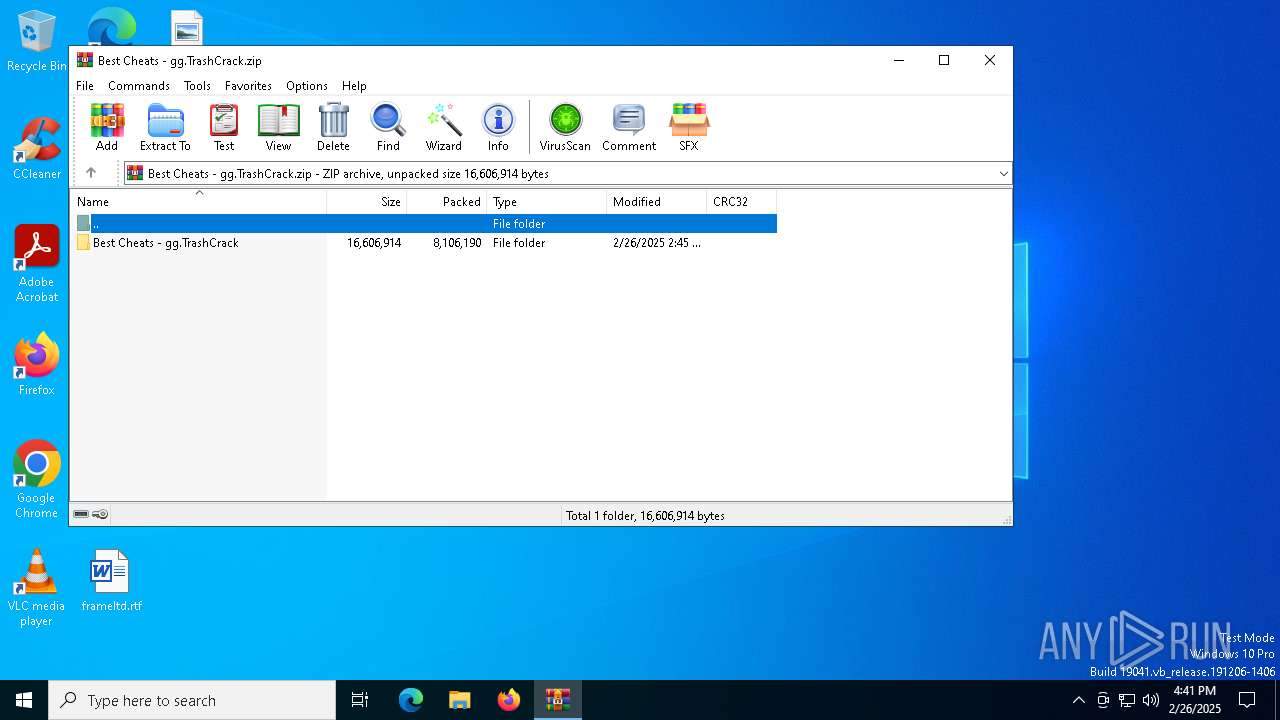
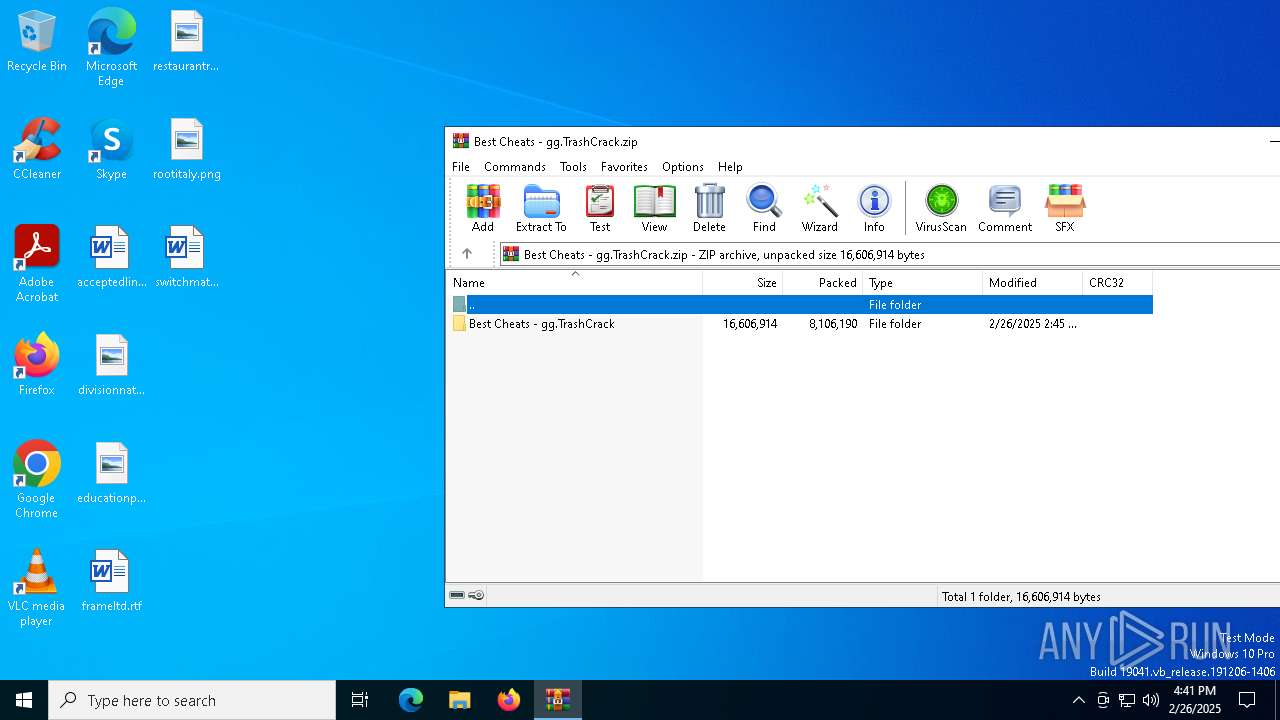
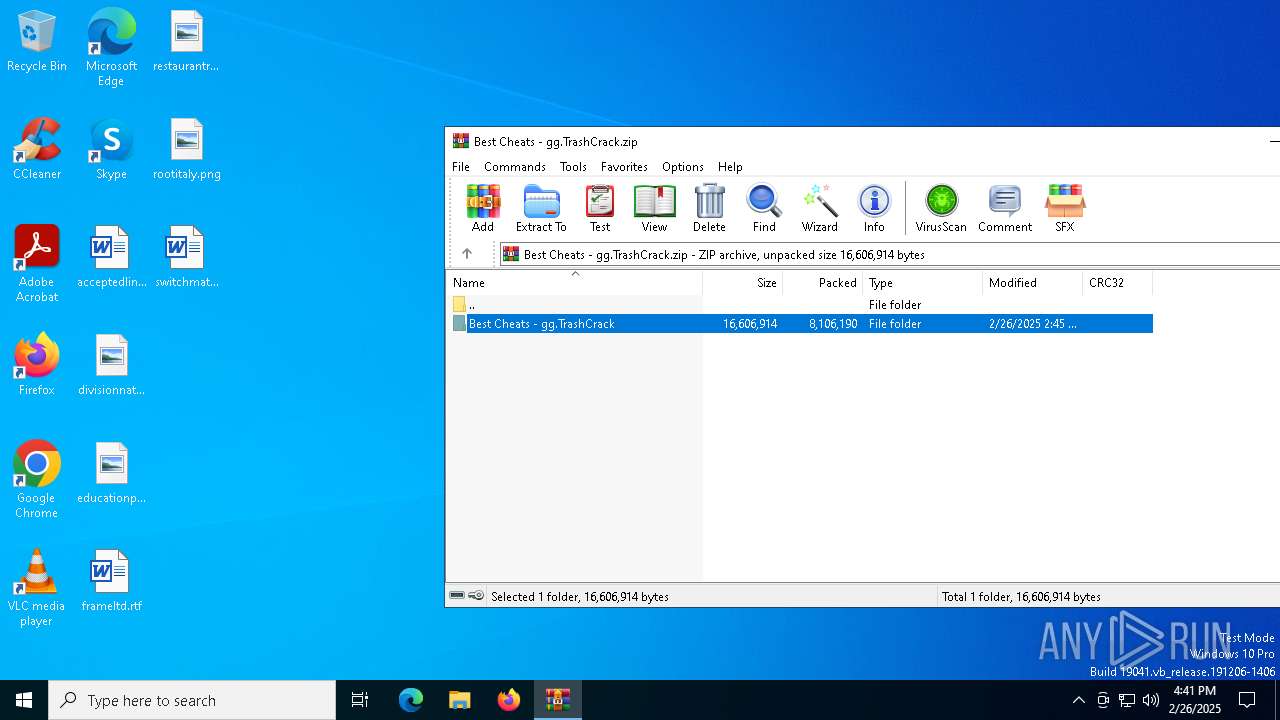
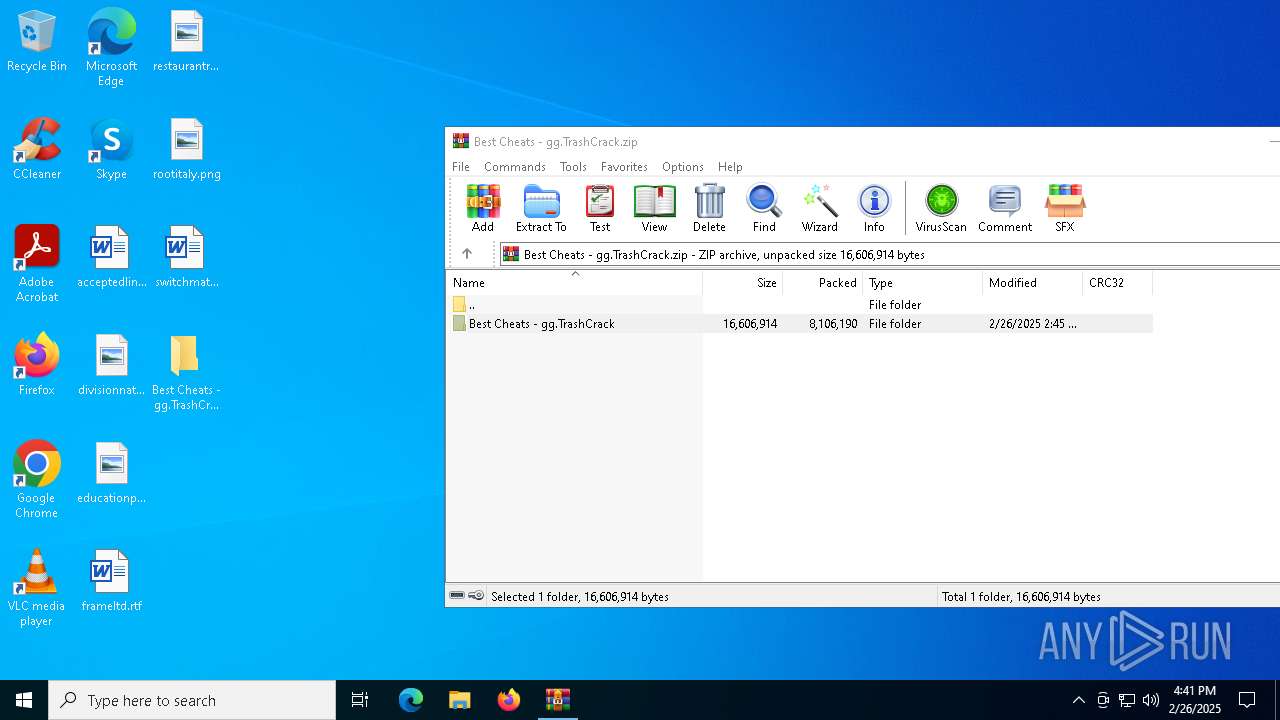
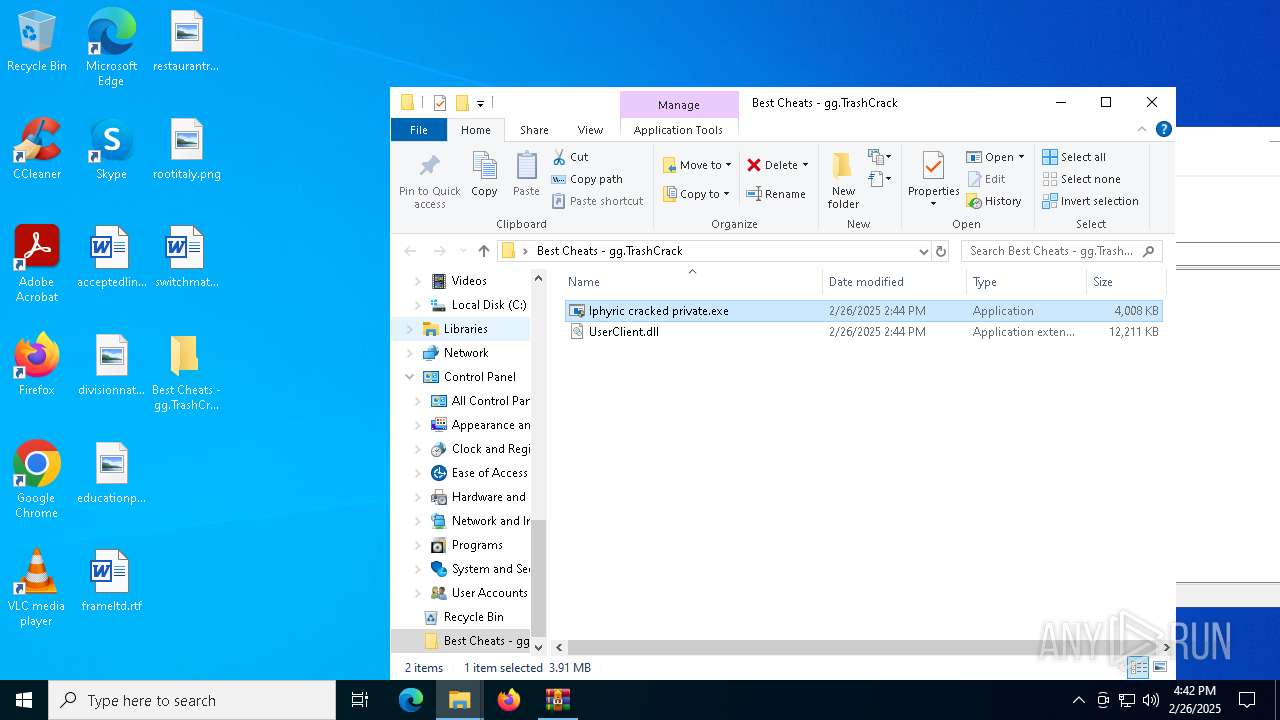
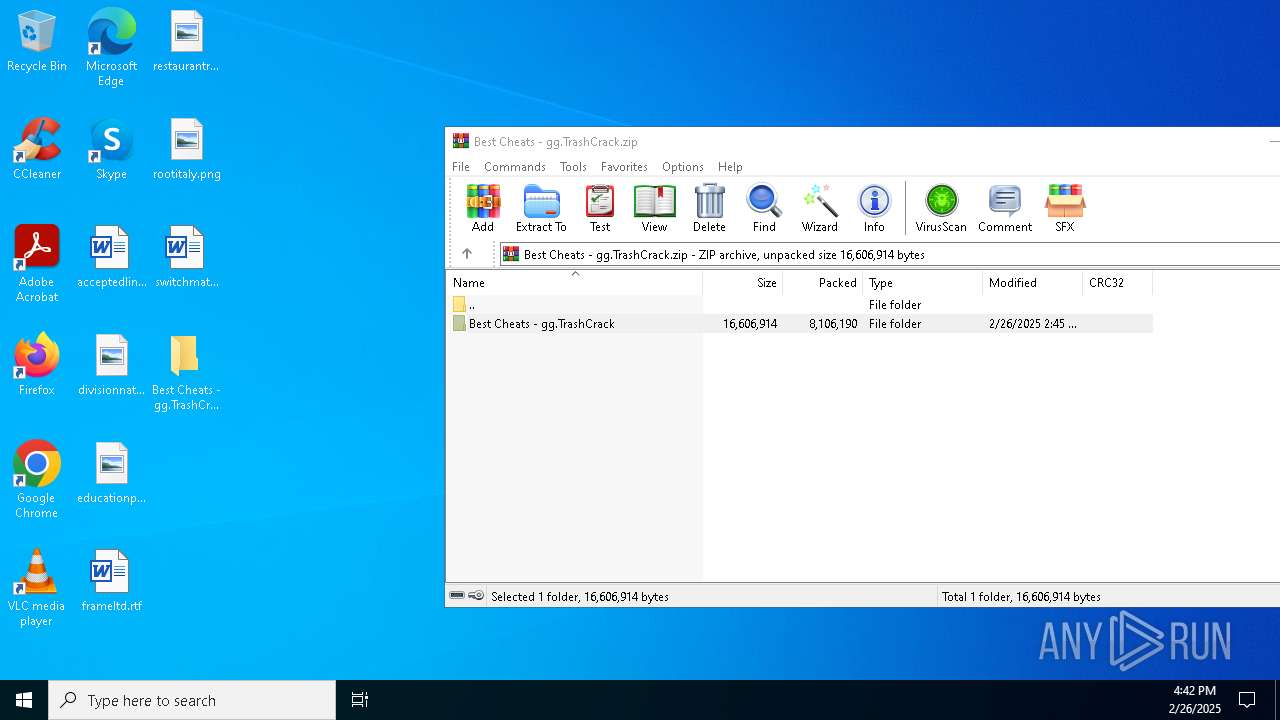
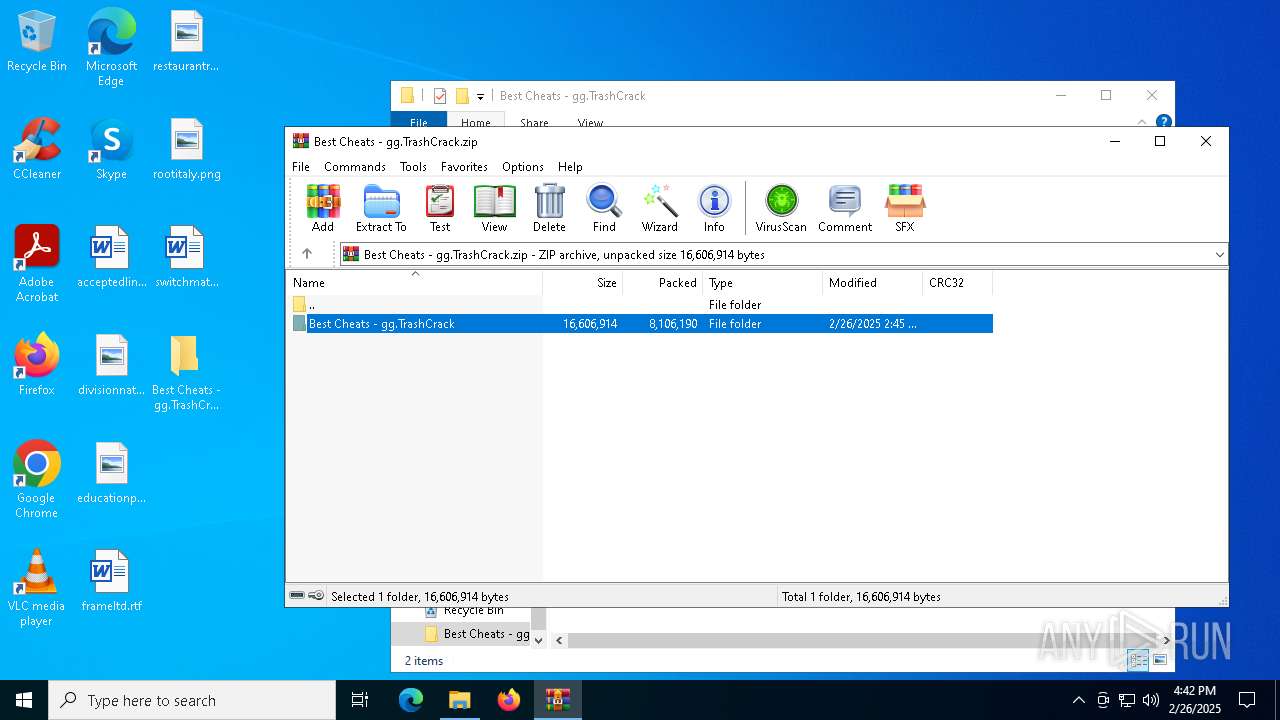
| File name: | Best Cheats - gg.TrashCrack.zip |
| Full analysis: | https://app.any.run/tasks/dc514f81-9721-46a3-ab4e-d8b49f03dde4 |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2025, 16:41:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 898FCCDF2F7744BBCAA3FF0E07511CF2 |
| SHA1: | CA773E558C2B3F55B8E37FF524F1BAD64F15E41A |
| SHA256: | C2E305871DEB943248491234DE87CA8481B9E17B5205A767CD2C6E1087C88445 |
| SSDEEP: | 98304:9d1tasNqv0r+kNQLqdGO+2yZ3GQiOzezQ16G4gv0mf1z2Ovt1/16g0Fu99rjdd8i:b0JQgVcIrYqDddMO8eKE4s |
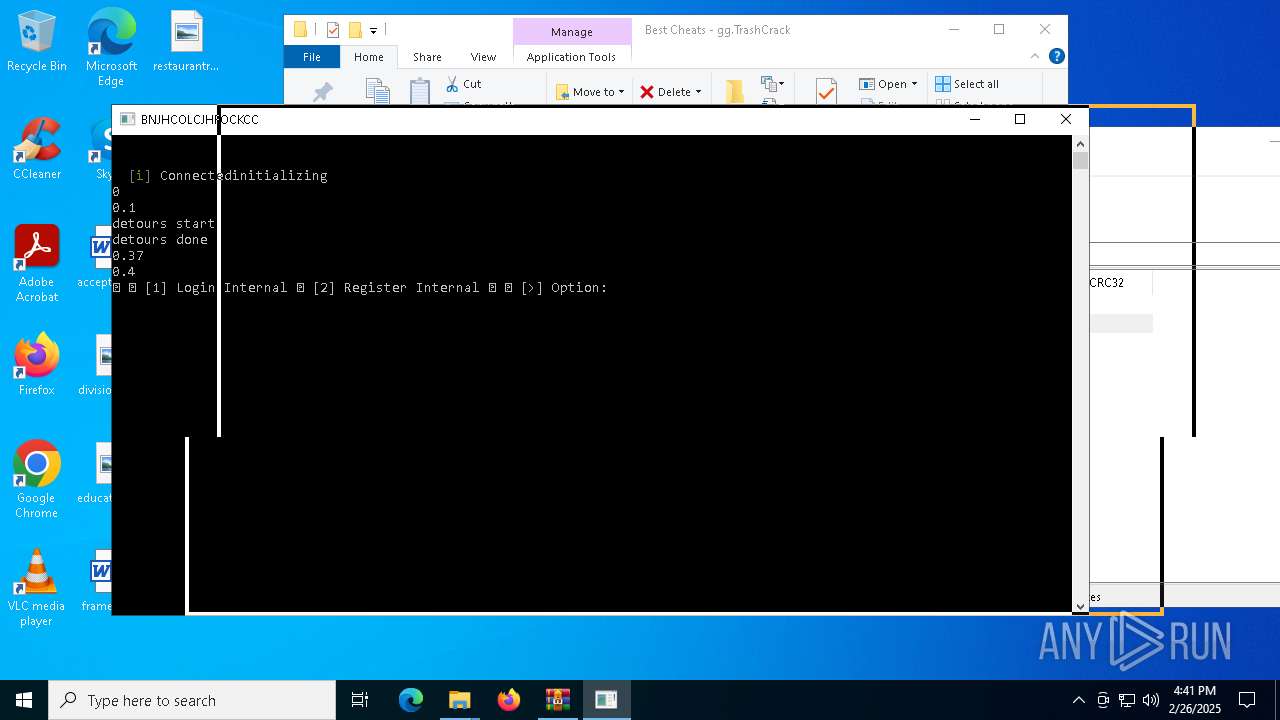
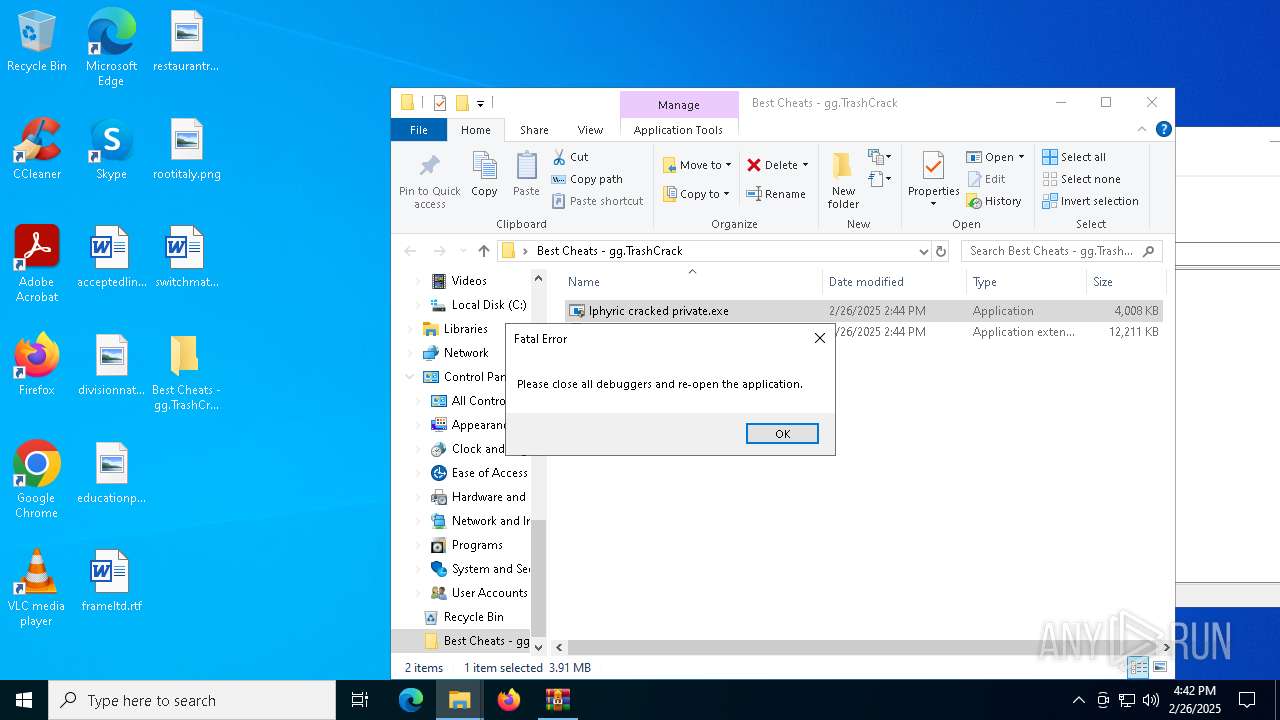
MALICIOUS
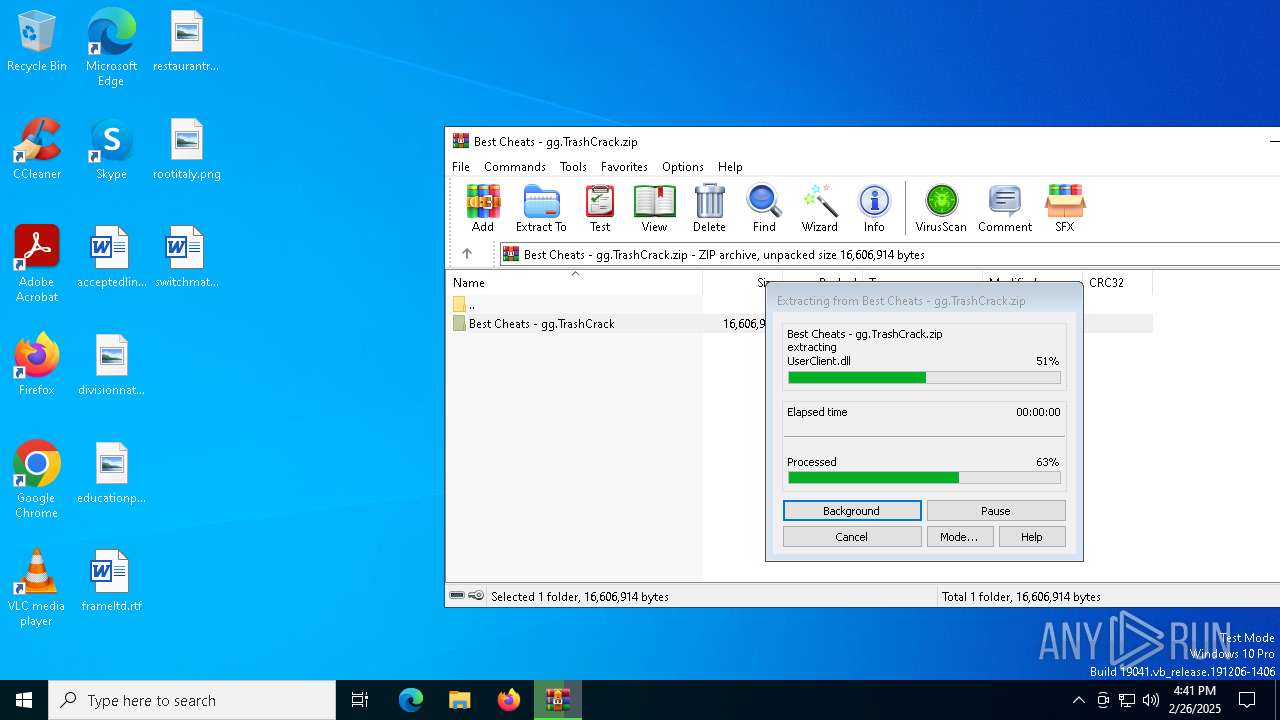
Generic archive extractor
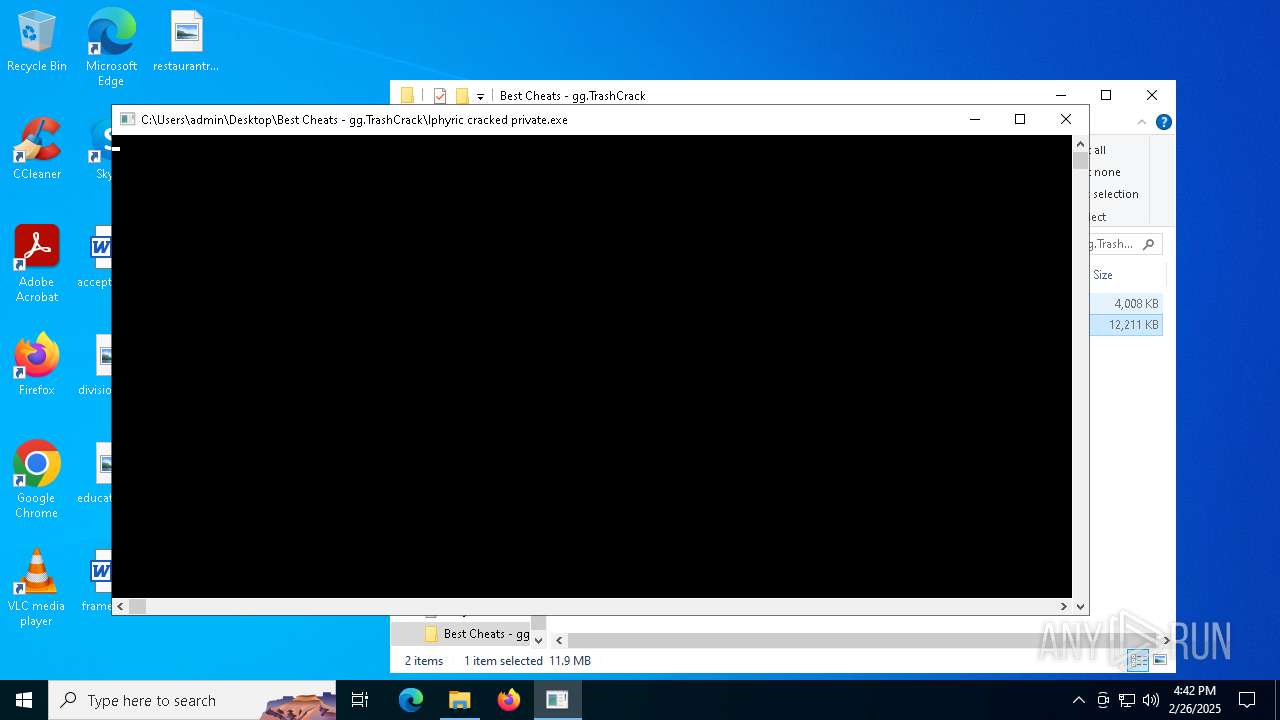
- WinRAR.exe (PID: 7500)
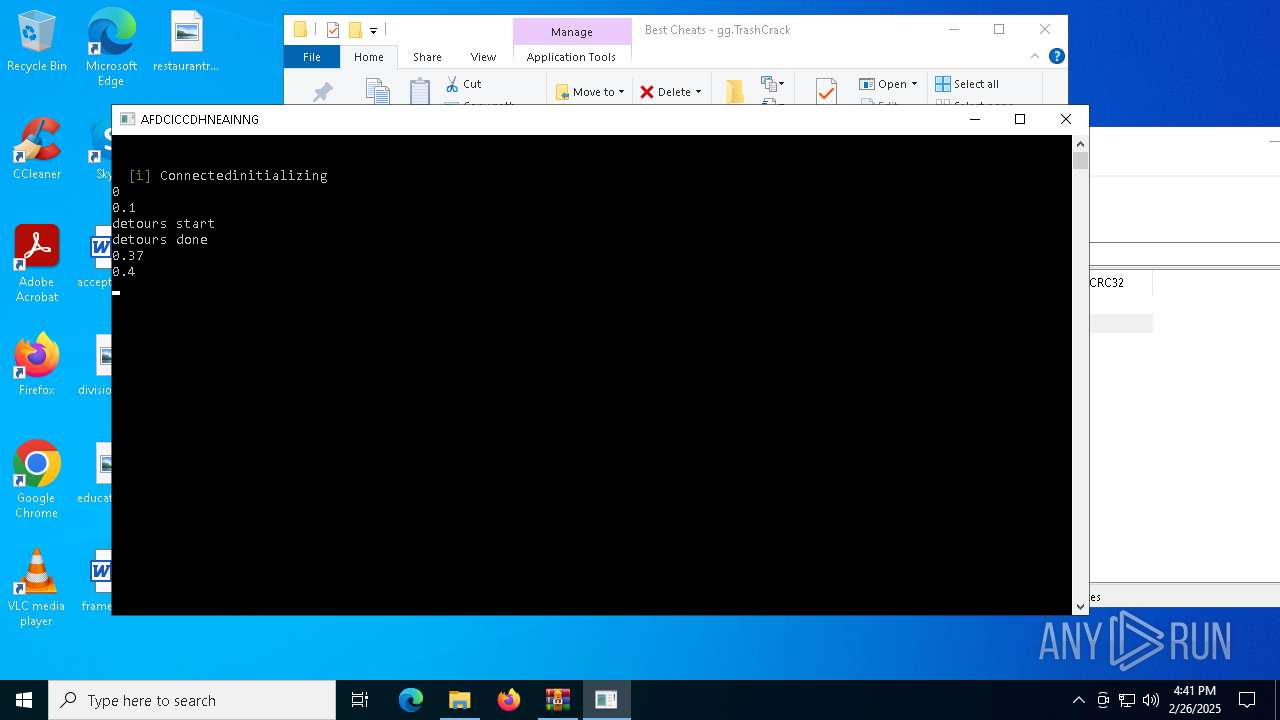
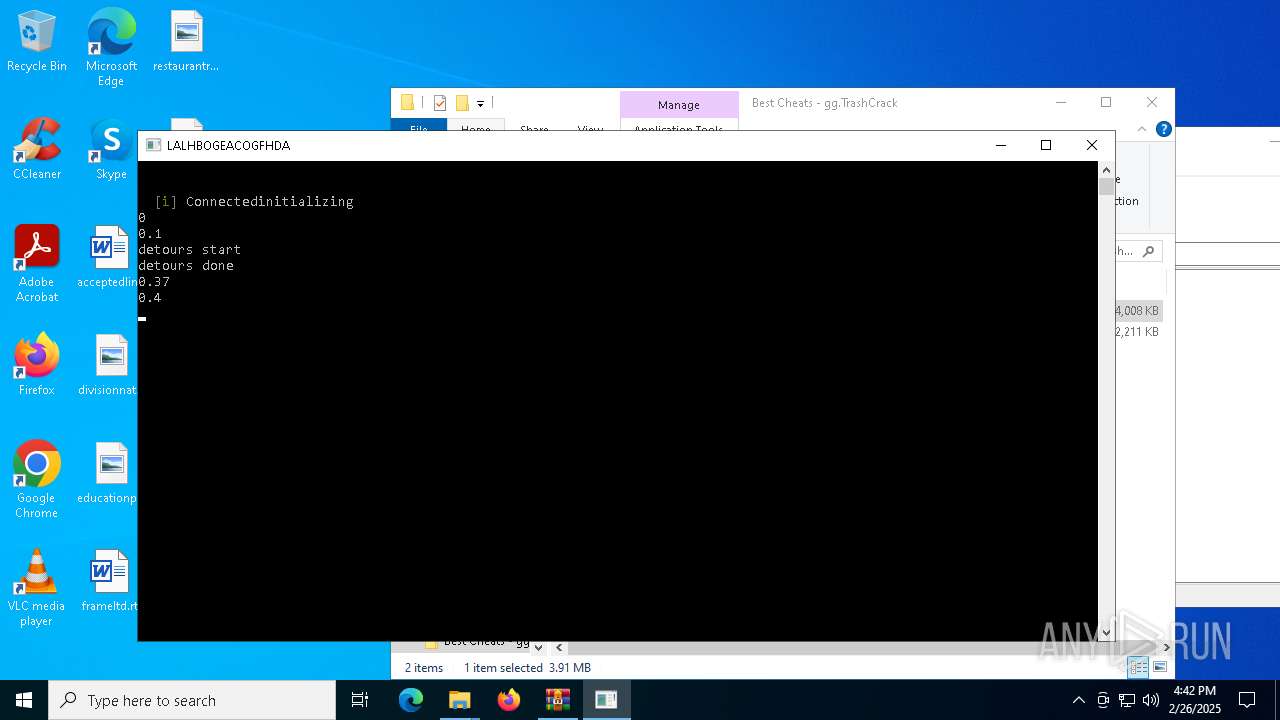
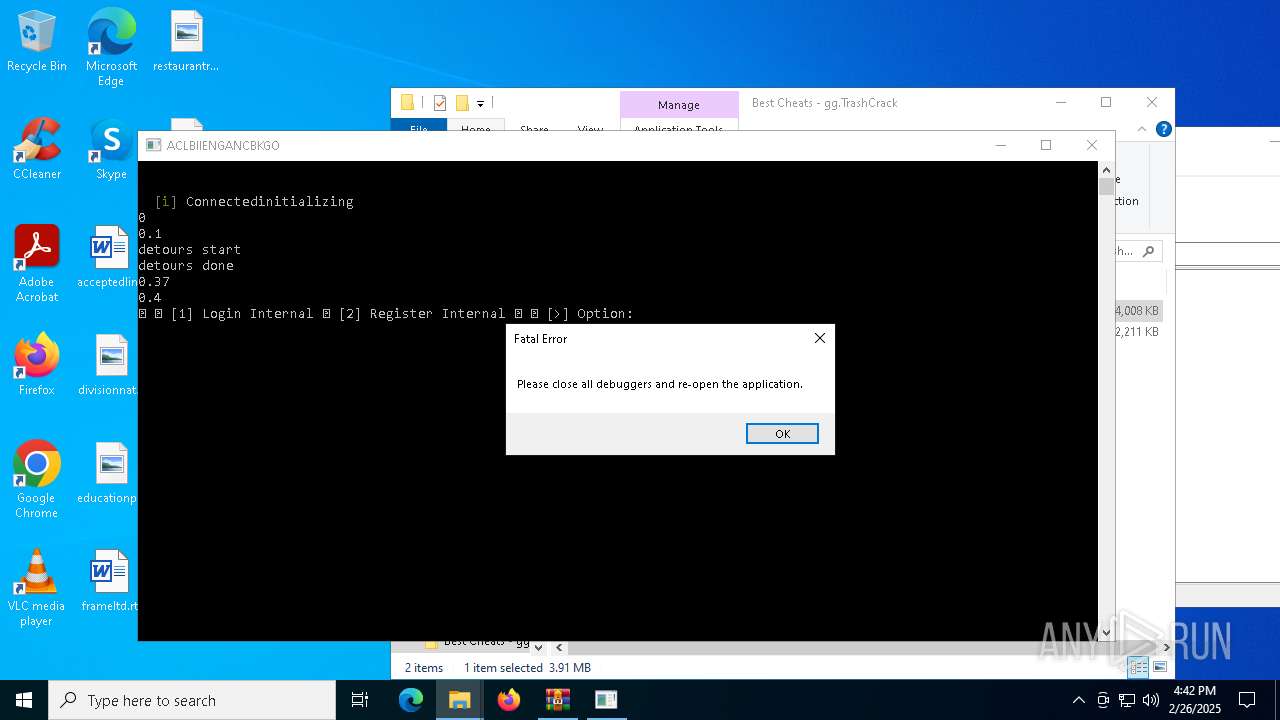
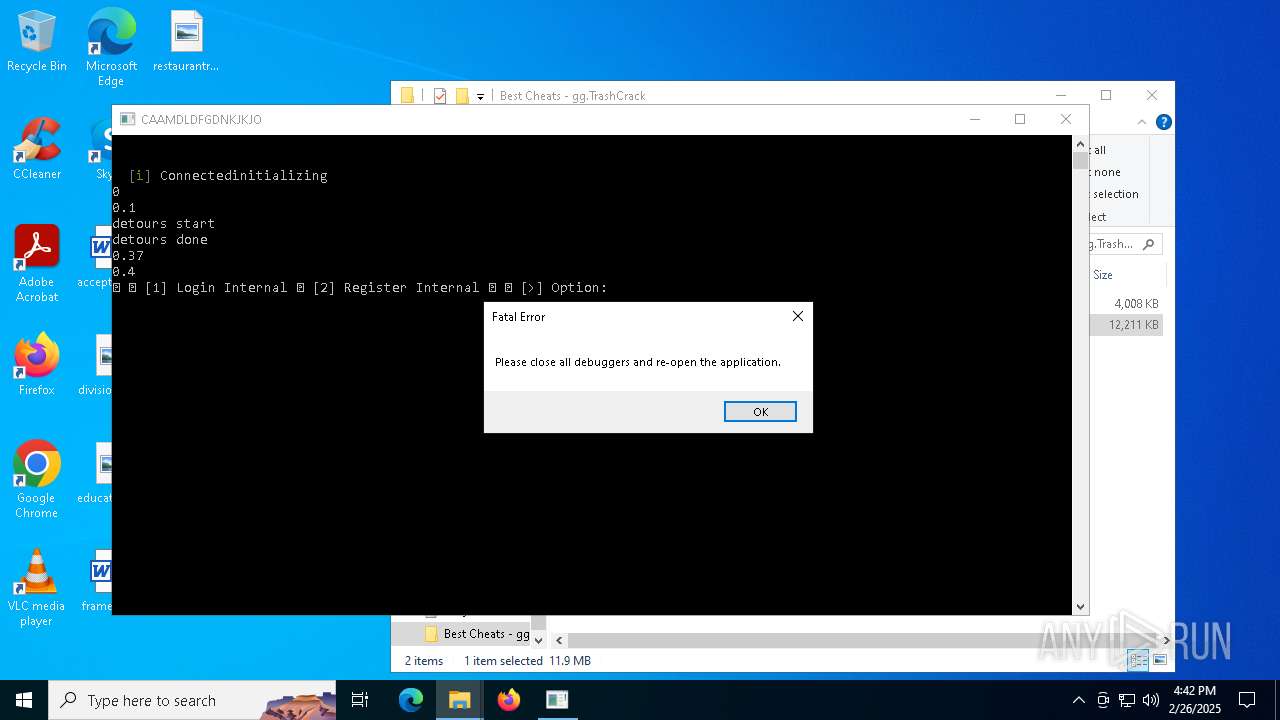
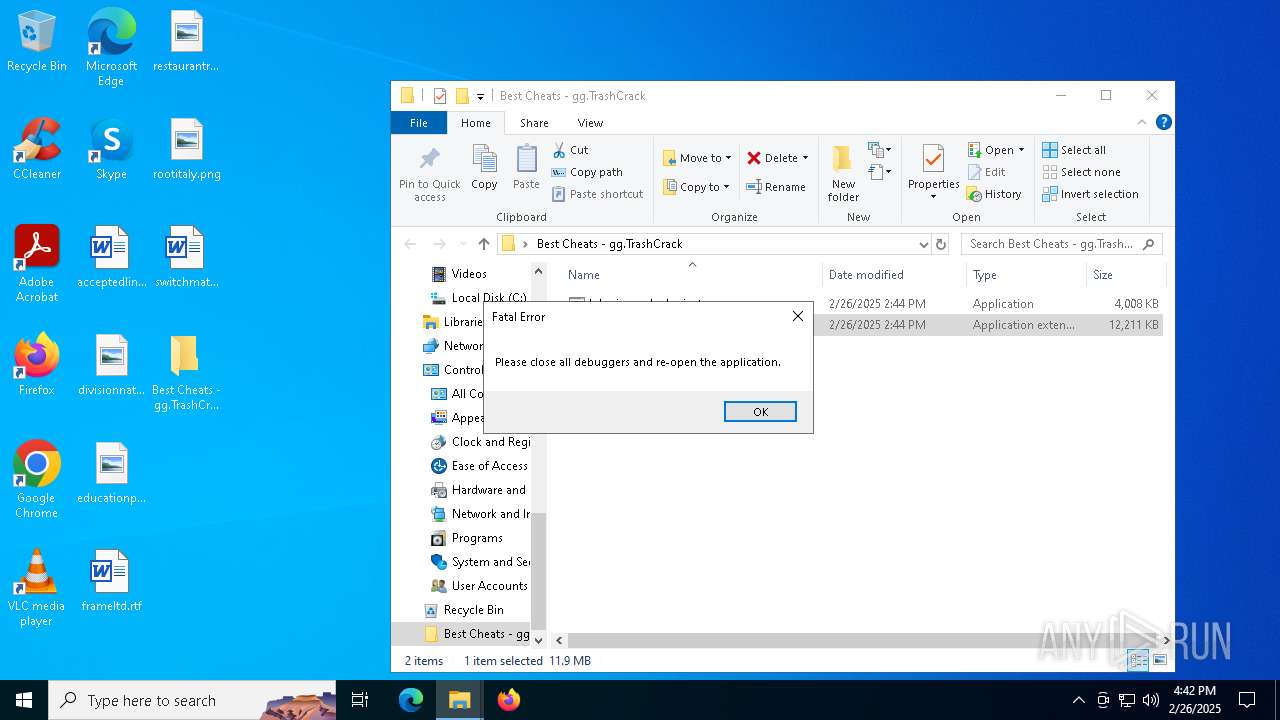
Runs injected code in another process
- lphyric cracked private.exe (PID: 7356)
- lphyric cracked private.exe (PID: 1052)
- lphyric cracked private.exe (PID: 4752)
Application was injected by another process
- explorer.exe (PID: 5492)
- explorer.exe (PID: 7832)
SUSPICIOUS
Starts CMD.EXE for commands execution
- lphyric cracked private.exe (PID: 7356)
- lphyric cracked private.exe (PID: 1052)
- lphyric cracked private.exe (PID: 4752)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 896)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 6012)
Hides command output
- cmd.exe (PID: 896)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 6012)
Executes application which crashes
- lphyric cracked private.exe (PID: 7356)
- lphyric cracked private.exe (PID: 1052)
- explorer.exe (PID: 5492)
- lphyric cracked private.exe (PID: 4752)
- explorer.exe (PID: 7832)
The process creates files with name similar to system file names
- WerFault.exe (PID: 7828)
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 4220)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 4220)
- SearchApp.exe (PID: 1276)
- StartMenuExperienceHost.exe (PID: 4776)
INFO
Checks supported languages
- lphyric cracked private.exe (PID: 7356)
- lphyric cracked private.exe (PID: 1052)
- TextInputHost.exe (PID: 4180)
- StartMenuExperienceHost.exe (PID: 4220)
- SearchApp.exe (PID: 1276)
- StartMenuExperienceHost.exe (PID: 4776)
- SearchApp.exe (PID: 4920)
- GameBar.exe (PID: 6968)
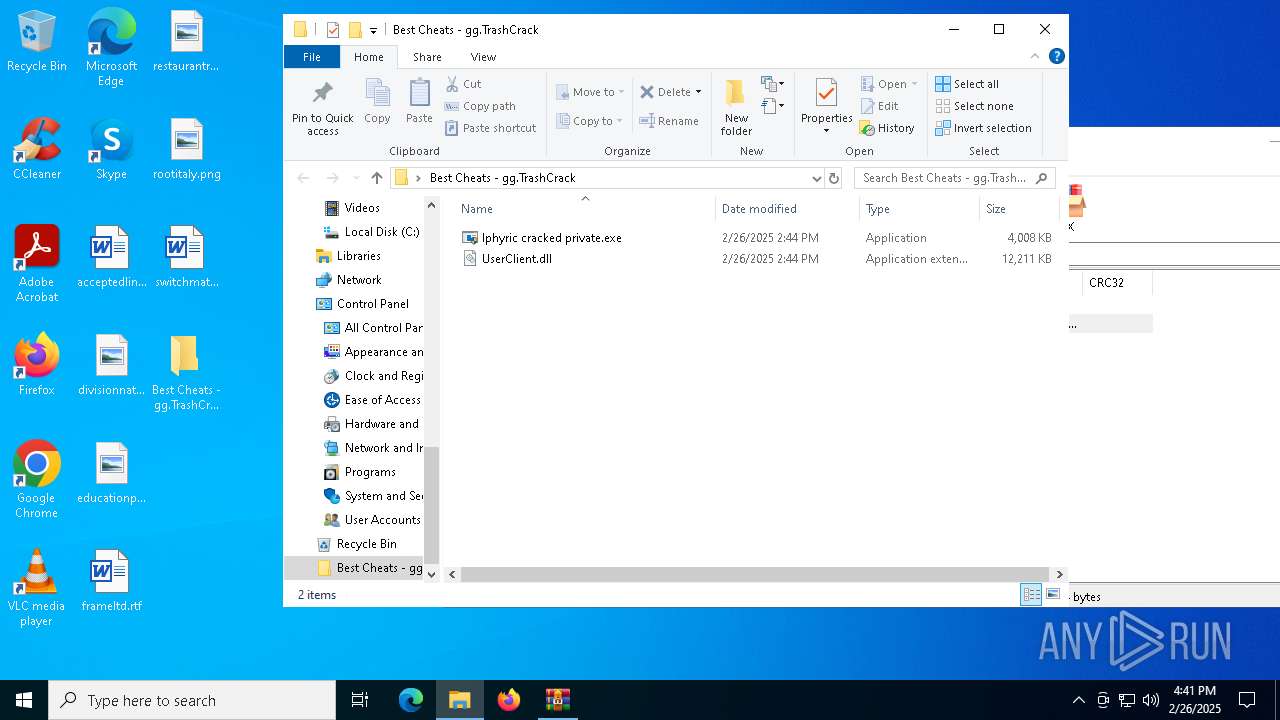
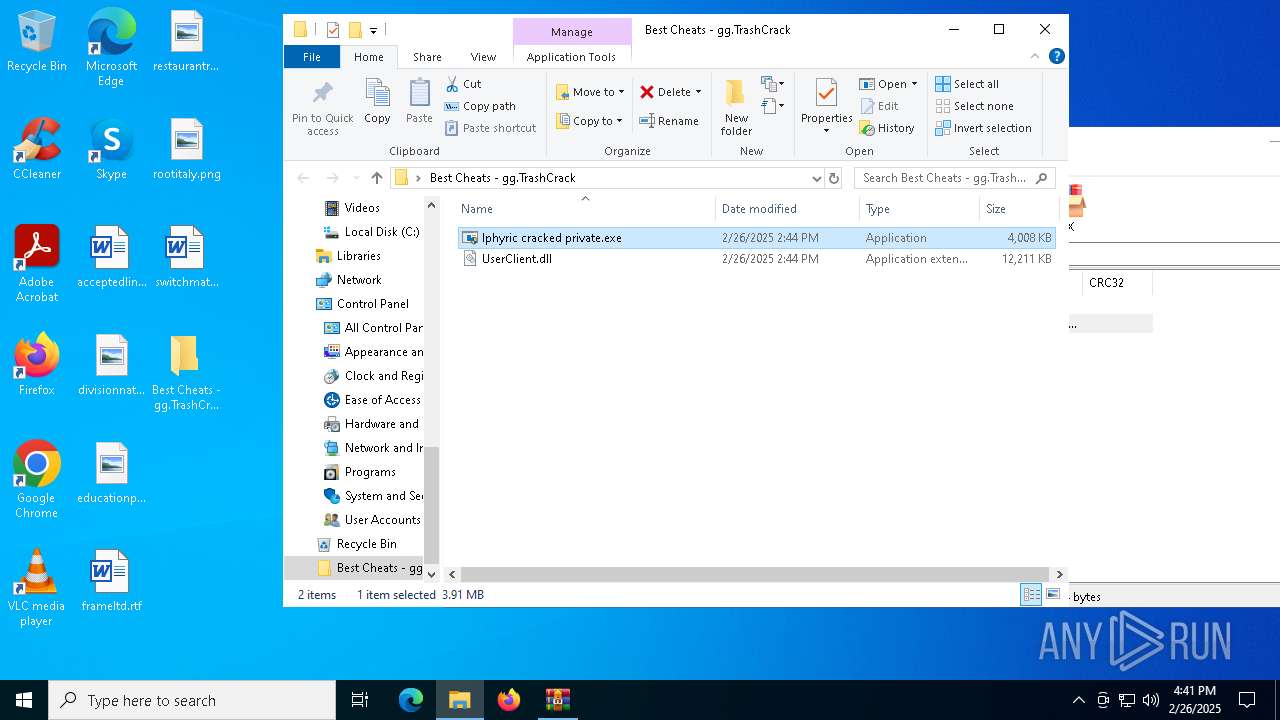
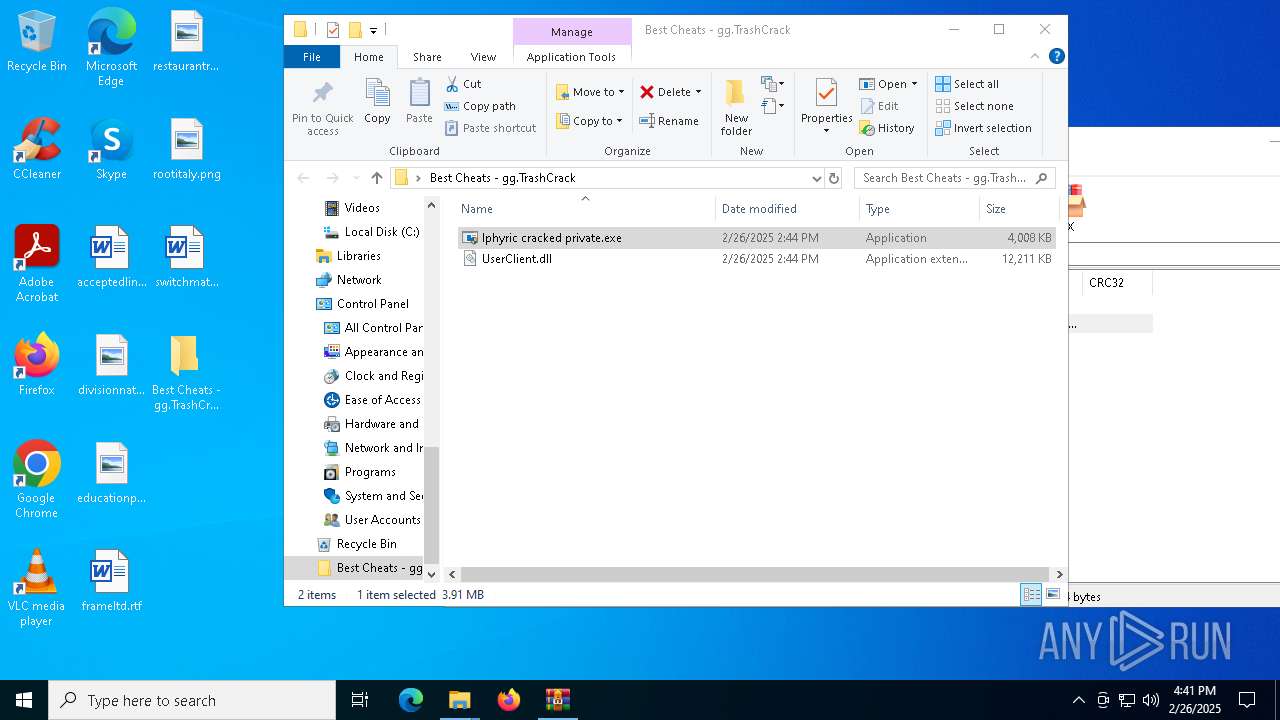
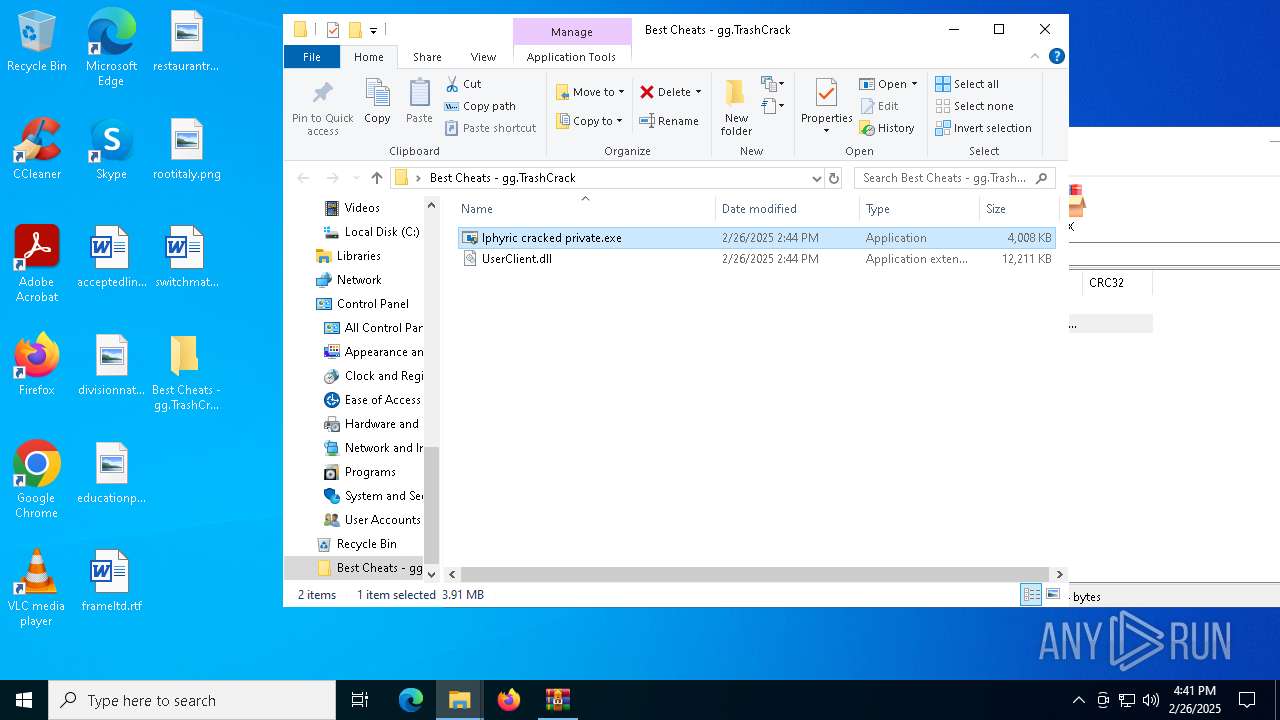
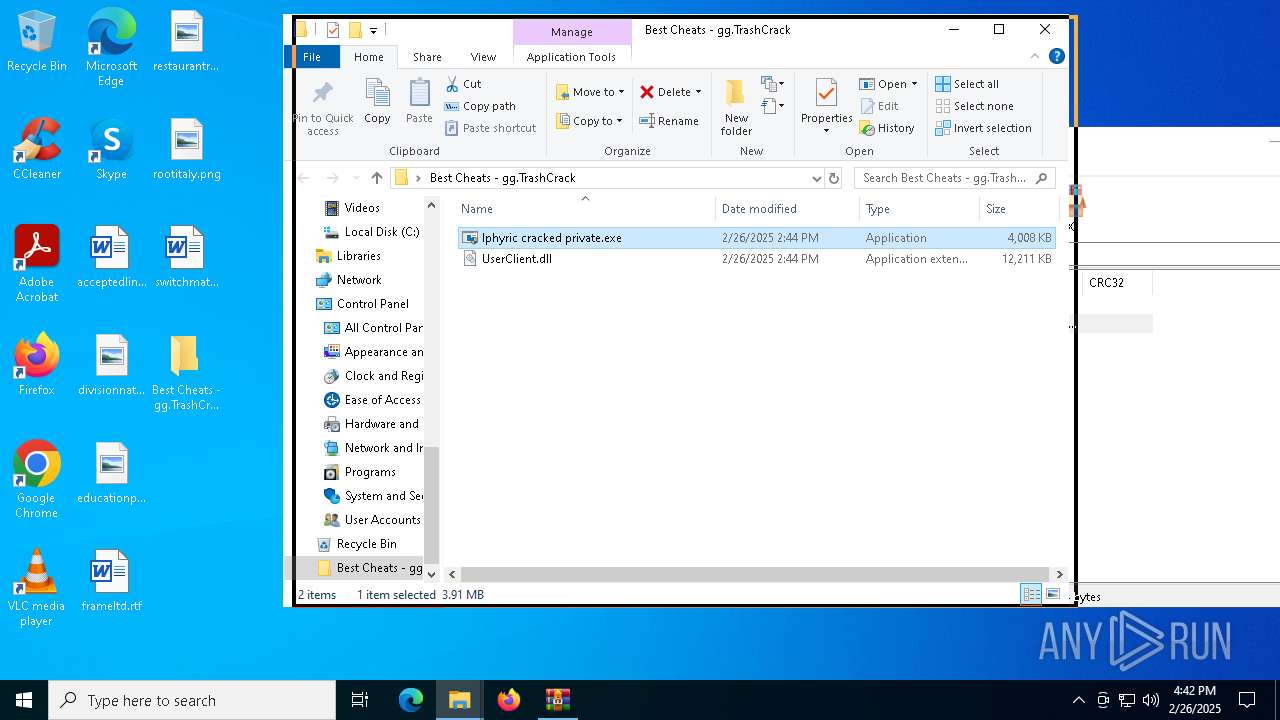
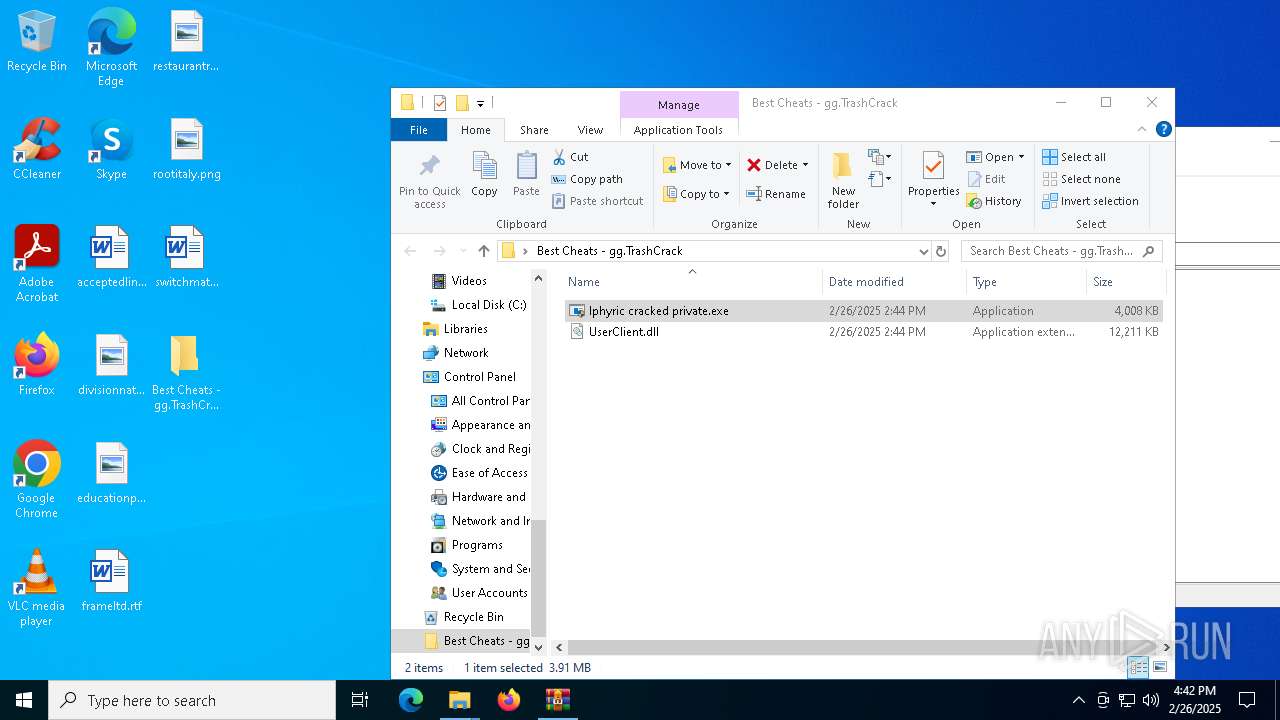
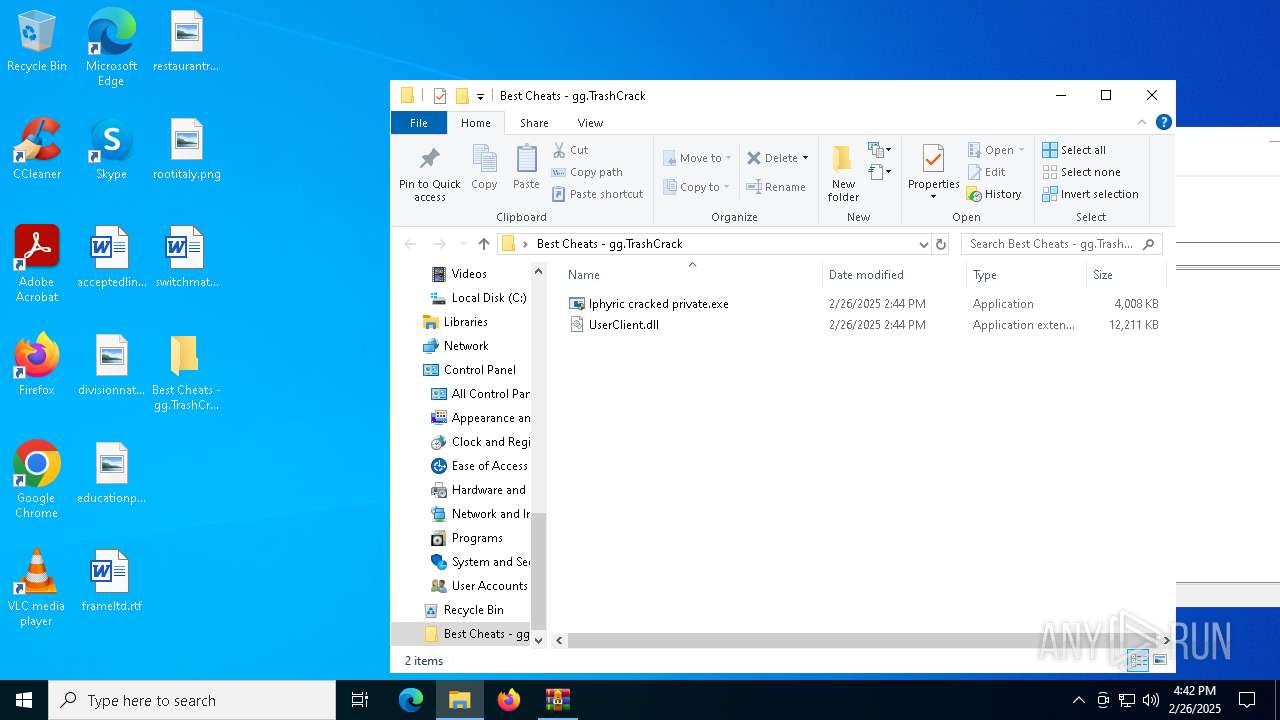
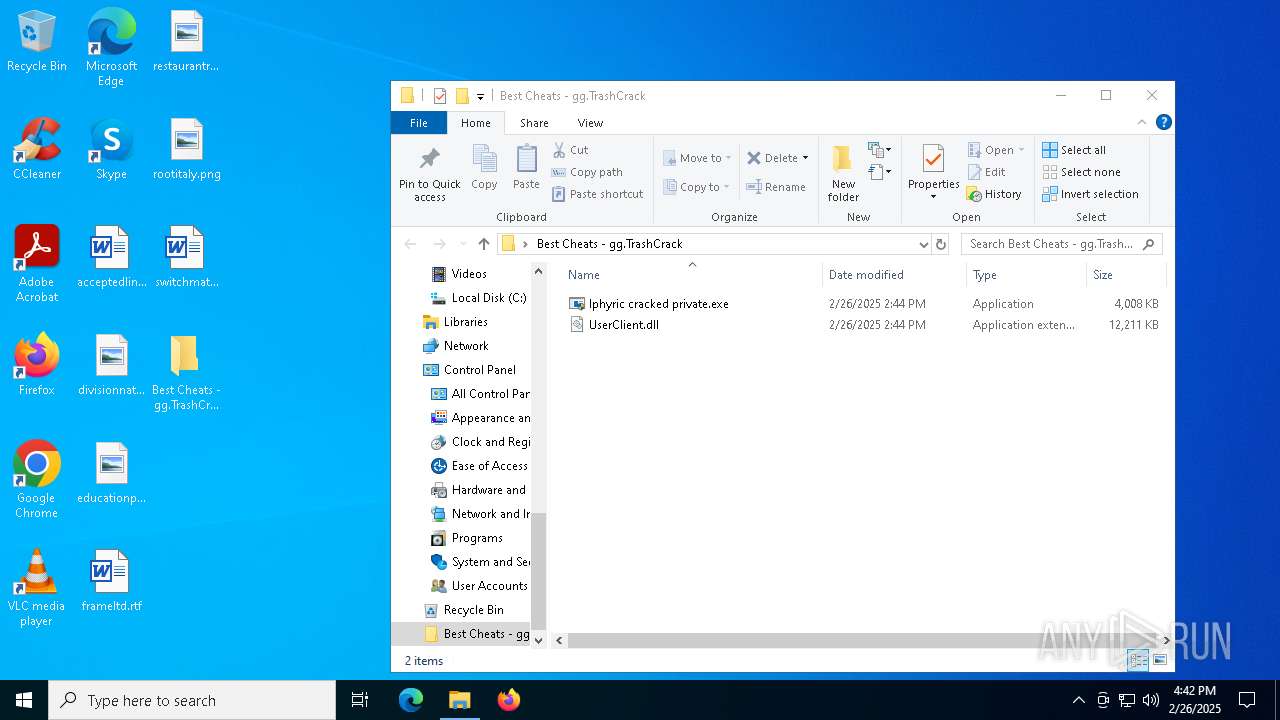
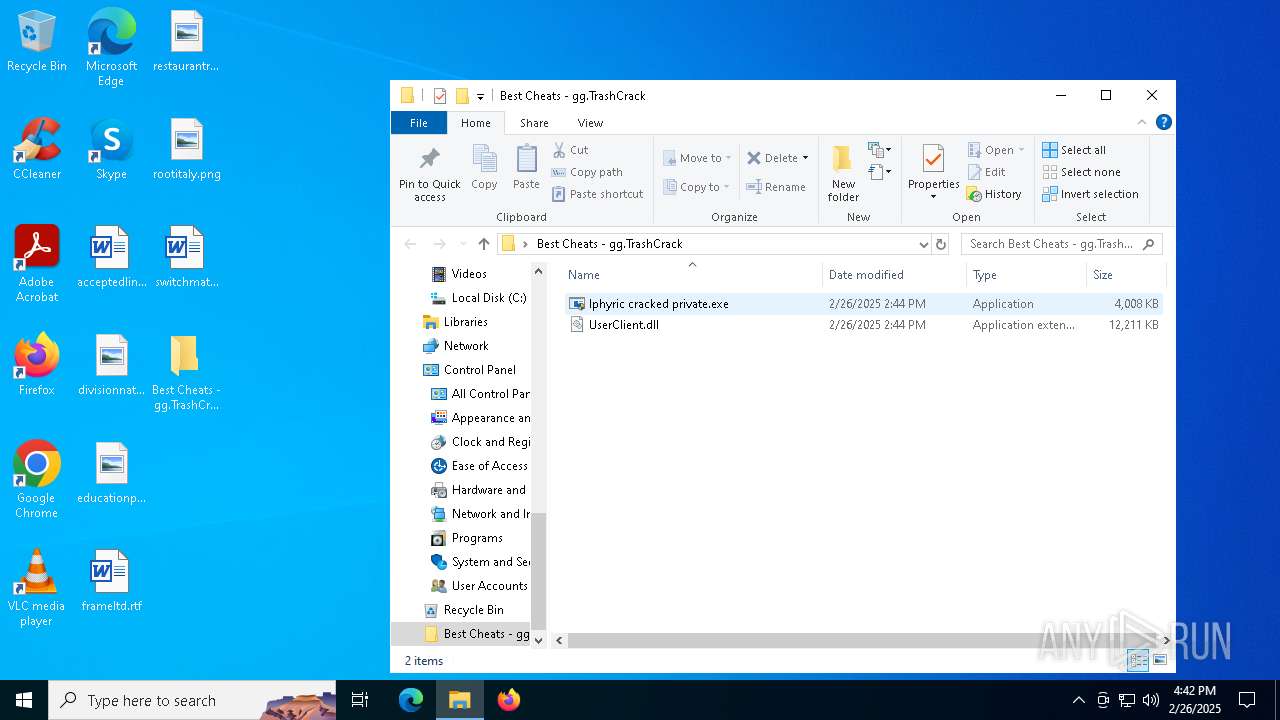
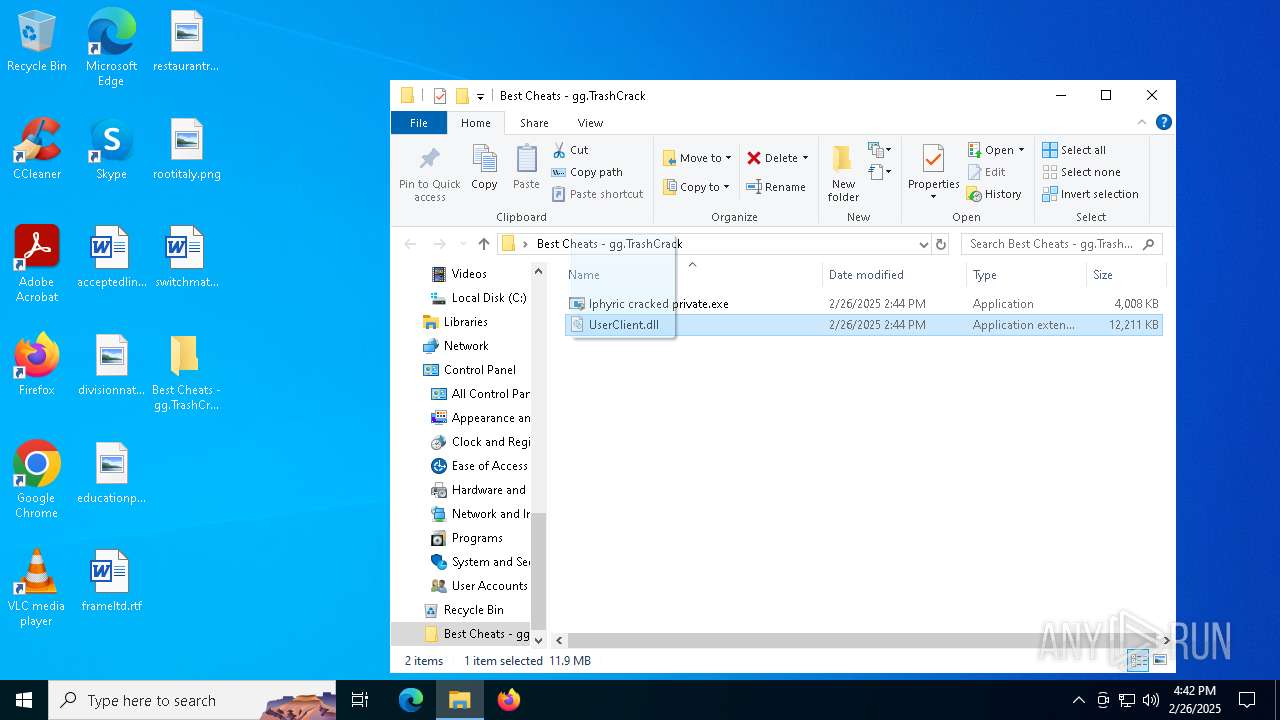
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7500)
The sample compiled with english language support
- WinRAR.exe (PID: 7500)
Manual execution by a user
- lphyric cracked private.exe (PID: 8180)
- lphyric cracked private.exe (PID: 7356)
- lphyric cracked private.exe (PID: 1164)
- lphyric cracked private.exe (PID: 1052)
- WerFault.exe (PID: 7828)
- lphyric cracked private.exe (PID: 5280)
- lphyric cracked private.exe (PID: 4752)
- WerFault.exe (PID: 5264)
Creates files or folders in the user directory
- WerFault.exe (PID: 7292)
- WerFault.exe (PID: 7148)
- WerFault.exe (PID: 7828)
- explorer.exe (PID: 7832)
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
- explorer.exe (PID: 7832)
Reads the computer name
- TextInputHost.exe (PID: 4180)
- StartMenuExperienceHost.exe (PID: 4220)
- SearchApp.exe (PID: 1276)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 4220)
- SearchApp.exe (PID: 1276)
- StartMenuExperienceHost.exe (PID: 4776)
- SearchApp.exe (PID: 4920)
Reads the software policy settings
- SearchApp.exe (PID: 1276)
- SearchApp.exe (PID: 4920)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 1276)
- SearchApp.exe (PID: 4920)
Reads Environment values
- SearchApp.exe (PID: 1276)
- SearchApp.exe (PID: 4920)
Checks proxy server information
- SearchApp.exe (PID: 1276)
- explorer.exe (PID: 7832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:02:26 15:45:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Best Cheats - gg.TrashCrack/ |
Total processes
183
Monitored processes
40
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | C:\WINDOWS\system32\cmd.exe /c reg delete "HKLM\software\microsoft\windows nt\currentversion\winlogon\specialaccounts\userlist" /v user /f > NUL 2>&1 | C:\Windows\System32\cmd.exe | — | lphyric cracked private.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\Desktop\Best Cheats - gg.TrashCrack\lphyric cracked private.exe" | C:\Users\admin\Desktop\Best Cheats - gg.TrashCrack\lphyric cracked private.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 3221225477 Version: 10.0.19041.4355 Modules
| |||||||||||||||
| 1164 | "C:\Users\admin\Desktop\Best Cheats - gg.TrashCrack\lphyric cracked private.exe" | C:\Users\admin\Desktop\Best Cheats - gg.TrashCrack\lphyric cracked private.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 3221226540 Version: 10.0.19041.4355 Modules
| |||||||||||||||
| 1276 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 1 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | C:\WINDOWS\system32\cmd.exe /c reg delete "HKLM\software\microsoft\windows nt\currentversion\winlogon\specialaccounts\userlist" /v user /f > NUL 2>&1 | C:\Windows\System32\cmd.exe | — | lphyric cracked private.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 1 Version: 123.26505.0.0 Modules
| |||||||||||||||
| 4220 | "C:\WINDOWS\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca | C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4400 | reg delete "HKLM\software\microsoft\windows nt\currentversion\winlogon\specialaccounts\userlist" /v user /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4460 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | lphyric cracked private.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
66 309
Read events
65 904
Write events
373
Delete events
32
Modification events
| (PID) Process: | (7500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Best Cheats - gg.TrashCrack.zip | |||
| (PID) Process: | (7500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7500) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000050292 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010010000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C0000001400000000000000610063006300650070007400650064006C0069006E006B002E007200740066003E0020002000000018000000000000006400690076006900730069006F006E006E006100740069006F006E0061006C002E0070006E0067003E00200020000000180000000000000065006400750063006100740069006F006E00700072006500730065006E0074002E0070006E0067003E0020002000000010000000000000006600720061006D0065006C00740064002E007200740066003E002000200000001D00000000000000720065007300740061007500720061006E0074007200650063006F006D006D0065006E006400650064002E0070006E0067003E00200020000000110000000000000072006F006F0074006900740061006C0079002E0070006E0067003E0020002000000014000000000000007300770069007400630068006D00610074007500720065002E007200740066003E002000200000001F000000000000004200650073007400200043006800650061007400730020002D002000670067002E005400720061007300680043007200610063006B003E005C0020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001000000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E00000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000000040000000400F00 | |||
Executable files
8
Suspicious files
64
Text files
144
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7292 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_lphyric cracked _2b9b0c0419d2fdee5792debb4ce66133f212_b30a1dd4_5afff727-e3b8-4a20-b1a7-1c7d82c1890c\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7292 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\lphyric cracked private.exe.7356.dmp | — | |
MD5:— | SHA256:— | |||
| 7148 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_lphyric cracked _a2f5d4c2e932851b6b4b58cc5416bf68ab44538_b30a1dd4_1317a063-c6a5-431d-8b41-a22f56afcbfc\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7148 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\lphyric cracked private.exe.1052.dmp | — | |
MD5:— | SHA256:— | |||
| 7828 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Explorer.EXE_112479ee69d568ac1c92a51887be24eb6bcb60_a6883b46_2a747e4f-bbbb-4980-ae03-d613e7e1c362\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7828 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\explorer.exe.5492.dmp | — | |
MD5:— | SHA256:— | |||
| 1276 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133850617375191682.txt~RF114af0.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\Internet Explorer\DOMStore\ZWUI0EBX\www.bing[1].xml | text | |
MD5:B4DF24E28A75D8CE1ABC7B52FCA881BD | SHA256:8ADABFABD394F0A8240DB9C4FE2D23D3DE932E2603CDE0236CB667BA9BEACDED | |||
| 7292 | WerFault.exe | C:\Windows\appcompat\Programs\Amcache.hve | binary | |
MD5:C1EE15AE4F2B81E97278A7C589B4E771 | SHA256:4D48AB93D3022E5D54491AA7A47CFB1500B76620F2E2FC8D75BD17C1905527DD | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\f01b4d95cf55d32a.automaticDestinations-ms | binary | |
MD5:5396C04FDF13B5360EF4B3C0A9DCC3DE | SHA256:F76B9FC9124B50E93AD97E183E8A537A2C1CE53E9D3F4B1261B831C6320E3ECD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
34
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1348 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1348 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3008 | backgroundTaskHost.exe | 23.15.178.168:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2040 | backgroundTaskHost.exe | 20.223.35.26:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1348 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1348 | SIHClient.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |