| File name: | c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775 |
| Full analysis: | https://app.any.run/tasks/896d1c4f-5b92-4b14-b90a-d8b46c5ab9f4 |
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2024, 04:48:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 01531F20ABDC9491EE999B76A00F9730 |
| SHA1: | E1E2ACDD11475BEA11A686F45A2C626EFC1A805B |
| SHA256: | C2D3089E50C9F65DA7C9C1BF85E71638CE37C842D5DF7E40DDF1DF9E94494775 |
| SSDEEP: | 98304:TUNs/EdLIpCBvVc5ZiOX7DZUnzPIpqrKejbeYjdTDBOBbjRkC2fQs0ffw3LnHlUF:ssLPy7l11ahK5ImA |
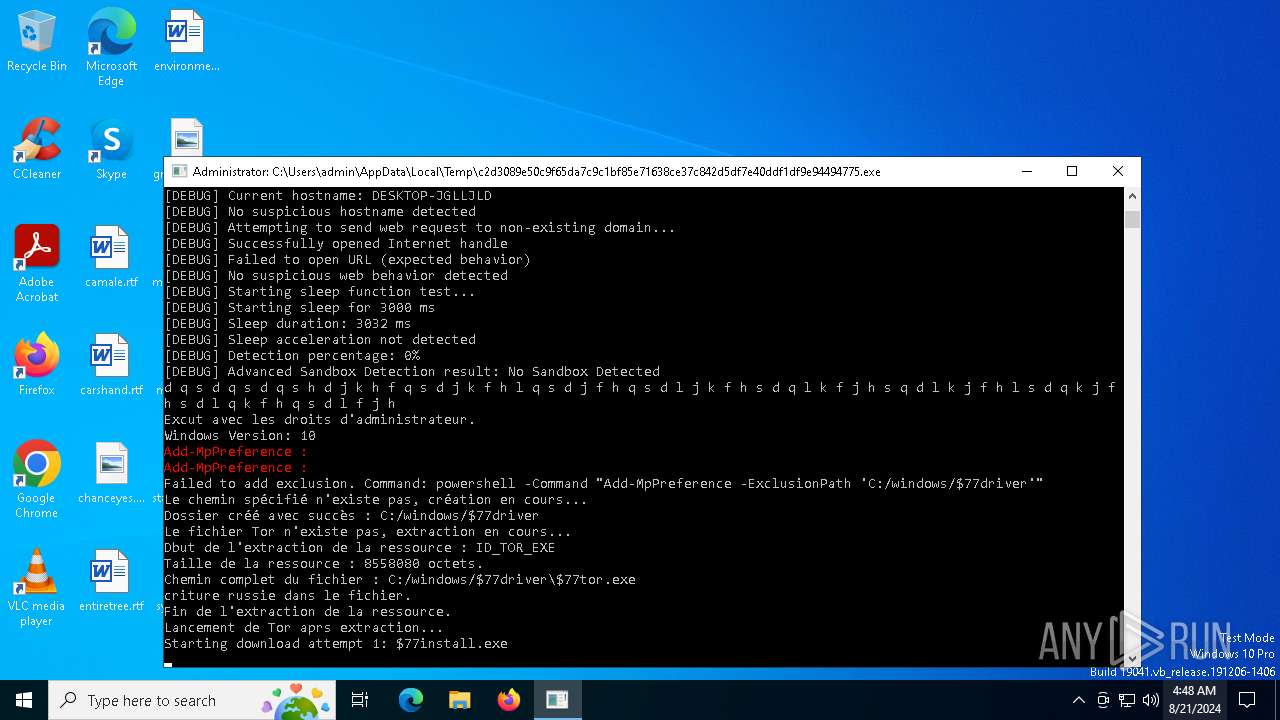
MALICIOUS
Adds path to the Windows Defender exclusion list
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
- cmd.exe (PID: 7092)
SUSPICIOUS
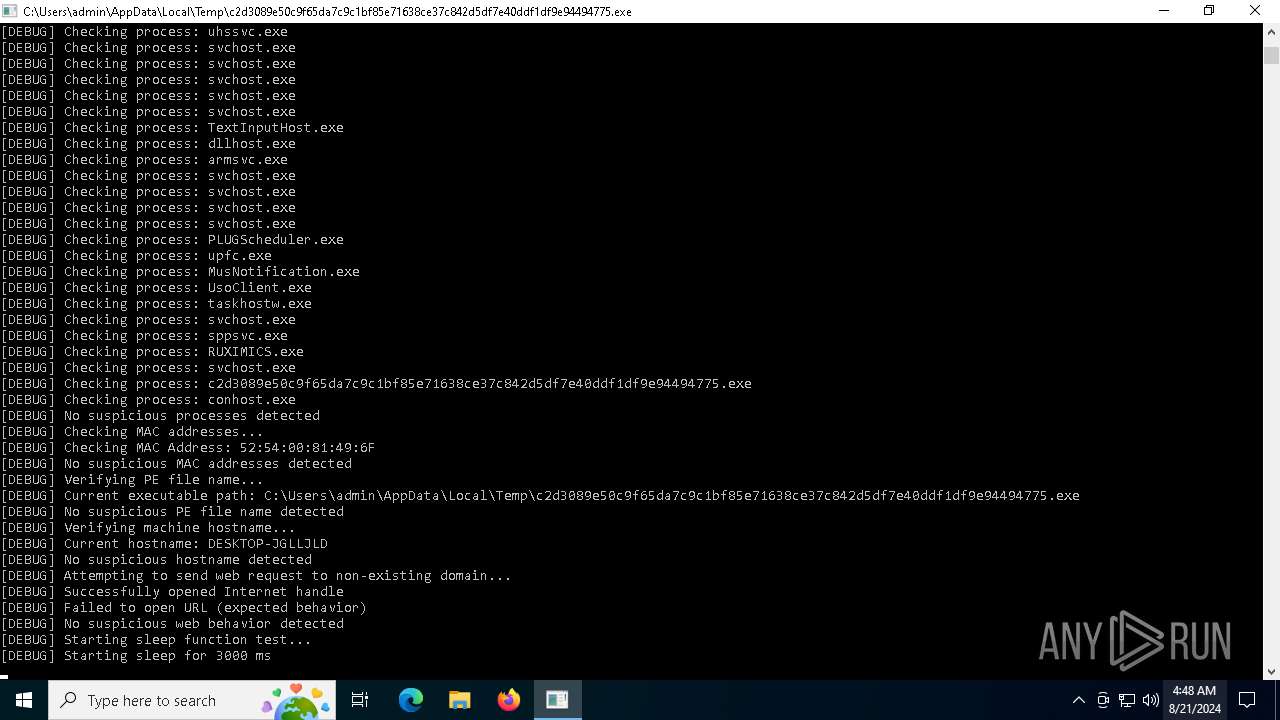
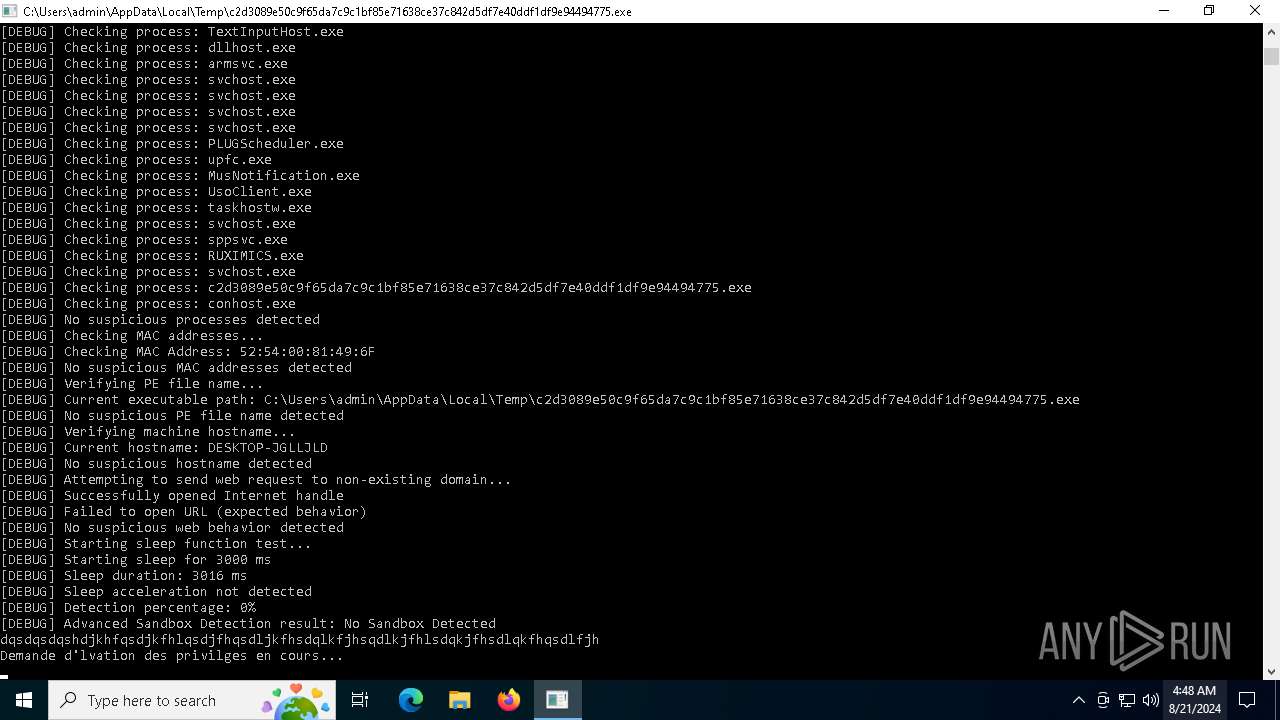
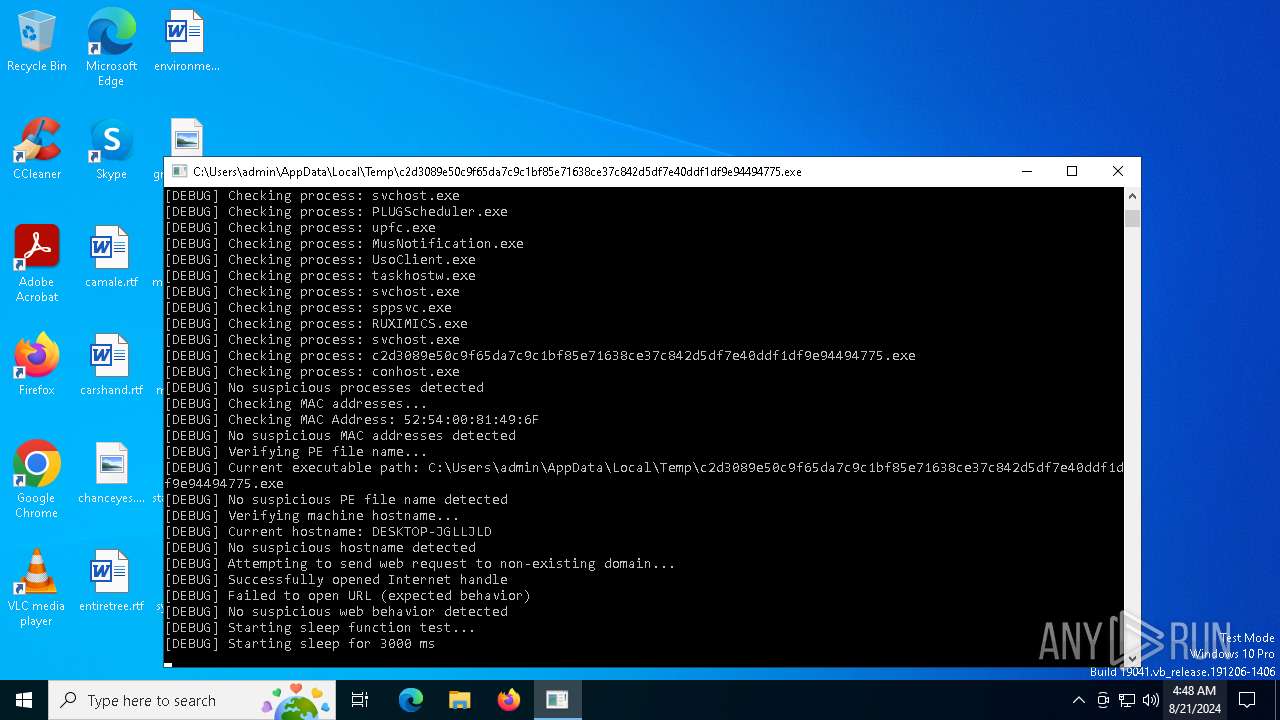
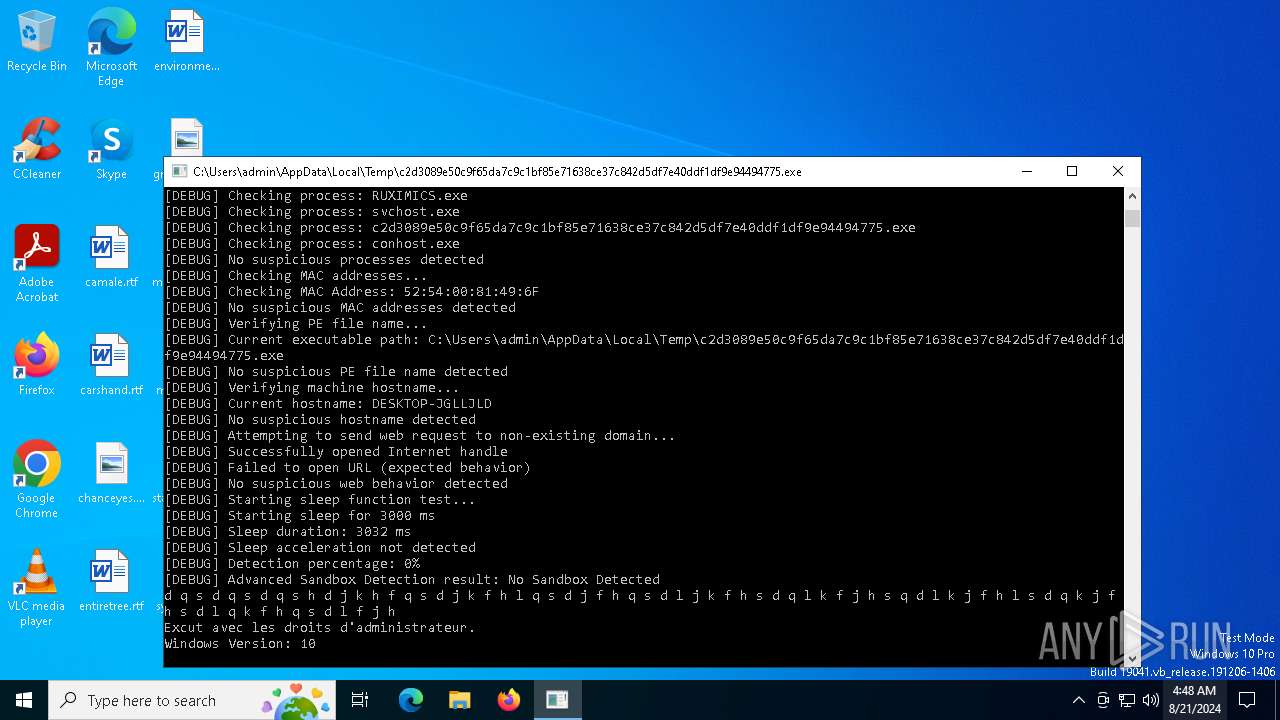
The process checks if it is being run in the virtual environment
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
Reads security settings of Internet Explorer
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
Drops the executable file immediately after the start
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
Reads the date of Windows installation
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
Application launched itself
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7092)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7092)
Starts CMD.EXE for commands execution
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
Executable content was dropped or overwritten
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
Connects to unusual port
- $77tor.exe (PID: 6264)
INFO
Checks proxy server information
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
Reads the computer name
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
- $77tor.exe (PID: 6264)
Checks supported languages
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6836)
- $77tor.exe (PID: 6264)
Process checks computer location settings
- c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe (PID: 6696)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7136)
Creates files or folders in the user directory
- $77tor.exe (PID: 6264)
Reads the machine GUID from the registry
- $77tor.exe (PID: 6264)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:07:13 14:01:04+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 706048 |
| InitializedDataSize: | 8801280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x78fe8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
140
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | $77tor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | C:/windows/$77driver\$77tor.exe | C:\Windows\$77driver\$77tor.exe | c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6696 | "C:\Users\admin\AppData\Local\Temp\c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe" | C:\Users\admin\AppData\Local\Temp\c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6704 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6836 | "C:\Users\admin\AppData\Local\Temp\c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe" | C:\Users\admin\AppData\Local\Temp\c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 6848 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7092 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "Add-MpPreference -ExclusionPath 'C:/windows/$77driver'" | C:\Windows\System32\cmd.exe | — | c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7136 | powershell -Command "Add-MpPreference -ExclusionPath 'C:/windows/$77driver'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 176
Read events
11 160
Write events
16
Delete events
0
Modification events
| (PID) Process: | (6696) c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6696) c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6696) c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6696) c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6836) c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6836) c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6836) c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6836) c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
1
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7136 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:1C877AAA120B0193DE4A4E3224F6C474 | SHA256:A529BC9AA1520A0F178ADF5AD83ED827DC28B4FA4F4A1A31F9C4F60F85B5BBF6 | |||
| 7136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ms5ffvh2.22r.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6264 | $77tor.exe | C:\Users\admin\AppData\Roaming\tor\state | text | |
MD5:60C666D7A0F3F410963AE9CBBFA85F69 | SHA256:815780EA8ED14BD8C242A1F811E7D8CE123FBC88D7067E0E72E0466B25466175 | |||
| 6264 | $77tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-certs | text | |
MD5:609D6BD227DD30998D4FF026C593F513 | SHA256:A5EDA87628BA46F29A2A9C5008F27BA4AC8FFD3D177D6266979C5A057CEB2B29 | |||
| 6264 | $77tor.exe | C:\Users\admin\AppData\Roaming\tor\cached-microdescs.new | text | |
MD5:7EBAD6BE53E78E941BDF1EDC09B9A7F8 | SHA256:3650C870E6DA8FC4F5405F362F2A7673CB99C11B4D11001E92E8AA226CDFB182 | |||
| 6836 | c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | C:\Windows\$77driver\$77install.exe | executable | |
MD5:1A7D1B5D24BA30C4D3D5502295AB5E89 | SHA256:B2CC4454C0A4FC80B1FC782C45AC7F76B1D95913D259090A2523819AEEC88EB5 | |||
| 6836 | c2d3089e50c9f65da7c9c1bf85e71638ce37c842d5df7e40ddf1df9e94494775.exe | C:\Windows\$77driver\$77tor.exe | executable | |
MD5:98E61B0349680D5630548911E355BCAD | SHA256:4DC2054D3023F671DF5CD839A1080CBA34E8D764897ACE57535DCEF6B1C11BF5 | |||
| 6264 | $77tor.exe | C:\Users\admin\AppData\Roaming\tor\unverified-microdesc-consensus.tmp | text | |
MD5:9C8F50326CFDA1DC3545B91C02B5D607 | SHA256:D2B9677B26403A40B53C1A9F9AF8D572B62F03EFB0DABAC0C966FBE0FE118C57 | |||
| 6264 | $77tor.exe | C:\Users\admin\AppData\Roaming\tor\state.tmp | text | |
MD5:60C666D7A0F3F410963AE9CBBFA85F69 | SHA256:815780EA8ED14BD8C242A1F811E7D8CE123FBC88D7067E0E72E0466B25466175 | |||
| 7136 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h4ftgwtr.4n2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
32
DNS requests
18
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3140 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7052 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6536 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4436 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5476 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4436 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3140 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3140 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6264 | $77tor.exe | 5.255.96.218:443 | — | The Infrastructure Group B.V. | NL | unknown |
6264 | $77tor.exe | 95.169.191.6:443 | — | Keyweb AG | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
thisshouldnotexist12345.com |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6264 | $77tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 712 |
6264 | $77tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 840 |
6264 | $77tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 320 |
6264 | $77tor.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 712 |