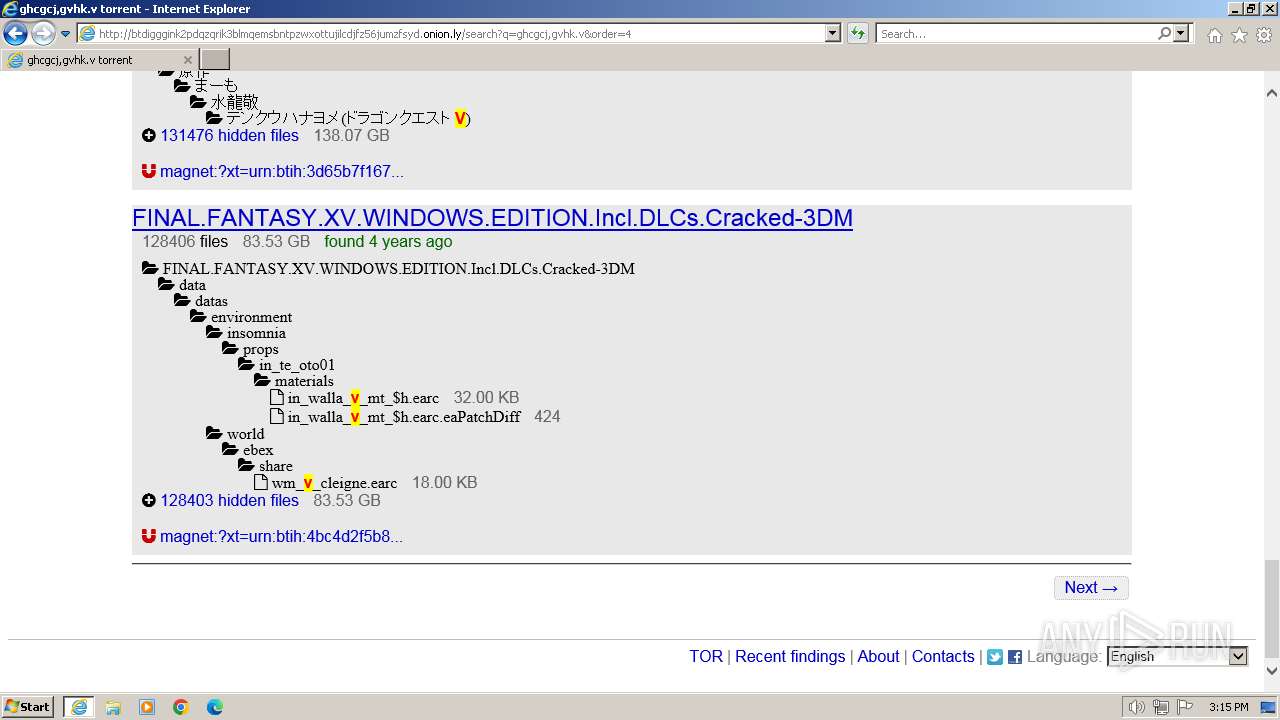
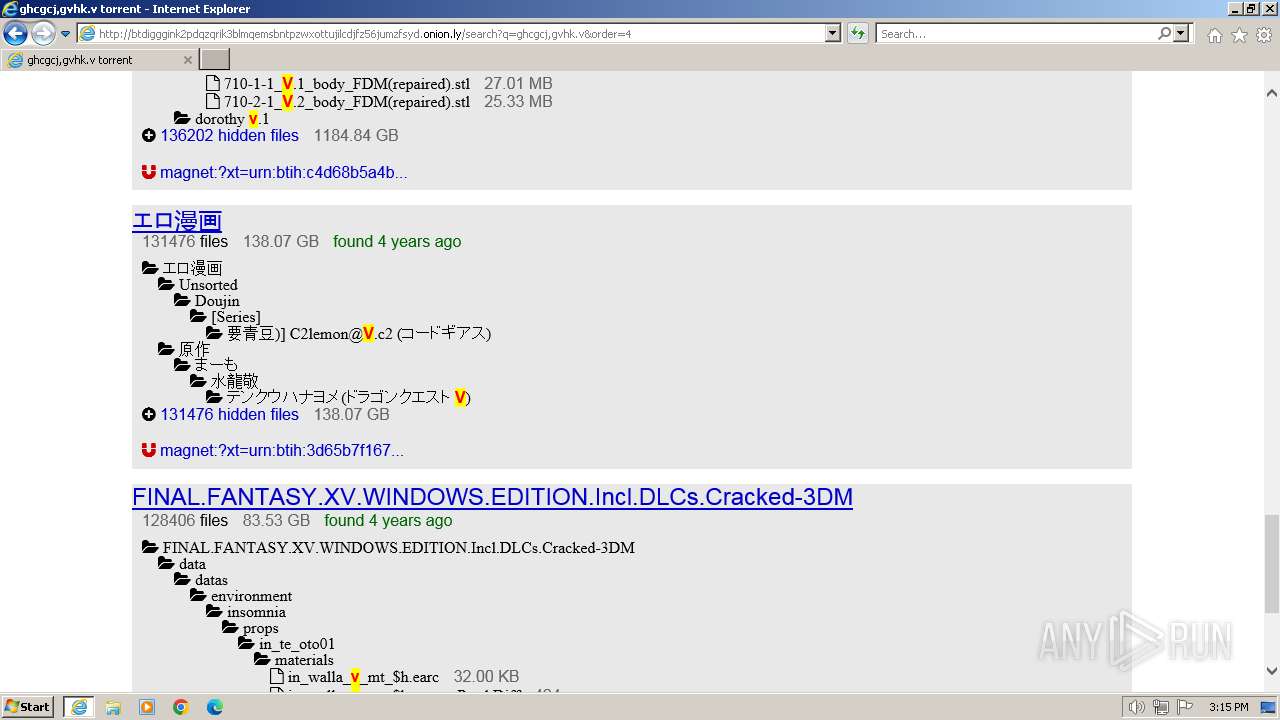
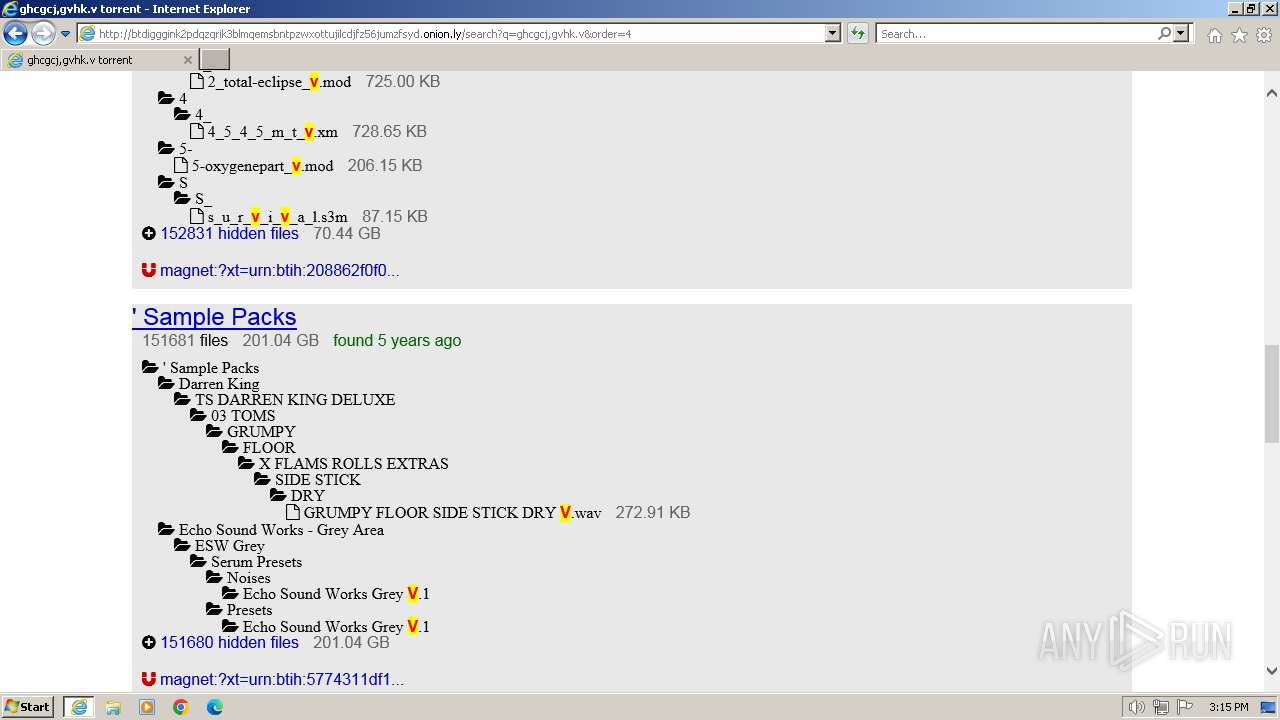
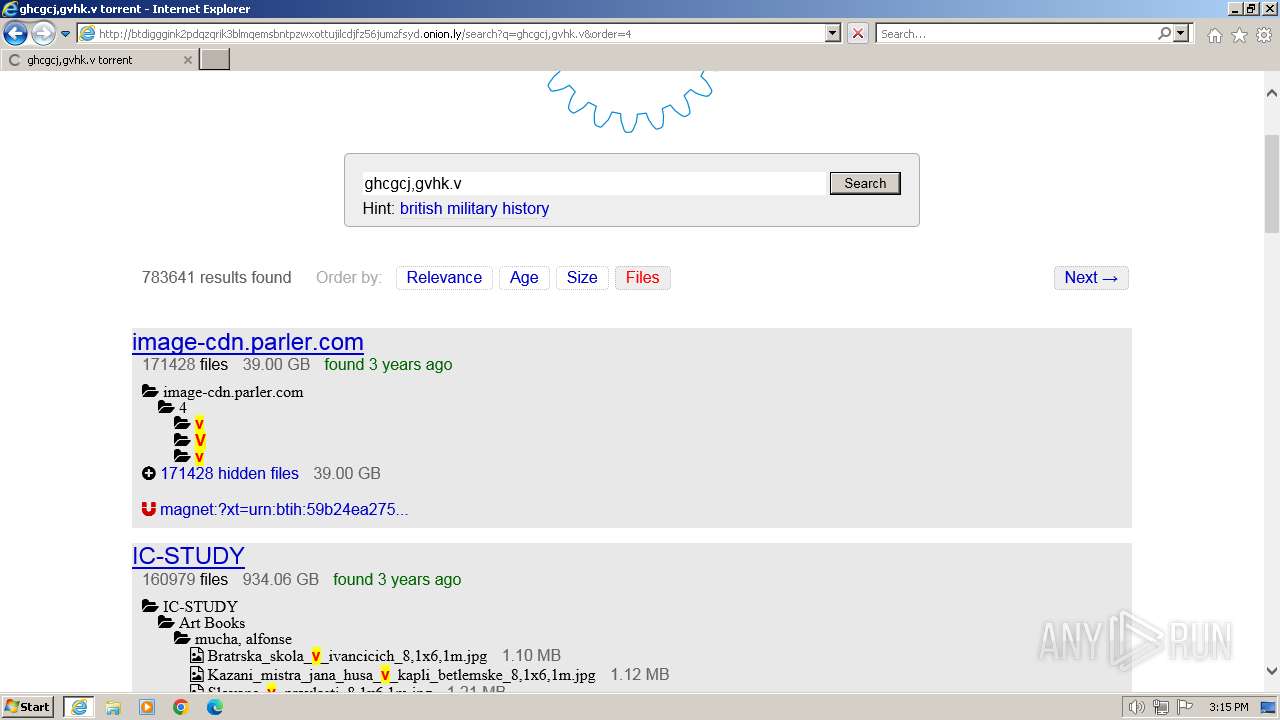
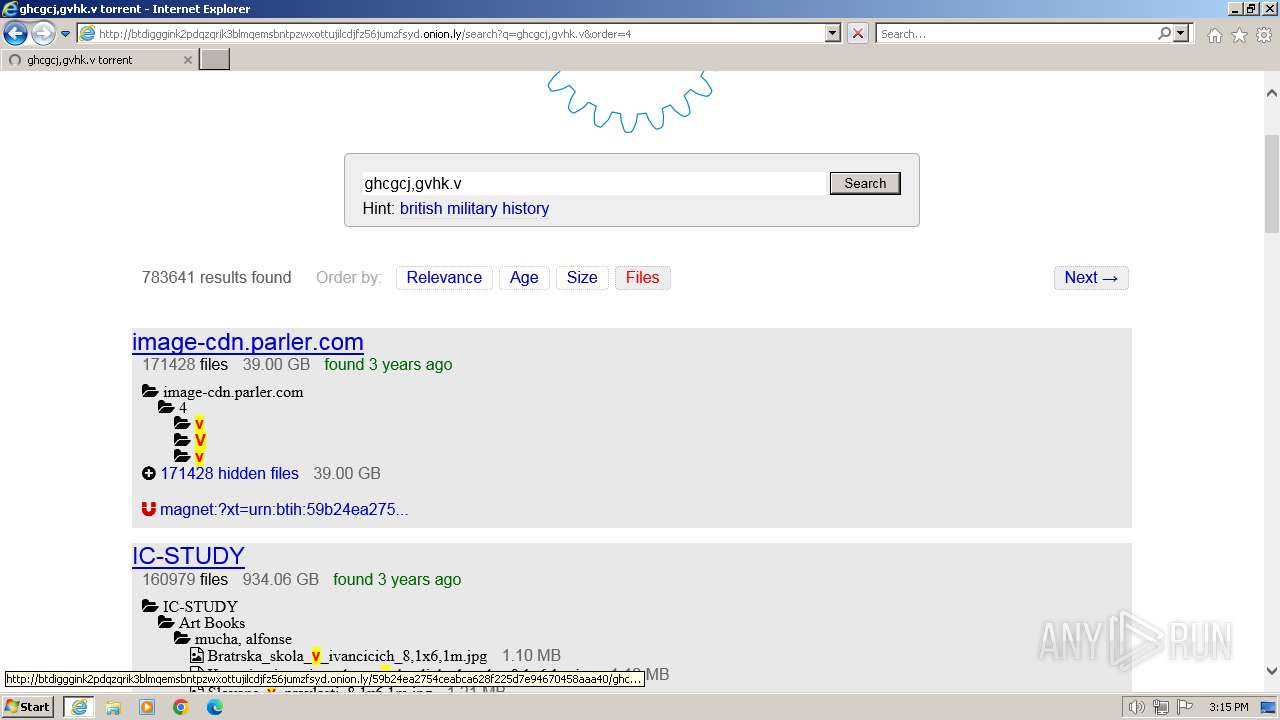
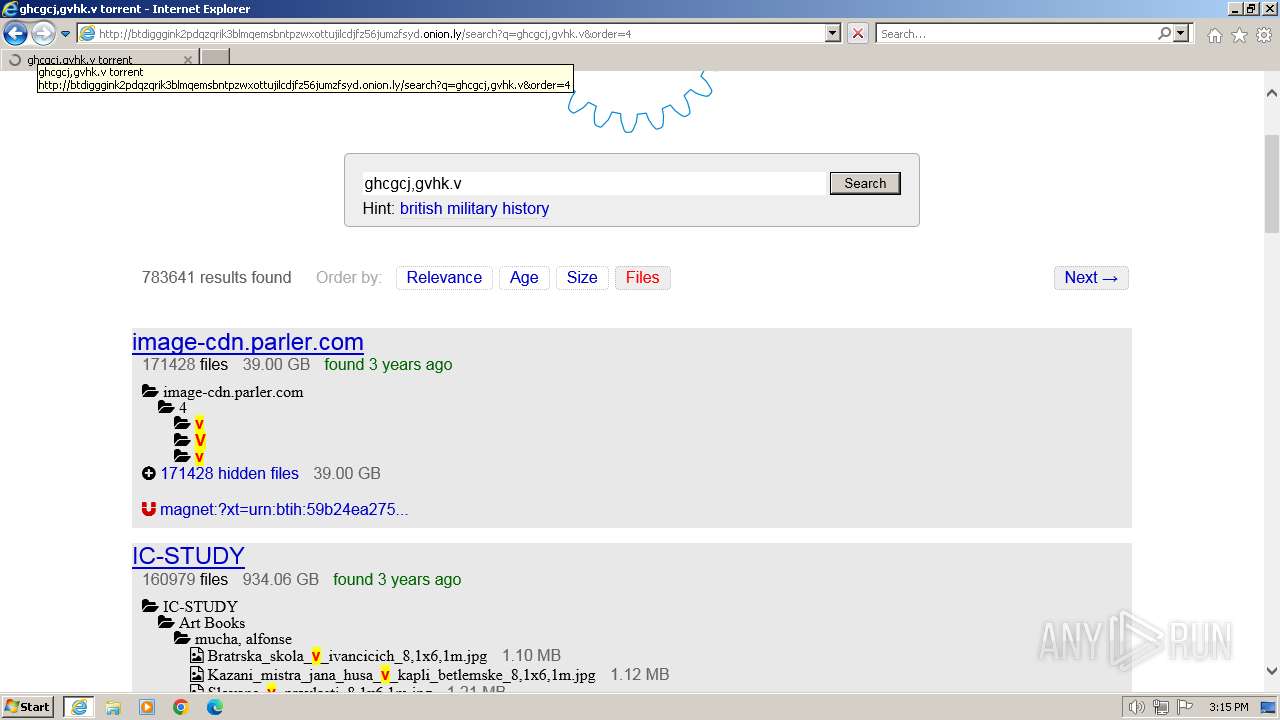
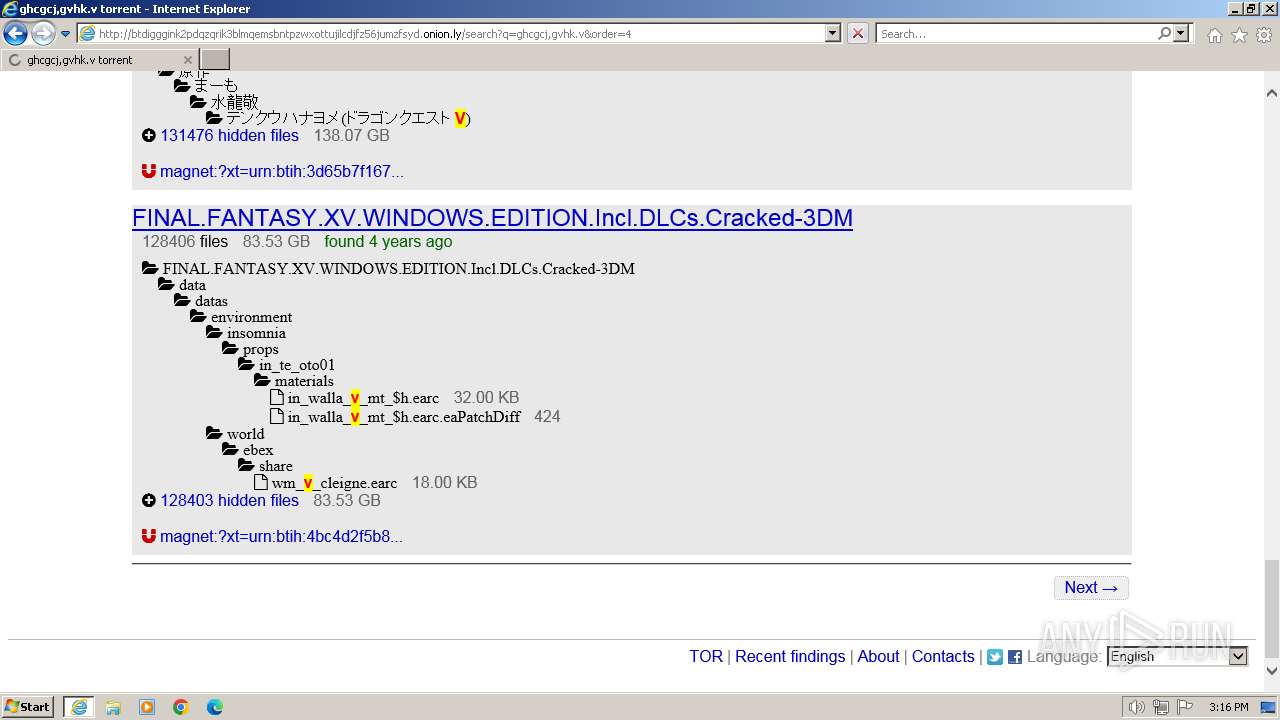
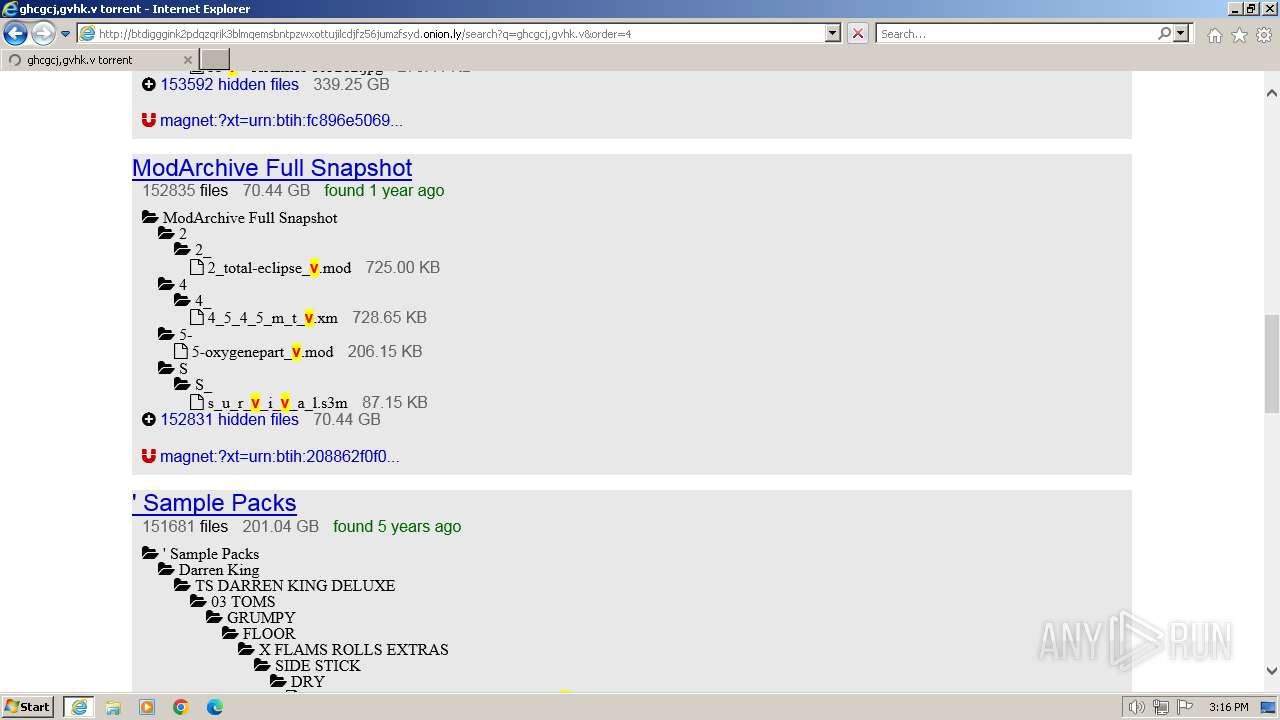
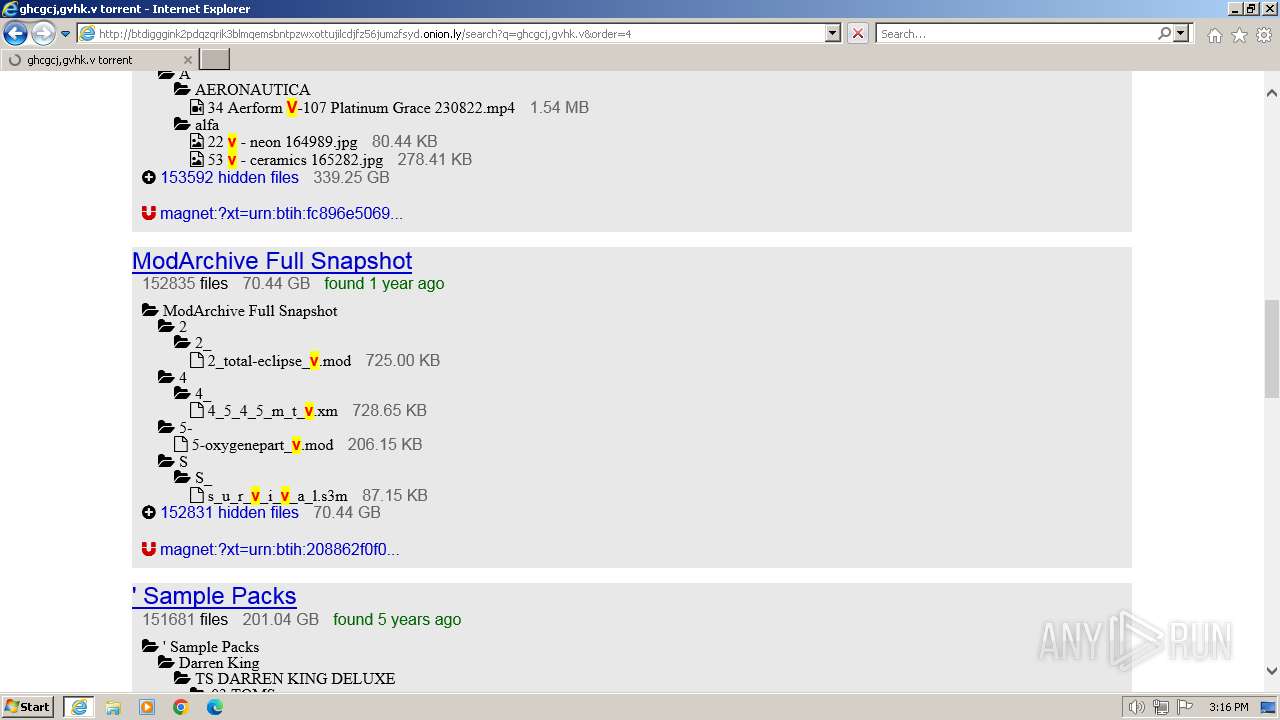
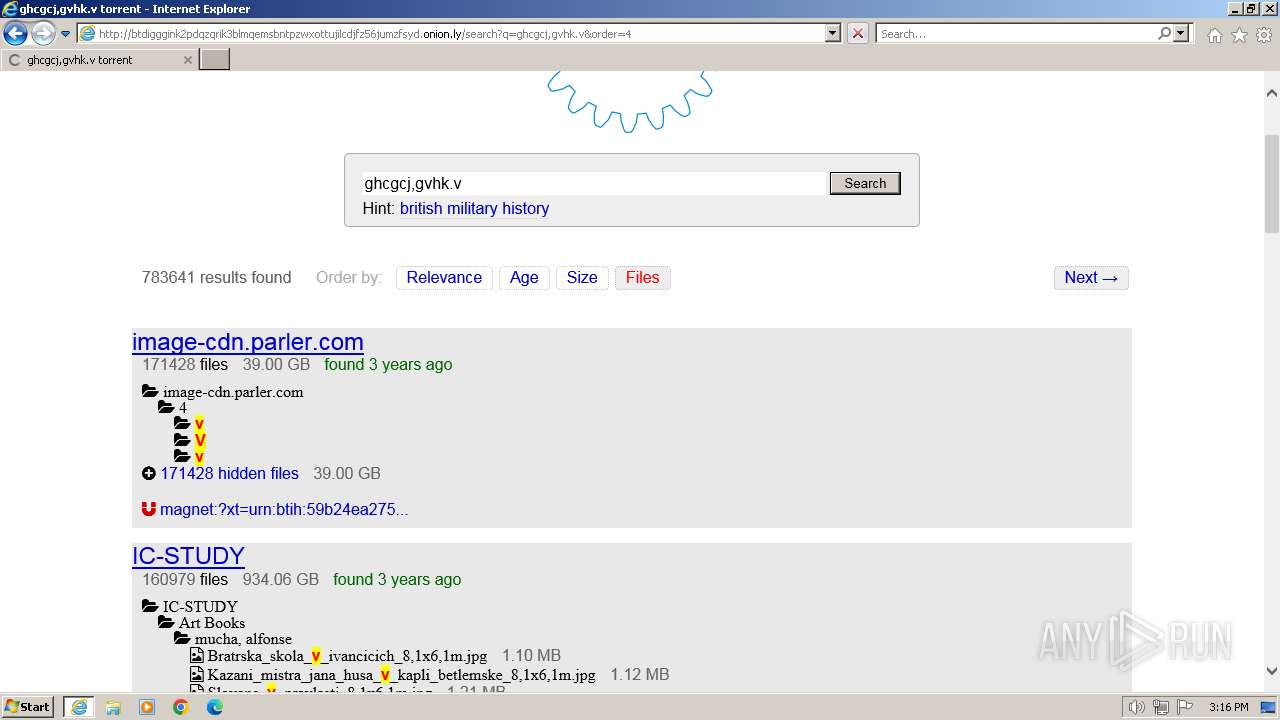
| URL: | btdigggink2pdqzqrik3blmqemsbntpzwxottujilcdjfz56jumzfsyd.onion.ly |
| Full analysis: | https://app.any.run/tasks/03335f7f-cb1b-4e42-aca5-7ffe0c66a5a9 |
| Verdict: | Malicious activity |
| Analysis date: | March 10, 2024, 15:11:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | DC31656C53F03FE2252FD79D1A2DDA56 |
| SHA1: | 624ED1D58D359C2C656F238BBD51F55F690009C2 |
| SHA256: | C2C05F820DCA08CFAA0996C99A0621B6D898061F22629062B17AD7D233B5E6F2 |
| SSDEEP: | 3:sCCC9/eorzSsRQ07rZeS:s09/vHSlMrV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Block-list domains
- iexplore.exe (PID: 2044)
- iexplore.exe (PID: 4052)
INFO
The dropped object may contain a URL to Tor Browser
- iexplore.exe (PID: 4052)
Application launched itself
- iexplore.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2044 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4052 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Internet Explorer\iexplore.exe" "btdigggink2pdqzqrik3blmqemsbntpzwxottujilcdjfz56jumzfsyd.onion.ly" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 592
Read events
22 450
Write events
103
Delete events
39
Modification events
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31093501 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31093501 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
21
Text files
70
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\LRH7LGJH.txt | text | |
MD5:66C936375D64F42149C76D5D907FE09F | SHA256:47918B89B857730370D863A1DC500A874735449106023F18F7D8E5FC4BA2DF6A | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\R8NB17I3.txt | text | |
MD5:A08FFF7A3AA8BBA67547DABF2385C385 | SHA256:EC808090A0ACF42F41E704E42909D9C4AB0AEC09B6313DA25544E386D91DC2A8 | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:A88028032B2F21C56D1EBCF81CD72FEE | SHA256:DEB77E66751B5330F93CC98E697E473EC8BEEB9C19743582C7D0FFC68D3C2D79 | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C6CF8DD4845563DE1BB03046868A0FB6 | SHA256:23BC2A8878559242D256A6A692A173A6559012FC942038FCE25F9DCCFA28B4F6 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\7JONOM7H.htm | html | |
MD5:9E6E5E00A77FE254976E3A33AE86C8E4 | SHA256:E295FB18691AA253C5AB9E48B954E46AE4B2FF0C75EFC634A6C3B95EB00148EE | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:63688761BA516A0CF0E63049694B7146 | SHA256:2D46EDA15EEB7351BE0F8DF6466EE4C3B131A352B19BA99F96BB542606553C51 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\ZCEBBMRK.txt | text | |
MD5:21BBF2FE827574A3A8705A401618B88C | SHA256:84B7EB6EC281C5F484FC34D3A1E33C90B5DA9CA9F222DCB5C08BE092B3E4CD85 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\FC8SQY4S.txt | text | |
MD5:C5354FCA1BA2A506892445913BBA9E99 | SHA256:38AFD7CF9E2ABFBC8EFA90C6A34C1230ECE08B1390E5BE011D0D7A5E7C051A13 | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\IADJPVRX.txt | text | |
MD5:CC745C9DA4FCF68BCE10C2094823ABD1 | SHA256:FE05BBEA1900C5E816CF5DA2B8C435A911A49248B1BF1B06FA5AB5500E22986E | |||
| 2044 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\M3H0U47Y.txt | text | |
MD5:CE92C9C69DCF96279055E84ADC0D0BC2 | SHA256:F9B3A72103A53E74A83065C900D47ACB7273427C6110FB69DE1F2BF3B83CFA7A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
68
DNS requests
20
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4052 | iexplore.exe | GET | 304 | 184.24.77.193:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?18014fff35250a83 | DE | — | — | unknown |
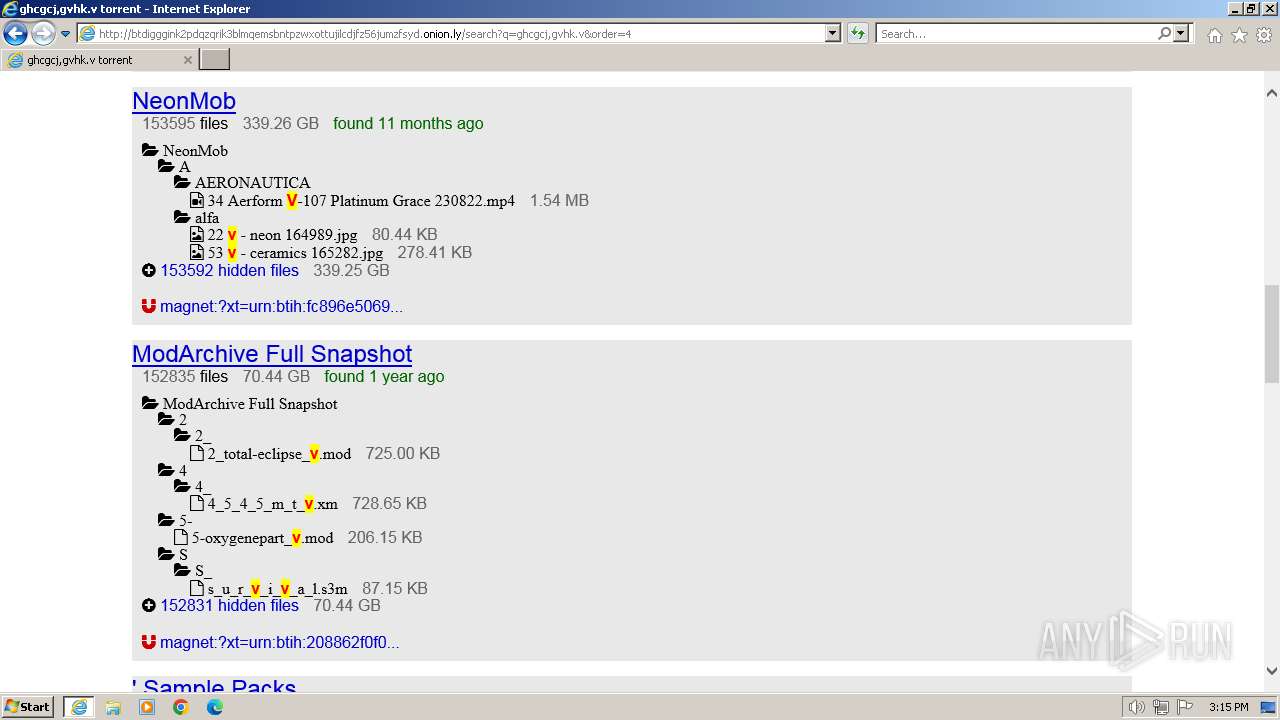
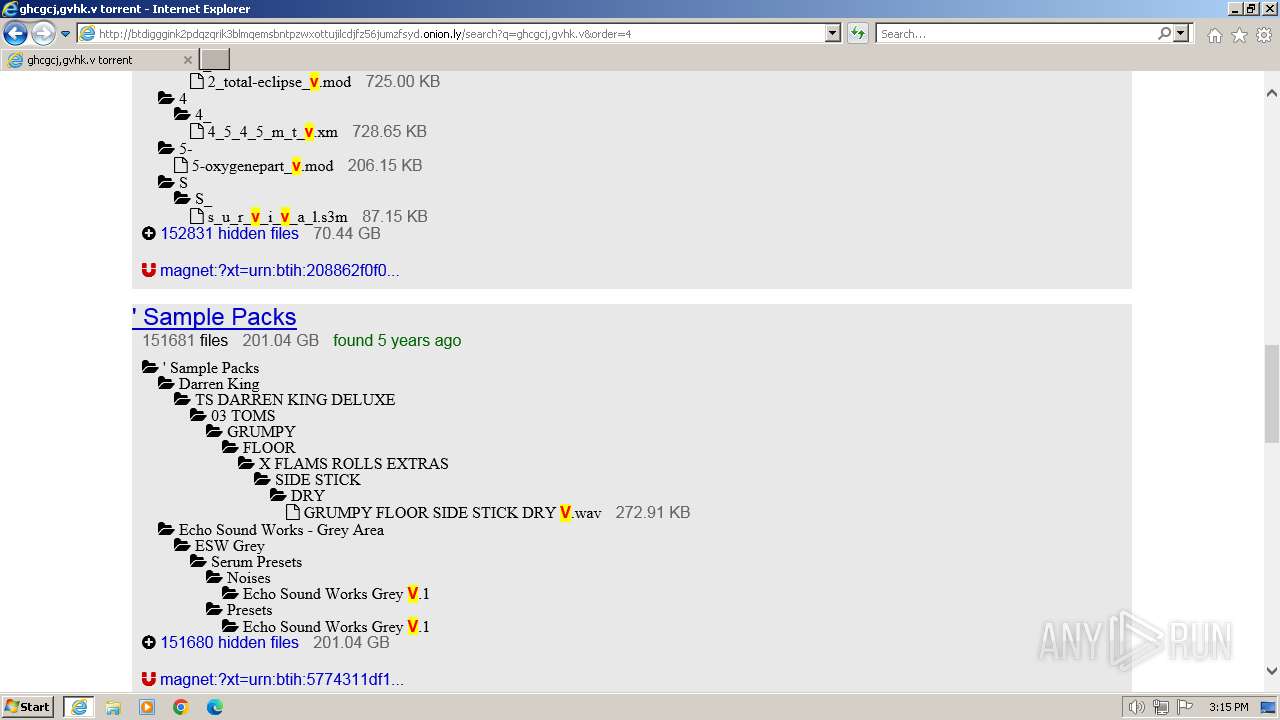
2044 | iexplore.exe | GET | 200 | 209.141.39.59:80 | http://btdigggink2pdqzqrik3blmqemsbntpzwxottujilcdjfz56jumzfsyd.onion.ly/ | US | html | 7.86 Kb | unknown |
4052 | iexplore.exe | GET | 304 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?70b4a85d87201c80 | DE | — | — | unknown |
4052 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | US | binary | 312 b | unknown |
2044 | iexplore.exe | GET | 200 | 209.141.39.59:80 | http://btdigggink2pdqzqrik3blmqemsbntpzwxottujilcdjfz56jumzfsyd.onion.ly/ajax/libs/font-awesome/4.7.0/css/font-awesome.css | US | text | 37.0 Kb | unknown |
2044 | iexplore.exe | GET | 200 | 209.141.39.59:80 | http://btdigggink2pdqzqrik3blmqemsbntpzwxottujilcdjfz56jumzfsyd.onion.ly/68747470733a2f2f73332e616d617a6f6e6177732e636f6d2f6769746875622f726962626f6e732f666f726b6d655f72696768745f7265645f6161303030302e706e67.png | US | image | 7.74 Kb | unknown |
2044 | iexplore.exe | GET | — | 209.141.39.59:80 | http://btdigggink2pdqzqrik3blmqemsbntpzwxottujilcdjfz56jumzfsyd.onion.ly/ajax/libs/font-awesome/4.7.0/fonts/fontawesome-webfont.eot? | US | — | — | unknown |
2044 | iexplore.exe | GET | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMg6MjhxJZrunSIw9UL3O8%2BzA%3D%3D | DE | binary | 503 b | unknown |
2044 | iexplore.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | DE | binary | 717 b | unknown |
4052 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2044 | iexplore.exe | 209.141.39.59:80 | btdigggink2pdqzqrik3blmqemsbntpzwxottujilcdjfz56jumzfsyd.onion.ly | PONYNET | US | unknown |
4052 | iexplore.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4052 | iexplore.exe | 184.24.77.193:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4052 | iexplore.exe | 184.24.77.187:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4052 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2044 | iexplore.exe | 104.20.66.115:80 | s10.histats.com | CLOUDFLARENET | — | unknown |
2044 | iexplore.exe | 54.39.128.117:443 | s4.histats.com | OVH SAS | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
btdigggink2pdqzqrik3blmqemsbntpzwxottujilcdjfz56jumzfsyd.onion.ly |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
s10.histats.com |
| whitelisted |
s4.histats.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to .onion proxy Domain (onion . ly) |
2044 | iexplore.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Tor2Web Host Proxy HTTP Request (.onion.) |
4052 | iexplore.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Tor2Web Host Proxy HTTP Request (.onion.) |
4052 | iexplore.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Tor2Web Host Proxy HTTP Request (.onion.) |