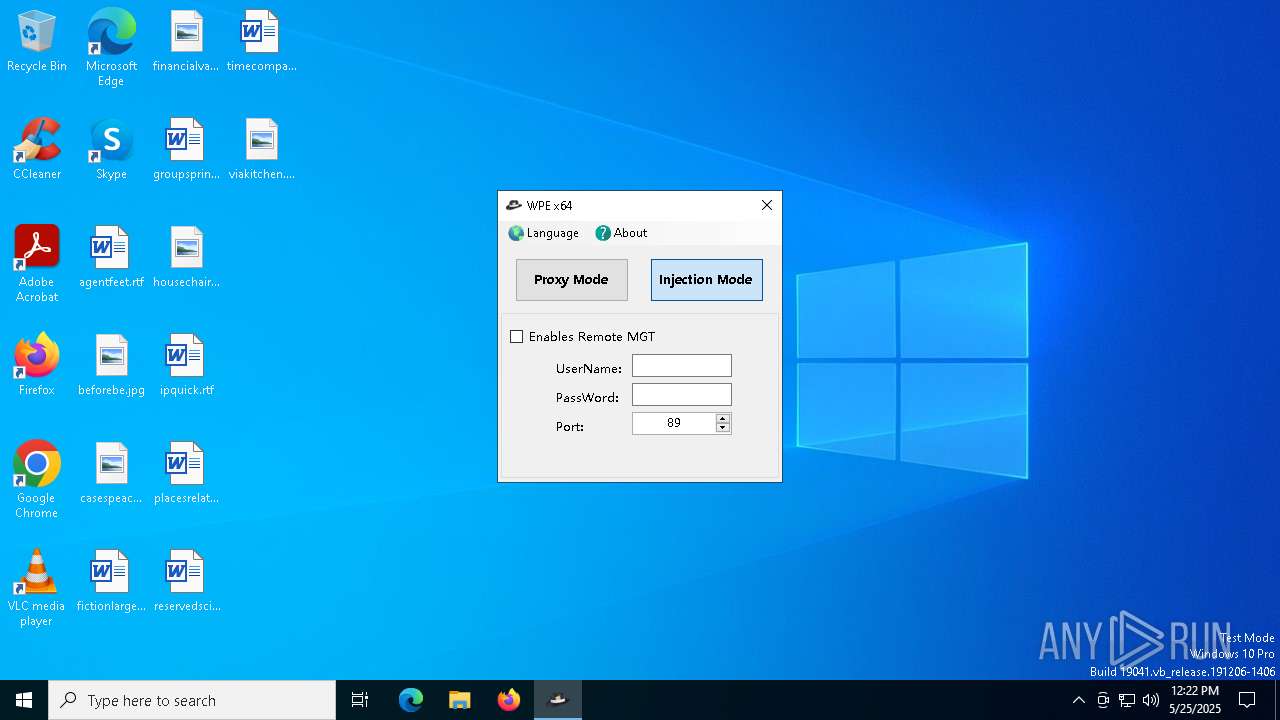
| File name: | WPE64 2.0.0.17.exe |
| Full analysis: | https://app.any.run/tasks/868b61c5-e988-4688-98fc-aa0c7c33af81 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2025, 12:22:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | EE12781D81FD56060F300BACB429D281 |
| SHA1: | F4B70D6BCFBB0F549172CDBD5A9378BC579B08CB |
| SHA256: | C28DFC5F61BD118C48037082757F18BFAA119B1C2DB8C05389A2C6AE510B14FE |
| SSDEEP: | 98304:5ZtMjY6vo5HnfG9M7EbQOnN/Wf+iS4LEltk0dM2ecWIZxvJSe2R/F5OFkg+LM4AR:1n7Xo+M5MEJ0bPQFX/ |
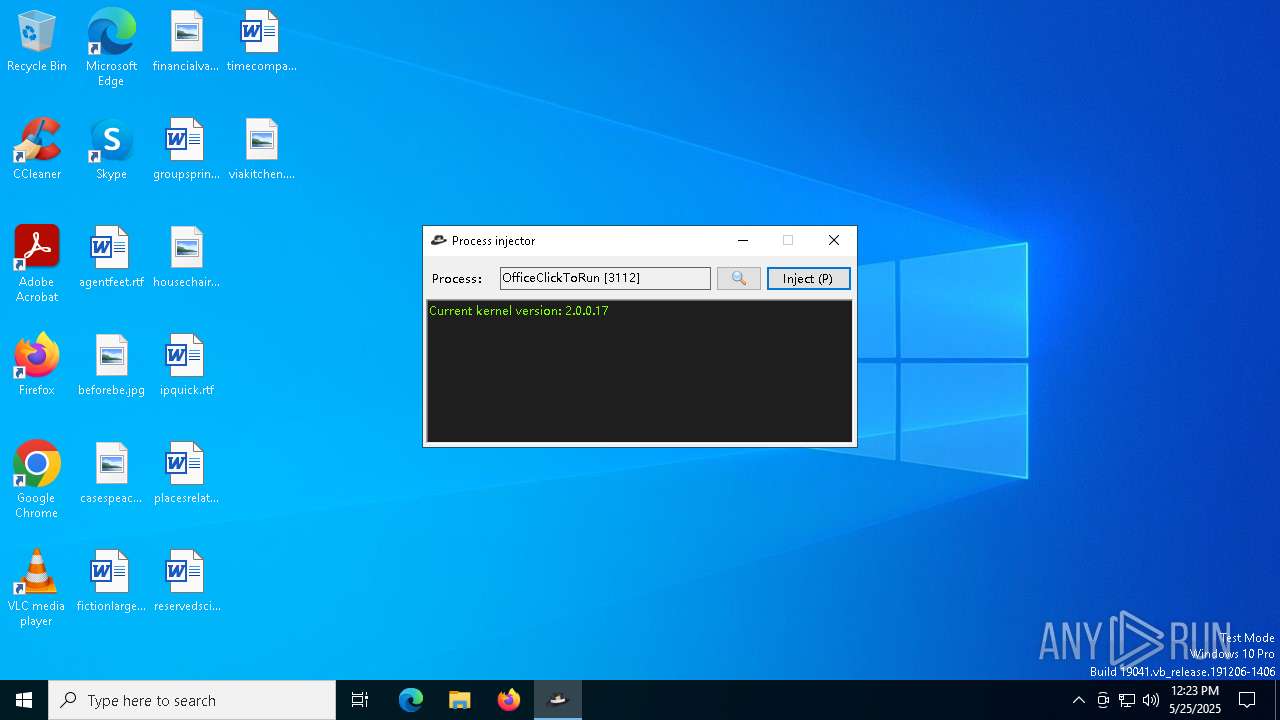
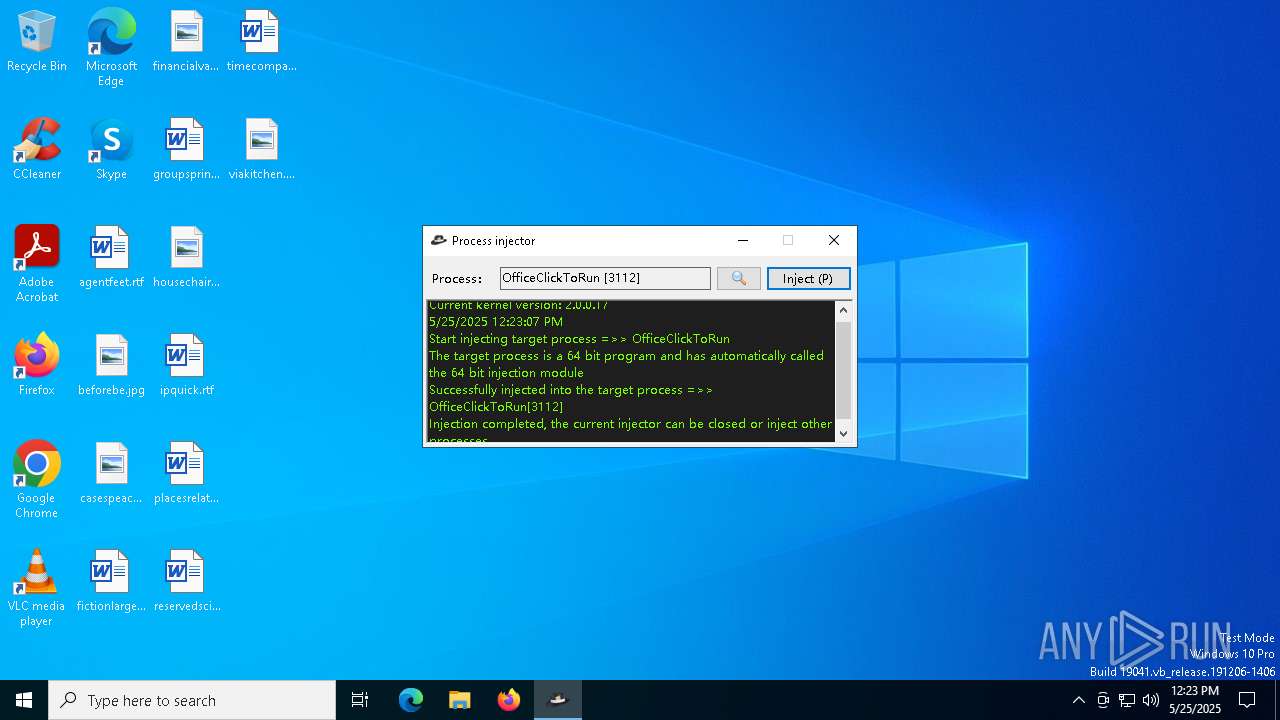
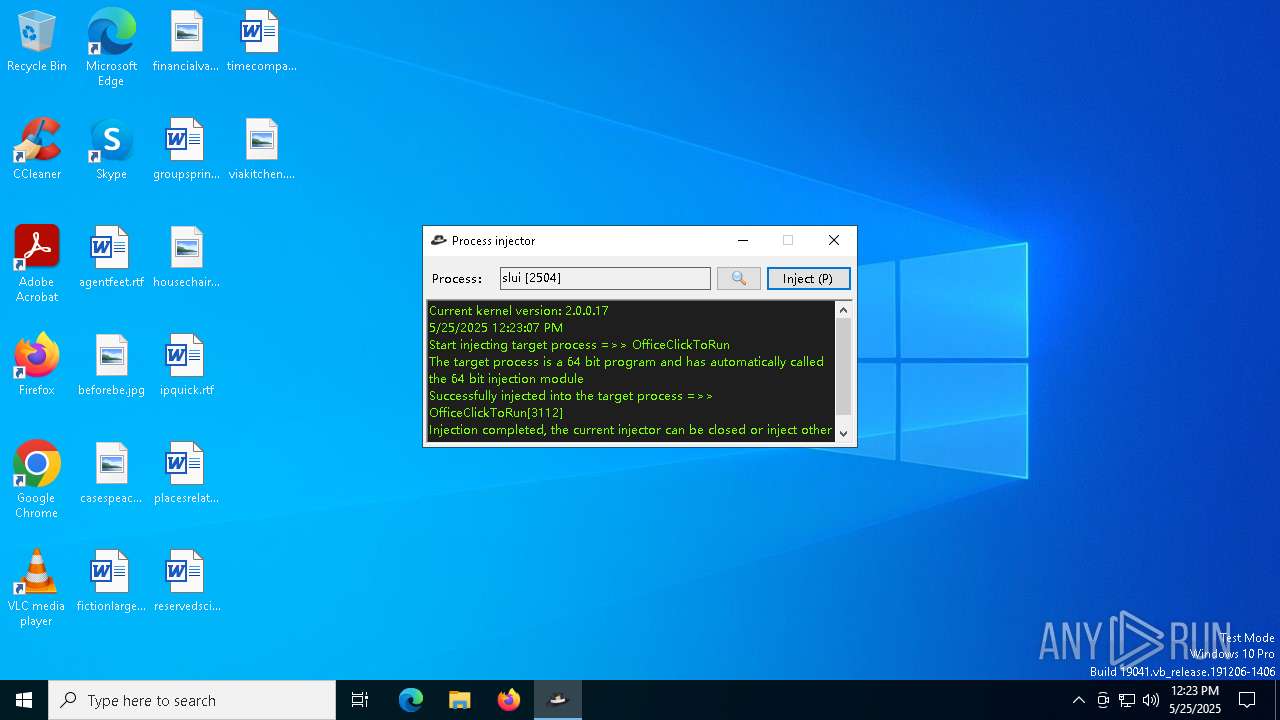
MALICIOUS
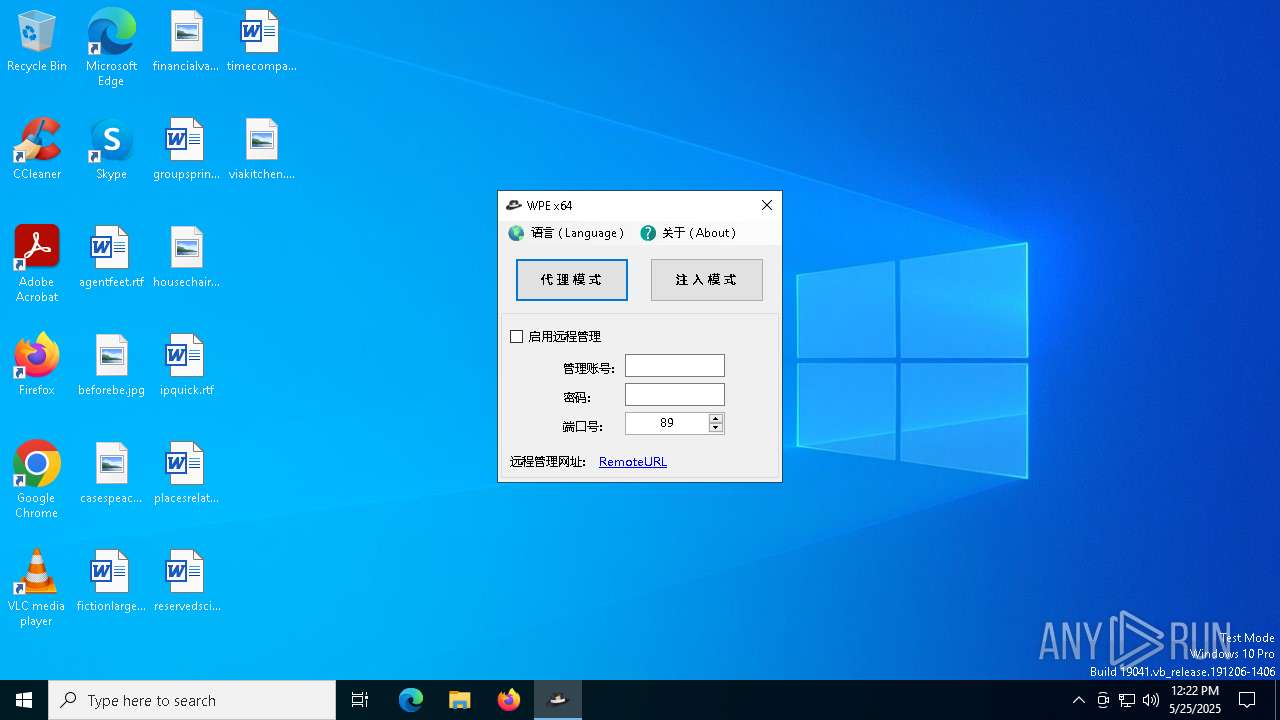
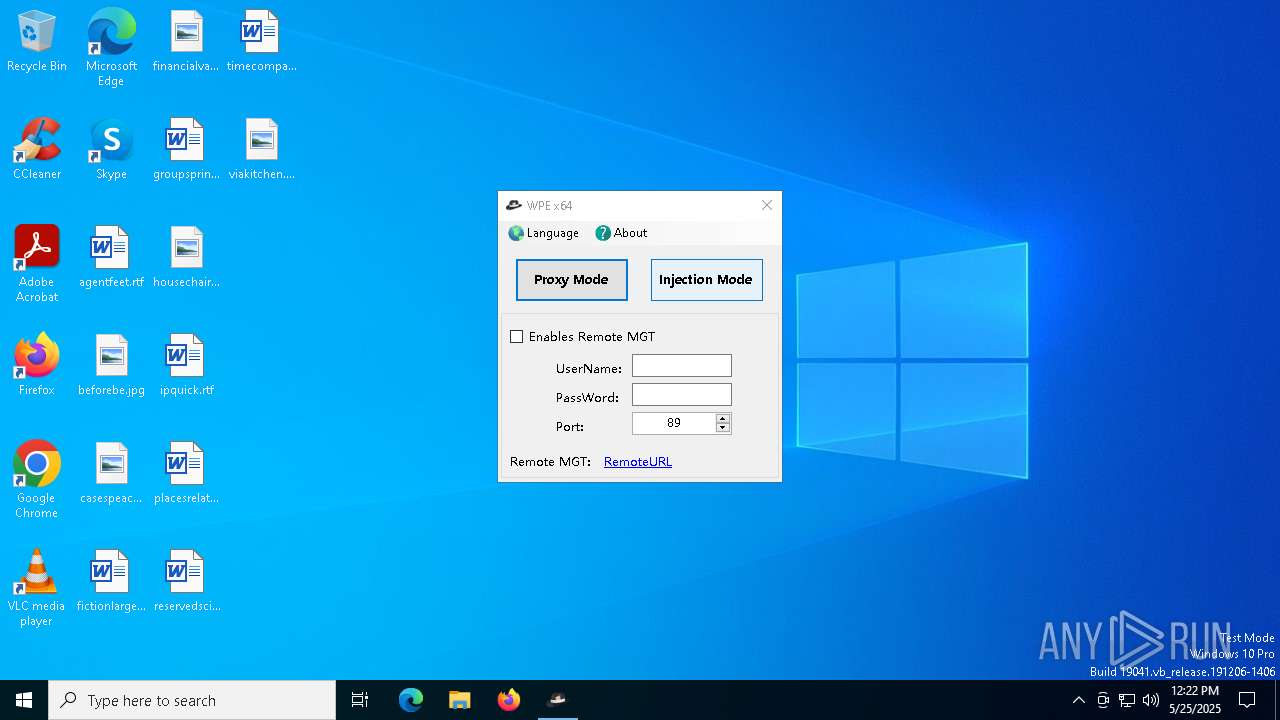
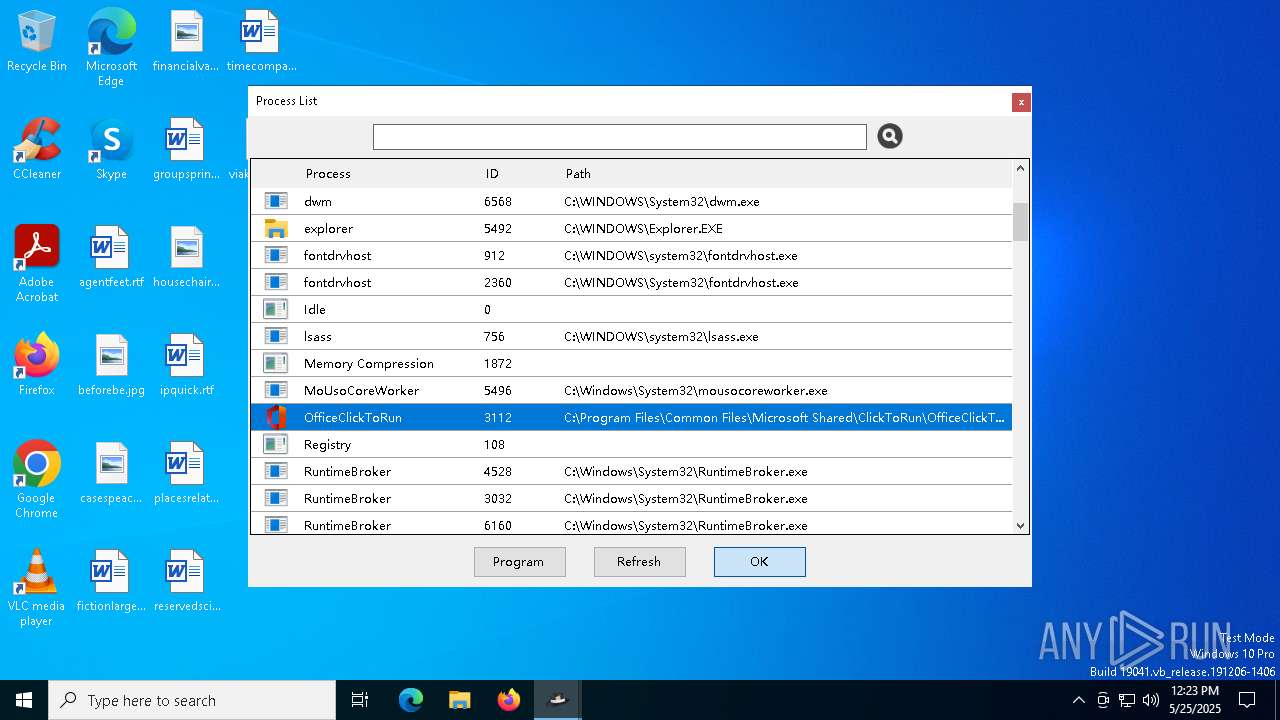
Application was injected by another process
- OfficeClickToRun.exe (PID: 3112)
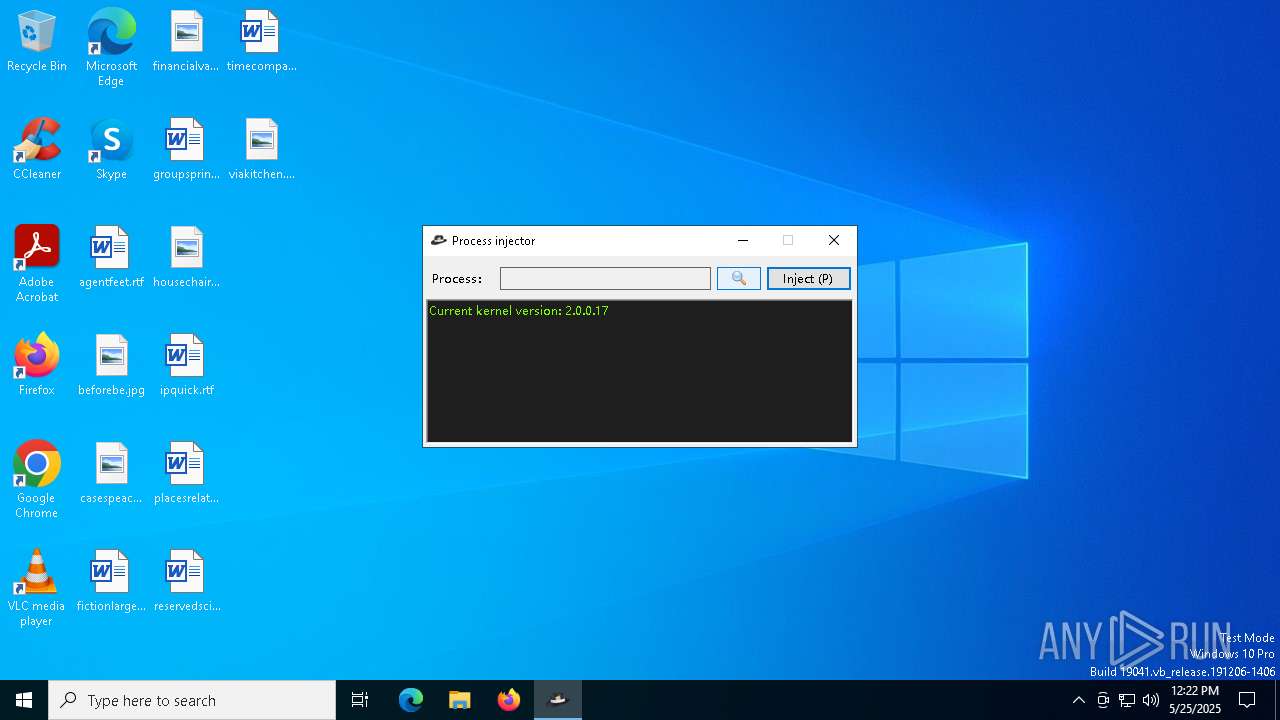
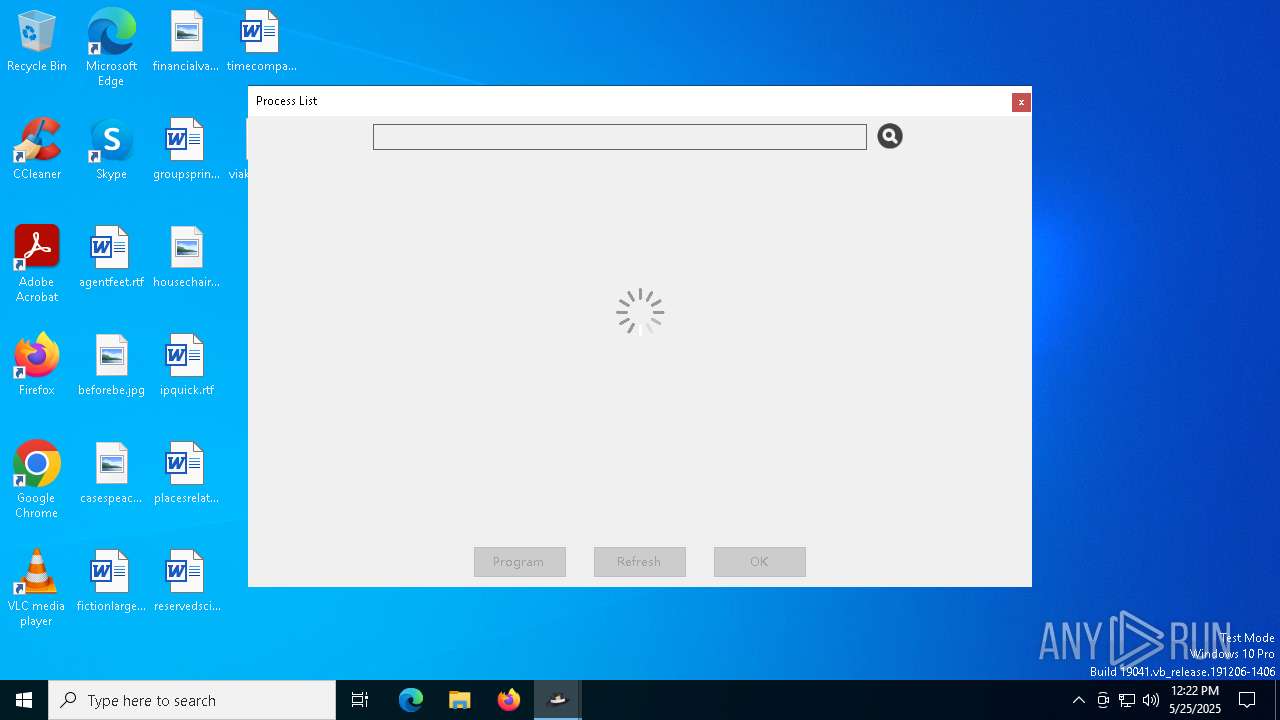
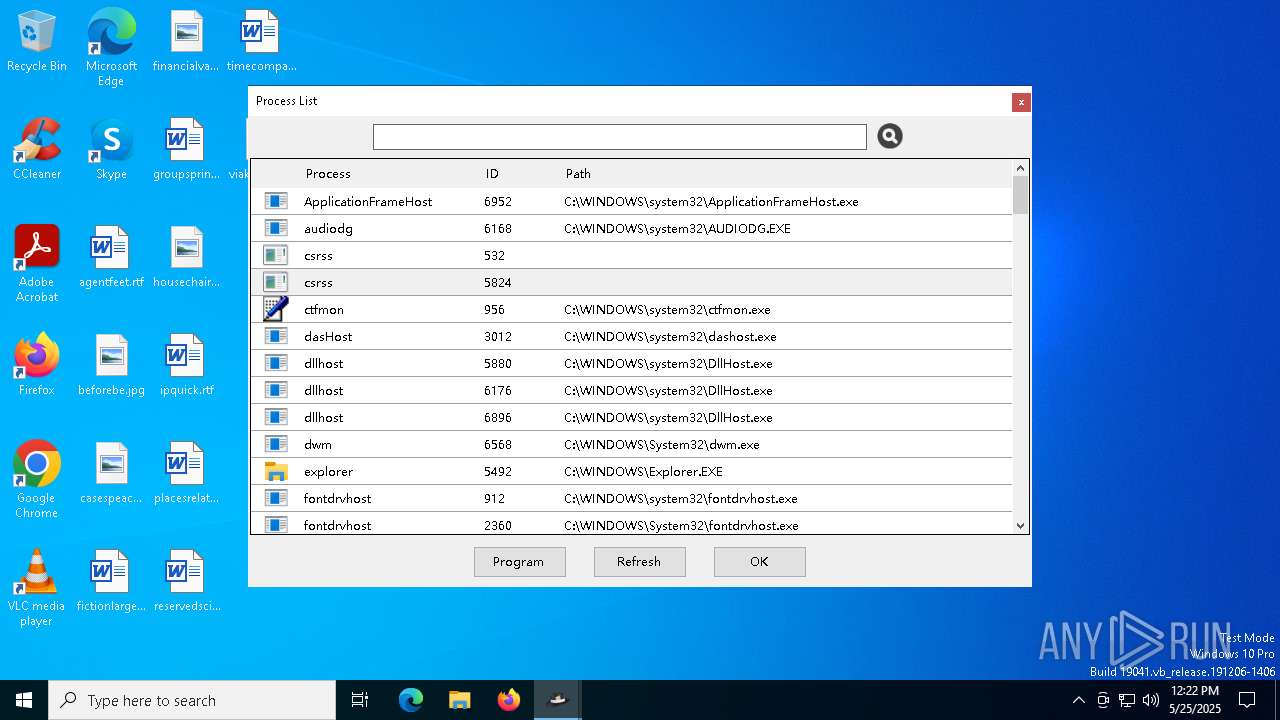
Runs injected code in another process
- WinsockPacketEditor.exe (PID: 2616)
SUSPICIOUS
Executable content was dropped or overwritten
- WPE64 2.0.0.17.exe (PID: 4776)
Reads security settings of Internet Explorer
- WPE64 2.0.0.17.exe (PID: 4776)
- WinsockPacketEditor.exe (PID: 6132)
- WinsockPacketEditor.exe (PID: 5956)
- WinsockPacketEditor.exe (PID: 2616)
Process drops legitimate windows executable
- WPE64 2.0.0.17.exe (PID: 4776)
Reads the date of Windows installation
- WPE64 2.0.0.17.exe (PID: 4776)
- WinsockPacketEditor.exe (PID: 6132)
- WinsockPacketEditor.exe (PID: 5956)
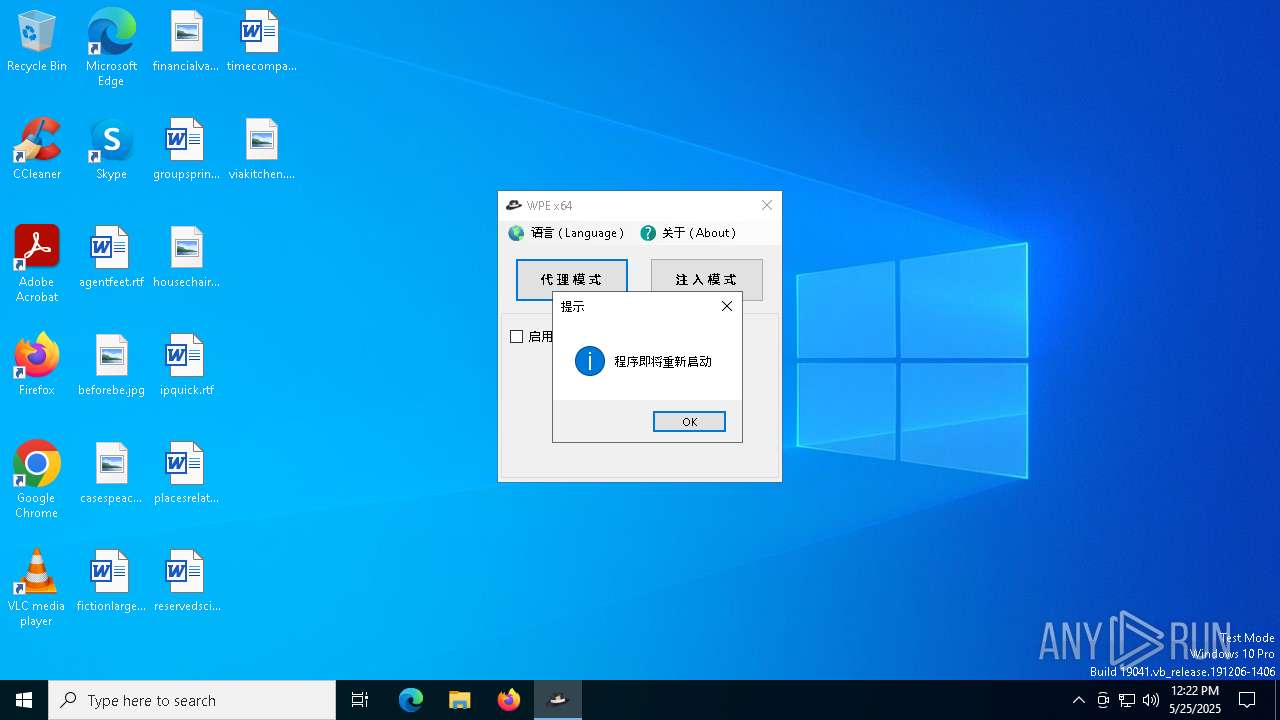
Application launched itself
- WinsockPacketEditor.exe (PID: 6132)
- WinsockPacketEditor.exe (PID: 5956)
Reads Internet Explorer settings
- WinsockPacketEditor.exe (PID: 5956)
- WinsockPacketEditor.exe (PID: 2616)
Executes as Windows Service
- WmiApSrv.exe (PID: 472)
The process checks if it is being run in the virtual environment
- OfficeClickToRun.exe (PID: 3112)
INFO
Reads the computer name
- WPE64 2.0.0.17.exe (PID: 4776)
- WinsockPacketEditor.exe (PID: 6132)
- WinsockPacketEditor.exe (PID: 5956)
- WinsockPacketEditor.exe (PID: 2616)
Checks supported languages
- WPE64 2.0.0.17.exe (PID: 4776)
- WinsockPacketEditor.exe (PID: 6132)
- WinsockPacketEditor.exe (PID: 5956)
- WinsockPacketEditor.exe (PID: 2616)
- OfficeClickToRun.exe (PID: 3112)
Process checks computer location settings
- WPE64 2.0.0.17.exe (PID: 4776)
- WinsockPacketEditor.exe (PID: 6132)
- WinsockPacketEditor.exe (PID: 5956)
Create files in a temporary directory
- WPE64 2.0.0.17.exe (PID: 4776)
The sample compiled with english language support
- WPE64 2.0.0.17.exe (PID: 4776)
Reads the machine GUID from the registry
- WinsockPacketEditor.exe (PID: 6132)
- WinsockPacketEditor.exe (PID: 5956)
- WinsockPacketEditor.exe (PID: 2616)
- OfficeClickToRun.exe (PID: 3112)
Creates files in the program directory
- WinsockPacketEditor.exe (PID: 6132)
Disables trace logs
- WinsockPacketEditor.exe (PID: 5956)
- WinsockPacketEditor.exe (PID: 2616)
Reads Environment values
- WinsockPacketEditor.exe (PID: 5956)
- WinsockPacketEditor.exe (PID: 2616)
Reads the software policy settings
- WinsockPacketEditor.exe (PID: 5956)
- WinsockPacketEditor.exe (PID: 2616)
Checks proxy server information
- WinsockPacketEditor.exe (PID: 2616)
- WinsockPacketEditor.exe (PID: 5956)
Reads the time zone
- OfficeClickToRun.exe (PID: 3112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:12 14:02:25+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 307200 |
| InitializedDataSize: | 484864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32680 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
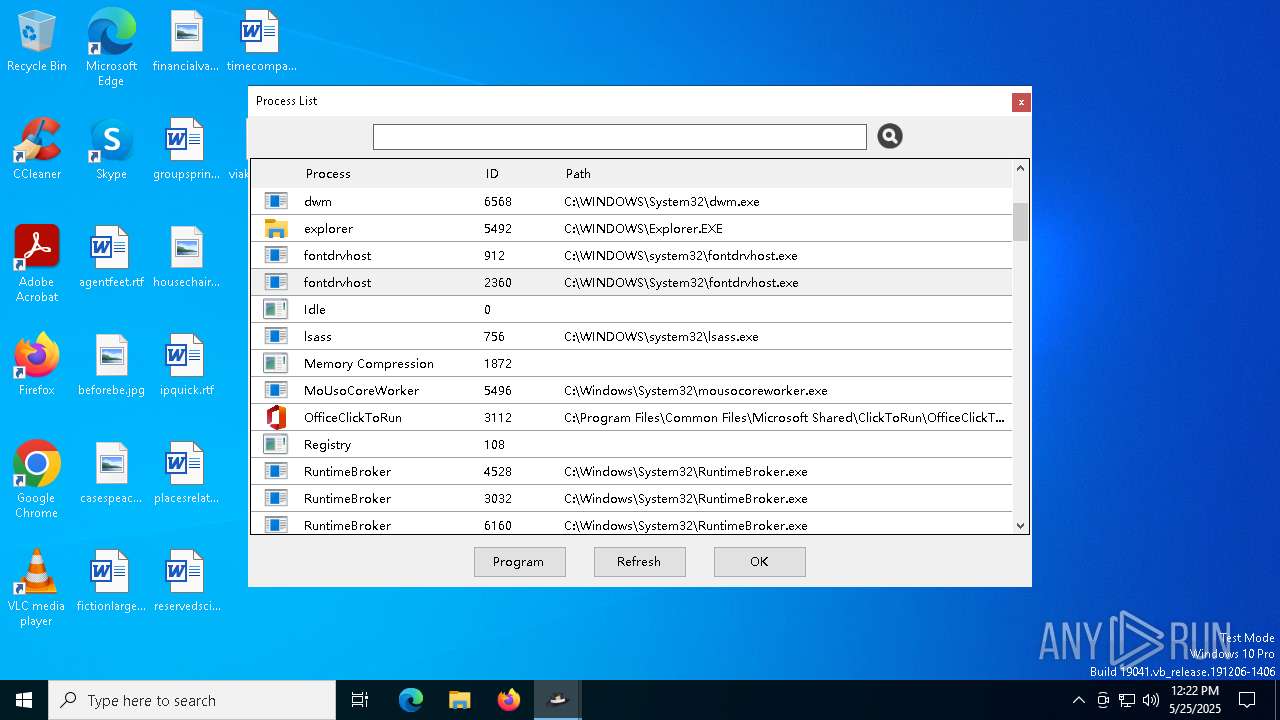
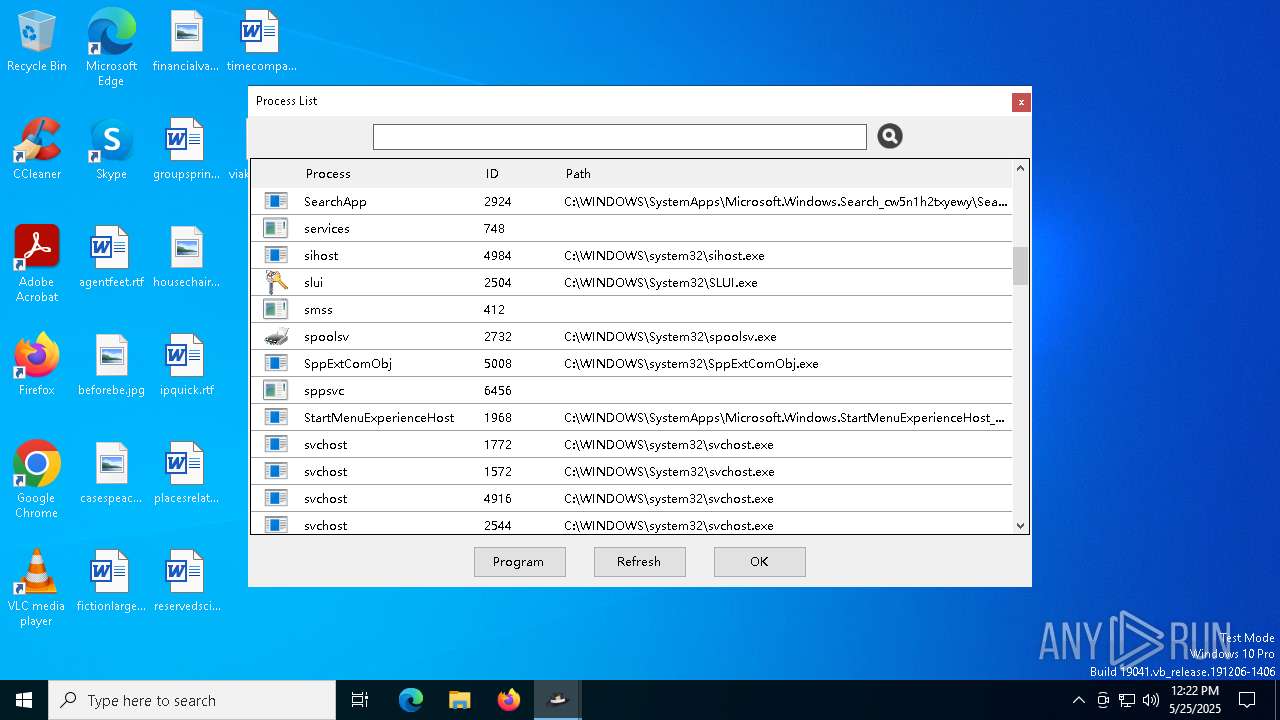
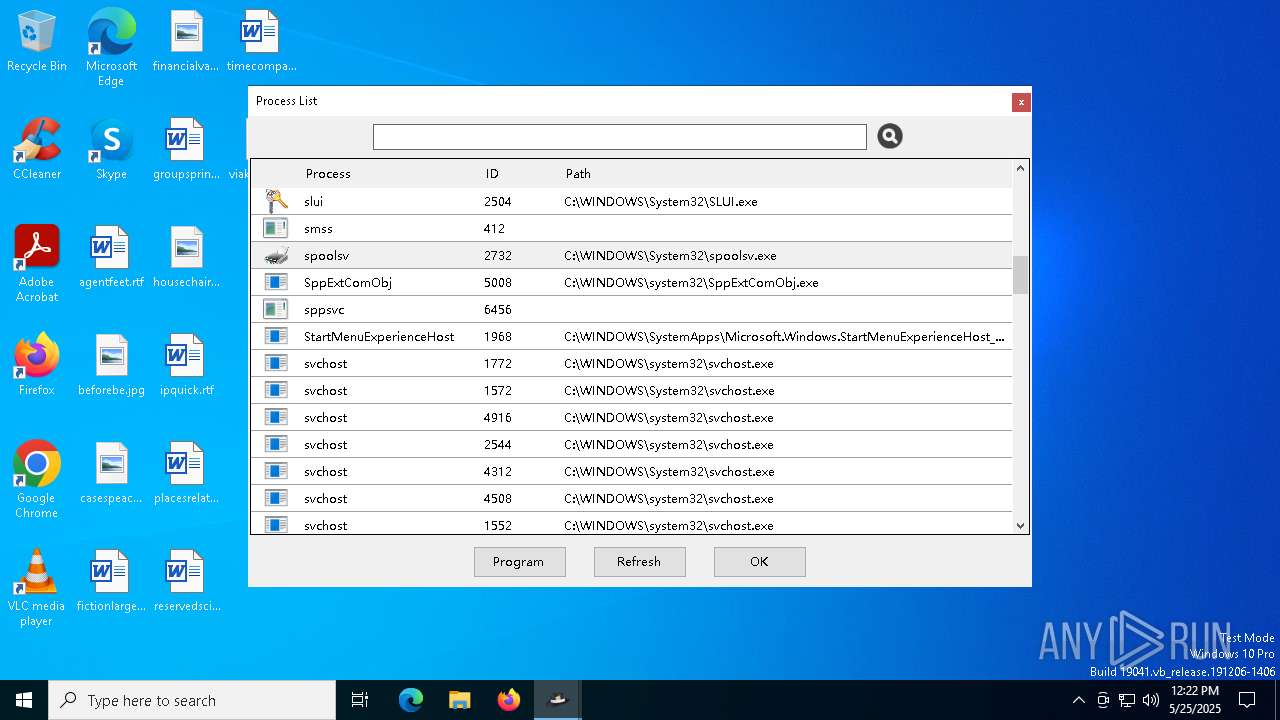
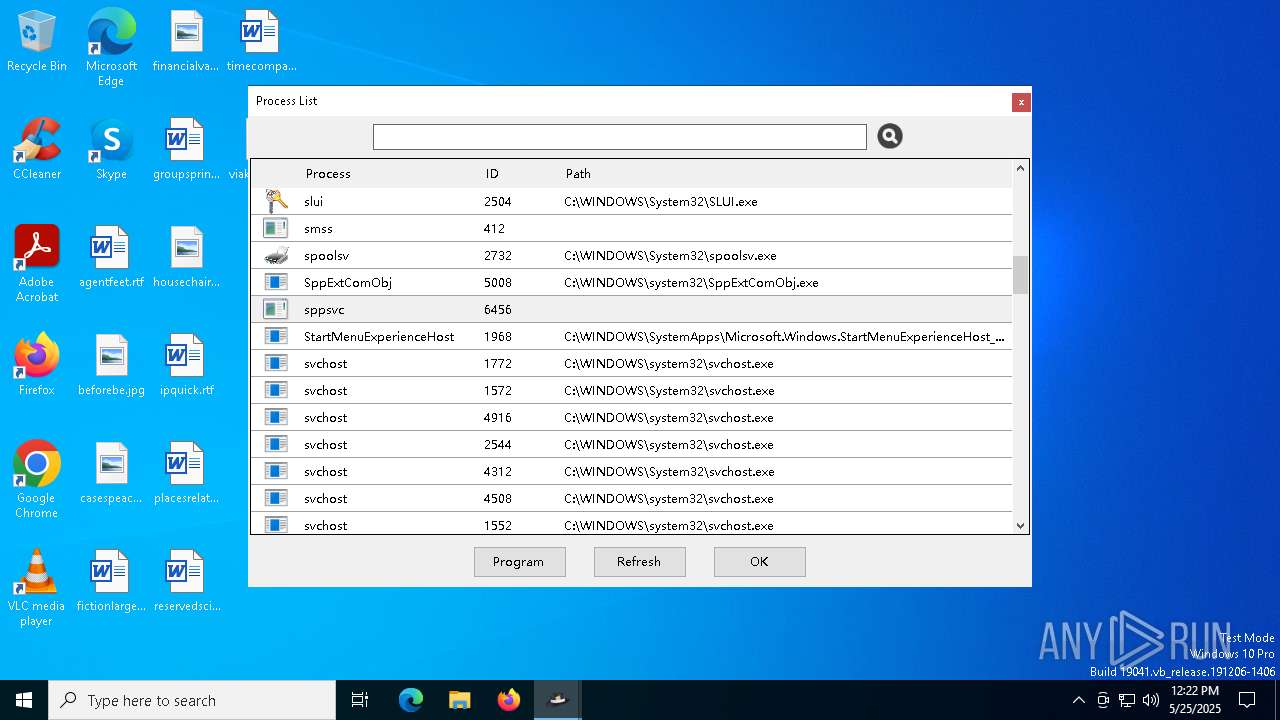
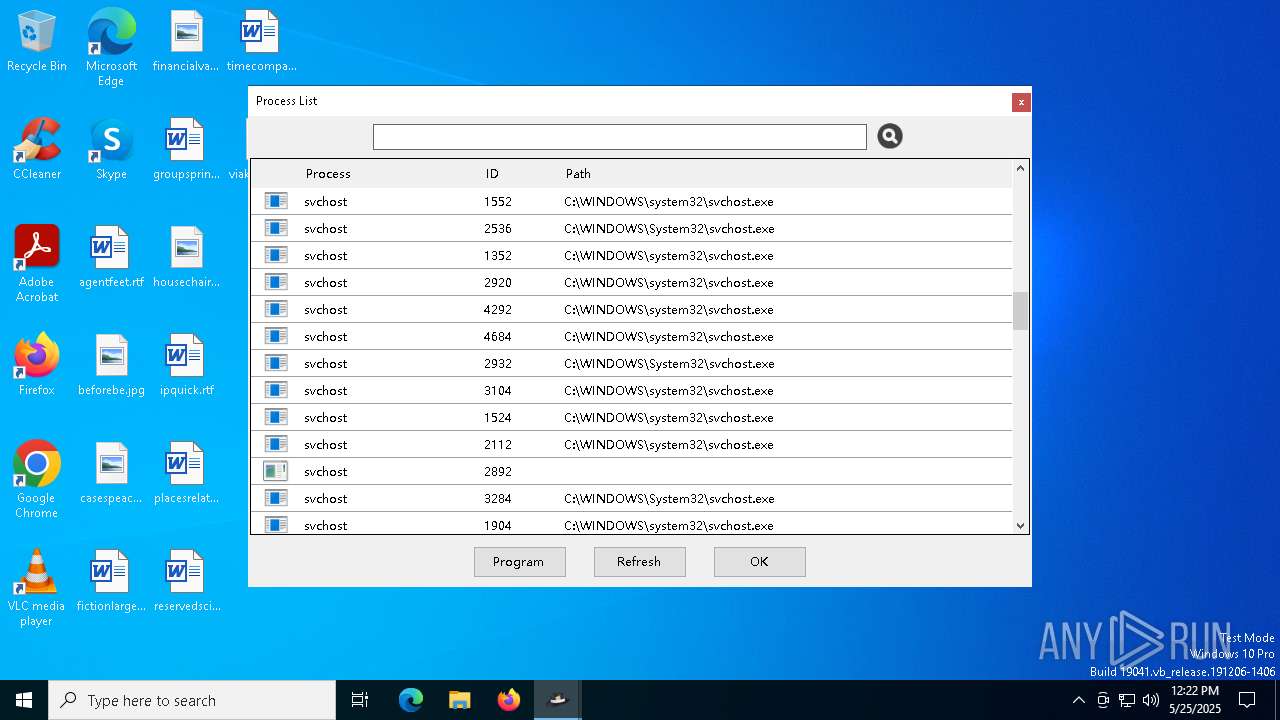
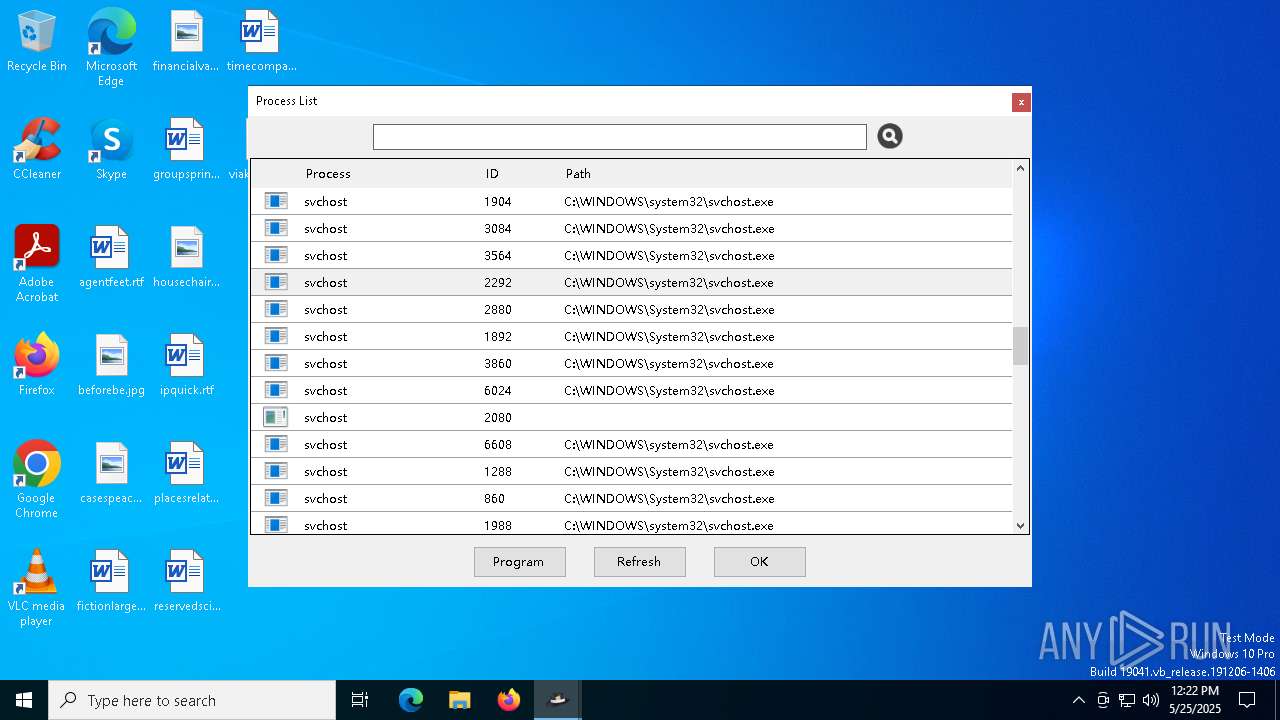
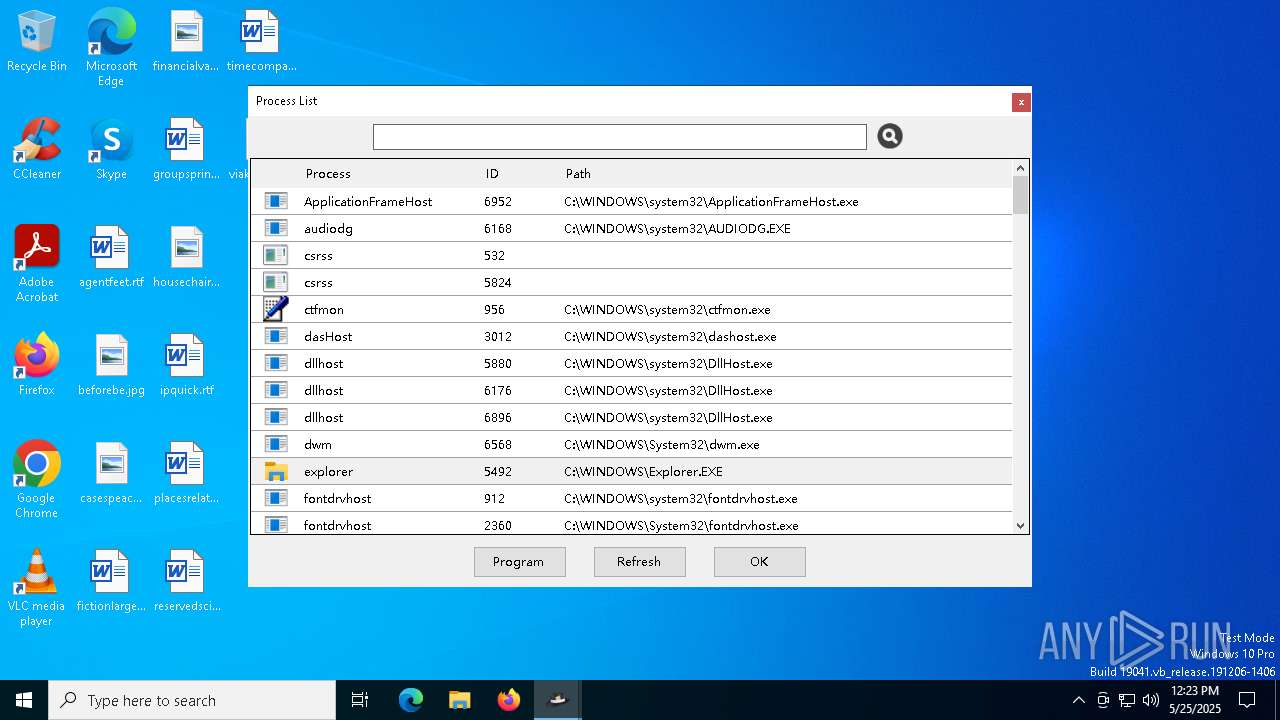
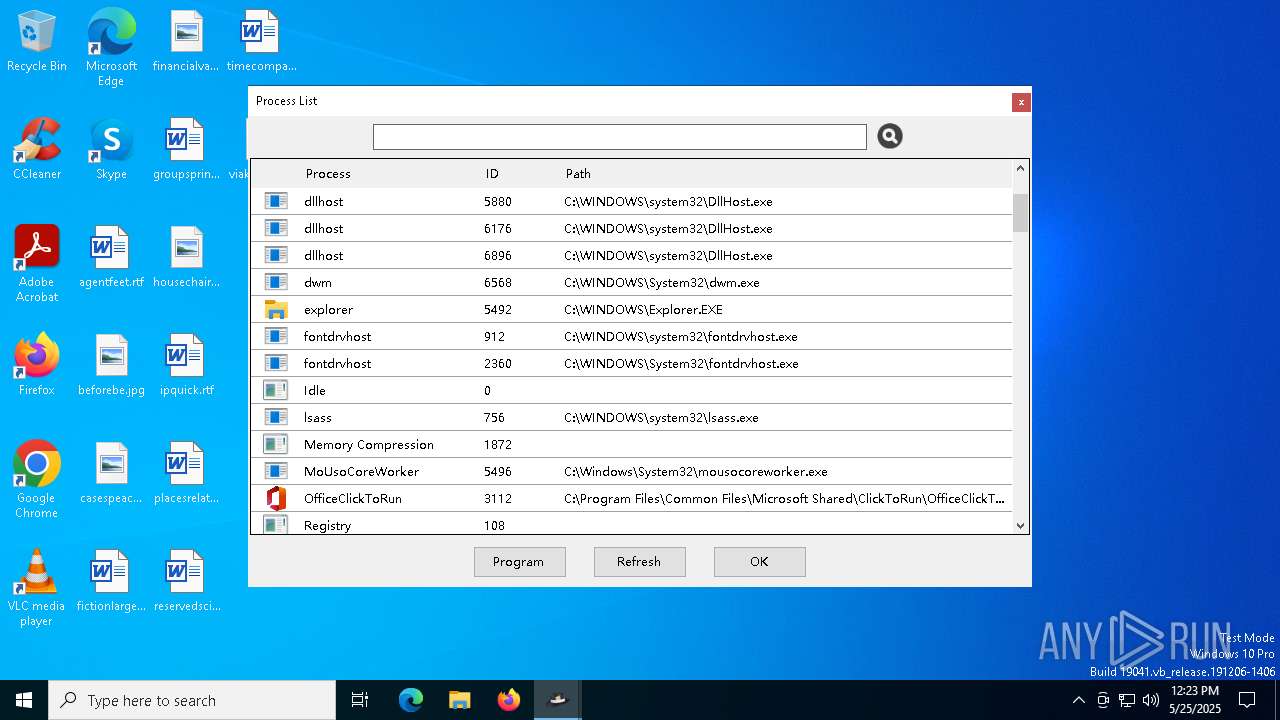
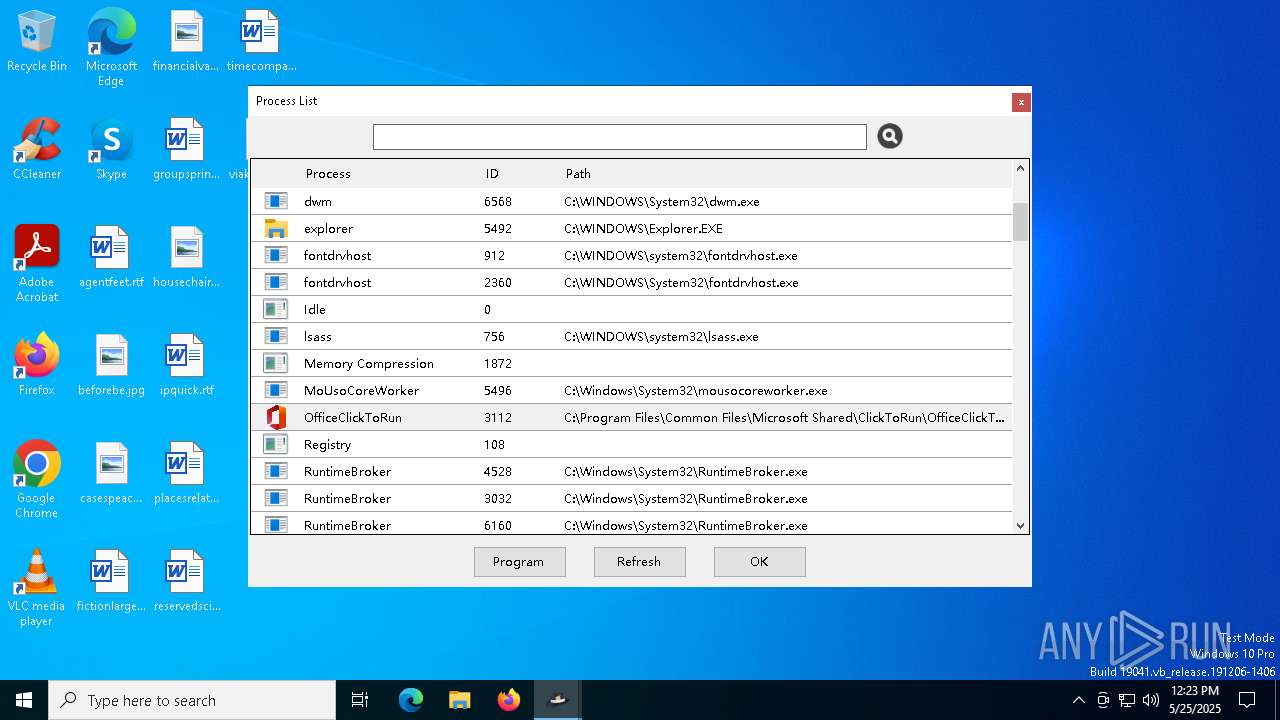
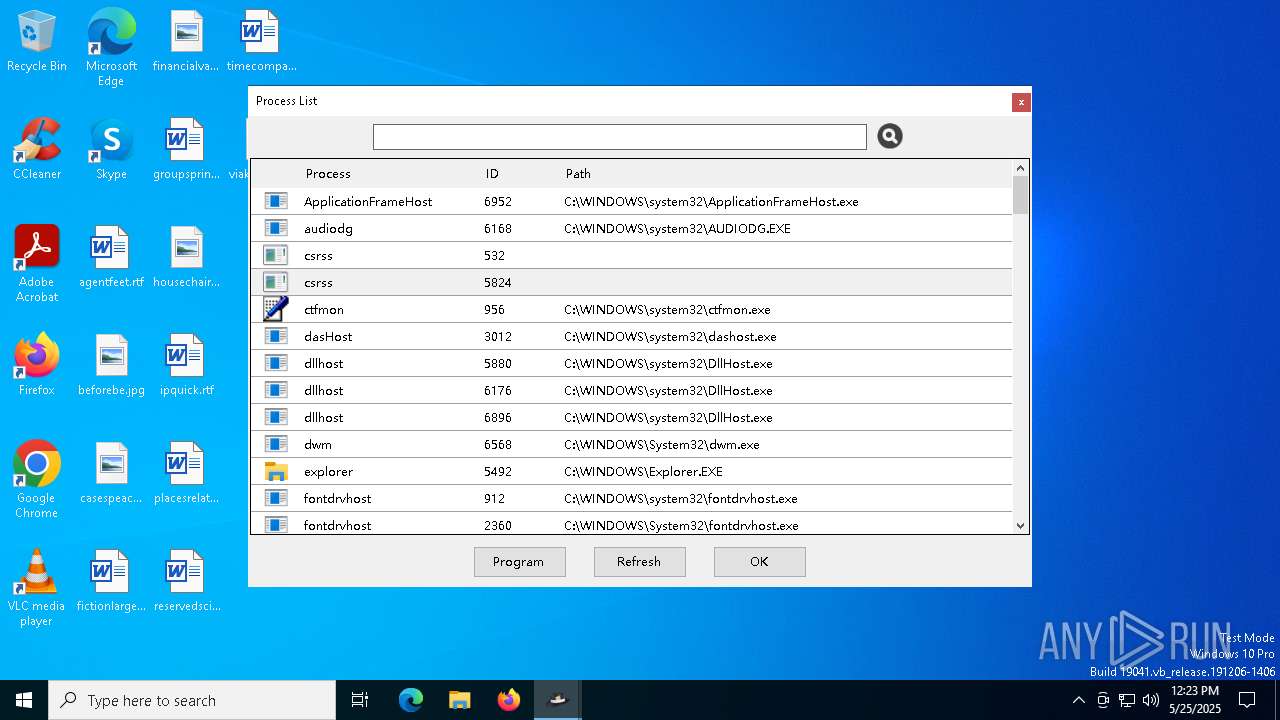
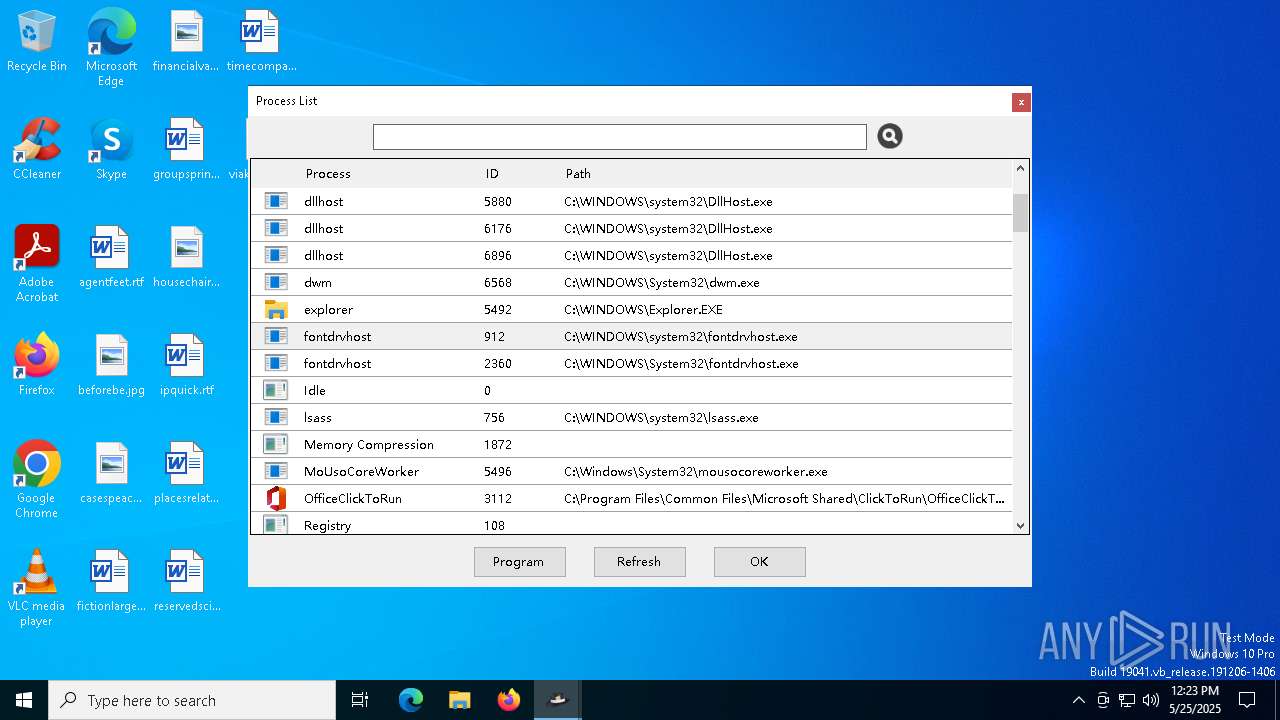
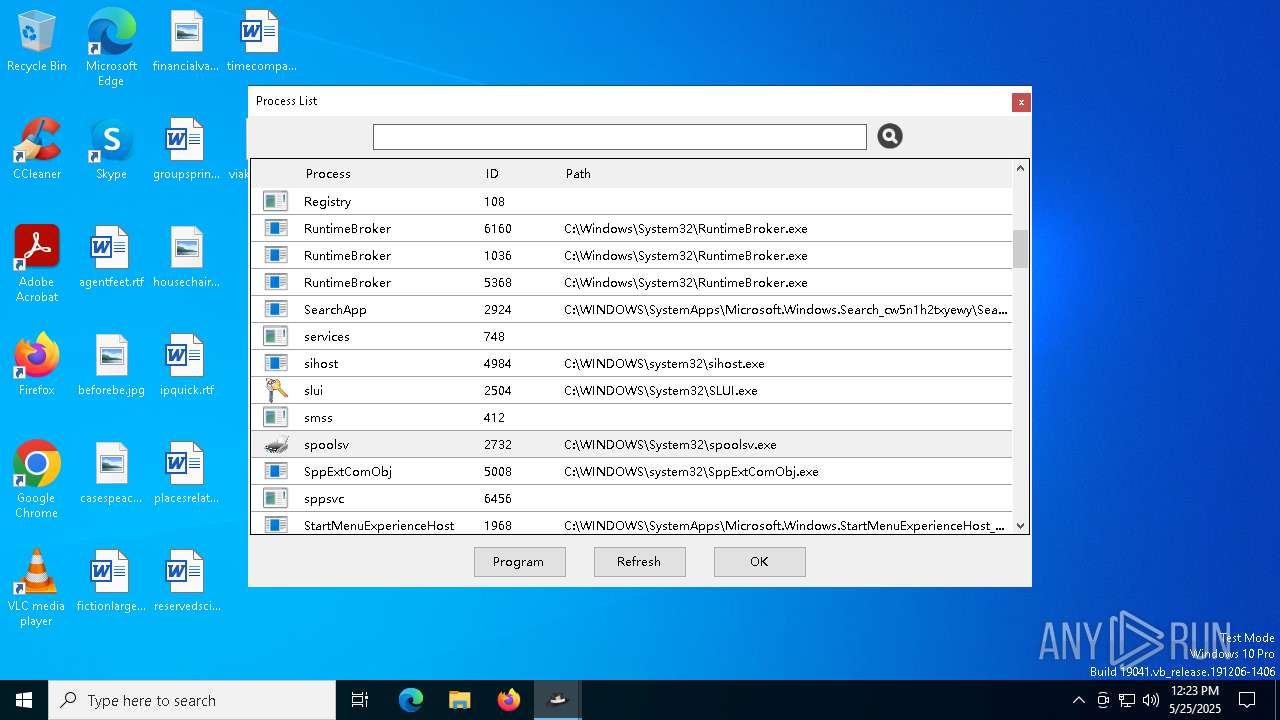
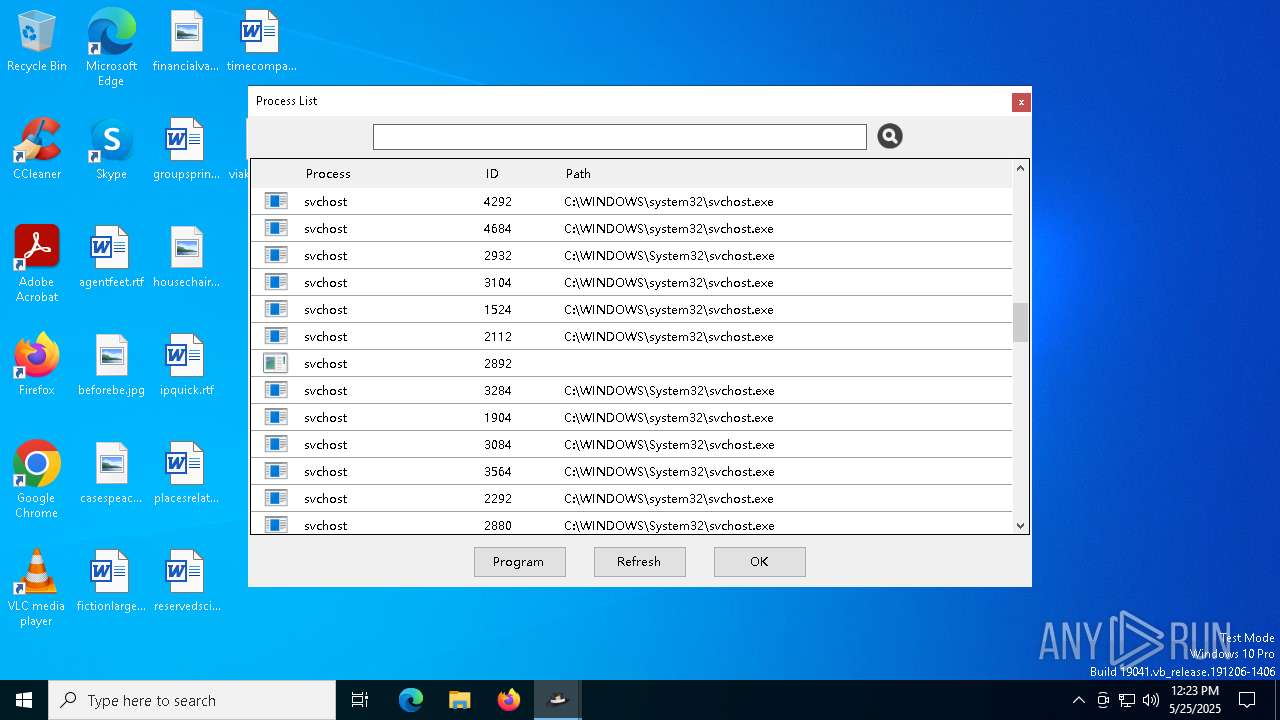
Total processes
136
Monitored processes
8
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
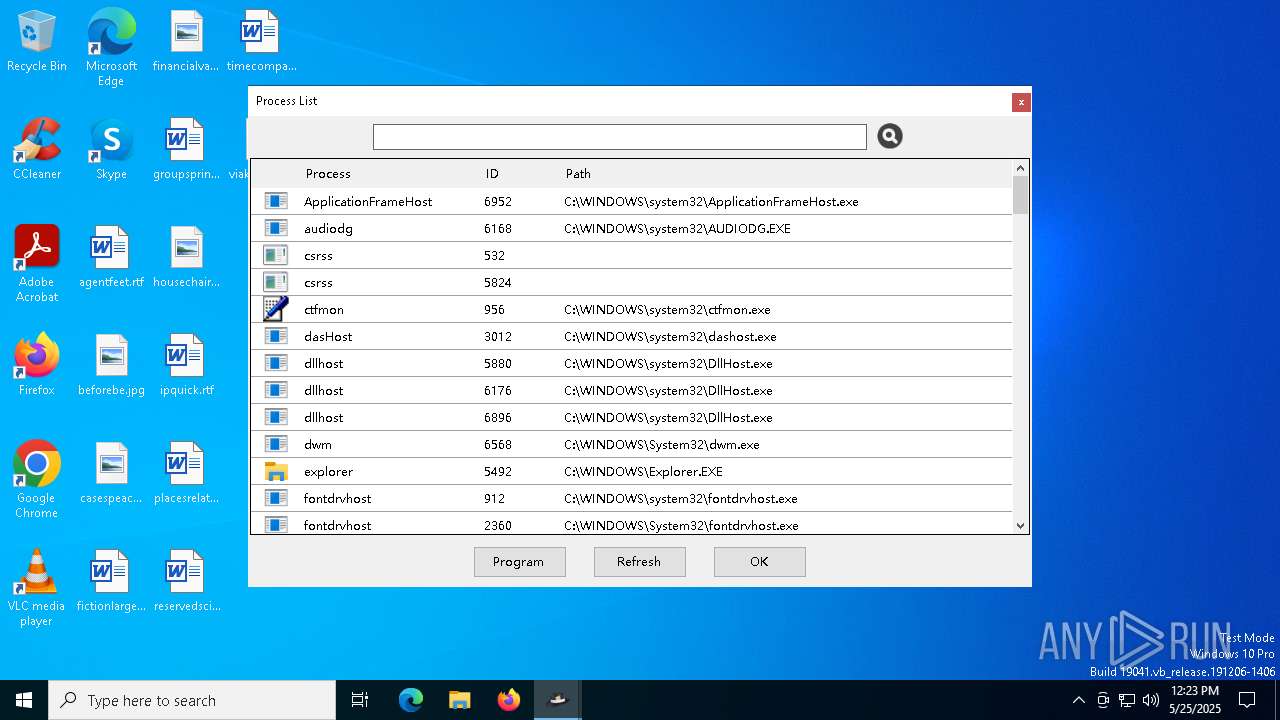
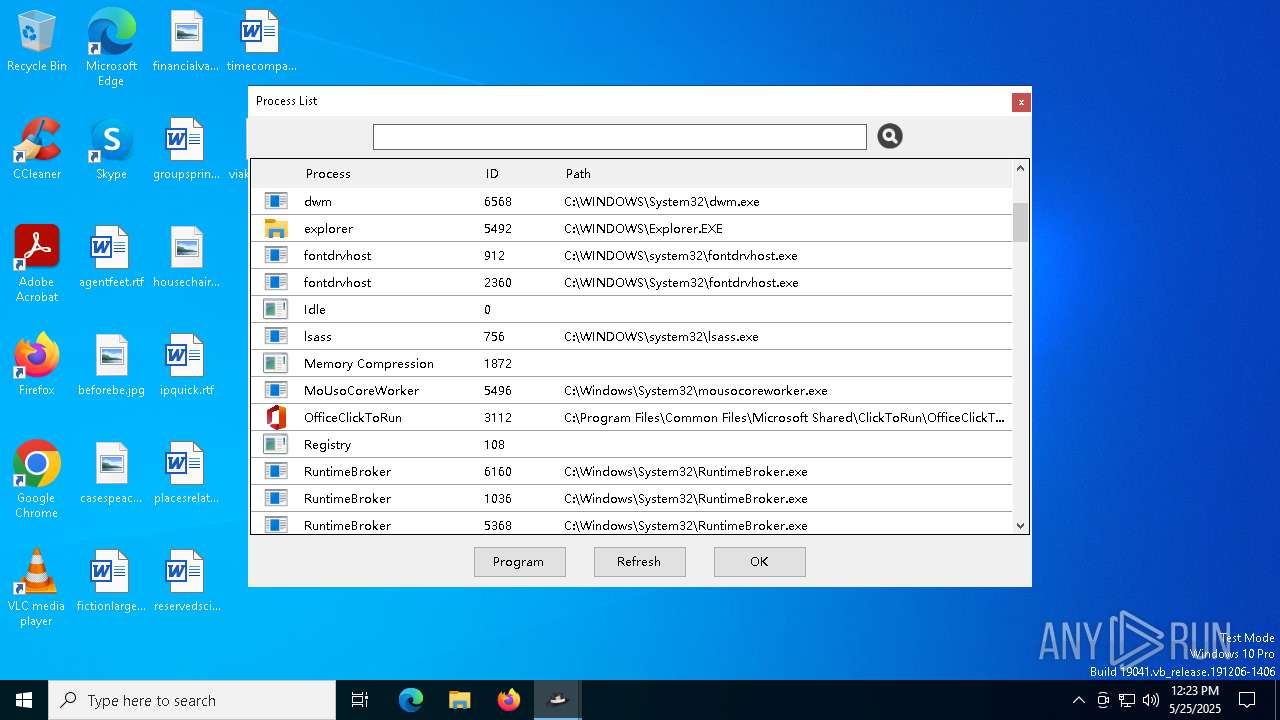
