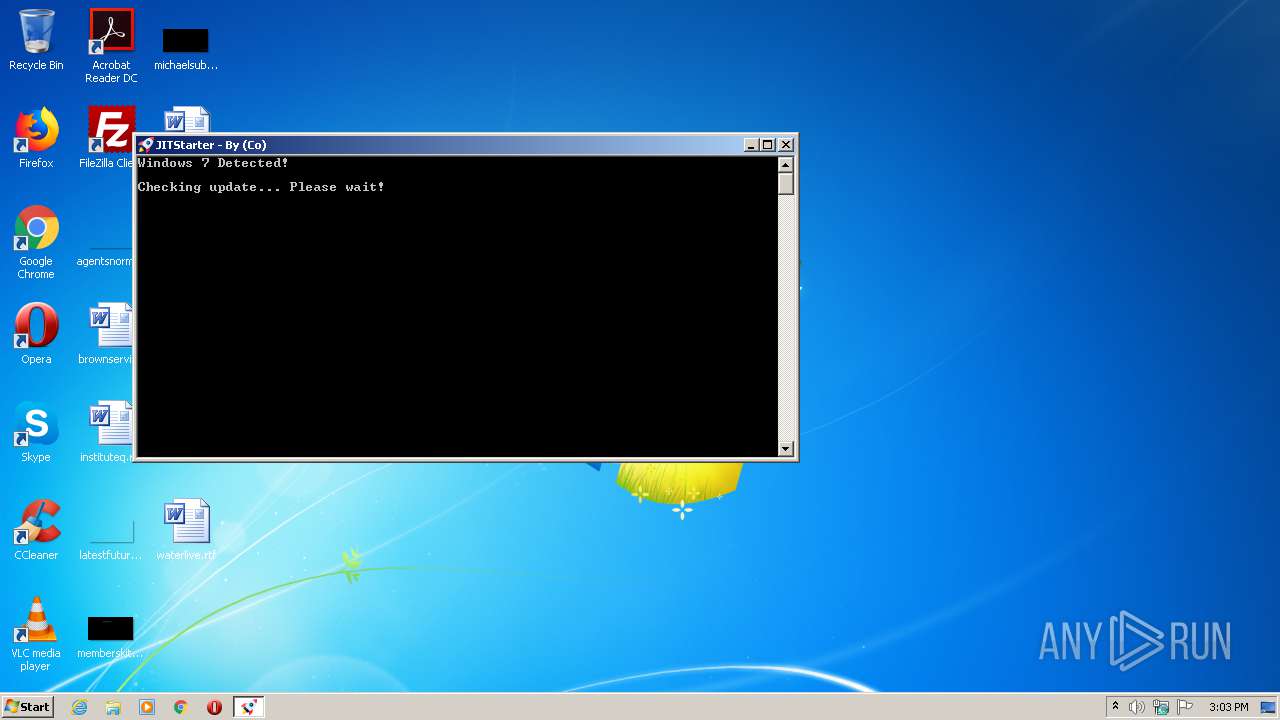
| File name: | JITStarter.exe |
| Full analysis: | https://app.any.run/tasks/0ea3f4e6-e875-47b7-b896-8a23f1a6b44f |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2021, 15:02:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0717AF0D8A446FC1B1BF30C9247BFD53 |
| SHA1: | A88242272CA2F21AE35C1A0EC30B30970C0795EE |
| SHA256: | C24DC0813D9A745CD3144365254F73D9B73214C781AAB8DC0FFCB9C88EBFA7B7 |
| SSDEEP: | 3072:dWnS6Id1qMGoN+OCDvuBLA6hWWMext5h4mecLxdwcLmqJOM333GnVW:dWn6dBG+DKah5/zdwQv |
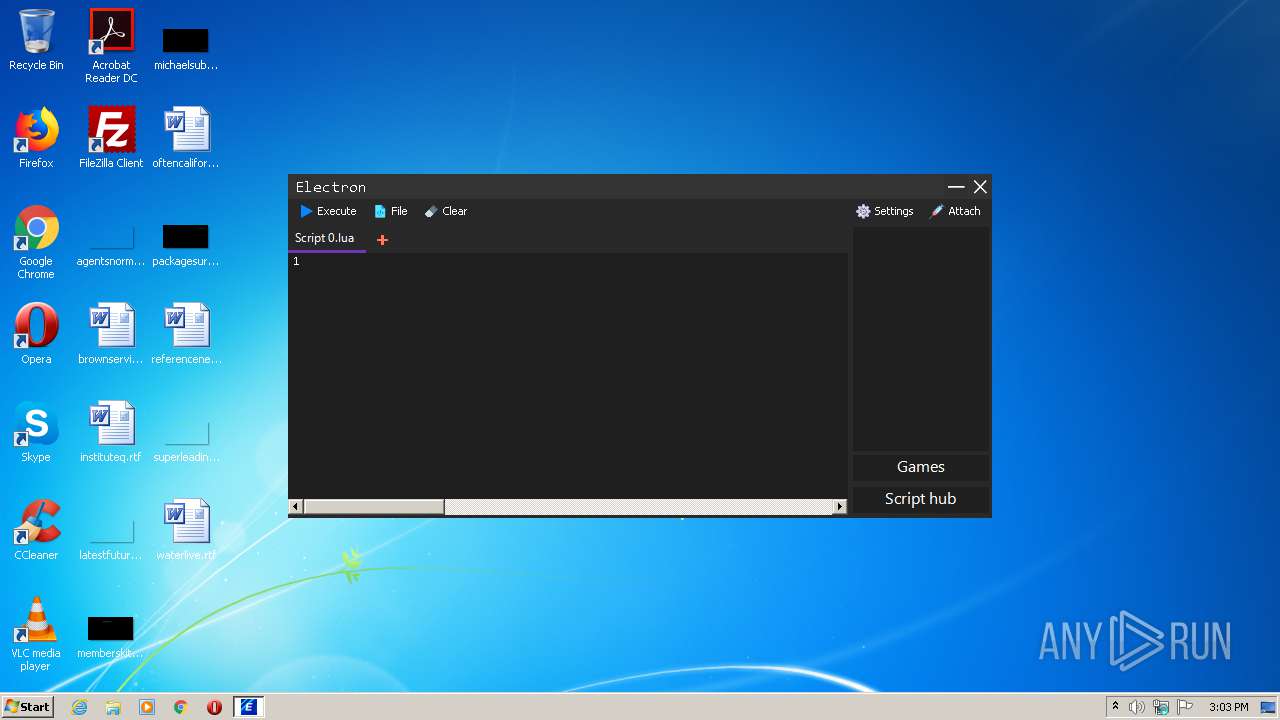
MALICIOUS
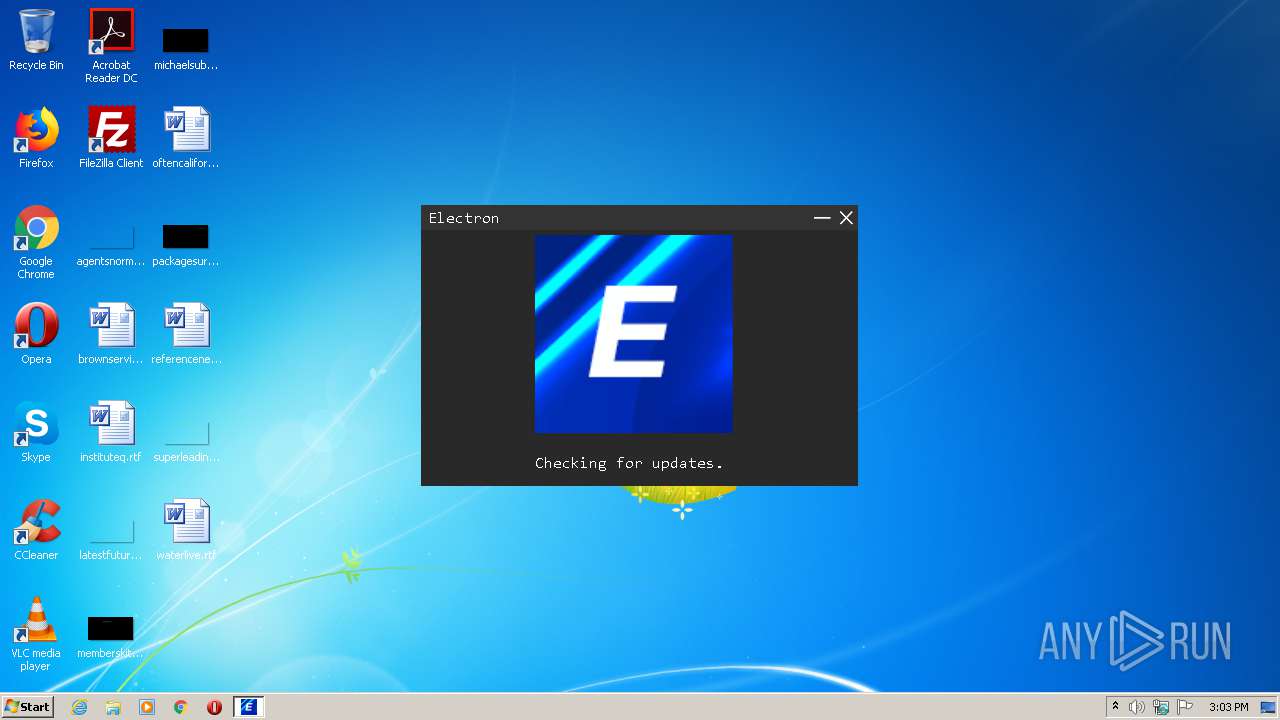
Application was dropped or rewritten from another process
- Electron.exe (PID: 2364)
Loads dropped or rewritten executable
- Electron.exe (PID: 2364)
SUSPICIOUS
Executable content was dropped or overwritten
- JITStarter.exe (PID: 3880)
- Electron.exe (PID: 2364)
Drops a file with too old compile date
- JITStarter.exe (PID: 3880)
Drops a file with a compile date too recent
- Electron.exe (PID: 2364)
Drops a file that was compiled in debug mode
- JITStarter.exe (PID: 3880)
- Electron.exe (PID: 2364)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2054:09:13 22:50:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 147456 |
| InitializedDataSize: | 105472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25f5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Electron |
| FileDescription: | JITStarter |
| FileVersion: | 1.0.0.0 |
| InternalName: | JITStarter.exe |
| LegalCopyright: | Copyright Electron © 2020 |
| LegalTrademarks: | - |
| OriginalFileName: | JITStarter.exe |
| ProductName: | JITStarter |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 08-Aug-1918 14:21:49 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | Electron |
| FileDescription: | JITStarter |
| FileVersion: | 1.0.0.0 |
| InternalName: | JITStarter.exe |
| LegalCopyright: | Copyright Electron © 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | JITStarter.exe |
| ProductName: | JITStarter |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 08-Aug-1918 14:21:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00023F64 | 0x00024000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96453 |
.rsrc | 0x00026000 | 0x00019898 | 0x00019A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.34446 |
.reloc | 0x00040000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.10648 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.12391 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.42498 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.16911 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.66616 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.79908 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
39
Monitored processes
2
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
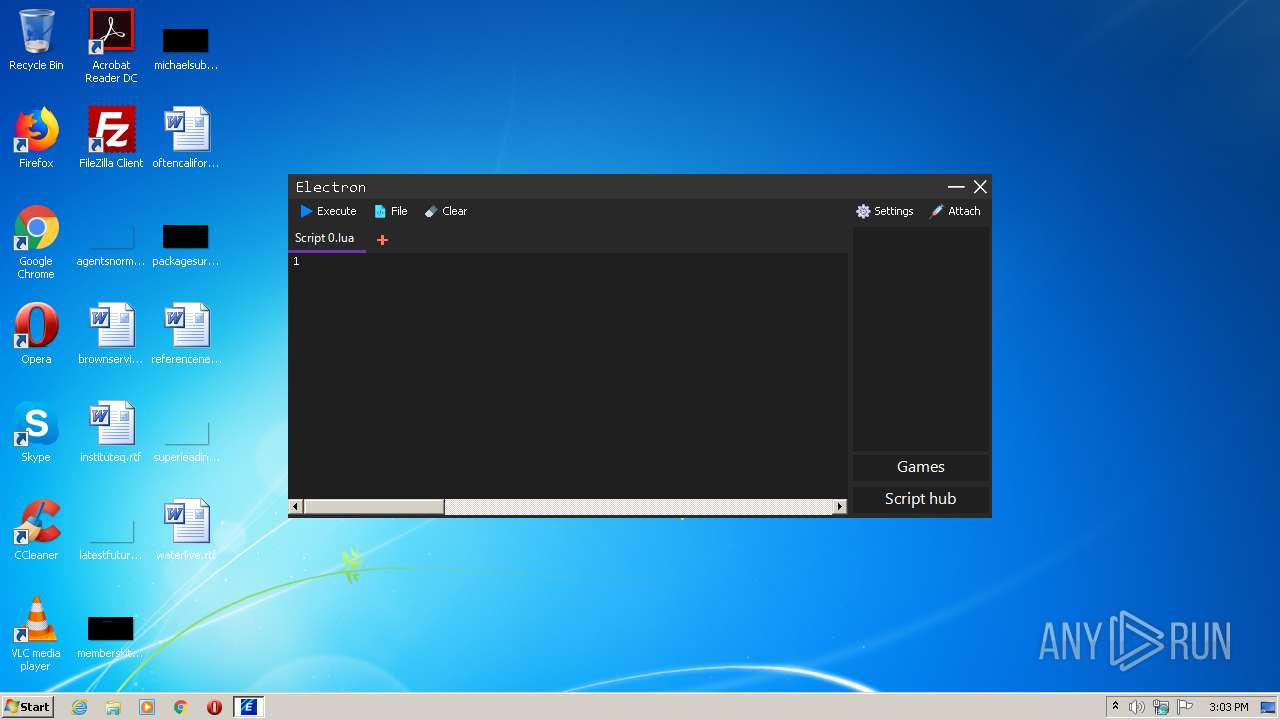
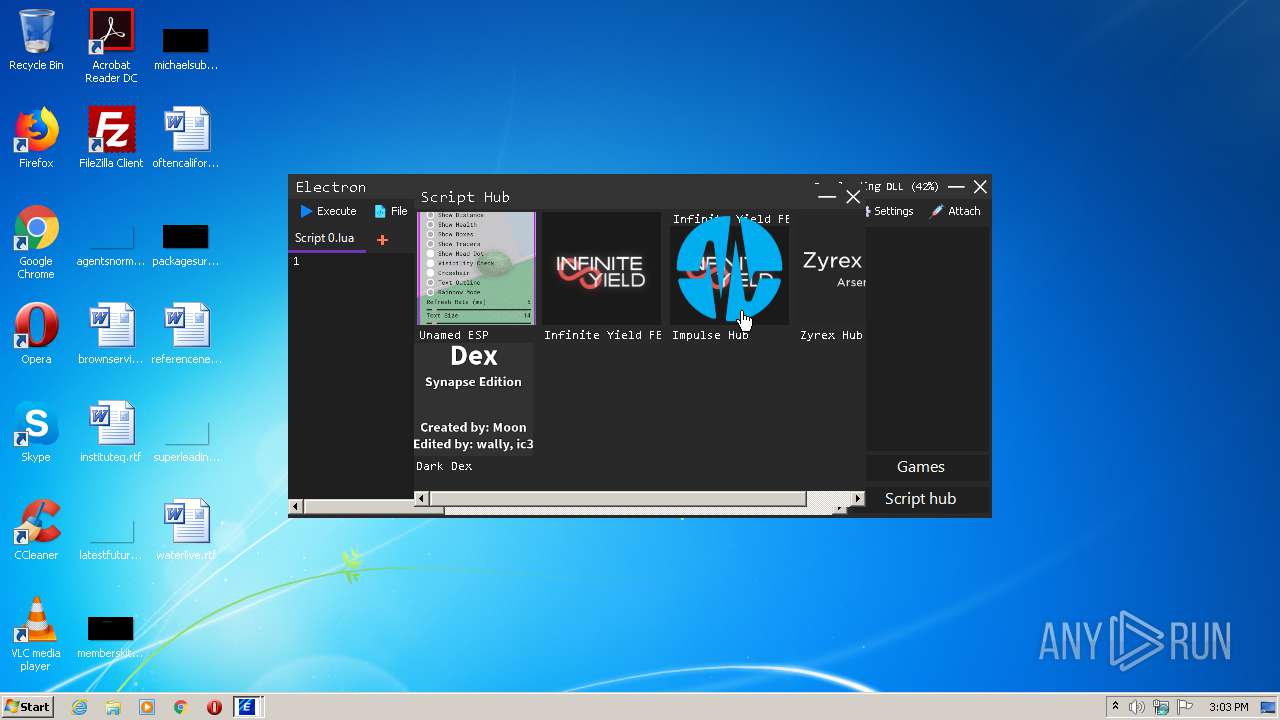
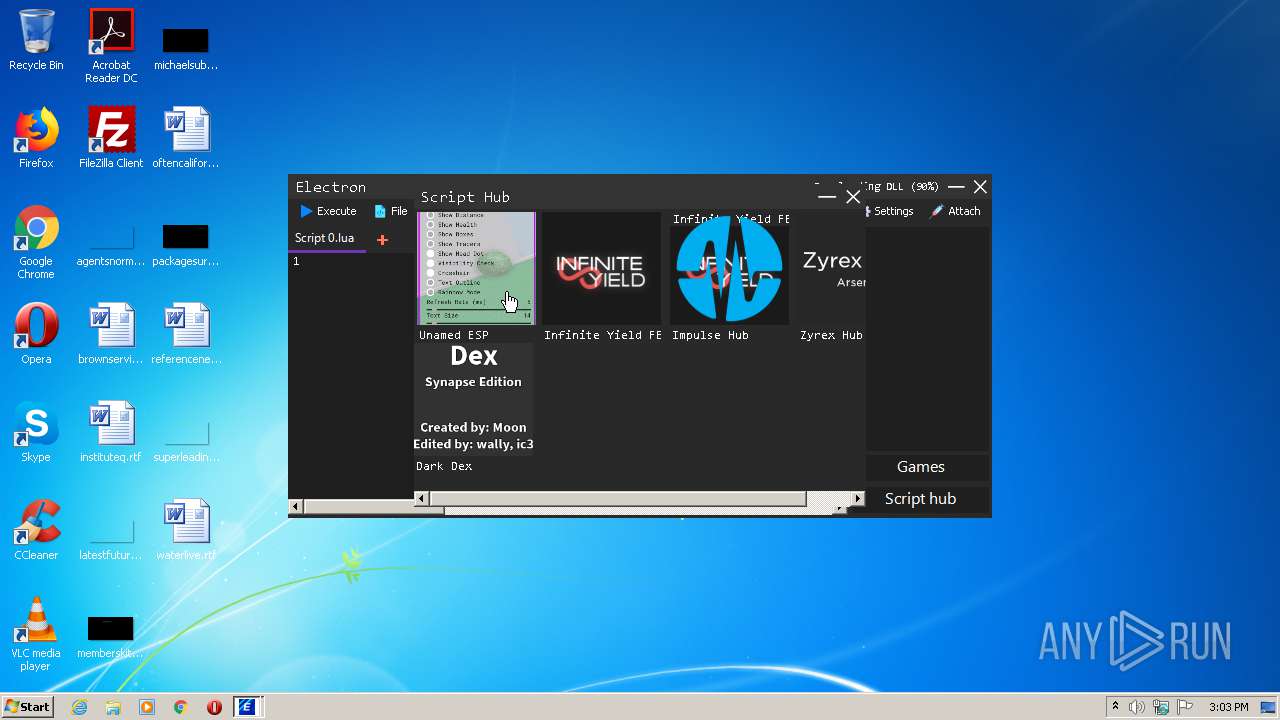
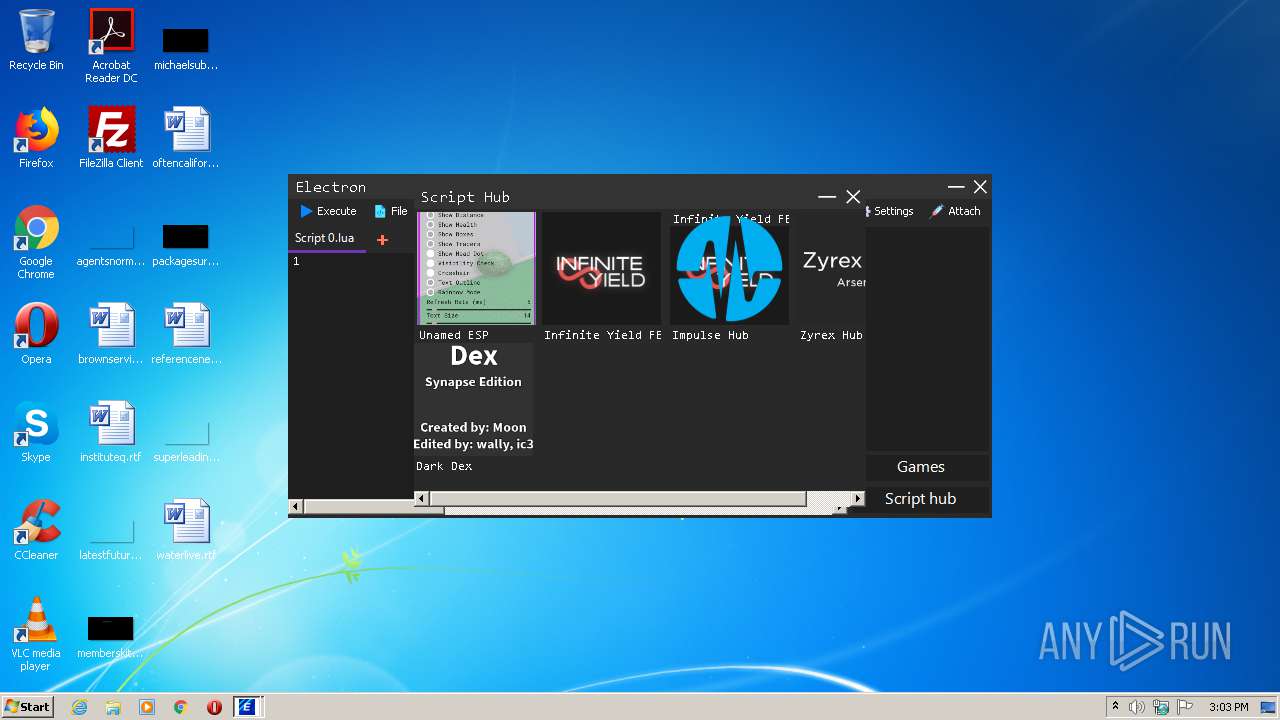
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | "C:\Users\admin\AppData\Local\Temp\Electron.exe" | C:\Users\admin\AppData\Local\Temp\Electron.exe | JITStarter.exe | ||||||||||||
User: admin Company: Electron Integrity Level: MEDIUM Description: ElectronUI Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\AppData\Local\Temp\JITStarter.exe" | C:\Users\admin\AppData\Local\Temp\JITStarter.exe | explorer.exe | ||||||||||||
User: admin Company: Electron Integrity Level: MEDIUM Description: JITStarter Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
510
Read events
457
Write events
53
Delete events
0
Modification events
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3880) JITStarter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\JITStarter_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
4
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | JITStarter.exe | C:\Users\admin\AppData\Local\Temp\temp | — | |
MD5:— | SHA256:— | |||
| 3880 | JITStarter.exe | C:\Users\admin\AppData\Local\Temp\bin\uiversion | text | |
MD5:— | SHA256:— | |||
| 2364 | Electron.exe | C:\Users\admin\AppData\Local\Temp\ElectronDLL.dll | executable | |
MD5:— | SHA256:— | |||
| 3880 | JITStarter.exe | C:\Users\admin\AppData\Local\Temp\Electron.exe | executable | |
MD5:— | SHA256:— | |||
| 2364 | Electron.exe | C:\Users\admin\AppData\Local\Temp\bin\Games.json | text | |
MD5:2D7769B2B603FBF02FC99365165DE3F8 | SHA256:4B4D6E611F85773E79D04F745780F62F021864123D00629474BF09459D3B5B3C | |||
| 2364 | Electron.exe | C:\Users\admin\AppData\Local\Temp\fe18e516-f12f-4073-bf13-52a839118bfb\GunaDotNetRT.dll | executable | |
MD5:9AF5EB006BB0BAB7F226272D82C896C7 | SHA256:77DC05A6BDA90757F66552EE3F469B09F1E00732B4EDCA0F542872FB591ED9DB | |||
| 2364 | Electron.exe | C:\Users\admin\AppData\Local\Temp\bin\Icons\Prison Life.jpg | image | |
MD5:36342F6D461E25A93C951CD50F3BBE2A | SHA256:0F959726CEAF961575ED2146E9F1037FB90A5E2D634DF5FD66CDDF281991C8BE | |||
| 2364 | Electron.exe | C:\Users\admin\AppData\Local\Temp\bin\version | binary | |
MD5:CFCD208495D565EF66E7DFF9F98764DA | SHA256:5FECEB66FFC86F38D952786C6D696C79C2DBC239DD4E91B46729D73A27FB57E9 | |||
| 3880 | JITStarter.exe | C:\Users\admin\AppData\Local\Temp\README_IMPORTANT.txt | text | |
MD5:2E854269E69DFCEDF8D8990DBC596761 | SHA256:6BC6E7C3A6DD8C1C7DD420AE902526C6BB91D2B83D40A2191686972E8A255C96 | |||
| 2364 | Electron.exe | C:\Users\admin\AppData\Local\Temp\ScintillaNET\3.6.3\x86\SciLexer.dll | executable | |
MD5:2FF7ACFA80647EE46CC3C0E446327108 | SHA256:08F0CBBC5162F236C37166772BE2C9B8FFD465D32DF17EA9D45626C4ED2C911D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
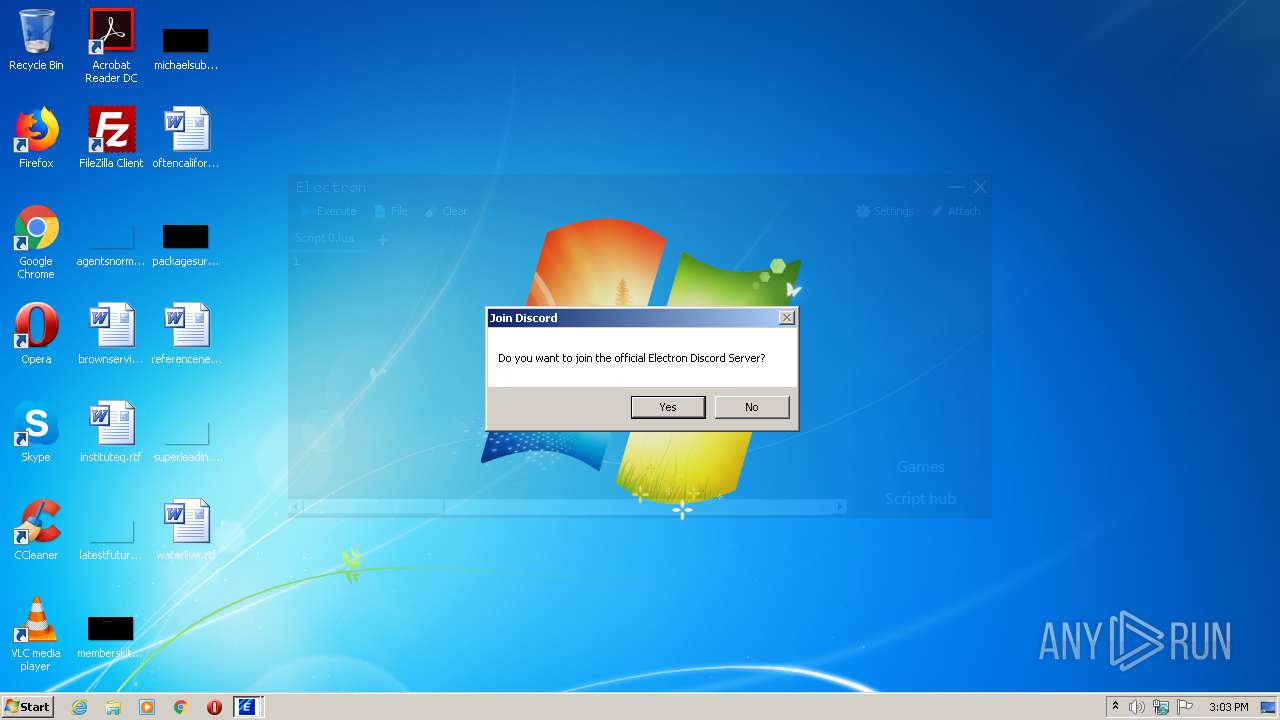
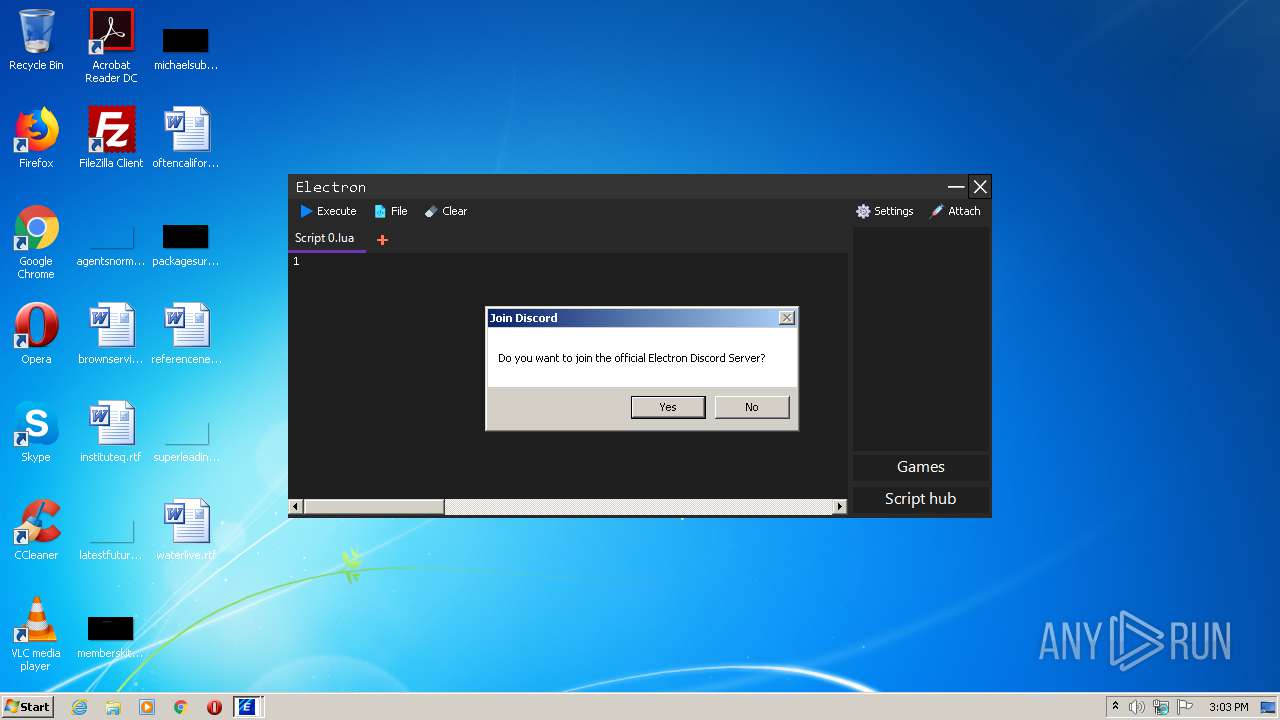
3880 | JITStarter.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2364 | Electron.exe | 162.159.130.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
2364 | Electron.exe | 172.67.176.122:443 | ryos.best | — | US | malicious |
2364 | Electron.exe | 151.101.112.193:443 | i.imgur.com | Fastly | US | malicious |
3880 | JITStarter.exe | 172.67.176.122:443 | ryos.best | — | US | malicious |
2364 | Electron.exe | 185.199.108.133:443 | raw.githubusercontent.com | GitHub, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ryos.best |
| unknown |
cdn.discordapp.com |
| shared |
raw.githubusercontent.com |
| shared |
i.imgur.com |
| malicious |