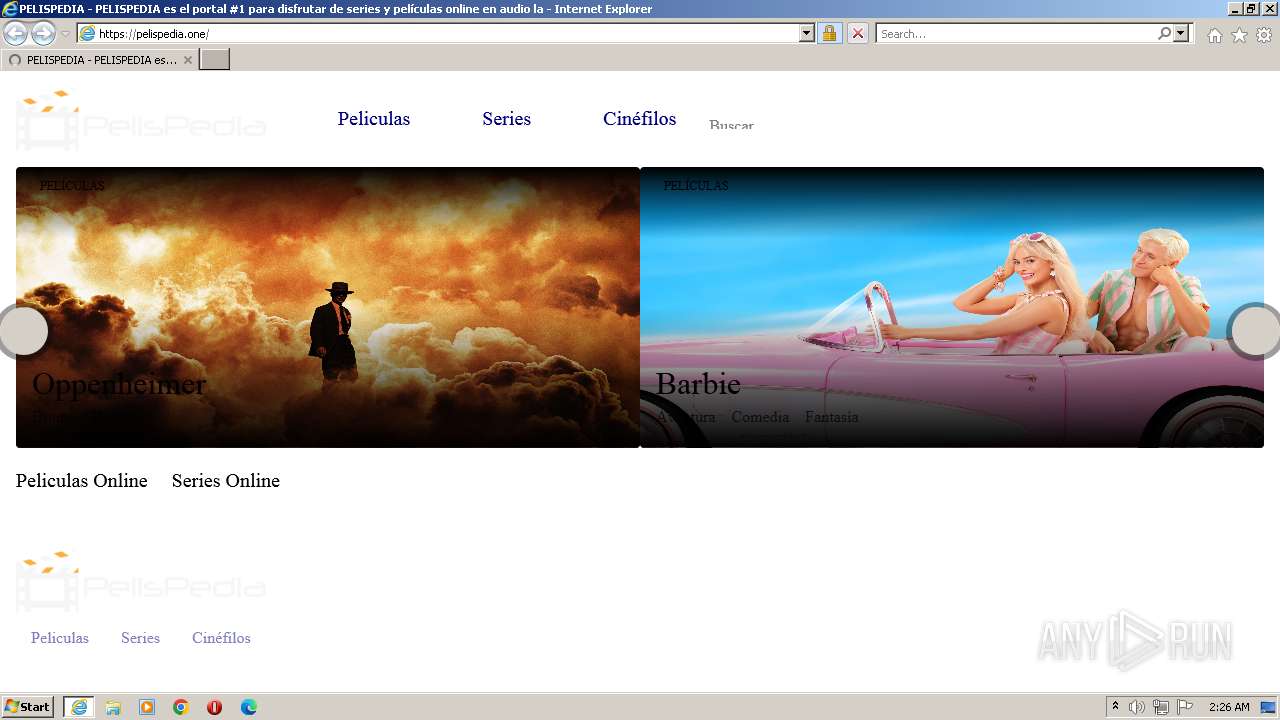
| URL: | https://pelispedia.one |
| Full analysis: | https://app.any.run/tasks/99adc63b-5d10-4957-8f64-6b7b589ff5a9 |
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2023, 01:26:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 345ED8912C45708471A36B7D278A09FF |
| SHA1: | EB1AF1241EA9DA9B15767E4FEB29EF49B80C463B |
| SHA256: | C2DD6C695B0C0AC035EC43EFD282378F74F9E72C4A10941F469700455826AF44 |
| SSDEEP: | 3:N8EVqBMa:2EIx |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 708 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1872 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://pelispedia.one" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 379
Read events
16 320
Write events
59
Delete events
0
Modification events
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1872) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
37
Text files
157
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | der | |
MD5:CFBC16E33DCBEF6F773F0F79AF528F45 | SHA256:F0937890FB1053069BAAC97B7992C6D22CB74CAE20317FC05D51070D96950FFA | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cv[1].css | text | |
MD5:A4AC75722DDCD8338731F214EA465C85 | SHA256:95DF4D820C01AACC202EF9BB0CEAD8DB2BD2ED8DC5FFBE67A938F84F20BD905E | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:AEB9C88176EB85A81BE53114EEFE6676 | SHA256:08F0622C3B7EF4379263434B8567B04FEC9A1F4C164FB0C18E81A24E6FF11101 | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:584322DC100013B19D83E9872E8AE45E | SHA256:1DA0E085BE0DD5C59B55818F9C85024C1D7A43CB21B86FF6D22A09858AD7038C | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cv[1].js | text | |
MD5:EA0CC8453A2AA738F8D401041748A9BA | SHA256:206CC6DB984C4454ADBD64E2553423FFF45BD79E2BA249FC0B512121B6648948 | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\al.min[1].js | text | |
MD5:910FB394AD5A74D7F7E354DF816DC3C0 | SHA256:9582841D623540B2A0087A2E45567A51511AB5D47A84DA256E96B8366BC3723A | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\tv-pub[1].css | text | |
MD5:7B8CF518B579C343028DD5FDD4376625 | SHA256:CFEA3E6D4369361D6B286DE868AB7151A097DBEE85E60E0A83605097929E9C77 | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A16C6C16D94F76E0808C087DFC657D99_CFE4500B88351D74719EA0C4D06650A1 | binary | |
MD5:6A805150F45D285FBDD329FC380F75E5 | SHA256:FB422716A5B379DF52F5C564618DE7A18B9F21DD4B778BEC52580278E353A7FC | |||
| 708 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:35D7745A6C546053F636518FEF2FE543 | SHA256:94A1E9AA9EA7F52C11395D54615899AEF0C365ED246398E0ADF3548B2916D792 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
73
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
708 | iexplore.exe | GET | — | 8.238.34.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e75f427ec8ad9072 | US | — | — | whitelisted |
708 | iexplore.exe | GET | — | 8.238.34.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ce618676216e08ed | US | — | — | whitelisted |
1872 | iexplore.exe | GET | 304 | 8.238.34.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a320ada0b6bdda7d | US | — | — | whitelisted |
1872 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
708 | iexplore.exe | GET | 200 | 23.56.202.135:80 | http://x1.c.lencr.org/ | GB | binary | 717 b | whitelisted |
708 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | US | binary | 724 b | whitelisted |
708 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDGEBdwFpkQsQqVJE7B7pj%2F | US | der | 472 b | whitelisted |
708 | iexplore.exe | GET | 200 | 143.204.214.21:80 | http://s.ss2.us/r.crl | US | binary | 486 b | whitelisted |
708 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEDSBhvknIB0VECgUwi8juNw%3D | US | der | 471 b | whitelisted |
708 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHCCT8p2aYmNEphb5gl7qb8%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
708 | iexplore.exe | 188.114.96.3:443 | pelispedia.one | CLOUDFLARENET | NL | malicious |
708 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
708 | iexplore.exe | 23.56.202.135:80 | x1.c.lencr.org | AKAMAI-AS | GB | suspicious |
708 | iexplore.exe | 142.250.186.74:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
708 | iexplore.exe | 142.250.186.168:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
1872 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
708 | iexplore.exe | 2.21.242.202:80 | r3.o.lencr.org | Akamai International B.V. | DE | whitelisted |
708 | iexplore.exe | 156.146.33.140:443 | ads.themoneytizer.com | Datacamp Limited | DE | suspicious |
708 | iexplore.exe | 143.204.214.21:80 | s.ss2.us | AMAZON-02 | US | suspicious |
708 | iexplore.exe | 52.222.250.185:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pelispedia.one |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
d31rse9wo0bxcx.cloudfront.net |
| unknown |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
image.tmdb.org |
| whitelisted |
ads.themoneytizer.com |
| whitelisted |
o.ss2.us |
| whitelisted |
x1.c.lencr.org |
| whitelisted |