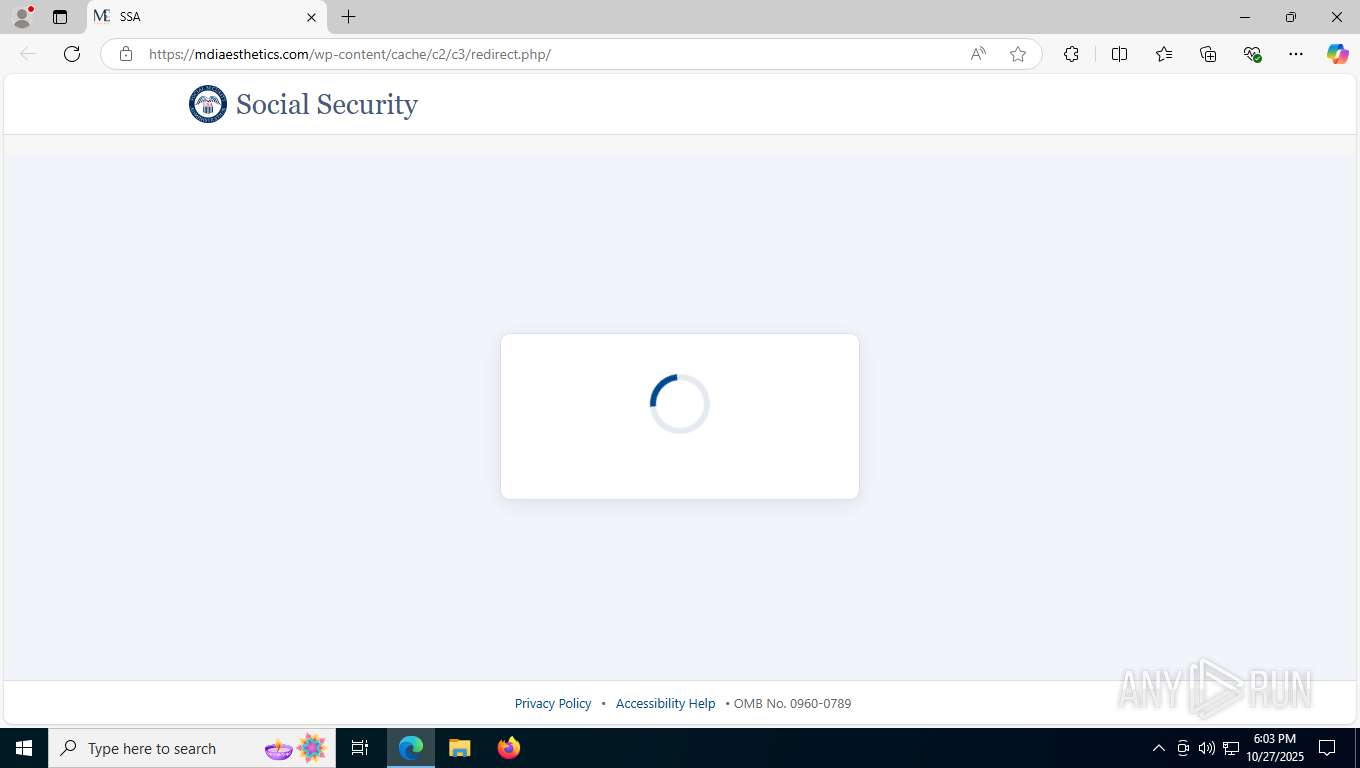
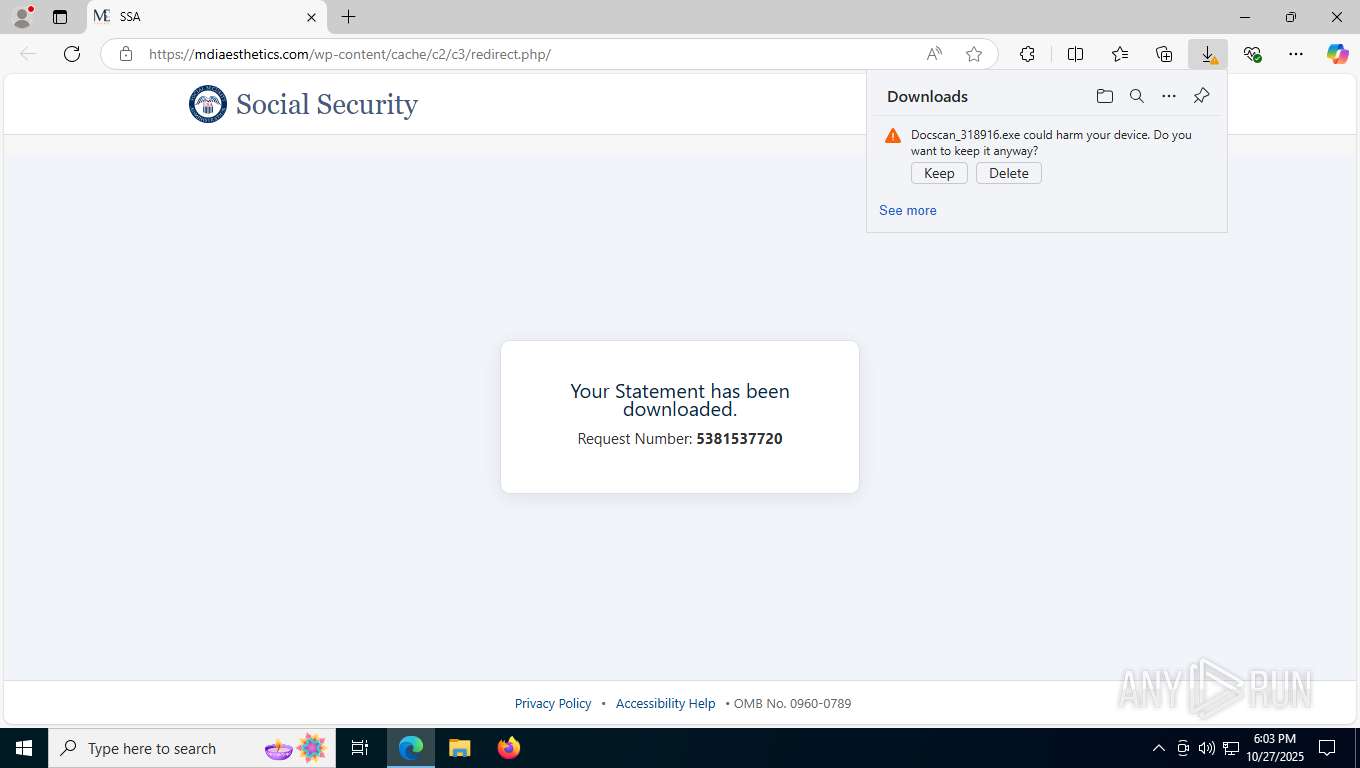
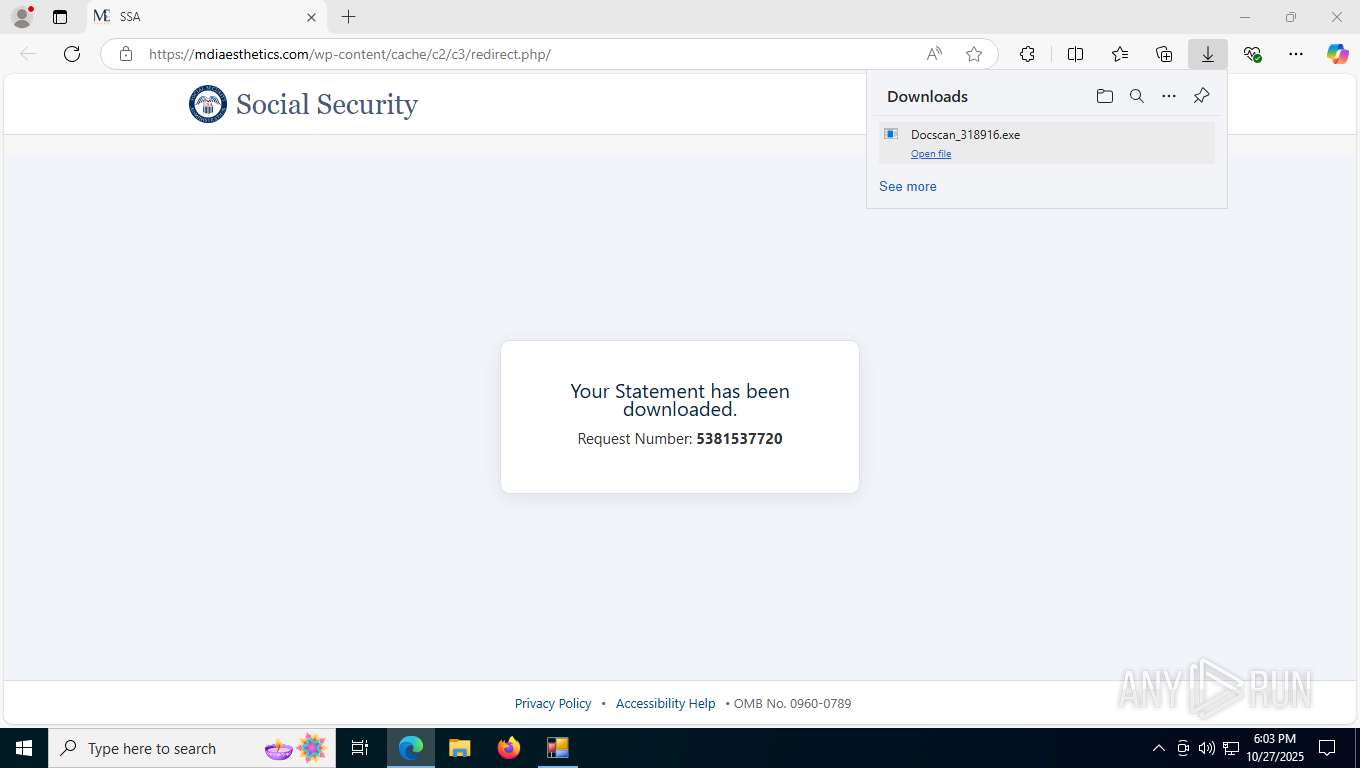
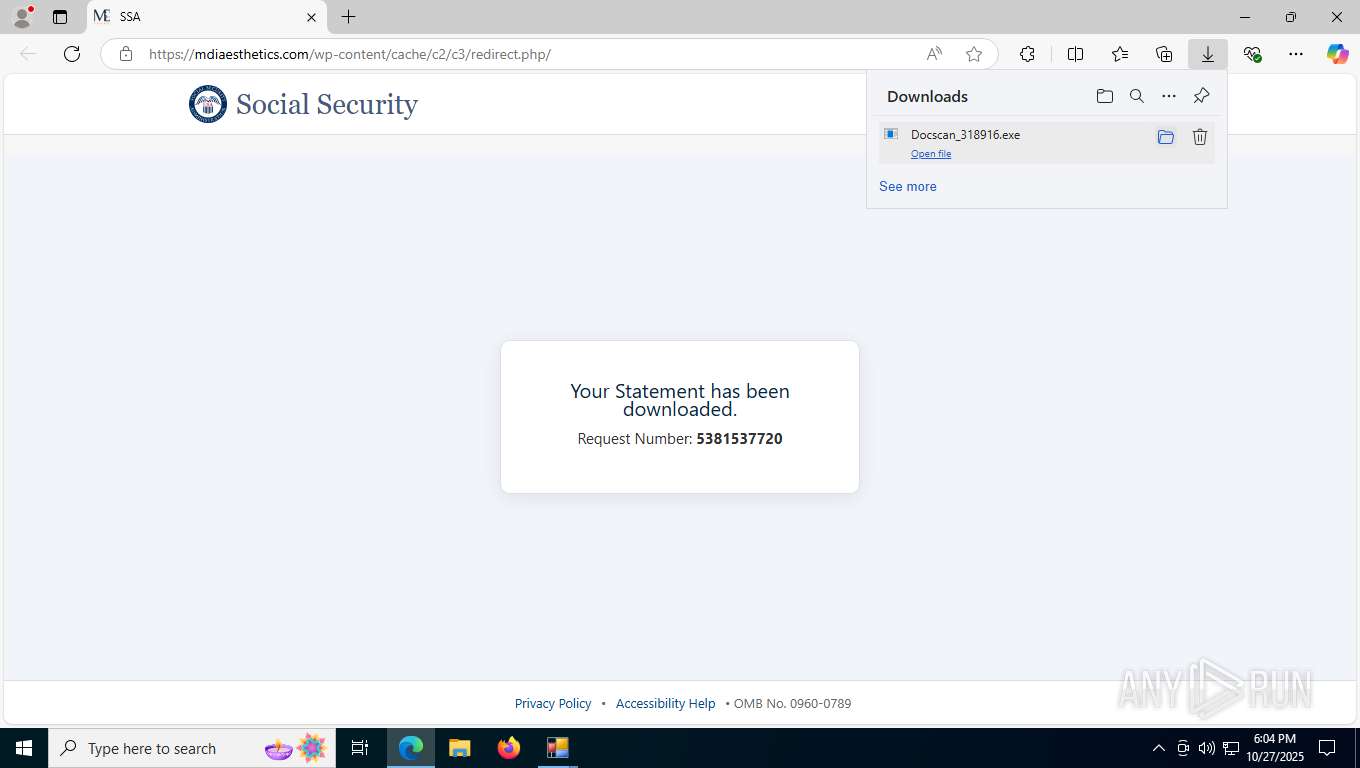
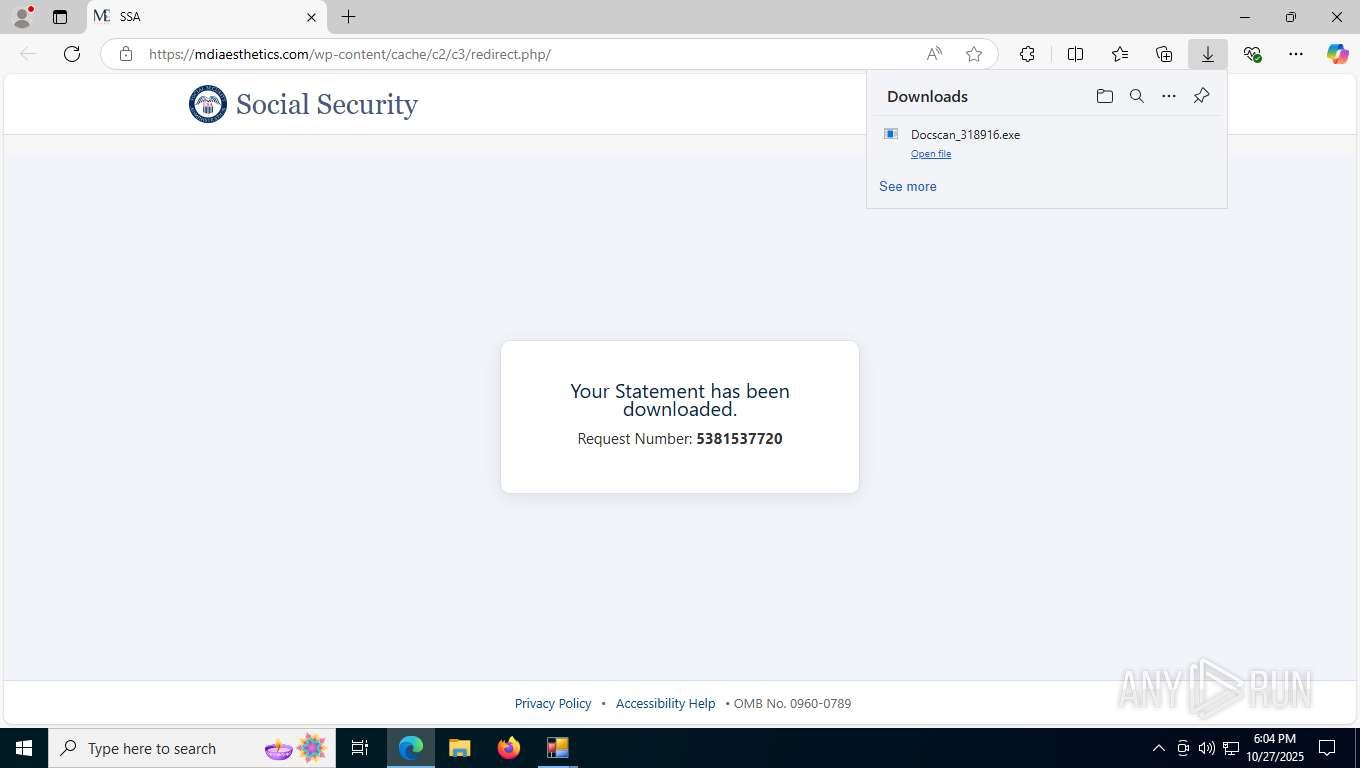
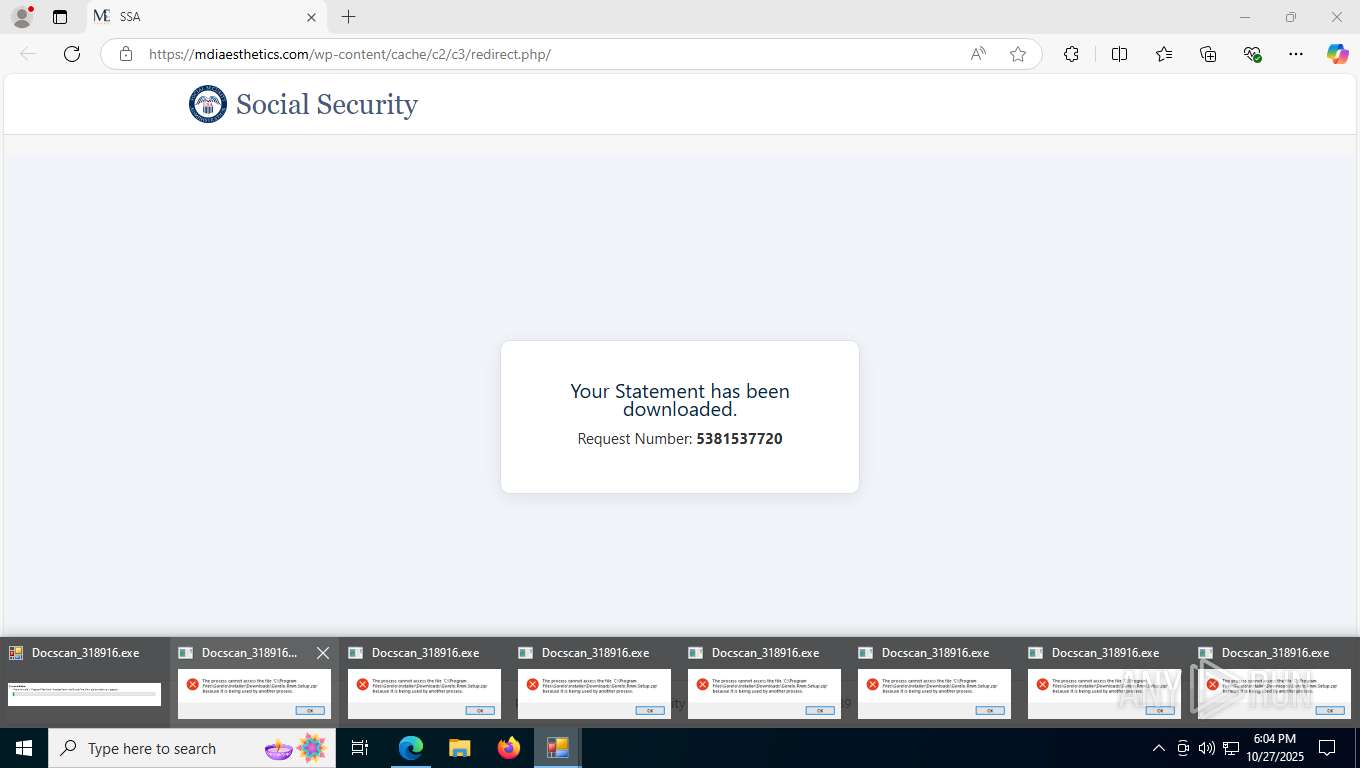
| URL: | https://mdiaesthetics.com/wp-content/cache/c2/c3/redirect.php/ |
| Full analysis: | https://app.any.run/tasks/aa34a814-d48c-485b-96f7-d8cc71053e3c |
| Verdict: | Malicious activity |
| Analysis date: | October 27, 2025, 18:03:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D261DBD5EE6CAD7E801056F5E98CDACA |
| SHA1: | 9853BB0D1EB82595C5C257F06F30C88DD346AF4D |
| SHA256: | C2785E6399E006E3C30F107A9BF454E6B5034C548D195D5BBF0CCBF3CA2CC859 |
| SSDEEP: | 3:N8rEYqkFVOlAQTLKJ8XLqn:2d/VOlAILKGLqn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 8368)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
Checks a user's role membership (POWERSHELL)
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 8368)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
Gets file extension (POWERSHELL)
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
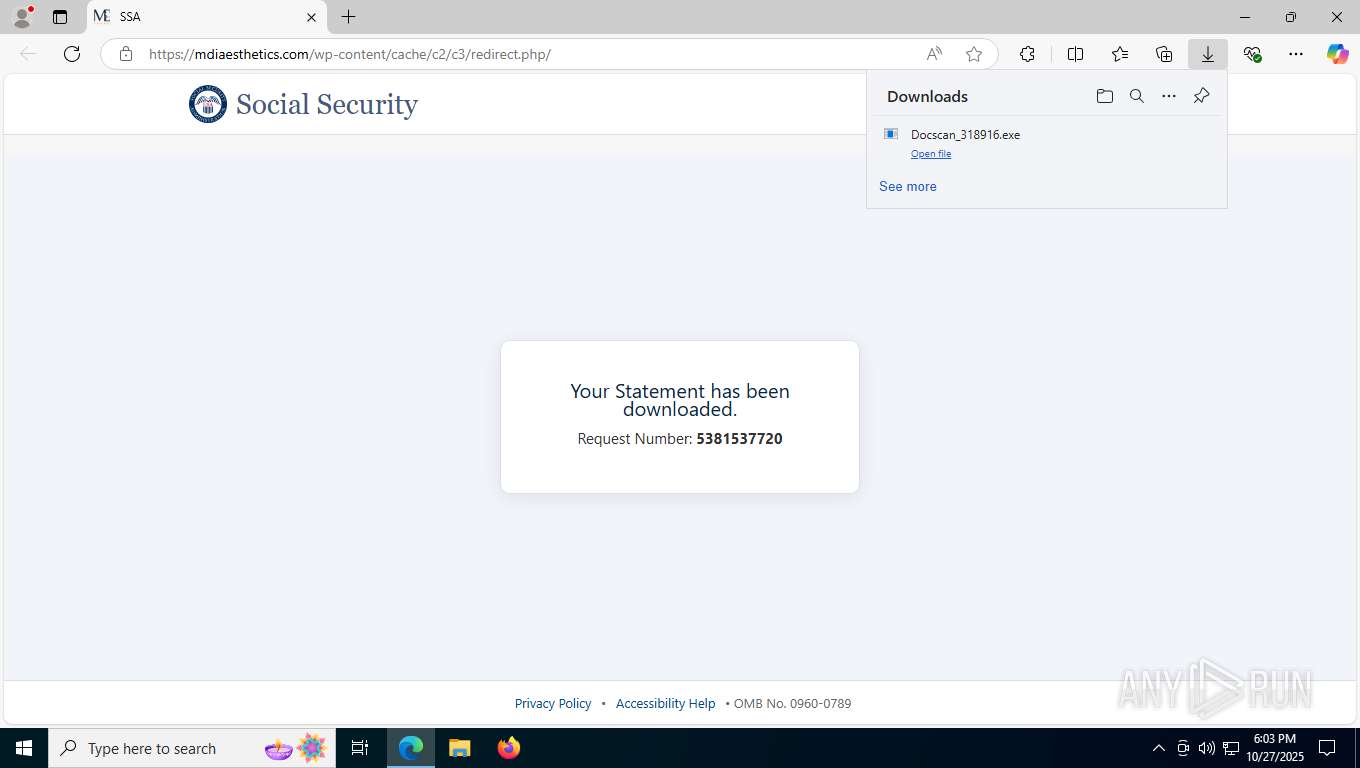
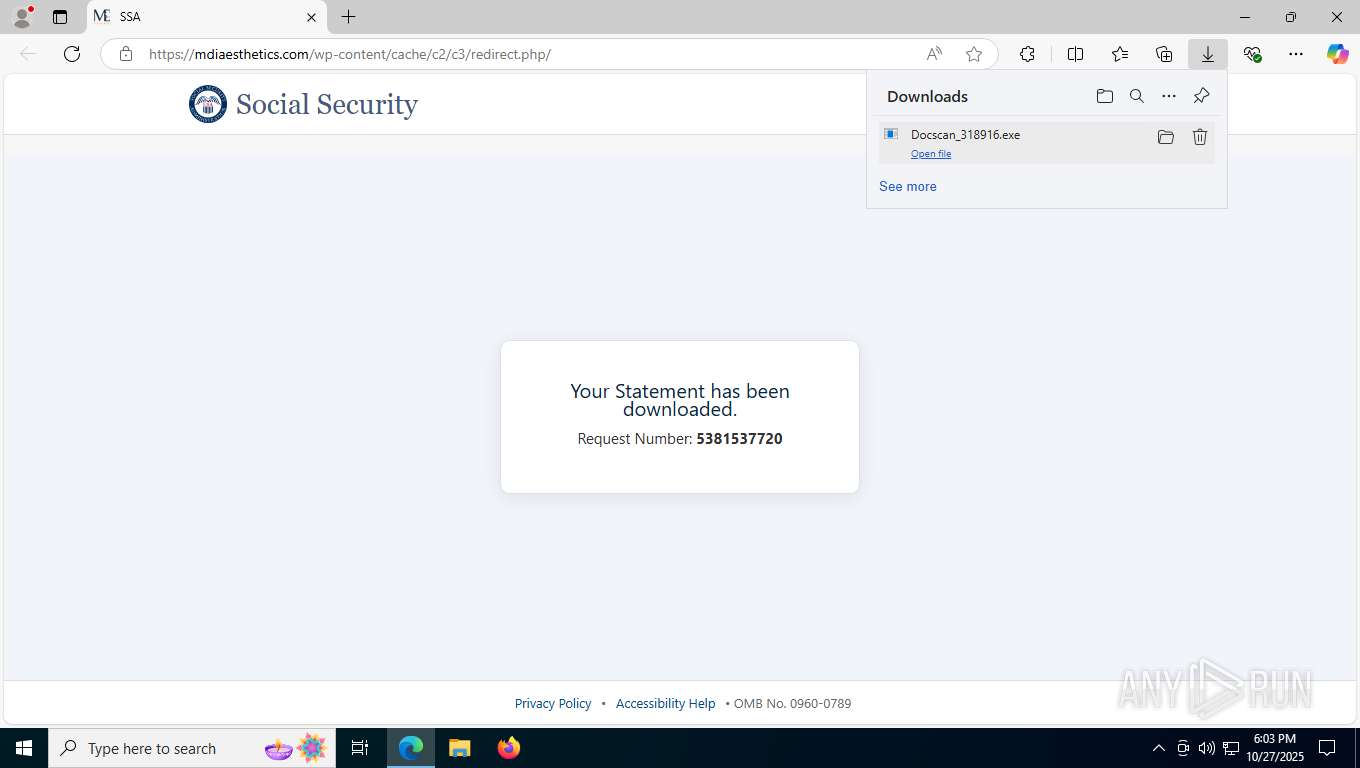
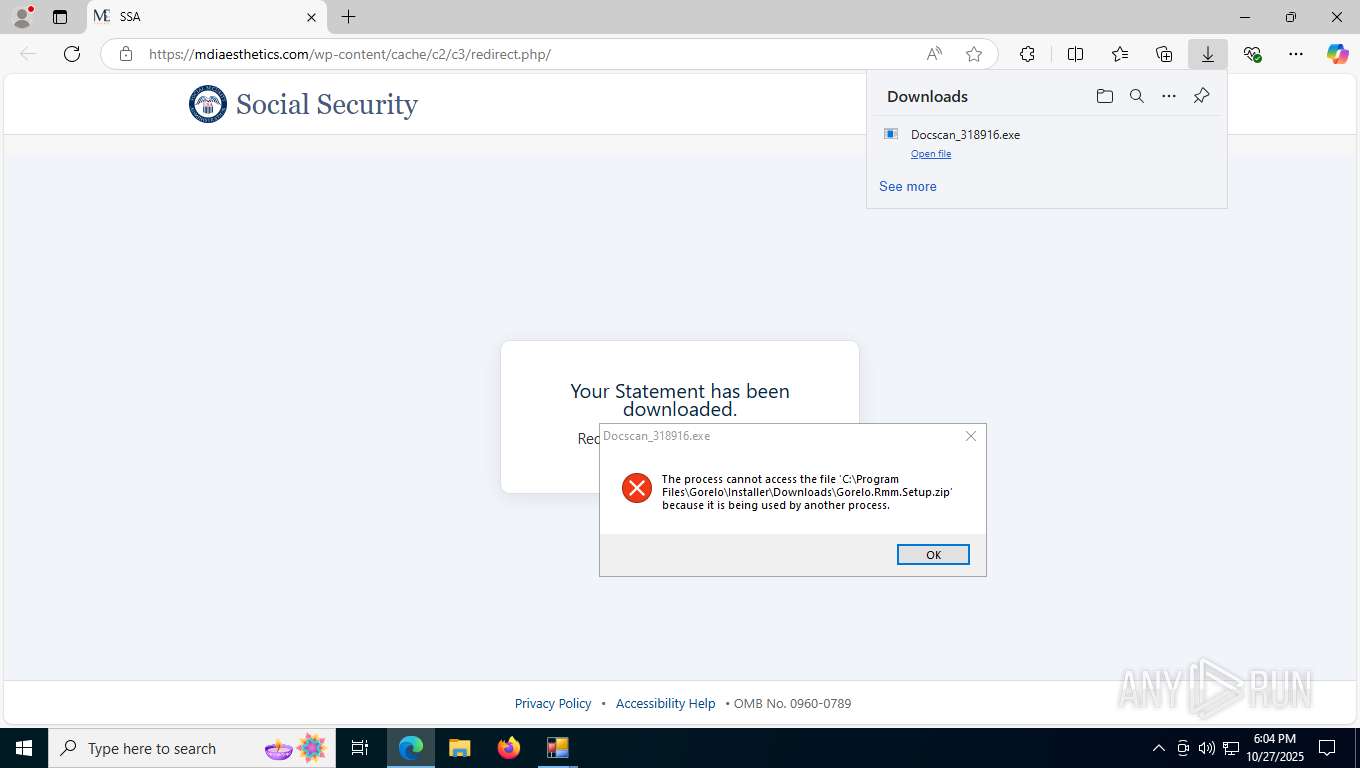
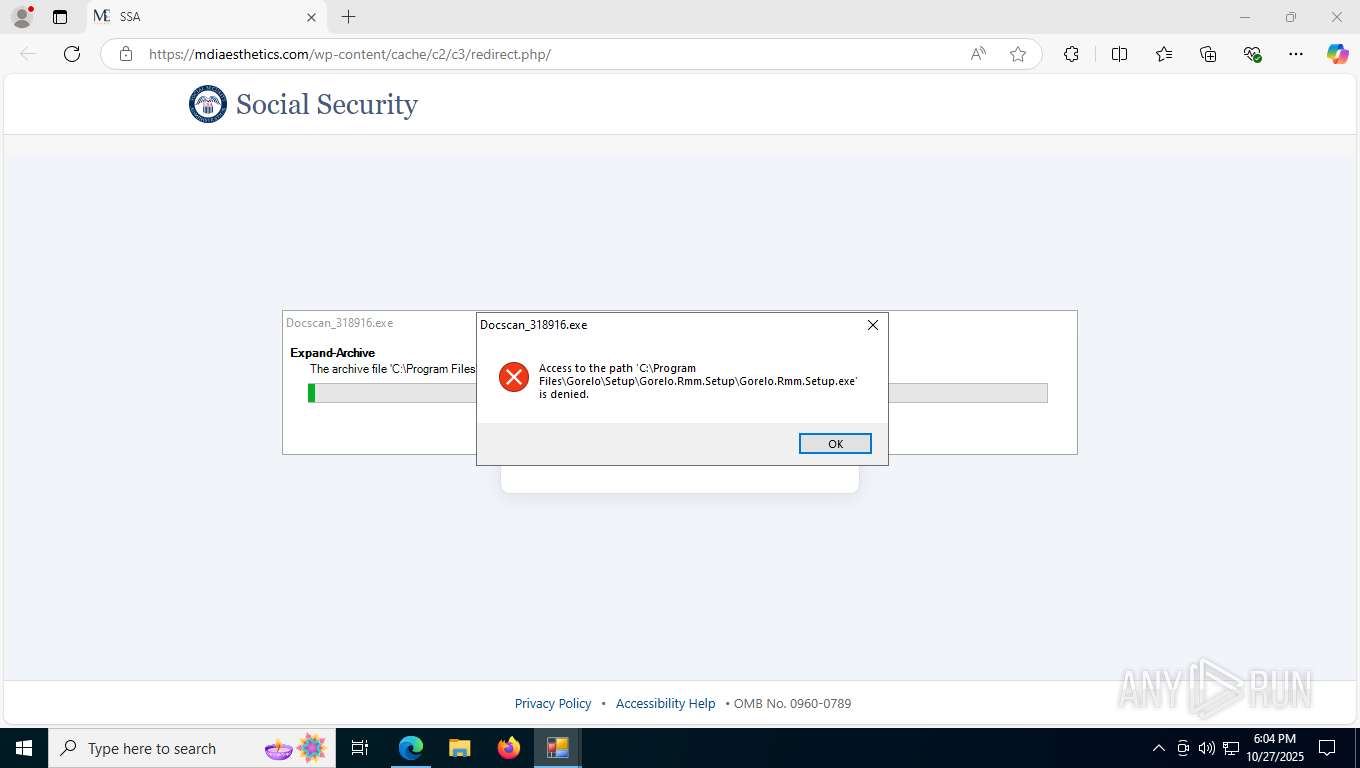
Executable content was dropped or overwritten
- Docscan_318916.exe (PID: 2976)
- Gorelo.Rmm.Installer.exe (PID: 5192)
Reads the date of Windows installation
- Docscan_318916.exe (PID: 2976)
Windows service management via SC.EXE
- sc.exe (PID: 7192)
- sc.exe (PID: 7192)
Starts SC.EXE for service management
- cmd.exe (PID: 5664)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 9176)
Starts CMD.EXE for commands execution
- Gorelo.Rmm.Setup.exe (PID: 5080)
- Gorelo.Rmm.Installer.exe (PID: 5192)
Creates a new Windows service
- sc.exe (PID: 5320)
- sc.exe (PID: 8996)
Executes as Windows Service
- Gorelo.Rmm.Installer.exe (PID: 5192)
- Gorelo.RemoteManagement.Shell.exe (PID: 5696)
Non windows owned service launched
- Gorelo.Rmm.Installer.exe (PID: 5192)
- Gorelo.RemoteManagement.Shell.exe (PID: 5696)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5664)
Uses WMIC.EXE to obtain Windows Installer data
- Gorelo.Rmm.Installer.Handler.exe (PID: 8576)
- Gorelo.Rmm.Installer.Handler.exe (PID: 1236)
- Gorelo.RemoteManagement.Agent.exe (PID: 8524)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 8932)
- WMIC.exe (PID: 9344)
- WMIC.exe (PID: 6224)
Starts POWERSHELL.EXE for commands execution
- Gorelo.Rmm.Installer.Handler.exe (PID: 8576)
- Gorelo.Rmm.Installer.exe (PID: 5192)
- Gorelo.Rmm.Installer.Handler.exe (PID: 1236)
- Gorelo.RemoteManagement.Agent.exe (PID: 8524)
The process creates files with name similar to system file names
- Gorelo.Rmm.Installer.exe (PID: 5192)
Process drops legitimate windows executable
- Gorelo.RemoteManagement.Agent.exe (PID: 8524)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 7832)
- msedge.exe (PID: 7484)
Reads Environment values
- identity_helper.exe (PID: 6388)
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 8368)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
- identity_helper.exe (PID: 5612)
Reads the computer name
- identity_helper.exe (PID: 6388)
- Docscan_318916.exe (PID: 2976)
- Gorelo.Rmm.Setup.exe (PID: 5080)
- Docscan_318916.exe (PID: 7252)
- Gorelo.Rmm.Installer.exe (PID: 5192)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 8368)
- Gorelo.Rmm.Installer.Handler.exe (PID: 8576)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
- Gorelo.Rmm.Installer.Handler.exe (PID: 1236)
- identity_helper.exe (PID: 5612)
- Gorelo.RemoteManagement.Shell.exe (PID: 5696)
- Gorelo.RemoteManagement.Agent.exe (PID: 8524)
Checks supported languages
- identity_helper.exe (PID: 6388)
- Docscan_318916.exe (PID: 2976)
- Gorelo.Rmm.Setup.exe (PID: 5080)
- Docscan_318916.exe (PID: 7252)
- Gorelo.Rmm.Installer.exe (PID: 5192)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 8368)
- Gorelo.Rmm.Installer.Handler.exe (PID: 8576)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
- Gorelo.RemoteManagement.Shell.exe (PID: 5696)
- Gorelo.Rmm.Installer.Handler.exe (PID: 1236)
- identity_helper.exe (PID: 5612)
- Gorelo.RemoteManagement.Agent.exe (PID: 8524)
Launching a file from the Downloads directory
- msedge.exe (PID: 7484)
Create files in a temporary directory
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
- Docscan_318916.exe (PID: 8368)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
Reads the machine GUID from the registry
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
- Docscan_318916.exe (PID: 8368)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
Application launched itself
- msedge.exe (PID: 7484)
Disables trace logs
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 8368)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
Creates files in the program directory
- Docscan_318916.exe (PID: 2976)
- Gorelo.Rmm.Setup.exe (PID: 5080)
- Gorelo.Rmm.Installer.exe (PID: 5192)
- Docscan_318916.exe (PID: 7252)
- Gorelo.Rmm.Installer.Handler.exe (PID: 8576)
- Gorelo.RemoteManagement.Shell.exe (PID: 5696)
- Gorelo.RemoteManagement.Agent.exe (PID: 8524)
Checks proxy server information
- Docscan_318916.exe (PID: 2976)
- Gorelo.Rmm.Setup.exe (PID: 5080)
- Docscan_318916.exe (PID: 7252)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 8368)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 8304)
Checks if a key exists in the options dictionary (POWERSHELL)
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
Reads the software policy settings
- Docscan_318916.exe (PID: 2976)
- Gorelo.Rmm.Setup.exe (PID: 5080)
- Gorelo.Rmm.Installer.exe (PID: 5192)
- Docscan_318916.exe (PID: 7252)
- Docscan_318916.exe (PID: 7648)
- Docscan_318916.exe (PID: 8368)
- Gorelo.Rmm.Installer.Handler.exe (PID: 8576)
- Docscan_318916.exe (PID: 4972)
- Docscan_318916.exe (PID: 4736)
- Docscan_318916.exe (PID: 9180)
- Docscan_318916.exe (PID: 8264)
- Gorelo.RemoteManagement.Shell.exe (PID: 5696)
- Gorelo.Rmm.Installer.Handler.exe (PID: 1236)
- Docscan_318916.exe (PID: 8304)
- Gorelo.RemoteManagement.Agent.exe (PID: 8524)
Process checks computer location settings
- Docscan_318916.exe (PID: 2976)
- Gorelo.Rmm.Installer.exe (PID: 5192)
- Gorelo.Rmm.Installer.Handler.exe (PID: 8576)
- Gorelo.RemoteManagement.Shell.exe (PID: 5696)
- Gorelo.RemoteManagement.Agent.exe (PID: 8524)
- Gorelo.Rmm.Installer.Handler.exe (PID: 1236)
Checks whether the specified file exists (POWERSHELL)
- Docscan_318916.exe (PID: 2976)
- Docscan_318916.exe (PID: 7252)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8932)
- WMIC.exe (PID: 6224)
- WMIC.exe (PID: 9344)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
253
Monitored processes
109
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5244,i,9278793589918561653,15507875369315856855,262144 --variations-seed-version --mojo-platform-channel-handle=6240 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Docscan_318916.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Gorelo\Installer\Gorelo.Rmm.Installer.Handler\Gorelo.Rmm.Installer.Handler.exe" 2776 | C:\Program Files\Gorelo\Installer\Gorelo.Rmm.Installer.Handler\Gorelo.Rmm.Installer.Handler.exe | Gorelo.Rmm.Installer.exe | ||||||||||||
User: SYSTEM Company: Gorelo.Rmm.Installer.Handler Integrity Level: SYSTEM Description: Gorelo.Rmm.Installer.Handler Version: 1.70.0.0 Modules
| |||||||||||||||
| 1364 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Gorelo.Rmm.Installer.Handler.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1548 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Docscan_318916.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\WINDOWS\system32\HOSTNAME.EXE" | C:\Windows\System32\HOSTNAME.EXE | — | Docscan_318916.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Hostname APP Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5428,i,9278793589918561653,15507875369315856855,262144 --variations-seed-version --mojo-platform-channel-handle=5528 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6448,i,9278793589918561653,15507875369315856855,262144 --variations-seed-version --mojo-platform-channel-handle=6152 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2336 | "C:\WINDOWS\system32\HOSTNAME.EXE" | C:\Windows\System32\HOSTNAME.EXE | — | Docscan_318916.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Hostname APP Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
62 268
Read events
62 239
Write events
23
Delete events
6
Modification events
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2976) Docscan_318916.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Docscan_318916_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
14
Suspicious files
241
Text files
85
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfb925.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfb935.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfb935.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfb944.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfb954.TMP | — | |
MD5:— | SHA256:— | |||
| 7484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfb944.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
110
DNS requests
69
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7832 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:2YKB8dG-Y535OQRrYp9l_utLJcxyaGvuK6DX9-y7fkg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4220 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
456 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
456 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
456 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4220 | svchost.exe | 20.190.160.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5256 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7832 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7832 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7832 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7832 | msedge.exe | 68.178.246.137:443 | mdiaesthetics.com | GO-DADDY-COM-LLC | US | unknown |
7832 | msedge.exe | 184.86.251.23:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mdiaesthetics.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.ssa.gov |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Check Security.Principal.WindowsBuiltInRole has been detected |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |
— | — | A Network Trojan was detected | LOADER [ANY.RUN] Gen.Powershell.Downloader Script Payload |
2276 | svchost.exe | Misc activity | ET INFO Abused Hosting Domain in DNS Lookup (azurewebsites .net) |
2976 | Docscan_318916.exe | Misc activity | ET INFO Abused Hosting Domain (azurewebsites .net) in TLS SNI |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
7252 | Docscan_318916.exe | Misc activity | ET INFO Abused Hosting Domain (azurewebsites .net) in TLS SNI |