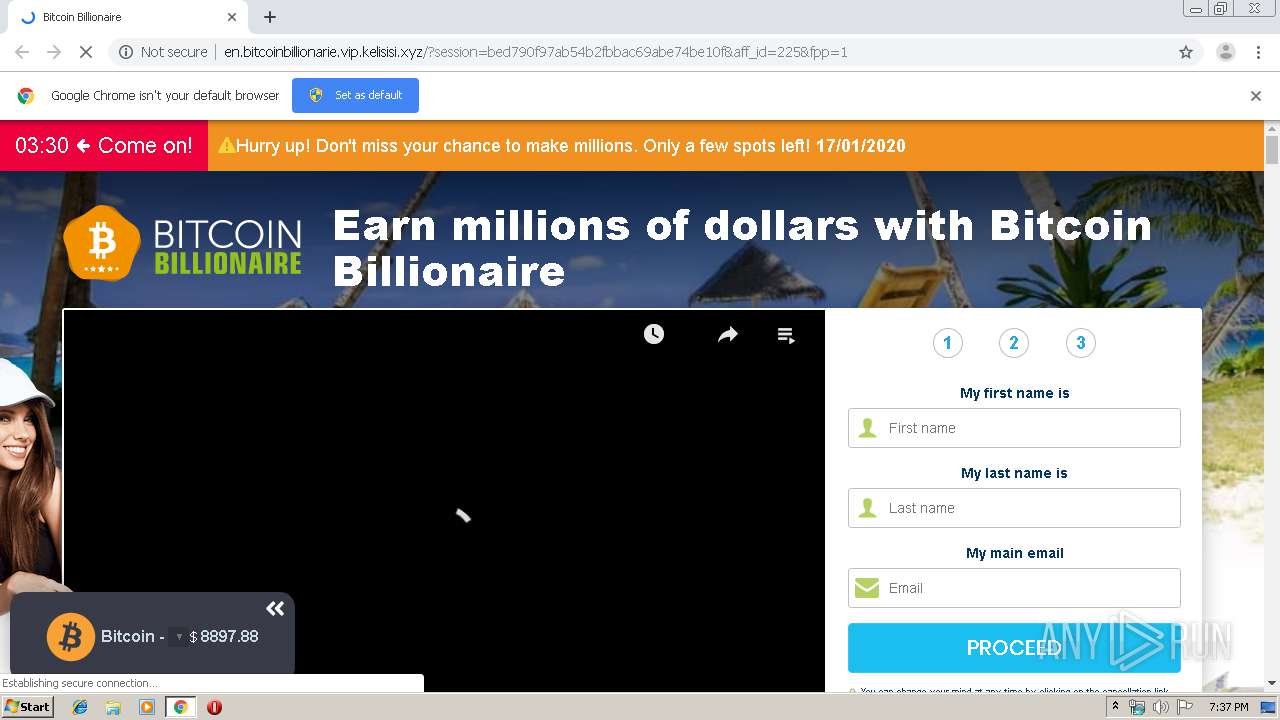
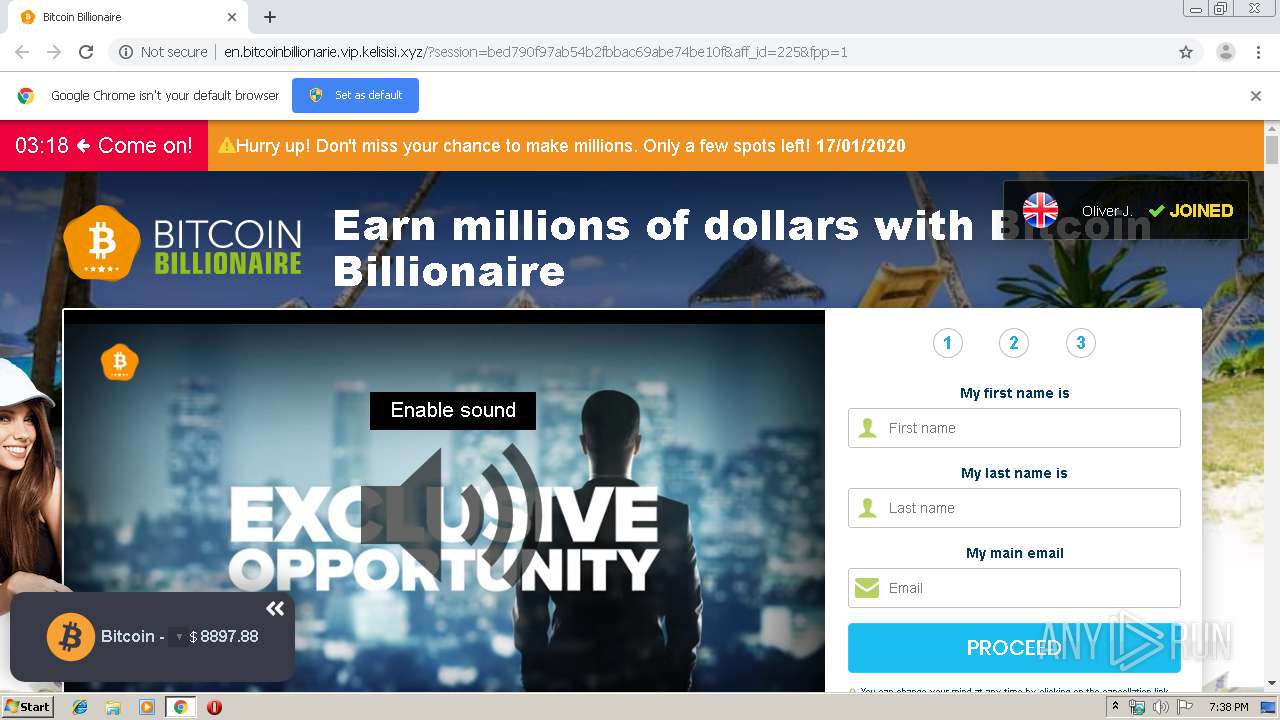
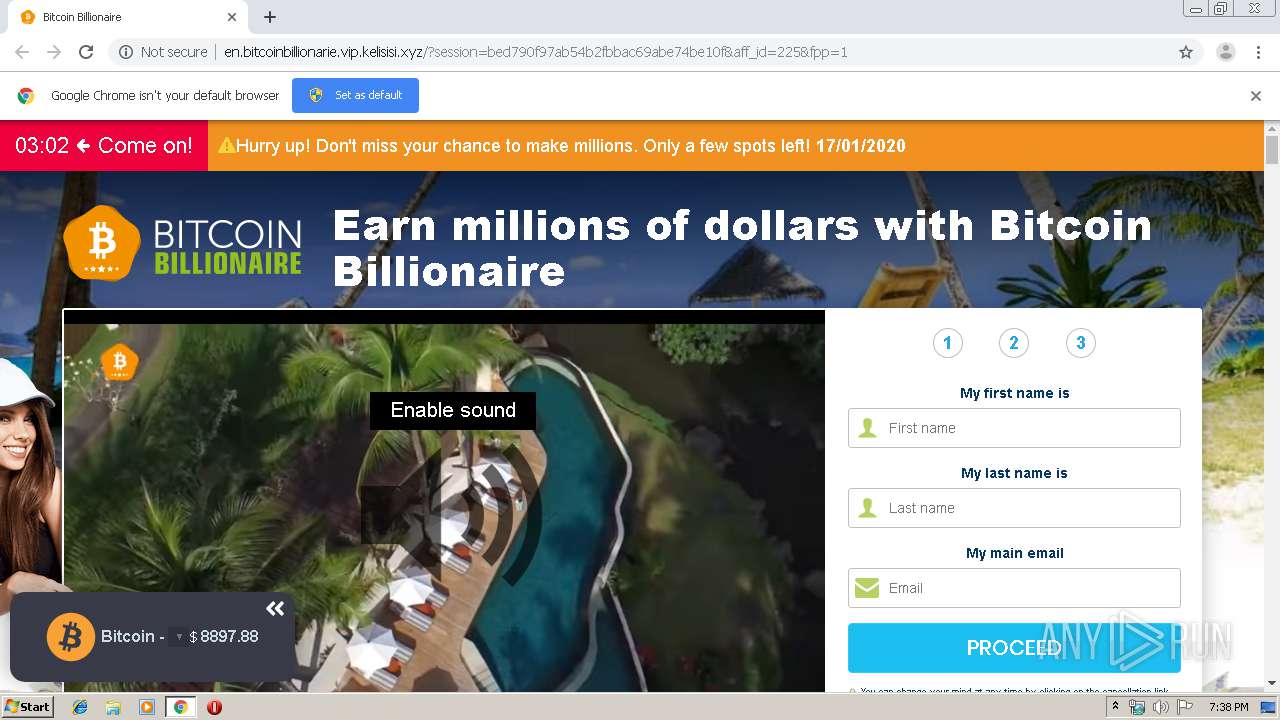
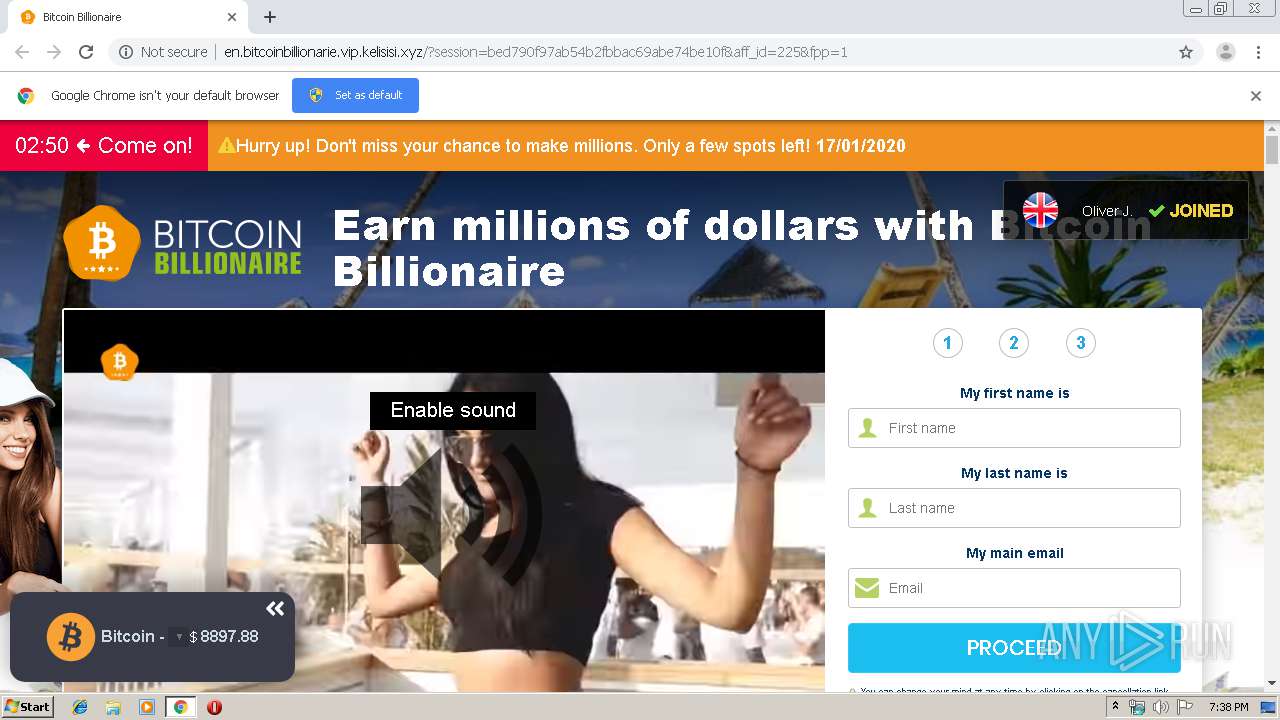
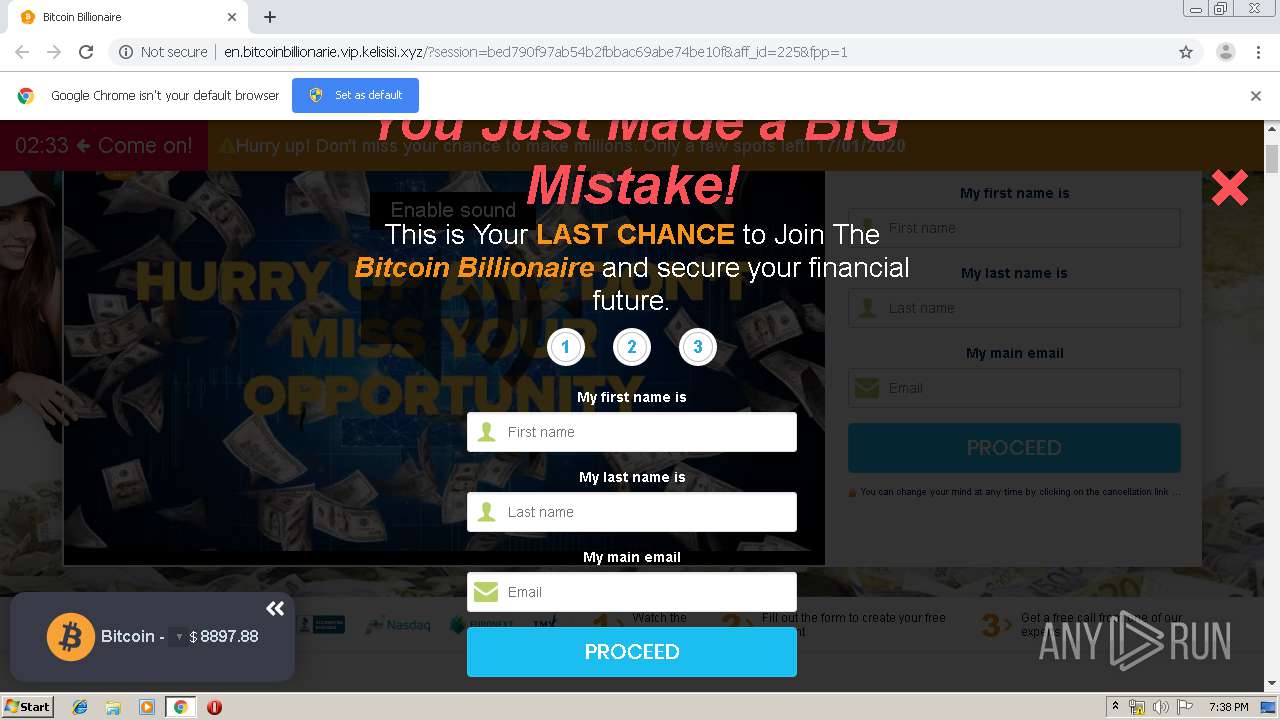
| URL: | https://somereri1975.blogspot.com.ee/ |
| Full analysis: | https://app.any.run/tasks/fc57ac8b-a61d-4015-adc6-3281aae2ada2 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 19:37:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9618EEE281C47B676D78B5B382FDA4DC |
| SHA1: | 64A8E8A18AF78FB371BC1D30FBF867638545A148 |
| SHA256: | C318C60886250079EEB17C0DC5137756042DAA8255778BEBC66D48981A5BE68F |
| SSDEEP: | 3:N8H9PUszJK4K5K:2HjKU |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2520)
INFO
Reads the hosts file
- chrome.exe (PID: 3720)
- chrome.exe (PID: 2520)
Application launched itself
- chrome.exe (PID: 2520)
Reads settings of System Certificates
- chrome.exe (PID: 3720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
38
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13275523109939803054 --mojo-platform-channel-handle=4824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8354528528974254728 --mojo-platform-channel-handle=3560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12819453400171812180 --mojo-platform-channel-handle=5124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=171047326912057820 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13881197684505073228 --mojo-platform-channel-handle=3432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4149874425932892877 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3944 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16558352827903300926 --mojo-platform-channel-handle=3488 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6648237194967040312 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12366251199491612406 --mojo-platform-channel-handle=5120 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13277056990849175937 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
627
Read events
525
Write events
97
Delete events
5
Modification events
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2520-13223763461986875 |
Value: 259 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2520) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
70
Text files
335
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5c56cfaf-2d6d-4e8f-8799-59524841ea6e.tmp | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3998c0.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF3998ef.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF39990e.TMP | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3998b0.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
100
TCP/UDP connections
55
DNS requests
35
Threats
98
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
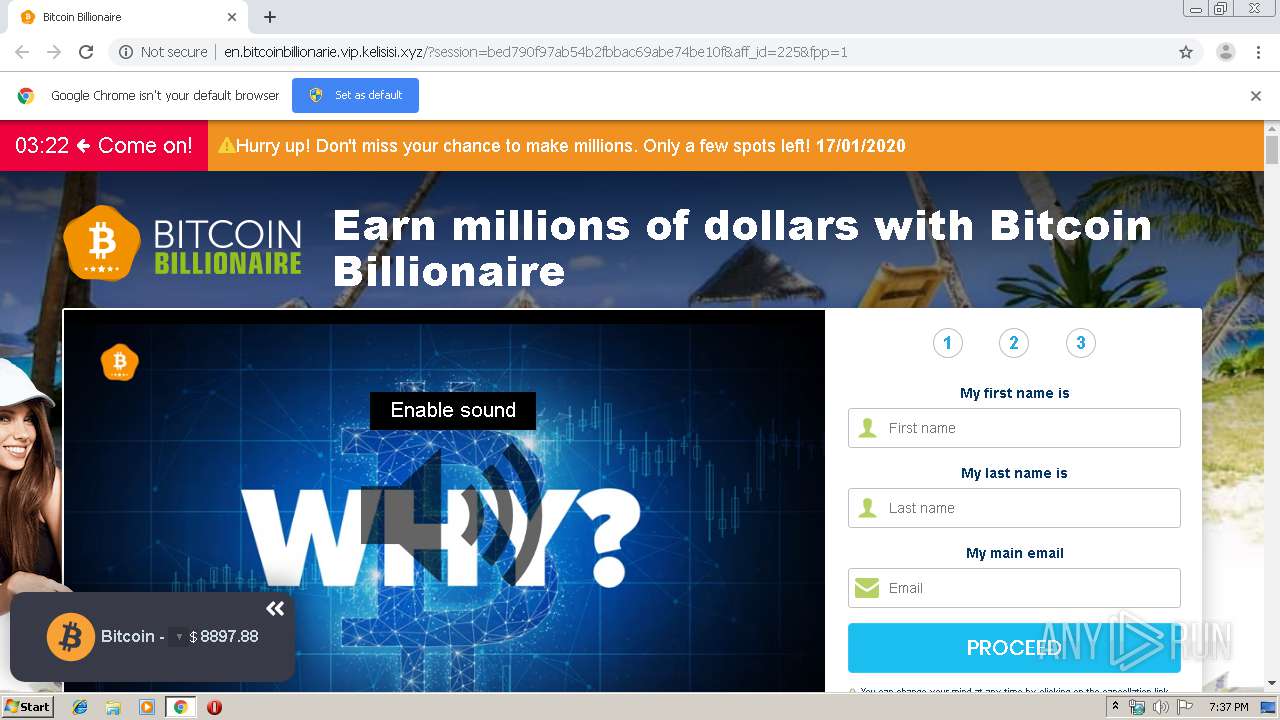
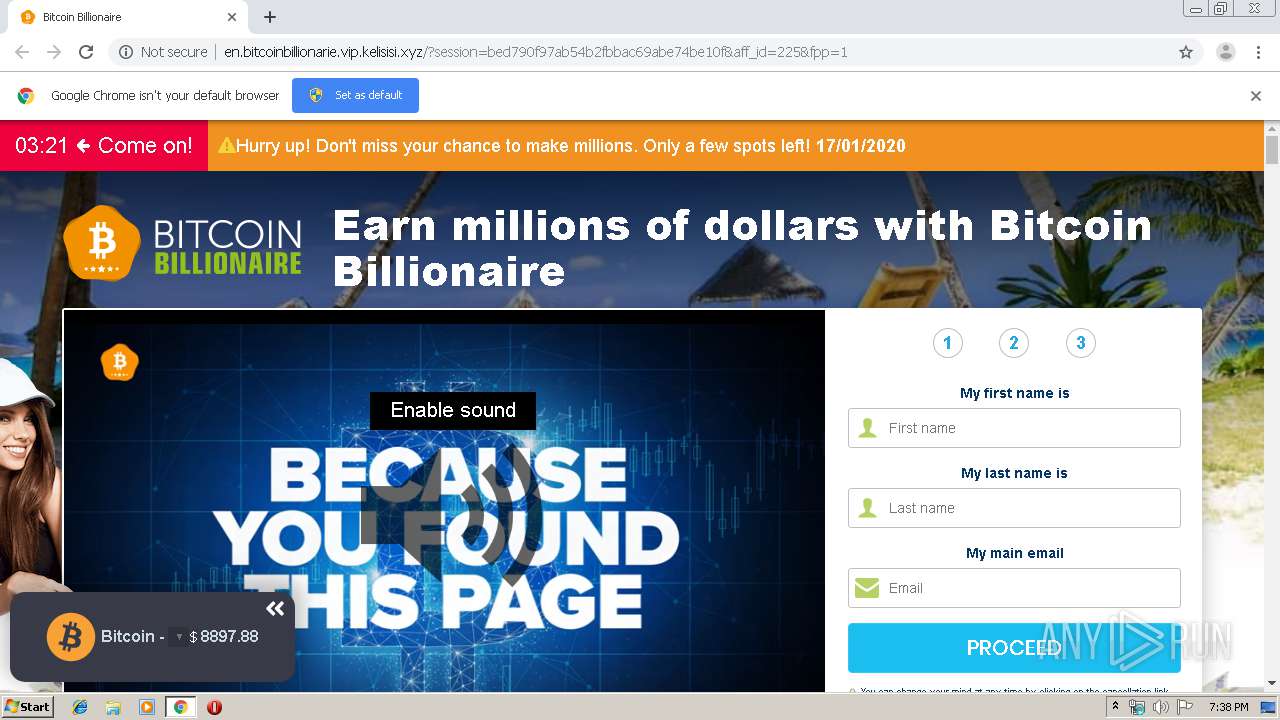
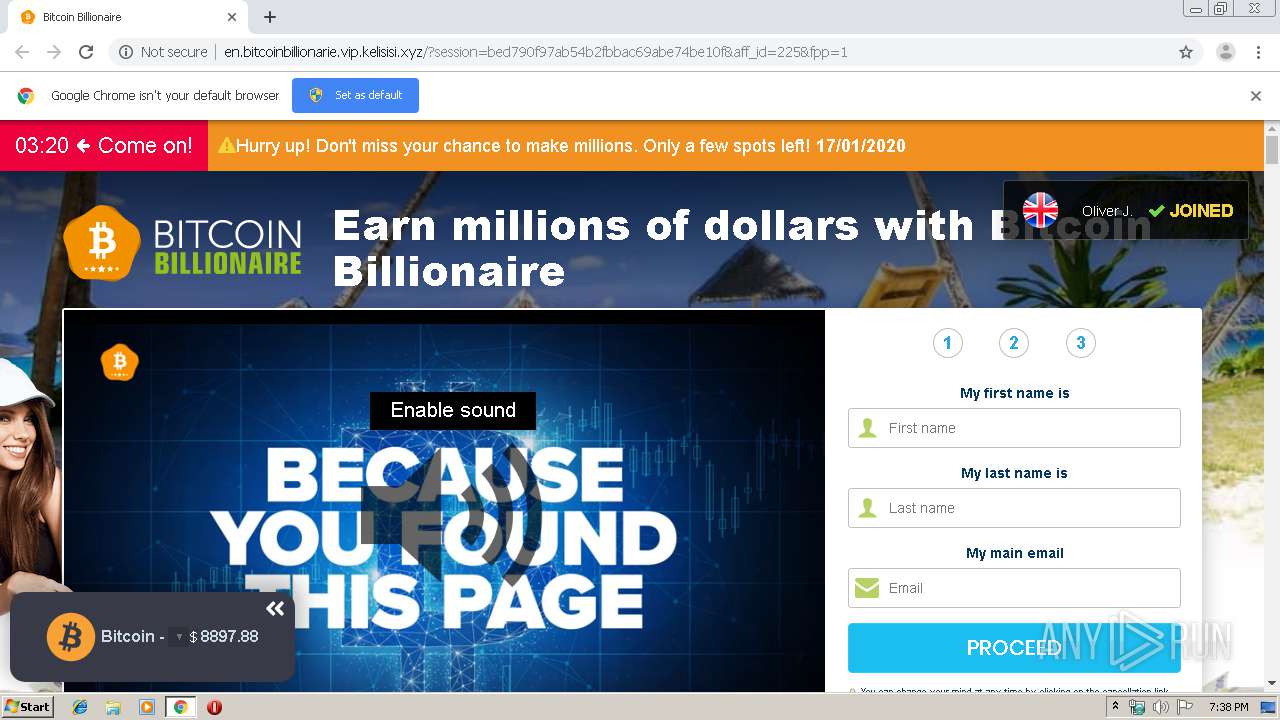
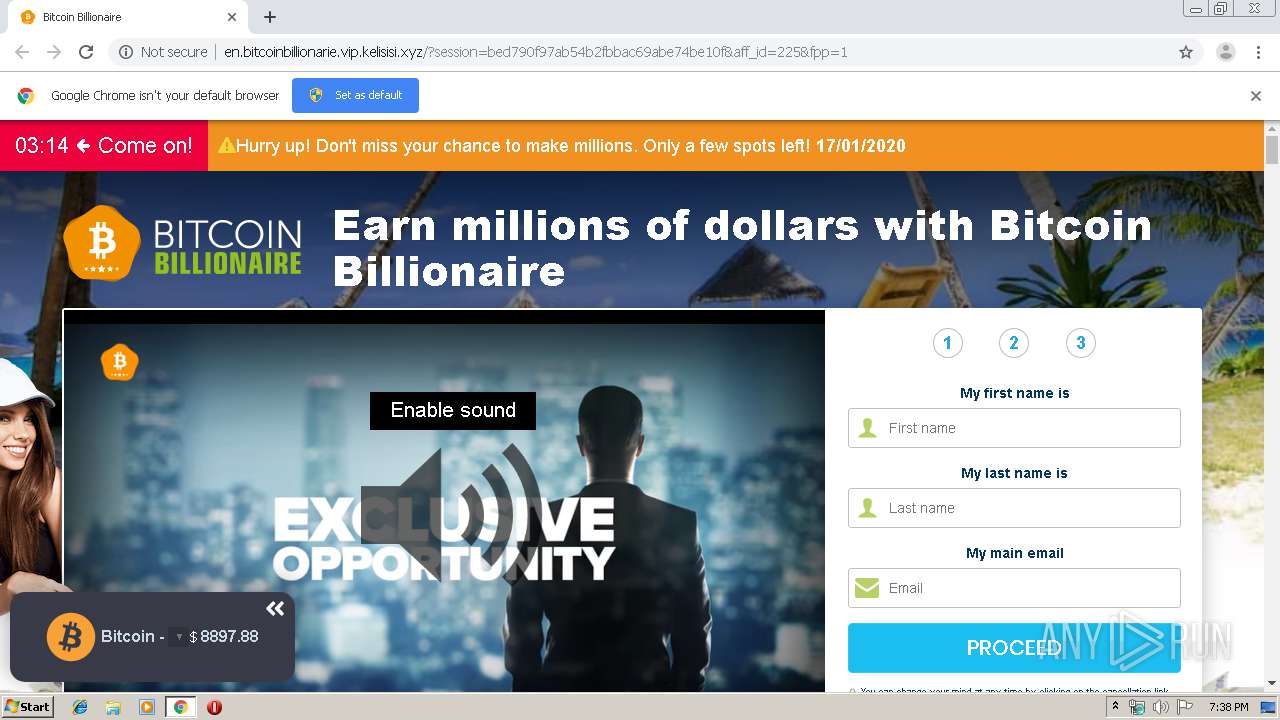
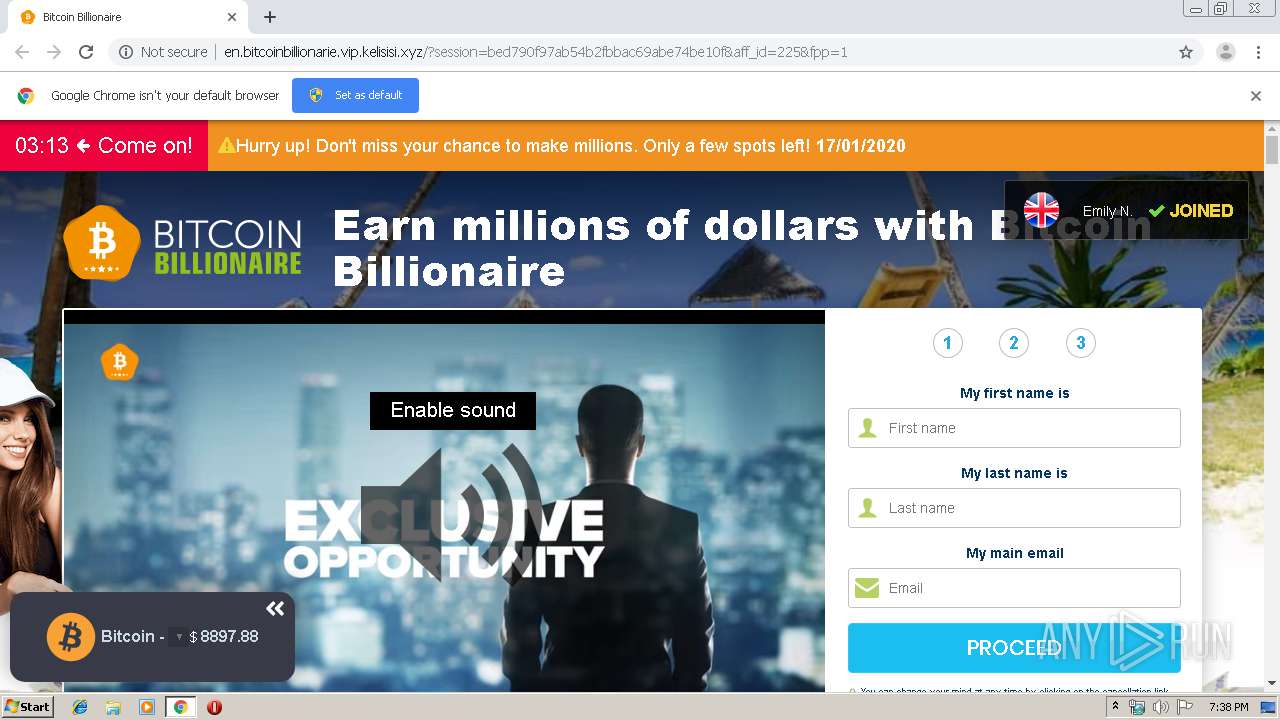
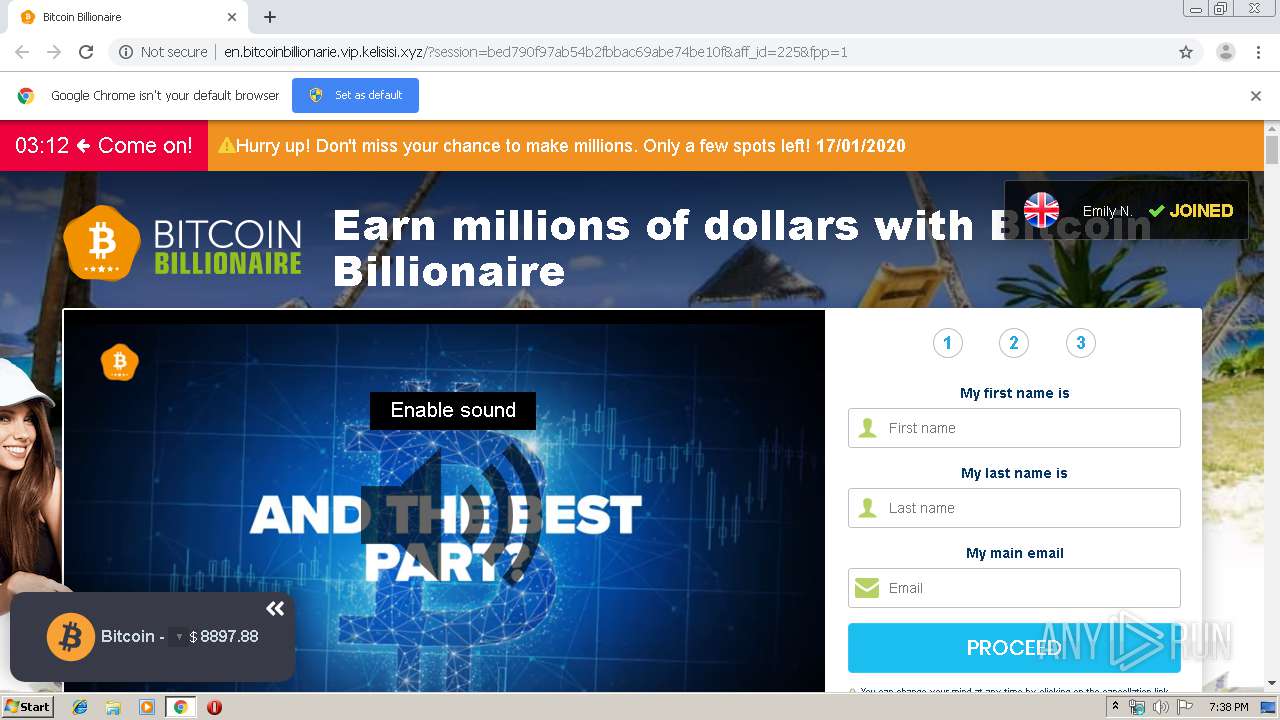
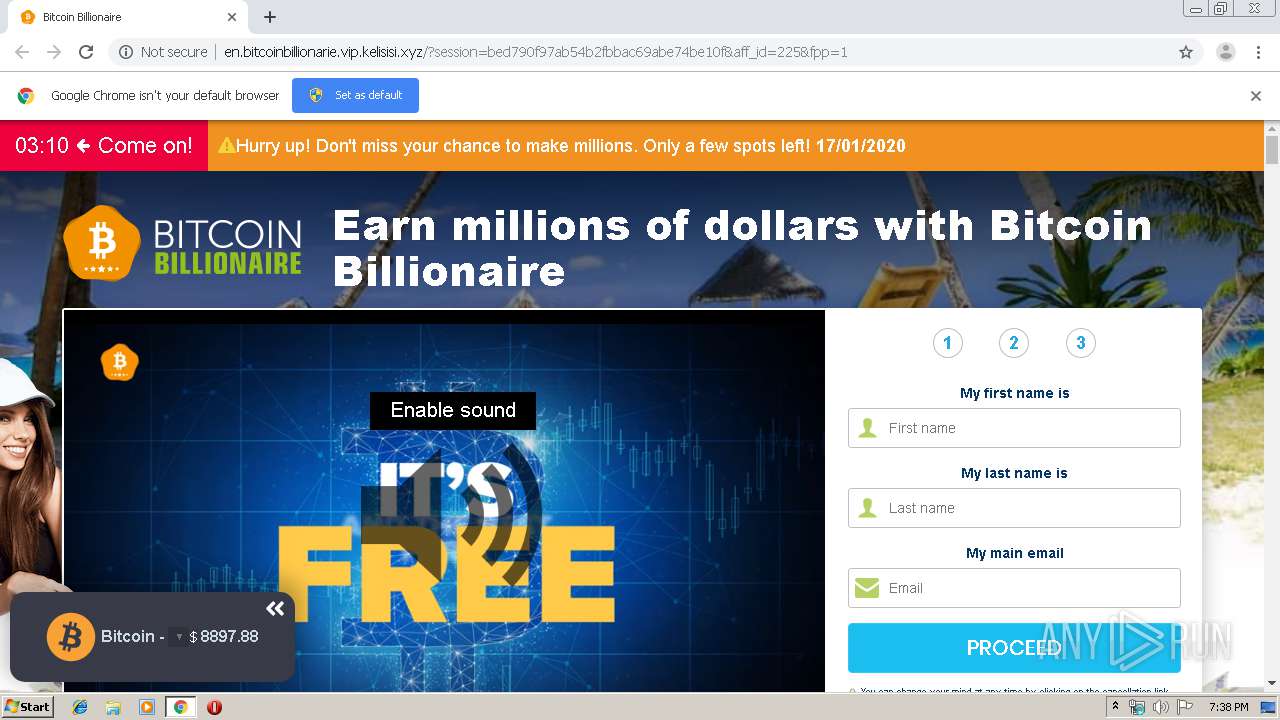
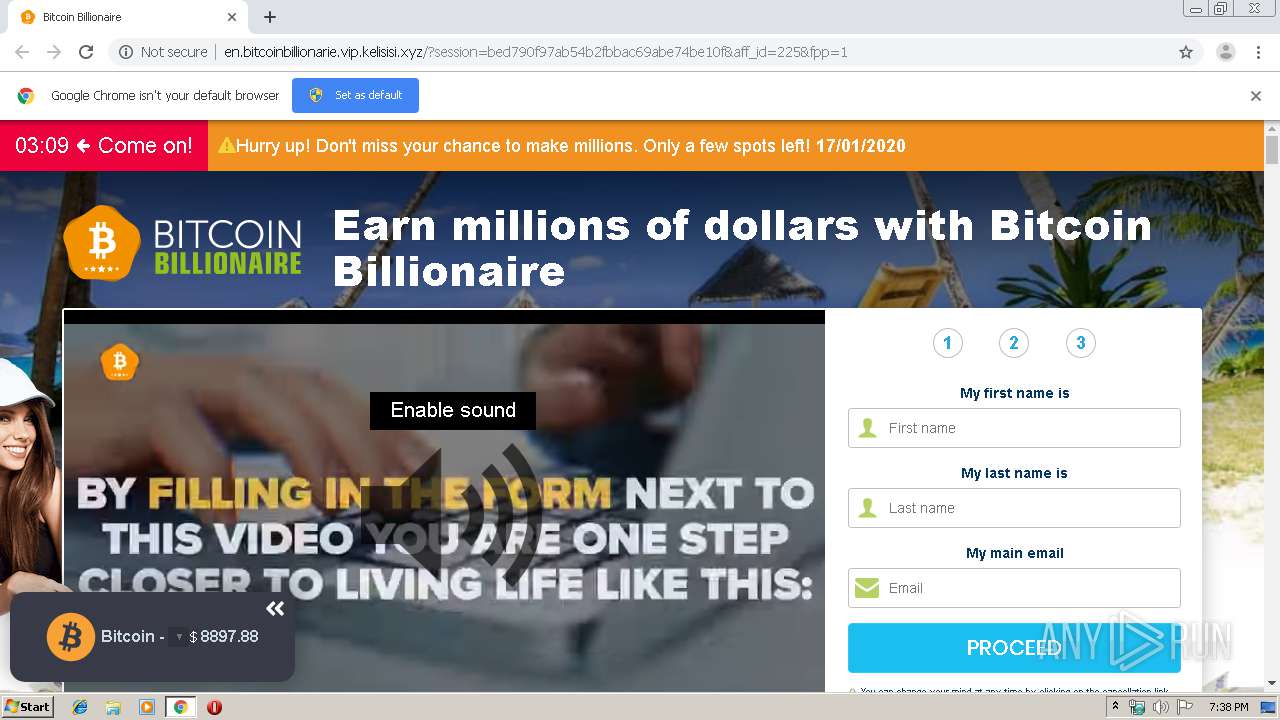
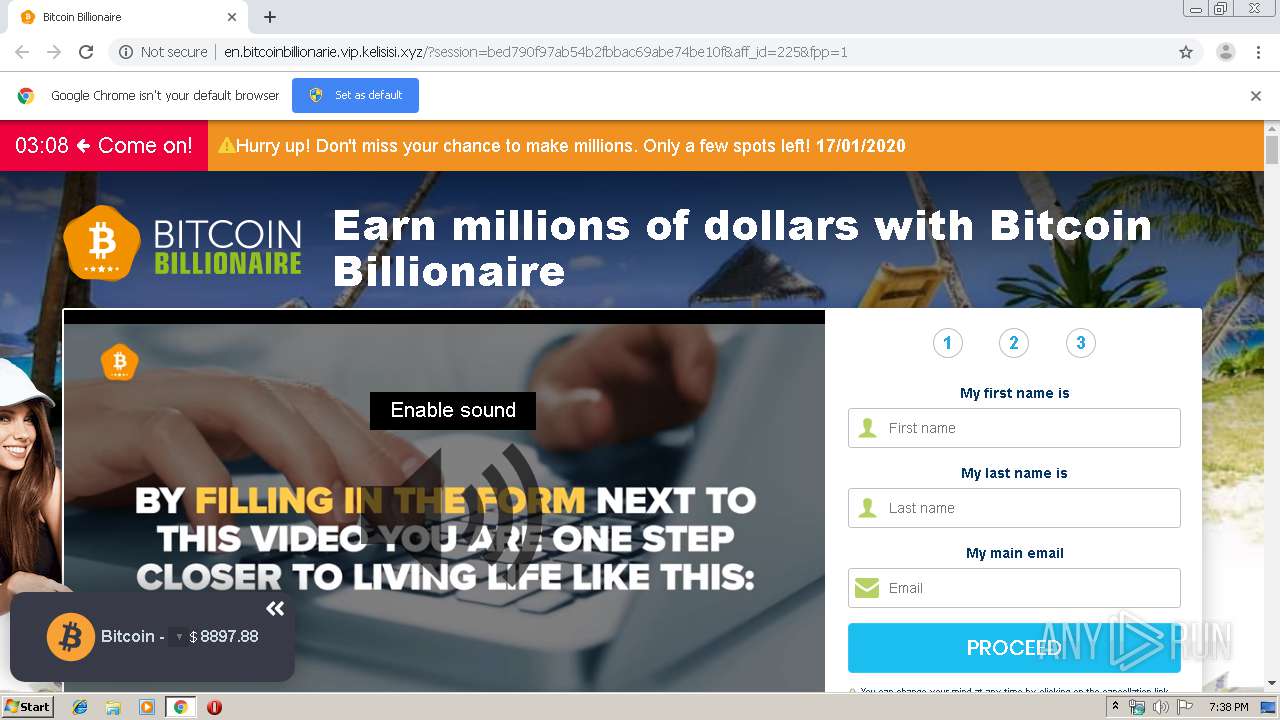
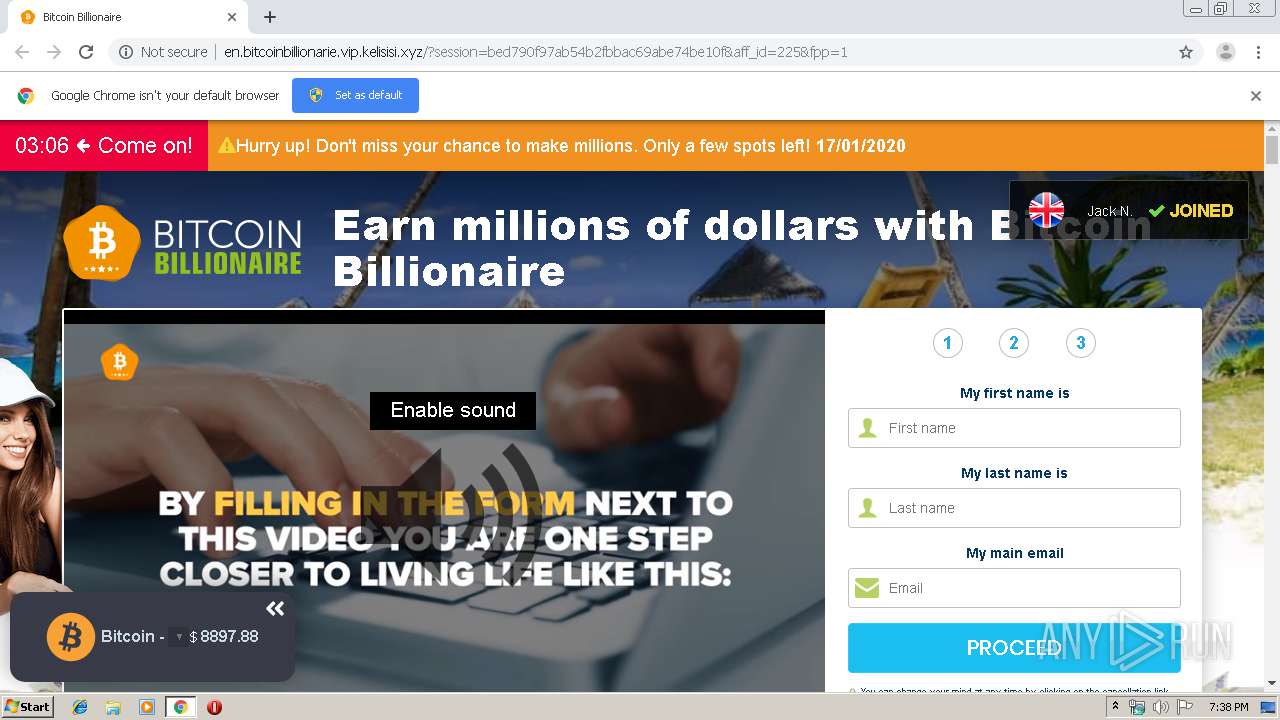
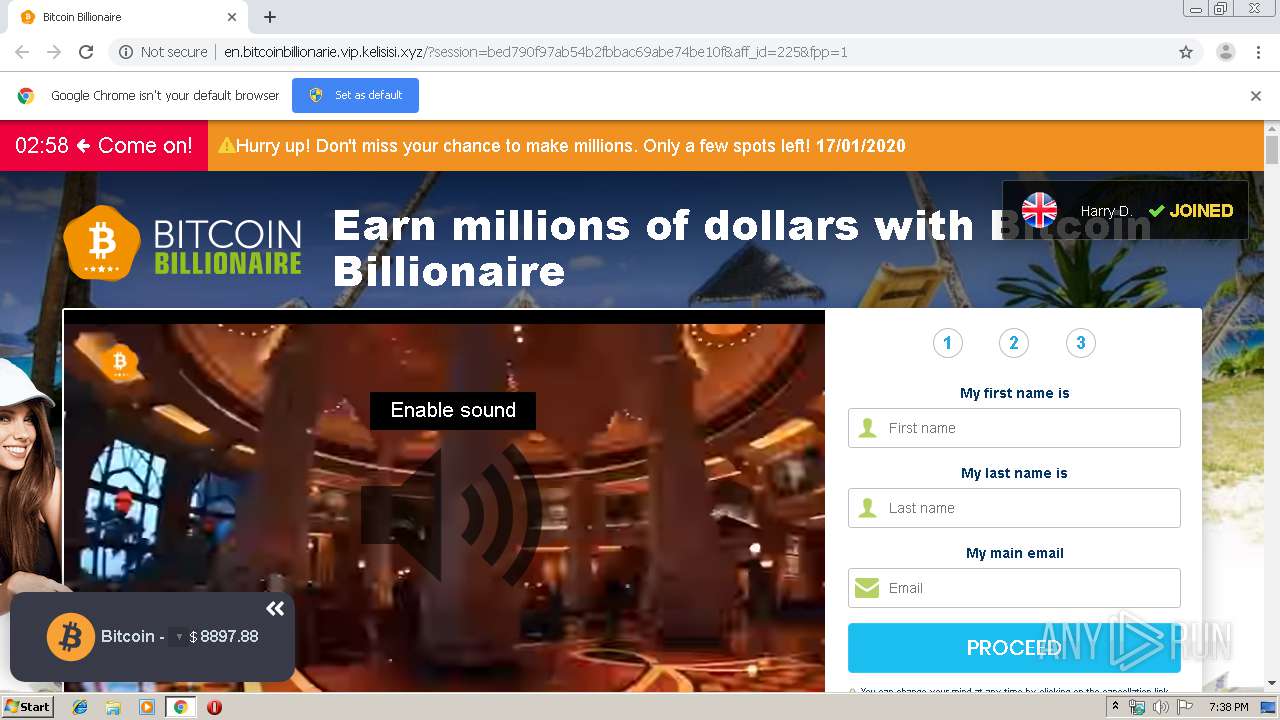
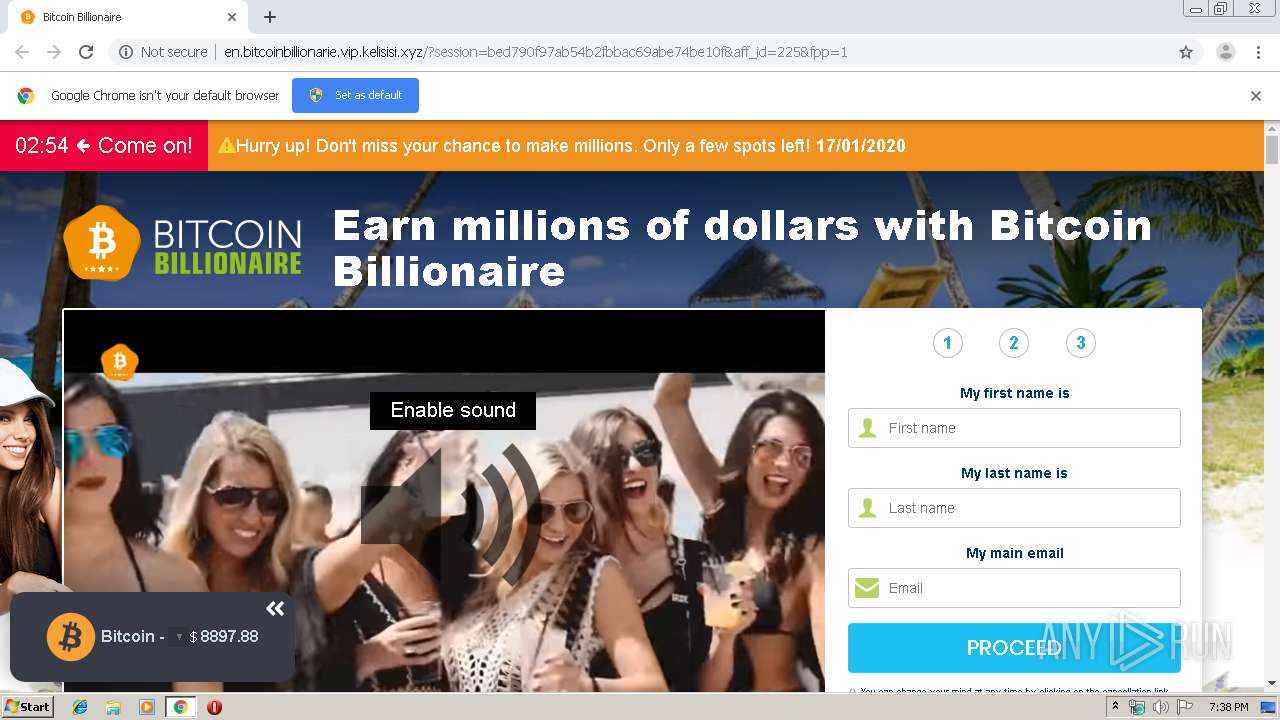
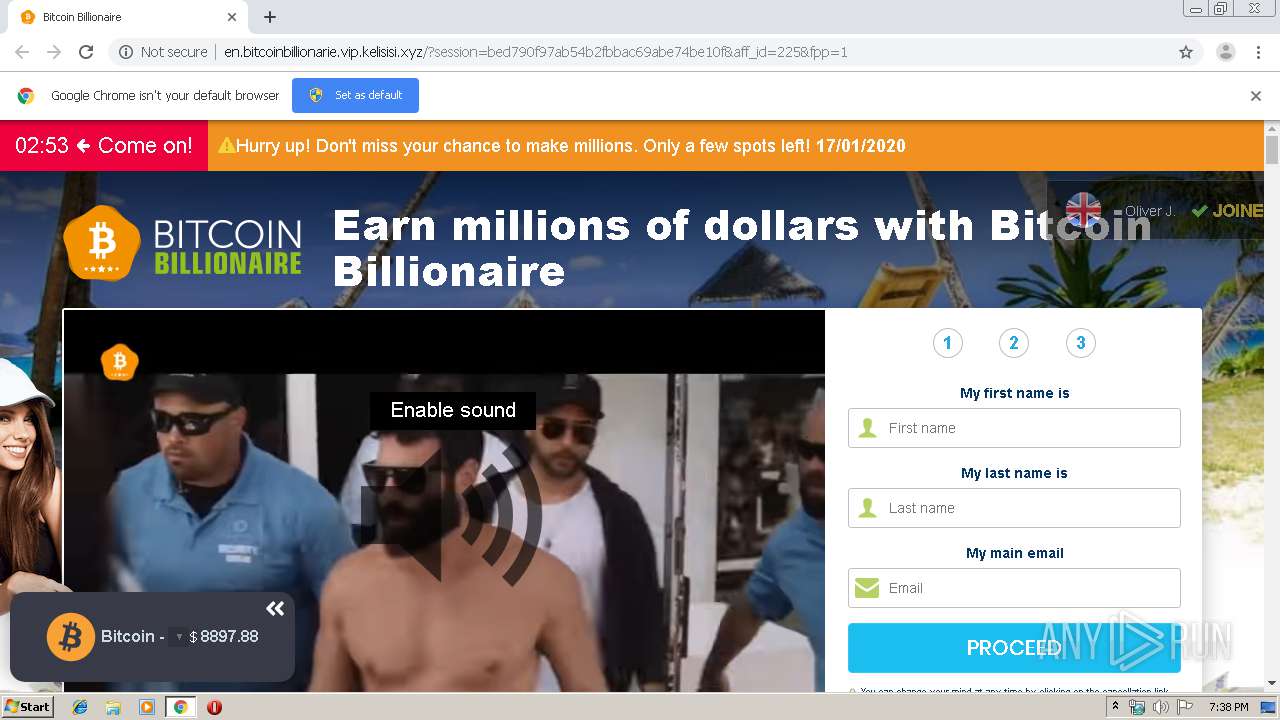
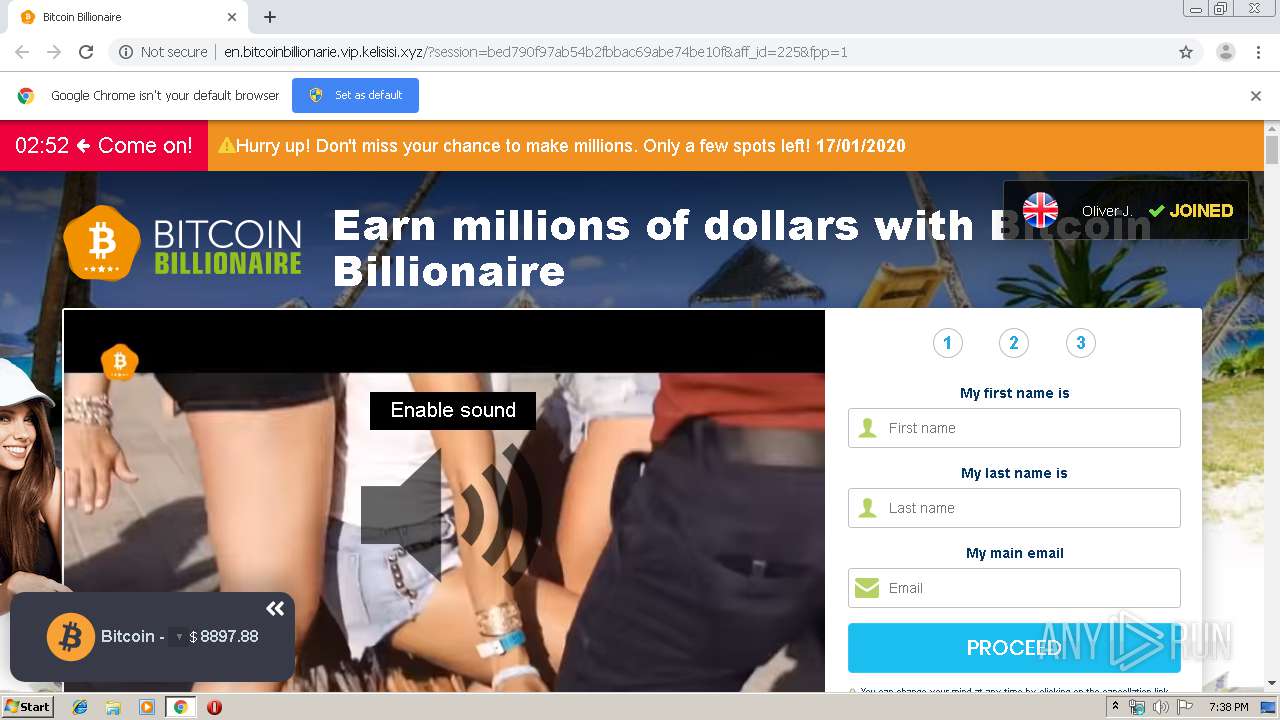
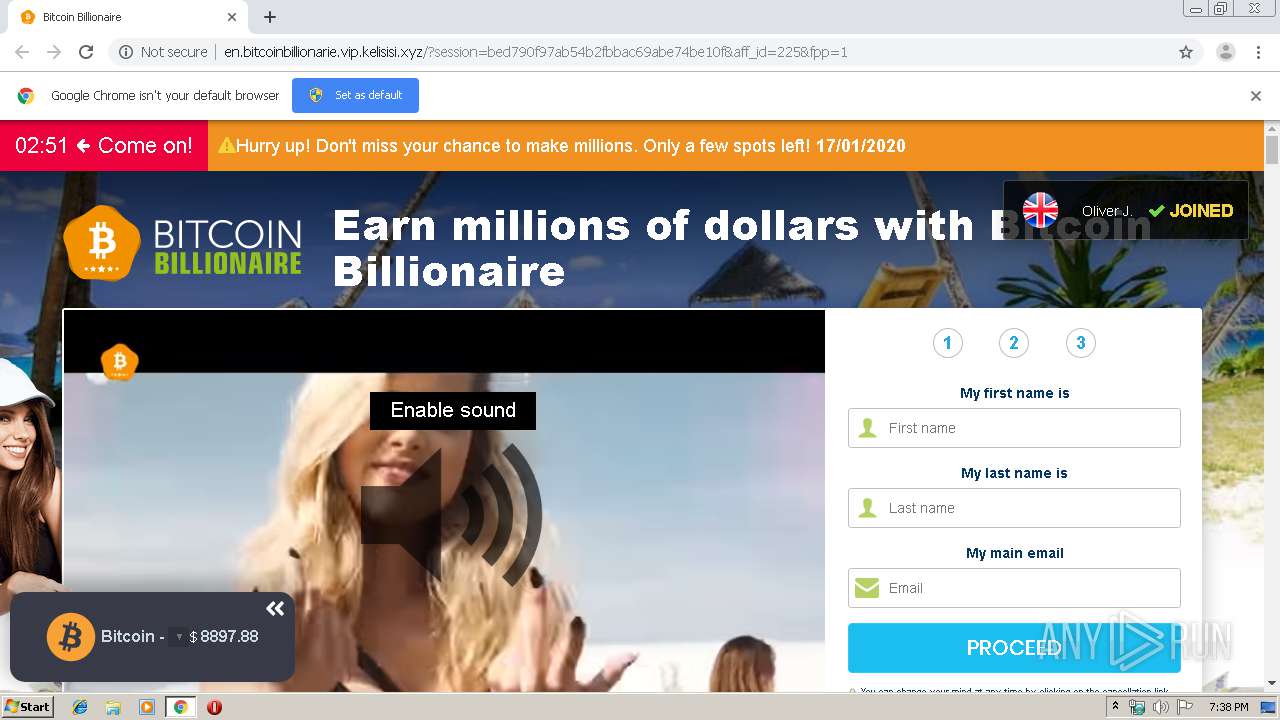
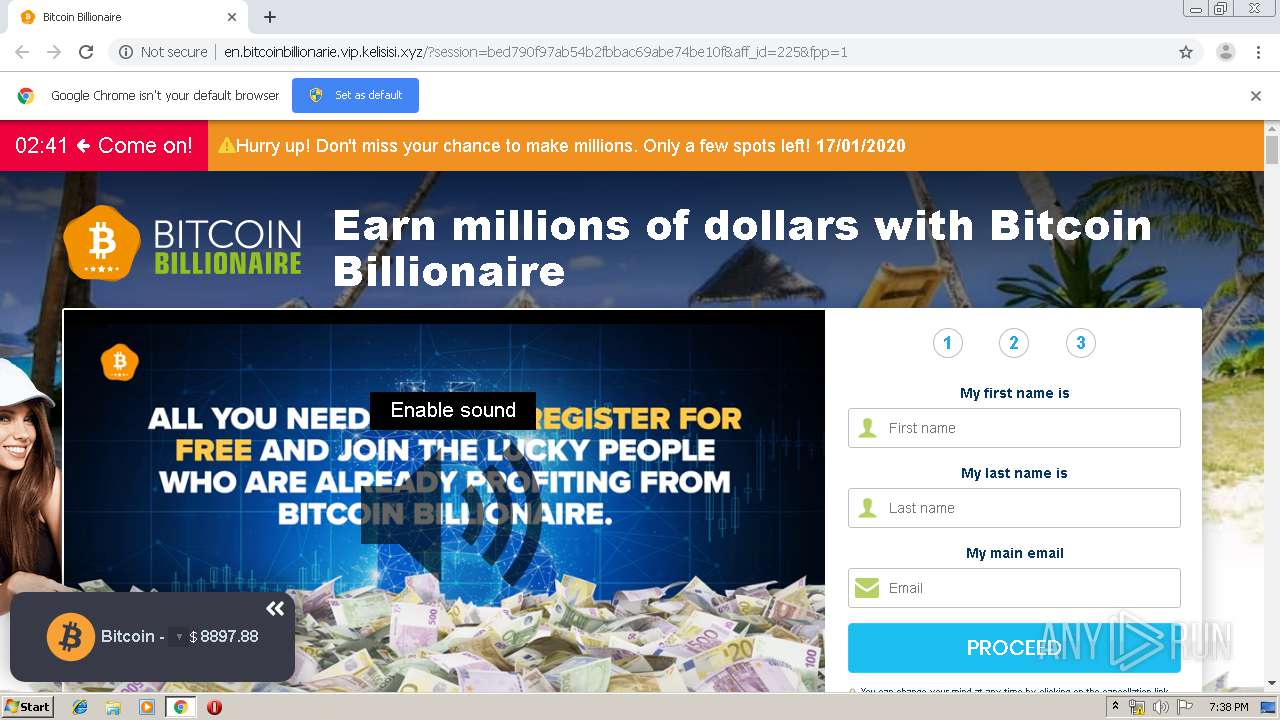
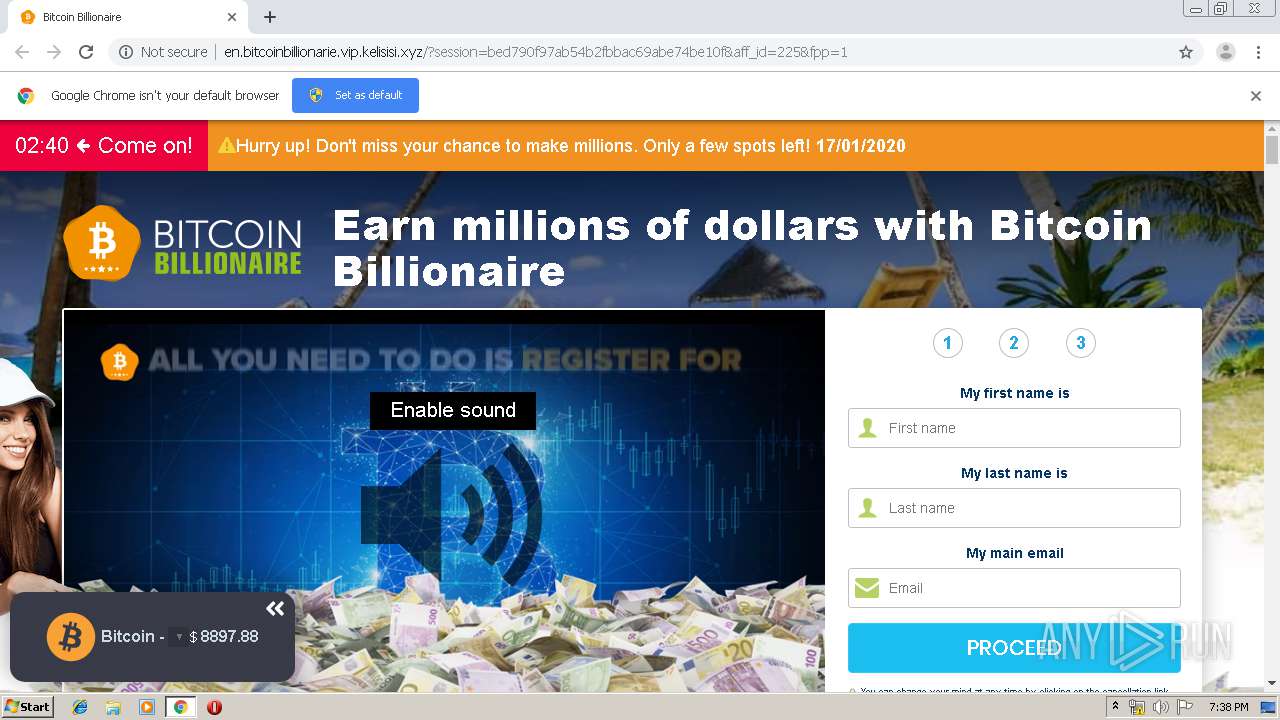
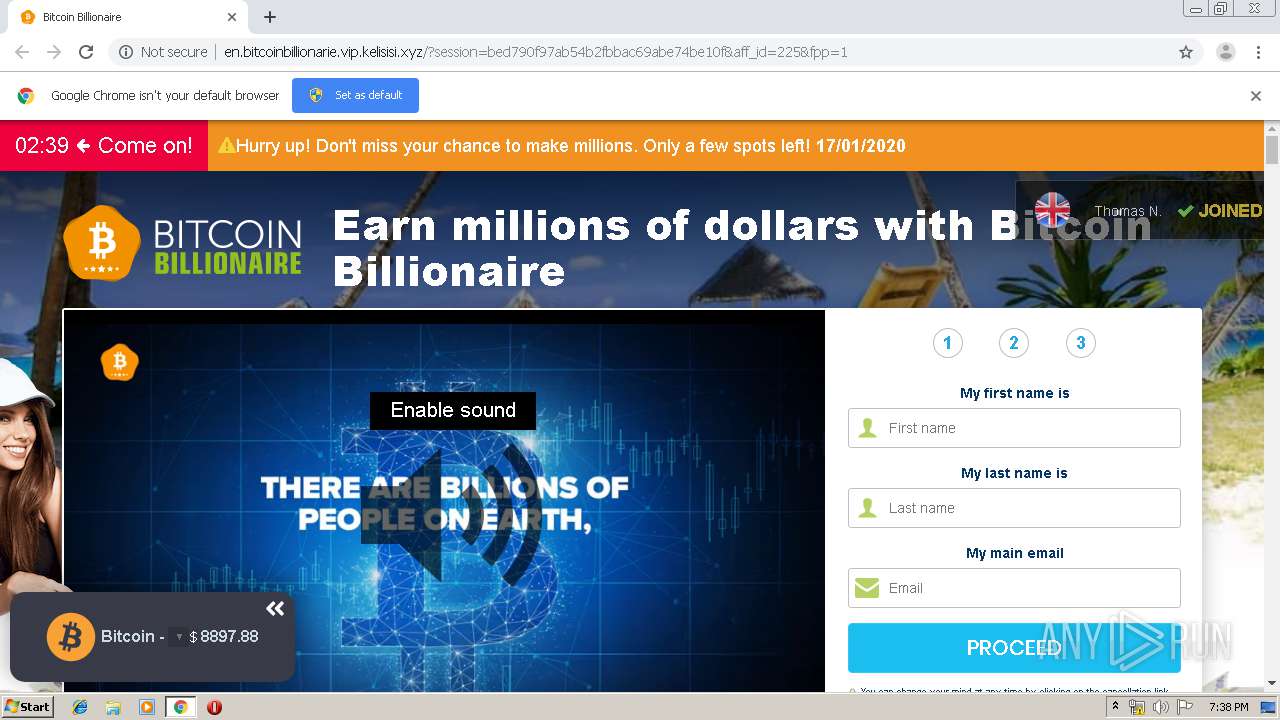
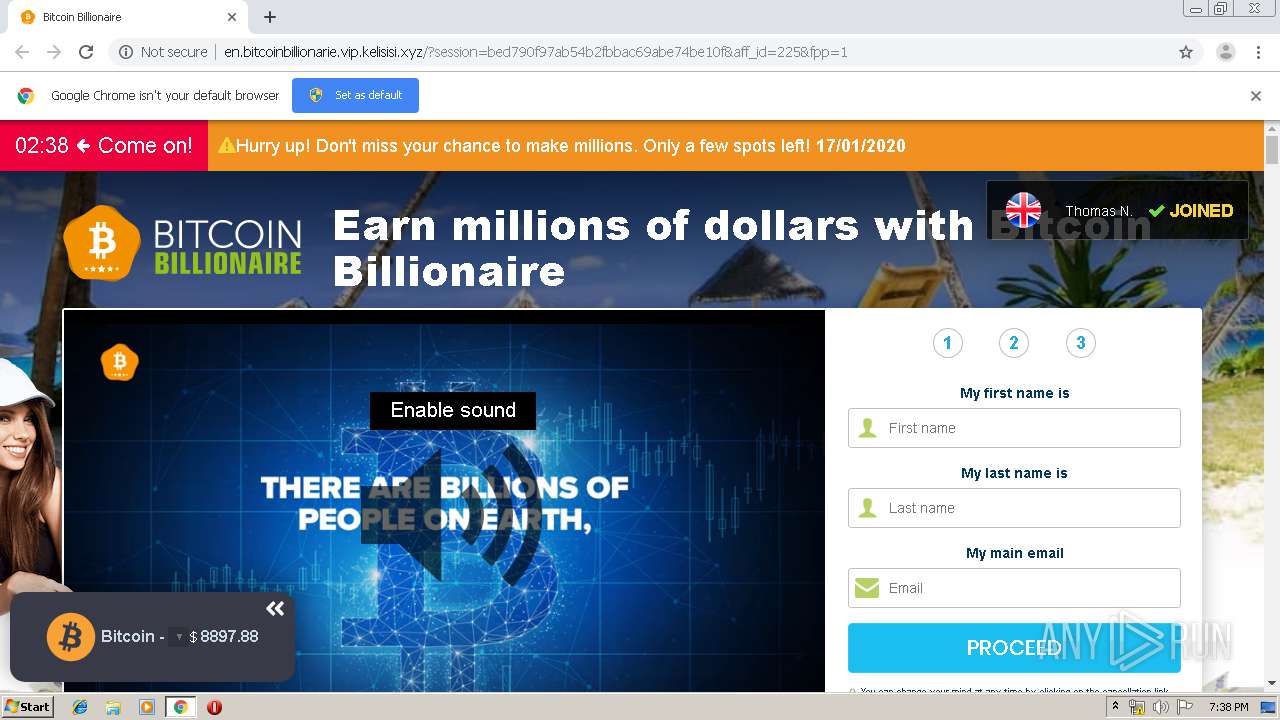
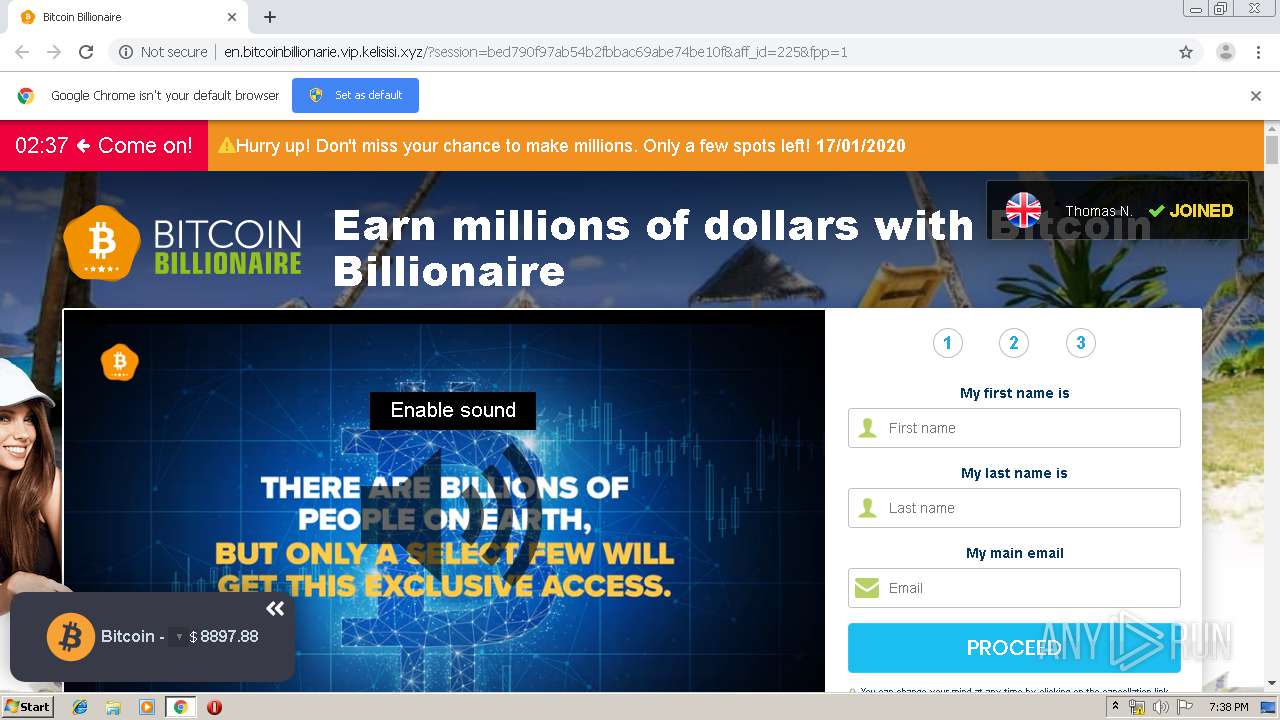
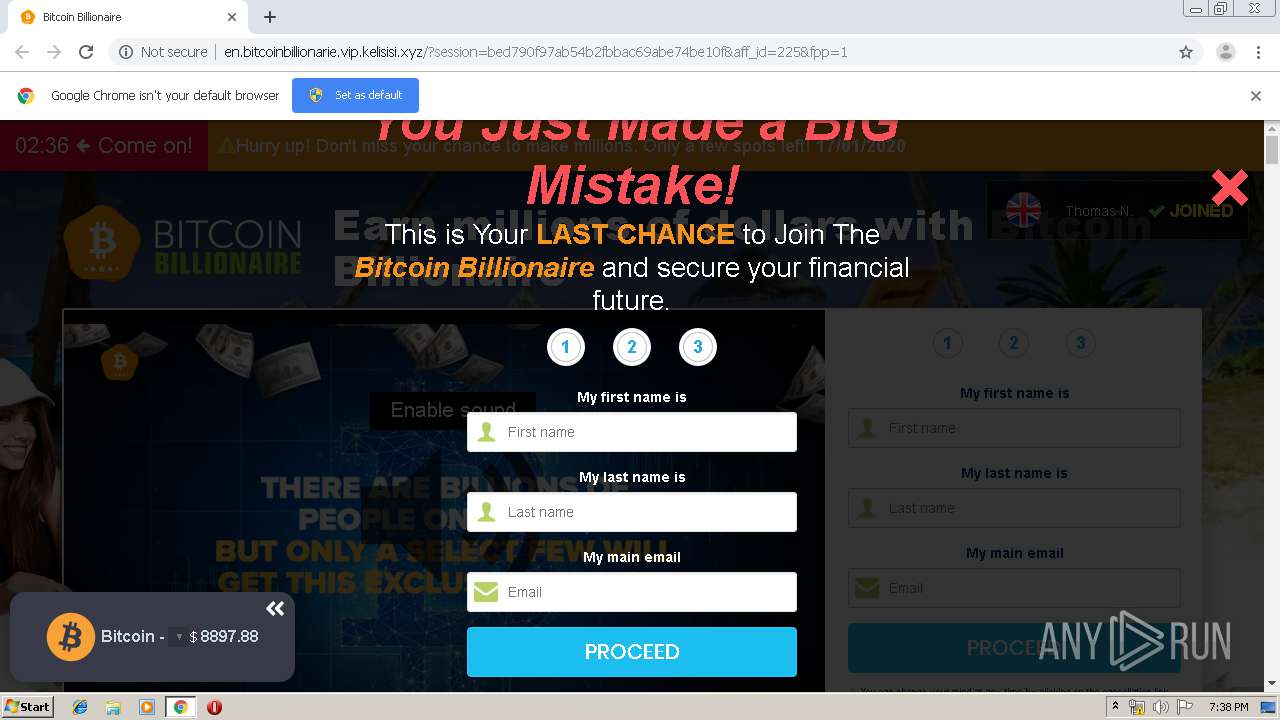
3720 | chrome.exe | GET | 302 | 8.208.77.248:80 | http://skinnerthomas.xyz/index | US | — | — | suspicious |
3720 | chrome.exe | GET | 302 | 8.208.77.248:80 | http://lkeir4751.xyz/favicon.ico | US | — | — | suspicious |
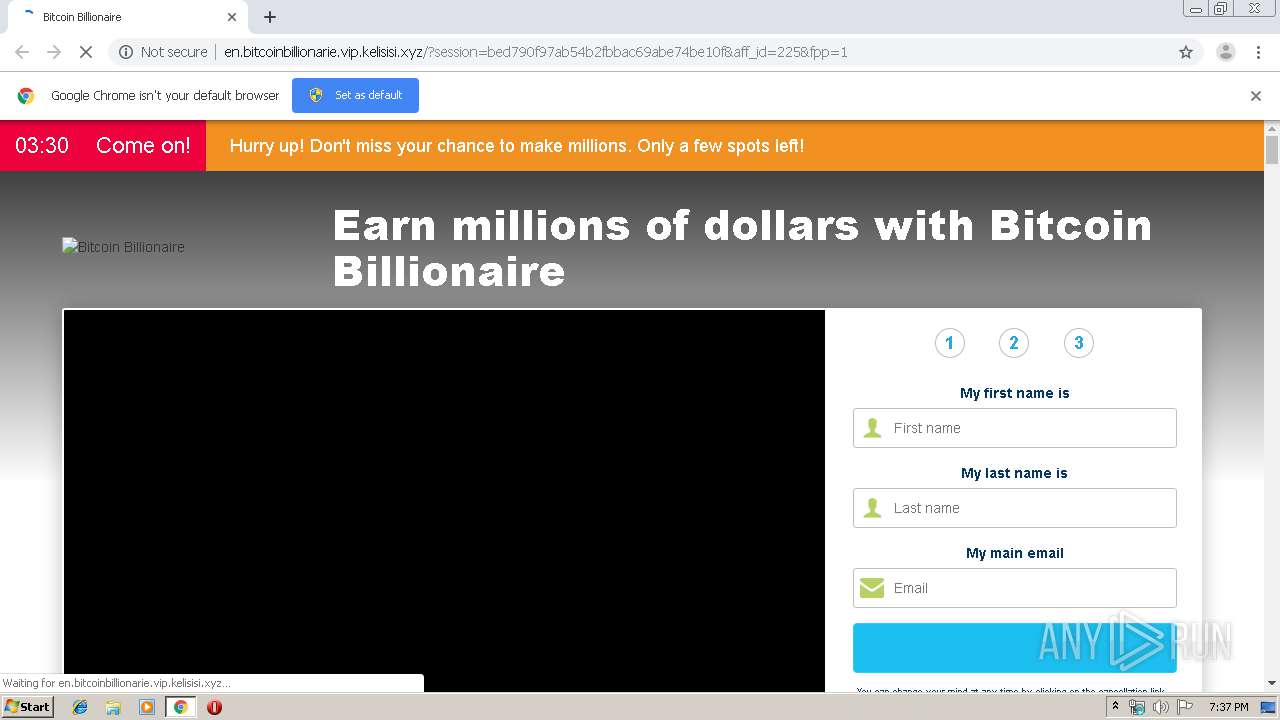
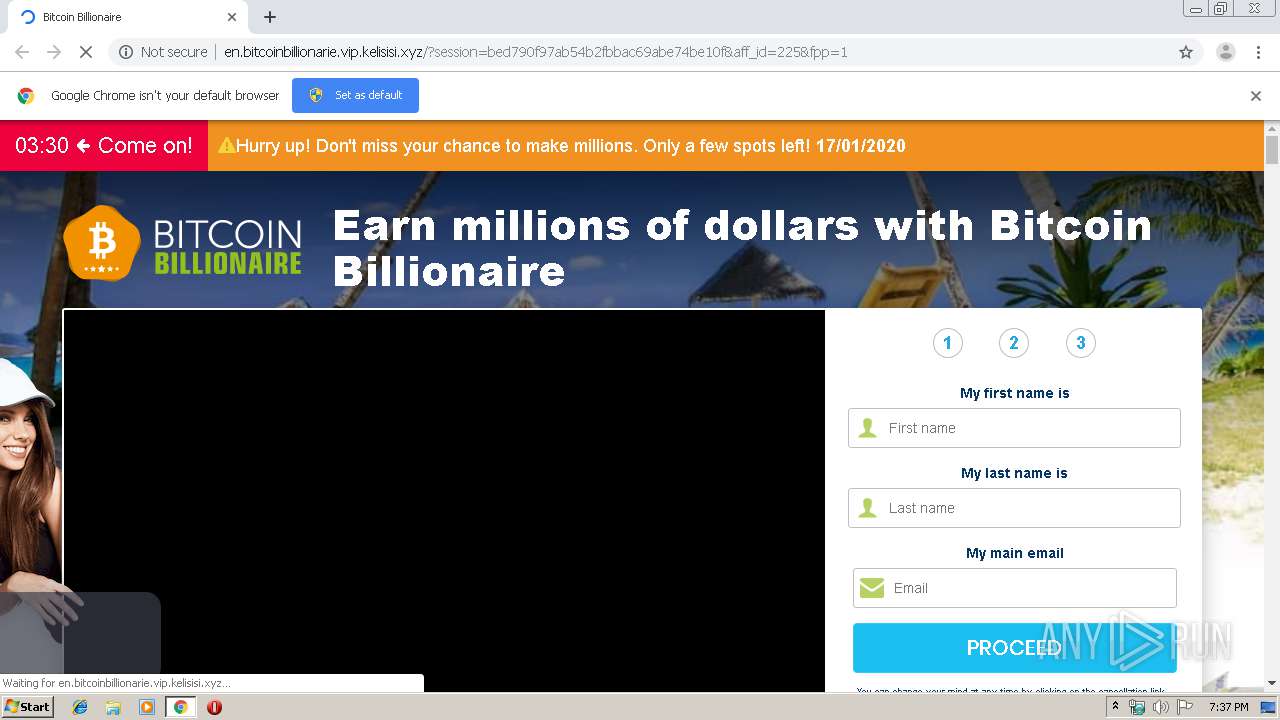
3720 | chrome.exe | GET | 302 | 104.24.97.120:80 | http://vip.kelisisi.xyz/02m0 | US | — | — | suspicious |
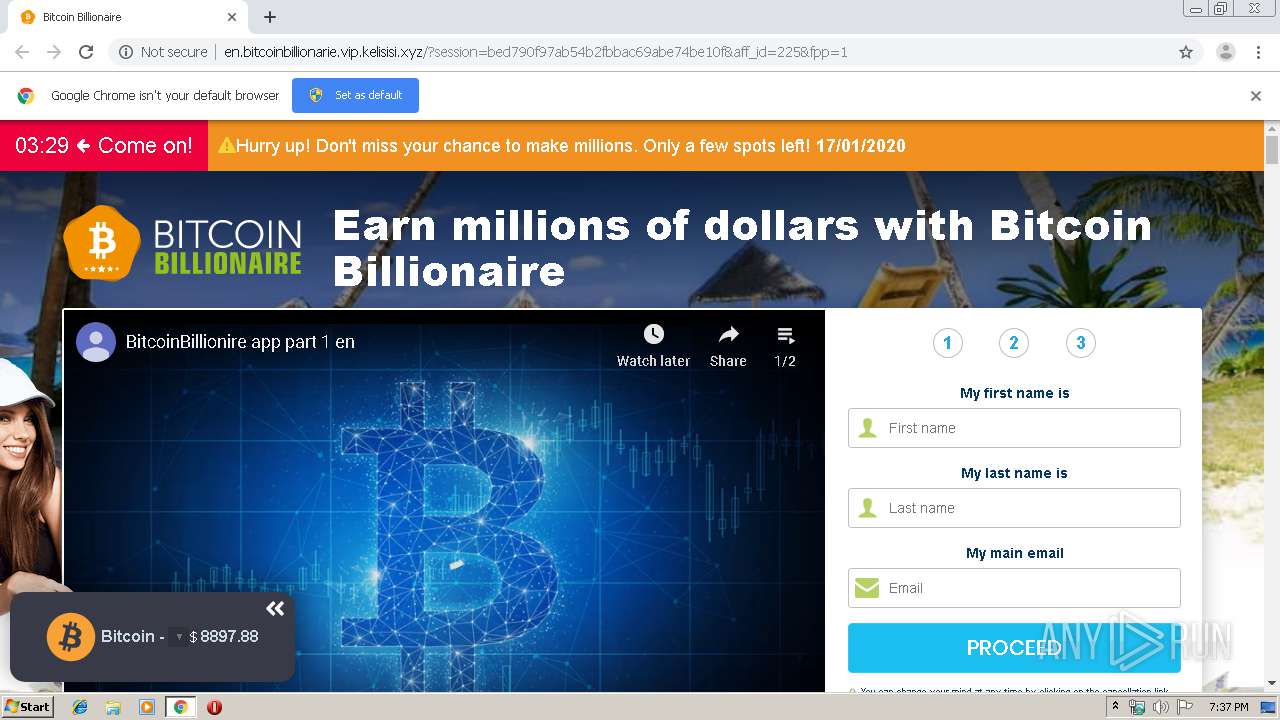
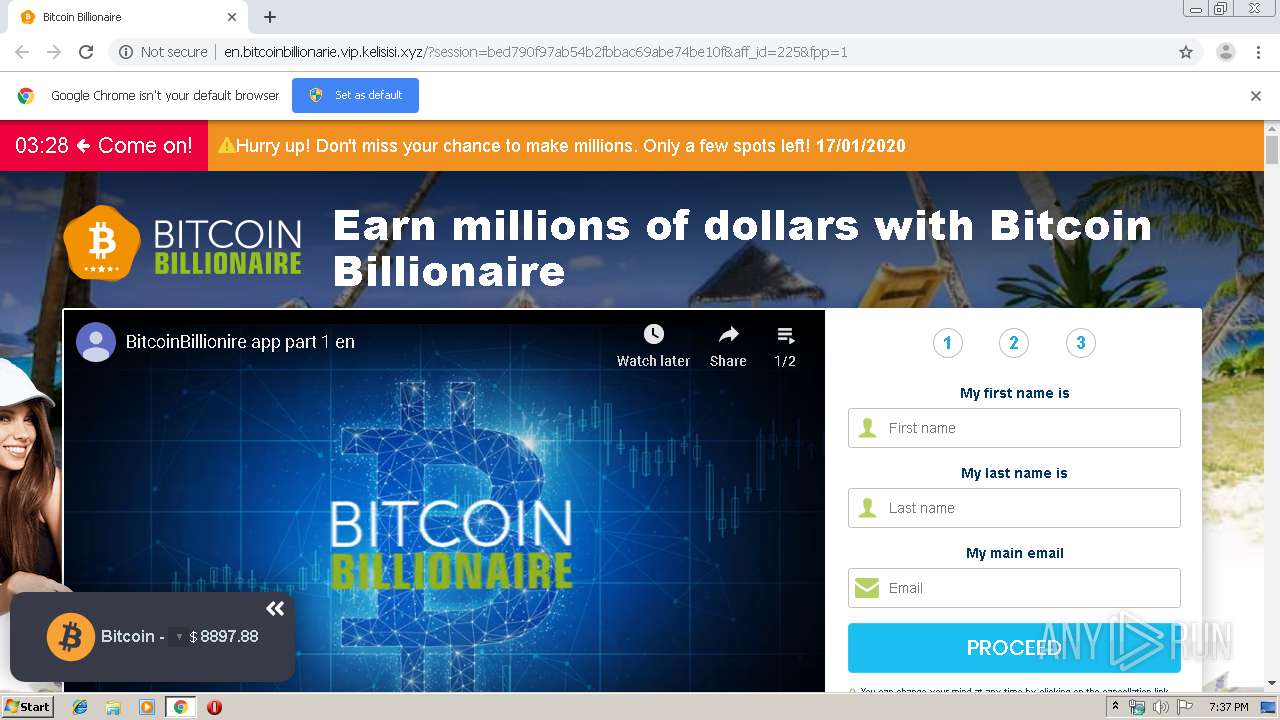
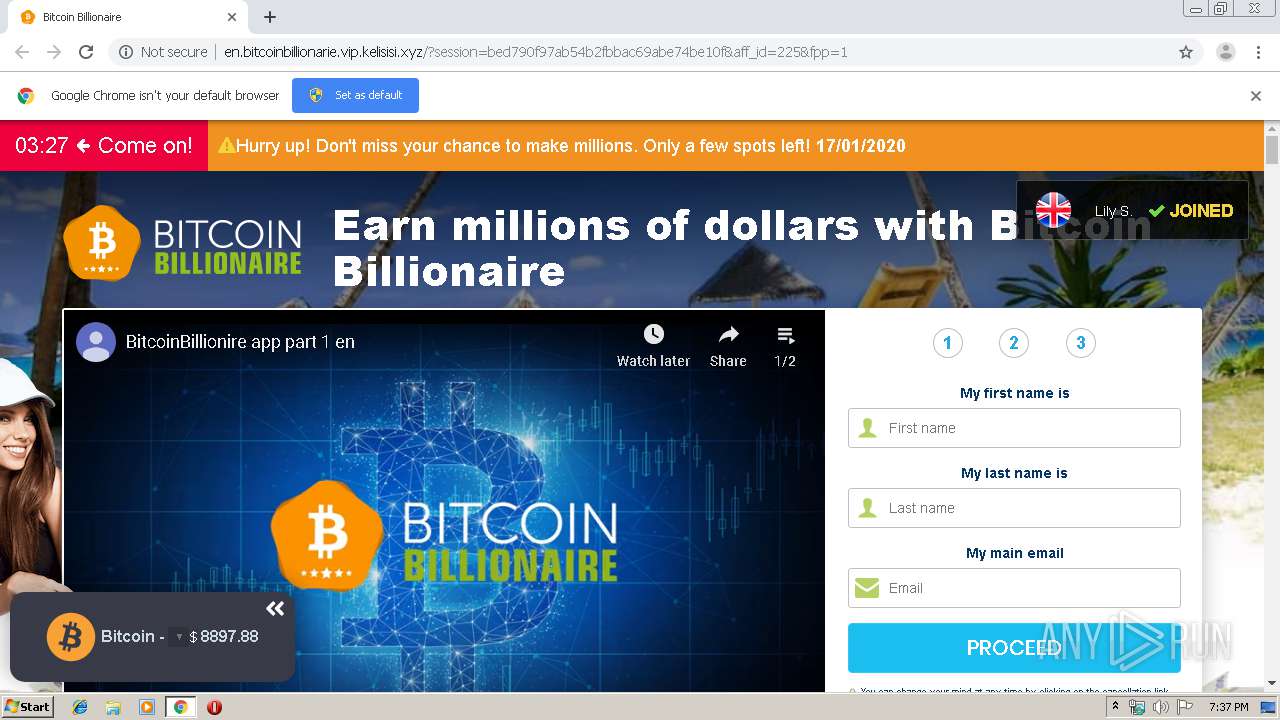
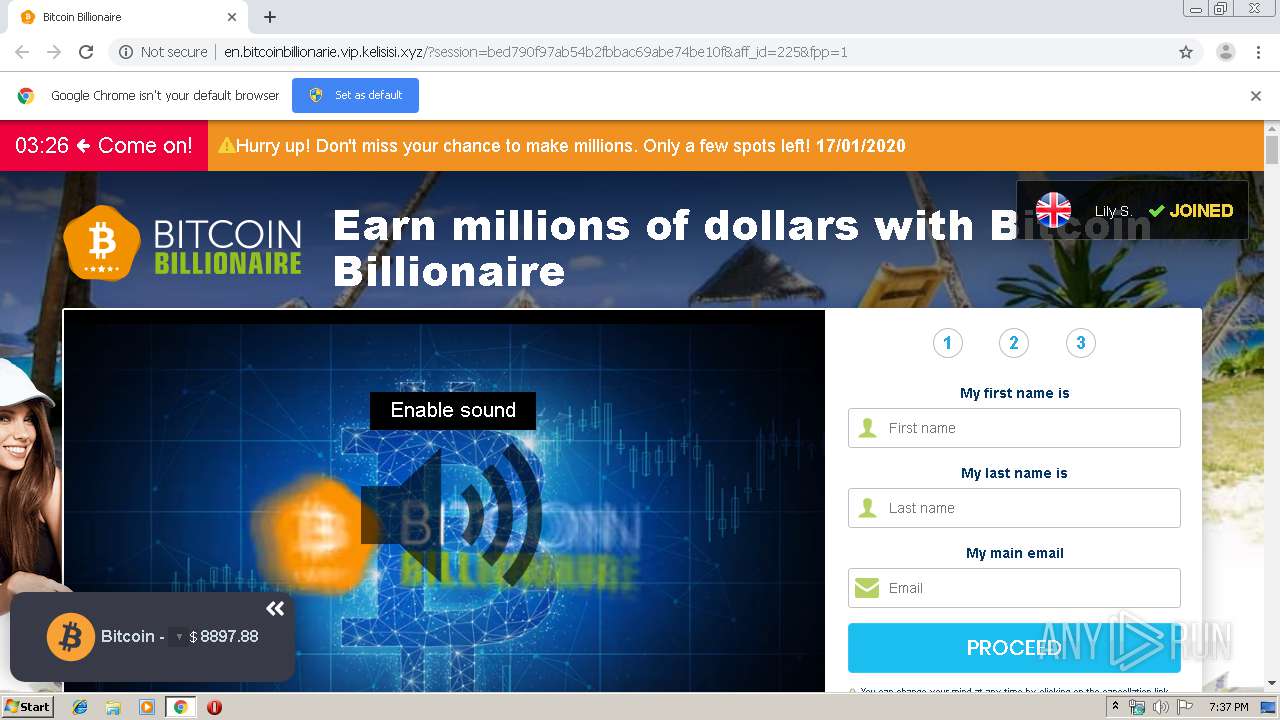
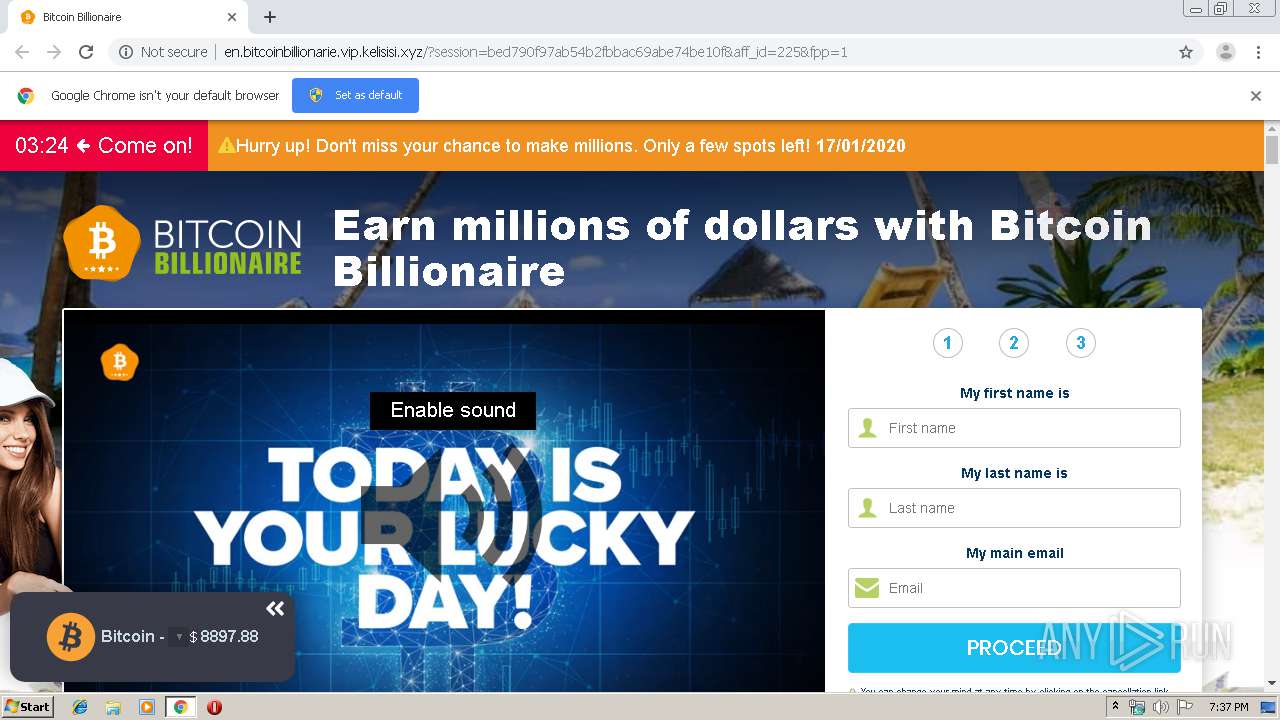
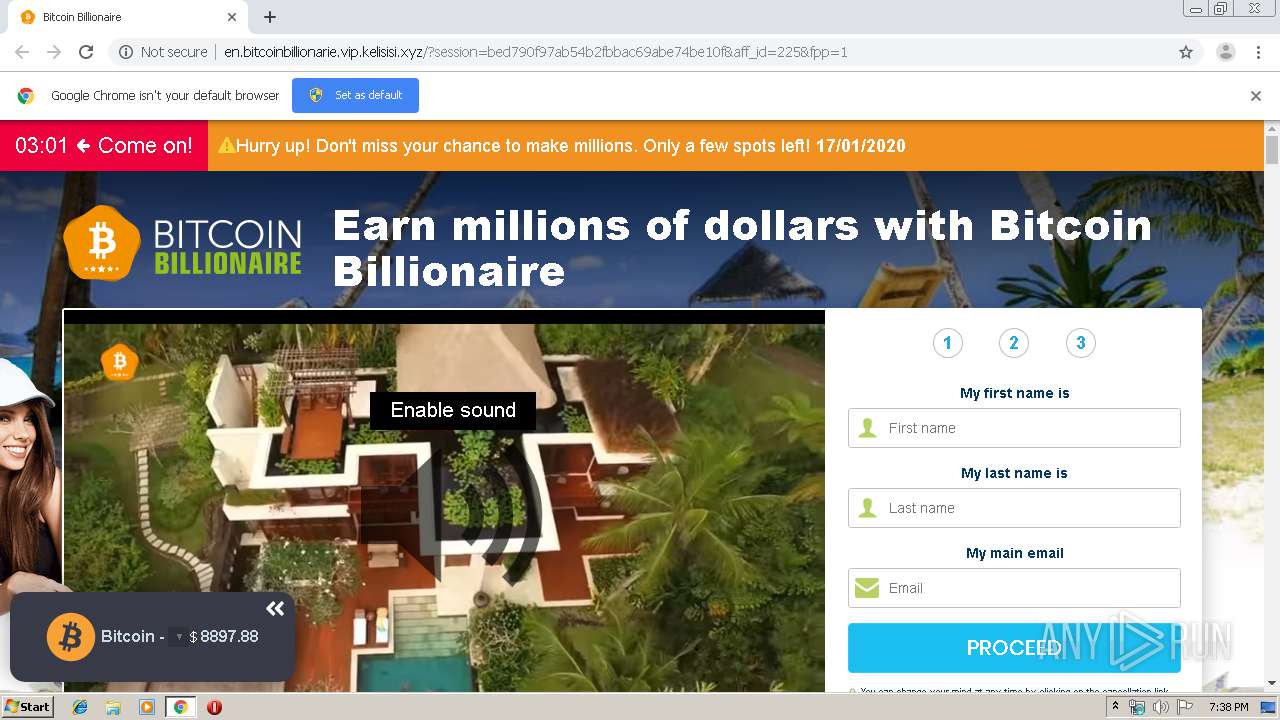
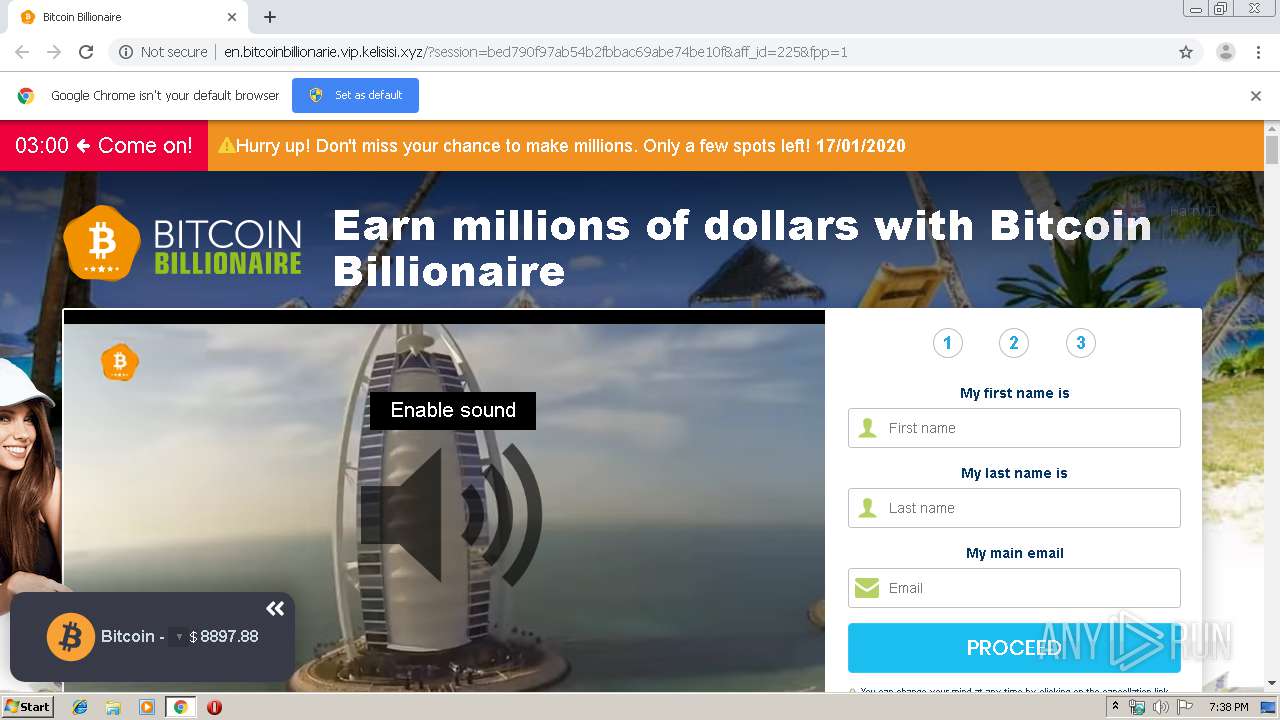
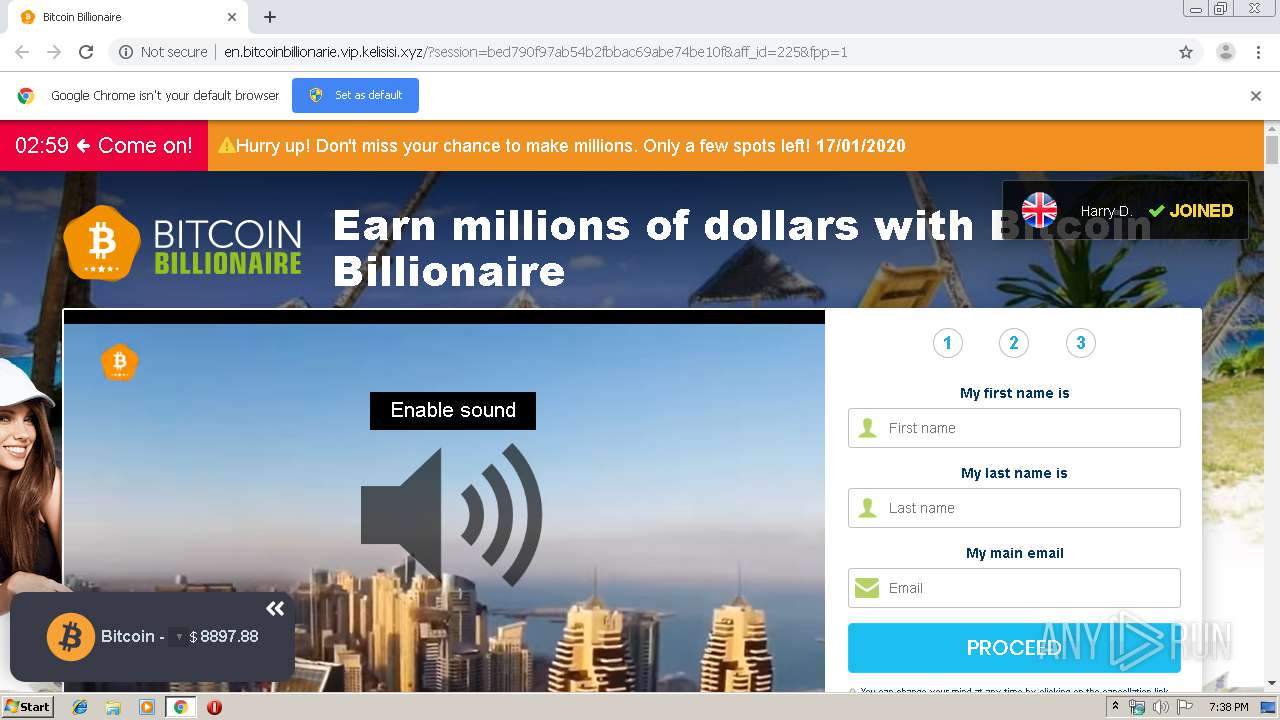
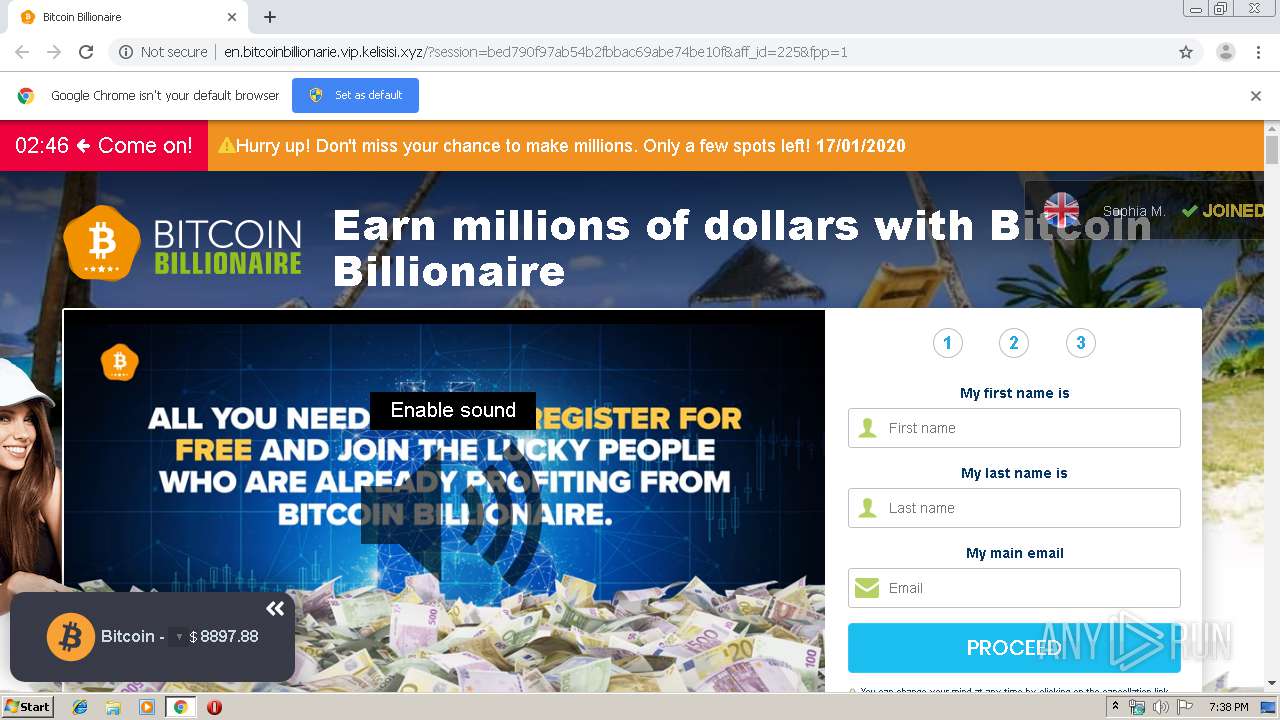
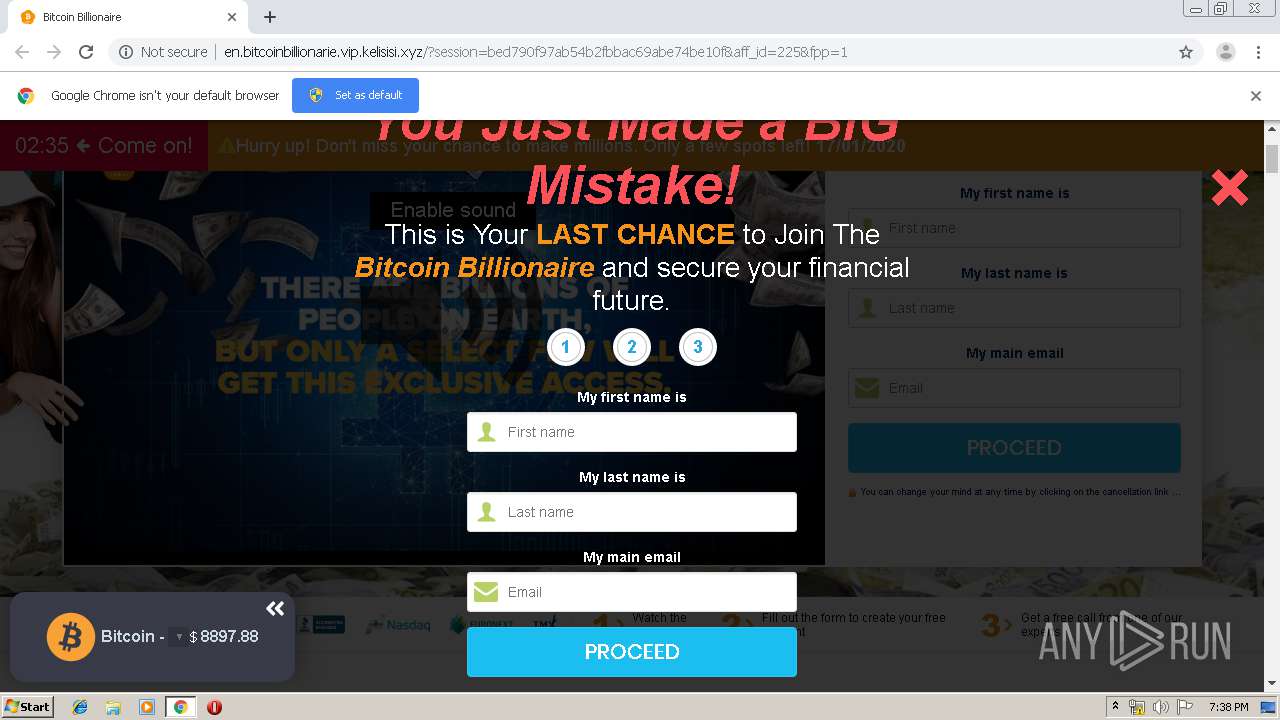
3720 | chrome.exe | GET | 200 | 104.24.96.120:80 | http://en.bitcoinbillionarie.vip.kelisisi.xyz/?session=bed790f97ab54b2fbbac69abe74be10f&aff_id=225&fpp=1 | US | html | 15.8 Kb | suspicious |
3720 | chrome.exe | GET | 200 | 104.24.96.120:80 | http://en.bitcoinbillionarie.vip.kelisisi.xyz/images/flags/GB.png | US | image | 2.66 Kb | suspicious |
3720 | chrome.exe | GET | 200 | 8.208.77.248:80 | http://lkeir4751.xyz/nl.html | US | html | 112 b | suspicious |
3720 | chrome.exe | GET | 200 | 104.24.96.120:80 | http://en.bitcoinbillionarie.vip.kelisisi.xyz/images/news-mix_en.jpg | US | image | 180 Kb | suspicious |
3720 | chrome.exe | GET | 200 | 104.24.96.120:80 | http://en.bitcoinbillionarie.vip.kelisisi.xyz/images/user_5.jpg | US | image | 4.76 Kb | suspicious |
3720 | chrome.exe | GET | 200 | 104.24.96.120:80 | http://en.bitcoinbillionarie.vip.kelisisi.xyz/images/user_1.jpg | US | image | 5.42 Kb | suspicious |
3720 | chrome.exe | GET | 200 | 104.24.96.120:80 | http://en.bitcoinbillionarie.vip.kelisisi.xyz/images/user_6.jpg | US | image | 5.29 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3720 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.18.97:443 | somereri1975.blogspot.com.ee | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.16.193:443 | themes.googleusercontent.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 172.217.16.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 8.208.77.248:80 | skinnerthomas.xyz | Level 3 Communications, Inc. | US | suspicious |
3720 | chrome.exe | 172.217.22.78:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3720 | chrome.exe | 104.24.96.120:80 | vip.kelisisi.xyz | Cloudflare Inc | US | shared |
3720 | chrome.exe | 104.24.97.120:80 | vip.kelisisi.xyz | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
somereri1975.blogspot.com.ee |
| whitelisted |
accounts.google.com |
| shared |
somereri1975.blogspot.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
themes.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
resources.blogblog.com |
| whitelisted |
www.blogger.com |
| shared |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3720 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |