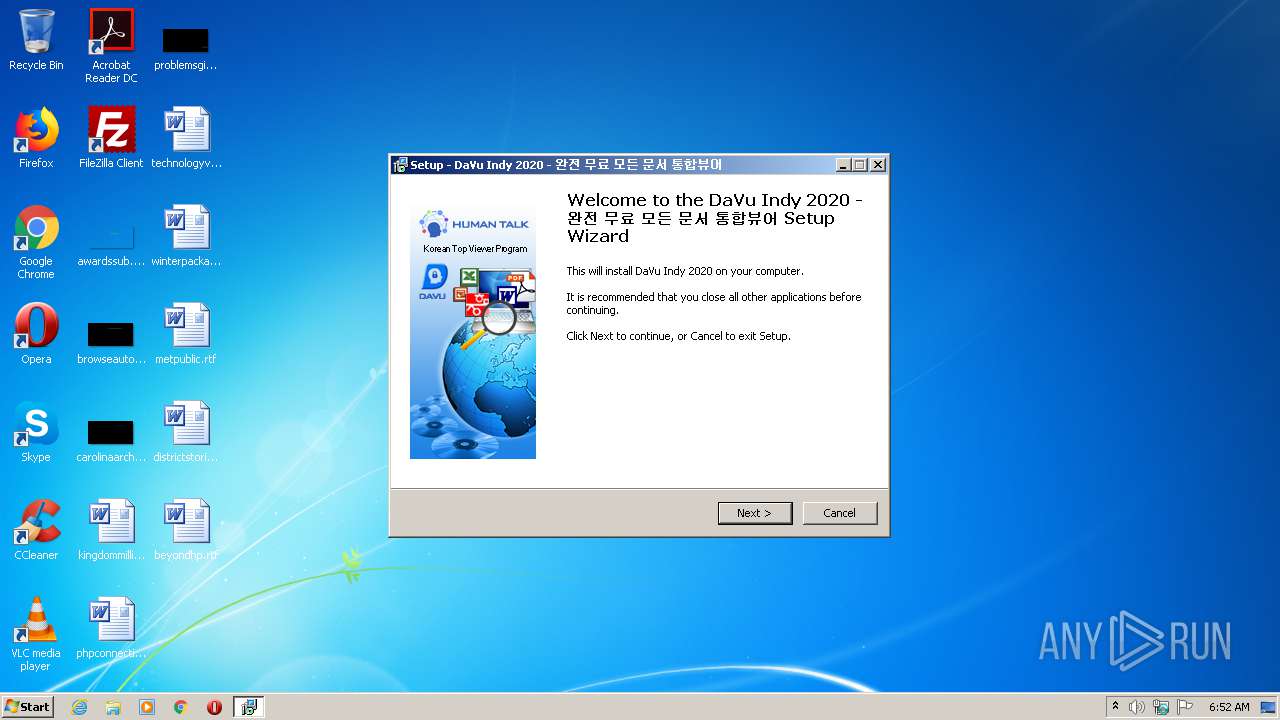
| File name: | DaVuIndy912.exe |
| Full analysis: | https://app.any.run/tasks/6e4b5698-11a8-473f-a51f-43f058a439a6 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2020, 05:51:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0B13440811F70BED3FB2906B9D100525 |
| SHA1: | 5800D21C551CDFE6E94F83FBF0D59CBB823FD755 |
| SHA256: | C2CF9BCE97AEE6E1CF22F914C1E32A705FEC6985D65E4DDE793C7B5D8612B30A |
| SSDEEP: | 196608:rzWMco8rRt+kZIkg/ncqcJfXAkFEvqZp8nTBuwa6UKxnzSBgn3/O8CK8NxeJtkpb:KrykgkqcRAkmvqZGgfqwmPy5eJOXMo |
MALICIOUS
Application was dropped or rewritten from another process
- DaView.exe (PID: 2428)
- LiveUpdate.exe (PID: 1880)
- DaView.exe (PID: 2504)
- LiveUpdate.exe (PID: 1492)
- WinServiceSupHT.exe (PID: 1196)
- winconSeMg.exe (PID: 3512)
- winconSe.exe (PID: 1088)
- LiveUpdate.exe (PID: 3812)
- DaView.exe (PID: 3596)
Changes the autorun value in the registry
- LiveUpdate.exe (PID: 1880)
- LiveUpdate.exe (PID: 1492)
- winconSeMg.exe (PID: 3512)
- LiveUpdate.exe (PID: 3812)
Changes settings of System certificates
- LiveUpdate.exe (PID: 1880)
Loads dropped or rewritten executable
- LiveUpdate.exe (PID: 1880)
- LiveUpdate.exe (PID: 1492)
- DaView.exe (PID: 2504)
- DaView.exe (PID: 2428)
- DaView.exe (PID: 3596)
- LiveUpdate.exe (PID: 3812)
SUSPICIOUS
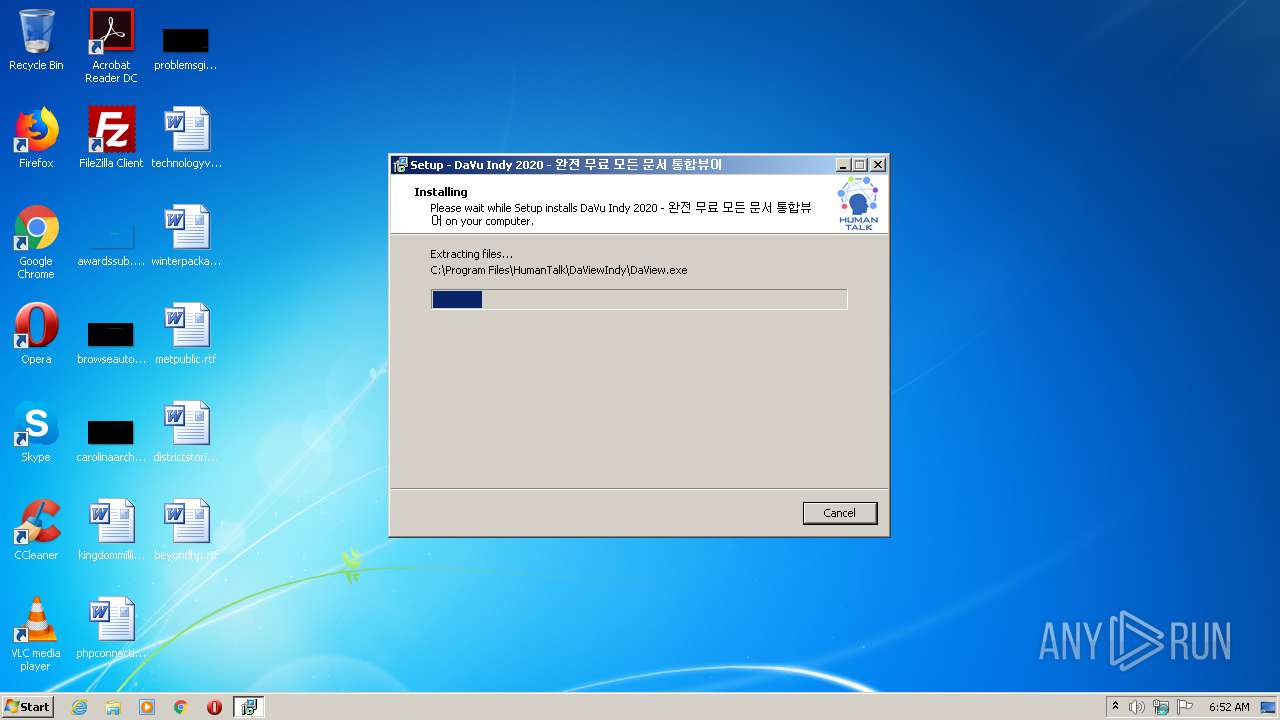
Executable content was dropped or overwritten
- DaVuIndy912.exe (PID: 700)
- DaVuIndy912.exe (PID: 2880)
- DaVuIndy912.tmp (PID: 668)
- WinServiceSupHT.exe (PID: 1196)
- WinServiceSupHT.tmp (PID: 1064)
- LiveUpdate.exe (PID: 1880)
Reads Windows owner or organization settings
- DaVuIndy912.tmp (PID: 668)
- WinServiceSupHT.tmp (PID: 1064)
Reads the Windows organization settings
- DaVuIndy912.tmp (PID: 668)
- WinServiceSupHT.tmp (PID: 1064)
Creates files in the Windows directory
- DaVuIndy912.tmp (PID: 668)
Creates files in the user directory
- DaVuIndy912.tmp (PID: 668)
- LiveUpdate.exe (PID: 1880)
- WinServiceSupHT.tmp (PID: 1064)
- winconSe.exe (PID: 1088)
Reads Internet Cache Settings
- DaView.exe (PID: 2428)
- LiveUpdate.exe (PID: 1880)
- LiveUpdate.exe (PID: 1492)
- DaView.exe (PID: 2504)
- LiveUpdate.exe (PID: 3812)
Modifies the open verb of a shell class
- DaView.exe (PID: 2428)
Changes IE settings (feature browser emulation)
- LiveUpdate.exe (PID: 1880)
Adds / modifies Windows certificates
- LiveUpdate.exe (PID: 1880)
Executed via COM
- iexplore.exe (PID: 2692)
INFO
Application was dropped or rewritten from another process
- DaVuIndy912.tmp (PID: 556)
- DaVuIndy912.tmp (PID: 668)
- WinServiceSupHT.tmp (PID: 1064)
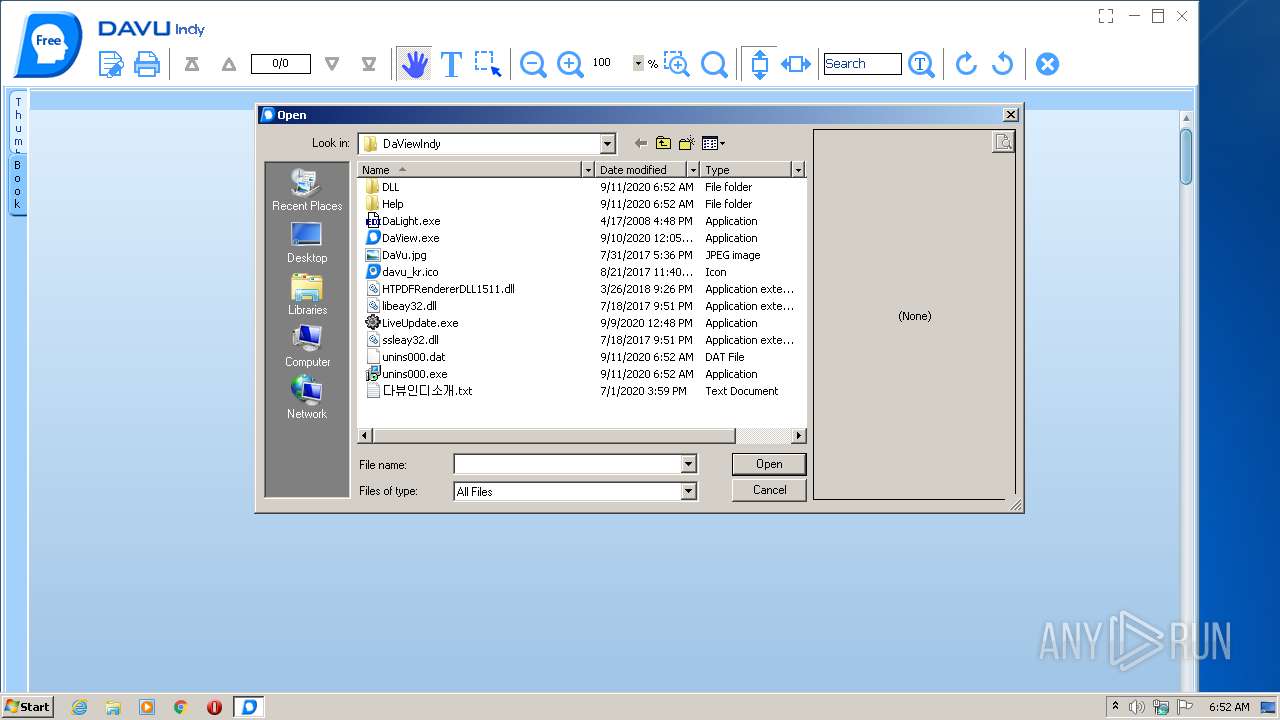
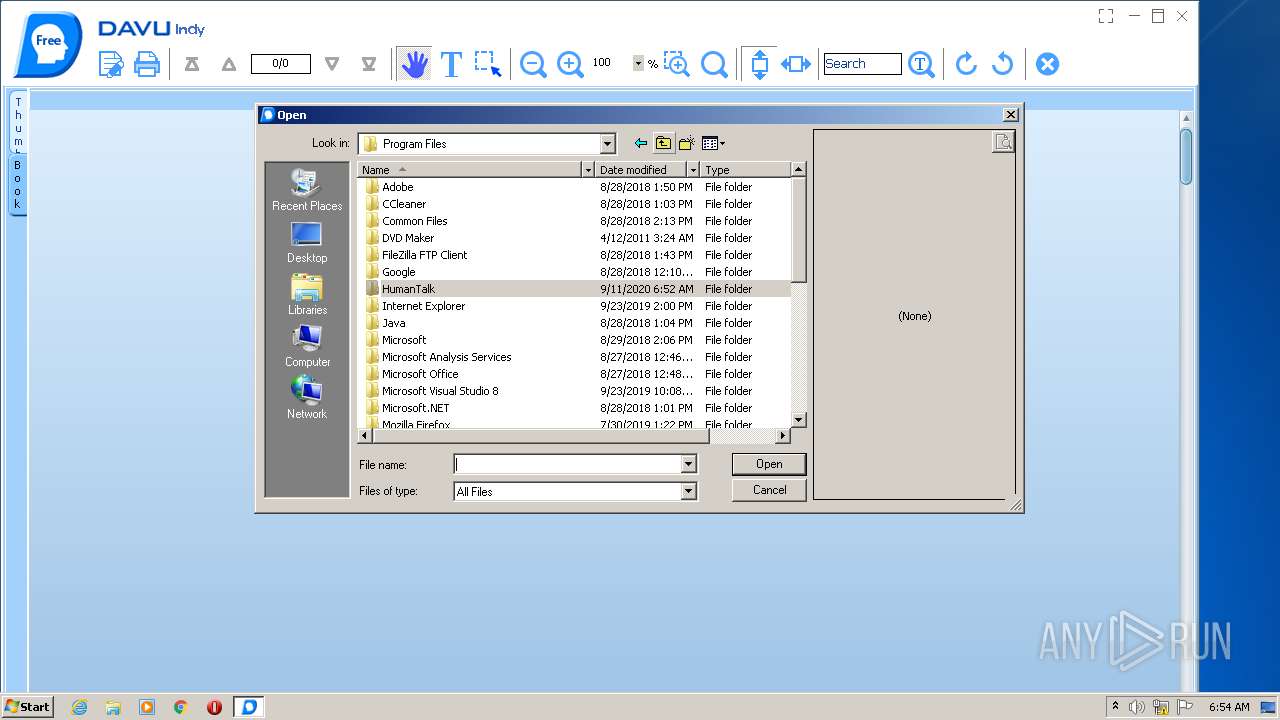
Creates files in the program directory
- DaVuIndy912.tmp (PID: 668)
Creates a software uninstall entry
- DaVuIndy912.tmp (PID: 668)
- WinServiceSupHT.tmp (PID: 1064)
Reads Internet Cache Settings
- iexplore.exe (PID: 2692)
- iexplore.exe (PID: 2492)
Reads internet explorer settings
- iexplore.exe (PID: 2492)
Application launched itself
- iexplore.exe (PID: 2692)
Reads settings of System Certificates
- iexplore.exe (PID: 2492)
Creates files in the user directory
- iexplore.exe (PID: 2492)
Changes internet zones settings
- iexplore.exe (PID: 2692)
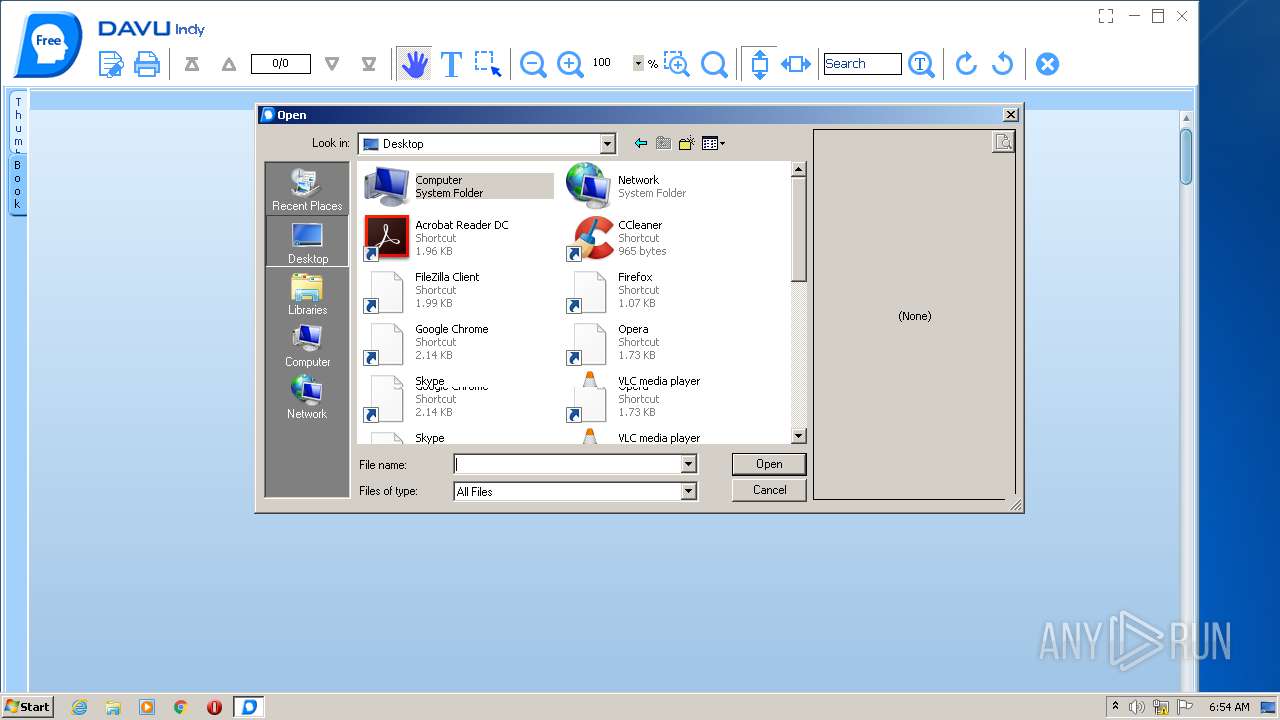
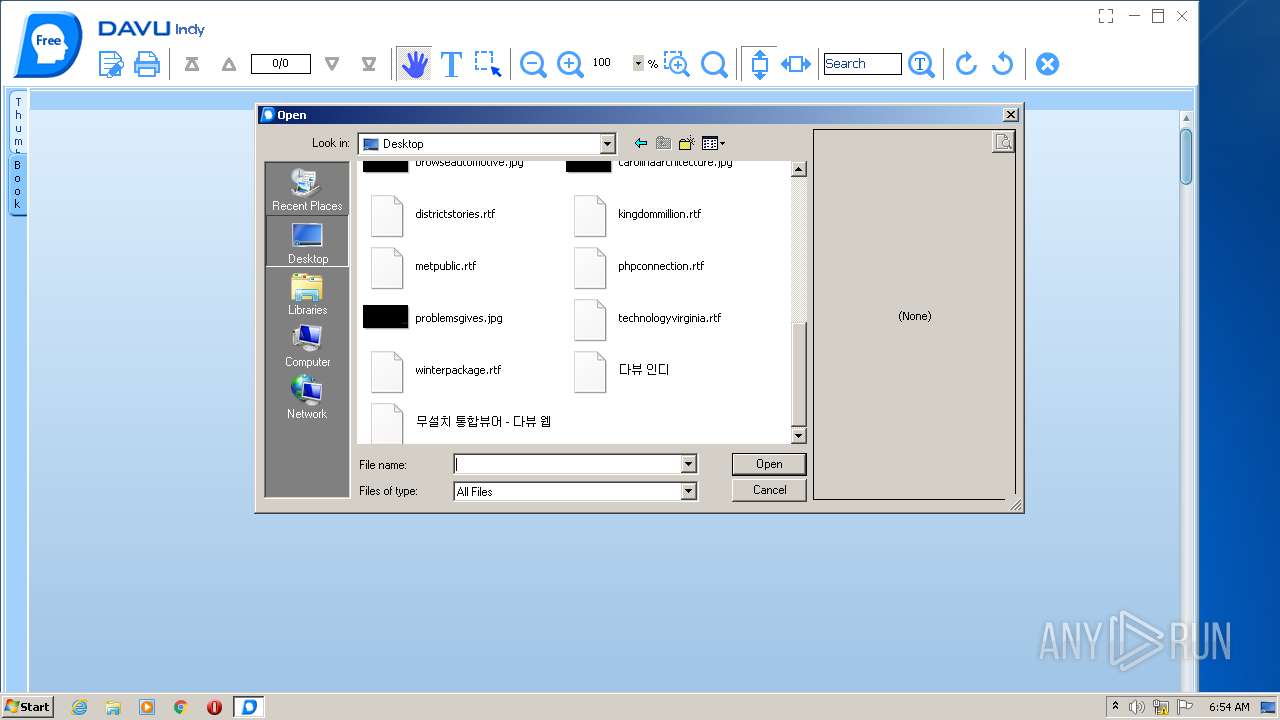
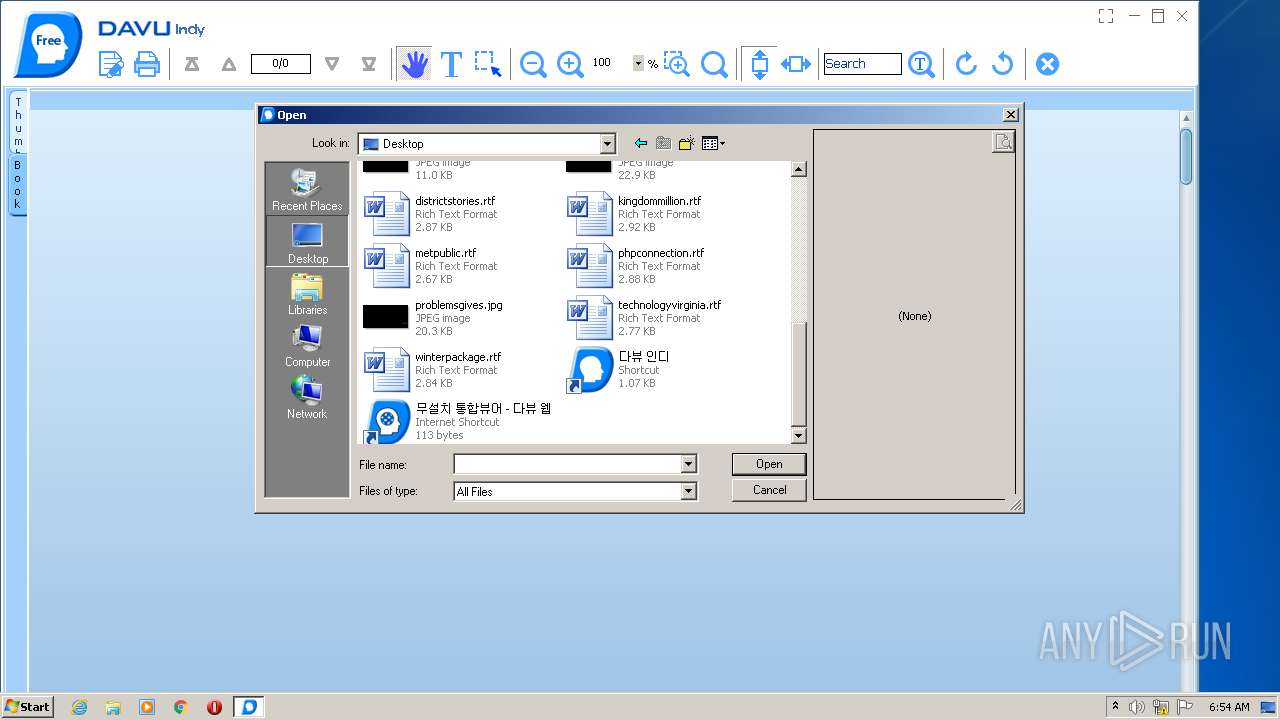
Manual execution by user
- DaView.exe (PID: 3596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.12.0.0 |
| ProductVersionNumber: | 9.12.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
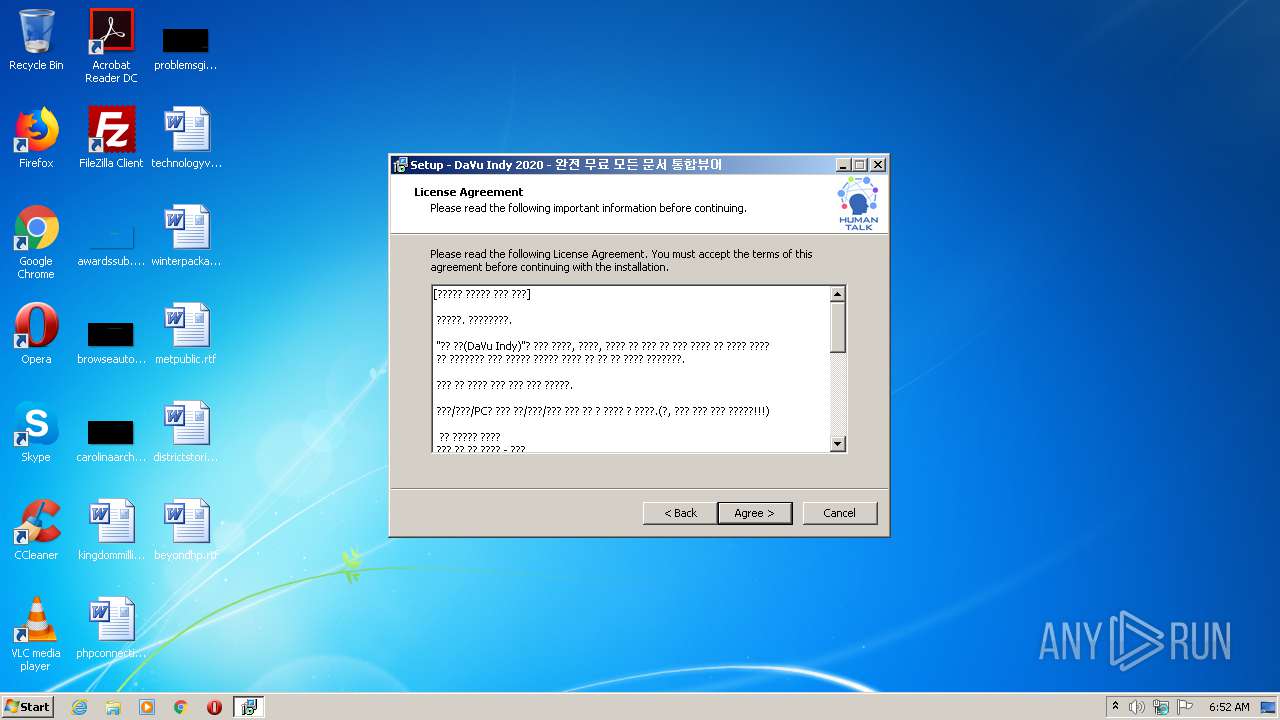
| Comments: | This installation was built with Inno Setup. |
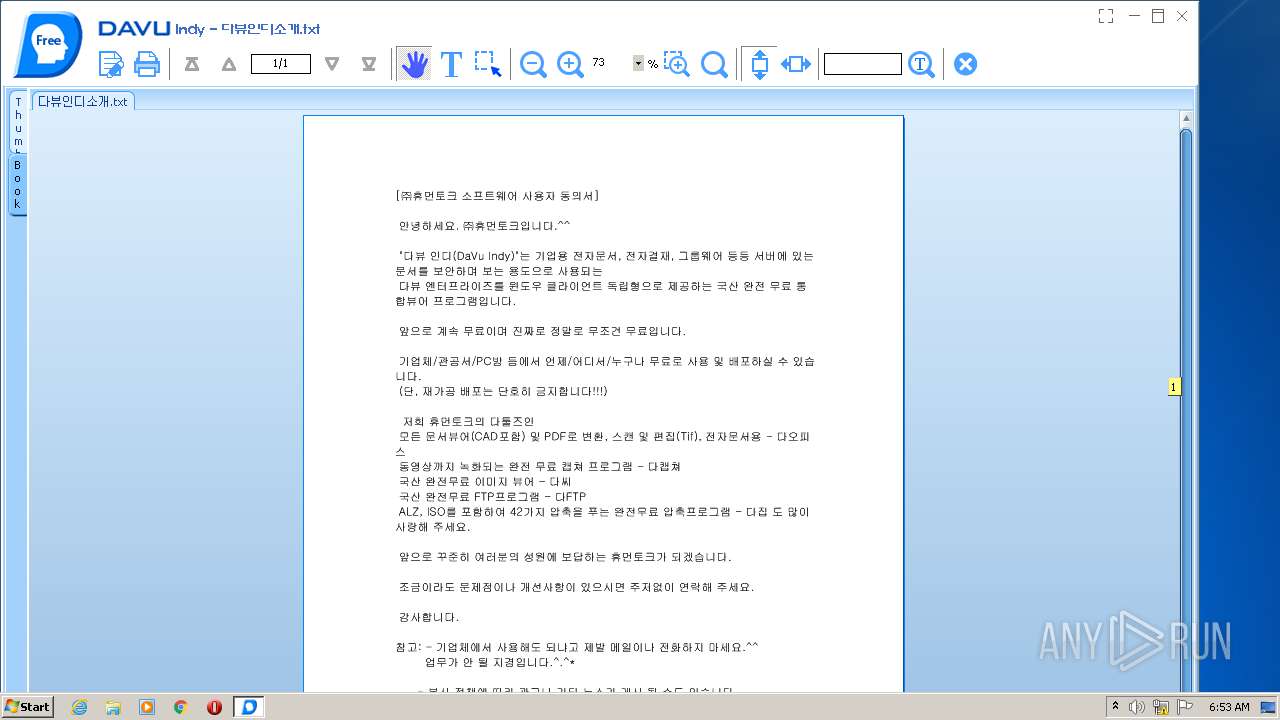
| CompanyName: | (주)휴먼토크 |
| FileDescription: | 다뷰 인디 설치 프로그램 |
| FileVersion: | 9.12 |
| LegalCopyright: | (주)휴먼토크 |
| ProductName: | 다뷰 인디 |
| ProductVersion: | 9.12 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | (주)휴먼토크 |
| FileDescription: | 다뷰 인디 설치 프로그램 |
| FileVersion: | 9.12 |
| LegalCopyright: | (주)휴먼토크 |
| ProductName: | 다뷰 인디 |
| ProductVersion: | 9.12 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14711 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
60
Monitored processes
16
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Users\admin\AppData\Local\Temp\is-M7DDJ.tmp\DaVuIndy912.tmp" /SL5="$90136,12968471,121344,C:\Users\admin\AppData\Local\Temp\DaVuIndy912.exe" | C:\Users\admin\AppData\Local\Temp\is-M7DDJ.tmp\DaVuIndy912.tmp | — | DaVuIndy912.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 668 | "C:\Users\admin\AppData\Local\Temp\is-NOIM0.tmp\DaVuIndy912.tmp" /SL5="$90138,12968471,121344,C:\Users\admin\AppData\Local\Temp\DaVuIndy912.exe" /SPAWNWND=$C012C /NOTIFYWND=$90136 | C:\Users\admin\AppData\Local\Temp\is-NOIM0.tmp\DaVuIndy912.tmp | DaVuIndy912.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 700 | "C:\Users\admin\AppData\Local\Temp\DaVuIndy912.exe" /SPAWNWND=$C012C /NOTIFYWND=$90136 | C:\Users\admin\AppData\Local\Temp\DaVuIndy912.exe | DaVuIndy912.tmp | ||||||||||||
User: admin Company: (주)휴먼토크 Integrity Level: HIGH Description: 다뷰 인디 설치 프로그램 Exit code: 0 Version: 9.12 Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\AppData\Local\Temp\is-7PPB4.tmp\WinServiceSupHT.tmp" /SL5="$250142,3356235,780288,C:\Users\admin\AppData\Roaming\WinServiceSup\WinServiceSupHT.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\is-7PPB4.tmp\WinServiceSupHT.tmp | WinServiceSupHT.exe | ||||||||||||
User: admin Company: Plan11 Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1088 | "C:\Users\admin\AppData\Roaming\WinServiceSup\winconSe.exe" | C:\Users\admin\AppData\Roaming\WinServiceSup\winconSe.exe | winconSeMg.exe | ||||||||||||
User: admin Company: plan11 Integrity Level: HIGH Exit code: 0 Version: 2020.8.31.3 Modules
| |||||||||||||||
| 1196 | "C:\Users\admin\AppData\Roaming\WinServiceSup\WinServiceSupHT.exe" /verysilent | C:\Users\admin\AppData\Roaming\WinServiceSup\WinServiceSupHT.exe | LiveUpdate.exe | ||||||||||||
User: admin Company: Plan11 Integrity Level: HIGH Description: WinSvcSupHT Setup Exit code: 0 Version: 2020.09.09.2 Modules
| |||||||||||||||
| 1492 | "C:\Users\admin\AppData\Roaming\HumanTalk\LiveUpdate\LiveUpdate.exe" "PROGRAMDVIWIN 9.12" 131642 HTUpdateDV_En.dat http://topview.kr | C:\Users\admin\AppData\Roaming\HumanTalk\LiveUpdate\LiveUpdate.exe | DaView.exe | ||||||||||||
User: admin Company: HumanTalk Integrity Level: MEDIUM Description: DaTools Update Program Exit code: 0 Version: 9.11.5.0 Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\AppData\Roaming\HumanTalk\LiveUpdate\LiveUpdate.exe" INST DVIWIN 9.12 http://topview.kr Components:plan11,coupang WV:6.01.7601 DF:HTUpdateDV.dat | C:\Users\admin\AppData\Roaming\HumanTalk\LiveUpdate\LiveUpdate.exe | DaVuIndy912.tmp | ||||||||||||
User: admin Company: HumanTalk Integrity Level: HIGH Description: DaTools Update Program Exit code: 0 Version: 9.11.5.0 Modules
| |||||||||||||||
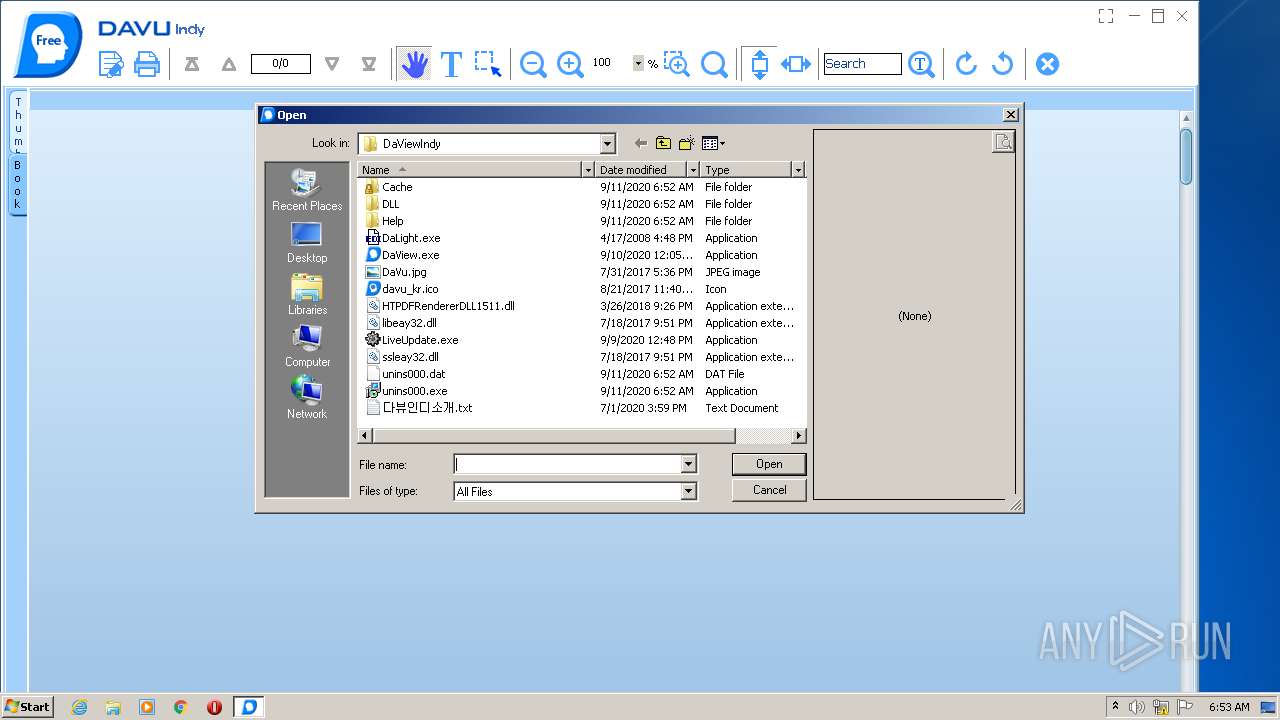
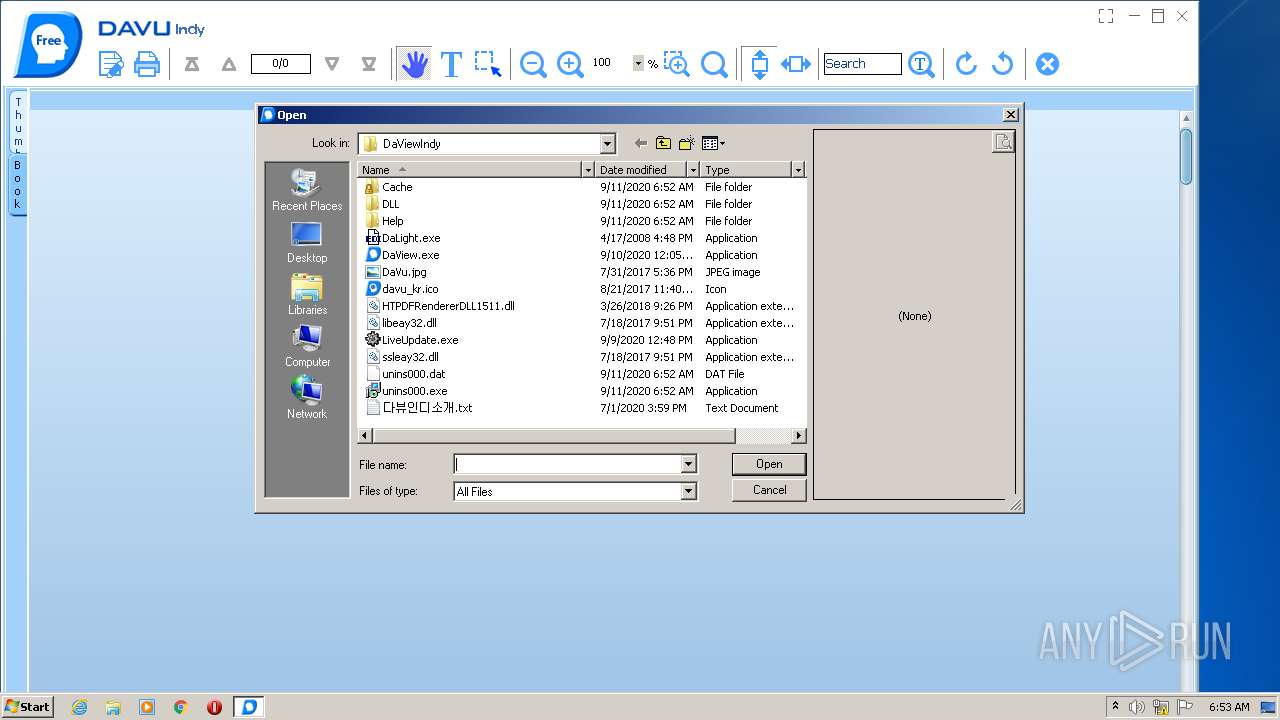
| 2428 | "C:\Program Files\HumanTalk\DaViewIndy\DaView.exe" -C | C:\Program Files\HumanTalk\DaViewIndy\DaView.exe | — | DaVuIndy912.tmp | |||||||||||
User: admin Company: (주)휴먼토크 Integrity Level: HIGH Description: DaVu - Viewer for All Documents. Exit code: 0 Version: 9.12.0.0 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2692 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
4 174
Read events
3 428
Write events
737
Delete events
9
Modification events
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_CURRENT_USER\Software\HumanTalk\LiveUpdate |
| Operation: | write | Name: | ForceClose |
Value: 1 | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\*\shell\DaView |
| Operation: | write | Name: | (default) |
Value: 다뷰 인디로 열기 | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\*\shell\DaView\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\HumanTalk\DaViewIndy\DaView.exe" "%1" | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DaVuIndy_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (u) | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DaVuIndy_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\HumanTalk\DaViewIndy | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DaVuIndy_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\HumanTalk\DaViewIndy\ | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DaVuIndy_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: 휴먼토크\다뷰인디 | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DaVuIndy_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DaVuIndy_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: full | |||
| (PID) Process: | (668) DaVuIndy912.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DaVuIndy_is1 |
| Operation: | write | Name: | Inno Setup: Selected Components |
Value: main,plan11,coupang | |||
Executable files
51
Suspicious files
61
Text files
88
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\is-G61N7.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\is-4SGLV.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\is-78000.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\is-I1B3F.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\is-6P3AV.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\is-3B7VO.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\DLL\is-960JU.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\DLL\is-B0AM2.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\Help\is-BFFJ0.tmp | — | |
MD5:— | SHA256:— | |||
| 668 | DaVuIndy912.tmp | C:\Program Files\HumanTalk\DaViewIndy\is-BFCUS.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
70
DNS requests
41
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1492 | LiveUpdate.exe | GET | 200 | 112.171.126.85:80 | http://topview.kr/DaStatistic/DaStc?name=DVIWIN&version=9.12&option=-resolution:1280X720-IS64:32-LU:9.115 | KR | — | — | suspicious |
1088 | winconSe.exe | GET | 304 | 193.108.153.18:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
3512 | winconSeMg.exe | GET | 304 | 193.108.153.18:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
1088 | winconSe.exe | GET | 304 | 193.108.153.18:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
1880 | LiveUpdate.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1880 | LiveUpdate.exe | GET | 200 | 193.108.153.5:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.0 Kb | whitelisted |
1880 | LiveUpdate.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2504 | DaView.exe | POST | 200 | 112.171.126.153:80 | http://dvwin14.inoview.kr/DaViewIndy/FileUpload?filepath=Indy/win/192168100124C4BA3647/ | KR | text | 48 b | suspicious |
1880 | LiveUpdate.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCfIlWn9rgZqF2qblWkPMmX | US | der | 472 b | whitelisted |
1880 | LiveUpdate.exe | GET | 304 | 193.108.153.5:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1880 | LiveUpdate.exe | 112.175.246.70:443 | www.hmtalk.com | Korea Telecom | KR | suspicious |
1880 | LiveUpdate.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1492 | LiveUpdate.exe | 112.175.246.70:443 | www.hmtalk.com | Korea Telecom | KR | suspicious |
1880 | LiveUpdate.exe | 112.175.69.174:443 | noform.co.kr | Korea Telecom | KR | suspicious |
1492 | LiveUpdate.exe | 112.171.126.85:80 | topview.kr | Korea Telecom | KR | unknown |
1880 | LiveUpdate.exe | 193.108.153.5:80 | www.download.windowsupdate.com | Akamai International B.V. | — | suspicious |
1088 | winconSe.exe | 112.175.69.174:443 | noform.co.kr | Korea Telecom | KR | suspicious |
1088 | winconSe.exe | 193.108.153.18:80 | www.download.windowsupdate.com | Akamai International B.V. | — | suspicious |
1088 | winconSe.exe | 112.175.69.181:443 | www.networkbence.co.kr | Korea Telecom | KR | unknown |
2492 | iexplore.exe | 112.171.126.153:80 | dvwin14.inoview.kr | Korea Telecom | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hmtalk.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
noform.co.kr |
| suspicious |
hmtalk.com |
| suspicious |
www.noform.co.kr |
| suspicious |
topview.kr |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
dvwin14.inoview.kr |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1880 | LiveUpdate.exe | Potential Corporate Privacy Violation | ET POLICY SSLv3 outbound connection from client vulnerable to POODLE attack |