| File name: | ism-2.7.4 MC-1.15.1_3fd317a5.exe |
| Full analysis: | https://app.any.run/tasks/db761eea-bb8e-45d7-bbaa-fd5b44c9303e |
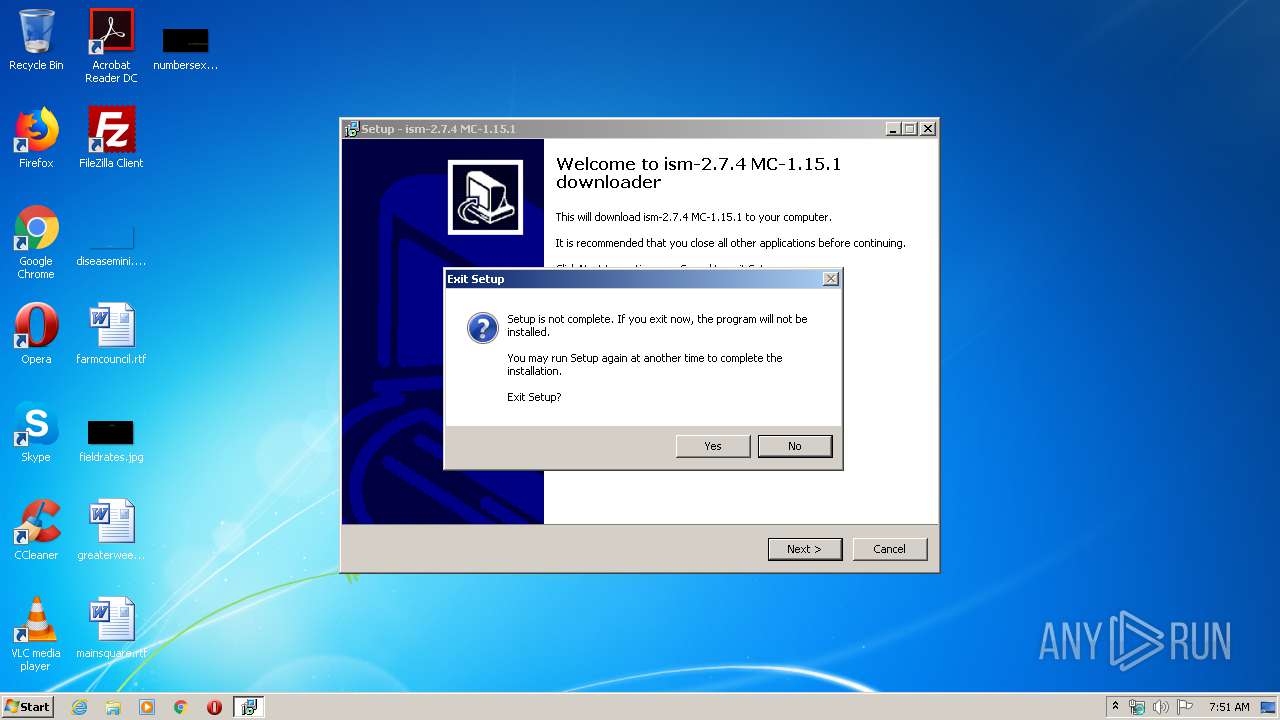
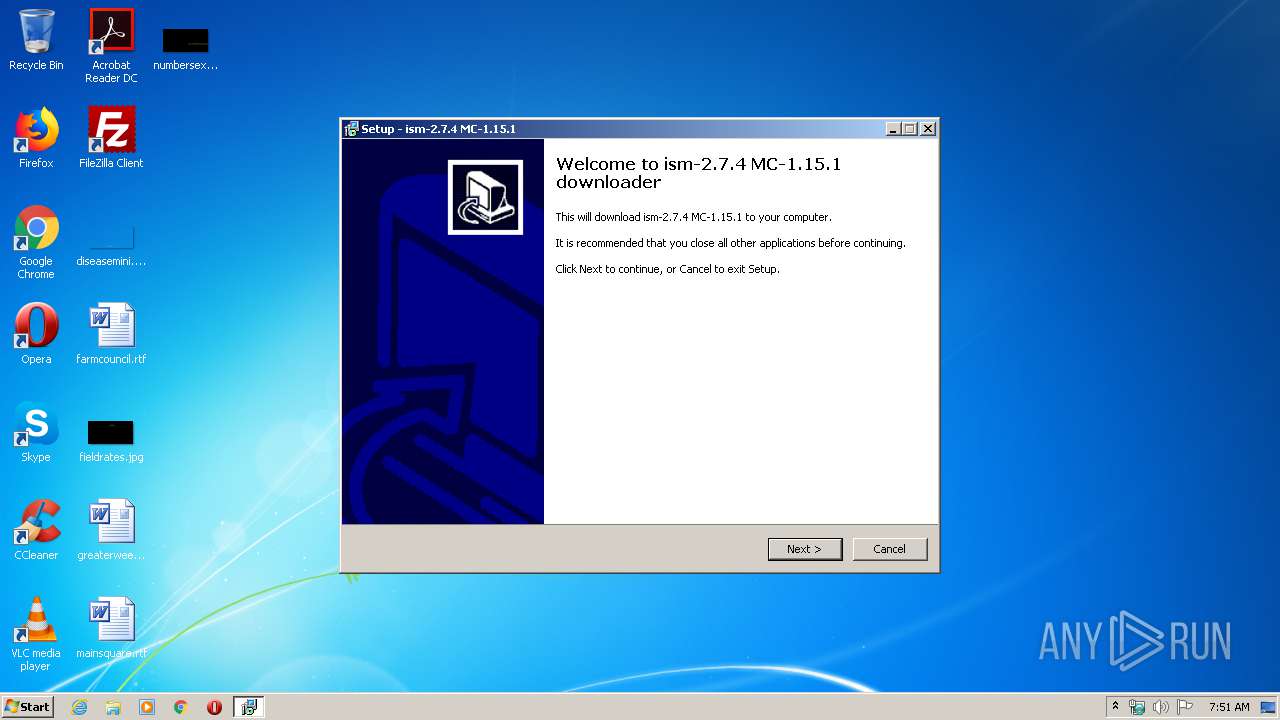
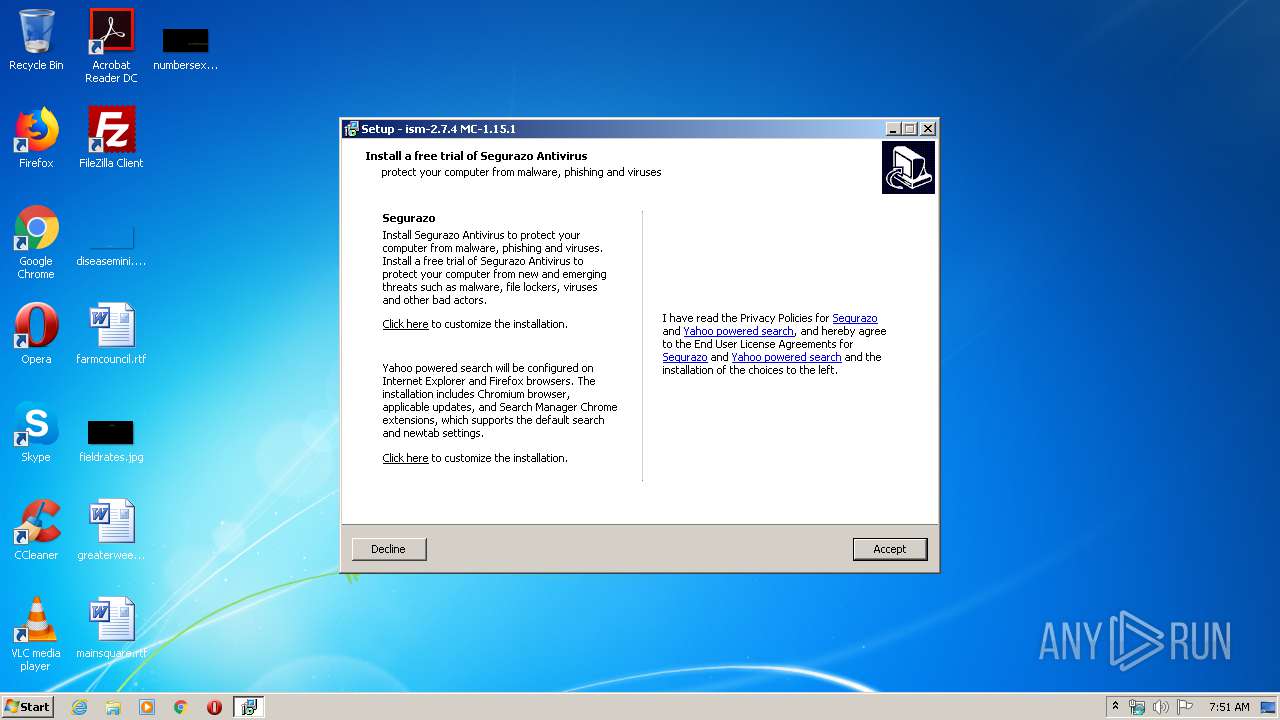
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 06:50:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 84BCE0194CBD1013E105DA7BE1579067 |
| SHA1: | 3CF715FE75D779285ABEA019414F27DE650ABF4E |
| SHA256: | C29322498C4C298BF01273019DD0EAC068886AA59F5F6C14293B8514233B6568 |
| SSDEEP: | 24576:LTfEsP85DgJrivY05+Qao/qKIcI7lWfZeik+wsud343HWAgjnEuIzSG:XcsQ6QleBIgs9udI3WA2n5fG |
MALICIOUS
Changes settings of System certificates
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
SUSPICIOUS
Executable content was dropped or overwritten
- ism-2.7.4 MC-1.15.1_3fd317a5.exe (PID: 3440)
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
- ism-2.7.4 MC-1.15.1_3fd317a5.exe (PID: 2068)
Reads the Windows organization settings
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
Reads the machine GUID from the registry
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
Reads Internet Cache Settings
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
Creates files in the user directory
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
Reads Windows owner or organization settings
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
Adds / modifies Windows certificates
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
INFO
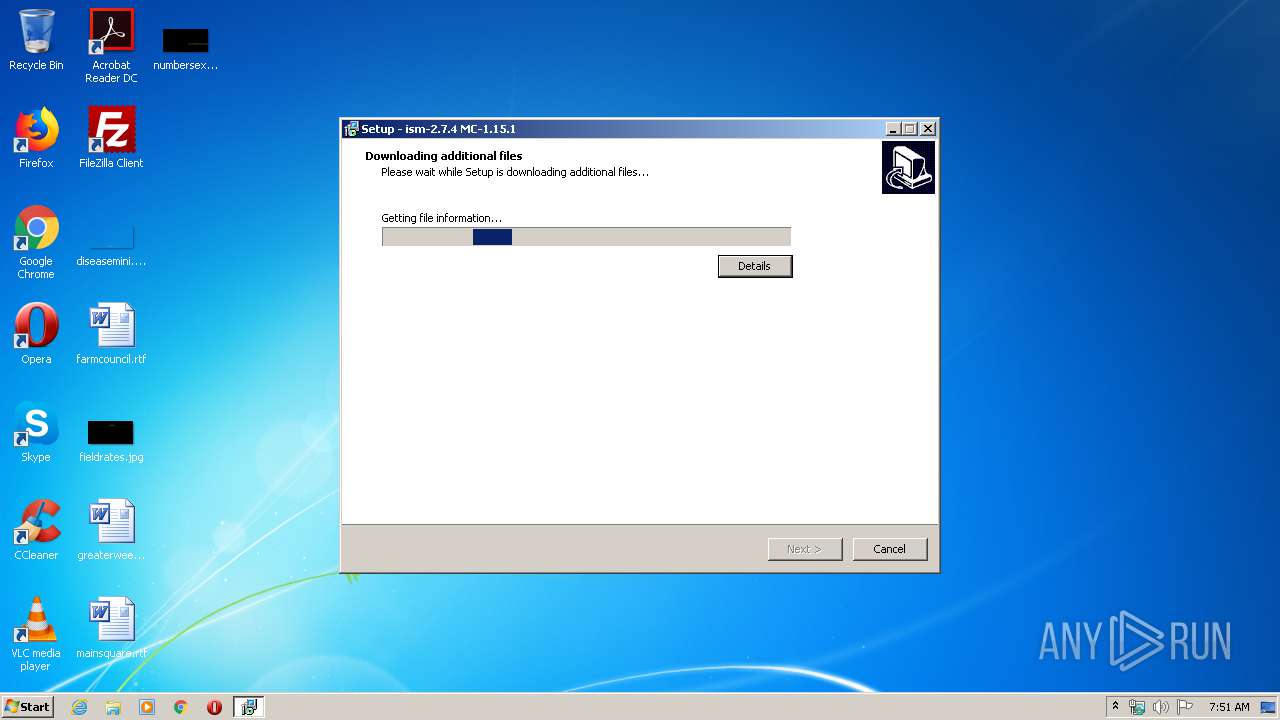
Application was dropped or rewritten from another process
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2756)
Loads dropped or rewritten executable
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
Creates files in the program directory
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
Reads settings of System Certificates
- ism-2.7.4 MC-1.15.1_3fd317a5.tmp (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:12 13:15:57+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 37888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | |
| ProductVersion: | 1.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Oct-2019 11:15:57 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 12-Oct-2019 11:15:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A50E8 | 0x000A5200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36928 |
.itext | 0x000A7000 | 0x00001668 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95181 |
.data | 0x000A9000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.03517 |
.bss | 0x000AD000 | 0x00006778 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000B4000 | 0x00000F1C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.79161 |
.didata | 0x000B5000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74582 |
.edata | 0x000B6000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.88107 |
.tls | 0x000B7000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000B8000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.37999 |
.rsrc | 0x000B9000 | 0x00004600 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.42483 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4086 | 3.16547 | 864 | UNKNOWN | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | UNKNOWN | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | UNKNOWN | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000B063C |
__dbk_fcall_wrapper | 2 | 0x0000D3DC |
TMethodImplementationIntercept | 3 | 0x00053AC0 |
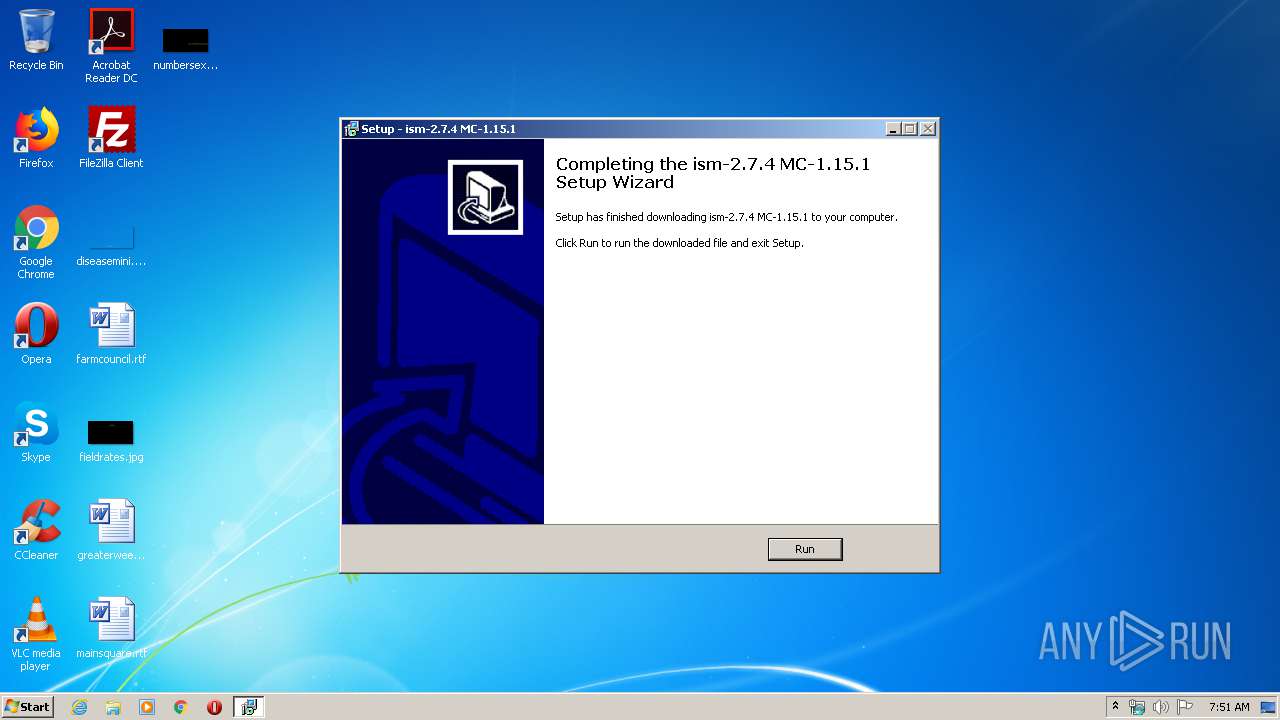
Total processes
39
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2068 | "C:\Users\admin\AppData\Local\Temp\ism-2.7.4 MC-1.15.1_3fd317a5.exe" /SPAWNWND=$601CA /NOTIFYWND=$90140 | C:\Users\admin\AppData\Local\Temp\ism-2.7.4 MC-1.15.1_3fd317a5.exe | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 0 Version: Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\AppData\Local\Temp\is-30UV7.tmp\ism-2.7.4 MC-1.15.1_3fd317a5.tmp" /SL5="$90150,870224,721408,C:\Users\admin\AppData\Local\Temp\ism-2.7.4 MC-1.15.1_3fd317a5.exe" /SPAWNWND=$601CA /NOTIFYWND=$90140 | C:\Users\admin\AppData\Local\Temp\is-30UV7.tmp\ism-2.7.4 MC-1.15.1_3fd317a5.tmp | ism-2.7.4 MC-1.15.1_3fd317a5.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2756 | "C:\Users\admin\AppData\Local\Temp\is-C6H8B.tmp\ism-2.7.4 MC-1.15.1_3fd317a5.tmp" /SL5="$90140,870224,721408,C:\Users\admin\AppData\Local\Temp\ism-2.7.4 MC-1.15.1_3fd317a5.exe" | C:\Users\admin\AppData\Local\Temp\is-C6H8B.tmp\ism-2.7.4 MC-1.15.1_3fd317a5.tmp | — | ism-2.7.4 MC-1.15.1_3fd317a5.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3440 | "C:\Users\admin\AppData\Local\Temp\ism-2.7.4 MC-1.15.1_3fd317a5.exe" | C:\Users\admin\AppData\Local\Temp\ism-2.7.4 MC-1.15.1_3fd317a5.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Exit code: 0 Version: Modules
| |||||||||||||||
Total events
1 645
Read events
444
Write events
1 197
Delete events
4
Modification events
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: A40A0000FCC4B7BB2807D601 | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 2CE9F1F423977051EE5C46242AC189BDFC2D082E556FEC1077488D86A8D581FC | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2724) ism-2.7.4 MC-1.15.1_3fd317a5.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
4
Suspicious files
4
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\Local\Temp\CabF286.tmp | — | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\Local\Temp\TarF297.tmp | — | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\Local\Temp\is-UHABM.tmp\SEG_default.rtf | text | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\KKW686VR.txt | text | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\Local\Temp\is-UHABM.tmp\ClickHere_default.rtf | text | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\Local\Temp\is-UHABM.tmp\woy.dll | executable | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Program Files\Common Files\ism-2.7.4 MC-1.15.1.jar | compressed | |
MD5:— | SHA256:— | |||
| 2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | C:\Users\admin\AppData\Local\Temp\is-UHABM.tmp\ism-2.7.4 MC-1.15.1.jar | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
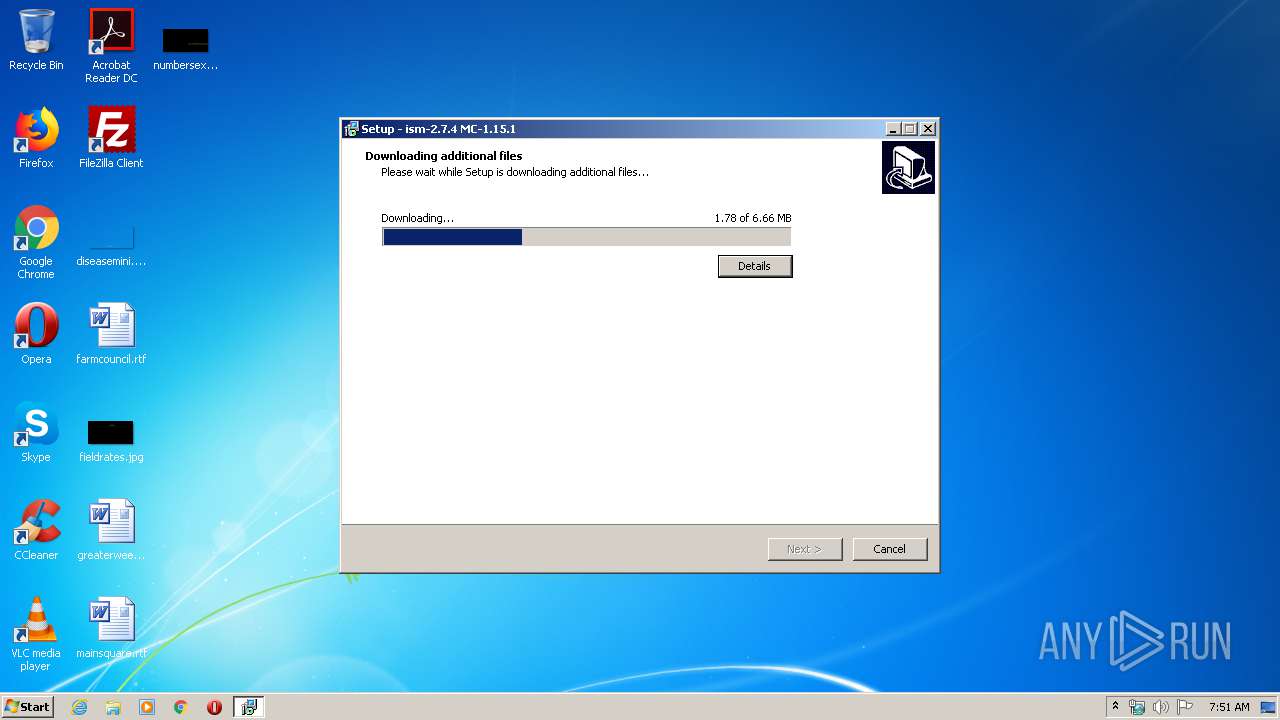
HTTP(S) requests
5
TCP/UDP connections
6
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | POST | 200 | 52.89.214.102:80 | http://test1.cedewugacmewonn.com/ | US | text | 721 b | unknown |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | GET | 200 | 143.204.98.146:80 | http://d356p1qym36an6.cloudfront.net/offers.json | US | text | 36 b | whitelisted |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | POST | 200 | 3.224.15.132:80 | http://rpt.seg-reports.com/ | US | text | 15 b | suspicious |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | POST | 200 | 3.224.15.132:80 | http://rpt.seg-reports.com/ | US | text | 15 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | 52.89.214.102:80 | test1.cedewugacmewonn.com | Amazon.com, Inc. | US | unknown |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | 3.93.104.160:80 | rpt.seg-reports.com | — | US | unknown |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | 3.224.15.132:80 | rpt.seg-reports.com | — | US | unknown |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | 143.204.98.146:80 | d356p1qym36an6.cloudfront.net | — | US | unknown |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | 104.18.46.207:443 | minecraft-mod.pw | Cloudflare Inc | US | unknown |
2724 | ism-2.7.4 MC-1.15.1_3fd317a5.tmp | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
test1.cedewugacmewonn.com |
| unknown |
rpt.seg-reports.com |
| suspicious |
dns.msftncsi.com |
| shared |
d356p1qym36an6.cloudfront.net |
| whitelisted |
minecraft-mod.pw |
| suspicious |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |