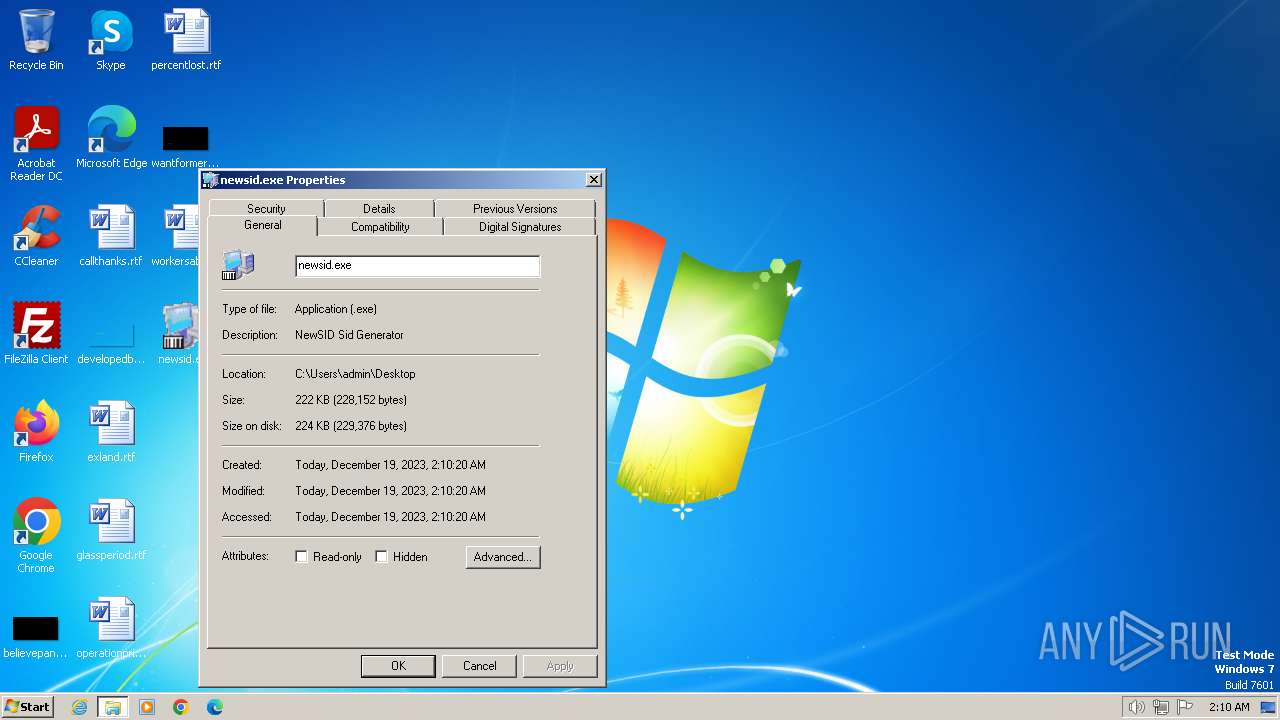
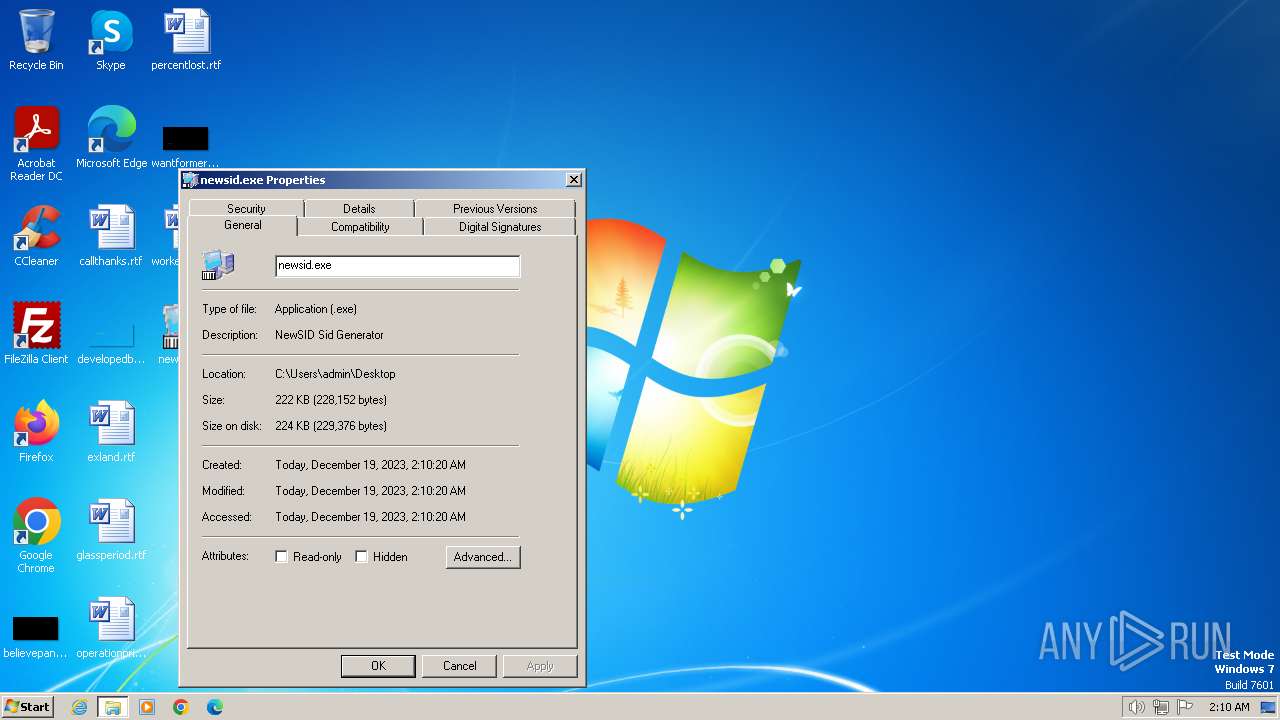
| File name: | newsid.exe |
| Full analysis: | https://app.any.run/tasks/9db663b8-e608-4ffc-969d-77b1b89f54bc |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2023, 02:09:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 73E708D1126E7AF86A4EF820C24D80E4 |
| SHA1: | 4C64DF34EF8F8FAA757E1D4482486453D7425752 |
| SHA256: | C2F4591F7E9598CEB47CBCE280180B3E104F70509DCE7D1E90CA758F69D79DDD |
| SSDEEP: | 1536:2se+EUq5pelNH5OsWXb7tML7zPWFDyu6QEh/CtA+dkmVnTA6uvp+3Xx+MV4iUVqK:Ah5p2NctMPeFDh6Qc/H+TxV9UVq2p |
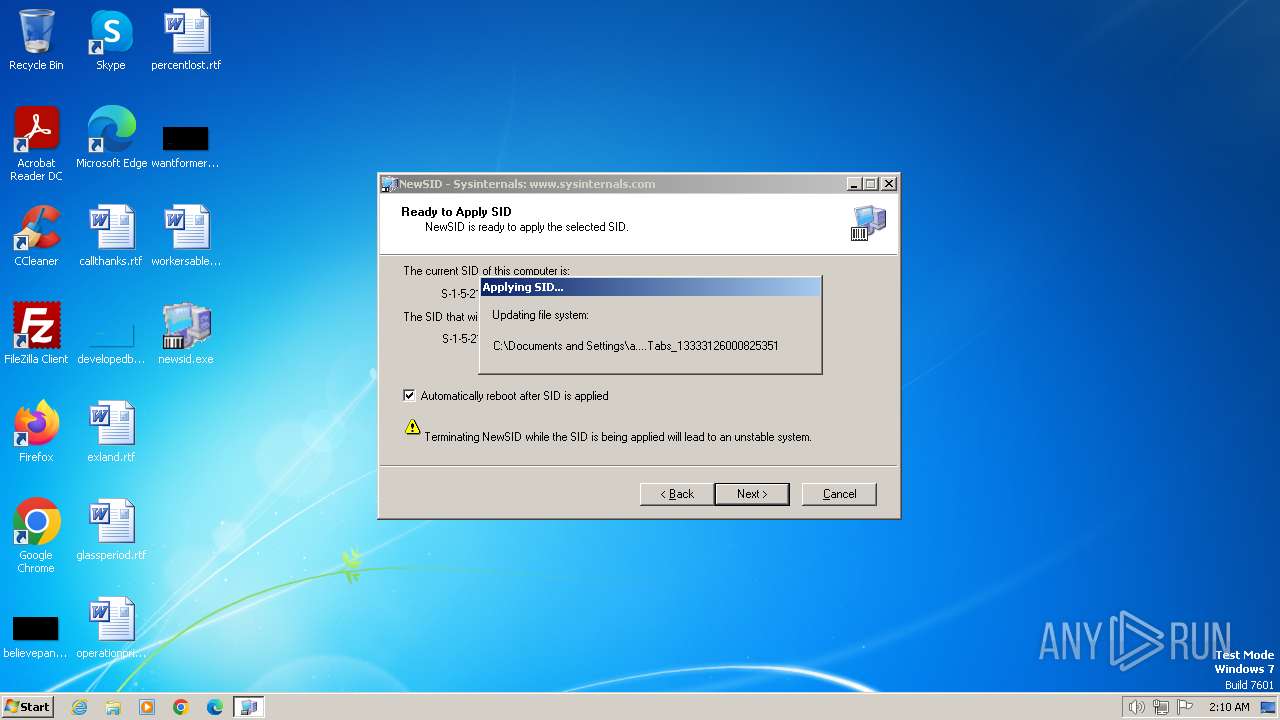
MALICIOUS
Steals credentials from Web Browsers
- newsid.exe (PID: 584)
Actions looks like stealing of personal data
- newsid.exe (PID: 584)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- newsid.exe (PID: 116)
- newsid.exe (PID: 584)
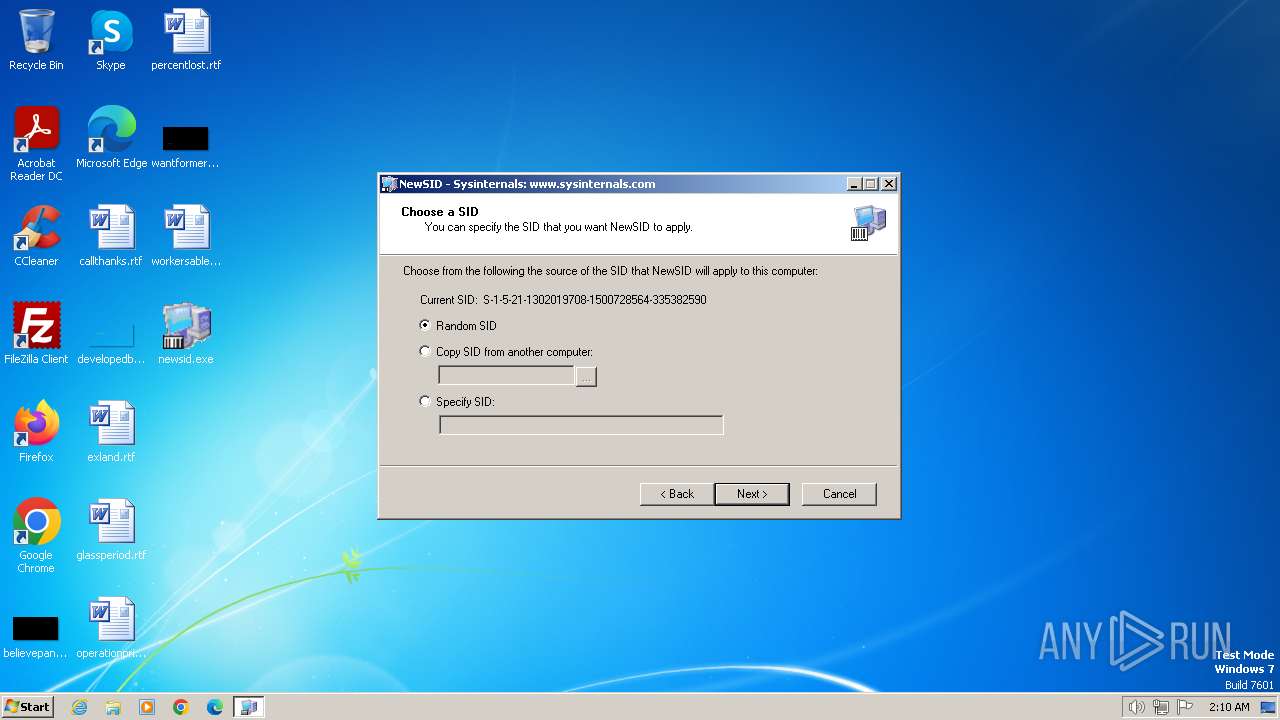
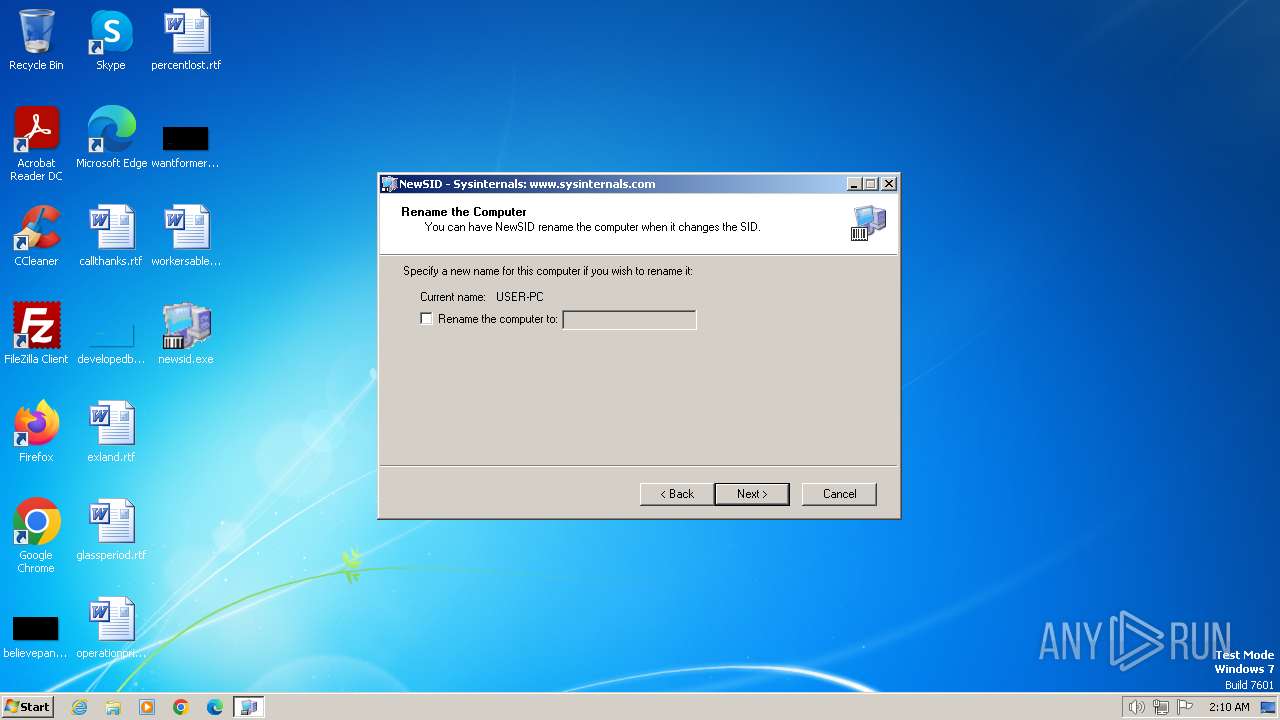
Reads the computer name
- newsid.exe (PID: 116)
- newsid.exe (PID: 584)
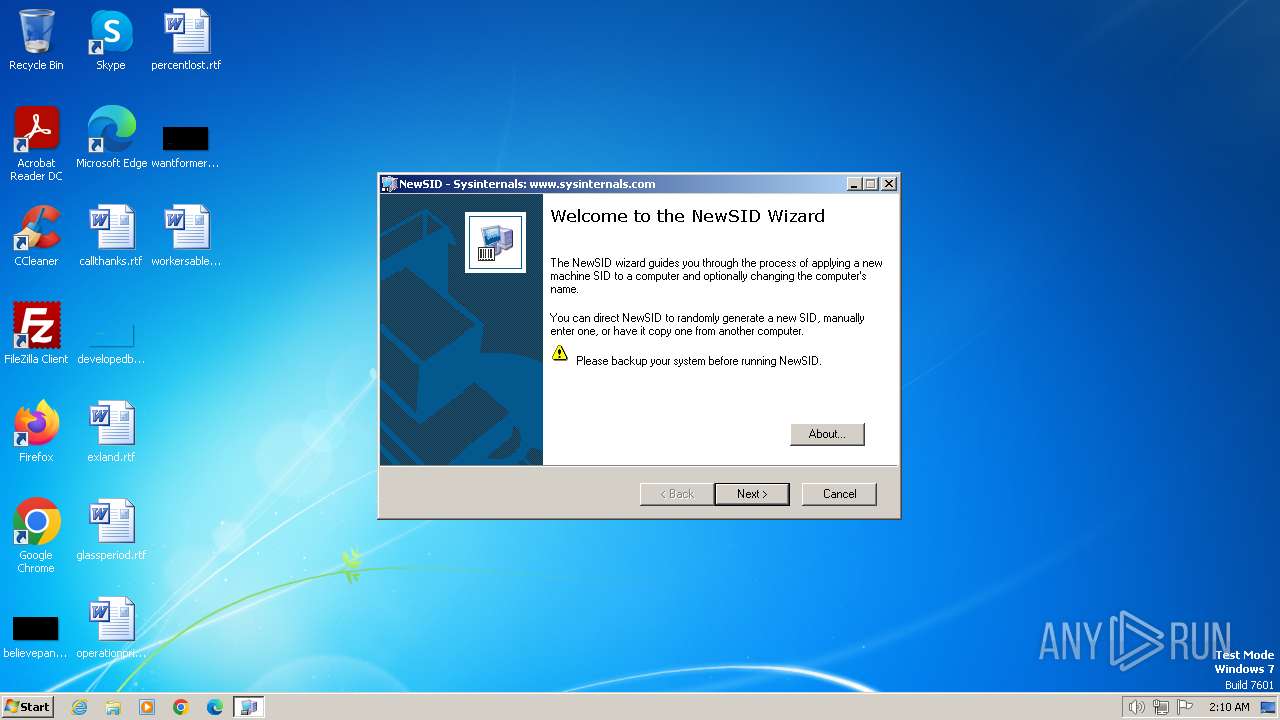
Manual execution by a user
- newsid.exe (PID: 584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:08:16 01:21:18+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 53248 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6850 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.10.0.0 |
| ProductVersionNumber: | 4.10.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
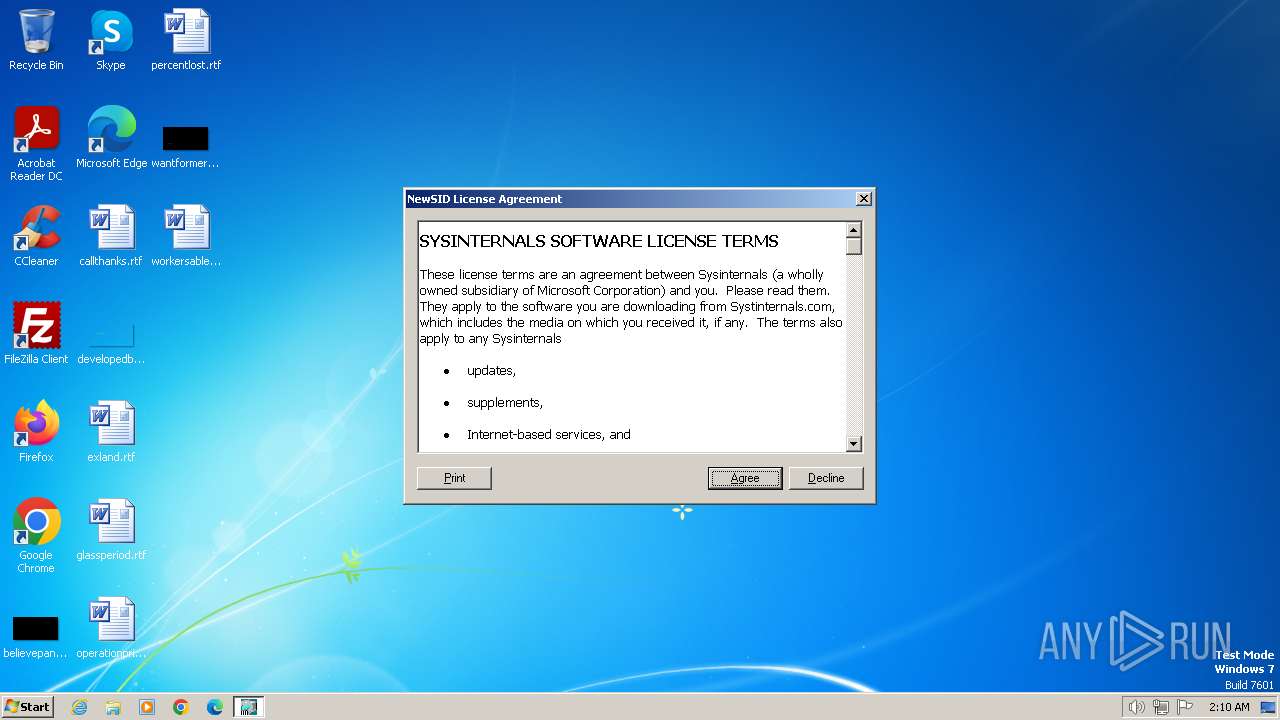
| CompanyName: | Sysinternals |
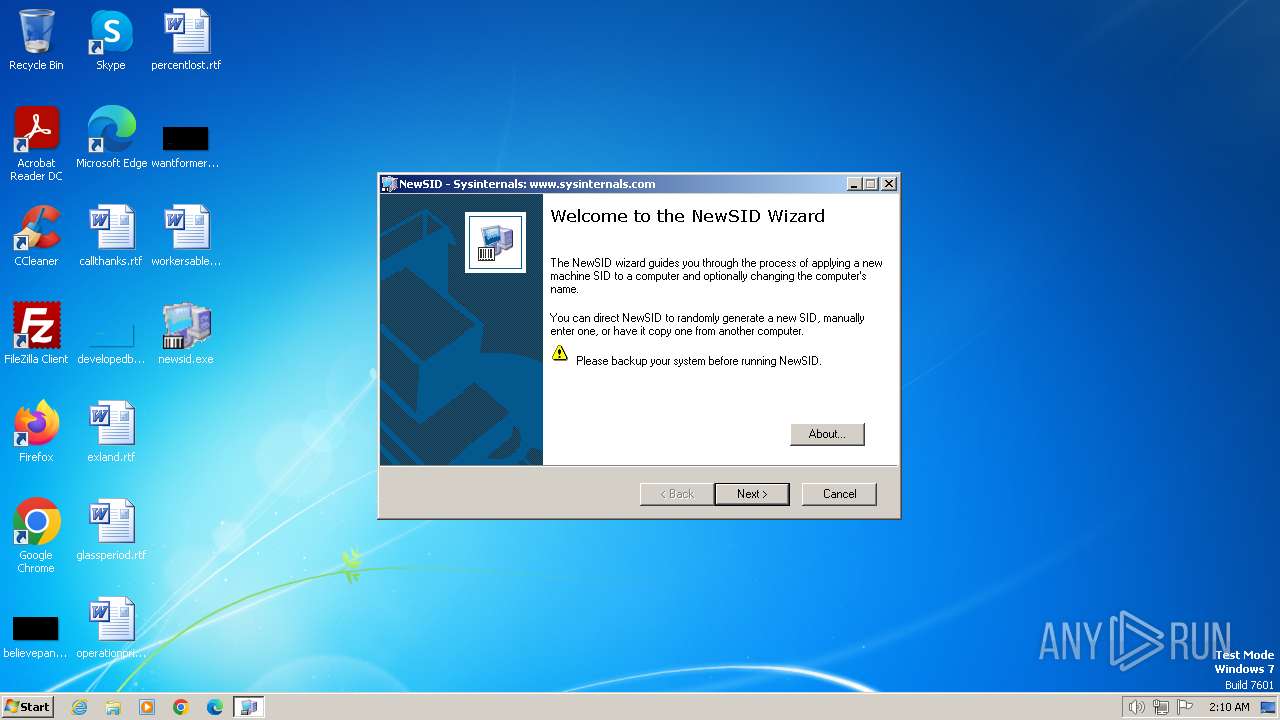
| FileDescription: | NewSID Sid Generator |
| FileVersion: | 4.1 |
| InternalName: | NewSID |
| LegalCopyright: | Copyright © 1998-2005 Mark Russinovich and Bryce Cogswell |
| LegalTrademarks: | - |
| OriginalFileName: | NewSID.exe |
| PrivateBuild: | - |
| ProductName: | NewSID |
| ProductVersion: | 4.1 |
| SpecialBuild: | - |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Temp\newsid.exe" | C:\Users\admin\AppData\Local\Temp\newsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals Integrity Level: MEDIUM Description: NewSID Sid Generator Exit code: 1 Version: 4.10 Modules
| |||||||||||||||
| 584 | "C:\Users\admin\Desktop\newsid.exe" | C:\Users\admin\Desktop\newsid.exe | explorer.exe | ||||||||||||
User: admin Company: Sysinternals Integrity Level: HIGH Description: NewSID Sid Generator Exit code: 0 Version: 4.10 Modules
| |||||||||||||||
Total events
165
Read events
152
Write events
5
Delete events
8
Modification events
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SECURITY\Policy\Accounts\S-1-5-21-1302019708-1500728564-335382590-501\ActSysAc |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SECURITY\Policy\Accounts\S-1-5-21-1302019708-1500728564-335382590-501\SecDesc |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SECURITY\Policy\Accounts\S-1-5-21-1302019708-1500728564-335382590-501\Sid |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SECURITY\Policy\Accounts\S-1-5-21-1302019708-1500728564-335382590-501 |
| Operation: | delete key | Name: | (default) |
Value: | |||
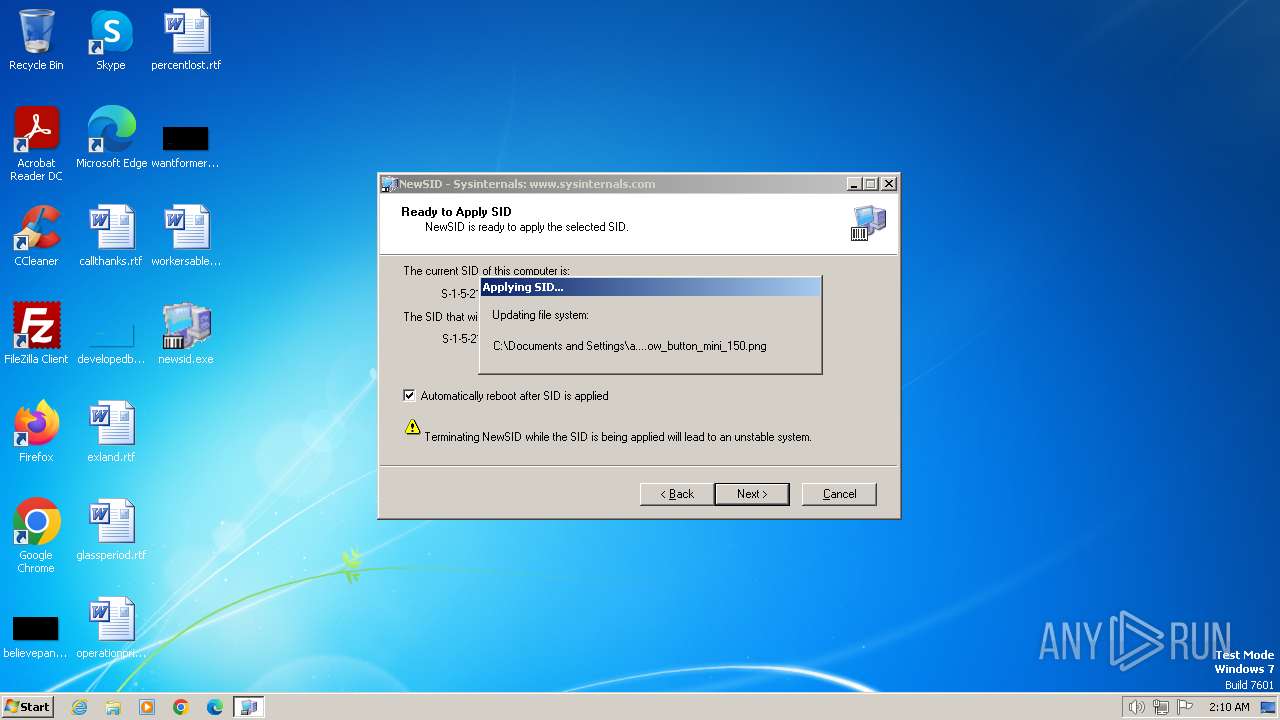
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account |
| Operation: | write | Name: | V |
Value: 00000000C800000002000100C80000001800000000000000E00000000000000000000000E0000000000000000000000001001480A8000000B80000001400000044000000020030000200000002C014007A04050101010000000000010000000002C01400FF070F000101000000000005070000000200640004000000000014008503020001010000000000010000000000001800850302000102000000000005200000002102000000001800DF070F000102000000000005200000002002000000001800D50302000102000000000005200000002402000001020000000000052000000020020000010200000000000520000000200200000104000000000005150000007C3E9B4DF44C73593E88FD13 | |||
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users\000001F4 |
| Operation: | write | Name: | V |
Value: 00000000BC00000002000100BC0000001A00000000000000D80000000000000000000000D80000006C000000000000004401000000000000000000004401000000000000000000004401000000000000000000004401000000000000000000004401000000000000000000004401000000000000000000004401000000000000000000004401000015000000A80000005C01000008000000010000006401000004000000000000006801000014000000000000007C0100000400000000000000800100000400000000000000010014809C000000AC0000001400000044000000020030000200000002C014004400050101010000000000010000000002C01400FFFF1F000101000000000005070000000200580003000000000014005B03020001010000000000010000000000001800FF070F000102000000000005200000002002000000002400440002000105000000000005150000007C3E9B4DF44C73593E88FD13F40100000102000000000005200000002002000001020000000000052000000020020000410064006D0069006E006900730074007200610074006F00720018004200750069006C0074002D0069006E0020006100630063006F0075006E007400200066006F0072002000610064006D0069006E006900730074006500720069006E0067002000740068006500200063006F006D00700075007400650072002F0064006F006D00610069006E00FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF00010001020000070000000300010003000100A27DC0107FBED91AA348E5DB610012EC0300010003000100 | |||
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Account\Users\000003E8 |
| Operation: | write | Name: | V |
Value: 00000000BC00000002000100BC0000000A00000000000000C80000000000000000000000C80000000000000000000000C80000000000000000000000C80000000000000000000000C80000000000000000000000C80000000000000000000000C80000000000000000000000C80000000000000000000000C80000000000000000000000C80000000000000000000000C80000000800000001000000D00000000400000000000000D40000001400000000000000E80000000400000000000000EC0000000400000000000000010014809C000000AC0000001400000044000000020030000200000002C014004400050101010000000000010000000002C01400FF070F00010100000000000507000000020058000300000000002400440002000105000000000005150000007C3E9B4DF44C73593E88FD13E803000000001800FF070F0001020000000000052000000020020000000014005B0302000101000000000001000000000102000000000005200000002002000001020000000000052000000020020000610064006D0069006E0000000102000007000000030001000300010007AC541403FAB518C2AE88E4C260A71F0300010003000100 | |||
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Builtin\Aliases\00000220 |
| Operation: | write | Name: | C |
Value: 20020000000000009800000002000100980000001C00000000000000B400000096000000000000004C01000038000000020000000100148078000000880000001400000044000000020030000200000002C014001300050101010000000000010000000002C01400FFFF1F000101000000000005070000000200340002000000000014000C000200010100000000000100000000000018001F000F00010200000000000520000000200200000102000000000005200000002002000001020000000000052000000020020000410064006D0069006E006900730074007200610074006F0072007300410064006D0069006E006900730074007200610074006F007200730020006800610076006500200063006F006D0070006C00650074006500200061006E006400200075006E0072006500730074007200690063007400650064002000610063006300650073007300200074006F002000740068006500200063006F006D00700075007400650072002F0064006F006D00610069006E00BABB0105000000000005150000007C3E9B4DF44C73593E88FD13F40100000105000000000005150000007C3E9B4DF44C73593E88FD13E8030000 | |||
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Builtin\Aliases\00000222 |
| Operation: | write | Name: | C |
Value: 2202000000000000C800000002000100C80000000C00000000000000D4000000FC00000000000000D00100001C0000000100000001001480A8000000B80000001400000044000000020030000200000002C014001300050101010000000000010000000002C01400FFFF1F000101000000000005070000000200640004000000000014000C000200010100000000000100000000000018001F000F0001020000000000052000000020020000000018001F000F0001020000000000052000000024020000000018001F000F000102000000000005200000002302000001020000000000052000000020020000010200000000000520000000200200004700750065007300740073004700750065007300740073002000680061007600650020007400680065002000730061006D006500200061006300630065007300730020006100730020006D0065006D00620065007200730020006F00660020007400680065002000550073006500720073002000670072006F00750070002000620079002000640065006600610075006C0074002C002000650078006300650070007400200066006F007200200074006800650020004700750065007300740020006100630063006F0075006E00740020007700680069006300680020006900730020006600750072007400680065007200200072006500730074007200690063007400650064000105000000000005150000007C3E9B4DF44C73593E88FD13F5010000 | |||
| (PID) Process: | (584) newsid.exe | Key: | HKEY_LOCAL_MACHINE\SAM\SAM\Domains\Builtin\Aliases\Members\S-1-5-21-1302019708-1500728564-335382590\000001F4 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |