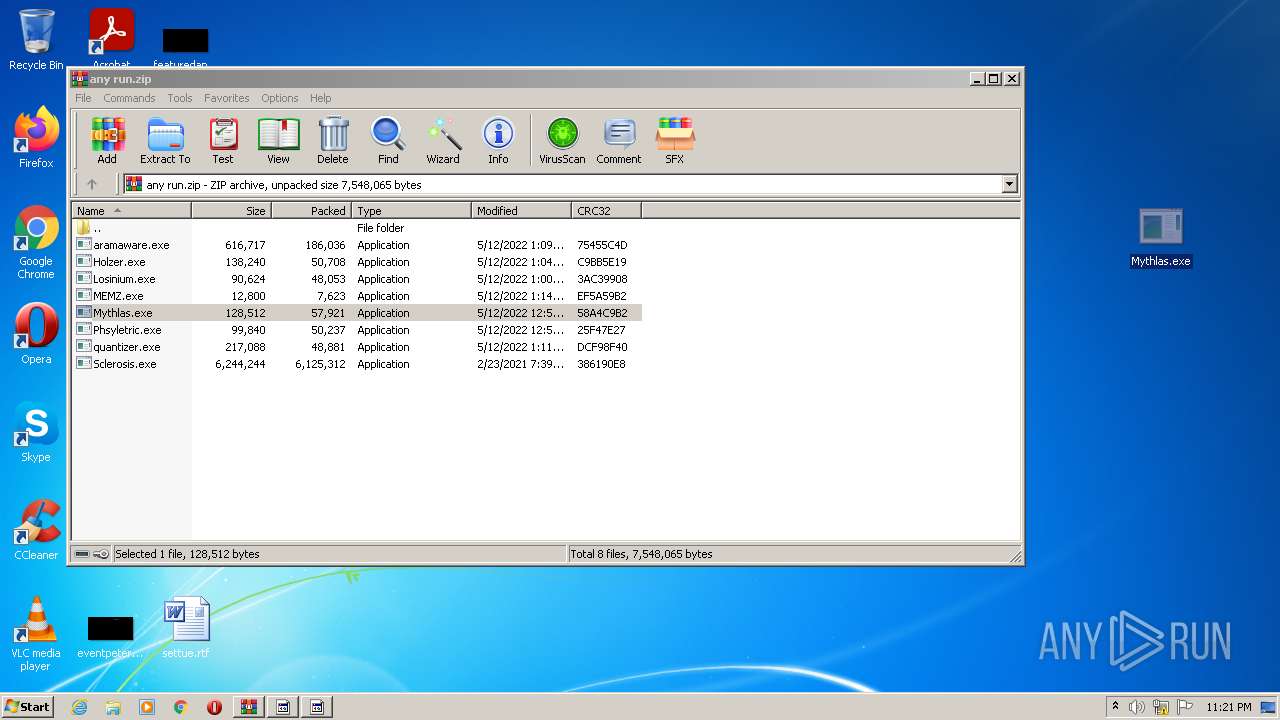
Manual execution by user
- Mythlas.exe (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
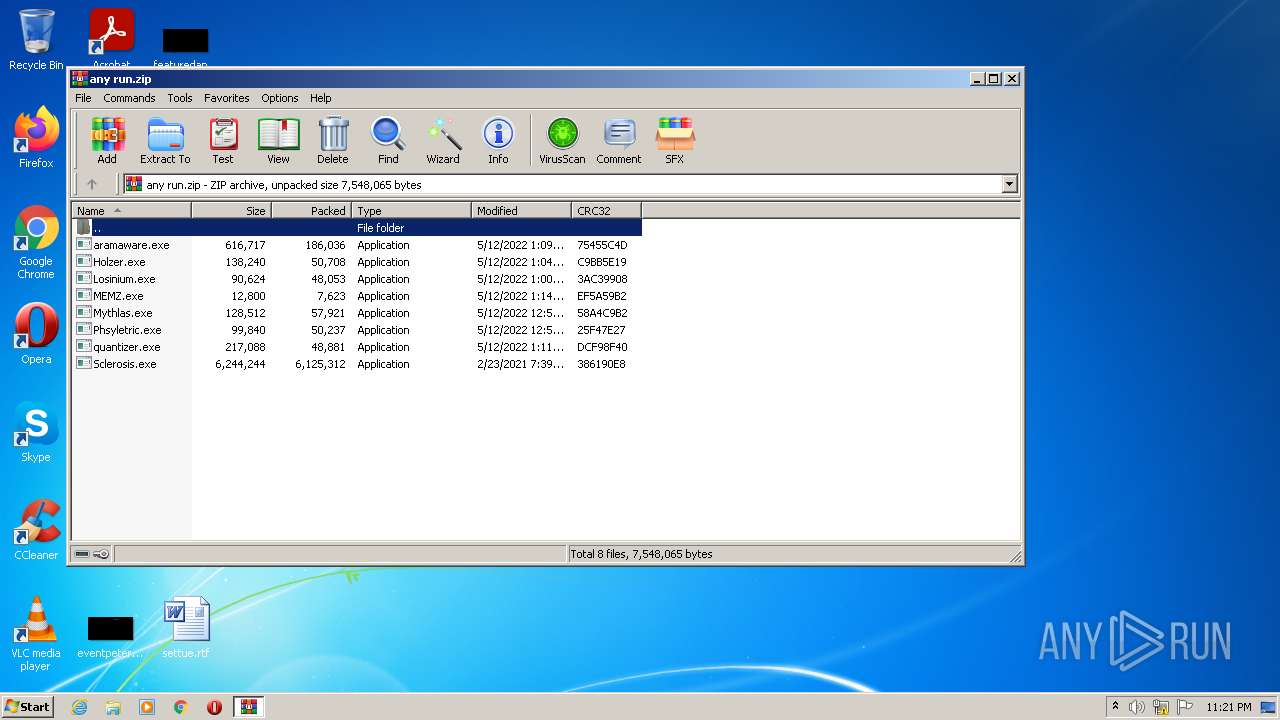
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | aramaware.exe |
|---|---|
| ZipUncompressedSize: | 616717 |
| ZipCompressedSize: | 186036 |
| ZipCRC: | 0x75455c4d |
| ZipModifyDate: | 2022:05:12 13:09:21 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
46
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2332 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\Losinium.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\Losinium.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\Desktop\Mythlas.exe" | C:\Users\admin\Desktop\Mythlas.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\Losinium.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\Losinium.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2860 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\Losinium.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\Losinium.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3068 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\any run.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4052 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\Losinium.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\Losinium.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
1 547
Read events
1 518
Write events
29
Delete events
0
Modification events
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\any run.zip | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
17
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\Sclerosis.exe | executable | |
MD5:— | SHA256:— | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\Losinium.exe | executable | |
MD5:3FAD30EF9BBB47488E86DEFA0F81ACAB | SHA256:69D2AD4DDD61C4B2E6FF350FD87B61DB5DE36218626812E69C4289DE5782CD0C | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\Mythlas.exe | executable | |
MD5:1BCCDB1CBBDB299F4053DBAB4236DADC | SHA256:E65C793A31137AE75A6F30AE2933BD7CAE74FCD4330B6C8770C14466BC3A878F | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\quantizer.exe | executable | |
MD5:1458480CF8803569195F934D47AC7481 | SHA256:68D528F9AC891E920449188198A233B71B2860838AF4FB970B9966F941CE82CA | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44292\Phsyletric.exe | executable | |
MD5:4DB23CF50F64A83759DB9DF6AD222D65 | SHA256:465F8BF12FE8FC53C9EF45E498B5F9D95B783C61096147BBC09182F6D19DD129 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\MEMZ.exe | executable | |
MD5:A7BCF7EA8E9F3F36EBFB85B823E39D91 | SHA256:3FF64F10603F0330FA2386FF99471CA789391ACE969BD0EC1C1B8CE1B4A6DB42 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\Holzer.exe | executable | |
MD5:C971C68B4E58CCC82802B21AE8488BC7 | SHA256:CEDE0B15D88C20BC750B516858F8BF31EE472F6CBD01640840890736C4333CCE | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\aramaware.exe | executable | |
MD5:3ACDCDEE17825753CACC8DFD414E57D3 | SHA256:82BB1809904786AFC0C13ABEC22A48B320581EC913BF5BBDDDD02FCE05EF77E8 | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\Losinium.exe | executable | |
MD5:3FAD30EF9BBB47488E86DEFA0F81ACAB | SHA256:69D2AD4DDD61C4B2E6FF350FD87B61DB5DE36218626812E69C4289DE5782CD0C | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3068.44344\Mythlas.exe | executable | |
MD5:1BCCDB1CBBDB299F4053DBAB4236DADC | SHA256:E65C793A31137AE75A6F30AE2933BD7CAE74FCD4330B6C8770C14466BC3A878F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report