| File name: | CuteWriter.exe |
| Full analysis: | https://app.any.run/tasks/4f63eba3-ffef-4449-bd4e-528d7e827cb7 |
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2023, 12:42:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 33A5B53825E6DEF2073DF020E4266921 |
| SHA1: | 3A5AADF9C98DC459914D5CF4D3E9D9029BB5472D |
| SHA256: | C25E751C467B09A3D7CA10159B91D7A76EB8A9BC883D5C1EE894B4F3027E26A3 |
| SSDEEP: | 24576:cna2FToSrKUWD0RwbRDsaV4WiBDsFtMi/0NXEYDvb/NoWZnEUpEL9VPQBnchvQ7s:caeUThDDABfUX8NUYzG8svGyC |
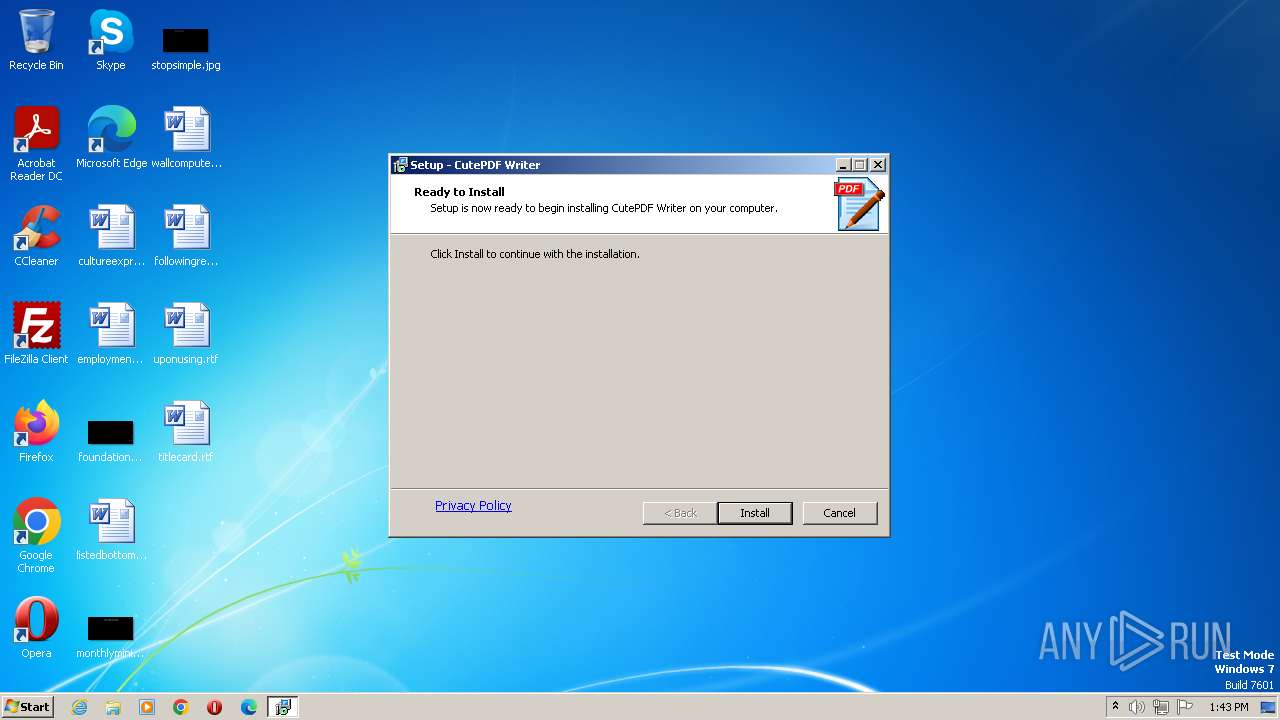
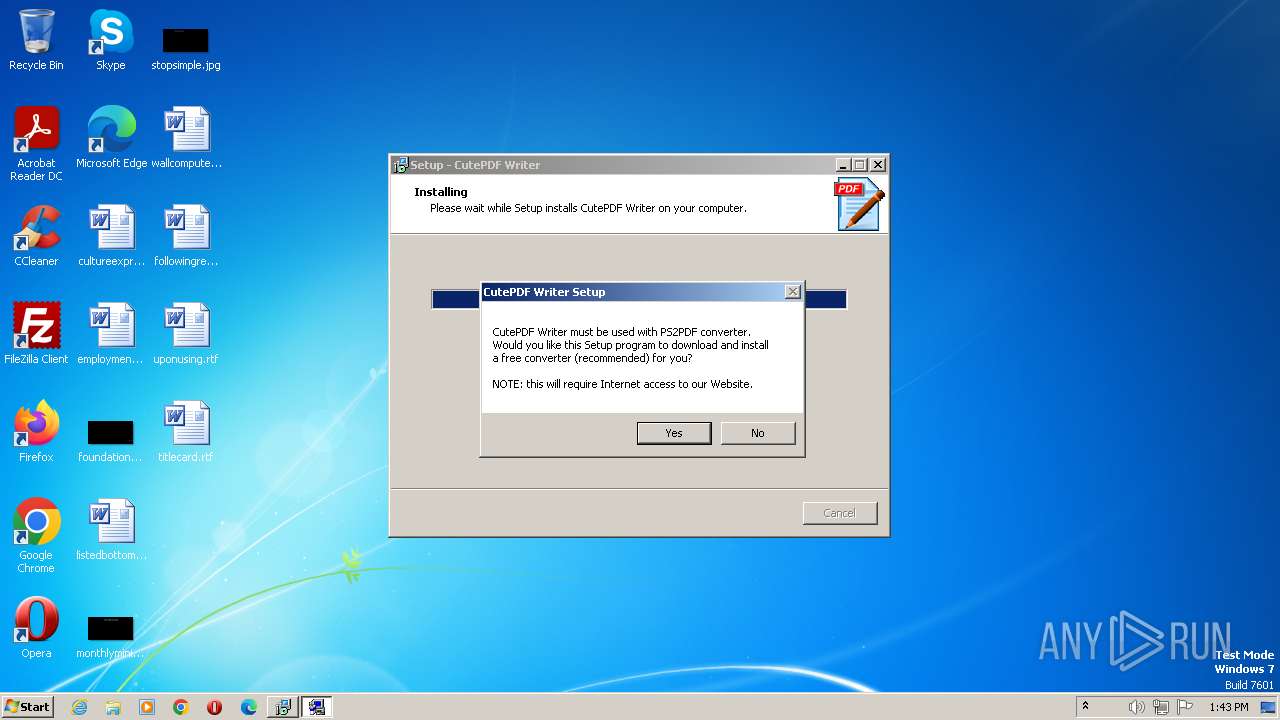
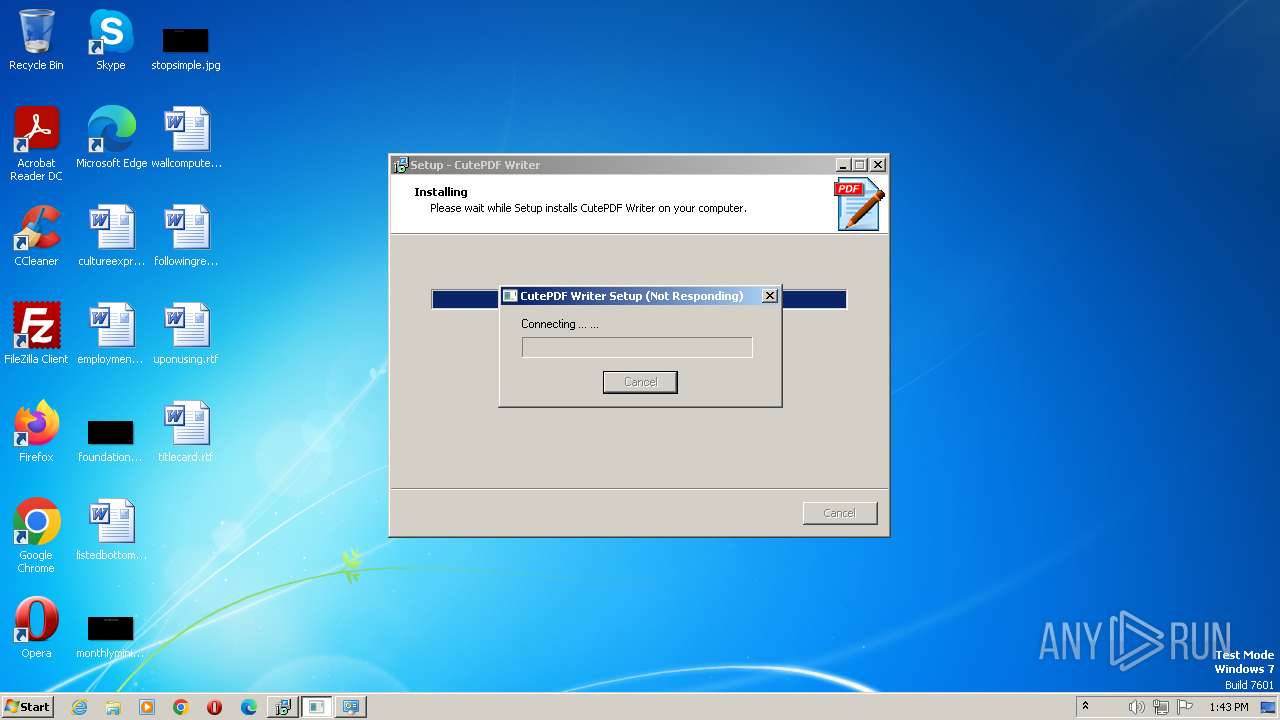
MALICIOUS
Loads dropped or rewritten executable
- CuteWriter.tmp (PID: 616)
- Setup.exe (PID: 952)
- spoolsv.exe (PID: 1228)
Creates a writable file the system directory
- Setup.exe (PID: 952)
- spoolsv.exe (PID: 1228)
SUSPICIOUS
Executable content was dropped or overwritten
- CuteWriter.exe (PID: 1872)
- CuteWriter.exe (PID: 1848)
- CuteWriter.tmp (PID: 616)
- Setup.exe (PID: 952)
- spoolsv.exe (PID: 1228)
Reads the Windows owner or organization settings
- CuteWriter.tmp (PID: 616)
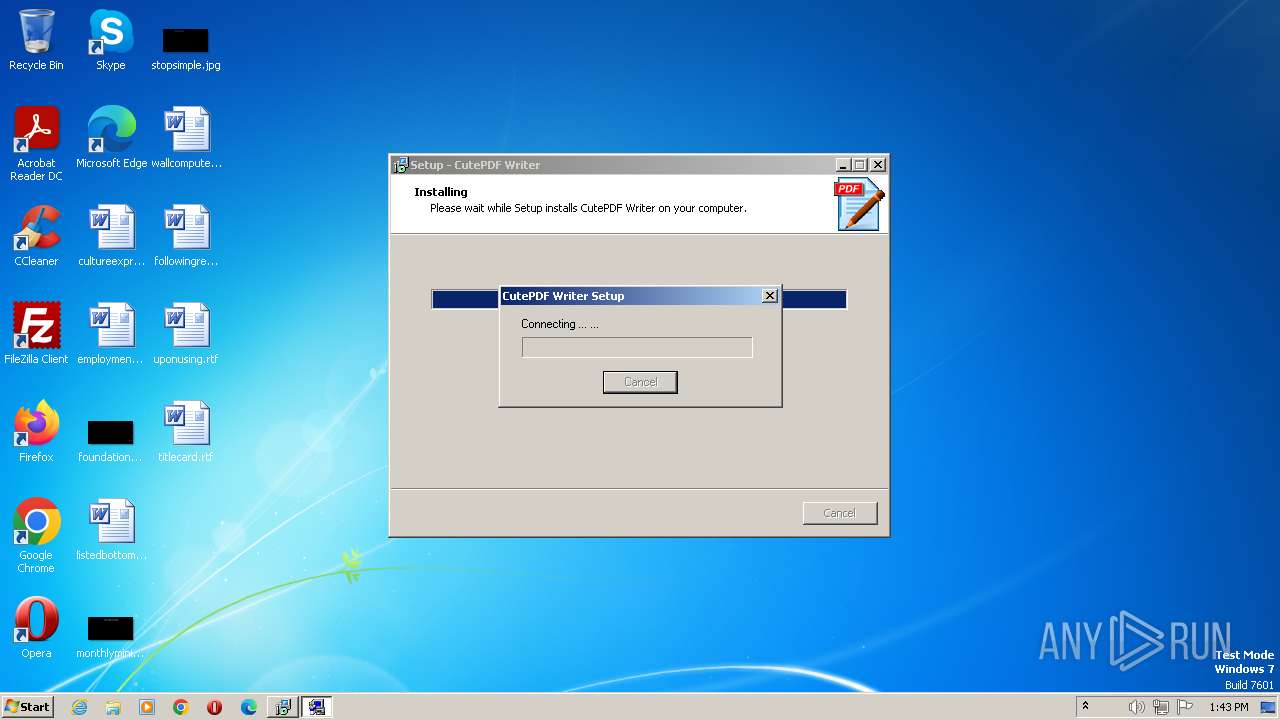
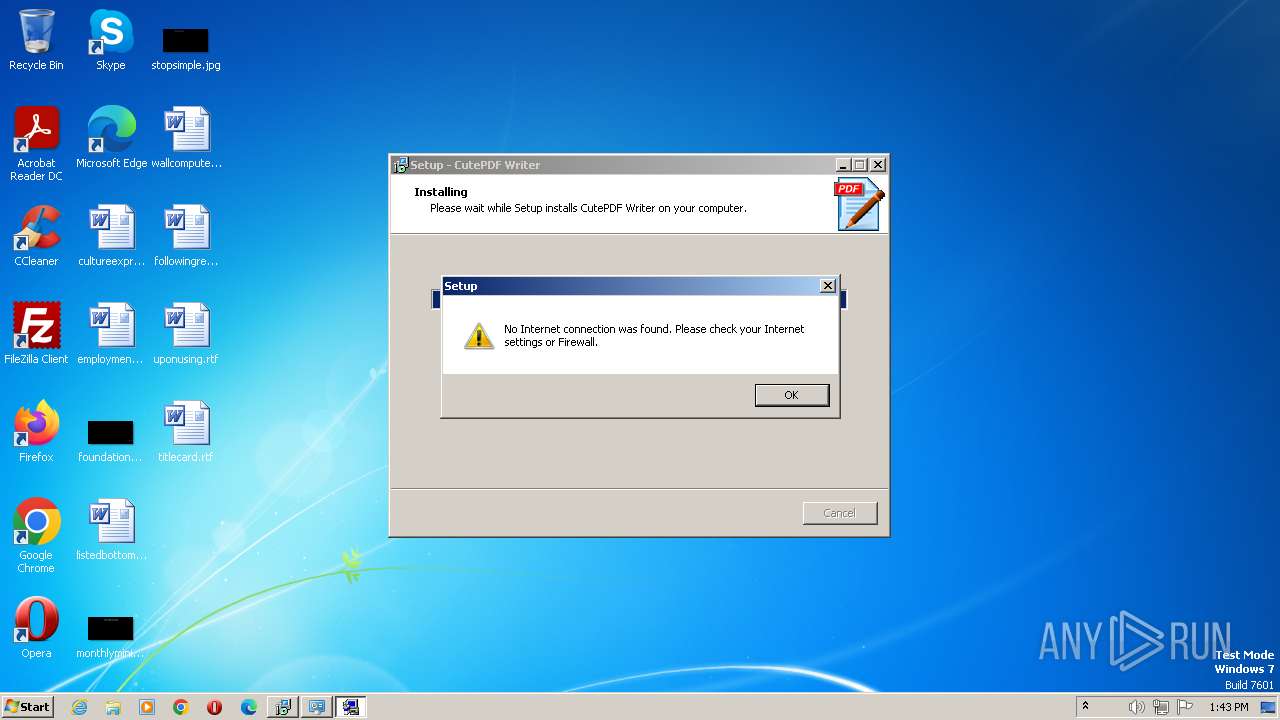
Reads the Internet Settings
- Offercast2801_ARS_.exe (PID: 2720)
- Offercast2801_ARS_.exe (PID: 2564)
- Setup.exe (PID: 952)
Application launched itself
- Offercast2801_ARS_.exe (PID: 2720)
Reads Microsoft Outlook installation path
- Offercast2801_ARS_.exe (PID: 2720)
Reads Internet Explorer settings
- Offercast2801_ARS_.exe (PID: 2720)
INFO
Reads the computer name
- CuteWriter.tmp (PID: 832)
- Offercast2801_ARS_.exe (PID: 2720)
- CuteWriter.tmp (PID: 616)
- Offercast2801_ARS_.exe (PID: 2564)
- Setup.exe (PID: 952)
Checks supported languages
- CuteWriter.exe (PID: 1872)
- CuteWriter.tmp (PID: 832)
- CuteWriter.exe (PID: 1848)
- CuteWriter.tmp (PID: 616)
- Offercast2801_ARS_.exe (PID: 2720)
- Offercast2801_ARS_.exe (PID: 2564)
- Setup.exe (PID: 952)
Create files in a temporary directory
- CuteWriter.exe (PID: 1872)
- CuteWriter.exe (PID: 1848)
- CuteWriter.tmp (PID: 616)
- Offercast2801_ARS_.exe (PID: 2720)
- Offercast2801_ARS_.exe (PID: 2564)
Checks proxy server information
- Offercast2801_ARS_.exe (PID: 2720)
- Offercast2801_ARS_.exe (PID: 2564)
- Setup.exe (PID: 952)
Reads the machine GUID from the registry
- Offercast2801_ARS_.exe (PID: 2564)
- Offercast2801_ARS_.exe (PID: 2720)
- Setup.exe (PID: 952)
Application was dropped or rewritten from another process
- CuteWriter.tmp (PID: 616)
- CuteWriter.tmp (PID: 832)
- Offercast2801_ARS_.exe (PID: 2720)
- Offercast2801_ARS_.exe (PID: 2564)
- Setup.exe (PID: 952)
Creates files or folders in the user directory
- Offercast2801_ARS_.exe (PID: 2564)
Creates files in the program directory
- Setup.exe (PID: 952)
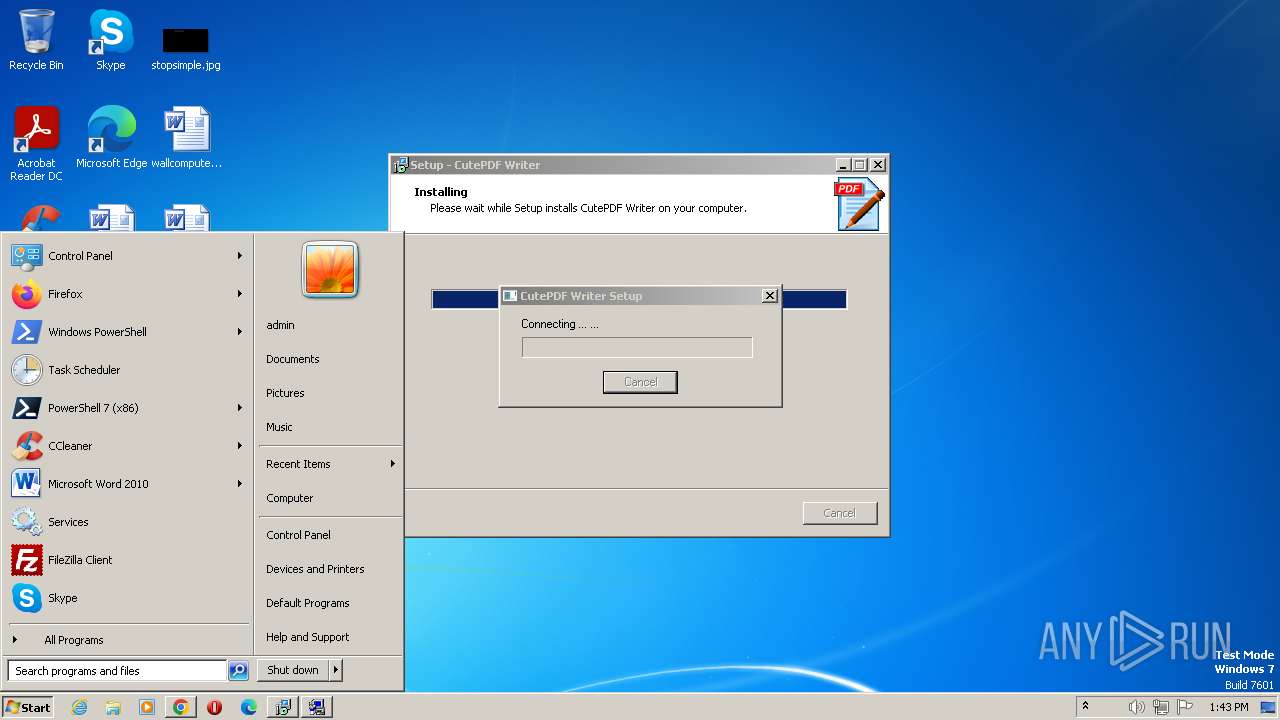
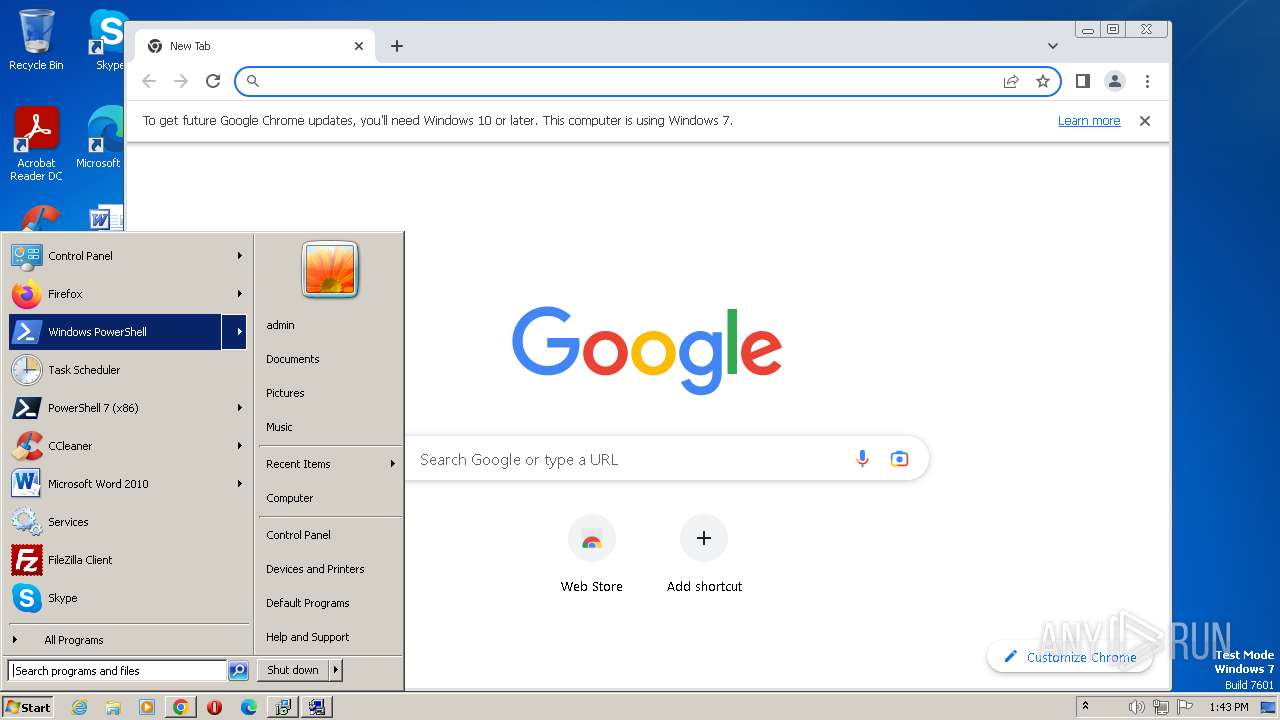
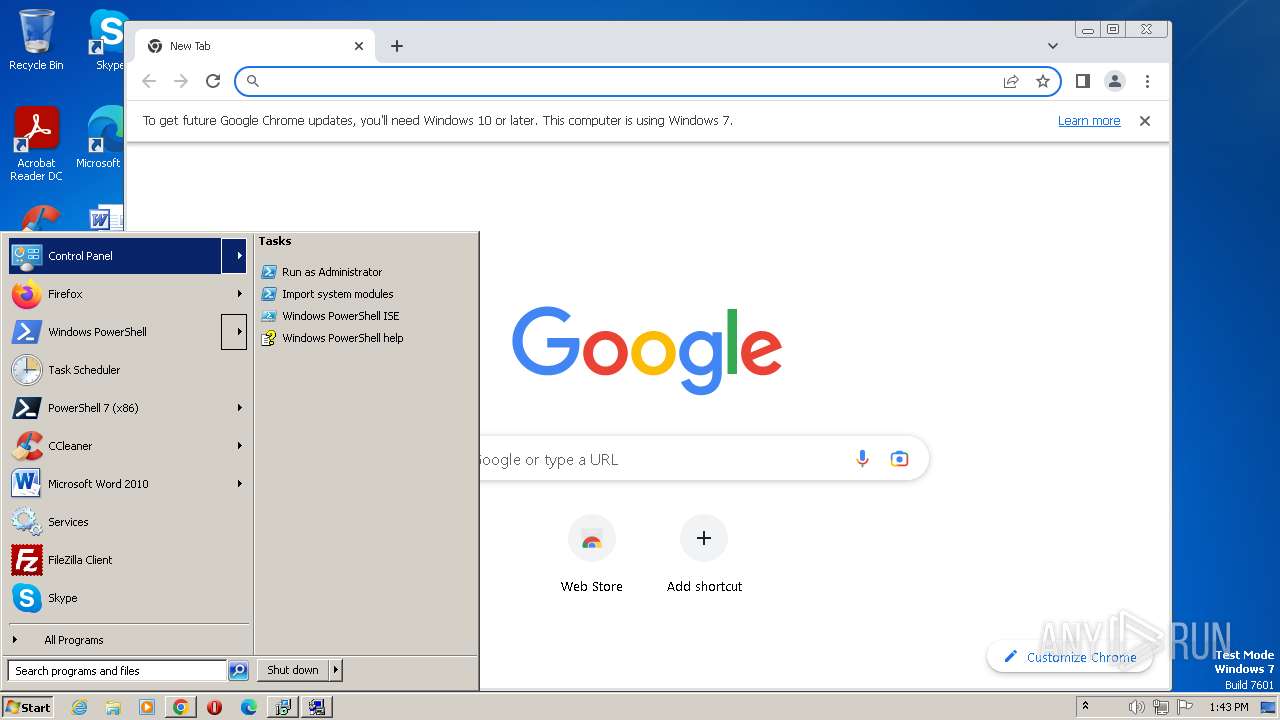
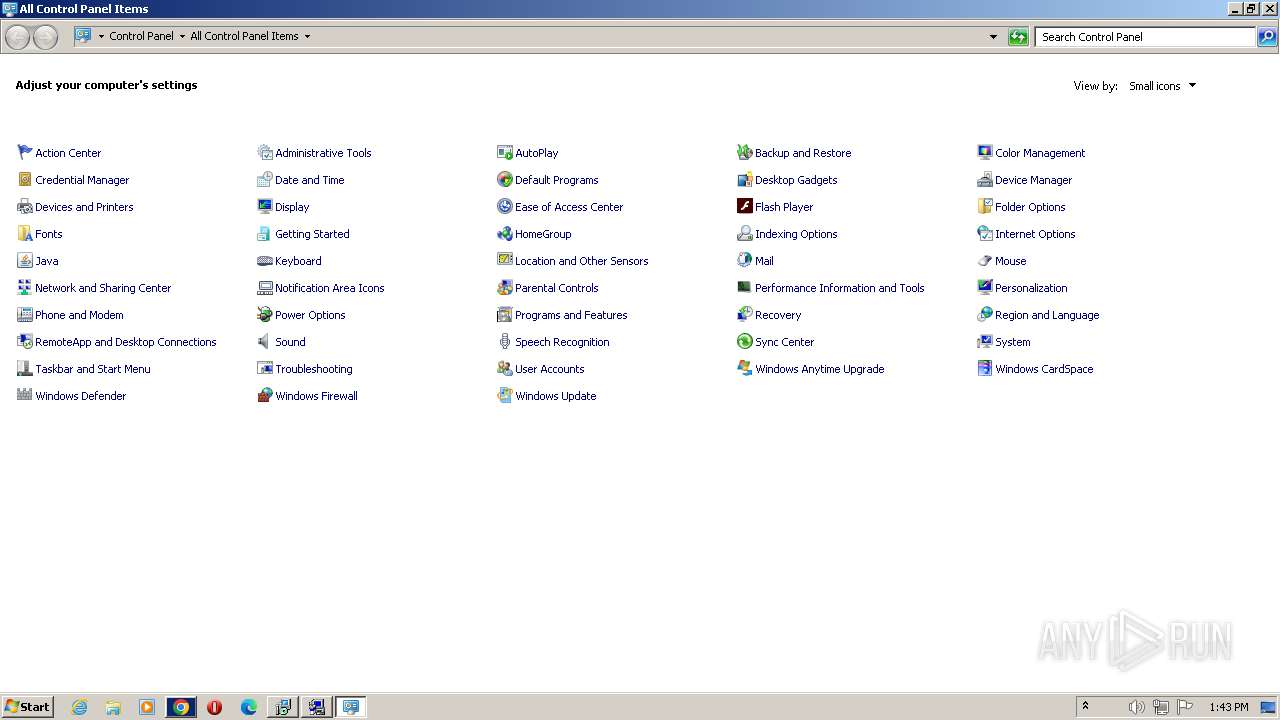
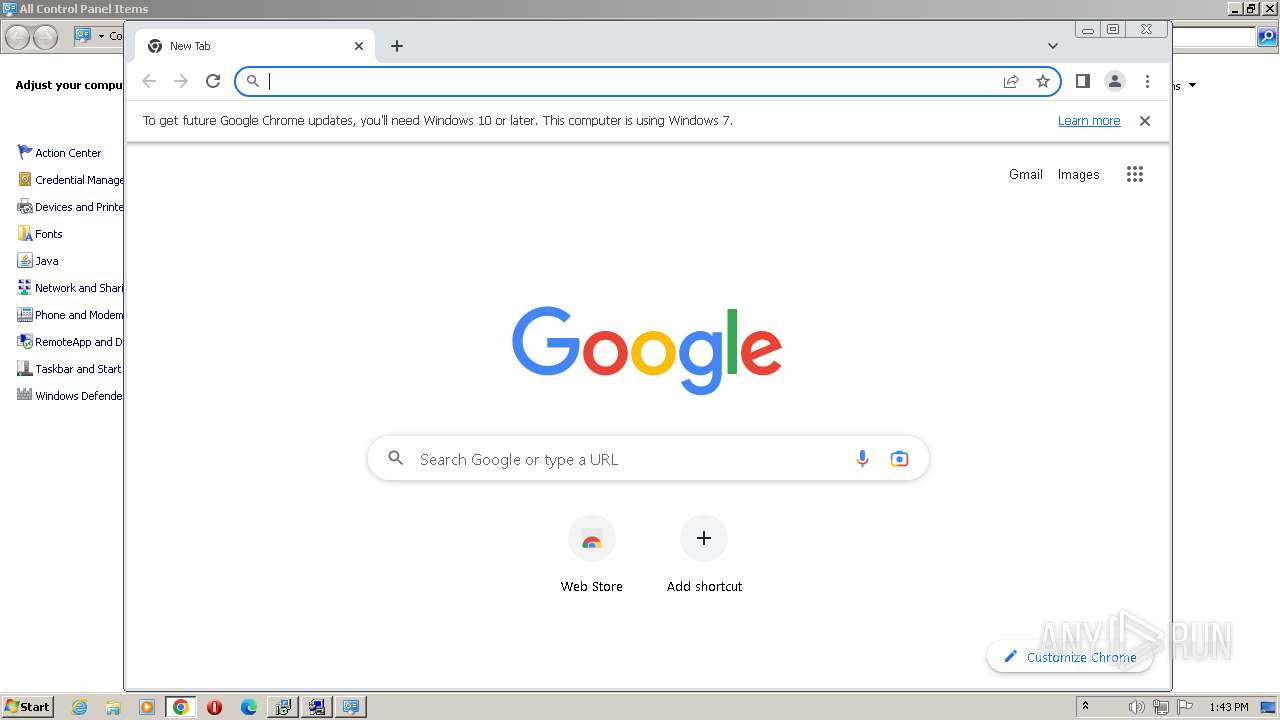
Manual execution by a user
- chrome.exe (PID: 4076)
- msedge.exe (PID: 2964)
- control.exe (PID: 2664)
Application launched itself
- chrome.exe (PID: 4076)
- msedge.exe (PID: 2528)
- msedge.exe (PID: 2964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| ProductVersion: | 3.0.0.1 |
|---|---|
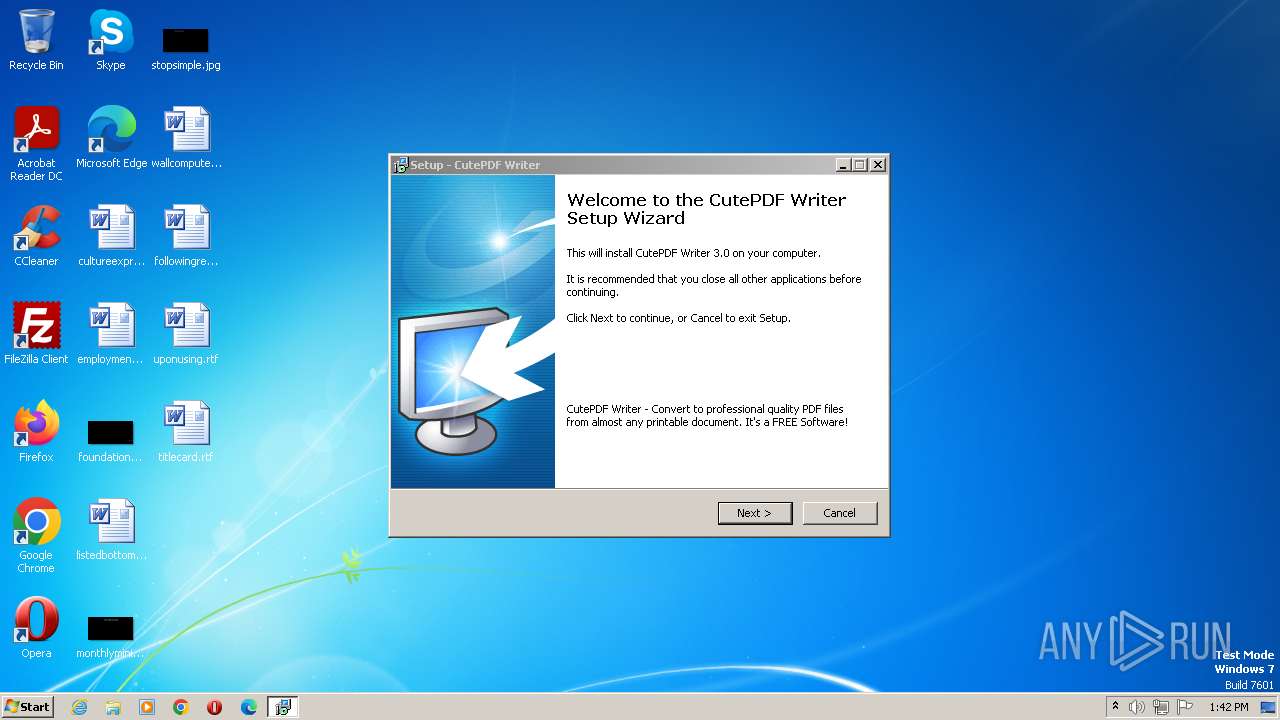
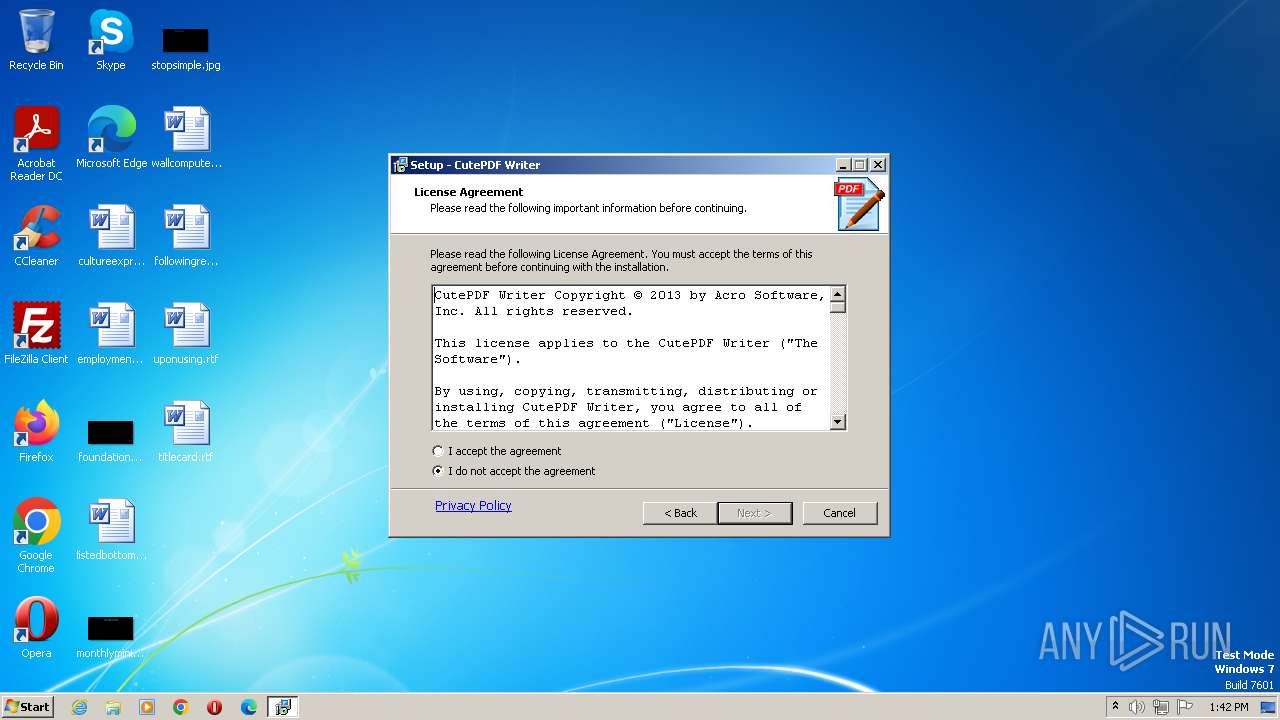
| ProductName: | CutePDF Writer |
| LegalCopyright: | |
| FileVersion: | 3.0.0.7 |
| FileDescription: | CutePDF Writer Setup |
| CompanyName: | Acro Software Inc. |
| Comments: | CutePDF Setup |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.0.0.1 |
| FileVersionNumber: | 3.0.0.7 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 1 |
| EntryPoint: | 0x9c40 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 17920 |
| CodeSize: | 37888 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | CutePDF Setup |
| CompanyName: | Acro Software Inc. |
| FileDescription: | CutePDF Writer Setup |
| FileVersion: | 3.0.0.7 |
| LegalCopyright: | - |
| ProductName: | CutePDF Writer |
| ProductVersion: | 3.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009364 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56223 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.75348 |
BSS | 0x0000C000 | 0x00000E4C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.4618 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
71
Monitored processes
33
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3412 --field-trial-handle=1140,i,11540173719316932009,5203113503514244552,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 616 | "C:\Users\admin\AppData\Local\Temp\is-3R7E0.tmp\CuteWriter.tmp" /SL5="$601CC,1730625,54272,C:\Users\admin\AppData\Local\Temp\CuteWriter.exe" /SPAWNWND=$90154 /NOTIFYWND=$50160 | C:\Users\admin\AppData\Local\Temp\is-3R7E0.tmp\CuteWriter.tmp | CuteWriter.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 832 | "C:\Users\admin\AppData\Local\Temp\is-R76JP.tmp\CuteWriter.tmp" /SL5="$50160,1730625,54272,C:\Users\admin\AppData\Local\Temp\CuteWriter.exe" | C:\Users\admin\AppData\Local\Temp\is-R76JP.tmp\CuteWriter.tmp | — | CuteWriter.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 952 | "C:\Users\admin\AppData\Local\Temp\is-27NLK.tmp\Setup.exe" /cpw07012009 /W5 | C:\Users\admin\AppData\Local\Temp\is-27NLK.tmp\Setup.exe | CuteWriter.tmp | ||||||||||||
User: admin Company: Acro Software Inc. Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 3, 0, 0, 5 Modules
| |||||||||||||||
| 1228 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2400 --field-trial-handle=1220,i,10566622858045775956,14422957436742143631,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6b768b38,0x6b768b48,0x6b768b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1472 --field-trial-handle=1264,i,3870547841798202906,5567224005473258959,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1356 --field-trial-handle=1140,i,11540173719316932009,5203113503514244552,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1848 | "C:\Users\admin\AppData\Local\Temp\CuteWriter.exe" /SPAWNWND=$90154 /NOTIFYWND=$50160 | C:\Users\admin\AppData\Local\Temp\CuteWriter.exe | CuteWriter.tmp | ||||||||||||
User: admin Company: Acro Software Inc. Integrity Level: HIGH Description: CutePDF Writer Setup Exit code: 0 Version: 3.0.0.7 Modules
| |||||||||||||||
Total events
6 385
Read events
5 845
Write events
537
Delete events
3
Modification events
| (PID) Process: | (2564) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2564) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2564) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2564) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2564) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2564) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000004F010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2564) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2564) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2720) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2720) Offercast2801_ARS_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
35
Suspicious files
39
Text files
108
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1848 | CuteWriter.exe | C:\Users\admin\AppData\Local\Temp\is-3R7E0.tmp\CuteWriter.tmp | executable | |
MD5:67C5A4F36E1C91A3B85E440EDD7AD026 | SHA256:99C299D6565AB53D9AF66E0146737DC0ECFBC52ECF4740825B552DB0CC4210C6 | |||
| 616 | CuteWriter.tmp | C:\Users\admin\AppData\Local\Temp\is-27NLK.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 616 | CuteWriter.tmp | C:\Users\admin\AppData\Local\Temp\is-27NLK.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 1872 | CuteWriter.exe | C:\Users\admin\AppData\Local\Temp\is-R76JP.tmp\CuteWriter.tmp | executable | |
MD5:67C5A4F36E1C91A3B85E440EDD7AD026 | SHA256:99C299D6565AB53D9AF66E0146737DC0ECFBC52ECF4740825B552DB0CC4210C6 | |||
| 616 | CuteWriter.tmp | C:\Users\admin\AppData\Local\Temp\is-27NLK.tmp\Offercast2801_ARS_.exe | executable | |
MD5:3EB7286BF1D179D2DEB77F342656CCF2 | SHA256:9AC9365008D86C530C88CE79750A1E104C085DEA1E382808565EAB07F46AAA9A | |||
| 2720 | Offercast2801_ARS_.exe | C:\Users\admin\AppData\Local\Temp\apn_pip_local\orchestrator.html | html | |
MD5:FDD740A29F5849B4082B4267C045E33E | SHA256:1C784689CBE6F5597D72E6A672FBD5D7D536E288E2B6FC3C0F55D67D2FD86752 | |||
| 2564 | Offercast2801_ARS_.exe | C:\Users\admin\AppData\Local\Temp\APNAnalytics.xml | xml | |
MD5:69B7C2EC83F0F95C81DC6E35AA2F6DE5 | SHA256:14269F2558D9AF0259153DFC77F43831F1A4D3F15DCB628E3E7A48CC3054C755 | |||
| 2720 | Offercast2801_ARS_.exe | C:\Users\admin\AppData\Local\Temp\apn_pip_local\v7tb.png | image | |
MD5:7B7CEF8722BCDC36492B14AF5C579702 | SHA256:DA80D5CFB7AE2612CD0D39B34C9BE2A2E2706C0C75378E5F9A872A10EF7A4DCD | |||
| 616 | CuteWriter.tmp | C:\Users\admin\AppData\Local\Temp\is-27NLK.tmp\is-6AF13.tmp | executable | |
MD5:2E31A21B082C644F0C50E44D6F2D5F86 | SHA256:9EEC4B7C6644AD432316D54403553C44CB07C8BB8C4D9C2BBE2A3C8C3B75E89E | |||
| 616 | CuteWriter.tmp | C:\Users\admin\AppData\Local\Temp\is-27NLK.tmp\is-S3BK8.tmp | executable | |
MD5:2C046C365F5A17FE3519B4ED8AF4960E | SHA256:7D2FB3C658E5F718215B3708F94E5BAD89ED08E2158CC8EEBE17E5D69667E4BC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
19
DNS requests
25
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2564 | Offercast2801_ARS_.exe | GET | 200 | 104.102.49.22:80 | http://ak.pipoffers.apnpartners.com/static/partners/ARS/APNAnalytics.xml | DE | xml | 1022 b | unknown |
2564 | Offercast2801_ARS_.exe | GET | 302 | 34.120.59.42:80 | http://pipoffers.apnpartners.com/PIP/Server.jhtml?partner_id=ARS&language=en&version=2.8.0.1 | US | html | 209 b | unknown |
2564 | Offercast2801_ARS_.exe | POST | 400 | 34.120.59.42:80 | http://pipoffers.apnpartners.com/PIP/OfferAccept.jhtml | US | html | 54 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | Offercast2801_ARS_.exe | 104.102.49.22:80 | ak.pipoffers.apnpartners.com | AKAMAI-AS | DE | unknown |
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2564 | Offercast2801_ARS_.exe | 34.120.59.42:80 | pipoffers.apnpartners.com | GOOGLE-CLOUD-PLATFORM | US | malicious |
2564 | Offercast2801_ARS_.exe | 34.117.28.143:80 | errdocs.zwinky.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
952 | Setup.exe | 64.34.201.145:80 | download.cutepdf.com | COGECO-PEER1 | US | unknown |
4076 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2816 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2816 | chrome.exe | 142.250.185.173:443 | accounts.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
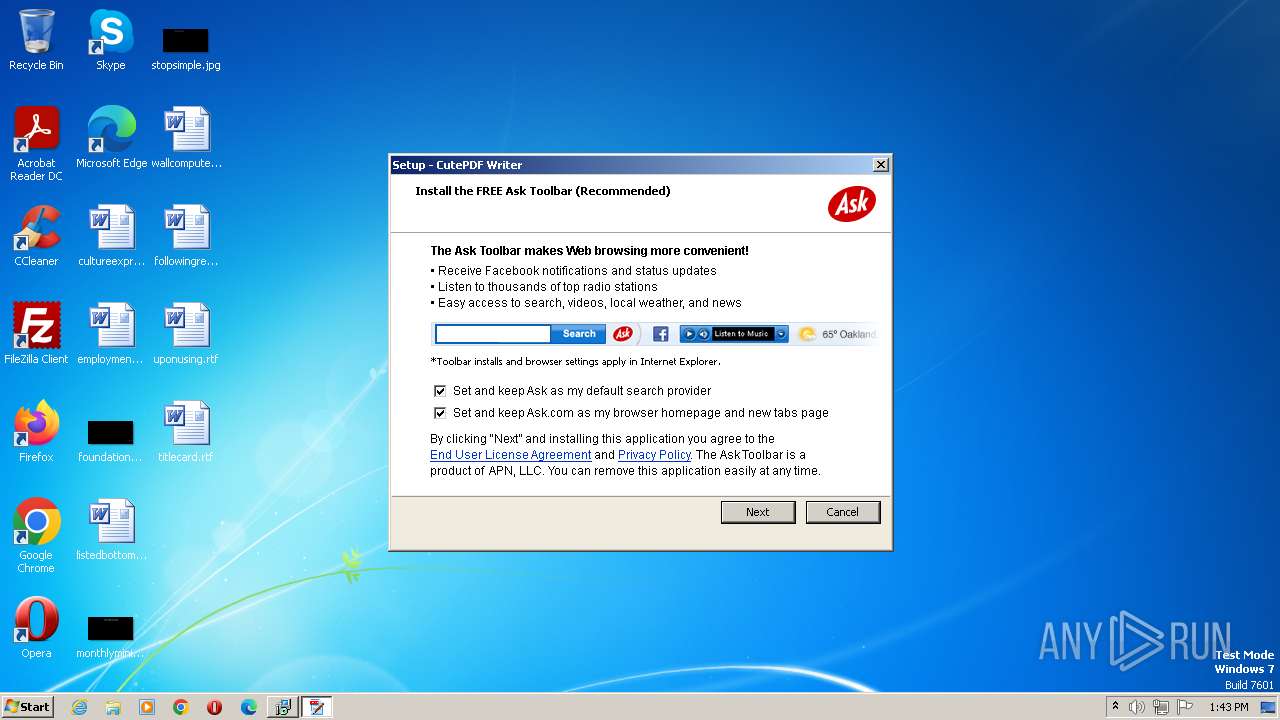
pipoffers.apnpartners.com |
| malicious |
42.59.120.34.in-addr.arpa |
| unknown |
ak.pipoffers.apnpartners.com |
| whitelisted |
errdocs.zwinky.com |
| unknown |
apnmedia.ask.com |
| unknown |
download.cutepdf.com |
| whitelisted |
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
Offercast2801_ARS_.exe | CreateSO called |
Offercast2801_ARS_.exe |
****** pirule setRule callBackFired : function called is Rule name: InstallCheckNumber: 2 |
Offercast2801_ARS_.exe | --- Enter InstallCheck with param of : "P_ARS" |
Offercast2801_ARS_.exe | CheckVersion :<ie> |
Offercast2801_ARS_.exe | Installed Toolbars : []
|
Offercast2801_ARS_.exe |
CanBeInstalled :<cr>
|
Offercast2801_ARS_.exe | Installed Toolbars : []
|
Offercast2801_ARS_.exe |
CanBeInstalled :<>
|
Offercast2801_ARS_.exe | Installed Toolbars : []
|
Offercast2801_ARS_.exe | Actual Param P_ARS *******Returned offers {"GeneralParameters":{"Height":"399","Width":"506","bgcolor":"efebdf","dlg_transparency":"255","defaultLanguage":"en","ShowOfferScreensOnly":"false","MessageUser":"false","BalloonIconPath":"http://ak.pipoffers.apnpartners.com/static/partners/{partnerid}/images/install.ico","TrayTipTime":"2000","PreviousX":"250","PreviousY":"50","NextX":"176","NextY":"50","CancelX":"91","CancelY":"50","CancelDeclinesOffer":"true","RetryTimeout":"300","NumberOfSecOffersToShow":"0","Orchestrator":"./orchestrator.html?PIPPID=ARS&PTBPartnerID=ARS3&tbType=vanilla&version={version}","CBID":"AIB","HidePrevious":"false","optintextsize":"12","ProgressBarCancelClickable":"true","ShowLoadingScreen":"false","showprogcanceldlg":"false","ShowProgressDlg":"false","SetDateTime":"2003/02/04 08:30:00"},"offers":[{"ToolbarID":"ARS3","bkgImage":"http://ak.pipoffers.apnpartners.com/static/partners/ARS/images/v7tb.png","cancelchoose":"true","displayname":"Ask Toolbar","id":"P_ARS","imageheight":"320","imagewidth":"500","offerProvider":"APNV6","offerType":"Toolbar","optout":"true","rules":"InstallCheck","tbType":"vanilla","title":"Setup - CutePDF Writer","transparency":"255"}]}
|