| File name: | 7958c2452a24ad4959d1359caf51deb41b798d30 |
| Full analysis: | https://app.any.run/tasks/c23935f2-6ad6-4c8b-bd22-7f1a6f1848c4 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 12:11:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5700AD9482964067898B120D523A438B |
| SHA1: | 7958C2452A24AD4959D1359CAF51DEB41B798D30 |
| SHA256: | C336262B2EFEF40616C20EFAF4E996F12FDB0D3B3A966F88A2496504B995C18A |
| SSDEEP: | 1536:jG6Rx3EQR3Mp5UXir1UBbaWzSVvplvCk+mhdIyOHrgZJJgafAMkYEImwC4Y:jGU359Mp6w1aazRDKuOafbk9ImwC4Y |
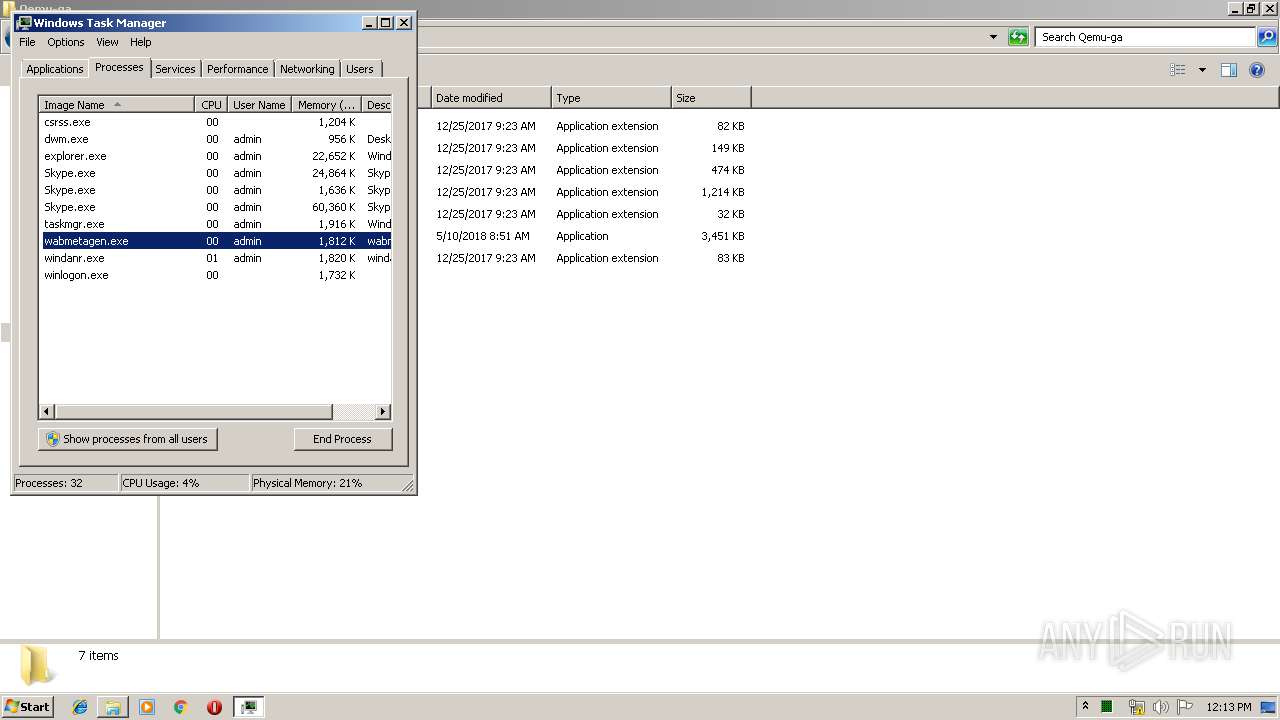
MALICIOUS
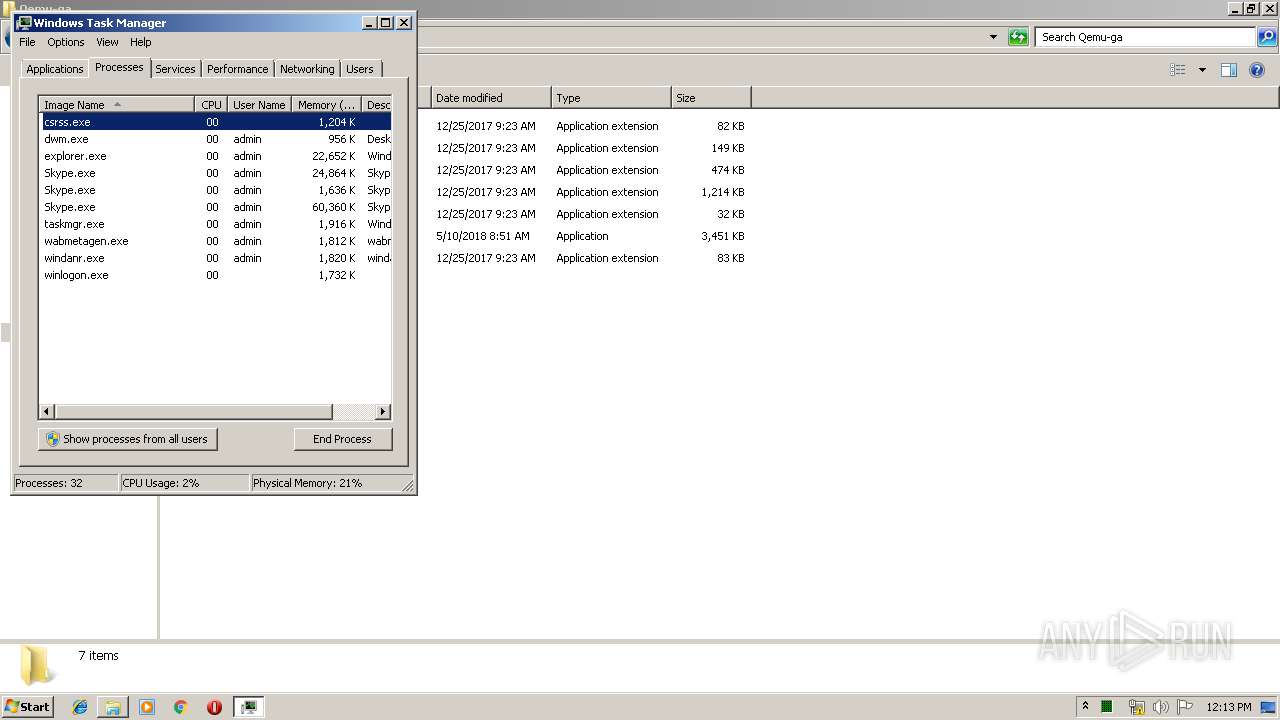
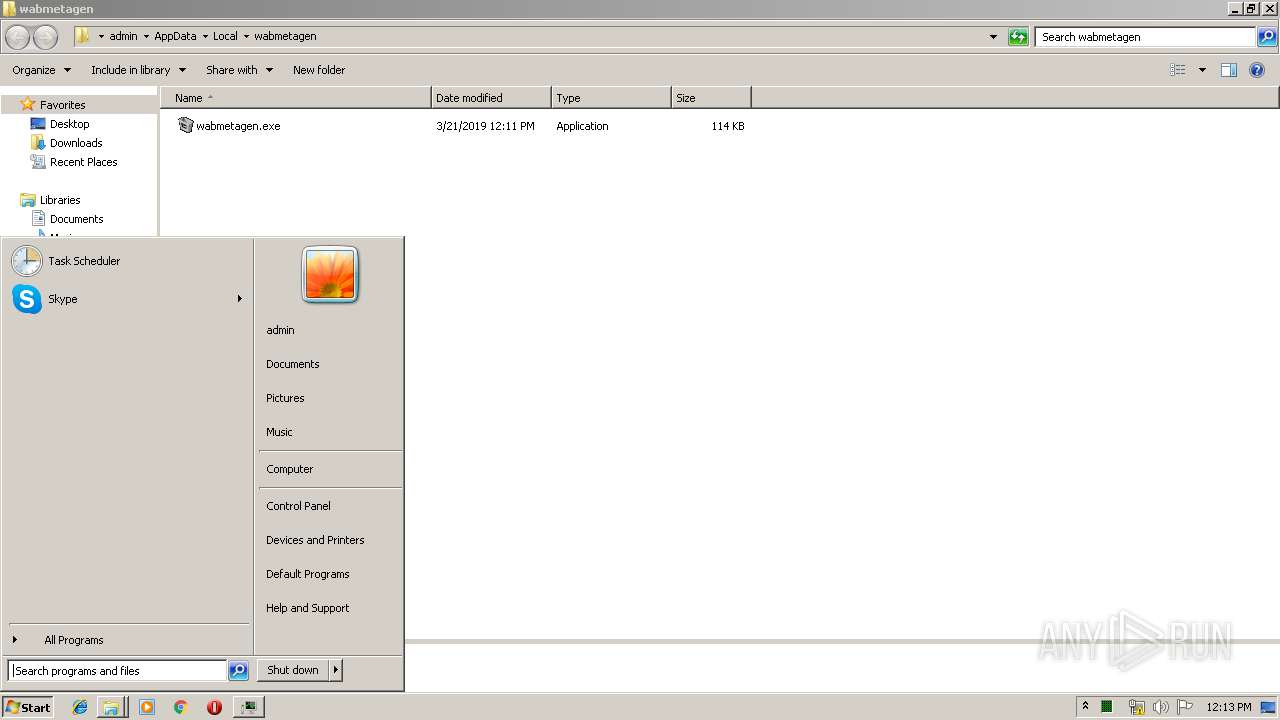
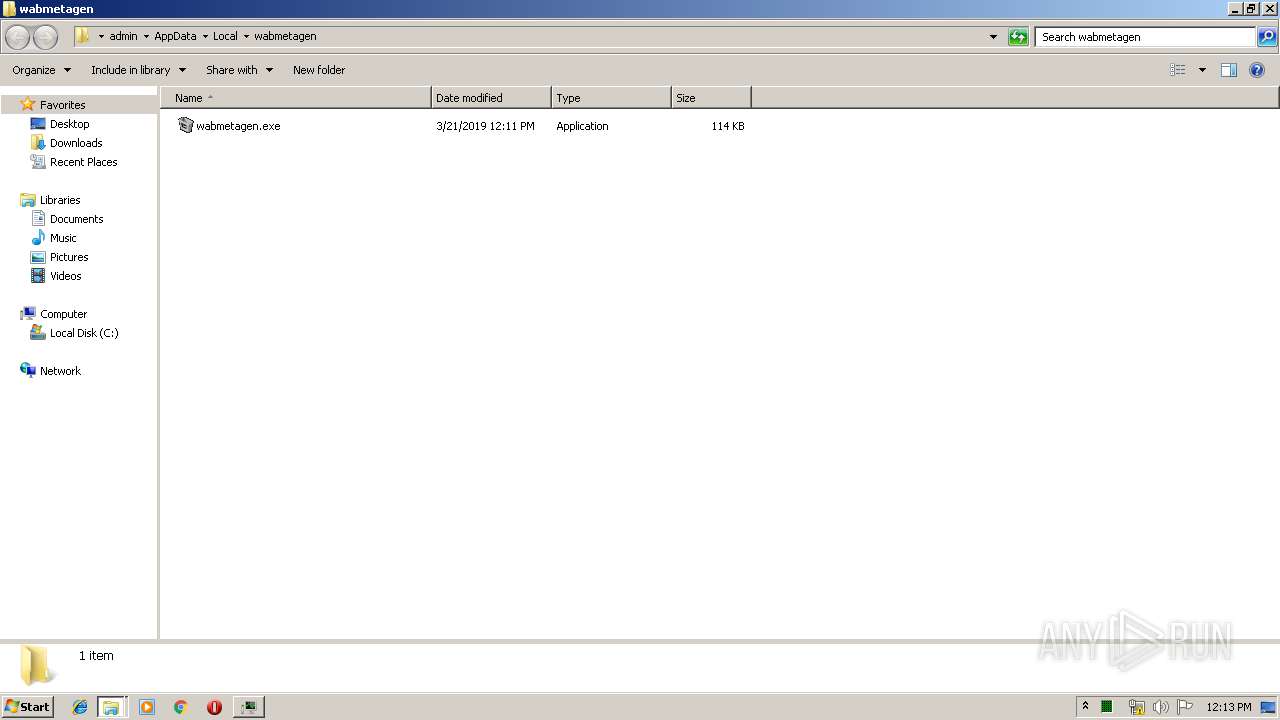
Emotet process was detected
- wabmetagen.exe (PID: 612)
EMOTET was detected
- wabmetagen.exe (PID: 1012)
Connects to CnC server
- wabmetagen.exe (PID: 1012)
Changes the autorun value in the registry
- reg.exe (PID: 2752)
- wabmetagen.exe (PID: 1012)
SUSPICIOUS
Starts itself from another location
- 7958c2452a24ad4959d1359caf51deb41b798d30.exe (PID: 2836)
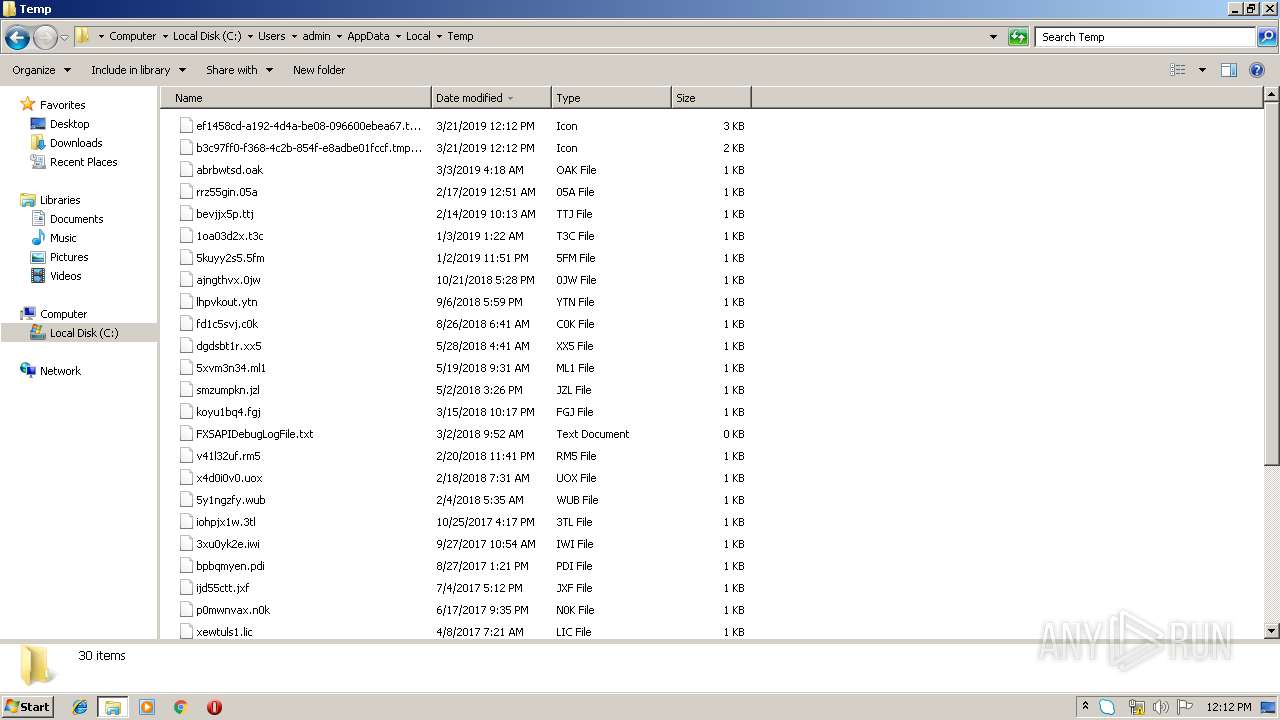
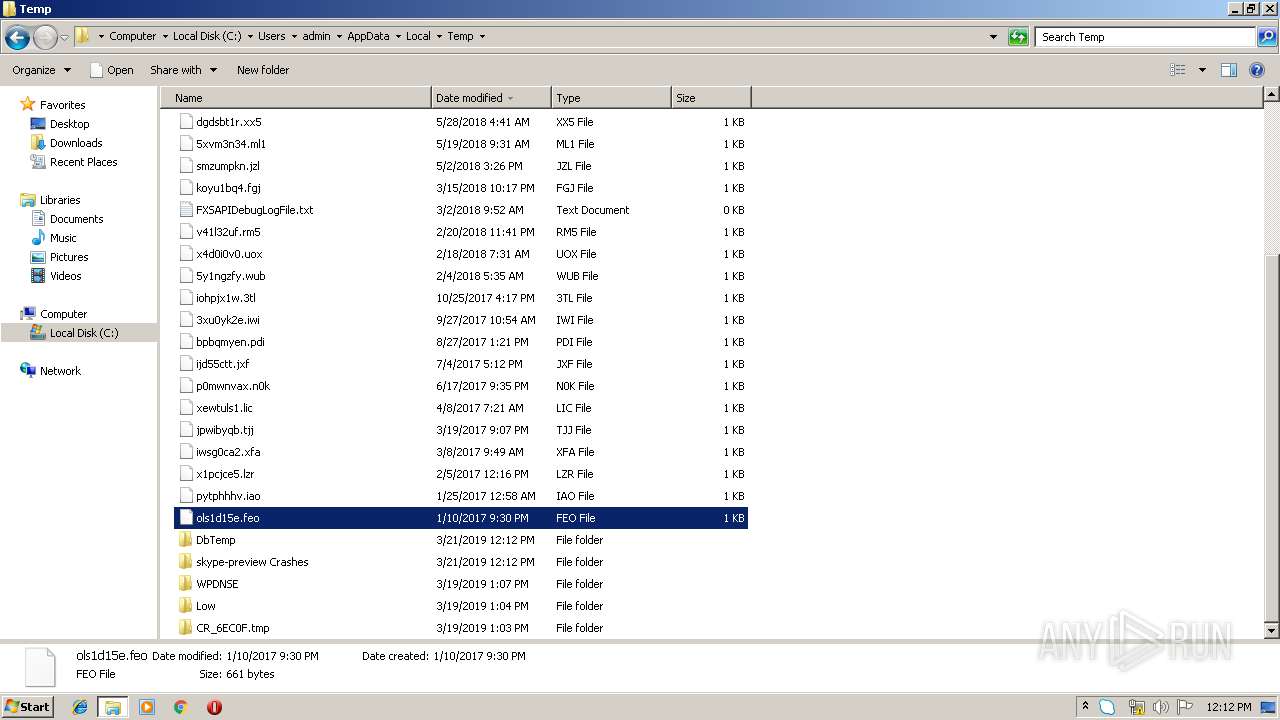
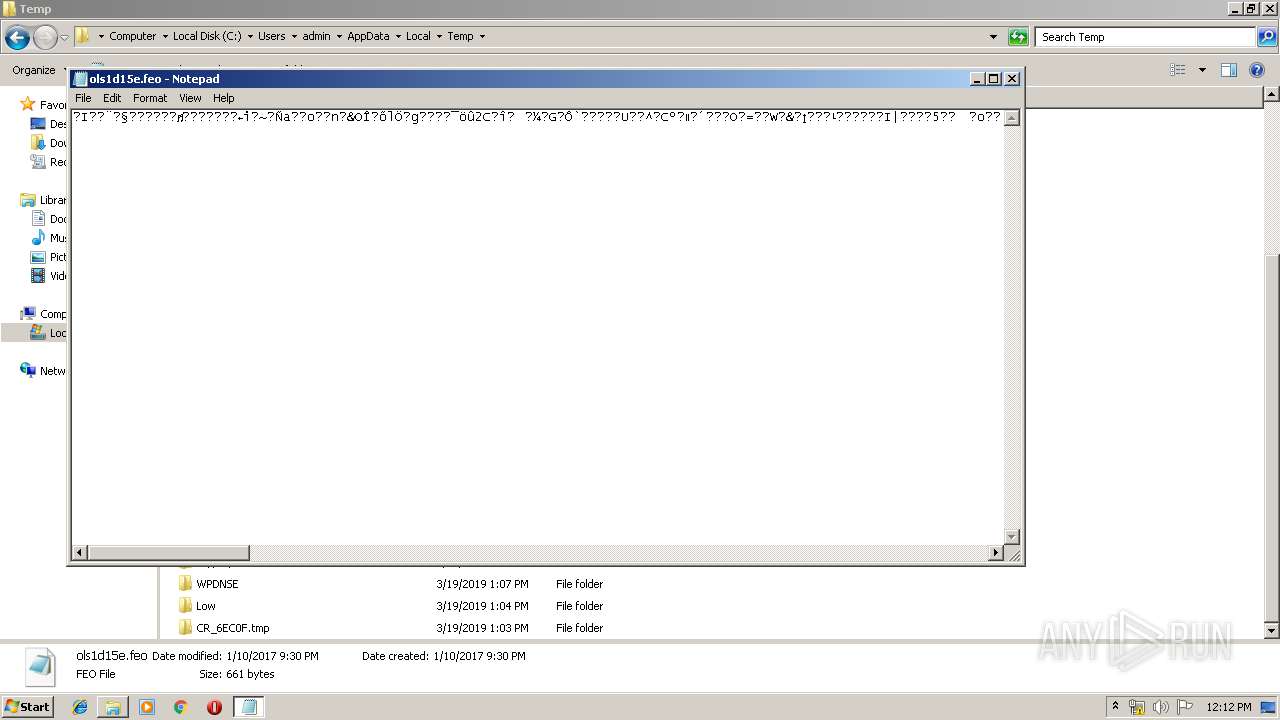
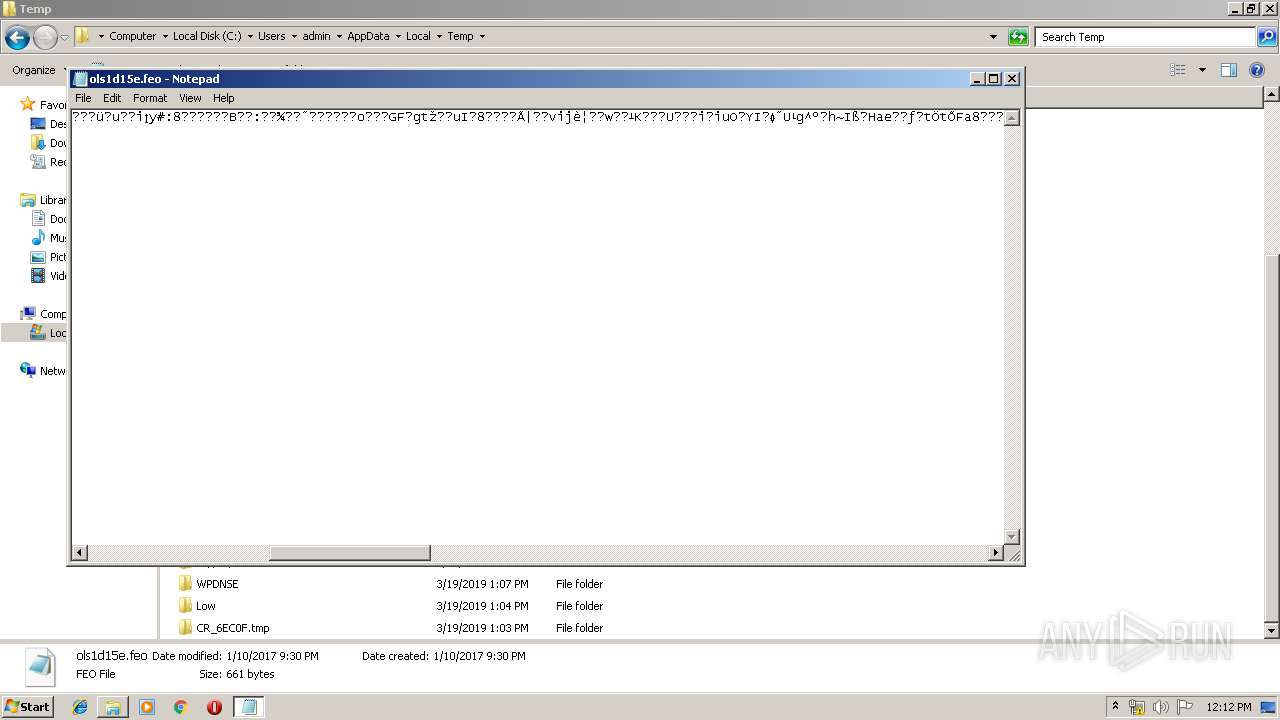
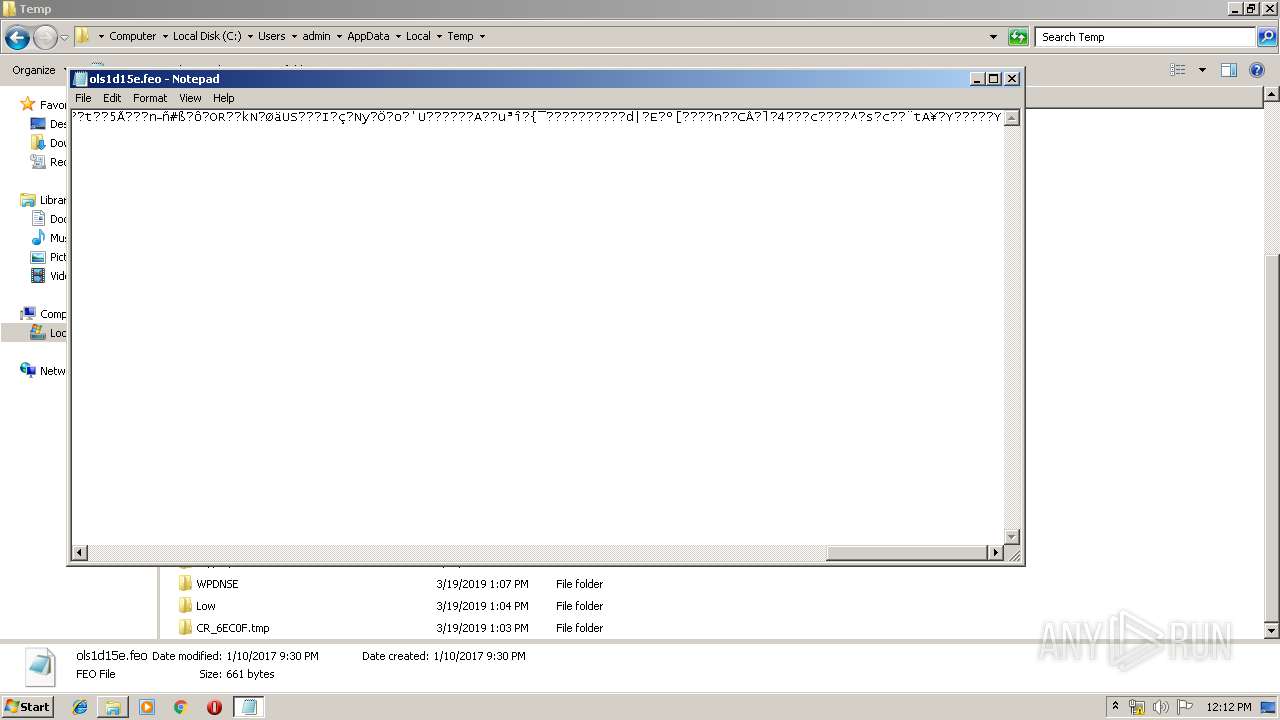
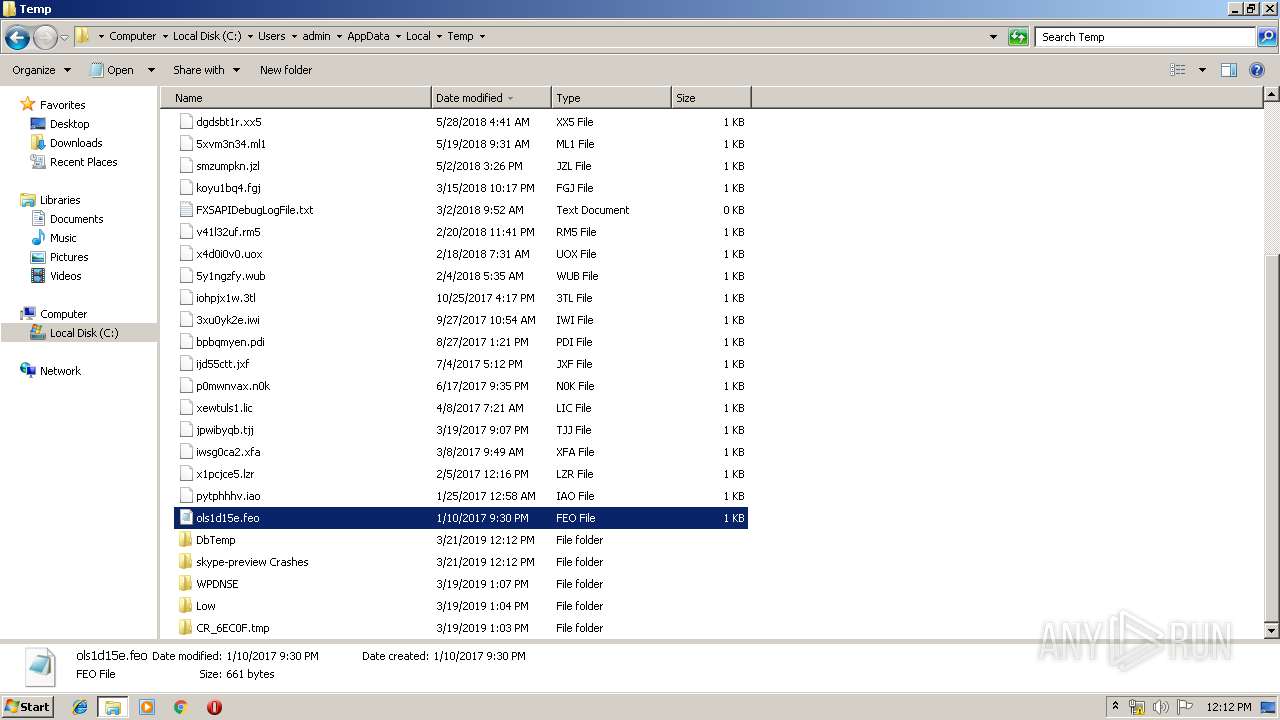
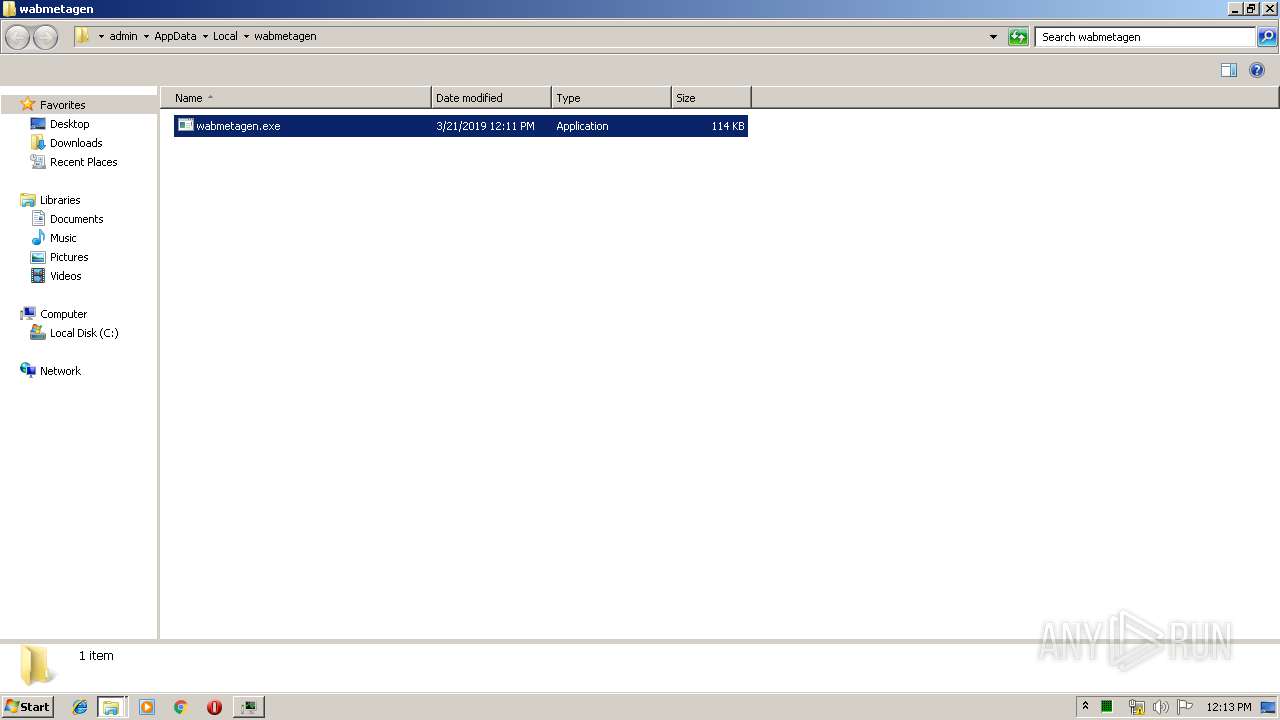
Executable content was dropped or overwritten
- 7958c2452a24ad4959d1359caf51deb41b798d30.exe (PID: 2836)
Creates files in the user directory
- Skype.exe (PID: 264)
- Skype.exe (PID: 2208)
- Skype.exe (PID: 3896)
Reads CPU info
- Skype.exe (PID: 264)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 264)
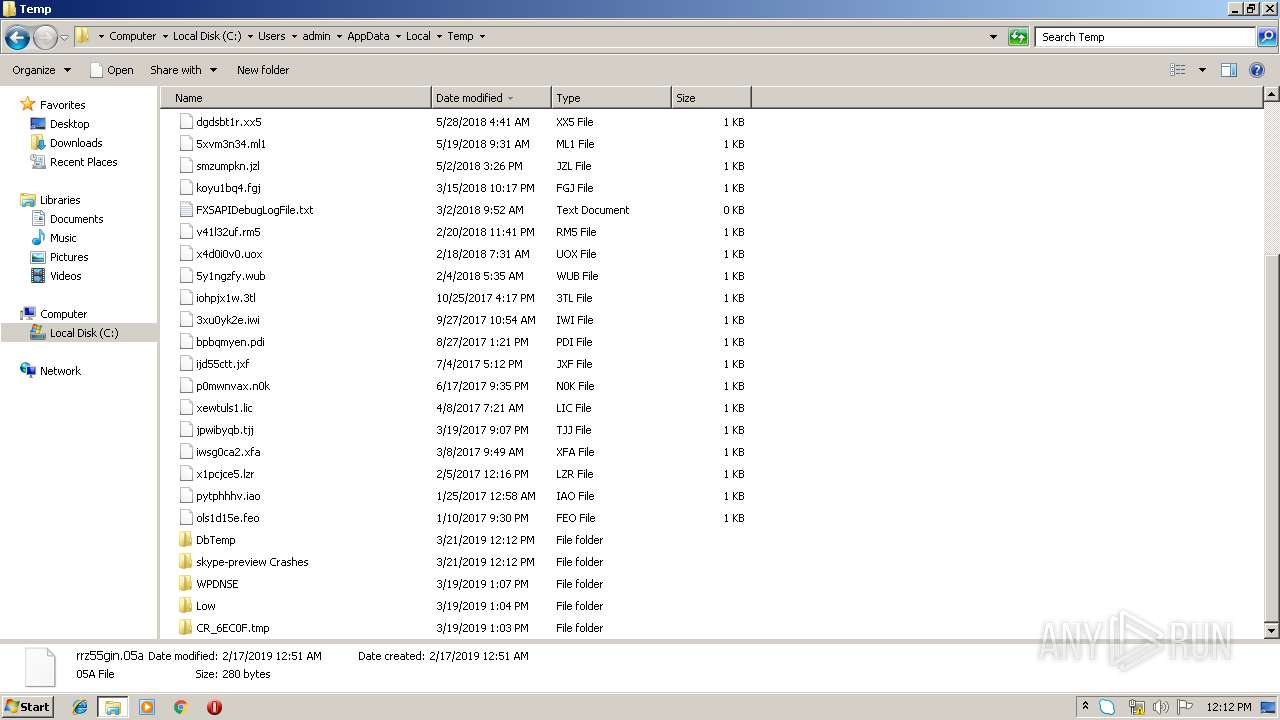
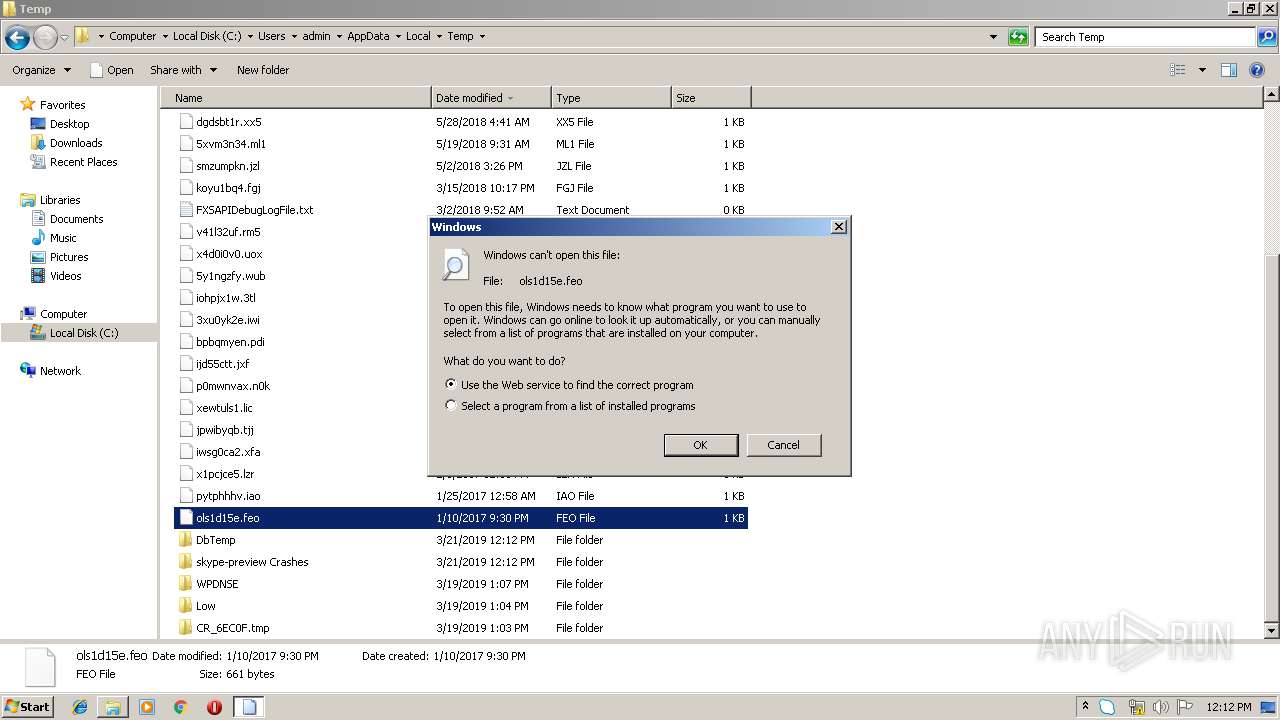
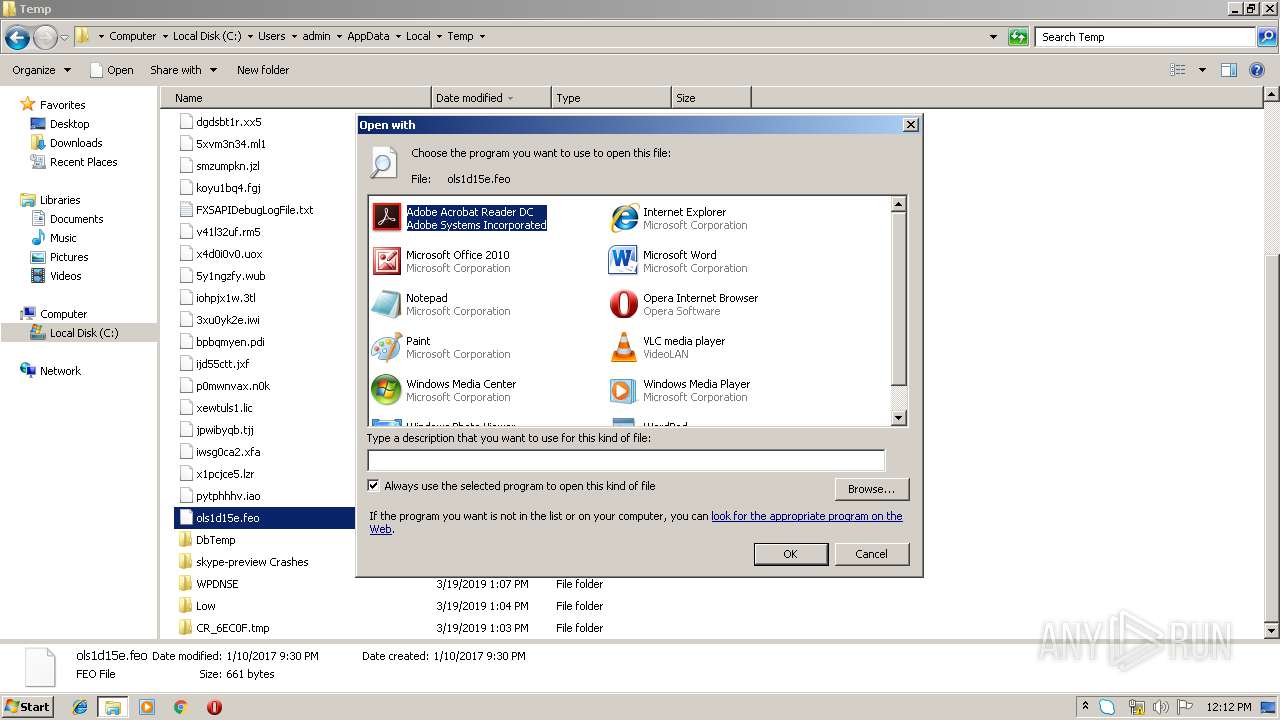
Modifies the open verb of a shell class
- Skype.exe (PID: 264)
Application launched itself
- 7958c2452a24ad4959d1359caf51deb41b798d30.exe (PID: 1476)
- wabmetagen.exe (PID: 612)
- Skype.exe (PID: 2208)
- Skype.exe (PID: 3896)
- Skype.exe (PID: 264)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3636)
INFO
Reads settings of System Certificates
- Skype.exe (PID: 264)
Dropped object may contain Bitcoin addresses
- Skype.exe (PID: 264)
Modifies the open verb of a shell class
- rundll32.exe (PID: 2860)
Application launched itself
- chrome.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:19 18:06:29+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 100352 |
| InitializedDataSize: | 11776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1dc0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | AOL LLC |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | 2009 - AOL LLC - All rights reserved |
| OriginalFileName: | AIMInst.exe |
| ProductVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Mar-2019 17:06:29 |
| Detected languages: |
|
| CompanyName: | AOL LLC |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | 2009 - AOL LLC - All rights reserved |
| OriginalFilename: | AIMInst.exe |
| ProductVersion: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 19-Mar-2019 17:06:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000187CB | 0x00018800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52146 |
.rdata | 0x0001A000 | 0x00001D8E | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.58682 |
.data | 0x0001C000 | 0x00000134 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.01929 |
.rsrc | 0x0001D000 | 0x00000C58 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.91529 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.23664 | 544 | UNKNOWN | English - United States | RT_VERSION |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
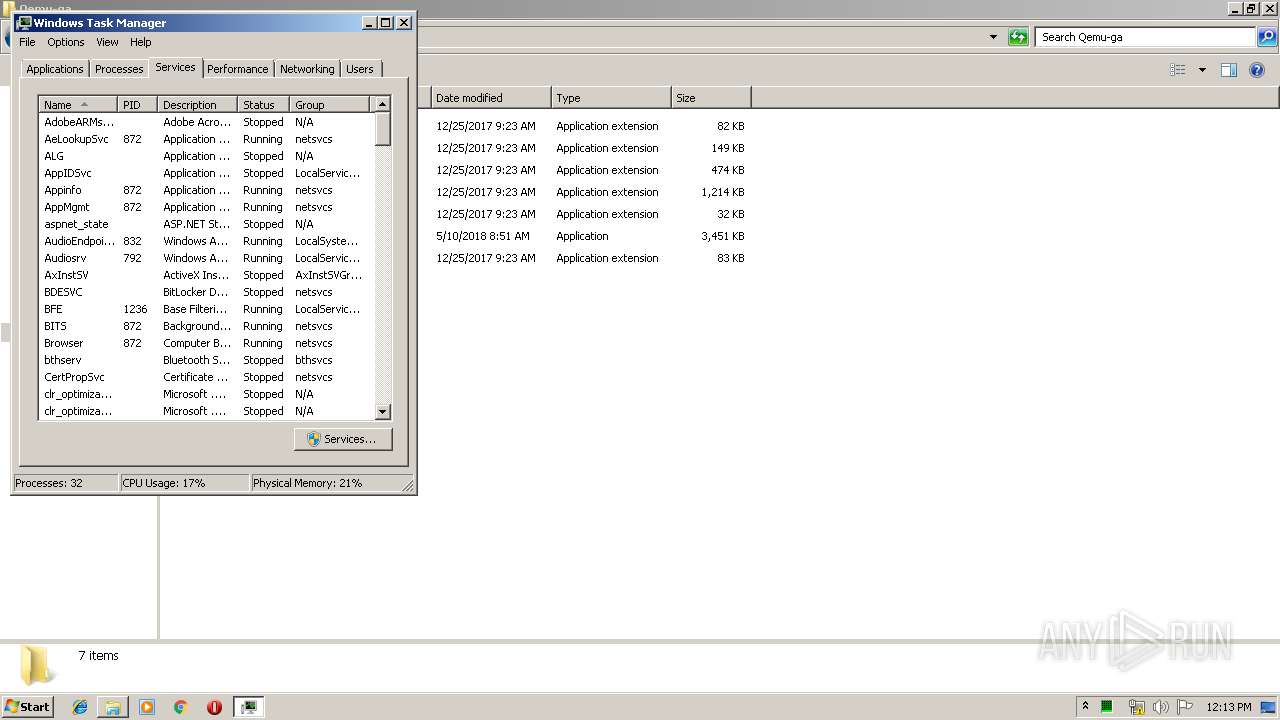
Total processes
94
Monitored processes
47
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
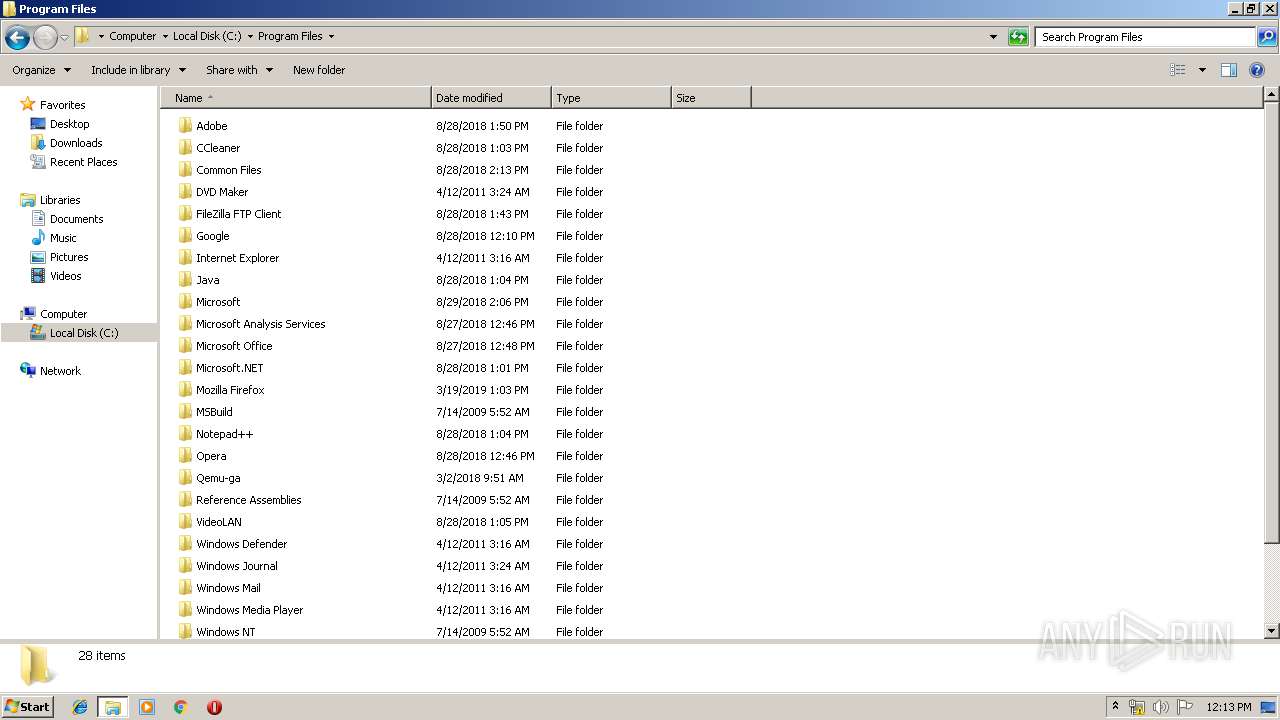
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,1628737454637458858,316635844183184766,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4184290414267245573 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4184290414267245573 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
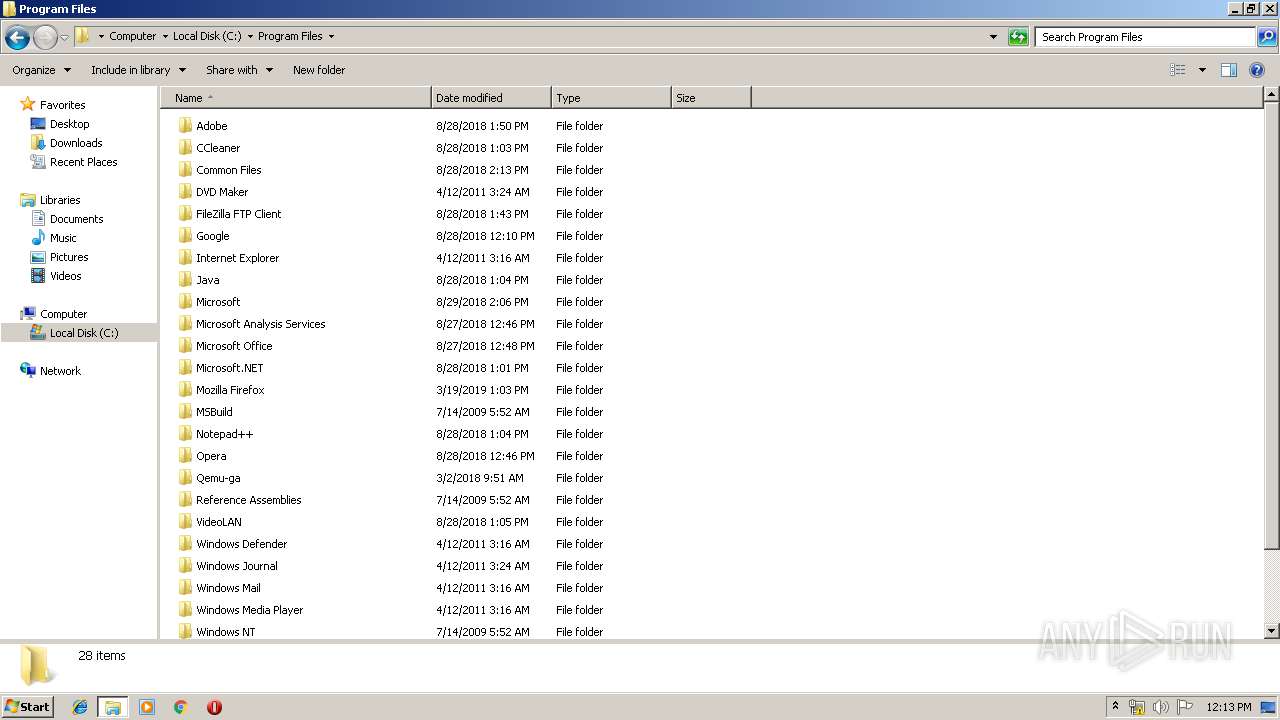
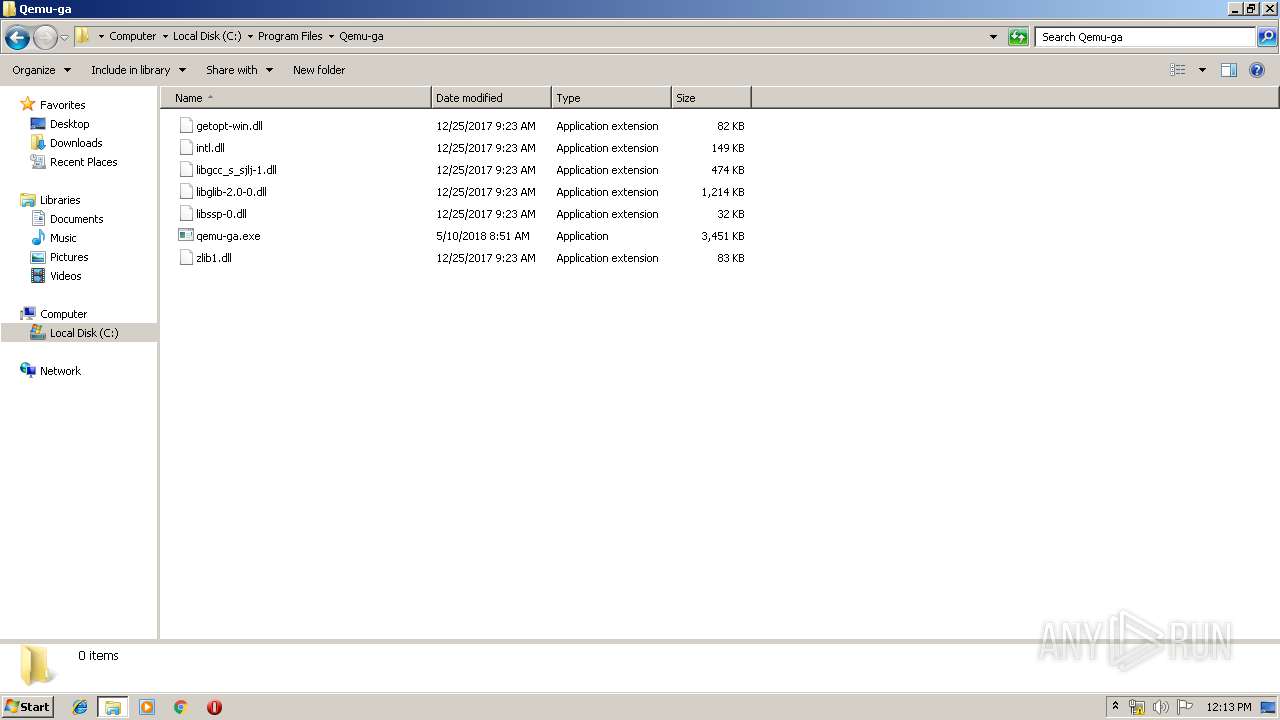
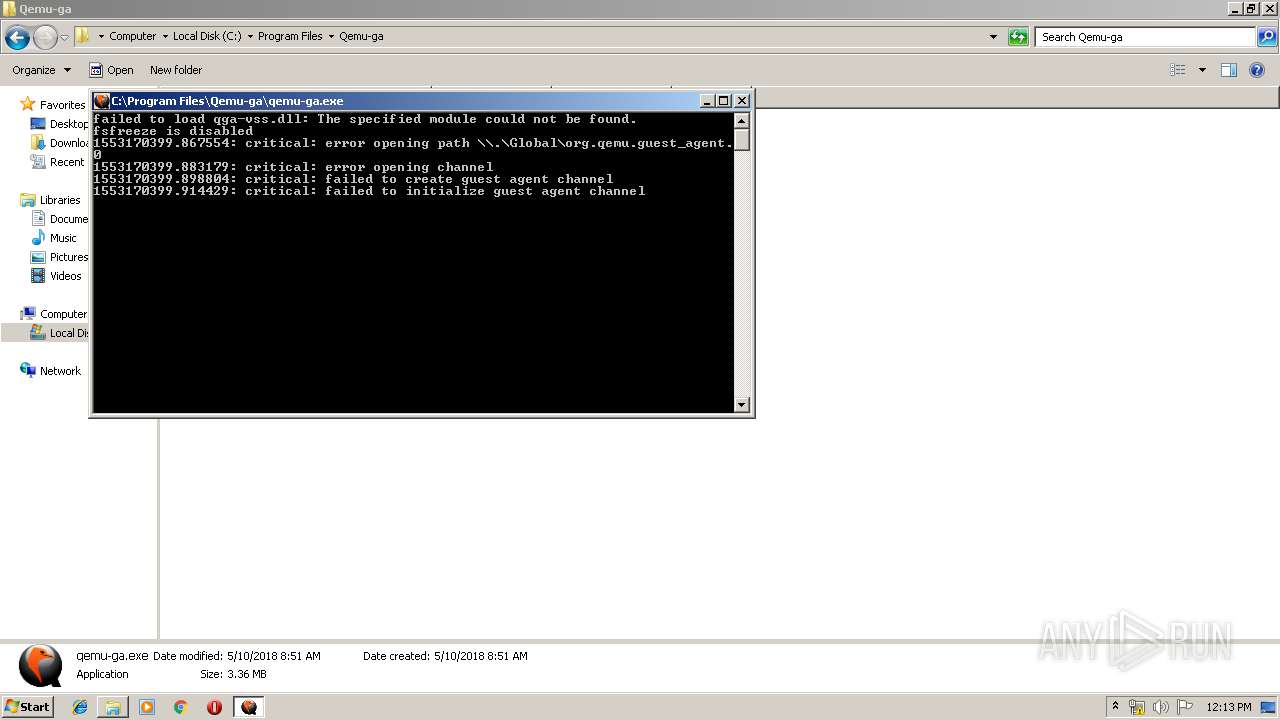
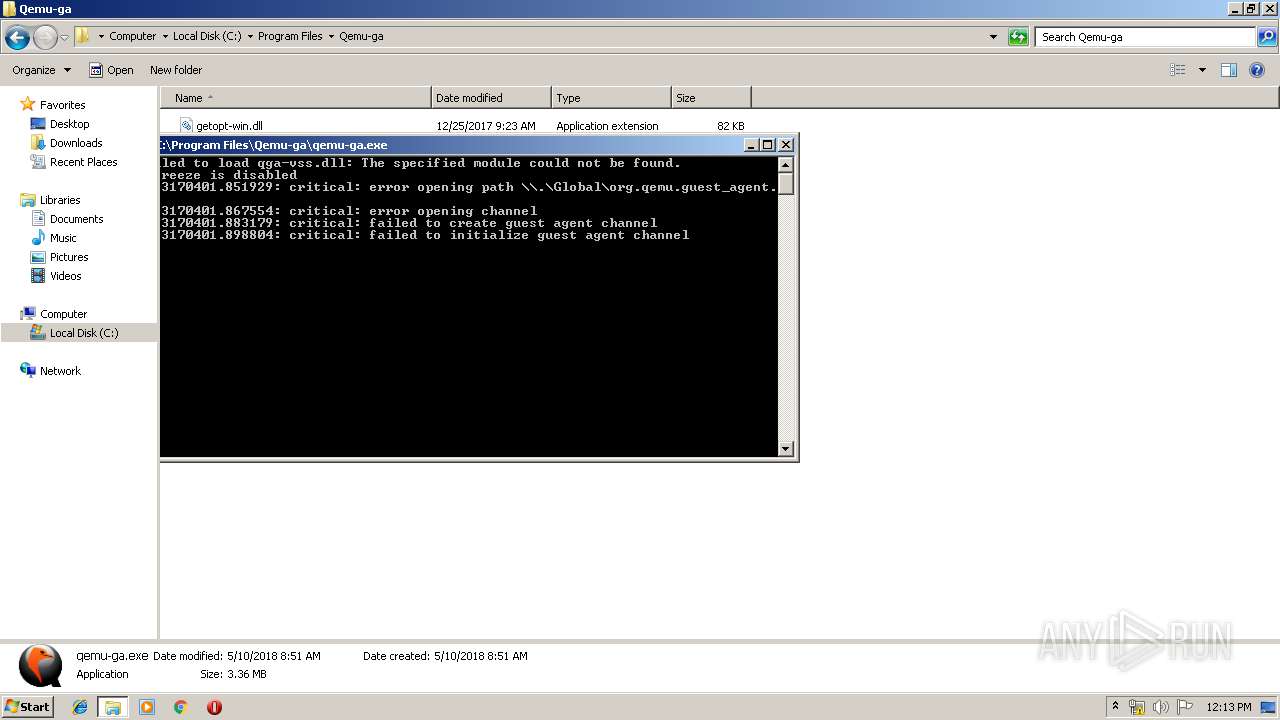
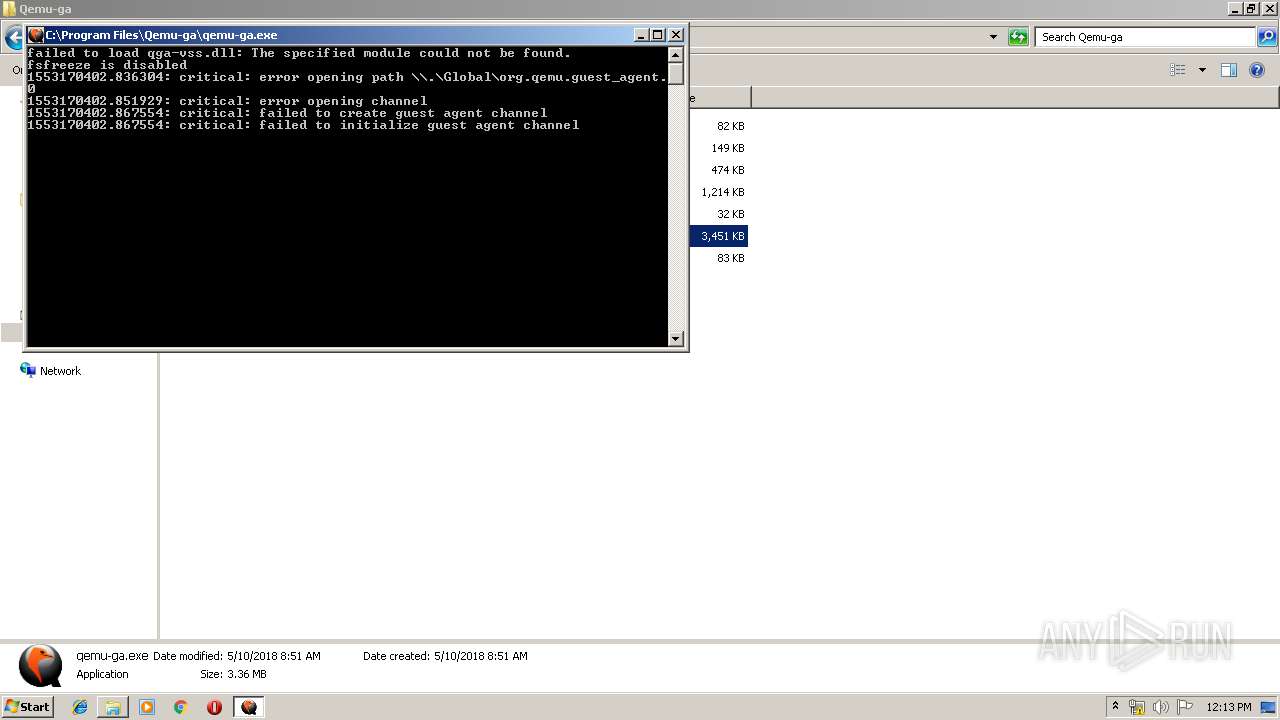
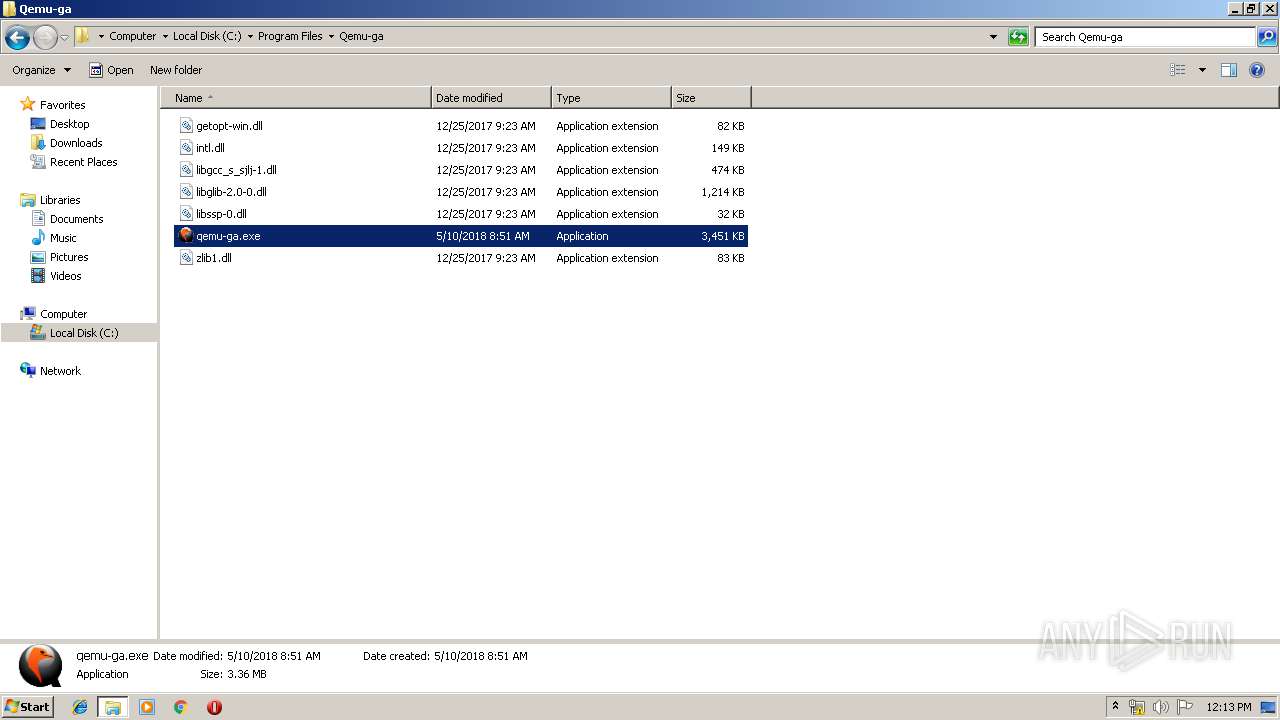
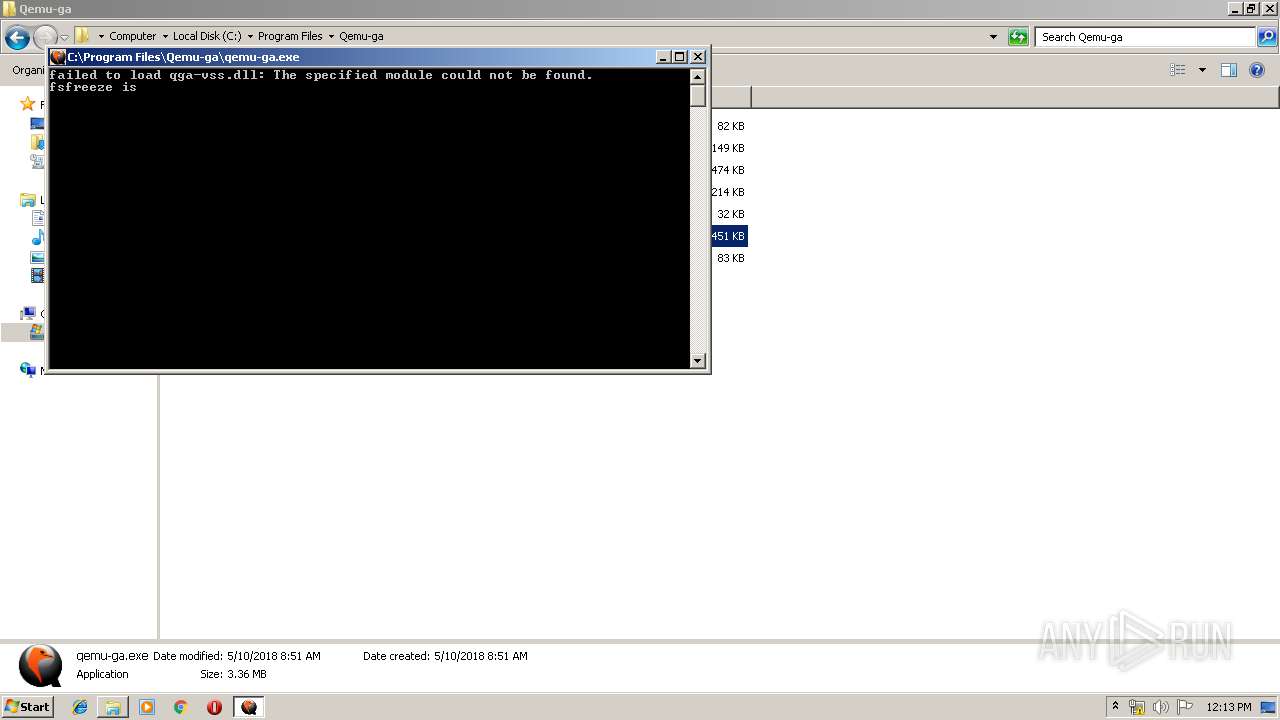
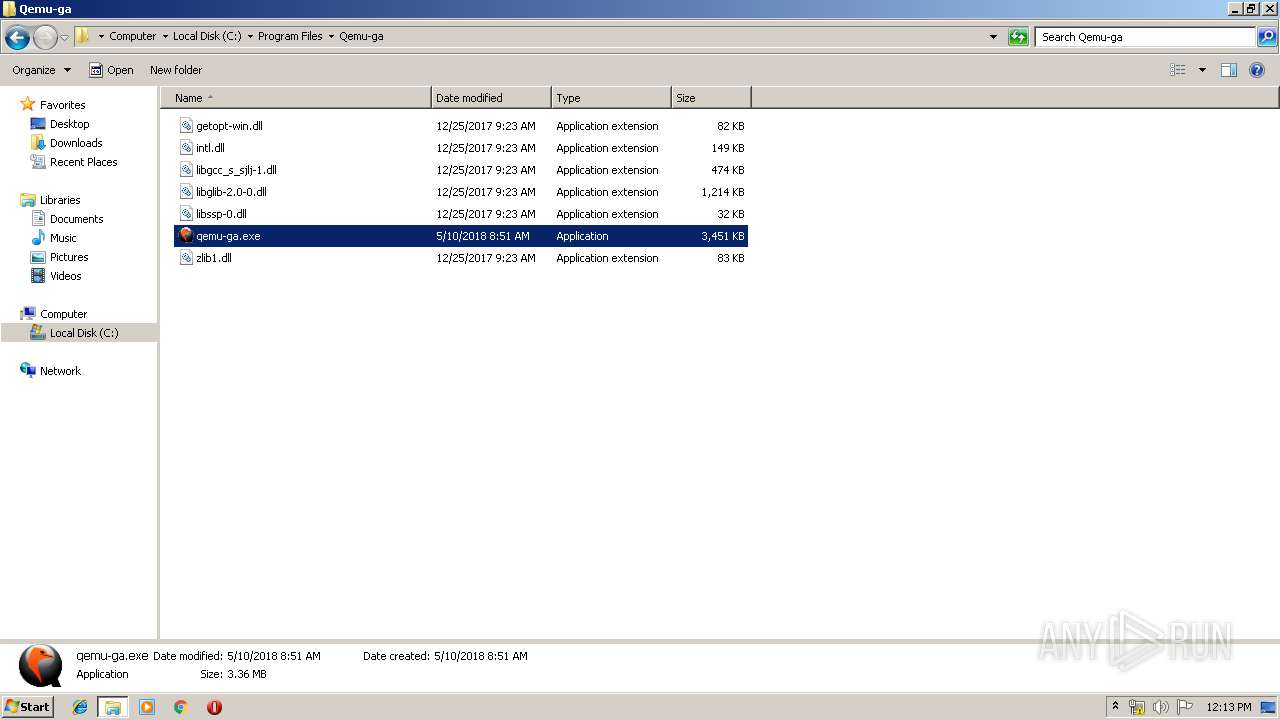
| 240 | "C:\Program Files\Qemu-ga\qemu-ga.exe" | C:\Program Files\Qemu-ga\qemu-ga.exe | — | explorer.exe | |||||||||||
User: admin Company: http://www.qemu-project.org Integrity Level: MEDIUM Description: QEMU machine emulators and tools Exit code: 1 Version: 2.10.59 Modules
| |||||||||||||||
| 264 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | explorer.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Qemu-ga\qemu-ga.exe" | C:\Program Files\Qemu-ga\qemu-ga.exe | — | explorer.exe | |||||||||||
User: admin Company: http://www.qemu-project.org Integrity Level: MEDIUM Description: QEMU machine emulators and tools Exit code: 1 Version: 2.10.59 Modules
| |||||||||||||||
| 400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,1628737454637458858,316635844183184766,131072 --enable-features=PasswordImport --service-pipe-token=4495186380218908630 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4495186380218908630 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Qemu-ga\qemu-ga.exe" | C:\Program Files\Qemu-ga\qemu-ga.exe | — | explorer.exe | |||||||||||
User: admin Company: http://www.qemu-project.org Integrity Level: MEDIUM Description: QEMU machine emulators and tools Exit code: 1 Version: 2.10.59 Modules
| |||||||||||||||
| 612 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 7958c2452a24ad4959d1359caf51deb41b798d30.exe | ||||||||||||
User: admin Company: AOL LLC Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,1628737454637458858,316635844183184766,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11248460185157930383 --mojo-platform-channel-handle=2548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: AOL LLC Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,1628737454637458858,316635844183184766,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2729153568275734905 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2729153568275734905 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 708
Read events
1 498
Write events
205
Delete events
5
Modification events
| (PID) Process: | (264) Skype.exe | Key: | HKEY_CLASSES_ROOT\skype |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (264) Skype.exe | Key: | HKEY_CLASSES_ROOT\skype |
| Operation: | write | Name: | |
Value: URL:skype | |||
| (PID) Process: | (264) Skype.exe | Key: | HKEY_CLASSES_ROOT\skype\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" -- "%1" | |||
| (PID) Process: | (2752) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Skype for Desktop |
Value: C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | |||
| (PID) Process: | (264) Skype.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1012) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1012) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1012) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1012) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1012) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
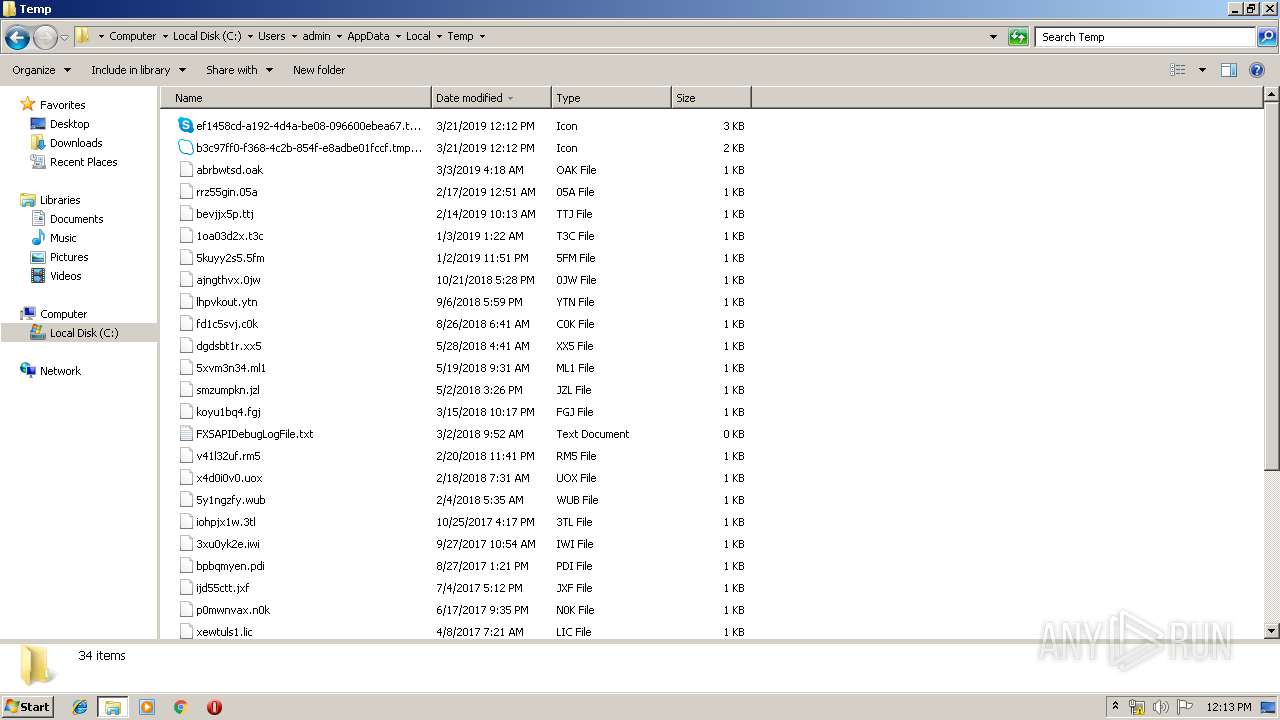
Executable files
1
Suspicious files
89
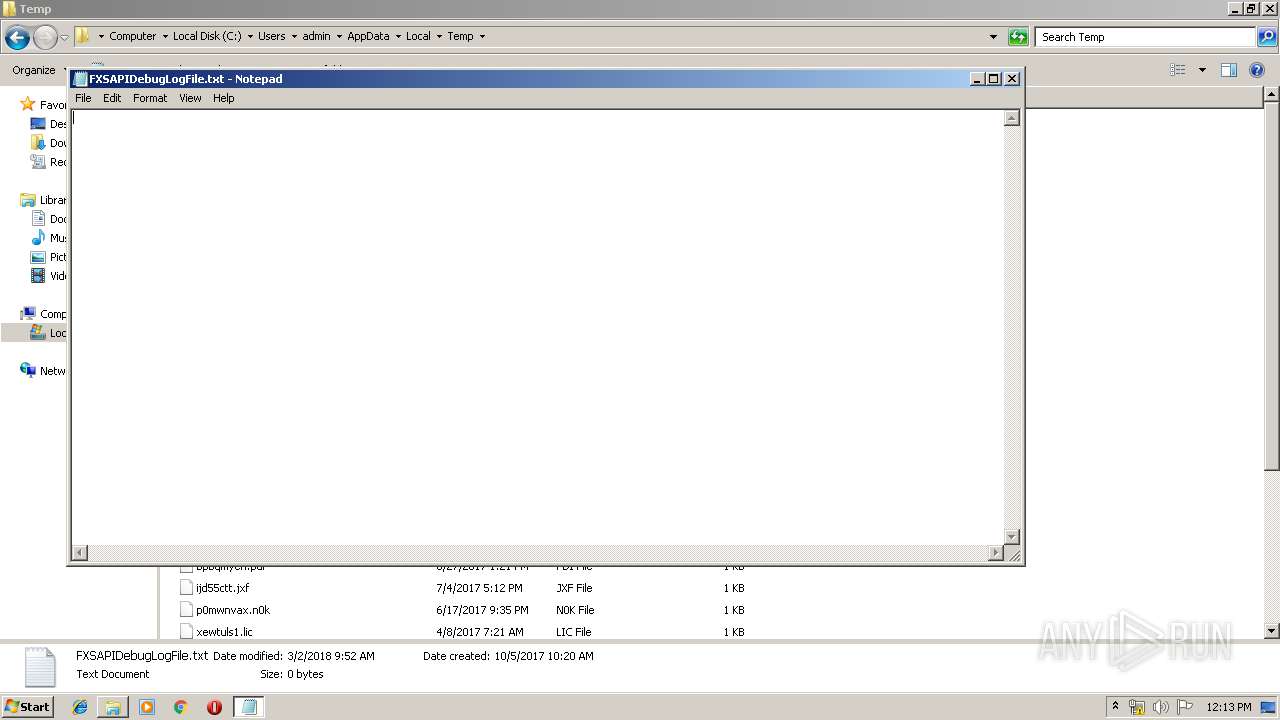
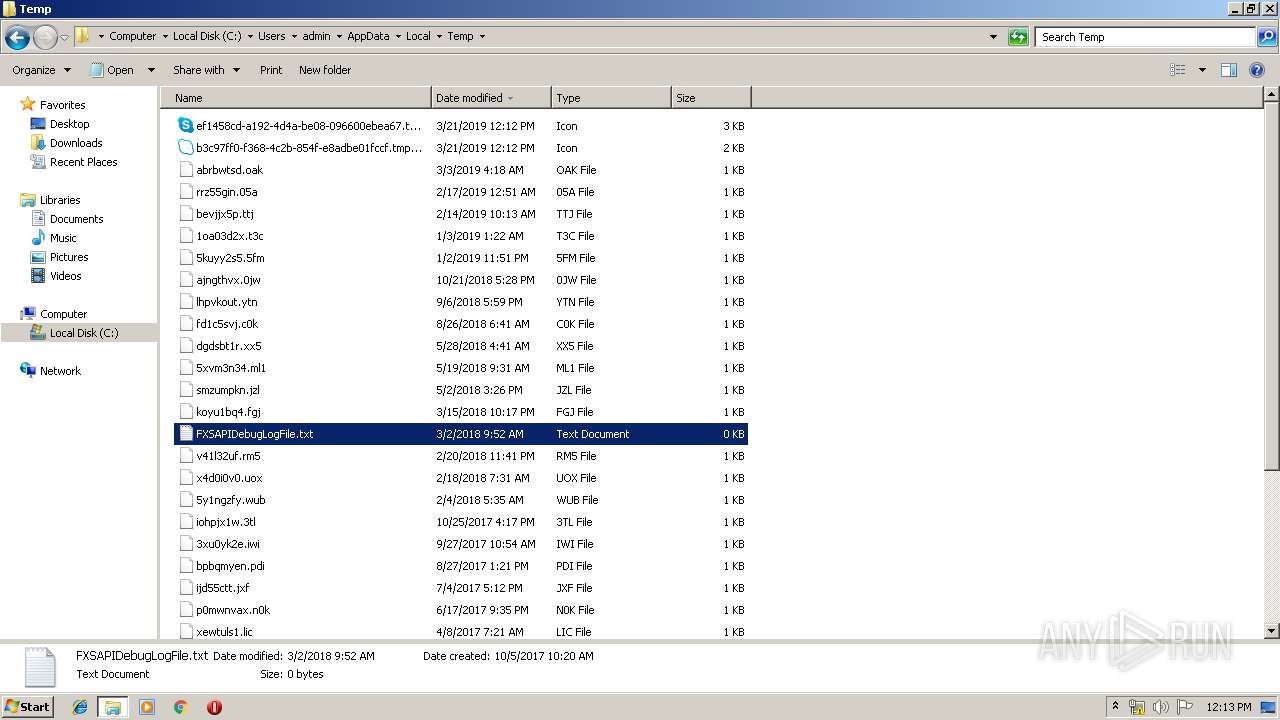
Text files
213
Unknown types
3
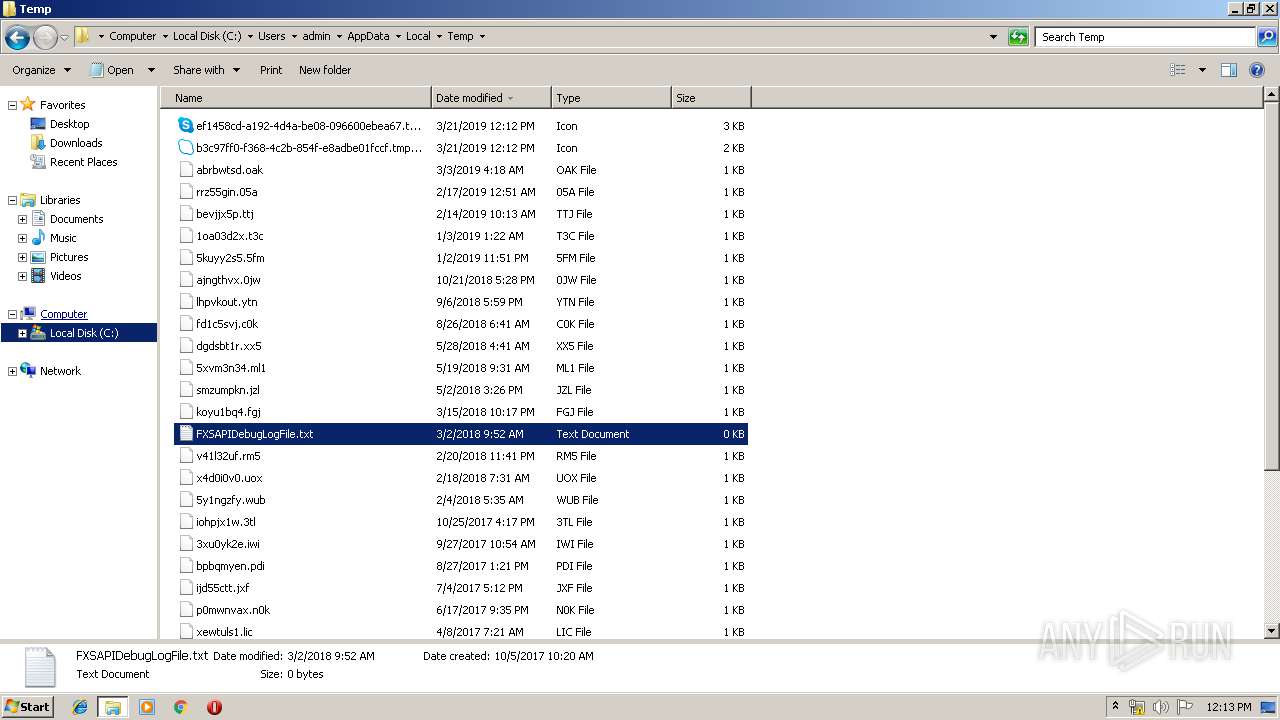
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 264 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UDHF3Z0K6E4040QKUZSA.temp | — | |
MD5:— | SHA256:— | |||
| 264 | Skype.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b916037c1e115fe0.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3556 | Skype.exe | C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\operation_log.txt | text | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2836 | 7958c2452a24ad4959d1359caf51deb41b798d30.exe | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | executable | |
MD5:— | SHA256:— | |||
| 3636 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
54
DNS requests
38
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
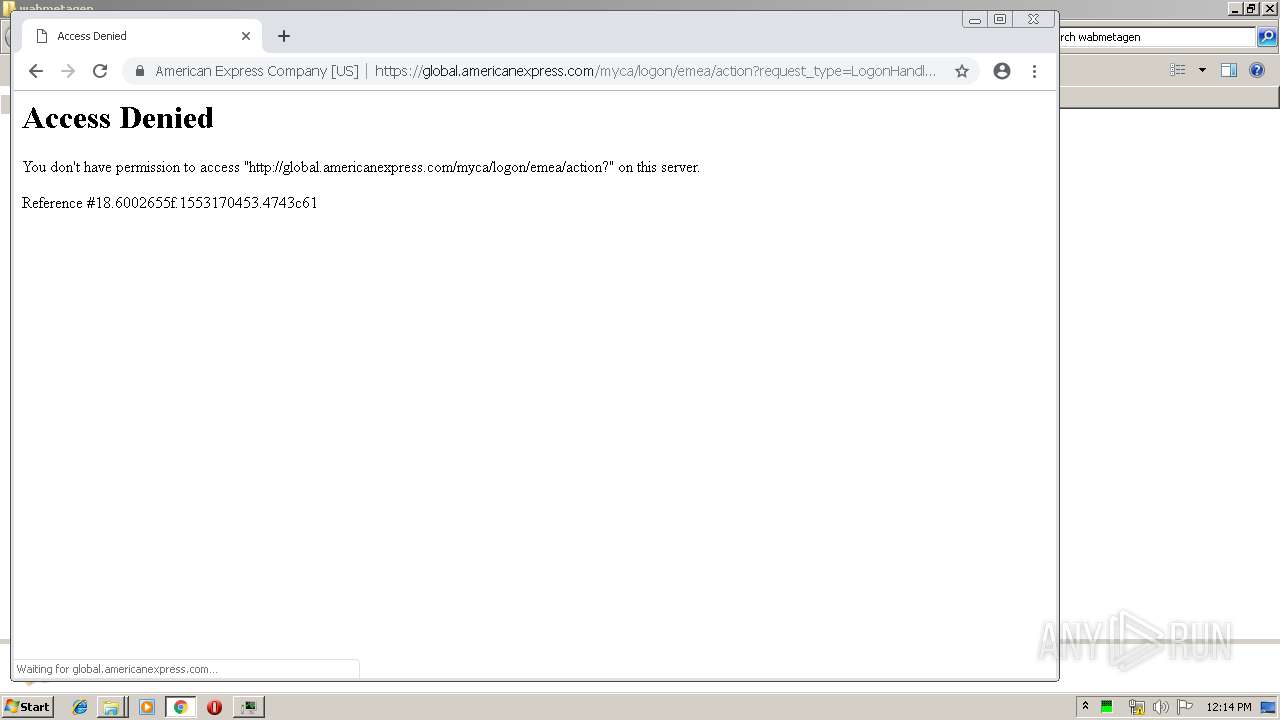
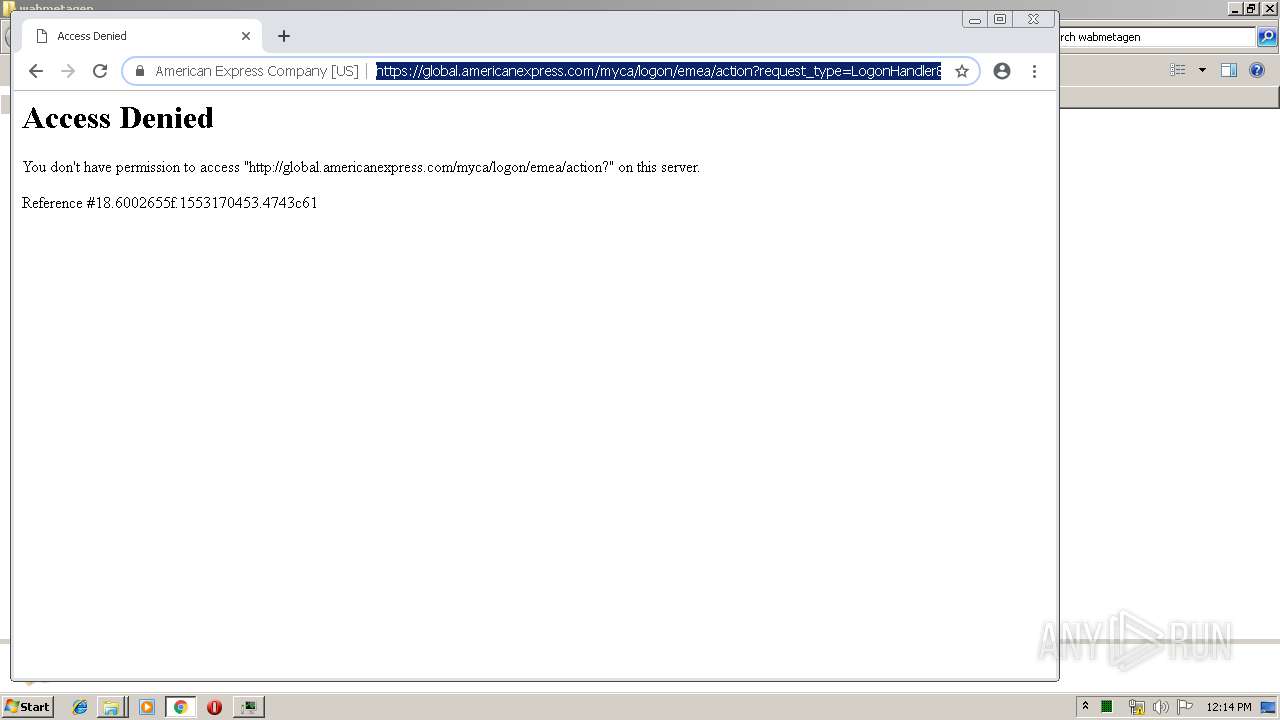
3180 | chrome.exe | GET | 200 | 185.192.249.19:80 | http://r6---sn-quxapm-3c2e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.109.23.2&mm=28&mn=sn-quxapm-3c2e&ms=nvh&mt=1553169519&mv=u&pl=20&shardbypass=yes | UA | crx | 842 Kb | whitelisted |
1012 | wabmetagen.exe | POST | 200 | 189.250.145.98:443 | http://189.250.145.98:443/acquire/guids/ | MX | binary | 132 b | malicious |
3180 | chrome.exe | GET | 302 | 172.217.20.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 508 b | whitelisted |
3180 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
264 | Skype.exe | 40.114.140.1:443 | a.config.skype.com | Microsoft Corporation | NL | unknown |
264 | Skype.exe | 88.221.164.208:443 | download.skype.com | Akamai International B.V. | — | whitelisted |
264 | Skype.exe | 216.58.212.170:443 | www.googleapis.com | Google Inc. | US | whitelisted |
264 | Skype.exe | 52.114.132.73:443 | pipe.skype.com | Microsoft Corporation | US | unknown |
264 | Skype.exe | 13.79.147.101:443 | avatar.skype.com | Microsoft Corporation | IE | unknown |
1012 | wabmetagen.exe | 189.250.145.98:443 | — | Uninet S.A. de C.V. | MX | malicious |
264 | Skype.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
3180 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3180 | chrome.exe | 172.217.20.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3180 | chrome.exe | 172.217.20.78:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
get.skype.com |
| whitelisted |
a.config.skype.com |
| whitelisted |
pipe.skype.com |
| whitelisted |
download.skype.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
avatar.skype.com |
| whitelisted |
config.edge.skype.com |
| malicious |
browser.pipe.aria.microsoft.com |
| whitelisted |
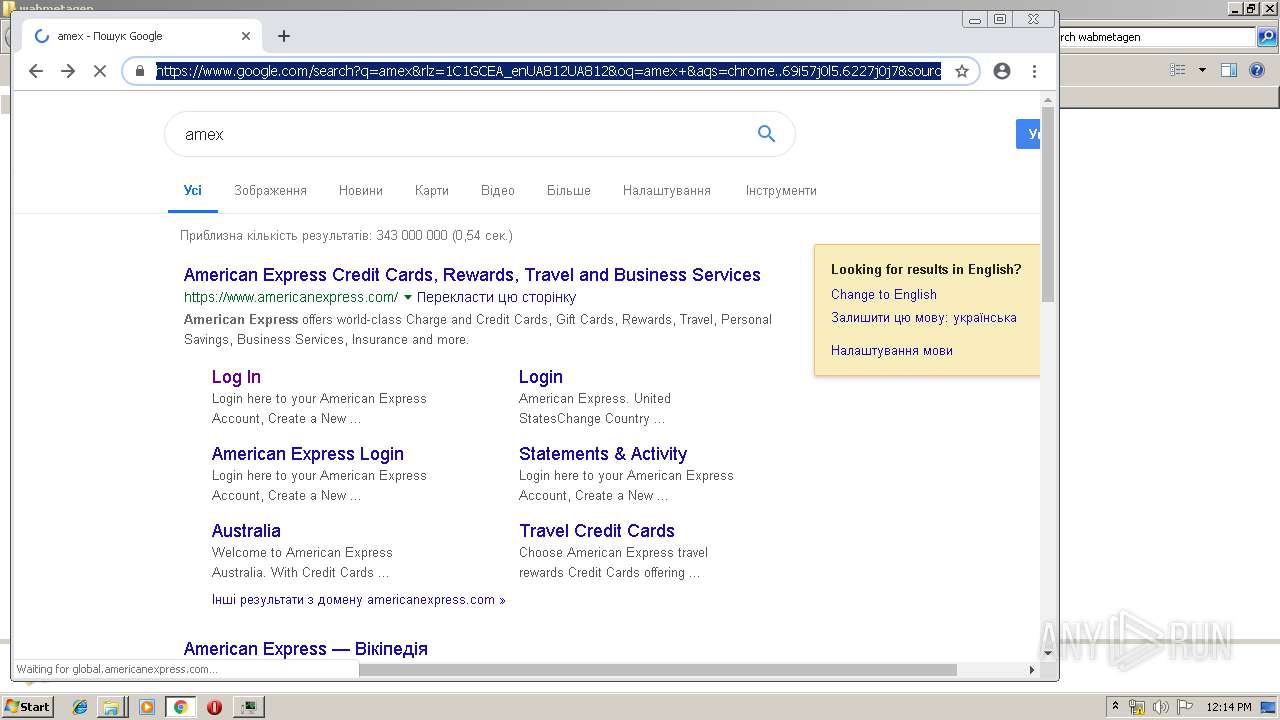
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1012 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] EMOTET/Feodo |
1012 | wabmetagen.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
Skype.exe | [1660:688:0321/121201.645:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [1660:688:0321/121201.645:VERBOSE1:crash_service.cc(145)] window handle is 00030160
|
Skype.exe | [1660:688:0321/121201.645:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [1660:688:0321/121201.645:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [1660:688:0321/121201.645:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [1660:3964:0321/121201.645:VERBOSE1:crash_service.cc(333)] client start. pid = 264
|
Skype.exe | [1660:3964:0321/121204.585:VERBOSE1:crash_service.cc(333)] client start. pid = 2208
|
Skype.exe | [3556:3516:0321/121204.850:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [3556:3516:0321/121204.850:VERBOSE1:crash_service.cc(145)] window handle is 00040124
|
Skype.exe | [3556:3516:0321/121204.850:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|