| File name: | http://cloudresemblao.top/kuhl.exe |
| Full analysis: | https://app.any.run/tasks/b702fcd7-e6fc-4a06-9353-0e8687aac379 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 18, 2019, 00:30:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9D68B5DBC07FC4FA6B4049F19F9A42D6 |
| SHA1: | F7AB50A0AC332B34A17A475B13CDFFD745B71338 |
| SHA256: | C24D86592C3FB9FA26C9C55448DD71083FD59F89E44697A23947D446A1FE04E7 |
| SSDEEP: | 3072:ISWuKNLYhTMJC5GPq7bjK5yrt5BWZiRGVrCMWkCvt:I8kLYhQPSvKoRnWCjQC |
MALICIOUS
GandCrab keys found
- kuhl.exe (PID: 3104)
Writes file to Word startup folder
- kuhl.exe (PID: 3104)
Actions looks like stealing of personal data
- kuhl.exe (PID: 3104)
Dropped file may contain instructions of ransomware
- kuhl.exe (PID: 3104)
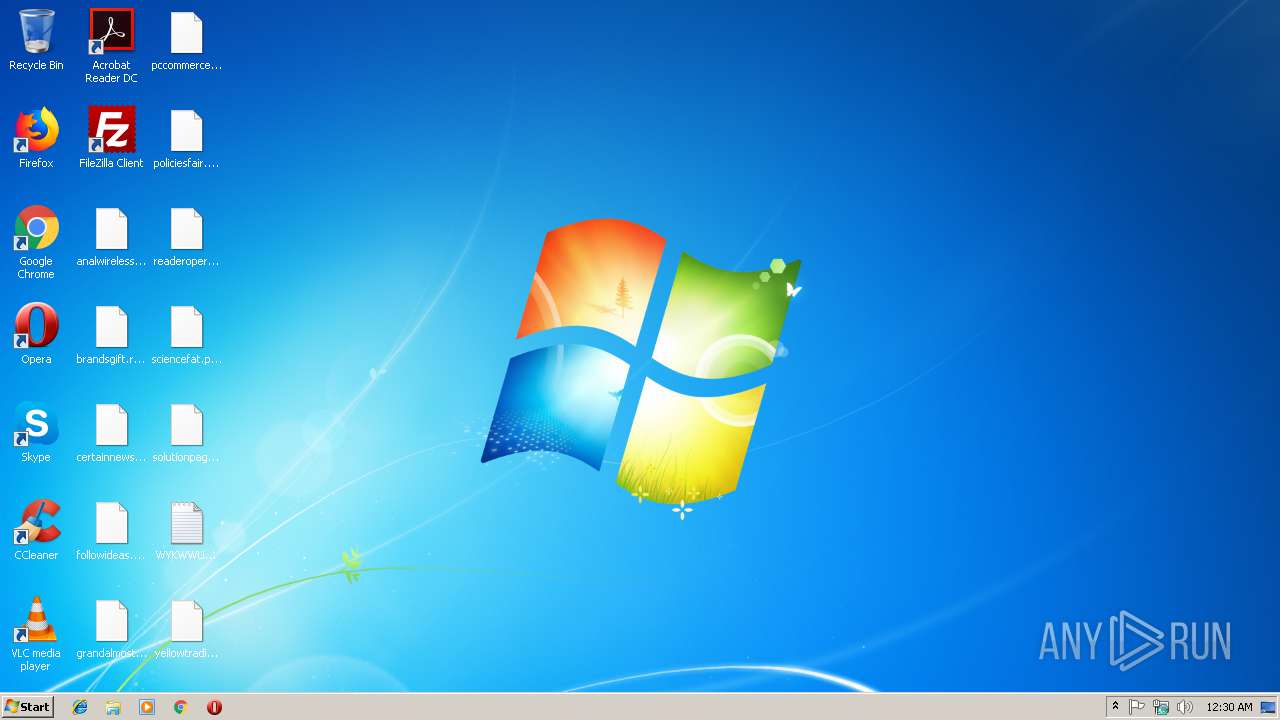
Renames files like Ransomware
- kuhl.exe (PID: 3104)
Deletes shadow copies
- kuhl.exe (PID: 3104)
Changes settings of System certificates
- kuhl.exe (PID: 3104)
SUSPICIOUS
Creates files in the program directory
- kuhl.exe (PID: 3104)
Reads the cookies of Mozilla Firefox
- kuhl.exe (PID: 3104)
Adds / modifies Windows certificates
- kuhl.exe (PID: 3104)
Creates files like Ransomware instruction
- kuhl.exe (PID: 3104)
Creates files in the user directory
- kuhl.exe (PID: 3104)
INFO
Dropped object may contain TOR URL's
- kuhl.exe (PID: 3104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:10:24 03:01:27+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 65536 |
| InitializedDataSize: | 172544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5072 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.45.8.4 |
| ProductVersionNumber: | 7.32.568.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 3.5.10.32 |
| ProductVersion: | 3.5.10.32 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Oct-2017 01:01:27 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Oct-2017 01:01:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000FEBB | 0x00010000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53949 |
.rdata | 0x00011000 | 0x0000410C | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16622 |
.data | 0x00016000 | 0x0001C0DC | 0x0001A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.87212 |
.rsrc | 0x00033000 | 0x00008F90 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.59547 |
.reloc | 0x0003C000 | 0x00001AD0 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.66383 |
Imports
KERNEL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
123299 | 0x00000000 |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
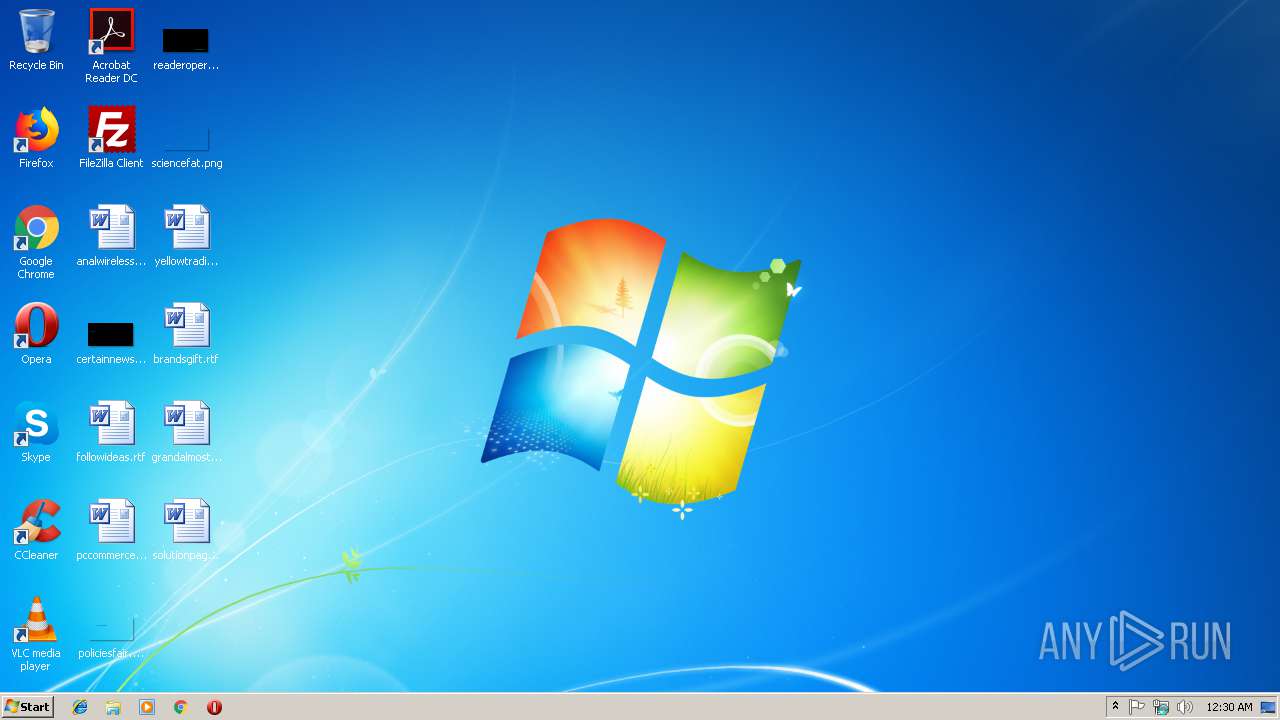
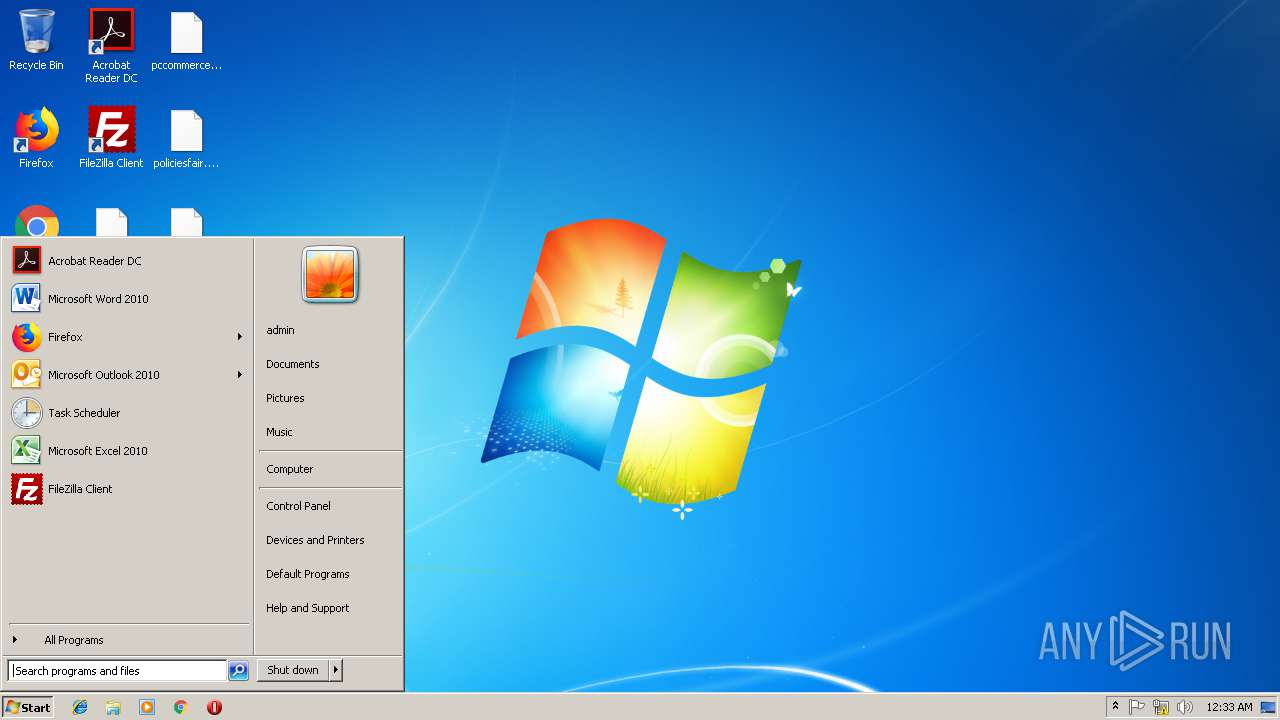
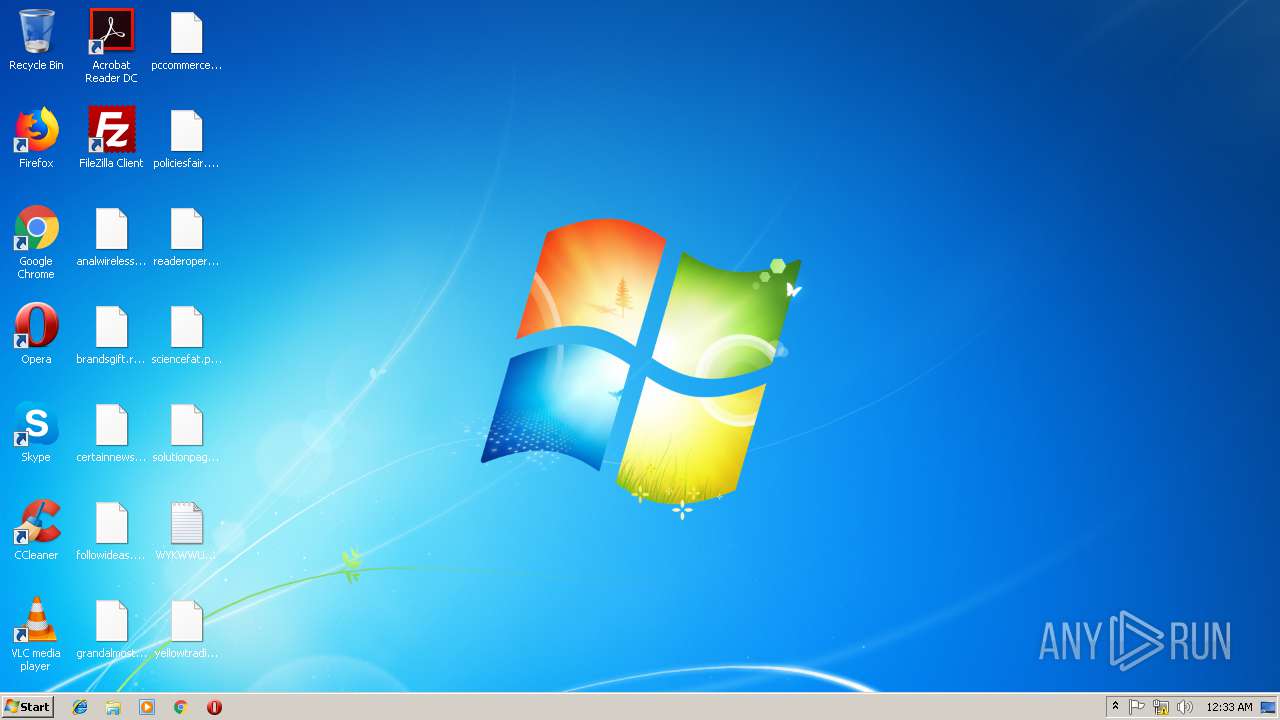
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2448 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | kuhl.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\AppData\Local\Temp\kuhl.exe" | C:\Users\admin\AppData\Local\Temp\kuhl.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
136
Read events
98
Write events
38
Delete events
0
Modification events
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E00770079006B0077007700750078000000 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A40000525341310008000001000100FDB99D167836A15451A2FD4A92A8B34A27B1864033ECDF9125EC5BE449ED47E4E8FC26EDD2DEFDD8E37BCE69C2544F0F09DE05948999175ACB3D0584FE485104C1526BC787DC5DDB584533AE9794DA348FEED3A9D4F6D067E4B36BD85FBD4E688B195D3A3634716DD98B1A9DC505FEA2008F6CB614EB2E12EEAFA383765D541C99662B087837C326B6D0F804E1DF4C5C48CAD8F24897340B20F5DA47D574198574F096102D5481CBC098A4373D5DC07AE421B58D96CD2F29AB55071473851F5EAC980FB2D41DE2AAE361F56457A8D01AEC96CA5C0F36DD6B8CFAE447CDEB2235286FE3F9B523A48EDE19C1B623B56FB6AA14B10E8B9F84FE5D1786A02D0A88B8 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 940400009A7E8151BED0C1DE3C899F6147EFCA634269BCAA4476570AB5D52C612FEEBAC16DBEAD5798FE1E506C233C598648709A018F9B8D5F3E5F05F0763F6E9C494D1375263CFF1EC4D8CB89E1D114D4E46809F13C2423C3D48A03F063516B1403EFC14981C582EBB89172D6BF7D191840B50D35AE33FA0E33C65812450E2C4D6901A19E92D14C2D2B8CA0E66900C19FFA2426FA29F4A6D3F12B2899A807830C2E44AFD8E4F4489E19E040B761E894722AEAF429E990DC021D874B46EB5102B66153CEDB8C59DE036AC9299CA7028F639F0020B639EC8BAFB368768F7FBBC63F32A7D59D5F5C16C7B141C05790E921A3DB2E6BA54FF3C0A4CCF695D1E63124F8E0639629A711545E965321DB29737AC7E951782749F61C5EF0B53BB9B57A9EF04DA9314241A5CB7DF6F3F45676EFF7097C0FA05E9705EC214F65287ED3F7C52A97C417903E708ECCC2DDDF78FD68558C5B0AD6A889545A3C6EA49D4E8D936C3B0E8CC5AB42B8FE82E56AD78D79631CE1BC32AD478CEBB841EF780558C4A355EE1EC20B592CFE334CE0AAFDB462B7A9A73967CF12DED26BC702551B9367725DB066C1F2EB898D1E390F2CA7A92459B83408804B2E15B41F78BC8BC4FE2508CBA63D0015EFA6EA3142B780FD826E7718CCD39699D85B3A185997085B12B2FFAAE21CC4DC8AFAFBF19097857A5DA97C3850ED745AA1FA02BF810632000467FB1D47BE663E95331C6850C365CC7760A9395AA323873777BB498DDF2004C30FE865831227B286B6EE97772ED35A459C961D5CFBCE95E11687A46F5F940DB8F40966FBD095B24D443B6FF78AA16EB483131C11F83686B0BC202D85B3BF21574AFCD087ED7A0056B427DC70E55572E65DE9B93A6833B5F1AC028019771B257219DF0E9D0A85613979019D22C62C891881C839D74658EC7EBFF1014938B2C2AB02DB5650146076B7258042572448543FBB6703F881D7F77B48EFD0D0691FD7C8F6E2E4962E0EC2D49A4618B2C6C1916781A03A62D6F7315A75D8F69295A53A9719F4C056BC71D6475D38819B5DD7A942D32ED872A24917759DD5B50F7B0453DB8B34BF9536BC3F8ADCC5176D2D29FA8C4470166CE2D415D97EB8B8901D11A385554B3B6E6FCF5561ACD926EBF38885F9427F3F0F31CA9D9DCBD0F1003E0045AF5C83443AEF452952F04A9319D0A20976E140C2653E831329E1C9936A5C105051A185C3AB10DE14187CA85E8475AEA3217E77A779E2EEEA6CFEBE5E4680F0FE43B5B0EAA2DFB327FB4DF462E9787B2DEBC00FCAE3473D0F071B5B8E7D8C1F4F19E5B488E395F8C419376F59C5503A318FACF1658455FA820DC3A7662EDDBA617377FD88BF4689FE43A1719A98B0CE7DFF56C825262D2F6955C658E009D2EFB44D03DFA89A88897F1568C2E4B196F0ADD46058F4514D8DC0025B7EC78D09D980158F409C25371321965FFB733C9794D5146F04A947FD05863F319261C537A4F9C4F19171140BCF40C7344CA808F5F95FCC9EED7835CF025DEBA42F952D7D3EFF53CEFE6A6D63B832F735AC044D07173F0F1021AA61FEC707523B347A8A916D1A43E80FF95D4590C9CC9E6E314CE1901D37856B05A9B276FBBAD8C3EEFA8A3E03F2416C42E5AEE6B2A8DDF6AEF3E72BC703F95DB621C6B167B9DC7087171333BCADDDF6F064D57F15DB8D808ECEE74E29A7A418741D9DFE9A7D52762F749141DEF7A365E626E87D0A55D049CD5B486A74C9B11619D23E849527253EA36386AC3EC58DB5DD6F2BBC98EA37550CC6B03E403A432F94026FD5B4F6F02BD0380F74E217265706911638426CABE96DE32601E6654529097C420B3BEFC1446F07BCA557066936979CD2044E02BC301BAC9D0B625F1698CD49B5DFDFFF09C72A88549435A78B9B3EBB10CFB323BCBF73F900D5B9E995A11B4BA43383144248B4E11DAAA86E1762CA1B1CE4B789B0008973F034EB94C322EAB89BF149D4E64801EAB793039EB8A4528C5743E700E0B28290F401B18B057B8B66FC1B0D253C8848F8C1FE9E932E670AAED671249EFF1E7B0D6F410F0B10E68CB86133741367A271257CDEC05FDF95FD8DB73E7DB161ECD7023B2DEEBB4CE39526728653EDB0A114CE7E0D058EC1DC2A1681EACB87E1EA883855BEC8F60D26CFD91CD1385C59C6862CE3B2A3701120D7033A180CFA03A2D79CD43796F6BDCC21CBC999DE68DAB77431E3A8CE566DABCB5C8DD1EEE5937B39F0B0C4AF59F3FD05988F9931373118F47FD5D7521EFF96056E0B76BA81ECA3941C5D3E70BC8DB8E9E1D51B817DA79C9411D2B10500E33601E662408B8E9CF3DD9E7D43E7422BA734DFDE7030291FC5B1ECBDCE46EF22A06738A99A02D78F770FB4E0B5A1C8B8C99EA712D65B71363DE9 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\kuhl_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\kuhl_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\kuhl_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\kuhl_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3104) kuhl.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\kuhl_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
422
Text files
318
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3104 | kuhl.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.wykwwux | — | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\$Recycle.Bin\WYKWWUX-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3104 | kuhl.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\WYKWWUX-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3104 | kuhl.exe | GET | 301 | 138.201.162.99:80 | http://www.kakaocorp.link/ | DE | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3104 | kuhl.exe | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
3104 | kuhl.exe | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |