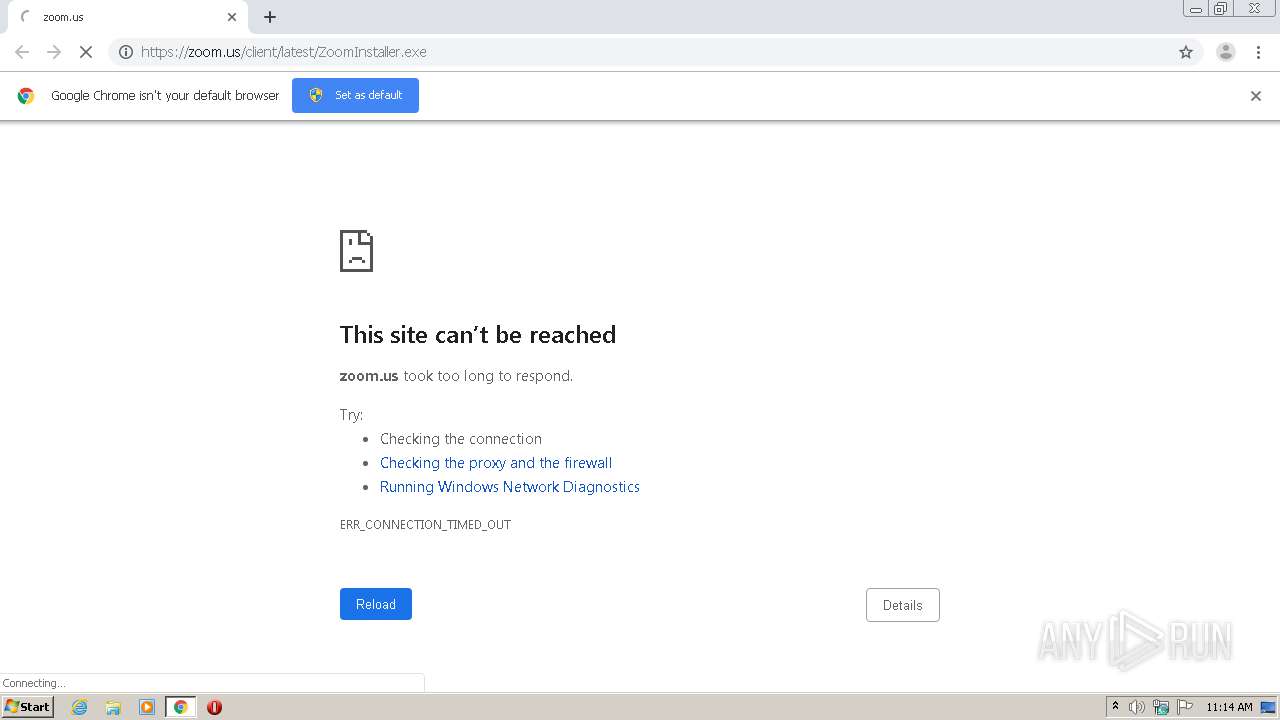
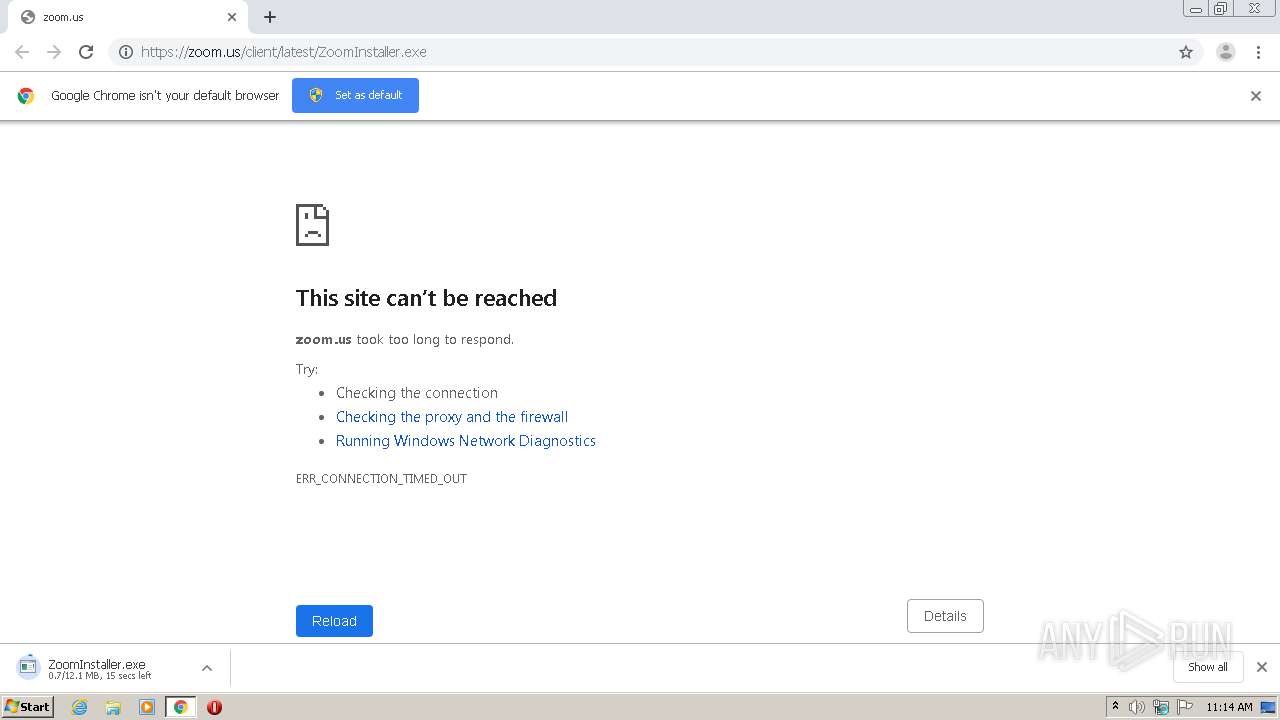
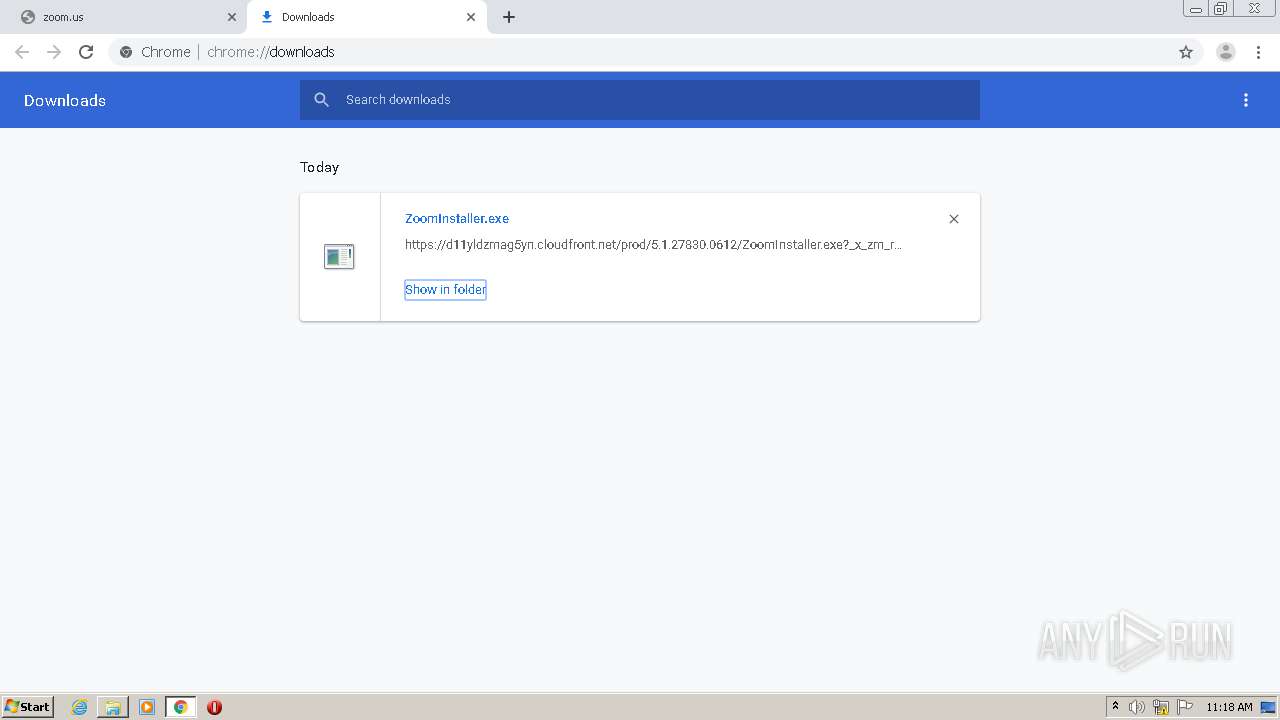
| URL: | https://zoom.us/client/latest/ZoomInstaller.exe |
| Full analysis: | https://app.any.run/tasks/8910d442-d950-4487-9434-77c7c55d0026 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2020, 10:14:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 063482C1F099E60CDD5BDFC1EBF056E1 |
| SHA1: | 588BCC720708BC1C81861CF122C9A03B9D469F44 |
| SHA256: | C272690A135BEF593718080C339CF0ED18F68BFBDE40BF9A48421540BD4C9DBB |
| SSDEEP: | 3:N88LW3RRiTXLNn:28LWWTXLN |
MALICIOUS
Actions looks like stealing of personal data
- Installer.exe (PID: 3980)
- Installer.exe (PID: 648)
Application was dropped or rewritten from another process
- ZoomInstaller.exe (PID: 1444)
- Installer.exe (PID: 3980)
- Installer.exe (PID: 4084)
- Zoom.exe (PID: 3036)
- Zoom.exe (PID: 2152)
- ZoomInstaller.exe (PID: 3692)
- Installer.exe (PID: 648)
- Installer.exe (PID: 372)
Loads dropped or rewritten executable
- Zoom.exe (PID: 3036)
- Installer.exe (PID: 3980)
- Zoom.exe (PID: 2152)
Changes settings of System certificates
- Installer.exe (PID: 3980)
SUSPICIOUS
Executable content was dropped or overwritten
- ZoomInstaller.exe (PID: 1444)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 404)
- Installer.exe (PID: 3980)
- ZoomInstaller.exe (PID: 3692)
- Installer.exe (PID: 648)
Modifies files in Chrome extension folder
- chrome.exe (PID: 404)
Application launched itself
- Installer.exe (PID: 3980)
- Zoom.exe (PID: 3036)
- Installer.exe (PID: 648)
Creates a software uninstall entry
- Installer.exe (PID: 3980)
Creates files in the user directory
- Installer.exe (PID: 3980)
- Zoom.exe (PID: 3036)
- Zoom.exe (PID: 2152)
- Installer.exe (PID: 648)
Modifies the open verb of a shell class
- Installer.exe (PID: 3980)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 3980)
Adds / modifies Windows certificates
- Installer.exe (PID: 3980)
INFO
Application launched itself
- chrome.exe (PID: 404)
Reads settings of System Certificates
- chrome.exe (PID: 4072)
- chrome.exe (PID: 404)
- Installer.exe (PID: 3980)
Reads Internet Cache Settings
- chrome.exe (PID: 404)
Reads the hosts file
- chrome.exe (PID: 404)
- chrome.exe (PID: 4072)
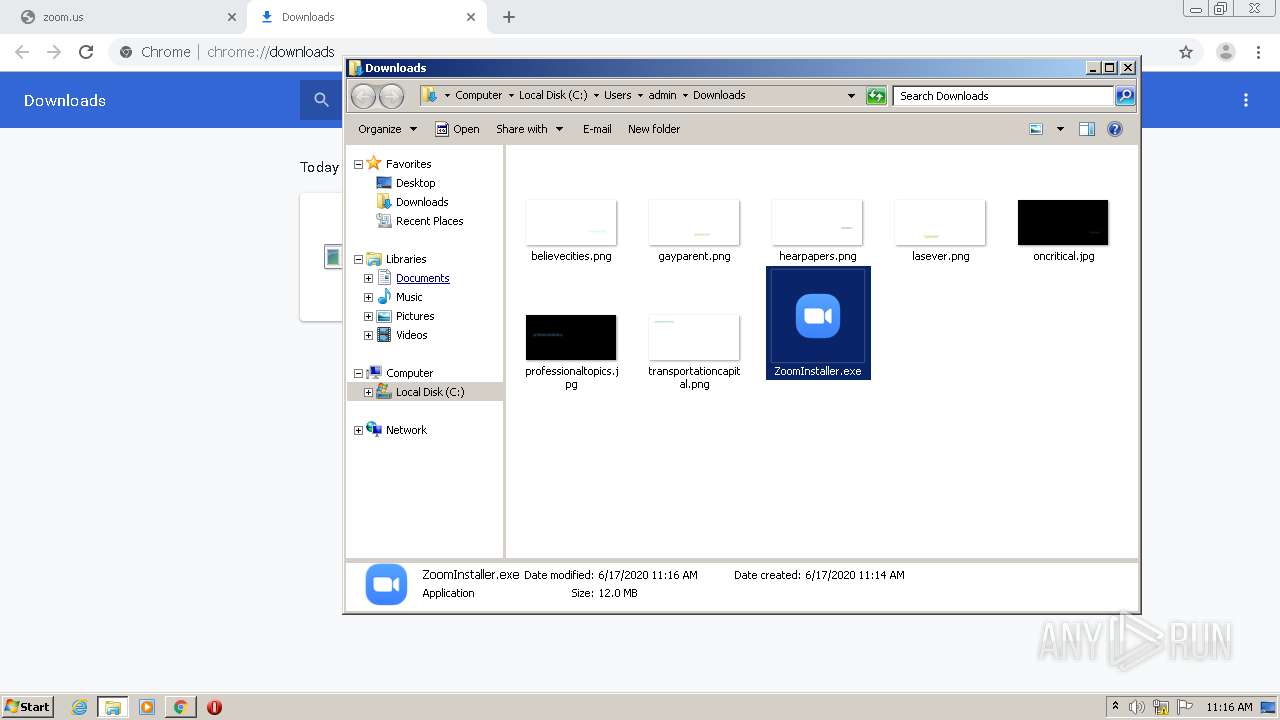
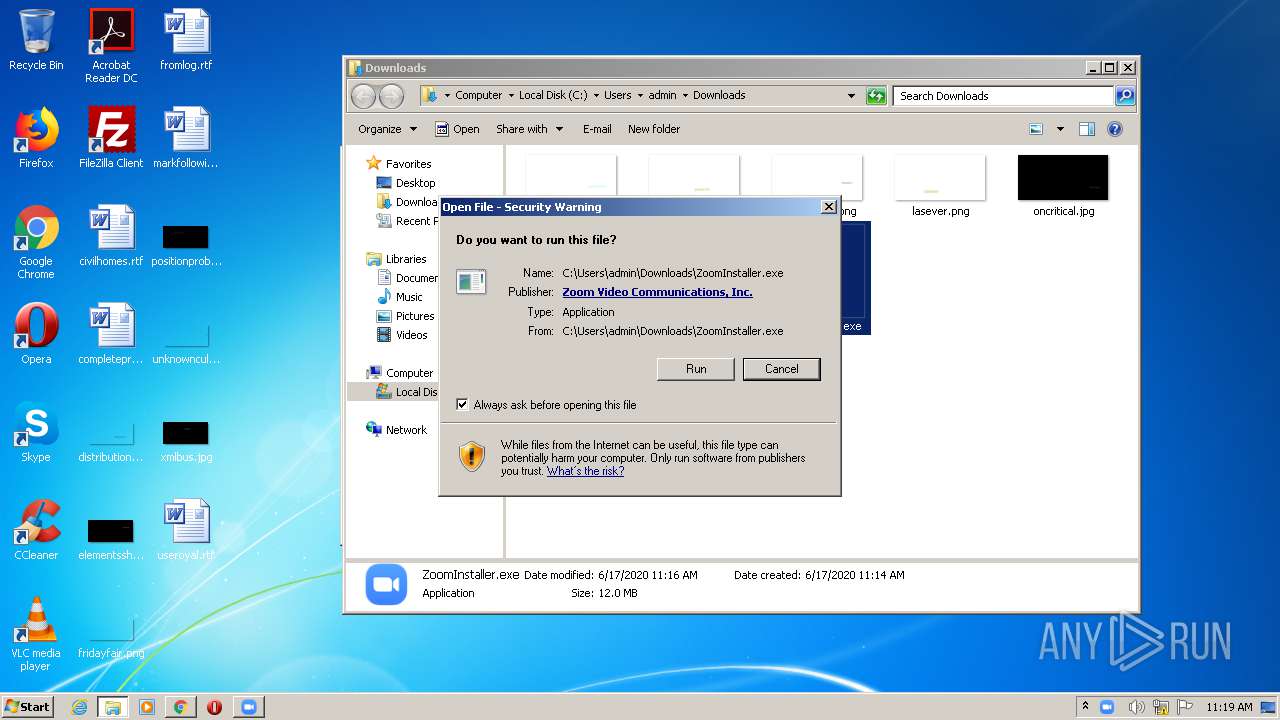
Manual execution by user
- ZoomInstaller.exe (PID: 1444)
- ZoomInstaller.exe (PID: 3692)
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 3980)
- Installer.exe (PID: 648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
38
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Users\admin\AppData\Local\Temp\7zSC6E8B70A\Installer.exe" /addfwexception --bin_home="C:\Users\admin\AppData\Roaming\Zoom\bin_00" | C:\Users\admin\AppData\Local\Temp\7zSC6E8B70A\Installer.exe | Installer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: HIGH Description: Zoom Installer Exit code: 0 Version: 5,1,27830,0612 Modules
| |||||||||||||||
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://zoom.us/client/latest/ZoomInstaller.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,8656611376081827868,12277255470542468146,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15084862841502637574 --mojo-platform-channel-handle=1920 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 648 | .\Installer.exe | C:\Users\admin\AppData\Local\Temp\7zSC6E8B70A\Installer.exe | ZoomInstaller.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Installer Exit code: 0 Version: 5,1,27830,0612 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,8656611376081827868,12277255470542468146,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10926745420747899233 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,8656611376081827868,12277255470542468146,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6585194159128815840 --mojo-platform-channel-handle=4268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
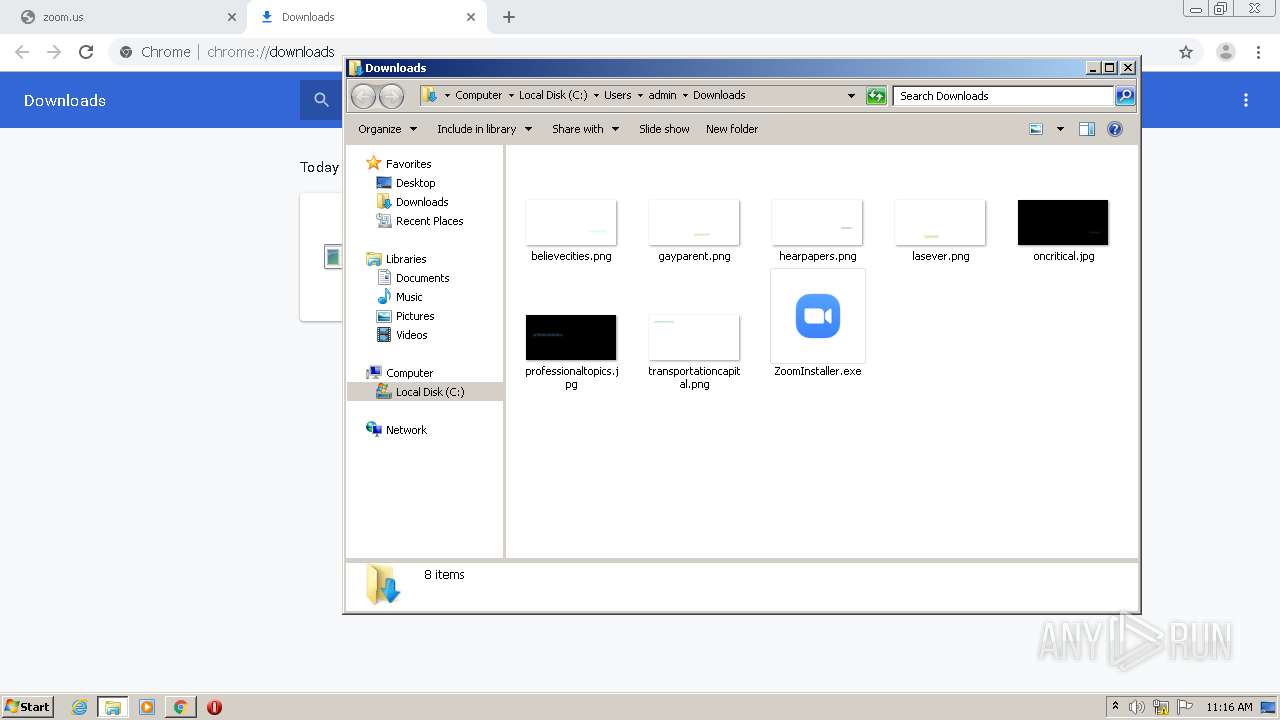
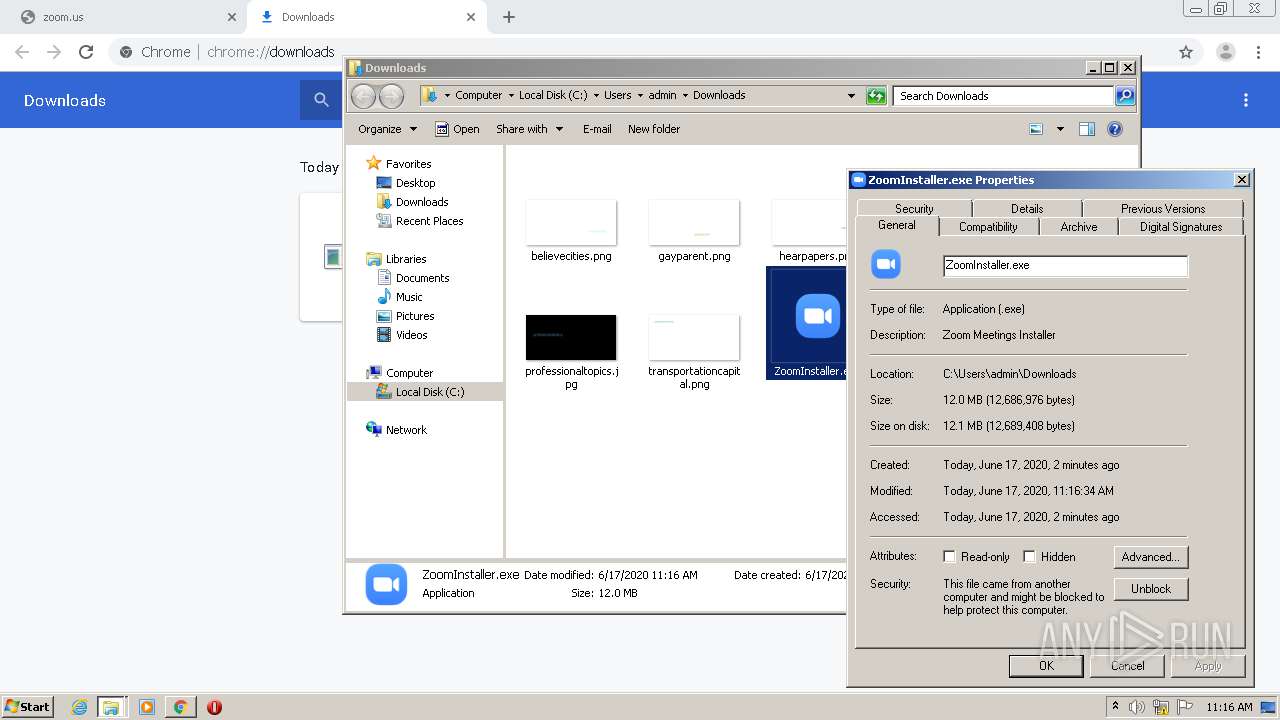
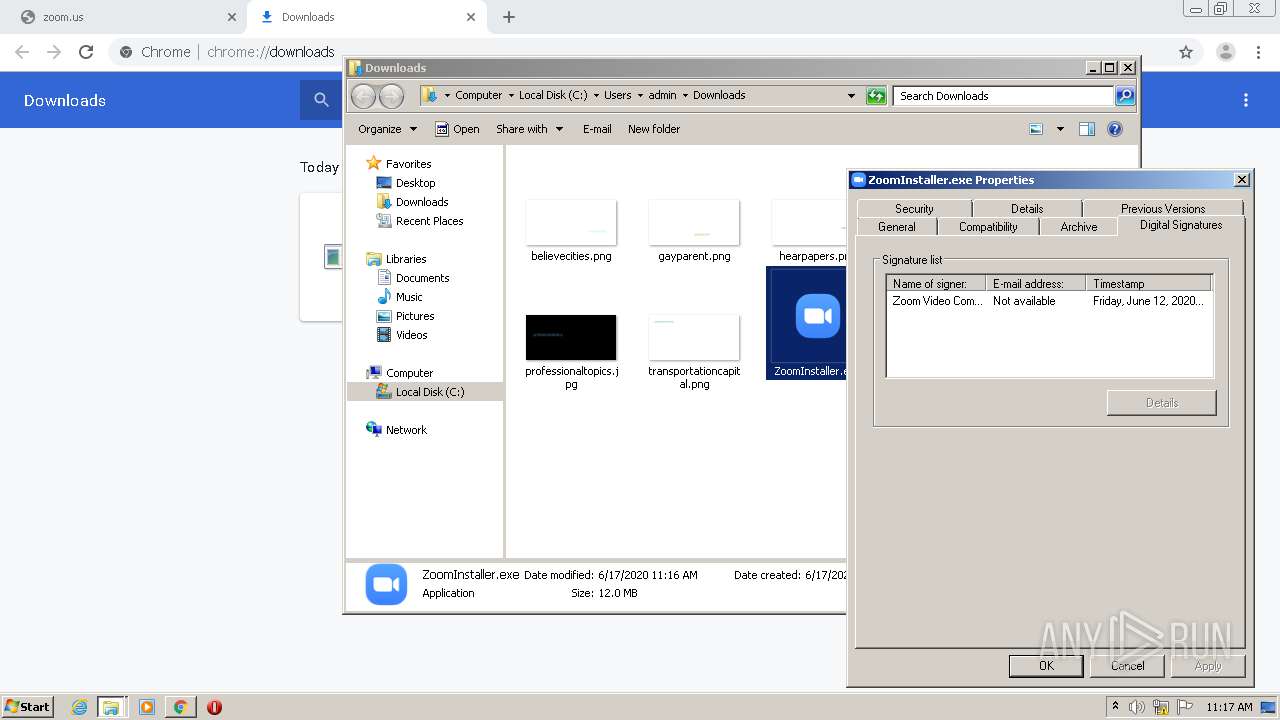
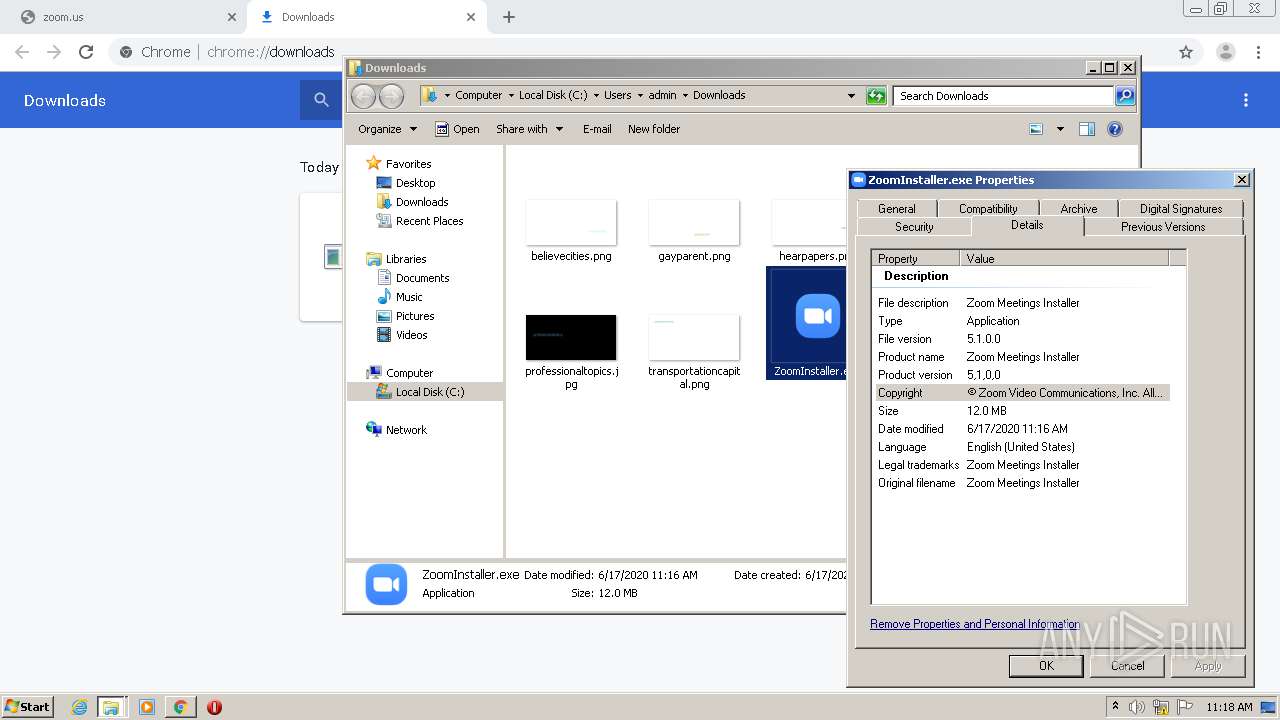
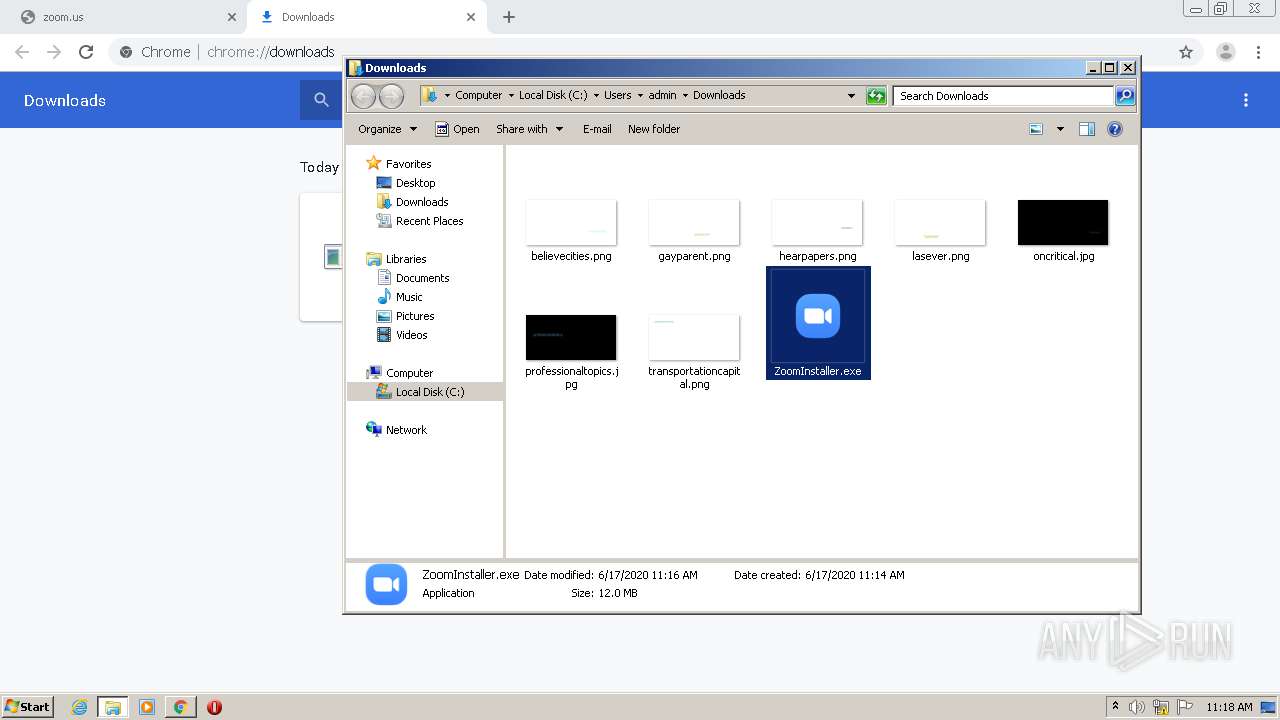
| 1444 | "C:\Users\admin\Downloads\ZoomInstaller.exe" | C:\Users\admin\Downloads\ZoomInstaller.exe | explorer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: HIGH Description: Zoom Meetings Installer Exit code: 0 Version: 5,1,0,0 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=440 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,8656611376081827868,12277255470542468146,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8978600460424054556 --mojo-platform-channel-handle=3668 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,8656611376081827868,12277255470542468146,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3268690571033567870 --mojo-platform-channel-handle=2188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 545
Read events
2 160
Write events
1 355
Delete events
30
Modification events
| (PID) Process: | (1488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 404-13236862463297375 |
Value: 259 | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (404) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
198
Suspicious files
67
Text files
285
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EE9ED00-194.pma | — | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ee218d79-e042-45ea-93bd-1319945e1aa2.tmp | — | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15cb68.TMP | text | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF15cbf4.TMP | text | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15cd8b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
27
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4072 | chrome.exe | GET | 204 | 216.58.205.227:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
4072 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
4072 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
4072 | chrome.exe | GET | 200 | 74.125.100.73:80 | http://r4---sn-5hne6nsz.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=185.128.27.133&mm=28&mn=sn-5hne6nsz&ms=nvh&mt=1592388794&mv=m&mvi=3&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
4072 | chrome.exe | GET | 200 | 172.217.132.103:80 | http://r2---sn-5hne6nsy.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.128.27.133&mm=28&mn=sn-5hne6nsy&ms=nvh&mt=1592388794&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4072 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 52.202.62.232:443 | zoom.us | Amazon.com, Inc. | US | suspicious |
4072 | chrome.exe | 216.58.205.227:80 | www.gstatic.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 216.58.207.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.132.103:80 | r2---sn-5hne6nsy.gvt1.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 74.125.100.73:80 | r4---sn-5hne6nsz.gvt1.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 172.217.22.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 216.58.205.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zoom.us |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
d11yldzmag5yn.cloudfront.net |
| whitelisted |
r2---sn-5hne6nsy.gvt1.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\uninstall |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\bin |
Installer.exe | [ProductPathHelper::RecursiveRemoveDirA] Path is: |
Installer.exe | |
Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\ |