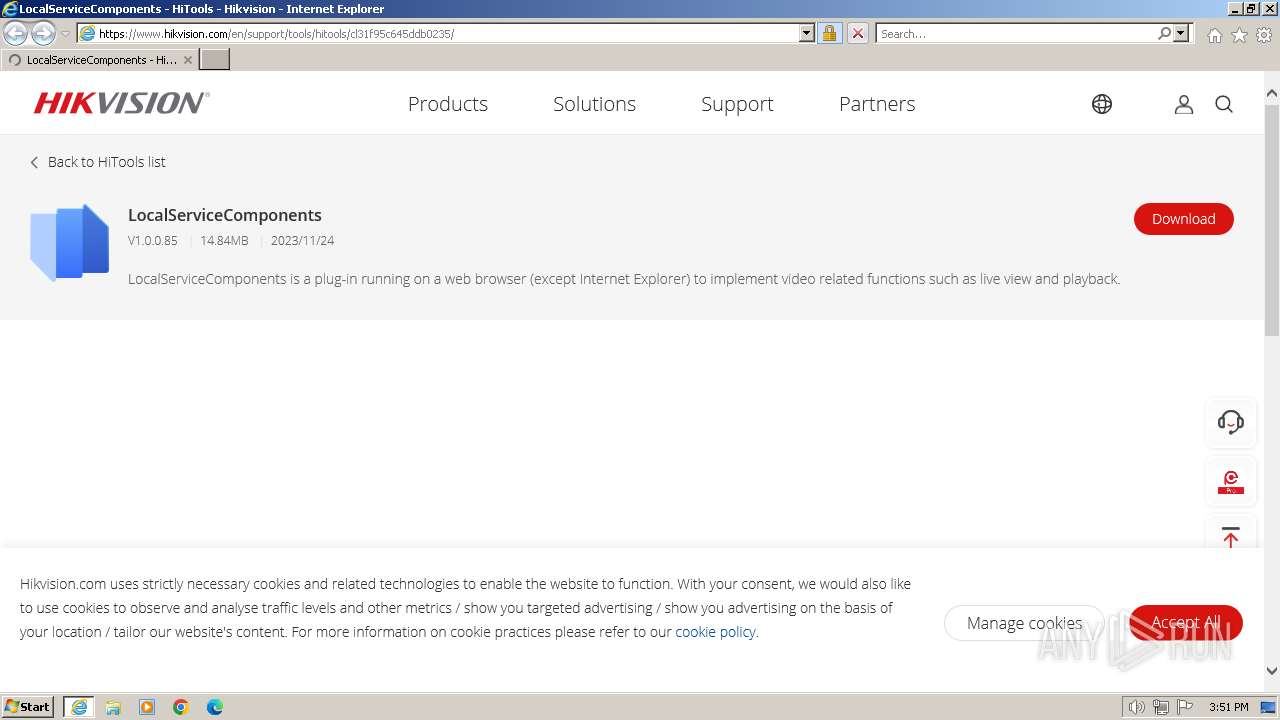
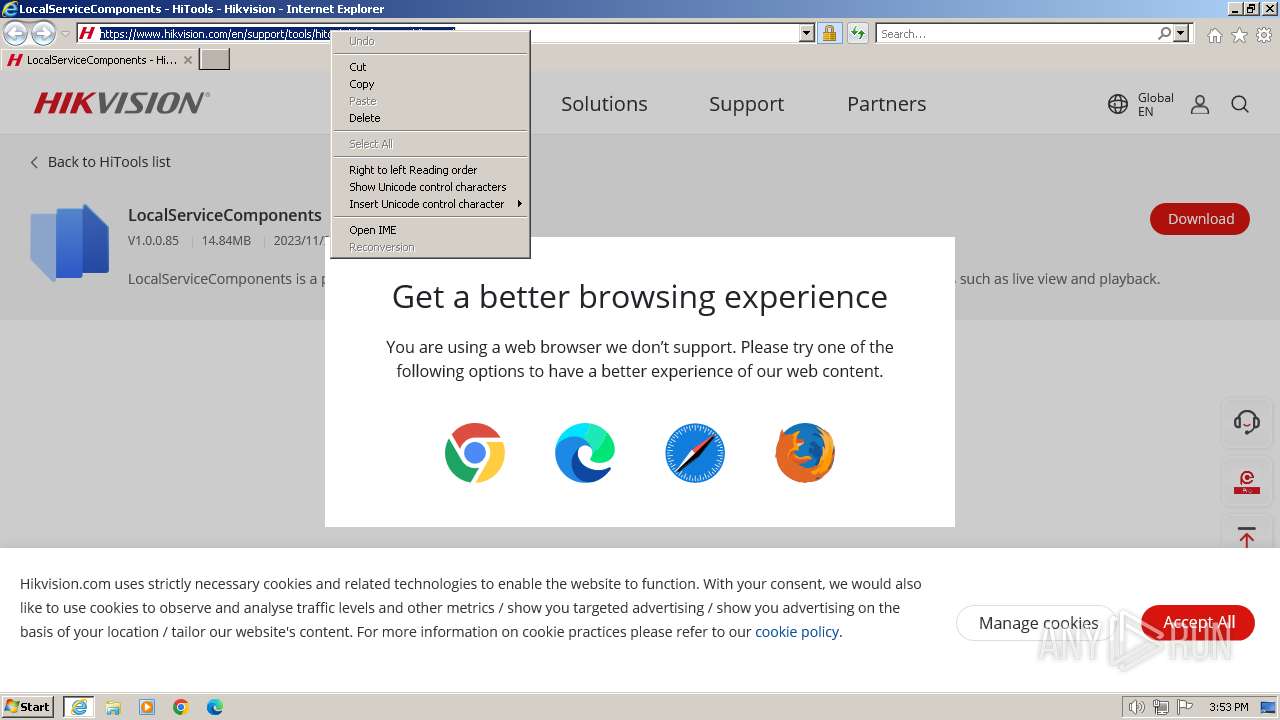
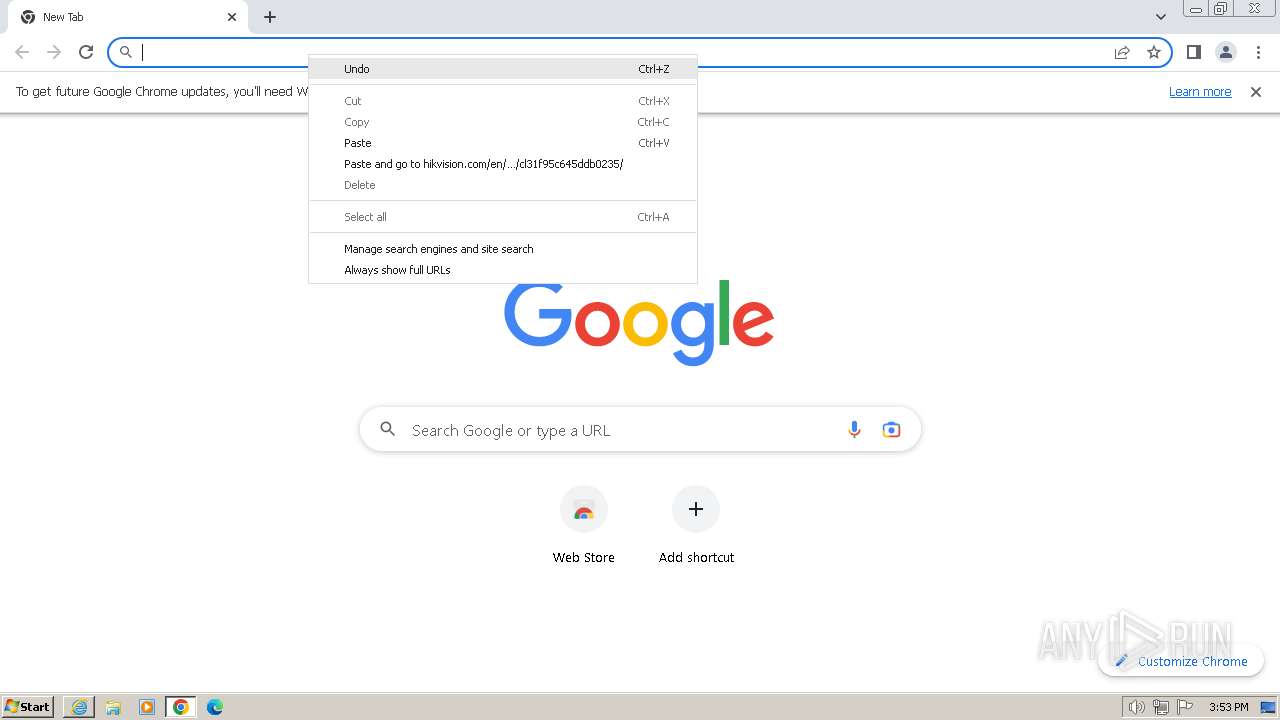
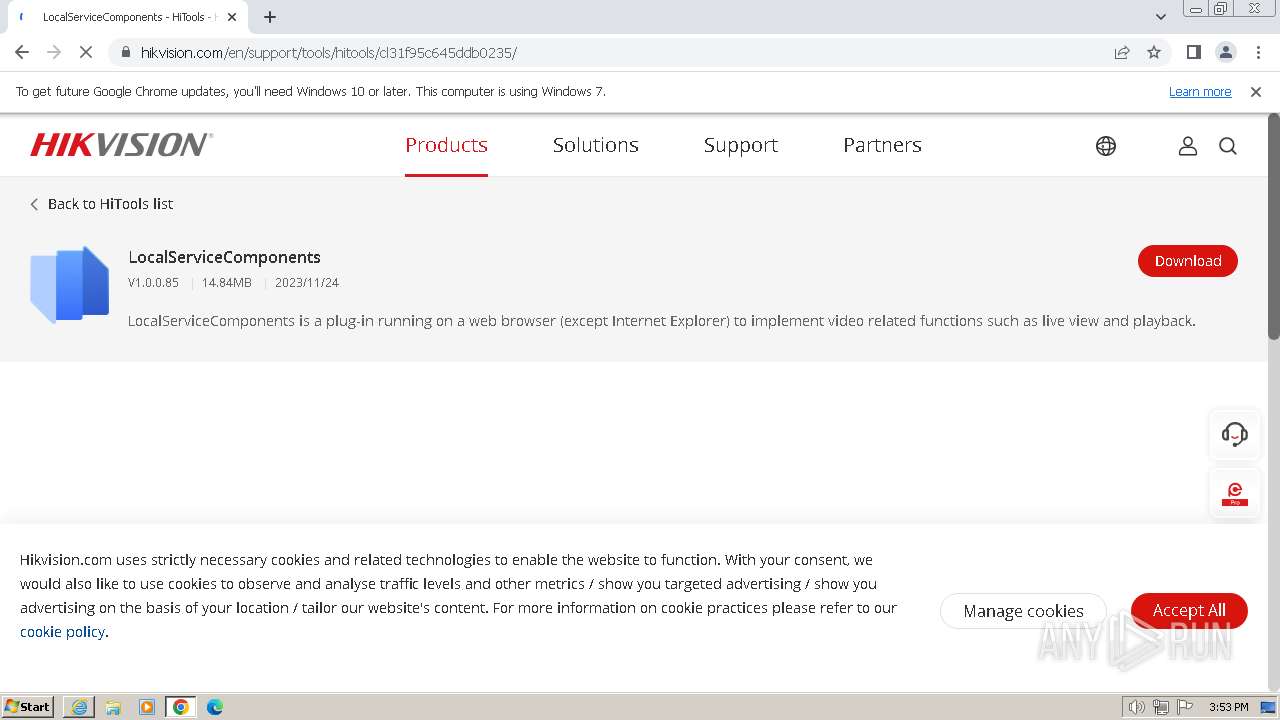
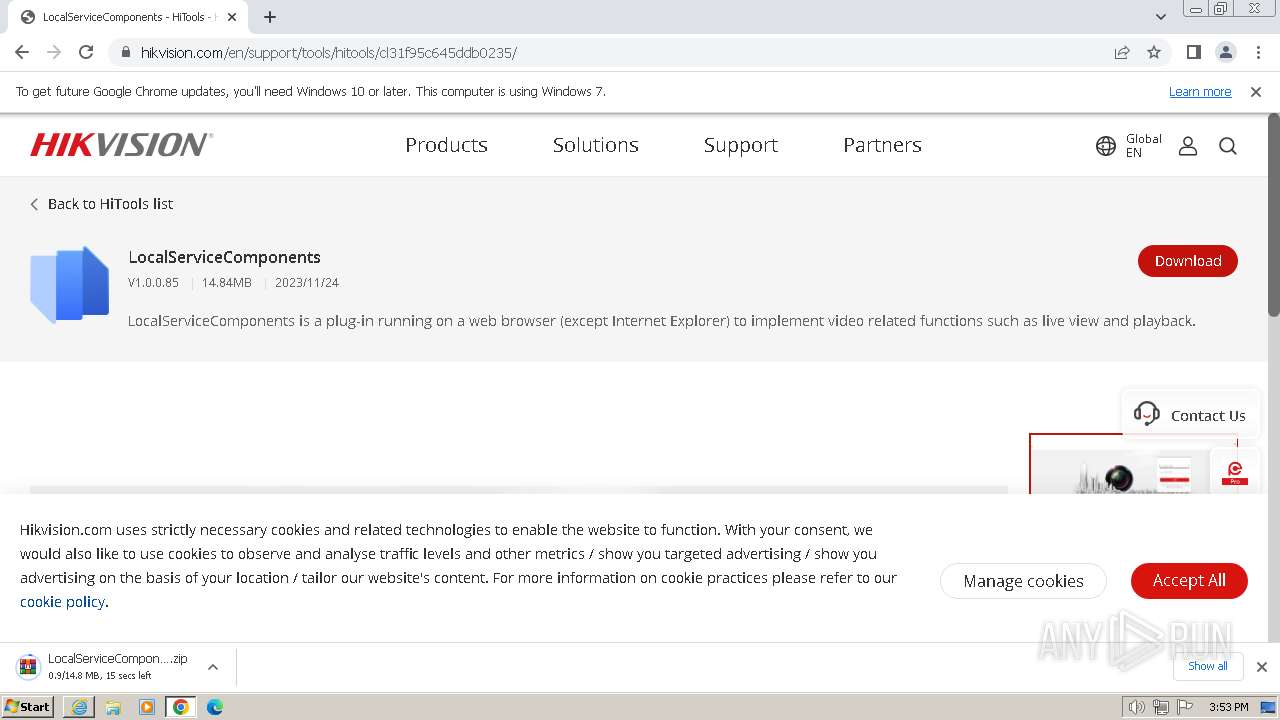
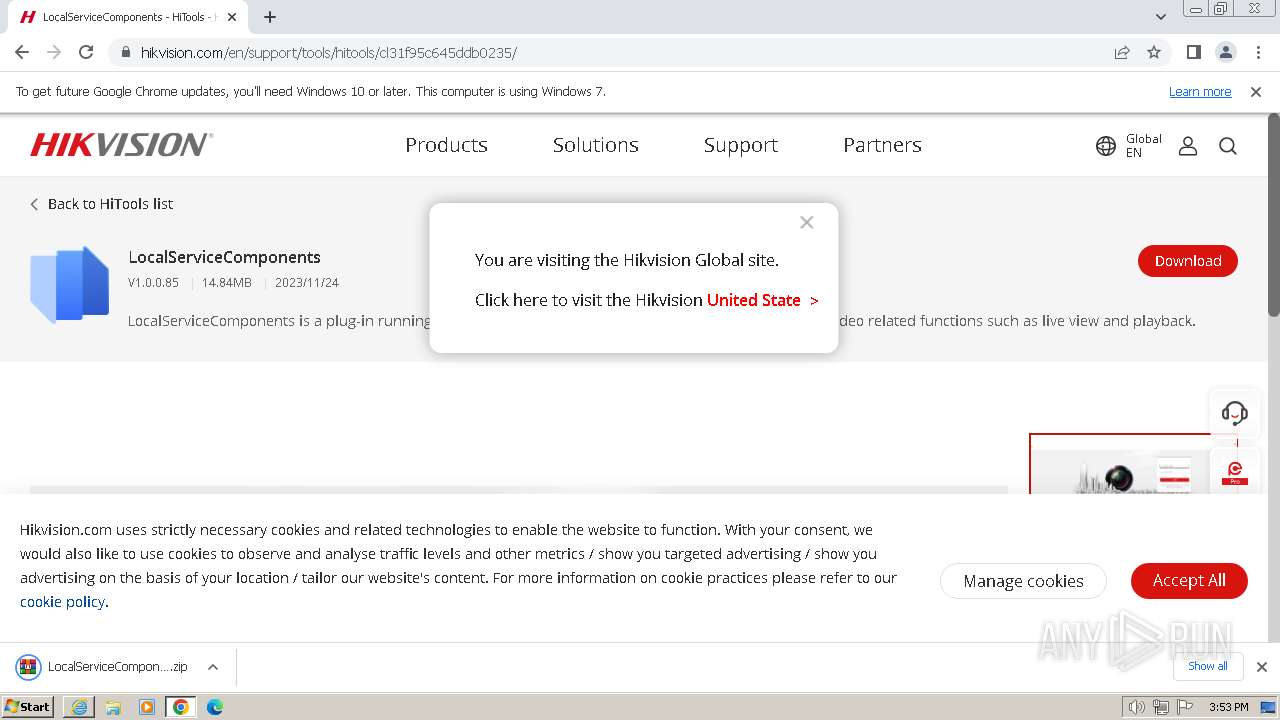
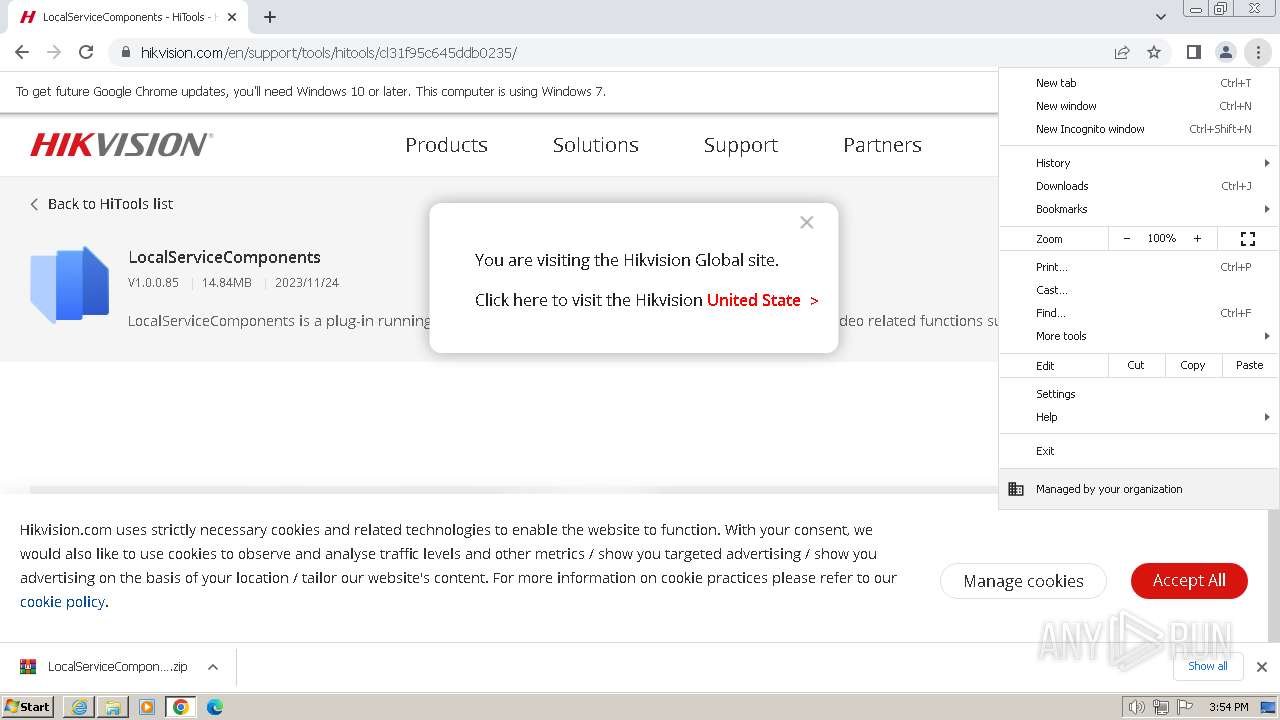
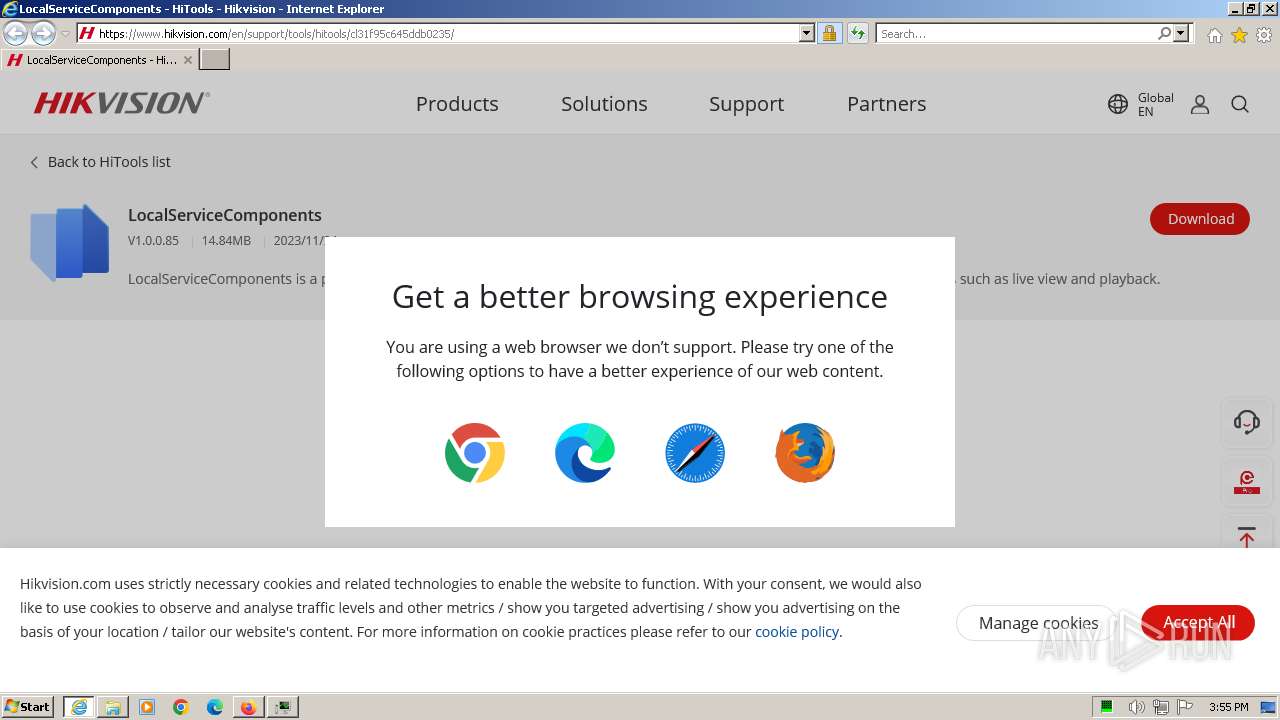
| URL: | https://www.hikvision.com/en/support/tools/hitools/cl31f95c645ddb0235/ |
| Full analysis: | https://app.any.run/tasks/2ffc0353-b097-4ecc-9a44-d36579e6d8ef |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2024, 14:51:31 |
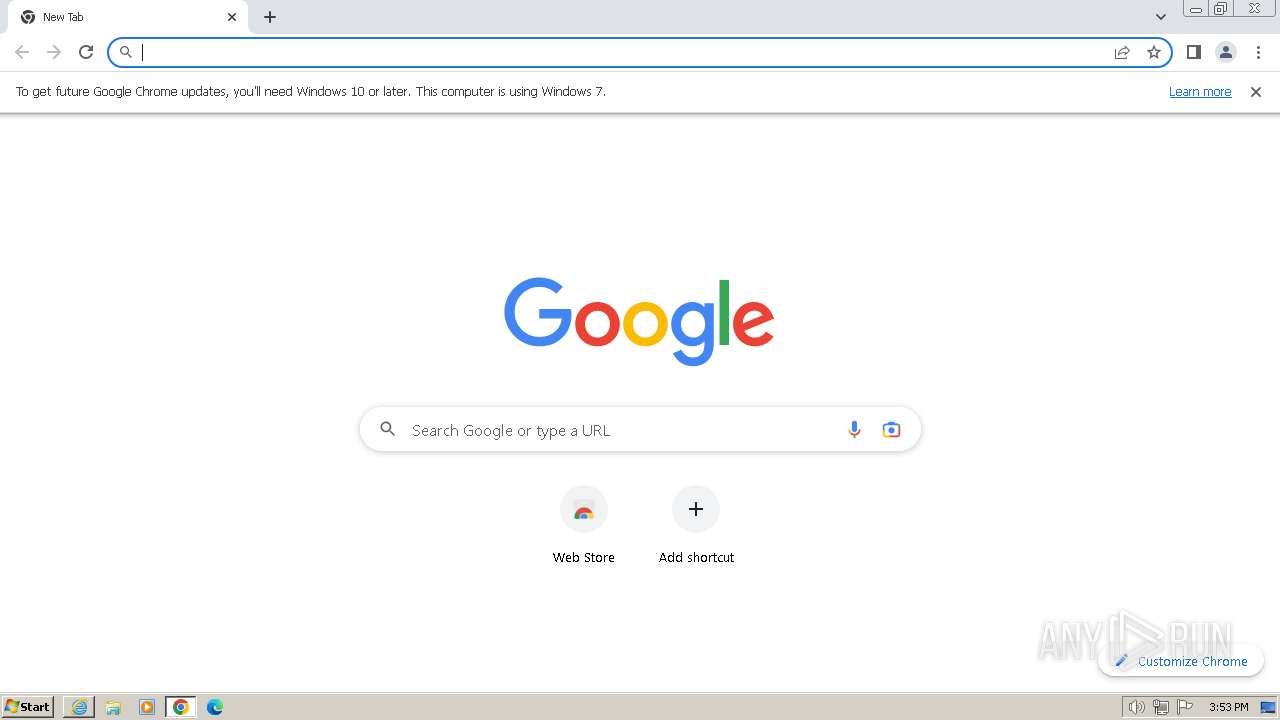
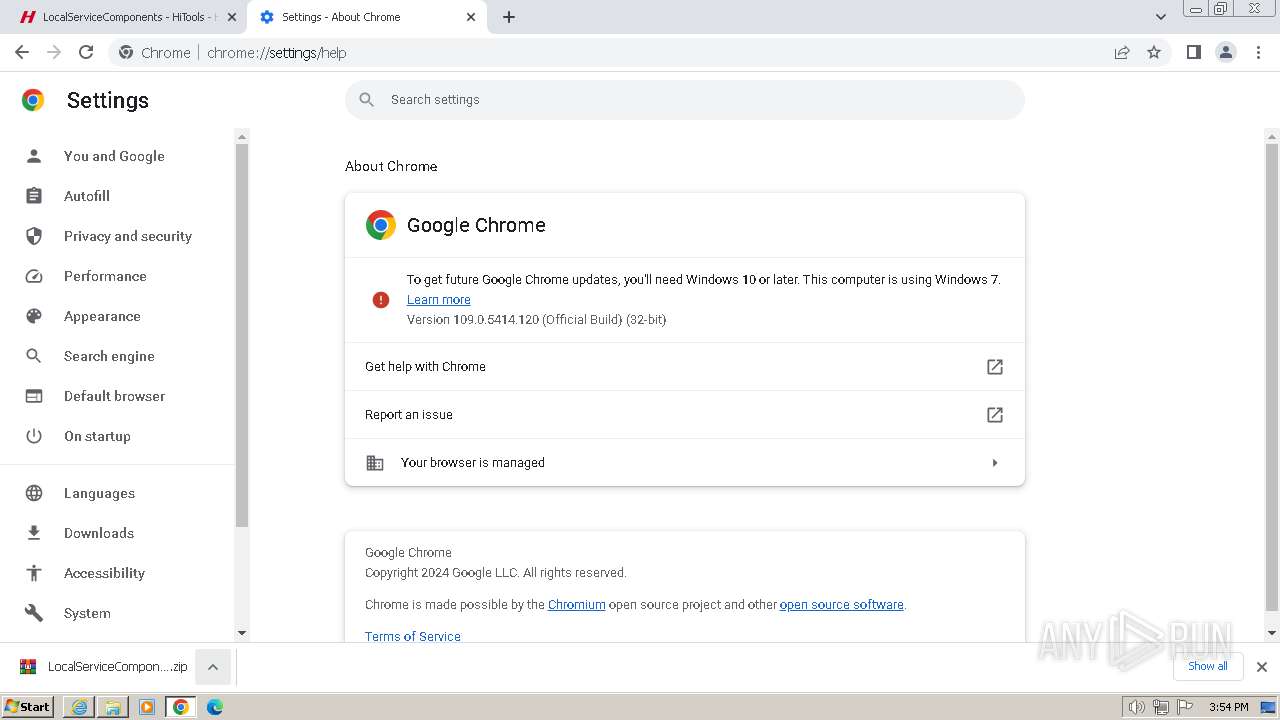
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7123C258EFF58B60C569ECF454A95766 |
| SHA1: | 7040C346520BC7A23A84F1F5000921AFB972D455 |
| SHA256: | C251ED825E45778211C6677C7E978F00894AD2B7F62B8EC6BE579FCDB7BC001F |
| SSDEEP: | 3:N8DSL1MVTb+WQIKsSksSNeWXTS3Vqn:2OLITb+XIokdNekTS3k |
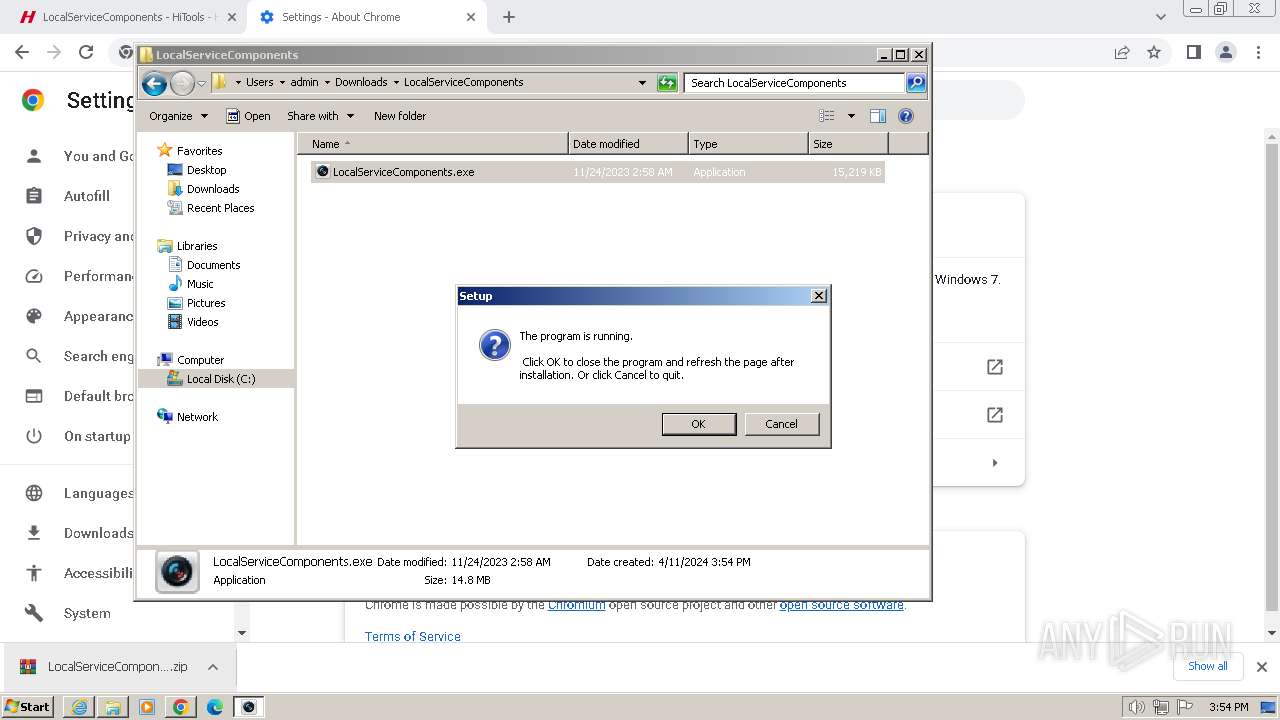
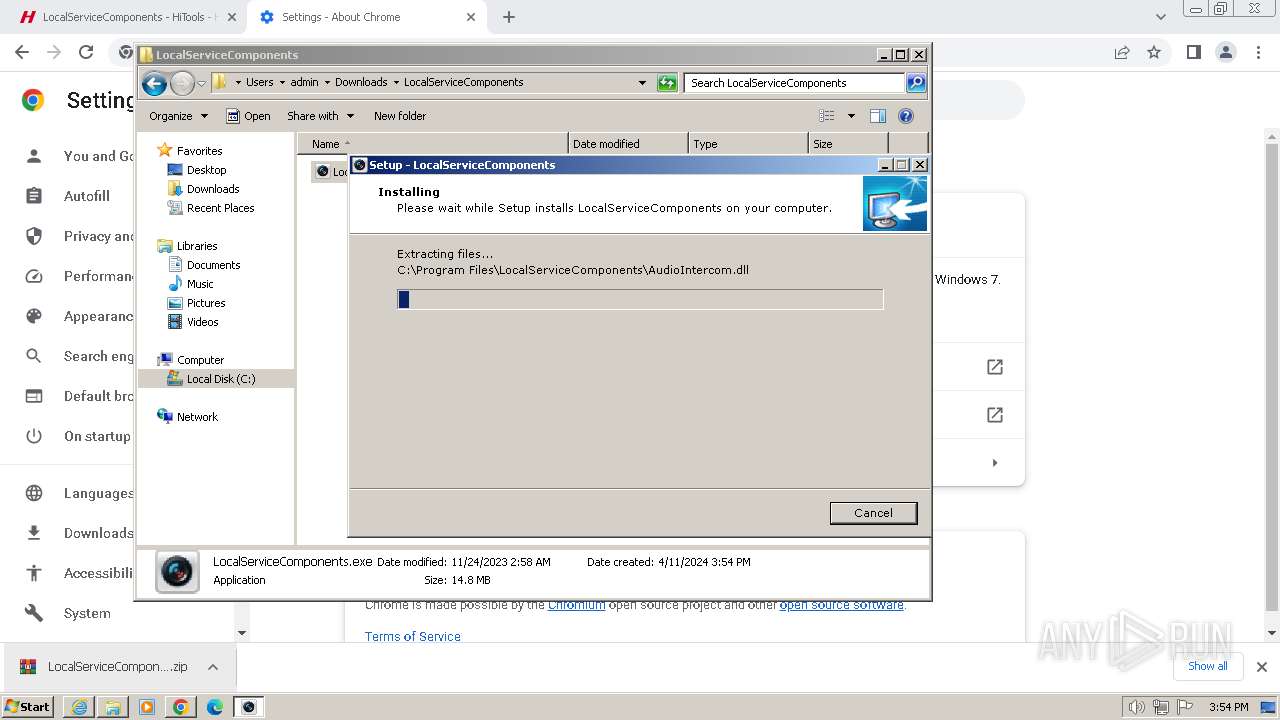
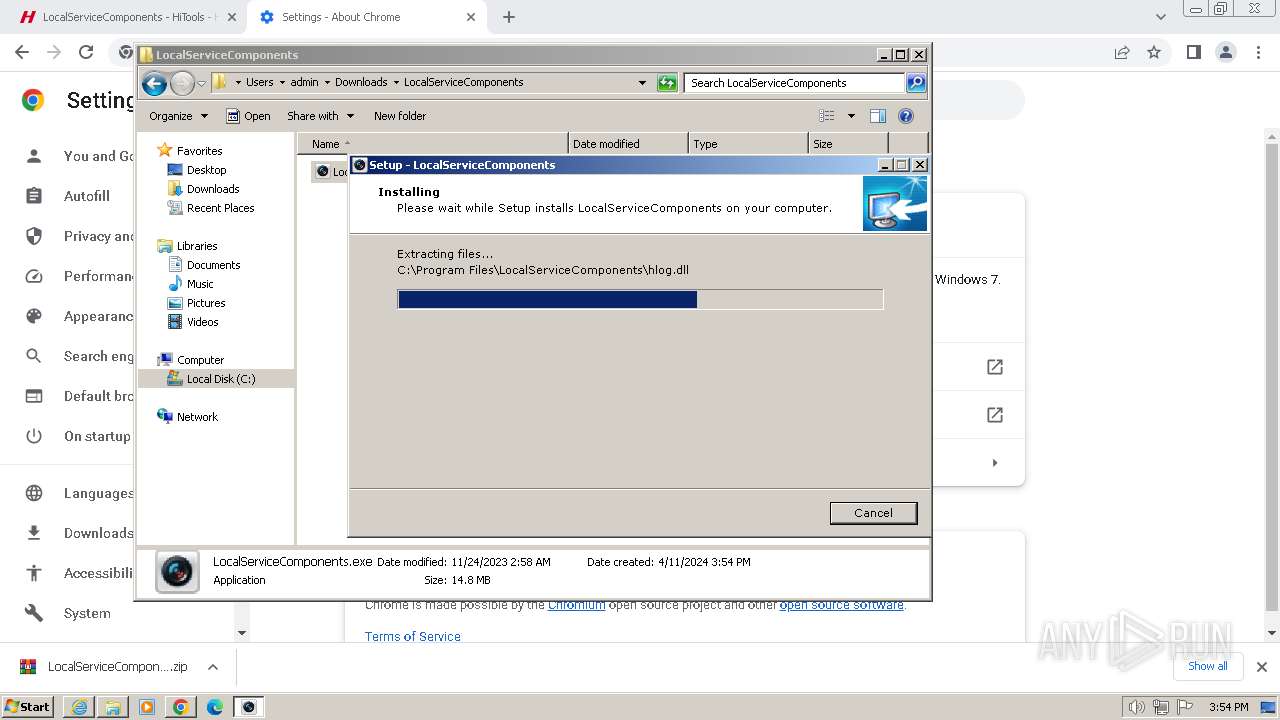
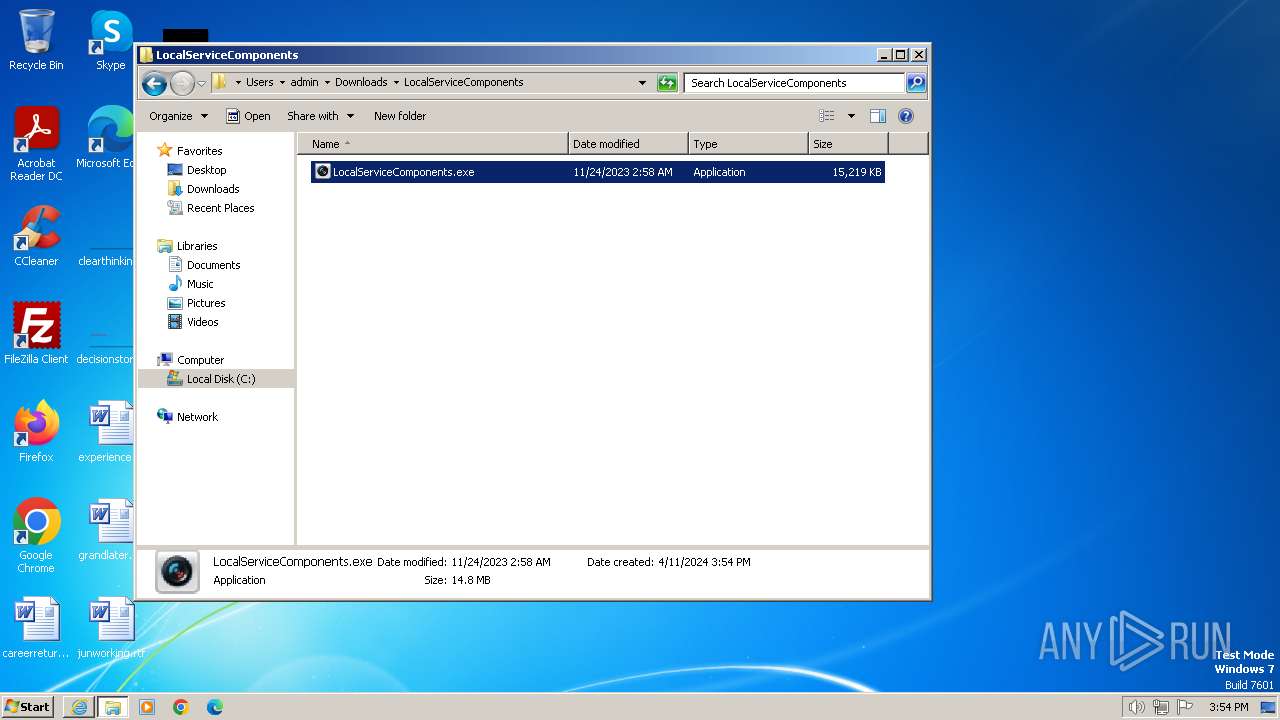
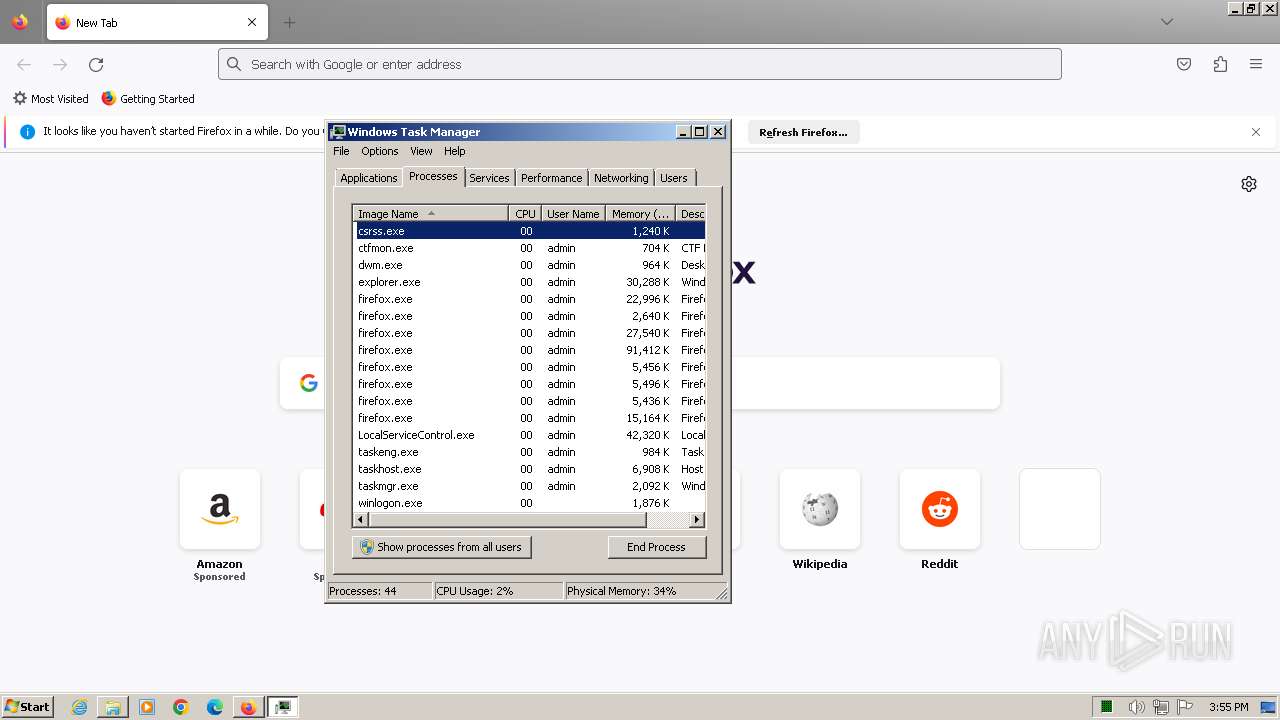
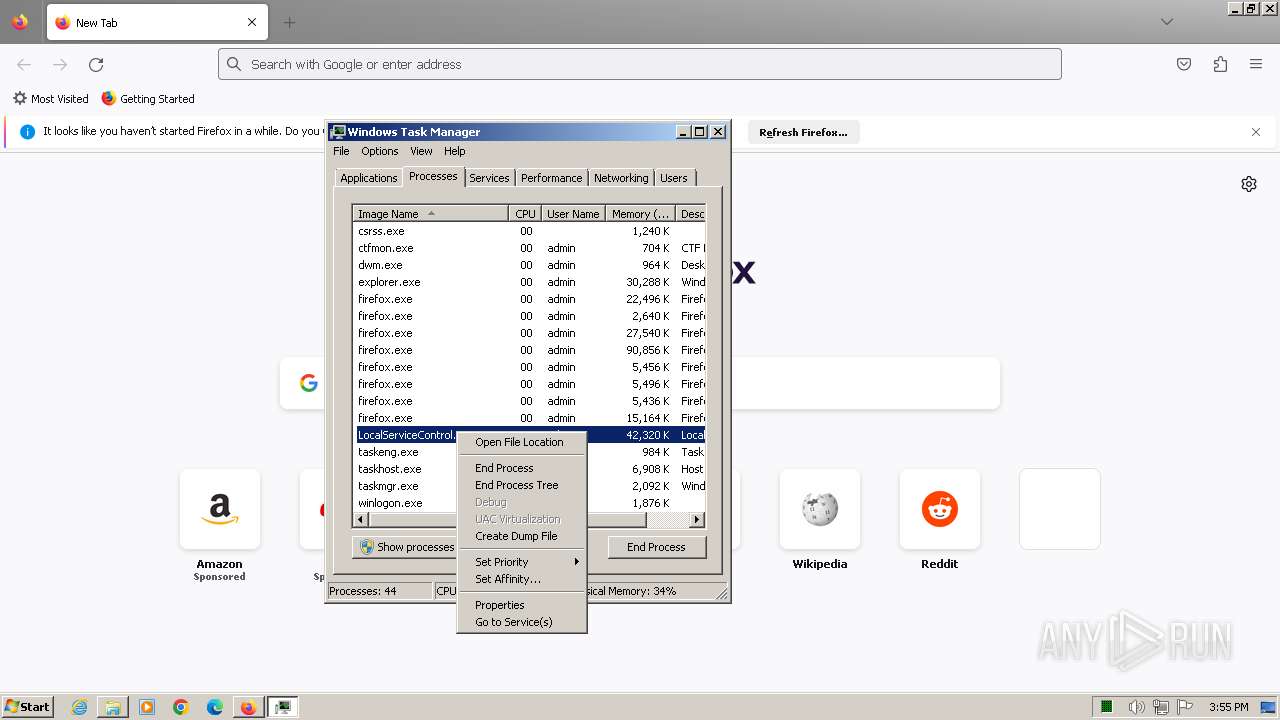
MALICIOUS
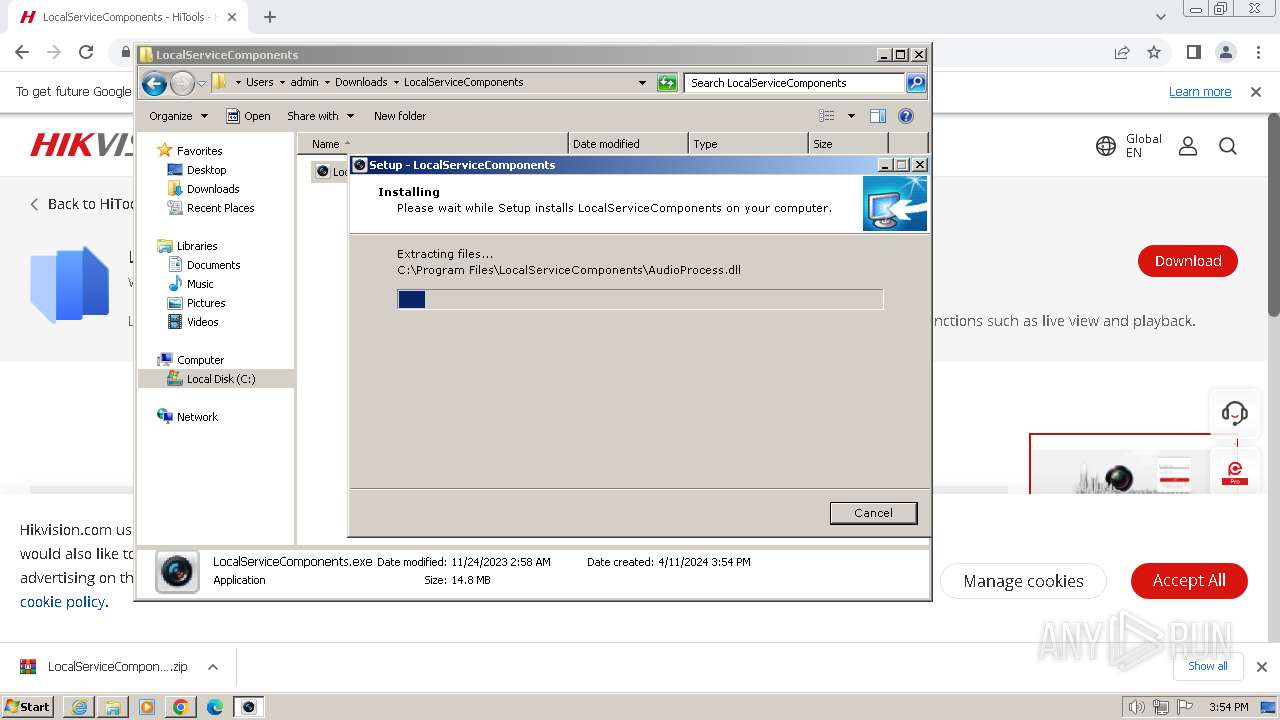
Drops the executable file immediately after the start
- LocalServiceComponents.exe (PID: 3228)
- LocalServiceComponents.exe (PID: 2440)
- LocalServiceComponents.exe (PID: 3296)
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceComponents.tmp (PID: 292)
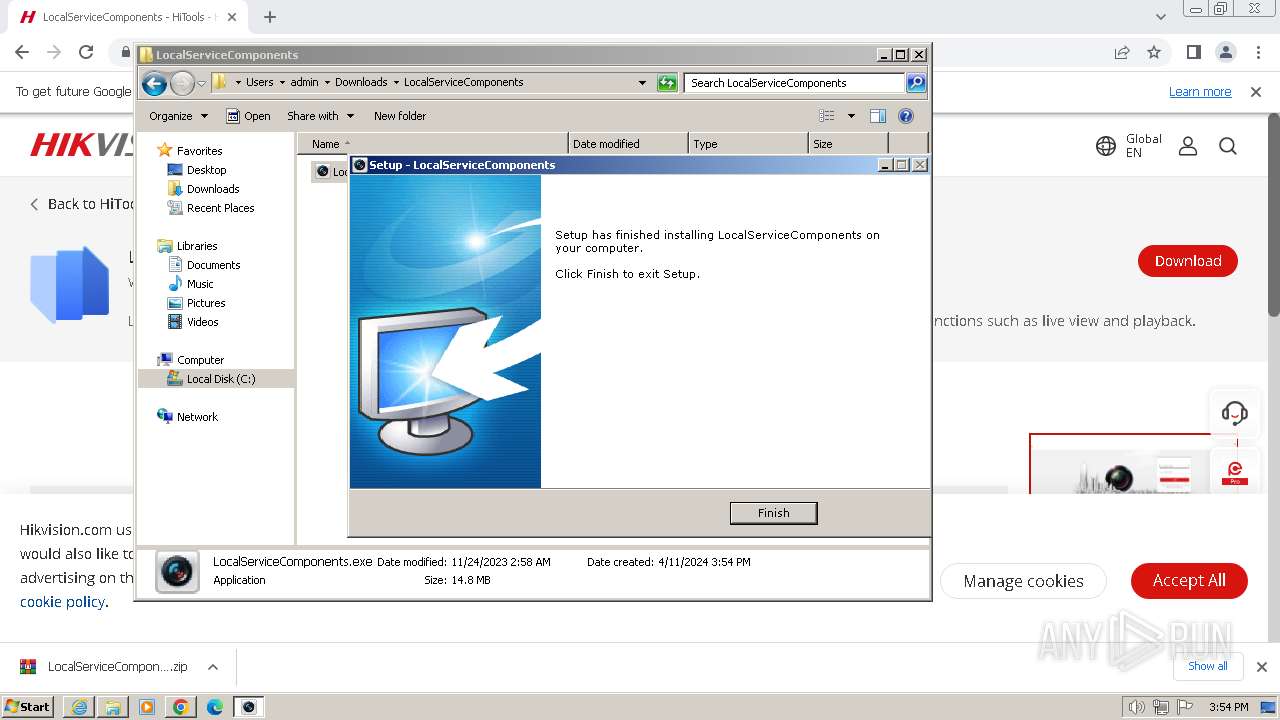
Changes the autorun value in the registry
- LocalServiceComponents.tmp (PID: 3952)
SUSPICIOUS
Executable content was dropped or overwritten
- LocalServiceComponents.exe (PID: 3228)
- LocalServiceComponents.exe (PID: 2440)
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceComponents.exe (PID: 3296)
- LocalServiceComponents.tmp (PID: 292)
Process drops legitimate windows executable
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceComponents.tmp (PID: 292)
Reads the Windows owner or organization settings
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceComponents.tmp (PID: 292)
The process drops C-runtime libraries
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceComponents.tmp (PID: 292)
Creates file in the systems drive root
- LocalServiceControl.exe (PID: 3924)
- LocalServiceControl.exe (PID: 2360)
- LocalServiceControl.exe (PID: 1596)
- LocalServiceControl.exe (PID: 2244)
Reads the Internet Settings
- GoogleUpdate.exe (PID: 3832)
- LocalServiceControl.exe (PID: 2244)
Reads settings of System Certificates
- GoogleUpdate.exe (PID: 3832)
Searches for installed software
- LocalServiceComponents.tmp (PID: 292)
Application launched itself
- LocalServiceControl.exe (PID: 2244)
Reads security settings of Internet Explorer
- LocalServiceControl.exe (PID: 2244)
INFO
Drops the executable file immediately after the start
- chrome.exe (PID: 2524)
- chrome.exe (PID: 448)
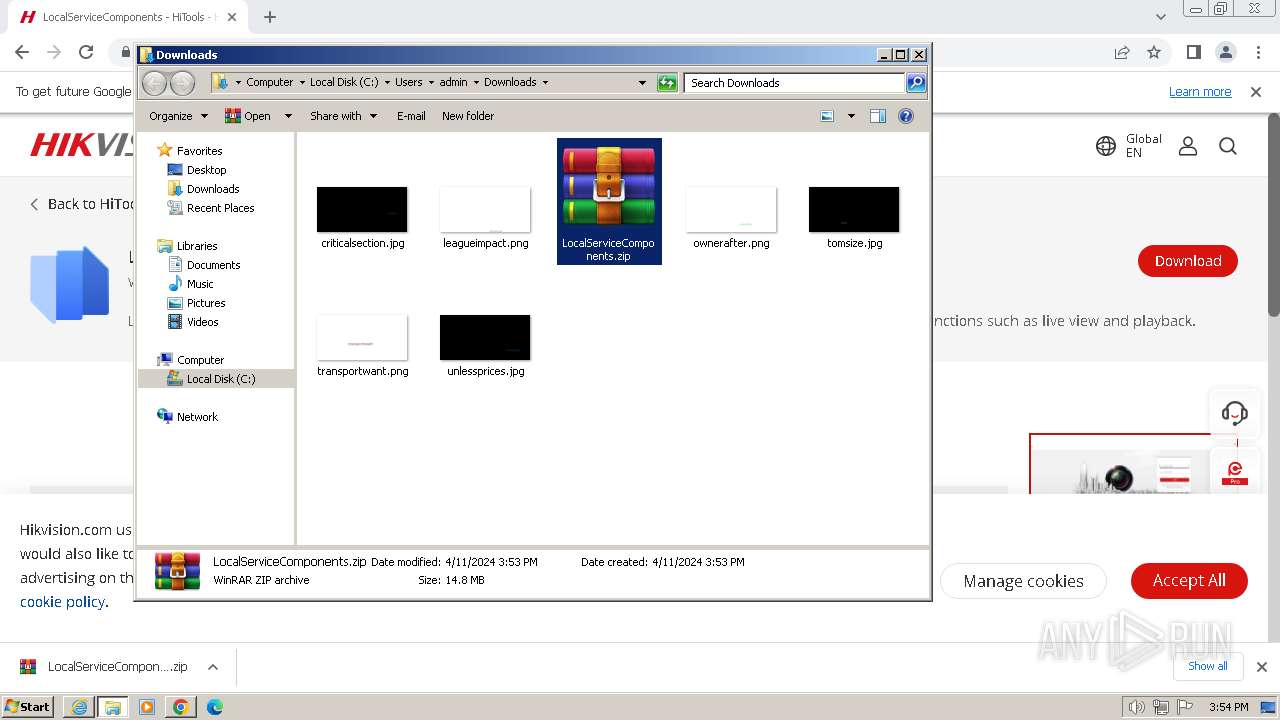
- WinRAR.exe (PID: 1900)
- chrome.exe (PID: 1864)
- firefox.exe (PID: 2560)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1900)
- chrome.exe (PID: 2524)
- firefox.exe (PID: 2560)
Checks supported languages
- LocalServiceComponents.exe (PID: 3228)
- LocalServiceComponents.tmp (PID: 3384)
- LocalServiceComponents.exe (PID: 2440)
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceControl.exe (PID: 3924)
- GoogleUpdateOnDemand.exe (PID: 3568)
- GoogleUpdate.exe (PID: 3832)
- LocalServiceComponents.exe (PID: 3296)
- LocalServiceComponents.tmp (PID: 292)
- GoogleUpdateBroker.exe (PID: 4080)
- GoogleUpdate.exe (PID: 3128)
- LocalServiceControl.exe (PID: 2360)
- LocalServiceControl.exe (PID: 2244)
- LocalServiceControl.exe (PID: 1596)
Create files in a temporary directory
- LocalServiceComponents.exe (PID: 3228)
- LocalServiceComponents.exe (PID: 2440)
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceComponents.exe (PID: 3296)
- LocalServiceComponents.tmp (PID: 292)
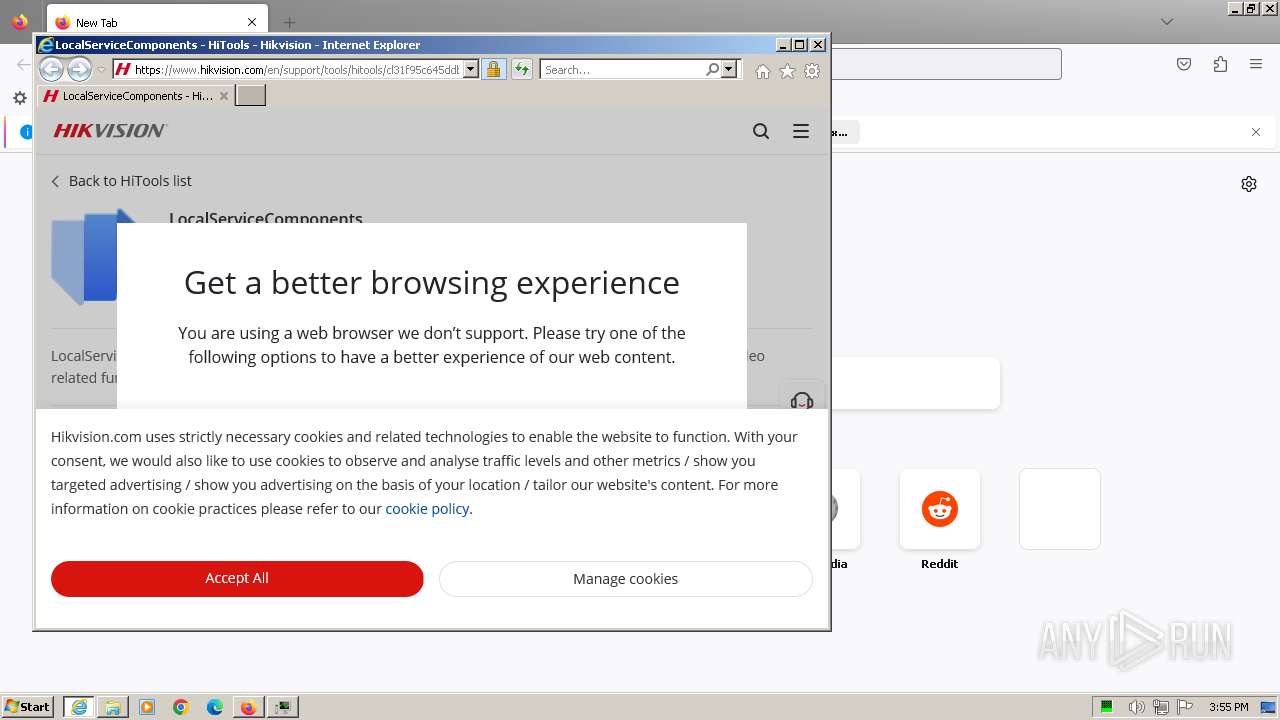
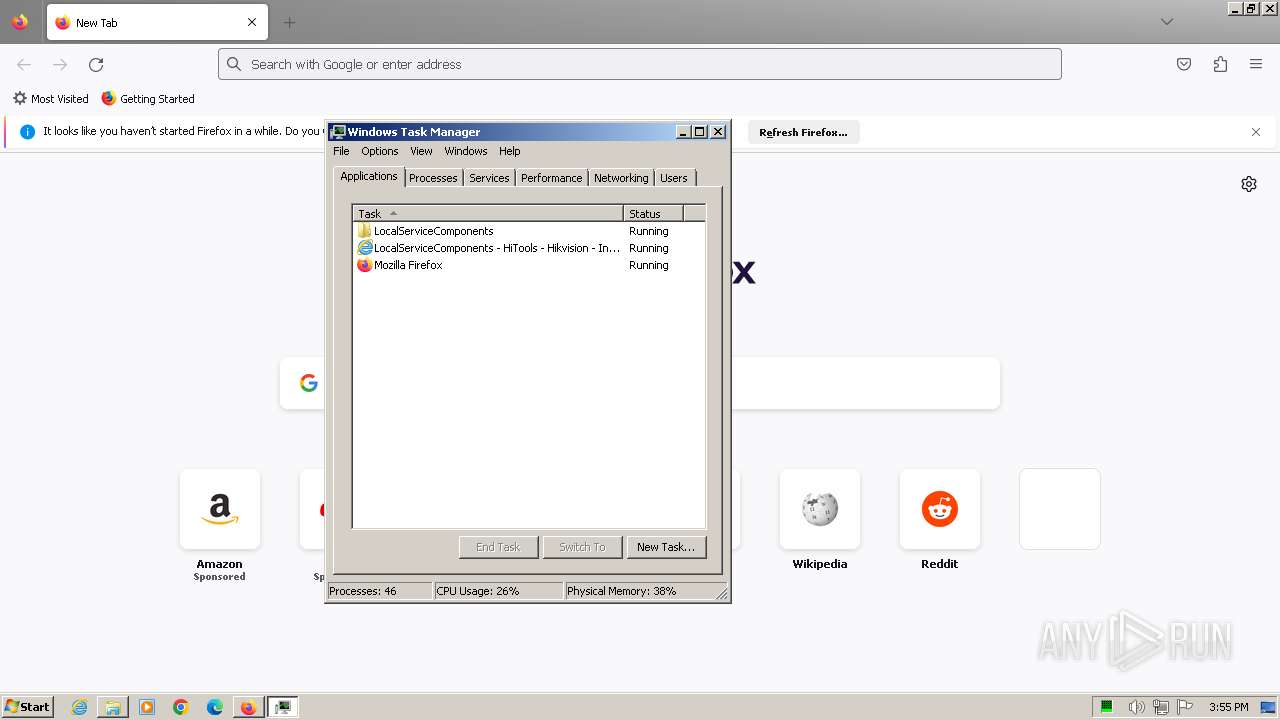
Application launched itself
- chrome.exe (PID: 1864)
- iexplore.exe (PID: 3956)
- firefox.exe (PID: 1092)
- firefox.exe (PID: 2560)
- msedge.exe (PID: 3780)
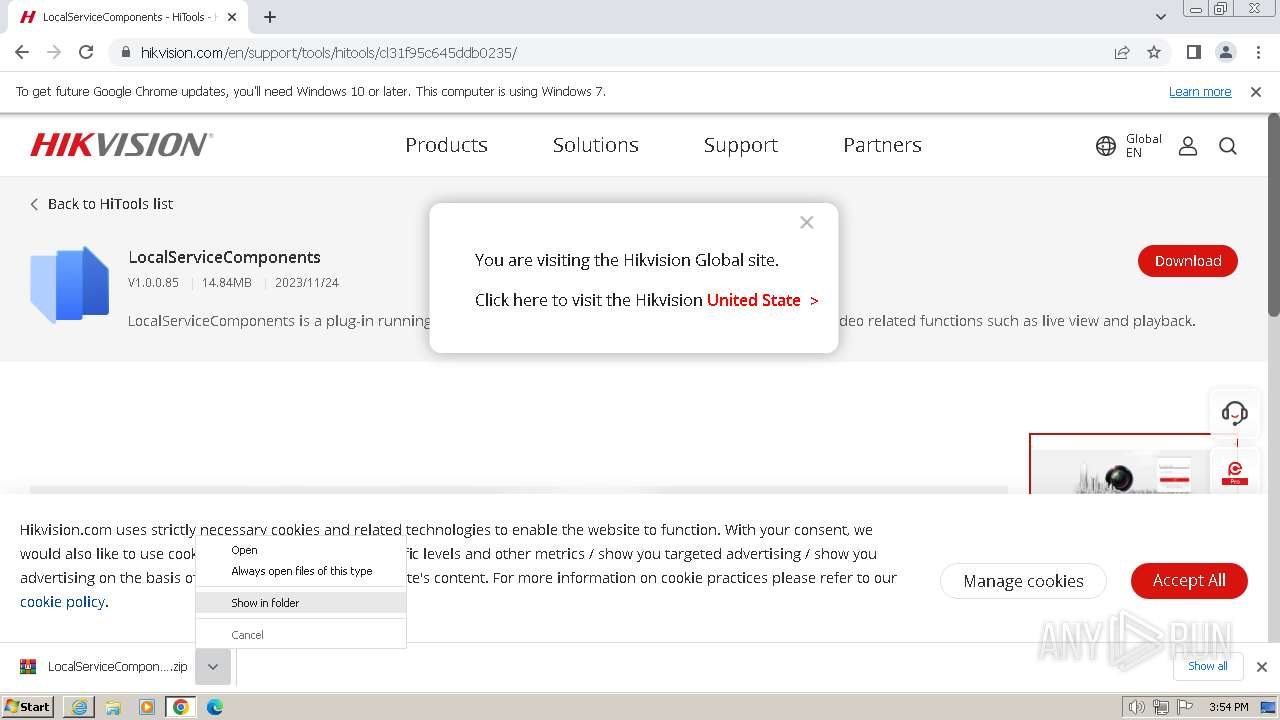
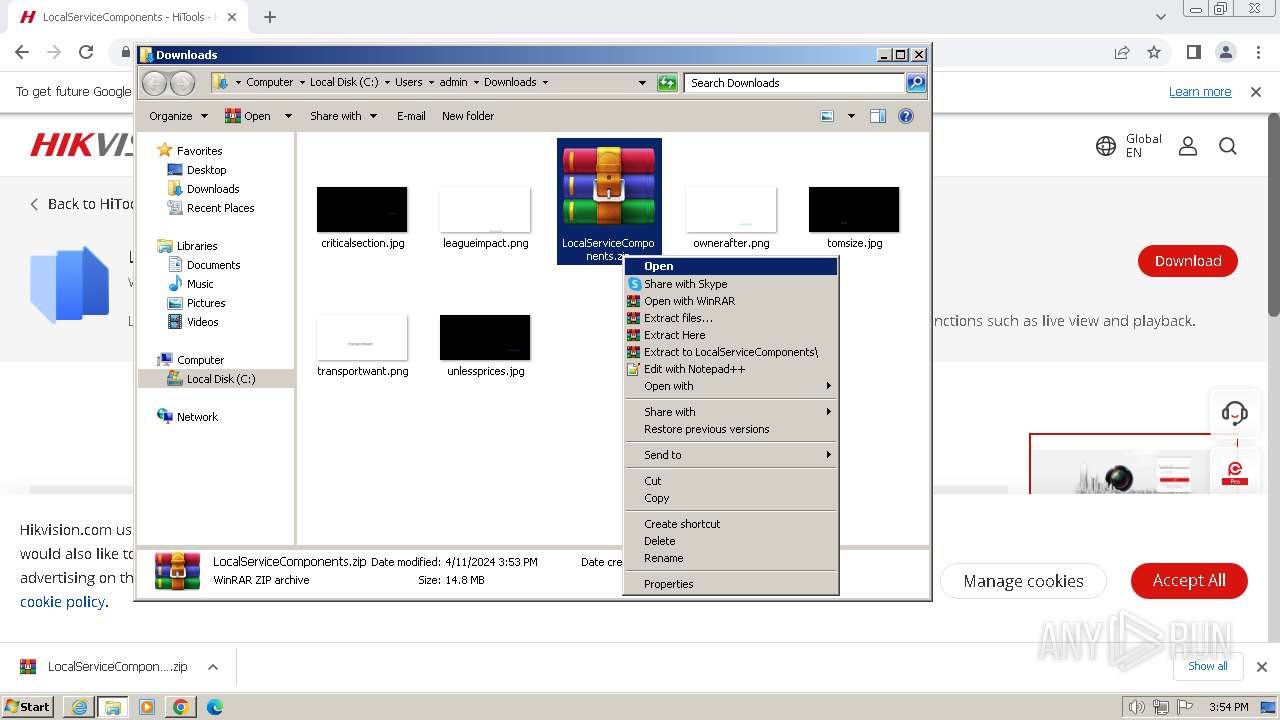
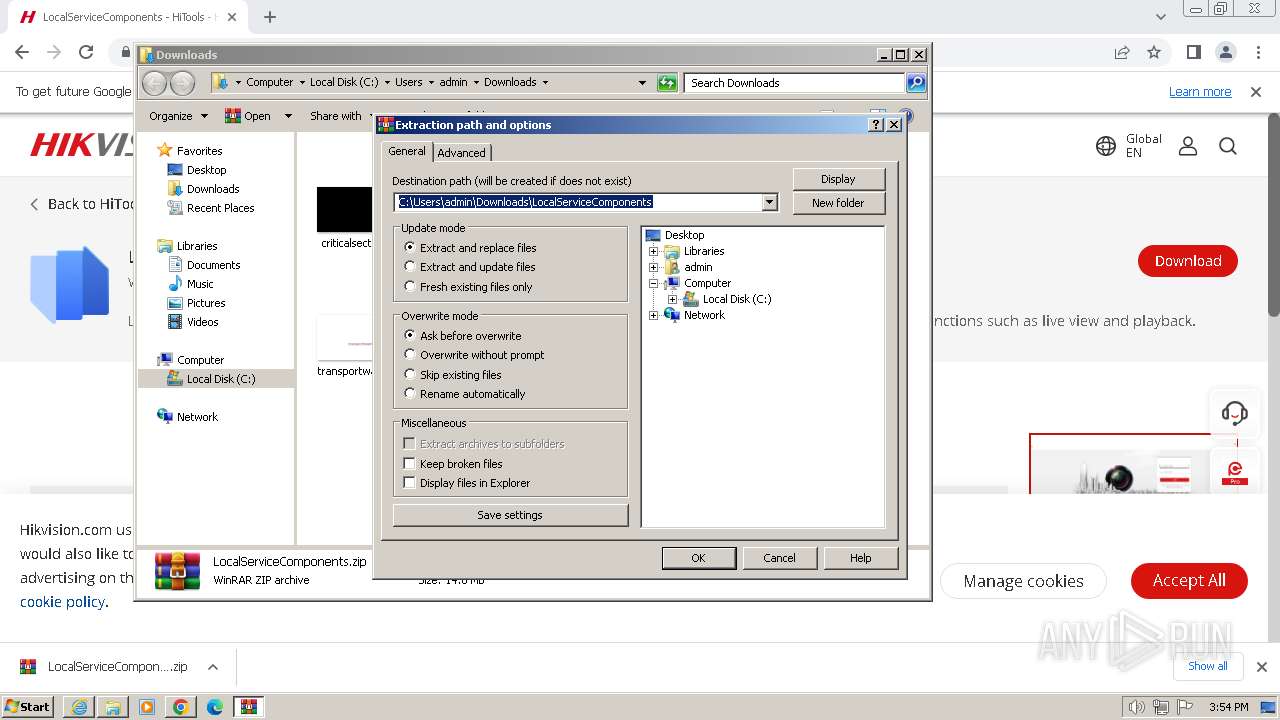
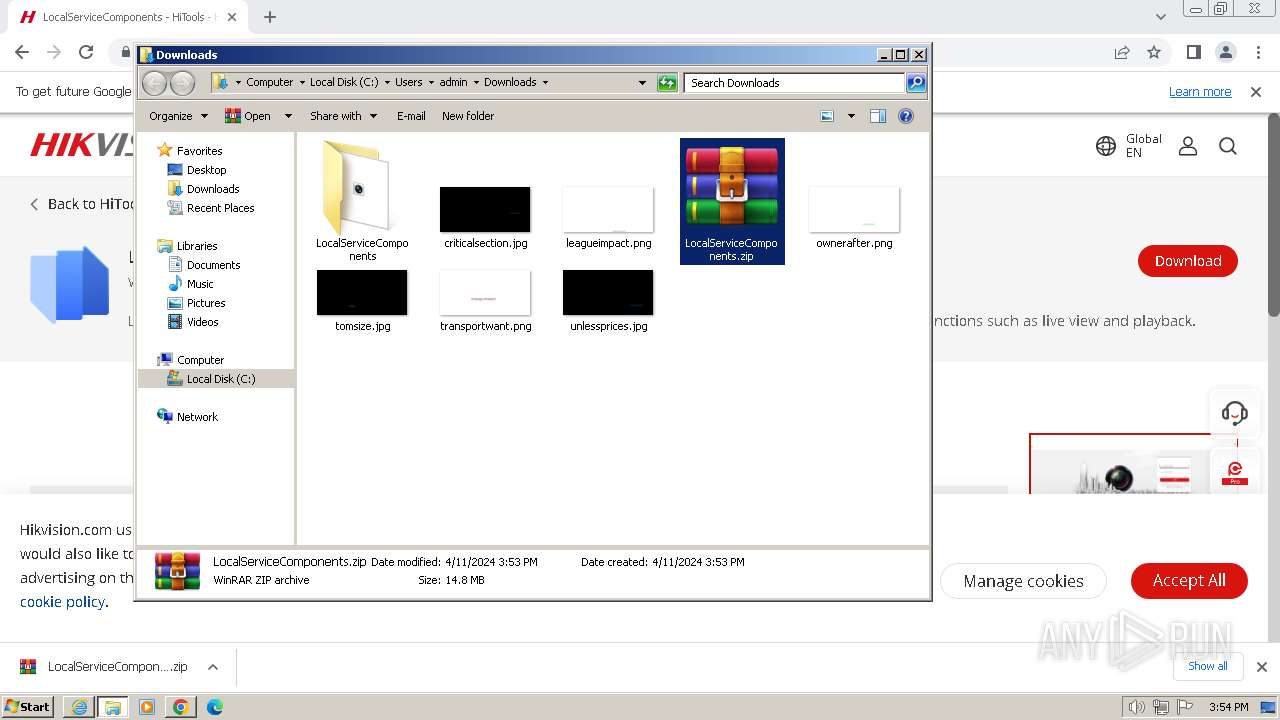
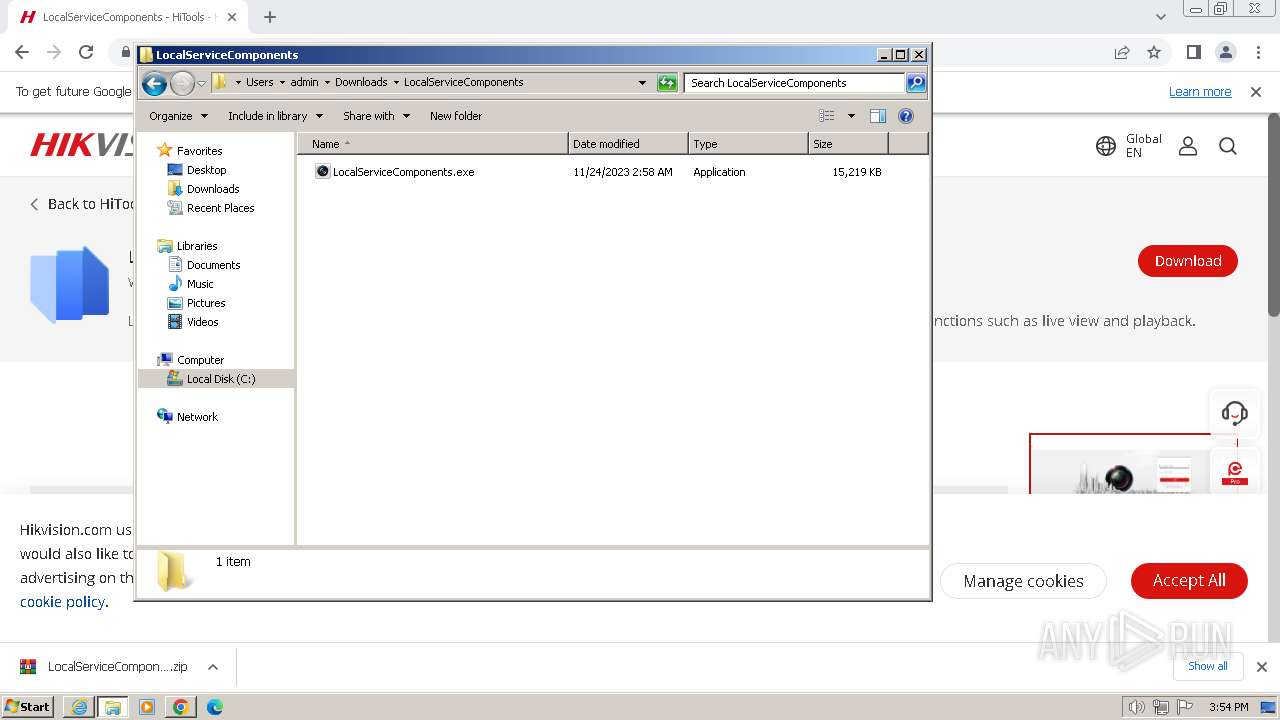
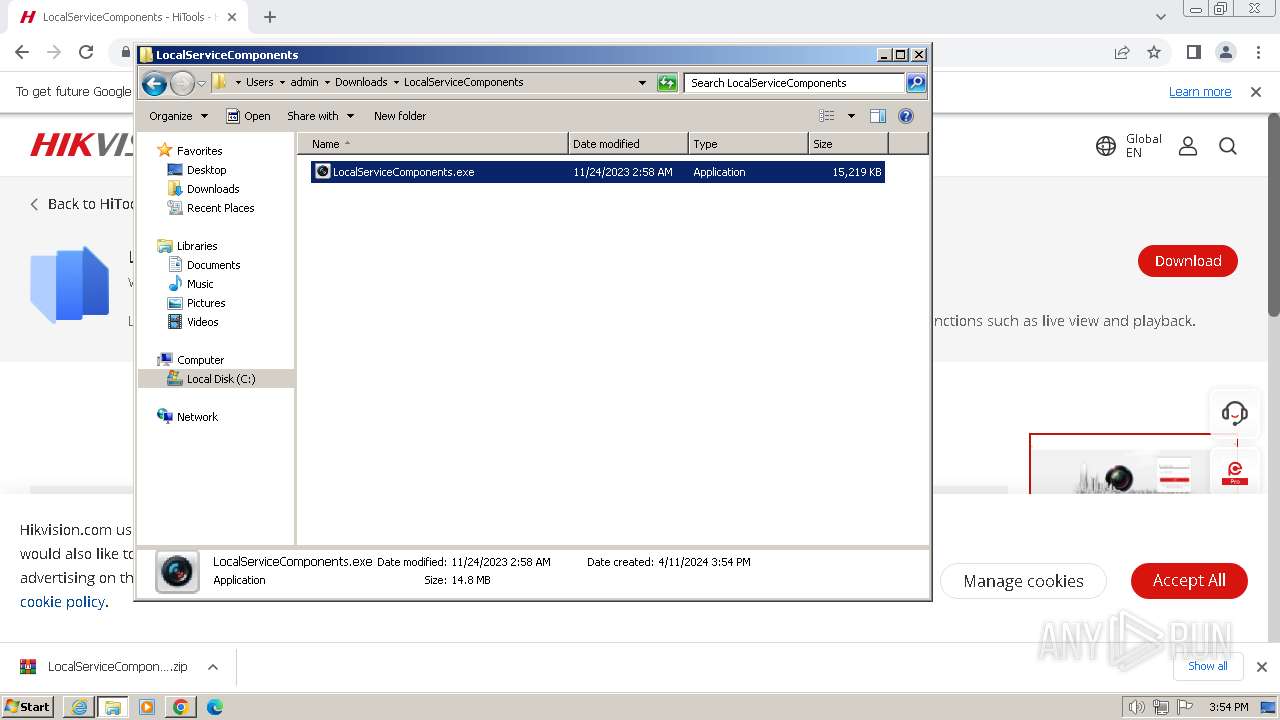
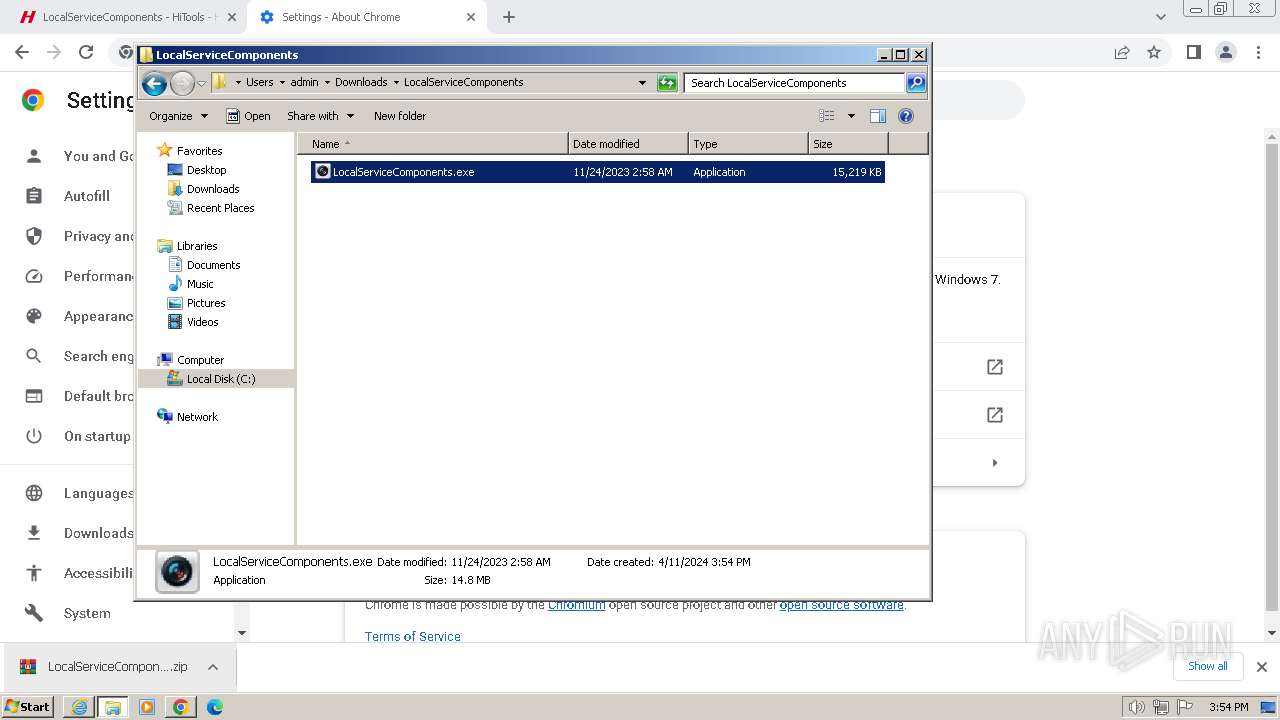
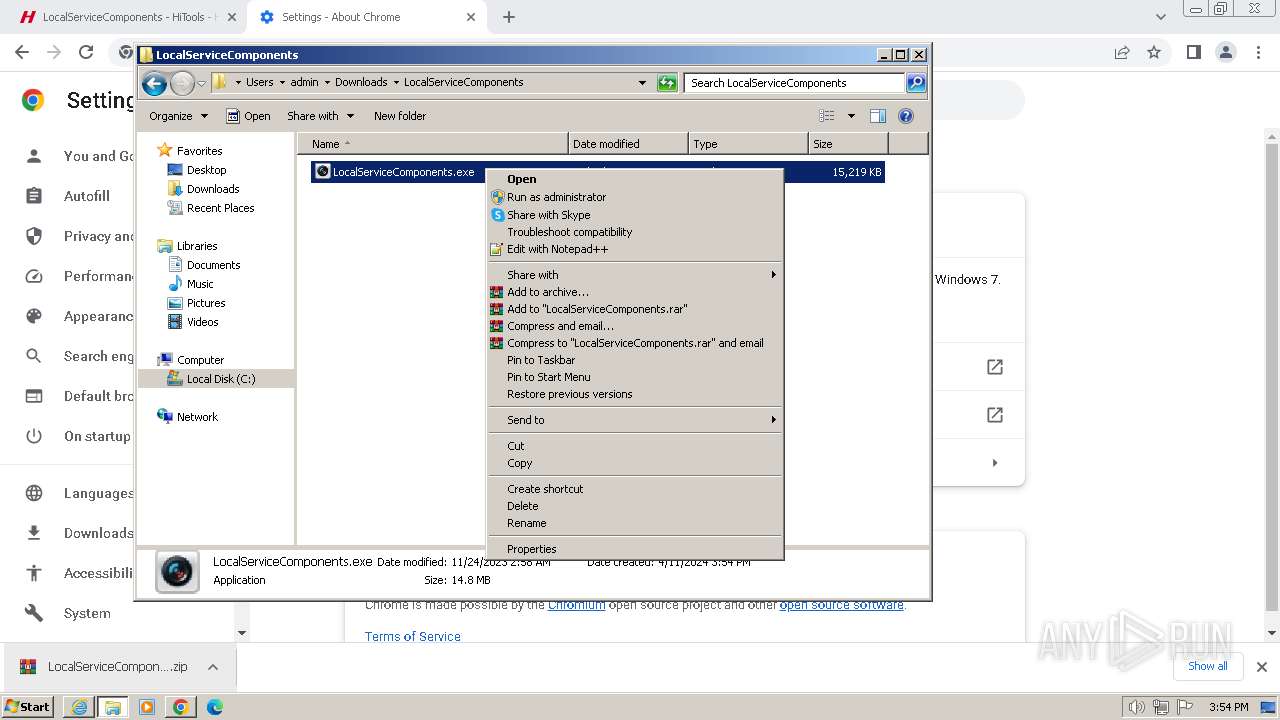
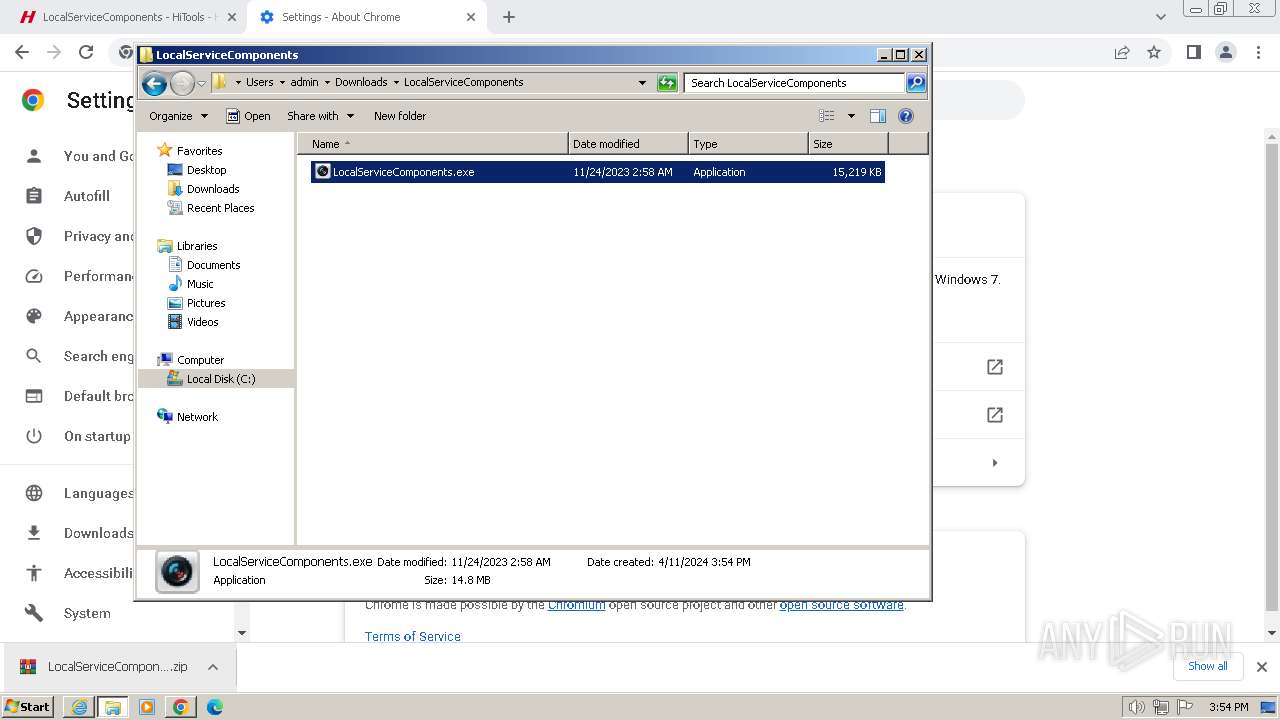
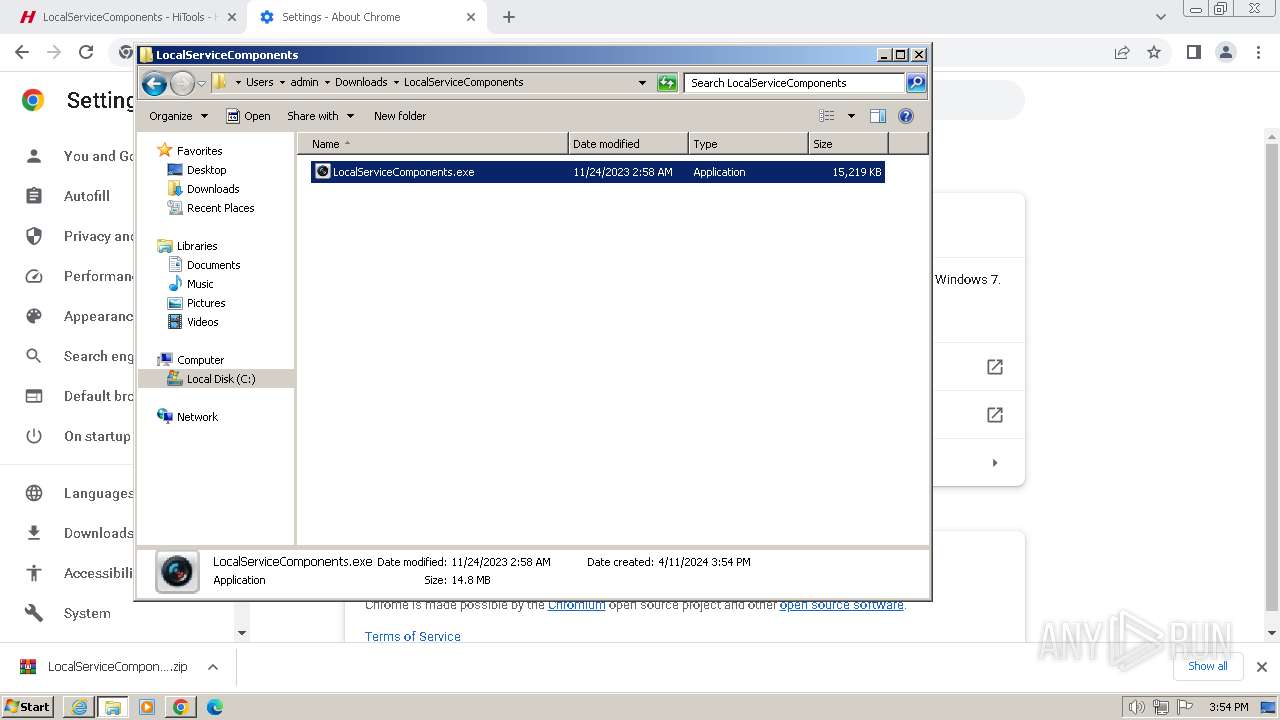
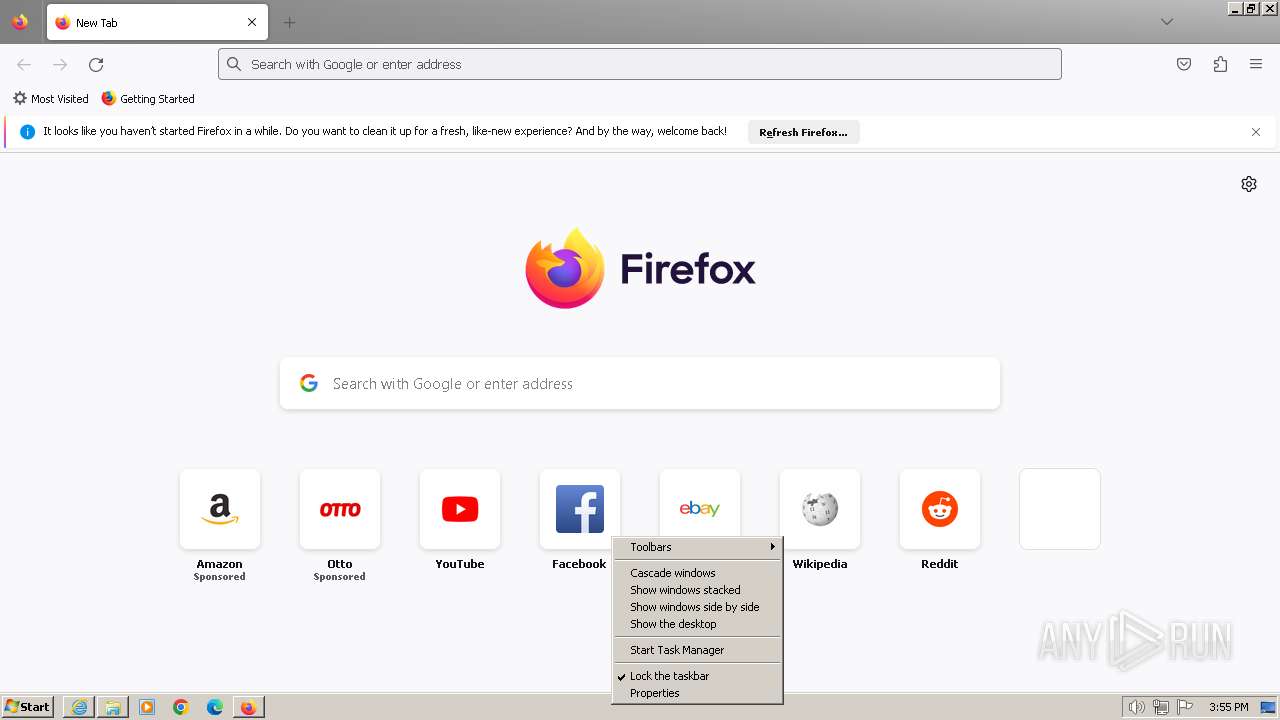
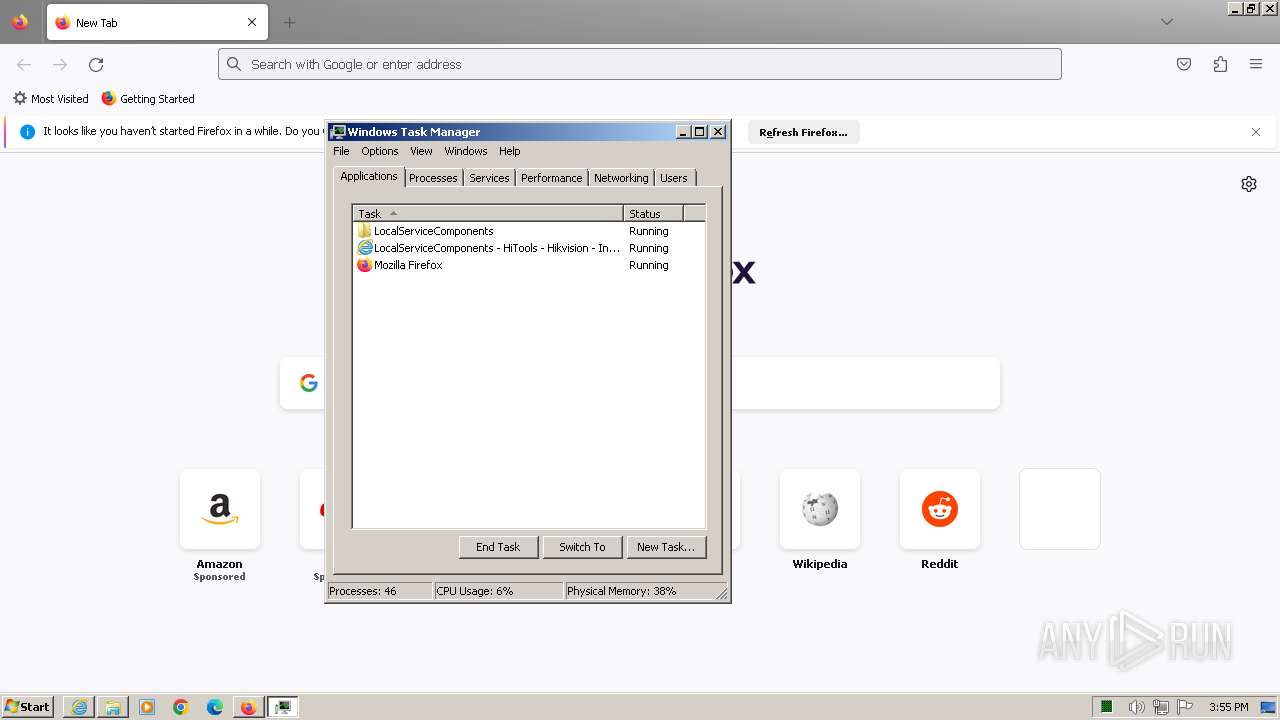
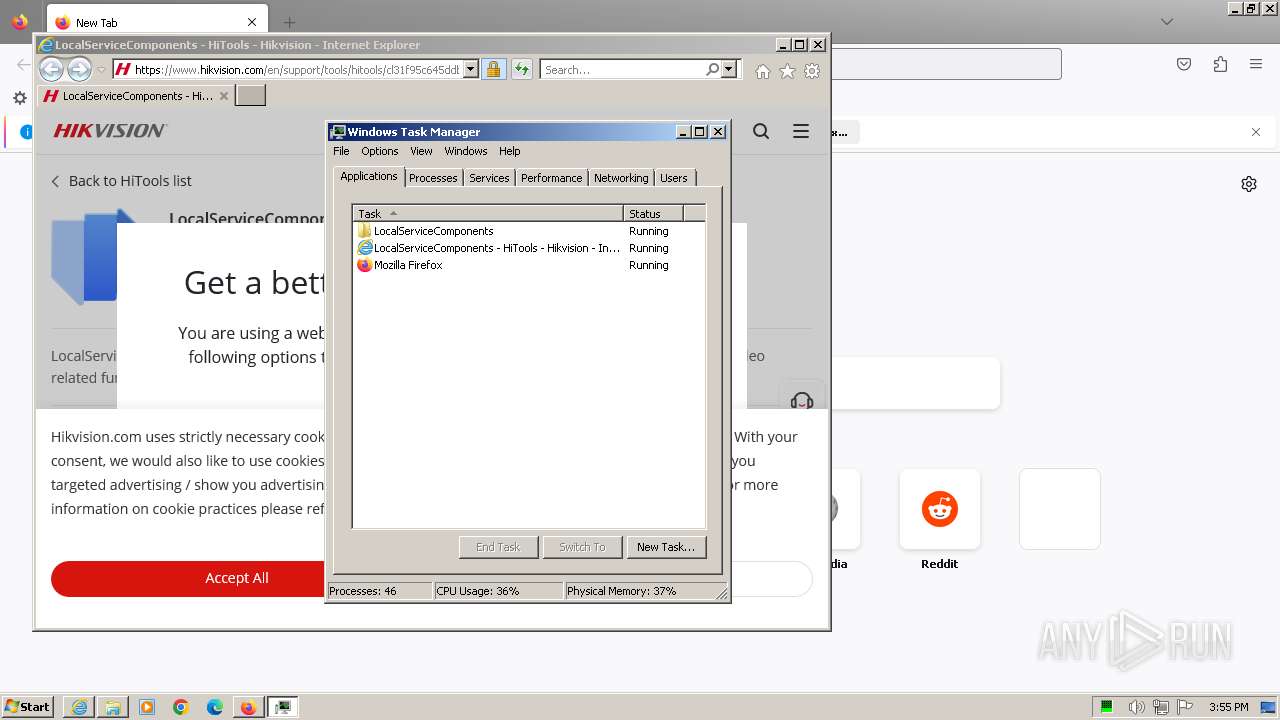
Manual execution by a user
- chrome.exe (PID: 1864)
- WinRAR.exe (PID: 1900)
- LocalServiceComponents.exe (PID: 3228)
- LocalServiceComponents.exe (PID: 3296)
- taskmgr.exe (PID: 3244)
- LocalServiceControl.exe (PID: 2244)
- firefox.exe (PID: 1092)
- msedge.exe (PID: 3780)
The process uses the downloaded file
- WinRAR.exe (PID: 1900)
- chrome.exe (PID: 2512)
Reads the computer name
- LocalServiceComponents.tmp (PID: 3384)
- LocalServiceComponents.tmp (PID: 3952)
- GoogleUpdate.exe (PID: 3128)
- GoogleUpdate.exe (PID: 3832)
- LocalServiceControl.exe (PID: 3924)
- LocalServiceComponents.tmp (PID: 292)
- LocalServiceControl.exe (PID: 2360)
- LocalServiceControl.exe (PID: 2244)
- LocalServiceControl.exe (PID: 1596)
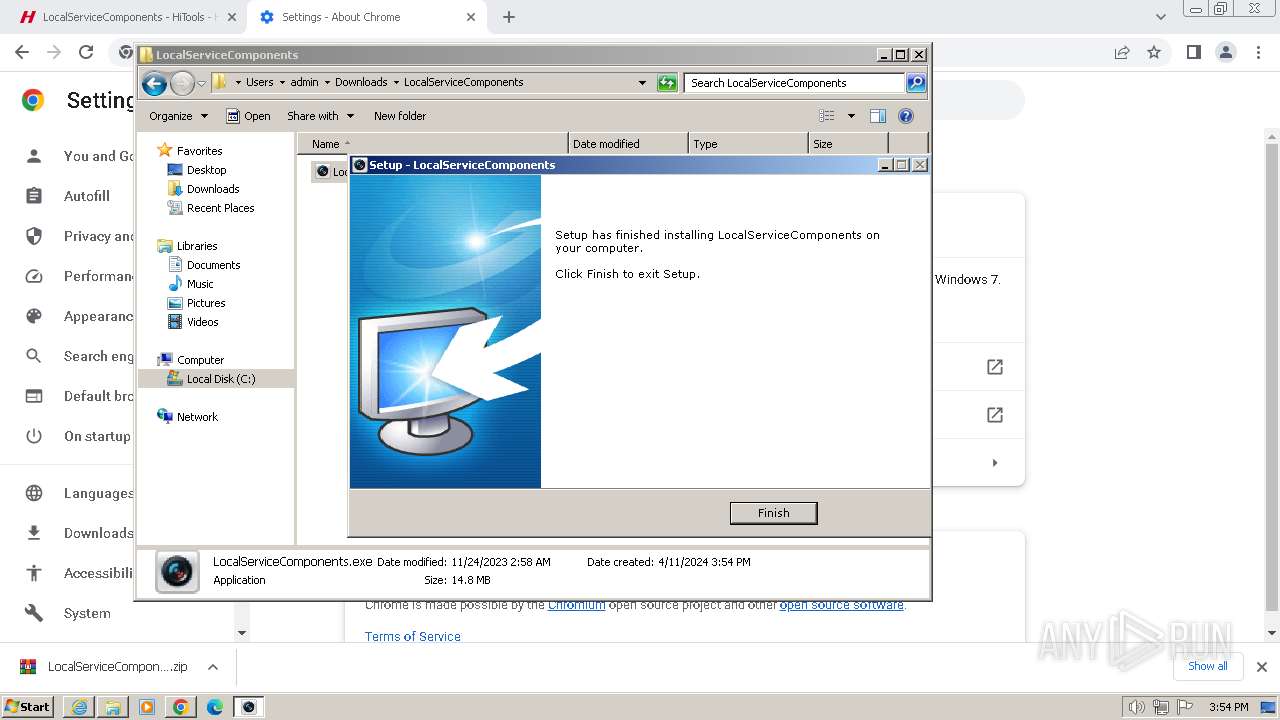
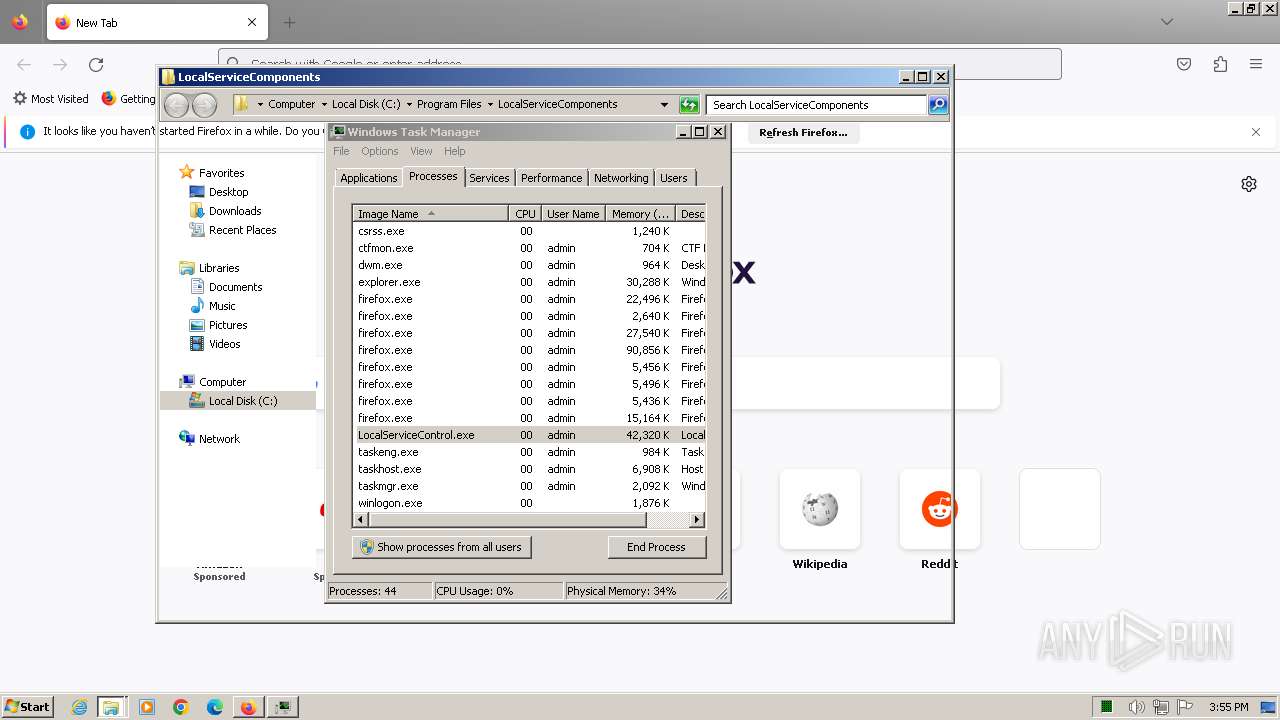
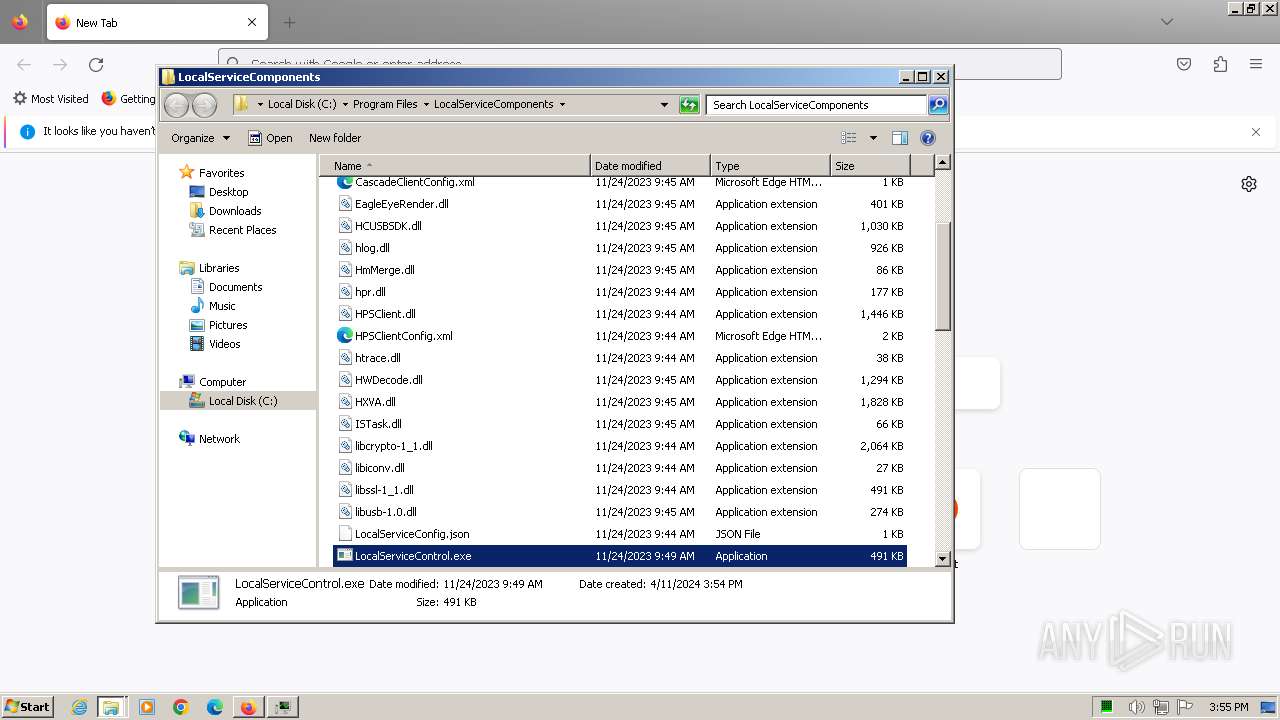
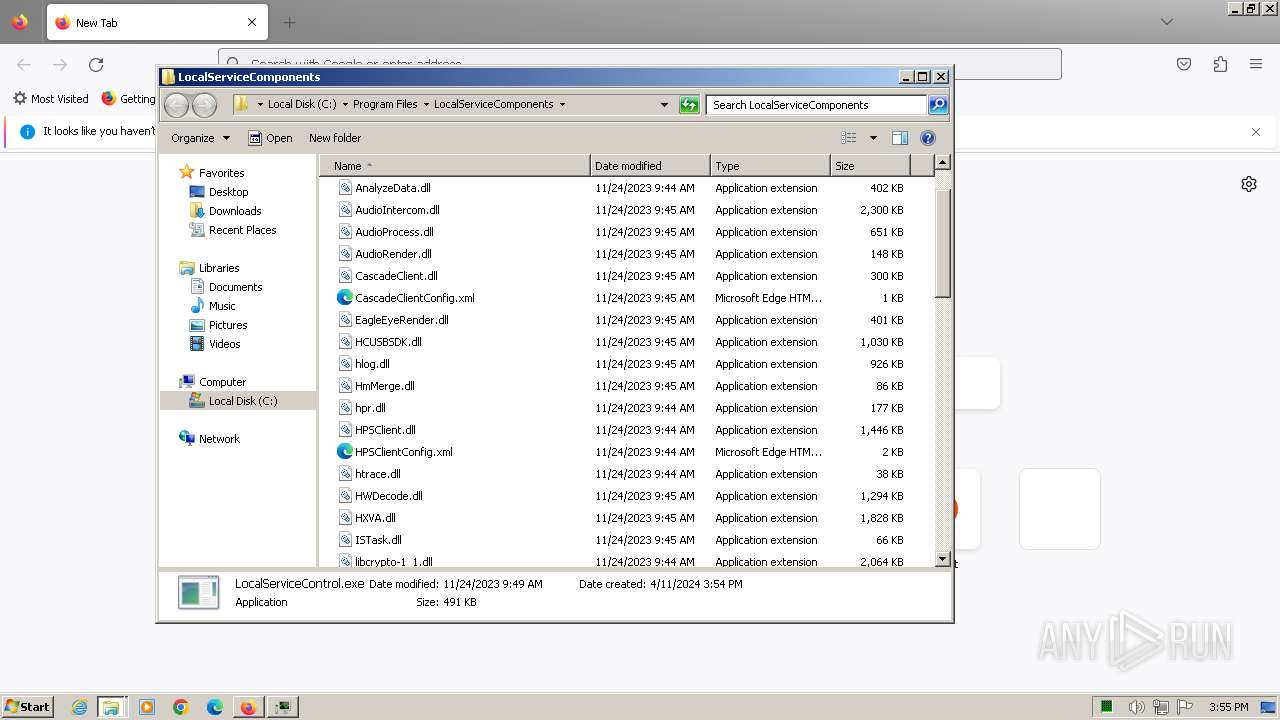
Creates files in the program directory
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceControl.exe (PID: 3924)
- LocalServiceComponents.tmp (PID: 292)
Creates a software uninstall entry
- LocalServiceComponents.tmp (PID: 3952)
- LocalServiceComponents.tmp (PID: 292)
Reads the machine GUID from the registry
- GoogleUpdate.exe (PID: 3128)
- GoogleUpdate.exe (PID: 3832)
Checks transactions between databases Windows and Oracle
- GoogleUpdate.exe (PID: 3128)
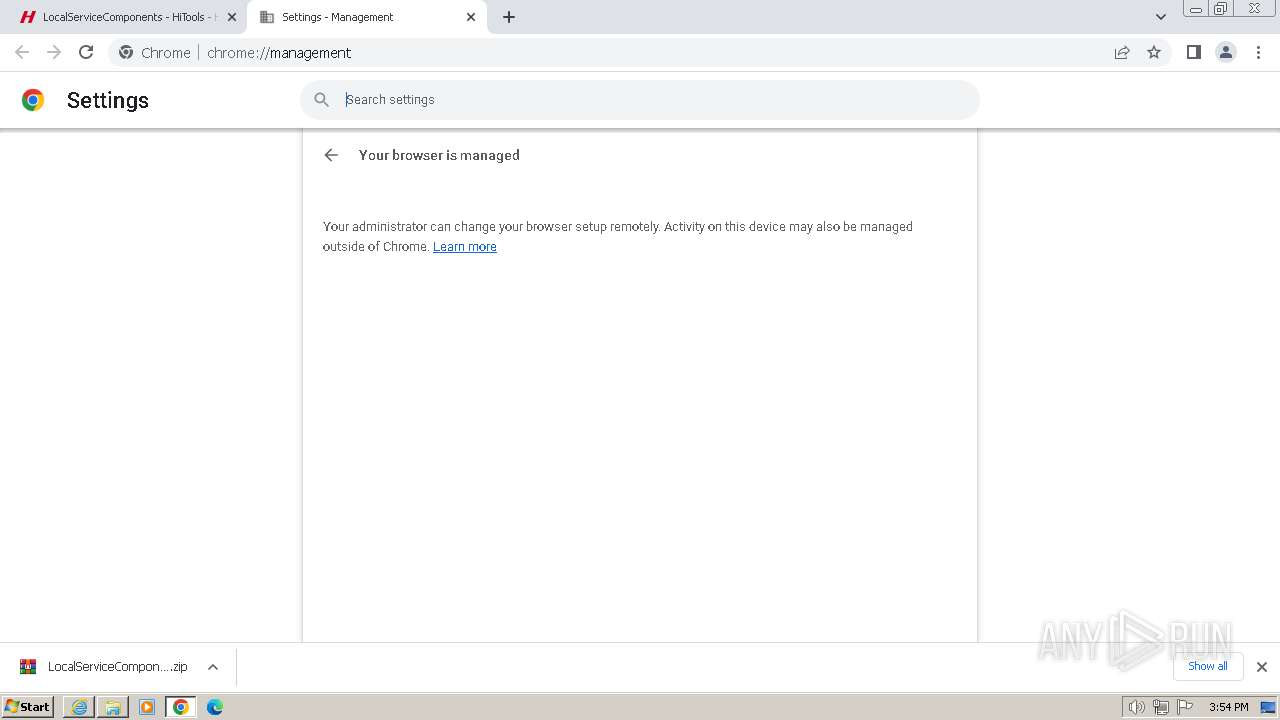
Reads the software policy settings
- GoogleUpdate.exe (PID: 3832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
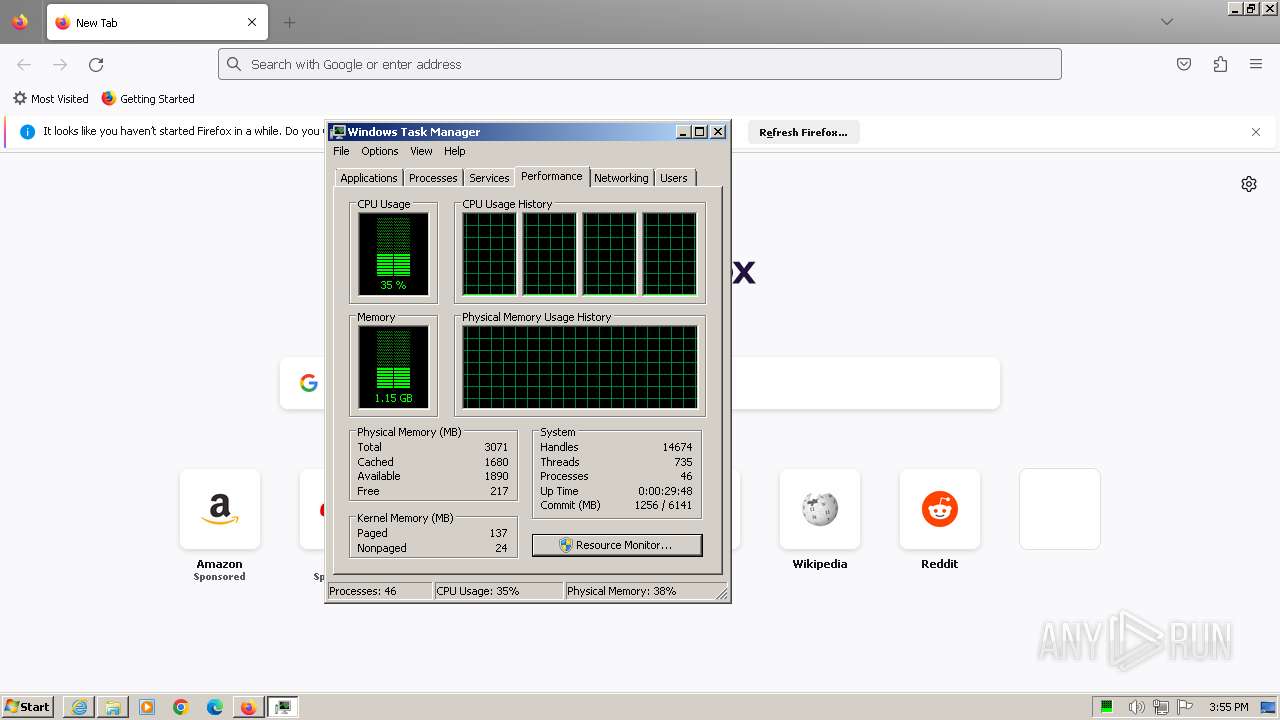
Total processes
119
Monitored processes
63
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Users\admin\AppData\Local\Temp\is-5R56P.tmp\LocalServiceComponents.tmp" /SL5="$801C6,15306282,53760,C:\Users\admin\Downloads\LocalServiceComponents\LocalServiceComponents.exe" | C:\Users\admin\AppData\Local\Temp\is-5R56P.tmp\LocalServiceComponents.tmp | LocalServiceComponents.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1364 --field-trial-handle=1144,i,18242558681128664271,8740425091790986469,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3668 --field-trial-handle=1276,i,3808876830885570130,11718278940620464909,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1388 --field-trial-handle=1144,i,18242558681128664271,8740425091790986469,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4012 --field-trial-handle=1276,i,3808876830885570130,11718278940620464909,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --mojo-platform-channel-handle=672 --field-trial-handle=1144,i,18242558681128664271,8740425091790986469,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4004 --field-trial-handle=1144,i,18242558681128664271,8740425091790986469,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1596 | "C:\Program Files\LocalServiceComponents\LocalServiceControl.exe" | C:\Program Files\LocalServiceComponents\LocalServiceControl.exe | LocalServiceControl.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1380 --field-trial-handle=1276,i,3808876830885570130,11718278940620464909,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
64 414
Read events
63 970
Write events
357
Delete events
87
Modification events
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31099935 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31099935 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
339
Suspicious files
498
Text files
362
Unknown types
456
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FA0A17BC17FF10008872A7205D0D43E2_F3D73775E602E9D349DDB76235C8D29B | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FA0A17BC17FF10008872A7205D0D43E2_F3D73775E602E9D349DDB76235C8D29B | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\AF42041BEE420CD1C686D7880DBFB982_4665B3FFB2E2E75C6A642AE28E4E2DEA | der | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\AF42041BEE420CD1C686D7880DBFB982_4665B3FFB2E2E75C6A642AE28E4E2DEA | binary | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cl31f95c645ddb0235[1].htm | html | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\clientlib-base.min.244c6d44618e866a77c6033a2c8d8bf7[1].css | text | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\clientlib-before.min.f8903ad30cc46b55c6e7f1a8a15996bd[1].js | text | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\player.min.5cec35acc6c8581abc894f54da1b001c[1].css | text | |
MD5:— | SHA256:— | |||
| 3964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\clientlib-third.min.72d30de8617a964d7c52b0cad825aca2[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
75
TCP/UDP connections
195
DNS requests
294
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3964 | iexplore.exe | GET | 304 | 173.222.108.226:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | CH | — | — | unknown |
3964 | iexplore.exe | GET | 200 | 163.181.56.211:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAtQ%2FmlMg8lc4iQVxglc%2FkA%3D | DE | binary | 471 b | unknown |
3964 | iexplore.exe | GET | 200 | 163.181.56.211:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSbdW2YlHyqbqMQSJMoyQlqUDWjrQQU70ULeBWRpbbRc6SSb2NaWdNfPp0CEAsSOCrY87Oo4ql97sXG73E%3D | DE | binary | 471 b | unknown |
3964 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJaiu8Zb34NbCEEshrmcCs%3D | US | binary | 471 b | unknown |
3956 | iexplore.exe | GET | 304 | 173.222.108.210:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?70d85e3b0e586cab | CH | — | — | unknown |
3956 | iexplore.exe | GET | 304 | 173.222.108.210:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?96c8eb5dfc595a04 | CH | — | — | unknown |
3956 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | US | binary | 313 b | unknown |
3964 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
3964 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
3964 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3964 | iexplore.exe | 163.171.128.188:443 | www.hikvision.com | QUANTILNETWORKS | DE | unknown |
3964 | iexplore.exe | 173.222.108.210:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
3964 | iexplore.exe | 173.222.108.226:80 | ctldl.windowsupdate.com | Akamai International B.V. | CH | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3964 | iexplore.exe | 163.181.56.211:80 | — | Zhejiang Taobao Network Co.,Ltd | DE | unknown |
3964 | iexplore.exe | 18.66.147.92:443 | tag.aticdn.net | AMAZON-02 | US | unknown |
3964 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hikvision.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.dcocsp.cn |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
snap.licdn.com |
| whitelisted |
tag.aticdn.net |
| unknown |
logws1320.ati-host.net |
| unknown |
Threats
Process | Message |
|---|---|
LocalServiceControl.exe | WriteLocalFile: "C:\\Users\\admin\\WebComponents\\local.json"
|
LocalServiceControl.exe | QCoreApplication::applicationDirPath: Please instantiate the QApplication object first
|
LocalServiceControl.exe | WriteLocalFile: "C:\\Users\\admin\\WebComponents\\local.json"
|
LocalServiceControl.exe | 5
|
LocalServiceControl.exe | 5
|
LocalServiceControl.exe | WriteLocalFile: "C:\\Users\\admin\\WebComponents\\local.json"
|
LocalServiceControl.exe | QCoreApplication::applicationDirPath: Please instantiate the QApplication object first
|
LocalServiceControl.exe | "No such file or directory"
|
LocalServiceControl.exe | "No such file or directory"
|
LocalServiceControl.exe | 5
|