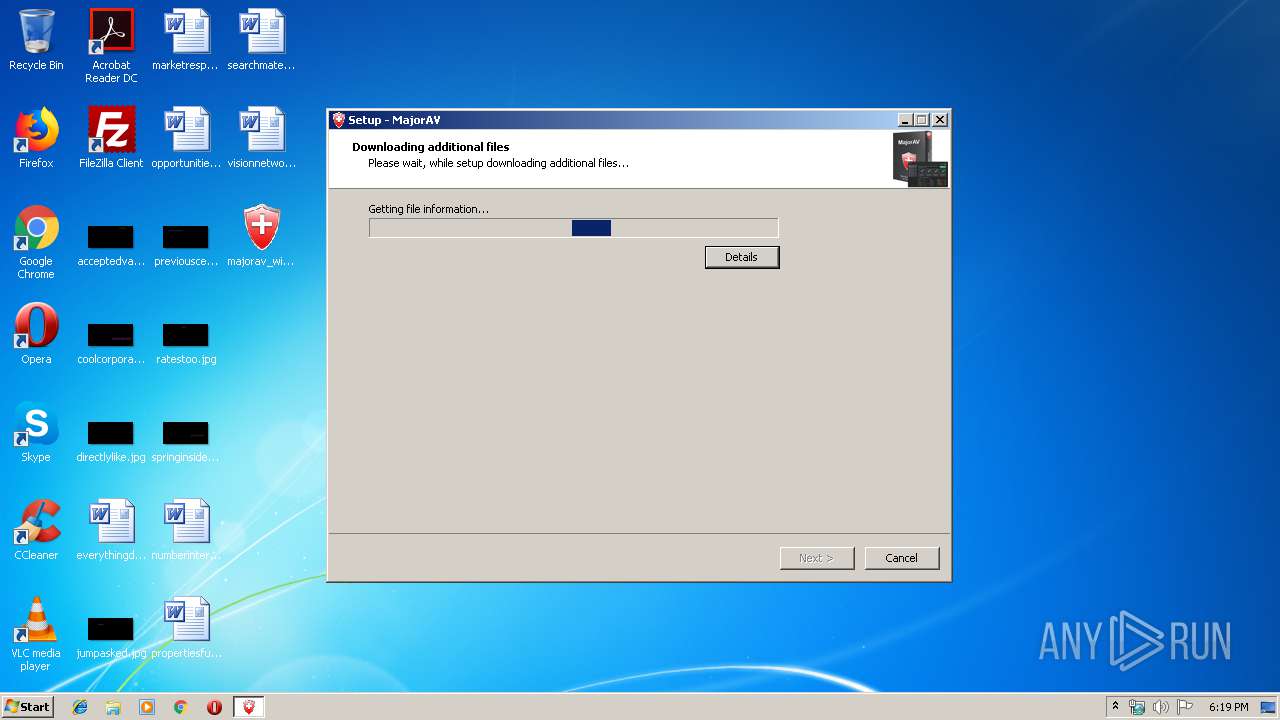
| File name: | majorav_win_setup.exe |
| Full analysis: | https://app.any.run/tasks/3fb6cad1-a36e-4995-a314-fb7ad7e01626 |
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2019, 17:19:17 |
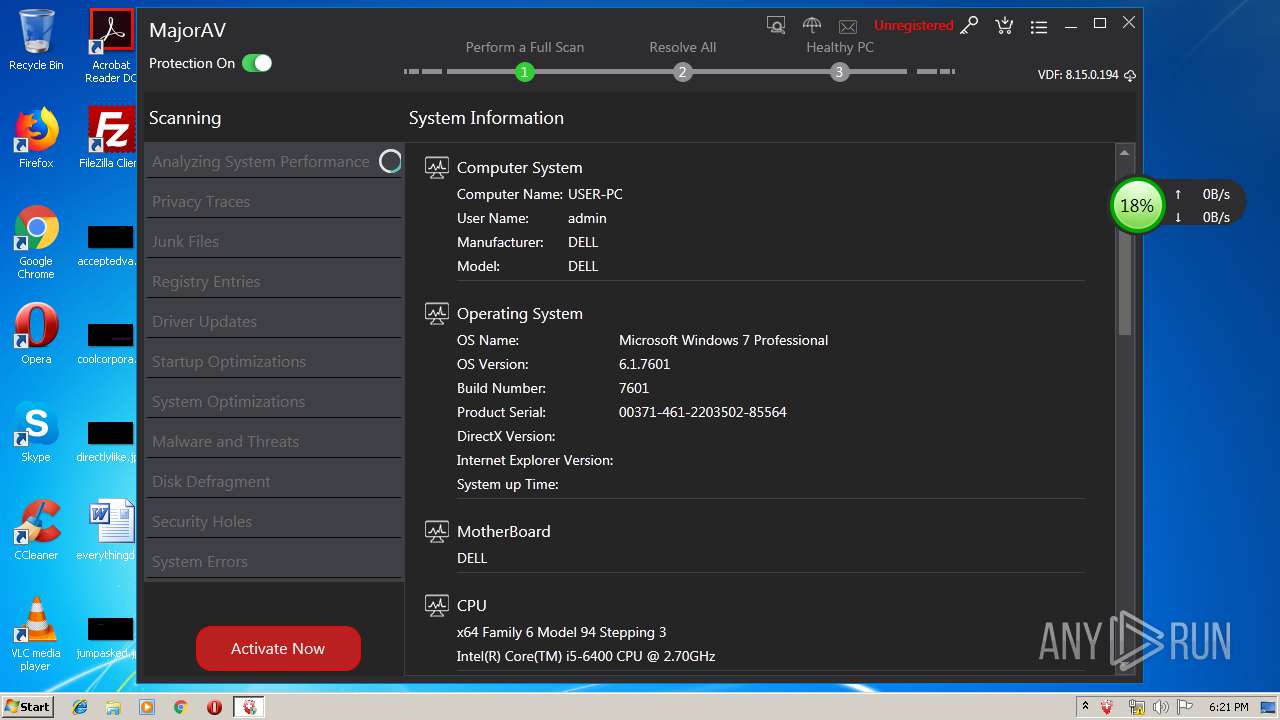
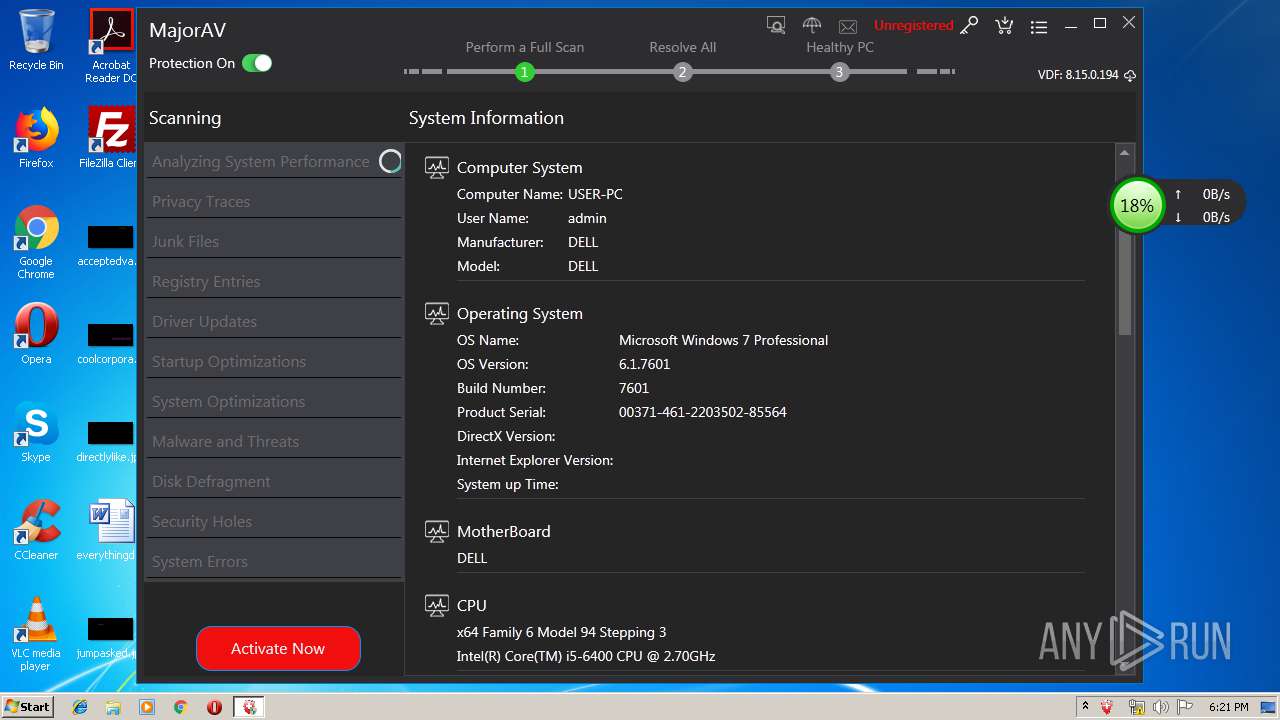
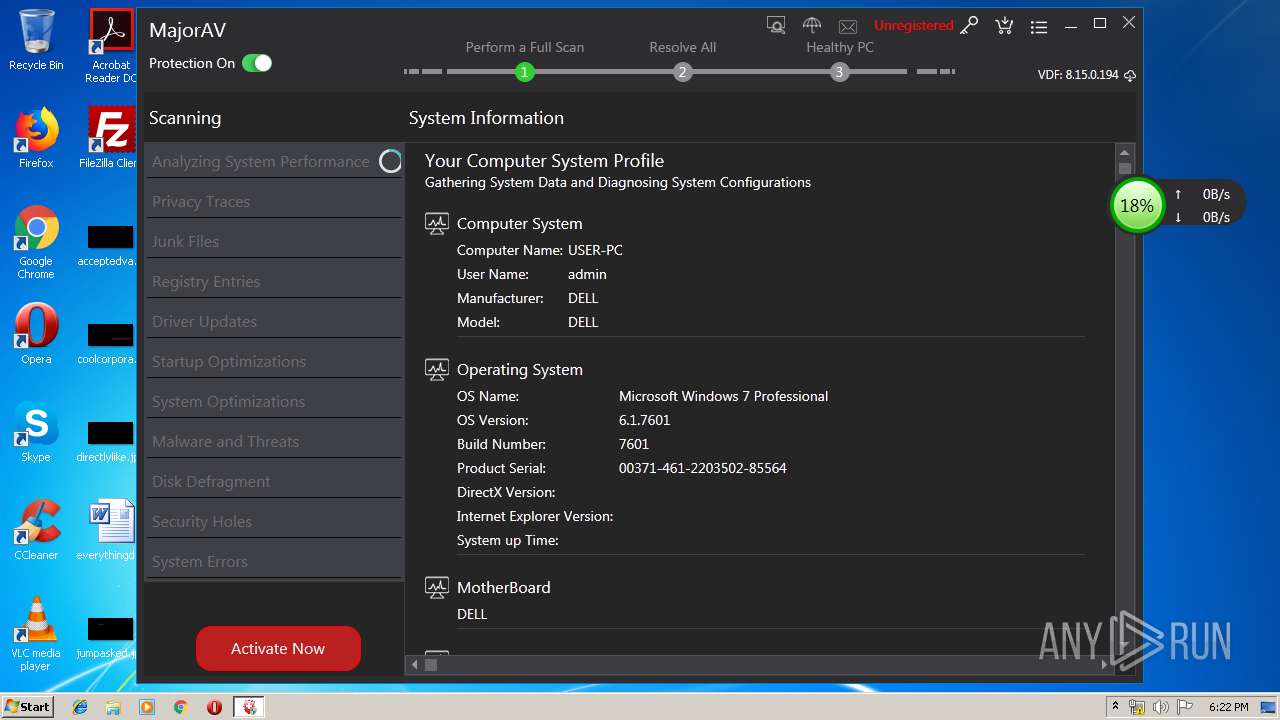
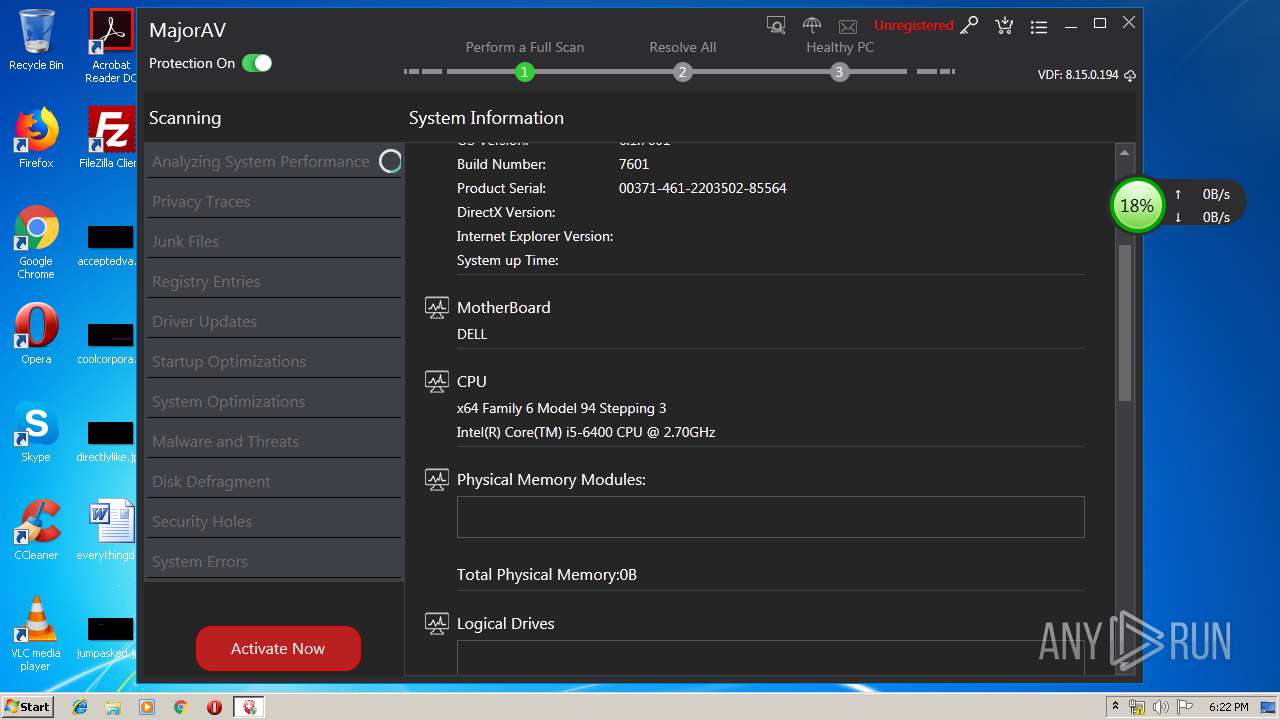
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 03471C5CAE2750B7F30BDE3A51C3DD93 |
| SHA1: | A61AFCB200E32B08F9BDAA9CD2642D595F900637 |
| SHA256: | C251ACE9B732310A68FD2E022DBB5AFF2A9CCD164CF6E5288058EA6C2C6C08A4 |
| SSDEEP: | 196608:RqMWZ1cnWFl2CbN3GFDIiPNCwxHpyvhsrw+W2O1Jdj9:hW8CEDYeyvGweODj9 |
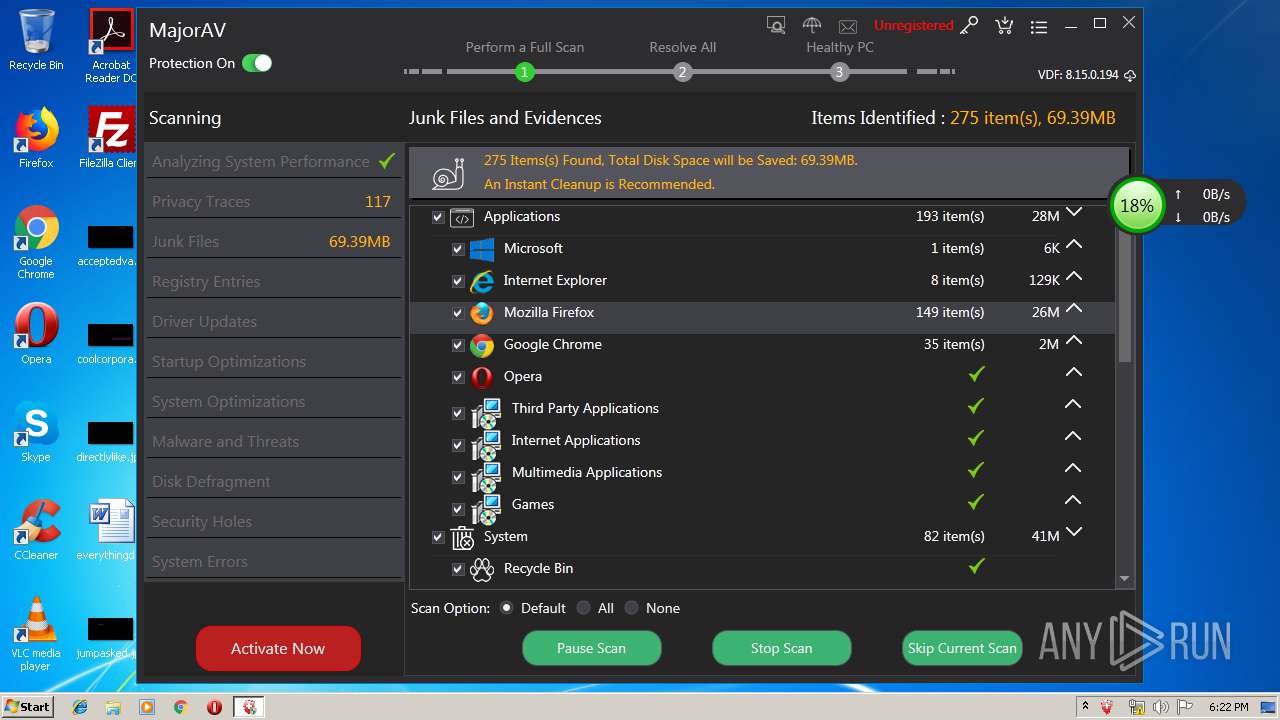
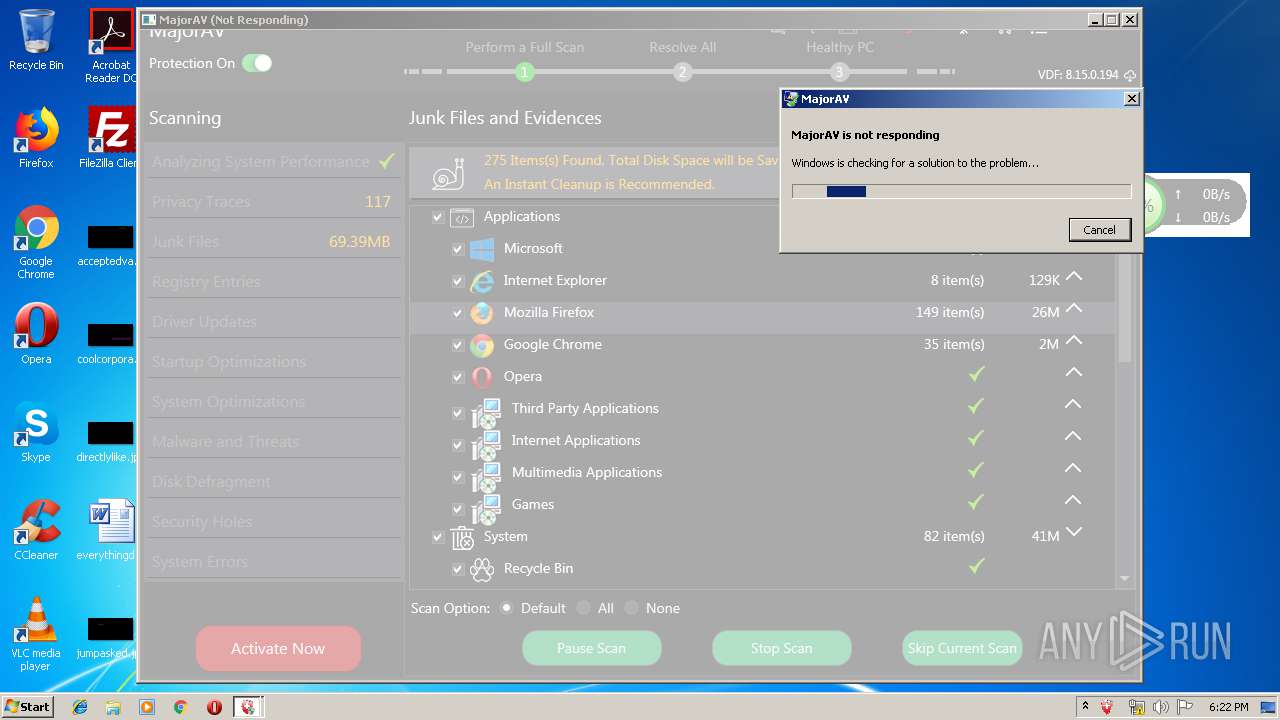
MALICIOUS
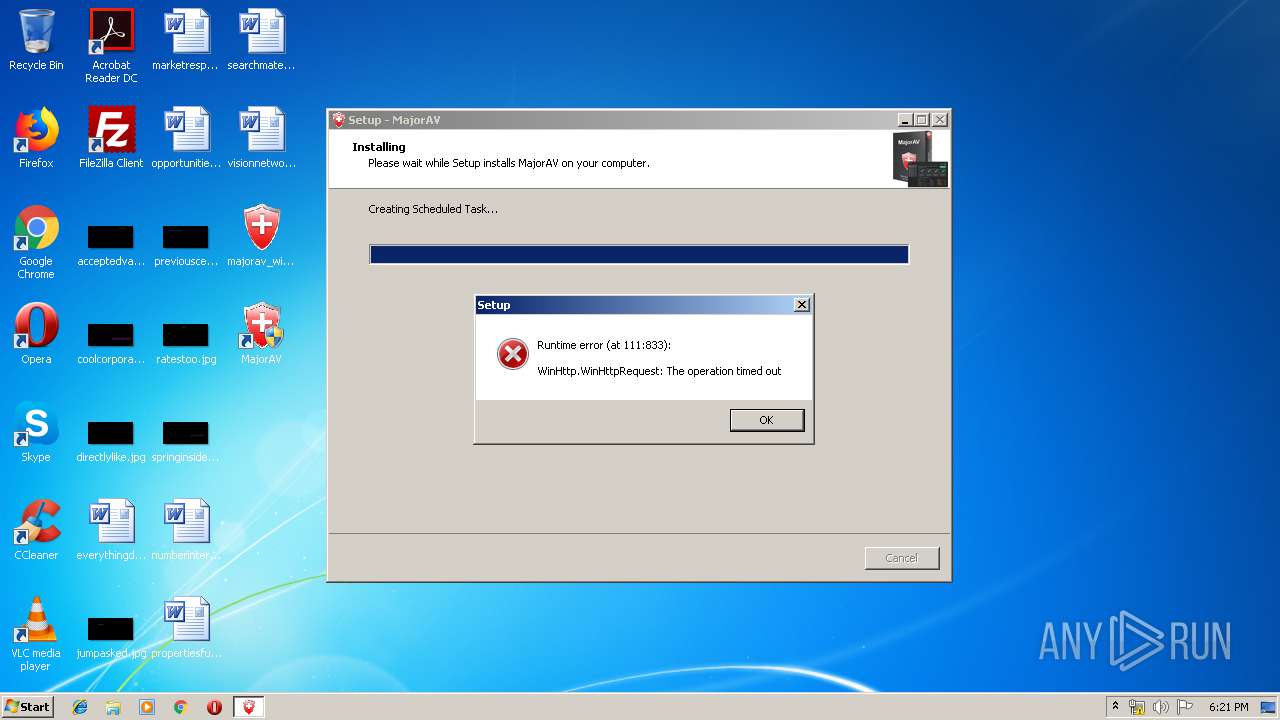
Uses Task Scheduler to run other applications
- majorav_win_setup.tmp (PID: 3352)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2380)
- schtasks.exe (PID: 3124)
- schtasks.exe (PID: 4032)
- MajorAv.exe (PID: 3024)
- MajorAV.exe (PID: 3224)
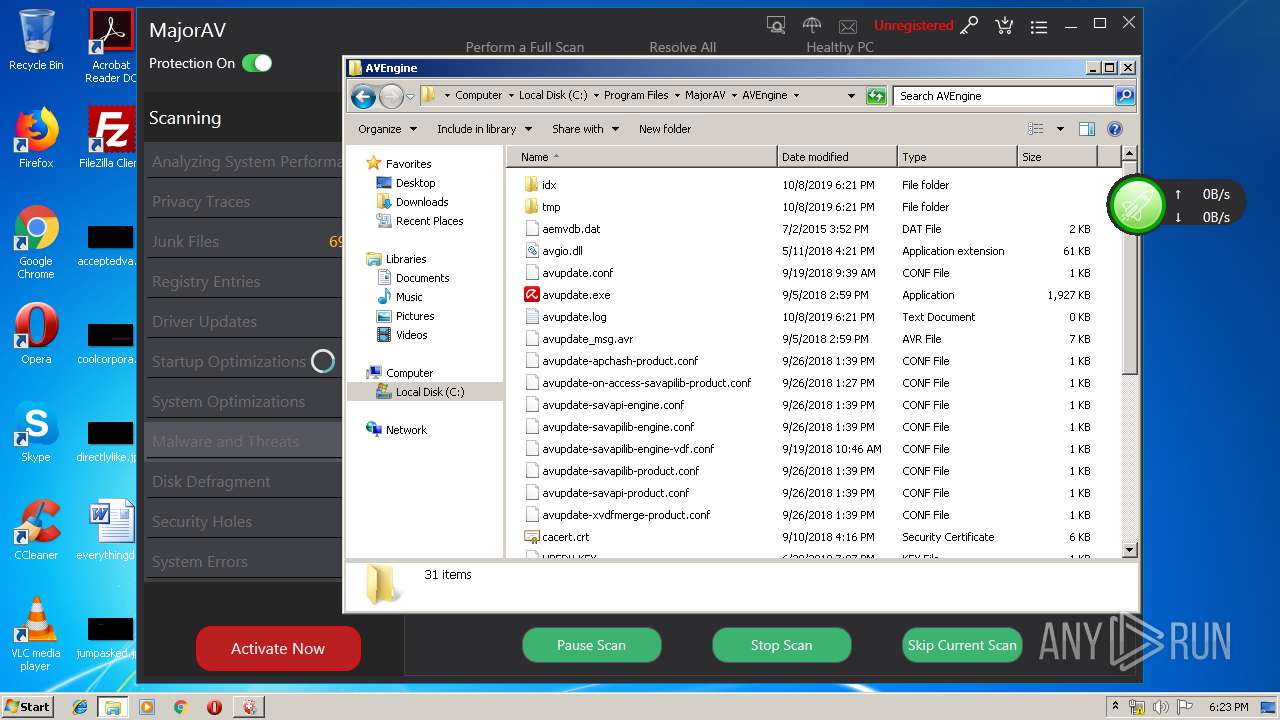
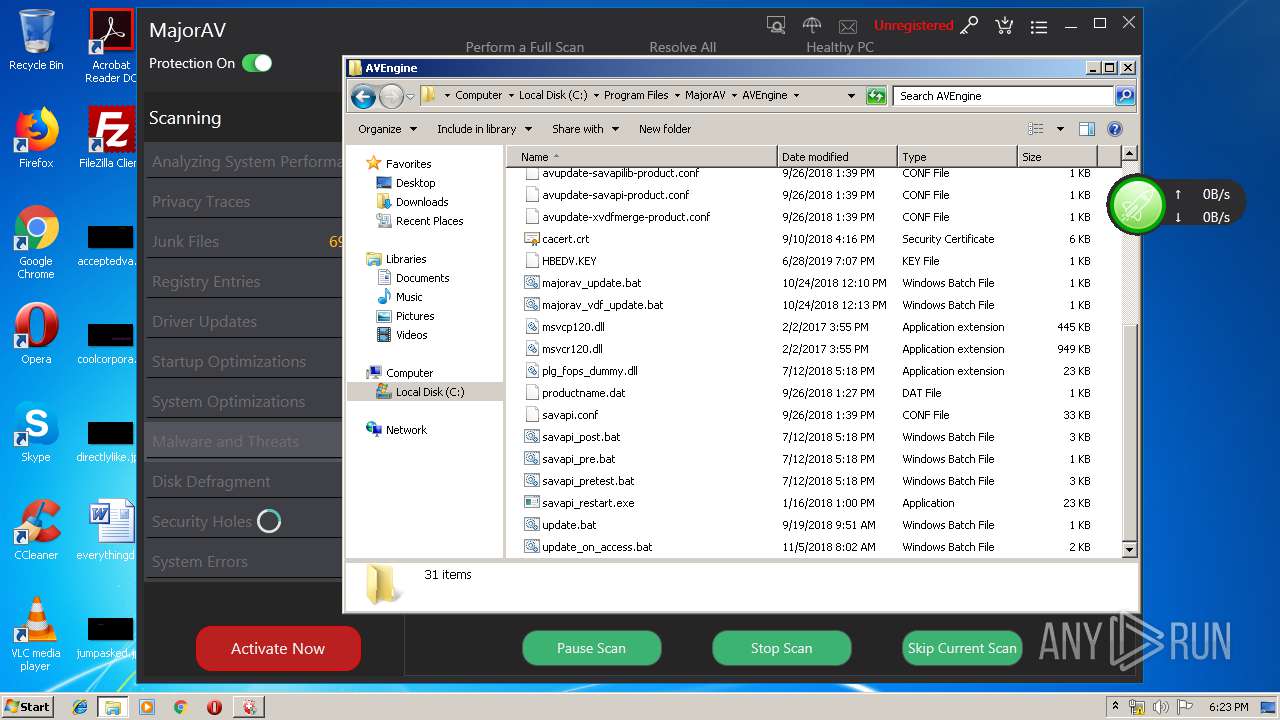
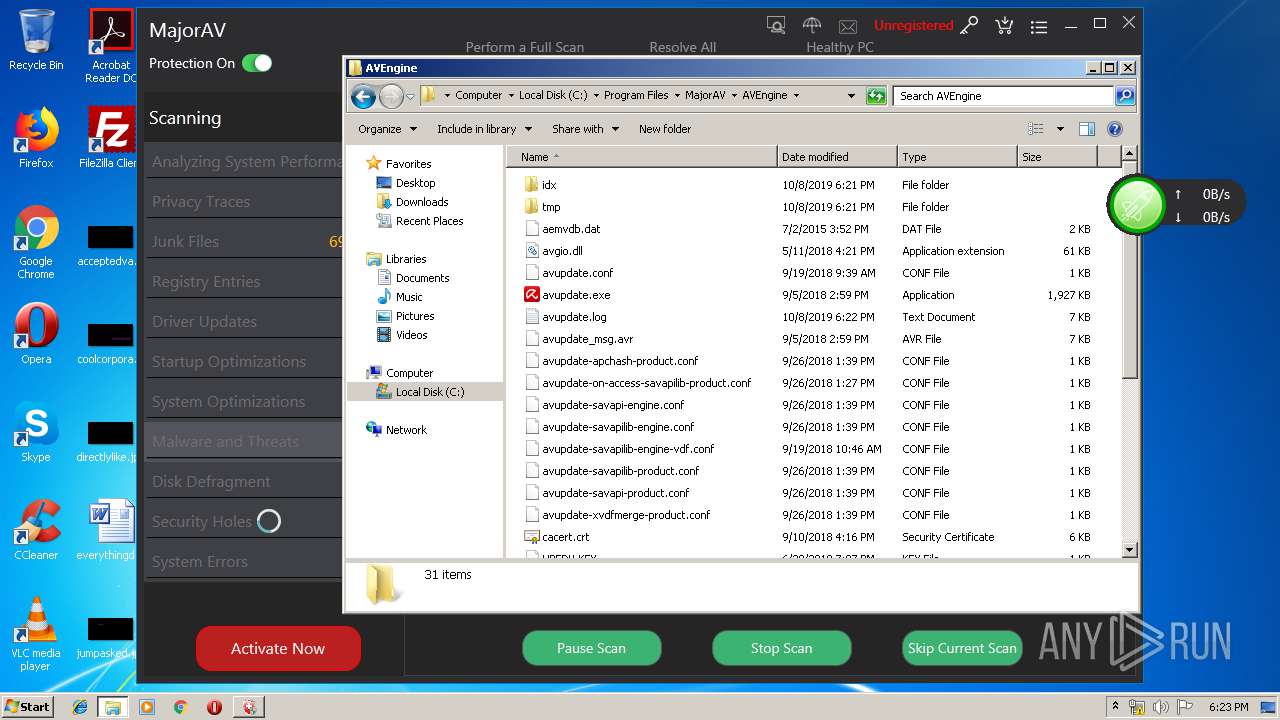
Loads dropped or rewritten executable
- avupdate.exe (PID: 3980)
- werfault.exe (PID: 3288)
- MajorAv.exe (PID: 3024)
- explorer.exe (PID: 236)
- MajorAV.exe (PID: 3224)
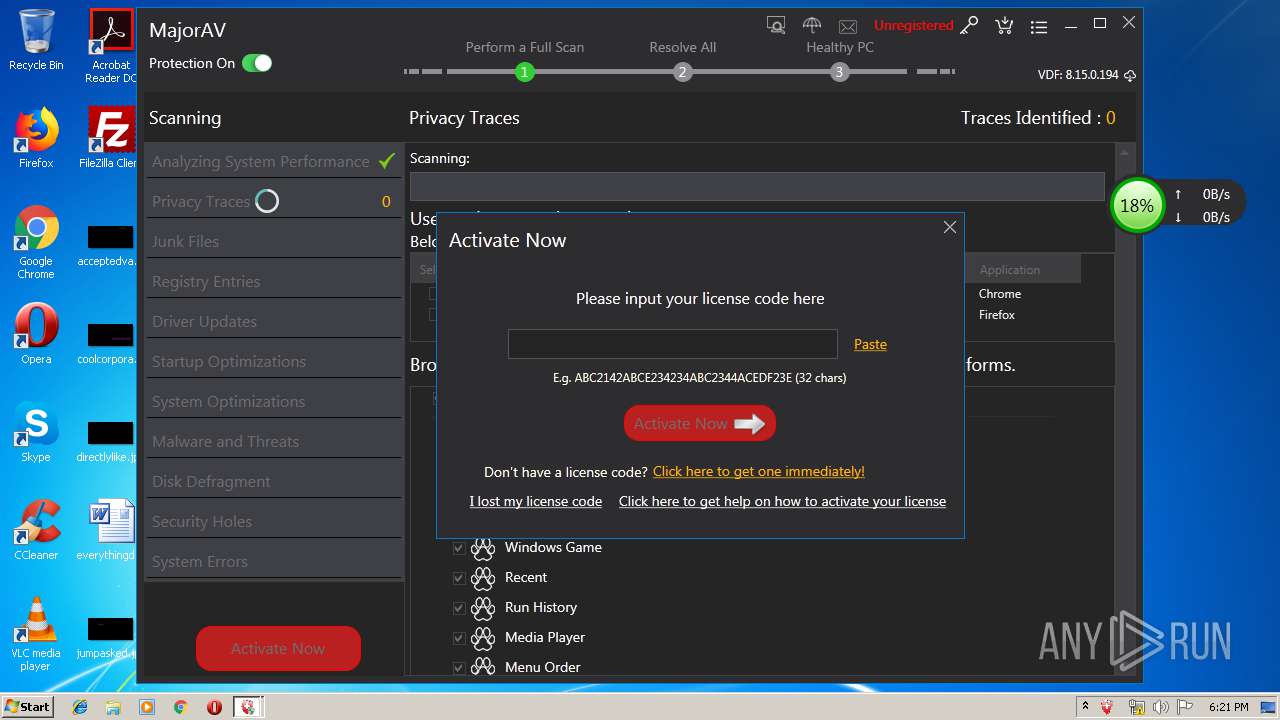
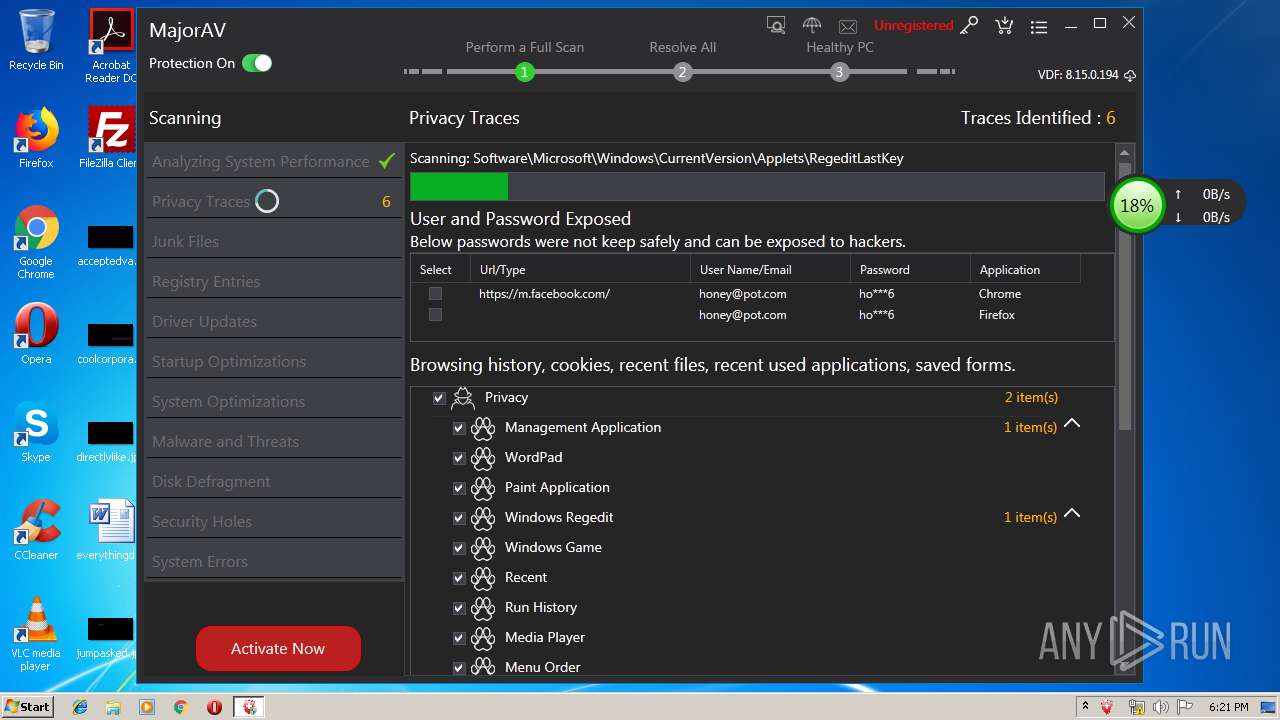
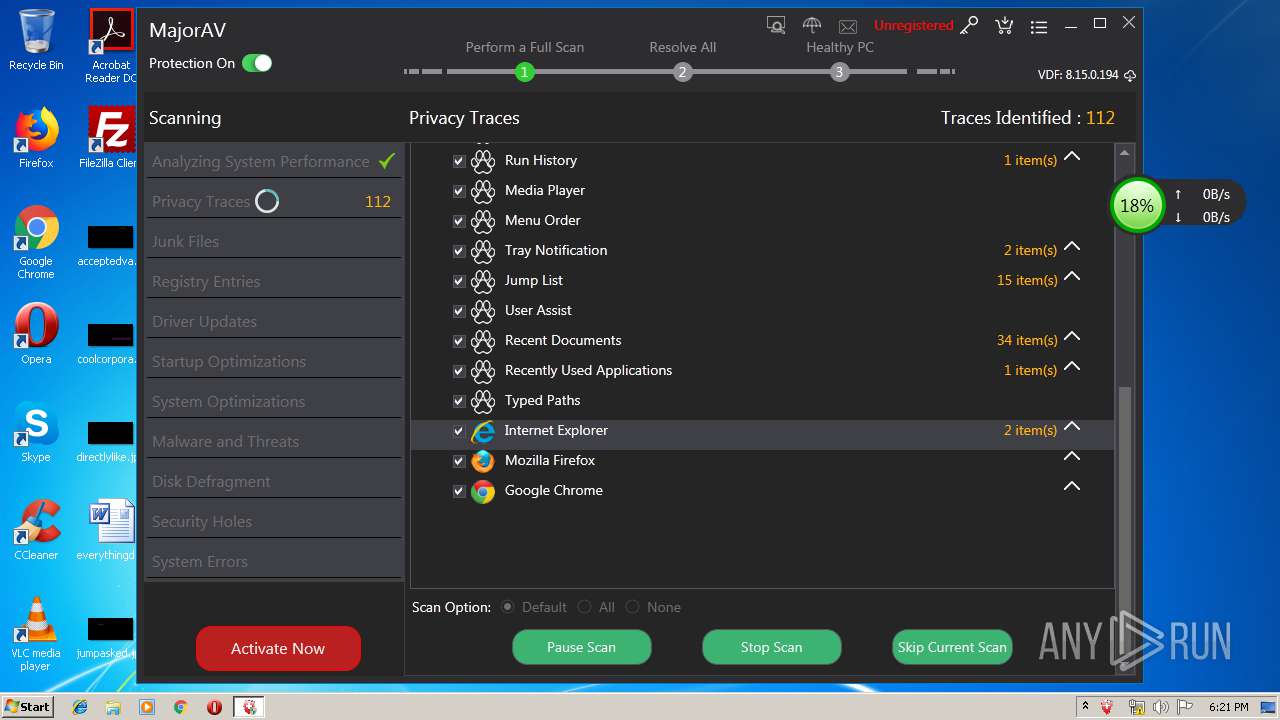
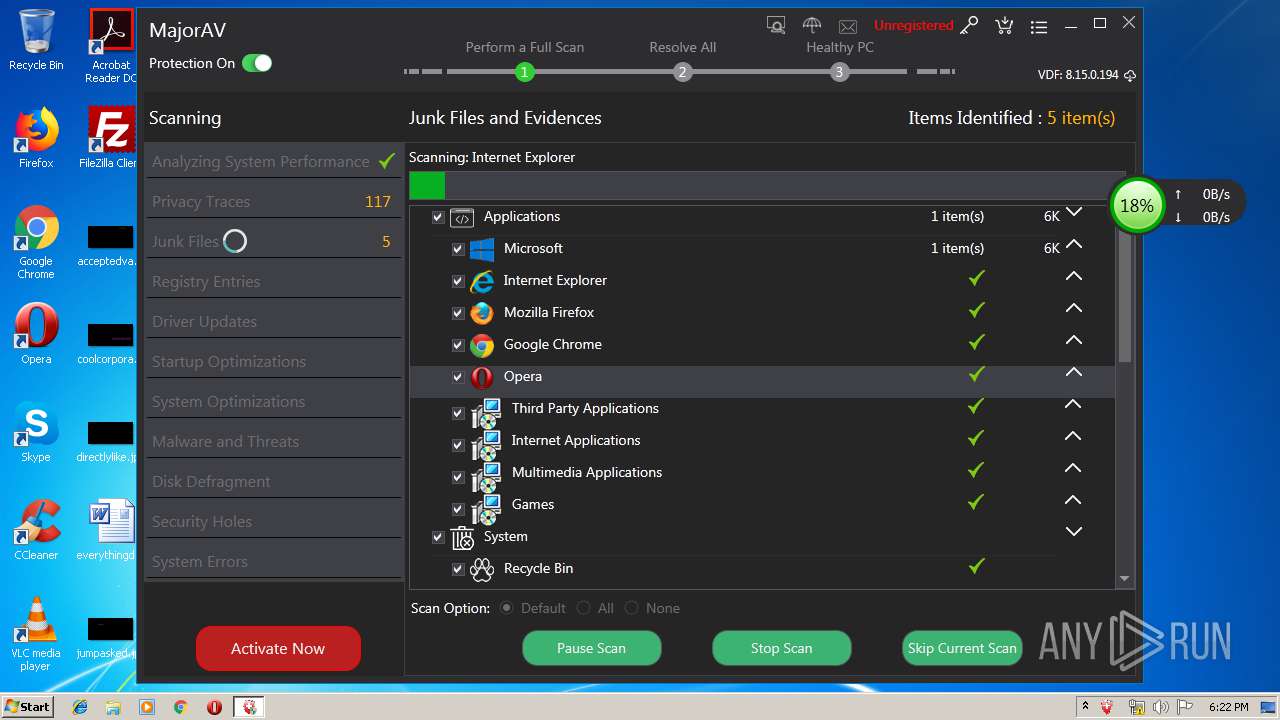
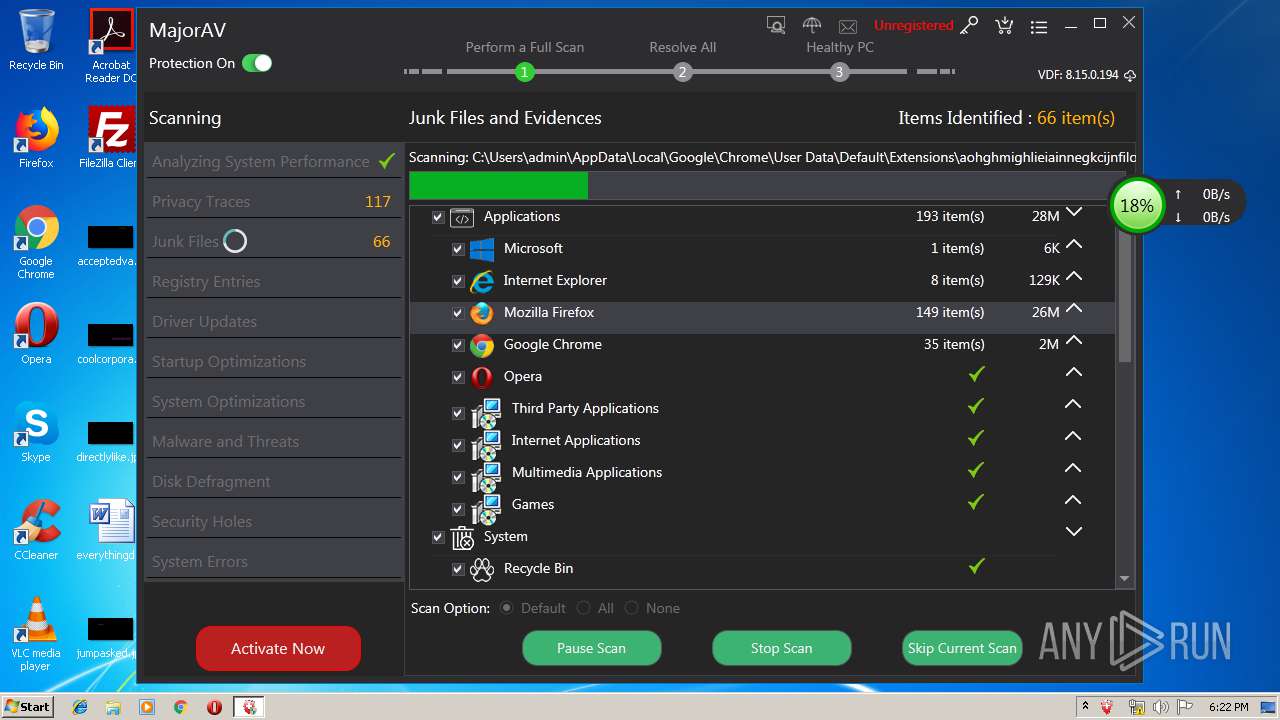
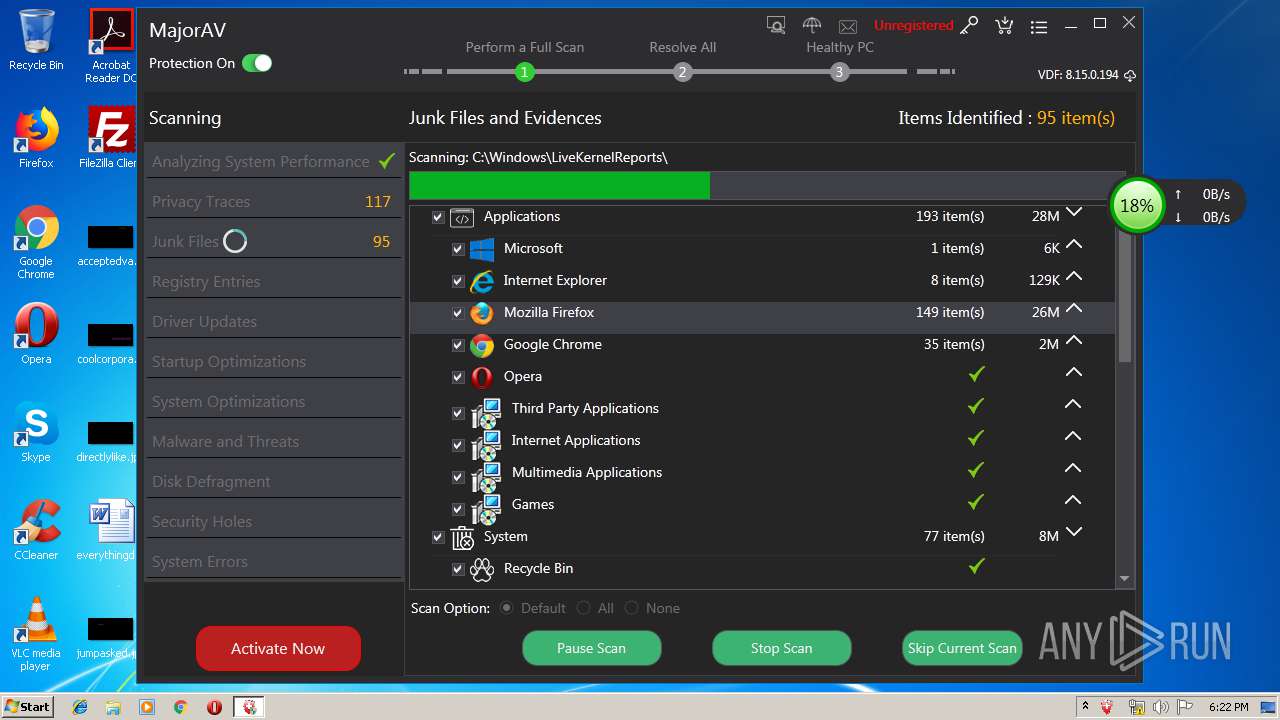
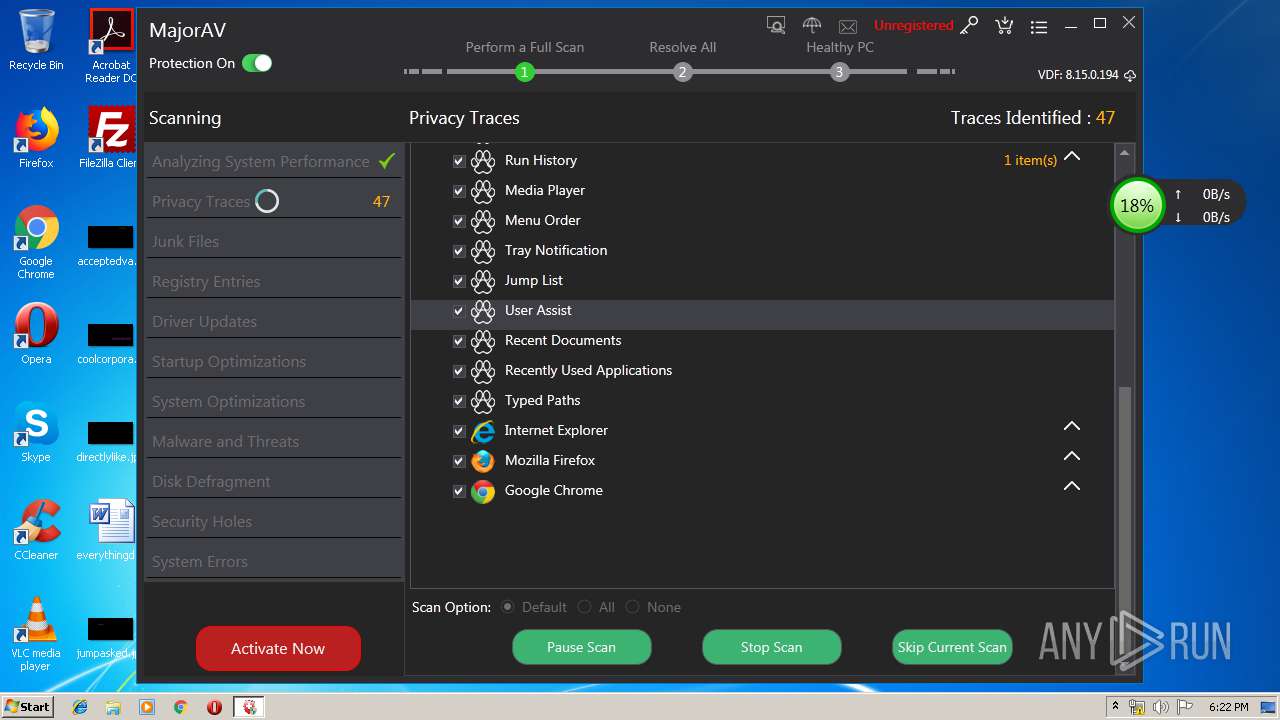
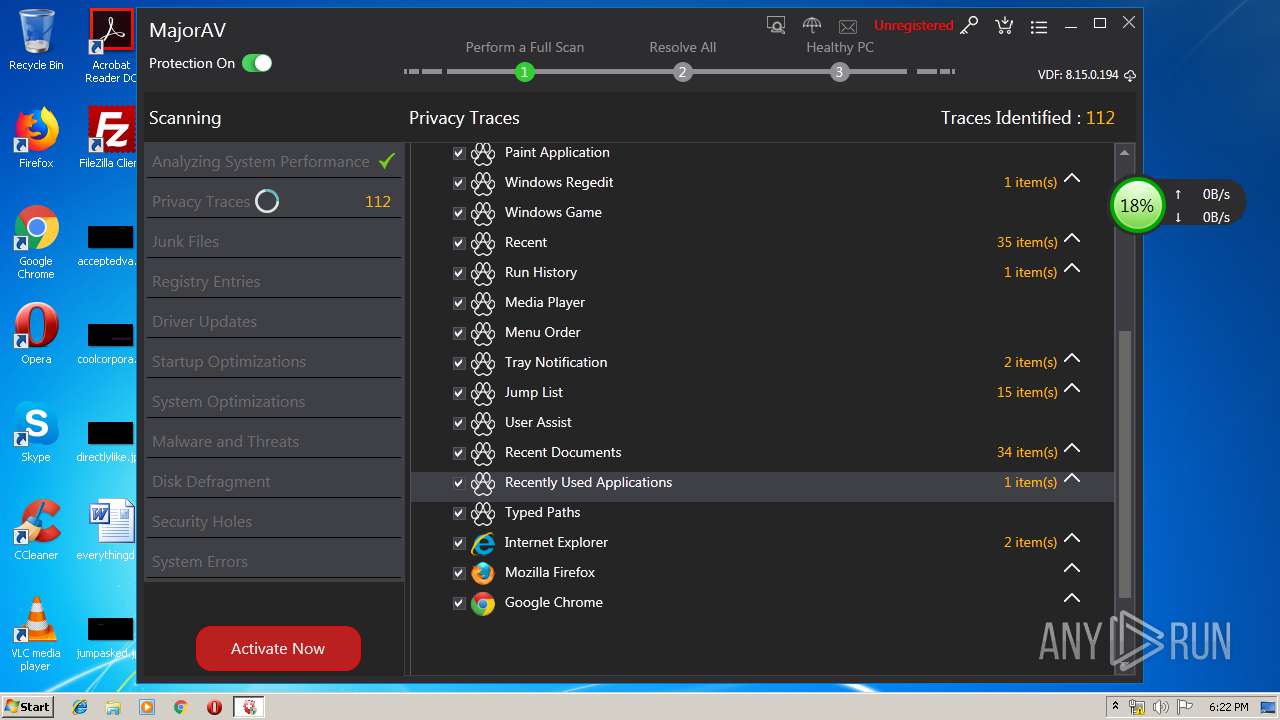
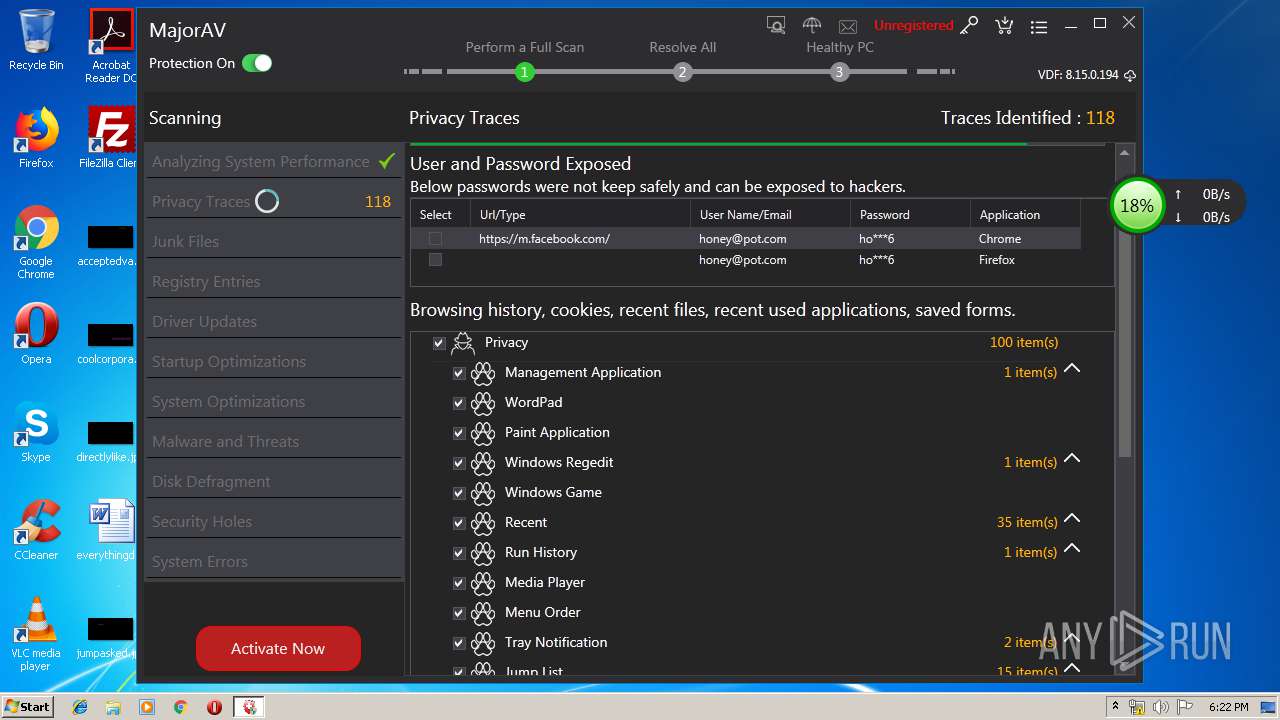
Actions looks like stealing of personal data
- MajorAV.exe (PID: 3224)
- MajorAv.exe (PID: 3024)
Application was dropped or rewritten from another process
- MajorAv.exe (PID: 3168)
- MajorAv.exe (PID: 3024)
- MajorAV.exe (PID: 3224)
- avupdate.exe (PID: 3980)
Changes settings of System certificates
- MajorAV.exe (PID: 3224)
SUSPICIOUS
Executable content was dropped or overwritten
- majorav_win_setup.tmp (PID: 3352)
- majorav_win_setup.exe (PID: 2652)
- majorav_win_setup.exe (PID: 3876)
- avupdate.exe (PID: 3980)
Reads the Windows organization settings
- majorav_win_setup.tmp (PID: 3352)
Reads Windows owner or organization settings
- majorav_win_setup.tmp (PID: 3352)
Creates files in the user directory
- majorav_win_setup.tmp (PID: 3352)
- MajorAv.exe (PID: 3024)
- MajorAV.exe (PID: 3224)
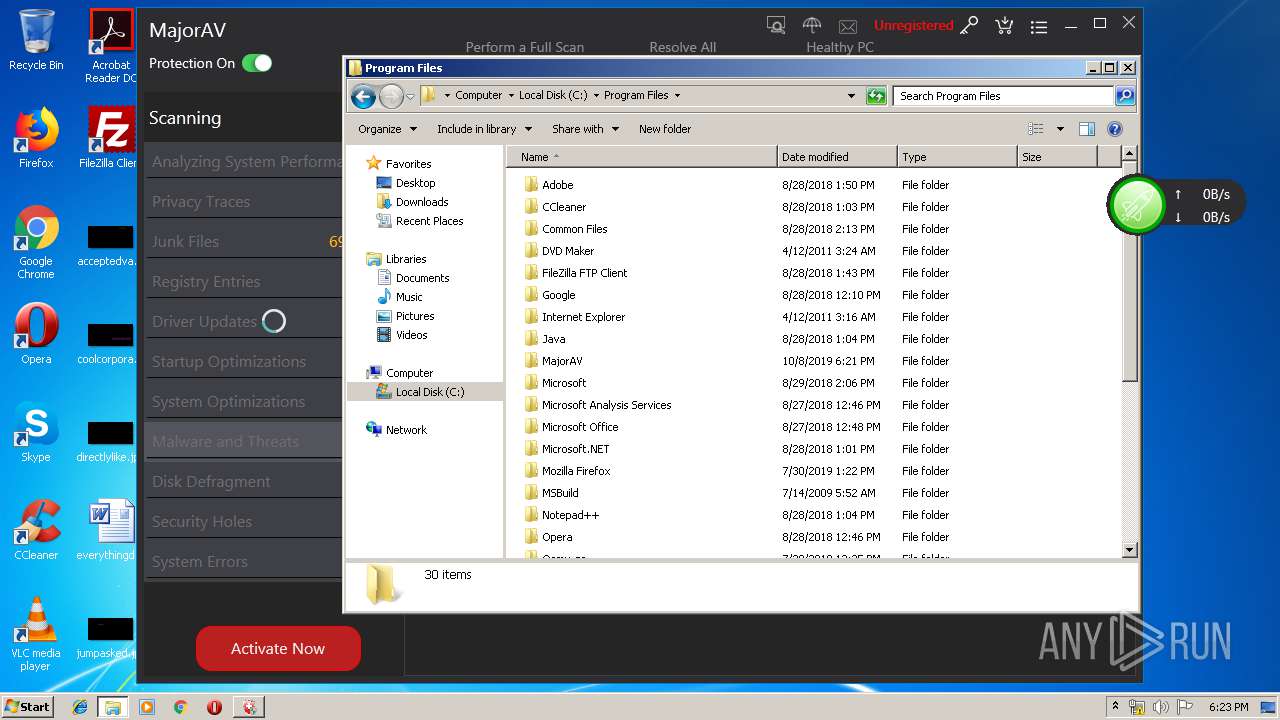
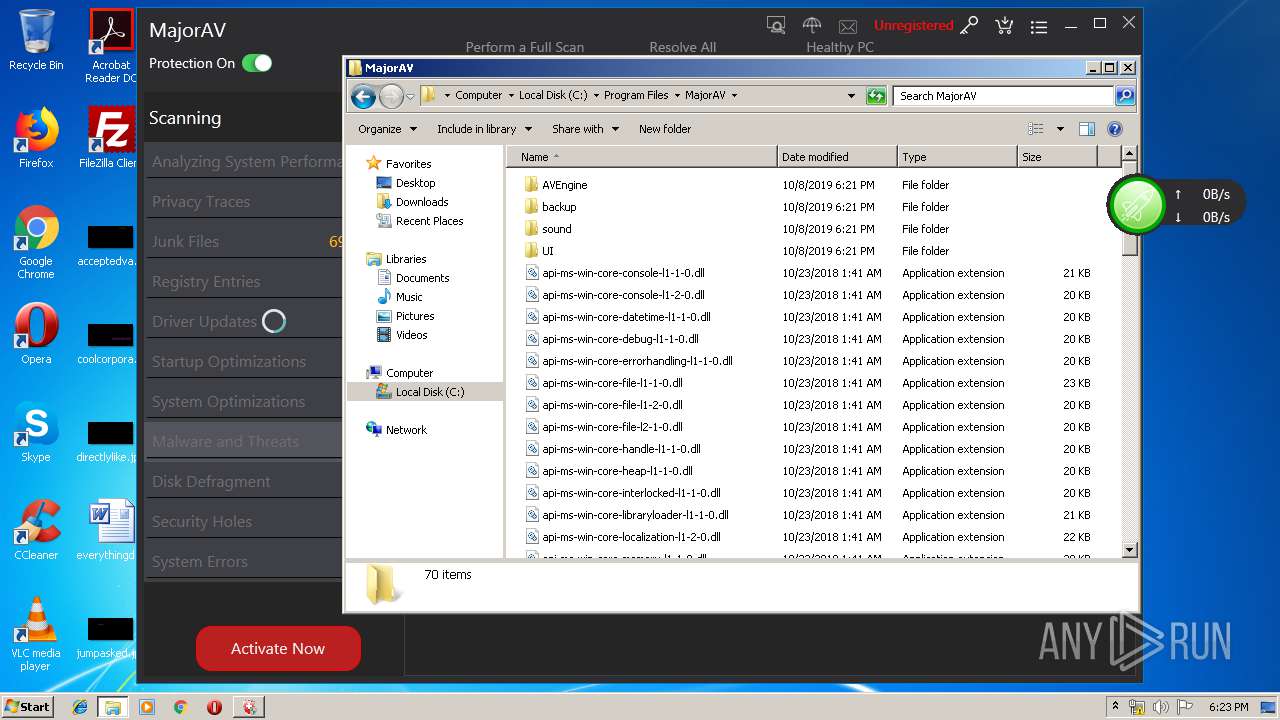
Creates files in the program directory
- avupdate.exe (PID: 3980)
- werfault.exe (PID: 3288)
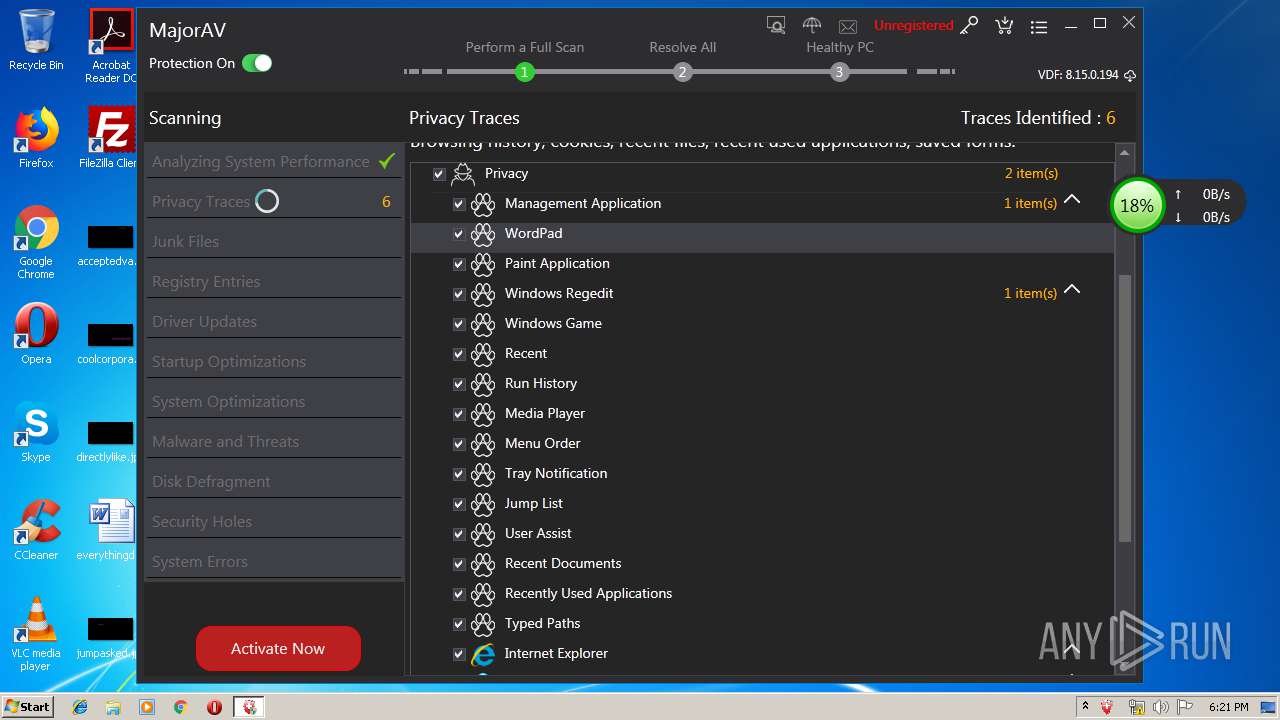
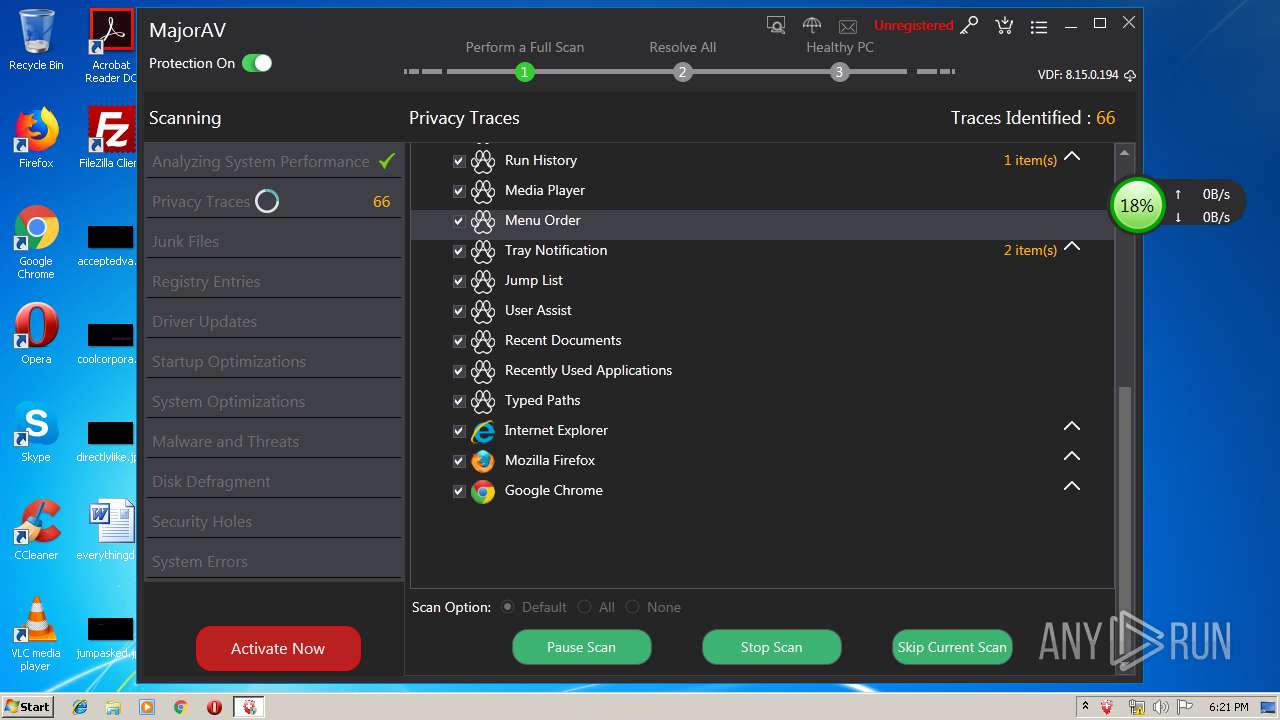
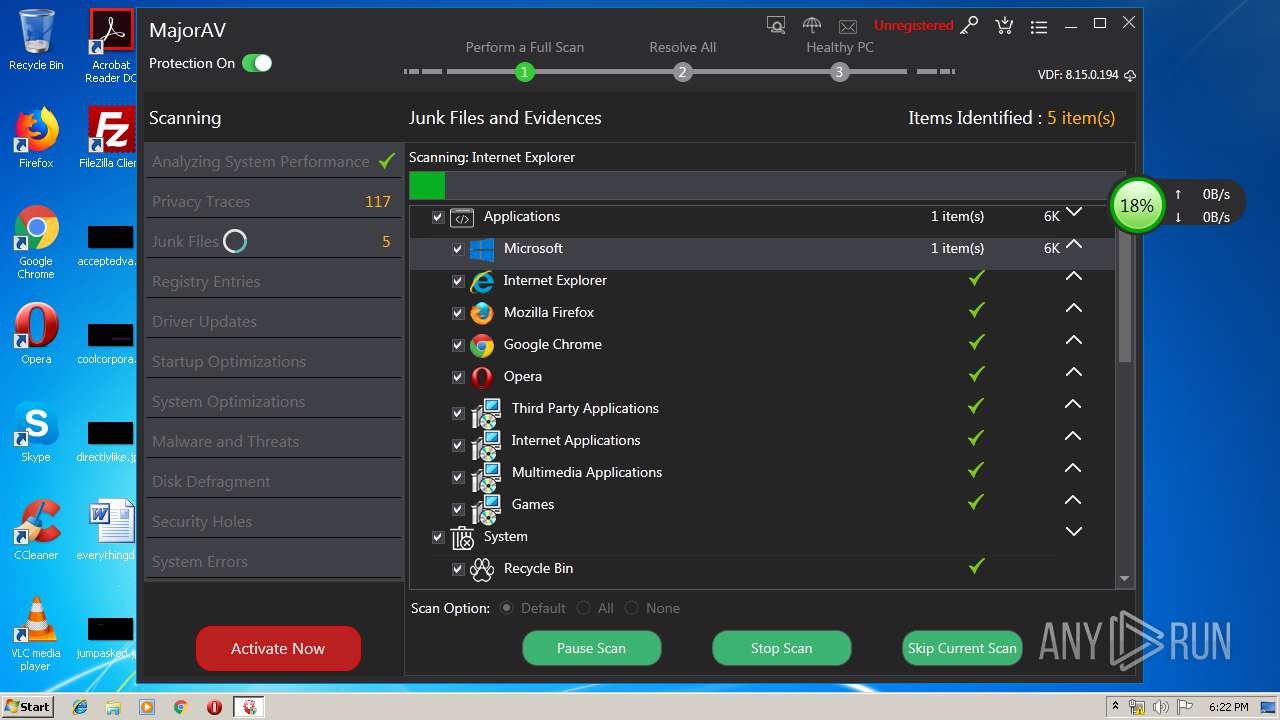
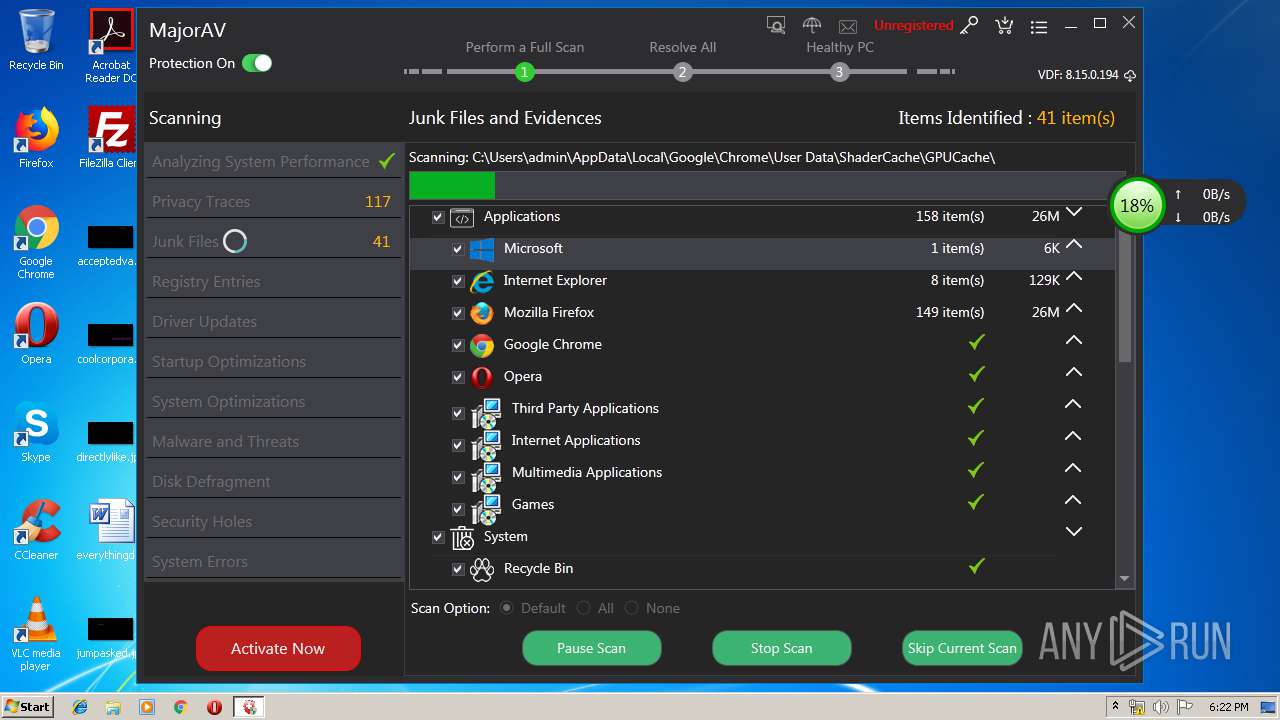
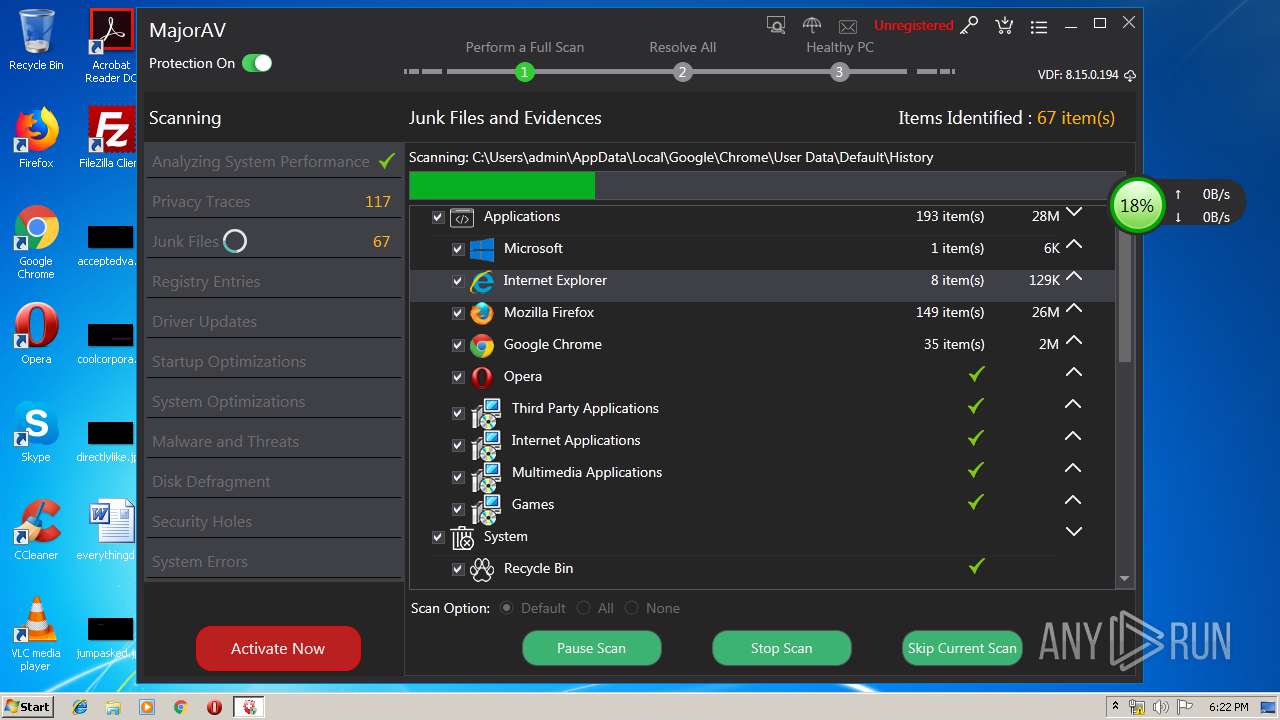
Reads Internet Cache Settings
- MajorAV.exe (PID: 3224)
- MajorAv.exe (PID: 3024)
Adds / modifies Windows certificates
- MajorAV.exe (PID: 3224)
Reads the cookies of Google Chrome
- MajorAV.exe (PID: 3224)
- MajorAv.exe (PID: 3024)
Loads DLL from Mozilla Firefox
- MajorAV.exe (PID: 3224)
- MajorAv.exe (PID: 3024)
Reads the cookies of Mozilla Firefox
- MajorAV.exe (PID: 3224)
- MajorAv.exe (PID: 3024)
INFO
Application was dropped or rewritten from another process
- majorav_win_setup.tmp (PID: 2928)
- majorav_win_setup.tmp (PID: 3352)
Loads dropped or rewritten executable
- majorav_win_setup.tmp (PID: 3352)
Creates a software uninstall entry
- majorav_win_setup.tmp (PID: 3352)
Reads settings of System Certificates
- MajorAV.exe (PID: 3224)
- MajorAv.exe (PID: 3024)
Manual execution by user
- MajorAv.exe (PID: 3168)
- MajorAv.exe (PID: 3024)
- explorer.exe (PID: 2724)
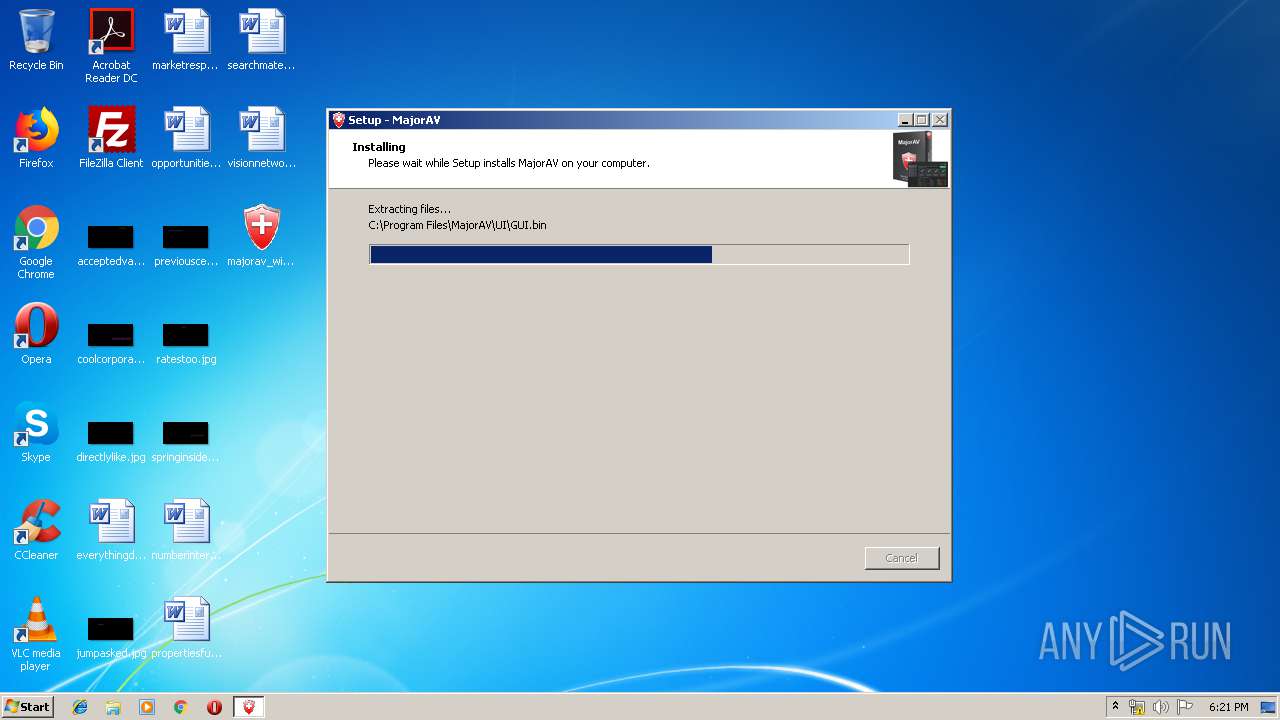
Creates files in the program directory
- majorav_win_setup.tmp (PID: 3352)
Dropped object may contain Bitcoin addresses
- avupdate.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 10:22:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 50176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.5.0 |
| ProductVersionNumber: | 1.0.5.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | MajorAV Software Co., Ltd |
| FileDescription: | MajorAV Setup |
| FileVersion: | 1.0.5 |
| LegalCopyright: | MajorAV Software Co., Ltd |
| OriginalFileName: | |
| ProductName: | MajorAV |
| ProductVersion: | 5.2.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 08:22:11 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | MajorAV Software Co., Ltd |
| FileDescription: | MajorAV Setup |
| FileVersion: | 1.0.5 |
| LegalCopyright: | MajorAV Software Co., Ltd |
| OriginalFileName: | - |
| ProductName: | MajorAV |
| ProductVersion: | 5.2.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 27-Apr-2019 08:22:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A50E0 | 0x000A5200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36825 |
.itext | 0x000A7000 | 0x00001668 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95049 |
.data | 0x000A9000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.02787 |
.bss | 0x000AD000 | 0x0000676C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000B4000 | 0x00000F1C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.79161 |
.didata | 0x000B5000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74582 |
.edata | 0x000B6000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.88107 |
.tls | 0x000B7000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000B8000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.36974 |
.rsrc | 0x000B9000 | 0x0000748C | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.65746 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
4086 | 3.16547 | 864 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.15425 | 156 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.31895 | 884 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.28786 | 920 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000B063C |
__dbk_fcall_wrapper | 2 | 0x0000D3DC |
TMethodImplementationIntercept | 3 | 0x00053ABC |
Total processes
64
Monitored processes
14
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2380 | "C:\Windows\system32\schtasks.exe" /Create /TN "MajorAV Startup" /XML "C:\Users\admin\AppData\Local\Temp\is-CTOPA.tmp\majoravstartup.xml" | C:\Windows\system32\schtasks.exe | — | majorav_win_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2652 | "C:\Users\admin\Desktop\majorav_win_setup.exe" /SPAWNWND=$C0142 /NOTIFYWND=$80144 | C:\Users\admin\Desktop\majorav_win_setup.exe | majorav_win_setup.tmp | ||||||||||||
User: admin Company: MajorAV Software Co., Ltd Integrity Level: HIGH Description: MajorAV Setup Exit code: 0 Version: 1.0.5 Modules
| |||||||||||||||
| 2724 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2928 | "C:\Users\admin\AppData\Local\Temp\is-VTEM0.tmp\majorav_win_setup.tmp" /SL5="$80144,8509910,733696,C:\Users\admin\Desktop\majorav_win_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-VTEM0.tmp\majorav_win_setup.tmp | — | majorav_win_setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\MajorAV\MajorAv.exe" | C:\Program Files\MajorAV\MajorAv.exe | explorer.exe | ||||||||||||
User: admin Company: MajorAV Software co., Ltd Integrity Level: HIGH Description: MajorAV Exit code: 0 Version: 1.2.0 Modules
| |||||||||||||||
| 3124 | "C:\Windows\system32\schtasks.exe" /Create /TN "MajorAV Virus definition Update" /XML "C:\Users\admin\AppData\Local\Temp\is-CTOPA.tmp\majorav_weekly.xml" | C:\Windows\system32\schtasks.exe | — | majorav_win_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3168 | "C:\Program Files\MajorAV\MajorAv.exe" | C:\Program Files\MajorAV\MajorAv.exe | — | explorer.exe | |||||||||||
User: admin Company: MajorAV Software co., Ltd Integrity Level: MEDIUM Description: MajorAV Exit code: 3221226540 Version: 1.2.0 Modules
| |||||||||||||||
| 3224 | "C:\Program Files\MajorAV\MajorAV.exe" | C:\Program Files\MajorAV\MajorAV.exe | majorav_win_setup.tmp | ||||||||||||
User: admin Company: MajorAV Software co., Ltd Integrity Level: HIGH Description: MajorAV Exit code: 3489660927 Version: 1.2.0 Modules
| |||||||||||||||
| 3288 | werfault.exe /h /shared Global\cf59df76bbe24f36b3642ebad3b3b3e8 | C:\Windows\system32\werfault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 2147943623 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 621
Read events
5 308
Write events
302
Delete events
11
Modification events
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 180D0000B82D9790FC7DD501 | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 5FFD0E735ABD870033B3653194277818CFA64313F21CA1003E461EE876306B88 | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\majorav_win_setup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\majorav_win_setup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\majorav_win_setup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\majorav_win_setup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\majorav_win_setup_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\majorav_win_setup_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3352) majorav_win_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\majorav_win_setup_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
80
Suspicious files
54
Text files
164
Unknown types
25
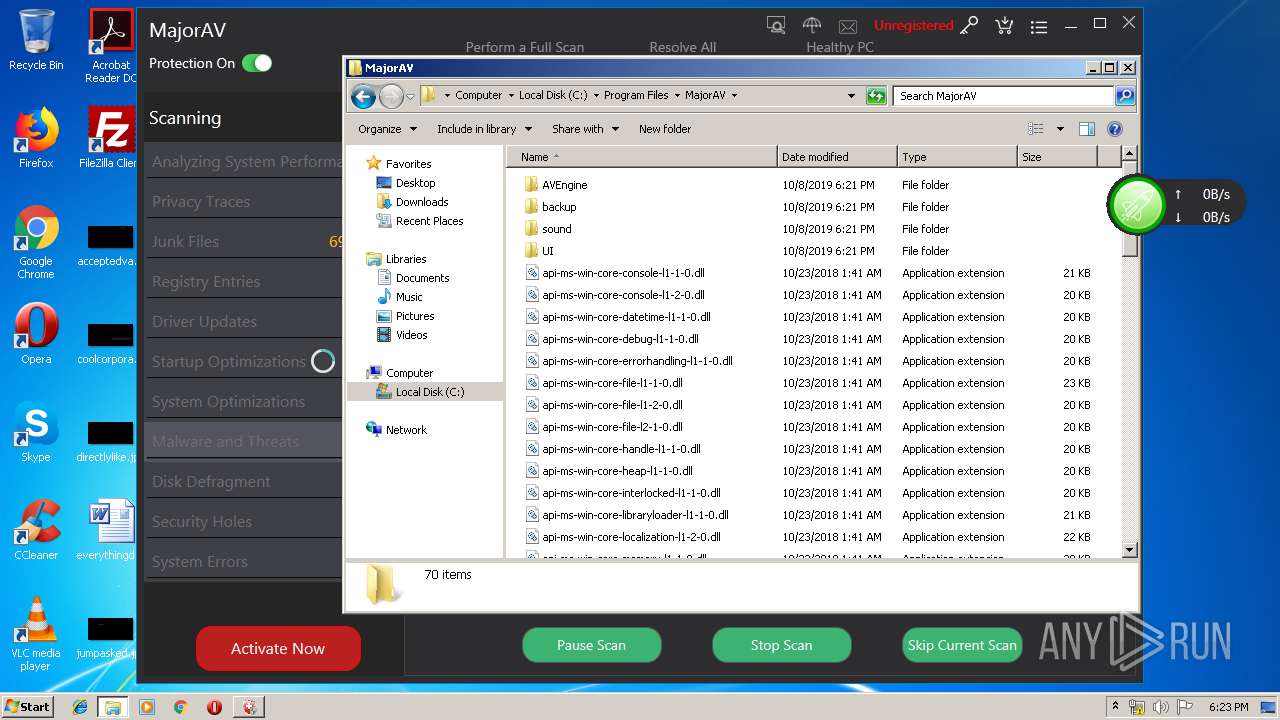
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\is-ILCHA.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\is-7ODSE.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\is-H3LKE.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\is-4G9DL.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\sound\is-UULI0.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\sound\is-M186U.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\sound\is-GQRBQ.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\sound\is-HUGHF.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\sound\is-LODFV.tmp | — | |
MD5:— | SHA256:— | |||
| 3352 | majorav_win_setup.tmp | C:\Program Files\MajorAV\UI\is-PA5JN.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
40
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
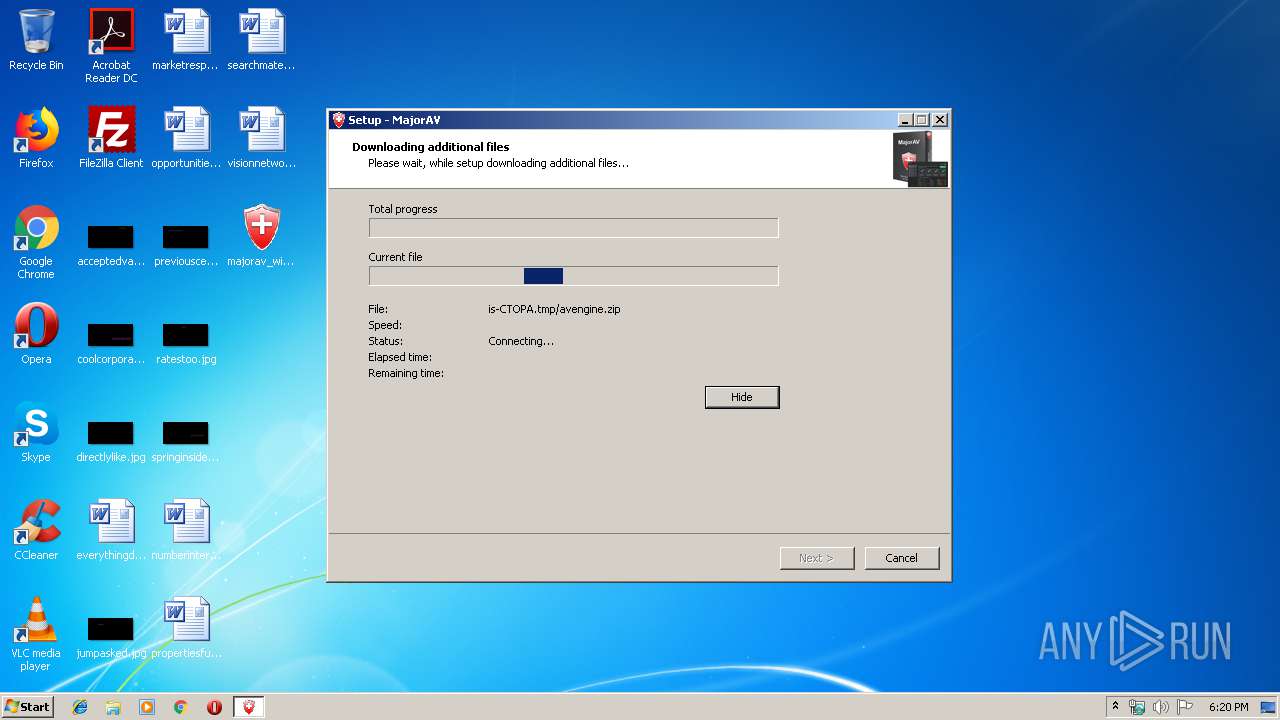
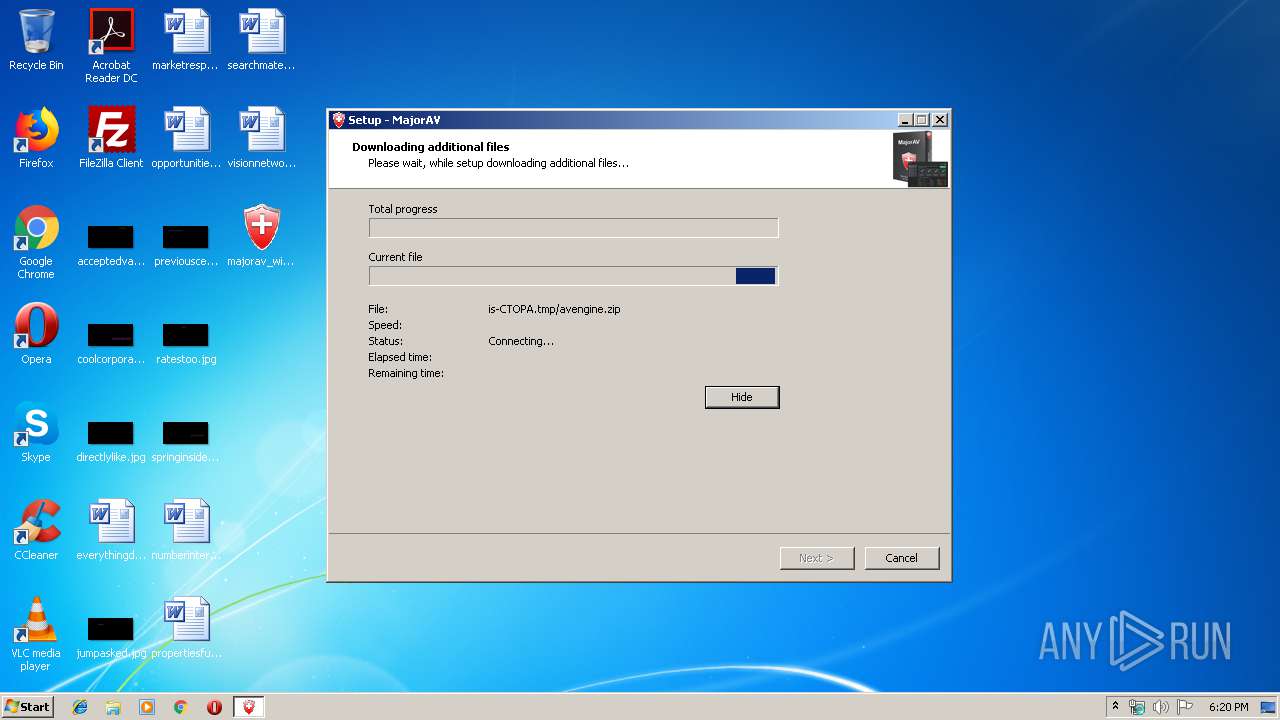
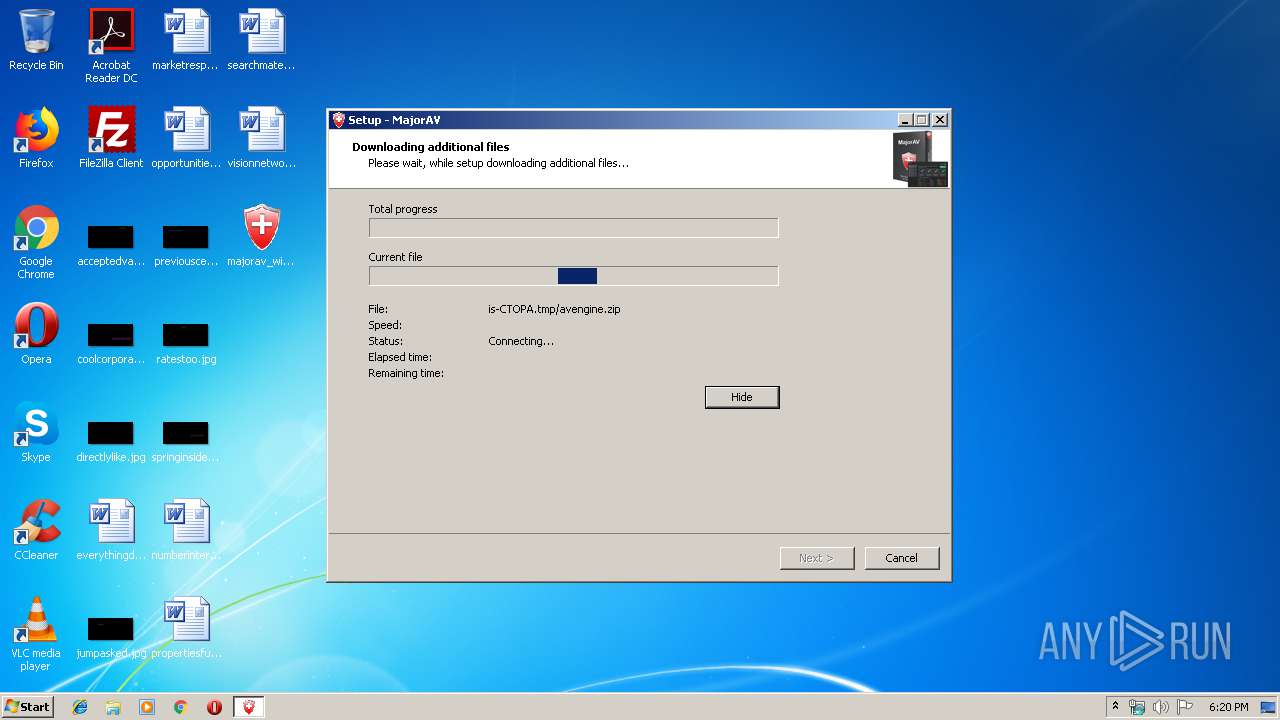
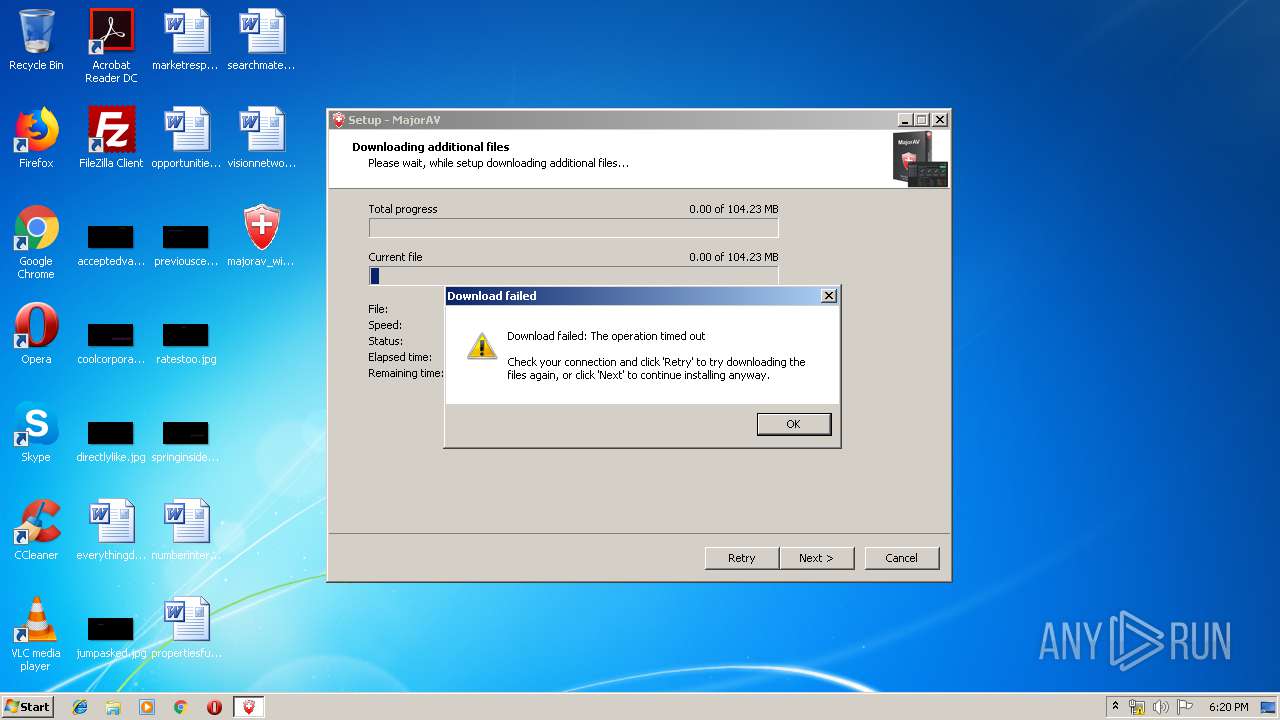
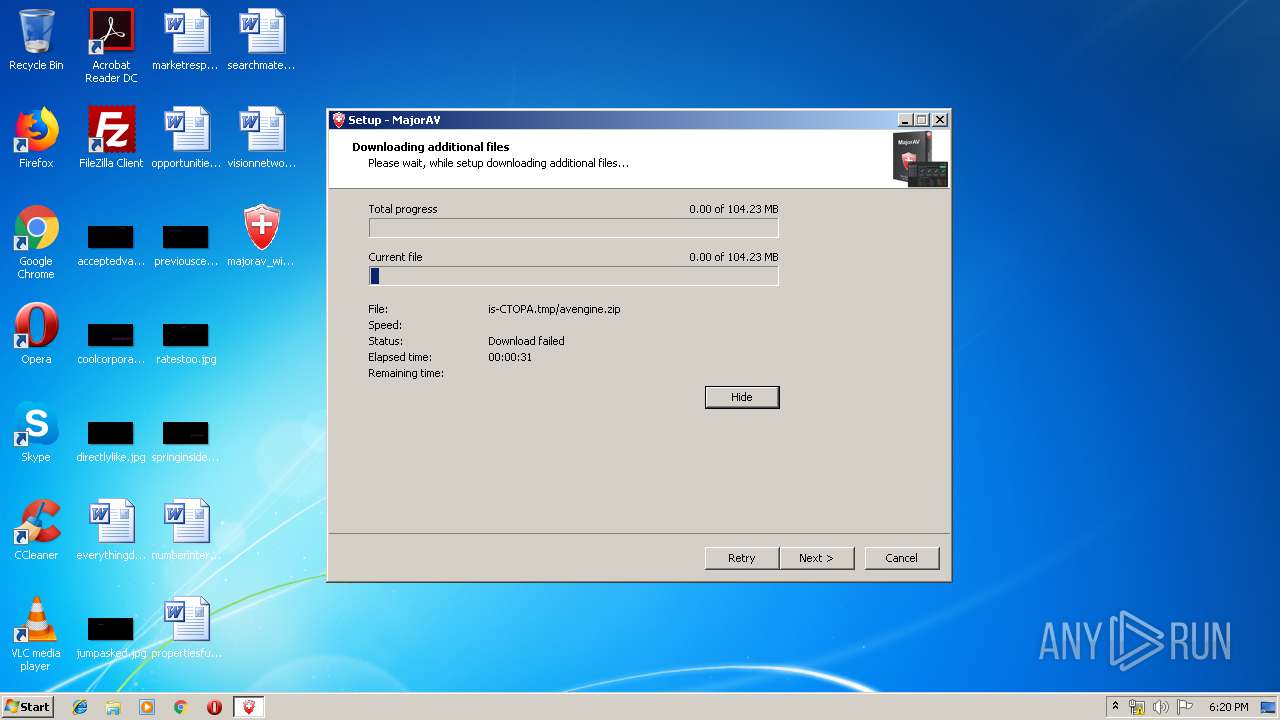
3352 | majorav_win_setup.tmp | GET | — | 198.11.205.6:80 | http://www.MajorAV.com/download/avengine.zip | US | — | — | suspicious |
3352 | majorav_win_setup.tmp | GET | — | 173.192.57.82:80 | http://download.MajorAV.com/download/avengine.zip | US | — | — | suspicious |
3024 | MajorAv.exe | GET | — | 198.11.205.6:80 | http://www.majorav.com/serverapi.php?code=E1E96F71153FE86B&action=special_offer | US | — | — | suspicious |
— | — | HEAD | 200 | 95.101.72.136:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?1910081723 | unknown | — | — | whitelisted |
3352 | majorav_win_setup.tmp | GET | 200 | 198.11.205.6:80 | http://www.majorav.com/pickuid.php | US | text | 9 b | suspicious |
3352 | majorav_win_setup.tmp | POST | — | 172.217.18.110:80 | http://www.google-analytics.com/collect | US | — | — | whitelisted |
3024 | MajorAv.exe | GET | — | 198.11.205.6:80 | http://www.majorav.com/serverapi.php?code=E1E96F71153FE86B&action=special_offer_picture&language=0 | US | — | — | suspicious |
3224 | MajorAV.exe | GET | 200 | 198.11.205.6:80 | http://www.majorav.com/serverapi.php?code=E1E96F71153FE86B&action=special_offer_picture&language=0 | US | text | 8 b | suspicious |
3024 | MajorAv.exe | POST | — | 198.11.205.6:80 | http://s1.majorav.com/ | US | — | — | suspicious |
3024 | MajorAv.exe | GET | 200 | 198.11.205.6:80 | http://www.majorav.com/serverapi.php?code=E1E96F71153FE86B&action=special_offer_picture&language=0 | US | text | 8 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3352 | majorav_win_setup.tmp | 198.11.205.6:80 | www.majorav.com | SoftLayer Technologies Inc. | US | suspicious |
3352 | majorav_win_setup.tmp | 172.217.18.110:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3352 | majorav_win_setup.tmp | 173.192.57.82:80 | download.majorav.com | SoftLayer Technologies Inc. | US | suspicious |
3224 | MajorAV.exe | 198.11.205.6:80 | www.majorav.com | SoftLayer Technologies Inc. | US | suspicious |
3224 | MajorAV.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3980 | avupdate.exe | 2.18.234.217:443 | oem.avira-update.com | Akamai International B.V. | — | whitelisted |
— | — | 151.101.2.133:80 | crl.globalsign.net | Fastly | US | malicious |
— | — | 216.58.205.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3024 | MajorAv.exe | 198.11.205.6:80 | www.majorav.com | SoftLayer Technologies Inc. | US | suspicious |
3024 | MajorAv.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.majorav.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
download.majorav.com |
| suspicious |
oem.avira-update.com |
| suspicious |
crl.globalsign.net |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
s1.majorav.com |
| suspicious |
s2.majorav.com |
| suspicious |
download.windowsupdate.com |
| whitelisted |
www.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3352 | majorav_win_setup.tmp | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
3352 | majorav_win_setup.tmp | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |