| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/9adb94e6-a5f9-4475-8327-5315a7f2e60a |
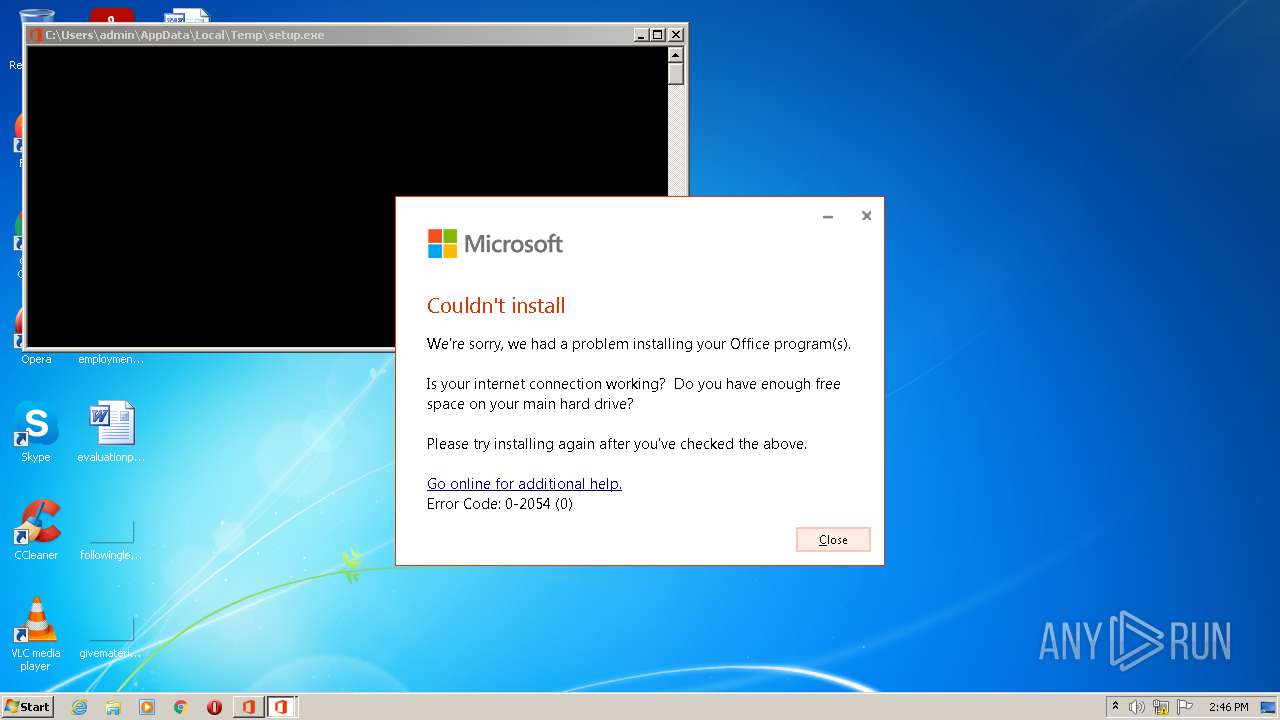
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2021, 13:46:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 91136349E80364A7F749B897570C6297 |
| SHA1: | FAC0661AE67575263293B2B013C520D1F021AF70 |
| SHA256: | C31270C8B3C949BFCF3ED256D442C403275B1B7EC374FDED4C4946D51036D206 |
| SSDEEP: | 98304:lWbf+IJuHHcCloqNvZNjtBEJ5TCxn0Xr9CBNw4MPC5P8ESg7PQEwY2h+FZ/:Eb2PoqNvZNjtyTHr9KNw4gI8ZgDQEWaR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- setup.exe (PID: 1728)
- setup.exe (PID: 3624)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 3932)
Reads the computer name
- setup.exe (PID: 1728)
- setup.exe (PID: 3624)
- powershell.exe (PID: 1868)
- powershell.exe (PID: 3932)
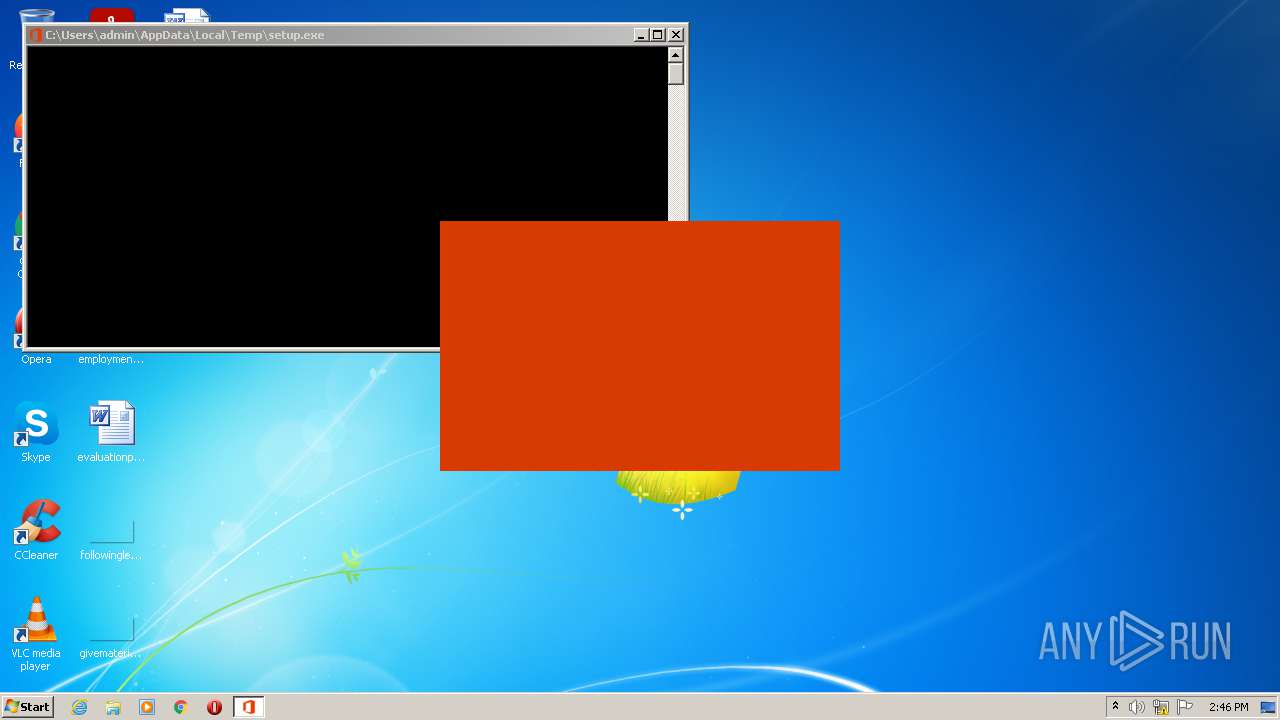
Application launched itself
- setup.exe (PID: 1728)
Reads the date of Windows installation
- powershell.exe (PID: 1868)
- powershell.exe (PID: 3932)
Executes PowerShell scripts
- setup.exe (PID: 3624)
Starts Internet Explorer
- setup.exe (PID: 3624)
Creates files in the user directory
- powershell.exe (PID: 1868)
- powershell.exe (PID: 3932)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3084)
INFO
Reads Microsoft Office registry keys
- setup.exe (PID: 1728)
- setup.exe (PID: 3624)
Reads settings of System Certificates
- setup.exe (PID: 3624)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 2172)
Checks supported languages
- iexplore.exe (PID: 2172)
- iexplore.exe (PID: 3084)
Reads the computer name
- iexplore.exe (PID: 2172)
- iexplore.exe (PID: 3084)
Reads internet explorer settings
- iexplore.exe (PID: 3084)
Application launched itself
- iexplore.exe (PID: 2172)
Changes internet zones settings
- iexplore.exe (PID: 2172)
Checks Windows Trust Settings
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 2172)
Creates files in the user directory
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 16.0.14026.20306 |
|---|---|
| ProductName: | Microsoft Office |
| OriginalFileName: | Bootstrapper.exe |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| InternalName: | Bootstrapper.exe |
| FileVersion: | 16.0.14026.20306 |
| FileDescription: | Microsoft Office |
| CompanyName: | Microsoft Corporation |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 16.0.14026.20306 |
| FileVersionNumber: | 16.0.14026.20306 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 5.2 |
| ImageVersion: | - |
| OSVersion: | 5.2 |
| EntryPoint: | 0x3b314a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2963968 |
| CodeSize: | 4366336 |
| LinkerVersion: | 14.28 |
| PEType: | PE32 |
| TimeStamp: | 2021:06:17 06:16:27+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 17-Jun-2021 04:16:27 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Office |
| FileVersion: | 16.0.14026.20306 |
| InternalName: | Bootstrapper.exe |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFilename: | Bootstrapper.exe |
| ProductName: | Microsoft Office |
| ProductVersion: | 16.0.14026.20306 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 17-Jun-2021 04:16:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00429FB9 | 0x0042A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70139 |
.rdata | 0x0042B000 | 0x001B0C14 | 0x001B0E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0848 |
.data | 0x005DC000 | 0x00034514 | 0x0002EA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.5763 |
.rsrc | 0x00611000 | 0x00095494 | 0x00095600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.4734 |
.reloc | 0x006A7000 | 0x00058FE4 | 0x00059000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.47672 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33138 | 1809 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.20562 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.87138 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
188 | 2.75178 | 182 | Latin 1 / Western European | English - United States | RT_STRING |
376 | 3.21432 | 2024 | Latin 1 / Western European | English - United States | RT_STRING |
377 | 3.2276 | 2432 | Latin 1 / Western European | English - United States | RT_STRING |
378 | 3.24318 | 2176 | Latin 1 / Western European | English - United States | RT_STRING |
379 | 3.27442 | 964 | Latin 1 / Western European | English - United States | RT_STRING |
380 | 3.36591 | 1170 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
RstrtMgr.DLL |
SETUPAPI.dll |
WINTRUST.dll |
WS2_32.dll |
api-ms-win-core-winrt-string-l1-1-0.dll (delay-loaded) |
Total processes
47
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1728 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Exit code: 0 Version: 16.0.14026.20306 Modules
| |||||||||||||||
| 1868 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile "$package = Get-AppxPackage Microsoft.Office.Desktop -allUsers; if (!$package) { $Error.Add(\"Package is not installed\")}; if ($error.Count -eq 0) { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '1' -Encoding ascii; } else { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '0' -Encoding ascii; Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateError.scratch' -InputObject $error -Encoding ascii;} " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
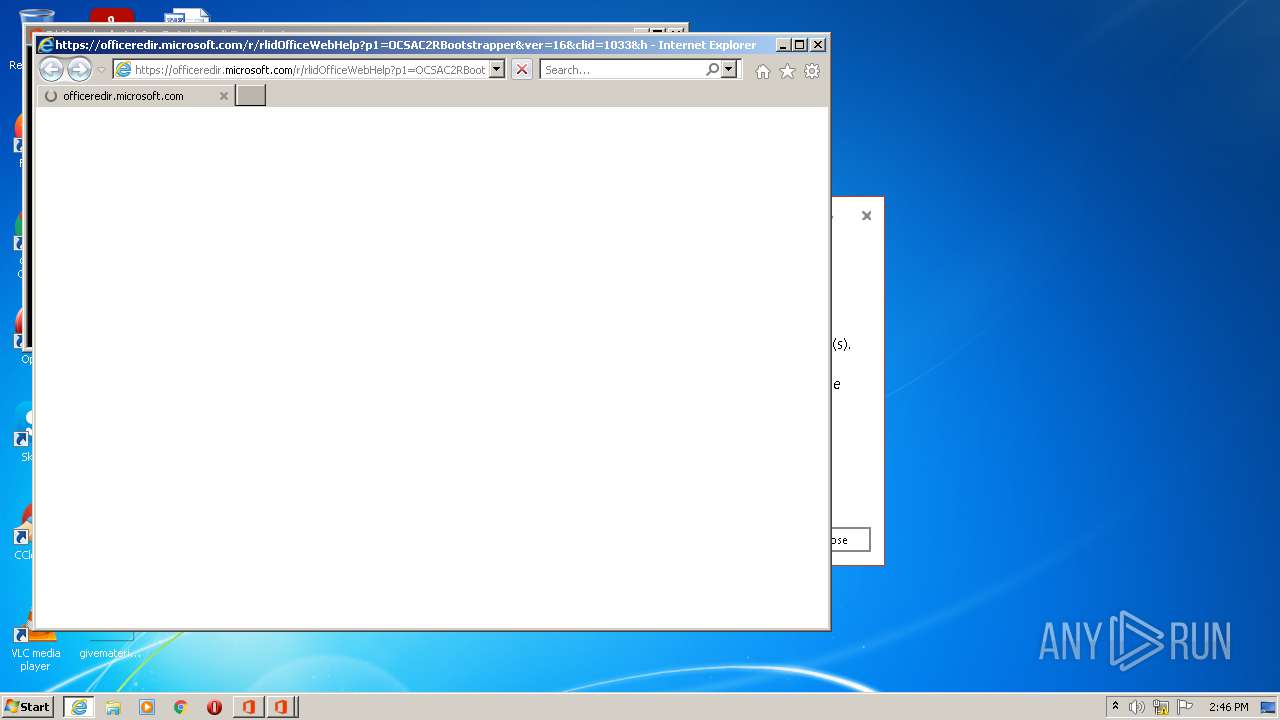
| 2172 | "C:\Program Files\Internet Explorer\iexplore.exe" https://officeredir.microsoft.com/r/rlidOfficeWebHelp?p1=OCSAC2RBootstrapper&ver=16&clid=1033&helpid=%220-2054-0%22&app=webview | C:\Program Files\Internet Explorer\iexplore.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3084 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2172 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3624 | "C:\Users\admin\AppData\Local\Temp\setup.exe" ELEVATED sid=S-1-5-21-1302019708-1500728564-335382590-1000 | C:\Users\admin\AppData\Local\Temp\setup.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Exit code: 0 Version: 16.0.14026.20306 Modules
| |||||||||||||||
| 3932 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile "$package = Get-AppxPackage Microsoft.Office.Desktop -allUsers; if (!$package) { $Error.Add(\"Package is not installed\")}; if ($error.Count -eq 0) { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '1' -Encoding ascii; } else { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateResult.scratch' -InputObject '0' -Encoding ascii; Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Office.ValidateError.scratch' -InputObject $error -Encoding ascii;} " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20 000
Read events
19 611
Write events
386
Delete events
3
Modification events
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | UIFallbackLanguages |
Value: x-none | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | HelpLanguageTag |
Value: en-US | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PreviousPreferredEditingLanguage |
Value: en-US | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | WordChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | WordMailChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | XLChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | PPTChangeInstallLanguage |
Value: No | |||
| (PID) Process: | (1728) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources |
| Operation: | write | Name: | AccessChangeInstallLanguage |
Value: No | |||
Executable files
0
Suspicious files
13
Text files
18
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1868 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2b4351.TMP | binary | |
MD5:— | SHA256:— | |||
| 1868 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\B2MSCP6C6P2NKW8NWP0X.temp | binary | |
MD5:— | SHA256:— | |||
| 3932 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2b4564.TMP | binary | |
MD5:— | SHA256:— | |||
| 1868 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3932 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XS5ABGKWCY79SK2ROYEK.temp | binary | |
MD5:— | SHA256:— | |||
| 3932 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 3084 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
40
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1356 | svchost.exe | GET | — | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3084 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3084 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1356 | svchost.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | der | 814 b | whitelisted |
2172 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3084 | iexplore.exe | GET | 200 | 205.185.216.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?09ee5e733194c58a | US | compressed | 4.70 Kb | whitelisted |
3084 | iexplore.exe | GET | 200 | 205.185.216.42:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d94c9532ea61a6d7 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2172 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3084 | iexplore.exe | 23.47.208.117:443 | support.microsoft.com | NTT DOCOMO, INC. | US | malicious |
1728 | setup.exe | 52.113.194.132:443 | ecs.office.com | Microsoft Corporation | US | suspicious |
3624 | setup.exe | 52.113.194.132:443 | ecs.office.com | Microsoft Corporation | US | suspicious |
1356 | svchost.exe | 40.77.226.250:443 | vortex-win.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
3084 | iexplore.exe | 52.109.88.176:443 | officeredir.microsoft.com | Microsoft Corporation | NL | suspicious |
3084 | iexplore.exe | 205.185.216.42:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3084 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3084 | iexplore.exe | 2.17.182.72:443 | support.office.com | Akamai Technologies, Inc. | — | unknown |
2172 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ecs.office.com |
| whitelisted |
vortex-win.data.microsoft.com |
| whitelisted |
officeredir.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
support.office.com |
| whitelisted |
support.microsoft.com |
| malicious |
iecvlist.microsoft.com |
| whitelisted |