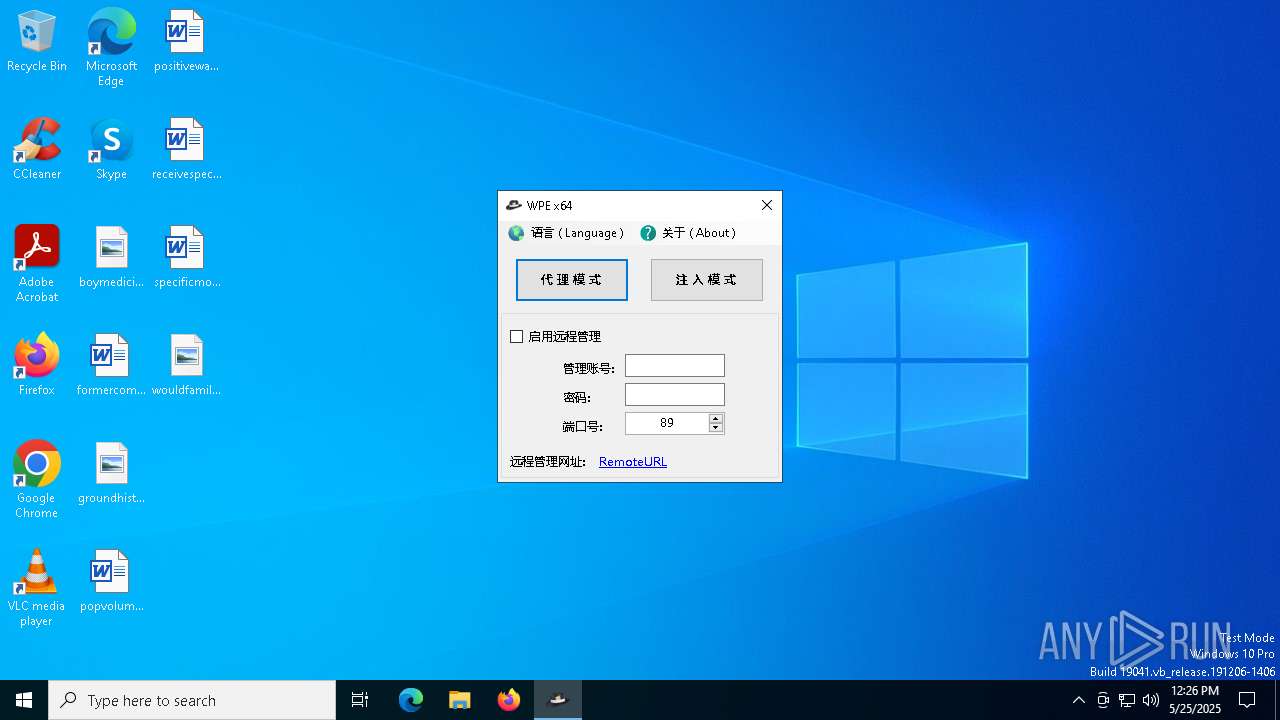
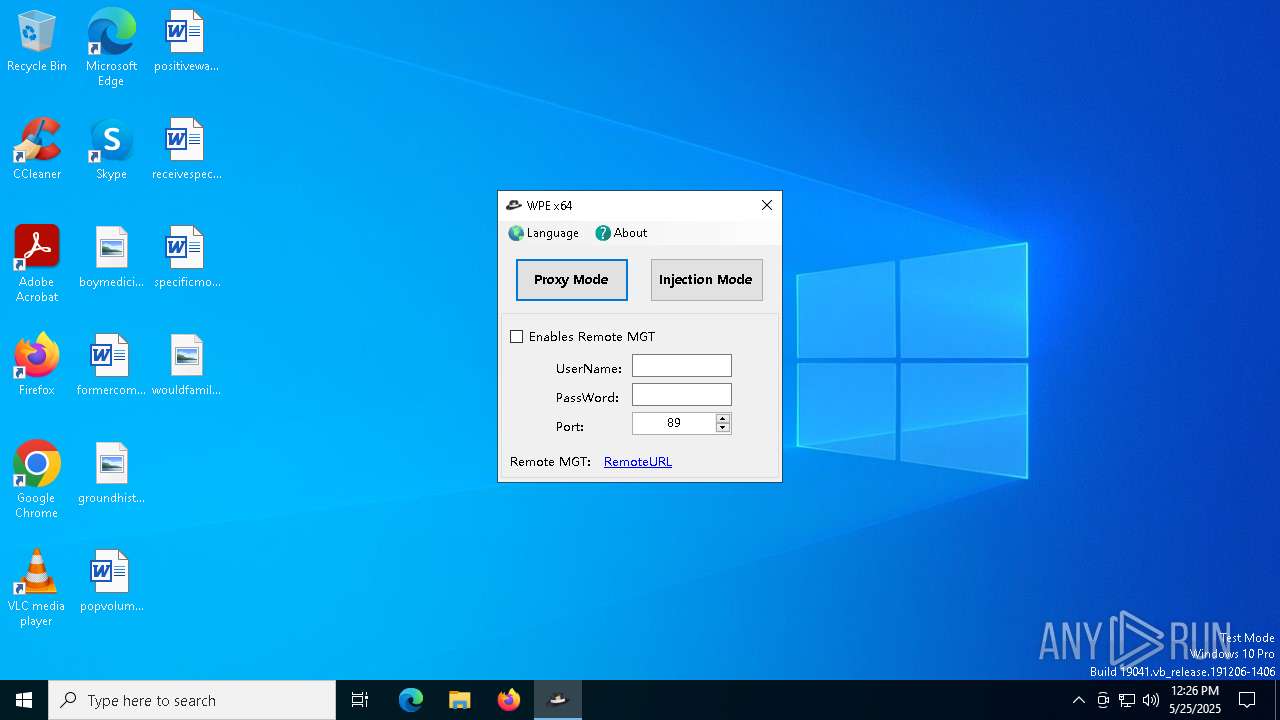
| File name: | WPE64 2.0.0.17.exe |
| Full analysis: | https://app.any.run/tasks/06169149-77d5-4983-b509-832e89462054 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2025, 12:26:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | EE12781D81FD56060F300BACB429D281 |
| SHA1: | F4B70D6BCFBB0F549172CDBD5A9378BC579B08CB |
| SHA256: | C28DFC5F61BD118C48037082757F18BFAA119B1C2DB8C05389A2C6AE510B14FE |
| SSDEEP: | 98304:5ZtMjY6vo5HnfG9M7EbQOnN/Wf+iS4LEltk0dM2ecWIZxvJSe2R/F5OFkg+LM4AR:1n7Xo+M5MEJ0bPQFX/ |
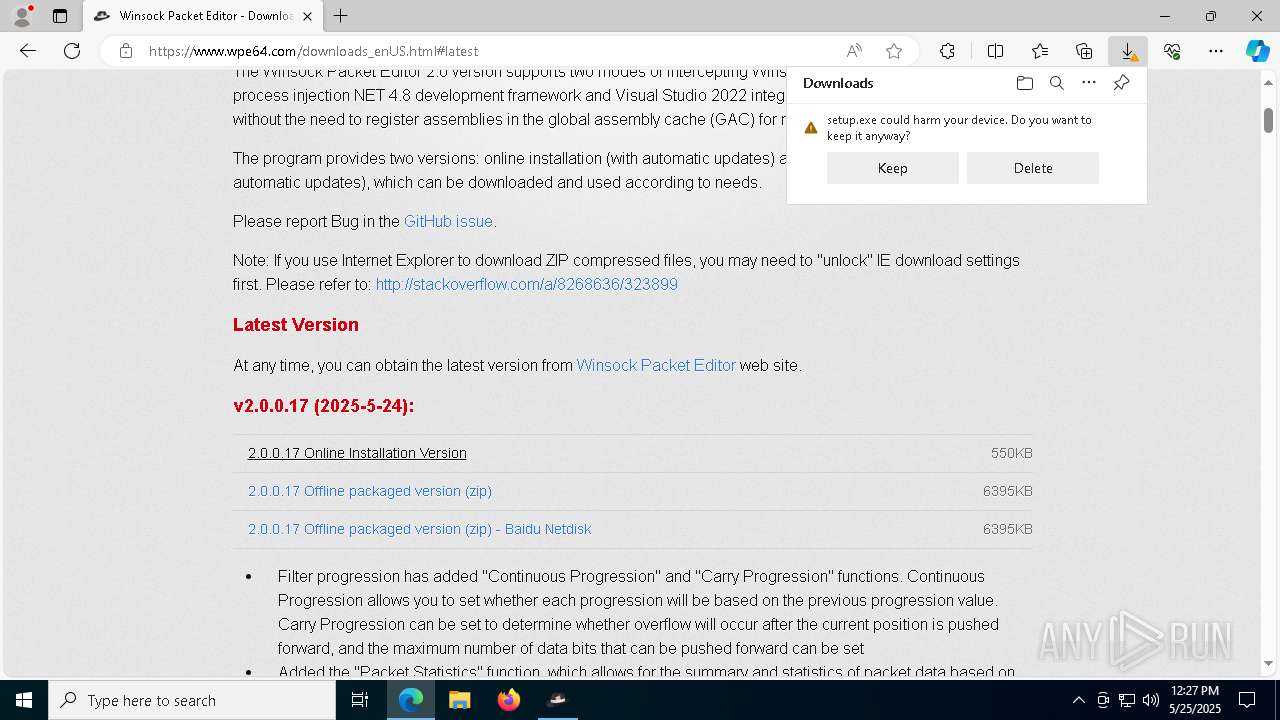
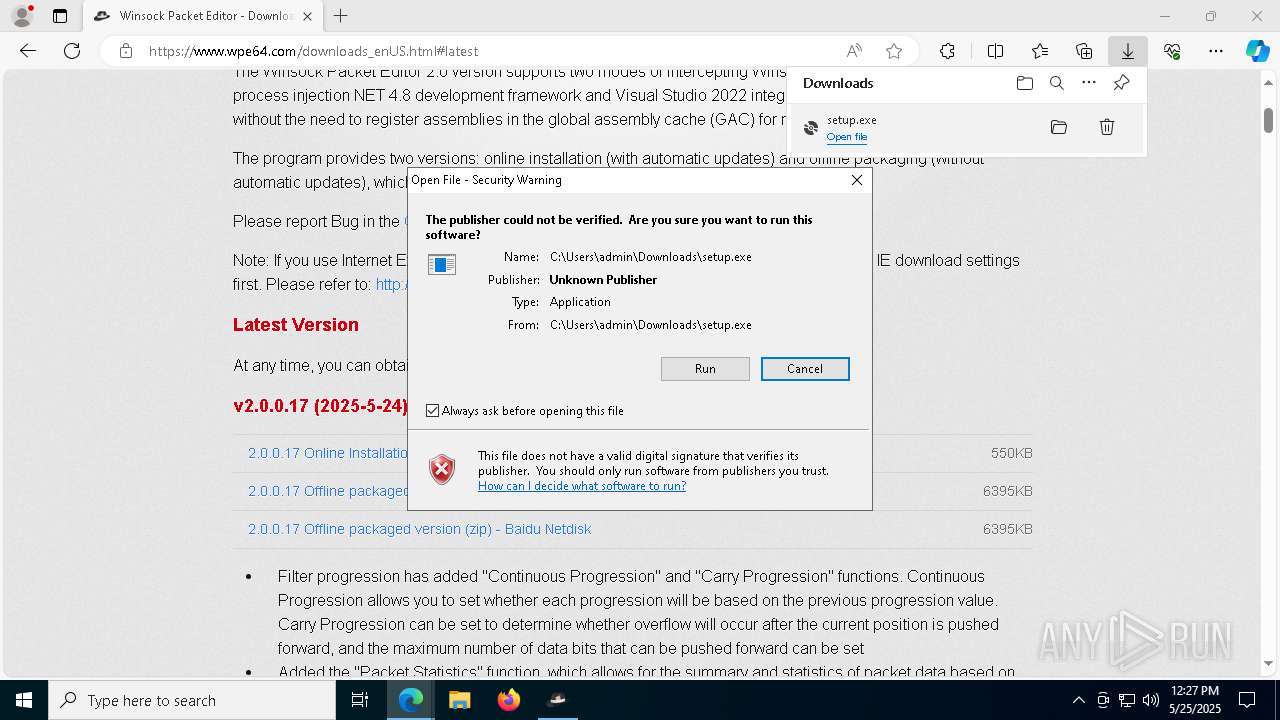
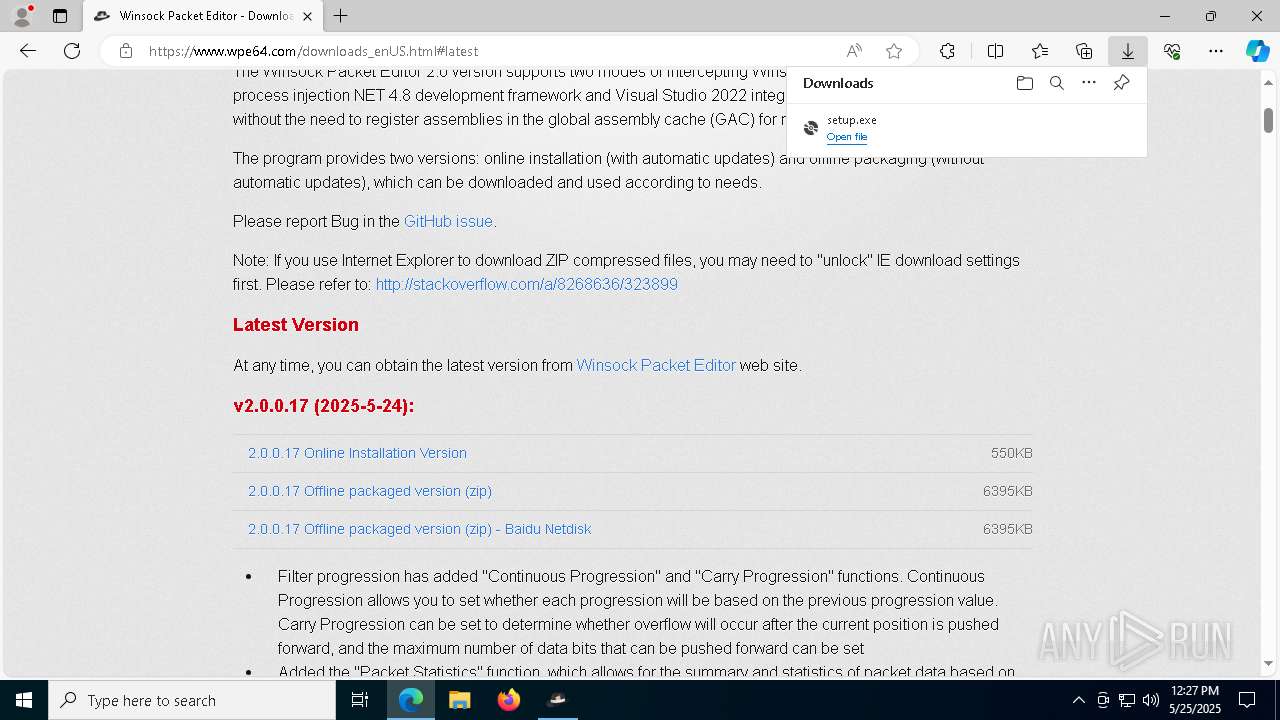
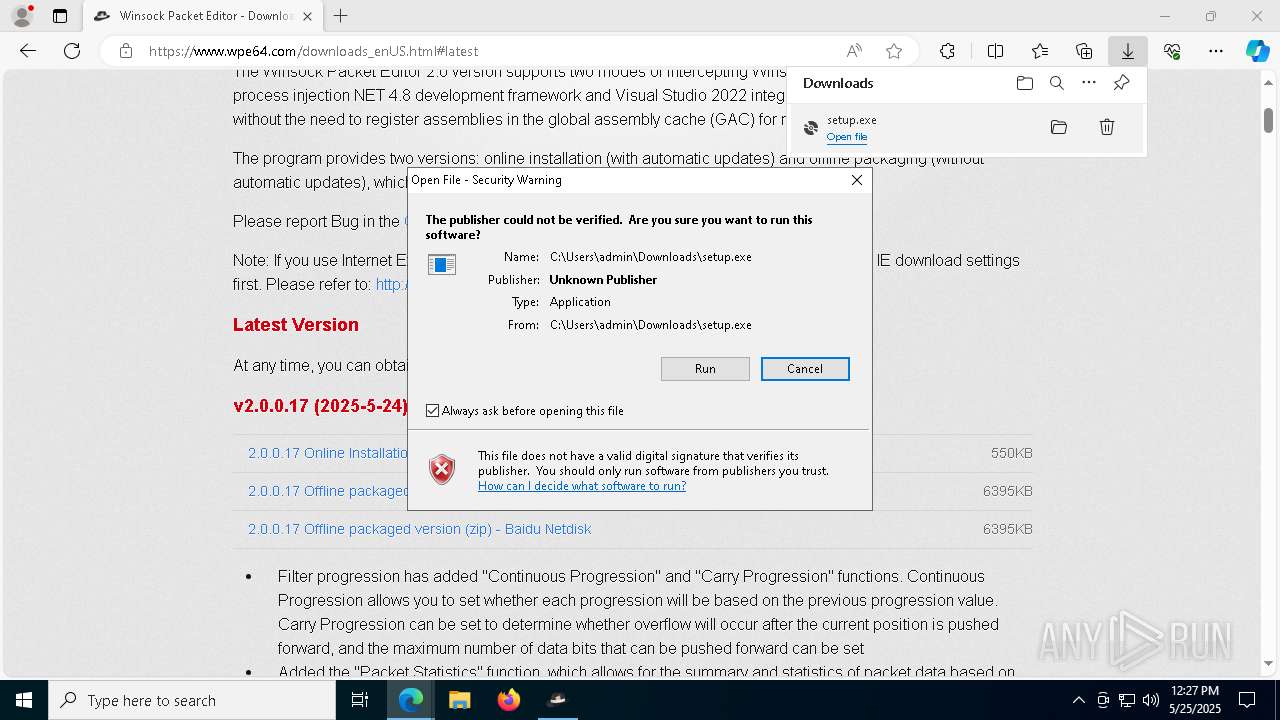
MALICIOUS
Executing a file with an untrusted certificate
- setup.exe (PID: 6488)
- setup.exe (PID: 5400)
SUSPICIOUS
Reads the date of Windows installation
- WPE64 2.0.0.17.exe (PID: 5248)
- WinsockPacketEditor.exe (PID: 6436)
- WinsockPacketEditor.exe (PID: 1184)
Reads security settings of Internet Explorer
- WPE64 2.0.0.17.exe (PID: 5248)
- WinsockPacketEditor.exe (PID: 6436)
- WinsockPacketEditor.exe (PID: 1184)
- setup.exe (PID: 5400)
- WinsockPacketEditor.exe (PID: 4020)
Executable content was dropped or overwritten
- WPE64 2.0.0.17.exe (PID: 5248)
- setup.exe (PID: 5400)
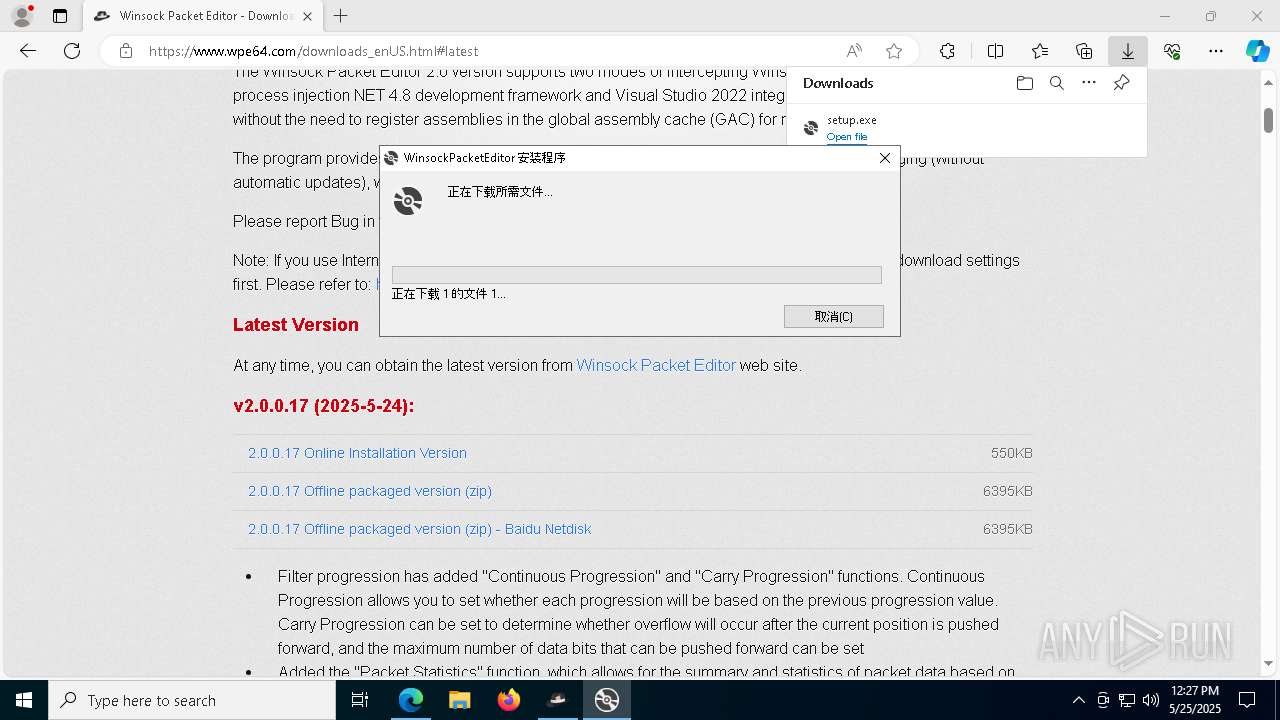
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
Process drops legitimate windows executable
- WPE64 2.0.0.17.exe (PID: 5248)
- setup.exe (PID: 5400)
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
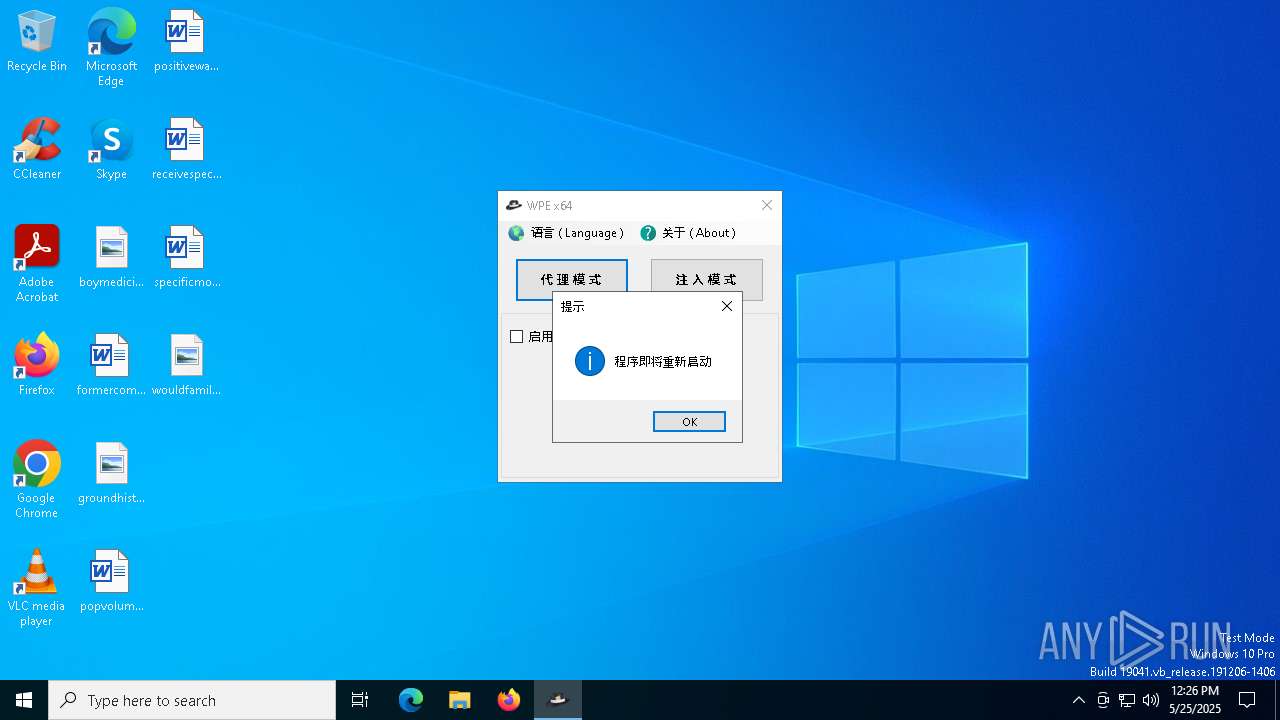
Application launched itself
- WinsockPacketEditor.exe (PID: 6436)
- WinsockPacketEditor.exe (PID: 1184)
Reads Internet Explorer settings
- WinsockPacketEditor.exe (PID: 1184)
- WinsockPacketEditor.exe (PID: 4020)
There is functionality for communication over UDP network (YARA)
- WinsockPacketEditor.exe (PID: 4020)
Creates file in the systems drive root
- msedge.exe (PID: 3032)
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
Starts a Microsoft application from unusual location
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
- NDP48-x86-x64-AllOS-CHS.exe (PID: 4192)
INFO
Process checks computer location settings
- WPE64 2.0.0.17.exe (PID: 5248)
- WinsockPacketEditor.exe (PID: 6436)
- WinsockPacketEditor.exe (PID: 1184)
- setup.exe (PID: 5400)
The sample compiled with english language support
- WPE64 2.0.0.17.exe (PID: 5248)
- msedge.exe (PID: 2892)
- msedge.exe (PID: 3032)
- setup.exe (PID: 5400)
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
Creates files in the program directory
- WinsockPacketEditor.exe (PID: 6436)
Create files in a temporary directory
- WPE64 2.0.0.17.exe (PID: 5248)
- setup.exe (PID: 6488)
- setup.exe (PID: 5400)
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
- Setup.exe (PID: 6060)
Reads the computer name
- WPE64 2.0.0.17.exe (PID: 5248)
- WinsockPacketEditor.exe (PID: 6436)
- WinsockPacketEditor.exe (PID: 1184)
- WinsockPacketEditor.exe (PID: 4020)
- identity_helper.exe (PID: 7356)
- setup.exe (PID: 5400)
- setup.exe (PID: 6488)
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
- Setup.exe (PID: 6060)
Checks supported languages
- WPE64 2.0.0.17.exe (PID: 5248)
- WinsockPacketEditor.exe (PID: 6436)
- WinsockPacketEditor.exe (PID: 1184)
- WinsockPacketEditor.exe (PID: 4020)
- identity_helper.exe (PID: 7356)
- setup.exe (PID: 5400)
- setup.exe (PID: 6488)
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
- Setup.exe (PID: 6060)
Reads the machine GUID from the registry
- WinsockPacketEditor.exe (PID: 6436)
- WinsockPacketEditor.exe (PID: 1184)
- WinsockPacketEditor.exe (PID: 4020)
- setup.exe (PID: 5400)
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
Checks proxy server information
- WinsockPacketEditor.exe (PID: 1184)
- WinsockPacketEditor.exe (PID: 4020)
- setup.exe (PID: 5400)
Disables trace logs
- WinsockPacketEditor.exe (PID: 1184)
- WinsockPacketEditor.exe (PID: 4020)
Reads the software policy settings
- WinsockPacketEditor.exe (PID: 1184)
- WinsockPacketEditor.exe (PID: 4020)
- setup.exe (PID: 5400)
Reads Environment values
- WinsockPacketEditor.exe (PID: 4020)
- WinsockPacketEditor.exe (PID: 1184)
- identity_helper.exe (PID: 7356)
Executable content was dropped or overwritten
- msedge.exe (PID: 2892)
- msedge.exe (PID: 3032)
Application launched itself
- msedge.exe (PID: 5416)
- msedge.exe (PID: 3032)
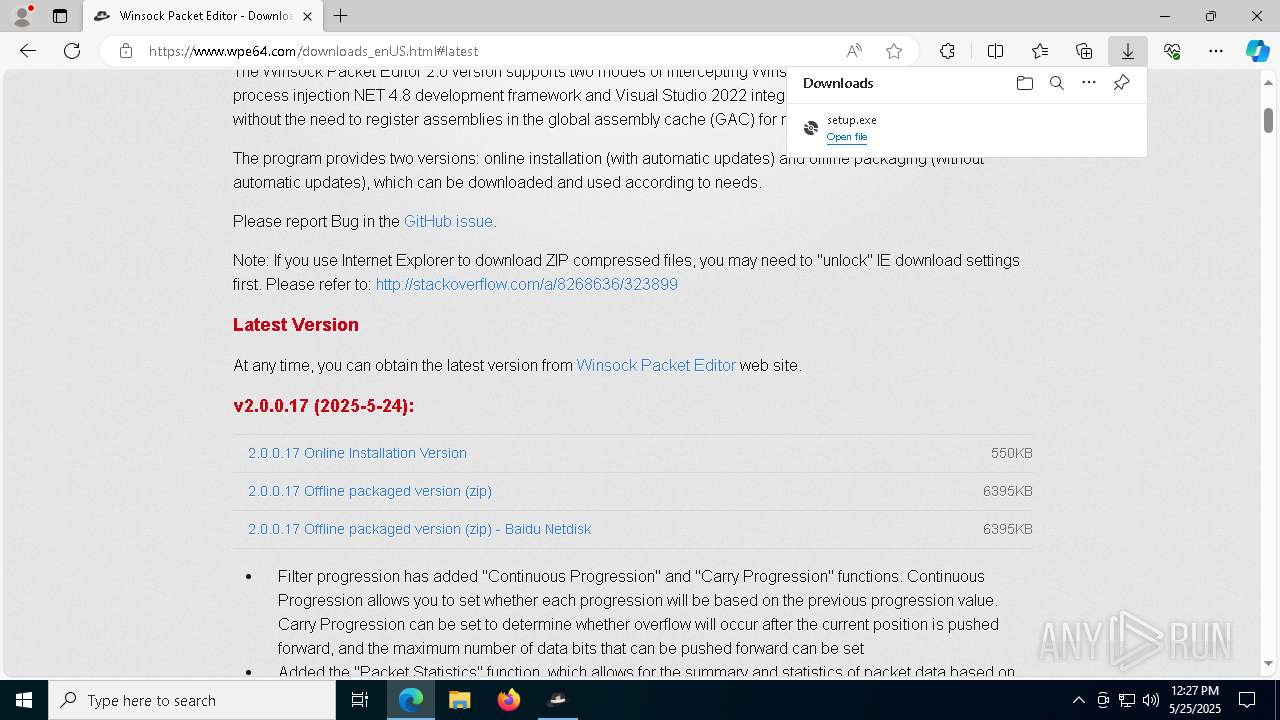
Manual execution by a user
- msedge.exe (PID: 3032)
Creates files or folders in the user directory
- setup.exe (PID: 5400)
Reads CPU info
- Setup.exe (PID: 6060)
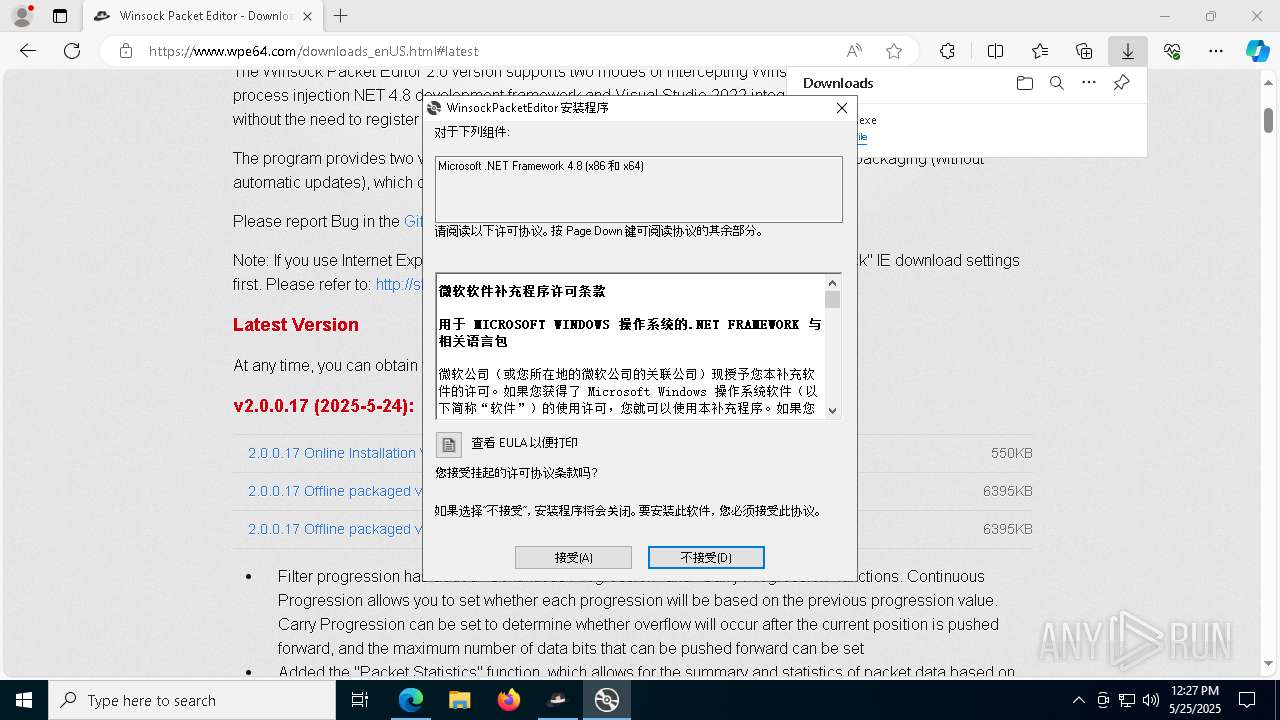
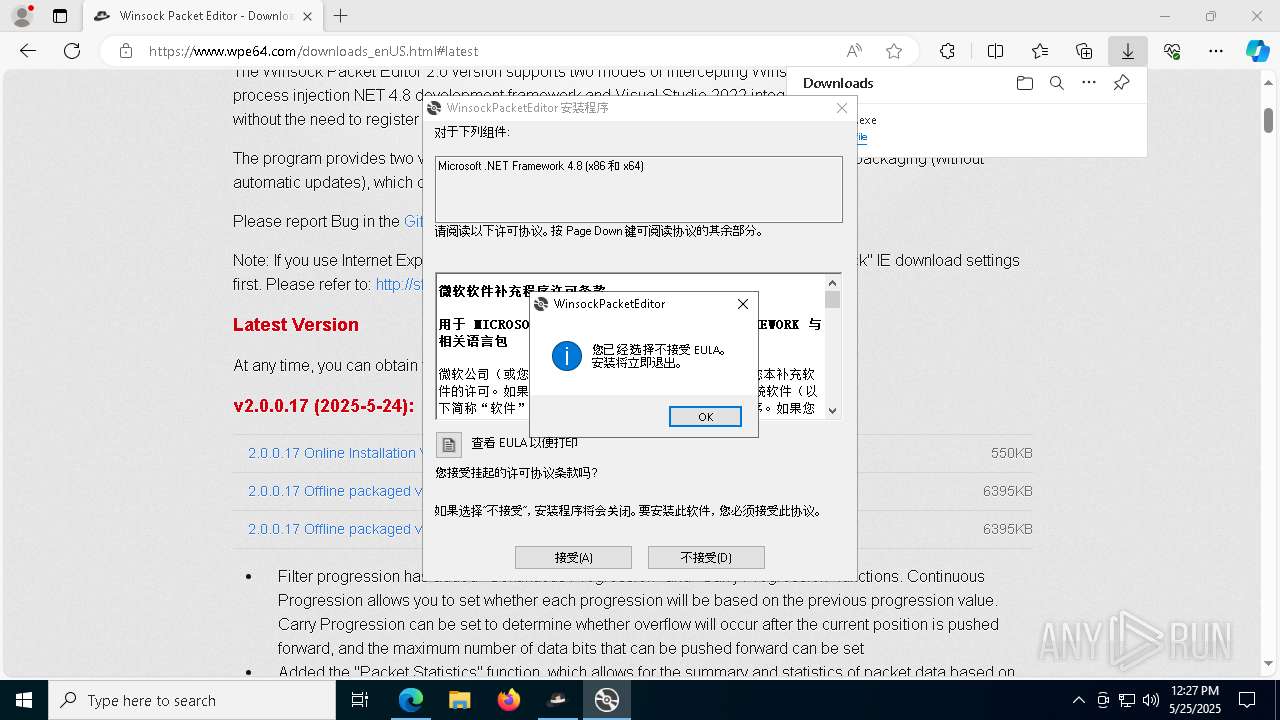
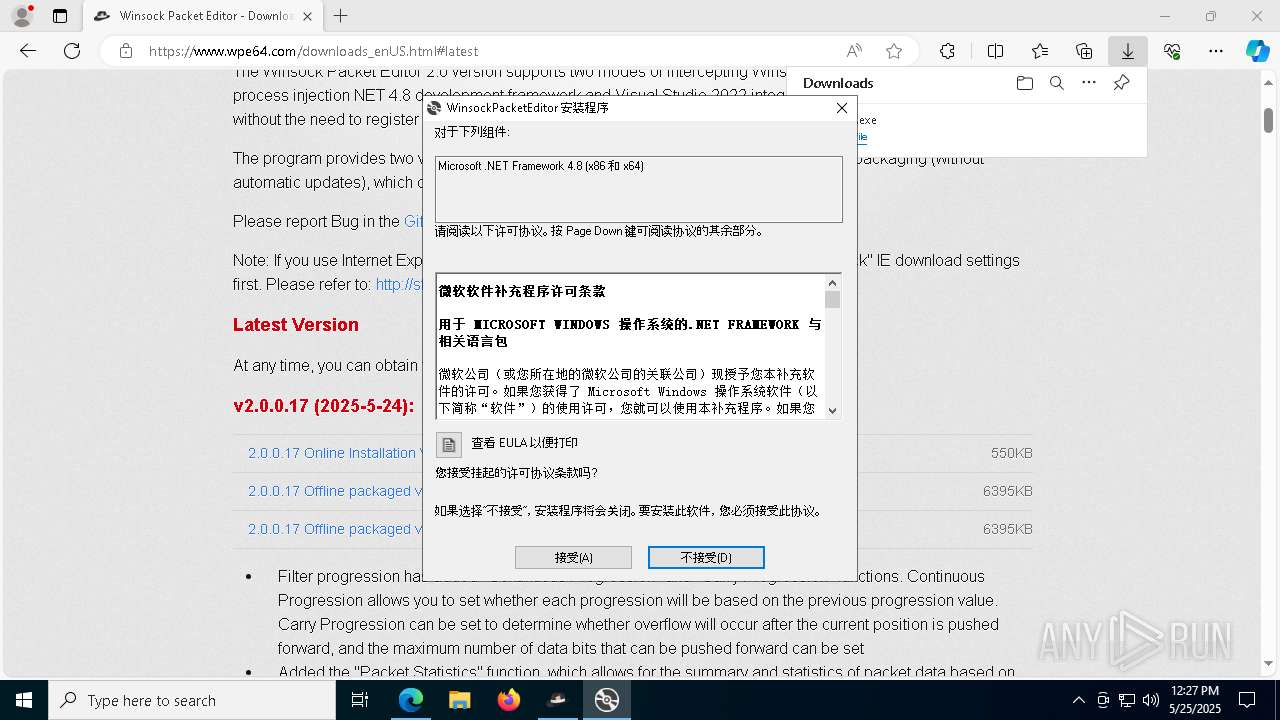
The sample compiled with chinese language support
- NDP48-x86-x64-AllOS-CHS.exe (PID: 5384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:12 14:02:25+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 307200 |
| InitializedDataSize: | 484864 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32680 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
177
Monitored processes
48
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6184 --field-trial-handle=2392,i,5355971784780056598,17622171193801146249,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1184 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe | WinsockPacketEditor.exe | |
User: admin Company: X-NAS Integrity Level: HIGH Description: WinsockPacketEditor Exit code: 4294967295 Version: 2.0.0.17 | ||||
| 1532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7364 --field-trial-handle=2392,i,5355971784780056598,17622171193801146249,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 2892 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2600 --field-trial-handle=2392,i,5355971784780056598,17622171193801146249,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
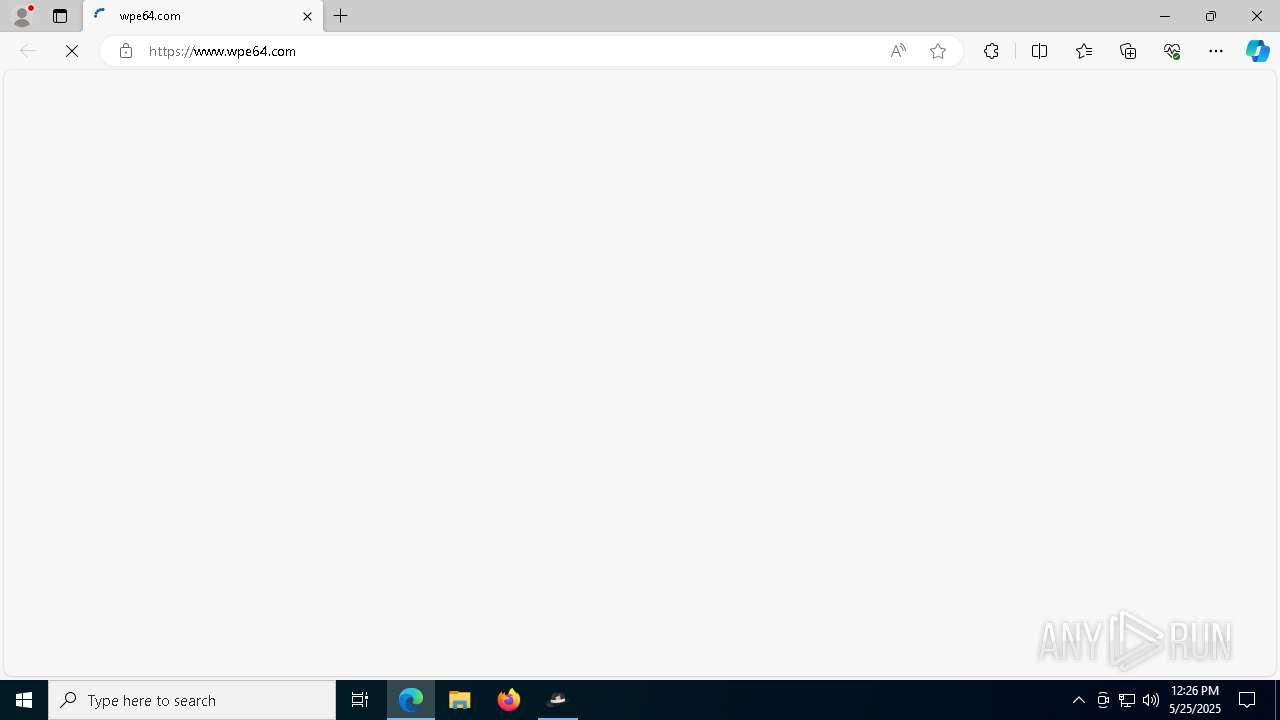
| 3032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --flag-switches-end --do-not-de-elevate --single-argument https://www.wpe64.com/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
| 4020 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\WinsockPacketEditor.exe | WinsockPacketEditor.exe | |
User: admin Company: X-NAS Integrity Level: HIGH Description: WinsockPacketEditor Version: 2.0.0.17 | ||||
| 4172 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x288,0x28c,0x7ffc812b5fd8,0x7ffc812b5fe4,0x7ffc812b5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
| 4192 | "C:\Users\admin\AppData\Local\Temp\VSD6ACD.tmp\DotNetFX48\NDP48-x86-x64-AllOS-CHS.exe" /q /norestart /skipenucheck /ChainingPackage FullX64ClickOnce | C:\Users\admin\AppData\Local\Temp\VSD6ACD.tmp\DotNetFX48\NDP48-x86-x64-AllOS-CHS.exe | — | setup.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.8 (CHS) Setup Exit code: 3221226540 Version: 4.8.03761.00 | ||||
| 4776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x310,0x314,0x318,0x308,0x320,0x7ffc812b5fd8,0x7ffc812b5fe4,0x7ffc812b5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 5228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7412 --field-trial-handle=2392,i,5355971784780056598,17622171193801146249,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
56
Suspicious files
100
Text files
113
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EasyHook.xml | xml | |
MD5:49E0E6169CA5BF10810FF0A404C3D11E | SHA256:CB35AAA4A765D65FEBFA269E7D68994D4FAC1F8D5A456FFF8A3757B5032ACEF8 | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Be.Windows.Forms.HexBox.xml | xml | |
MD5:B534569D28458990C1B2F68EAFA60BC3 | SHA256:415EA2D9A22AB58E5F89ECE1CAF45FD61F2579EF0C700C990A997841F284E4E3 | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Be.Windows.Forms.HexBox.dll | executable | |
MD5:1ABB997D4E809B9D7F9016617DC01294 | SHA256:4938A4DBB51FD8D35DFDF2C5D42E9A127B9365D495461864E6BB9EC7FC9A3CB7 | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EasyHook32Svc.exe | executable | |
MD5:828B9A7AE0651E0F690C00816EEC1A94 | SHA256:9CFDA284E280CF9C6AFEB2D3016D78BEDA4E5B3CBAAF893684B569F5C246B99E | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EasyHook64.dll | executable | |
MD5:163C08C9333279DF7BC4788CF53A0990 | SHA256:03E75032981FD6152F4D9EE18D321BF553F9191F254F326DE87B9AD0AF0B8CED | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EasyHook32.dll | executable | |
MD5:42ACE4B57A5646B62D838D573CBE4CDB | SHA256:FEA2C5634555D29FBAE098D6EA7DDAB927B25D4CE68B4D877AA35FF3DA7E9E51 | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Microsoft.Owin.dll | executable | |
MD5:C24CF68C9012B4E261D2FD6B2240BBE8 | SHA256:42ED395C54526DAD6AA275CA2A65F6DE6E94BC8CEC8548CFB9891BA430FF1974 | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Microsoft.Owin.FileSystems.dll | executable | |
MD5:B5F2D52FA39BF821120A7C294B8CFB62 | SHA256:B6544BB3A14FAE2765980D21FFF9D63DF0CDEA116D69BE9A7E56B57ACCE7728B | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\EntityFramework.SqlServer.xml | xml | |
MD5:2D1549C365902D6CBEE20E02A985B68B | SHA256:902F57044BAF104DD9A491DADCBA4C787B6F64531880DC3B11345D5758D7BD81 | |||
| 5248 | WPE64 2.0.0.17.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\Microsoft.Owin.Hosting.dll | executable | |
MD5:056A3B1C036A46447EBCA7083DA271A5 | SHA256:6BEDFFF38EB390D01F0D51340B7B4F8F7B3D1C1C6CEE8888C0A8088EDA19283D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
72
DNS requests
58
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7860 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5400 | setup.exe | GET | 302 | 95.100.186.9:80 | http://go.microsoft.com/fwlink/?LinkId=2053984&clcid=0x804 | unknown | — | — | whitelisted |
7860 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5400 | setup.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5400 | setup.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5400 | setup.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6384 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5796 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1184 | WinsockPacketEditor.exe | 101.132.222.195:443 | www.wpe64.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4020 | WinsockPacketEditor.exe | 101.132.222.195:443 | www.wpe64.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.wpe64.com |
| unknown |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2892 | msedge.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
2892 | msedge.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |