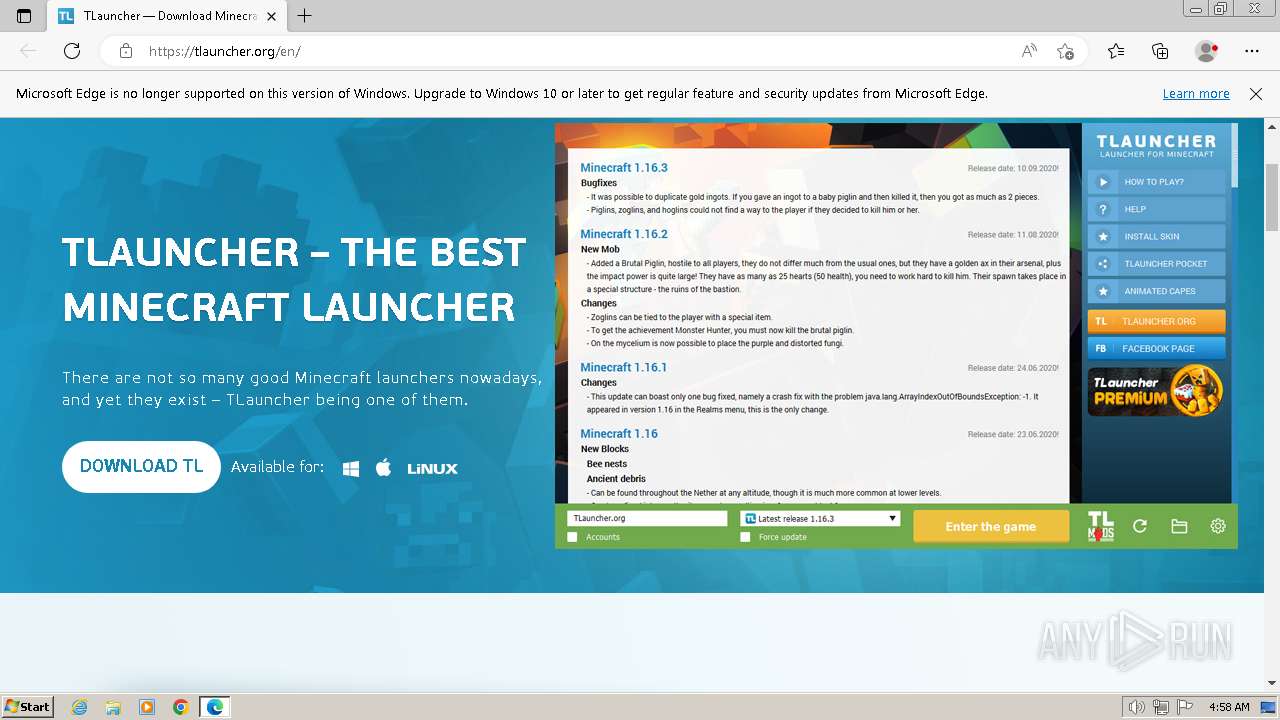
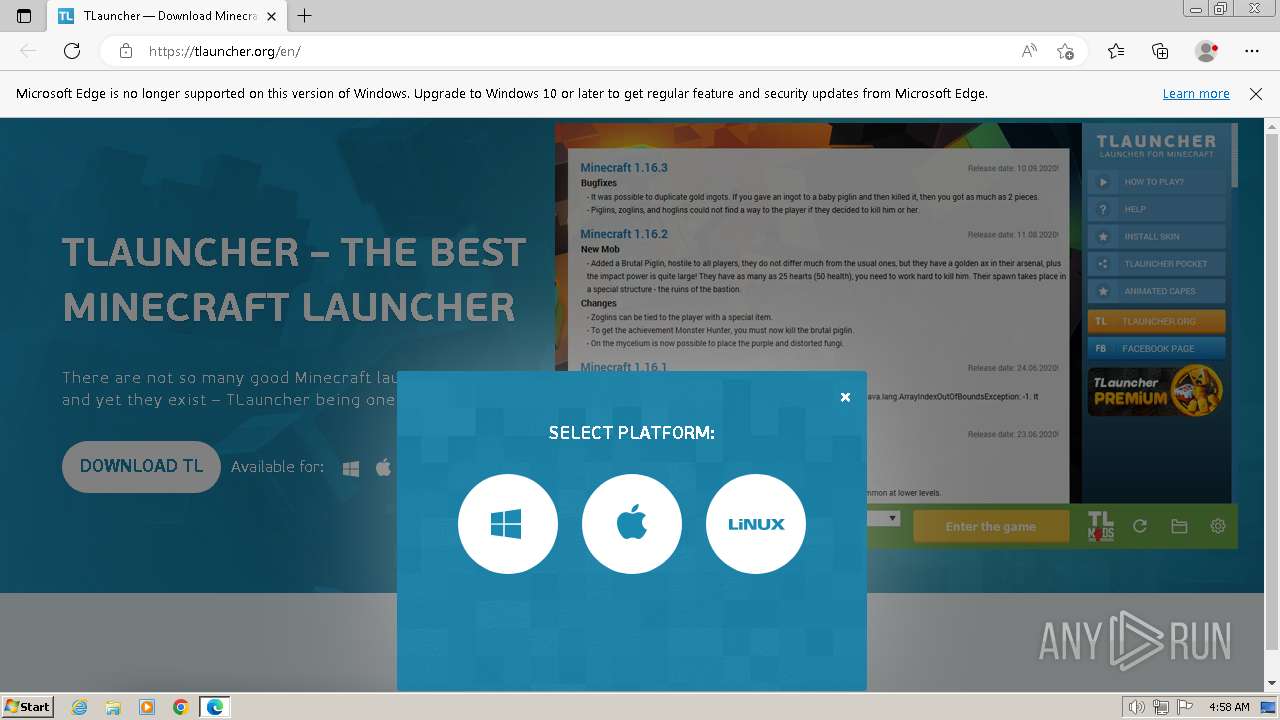
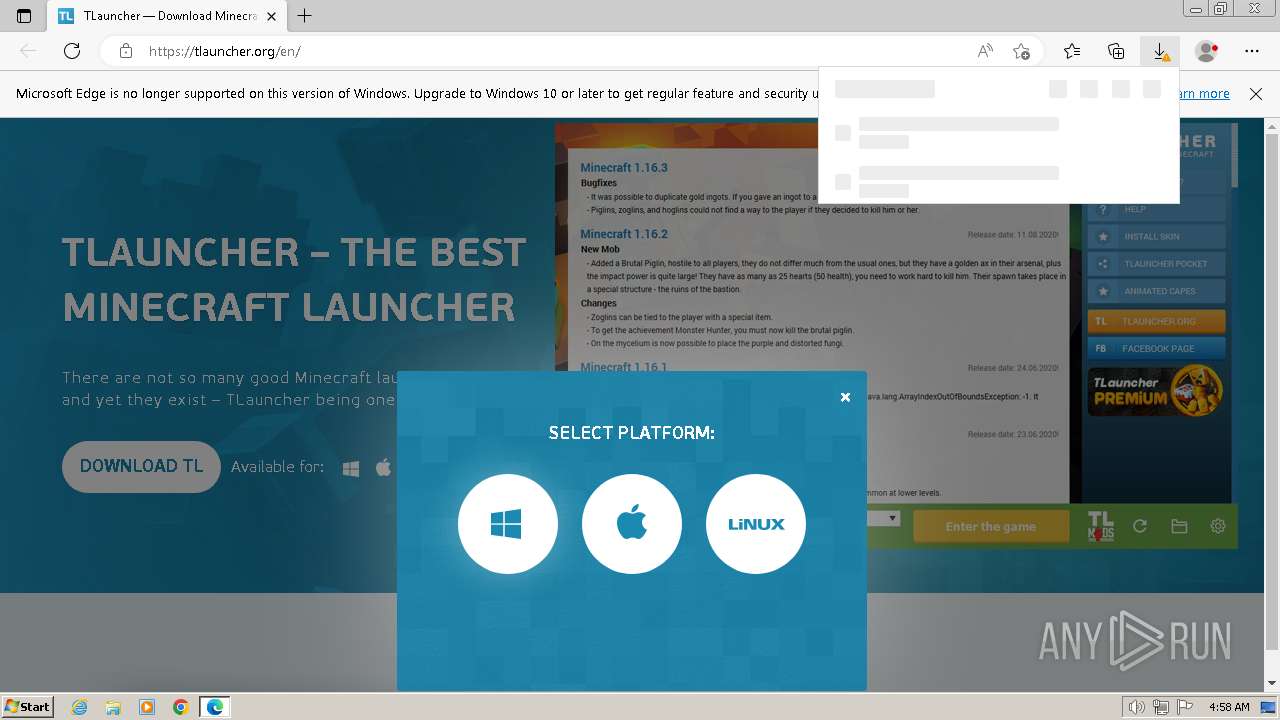
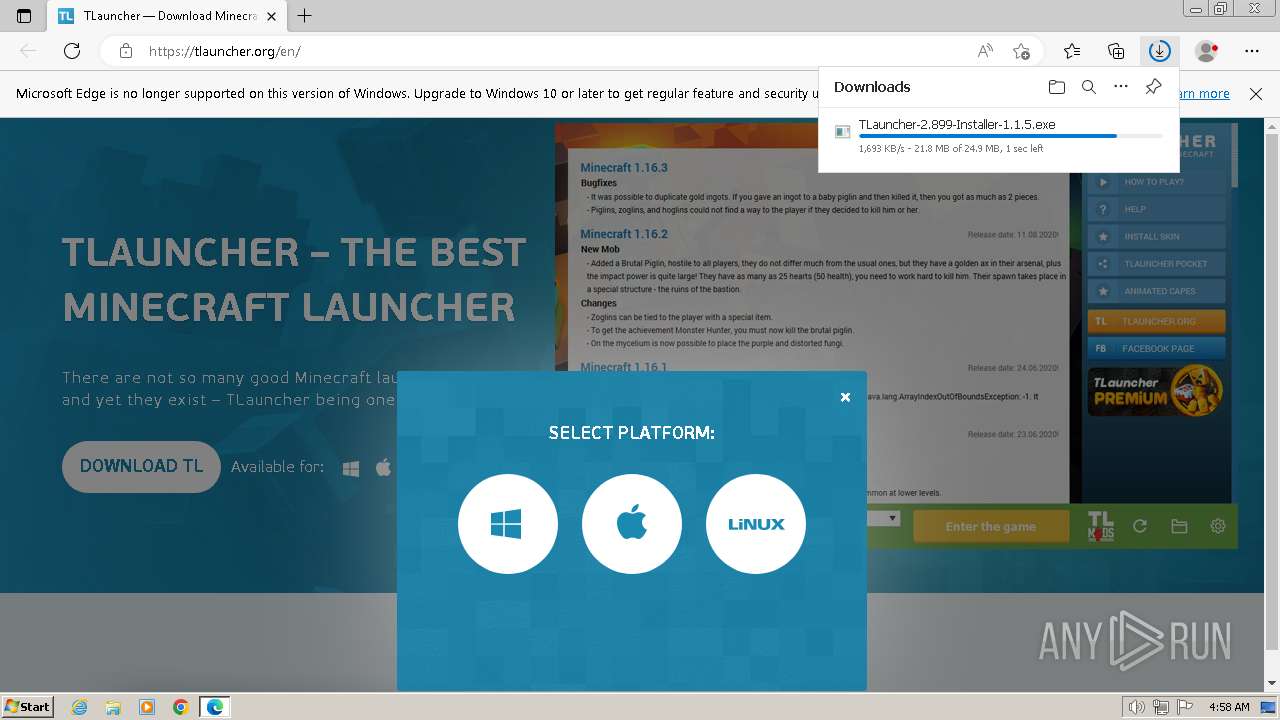
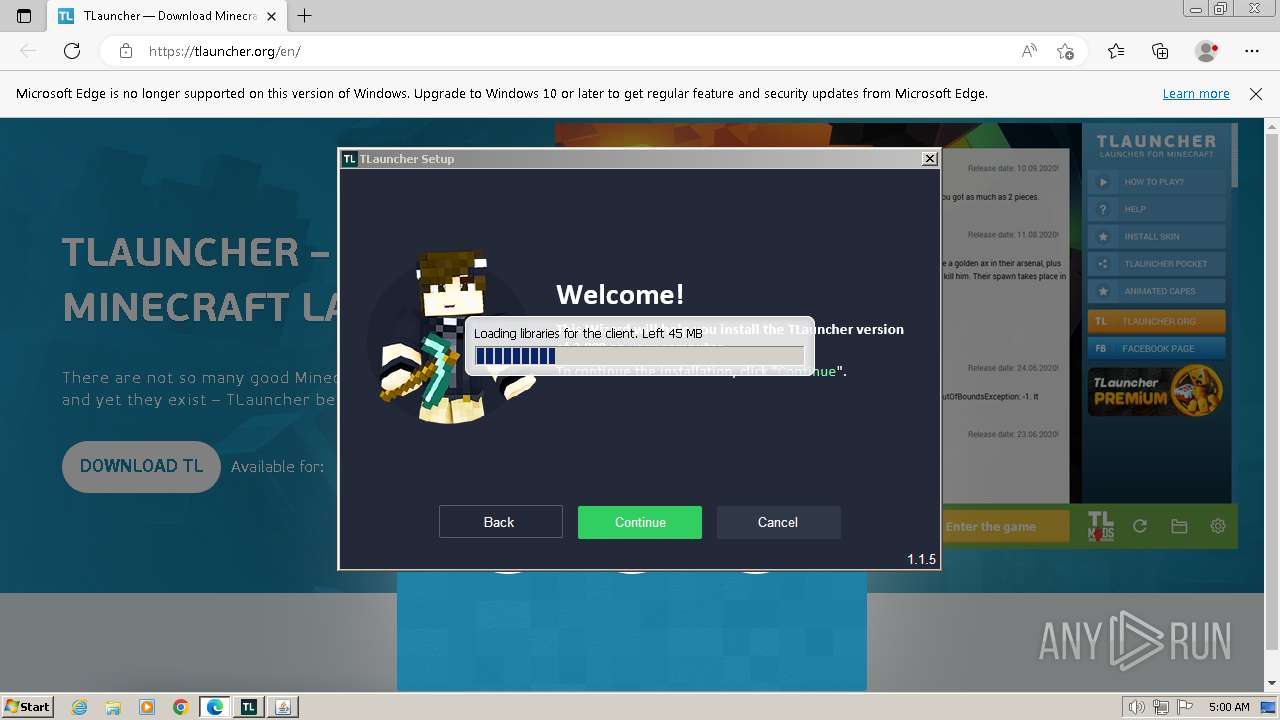
| URL: | https://tlauncher.org/en/ |
| Full analysis: | https://app.any.run/tasks/a18c3e5d-2b2e-40f2-b57a-a247d855f7aa |
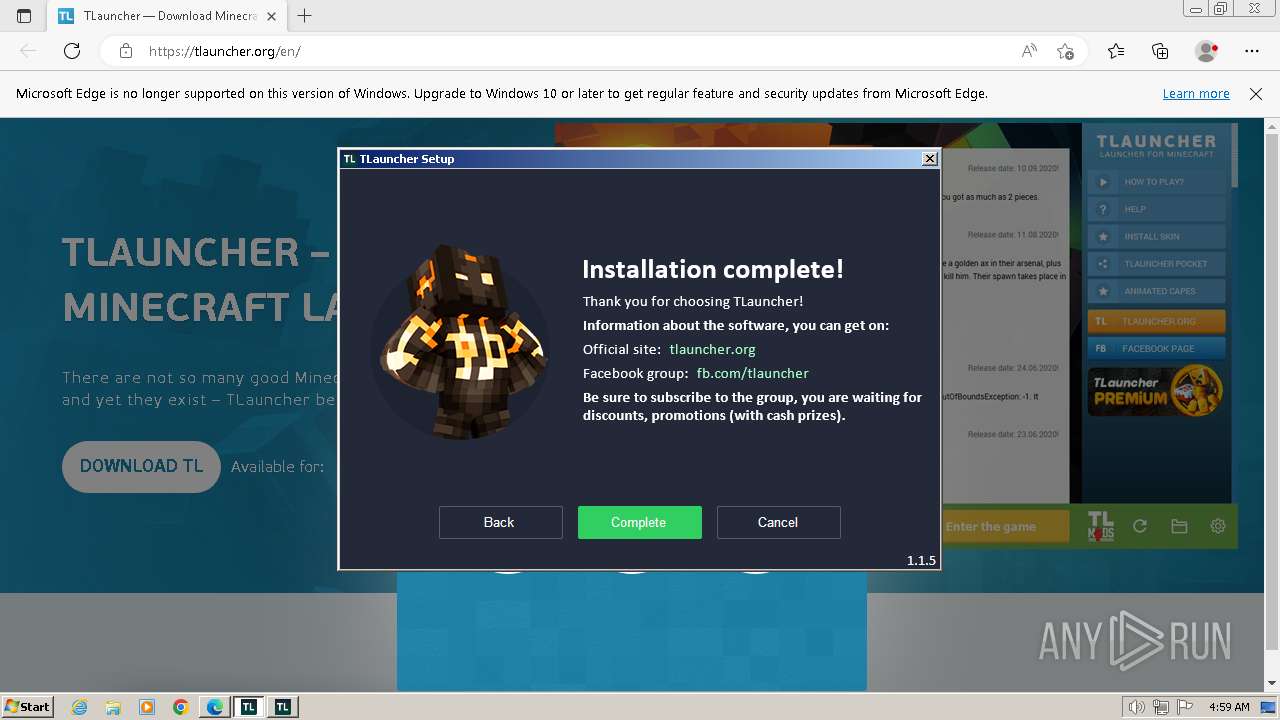
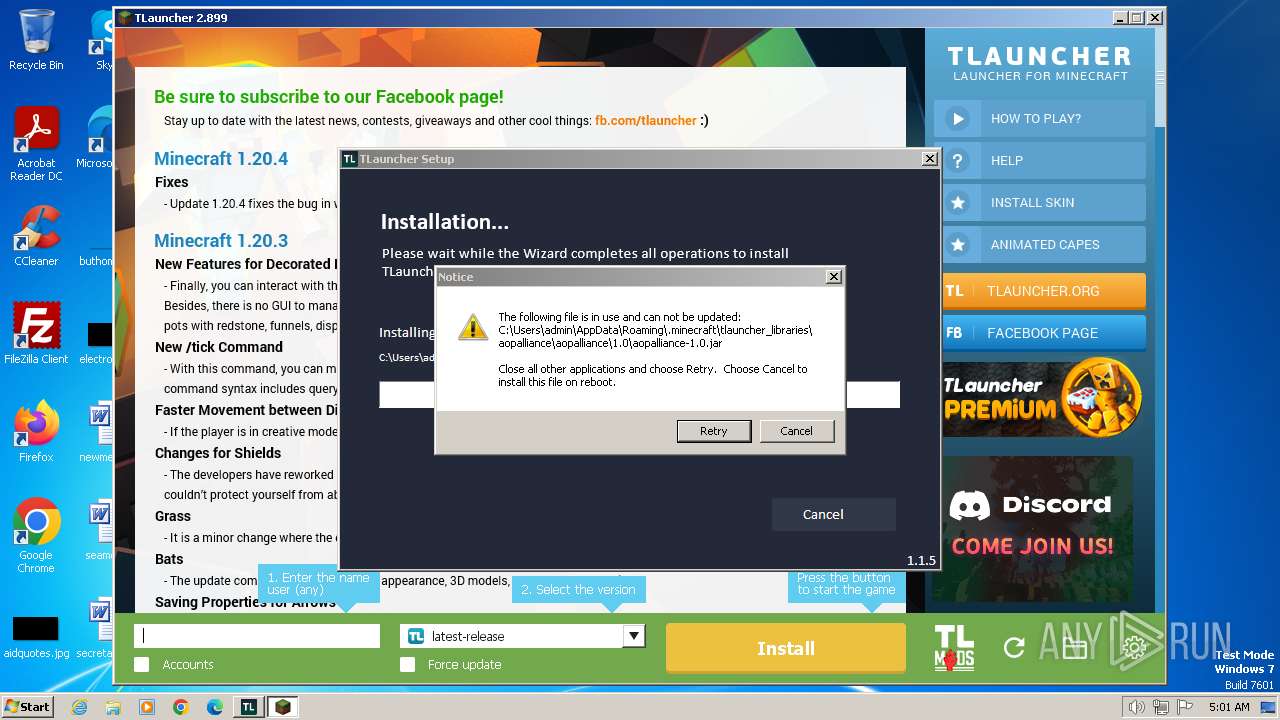
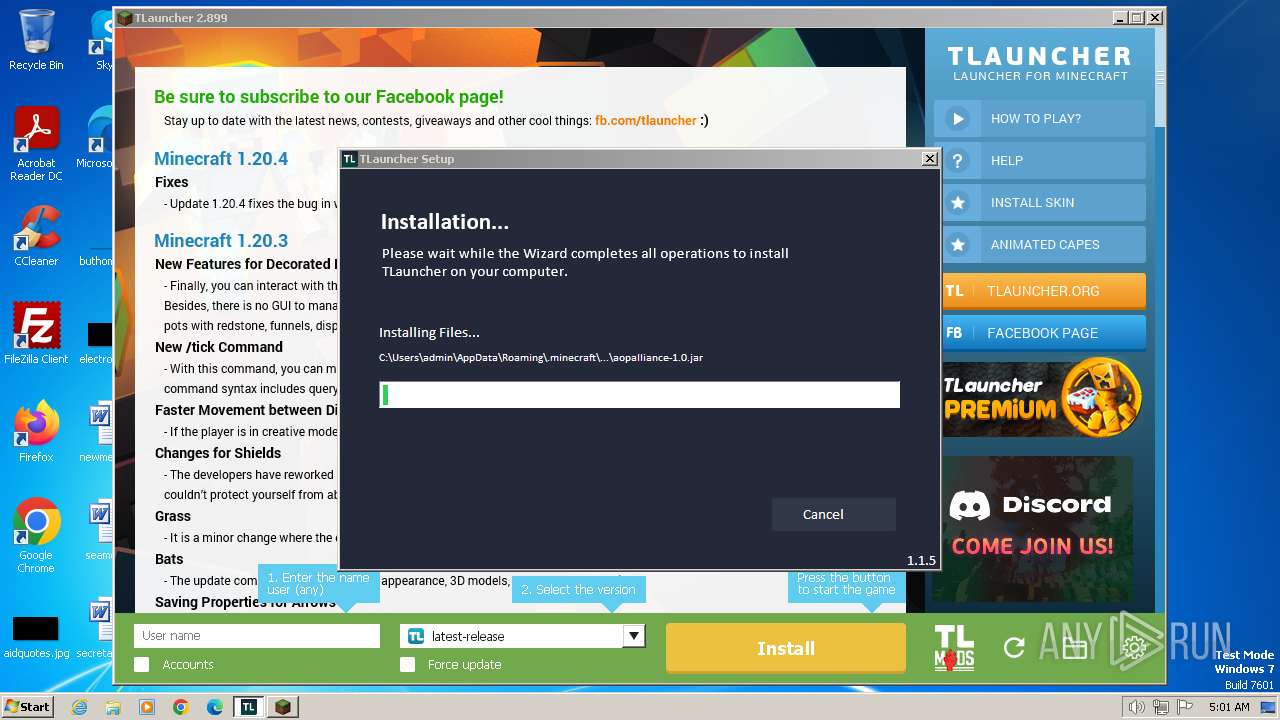
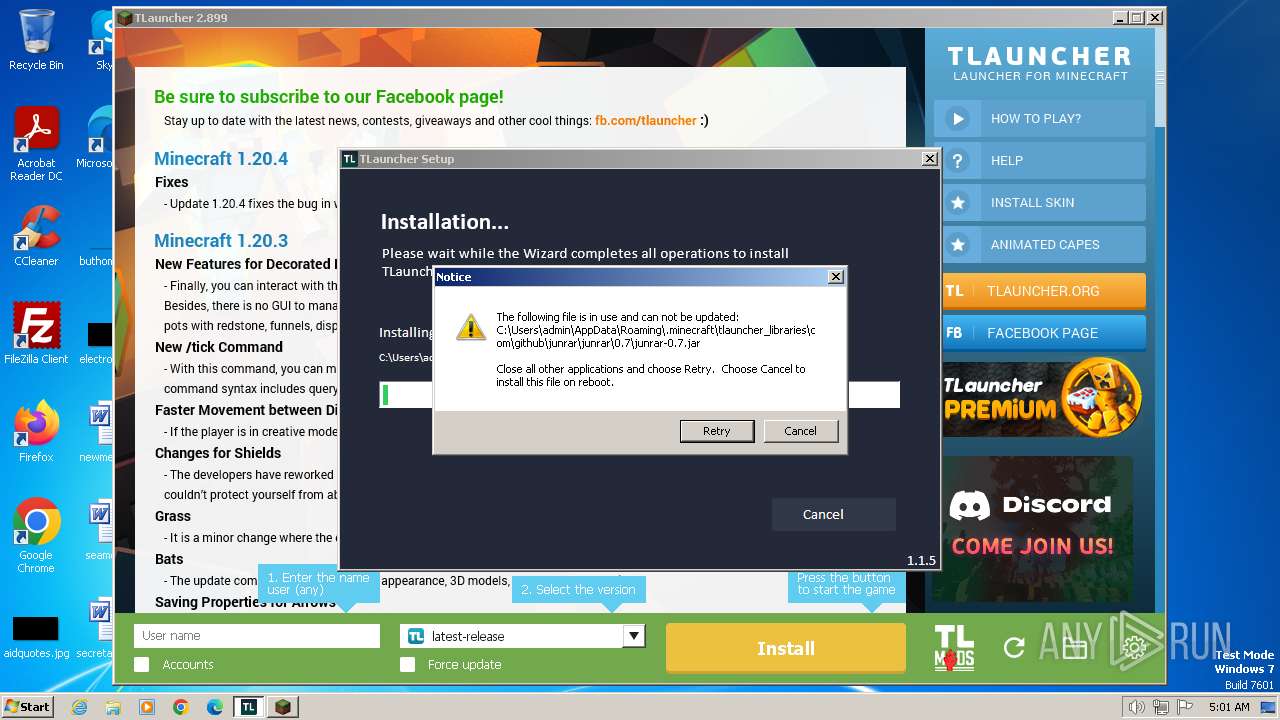
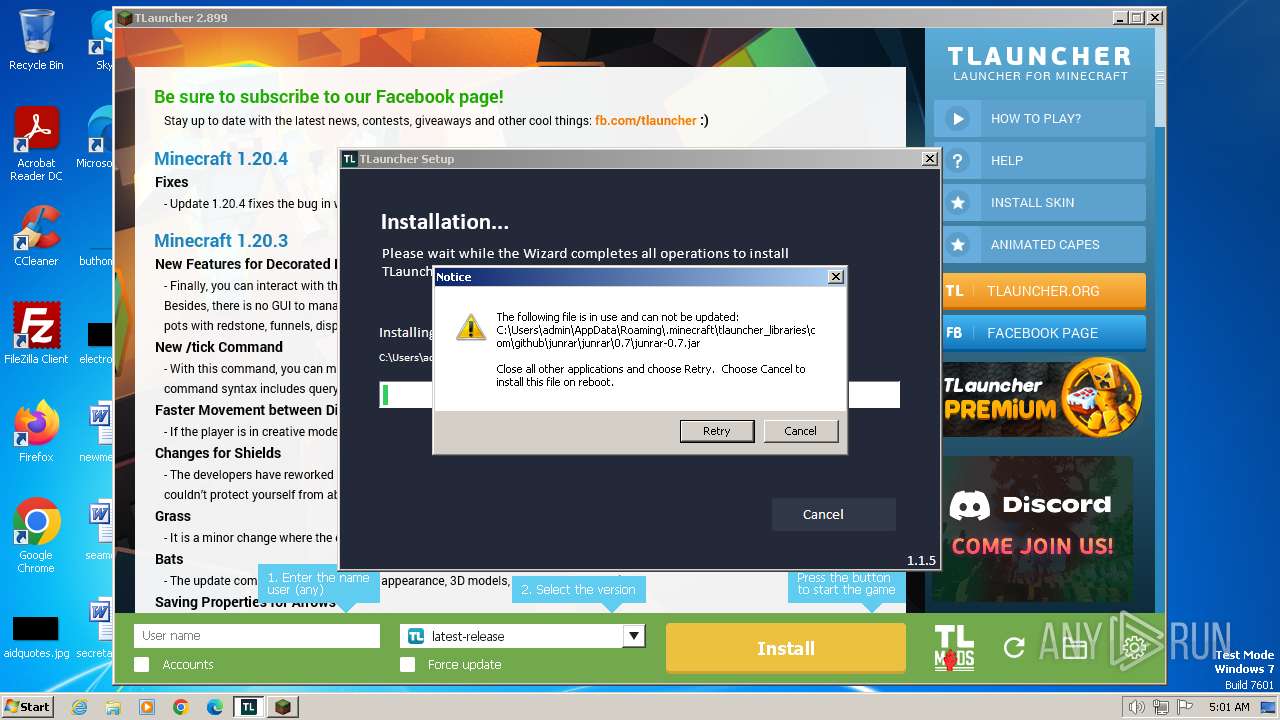
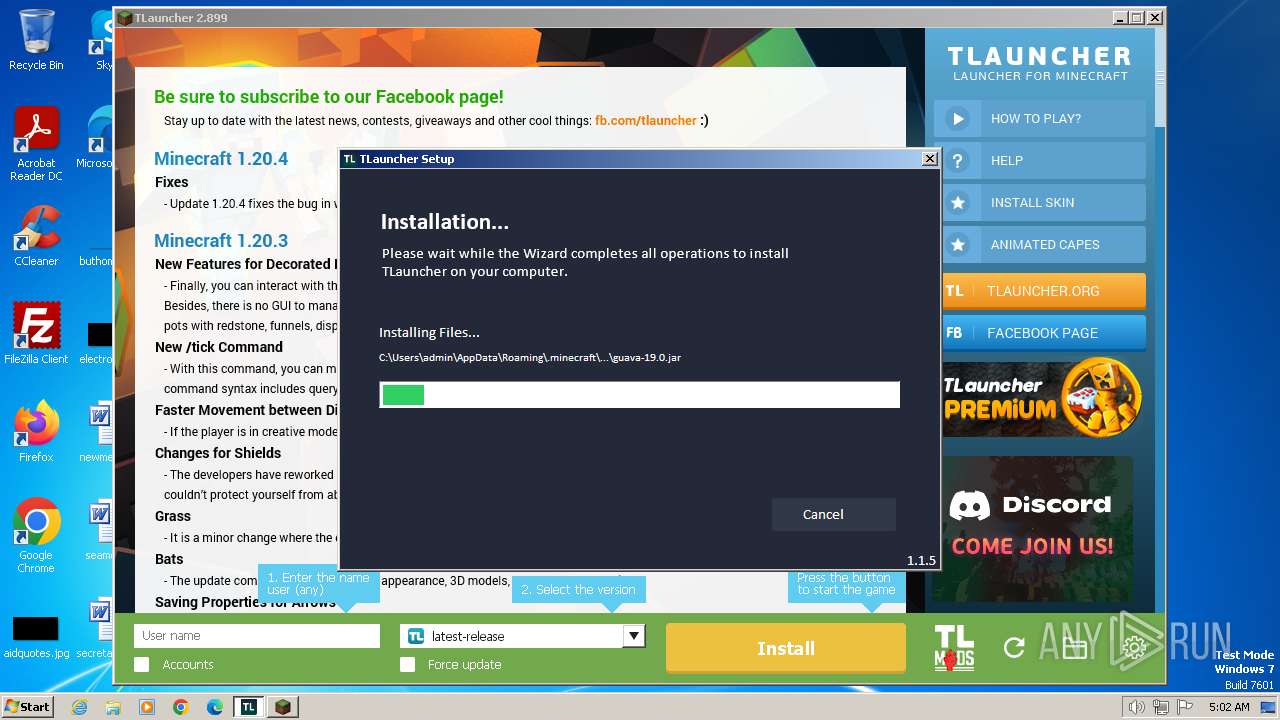
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2024, 04:57:58 |
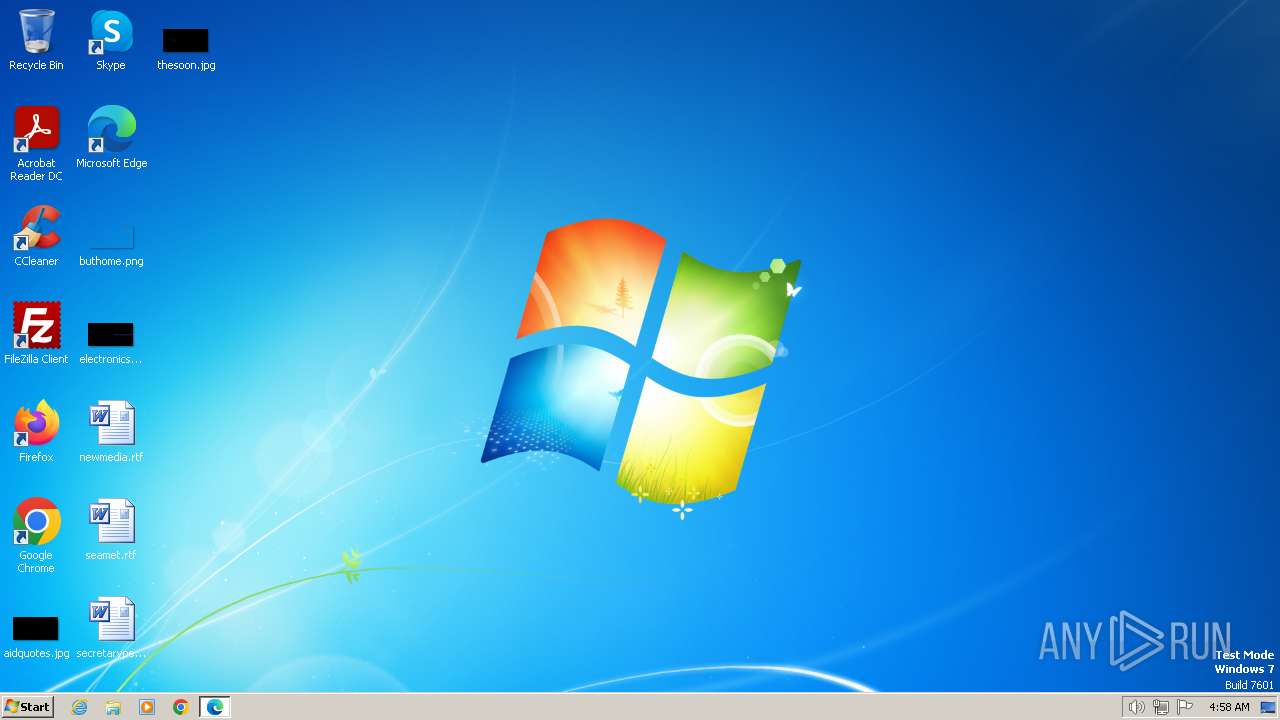
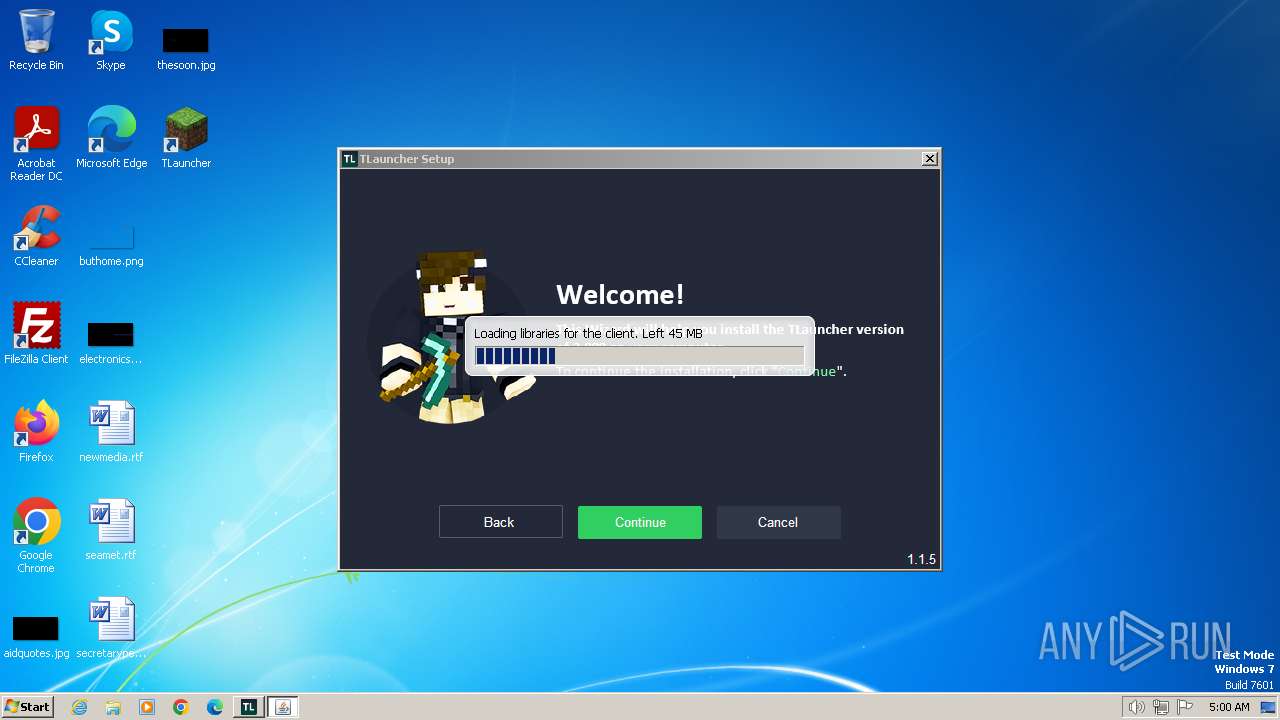
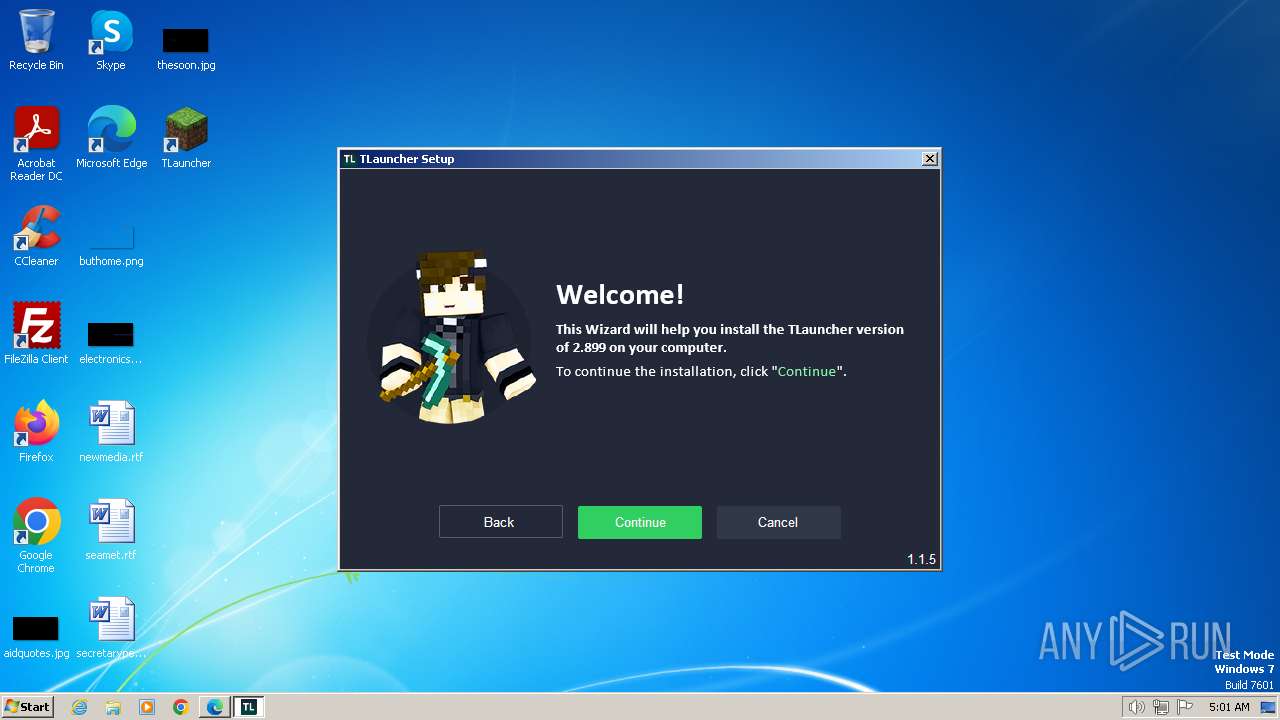
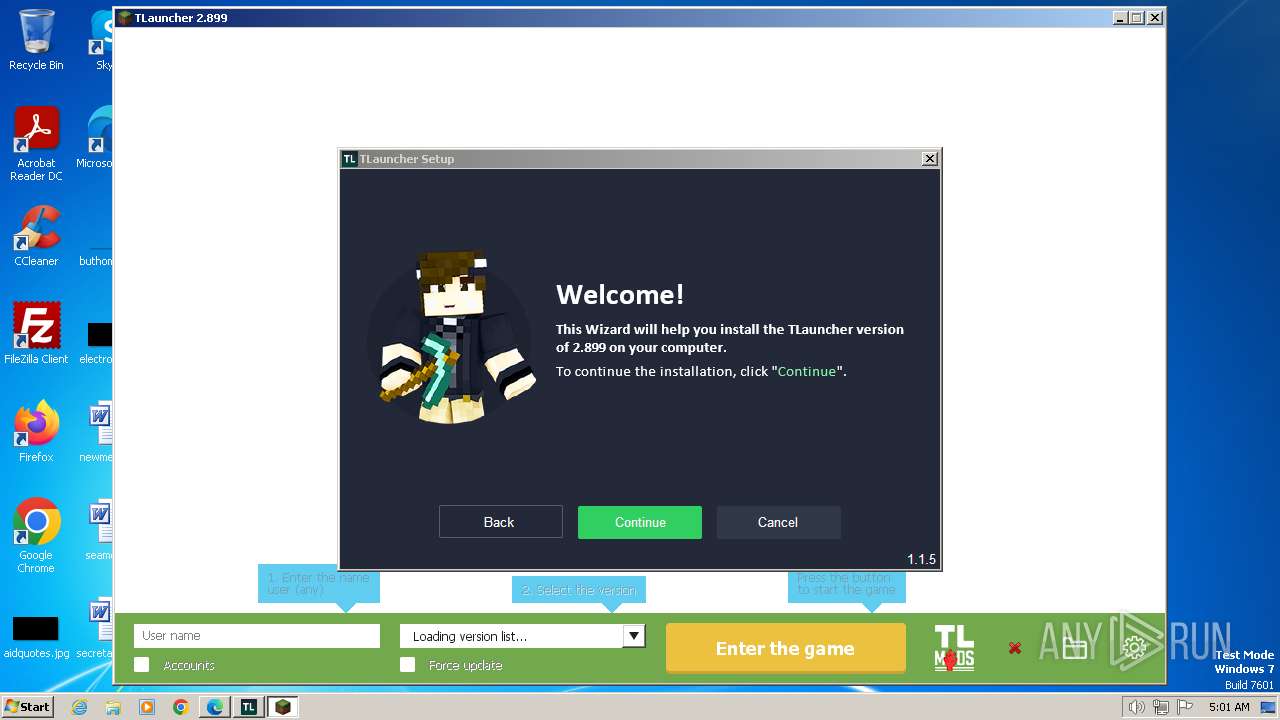
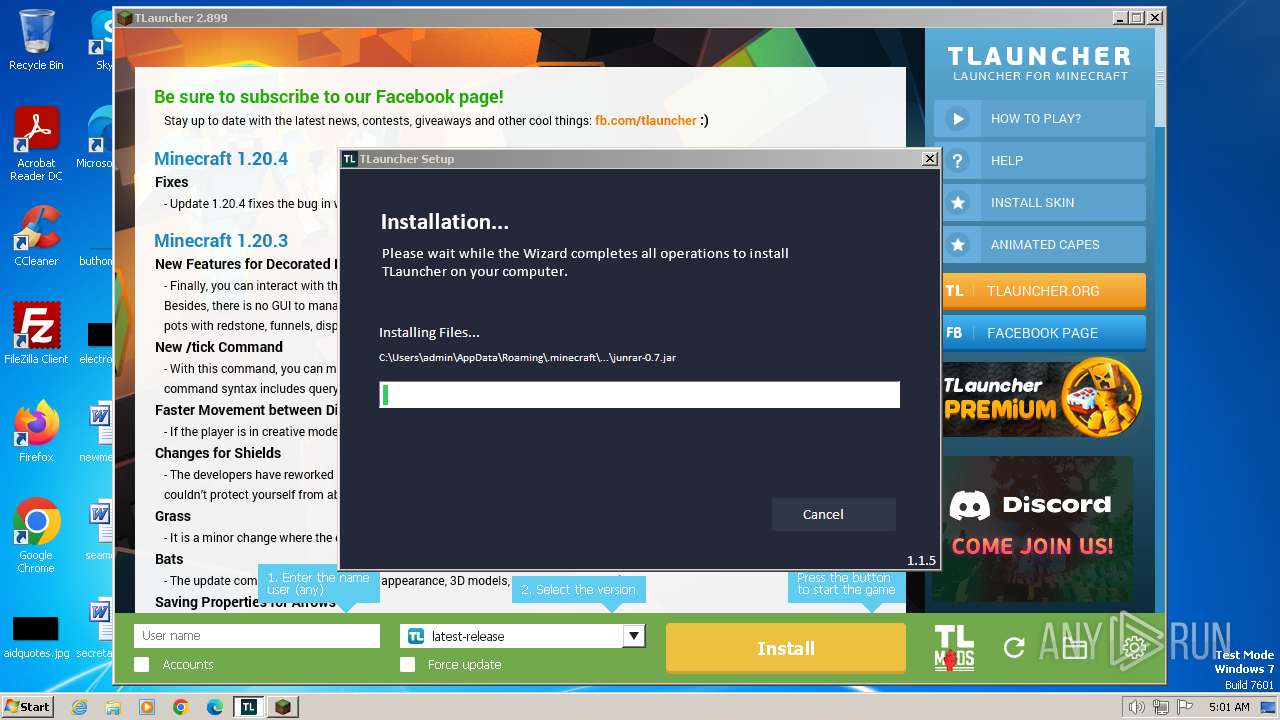
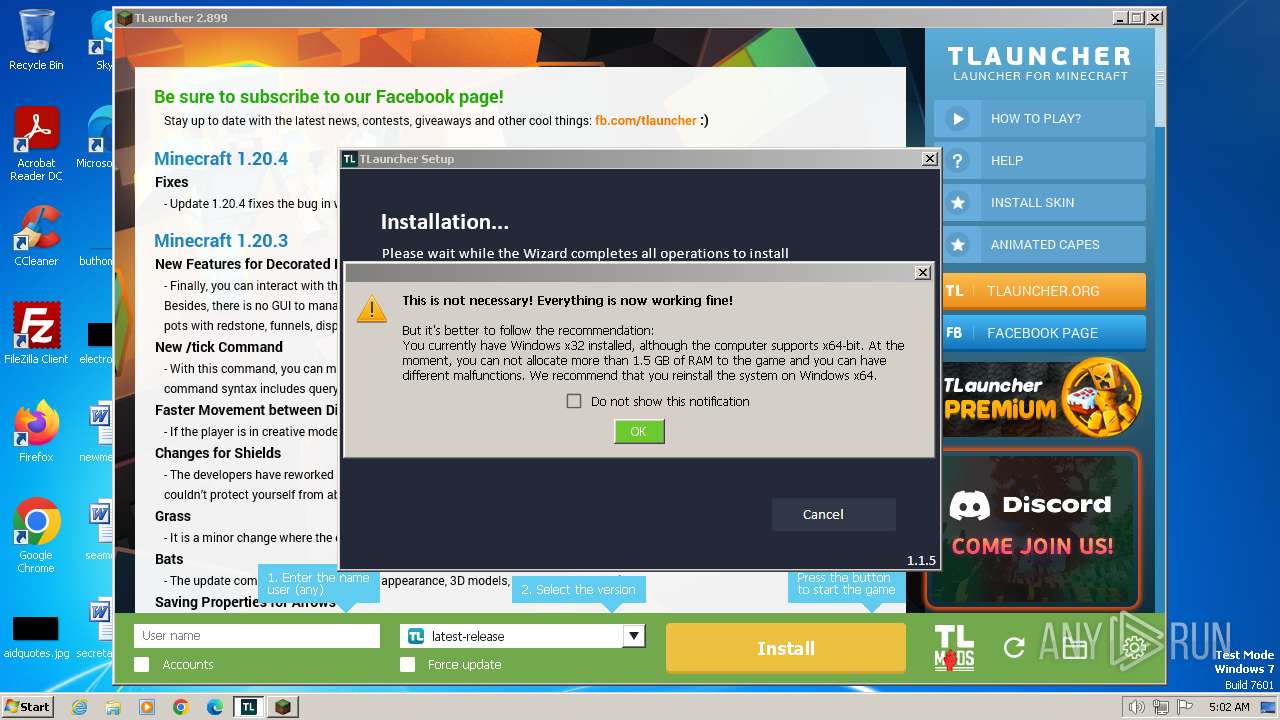
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
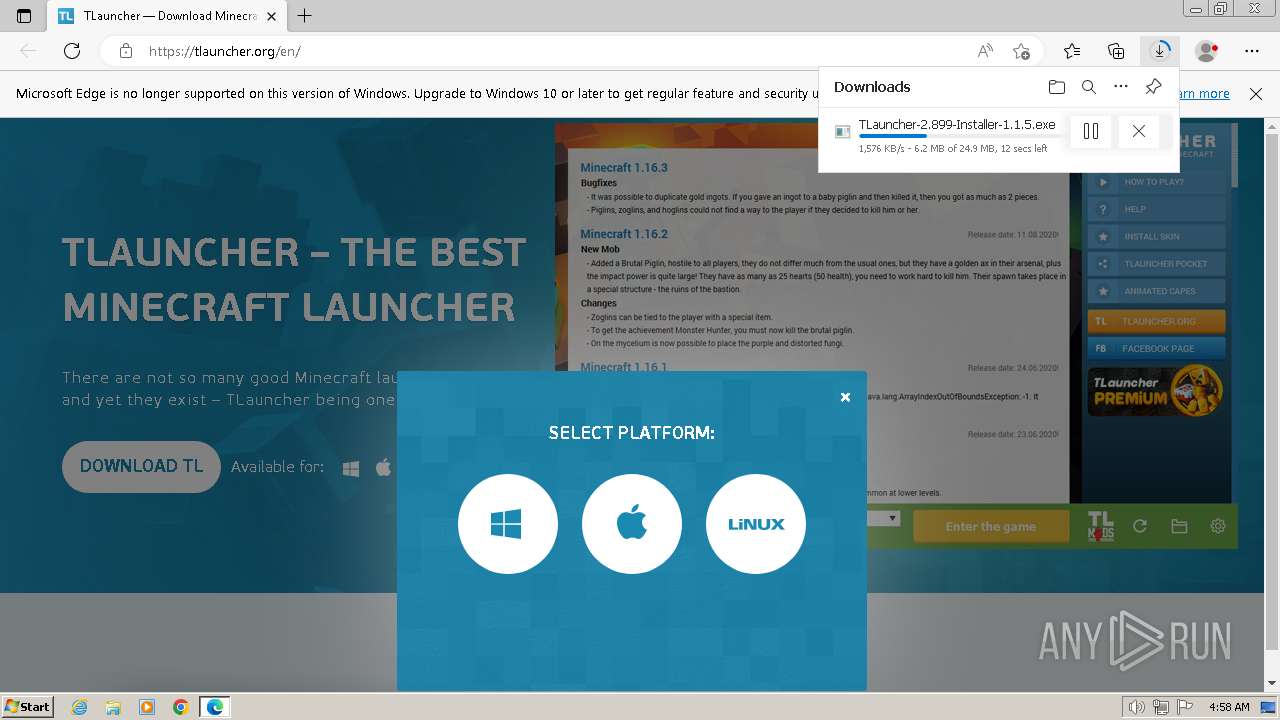
| MD5: | C146A57F50544DCA592397189220E6B5 |
| SHA1: | 91D2079252AA9D349CA4BFDD7CA031A8D9CEA748 |
| SHA256: | C322DB70597221ED0C6CC05BB9208F5EF70614DBA14B01209EB4015E9EF96868 |
| SSDEEP: | 3:N8BEeLu5A+:2K5F |
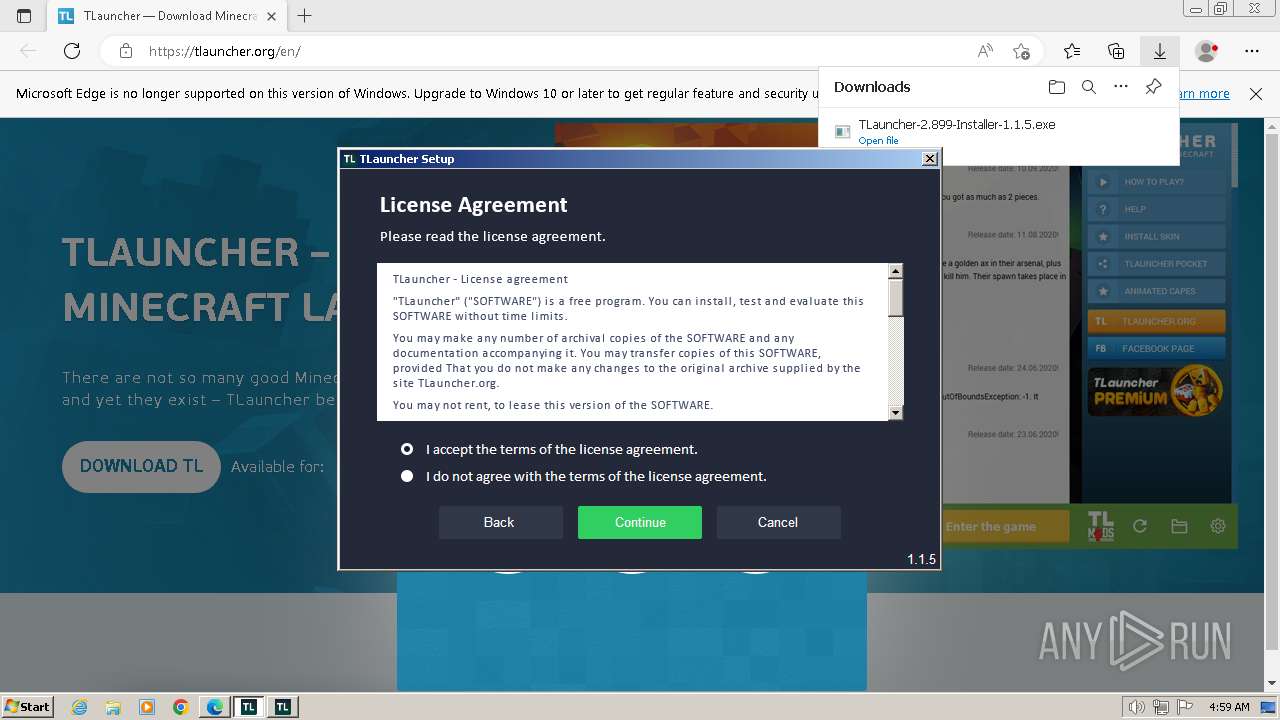
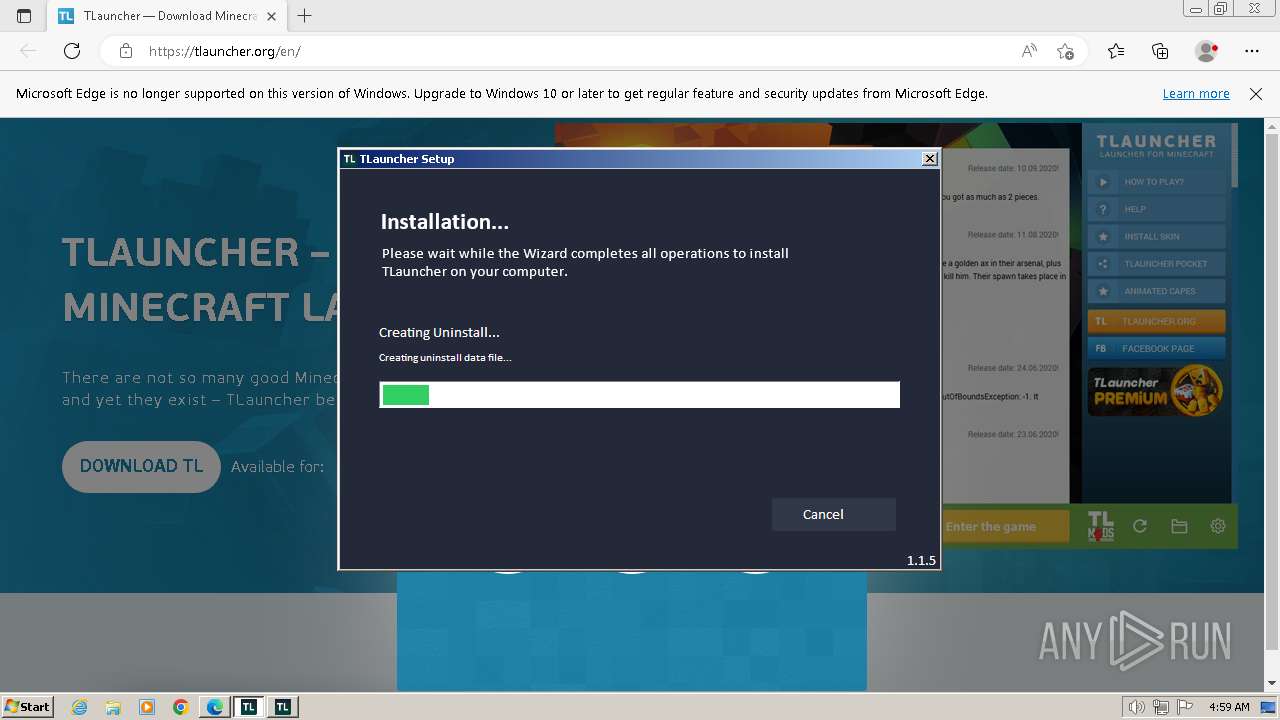
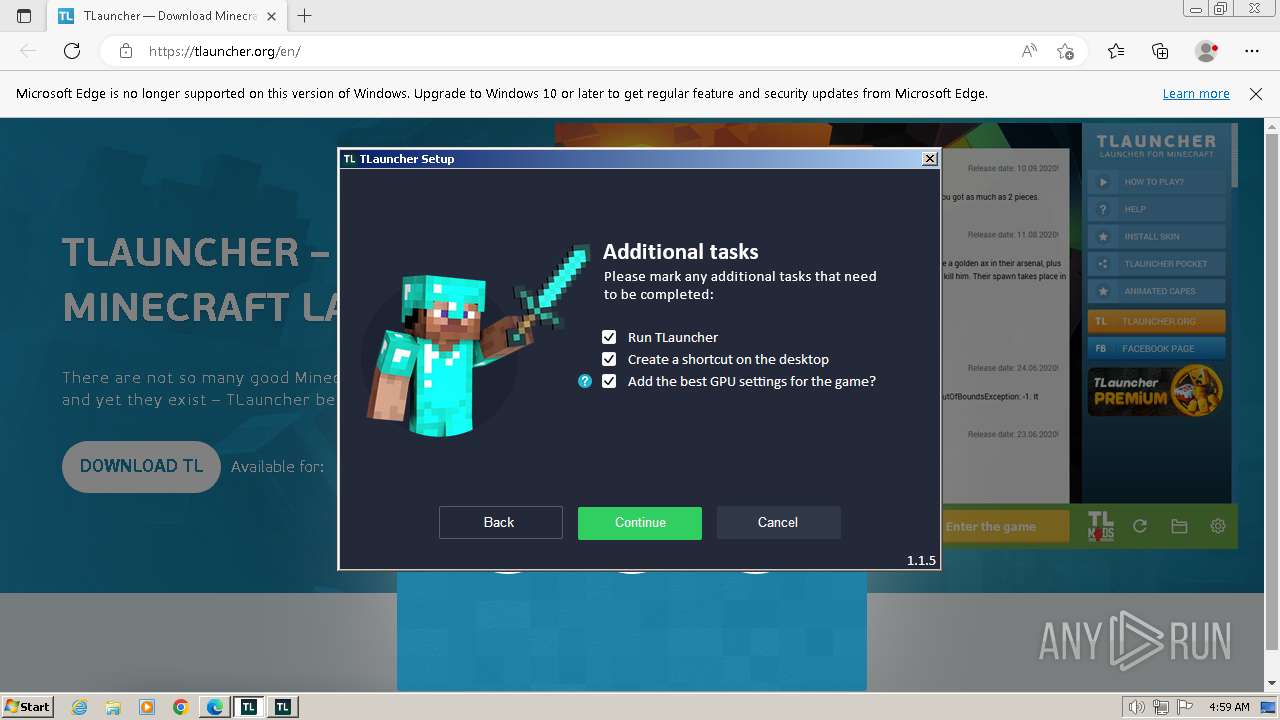
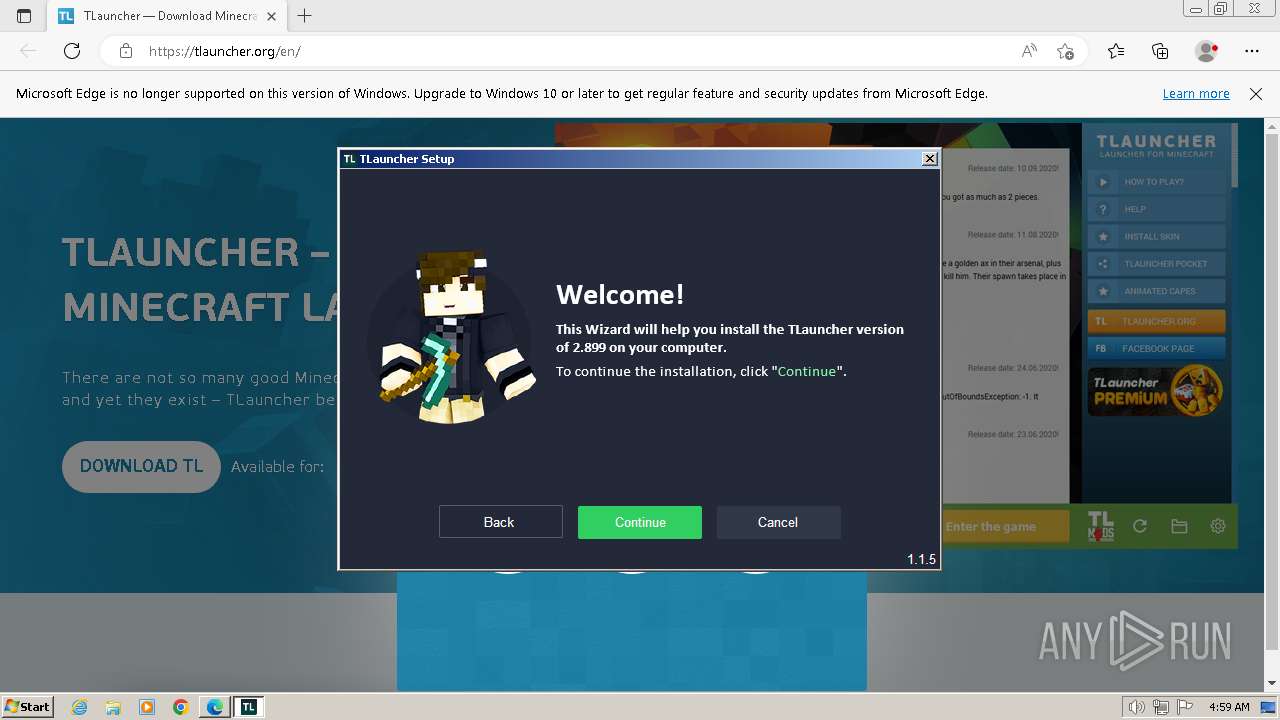
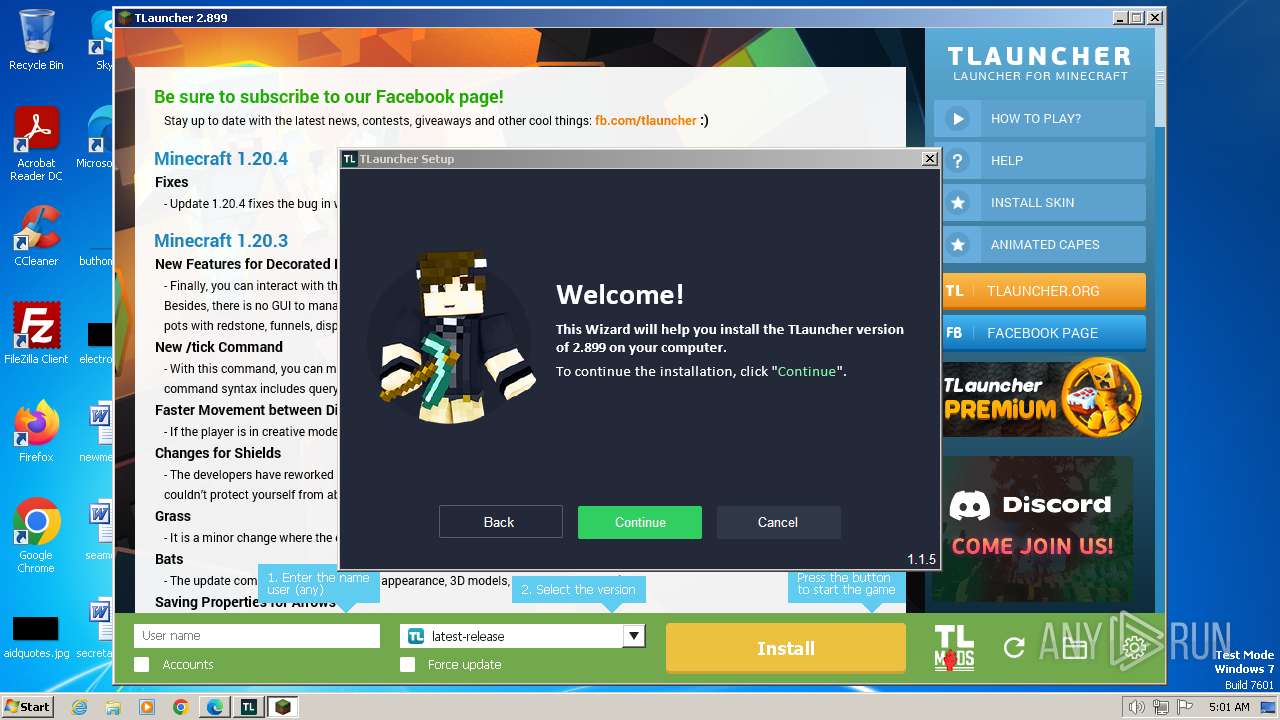
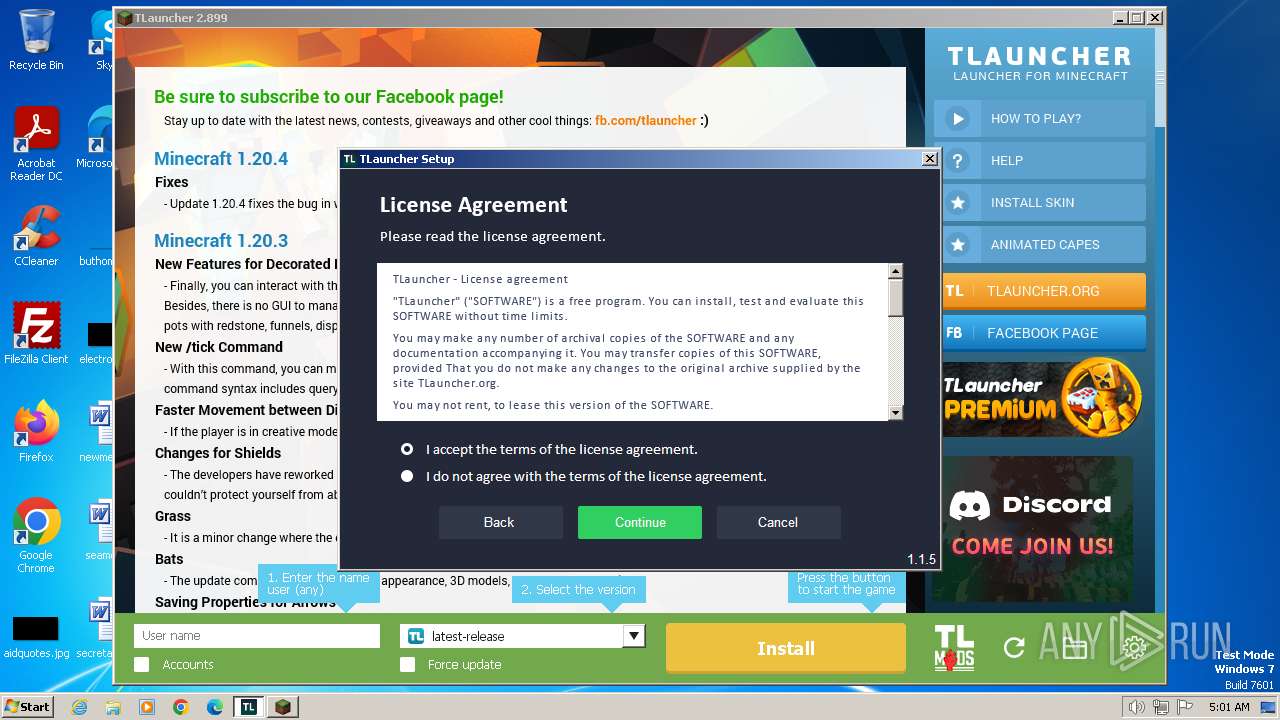
MALICIOUS
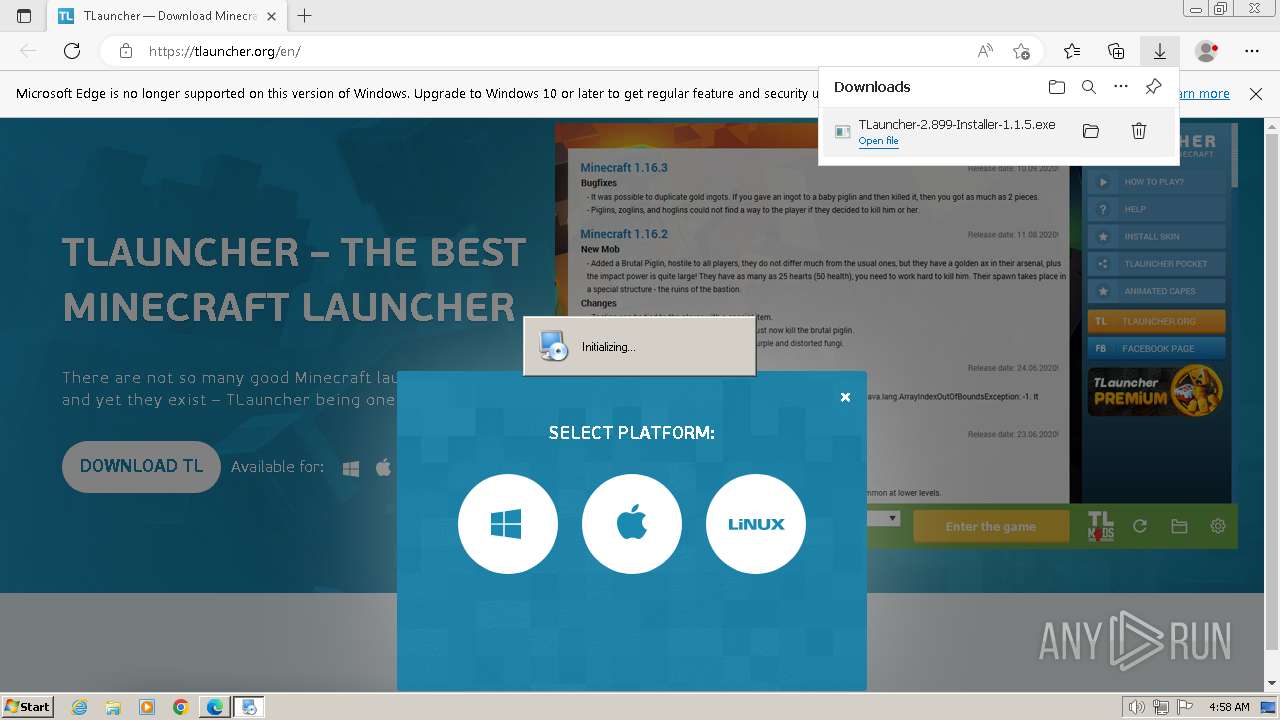
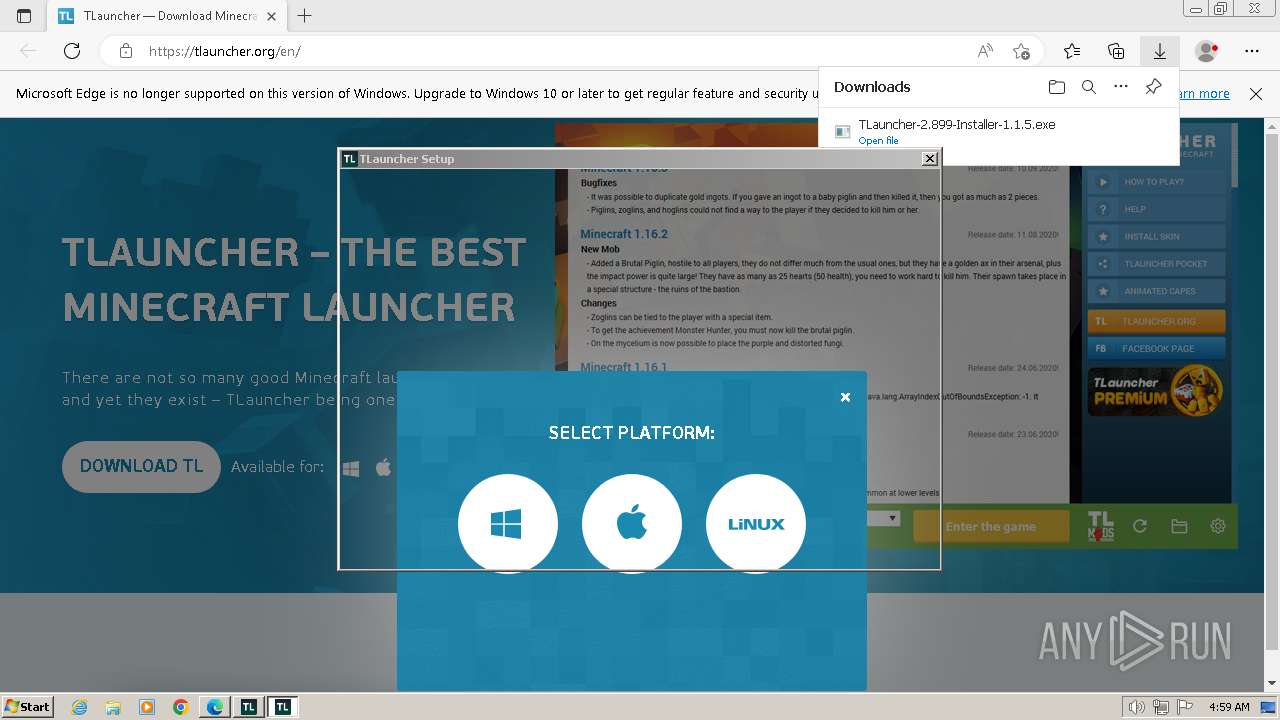
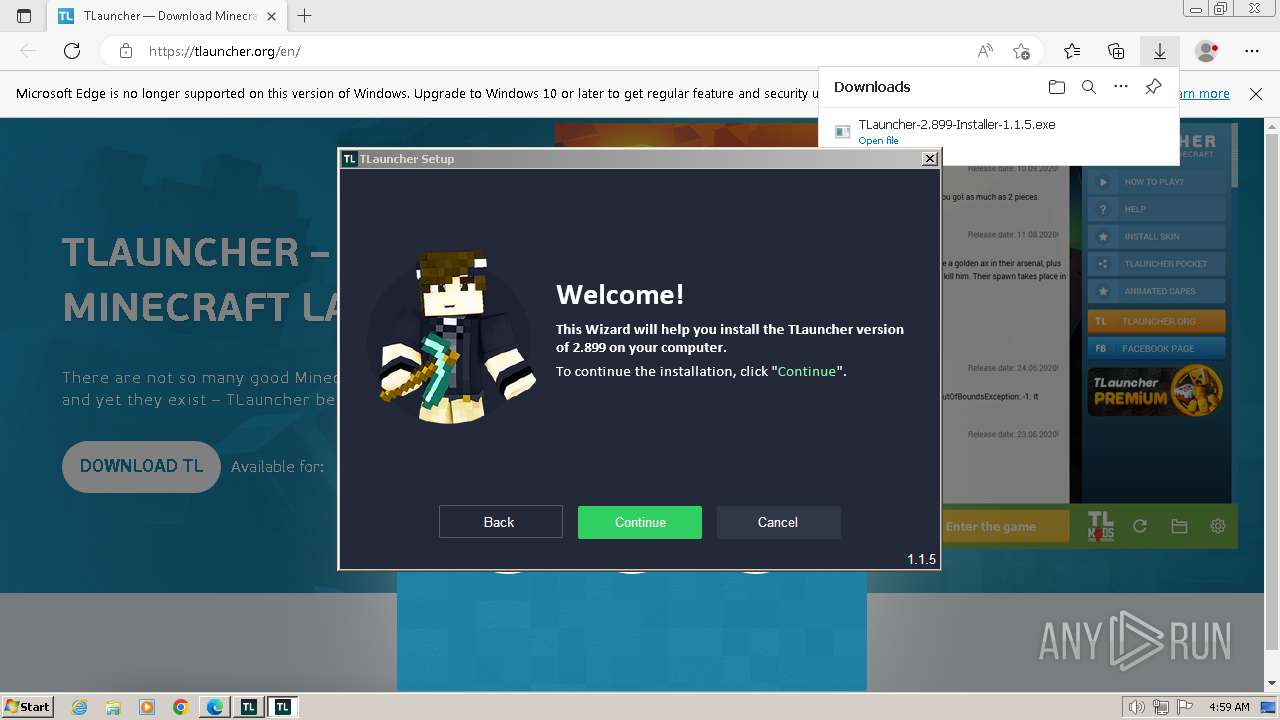
Drops the executable file immediately after the start
- TLauncher-2.899-Installer-1.1.5.exe (PID: 2104)
- TLauncher-2.899-Installer-1.1.5.exe (PID: 3436)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 668)
- BrowserInstaller.exe (PID: 2184)
- javaw.exe (PID: 1624)
- BrowserInstaller.exe (PID: 1404)
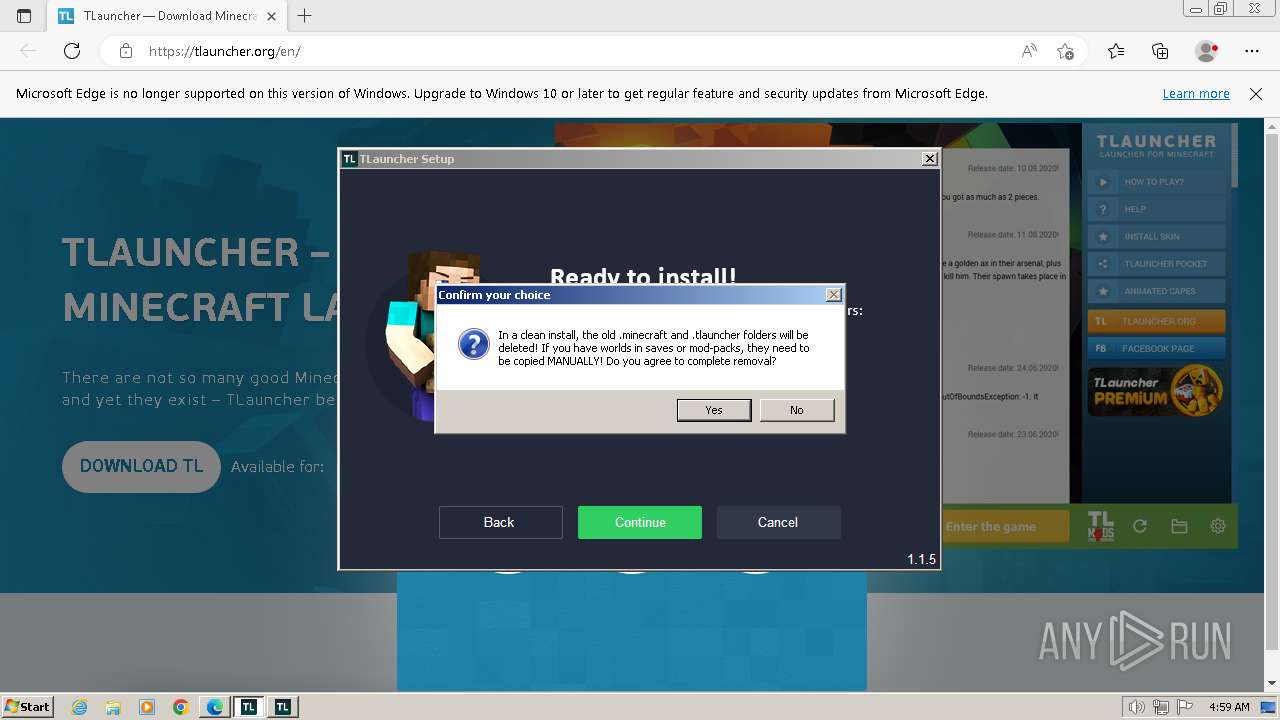
Actions looks like stealing of personal data
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
SUSPICIOUS
Reads the Internet Settings
- TLauncher-2.899-Installer-1.1.5.exe (PID: 2104)
- TLauncher-2.899-Installer-1.1.5.exe (PID: 3436)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 668)
- BrowserInstaller.exe (PID: 2184)
- irsetup.exe (PID: 3072)
- WMIC.exe (PID: 1584)
- WMIC.exe (PID: 3960)
- WMIC.exe (PID: 3868)
- BrowserInstaller.exe (PID: 1404)
- irsetup.exe (PID: 2760)
- WMIC.exe (PID: 2988)
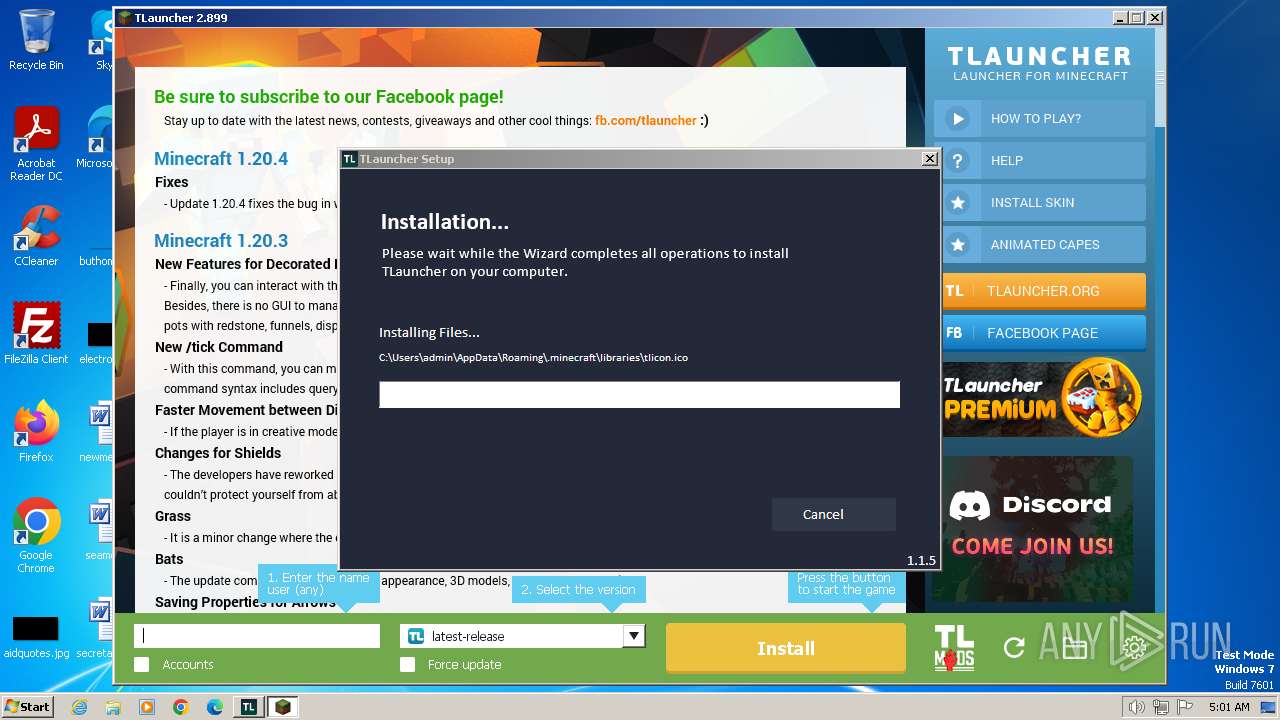
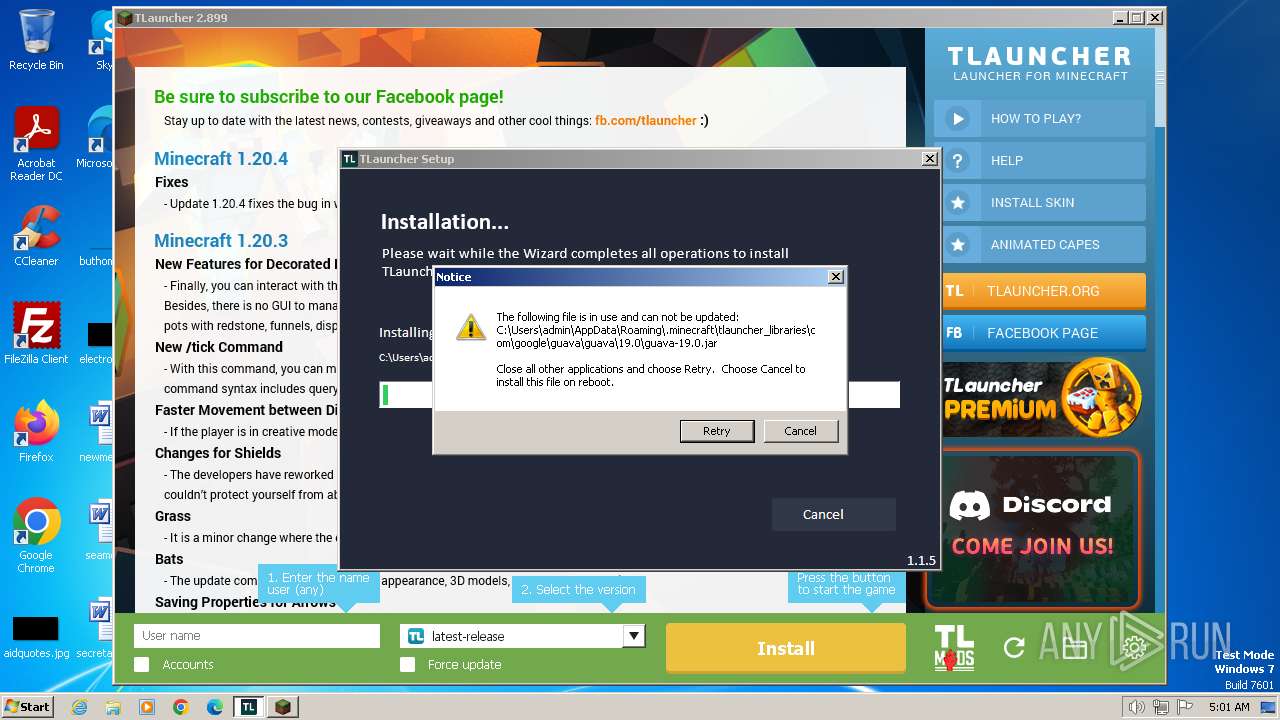
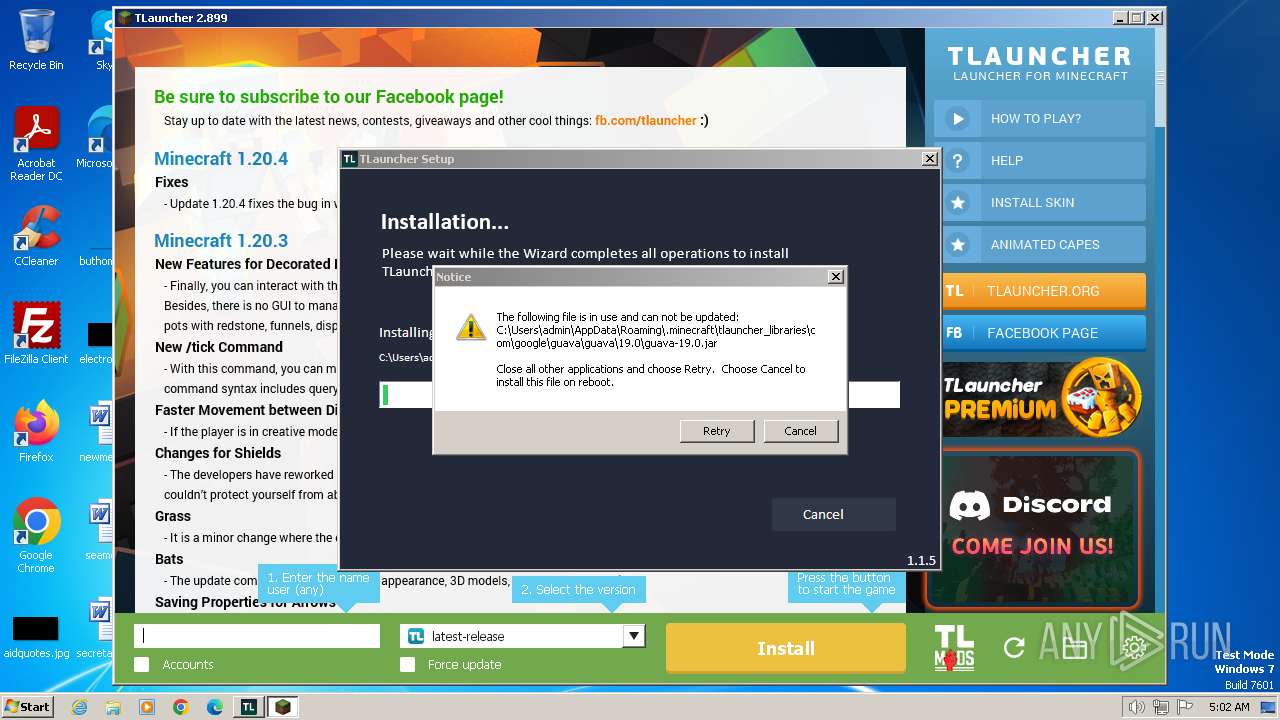
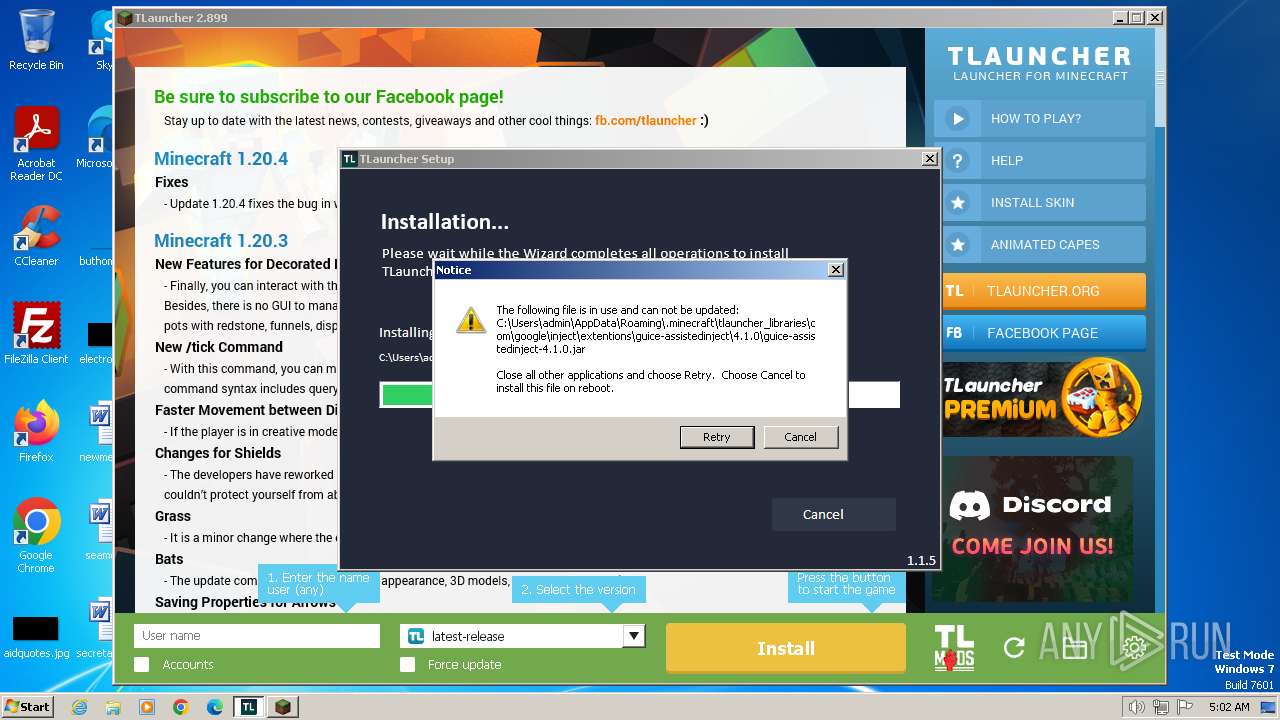
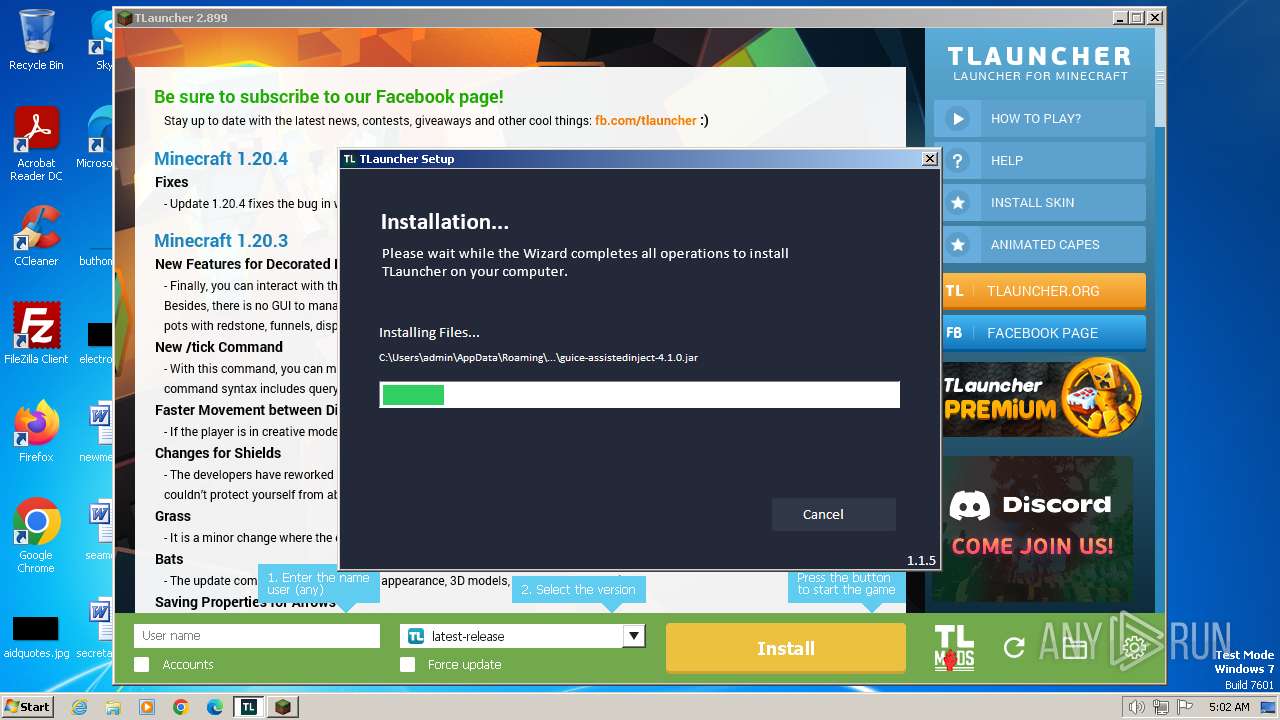
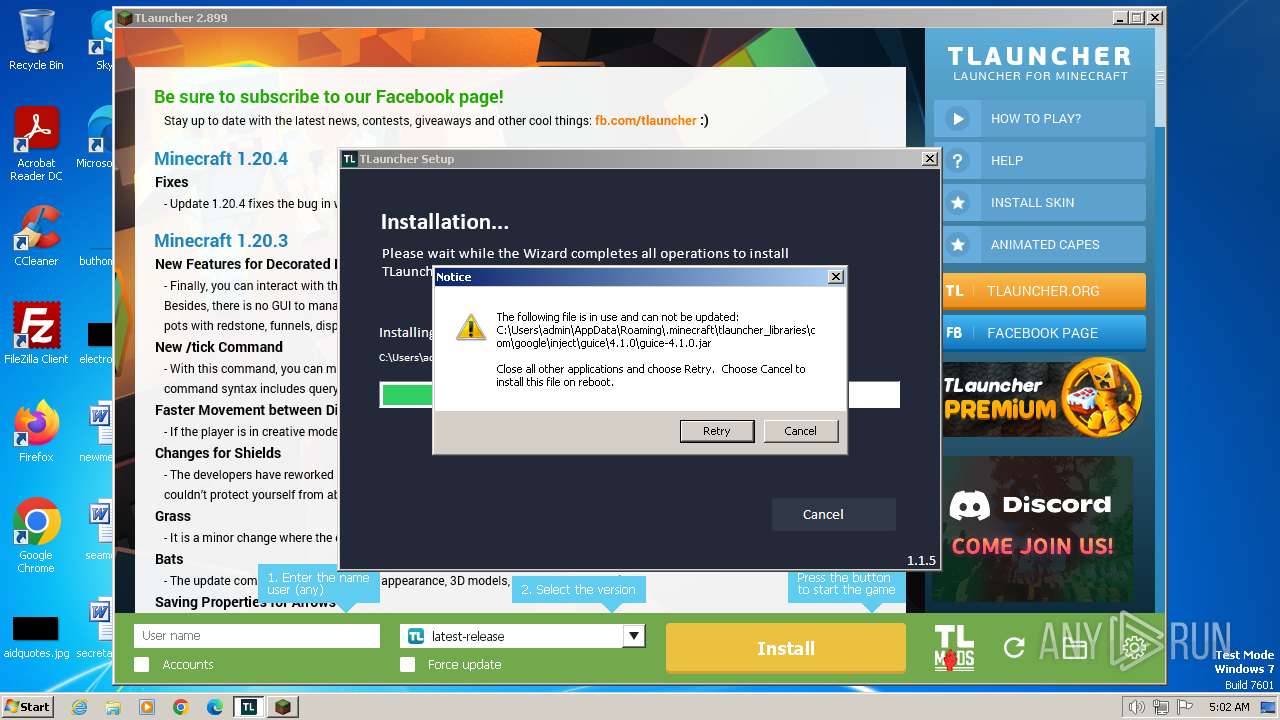
Executable content was dropped or overwritten
- TLauncher-2.899-Installer-1.1.5.exe (PID: 2104)
- TLauncher-2.899-Installer-1.1.5.exe (PID: 3436)
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
- BrowserInstaller.exe (PID: 2184)
- javaw.exe (PID: 1624)
- BrowserInstaller.exe (PID: 1404)
Reads security settings of Internet Explorer
- TLauncher-2.899-Installer-1.1.5.exe (PID: 2104)
- TLauncher-2.899-Installer-1.1.5.exe (PID: 3436)
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
- BrowserInstaller.exe (PID: 2184)
- irsetup.exe (PID: 3072)
- BrowserInstaller.exe (PID: 1404)
- irsetup.exe (PID: 2760)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 3072)
- irsetup.exe (PID: 2760)
Checks for Java to be installed
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 668)
- TLauncher.exe (PID: 712)
Reads settings of System Certificates
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 3072)
- dxdiag.exe (PID: 1892)
- irsetup.exe (PID: 2760)
Checks Windows Trust Settings
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 3072)
- irsetup.exe (PID: 2760)
Adds/modifies Windows certificates
- irsetup.exe (PID: 668)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
Reads Internet Explorer settings
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 668)
Creates a software uninstall entry
- irsetup.exe (PID: 668)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 1624)
- javaw.exe (PID: 3756)
Starts application with an unusual extension
- cmd.exe (PID: 2308)
- cmd.exe (PID: 1628)
- cmd.exe (PID: 1544)
- cmd.exe (PID: 3180)
- cmd.exe (PID: 3388)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 3960)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 2308)
- cmd.exe (PID: 1628)
Process drops legitimate windows executable
- javaw.exe (PID: 1624)
The process drops C-runtime libraries
- javaw.exe (PID: 1624)
Process requests binary or script from the Internet
- javaw.exe (PID: 3756)
Uses ICACLS.EXE to modify access control lists
- javaw.exe (PID: 3756)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 3180)
Creates/Modifies COM task schedule object
- dxdiag.exe (PID: 1892)
Uses WMIC.EXE to obtain quick Fix Engineering (patches) data
- cmd.exe (PID: 3960)
INFO
Application launched itself
- msedge.exe (PID: 3700)
Executable content was dropped or overwritten
- msedge.exe (PID: 3700)
- msedge.exe (PID: 1040)
Drops the executable file immediately after the start
- msedge.exe (PID: 3700)
- msedge.exe (PID: 1040)
The process uses the downloaded file
- msedge.exe (PID: 3232)
- msedge.exe (PID: 3700)
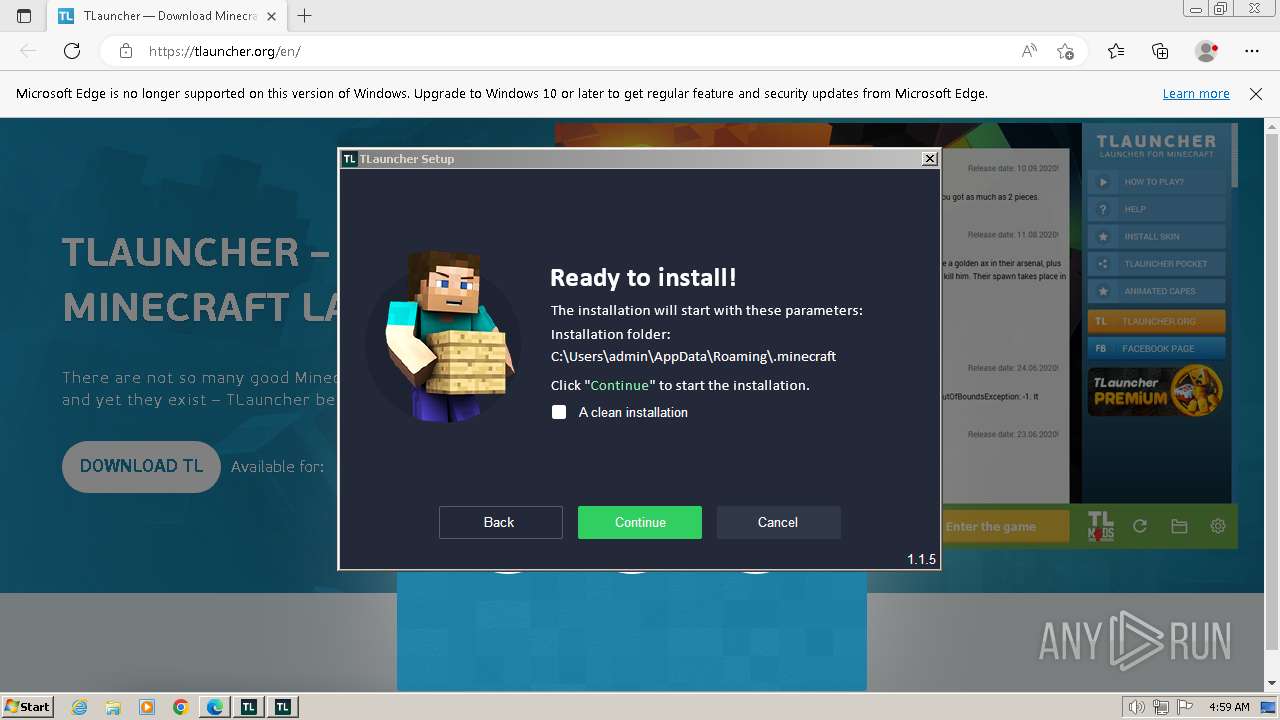
Create files in a temporary directory
- TLauncher-2.899-Installer-1.1.5.exe (PID: 2104)
- irsetup.exe (PID: 668)
- TLauncher-2.899-Installer-1.1.5.exe (PID: 3436)
- irsetup.exe (PID: 2824)
- BrowserInstaller.exe (PID: 2184)
- irsetup.exe (PID: 3072)
- javaw.exe (PID: 1624)
- javaw.exe (PID: 3756)
- BrowserInstaller.exe (PID: 1404)
- irsetup.exe (PID: 2760)
Checks supported languages
- TLauncher-2.899-Installer-1.1.5.exe (PID: 2104)
- irsetup.exe (PID: 668)
- TLauncher-2.899-Installer-1.1.5.exe (PID: 3436)
- irsetup.exe (PID: 2824)
- BrowserInstaller.exe (PID: 2184)
- TLauncher.exe (PID: 712)
- irsetup.exe (PID: 3072)
- chcp.com (PID: 2808)
- javaw.exe (PID: 1624)
- chcp.com (PID: 1876)
- javaw.exe (PID: 3756)
- chcp.com (PID: 2372)
- chcp.com (PID: 3404)
- chcp.com (PID: 2520)
- chcp.com (PID: 2572)
- chcp.com (PID: 968)
- BrowserInstaller.exe (PID: 1404)
- irsetup.exe (PID: 2760)
Reads the computer name
- TLauncher-2.899-Installer-1.1.5.exe (PID: 2104)
- TLauncher-2.899-Installer-1.1.5.exe (PID: 3436)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 668)
- BrowserInstaller.exe (PID: 2184)
- irsetup.exe (PID: 3072)
- javaw.exe (PID: 1624)
- javaw.exe (PID: 3756)
- BrowserInstaller.exe (PID: 1404)
- irsetup.exe (PID: 2760)
Checks proxy server information
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 3072)
- irsetup.exe (PID: 2760)
Reads the machine GUID from the registry
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 3072)
- javaw.exe (PID: 1624)
- javaw.exe (PID: 3756)
- irsetup.exe (PID: 2760)
Reads the software policy settings
- irsetup.exe (PID: 668)
- irsetup.exe (PID: 2824)
- irsetup.exe (PID: 3072)
- dxdiag.exe (PID: 1892)
- irsetup.exe (PID: 2760)
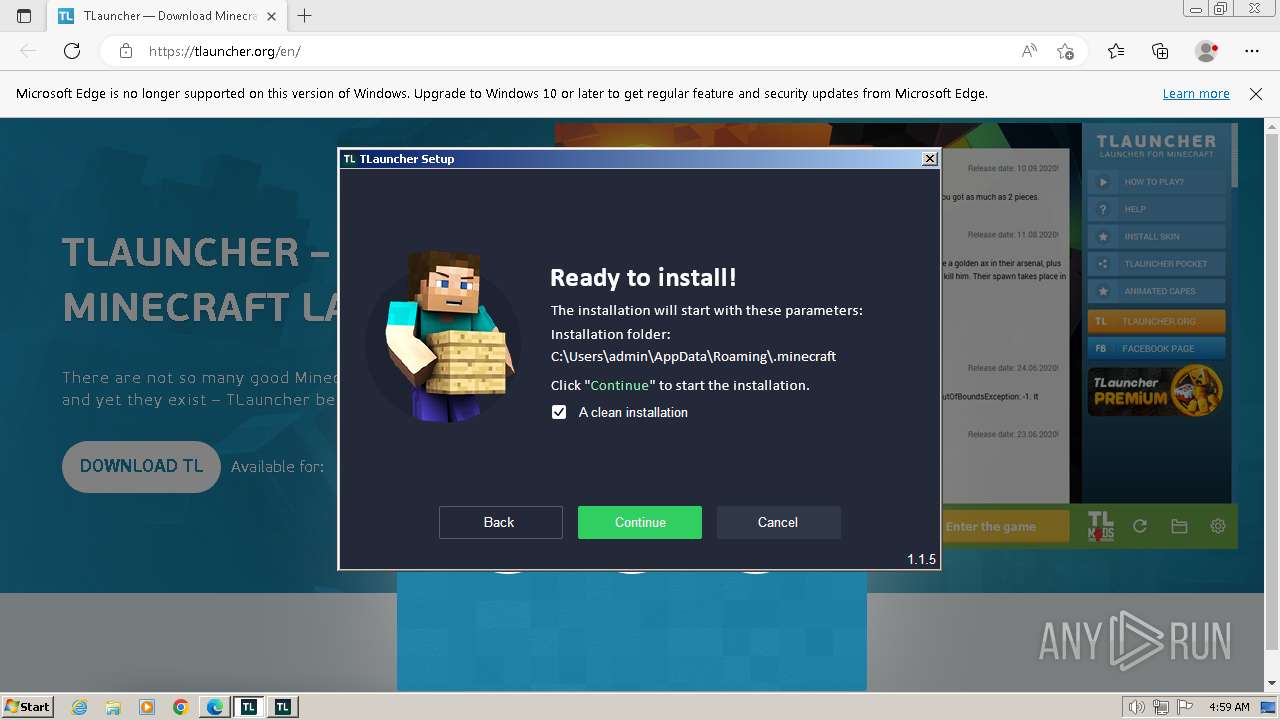
Creates files in the program directory
- irsetup.exe (PID: 668)
- javaw.exe (PID: 1624)
- javaw.exe (PID: 3756)
Creates files or folders in the user directory
- irsetup.exe (PID: 3072)
- irsetup.exe (PID: 668)
- javaw.exe (PID: 1624)
- javaw.exe (PID: 3756)
- irsetup.exe (PID: 2824)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 1892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
116
Monitored processes
57
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
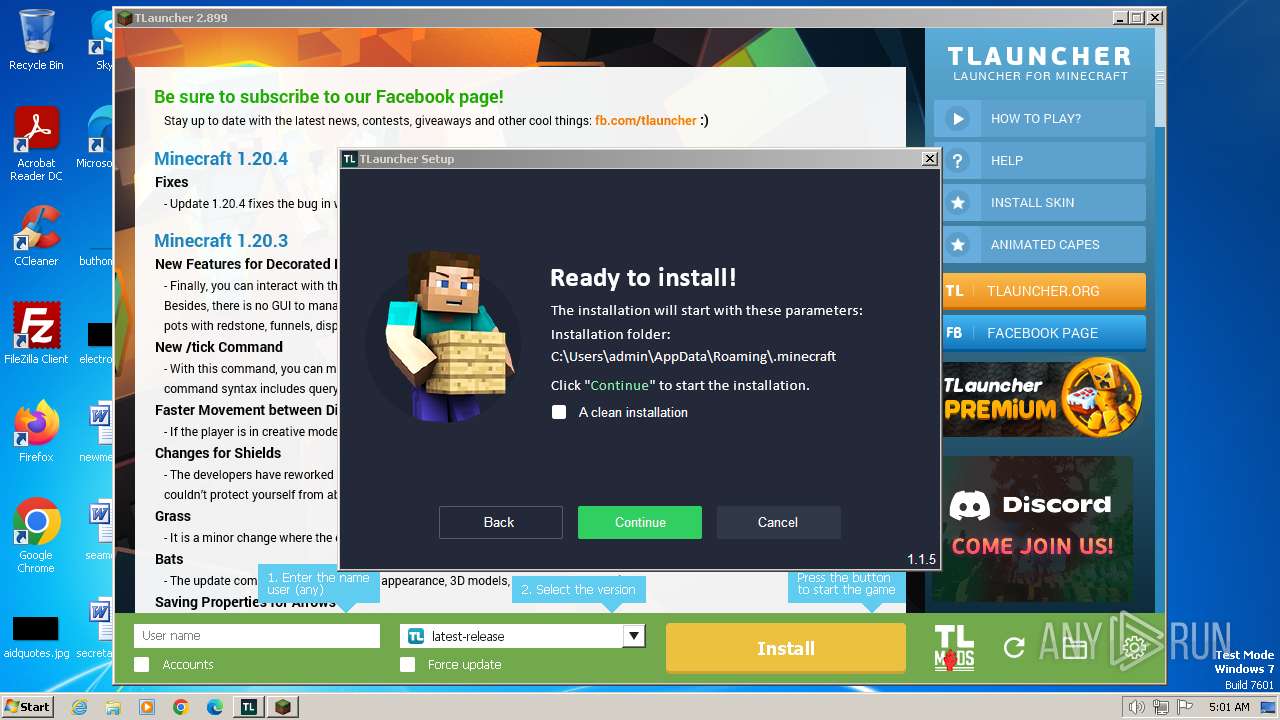
| 548 | "C:\Users\admin\Downloads\TLauncher-2.899-Installer-1.1.5.exe" | C:\Users\admin\Downloads\TLauncher-2.899-Installer-1.1.5.exe | — | msedge.exe | |||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Setup Exit code: 3221226540 Version: 1.1.5.0 Modules
| |||||||||||||||
| 668 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:1910546 "__IRAFN:C:\Users\admin\Downloads\TLauncher-2.899-Installer-1.1.5.exe" "__IRCT:3" "__IRTSS:26073958" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | TLauncher-2.899-Installer-1.1.5.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.3.0 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3740 --field-trial-handle=1368,i,8831119661634703007,14809189091731912993,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 712 | "C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe" | C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe | — | irsetup.exe | |||||||||||
User: admin Company: TLauncher Inc. Integrity Level: HIGH Description: TLauncher Exit code: 0 Version: 2.899 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1636 --field-trial-handle=1368,i,8831119661634703007,14809189091731912993,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 968 | chcp 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4436 --field-trial-handle=1368,i,8831119661634703007,14809189091731912993,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1472 --field-trial-handle=1368,i,8831119661634703007,14809189091731912993,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1264 | "C:\Users\admin\Downloads\TLauncher-2.899-Installer-1.1.5.exe" | C:\Users\admin\Downloads\TLauncher-2.899-Installer-1.1.5.exe | — | msedge.exe | |||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Setup Exit code: 3221226540 Version: 1.1.5.0 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3852 --field-trial-handle=1368,i,8831119661634703007,14809189091731912993,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
58 982
Read events
58 431
Write events
484
Delete events
67
Modification events
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 506711ECC3702F00 | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3700) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
144
Suspicious files
109
Text files
771
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17f50e.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17f52d.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17f55c.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF17f50e.TMP | text | |
MD5:A9B940DA81B2E13D048EBB32E79FA414 | SHA256:9061129705411EA6CFDD34177BF841CC85EB857BA909D3C4AA69BE8A5C59A8B0 | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f52d.TMP | text | |
MD5:AB24748B6383043489AC0960A5BBCA45 | SHA256:502CF9B7B647DC938CB1C9A0F7E50B13087881494E81D81420BFB425BC02DD4B | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:0FFCDE9AA0F7BF34DC35C8AEADCA5BA5 | SHA256:5A9F6E7DDB2557B2C5921117AE4D6A407BB2504F6728DD1352FF88492E0ECC3D | |||
| 3700 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:DF0BCCD68449F07F531D76F53C718178 | SHA256:12025F4DA9E53A8B91892D4F6E6A9B89513F3488BFE9F1EEEC3C05F7EF96BDD8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
62
DNS requests
51
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3072 | irsetup.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | binary | 2.18 Kb | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?89bca2e7018c82c0 | GB | compressed | 65.2 Kb | unknown |
1624 | javaw.exe | GET | 302 | 78.46.66.120:80 | http://res.tlauncher.org/unb/client/jre/windows/jre-8u111-windows-i586.tar.gz | DE | — | — | unknown |
1624 | javaw.exe | GET | 302 | 78.46.66.120:80 | http://res.tlauncher.org/b/client/jre/windows/jre-8u111-windows-i586.tar.gz | DE | — | — | unknown |
3072 | irsetup.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fea87acf361fbe14 | GB | — | — | unknown |
3756 | javaw.exe | HEAD | 200 | 104.20.65.88:80 | http://page.tlauncher.org/ | unknown | — | — | unknown |
1624 | javaw.exe | GET | 200 | 78.46.66.120:80 | http://cdn3-res.tlauncher.org/client/jre/windows/jre-8u111-windows-i586.tar.gz | DE | compressed | 59.4 Mb | unknown |
3756 | javaw.exe | GET | 200 | 104.26.11.134:80 | http://img.fastrepo.org/update/downloads/configs/client/video/tl-discord-en.png | US | image | 49.2 Kb | unknown |
3756 | javaw.exe | GET | 200 | 104.20.64.88:80 | http://repo.tlauncher.org/update/downloads/configs/inner_servers-1.1.json | unknown | text | 5.02 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1040 | msedge.exe | 104.20.65.88:443 | tlauncher.org | CLOUDFLARENET | — | unknown |
3700 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
1040 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1040 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1040 | msedge.exe | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
1040 | msedge.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1040 | msedge.exe | 104.16.57.101:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
tlauncher.org |
| unknown |
edge.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
hcaptcha.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
www.gstatic.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |
1624 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
1624 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
1624 | javaw.exe | A Network Trojan was detected | ET HUNTING suspicious - gzipped file via JAVA - could be pack200-ed JAR |