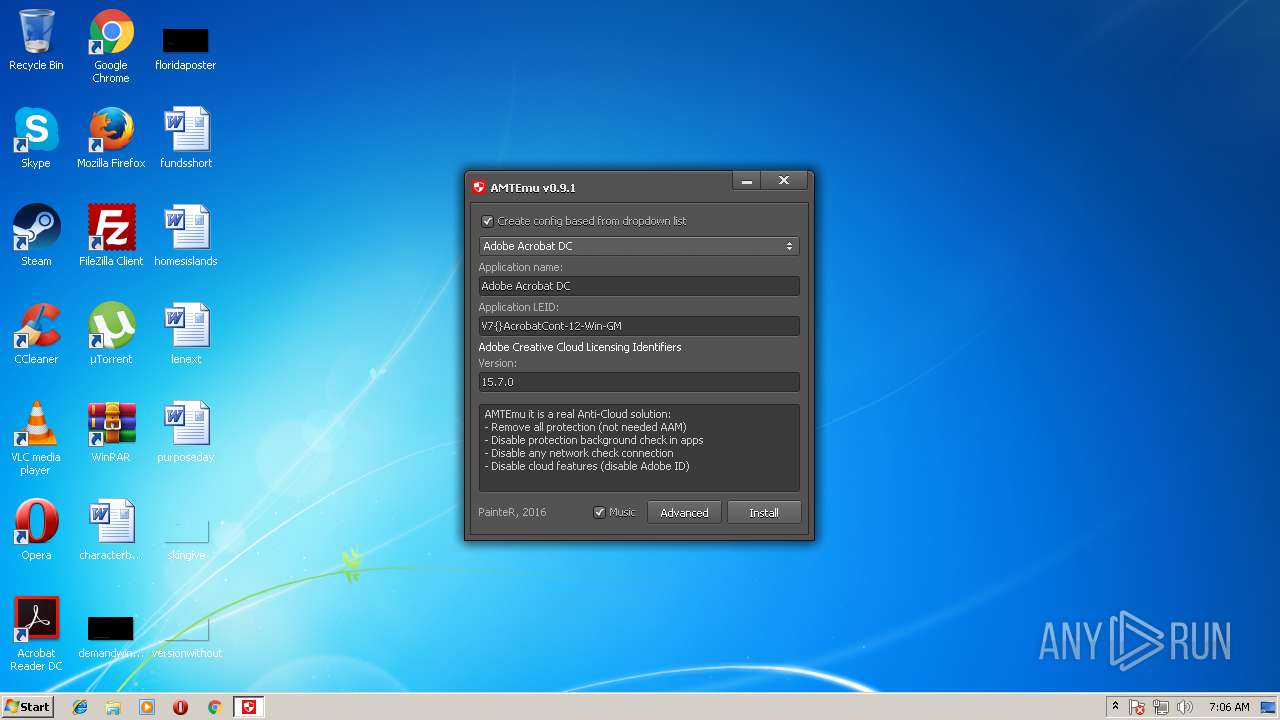
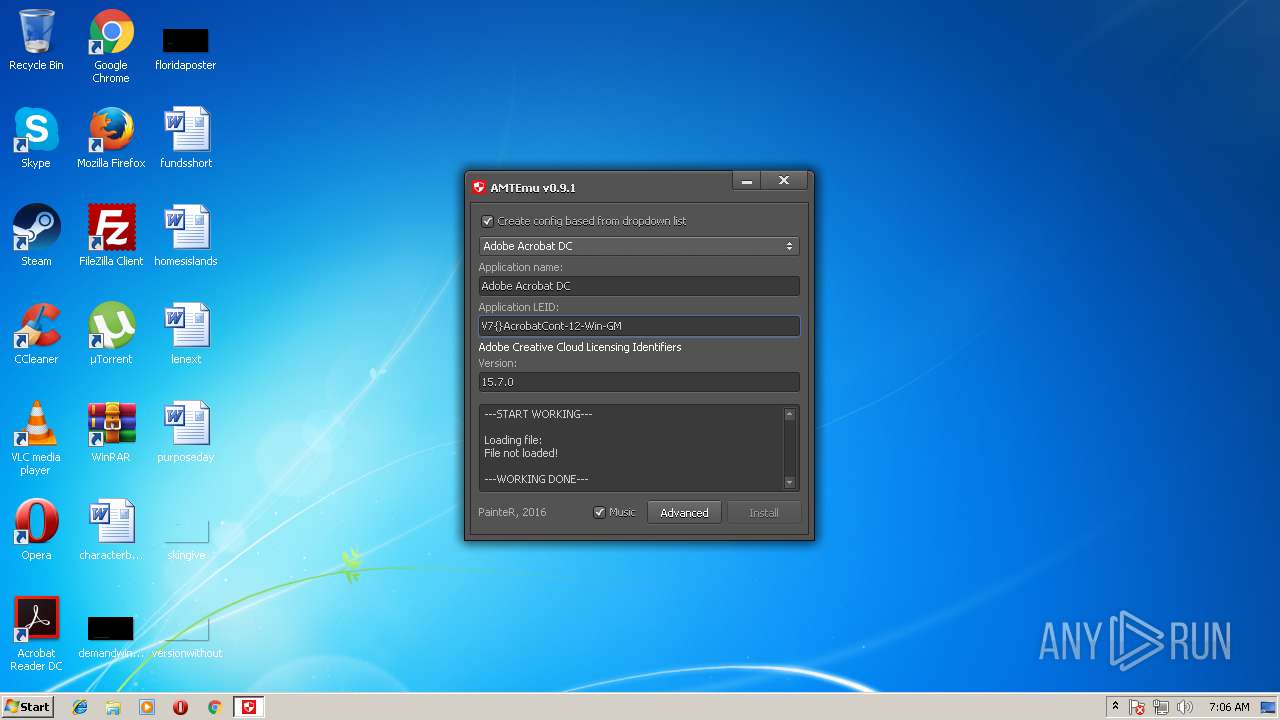
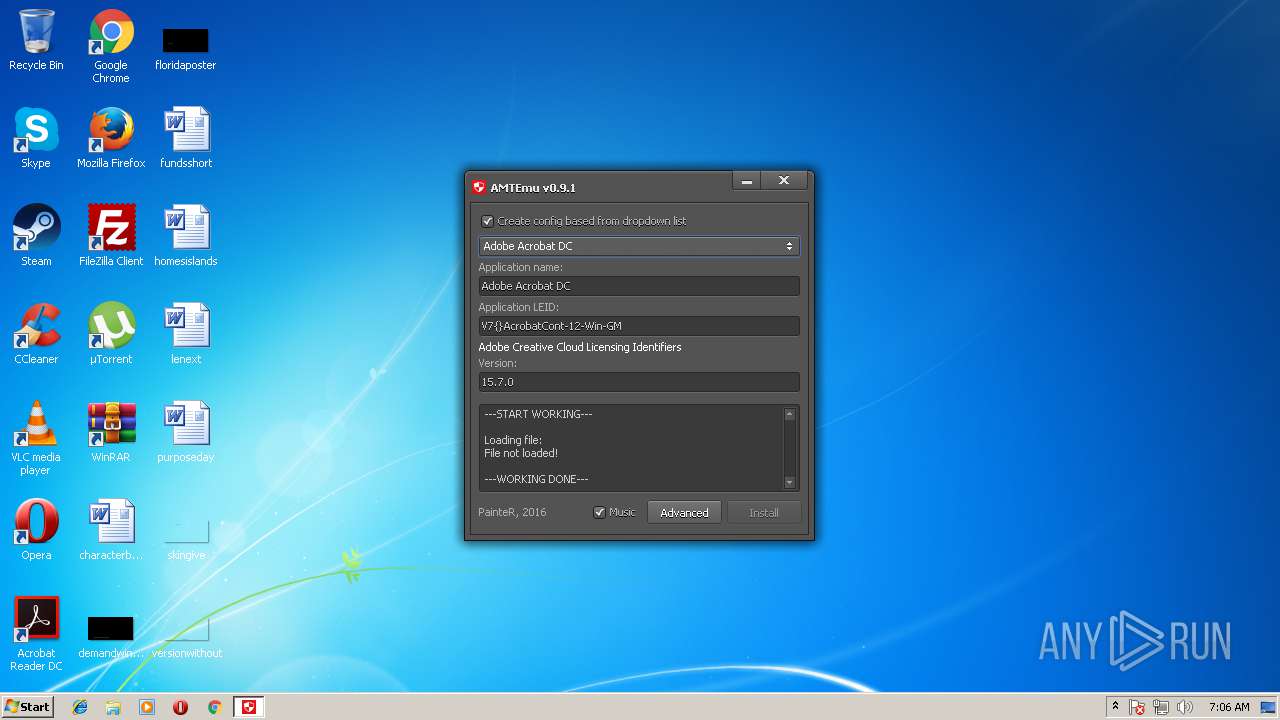
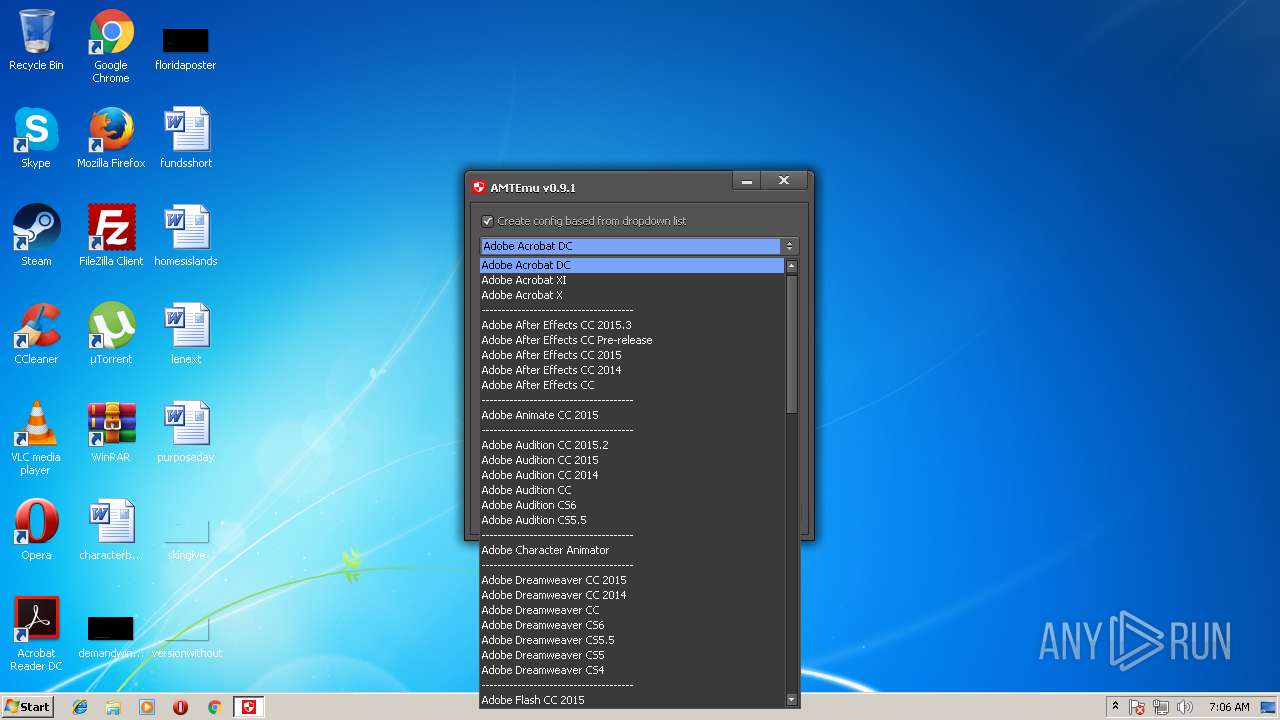
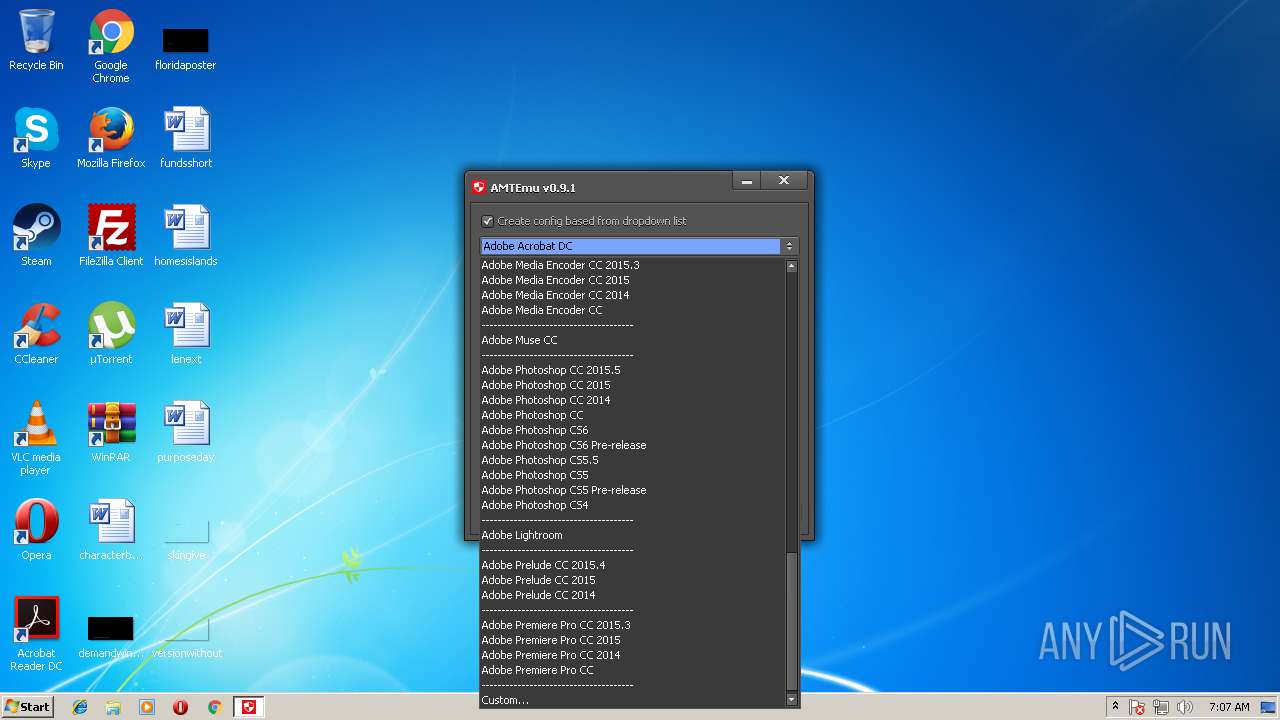
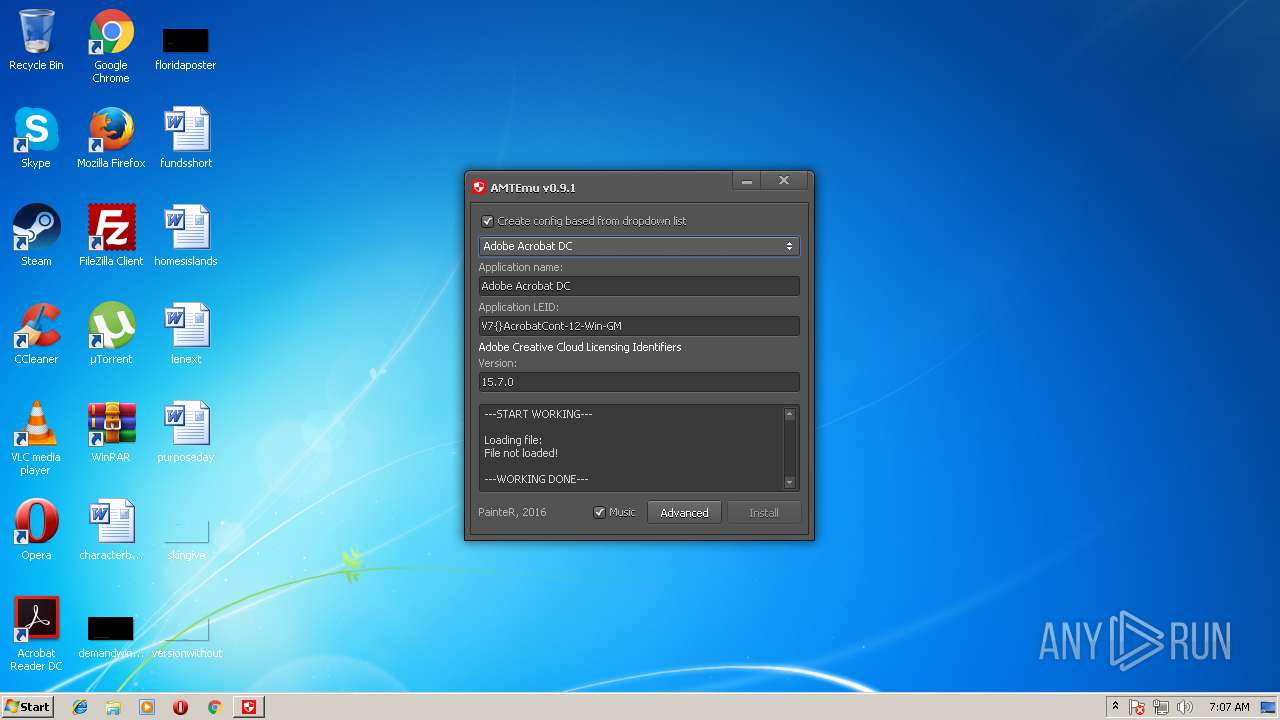
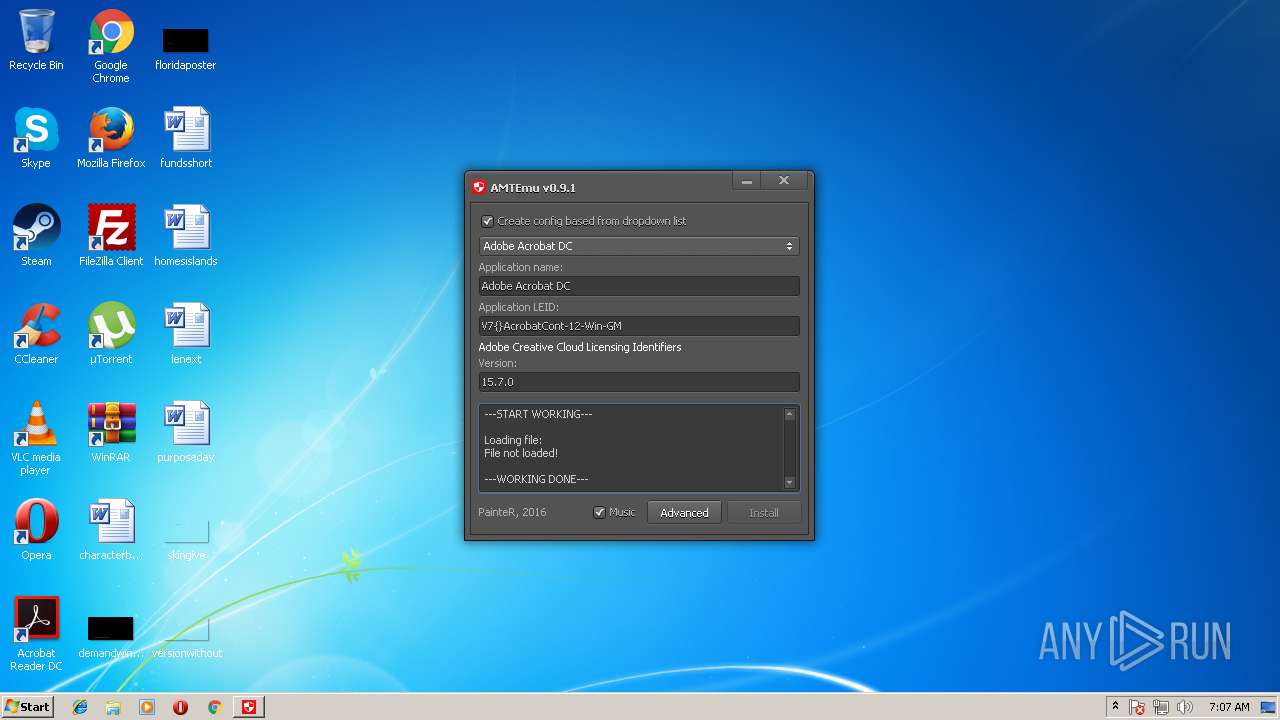
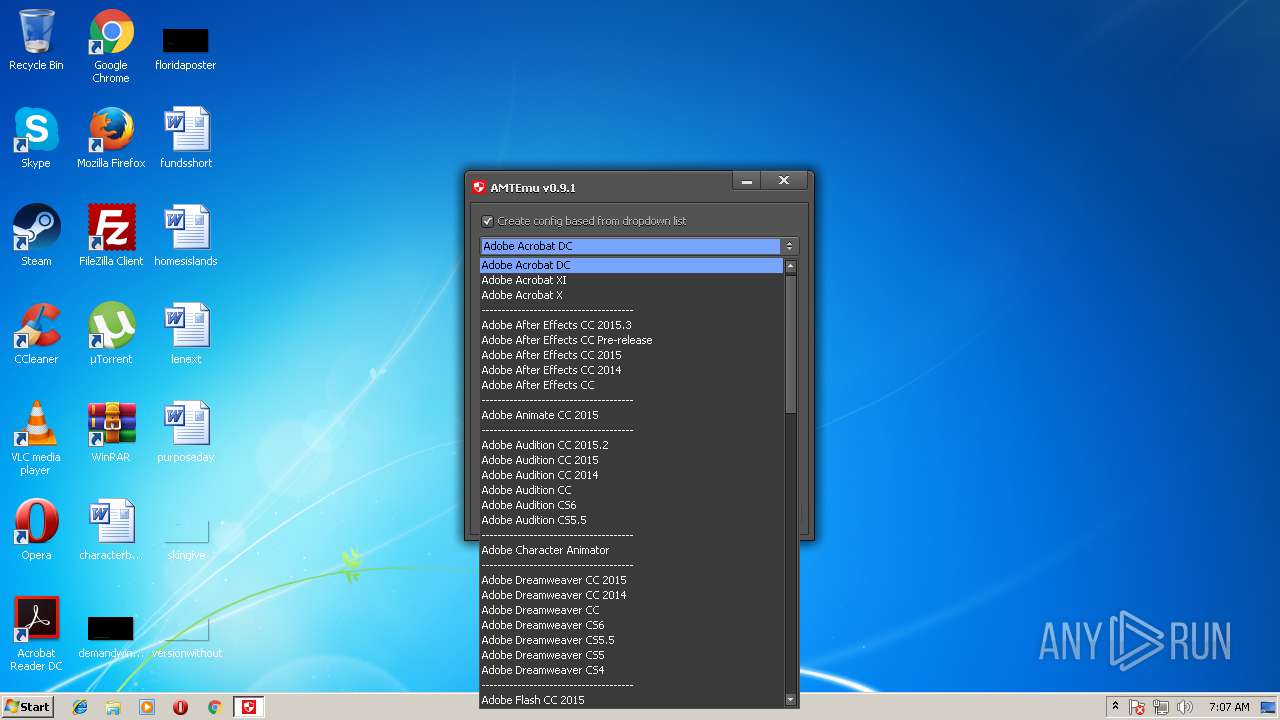
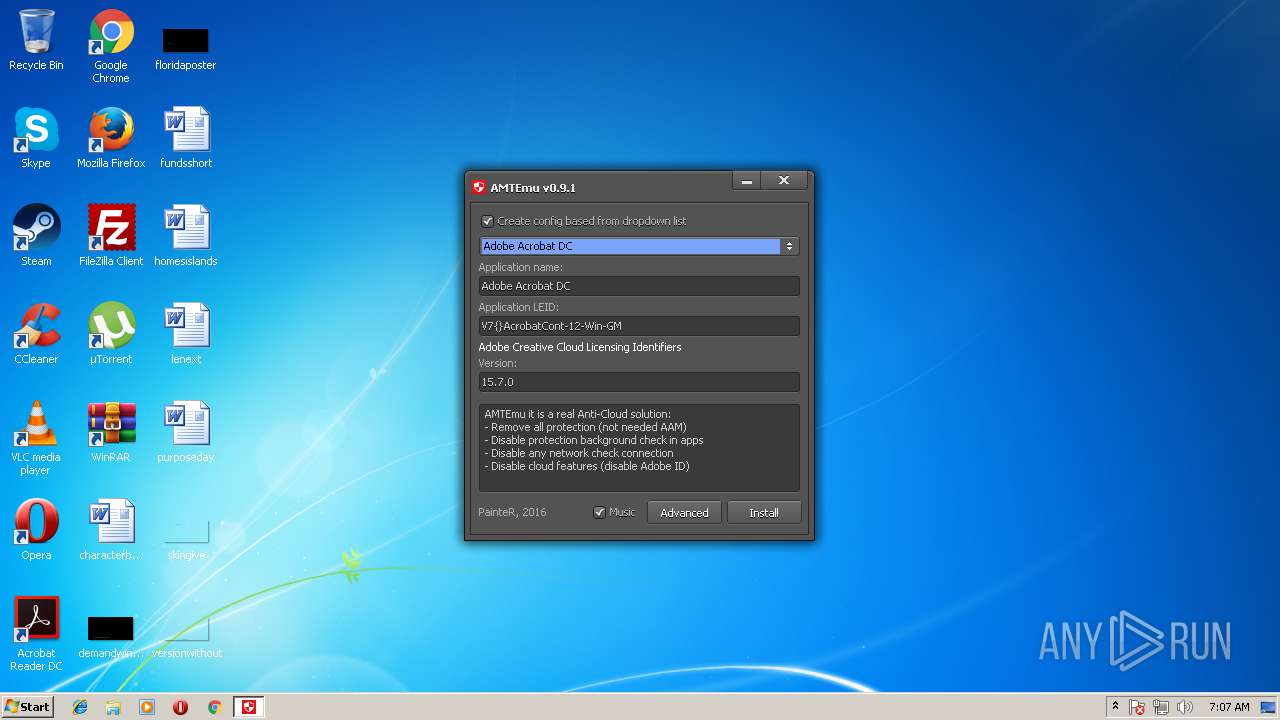
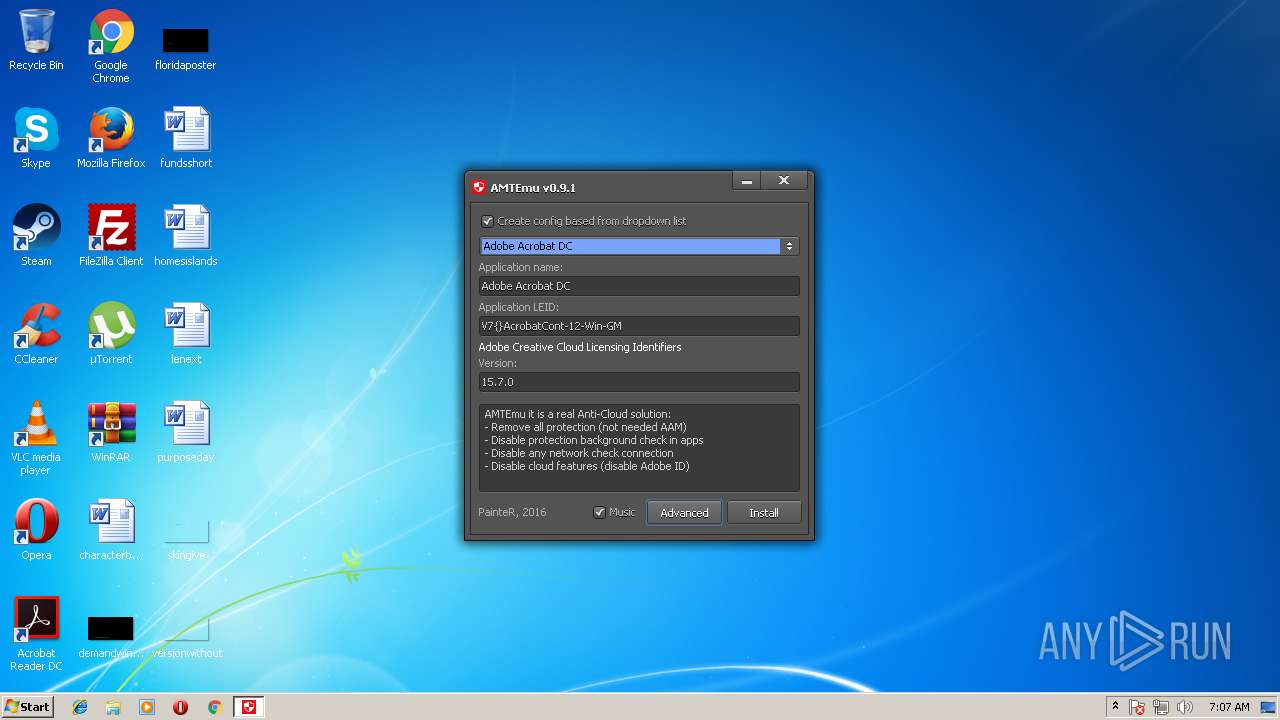
| File name: | amtemu.v0.9.1-painter.exe |
| Full analysis: | https://app.any.run/tasks/dedc9b2c-487b-4680-a8fd-1d63eac34379 |
| Verdict: | No threats detected |
| Analysis date: | July 21, 2018, 06:06:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A209B88B9B2CF7339BE0AC5126417875 |
| SHA1: | 16CCCEF91EE368F9E4BBF09C5EAB30865B380150 |
| SHA256: | C2F6D462A20F92B97C49C3AF19872FC4DF6AABD4F66F4B8B298A1303881422F6 |
| SSDEEP: | 49152:4keFZ2jcLaZBHiMT0uR5Y+BdxyHSSzZLMZ:4kTZBCHuvFkGZ |
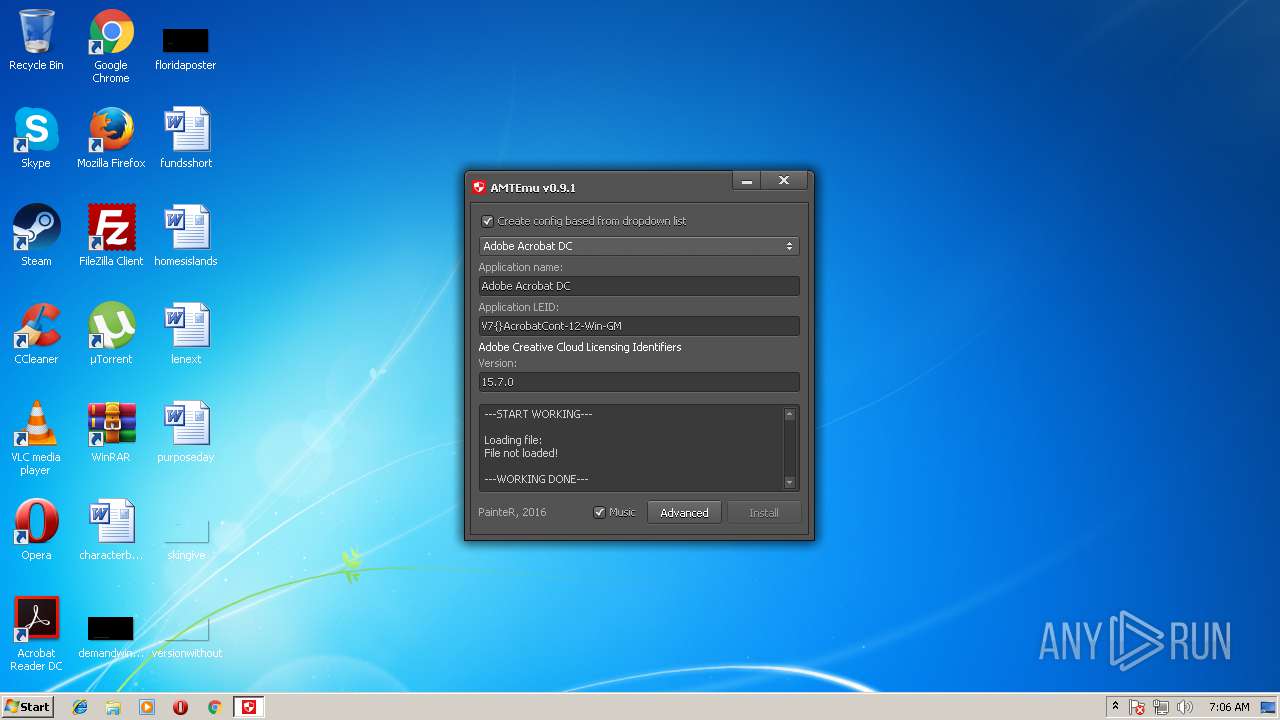
MALICIOUS
Loads dropped or rewritten executable
- amtemu.v0.9.1-painter.exe (PID: 1732)
SUSPICIOUS
Executable content was dropped or overwritten
- amtemu.v0.9.1-painter.exe (PID: 1732)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (43.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (21.7) |
| .exe | | | Win32 Executable (generic) (14.8) |
| .exe | | | Win16/32 Executable Delphi generic (6.8) |
| .exe | | | Generic Win/DOS Executable (6.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1127936 |
| InitializedDataSize: | 537600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2519f4 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.9.1.0 |
| ProductVersionNumber: | 0.9.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Unicode |
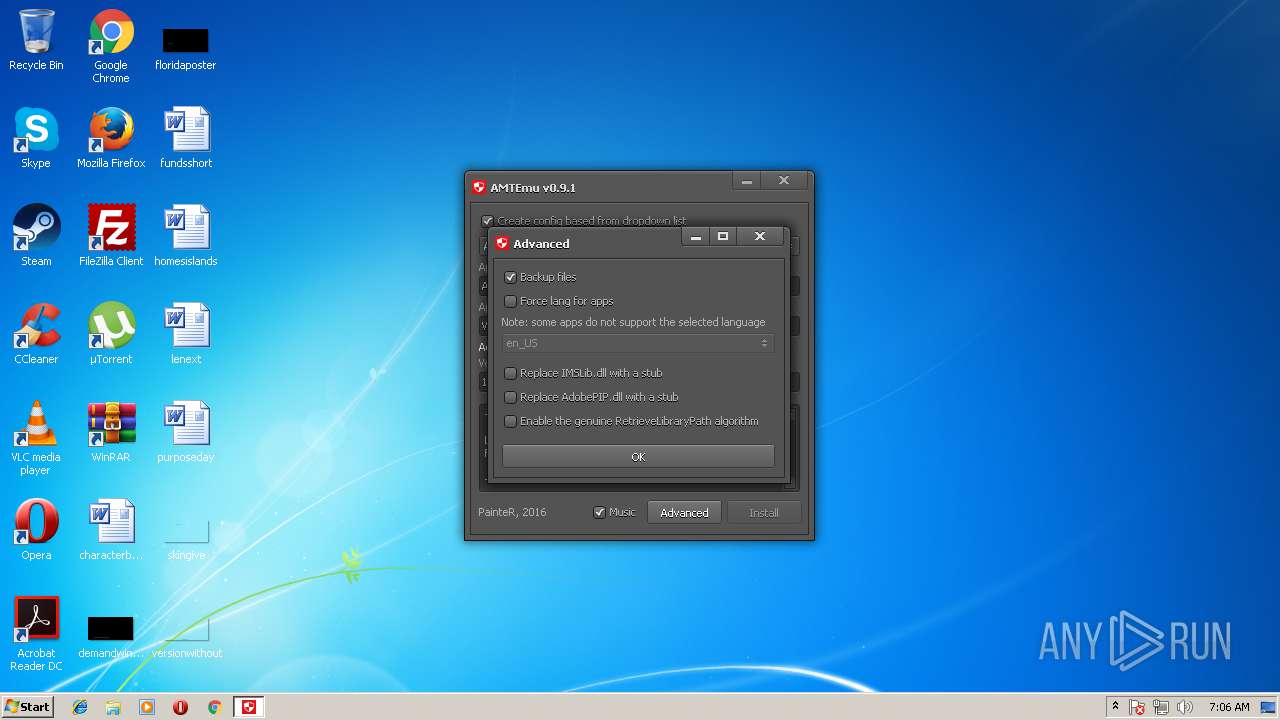
| CompanyName: | PainteR |
| FileDescription: | ProxyEmu |
| FileVersion: | 0.9.1.0 |
| InternalName: | ProxyEmu |
| LegalCopyright: | painter |
| OriginalFileName: | emuext.exe |
| ProductName: | ProxyEmu |
| ProductVersion: | 0.9.1.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | PainteR |
| FileDescription: | ProxyEmu |
| FileVersion: | 0.9.1.0 |
| InternalName: | ProxyEmu |
| LegalCopyright: | painter |
| OriginalFilename: | emuext.exe |
| ProductName: | ProxyEmu |
| ProductVersion: | 0.9.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x001135E4 | 0x00113600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52759 |
DATA | 0x00115000 | 0x00015A2C | 0x00015C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.13416 |
BSS | 0x0012B000 | 0x000011BD | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0012D000 | 0x000029B4 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.09062 |
.tls | 0x00130000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00131000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.164765 |
.pr0 | 0x00132000 | 0x0011CBE1 | 0x0011CC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89947 |
.pr1 | 0x0024F000 | 0x0000F468 | 0x0000F600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.22087 |
.reloc | 0x0025F000 | 0x0000F4D4 | 0x0000F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.66781 |
.rsrc | 0x0026F000 | 0x00005E92 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.0178 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27457 | 1418 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.28302 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.36835 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.39554 | 1128 | UNKNOWN | English - United States | RT_ICON |
MAINICON | 2.88469 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1708 | "C:\Users\admin\AppData\Local\Temp\amtemu.v0.9.1-painter.exe" | C:\Users\admin\AppData\Local\Temp\amtemu.v0.9.1-painter.exe | — | explorer.exe | |||||||||||
User: admin Company: PainteR Integrity Level: MEDIUM Description: ProxyEmu Exit code: 3221226540 Version: 0.9.1.0 Modules
| |||||||||||||||
| 1732 | "C:\Users\admin\AppData\Local\Temp\amtemu.v0.9.1-painter.exe" | C:\Users\admin\AppData\Local\Temp\amtemu.v0.9.1-painter.exe | explorer.exe | ||||||||||||
User: admin Company: PainteR Integrity Level: HIGH Description: ProxyEmu Exit code: 0 Version: 0.9.1.0 Modules
| |||||||||||||||
Total events
556
Read events
465
Write events
88
Delete events
3
Modification events
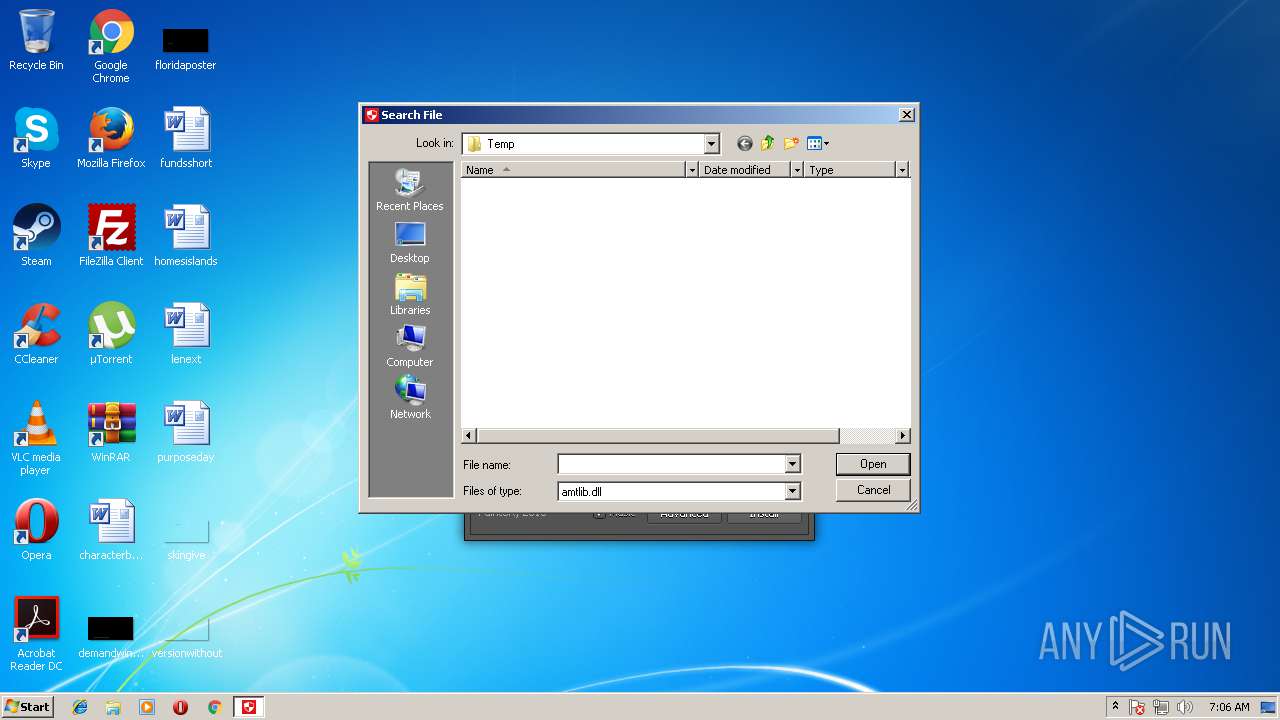
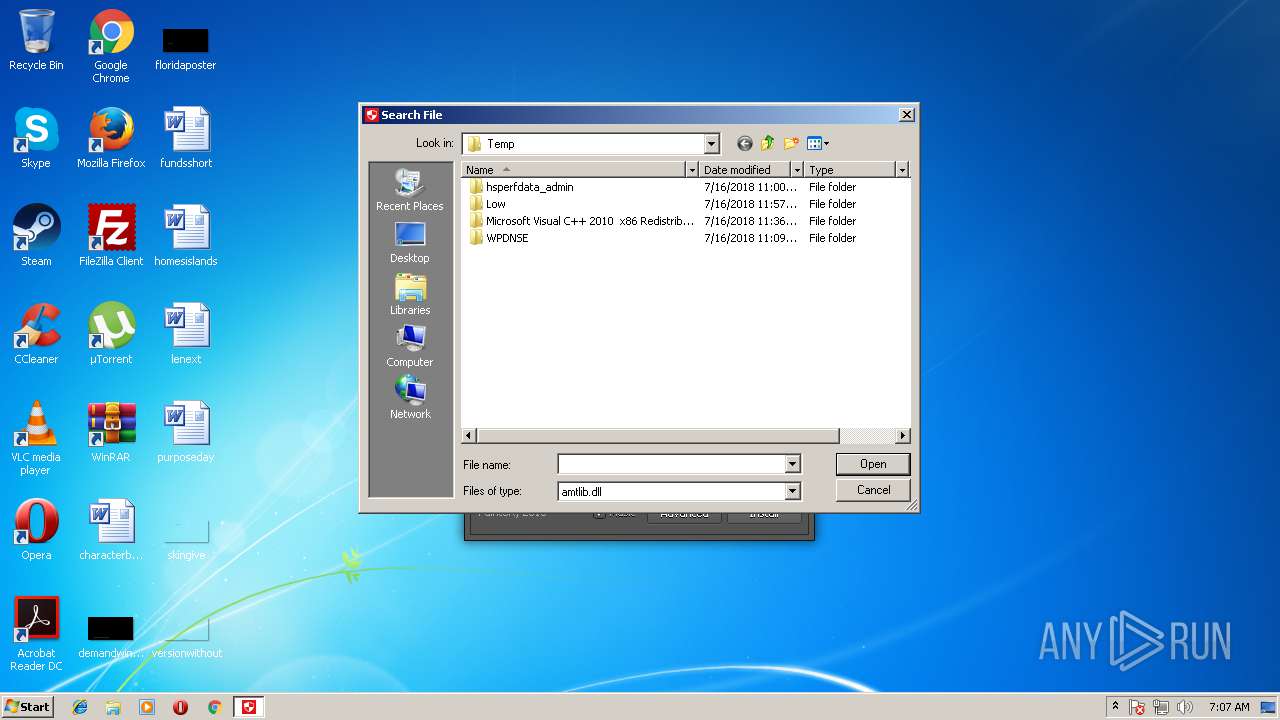
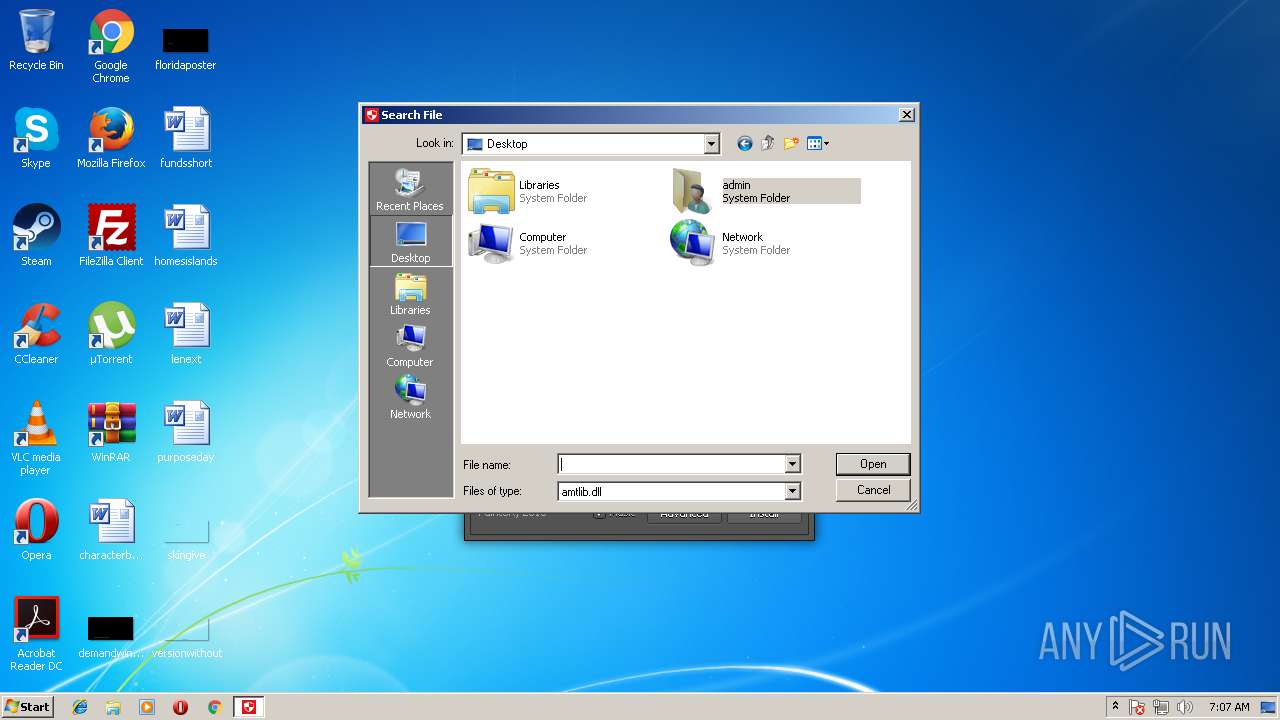
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0061006D00740065006D0075002E00760030002E0039002E0031002D007000610069006E007400650072002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070000000 | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\59\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0700000002000000010000000000000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7 |
| Operation: | write | Name: | 1 |
Value: 7E0074001C00434653461600310000000000454B814A122041707044617461000000741A595E96DFD3488D671733BCEE28BAC5CDFADF9F6756418947C5C76BC0B67F3C0008000400EFBE454B814A454B814A2A0000007C0100000000020000000000000000000000000000004100700070004400610074006100000042000000 | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1 |
| Operation: | write | Name: | 0 |
Value: 4C00310000000000F04C045310204C6F63616C00380008000400EFBE454B814AF04C04532A0000008F0100000000020000000000000000000000000000004C006F00630061006C00000014000000 | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1 |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (1732) amtemu.v0.9.1-painter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\7\1\0 |
| Operation: | write | Name: | 0 |
Value: 4A00310000000000F54CD230102054656D700000360008000400EFBE454B814AF54CD2302A00000090010000000002000000000000000000000000000000540065006D007000000014000000 | |||
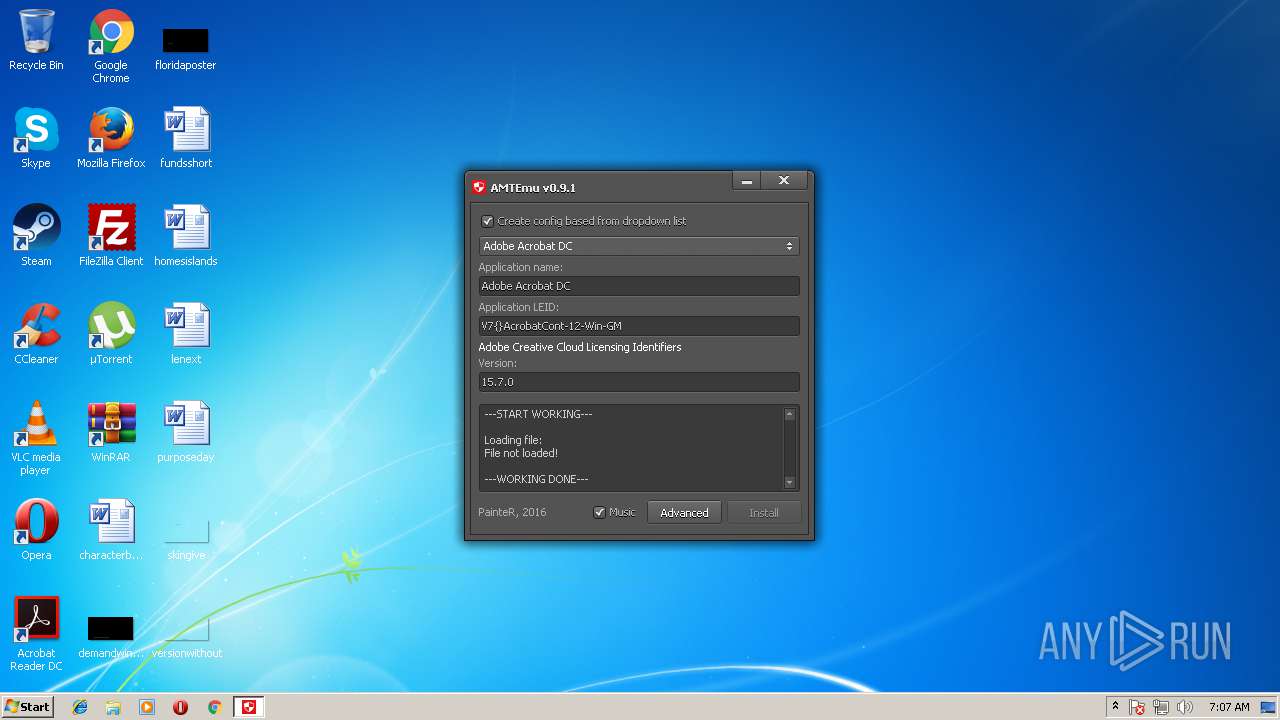
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1732 | amtemu.v0.9.1-painter.exe | C:\Users\admin\AppData\Local\Temp\spc_player.dll | executable | |
MD5:41AFBF49BA7F6EE164F31FAA2CD38E15 | SHA256:50D30B7AA7B9858F91F33165314C7CF7F2ACC97157091676C7E7925E018FD387 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report