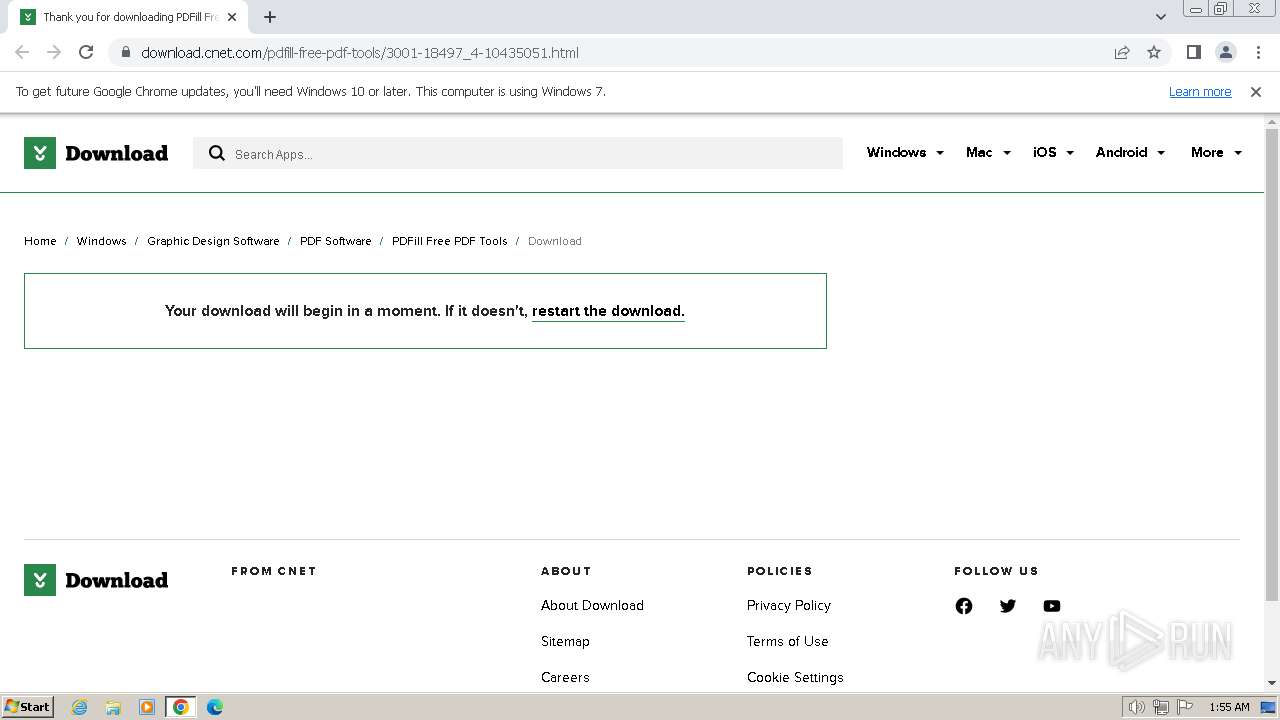
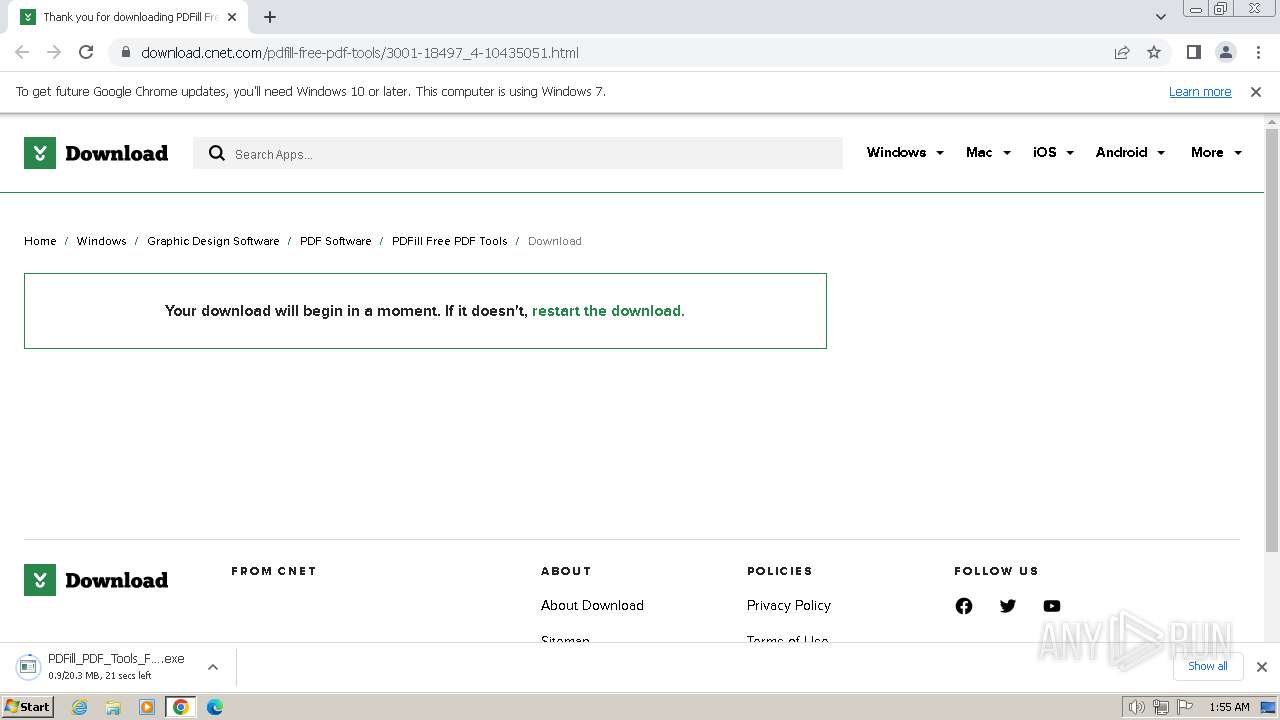
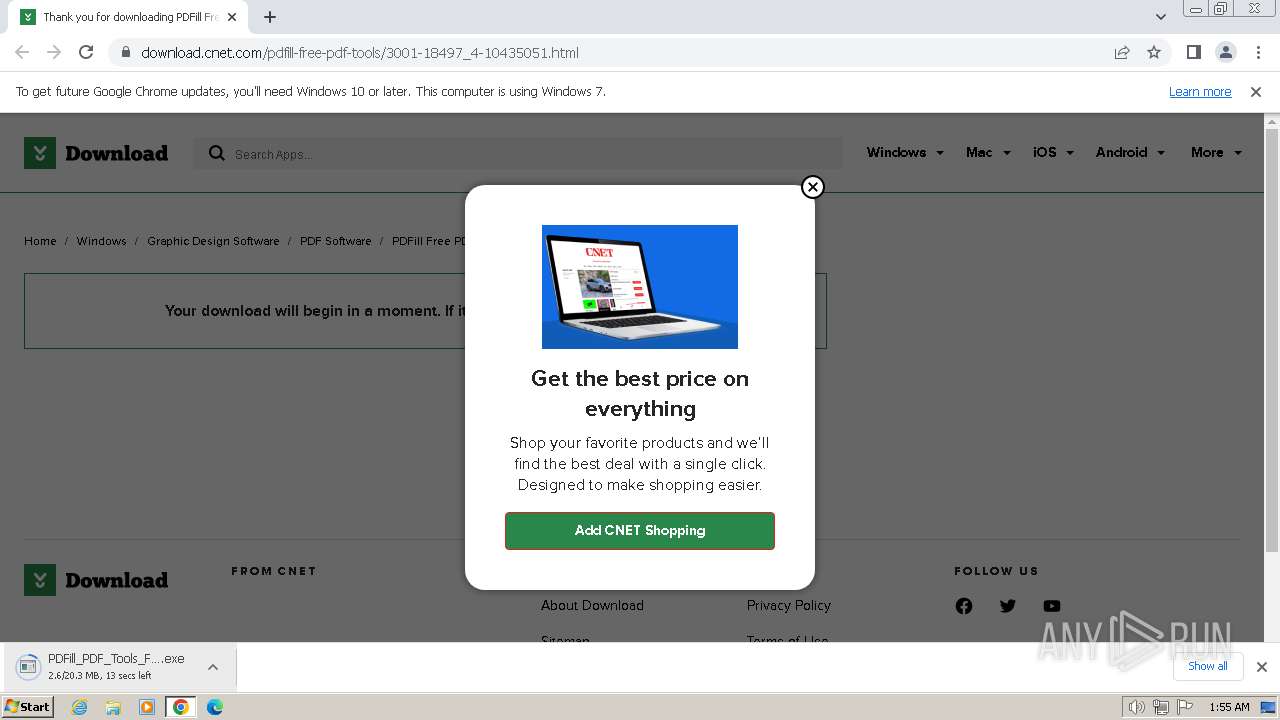
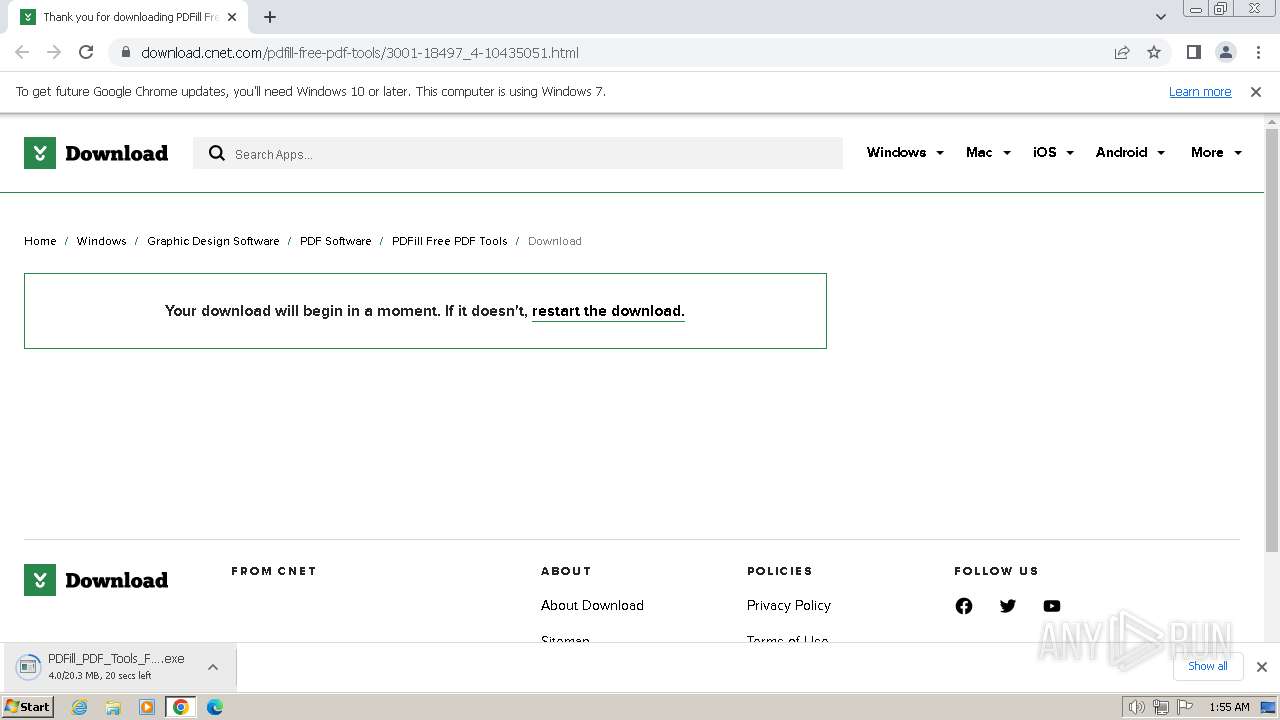
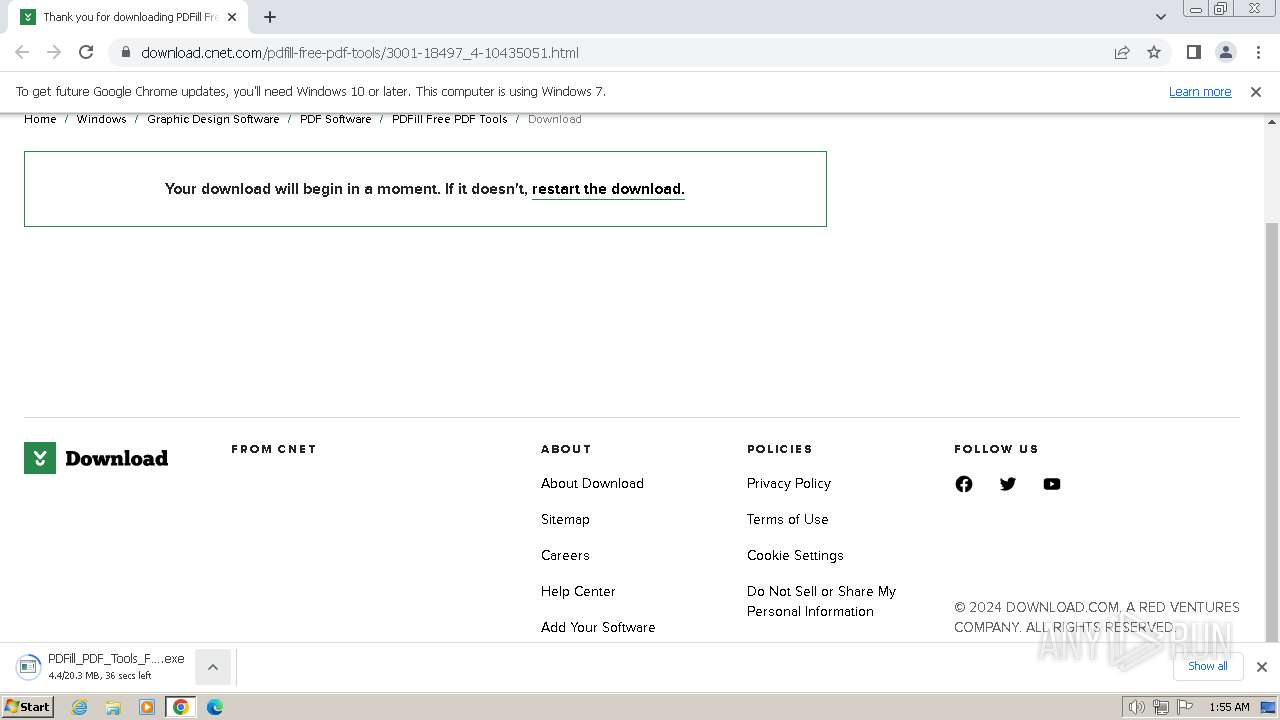
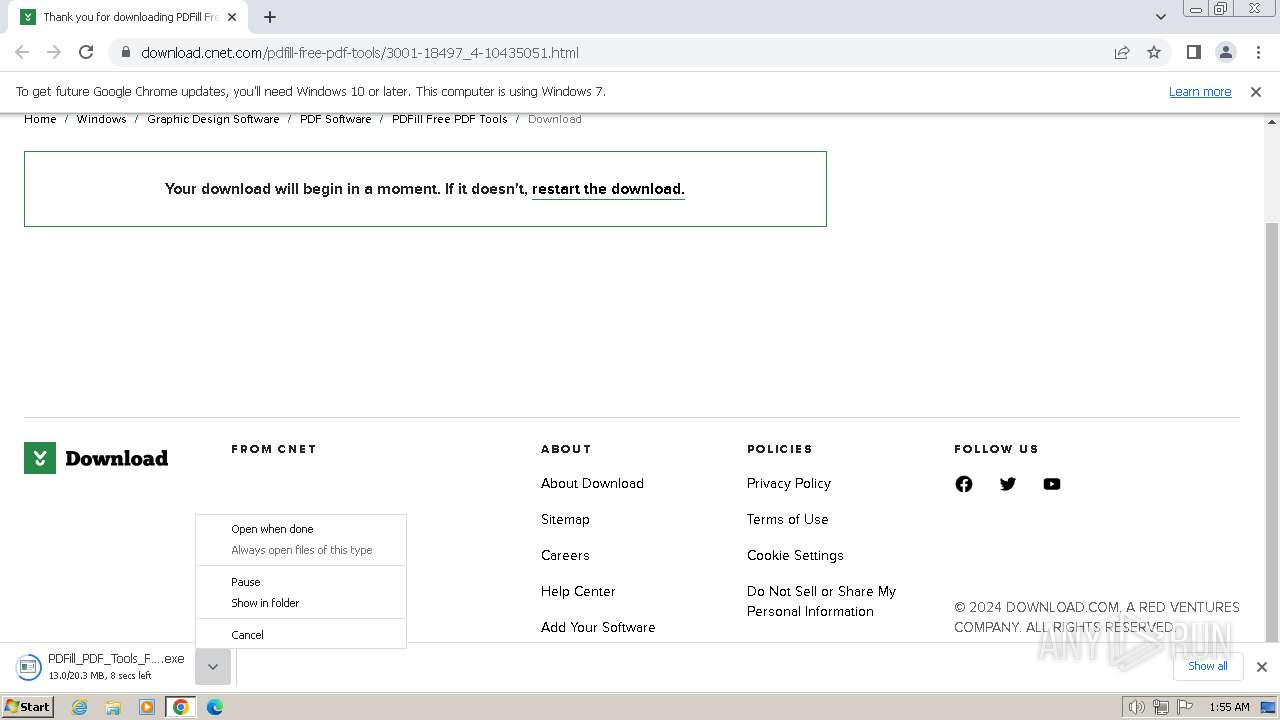
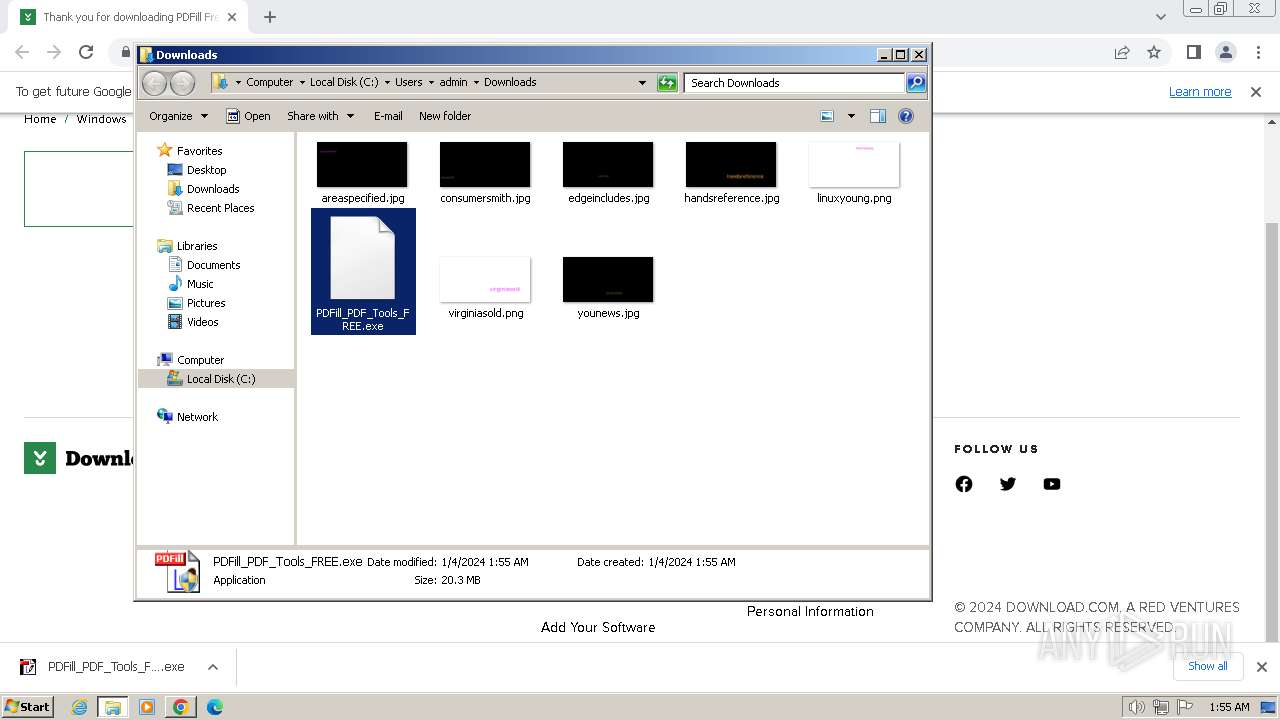
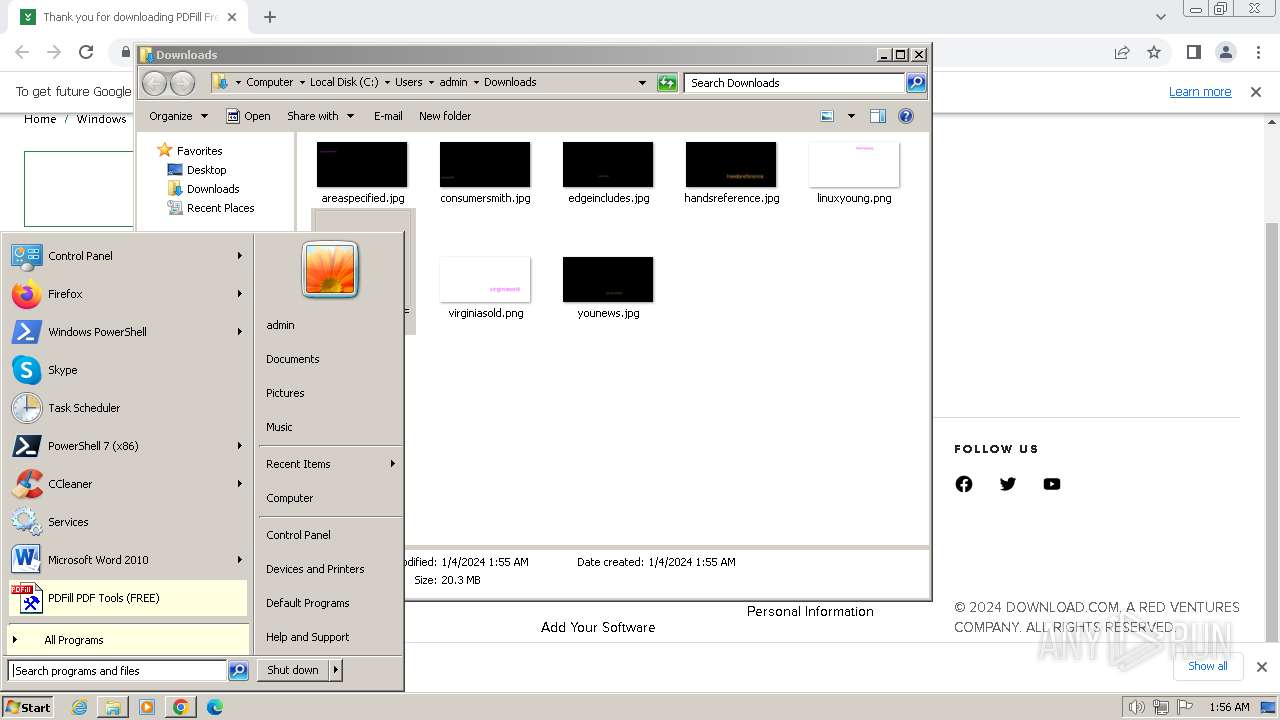
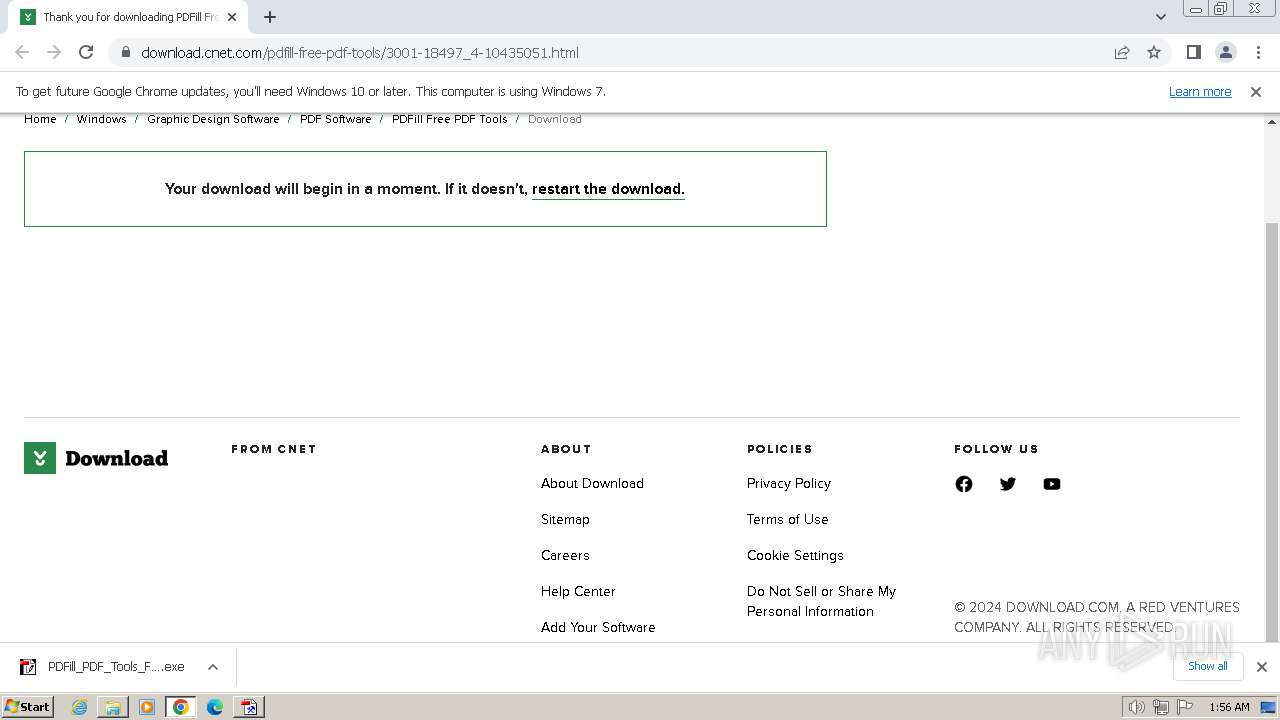
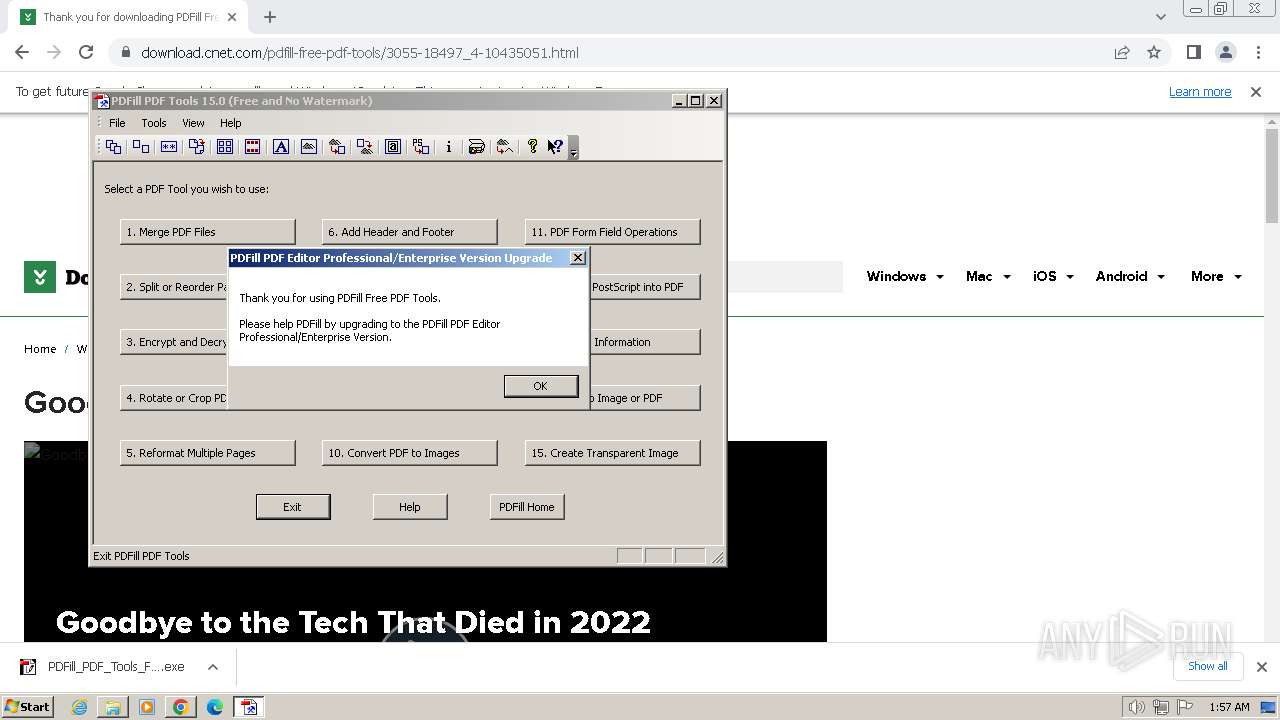
| URL: | https://download.cnet.com/pdfill-free-pdf-tools/3001-18497_4-10435051.html |
| Full analysis: | https://app.any.run/tasks/37a28150-3779-4364-b097-44c2b1feca09 |
| Verdict: | Malicious activity |
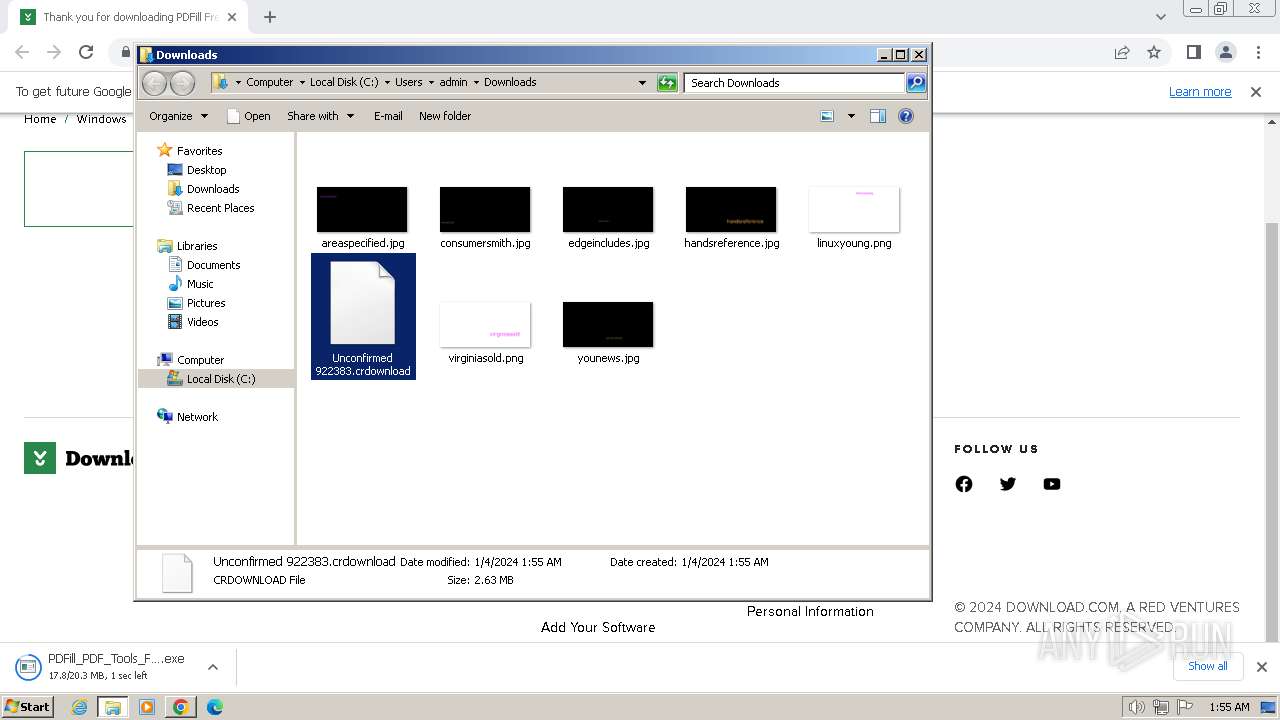
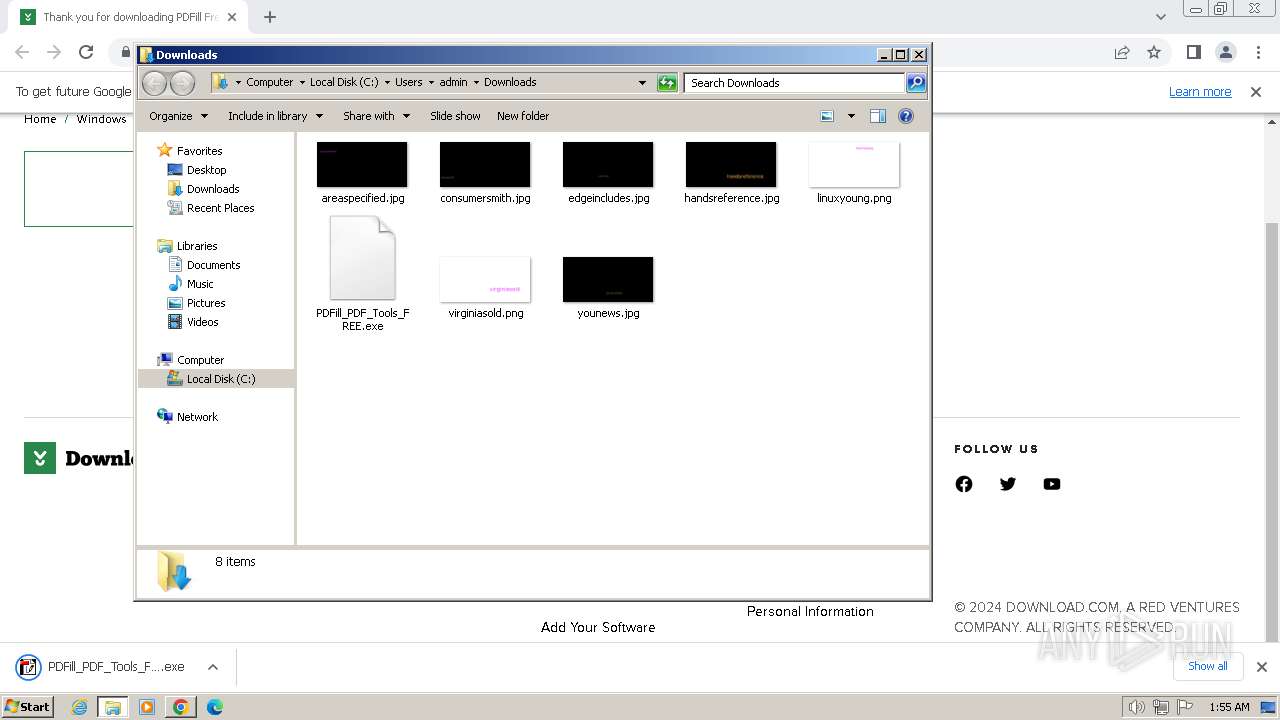
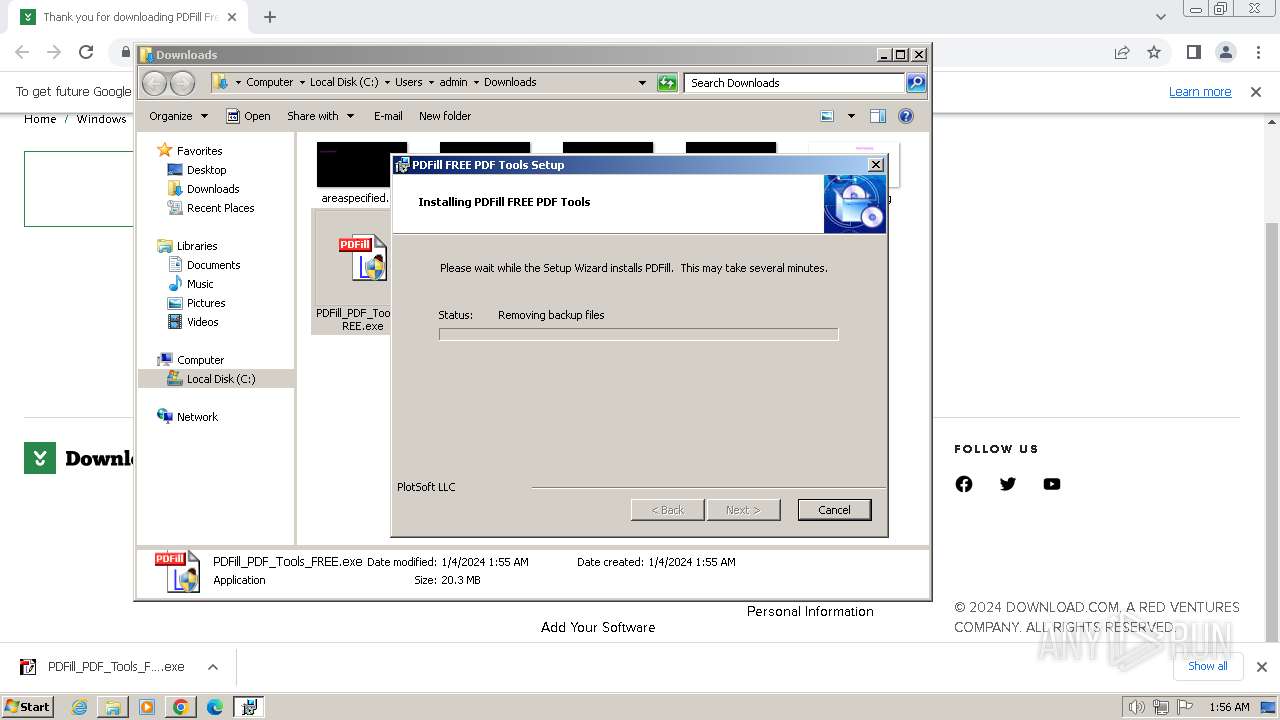
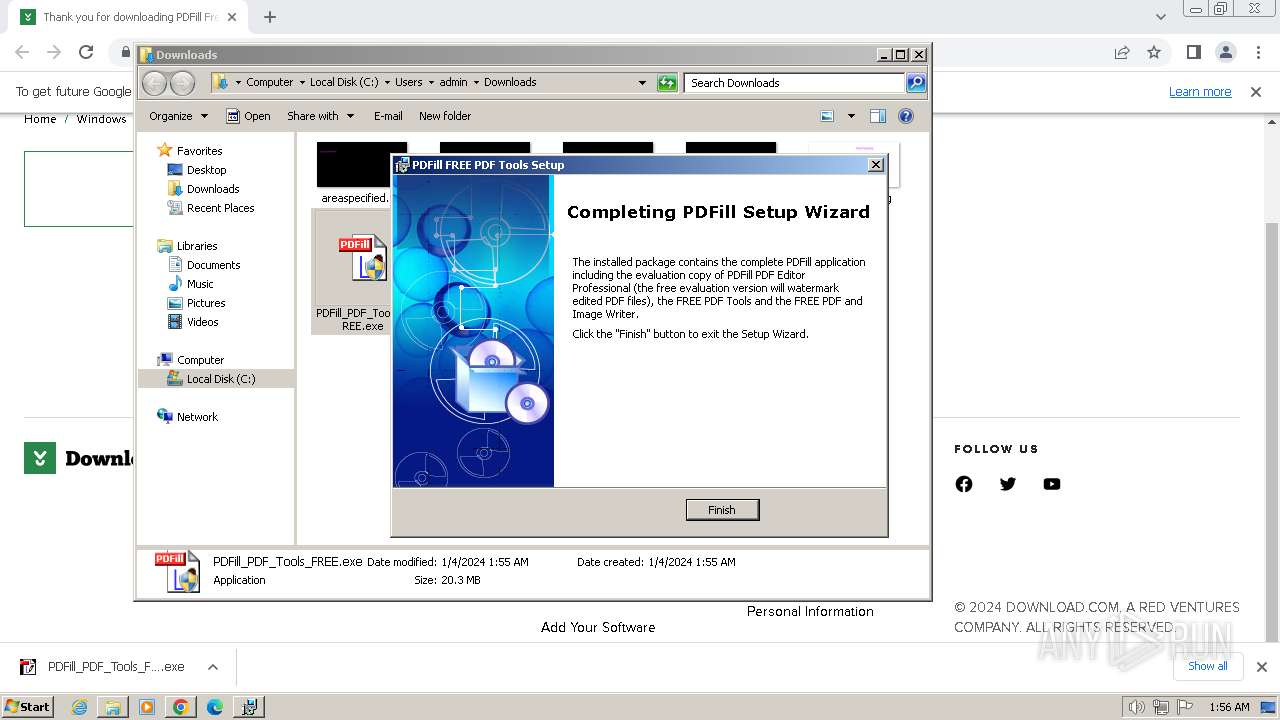
| Analysis date: | January 04, 2024, 01:55:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AB8859E4BD027842F886CF8AB150904D |
| SHA1: | 1C64F22B9CA73F36A3FC639D4D76C42E84BB0B89 |
| SHA256: | C290B648E60AA61ABA87E4B389141739E34BFB0FB2A19894239C05CCD9D91BB4 |
| SSDEEP: | 3:N8SElbKuQoLmUJWKWVVUpH67w1SNR0n:2SKmKRJWKWVVUpHY0 |
MALICIOUS
Creates a writable file in the system directory
- msiexec.exe (PID: 2772)
- DownloadComponents.exe (PID: 2776)
SUSPICIOUS
Adds/modifies Windows certificates
- msiexec.exe (PID: 3328)
- DownloadComponents.exe (PID: 2776)
Checks Windows Trust Settings
- msiexec.exe (PID: 2772)
- DownloadComponents.exe (PID: 2776)
The process creates files with name similar to system file names
- msiexec.exe (PID: 2772)
Executing commands from a ".bat" file
- msiexec.exe (PID: 2940)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 2940)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 584)
- cmd.exe (PID: 3128)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 1408)
- cmd.exe (PID: 3096)
Reads the Internet Settings
- msiexec.exe (PID: 3388)
- PDFill_PDF_Tools.exe (PID: 2336)
INFO
Checks supported languages
- PDFill_PDF_Tools_FREE.exe (PID: 3276)
- msiexec.exe (PID: 2772)
- msiexec.exe (PID: 3388)
- msiexec.exe (PID: 116)
- msiexec.exe (PID: 2940)
- DownloadComponents.exe (PID: 2776)
- PDFillZip.exe (PID: 2492)
- DownloadComponents.exe (PID: 1696)
- PDFill_PDF_Tools.exe (PID: 2336)
Reads the computer name
- PDFill_PDF_Tools_FREE.exe (PID: 3276)
- msiexec.exe (PID: 2772)
- msiexec.exe (PID: 3388)
- msiexec.exe (PID: 116)
- msiexec.exe (PID: 2940)
- DownloadComponents.exe (PID: 2776)
- PDFill_PDF_Tools.exe (PID: 2336)
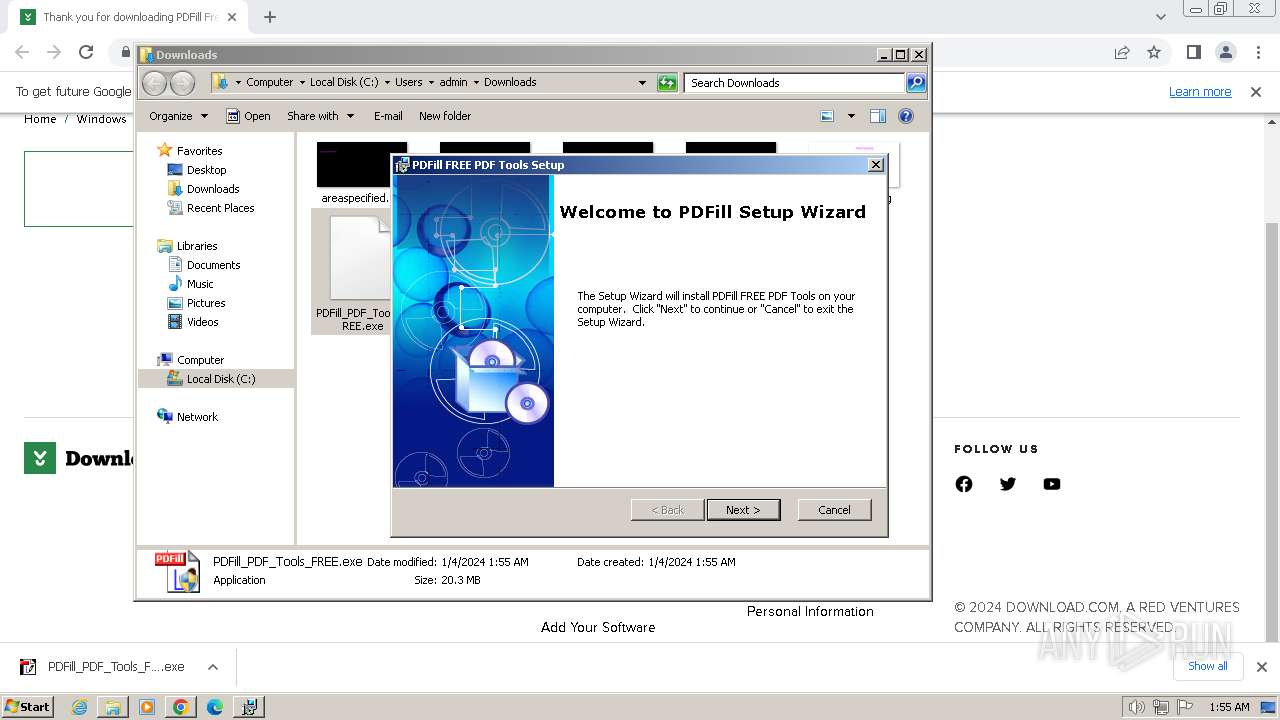
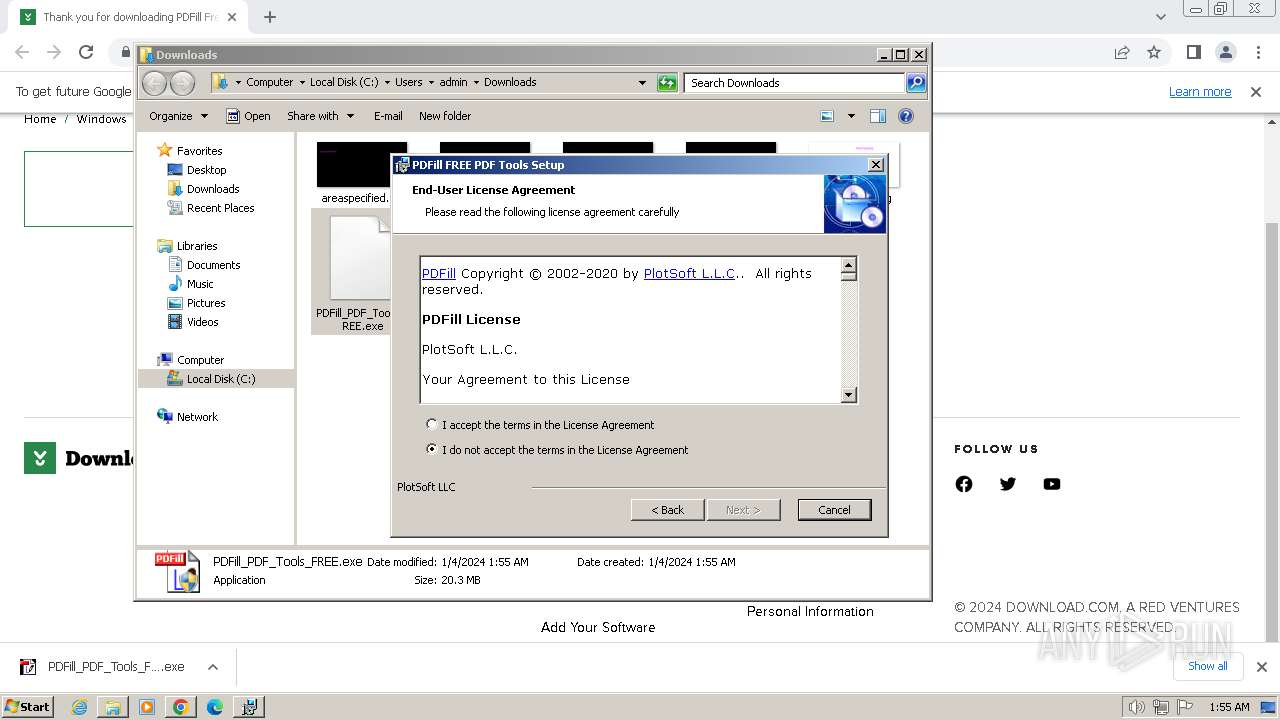
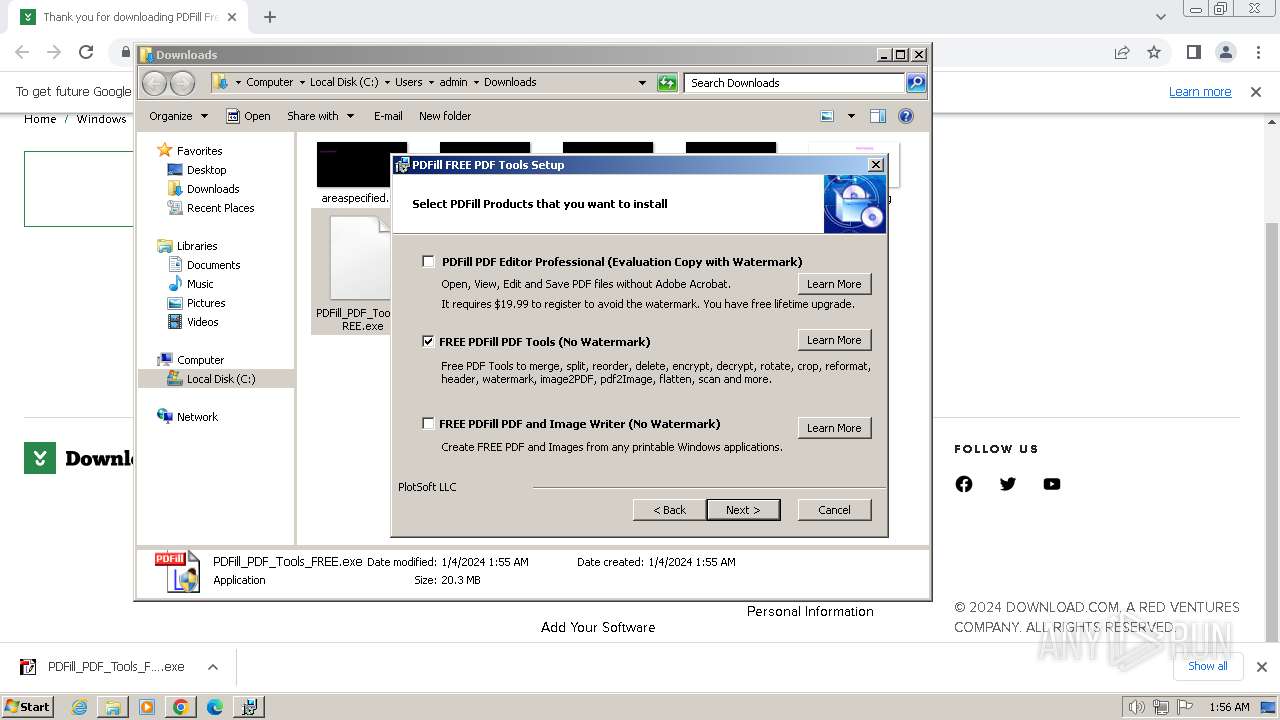
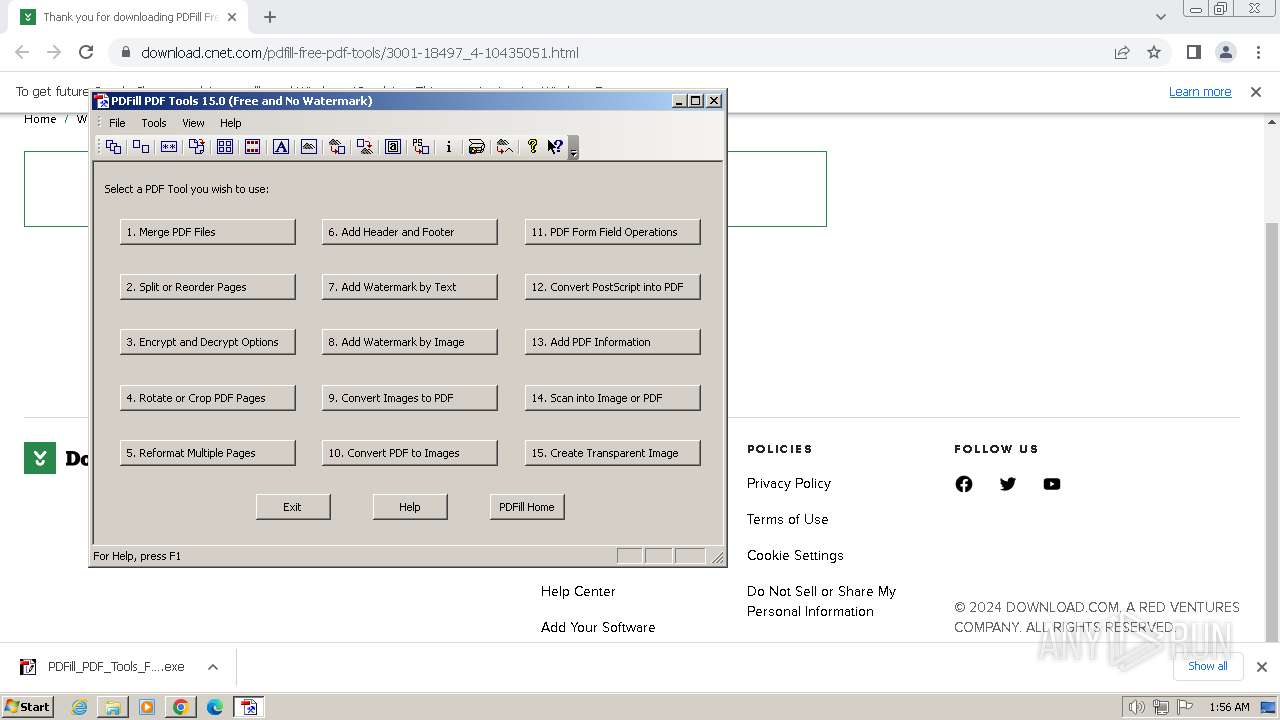
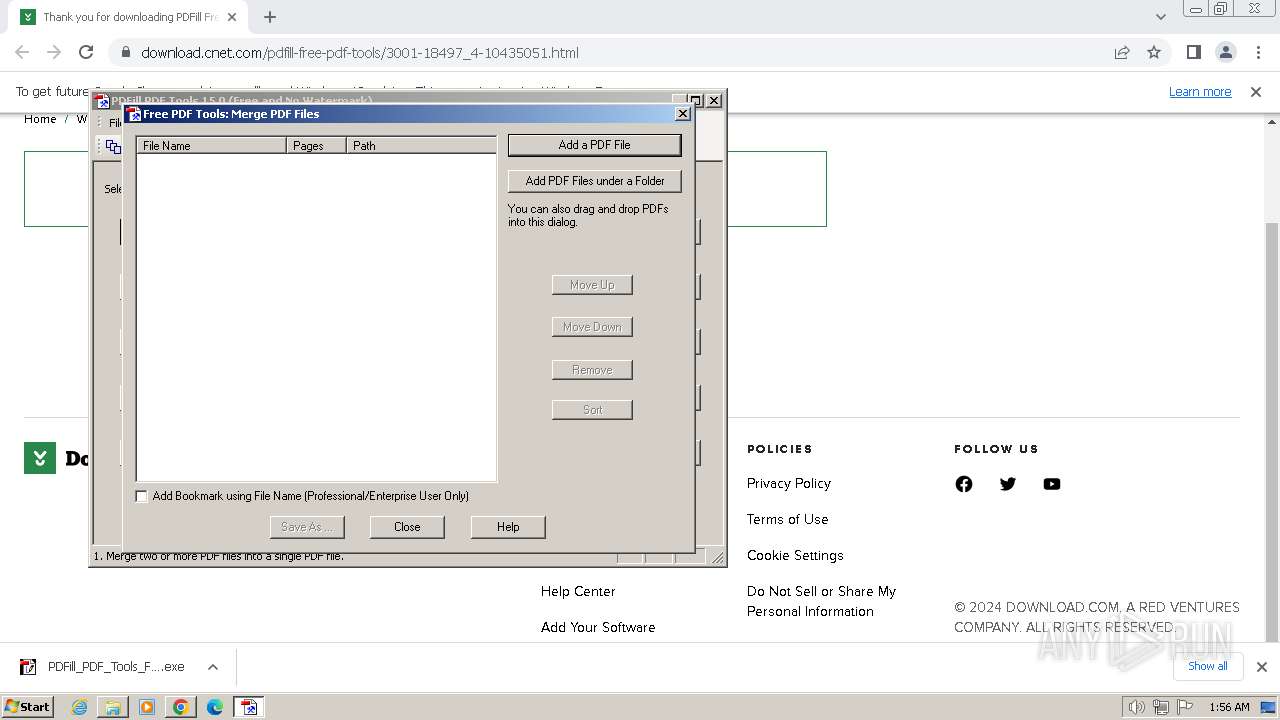
Manual execution by a user
- PDFill_PDF_Tools_FREE.exe (PID: 2460)
- PDFill_PDF_Tools_FREE.exe (PID: 3276)
- PDFill_PDF_Tools.exe (PID: 2336)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3328)
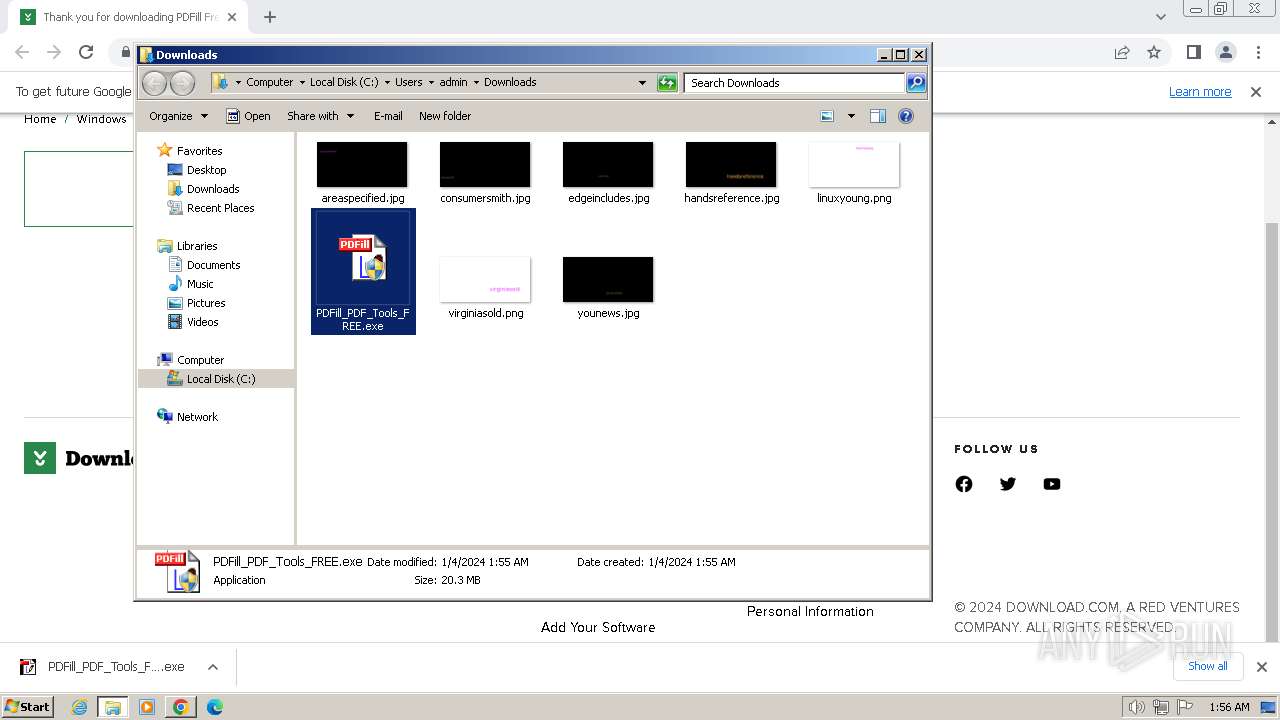
Drops the executable file immediately after the start
- chrome.exe (PID: 124)
- PDFill_PDF_Tools_FREE.exe (PID: 3276)
- msiexec.exe (PID: 3328)
- msiexec.exe (PID: 2772)
- PDFillZip.exe (PID: 2492)
- chrome.exe (PID: 2968)
Reads the machine GUID from the registry
- msiexec.exe (PID: 2772)
- msiexec.exe (PID: 3388)
- msiexec.exe (PID: 116)
- msiexec.exe (PID: 2940)
- DownloadComponents.exe (PID: 2776)
- PDFill_PDF_Tools.exe (PID: 2336)
The process uses the downloaded file
- chrome.exe (PID: 2356)
Application launched itself
- msiexec.exe (PID: 2772)
- chrome.exe (PID: 124)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 3128)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 584)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 1408)
- cmd.exe (PID: 3096)
- msedge.exe (PID: 3252)
Creates files or folders in the user directory
- PDFill_PDF_Tools_FREE.exe (PID: 3276)
Executes as Windows Service
- VSSVC.exe (PID: 3684)
Create files in a temporary directory
- msiexec.exe (PID: 116)
- msiexec.exe (PID: 2940)
- msiexec.exe (PID: 2772)
- DownloadComponents.exe (PID: 2776)
The process drops C-runtime libraries
- PDFill_PDF_Tools_FREE.exe (PID: 3276)
Process drops legitimate windows executable
- msiexec.exe (PID: 2772)
- PDFill_PDF_Tools_FREE.exe (PID: 3276)
Creates files in the program directory
- DownloadComponents.exe (PID: 2776)
- PDFillZip.exe (PID: 2492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
121
Monitored processes
72
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\system32\MsiExec.exe -Embedding C12463248653B1AD46DFF53829DD29AC | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://download.cnet.com/pdfill-free-pdf-tools/3001-18497_4-10435051.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1128 --field-trial-handle=1156,i,1392153033837297887,5431260014056524989,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 584 | /C "C:\Users\admin\AppData\Local\Temp\{673C8D87-0795-4F84-85C4-C87AEBB263D5}.bat" | C:\Windows\System32\cmd.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2000 --field-trial-handle=1156,i,1392153033837297887,5431260014056524989,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1356 --field-trial-handle=1156,i,1392153033837297887,5431260014056524989,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1640 --field-trial-handle=1336,i,14220805674543108927,11189025431377774142,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 948 | C:\Windows\system32\cmd.exe /c dir /b /a "1" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | xcopy /E /Y /K /H /I "2\*" "C:\Program Files\PlotSoft\PDFill\Saved\CustomShapes\" | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=3360 --field-trial-handle=1156,i,1392153033837297887,5431260014056524989,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
26 541
Read events
26 300
Write events
217
Delete events
24
Modification events
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (124) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
69
Suspicious files
133
Text files
99
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdf8e7.TMP | — | |
MD5:— | SHA256:— | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFdf8e7.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFdfa8d.TMP | text | |
MD5:C5B082BC8EA6A9BD1DC6782C00A79605 | SHA256:6168A9E585264DE05DEE1B67427B1BC277F1B83B9297184EFACC5D3BB061ABDE | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFdffad.TMP | — | |
MD5:— | SHA256:— | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RFdfb39.TMP | text | |
MD5:0272AD43ECEA4DC6C694BE6D918B5BA7 | SHA256:530F5A3F46B293038FEBEF2035CFA622F05B202363ABFAF9E40E105BD1472432 | |||
| 124 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RFe0f6d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
108
DNS requests
143
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 19.4 Kb | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | — | — | unknown |
2776 | DownloadComponents.exe | GET | 304 | 23.32.238.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f38c730c54b45b43 | DE | — | — | unknown |
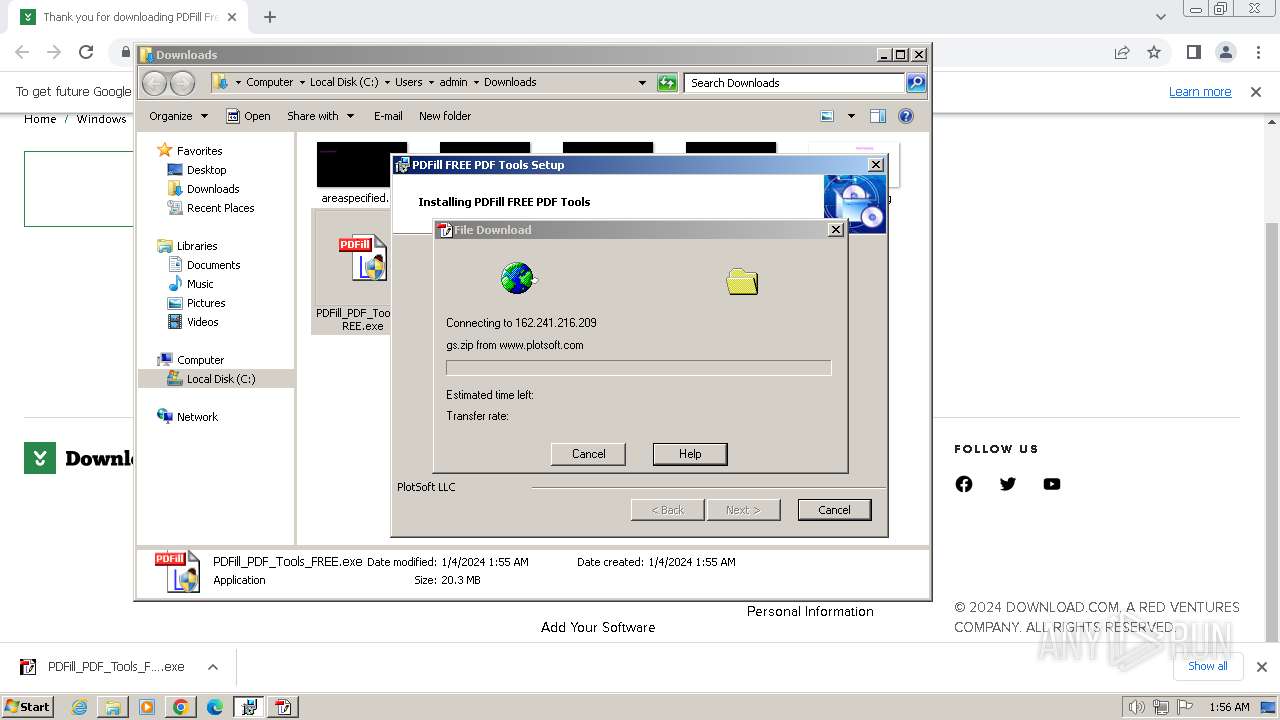
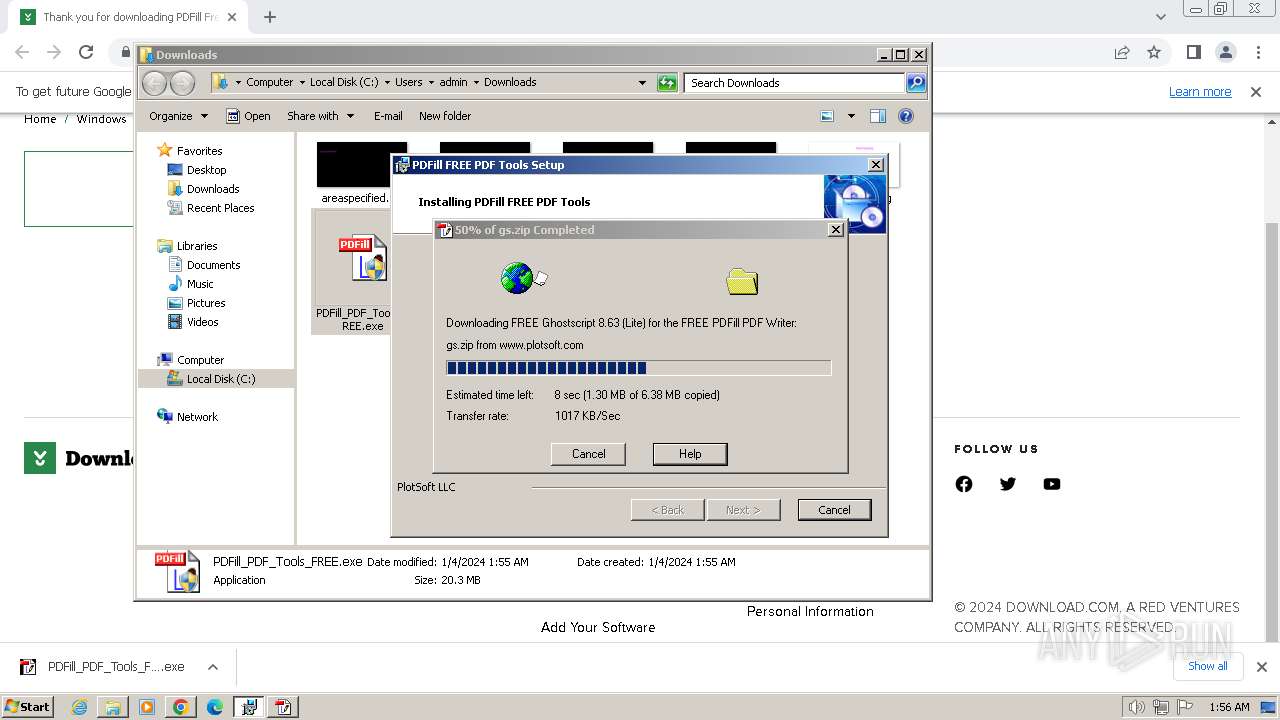
2776 | DownloadComponents.exe | GET | 301 | 162.241.216.209:80 | http://www.plotsoft.com/download/gs.zip | US | html | 248 b | unknown |
2776 | DownloadComponents.exe | GET | 200 | 23.32.238.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e27e2bb39ea5eb75 | DE | compressed | 65.2 Kb | unknown |
2776 | DownloadComponents.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | DE | binary | 717 b | unknown |
2776 | DownloadComponents.exe | GET | 200 | 184.24.77.79:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTSsMWpWTAymkqChS7925jY9g%3D%3D | DE | binary | 503 b | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 9.53 Kb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 1.37 Mb | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 1.49 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
124 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
784 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
784 | chrome.exe | 199.232.194.154:443 | download.cnet.com | FASTLY | US | unknown |
784 | chrome.exe | 151.101.1.91:443 | spn-v1.revampcdn.com | FASTLY | US | unknown |
784 | chrome.exe | 151.101.194.154:443 | at.adtech.redventures.io | FASTLY | US | unknown |
784 | chrome.exe | 216.58.206.40:443 | www.googletagmanager.com | GOOGLE | US | unknown |
784 | chrome.exe | 172.217.23.98:443 | securepubads.g.doubleclick.net | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
download.cnet.com |
| whitelisted |
spn-v1.revampcdn.com |
| unknown |
at.adtech.redventures.io |
| unknown |
securepubads.g.doubleclick.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdn.cookielaw.org |
| whitelisted |
cdn.cohesionapps.com |
| whitelisted |
geolocation.onetrust.com |
| whitelisted |
ingest.make.rvapps.io |
| unknown |
Threats
Process | Message |
|---|---|
msiexec.exe | # 2024-01-04 @01:56:20 [PID=116|Thread=1892] | OnAiBackupImmediate begin.
|
msiexec.exe | # 2024-01-04 @01:56:20 [PID=116|Thread=1892] | MsiTableReader: Getting the active MSI database for this installation session...
|
msiexec.exe | # 2024-01-04 @01:56:20 [PID=116|Thread=1892] | Building Custom Action Data...
|
msiexec.exe | # 2024-01-04 @01:56:20 [PID=116|Thread=1892] | SELECT Query: [SELECT * FROM `AI_PersistentData`].
|
msiexec.exe | # 2024-01-04 @01:56:20 [PID=116|Thread=1892] | MsiTableReader::ExecuteQuery [SELECT * FROM `AI_PersistentData`]...
|
msiexec.exe | # 2024-01-04 @01:56:20 [PID=116|Thread=1892] | CollectRemoveFileData start.
|
msiexec.exe | # 2024-01-04 @01:56:20 [PID=116|Thread=1892] | CollectRemoveFileData end.
|
msiexec.exe | # 2024-01-04 @01:56:20 [PID=116|Thread=1892] | OnAiBackupImmediate end.
|
msiexec.exe | DBGHELP: D:\BranchAI\win\Release\custact\x86\ResourceCleaner.pdb - file not found
|
msiexec.exe | DBGHELP: Symbol Search Path: C:\Windows\system32
|