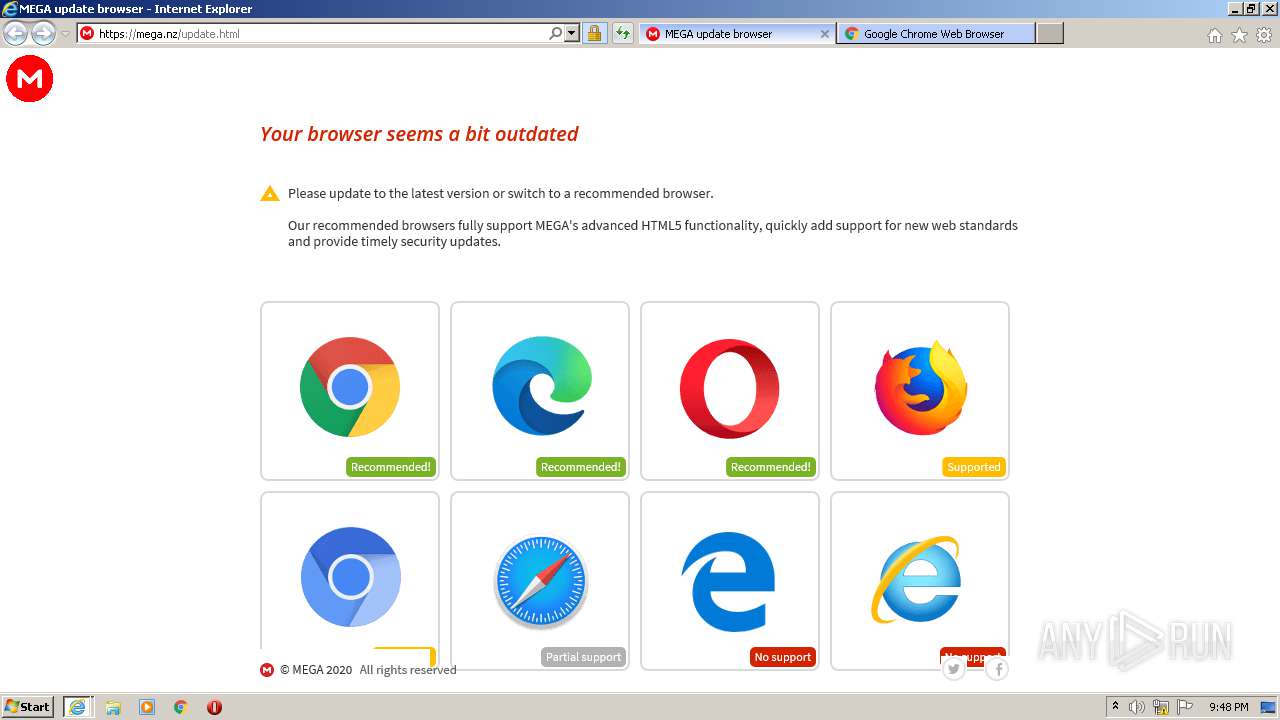
| URL: | https://mega.nz/folder/mHJWzZDS#o0yOModu4PuRUjXDvUTOHA |
| Full analysis: | https://app.any.run/tasks/c1ae35de-d2d6-43f0-a364-2464b094f9df |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 20:47:15 |
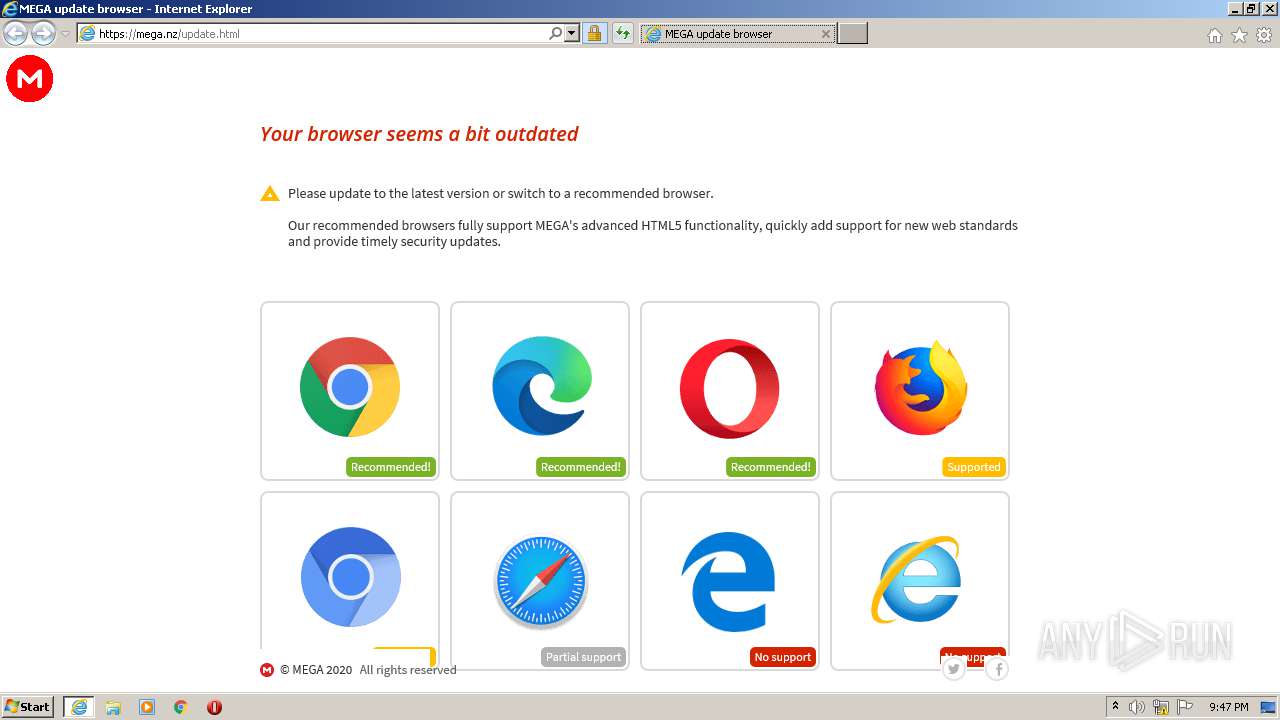
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4B3EEDE49A506F72AA08B489AE46CB54 |
| SHA1: | 484033A515B1464B5773C19BFEB60B77198F2C83 |
| SHA256: | C2FEDC711BE112AF8640E08C8582CFAB105BF074642851674190ACED01E49918 |
| SSDEEP: | 3:N8X/iuyK6esEaGhgj:26EXa/j |
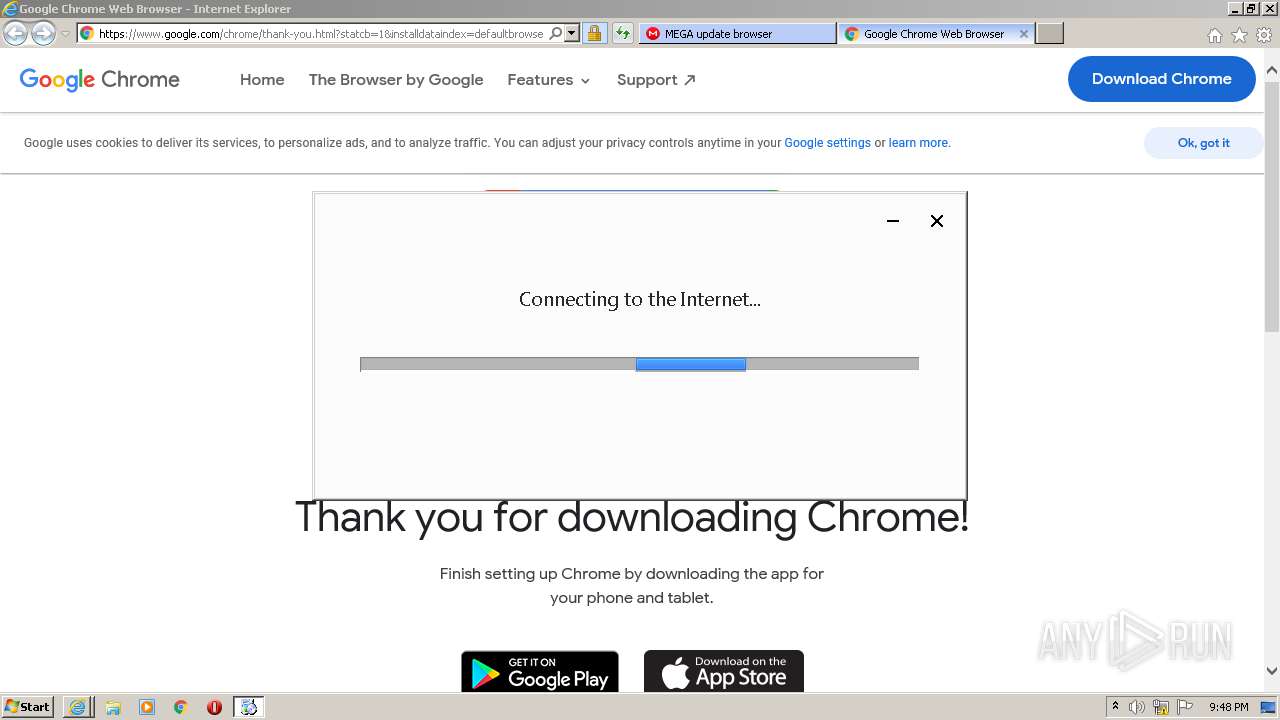
MALICIOUS
Application was dropped or rewritten from another process
- ChromeSetup.exe (PID: 656)
- GoogleUpdate.exe (PID: 992)
- GoogleUpdateSetup.exe (PID: 2204)
- GoogleUpdate.exe (PID: 2444)
Loads dropped or rewritten executable
- GoogleUpdate.exe (PID: 992)
- GoogleUpdate.exe (PID: 2444)
- GoogleUpdate.exe (PID: 1416)
- GoogleUpdate.exe (PID: 2868)
- GoogleUpdate.exe (PID: 3220)
- GoogleUpdate.exe (PID: 2216)
- GoogleUpdate.exe (PID: 868)
- GoogleUpdate.exe (PID: 1964)
Loads the Task Scheduler COM API
- GoogleUpdate.exe (PID: 2444)
Changes settings of System certificates
- GoogleUpdate.exe (PID: 2868)
SUSPICIOUS
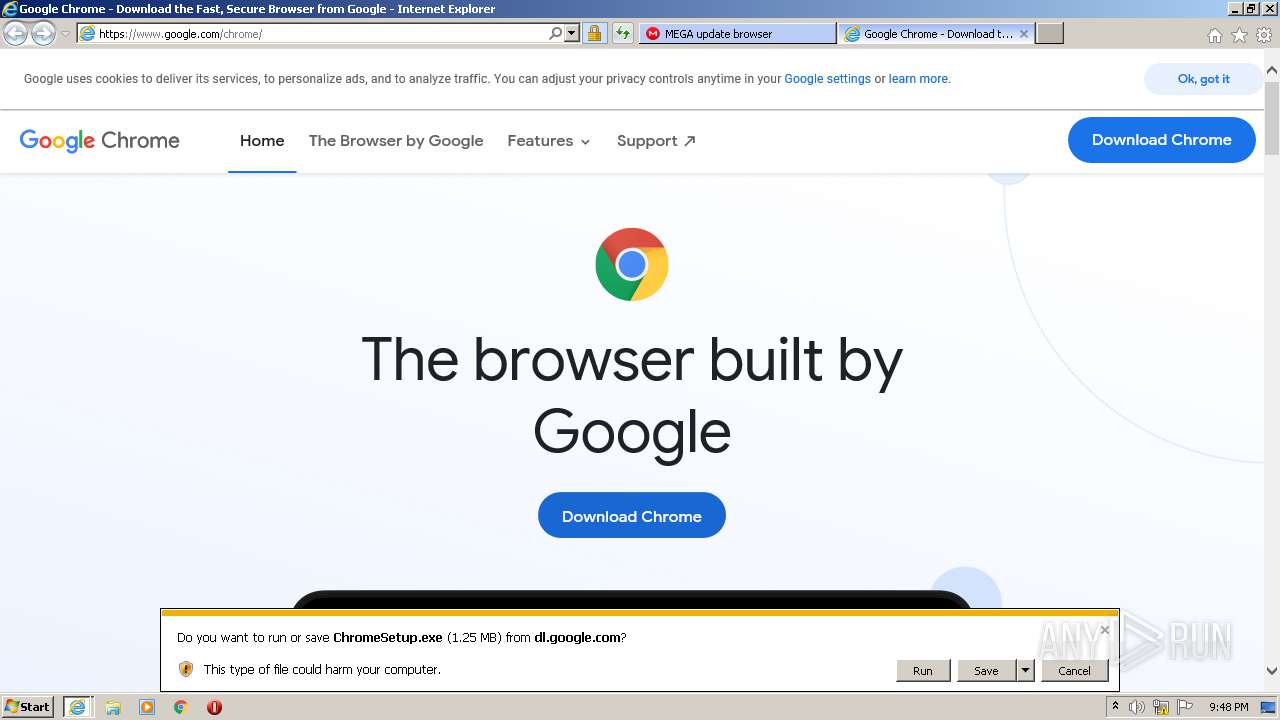
Executable content was dropped or overwritten
- iexplore.exe (PID: 2552)
- iexplore.exe (PID: 2464)
- ChromeSetup.exe (PID: 656)
- GoogleUpdate.exe (PID: 2444)
- GoogleUpdateSetup.exe (PID: 2204)
Creates files in the program directory
- GoogleUpdateSetup.exe (PID: 2204)
- GoogleUpdate.exe (PID: 2444)
Disables SEHOP
- GoogleUpdate.exe (PID: 2444)
Application launched itself
- GoogleUpdate.exe (PID: 868)
Creates COM task schedule object
- GoogleUpdate.exe (PID: 2216)
Executed as Windows Service
- GoogleUpdate.exe (PID: 868)
Adds / modifies Windows certificates
- GoogleUpdate.exe (PID: 2868)
Executed via COM
- DllHost.exe (PID: 2728)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 1496)
- iexplore.exe (PID: 2552)
Reads settings of System Certificates
- iexplore.exe (PID: 2464)
- iexplore.exe (PID: 1496)
- iexplore.exe (PID: 2552)
Changes internet zones settings
- iexplore.exe (PID: 2464)
Application launched itself
- iexplore.exe (PID: 2464)
- chrome.exe (PID: 3912)
Reads internet explorer settings
- iexplore.exe (PID: 1496)
- iexplore.exe (PID: 2552)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2464)
Creates files in the user directory
- iexplore.exe (PID: 2552)
- iexplore.exe (PID: 2464)
Changes settings of System certificates
- iexplore.exe (PID: 2464)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2464)
Manual execution by user
- chrome.exe (PID: 3912)
Modifies the open verb of a shell class
- chrome.exe (PID: 3912)
Reads the hosts file
- chrome.exe (PID: 272)
- chrome.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
30
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,14338818857144182858,14584614173528169290,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6831586726591446795 --mojo-platform-channel-handle=1596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,14338818857144182858,14584614173528169290,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7797609821295637288 --mojo-platform-channel-handle=3004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\ChromeSetup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\ChromeSetup.exe | iexplore.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Update Setup Exit code: 2147747856 Version: 1.3.36.32 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,14338818857144182858,14584614173528169290,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4453311934526531733 --mojo-platform-channel-handle=3368 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /svc | C:\Program Files\Google\Update\GoogleUpdate.exe | services.exe | ||||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: SYSTEM Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 992 | C:\Users\admin\AppData\Local\Temp\GUM9497.tmp\GoogleUpdate.exe /installsource taggedmi /install "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={2145529A-CD46-93C8-954D-0D1482C70233}&lang=en&browser=2&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=stable-arch_x86-statsdef_1&installdataindex=defaultbrowser" | C:\Users\admin\AppData\Local\Temp\GUM9497.tmp\GoogleUpdate.exe | — | ChromeSetup.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Installer Exit code: 2147747856 Version: 1.3.36.31 Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /regsvc | C:\Program Files\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2464 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,14338818857144182858,14584614173528169290,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16464241816913103432 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,14338818857144182858,14584614173528169290,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11404354003810385126 --mojo-platform-channel-handle=3520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 611
Read events
2 394
Write events
1 075
Delete events
142
Modification events
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 685335270 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844505 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
210
Suspicious files
110
Text files
157
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1496 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab4ADC.tmp | — | |
MD5:— | SHA256:— | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4ADD.tmp | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab5F10.tmp | — | |
MD5:— | SHA256:— | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar5F11.tmp | — | |
MD5:— | SHA256:— | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0DCE0DB770F344BE5235C09F571E5D82 | der | |
MD5:— | SHA256:— | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\024823B39FBEACCDB5C06426A8168E99_D68CE7E43423900A941540A442CDF262 | der | |
MD5:— | SHA256:— | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0DCE0DB770F344BE5235C09F571E5D82 | binary | |
MD5:— | SHA256:— | |||
| 1496 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
106
DNS requests
46
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1496 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEDaCXn%2B1pIGTfvbRc2u5PKY%3D | US | der | 727 b | whitelisted |
1496 | iexplore.exe | GET | 200 | 2.16.177.210:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2552 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCYiHlVi1YSqAgAAAAAWy82 | US | der | 472 b | whitelisted |
1496 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQLqIKj6Gi5thHaqKC1ECU9aXsCRQQUmvMr2s%2BtT7YvuypISCoStxtCwSQCEFqIMDLoe3Fk8%2BTO2VcKXOA%3D | US | der | 471 b | whitelisted |
1496 | iexplore.exe | GET | 200 | 2.16.177.160:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgSVjiwq9XdSbtMbXftq8PMFzw%3D%3D | unknown | der | 527 b | whitelisted |
2552 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEB3oRgfjsJWUCAAAAABbLrQ%3D | US | der | 471 b | whitelisted |
2552 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECiWpPQxRDpPAgAAAAB8NWE%3D | US | der | 471 b | whitelisted |
2552 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCOUTy4wn8XWggAAAAAWy8I | US | der | 472 b | whitelisted |
2552 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD6dnW313dJuggAAAAAXcH8 | US | der | 472 b | whitelisted |
2552 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQD6dnW313dJuggAAAAAXcH8 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1496 | iexplore.exe | 89.44.169.135:443 | mega.nz | Datacenter Luxembourg S.A. | LU | suspicious |
1496 | iexplore.exe | 2.16.177.160:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | unknown |
1496 | iexplore.exe | 66.203.124.37:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
1496 | iexplore.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1496 | iexplore.exe | 2.16.177.210:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | unknown |
2464 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2552 | iexplore.exe | 216.58.210.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2552 | iexplore.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2552 | iexplore.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2552 | iexplore.exe | 172.217.23.142:443 | tools.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
eu.static.mega.co.nz |
| shared |
ocsp.comodoca.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| malicious |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |