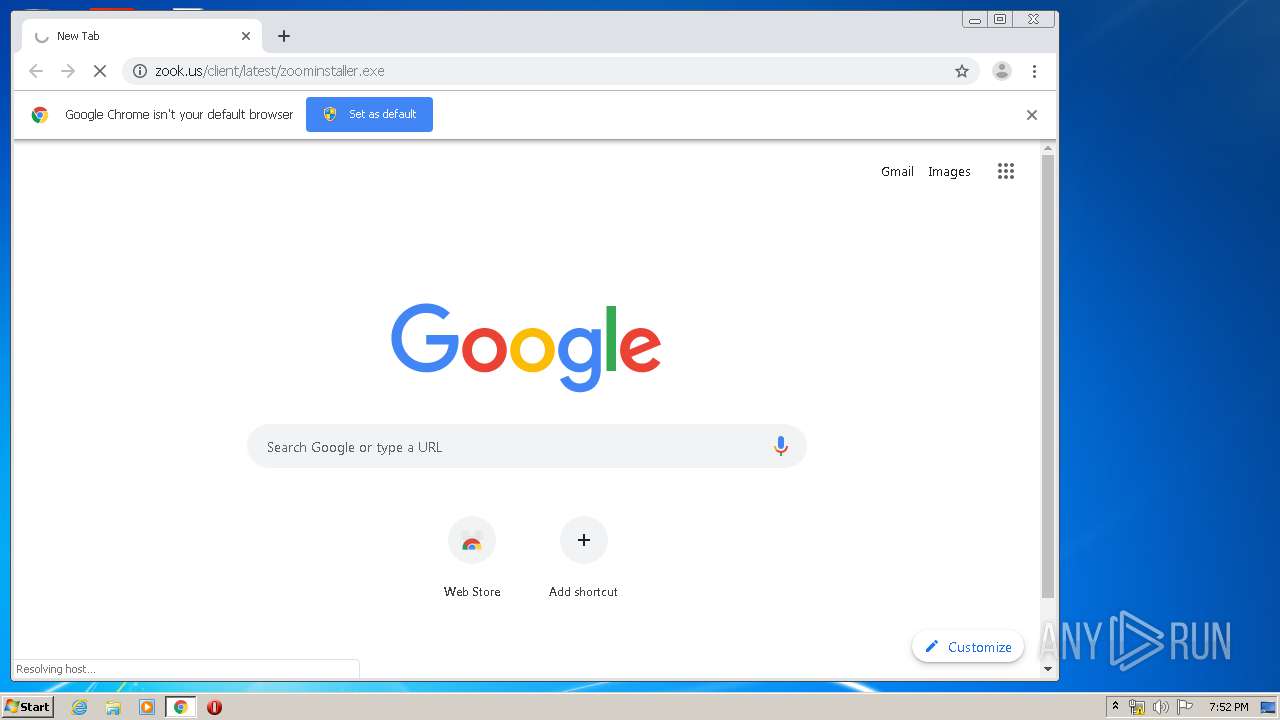
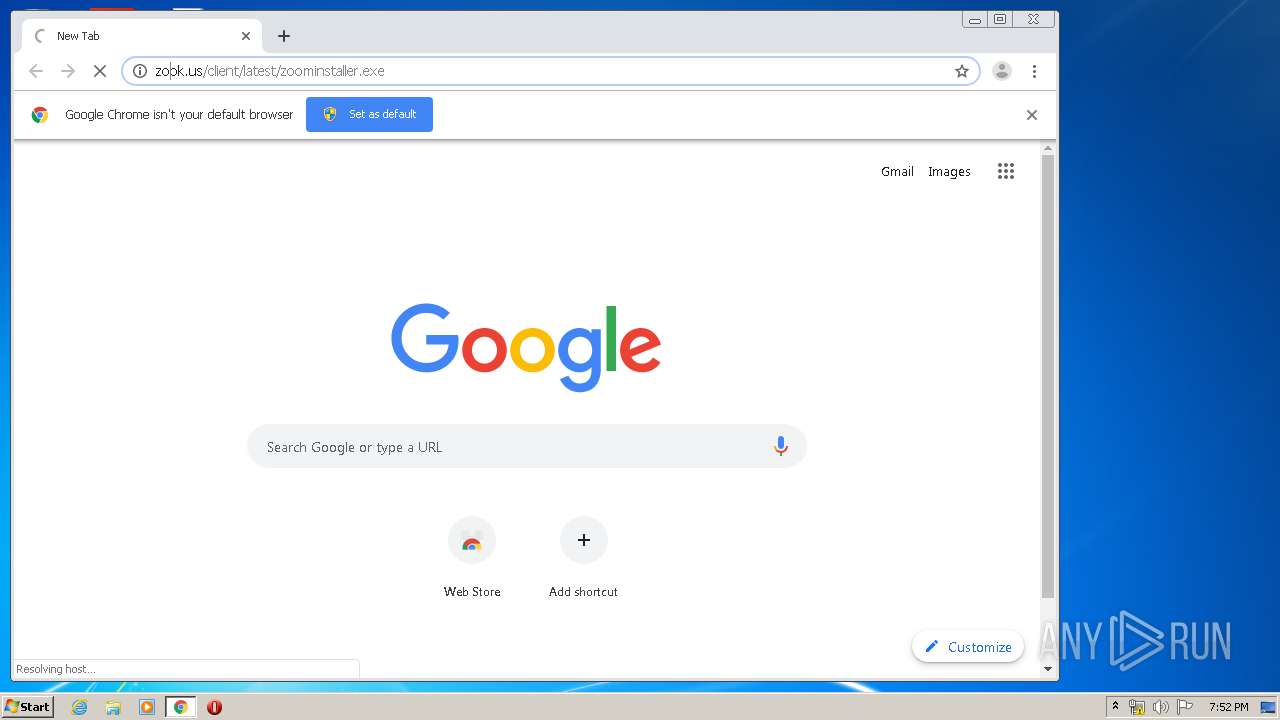
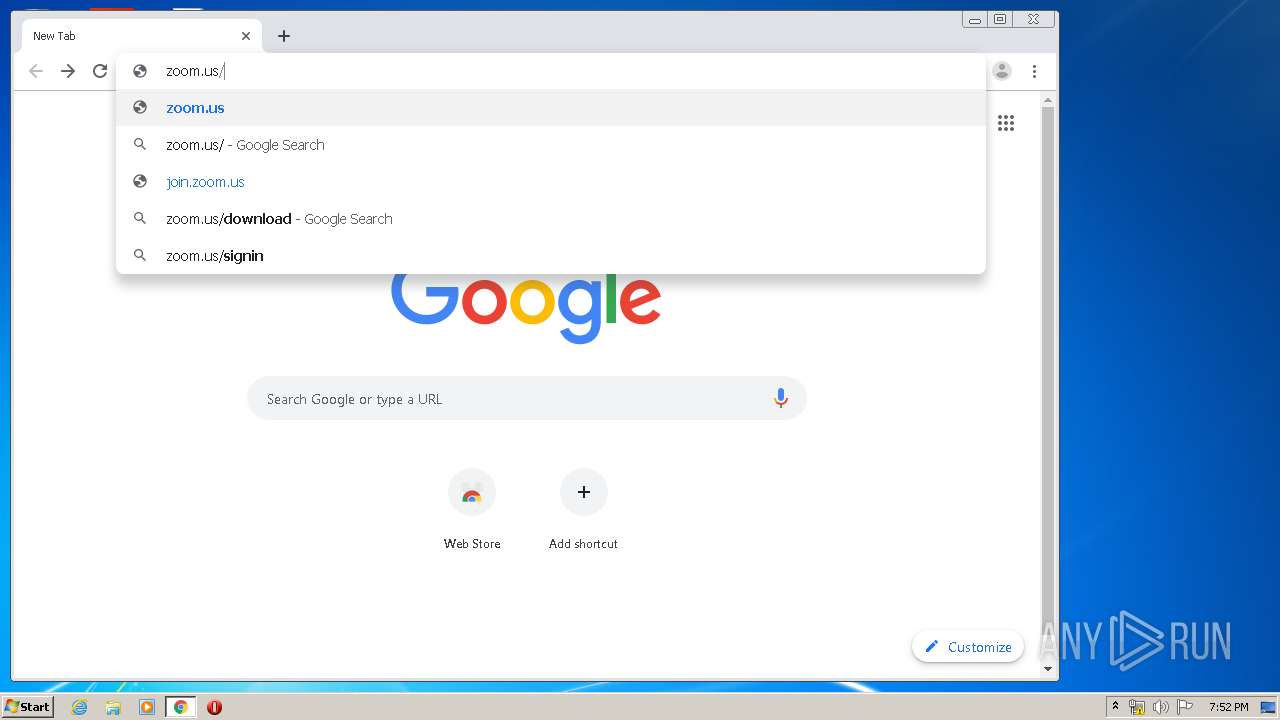
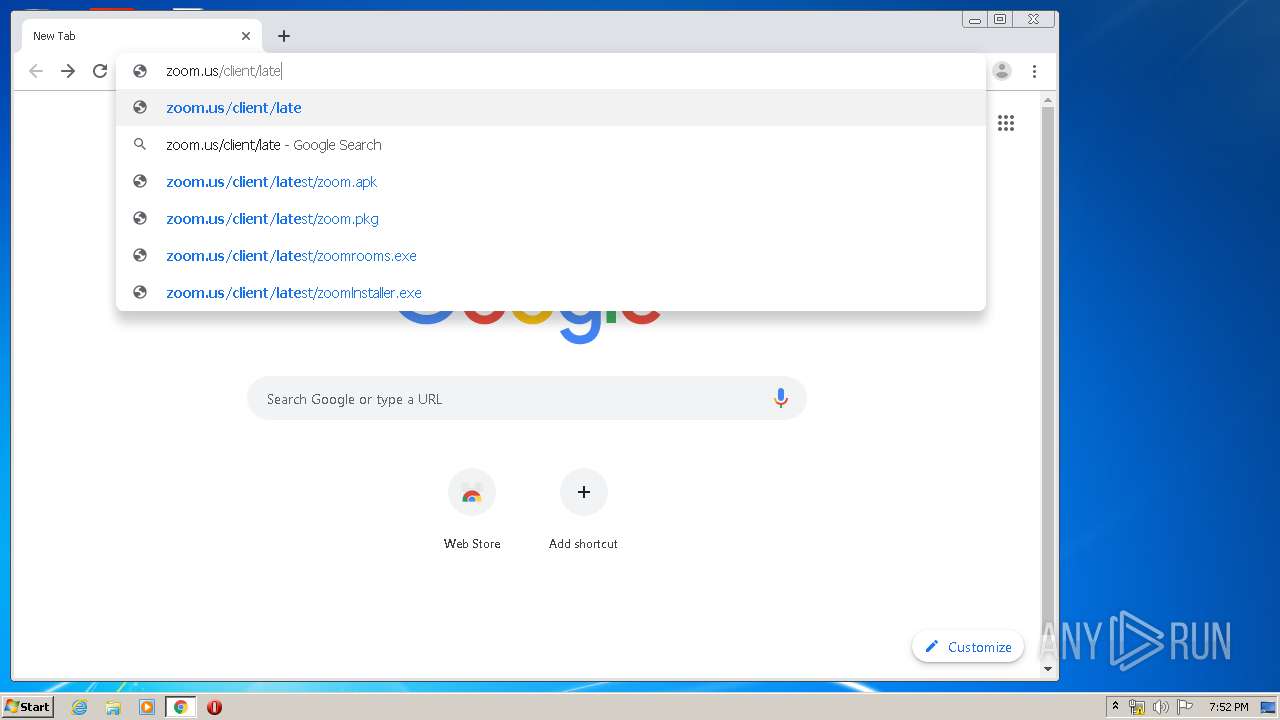
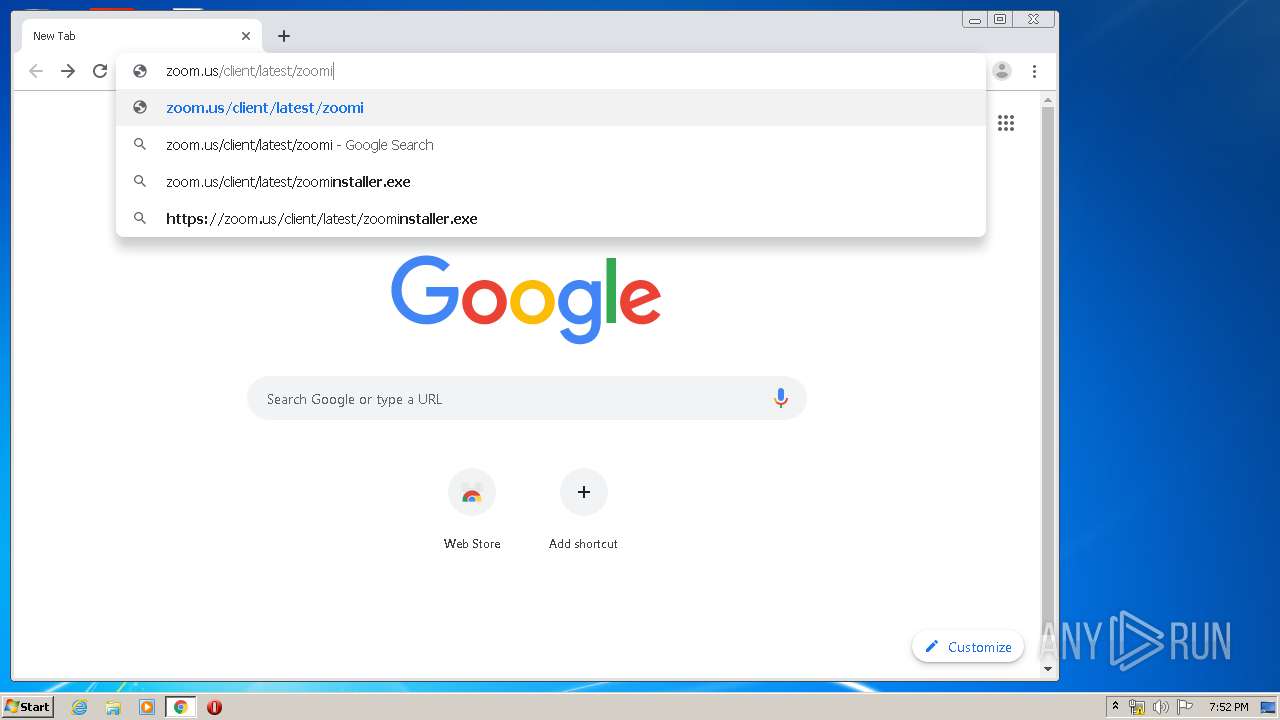
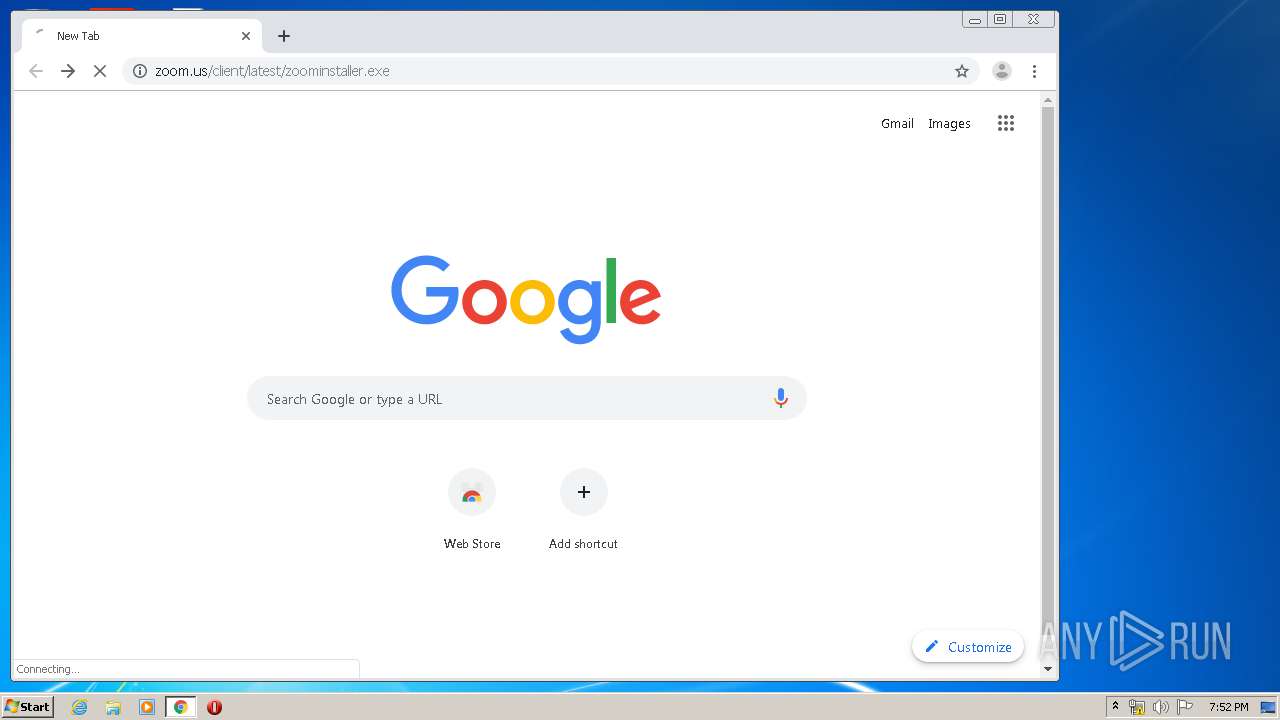
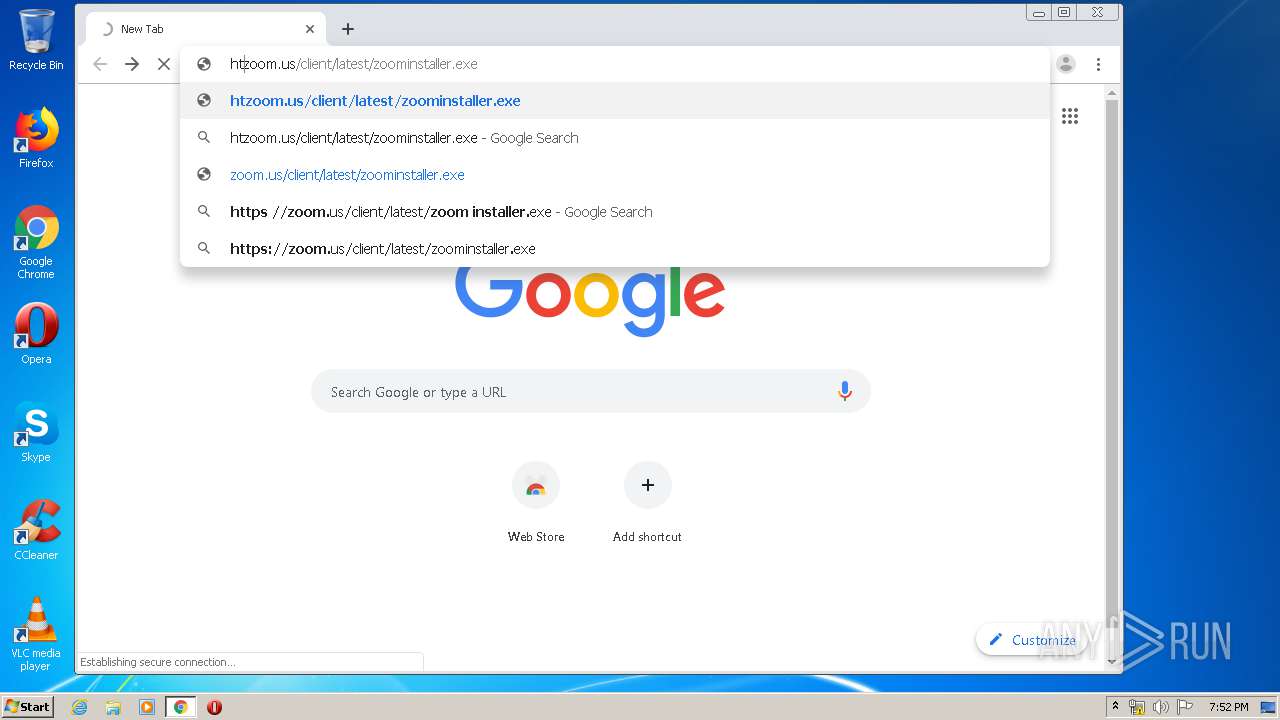
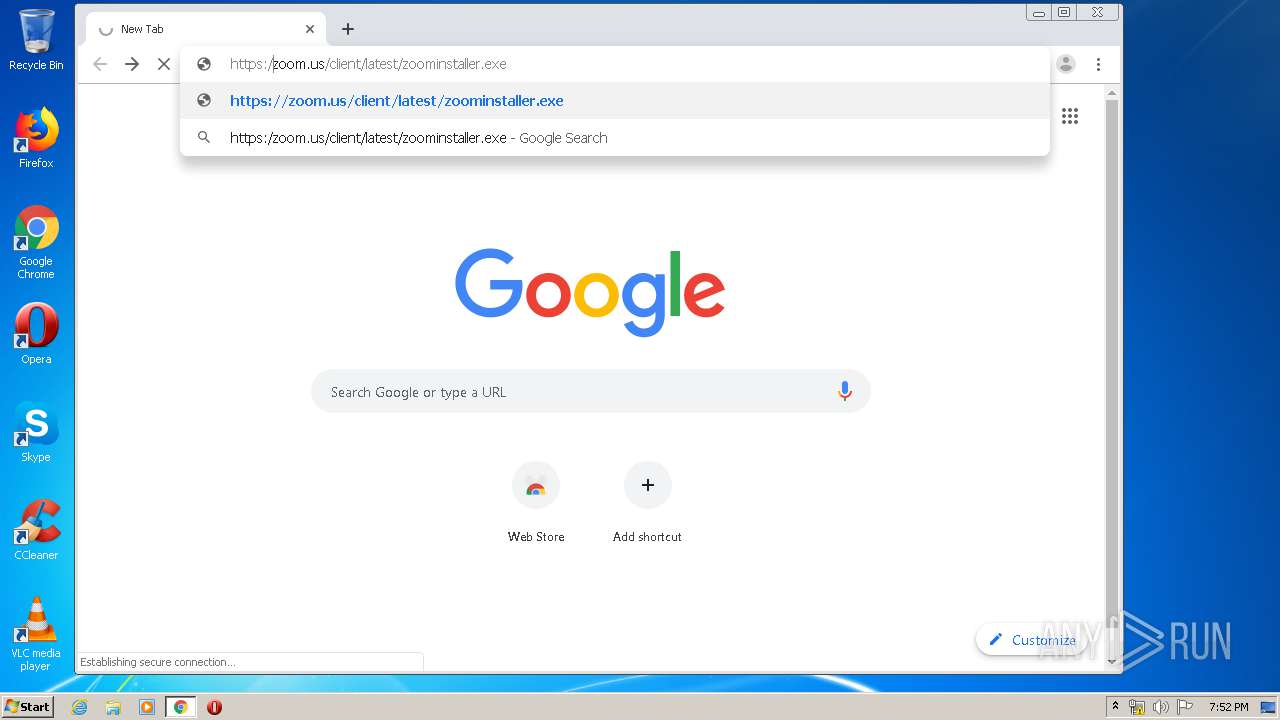
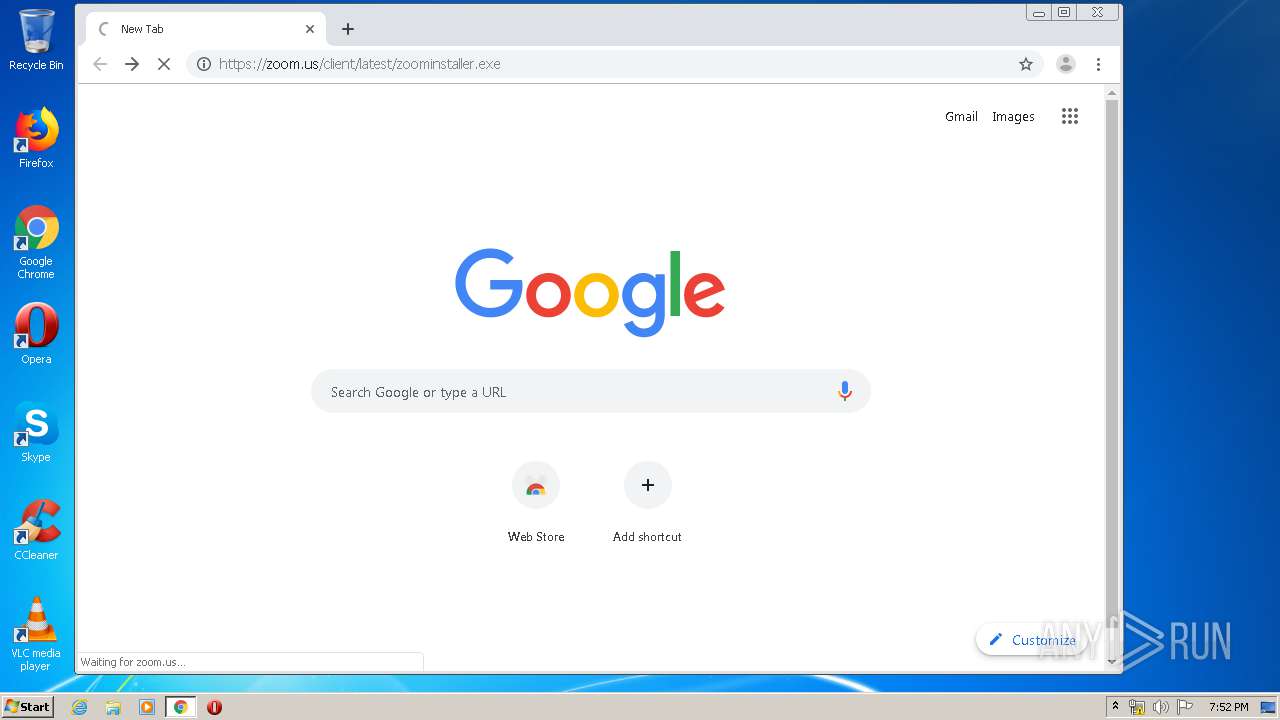
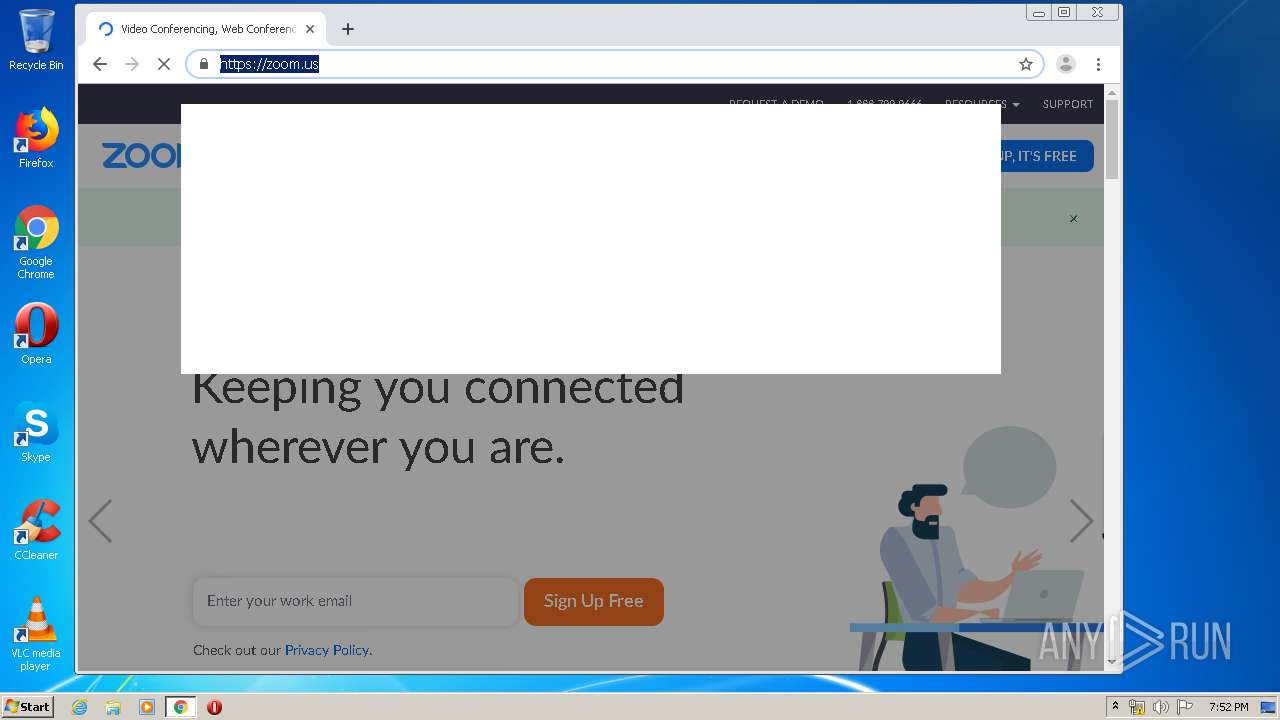
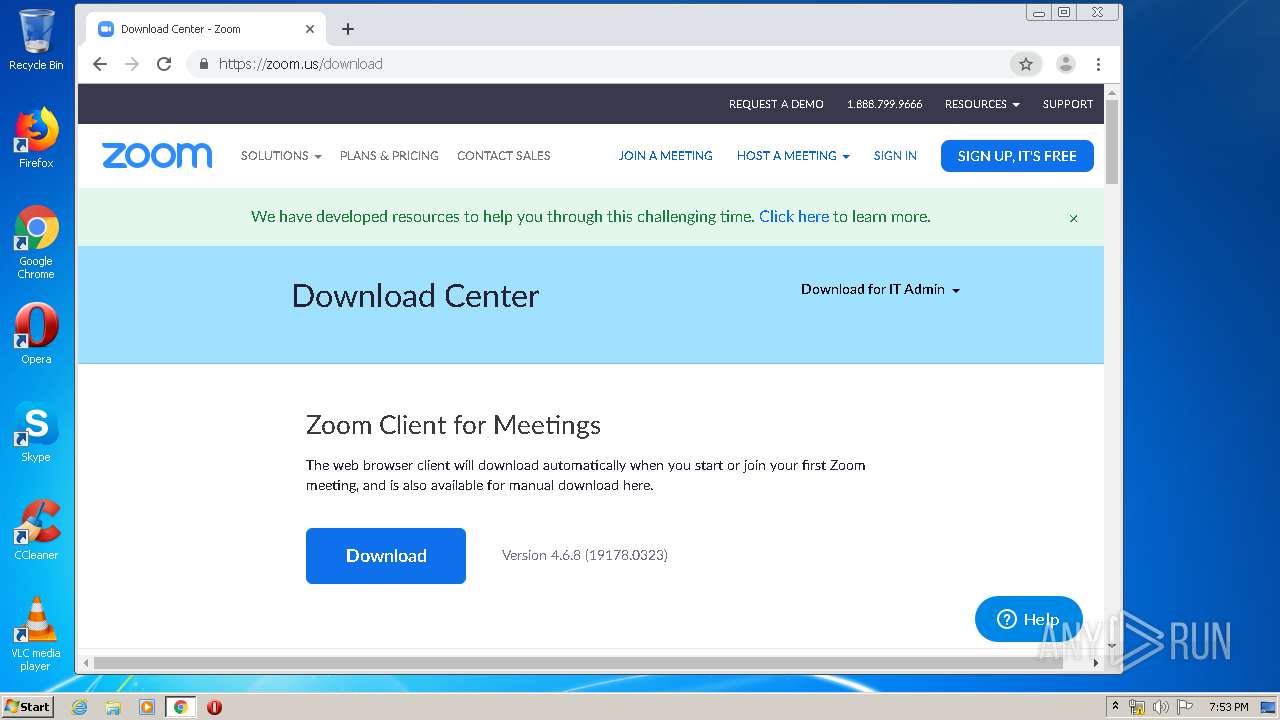
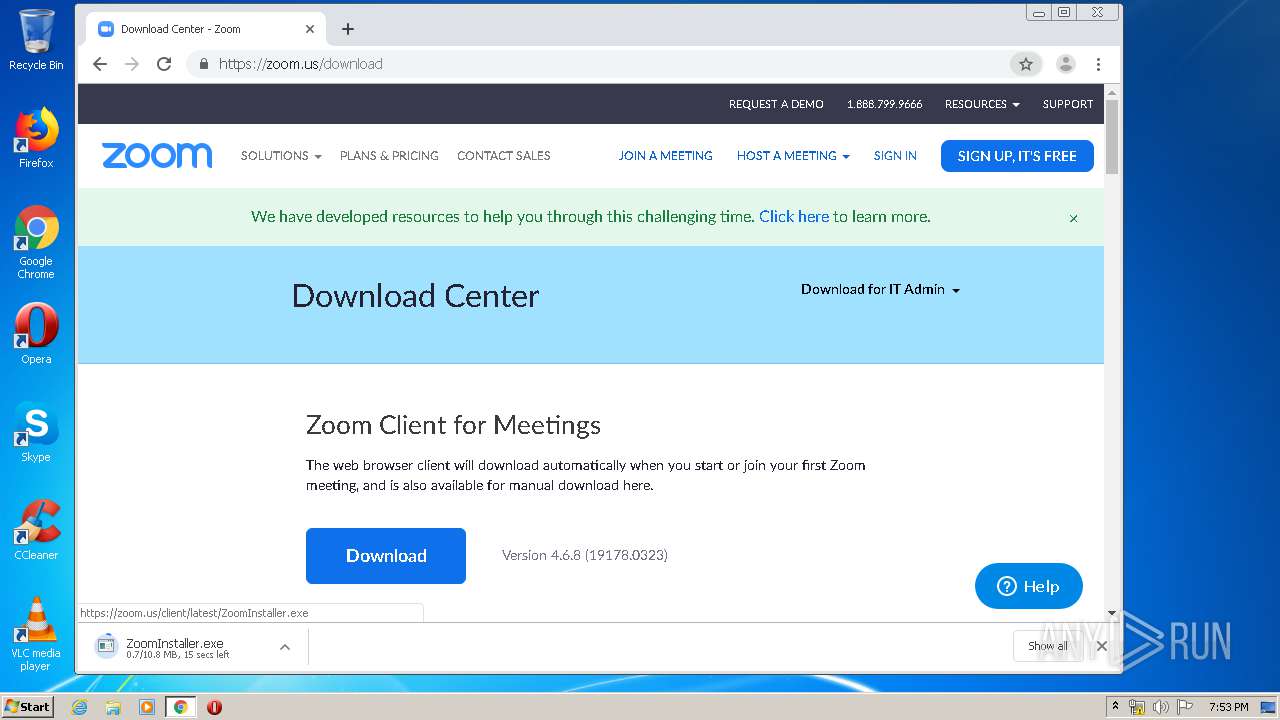
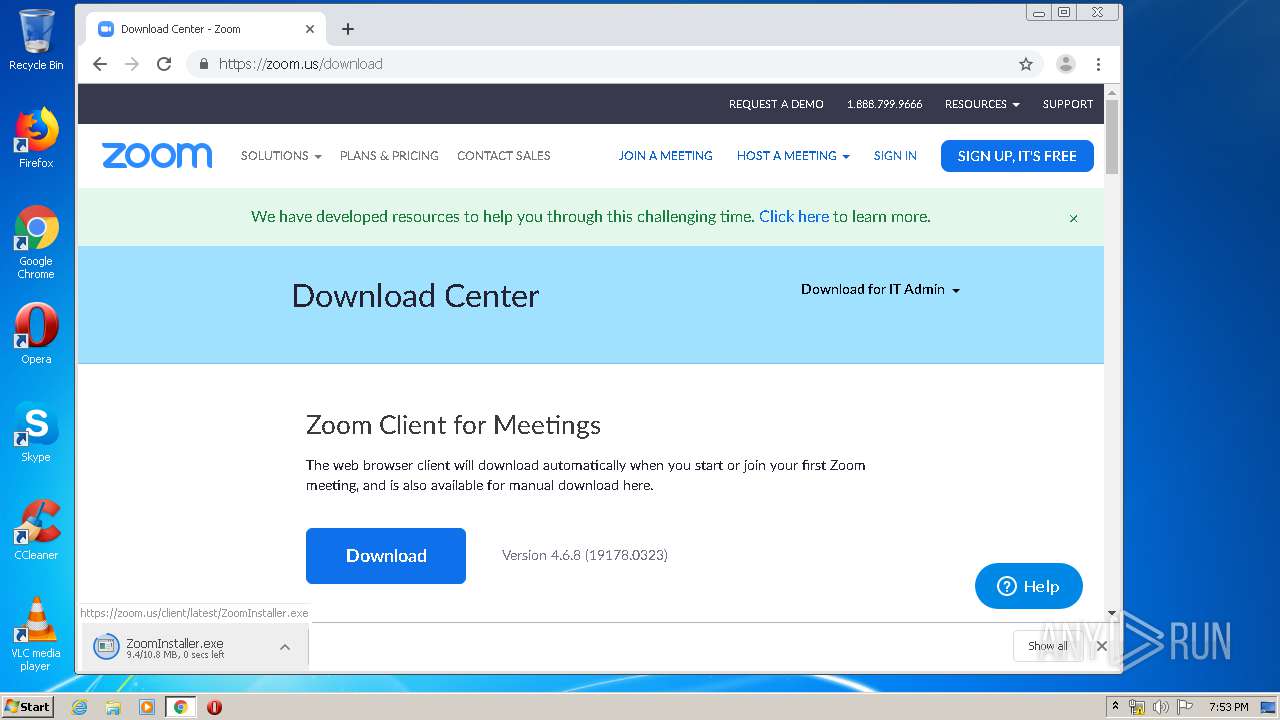
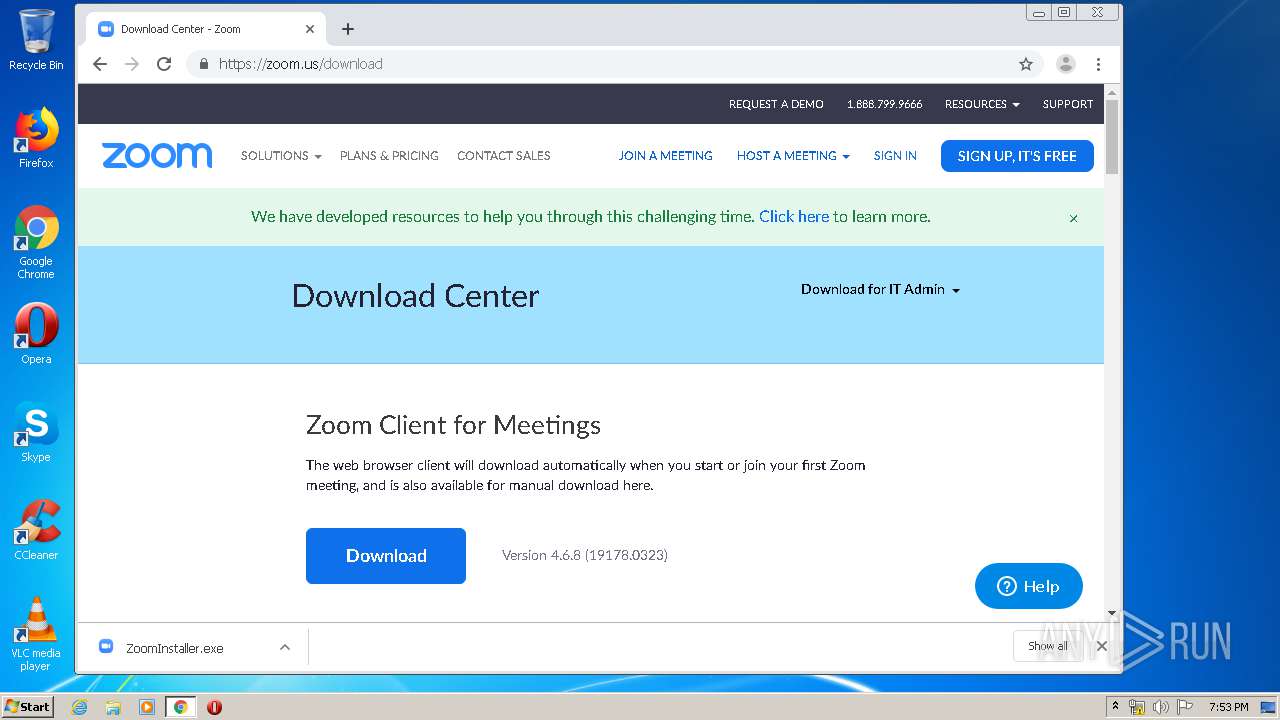
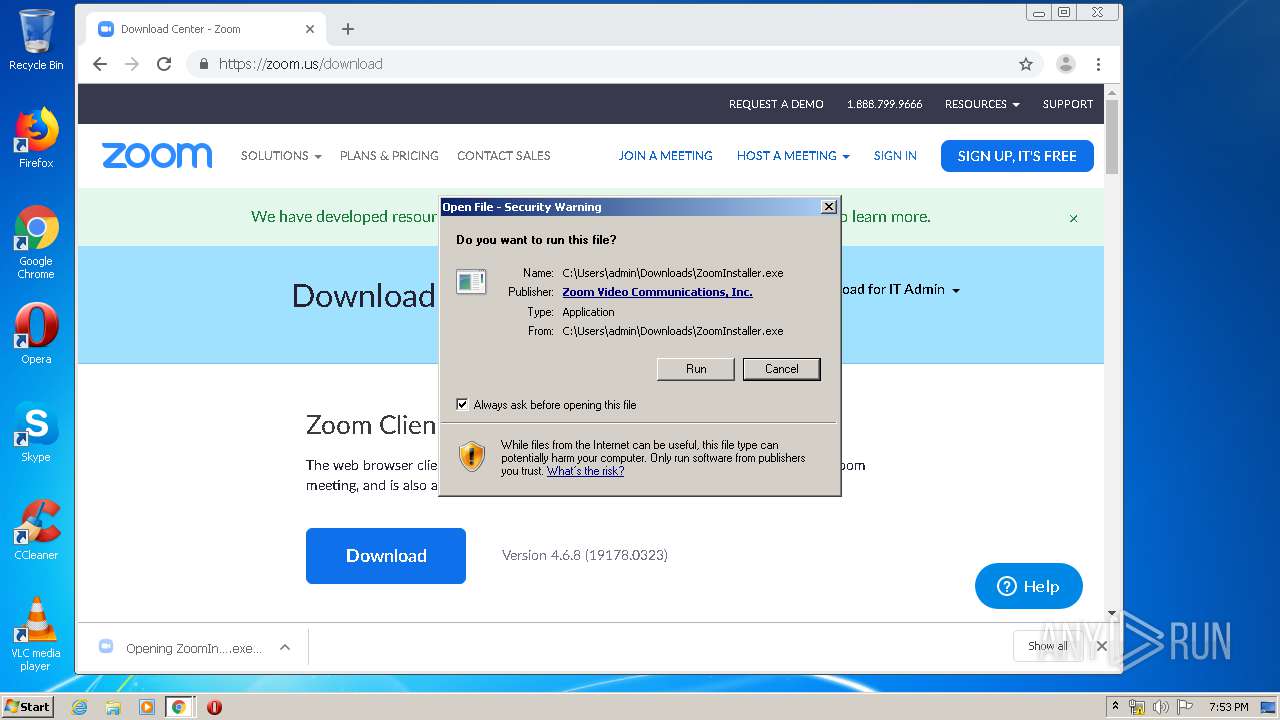
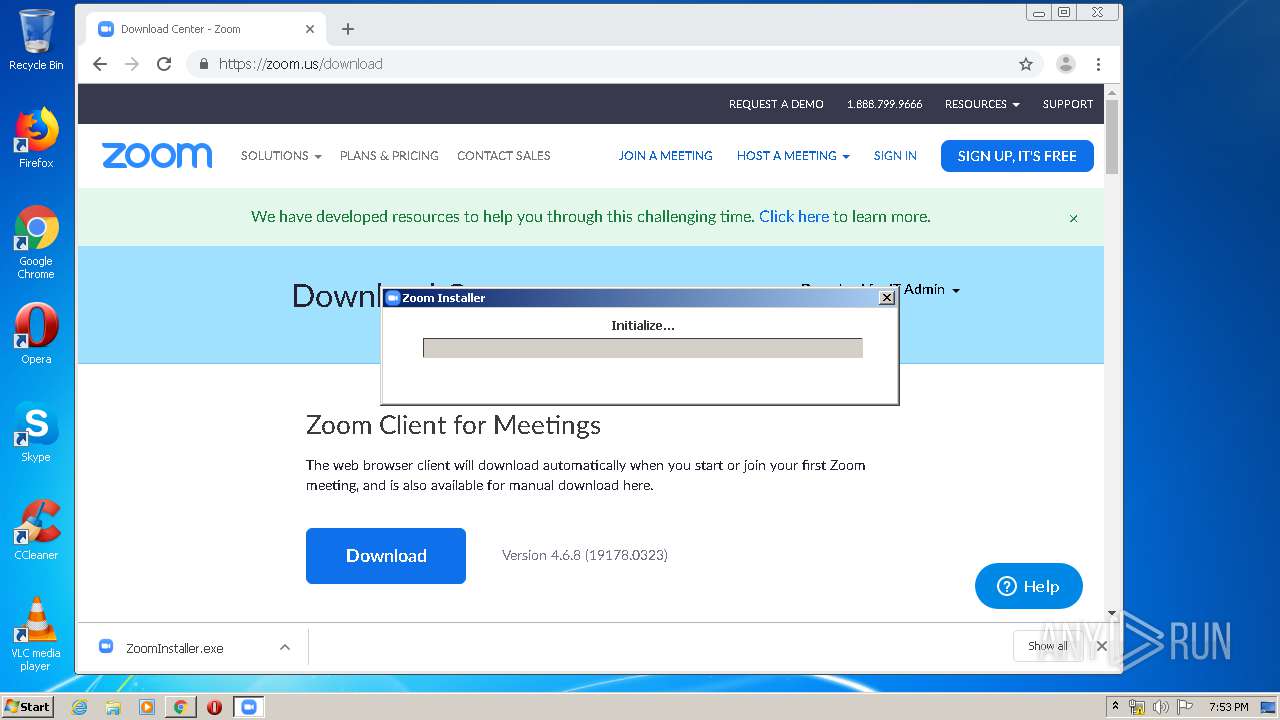
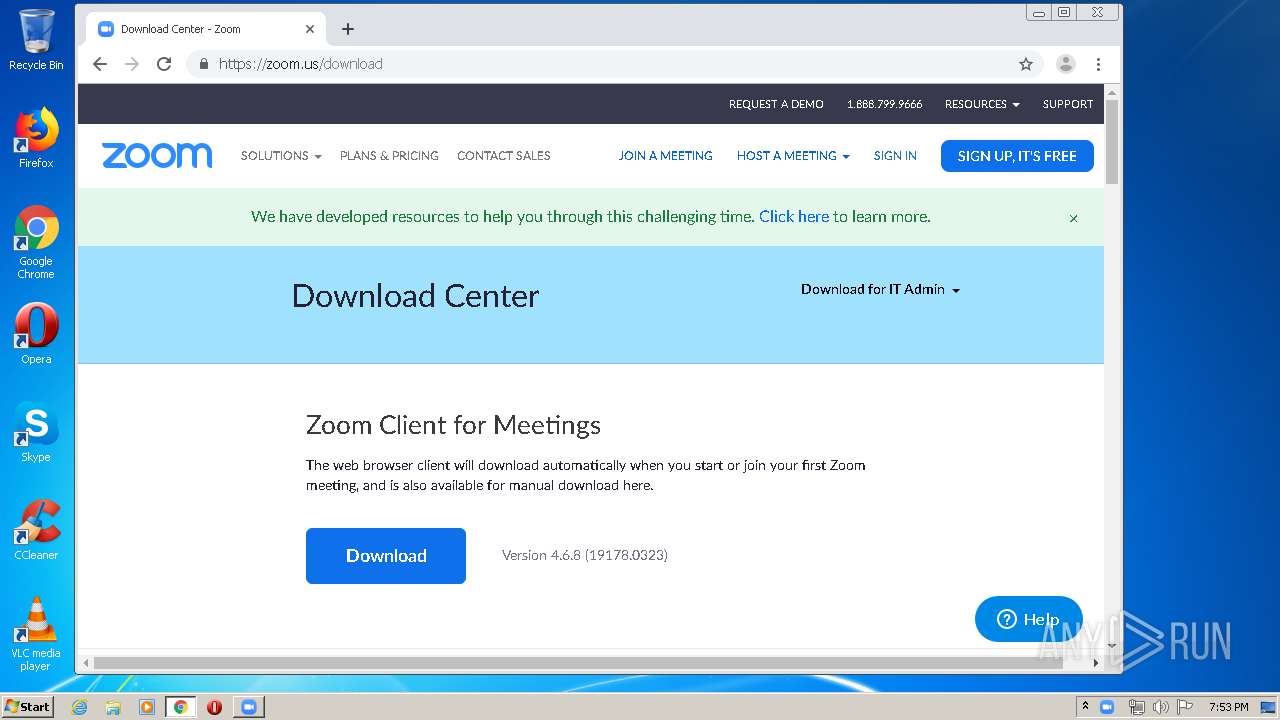
| URL: | https://zoom.us/client/latest/ZoomInstaller.exe |
| Full analysis: | https://app.any.run/tasks/a960713a-53c7-4397-a9ca-f377d3ec1820 |
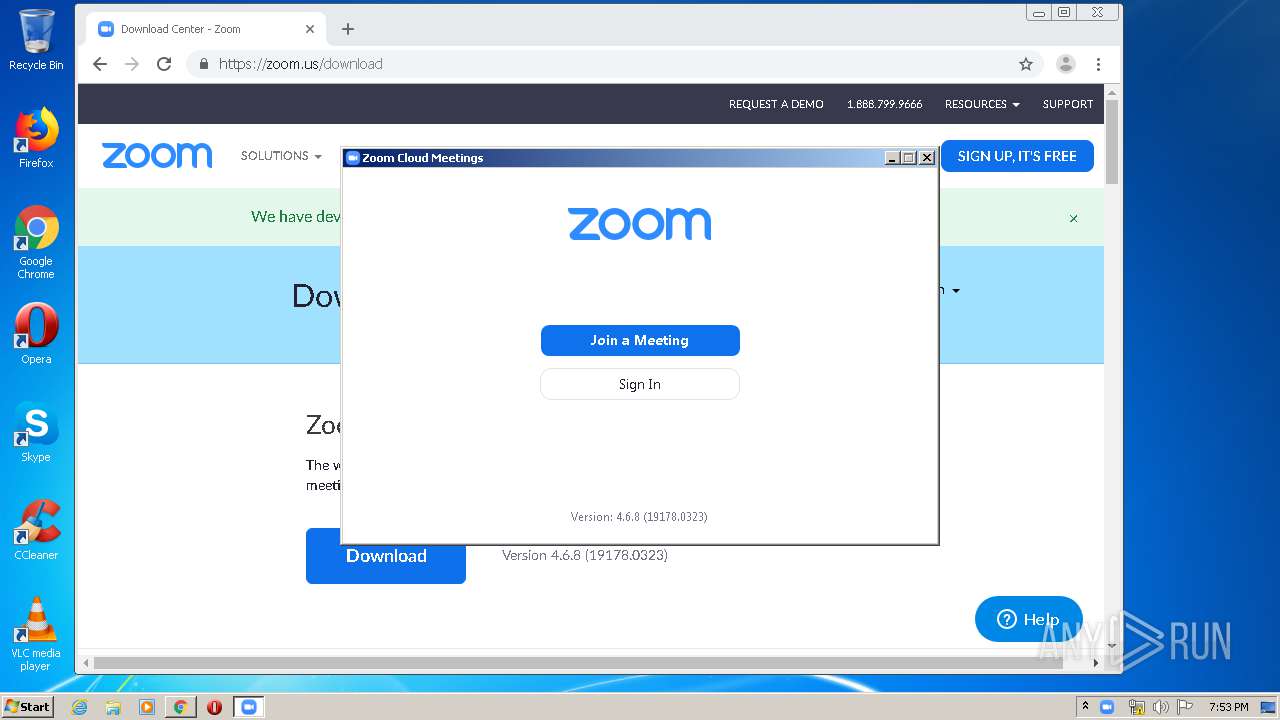
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2020, 19:50:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 063482C1F099E60CDD5BDFC1EBF056E1 |
| SHA1: | 588BCC720708BC1C81861CF122C9A03B9D469F44 |
| SHA256: | C272690A135BEF593718080C339CF0ED18F68BFBDE40BF9A48421540BD4C9DBB |
| SSDEEP: | 3:N88LW3RRiTXLNn:28LWWTXLN |
MALICIOUS
Runs injected code in another process
- chrome.exe (PID: 304)
Application was injected by another process
- dllhost.exe (PID: 1492)
Application was dropped or rewritten from another process
- ZoomInstaller.exe (PID: 3780)
- Installer.exe (PID: 3516)
- Installer.exe (PID: 1828)
- Zoom.exe (PID: 3608)
- Zoom.exe (PID: 2532)
- Zoom.exe (PID: 3064)
- cpthost.exe (PID: 2408)
Loads dropped or rewritten executable
- Installer.exe (PID: 3516)
- Zoom.exe (PID: 3608)
- Zoom.exe (PID: 2532)
- Zoom.exe (PID: 3064)
- cpthost.exe (PID: 2408)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 3052)
- chrome.exe (PID: 304)
- chrome.exe (PID: 3960)
- ZoomInstaller.exe (PID: 3780)
- Installer.exe (PID: 3516)
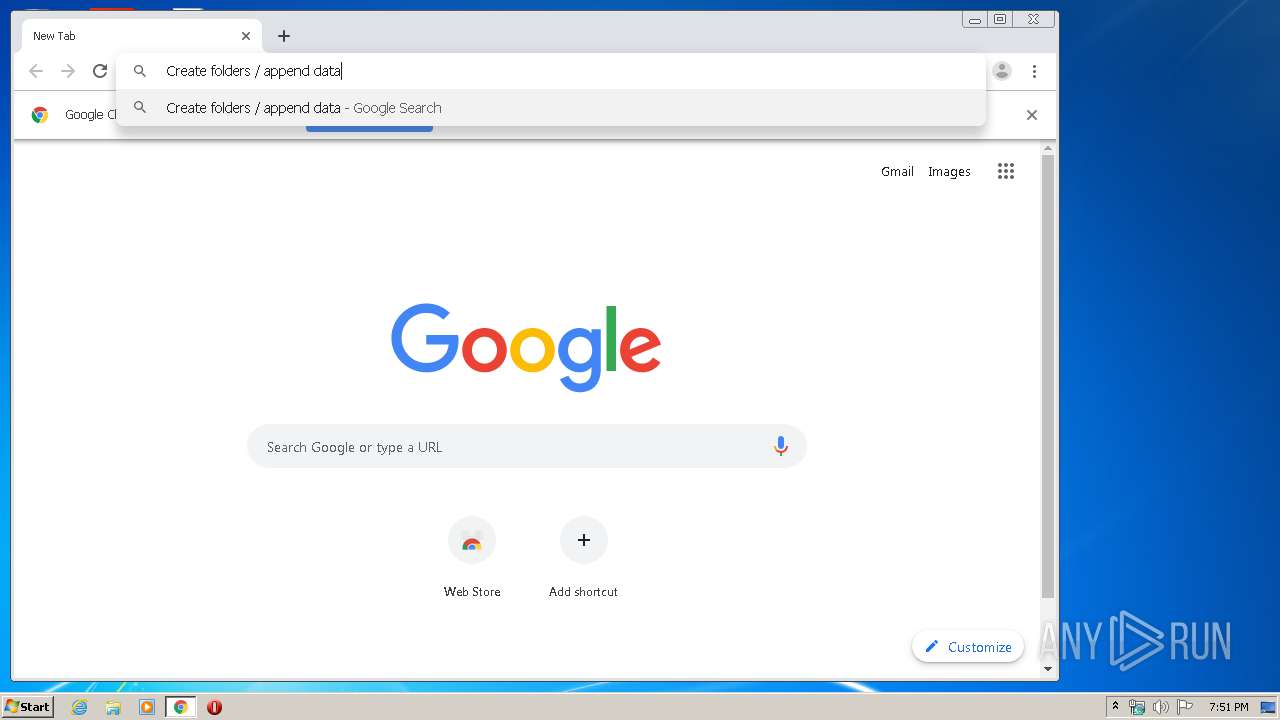
Modifies files in Chrome extension folder
- chrome.exe (PID: 304)
Uses RUNDLL32.EXE to load library
- iexplore.exe (PID: 3052)
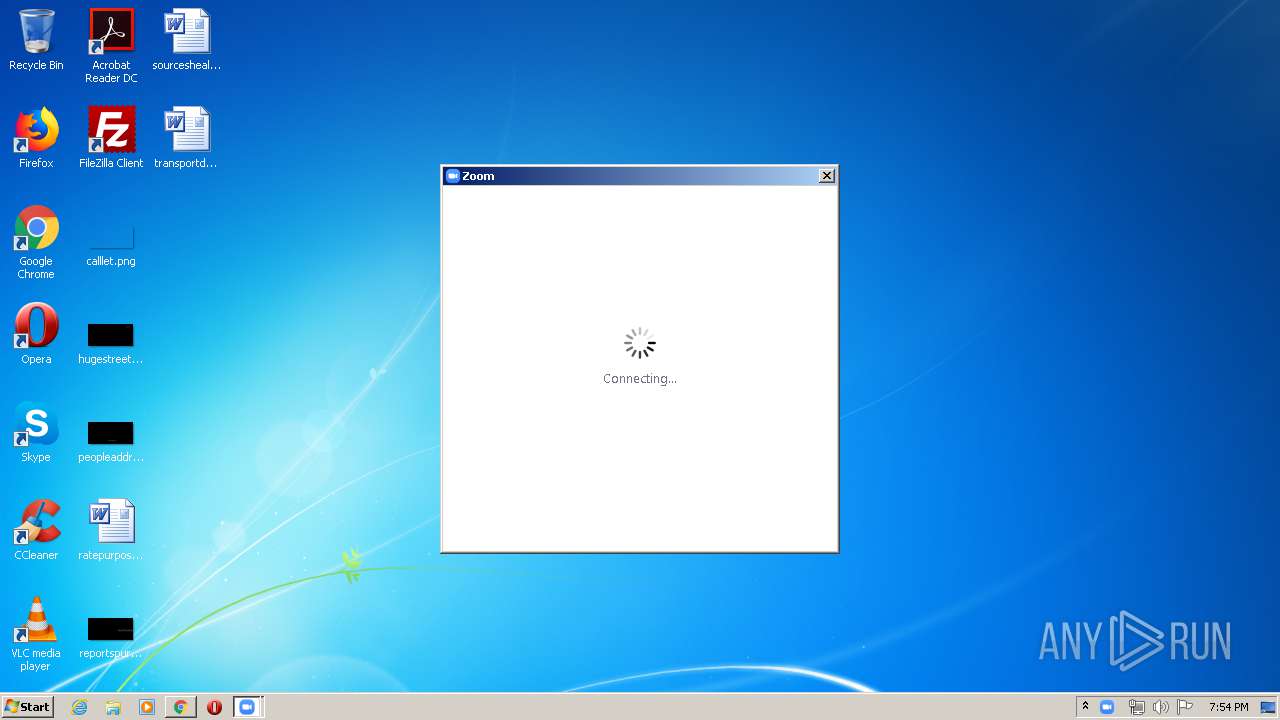
Application launched itself
- Installer.exe (PID: 3516)
- Zoom.exe (PID: 3608)
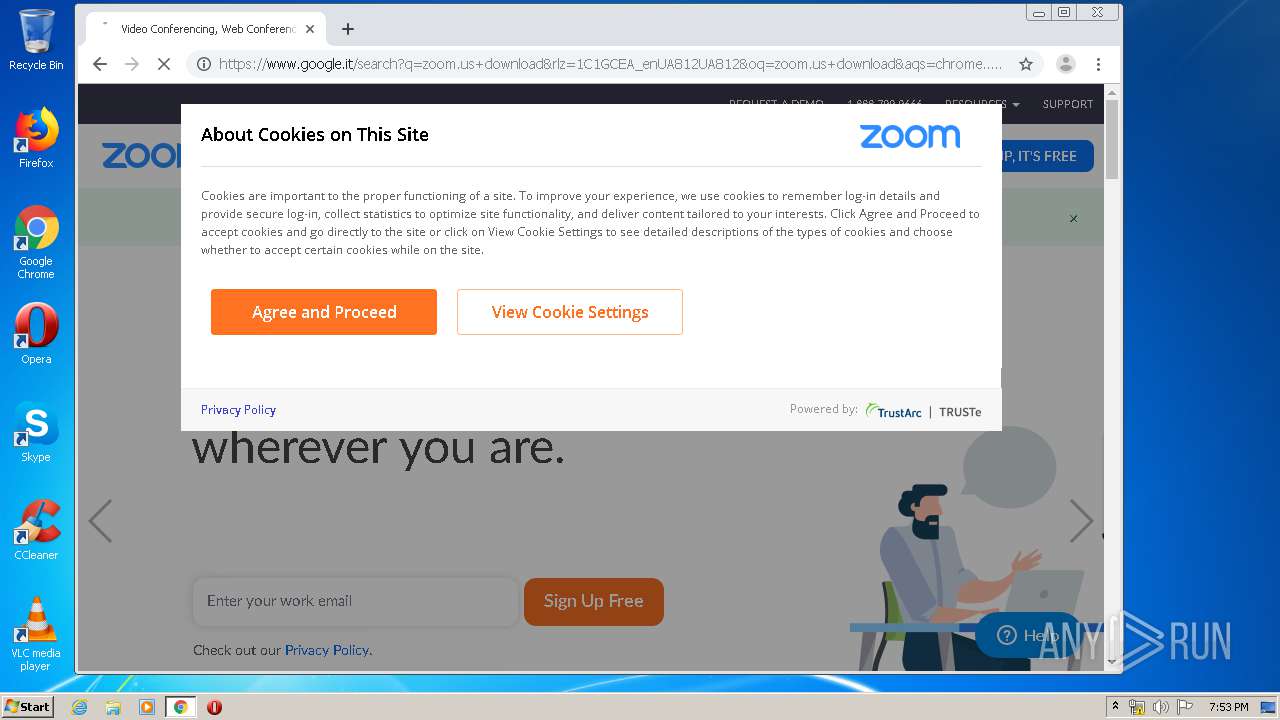
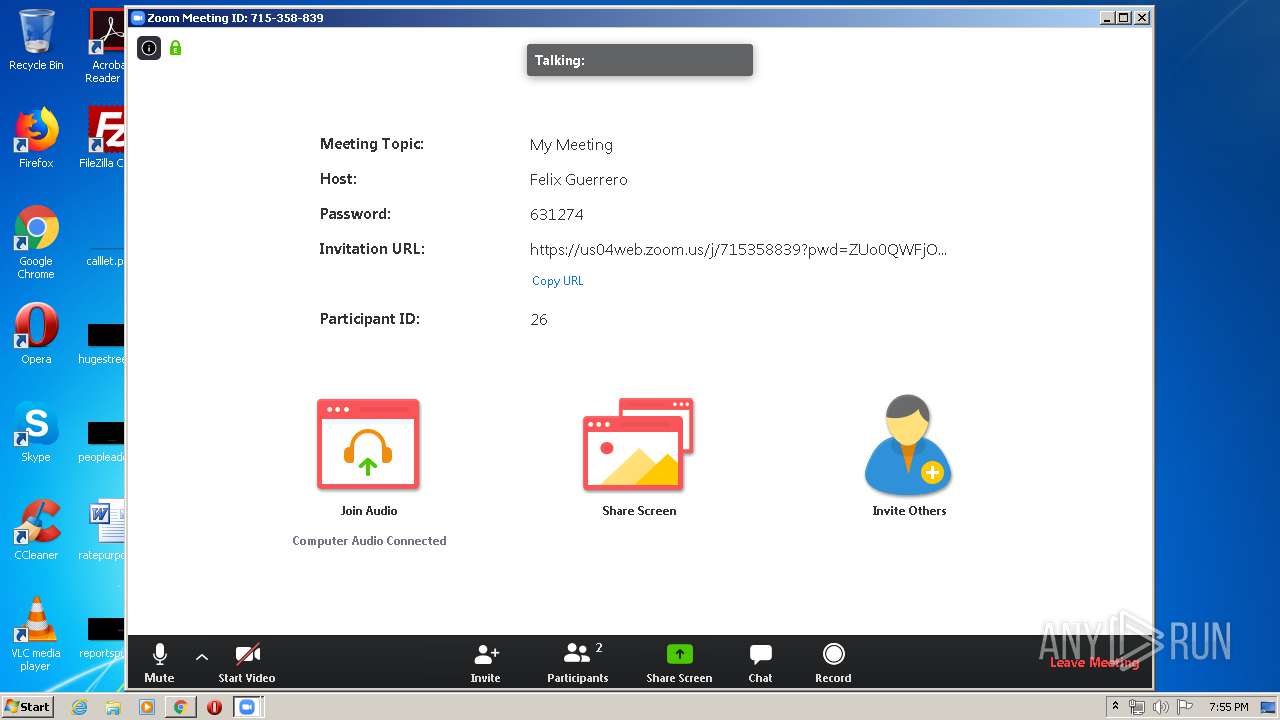
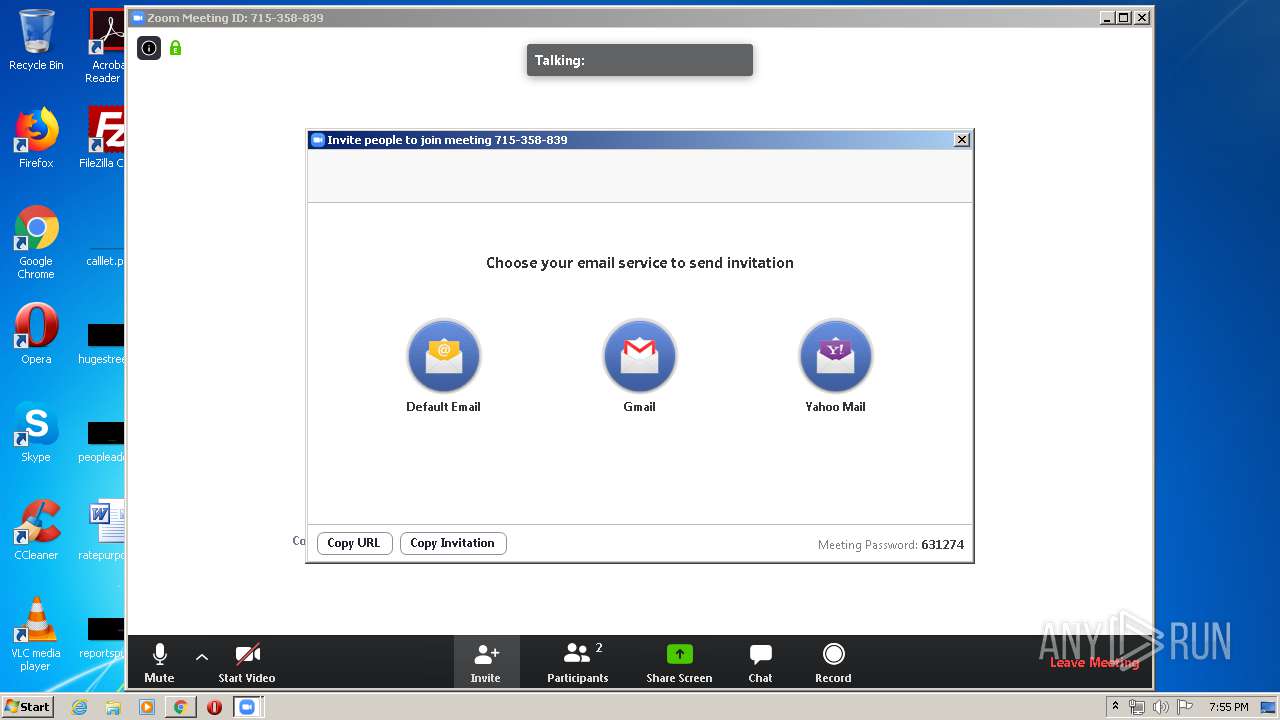
Creates a software uninstall entry
- Installer.exe (PID: 3516)
Modifies the open verb of a shell class
- Installer.exe (PID: 3516)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 3516)
Creates files in the user directory
- Zoom.exe (PID: 2532)
- Installer.exe (PID: 3516)
- Zoom.exe (PID: 3608)
- Zoom.exe (PID: 3064)
- cpthost.exe (PID: 2408)
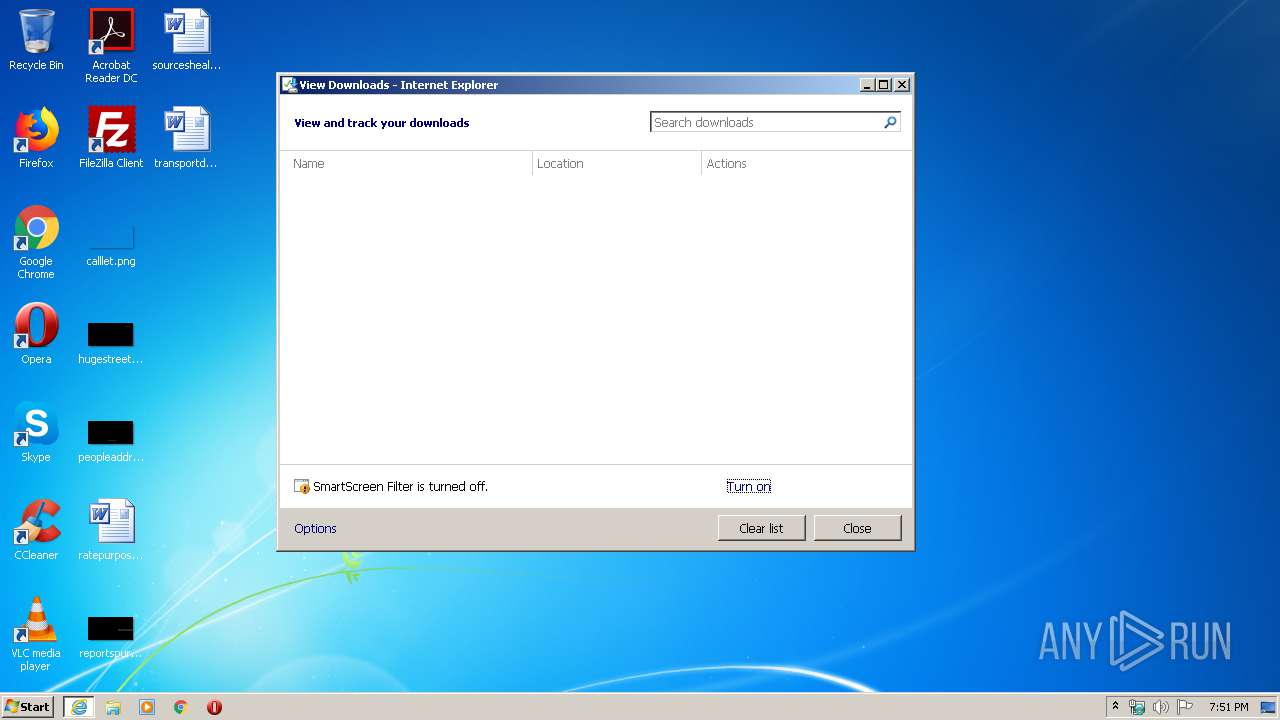
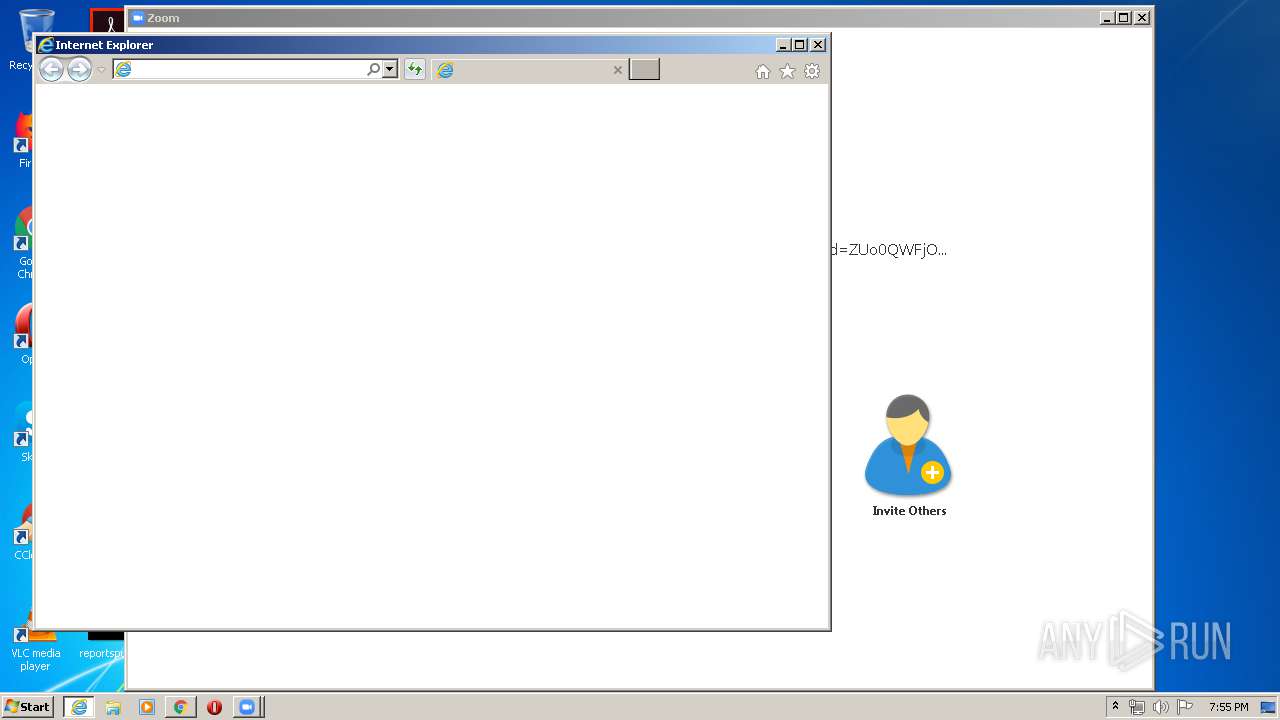
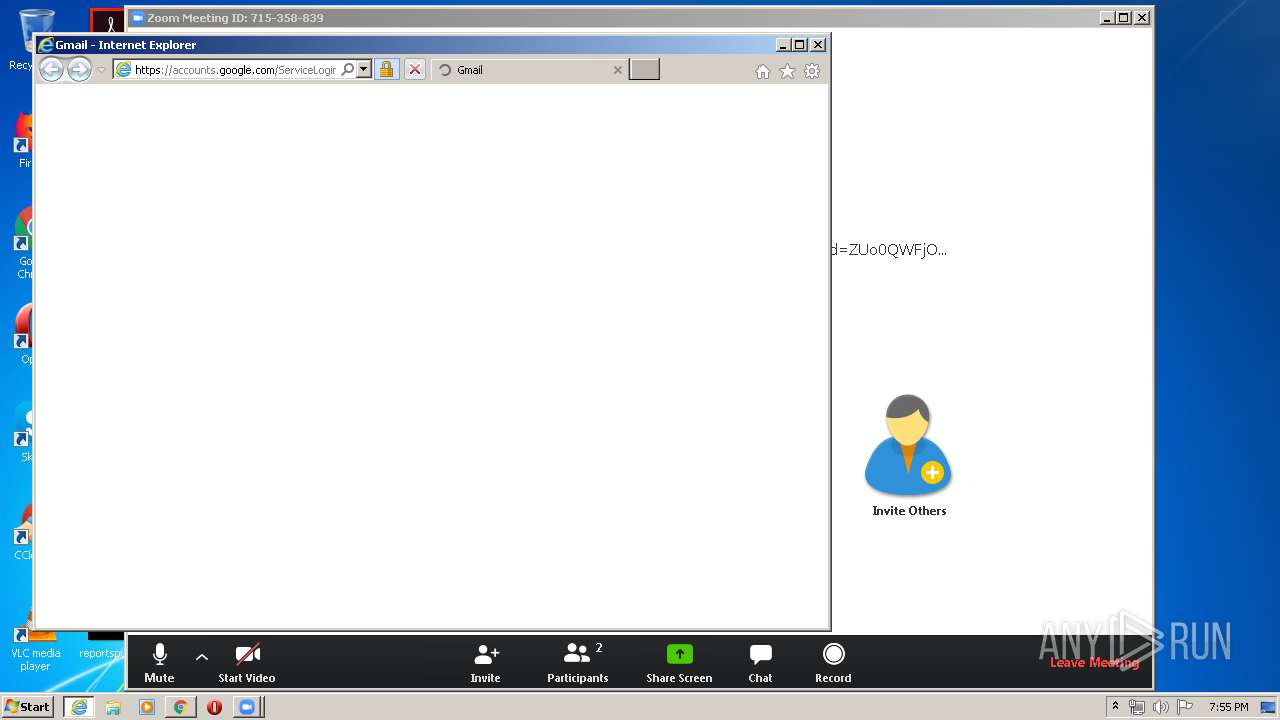
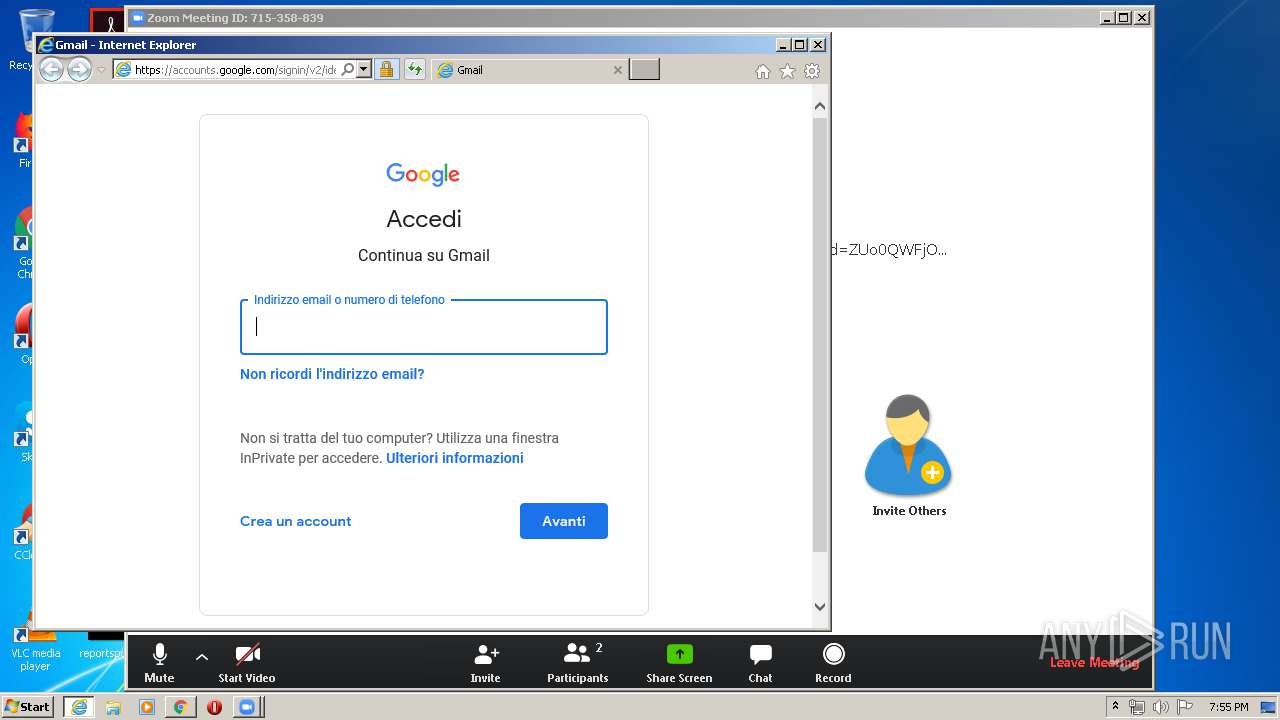
Starts Internet Explorer
- Zoom.exe (PID: 3608)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 2432)
- iexplore.exe (PID: 3152)
Creates files in the user directory
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 2448)
- iexplore.exe (PID: 1848)
Reads settings of System Certificates
- iexplore.exe (PID: 3052)
- chrome.exe (PID: 304)
- iexplore.exe (PID: 3716)
- Installer.exe (PID: 3516)
- Zoom.exe (PID: 3064)
- iexplore.exe (PID: 2448)
- iexplore.exe (PID: 1848)
- iexplore.exe (PID: 3152)
Reads Internet Cache Settings
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 3052)
- chrome.exe (PID: 304)
- iexplore.exe (PID: 2432)
- iexplore.exe (PID: 3152)
- iexplore.exe (PID: 2448)
- iexplore.exe (PID: 1848)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3052)
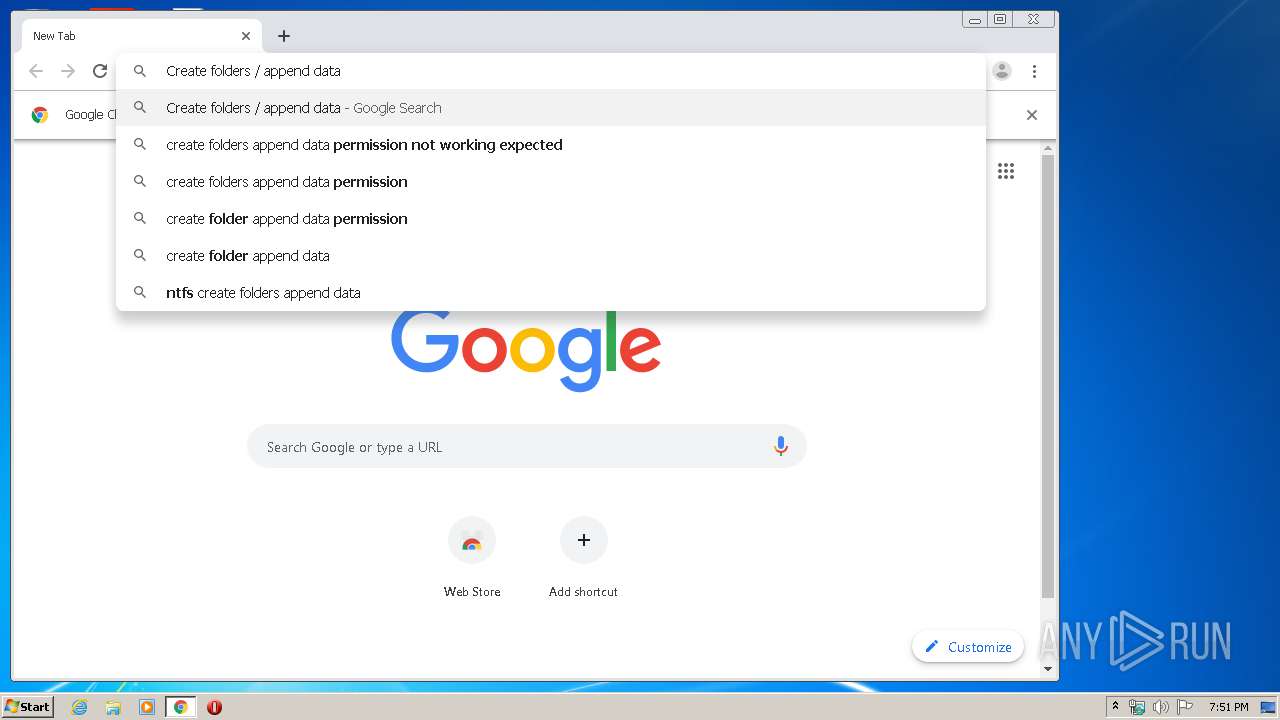
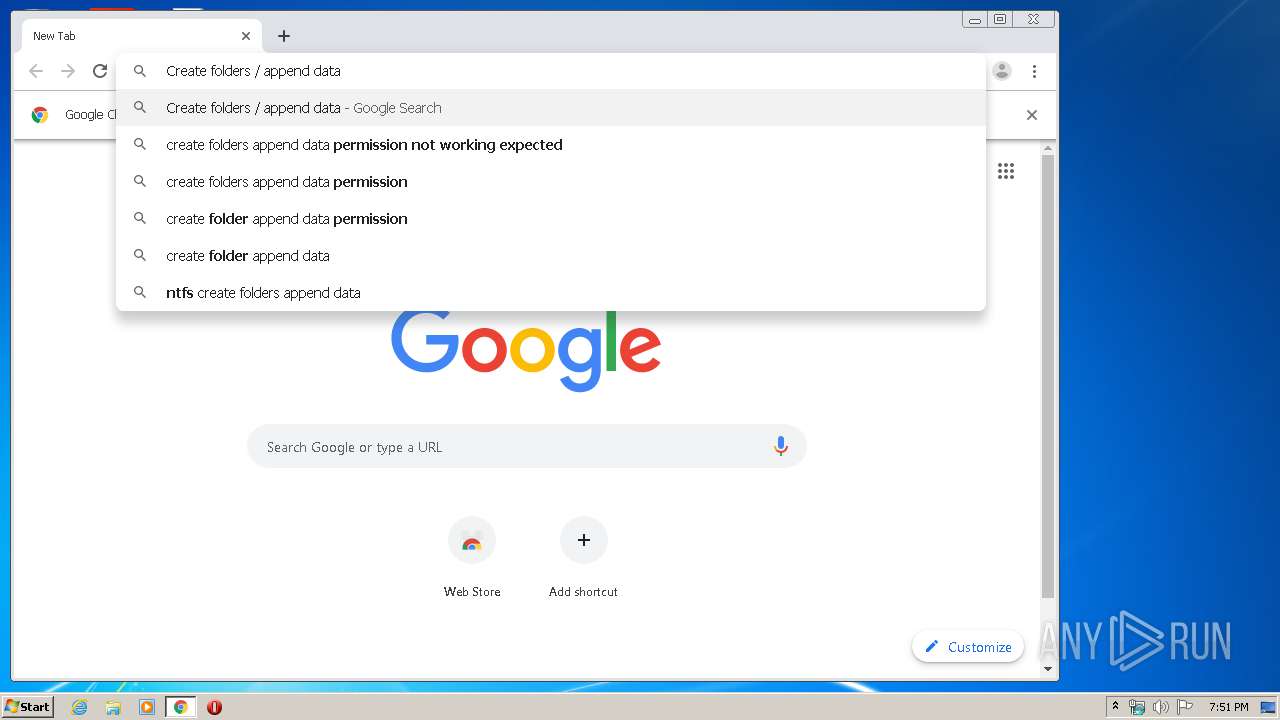
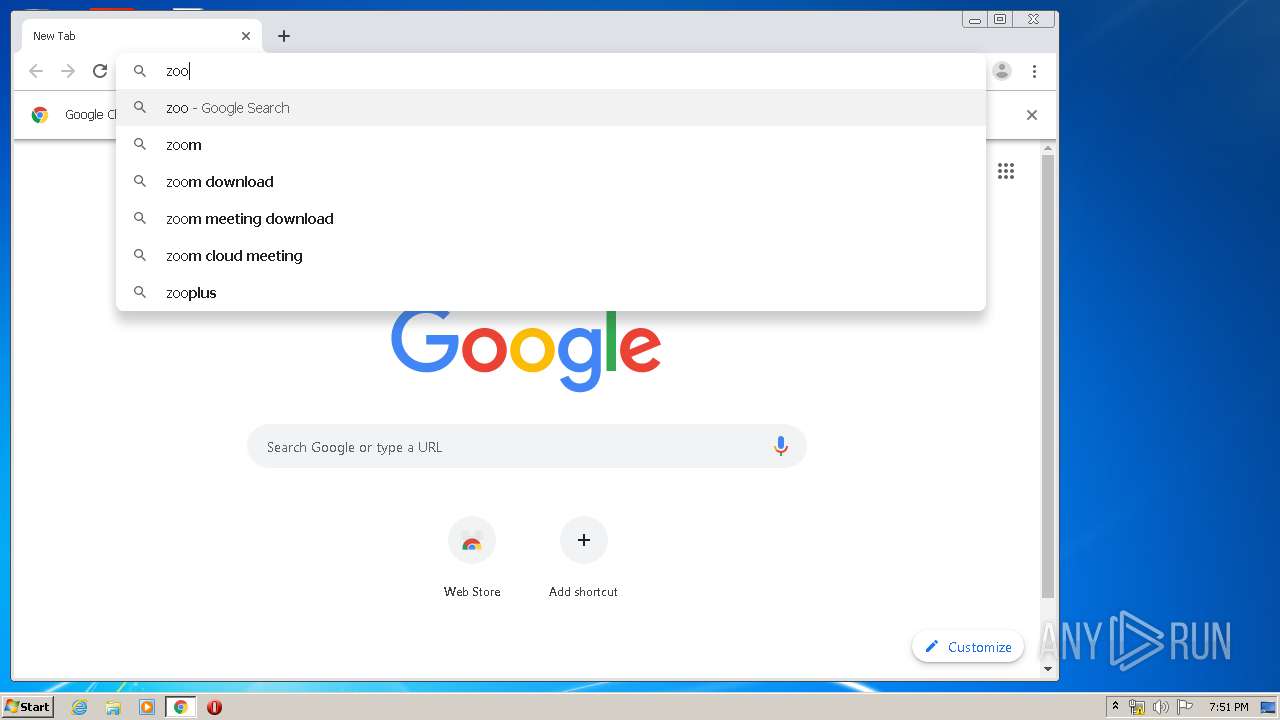
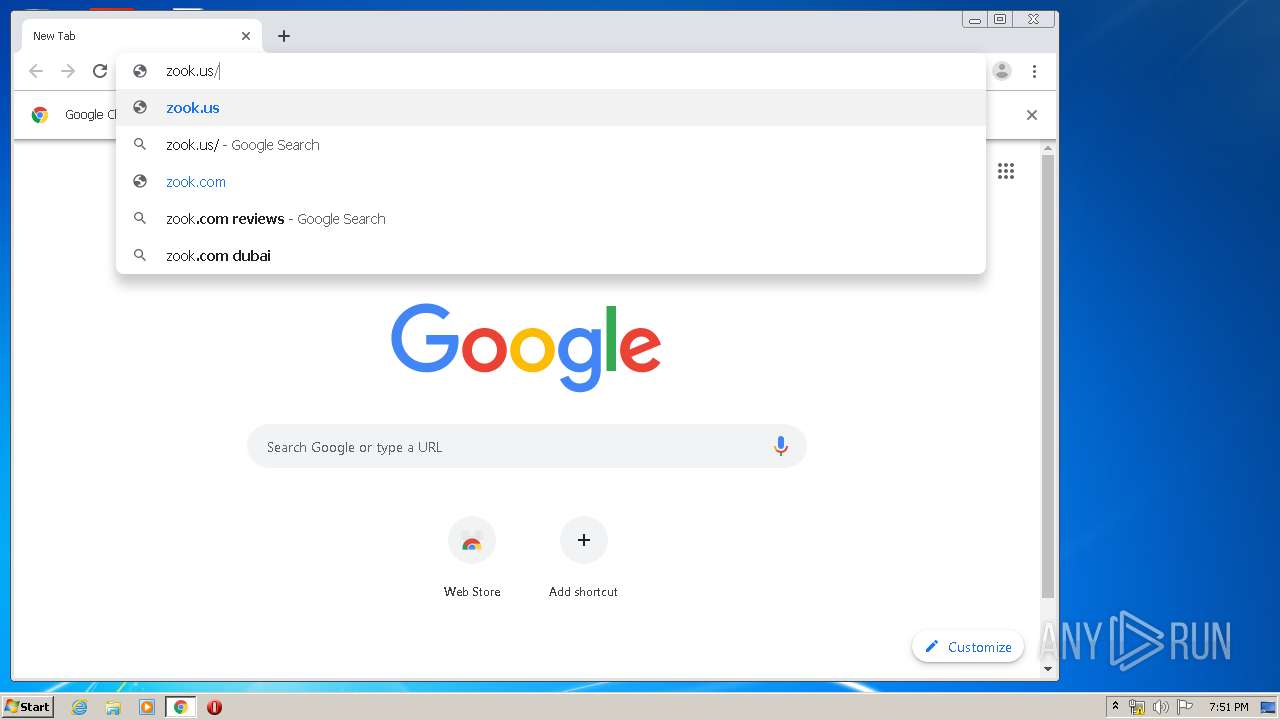
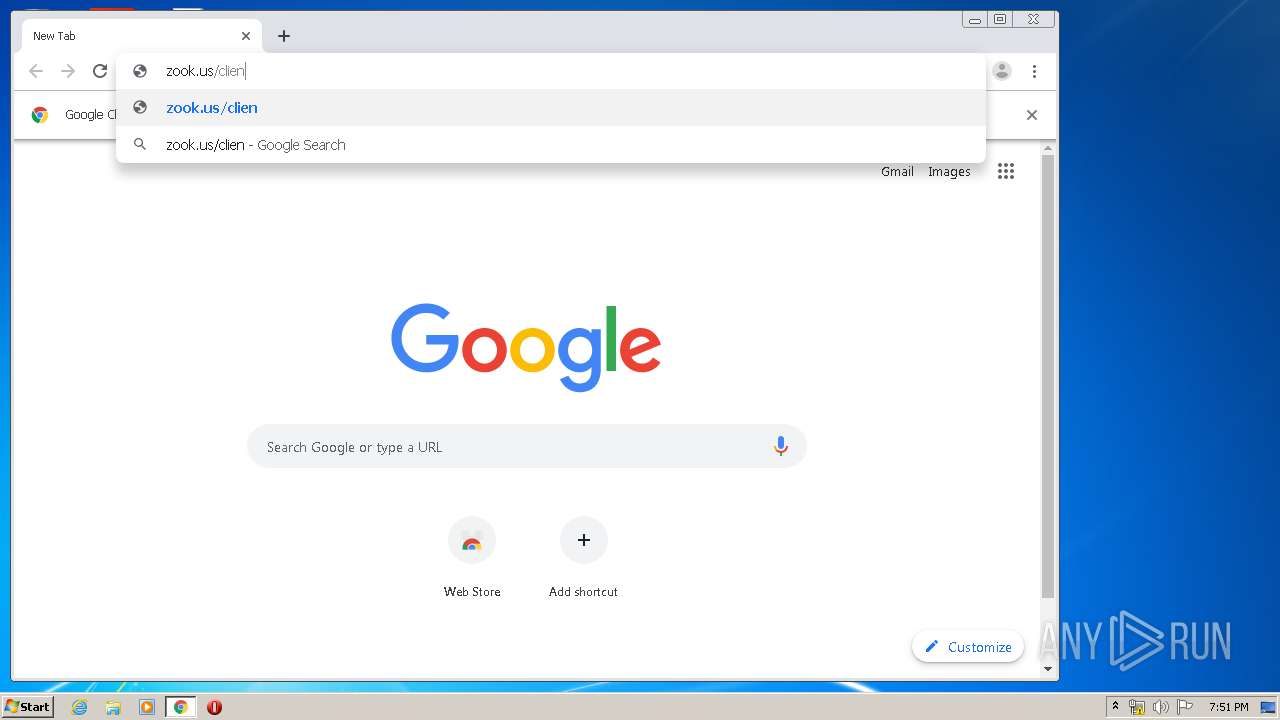
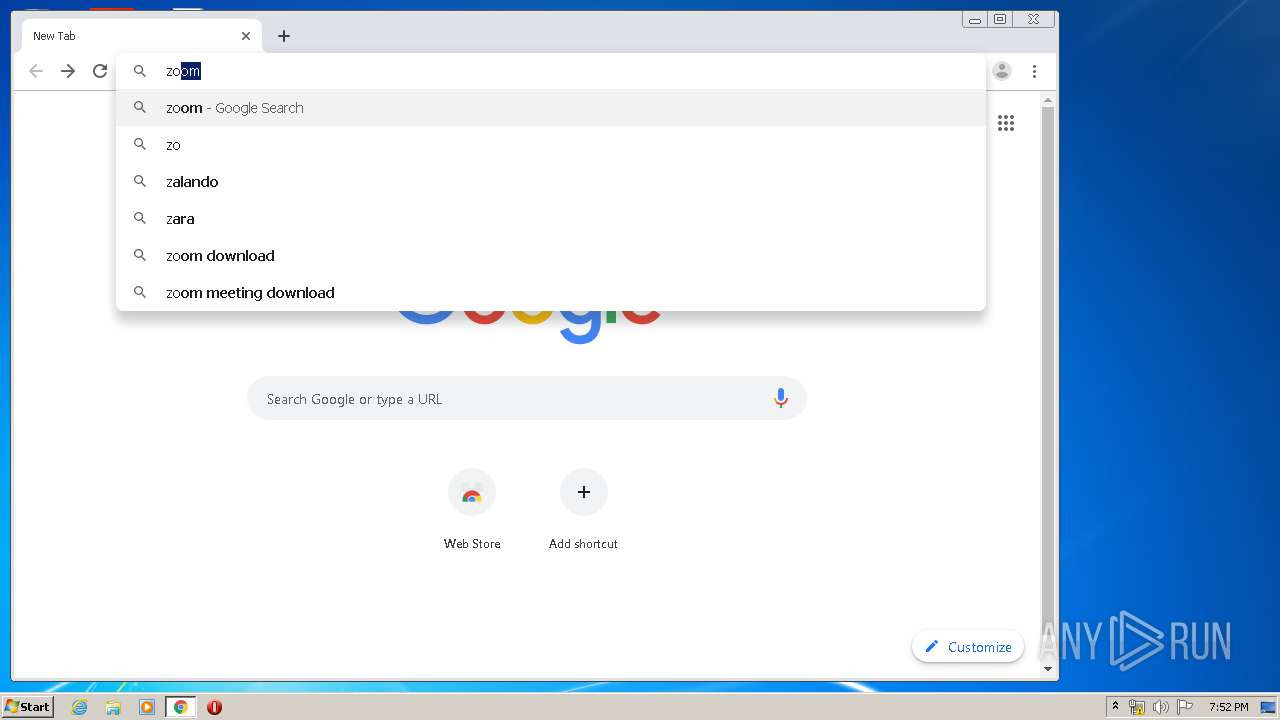
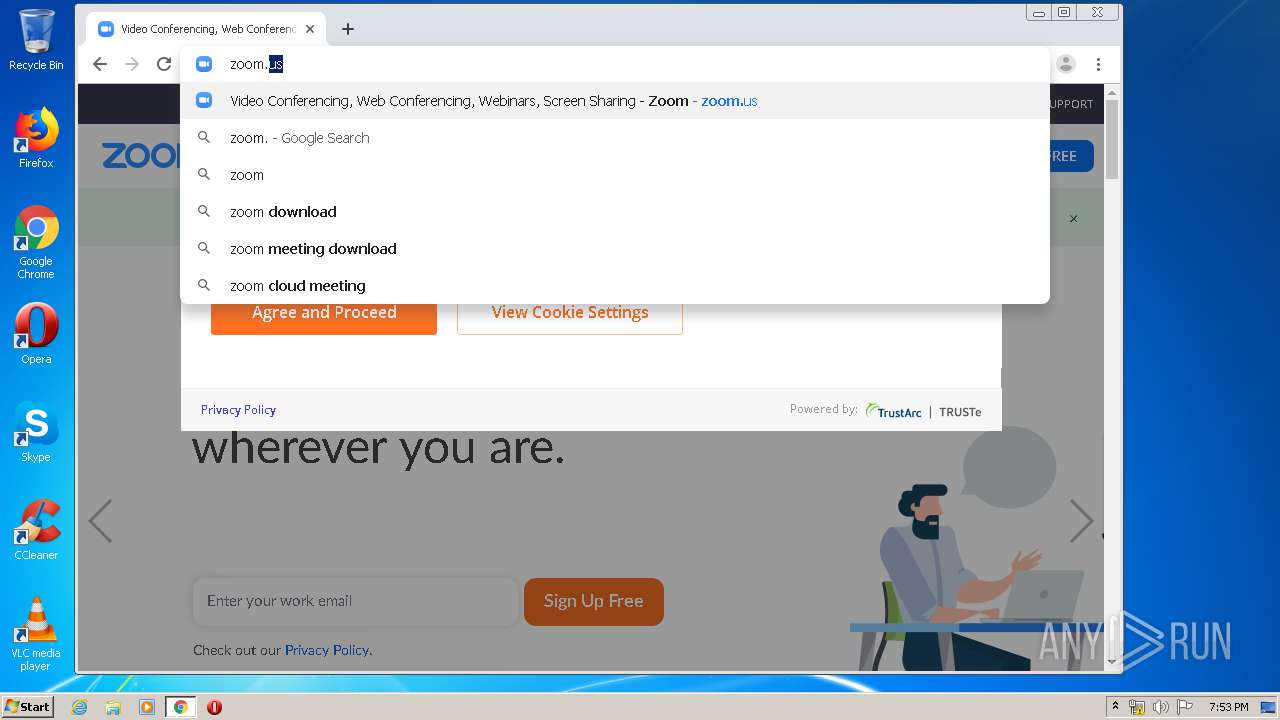
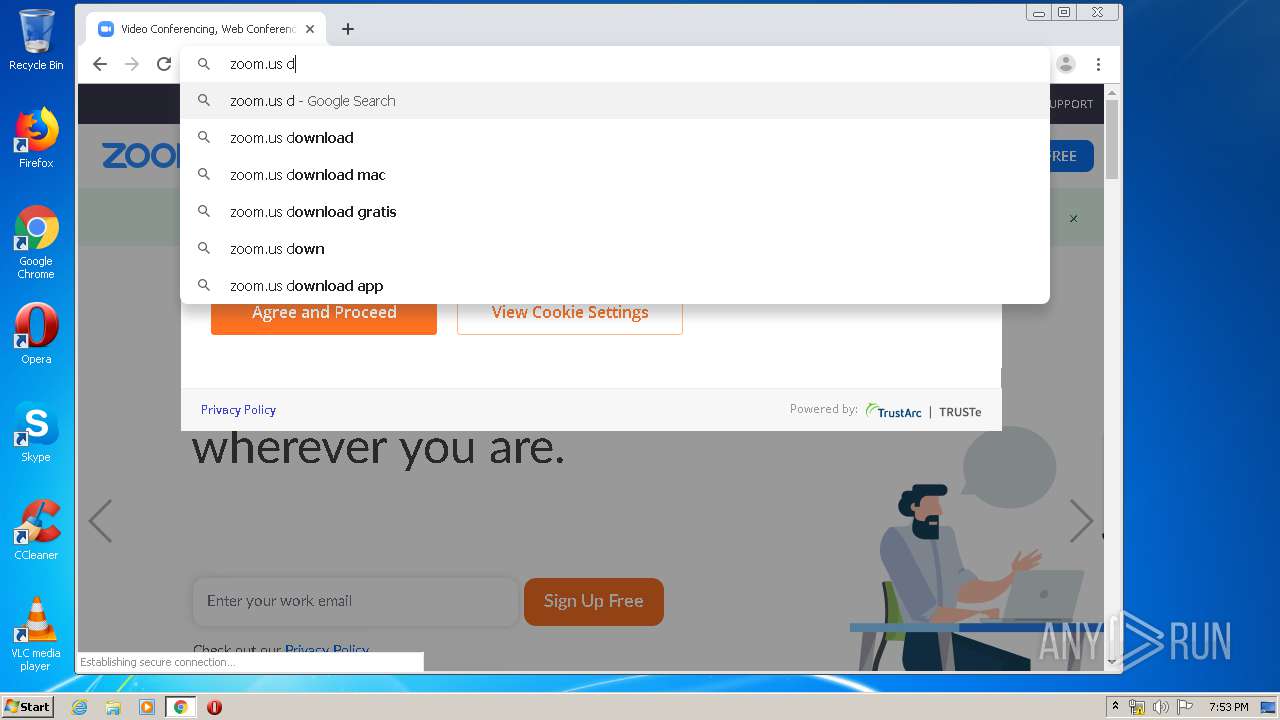
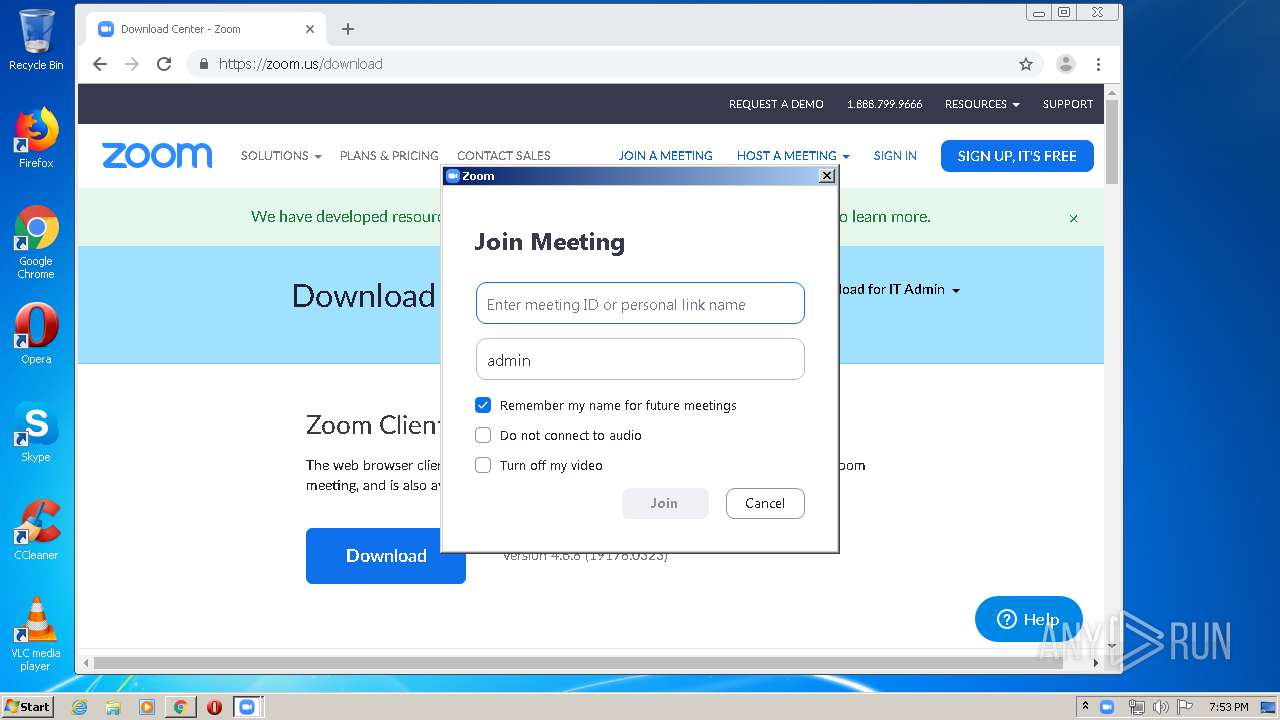
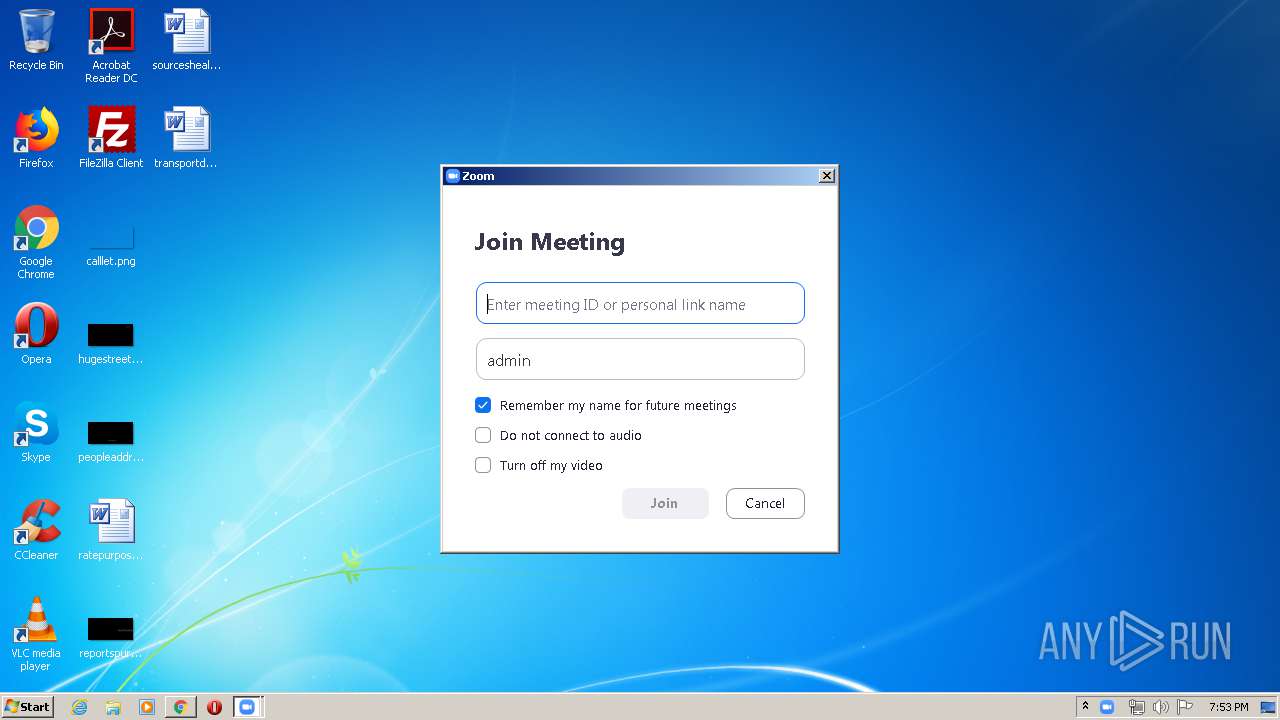
Manual execution by user
- chrome.exe (PID: 304)
Reads the hosts file
- chrome.exe (PID: 304)
- chrome.exe (PID: 3960)
Application launched itself
- chrome.exe (PID: 304)
- iexplore.exe (PID: 2432)
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 3516)
Reads internet explorer settings
- iexplore.exe (PID: 2448)
- iexplore.exe (PID: 1848)
Changes settings of System certificates
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 3152)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
63
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,520881860142997908,10443824306443473792,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11288569589719689797 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,520881860142997908,10443824306443473792,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7681392689186413935 --mojo-platform-channel-handle=3868 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,520881860142997908,10443824306443473792,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1578149427850768690 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,520881860142997908,10443824306443473792,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6734194636676052614 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,520881860142997908,10443824306443473792,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8406388555749124017 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,520881860142997908,10443824306443473792,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13495877307442143768 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,520881860142997908,10443824306443473792,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12745449004486257779 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | dllhost.exe | svchost.exe | |||||||||||||
Integrity Level: UNKNOWN Exit code: 0 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,520881860142997908,10443824306443473792,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10240347149981581083 --mojo-platform-channel-handle=3080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
13 042
Read events
4 012
Write events
6 116
Delete events
2 914
Modification events
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 462011128 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803057 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3052) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
95
Suspicious files
209
Text files
312
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab70B4.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar70B5.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\I62BBKP0.txt | — | |
MD5:— | SHA256:— | |||
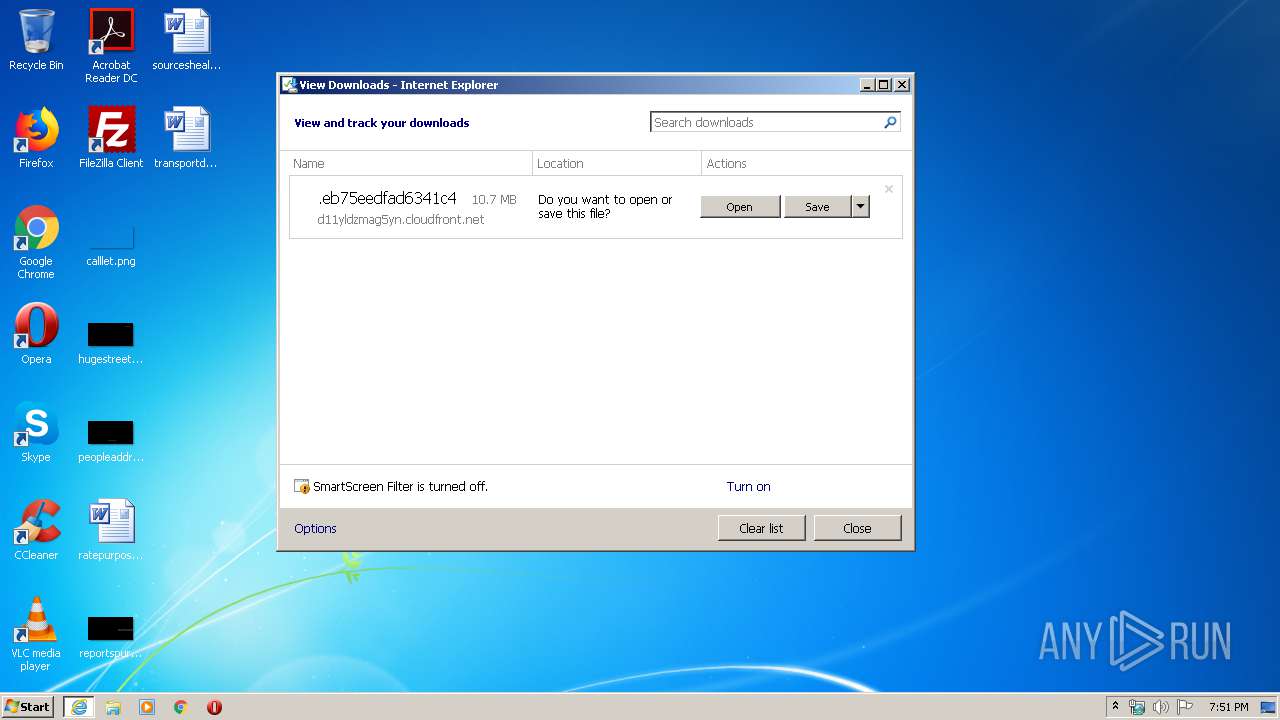
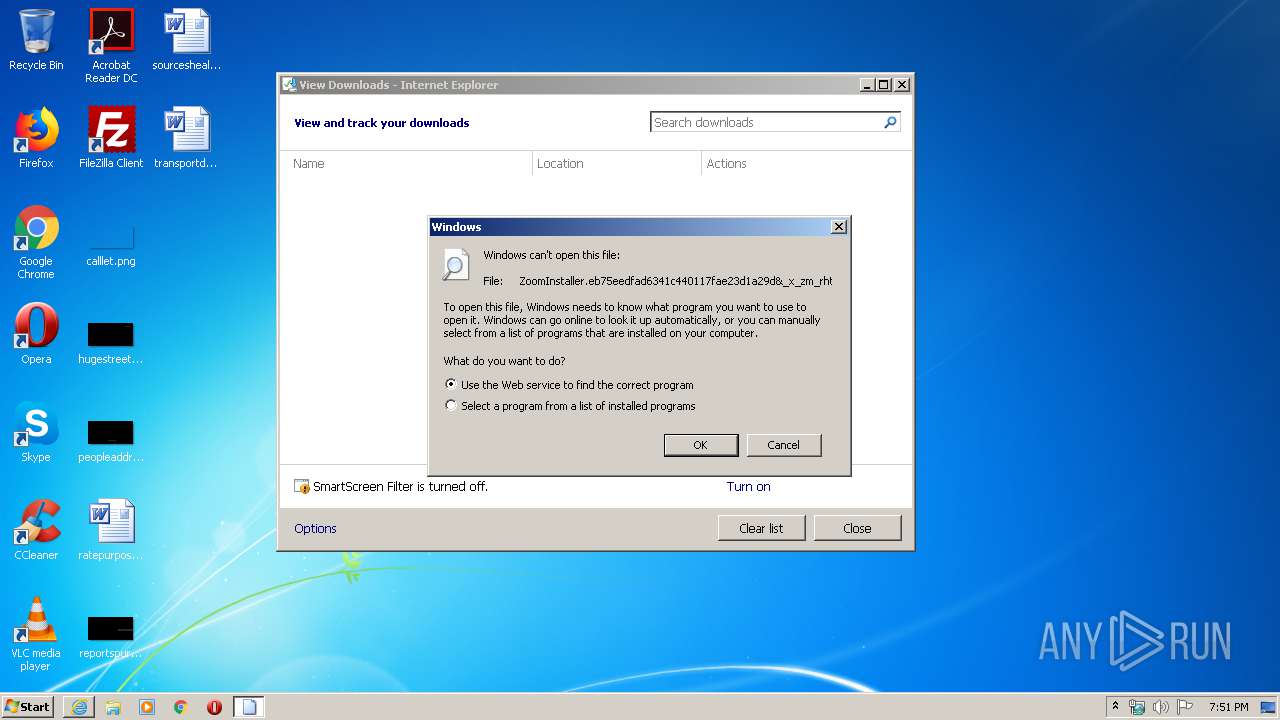
| 3716 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ZoomInstaller.eb75eedfad6341c440117fae23d1a29d&_x_zm_rhtaid=195.7fkn8kj.partial | — | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF054C7E3CC68EC5E6.TMP | — | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ZoomInstaller.eb75eedfad6341c440117fae23d1a29d&_x_zm_rhtaid=195.7fkn8kj.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF072AF836B1121971.TMP | — | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{4748B811-7064-11EA-972D-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 304 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E7E594B-130.pma | — | |
MD5:— | SHA256:— | |||
| 3716 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C5FD5BF0CE6372B1CAFE381FD0BC969C | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
176
DNS requests
120
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3716 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
2448 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEF%2FPCEW05qXHCAAAAAAyCqs%3D | US | der | 471 b | whitelisted |
3960 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2448 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
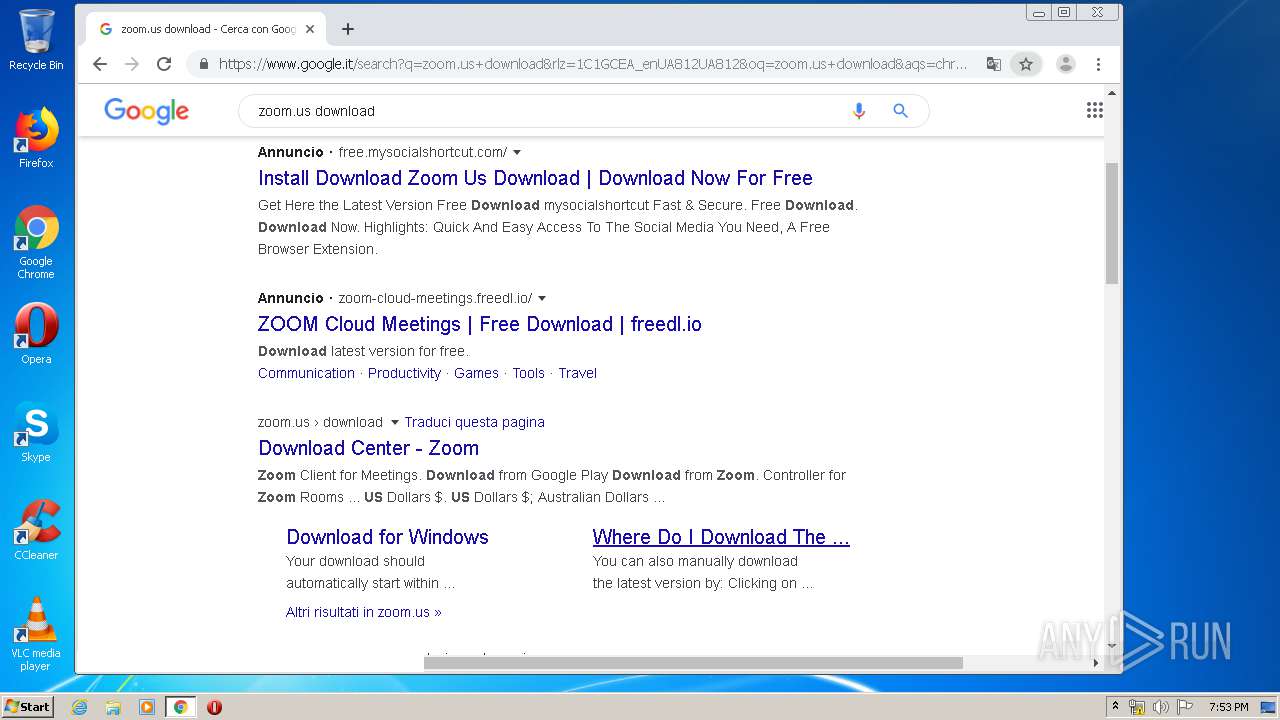
3960 | chrome.exe | GET | 301 | 3.235.72.190:80 | http://zoom.us/client/latest/zoominstaller.exe | US | html | 161 b | whitelisted |
2448 | iexplore.exe | GET | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEF%2FPCEW05qXHCAAAAAAyCqs%3D | US | der | 471 b | whitelisted |
3716 | iexplore.exe | GET | 200 | 23.37.43.27:80 | http://s.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEGMYDTj7gJd4qdA1oxYY%2BEA%3D | NL | der | 1.71 Kb | shared |
3960 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3716 | iexplore.exe | 52.202.62.235:443 | — | Amazon.com, Inc. | US | suspicious |
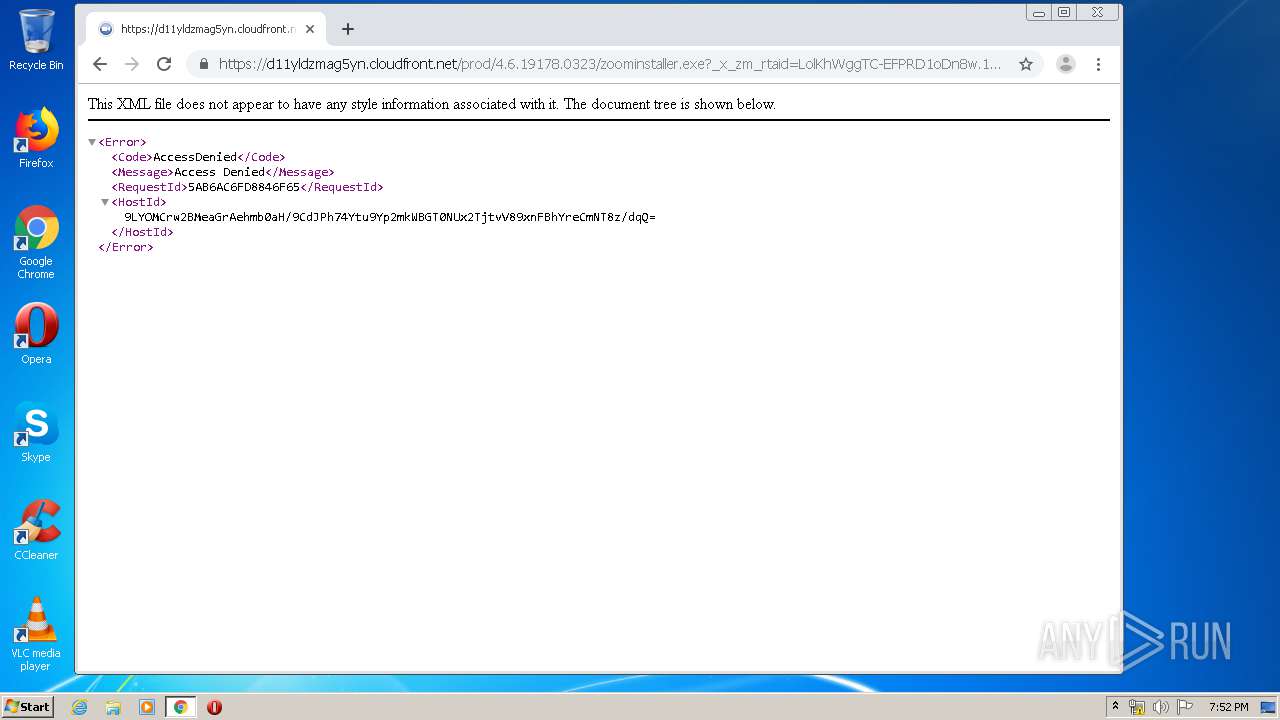
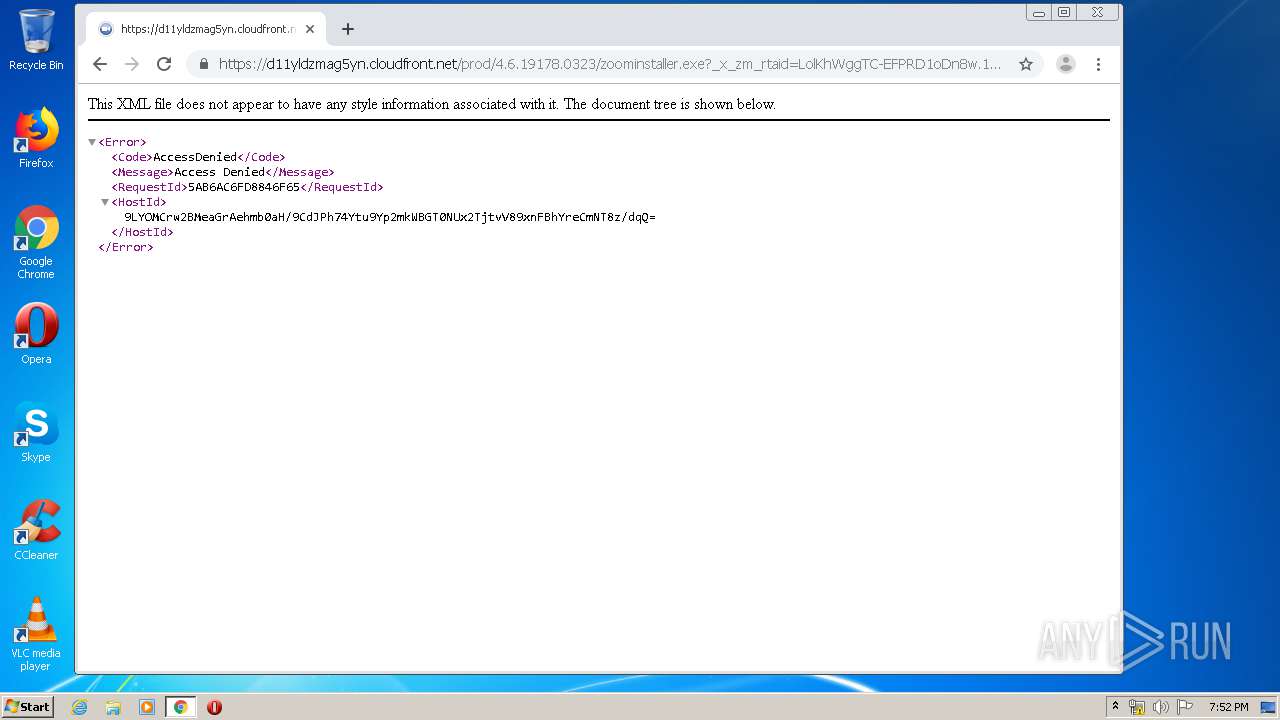
3716 | iexplore.exe | 13.224.197.164:443 | d11yldzmag5yn.cloudfront.net | — | US | unknown |
3716 | iexplore.exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3716 | iexplore.exe | 23.37.43.27:80 | s.symcd.com | Akamai Technologies, Inc. | NL | whitelisted |
3960 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3716 | iexplore.exe | 192.124.249.41:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
3960 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3960 | chrome.exe | 172.217.22.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3716 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zoom.us |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
d11yldzmag5yn.cloudfront.net |
| whitelisted |
s.symcd.com |
| shared |
ocsp.digicert.com |
| whitelisted |
crl.godaddy.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | |
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\uninstall |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\uninstall |
Installer.exe | |
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\bin |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\ |