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | C:\WINDOWS\system32\wbem\WmiApSrv.exe | C:\Windows\System32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
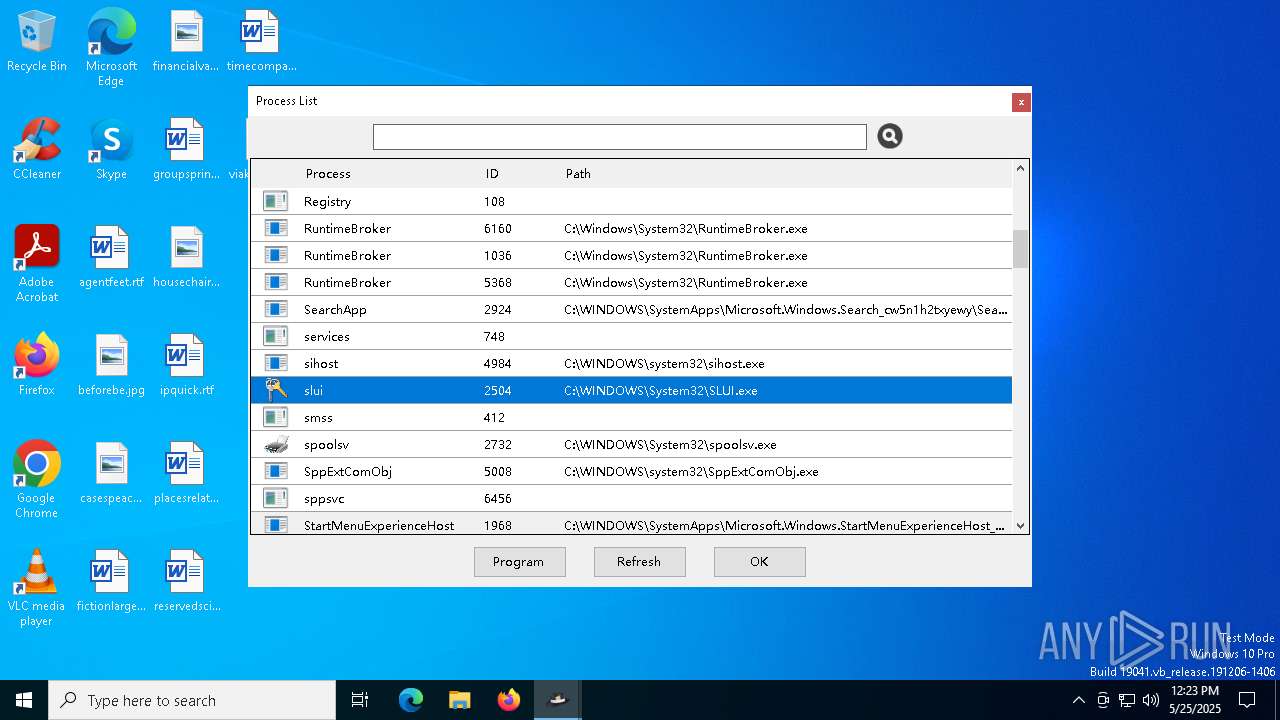
| 2504 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe | WinsockPacketEditor.exe | ||||||||||||
User: admin Company: X-NAS Integrity Level: HIGH Description: WinsockPacketEditor Version: 2.0.0.17 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe" /service | C:\Program Files\Common Files\microsoft shared\ClickToRun\OfficeClickToRun.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Click-to-Run (SxS) Version: 16.0.16026.20140 Modules
| |||||||||||||||
| 4776 | "C:\Users\admin\AppData\Local\Temp\WPE64 2.0.0.17.exe" | C:\Users\admin\AppData\Local\Temp\WPE64 2.0.0.17.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5008 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5956 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe | WinsockPacketEditor.exe | ||||||||||||
User: admin Company: X-NAS Integrity Level: HIGH Description: WinsockPacketEditor Exit code: 4294967295 Version: 2.0.0.17 Modules
| |||||||||||||||
| 6132 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe | — | WPE64 2.0.0.17.exe | |||||||||||
User: admin Company: X-NAS Integrity Level: MEDIUM Description: WinsockPacketEditor Exit code: 0 Version: 2.0.0.17 Modules
| |||||||||||||||
Total events
5 816
Read events
5 790
Write events
26
Delete events
0
Modification events
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5956) WinsockPacketEditor.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WinsockPacketEditor_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
37
Suspicious files
18
Text files
47
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Be.Windows.Forms.HexBox.dll | executable | |
MD5:1ABB997D4E809B9D7F9016617DC01294 | SHA256:4938A4DBB51FD8D35DFDF2C5D42E9A127B9365D495461864E6BB9EC7FC9A3CB7 | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EasyHook32Svc.exe | executable | |
MD5:828B9A7AE0651E0F690C00816EEC1A94 | SHA256:9CFDA284E280CF9C6AFEB2D3016D78BEDA4E5B3CBAAF893684B569F5C246B99E | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EasyHook64.dll | executable | |
MD5:163C08C9333279DF7BC4788CF53A0990 | SHA256:03E75032981FD6152F4D9EE18D321BF553F9191F254F326DE87B9AD0AF0B8CED | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Be.Windows.Forms.HexBox.xml | xml | |
MD5:B534569D28458990C1B2F68EAFA60BC3 | SHA256:415EA2D9A22AB58E5F89ECE1CAF45FD61F2579EF0C700C990A997841F284E4E3 | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EasyHook64Svc.exe | executable | |
MD5:43AF289E93CF2F8BD491393C695D4812 | SHA256:B84C26F91D304F0922E620C96B606D325893760C14F9417AD73F7A152C539F9C | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EntityFramework.SqlServer.dll | executable | |
MD5:9FB212F4EFF8DD1EE42E49C61A39B2D0 | SHA256:A0DCF975C7E3A1496D8E58CC972210B4CF91193E474D2C868A0869C7643ADE5A | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Microsoft.Owin.FileSystems.xml | xml | |
MD5:E256891EFA05186F9FF4AF37926AFF66 | SHA256:4B07AA26670756C4A55CDCFDD8E26058596A5C38D51BFE0EC661952EE0DF4BE3 | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EasyLoad32.dll | executable | |
MD5:FFC0CD23FFA6929D90868D8F7DE133B3 | SHA256:6AE23E848531C6D67327071E994F65B37B8EFCE27E4E3E1B53D96A2D3A1D2F2F | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EntityFramework.dll | executable | |
MD5:29716264EFCC4C38E96B94917375129A | SHA256:CE25578A749C17A559832340004AC1AF2BF3594B79795AE53F8CAB09999E8FF6 | |||
| 4776 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EntityFramework.SqlServer.xml | xml | |
MD5:2D1549C365902D6CBEE20E02A985B68B | SHA256:902F57044BAF104DD9A491DADCBA4C787B6F64531880DC3B11345D5758D7BD81 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
23
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6752 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6752 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5956 | WinsockPacketEditor.exe | 101.132.222.195:443 | www.wpe64.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.wpe64.com |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
OfficeClickToRun.exe | [2025-05-25 12:23:07.8862194] System.Data.SQLite (Preload): Native library pre-loader is trying to load native SQLite library "C:\Users\admin\AppData\Local\Temp\RarSFX0\x64\SQLite.Interop.dll"...
|